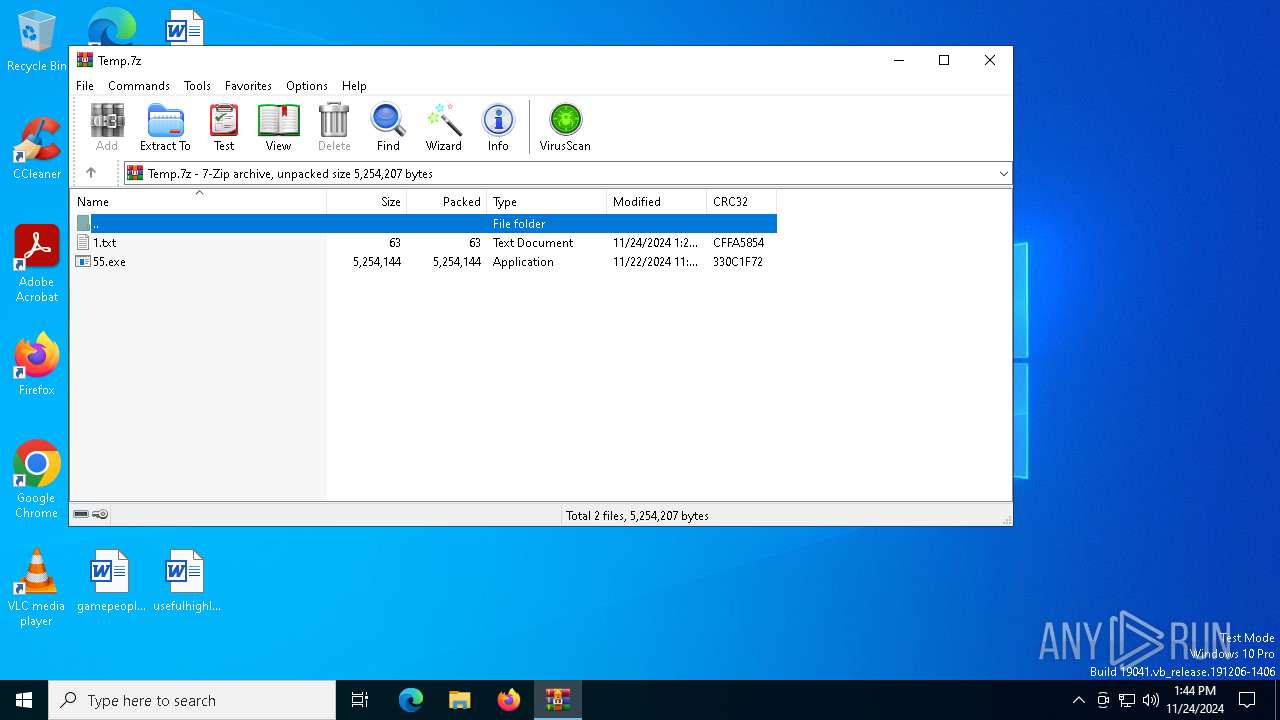
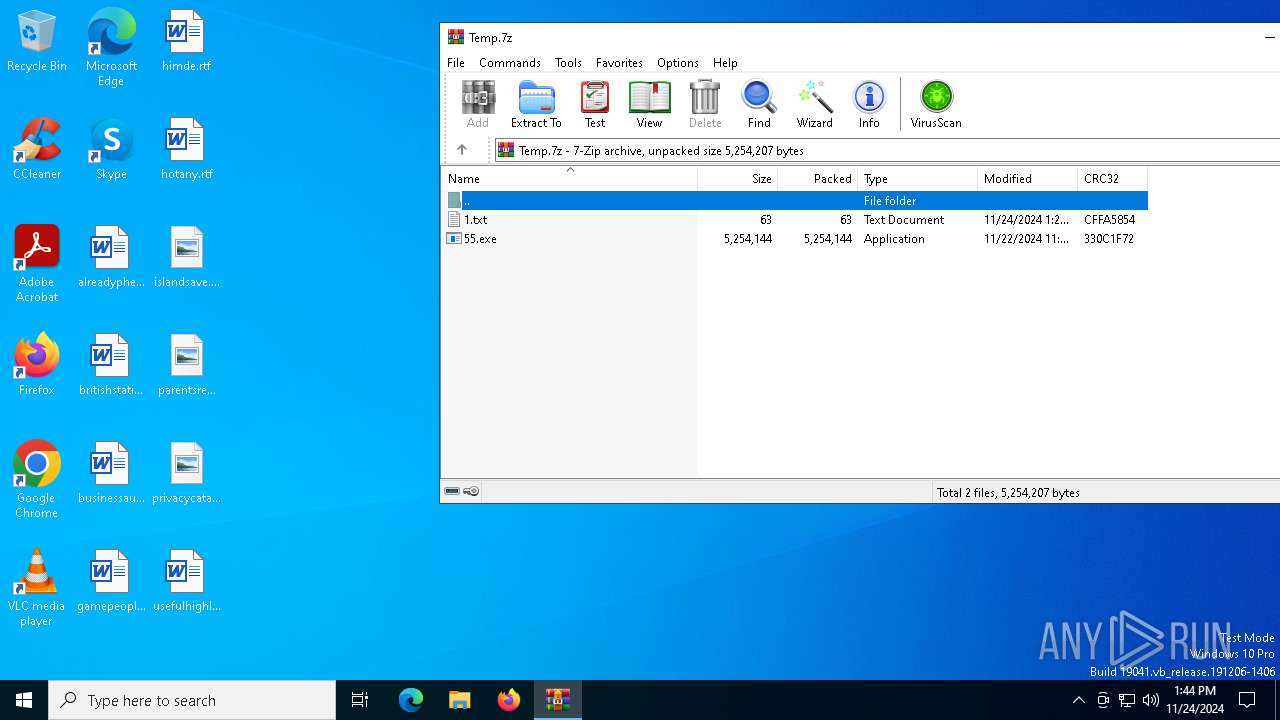
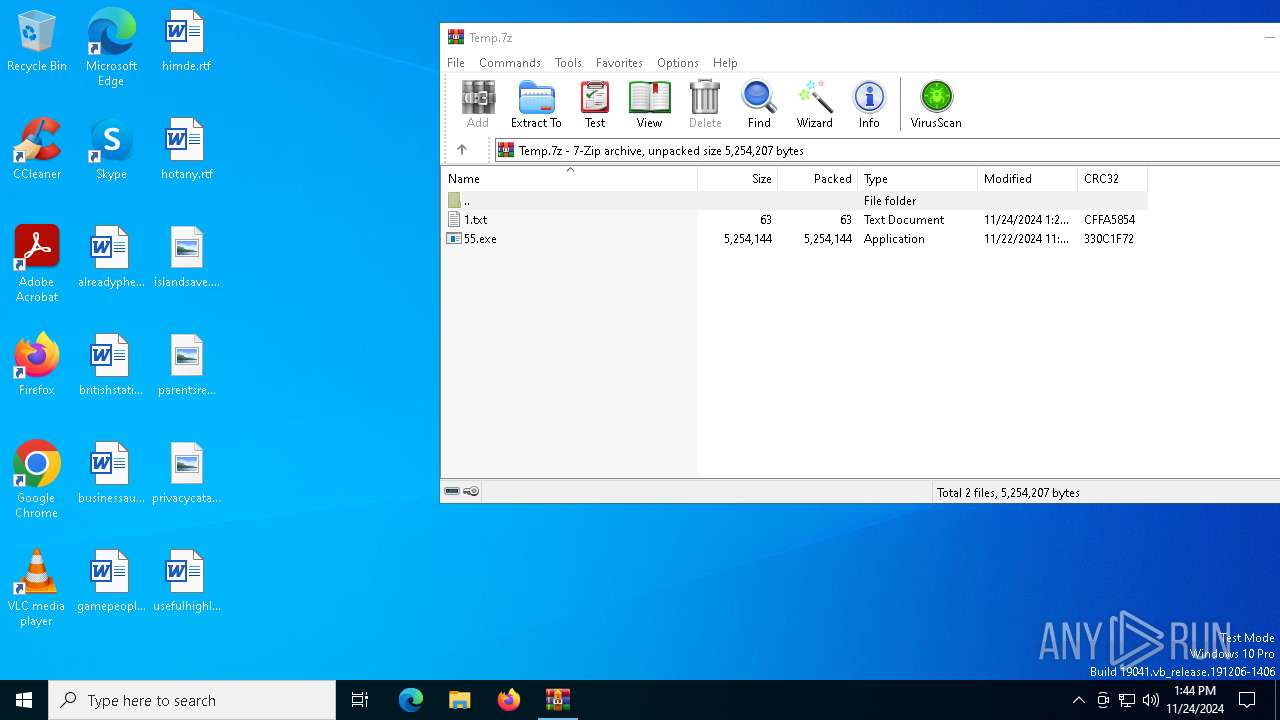
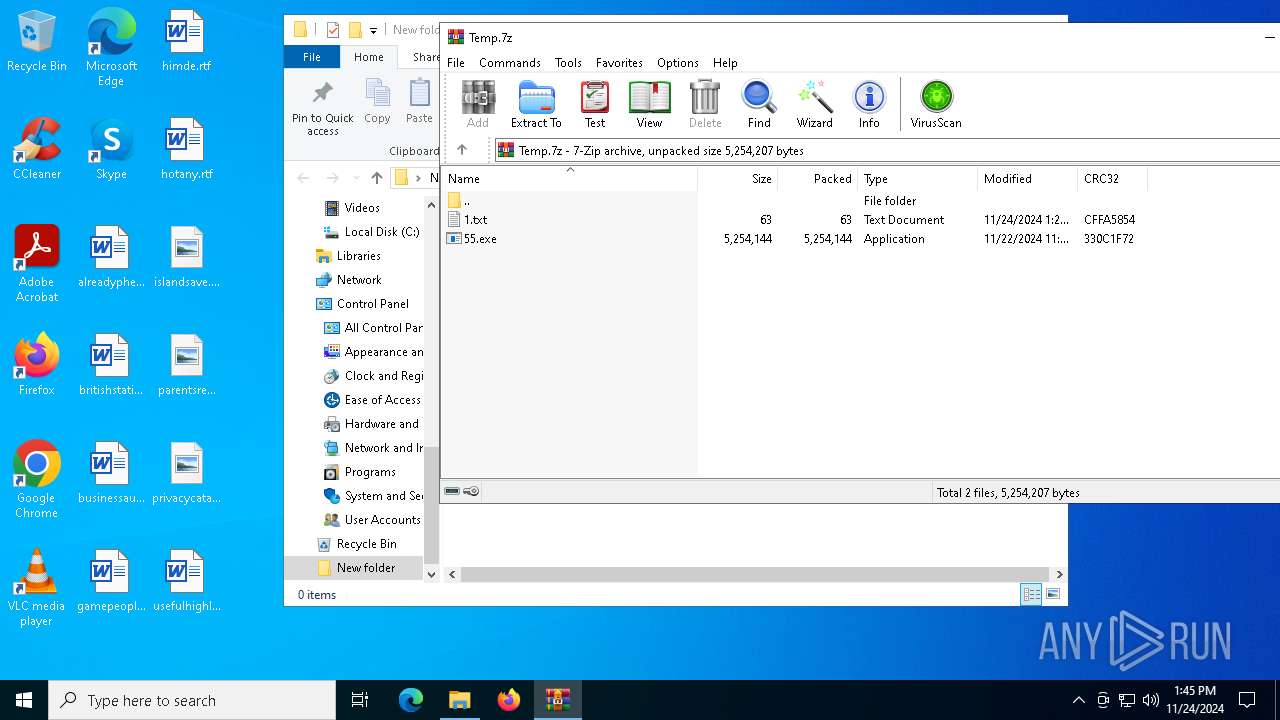
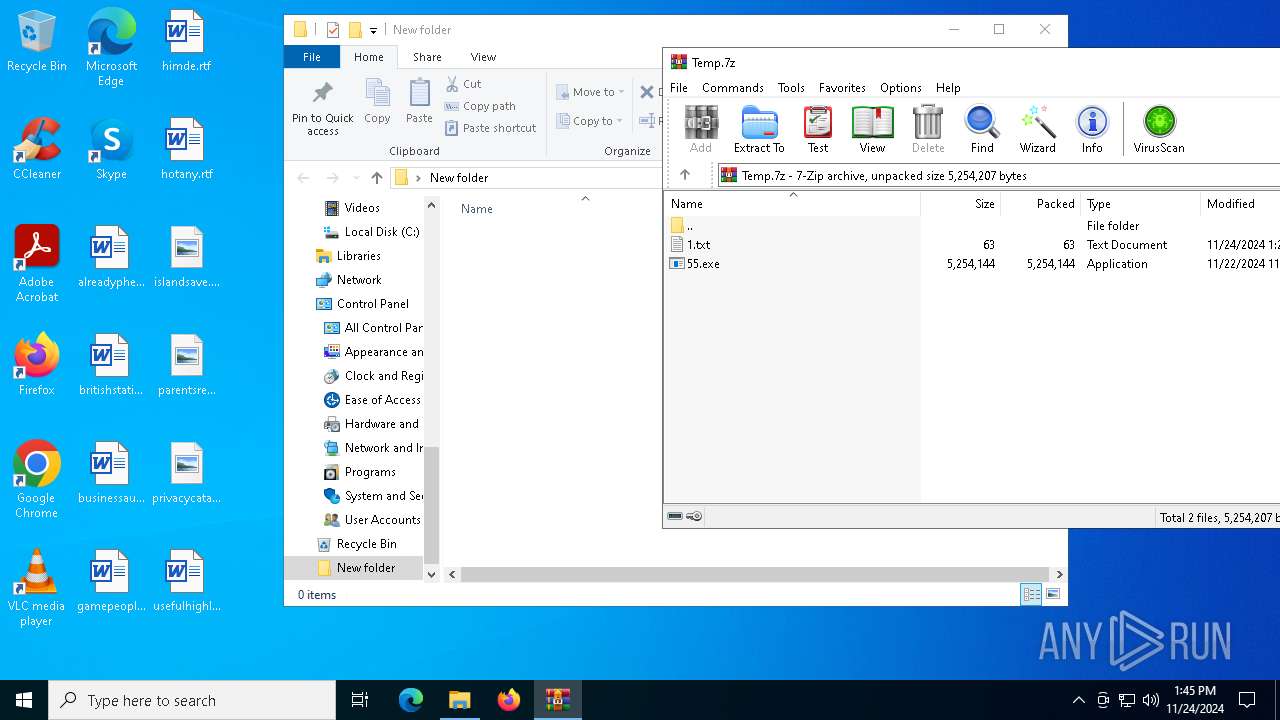
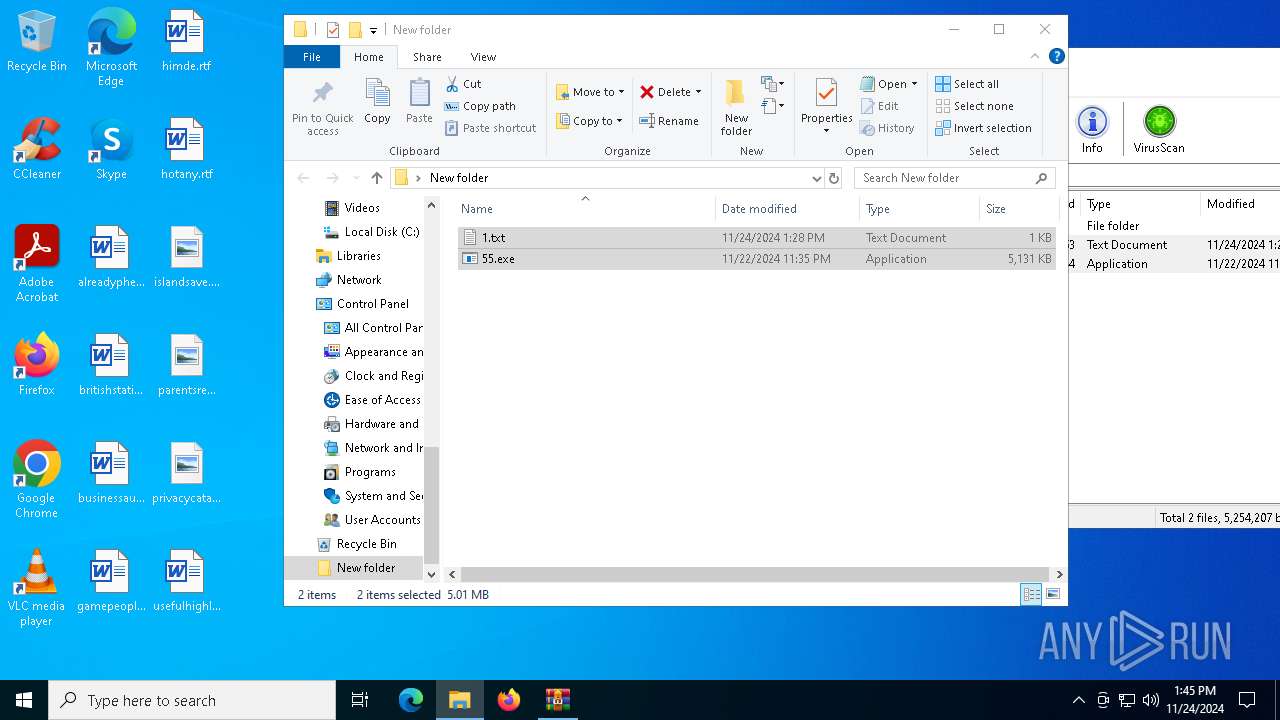
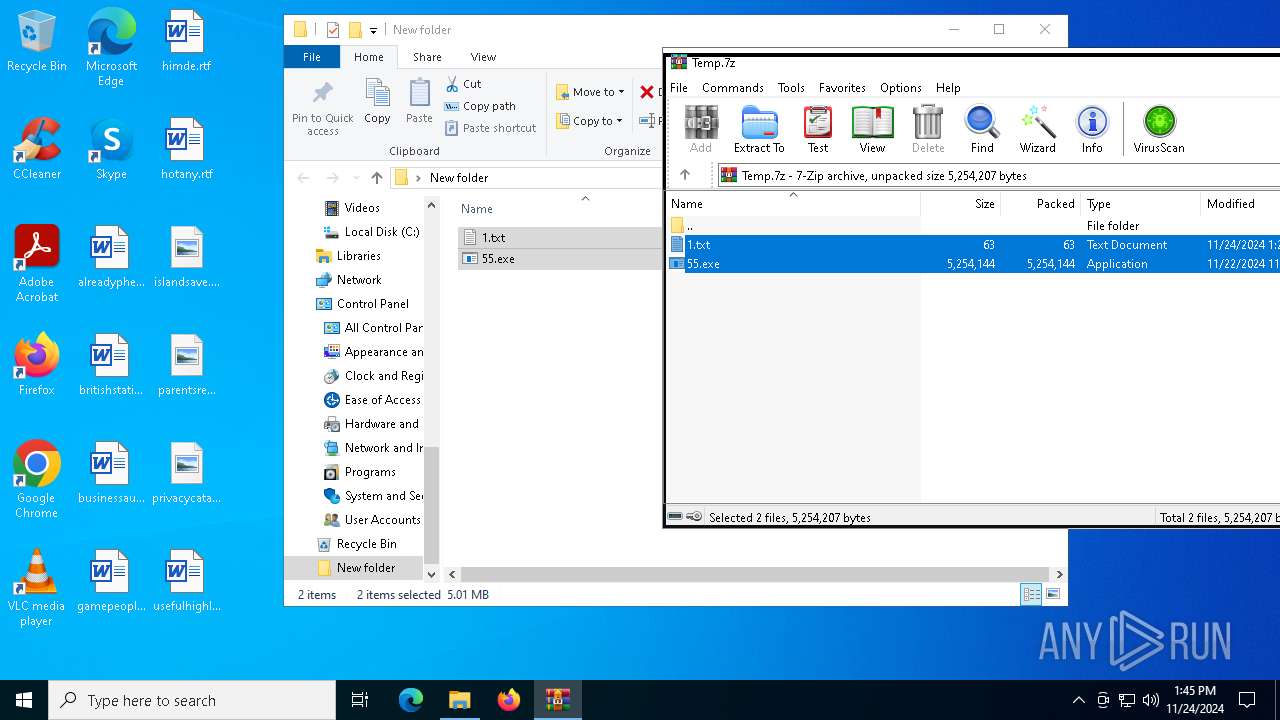
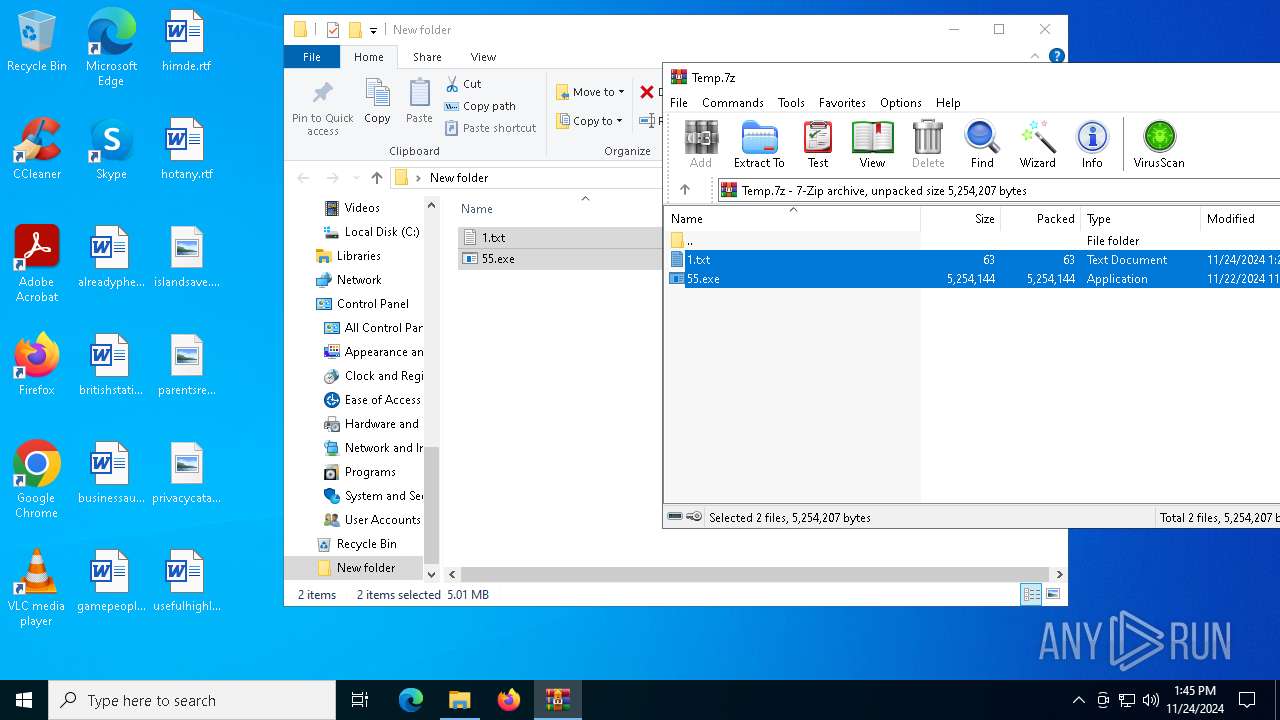
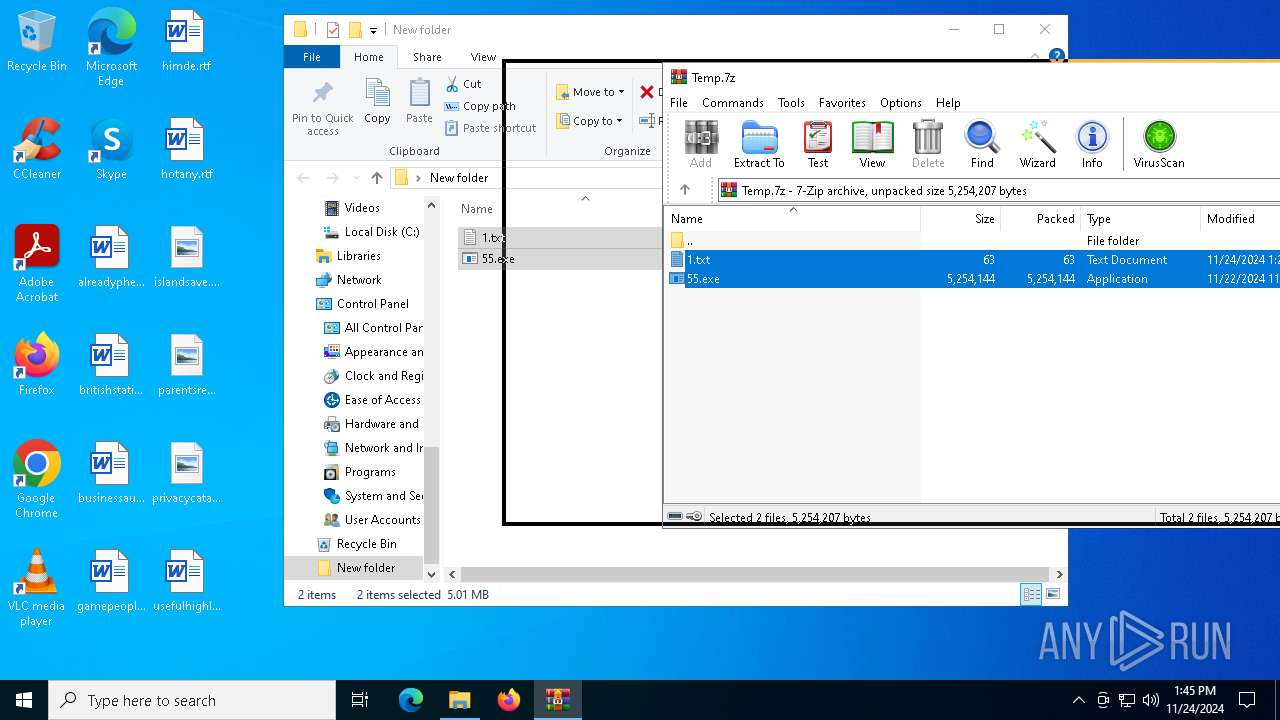
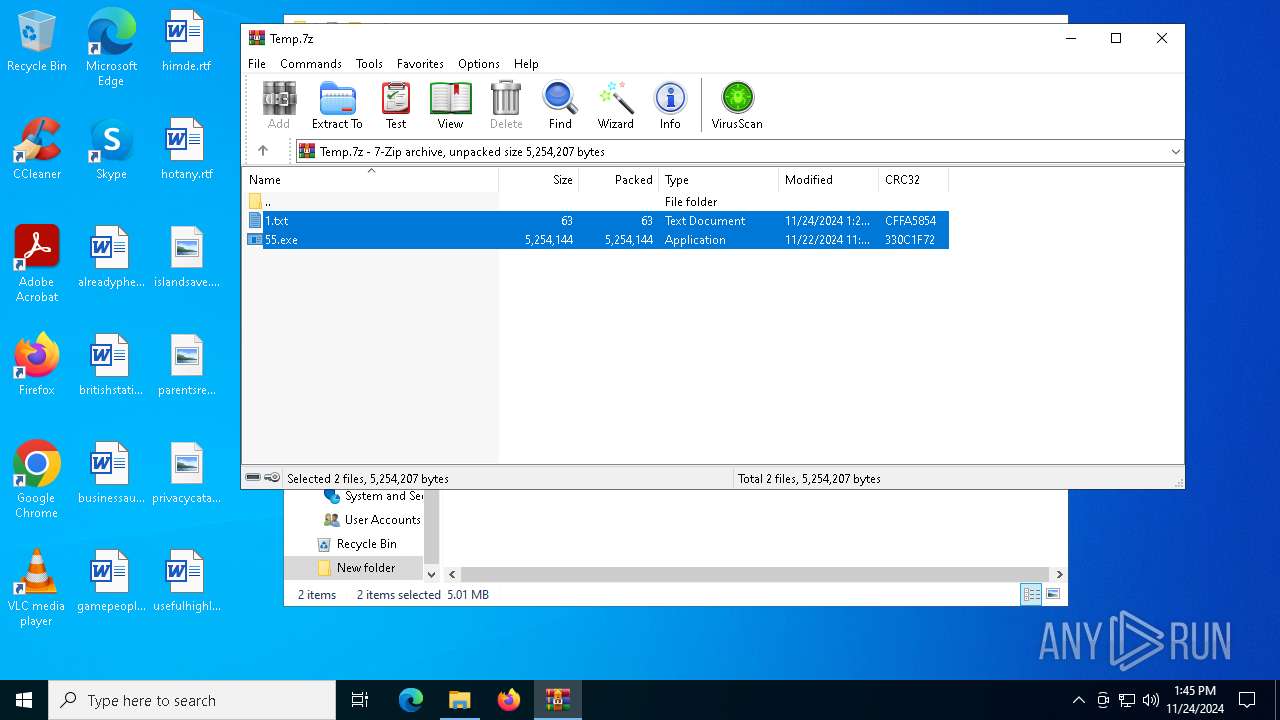
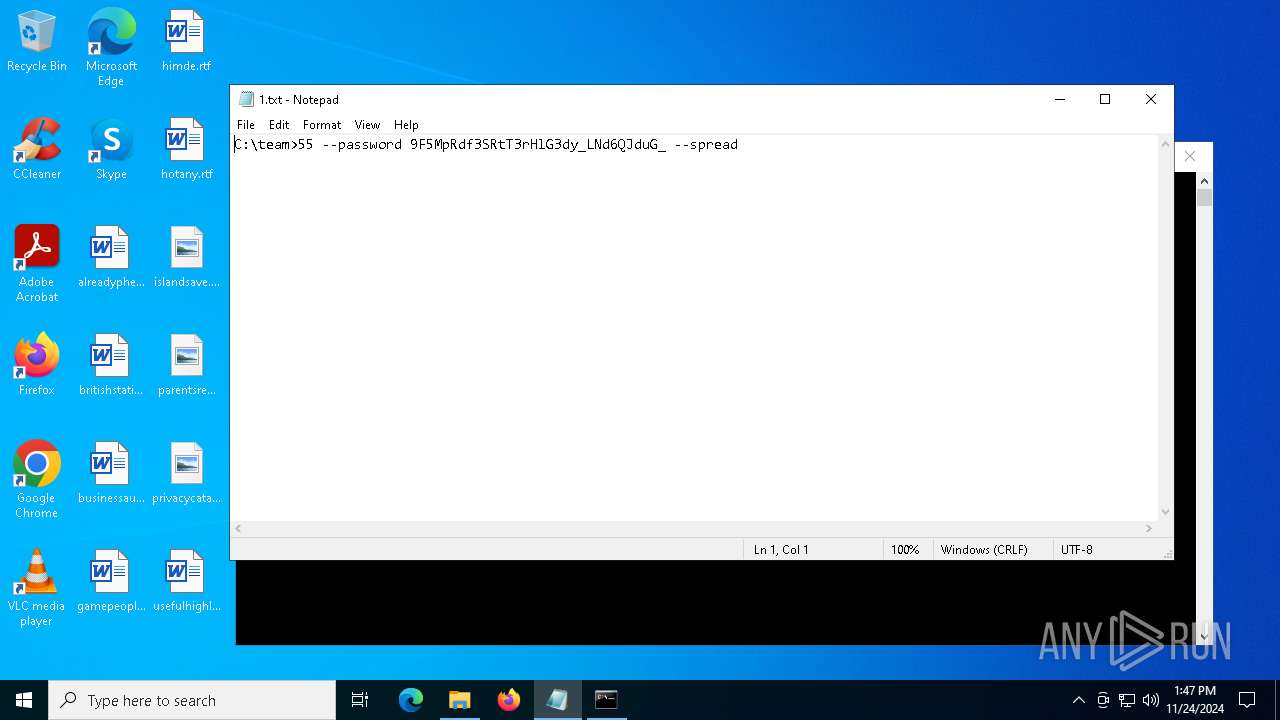
| File name: | Temp.7z |
| Full analysis: | https://app.any.run/tasks/24d0704e-2779-4759-b17d-90ec20c081ca |
| Verdict: | Malicious activity |
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
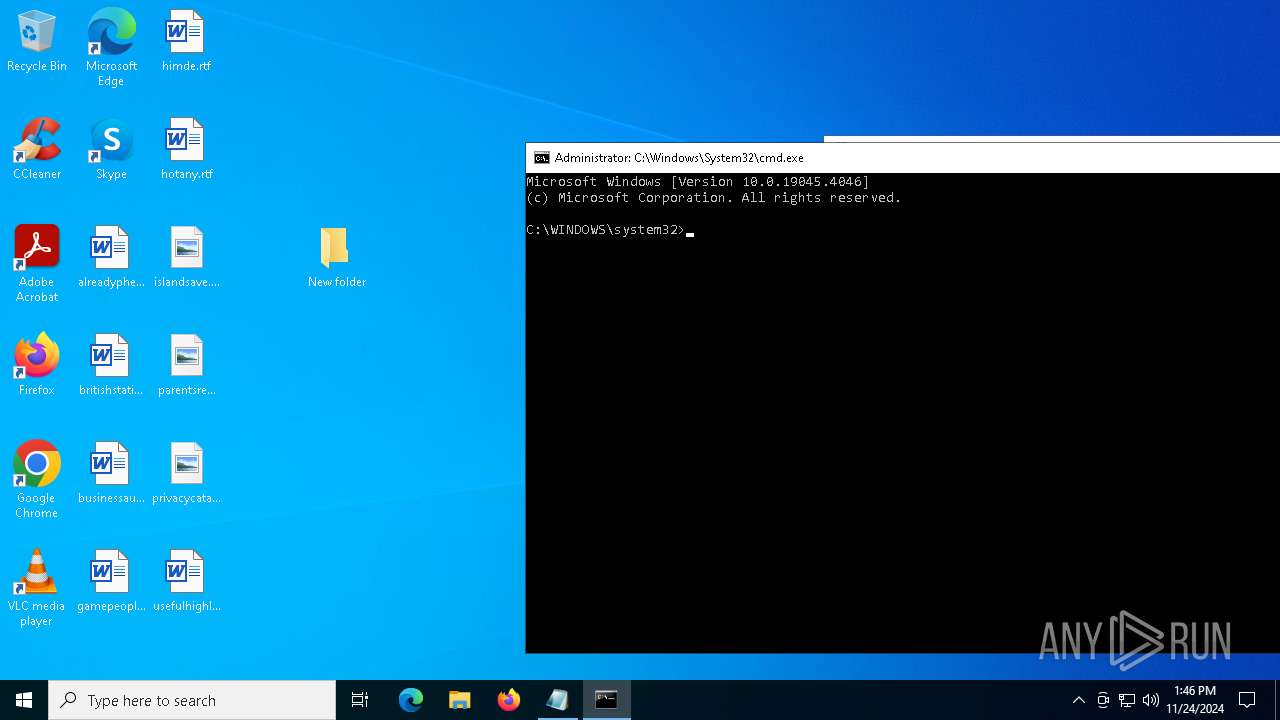
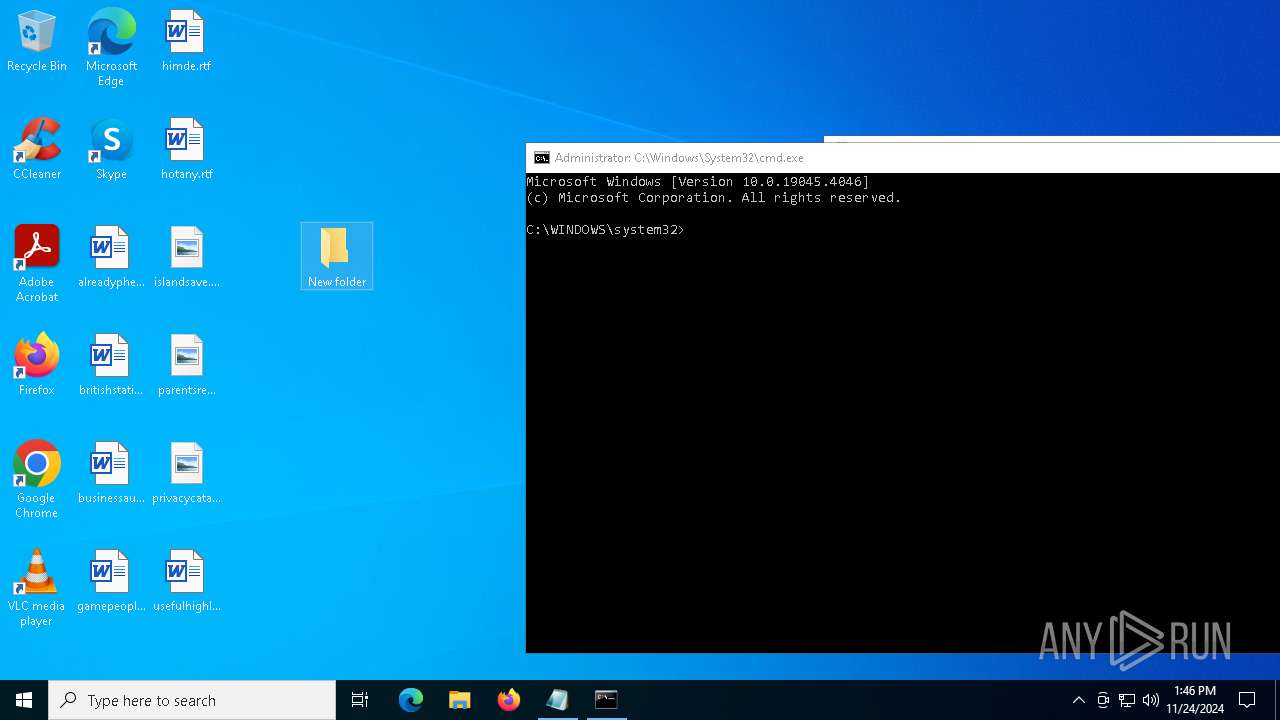
| Analysis date: | November 24, 2024, 13:44:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | ABC77B67CDF3FF892A674B946A654B53 |
| SHA1: | 658F4EDAC95636FACDEA111ACC0898EFBC1593C5 |
| SHA256: | 6FA9C96E4FA2B48C30A58EFE9A78C2862BCAFAD7798AB3D5F30AC6957529C32D |
| SSDEEP: | 98304:ahcGI9zrHMBH3eEEjq5LpQRZS1y3Xgsmau6lPQNC0C92np74o103vP5NVnhEAB7B:CmdAA |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 4556)
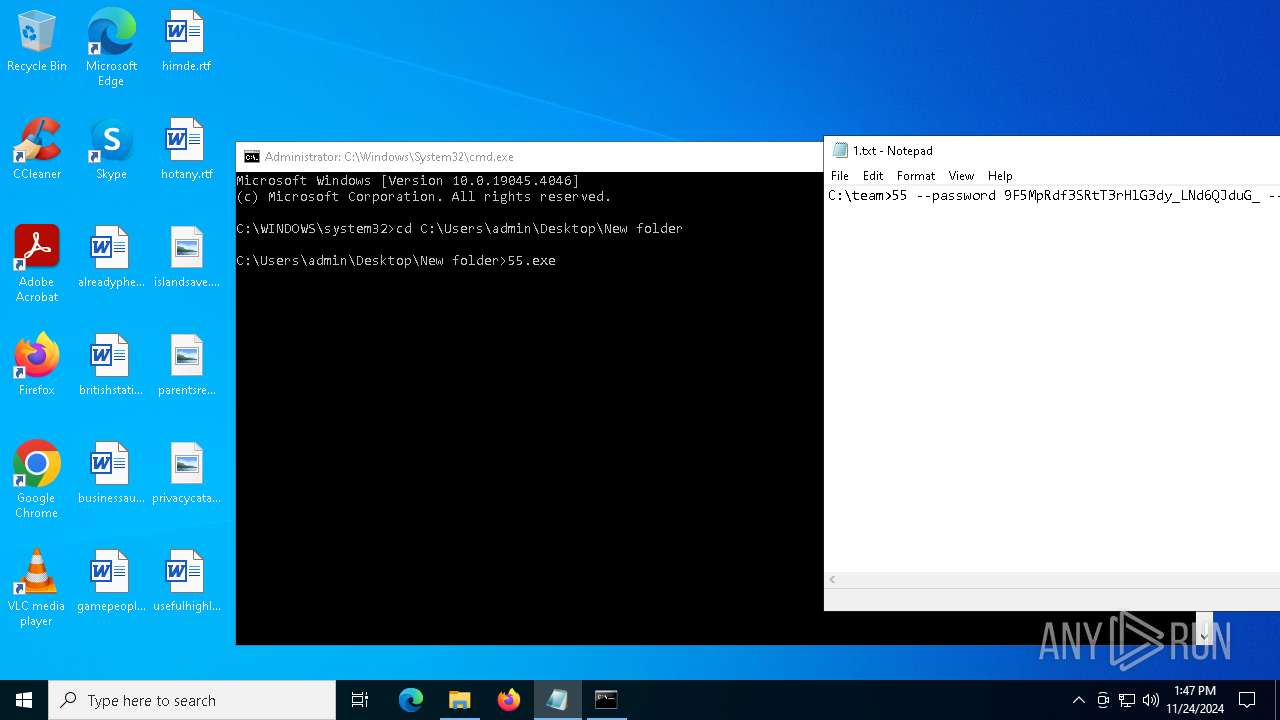
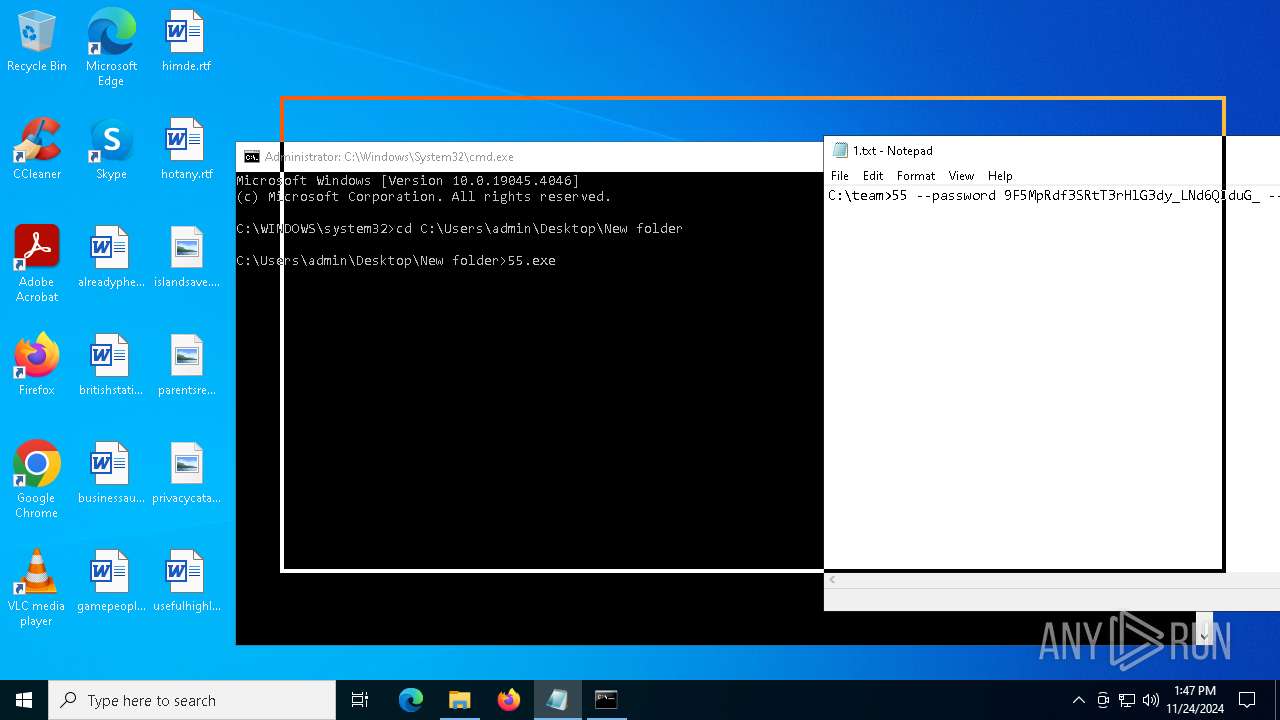
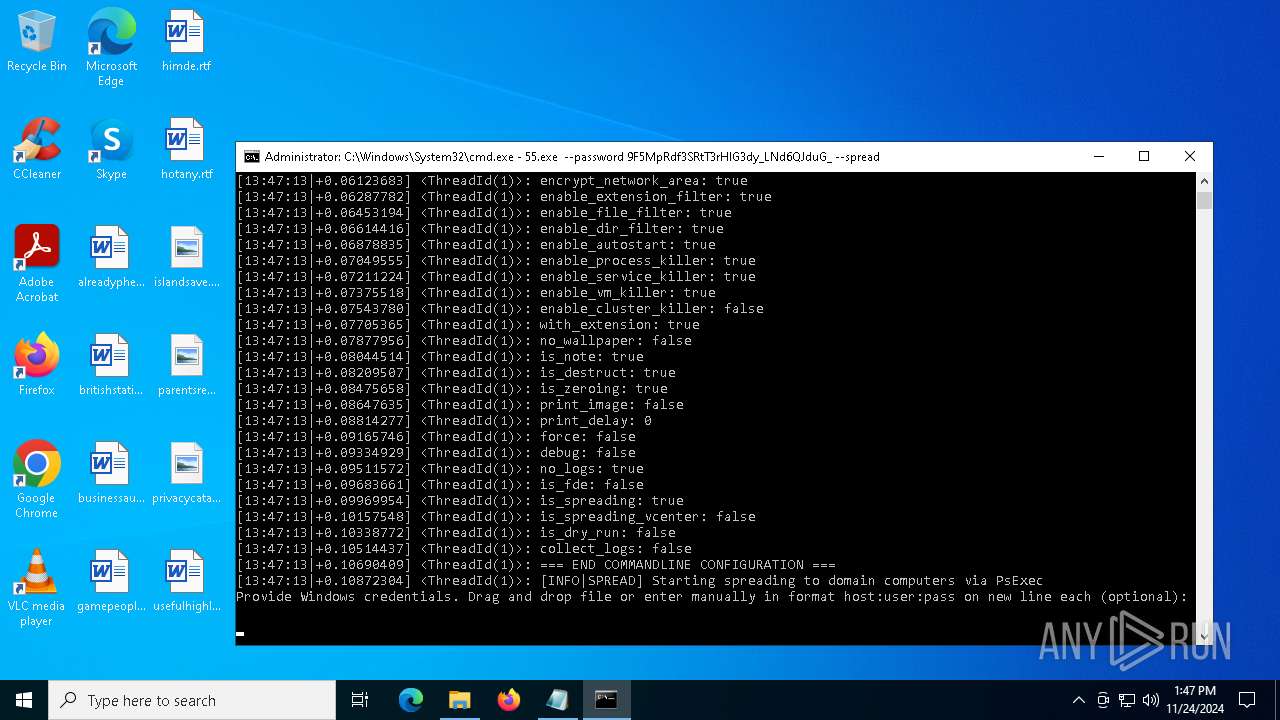
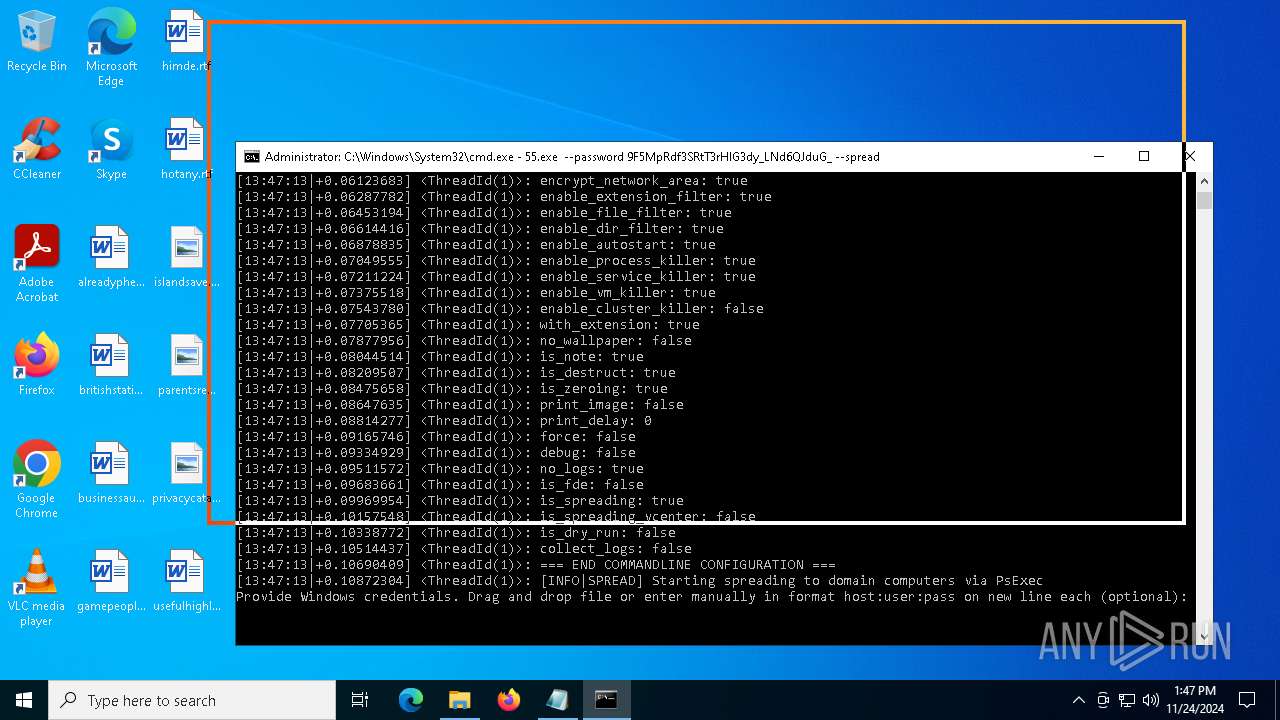
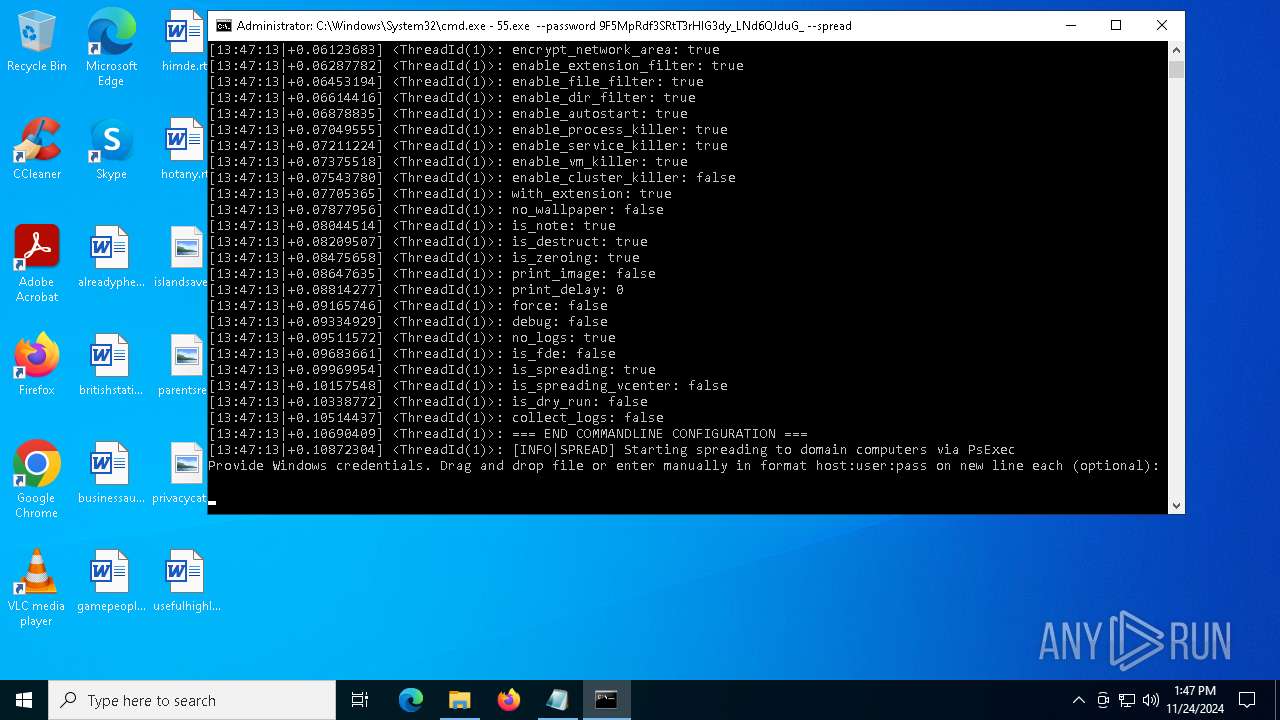
MORTISLOCKER has been detected (YARA)
- 55.exe (PID: 7148)
- 55.exe (PID: 4824)
Changes the autorun value in the registry
- 55.exe (PID: 4824)
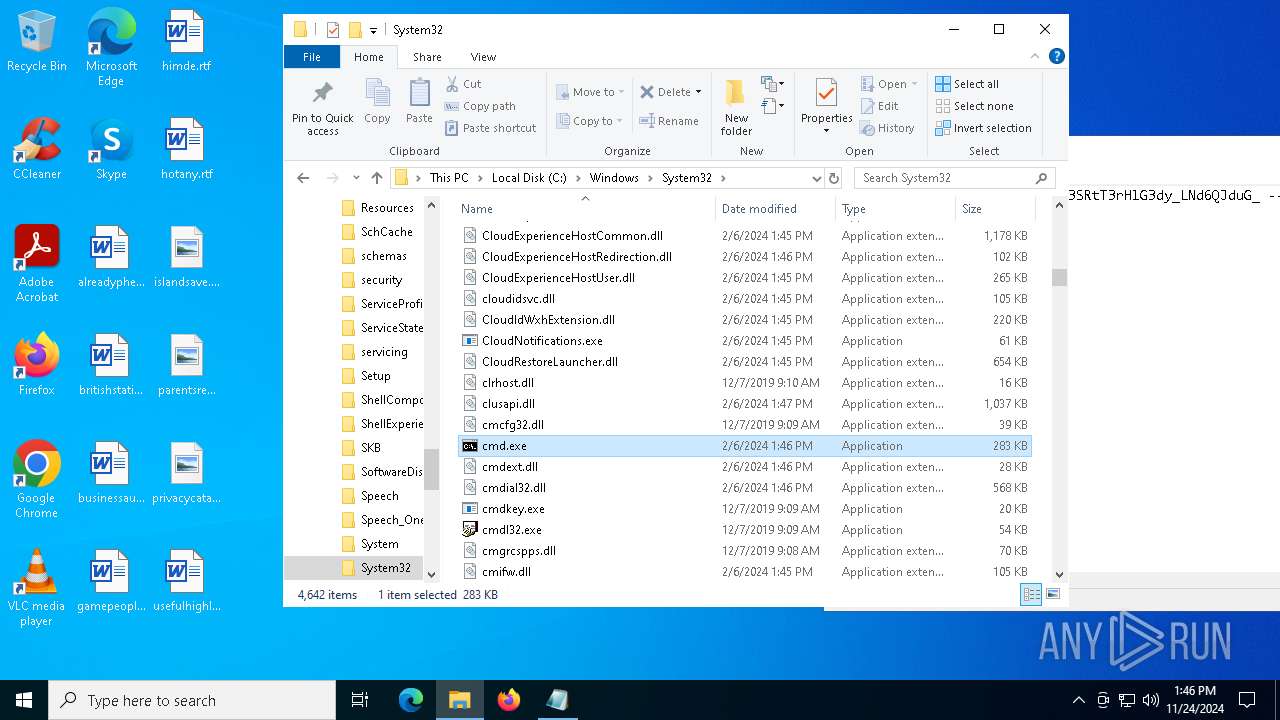
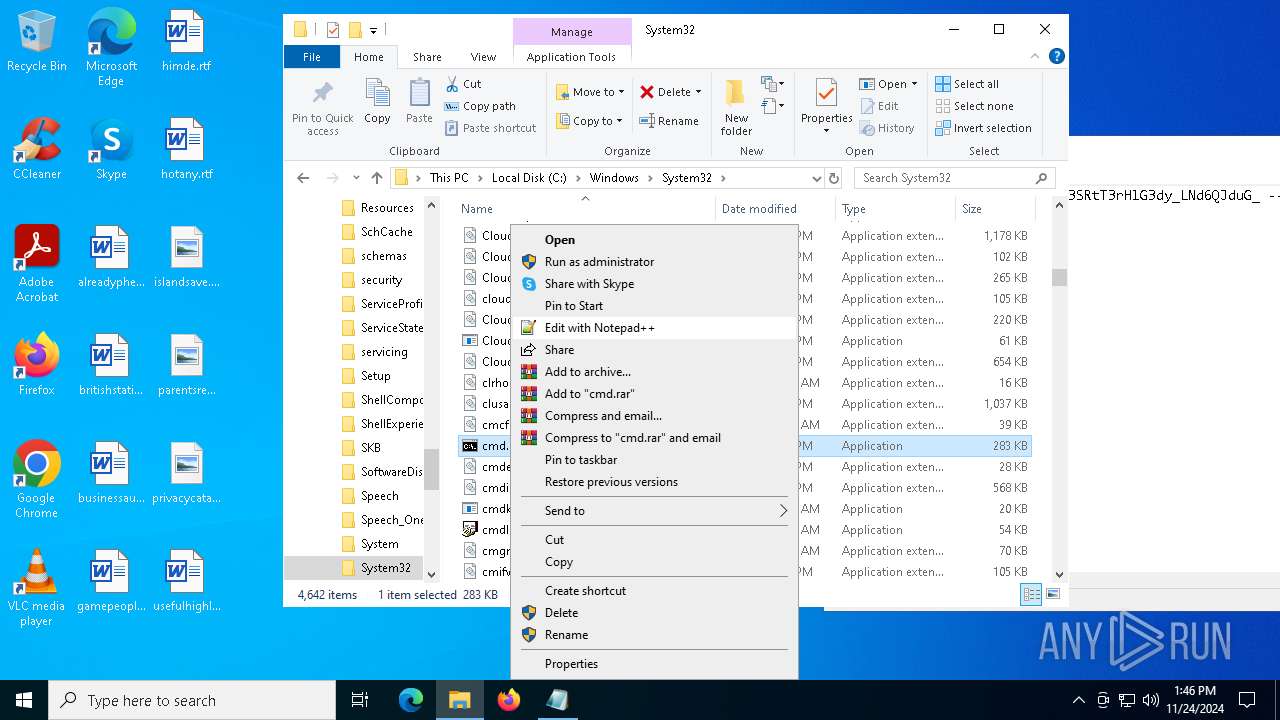
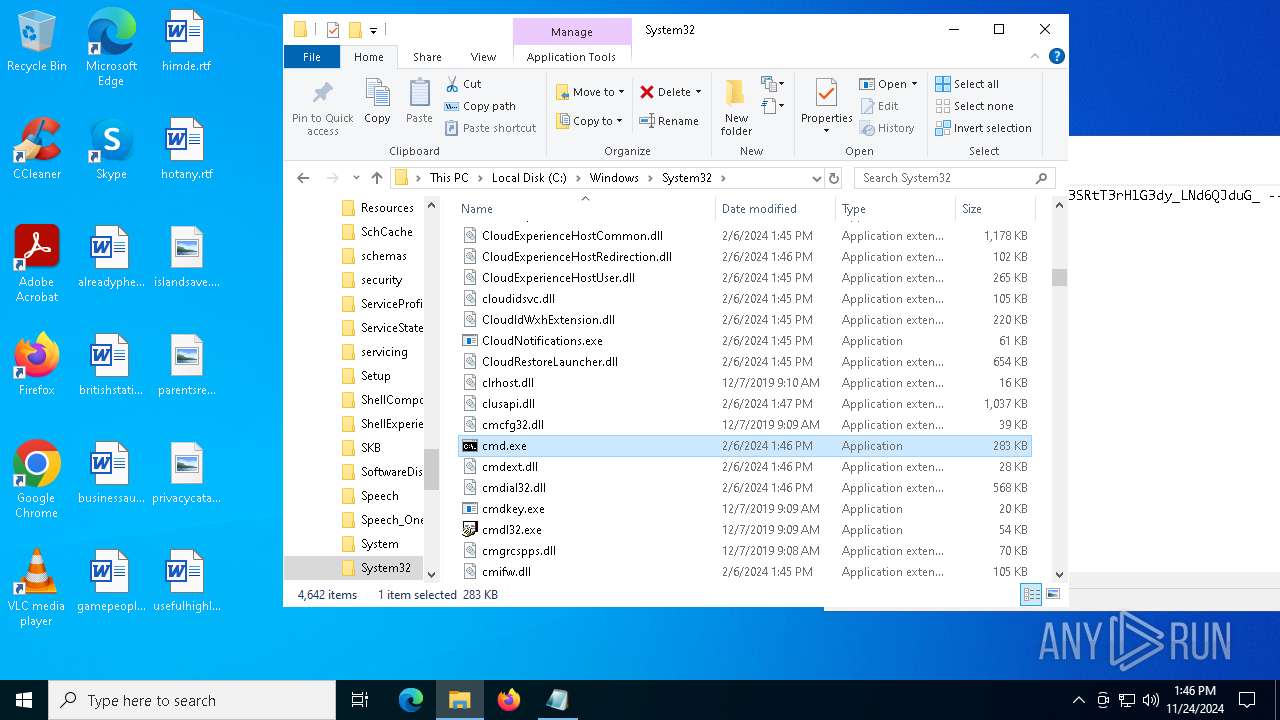
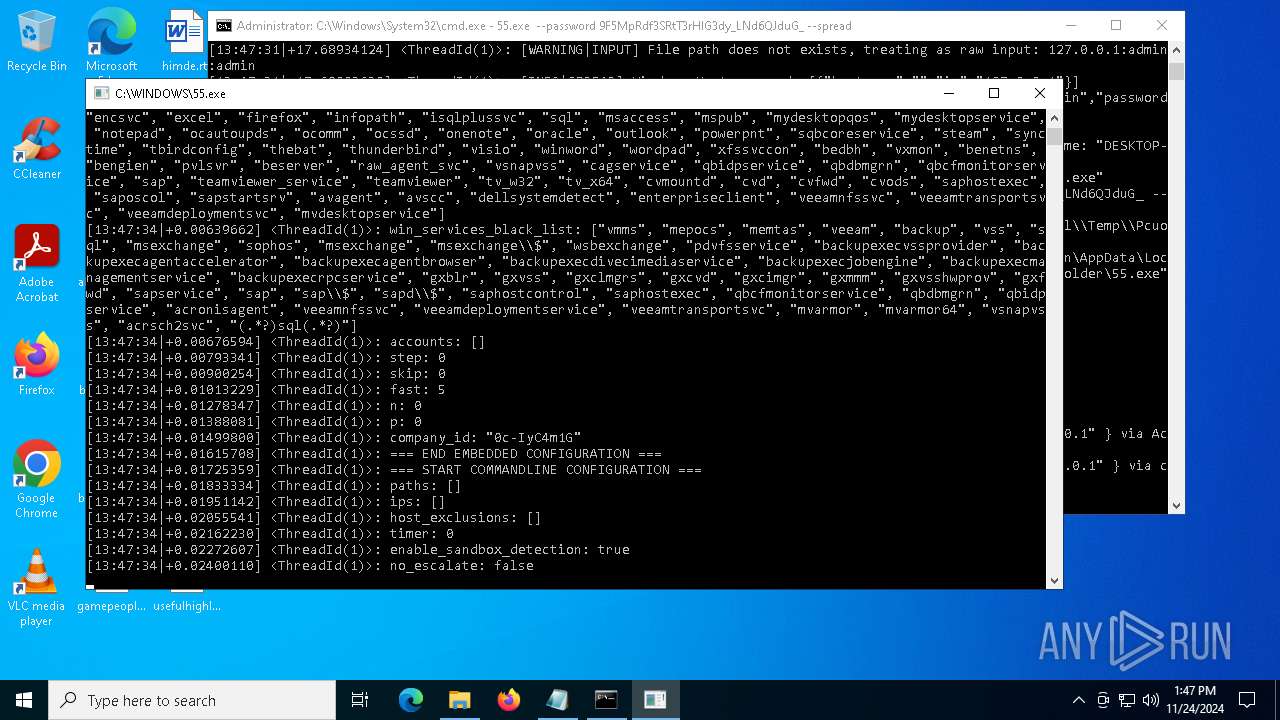
Starts NET.EXE for service management
- cmd.exe (PID: 3920)
- net.exe (PID: 5592)
- cmd.exe (PID: 4392)
- net.exe (PID: 3172)
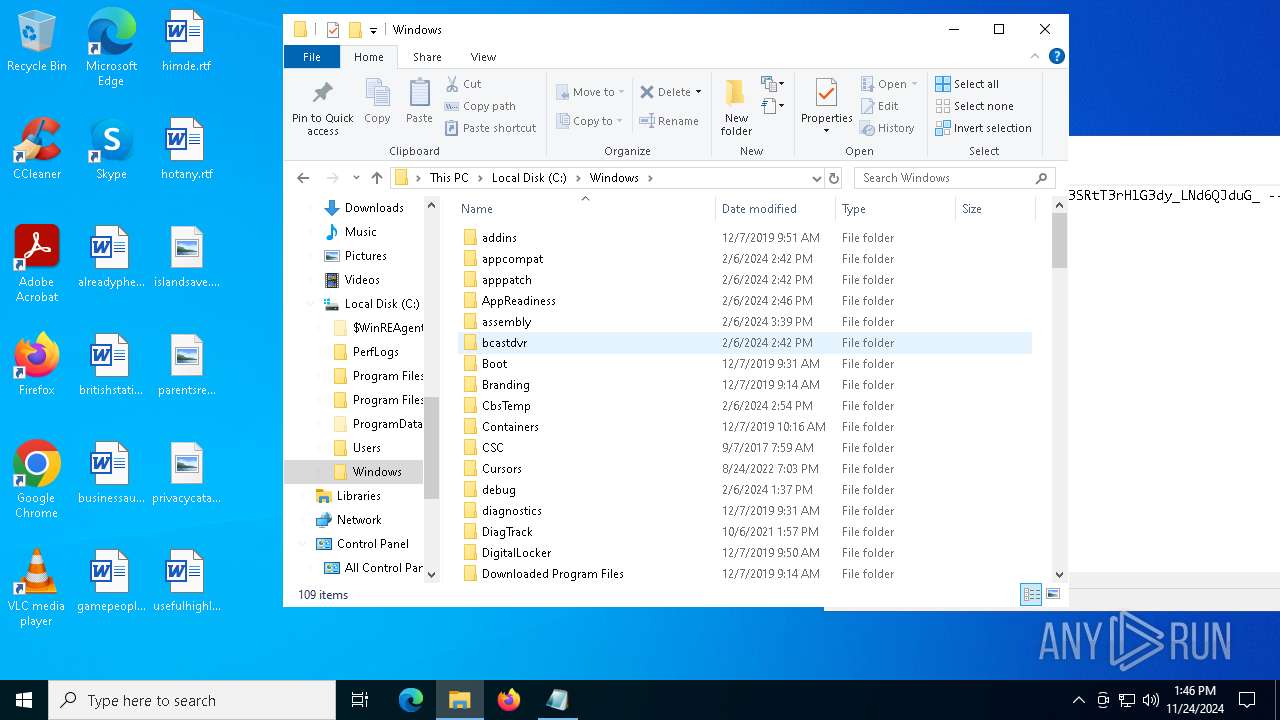
Deletes shadow copies
- cmd.exe (PID: 4204)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- 55.exe (PID: 7148)
- 55.exe (PID: 4824)
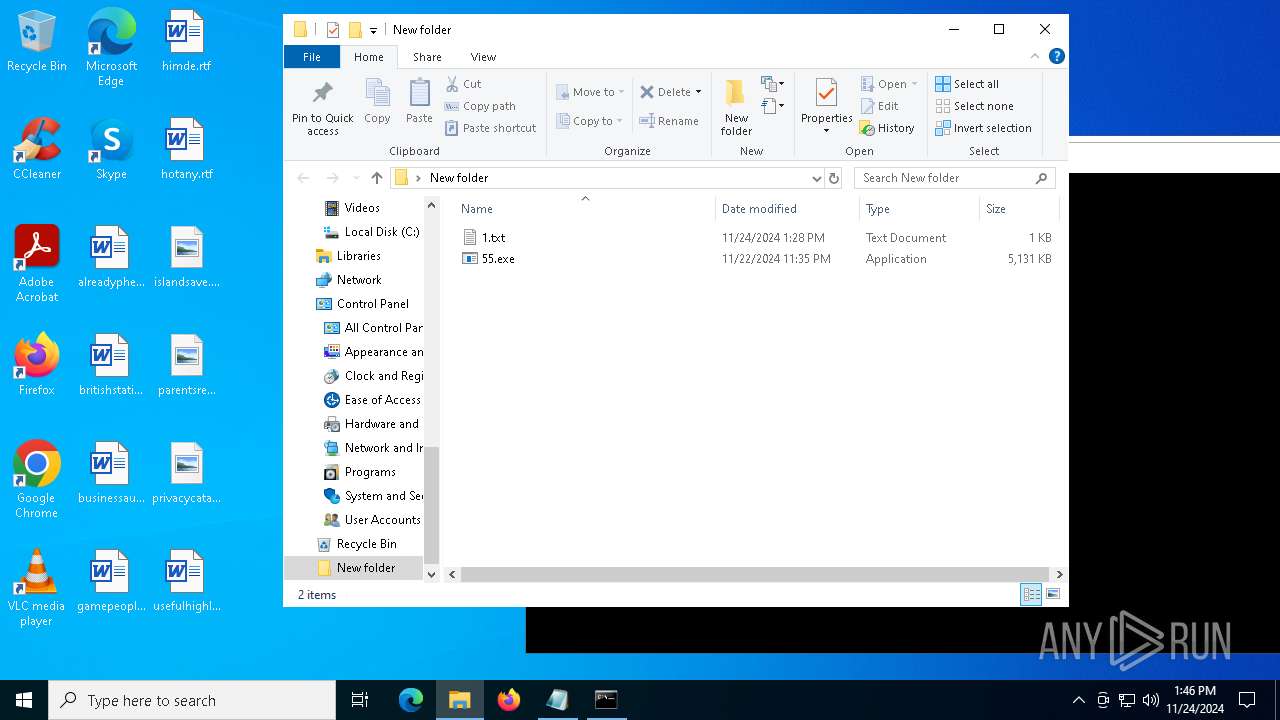
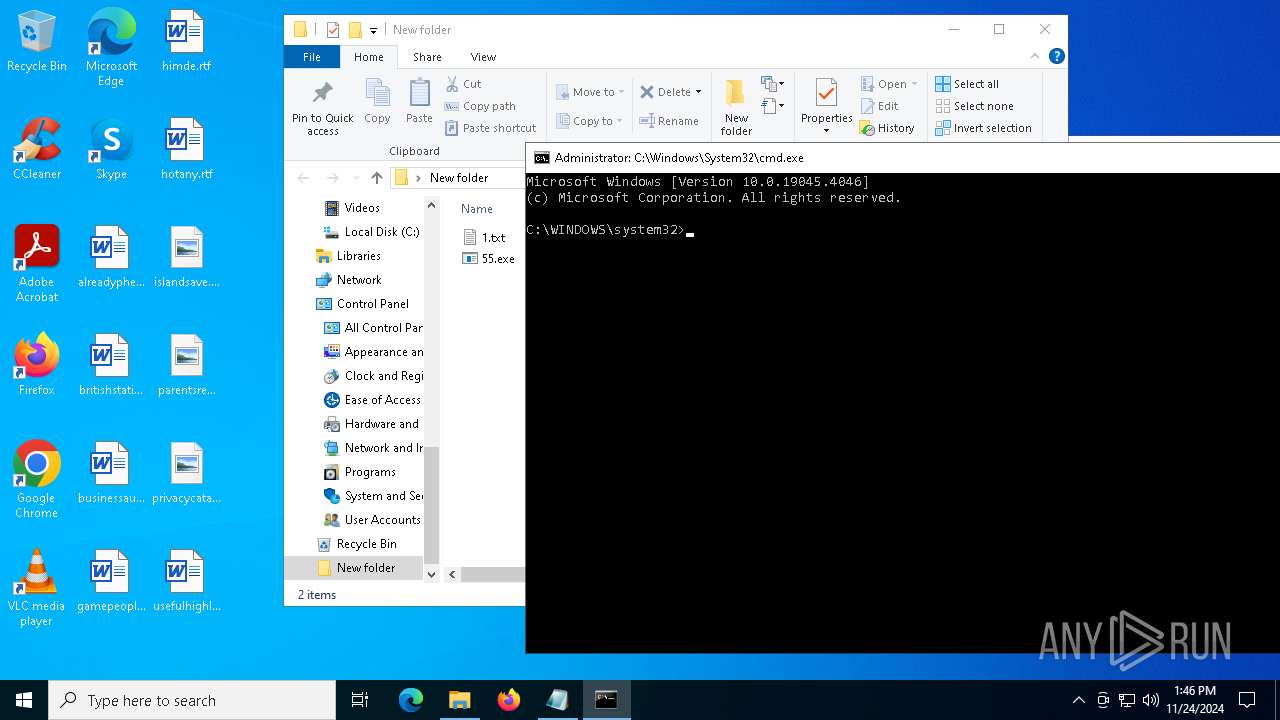
Executable content was dropped or overwritten
- 55.exe (PID: 7148)
- Pcuolnqz.exe (PID: 1520)
- Pcuolnqz.exe (PID: 5892)
- powershell.exe (PID: 6544)
- powershell.exe (PID: 3416)
There is functionality for VM detection antiVM strings (YARA)
- 55.exe (PID: 7148)
- 55.exe (PID: 4824)
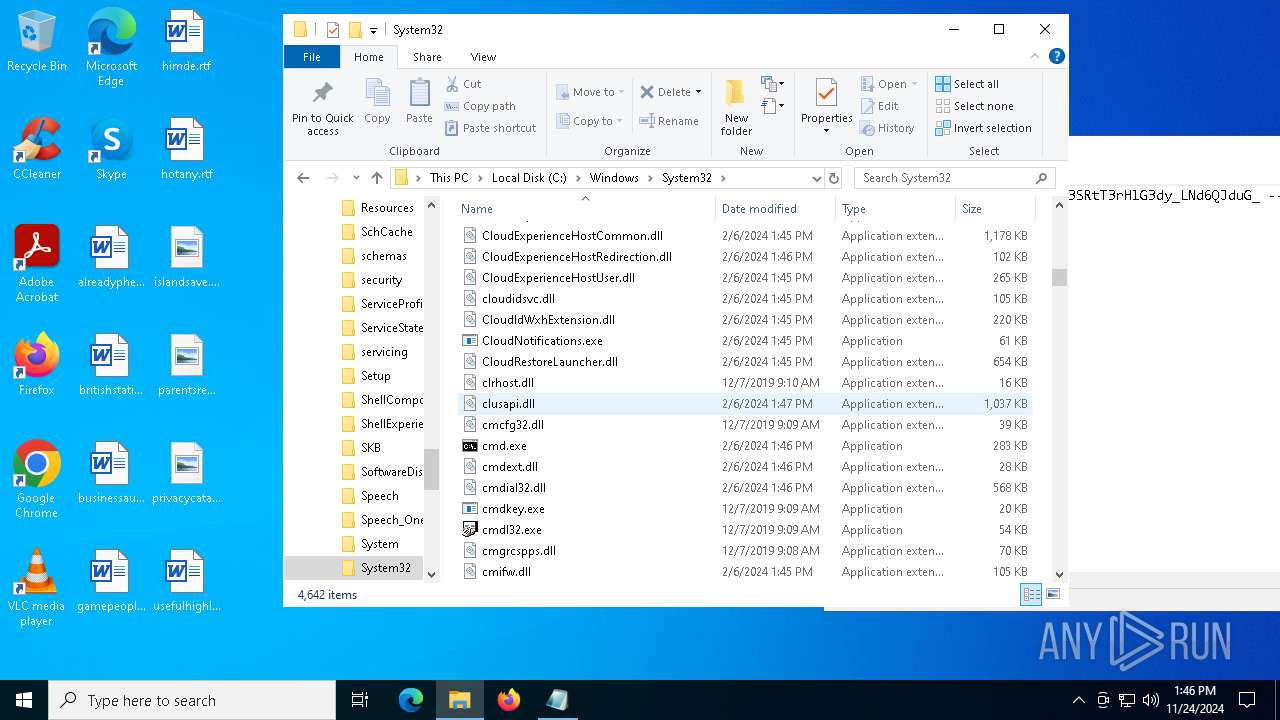
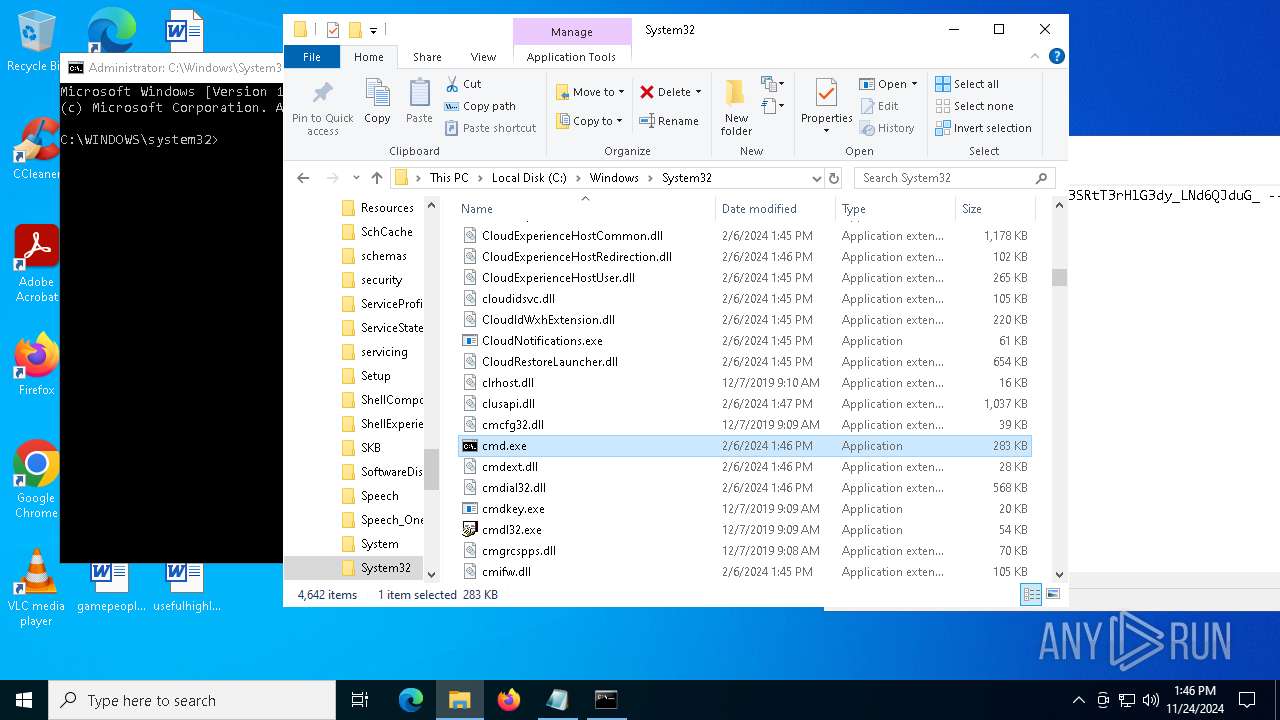
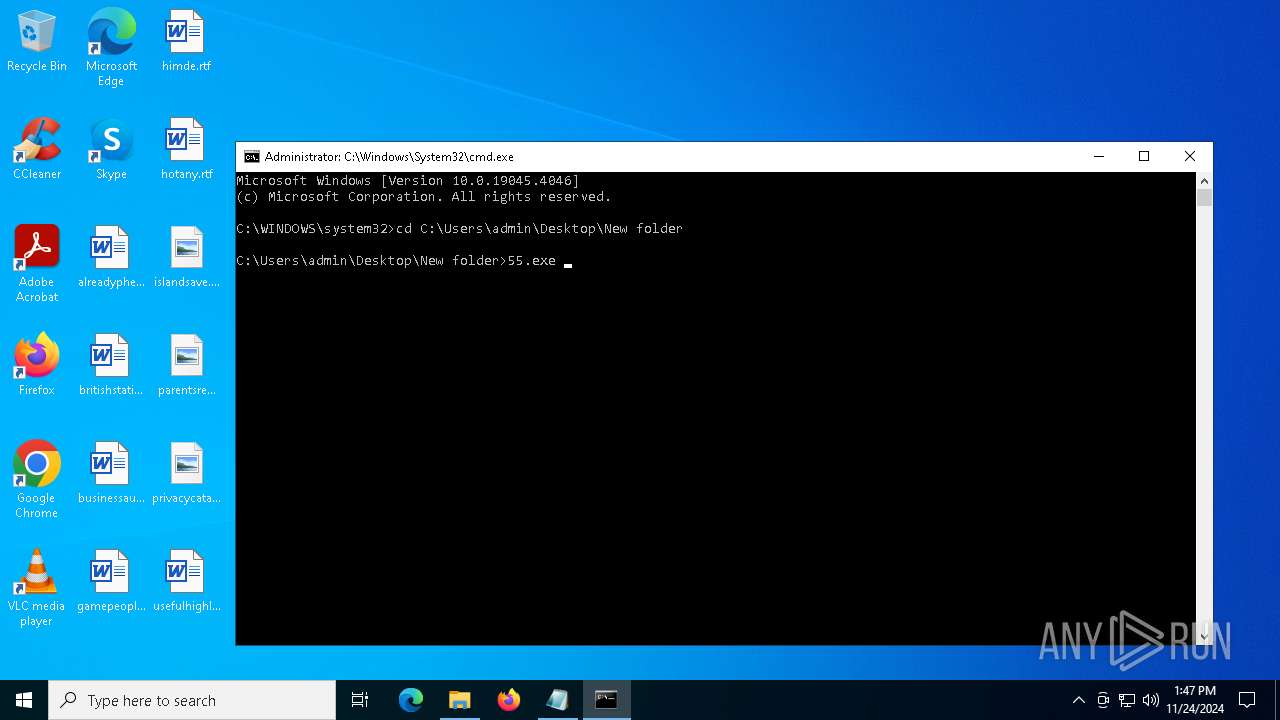
The executable file from the user directory is run by the CMD process
- Pcuolnqz.exe (PID: 5892)
- Pcuolnqz.exe (PID: 1520)
Starts CMD.EXE for commands execution
- 55.exe (PID: 7148)
- 55.exe (PID: 4824)
There is functionality for VM detection Parallels (YARA)
- 55.exe (PID: 7148)
- 55.exe (PID: 4824)
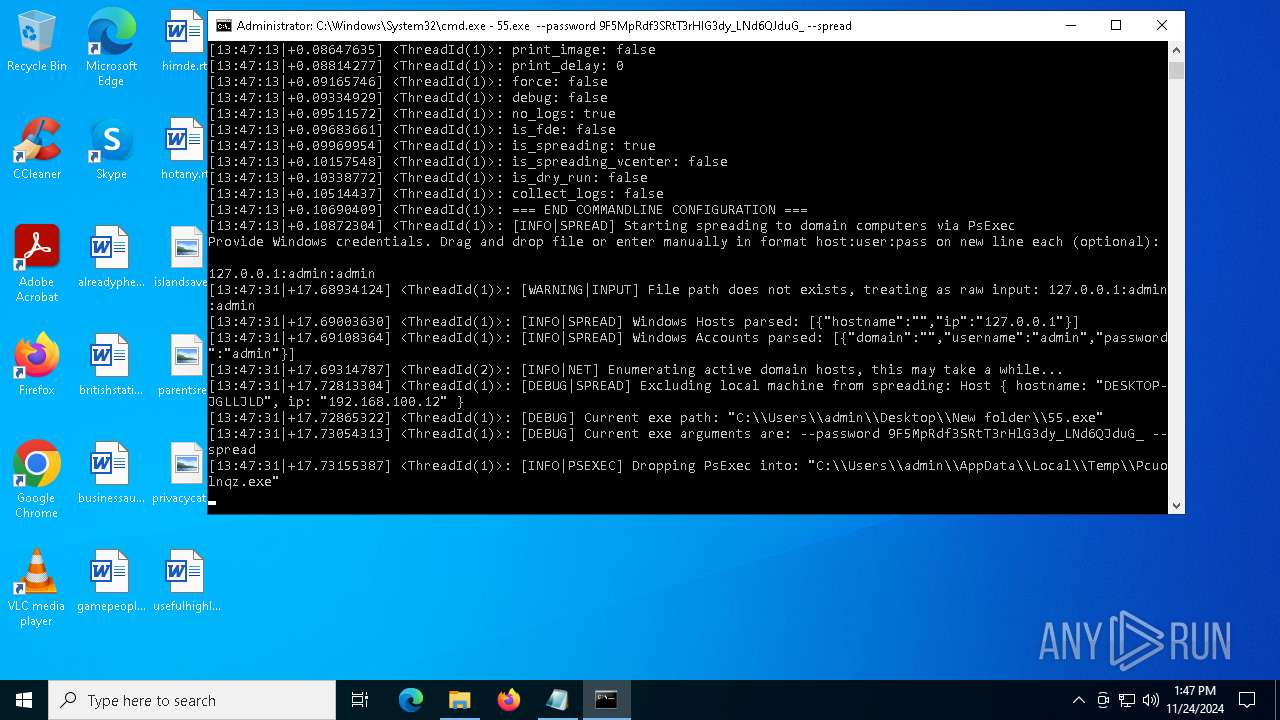
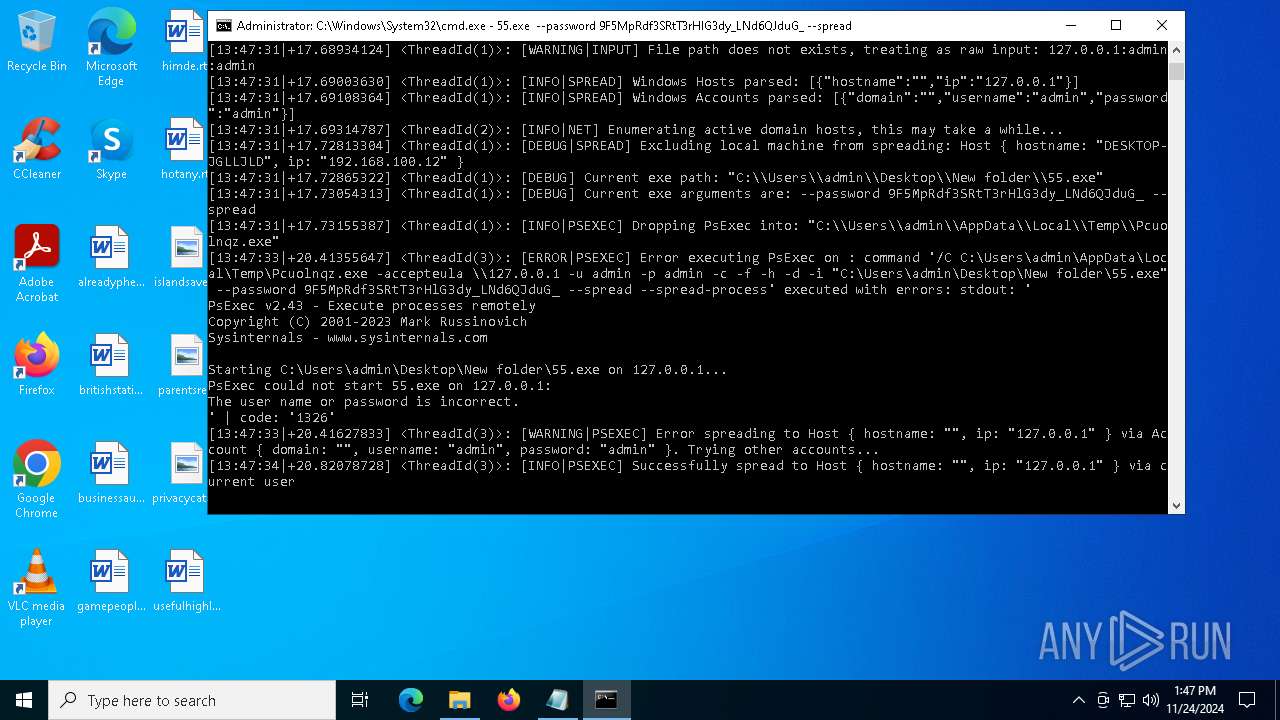
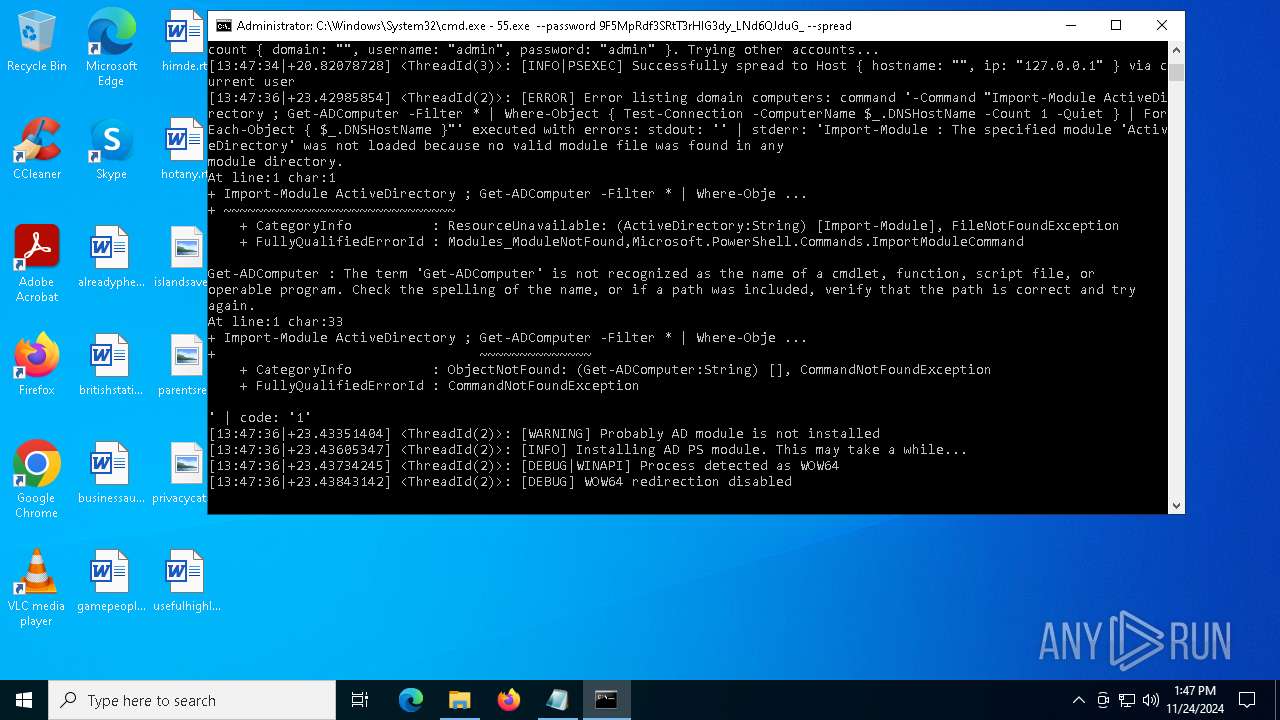
PSEXEC has been detected
- Pcuolnqz.exe (PID: 5892)
- Pcuolnqz.exe (PID: 1520)
Executes as Windows Service
- PSEXESVC.exe (PID: 1536)
- PSEXESVC.exe (PID: 1140)
- VSSVC.exe (PID: 4012)
Process drops legitimate windows executable
- powershell.exe (PID: 3416)
- powershell.exe (PID: 6544)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 2120)
- cmd.exe (PID: 6492)
Starts NET.EXE to map network drives
- cmd.exe (PID: 1732)
Found IP address in command line
- powershell.exe (PID: 3416)
- powershell.exe (PID: 6544)
Suspicious use of asymmetric encryption in PowerShell
- 55.exe (PID: 7148)
- 55.exe (PID: 4824)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 2804)
- DismHost.exe (PID: 6944)
INFO
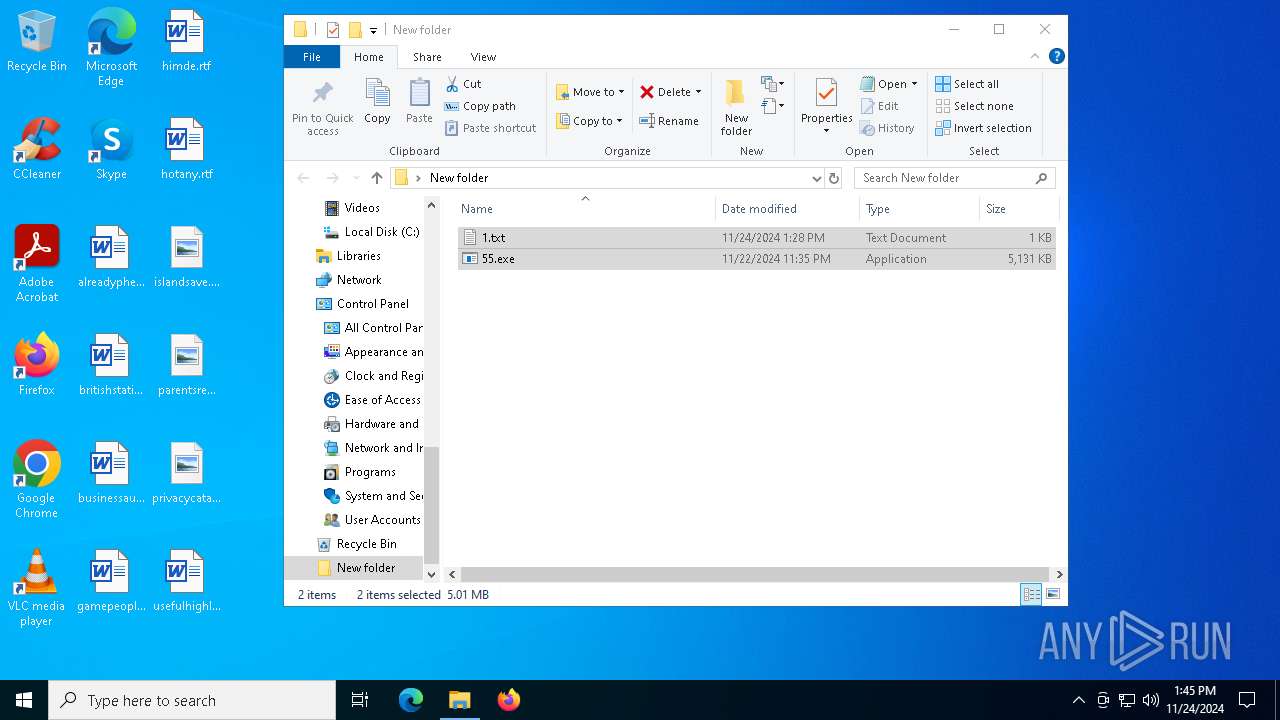
The process uses the downloaded file
- WinRAR.exe (PID: 4556)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4556)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6776)
- WMIC.exe (PID: 1544)
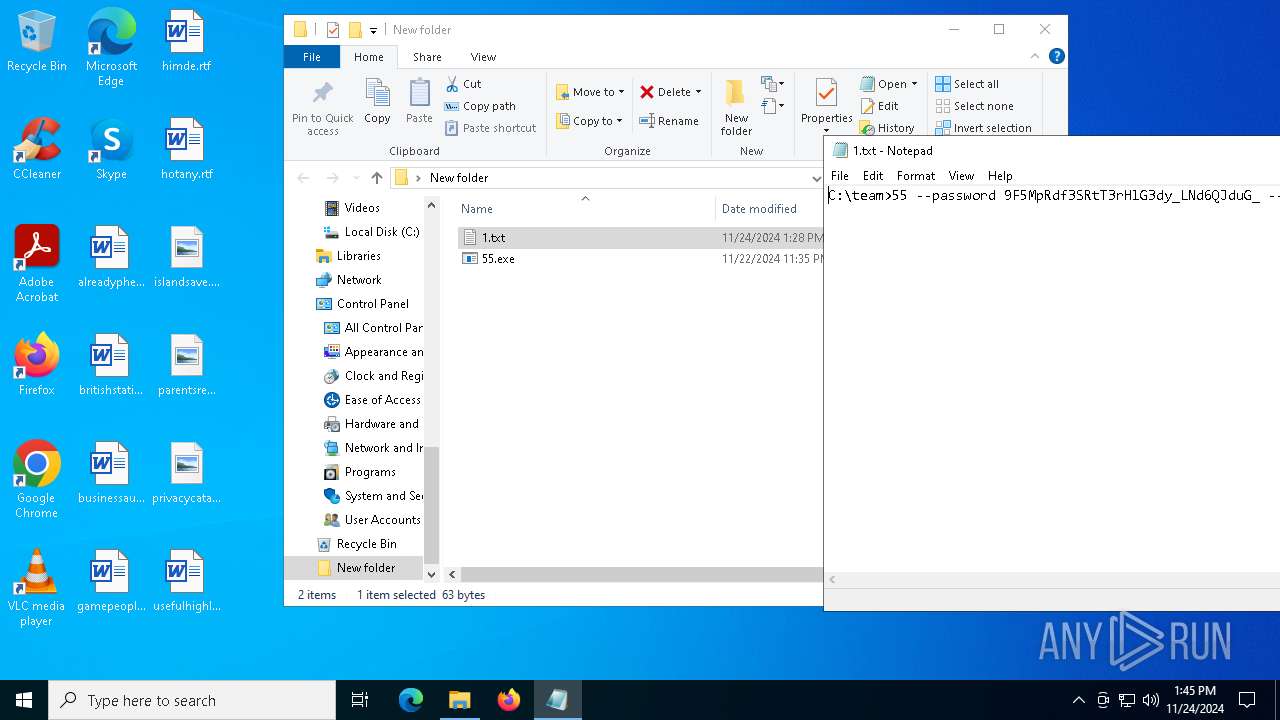
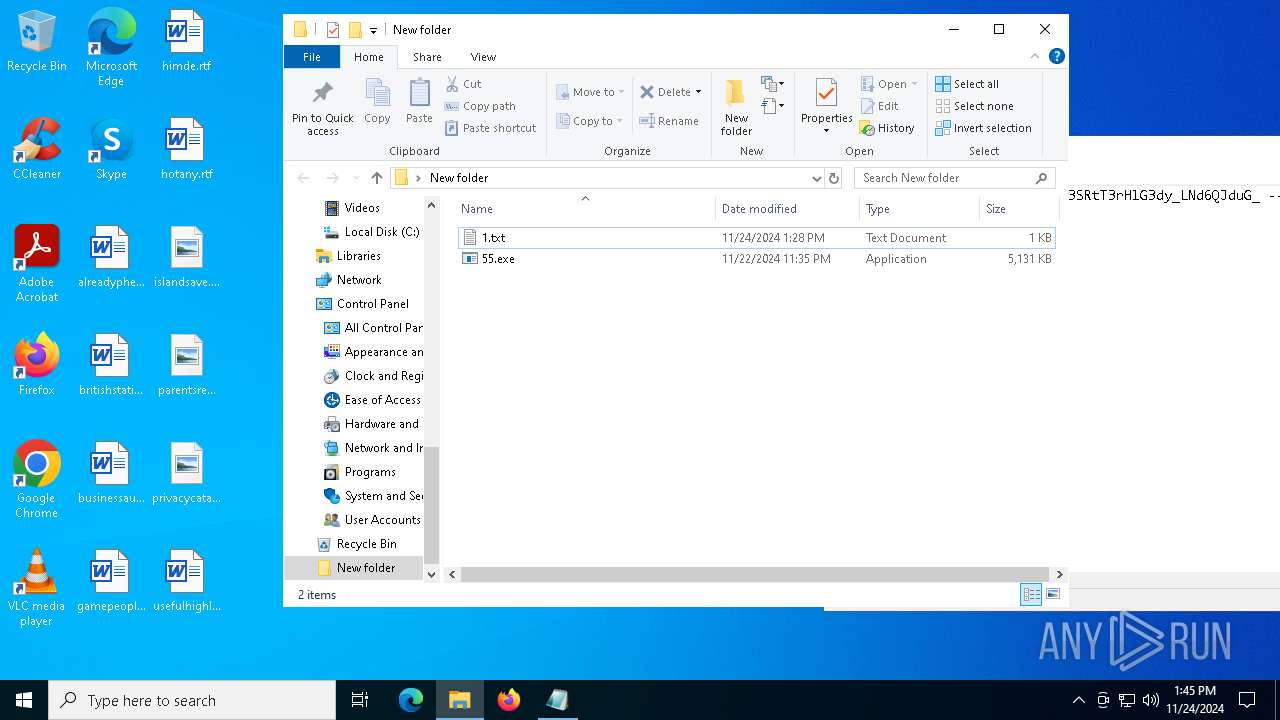
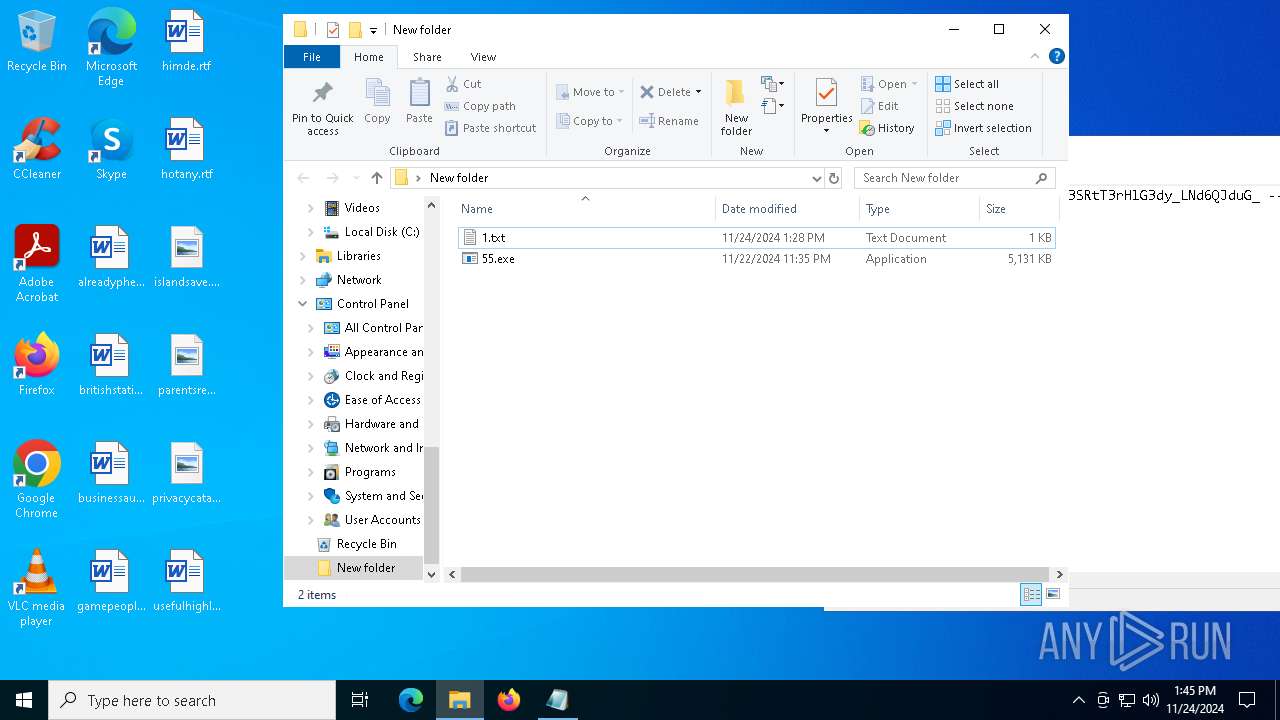
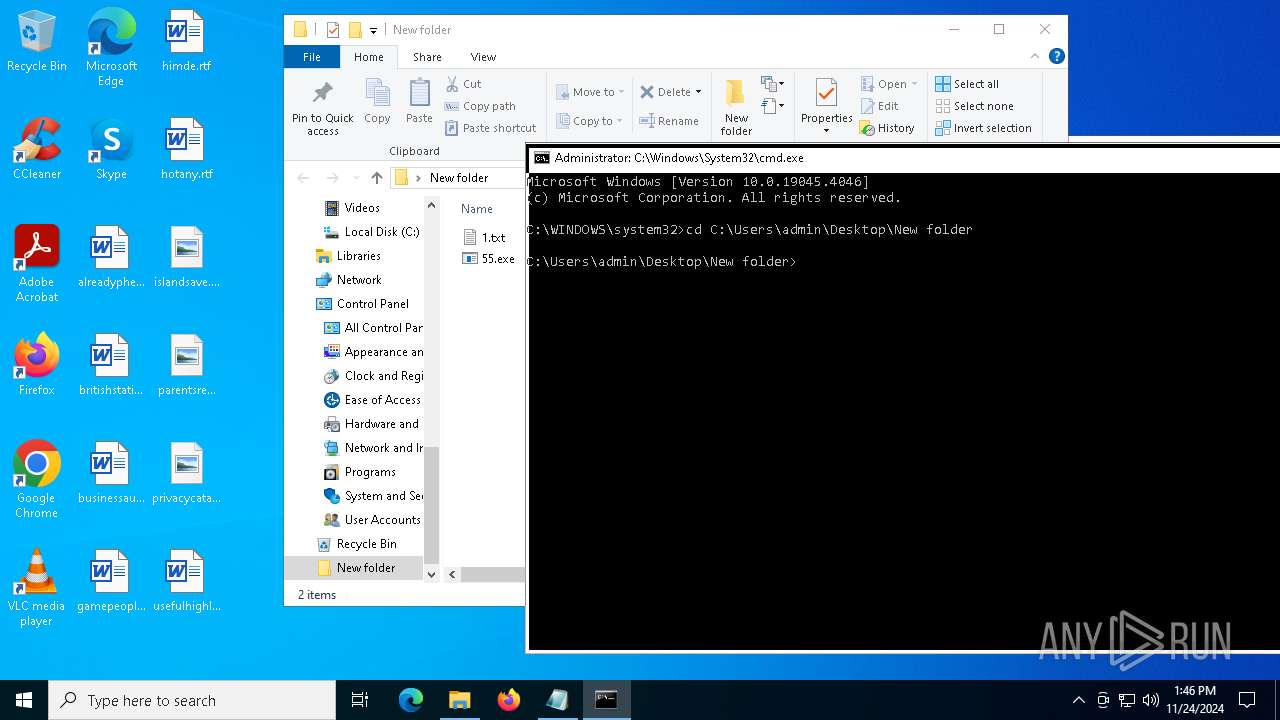
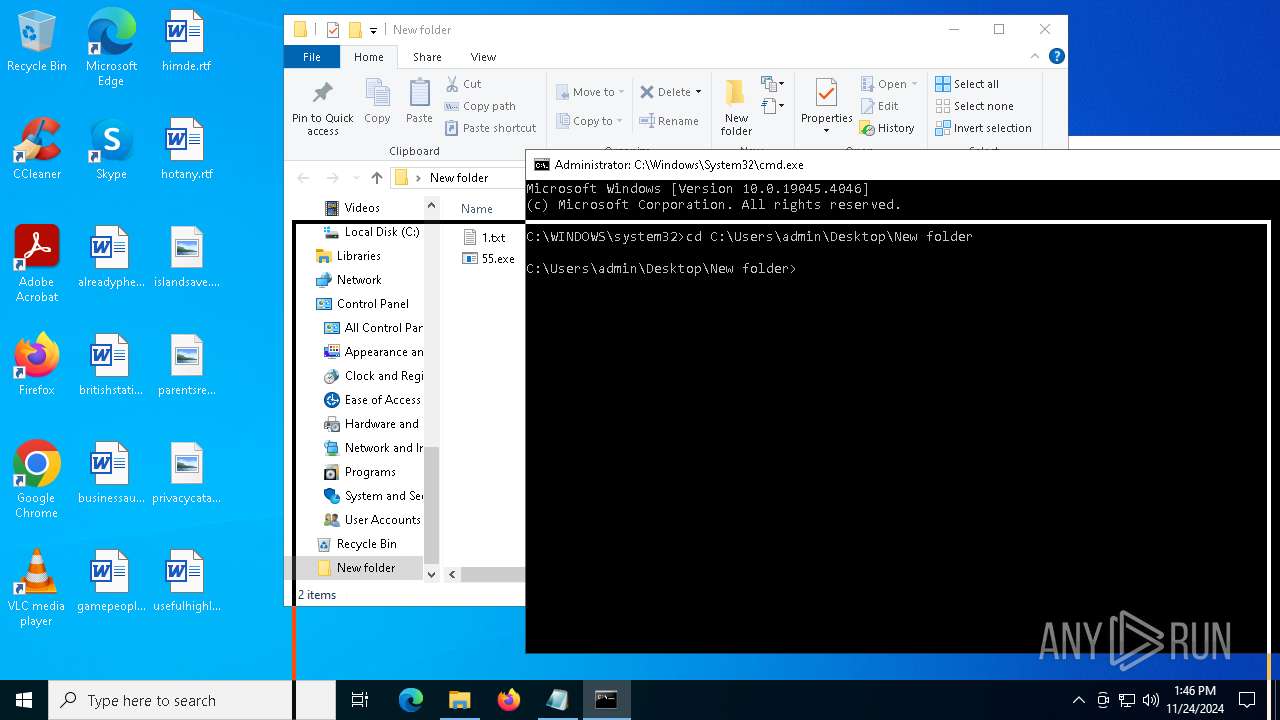
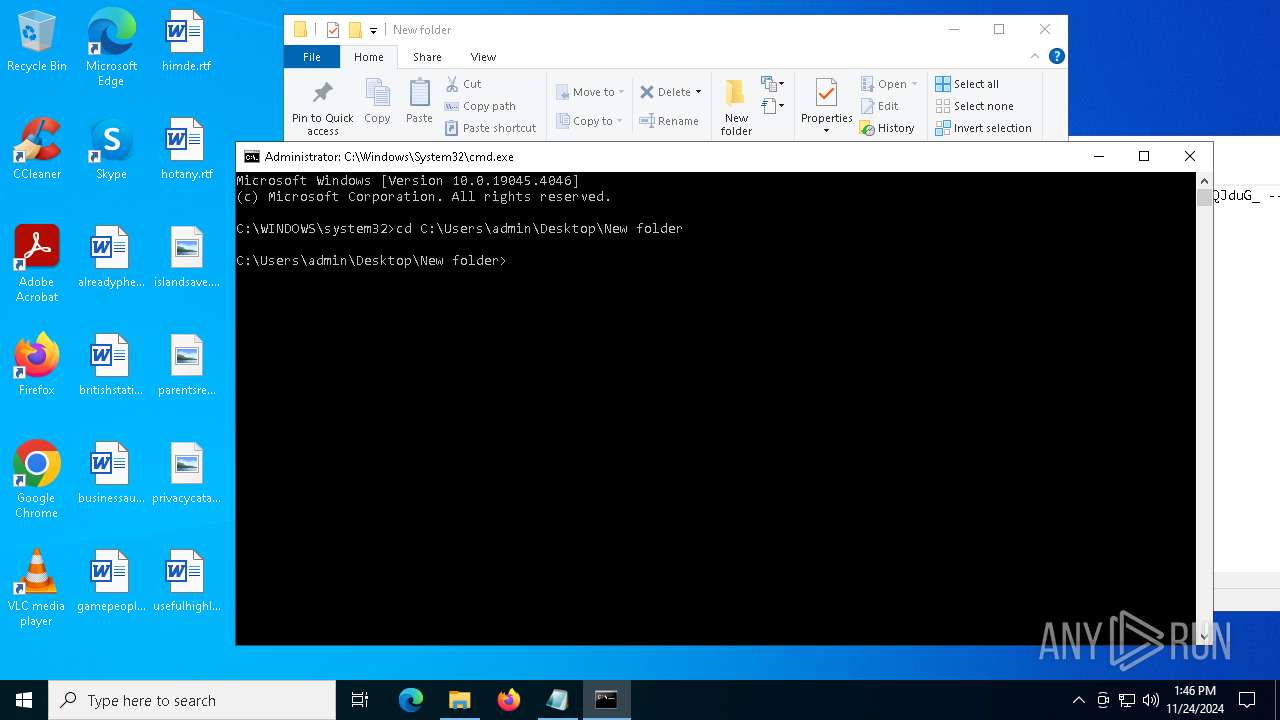
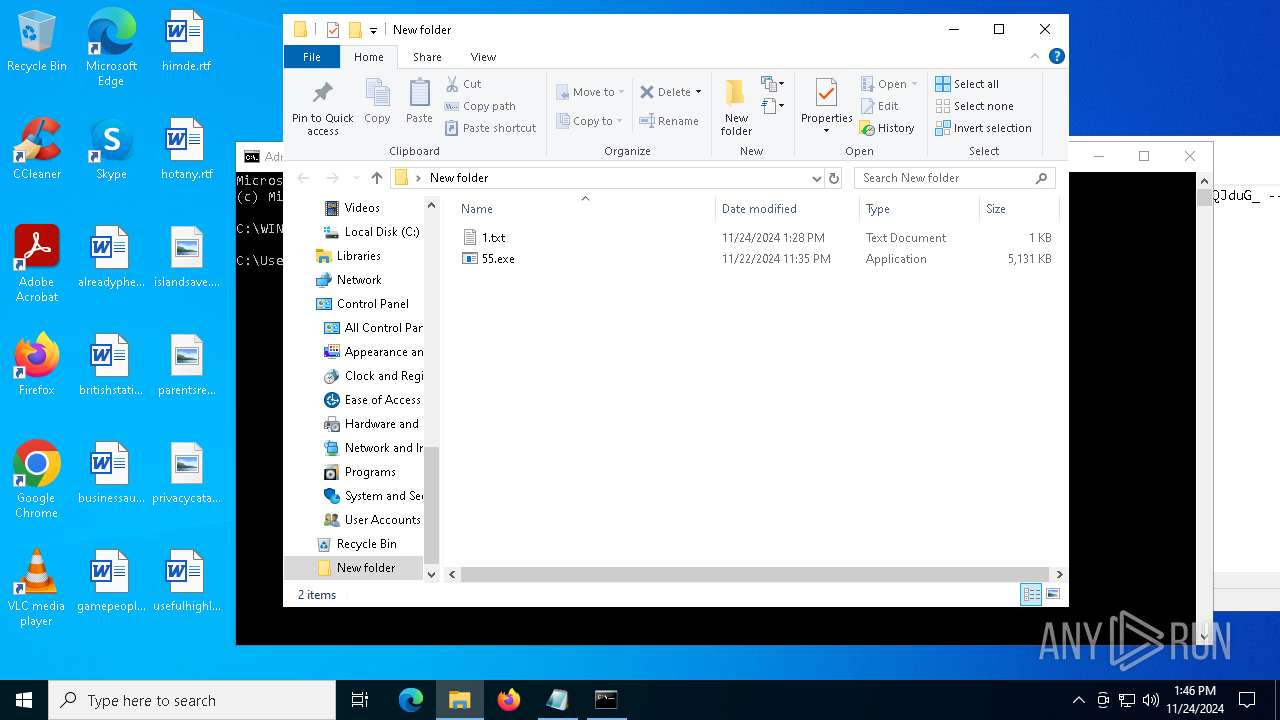
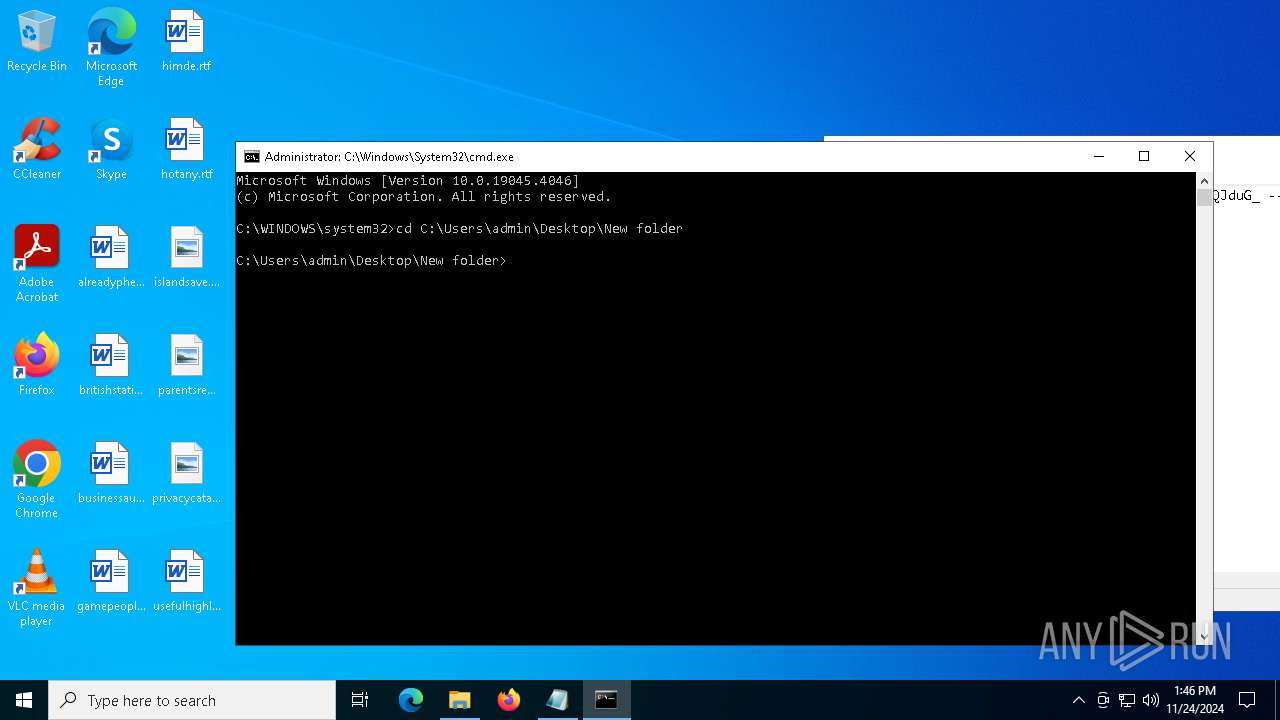
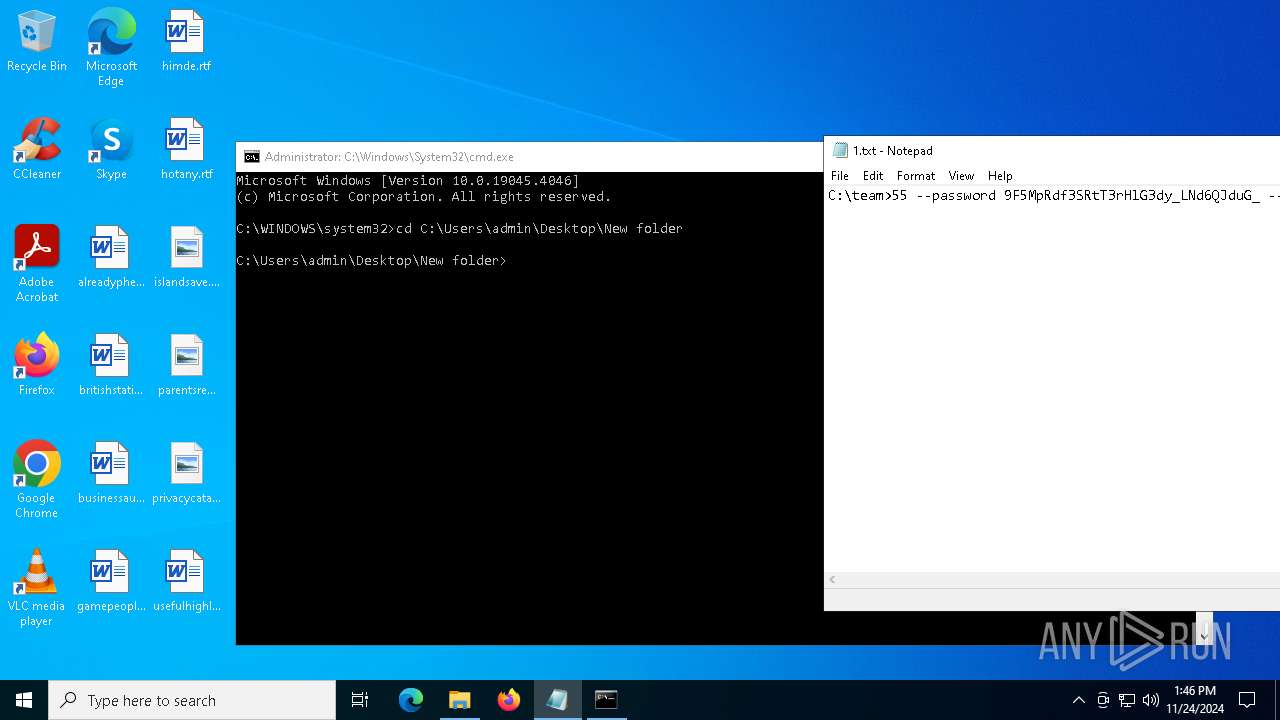
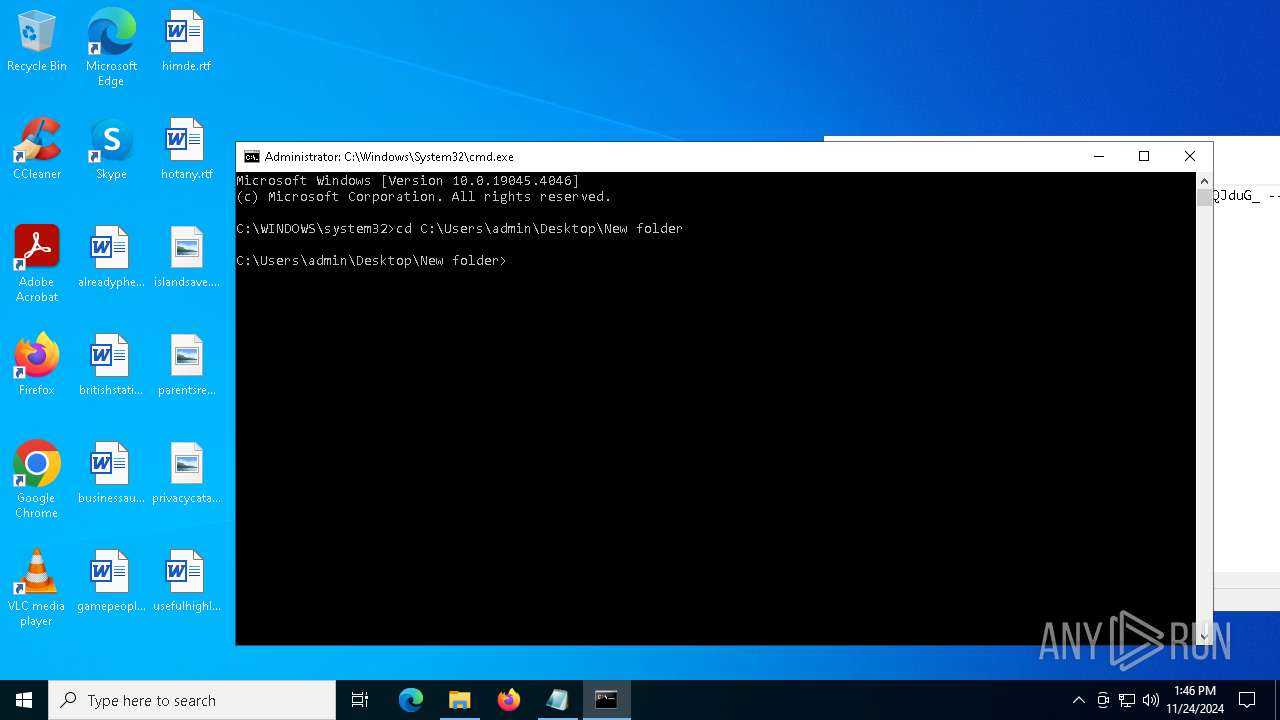
Manual execution by a user
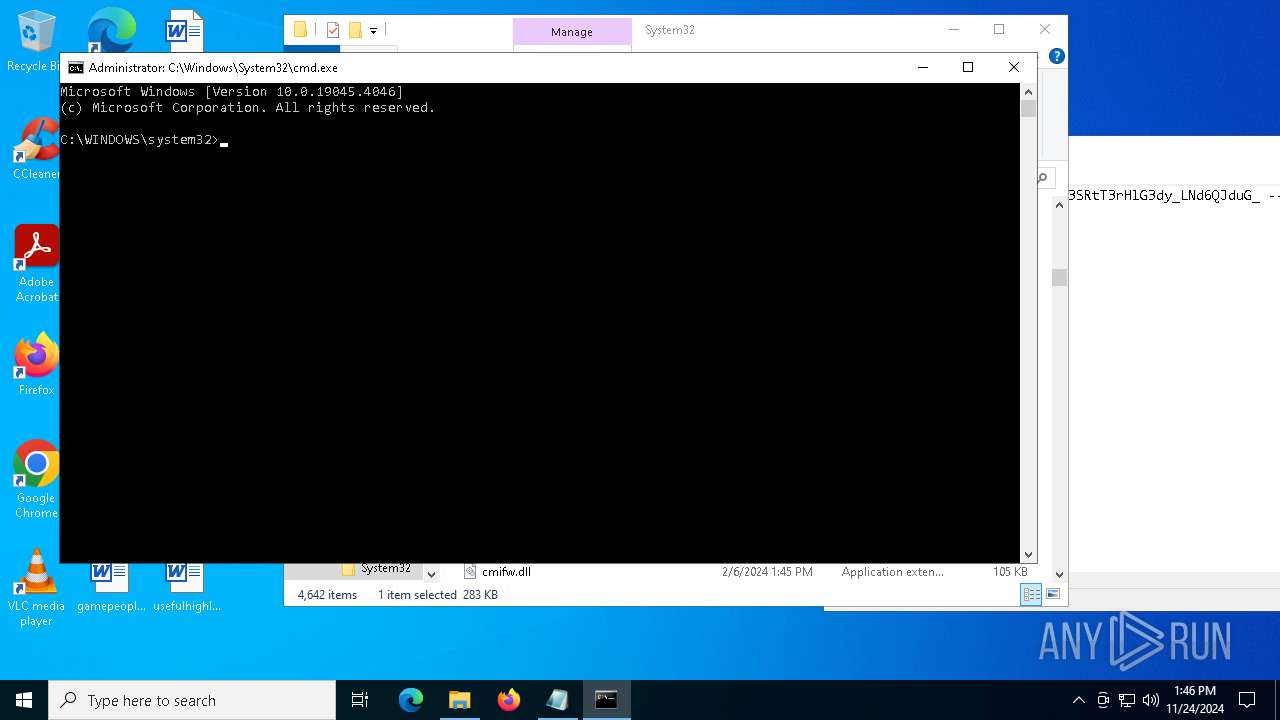
- cmd.exe (PID: 6976)
- notepad.exe (PID: 6776)
Checks supported languages
- 55.exe (PID: 7148)
- Pcuolnqz.exe (PID: 5892)
- PSEXESVC.exe (PID: 1536)
- Pcuolnqz.exe (PID: 1520)
- PSEXESVC.exe (PID: 1140)
- 55.exe (PID: 4824)
Reads the computer name
- 55.exe (PID: 7148)
- Pcuolnqz.exe (PID: 5892)
- PSEXESVC.exe (PID: 1536)
- PSEXESVC.exe (PID: 1140)
- Pcuolnqz.exe (PID: 1520)
- 55.exe (PID: 4824)
Create files in a temporary directory
- 55.exe (PID: 7148)
Checks proxy server information
- Pcuolnqz.exe (PID: 5892)
Reads the machine GUID from the registry
- PSEXESVC.exe (PID: 1536)
- Pcuolnqz.exe (PID: 5892)
- Pcuolnqz.exe (PID: 1520)
- PSEXESVC.exe (PID: 1140)
Creates files in the program directory
- PSEXESVC.exe (PID: 1536)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6212)
The executable file from the user directory is run by the Powershell process
- DismHost.exe (PID: 6944)
- DismHost.exe (PID: 2804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2024:11:24 13:28:49+00:00 |
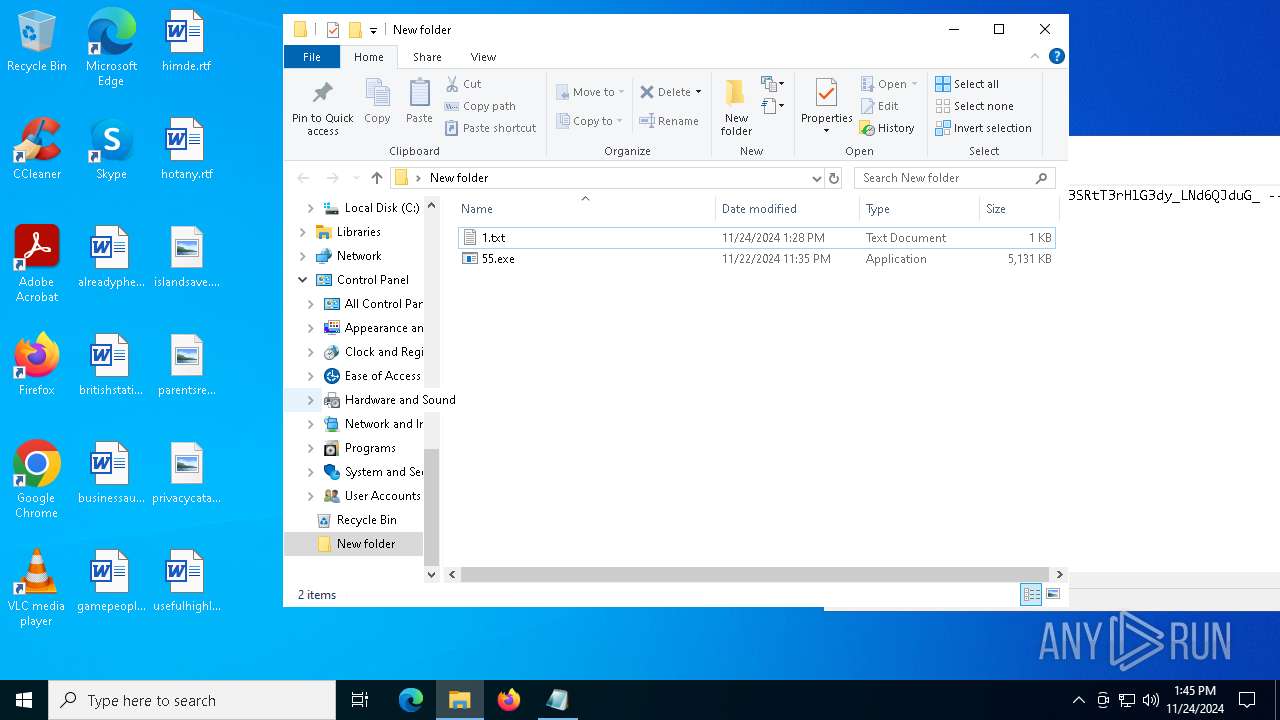
| ArchivedFileName: | 1.txt |
Total processes
189
Monitored processes
56
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
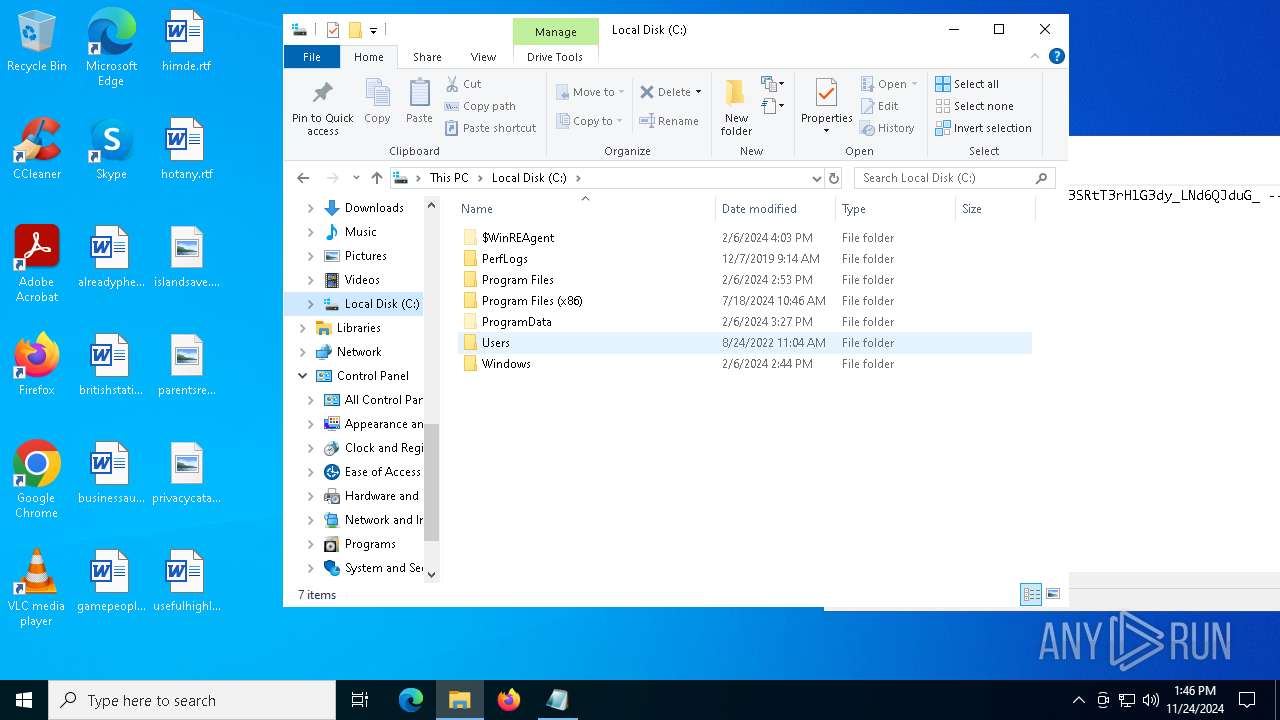
| 1140 | C:\WINDOWS\PSEXESVC.exe | C:\Windows\PSEXESVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Sysinternals Integrity Level: SYSTEM Description: PsExec Service Exit code: 0 Version: 2.43 Modules
| |||||||||||||||
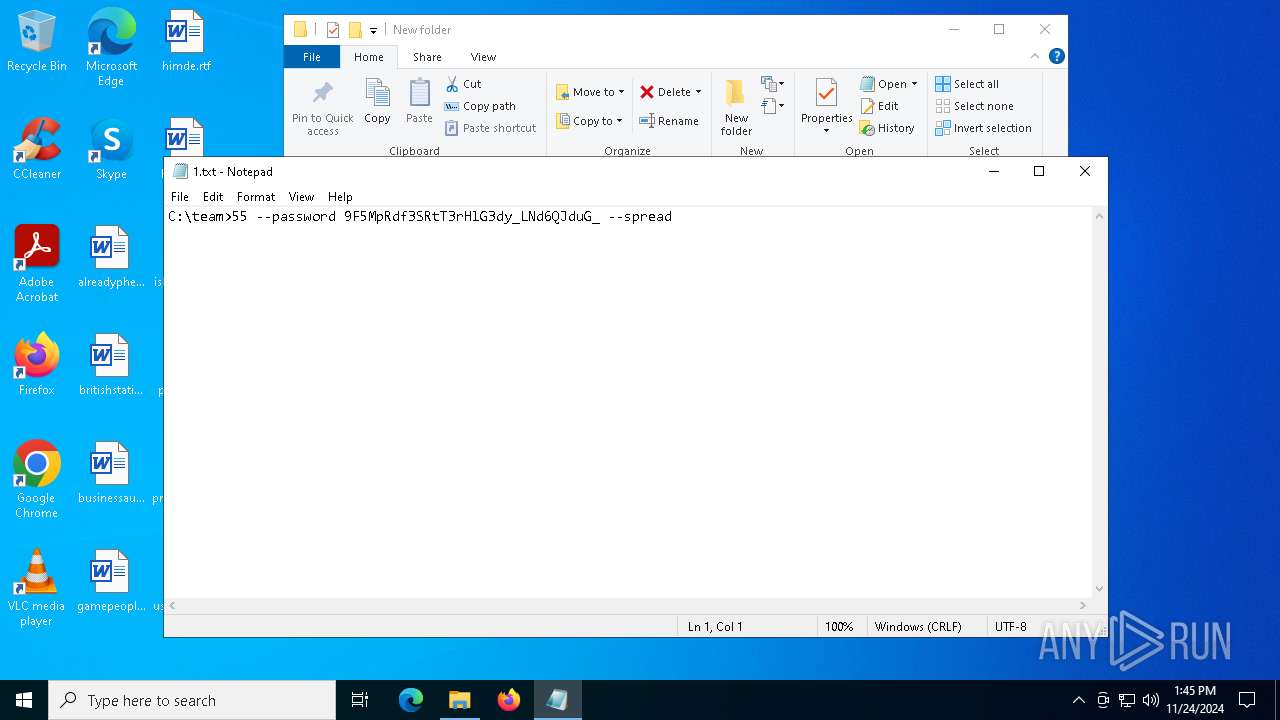
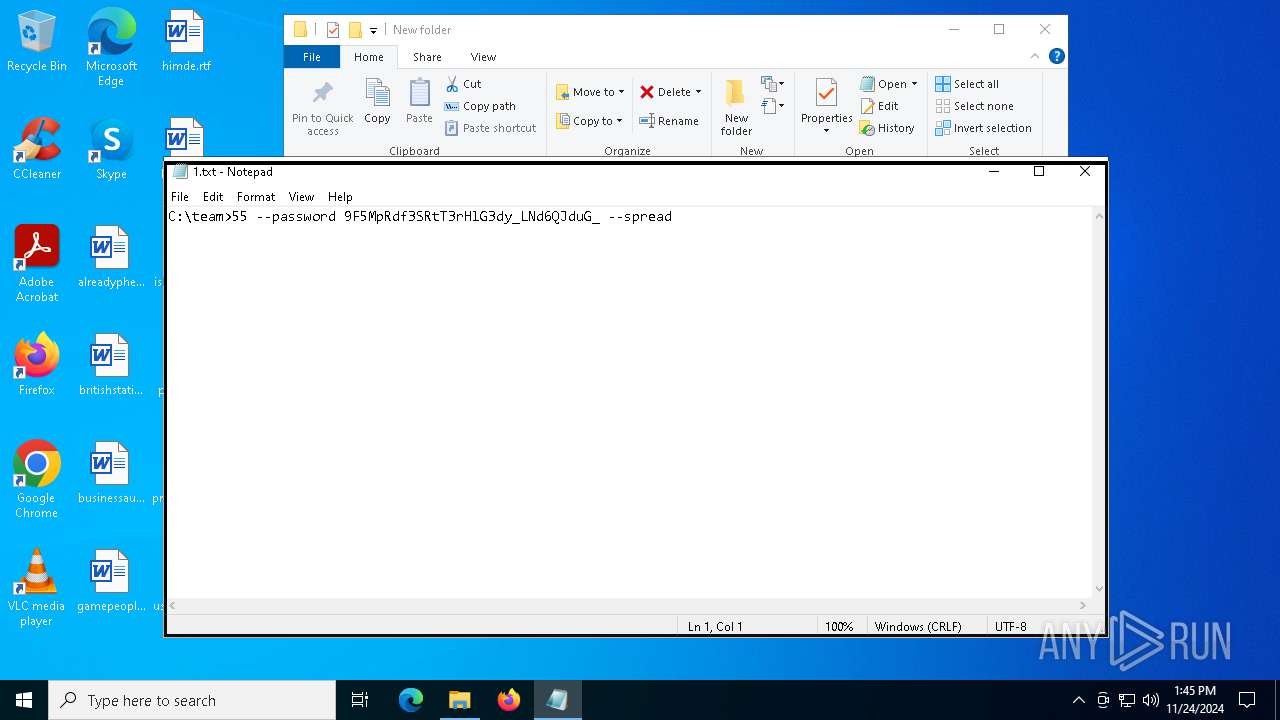
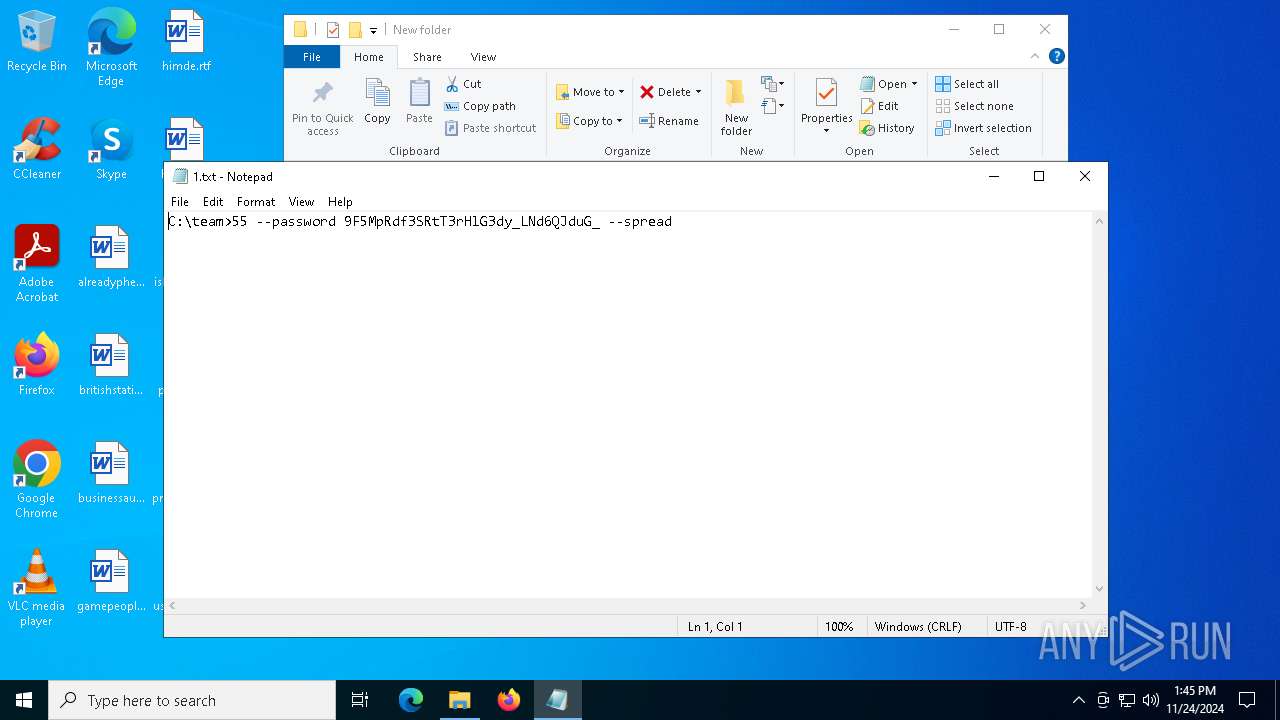
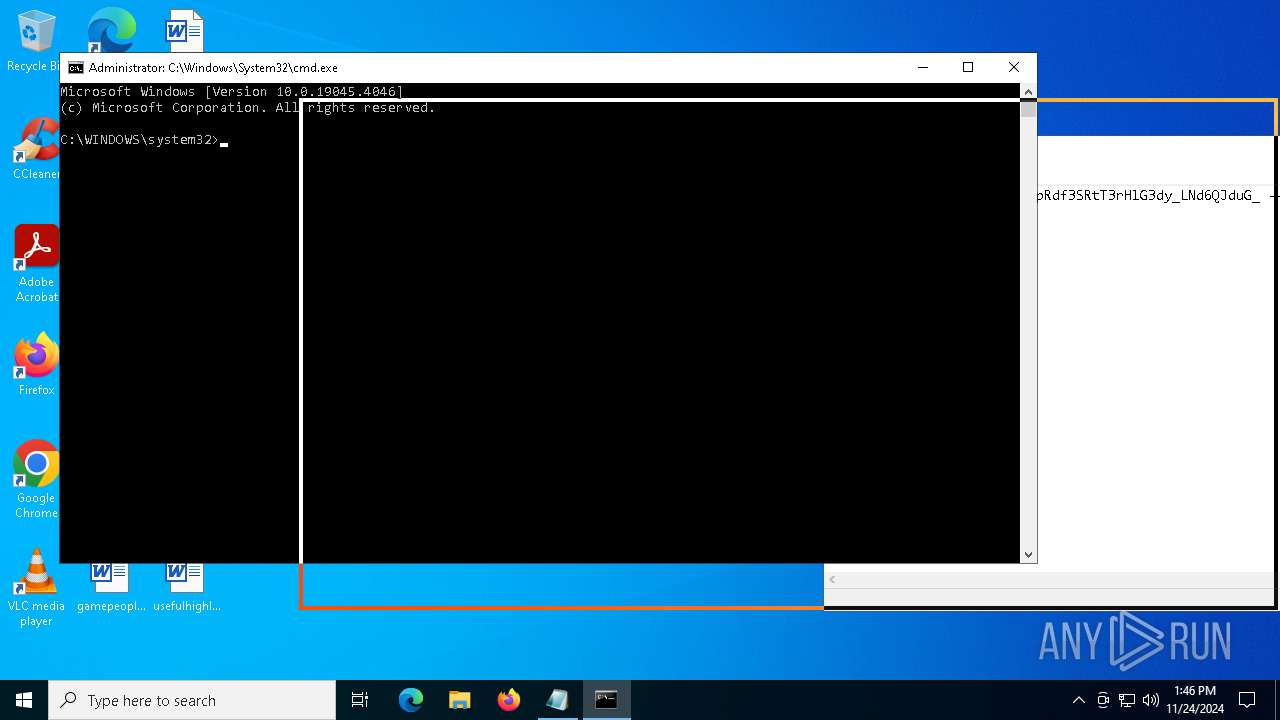
| 1520 | C:\Users\admin\AppData\Local\Temp\Pcuolnqz.exe -accepteula \\127.0.0.1 -c -f -h -d -i "C:\Users\admin\Desktop\New folder\55.exe" --password 9F5MpRdf3SRtT3rHlG3dy_LNd6QJduG_ --spread --spread-process | C:\Users\admin\AppData\Local\Temp\Pcuolnqz.exe | cmd.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Execute processes remotely Exit code: 4824 Version: 2.43 Modules
| |||||||||||||||
| 1536 | C:\WINDOWS\PSEXESVC.exe | C:\Windows\PSEXESVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Sysinternals Integrity Level: SYSTEM Description: PsExec Service Exit code: 0 Version: 2.43 Modules
| |||||||||||||||
| 1544 | wmic service where name='vss' call ChangeStartMode Manual | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1732 | "cmd" /C net use | C:\Windows\SysWOW64\cmd.exe | — | 55.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | "cmd" /C wmic service where name='vss' call ChangeStartMode Manual | C:\Windows\SysWOW64\cmd.exe | — | 55.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2548 | vssadmin.exe delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2572 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2804 | C:\Users\admin\AppData\Local\Temp\E4E947E1-EEE8-482A-91D2-FB955D44C9C6\dismhost.exe {5B03B1D2-07A9-4CBF-B69E-3ABA3029F572} | C:\Users\admin\AppData\Local\Temp\E4E947E1-EEE8-482A-91D2-FB955D44C9C6\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
Total events
27 980
Read events
27 928
Write events
47
Delete events
5
Modification events
| (PID) Process: | (4556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Temp.7z | |||
| (PID) Process: | (4556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFE900000017000000A9040000F1010000 | |||
| (PID) Process: | (4556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
107
Suspicious files
334
Text files
205
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5892 | Pcuolnqz.exe | \Device\Mup:\127.0.0.1\pipe\PSEXESVC | — | |
MD5:— | SHA256:— | |||
| 1520 | Pcuolnqz.exe | \Device\Mup:\127.0.0.1\pipe\PSEXESVC | — | |
MD5:— | SHA256:— | |||
| 6212 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_obmwujg2.4nu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4556.24608\55.exe | executable | |
MD5:2BB209CCFC5103ECCAB523C875050CFA | SHA256:43691290AC03EBB26754203F1CC3940B32F036BABB7CFAB3CB14FE2128389C0C | |||
| 7148 | 55.exe | C:\Users\admin\AppData\Local\Temp\QLOG\ThreadId(2).LOG | text | |
MD5:8691CEF9064793AB455CF3328743F77A | SHA256:C99EC4943DFA72C84BD8BE701D4FF63934079A55514A5E411ACF90BFF949DB2F | |||
| 5892 | Pcuolnqz.exe | \Device\Mup:\127.0.0.1\ADMIN$\55.exe | executable | |
MD5:2BB209CCFC5103ECCAB523C875050CFA | SHA256:43691290AC03EBB26754203F1CC3940B32F036BABB7CFAB3CB14FE2128389C0C | |||
| 6212 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_j1flnbpy.nwg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7148 | 55.exe | C:\Users\admin\AppData\Local\Temp\Pcuolnqz.exe | executable | |
MD5:24A648A48741B1AC809E47B9543C6F12 | SHA256:078163D5C16F64CAA5A14784323FD51451B8C831C73396B967B4E35E6879937B | |||
| 5892 | Pcuolnqz.exe | \Device\Mup:\127.0.0.1\ADMIN$\PSEXESVC.exe | executable | |
MD5:44118D8FB41634B3D8D8B1C6FDF9C421 | SHA256:CC14DF781475EF0F3F2C441D03A622EA67CD86967526F8758EAD6F45174DB78E | |||
| 5892 | Pcuolnqz.exe | \Device\Mup:\127.0.0.1\ADMIN$\\PSEXEC-DESKTOP-JGLLJLD-D208D013.key | binary | |
MD5:01730B17F5C4B34429521F641FB8FDD5 | SHA256:9D0FCD60C8C24F202CE675F987A9CB3323DC68622427645B4368955BB8FE78A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5580 | svchost.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5580 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6440 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6440 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1904 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 92.123.104.17:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5580 | svchost.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5580 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1076 | svchost.exe | 23.52.181.141:443 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
powershell.exe | PID=3416 TID=3124 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=3416 TID=3124 Input parameters: LogLevel: 2, LogFilePath: C:\WINDOWS\Logs\DISM\dism.log, ScratchDirectory: (null) - DismInitializeInternal
|
powershell.exe | PID=3416 TID=3124 Initialized GlobalConfig - DismInitializeInternal
|
powershell.exe | PID=3416 TID=3124 DismApi.dll: <----- Starting DismApi.dll session -----> - DismInitializeInternal
|
powershell.exe | PID=3416 TID=3124 Enter DismInitializeInternal - DismInitializeInternal
|
powershell.exe | PID=3416 TID=3124 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=3416 TID=3124 DismApi.dll: Host machine information: OS Version=10.0.19045, Running architecture=amd64, Number of processors=4 - DismInitializeInternal
|
powershell.exe | PID=3416 TID=3124 Initialized SessionTable - DismInitializeInternal
|
powershell.exe | PID=3416 TID=3124 Lookup in table by path failed for: DummyPath-2BA51B78-C7F7-4910-B99D-BB7345357CDC - CTransactionalImageTable::LookupImagePath
|
powershell.exe | PID=3416 TID=3124 DismApi.dll: API Version 10.0.19041.3758 - DismInitializeInternal
|