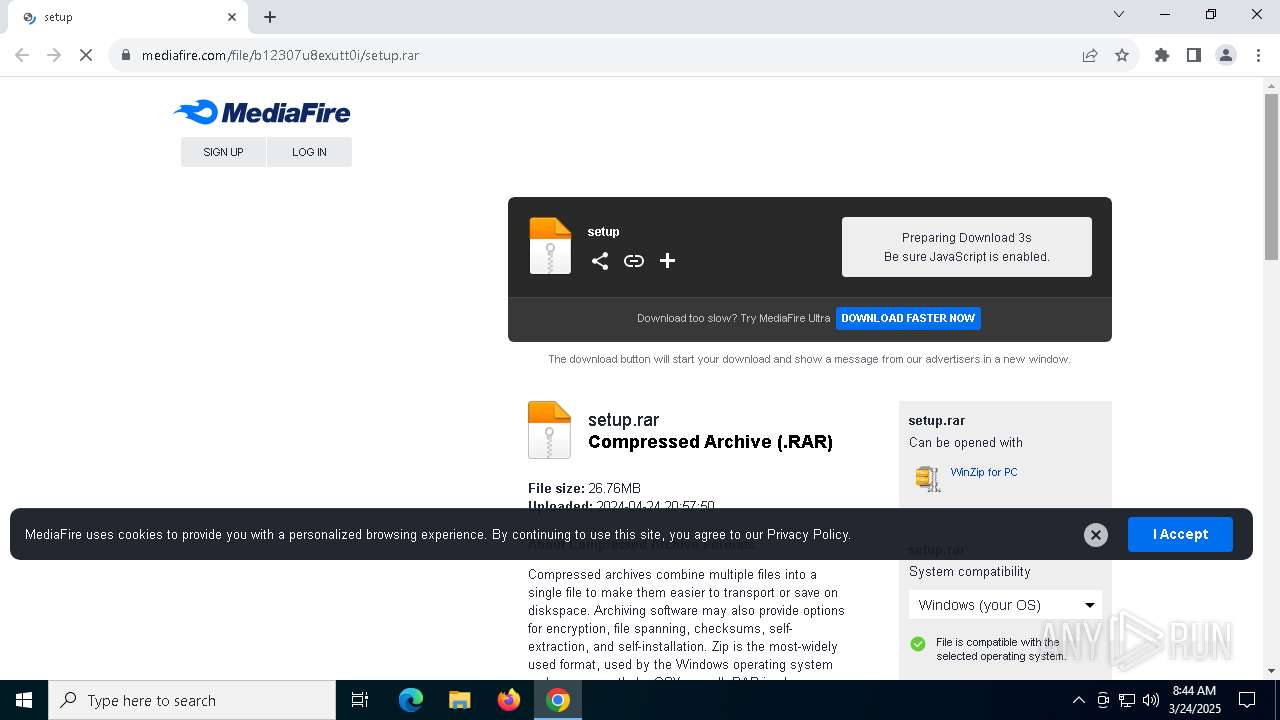
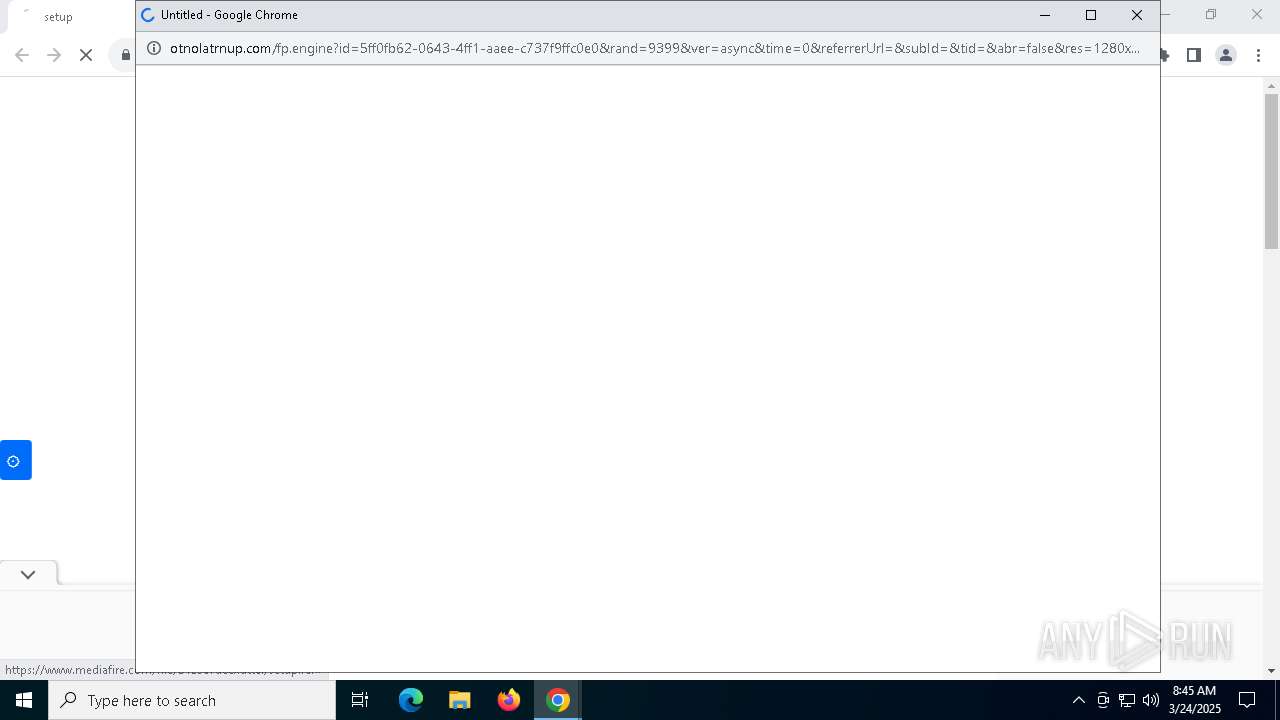
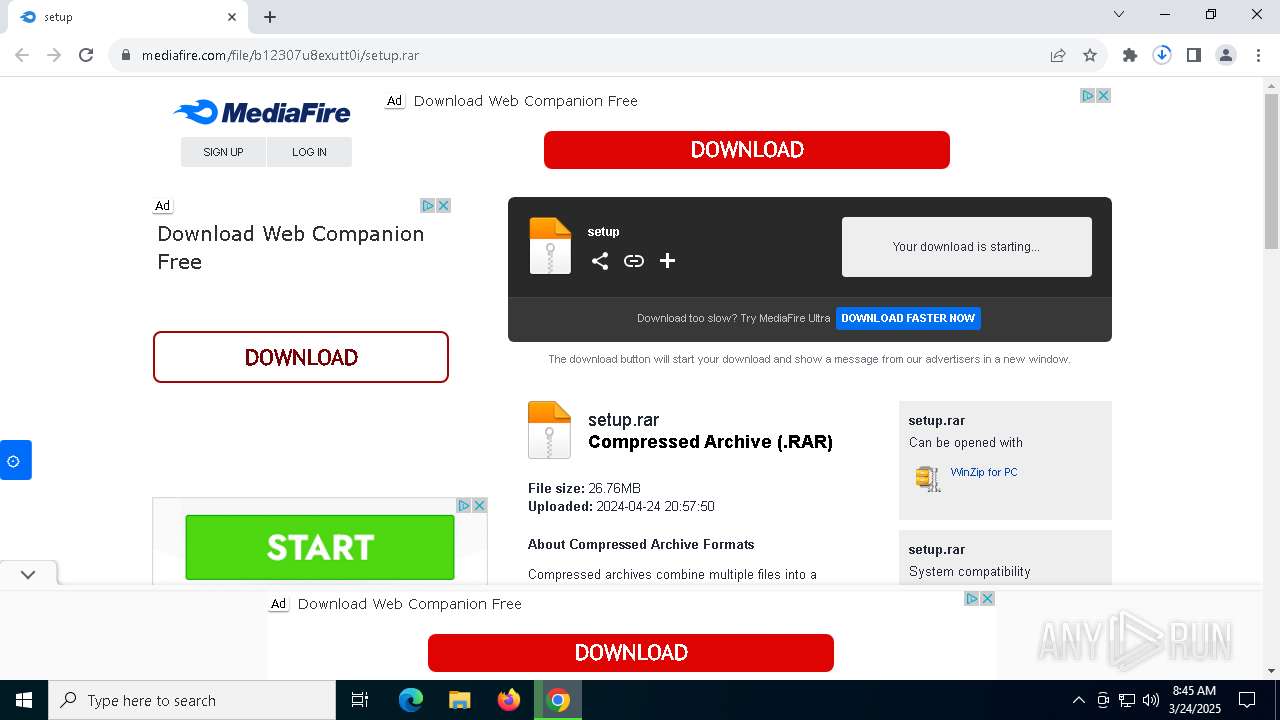
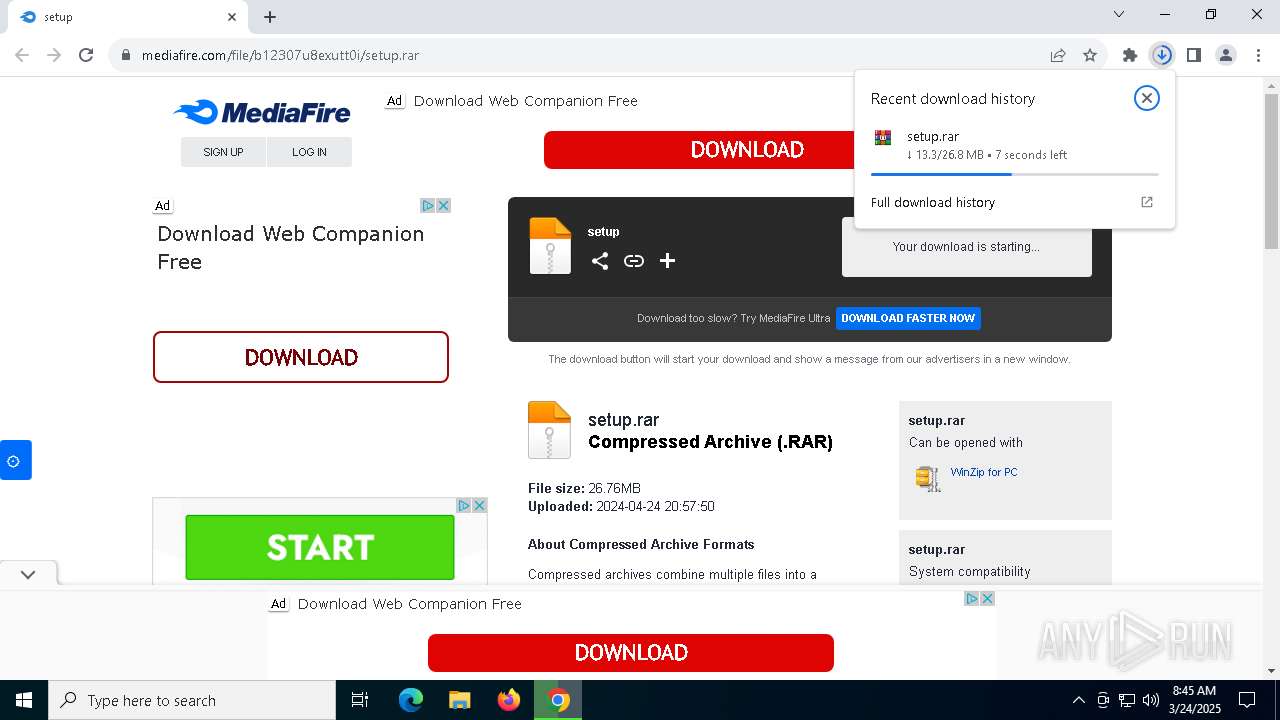
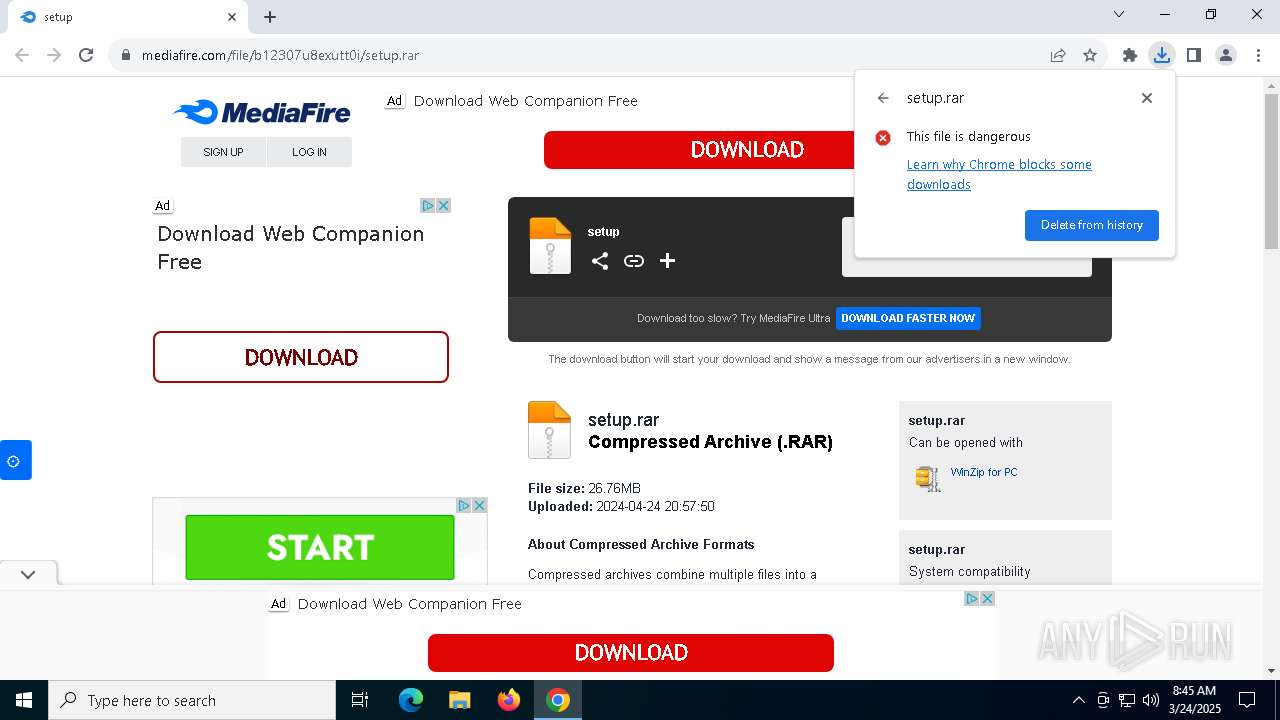
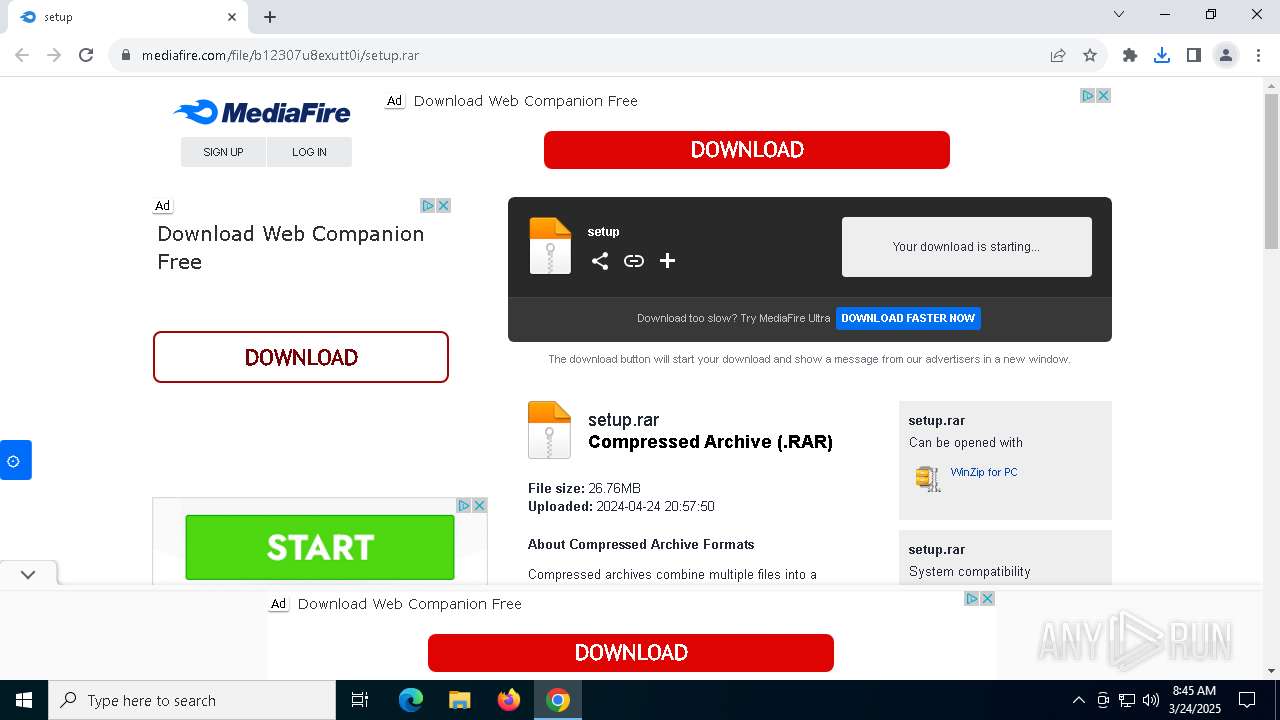
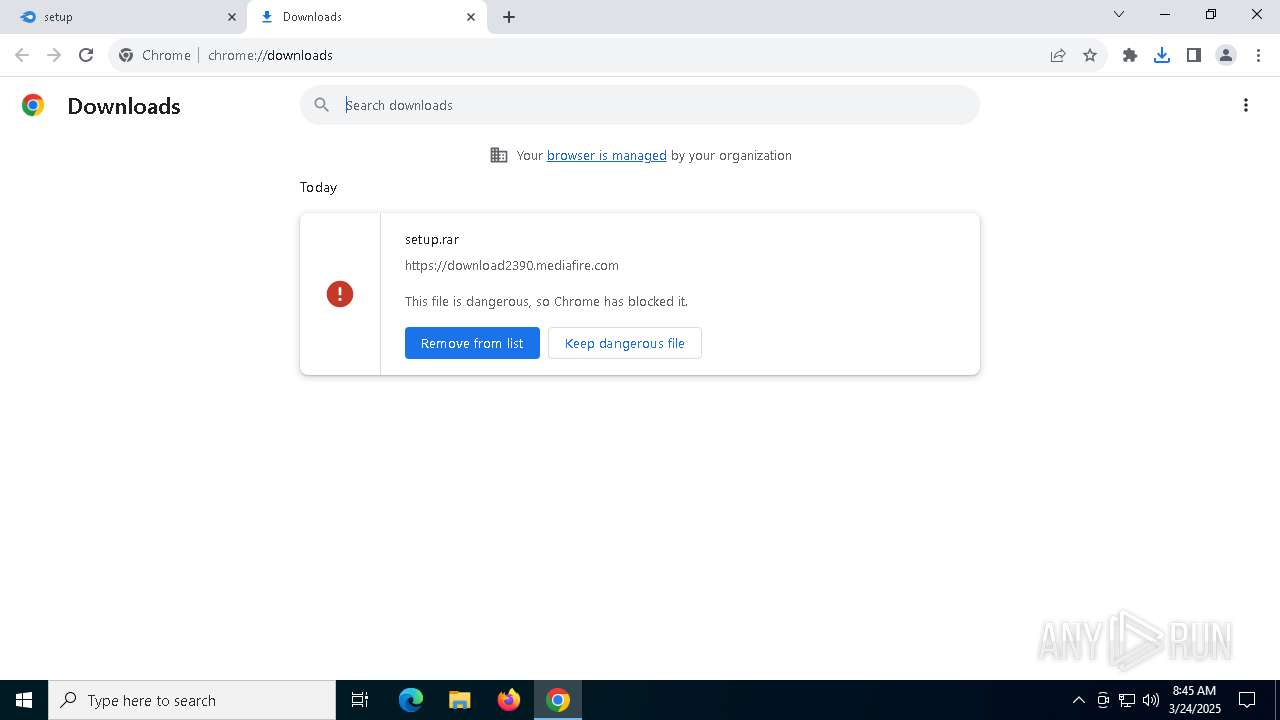
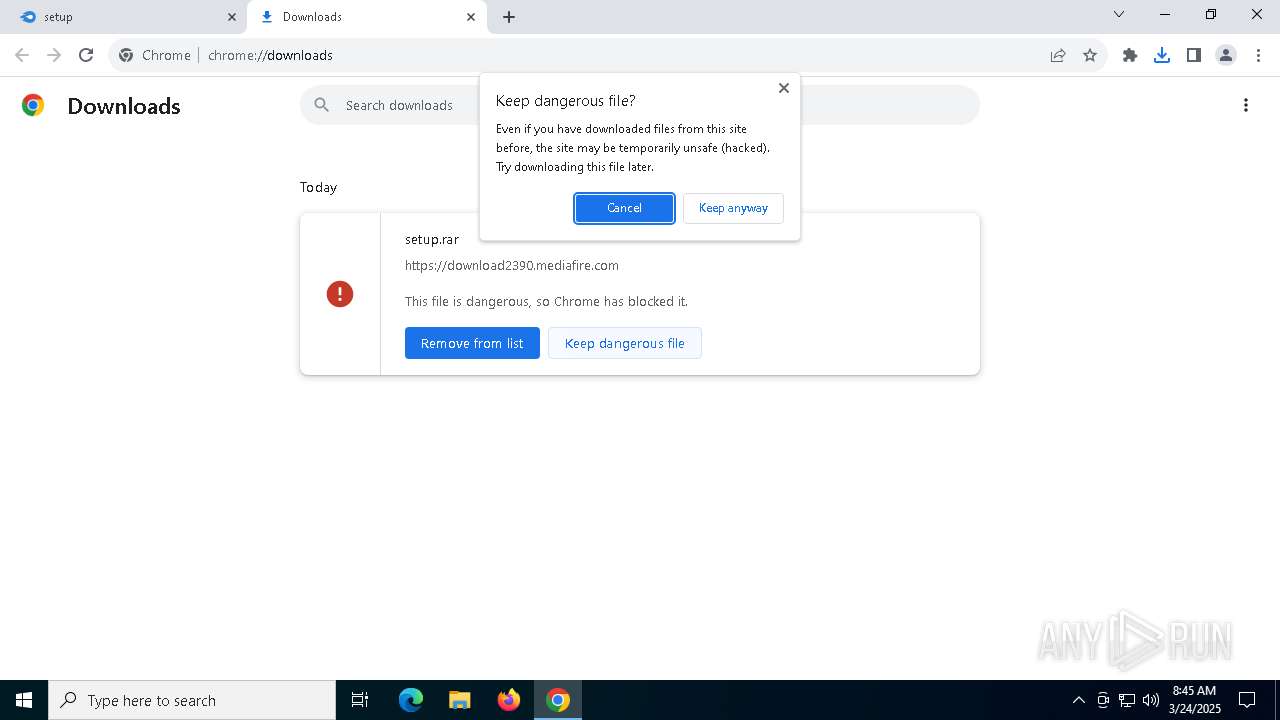
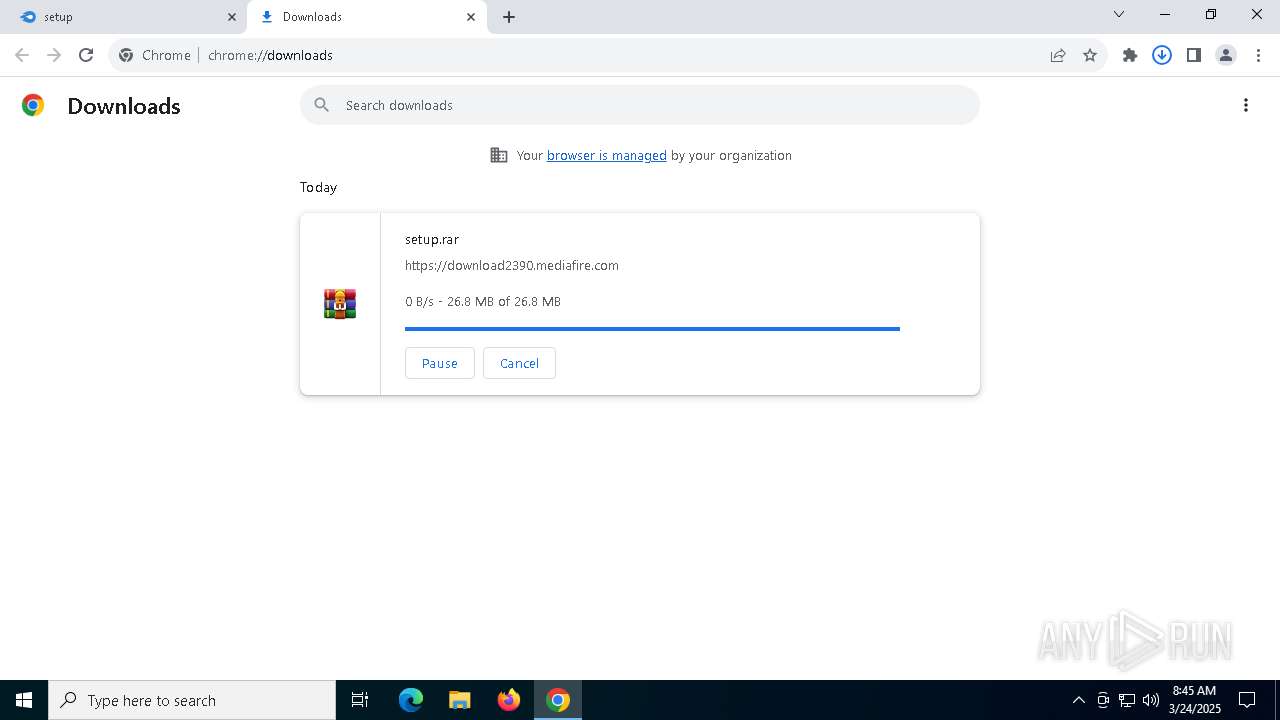
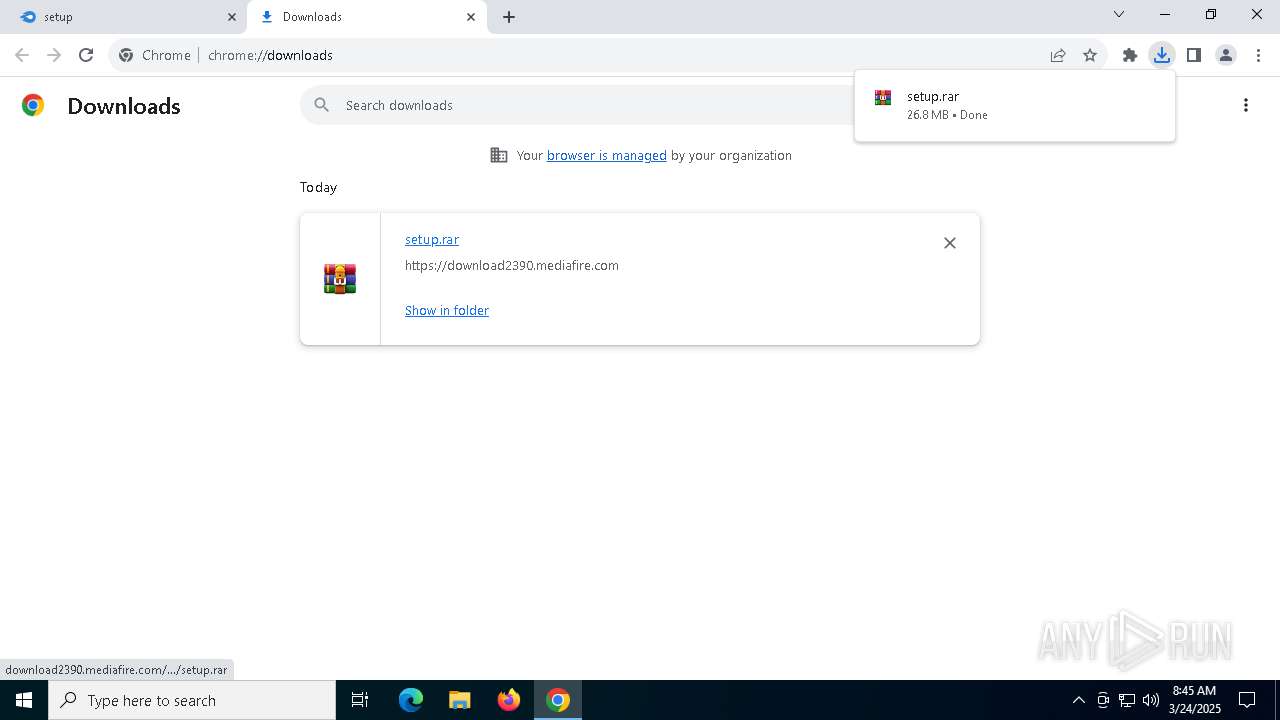
| URL: | https://www.mediafire.com/file/b12307u8exutt0i/setup.rar |
| Full analysis: | https://app.any.run/tasks/80bff633-ad16-4ed0-8224-d73800feee9a |
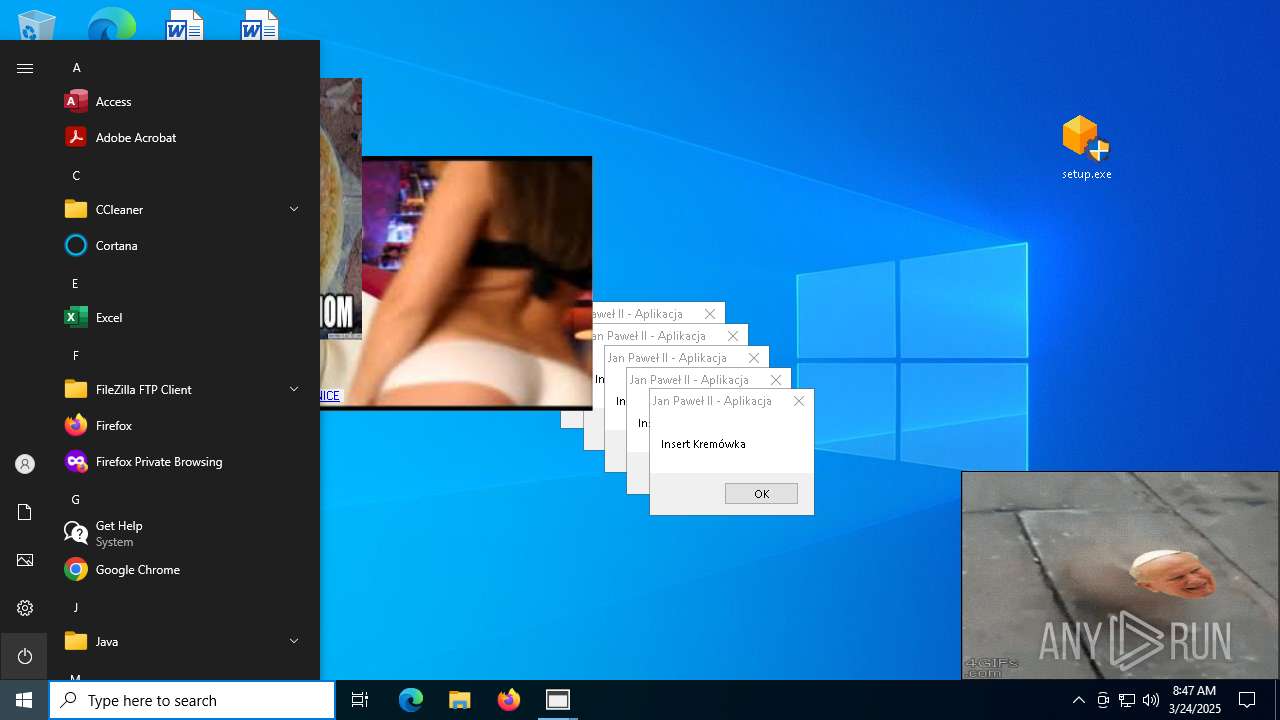
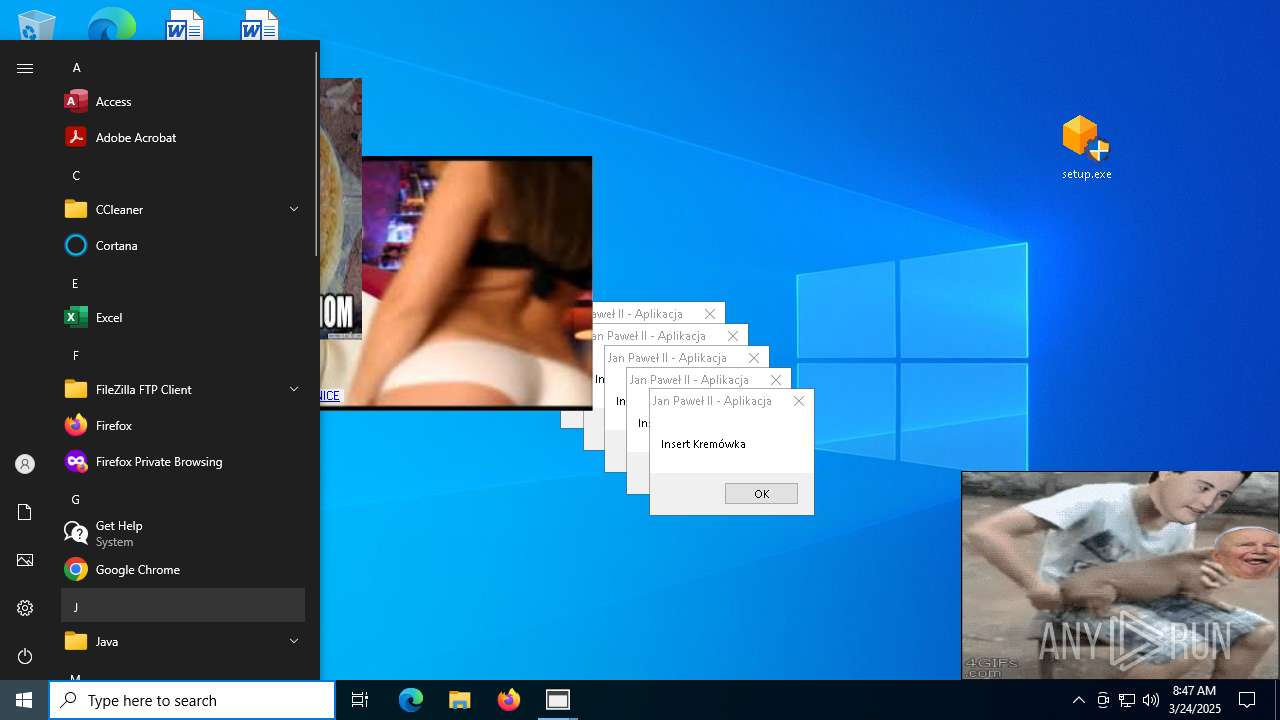
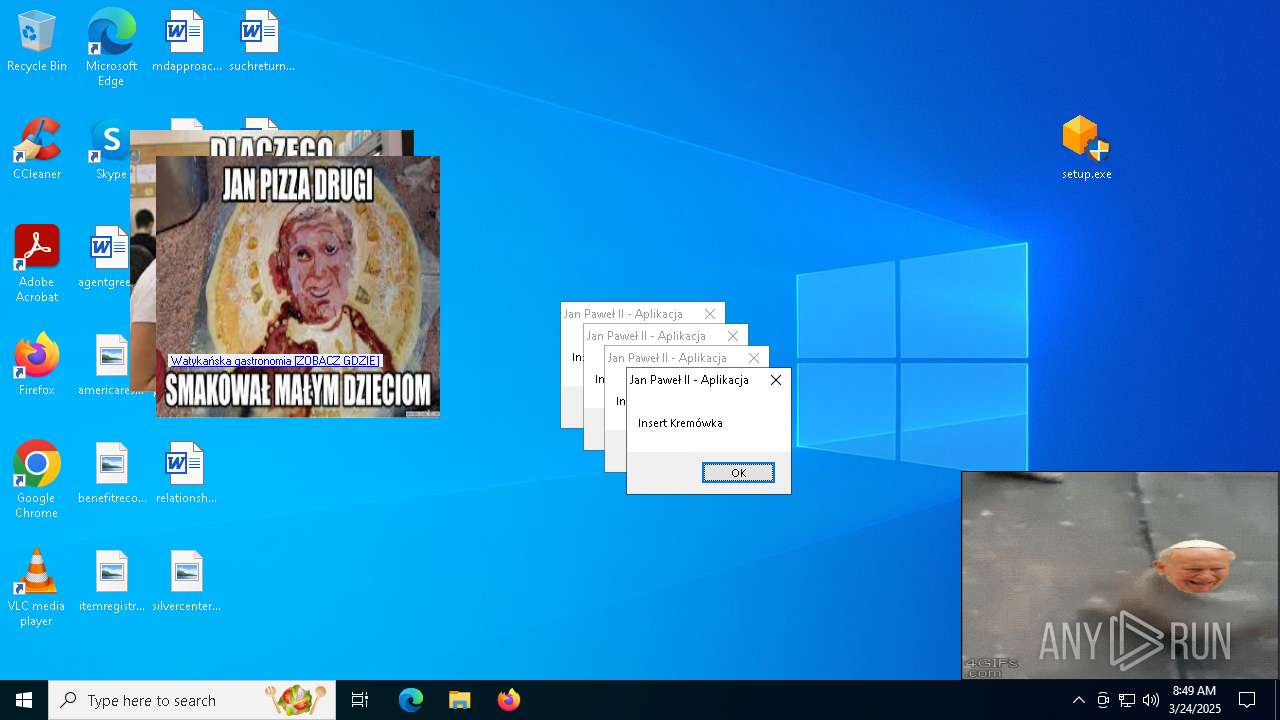
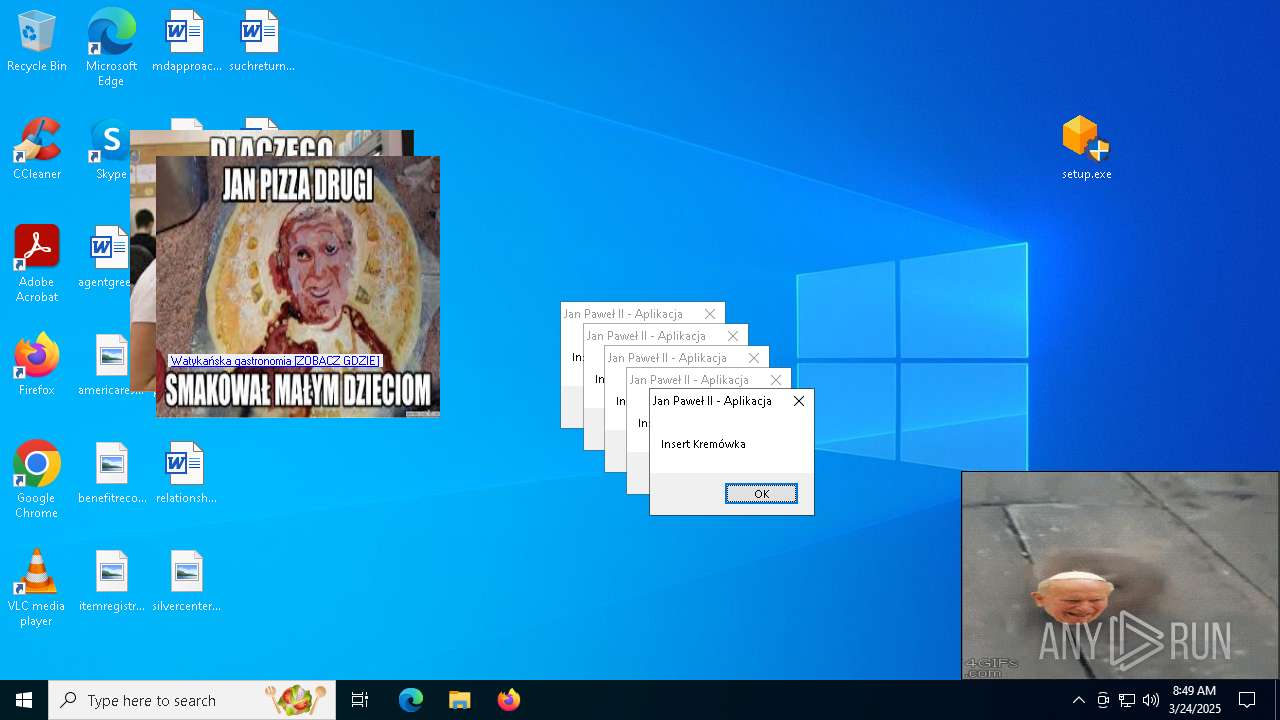
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | March 24, 2025, 08:44:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 422981AAE6A46E59CE0075F776FBAD0E |
| SHA1: | 821E7C1FC1E2C125888919A19CE8C0F6FF6CD69A |
| SHA256: | 703076211C90CCD91B088F8519AFDE5AC1AC04B4B8EB9141B386B845D0DC50B3 |
| SSDEEP: | 3:N8DSLw3eGUoZ4YRzMNPOn:2OLw3eGy8gVO |
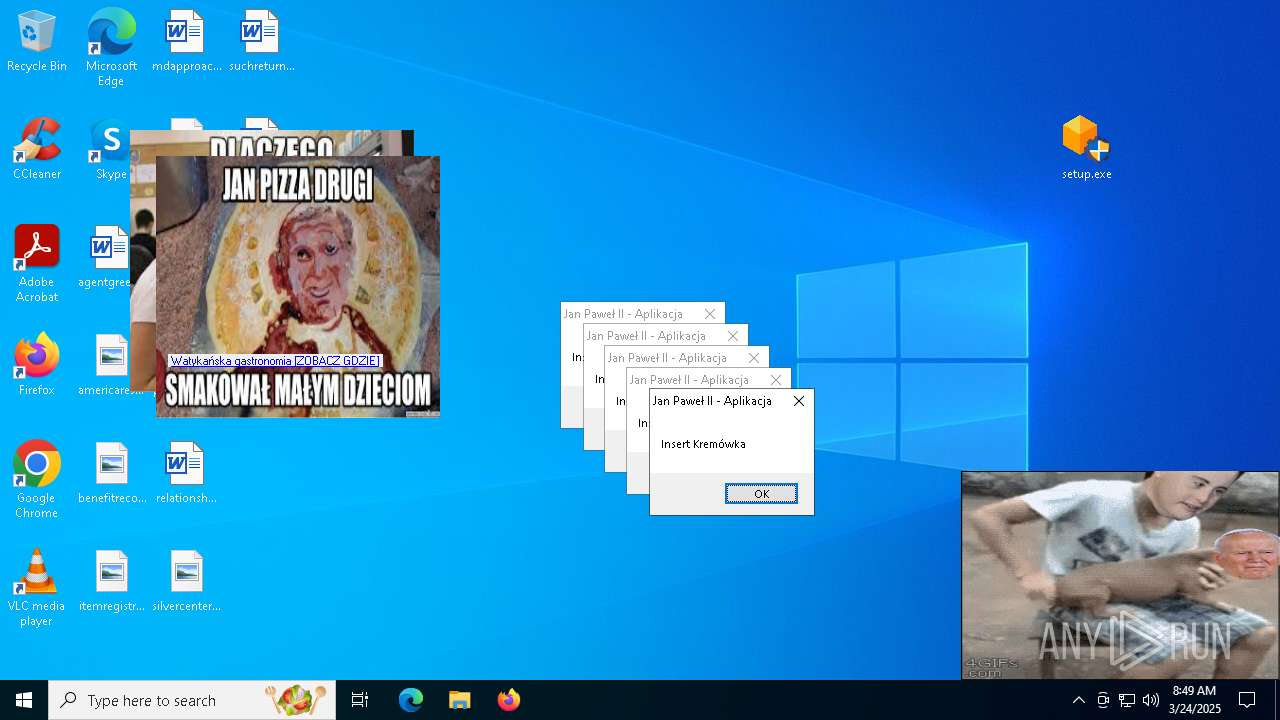
MALICIOUS
Changes Windows Defender settings
- setup.exe (PID: 3768)
- updater.exe (PID: 7036)
