| File name: | Quotation.jar |
| Full analysis: | https://app.any.run/tasks/ece46c6d-6c4e-4564-8802-91ca043fbadd |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | April 08, 2019, 05:26:04 |
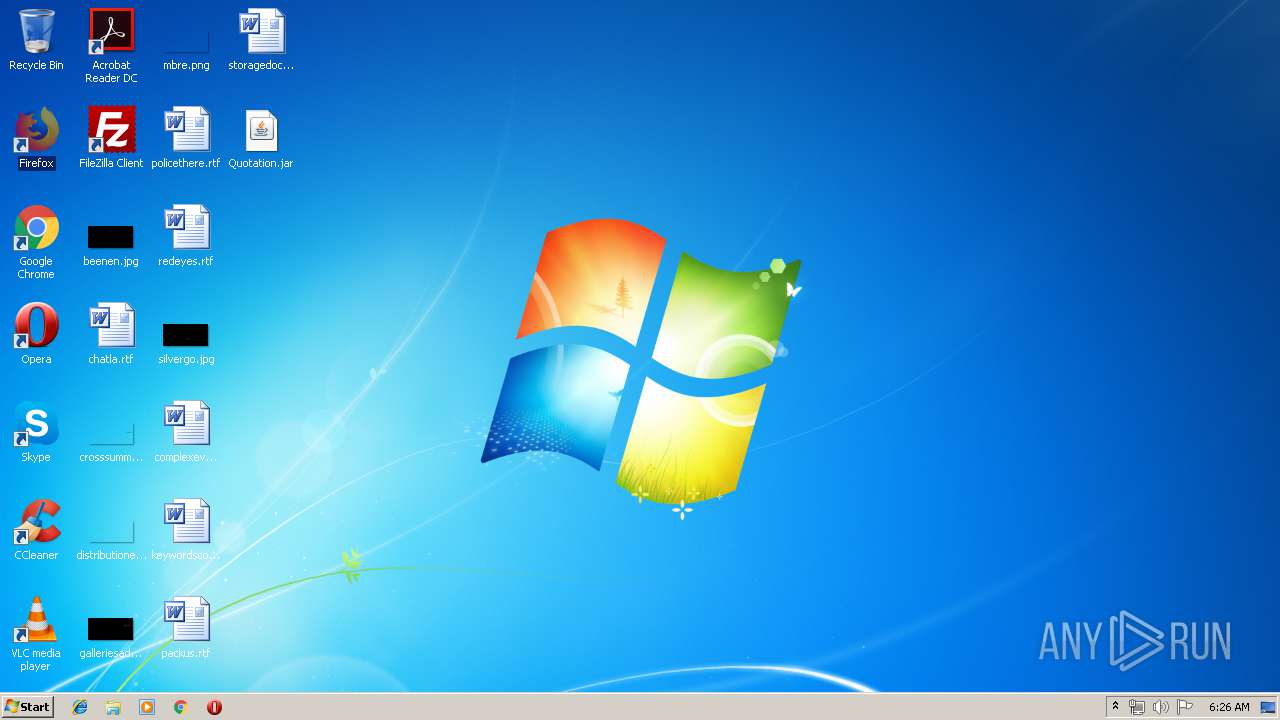
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | EC3761C28A6C741E3EF508E9DF020F73 |
| SHA1: | 9CF2E1ABE4539E7D4CA356A3B6ECA97EB4361C7A |
| SHA256: | 6ECA74891D389AE65B1AFCF8A20E7C720D84C4B6F2466A608D5A9B21E922C1DF |
| SSDEEP: | 12288:dM5Mw9Mt6hEGmCShPwQ/pFPfVCeX94892bzRJECLM+rrVkmAJlmuSs6fg:YL9vdmCaPwQ/p3dNJ92b1JECL9rBA+uL |
MALICIOUS
Changes the autorun value in the registry
- WScript.exe (PID: 3892)
- reg.exe (PID: 3564)
Uses Task Scheduler to run other applications
- WScript.exe (PID: 3892)
Writes to a start menu file
- WScript.exe (PID: 3892)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1300)
AdWind was detected
- java.exe (PID: 2232)
- java.exe (PID: 2524)
Loads dropped or rewritten executable
- javaw.exe (PID: 324)
- svchost.exe (PID: 820)
- java.exe (PID: 2232)
- javaw.exe (PID: 2812)
- explorer.exe (PID: 2044)
- javaw.exe (PID: 2412)
- wscript.exe (PID: 944)
- java.exe (PID: 2524)
Application was dropped or rewritten from another process
- java.exe (PID: 2232)
- javaw.exe (PID: 2812)
- javaw.exe (PID: 324)
- javaw.exe (PID: 2412)
- java.exe (PID: 2524)
SUSPICIOUS
Application launched itself
- wscript.exe (PID: 944)
Executes scripts
- wscript.exe (PID: 944)
- javaw.exe (PID: 2812)
- cmd.exe (PID: 2164)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 3672)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 1580)
- cmd.exe (PID: 2940)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 1300)
Creates files in the user directory
- wscript.exe (PID: 944)
- javaw.exe (PID: 324)
- WScript.exe (PID: 3892)
- xcopy.exe (PID: 3676)
Executes JAVA applets
- wscript.exe (PID: 944)
- explorer.exe (PID: 2044)
- javaw.exe (PID: 324)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 324)
- java.exe (PID: 2232)
- java.exe (PID: 2524)
- javaw.exe (PID: 2412)
Connects to unusual port
- WScript.exe (PID: 3892)
- javaw.exe (PID: 2412)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 324)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 324)
Starts itself from another location
- javaw.exe (PID: 324)
Executable content was dropped or overwritten
- xcopy.exe (PID: 3676)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:04 23:44:07 |
| ZipCRC: | 0xa3204dab |
| ZipCompressedSize: | 637286 |
| ZipUncompressedSize: | 948721 |
| ZipFileName: | fjvmjnfyaf/resources/zqwskvbkbx |
Total processes
76
Monitored processes
31
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Roaming\skczwdjfn.txt" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | wscript.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 804 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive5771667911925478622.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 820 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | wscript C:\Users\admin/tivrgurbmf.js | C:\Windows\system32\wscript.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1300 | "C:\Windows\System32\schtasks.exe" /create /sc minute /mo 30 /tn Skype /tr "C:\Users\admin\AppData\Roaming\gzgKuCQfGF.js | C:\Windows\System32\schtasks.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1300 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive4228023454819548851.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1580 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive5991684939990966311.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1868 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive2005600612245154053.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2044 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2100 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive5222562136417505592.vbs | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 464
Read events
2 439
Write events
25
Delete events
0
Modification events
| (PID) Process: | (944) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (944) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3892) WScript.exe | Key: | HKEY_CURRENT_USER |
| Operation: | write | Name: | vjw0rm |
Value: FALSE | |||
| (PID) Process: | (3892) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 0IDR124VF6 |
Value: "C:\Users\admin\AppData\Roaming\gzgKuCQfGF.js" | |||
| (PID) Process: | (3892) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3892) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3892) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3892) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3892) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3892) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
110
Suspicious files
10
Text files
78
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 944 | wscript.exe | C:\Users\admin\AppData\Roaming\skczwdjfn.txt | java | |
MD5:E85521436367EF15394A55676D0C977E | SHA256:38EE9C0502E7EA61903830A7706EEA87A21588F586AE4B0183328D6F00259CC0 | |||
| 324 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:7B2F93D7D31F08C995CDE4523099D699 | SHA256:9C4A9F92769D57C5E1BFAB4F7222387381FAADFF6858CB4CC9B0575E043AFB67 | |||
| 944 | wscript.exe | C:\Users\admin\AppData\Roaming\gzgKuCQfGF.js | text | |
MD5:C2C73616F079565531C2D1184108640F | SHA256:8557E9B4B68851821304F3C19CE857BA3198DCE227FB1BD3D2BEF078C1C66FB9 | |||
| 2812 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:0B0F9EE889B3341DD9797CA6E69B13FD | SHA256:0C4E9EBD406C3346311F94C5E0DFB8CA96CEBC0FC074A16653D185D9C93F48C9 | |||
| 3892 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\gzgKuCQfGF.js | text | |
MD5:C2C73616F079565531C2D1184108640F | SHA256:8557E9B4B68851821304F3C19CE857BA3198DCE227FB1BD3D2BEF078C1C66FB9 | |||
| 2232 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:15E12843A884A4E498B75764BE996066 | SHA256:4A7D3B4058D7411BD51905A2B0474E33D160F9E2B6914D05A0F6E4D9CEF0E2DB | |||
| 2812 | javaw.exe | C:\Users\admin\tivrgurbmf.js | text | |
MD5:9916F016ACB498EDFEA7F523F42A7B0D | SHA256:B0B94DD88D4E6CBAFA4B50EF01693296481A373619452EF8782C8F3340B67D7C | |||
| 3676 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\README.txt | text | |
MD5:0F1123976B959AC5E8B89EB8C245C4BD | SHA256:963095CF8DB76FB8071FD19A3110718A42F2AB42B27A3ADFD9EC58981C3E88D2 | |||
| 2232 | java.exe | C:\Users\admin\AppData\Local\Temp\Retrive2005600612245154053.vbs | text | |
MD5:A32C109297ED1CA155598CD295C26611 | SHA256:45BFE34AA3EF932F75101246EB53D032F5E7CF6D1F5B4E495334955A255F32E7 | |||
| 3676 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\LICENSE | text | |
MD5:98F46AB6481D87C4D77E0E91A6DBC15F | SHA256:23F9A5C12FA839650595A32872B7360B9E030C7213580FB27DD9185538A5828C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
67
DNS requests
3
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3892 | WScript.exe | 194.5.98.8:7755 | unknownsoft.duckdns.org | — | FR | malicious |
2412 | javaw.exe | 194.5.98.28:7121 | Blesseddon.dynu.net | — | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
unknownsoft.duckdns.org |
| malicious |
Blesseddon.dynu.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |