| File name: | 12345.exe |
| Full analysis: | https://app.any.run/tasks/f70ba686-2538-4232-bcf8-6db6d40ca6c7 |
| Verdict: | Malicious activity |
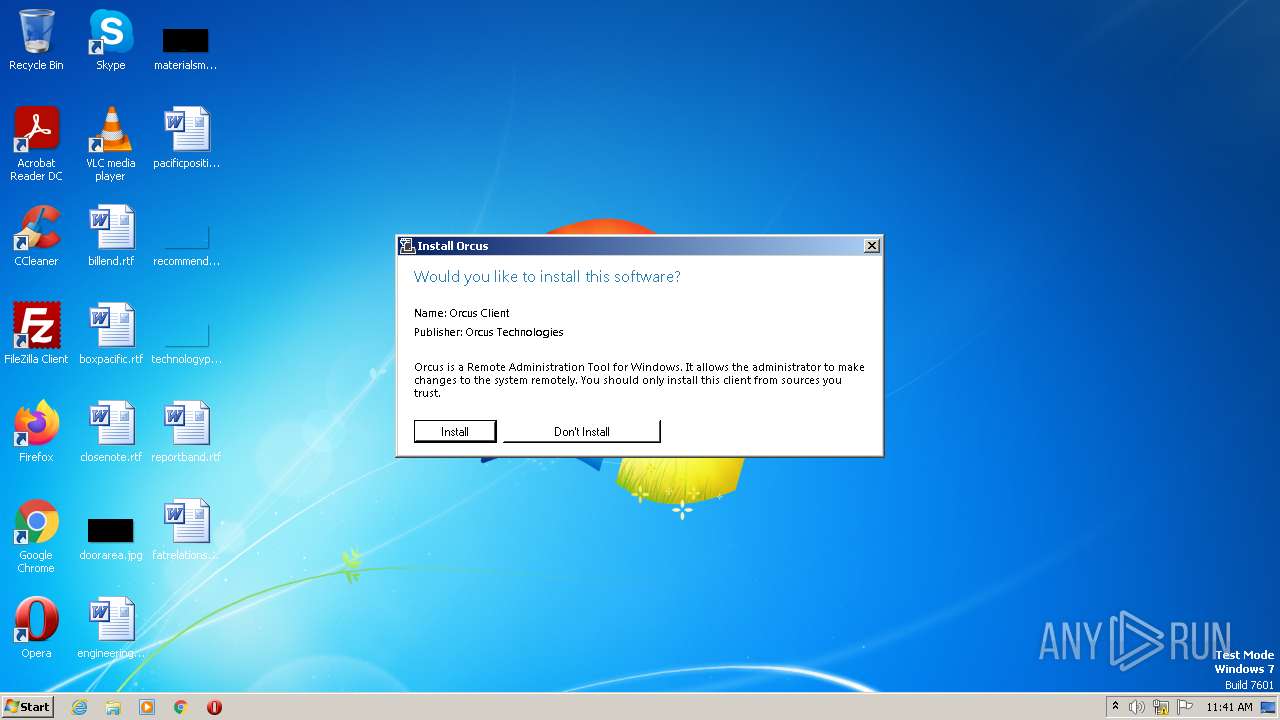
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | April 01, 2023, 10:41:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 961638A473CA1FE3BF57C687A8E0E8CB |
| SHA1: | E56512C9400C1C93458595A9A1A8A0AD1C1F3ACE |
| SHA256: | 6F38E38E0D518F3A15D57D2C329CD76F26952541FDBEAAB74E66C5FE30FE9CB0 |
| SSDEEP: | 24576:n1X4MROxnFVpSxXSgrrcI0AilFEvxHP2oooq:n+MihKSgrrcI0AilFEvxHP2 |
MALICIOUS
Orcus is detected
- 12345.exe (PID: 2696)
- 12345.exe (PID: 3724)
- Orcus.exe (PID: 664)
ORCUS detected by memory dumps
- Orcus.exe (PID: 664)
ORCUS was detected
- Orcus.exe (PID: 664)
Loads dropped or rewritten executable
- Orcus.exe (PID: 664)
SUSPICIOUS
Reads the Internet Settings
- 12345.exe (PID: 2696)
- 12345.exe (PID: 3724)
- Orcus.exe (PID: 664)
Application launched itself
- 12345.exe (PID: 2696)
Executable content was dropped or overwritten
- 12345.exe (PID: 3724)
- Orcus.exe (PID: 664)
Starts itself from another location
- 12345.exe (PID: 3724)
Reads settings of System Certificates
- Orcus.exe (PID: 664)
Starts CMD.EXE for commands execution
- Orcus.exe (PID: 664)
INFO
Checks supported languages
- 12345.exe (PID: 2696)
- 12345.exe (PID: 3724)
- Orcus.exe (PID: 664)
- wmpnscfg.exe (PID: 3148)
The process checks LSA protection
- 12345.exe (PID: 2696)
- Orcus.exe (PID: 664)
- 12345.exe (PID: 3724)
- wmpnscfg.exe (PID: 3148)
Reads the computer name
- 12345.exe (PID: 2696)
- 12345.exe (PID: 3724)
- Orcus.exe (PID: 664)
- wmpnscfg.exe (PID: 3148)
Reads the machine GUID from the registry
- 12345.exe (PID: 2696)
- Orcus.exe (PID: 664)
- 12345.exe (PID: 3724)
- wmpnscfg.exe (PID: 3148)
Creates files or folders in the user directory
- 12345.exe (PID: 2696)
- Orcus.exe (PID: 664)
Creates files in the program directory
- 12345.exe (PID: 3724)
Manual execution by a user
- wmpnscfg.exe (PID: 3148)
Reads Environment values
- Orcus.exe (PID: 664)
Create files in a temporary directory
- Orcus.exe (PID: 664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Orcus
(PID) Process(664) Orcus.exe
C2 (2)192.168.0.200:1605
212.ip.ply.gg:25428
Keys
AES3bf85c4519bdadc62c8fffaee211dc4bbaba229a6bc85c636dbf4edaa60d00c8
Salt
Options
AutostartBuilderProperty
AutostartMethodDisable
TaskSchedulerTaskNameOrcus
TaskHighestPrivilegestrue
RegistryHiddenStarttrue
RegistryKeyNameOrcus
TryAllAutostartMethodsOnFailtrue
ChangeAssemblyInformationBuilderProperty
ChangeAssemblyInformationfalse
AssemblyTitlenull
AssemblyDescriptionnull
AssemblyCompanyNamenull
AssemblyProductNamenull
AssemblyCopyrightnull
AssemblyTrademarksnull
AssemblyProductVersion1.0.0.0
AssemblyFileVersion1.0.0.0
ChangeCreationDateBuilderProperty
IsEnabledfalse
NewCreationDate2023-04-01T13:40:53.6657442+03:00
ChangeIconBuilderProperty
ChangeIconfalse
IconPathnull
ClientTagBuilderProperty
ClientTagnull
DataFolderBuilderProperty
Path%appdata%\Orcus
DefaultPrivilegesBuilderProperty
RequireAdministratorRightsfalse
DisableInstallationPromptBuilderProperty
IsDisabledfalse
FrameworkVersionBuilderProperty
FrameworkVersionNET45
HideFileBuilderProperty
HideFilefalse
InstallationLocationBuilderProperty
Path%programfiles%\Orcus\Orcus.exe
InstallBuilderProperty
Installtrue
KeyloggerBuilderProperty
IsEnabledfalse
MutexBuilderProperty
Mutex7a178cd1e596406eaee358484e3dc604
ProxyBuilderProperty
ProxyOptionNone
ProxyAddressnull
ProxyPort1080
ProxyType2
ReconnectDelayProperty
Delay10000
RequireAdministratorPrivilegesInstallerBuilderProperty
RequireAdministratorPrivilegestrue
RespawnTaskBuilderProperty
IsEnabledfalse
TaskNameOrcus Respawner
ServiceBuilderProperty
Installfalse
SetRunProgramAsAdminFlagBuilderProperty
SetFlagfalse
WatchdogBuilderProperty
IsEnabledfalse
NameOrcusWatchdog.exe
WatchdogLocationAppData
PreventFileDeletionfalse
Plugins
PluginNameBSoD Protection
PluginVersion2.0
ResourceName73ecf4af02f048129e7a7e13ee43956f
ResourceTypeClientPlugin
Guiddccbc1db-f7d1-413d-bba4-72611d485d3a
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | - |
| OriginalFileName: | Orcus.exe |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | Orcus.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | - |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xe333e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4608 |
| CodeSize: | 922624 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:04:01 10:41:28+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Apr-2023 10:41:28 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Orcus.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | Orcus.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Apr-2023 10:41:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000E1344 | 0x000E1400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.15155 |
.rsrc | 0x000E4000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99491 |
.reloc | 0x000E6000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99793 | 3128 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
44
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Orcus\Orcus.exe" | C:\Program Files\Orcus\Orcus.exe | 12345.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
Orcus(PID) Process(664) Orcus.exe C2 (2)192.168.0.200:1605 212.ip.ply.gg:25428 Keys AES3bf85c4519bdadc62c8fffaee211dc4bbaba229a6bc85c636dbf4edaa60d00c8 Salt Options AutostartBuilderProperty AutostartMethodDisable TaskSchedulerTaskNameOrcus TaskHighestPrivilegestrue RegistryHiddenStarttrue RegistryKeyNameOrcus TryAllAutostartMethodsOnFailtrue ChangeAssemblyInformationBuilderProperty ChangeAssemblyInformationfalse AssemblyTitlenull AssemblyDescriptionnull AssemblyCompanyNamenull AssemblyProductNamenull AssemblyCopyrightnull AssemblyTrademarksnull AssemblyProductVersion1.0.0.0 AssemblyFileVersion1.0.0.0 ChangeCreationDateBuilderProperty IsEnabledfalse NewCreationDate2023-04-01T13:40:53.6657442+03:00 ChangeIconBuilderProperty ChangeIconfalse IconPathnull ClientTagBuilderProperty ClientTagnull DataFolderBuilderProperty Path%appdata%\Orcus DefaultPrivilegesBuilderProperty RequireAdministratorRightsfalse DisableInstallationPromptBuilderProperty IsDisabledfalse FrameworkVersionBuilderProperty FrameworkVersionNET45 HideFileBuilderProperty HideFilefalse InstallationLocationBuilderProperty Path%programfiles%\Orcus\Orcus.exe InstallBuilderProperty Installtrue KeyloggerBuilderProperty IsEnabledfalse MutexBuilderProperty Mutex7a178cd1e596406eaee358484e3dc604 ProxyBuilderProperty ProxyOptionNone ProxyAddressnull ProxyPort1080 ProxyType2 ReconnectDelayProperty Delay10000 RequireAdministratorPrivilegesInstallerBuilderProperty RequireAdministratorPrivilegestrue RespawnTaskBuilderProperty IsEnabledfalse TaskNameOrcus Respawner ServiceBuilderProperty Installfalse SetRunProgramAsAdminFlagBuilderProperty SetFlagfalse WatchdogBuilderProperty IsEnabledfalse NameOrcusWatchdog.exe WatchdogLocationAppData PreventFileDeletionfalse Plugins PluginNameBSoD Protection PluginVersion2.0 ResourceName73ecf4af02f048129e7a7e13ee43956f ResourceTypeClientPlugin Guiddccbc1db-f7d1-413d-bba4-72611d485d3a | |||||||||||||||
| 1896 | "cmd.exe" | C:\Windows\System32\cmd.exe | — | Orcus.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2696 | "C:\Users\admin\AppData\Local\Temp\12345.exe" | C:\Users\admin\AppData\Local\Temp\12345.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3724 | "C:\Users\admin\AppData\Local\Temp\12345.exe" /wait | C:\Users\admin\AppData\Local\Temp\12345.exe | 12345.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
11 552
Read events
11 468
Write events
78
Delete events
6
Modification events
| (PID) Process: | (2696) 12345.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2696) 12345.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2696) 12345.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2696) 12345.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3724) 12345.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3724) 12345.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3724) 12345.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3724) 12345.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (664) Orcus.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3148) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{58414CB1-6D0E-44F9-A84C-4173CC0EF056}\{D2CD817F-C35F-4550-B6DA-3906D332BFF7} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
18
Suspicious files
6
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3724 | 12345.exe | C:\Program Files\Orcus\Orcus.exe | executable | |
MD5:— | SHA256:— | |||
| 2696 | 12345.exe | C:\Users\admin\AppData\Roaming\.orcusInstallation | text | |
MD5:— | SHA256:— | |||
| 664 | Orcus.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 664 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\Cab36EA.tmp | compressed | |
MD5:E71C8443AE0BC2E282C73FAEAD0A6DD3 | SHA256:95B0A5ACC5BF70D3ABDFD091D0C9F9063AA4FDE65BD34DBF16786082E1992E72 | |||
| 664 | Orcus.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:E71C8443AE0BC2E282C73FAEAD0A6DD3 | SHA256:95B0A5ACC5BF70D3ABDFD091D0C9F9063AA4FDE65BD34DBF16786082E1992E72 | |||
| 664 | Orcus.exe | C:\Users\admin\AppData\Local\Temp\Tar36EB.tmp | cat | |
MD5:BE2BEC6E8C5653136D3E72FE53C98AA3 | SHA256:1919AAB2A820642490169BDC4E88BD1189E22F83E7498BF8EBDFB62EC7D843FD | |||
| 664 | Orcus.exe | C:\Users\admin\AppData\Roaming\Orcus\lib_7a178cd1e596406eaee358484e3dc604\AForge.Video.DirectShow.dll | executable | |
MD5:17ED442E8485AC3F7DC5B3C089654A61 | SHA256:666D44798D94EAFA1ED21AF79E9BC0293FFD96F863AB5D87F78BCEE9EF9FFD6B | |||
| 3724 | 12345.exe | C:\Program Files\Orcus\Orcus.exe.config | xml | |
MD5:A2B76CEA3A59FA9AF5EA21FF68139C98 | SHA256:F99EF5BF79A7C43701877F0BB0B890591885BB0A3D605762647CC8FFBF10C839 | |||
| 664 | Orcus.exe | C:\Users\admin\AppData\Roaming\Orcus\lib_7a178cd1e596406eaee358484e3dc604\SharpDX.Direct3D11.dll | executable | |
MD5:98EB5BA5871ACDEAEBF3A3B0F64BE449 | SHA256:D7617D926648849CBFEF450B8F48E458EE52E2793FB2251A30094B778AA8848C | |||
| 664 | Orcus.exe | C:\Users\admin\AppData\Roaming\Orcus\lib_7a178cd1e596406eaee358484e3dc604\SharpDX.dll | executable | |
MD5:FFB4B61CC11BEC6D48226027C2C26704 | SHA256:061542FF3FB36039B7BBFFDF3E07B66176B264C1DFD834A14B09C08620717303 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
664 | Orcus.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d20ab13272eb711e | US | compressed | 61.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
664 | Orcus.exe | 13.107.4.50:80 | ctldl.windowsupdate.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 209.25.141.212:25428 | 212.ip.ply.gg | PLAYIT-GG | US | malicious |
— | — | 192.168.100.237:49175 | — | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
212.ip.ply.gg |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report