Adds extension to the Windows Defender exclusion list
- setup.exe (PID: 3768)
- updater.exe (PID: 7036)
Changes the autorun value in the registry
- Watykanczyk.exe (PID: 3676)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 8084)
MINER has been detected (SURICATA)
- msedge.exe (PID: 7476)
Vulnerable driver has been detected
- updater.exe (PID: 7036)
- updater.exe (PID: 2872)
XMRIG has been detected (YARA)
- explorer.exe (PID: 812)
SUSPICIOUS
BASE64 encoded PowerShell command has been detected
- setup.exe (PID: 7480)
Starts POWERSHELL.EXE for commands execution
- setup.exe (PID: 7480)
- setup.exe (PID: 3768)
- updater.exe (PID: 7036)
Executable content was dropped or overwritten
- setup.exe (PID: 7480)
- setup.exe (PID: 3768)
- updater.exe (PID: 7036)
- updater.exe (PID: 2872)
Base64-obfuscated command line is found
- setup.exe (PID: 7480)
Reads security settings of Internet Explorer
- setup.exe (PID: 7480)
- Watykanczyk.exe (PID: 3676)
Script adds exclusion path to Windows Defender
- setup.exe (PID: 3768)
- updater.exe (PID: 7036)
Script adds exclusion extension to Windows Defender
- setup.exe (PID: 3768)
- updater.exe (PID: 7036)
Manipulates environment variables
- powershell.exe (PID: 7520)
- powershell.exe (PID: 8040)
Starts CMD.EXE for commands execution
- setup.exe (PID: 3768)
- updater.exe (PID: 7036)
- updater.exe (PID: 2872)
Stops a currently running service
- sc.exe (PID: 8116)
- sc.exe (PID: 7812)
- sc.exe (PID: 7396)
- sc.exe (PID: 7400)
- sc.exe (PID: 7784)
- sc.exe (PID: 6208)
- sc.exe (PID: 7252)
- sc.exe (PID: 3020)
- sc.exe (PID: 632)
- sc.exe (PID: 4612)
- sc.exe (PID: 5884)
- sc.exe (PID: 3924)
- sc.exe (PID: 3944)
- sc.exe (PID: 6092)
- sc.exe (PID: 7624)
- sc.exe (PID: 8148)
Modifies hosts file to alter network resolution
- setup.exe (PID: 3768)
- updater.exe (PID: 2872)
Uses powercfg.exe to modify the power settings
- setup.exe (PID: 3768)
- updater.exe (PID: 7036)
- updater.exe (PID: 2872)
Windows service management via SC.EXE
- sc.exe (PID: 7328)
- sc.exe (PID: 2084)
Creates a new Windows service
- sc.exe (PID: 6728)
Starts SC.EXE for service management
- setup.exe (PID: 3768)
- updater.exe (PID: 7036)
- updater.exe (PID: 2872)
Executes as Windows Service
- updater.exe (PID: 7036)
Process uninstalls Windows update
- wusa.exe (PID: 7384)
- wusa.exe (PID: 8004)
Reads Internet Explorer settings
- Watykanczyk.exe (PID: 3676)
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 7036)
- updater.exe (PID: 2872)
Potential Corporate Privacy Violation
- msedge.exe (PID: 7476)
Connects to unusual port
- explorer.exe (PID: 812)
- explorer.exe (PID: 6152)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4252)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 8056)
Reads Microsoft Office registry keys
- chrome.exe (PID: 4944)
Autorun file from Downloads
- chrome.exe (PID: 1164)
Executable content was dropped or overwritten
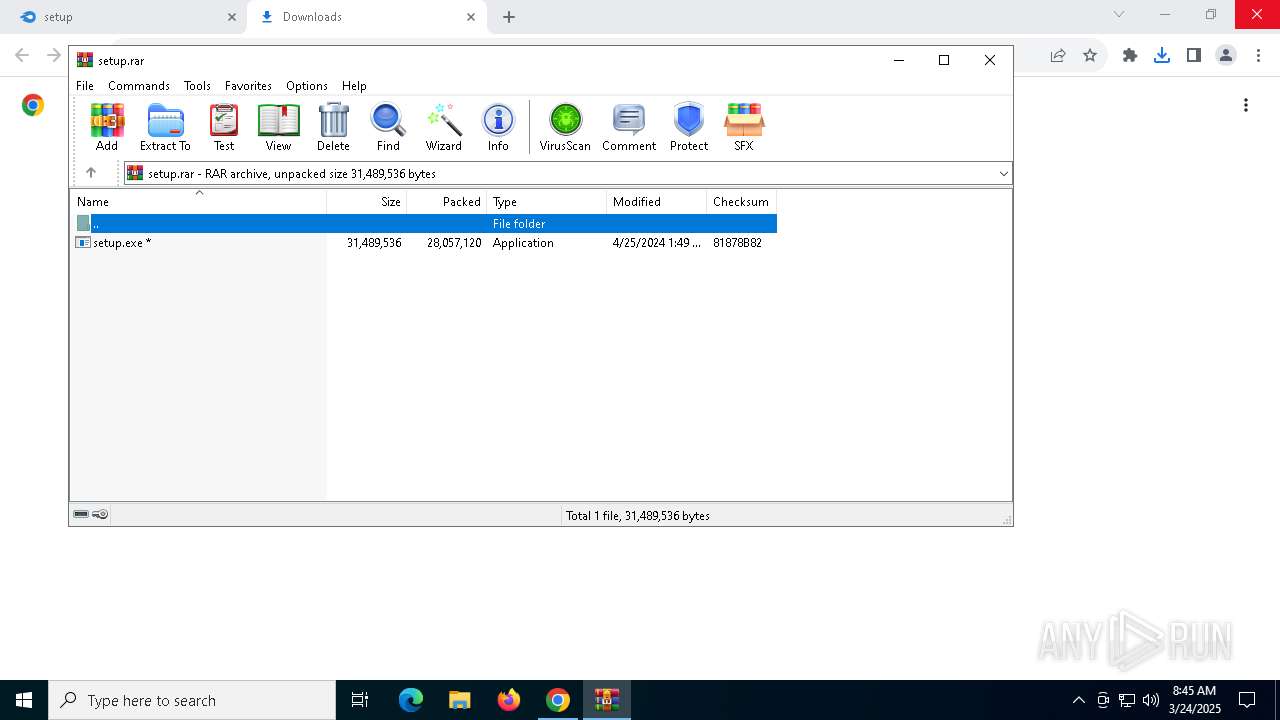
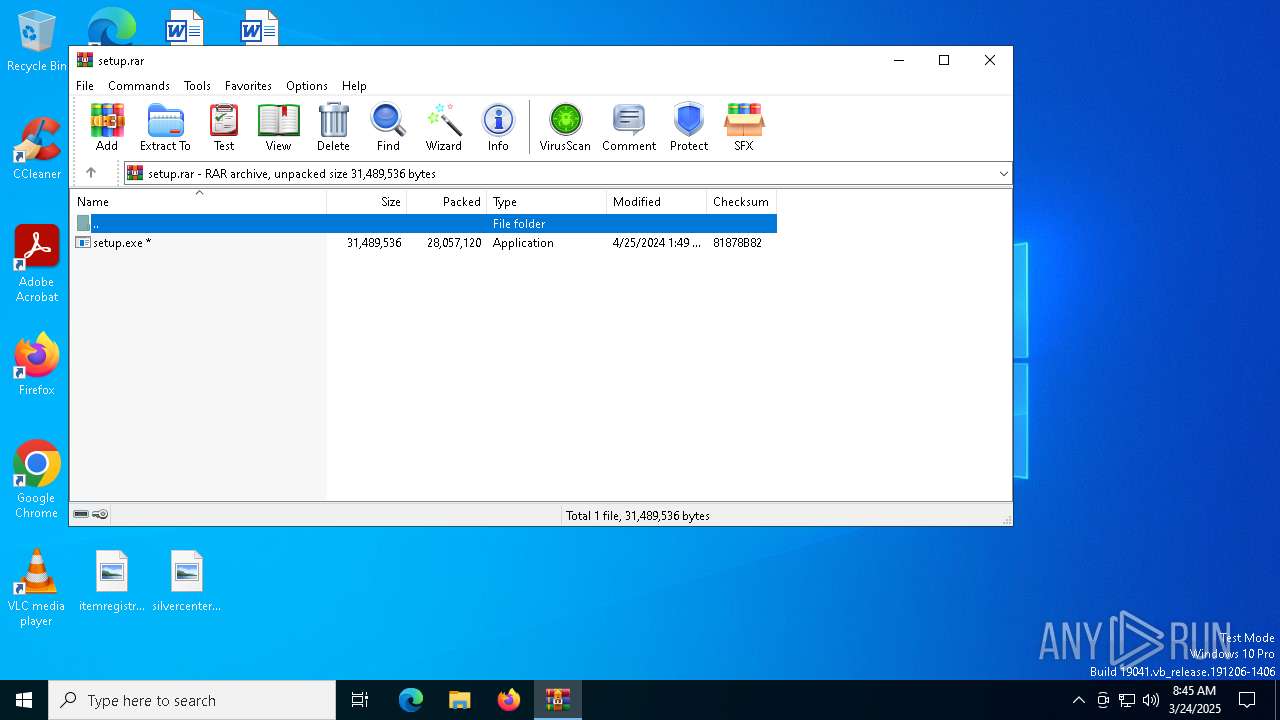
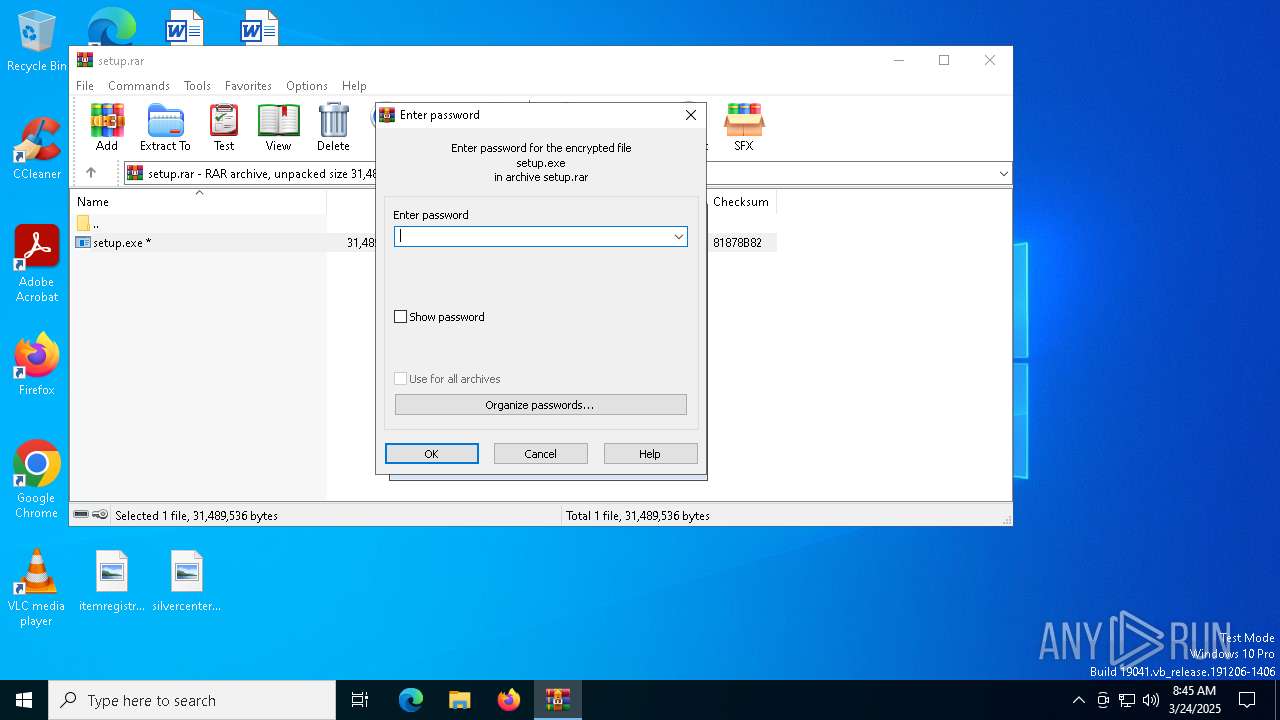
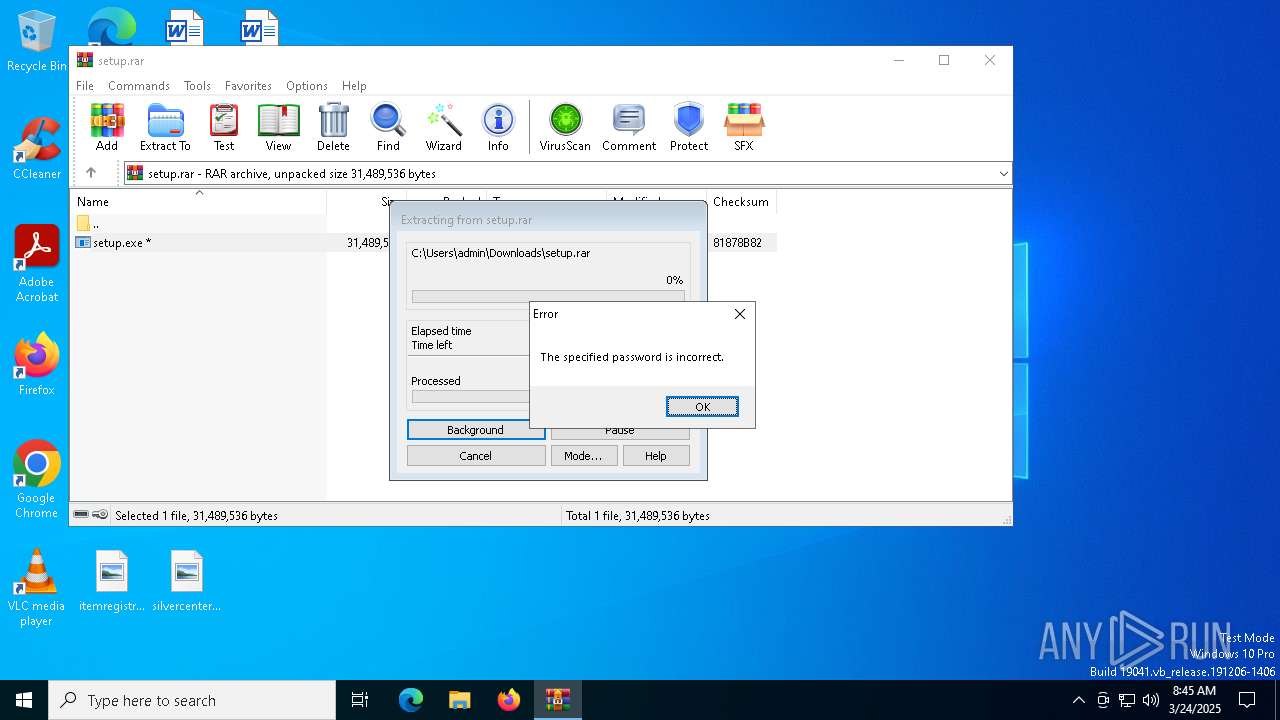
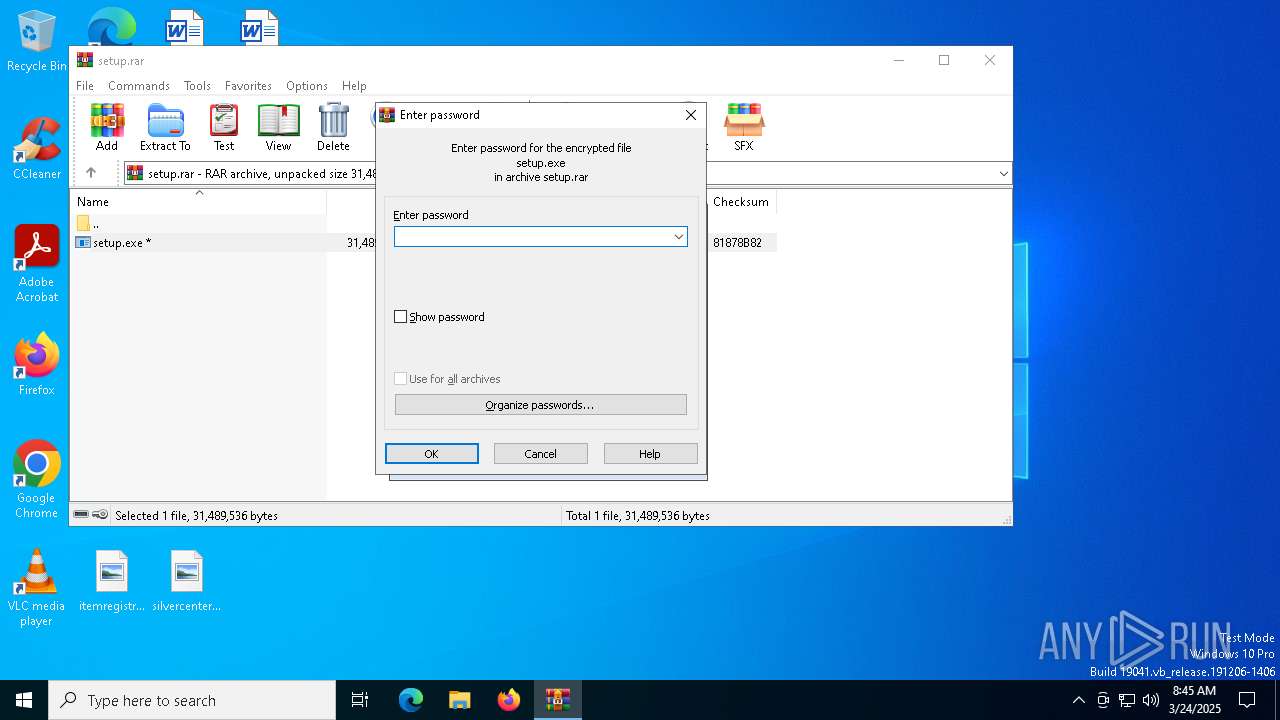
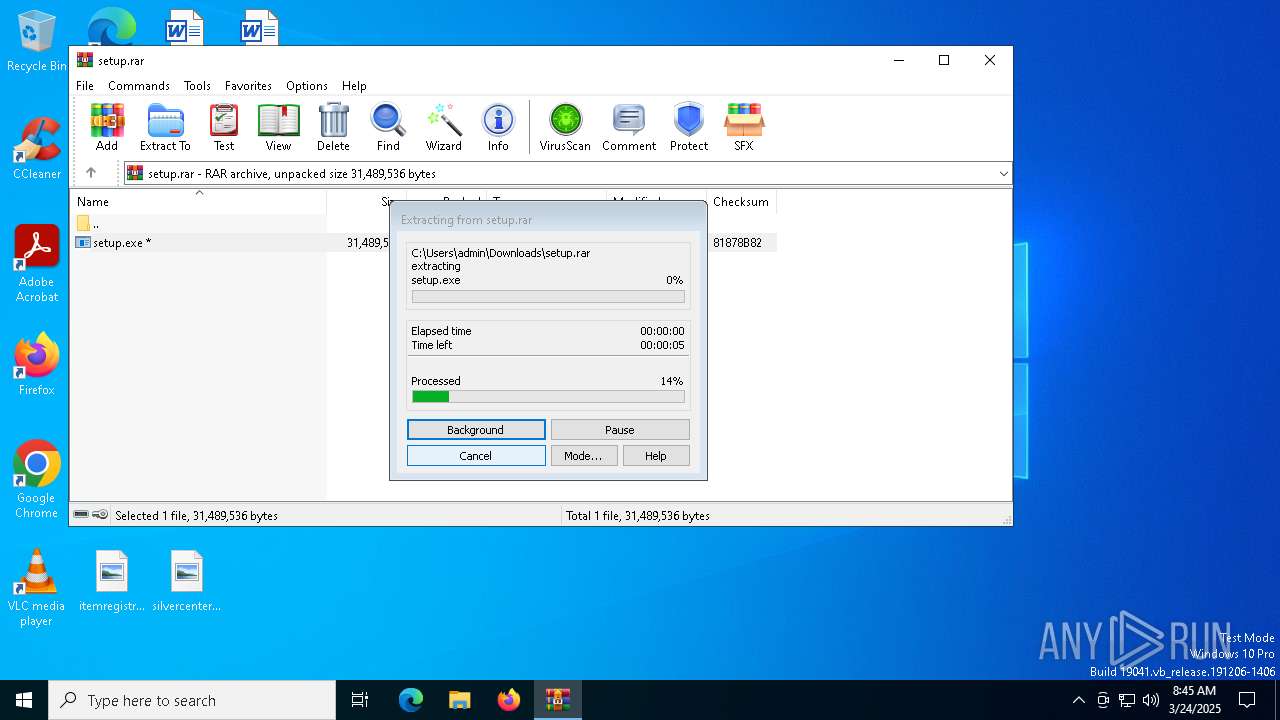
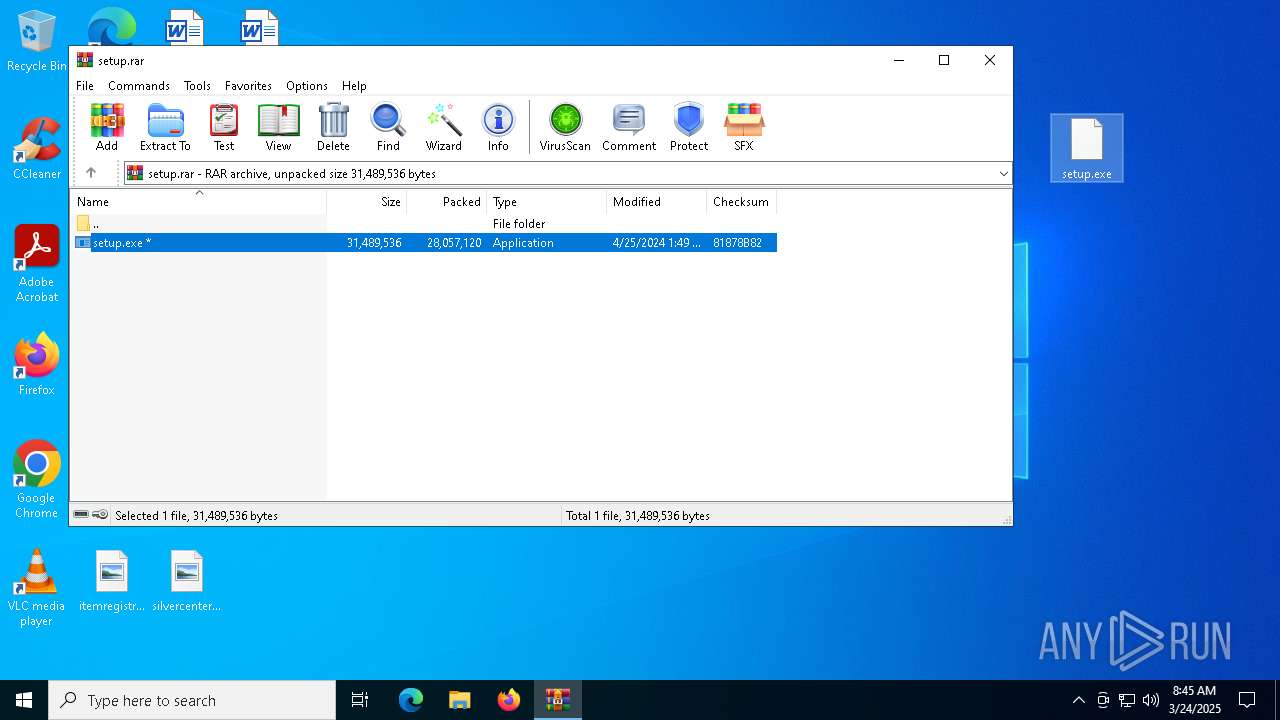
- WinRAR.exe (PID: 8056)
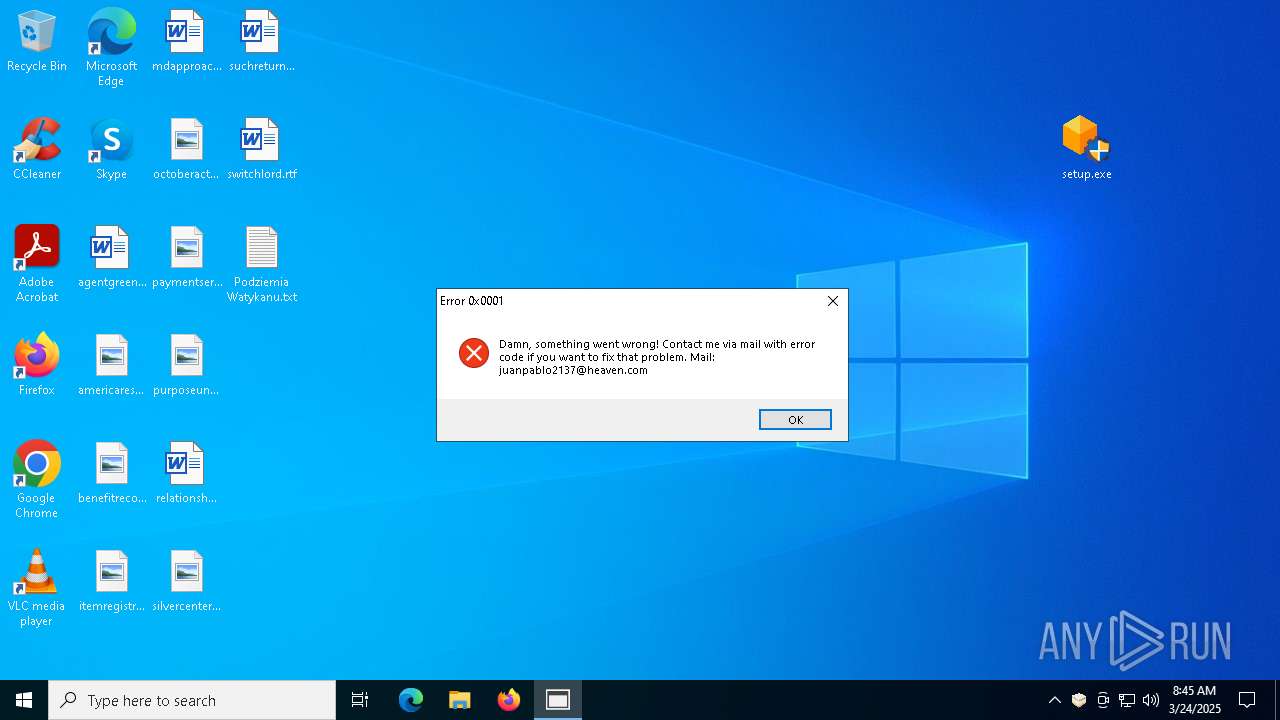
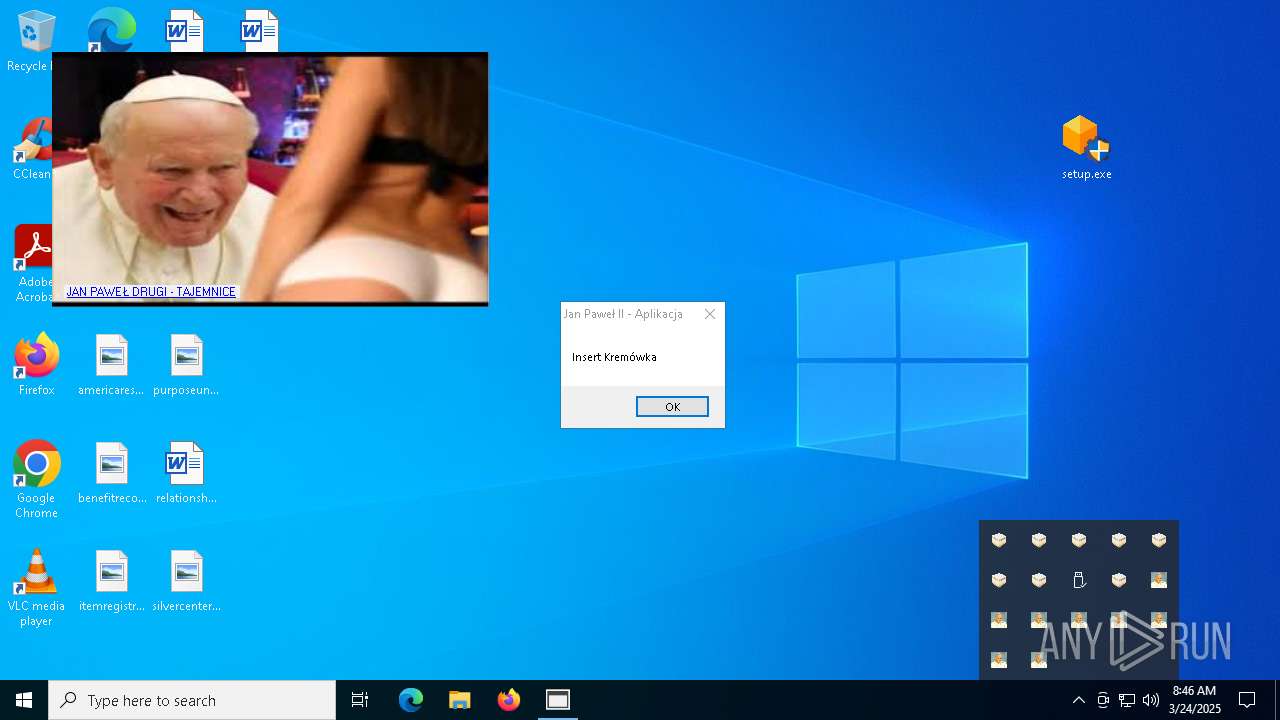
Manual execution by a user
- setup.exe (PID: 3884)
- setup.exe (PID: 7480)
- msedge.exe (PID: 536)
- Watykanczyk.exe (PID: 6796)
Checks supported languages
- setup.exe (PID: 7480)
- setup.exe (PID: 3768)
- Watykanczyk.exe (PID: 3676)
- updater.exe (PID: 7036)
- identity_helper.exe (PID: 8056)
- identity_helper.exe (PID: 1512)
- Watykanczyk.exe (PID: 6796)
Process checks computer location settings
- setup.exe (PID: 7480)
Reads the computer name
- setup.exe (PID: 7480)
- Watykanczyk.exe (PID: 3676)
- identity_helper.exe (PID: 8056)
Reads the machine GUID from the registry
- Watykanczyk.exe (PID: 3676)
Create files in a temporary directory
- setup.exe (PID: 7480)
Application launched itself
- chrome.exe (PID: 4944)
- msedge.exe (PID: 8112)
- msedge.exe (PID: 536)
- msedge.exe (PID: 7768)
Reads Environment values
- Watykanczyk.exe (PID: 3676)
- identity_helper.exe (PID: 8056)
Creates files or folders in the user directory
- Watykanczyk.exe (PID: 3676)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 7520)
- powershell.exe (PID: 8040)
Disables trace logs
- Watykanczyk.exe (PID: 3676)
Checks proxy server information
- Watykanczyk.exe (PID: 3676)
- slui.exe (PID: 8008)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 7520)
- powershell.exe (PID: 8040)
Reads the software policy settings
- slui.exe (PID: 7908)
- slui.exe (PID: 8008)
Creates files in the program directory
- setup.exe (PID: 3768)
- PLUGScheduler.exe (PID: 4252)
The sample compiled with japanese language support
- updater.exe (PID: 7036)
- updater.exe (PID: 2872)
UPX packer has been detected
- explorer.exe (PID: 812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
420
Monitored processes
169
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --flag-switches-end --do-not-de-elevate --single-argument http://karachan.org/b/ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\WINDOWS\system32\sc.exe stop dosvc | C:\Windows\System32\sc.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6484 --field-trial-handle=2336,i,6930284048627682165,8363189001682386400,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | explorer.exe | C:\Windows\explorer.exe | updater.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Explorer Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4928 --field-trial-handle=2320,i,1584149532314973613,3606665031696634265,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x310,0x314,0x318,0x308,0x320,0x7ffc80855fd8,0x7ffc80855fe4,0x7ffc80855ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 669
Read events
34 572
Write events
96
Delete events
1
Modification events
| (PID) Process: | (4944) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4944) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4944) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4944) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4944) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000008767F717999CDB01 | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\setup.rar | |||
Executable files
16
Suspicious files
317
Text files
137
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c40d.TMP | — | |
MD5:— | SHA256:— | |||
| 4944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c40d.TMP | — | |
MD5:— | SHA256:— | |||
| 4944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c40d.TMP | — | |
MD5:— | SHA256:— | |||
| 4944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c40d.TMP | — | |
MD5:— | SHA256:— | |||
| 4944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c41d.TMP | — | |
MD5:— | SHA256:— | |||
| 4944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
272
DNS requests
380
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7632 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3676 | Watykanczyk.exe | GET | 301 | 199.232.196.193:80 | http://i.imgur.com/FzGMM7P.jpg | unknown | — | — | whitelisted |
7668 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7668 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5568 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7312 | chrome.exe | 104.17.150.117:443 | www.mediafire.com | CLOUDFLARENET | — | whitelisted |
4944 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7312 | chrome.exe | 142.251.18.84:443 | — | GOOGLE | US | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7312 | chrome.exe | 104.21.42.32:443 | the.gatekeeperconsent.com | CLOUDFLARENET | — | unknown |
7312 | chrome.exe | 142.250.185.200:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| whitelisted |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
the.gatekeeperconsent.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
static.mediafire.com |
| whitelisted |
privacy.gatekeeperconsent.com |
| unknown |
btloader.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7312 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7312 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7312 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7312 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
7476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7476 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Observed DNS Query to Coin Mining Domain (nanopool .org) |
7476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |