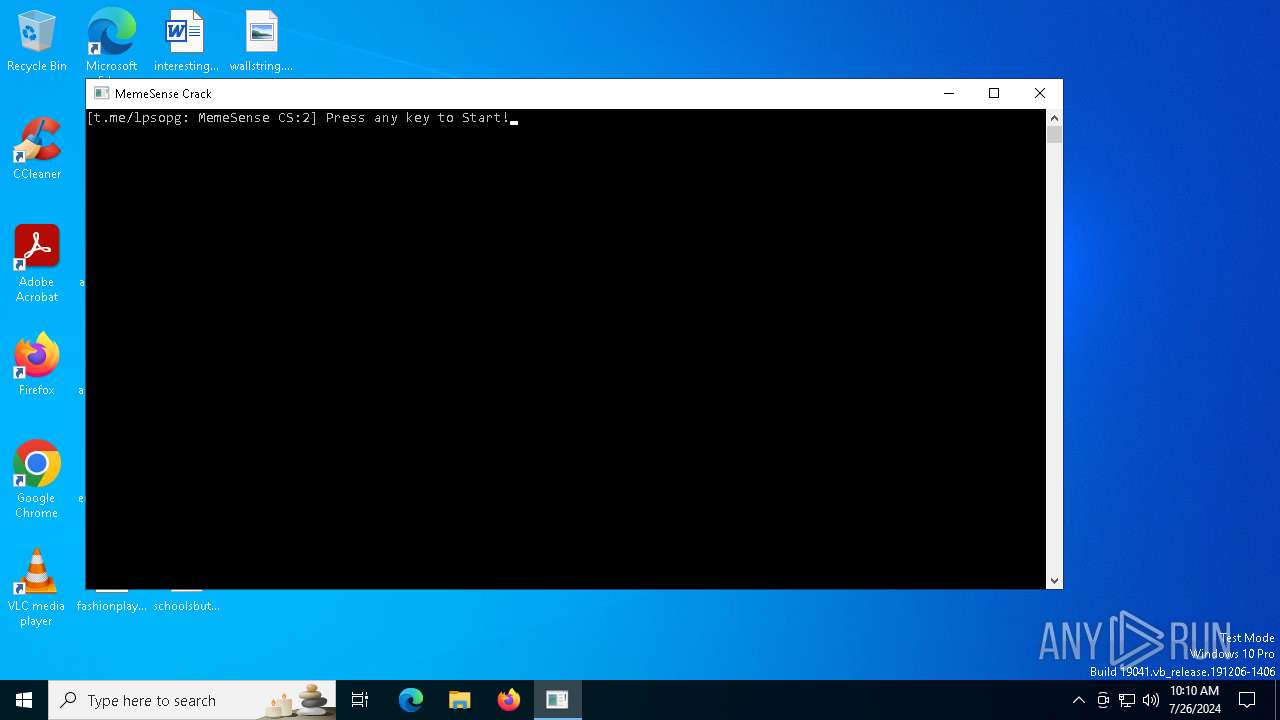
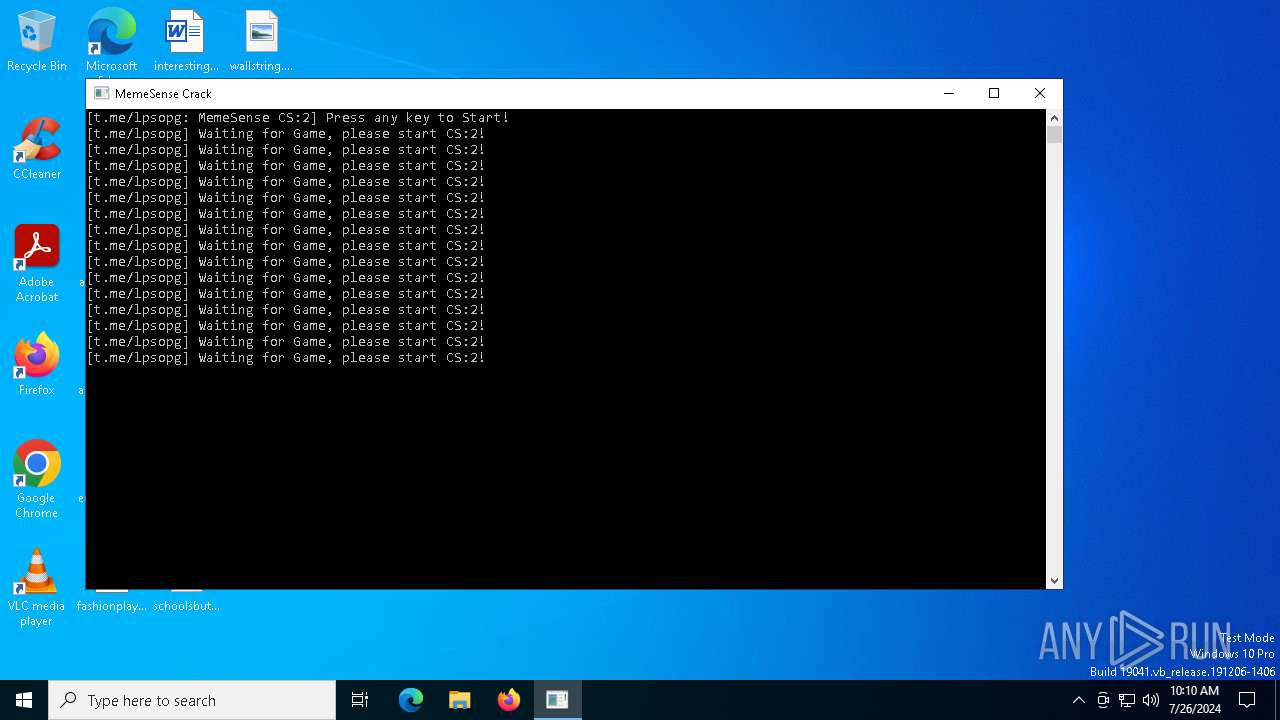
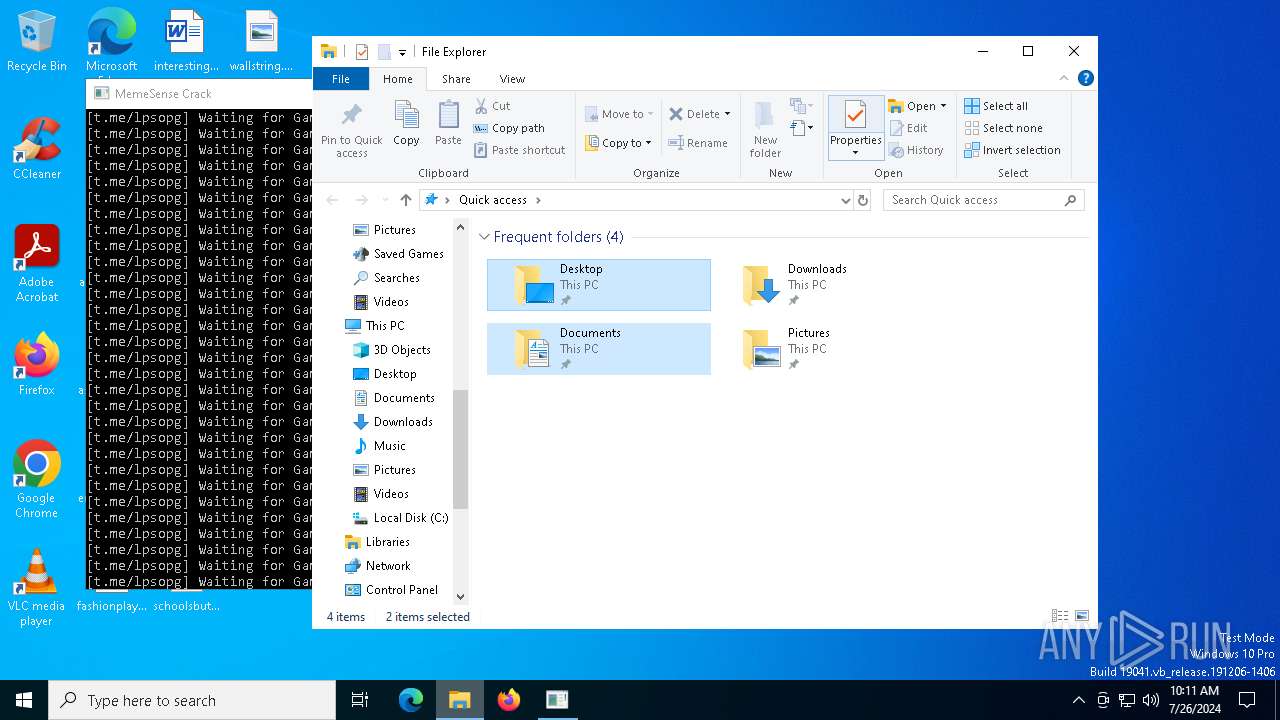
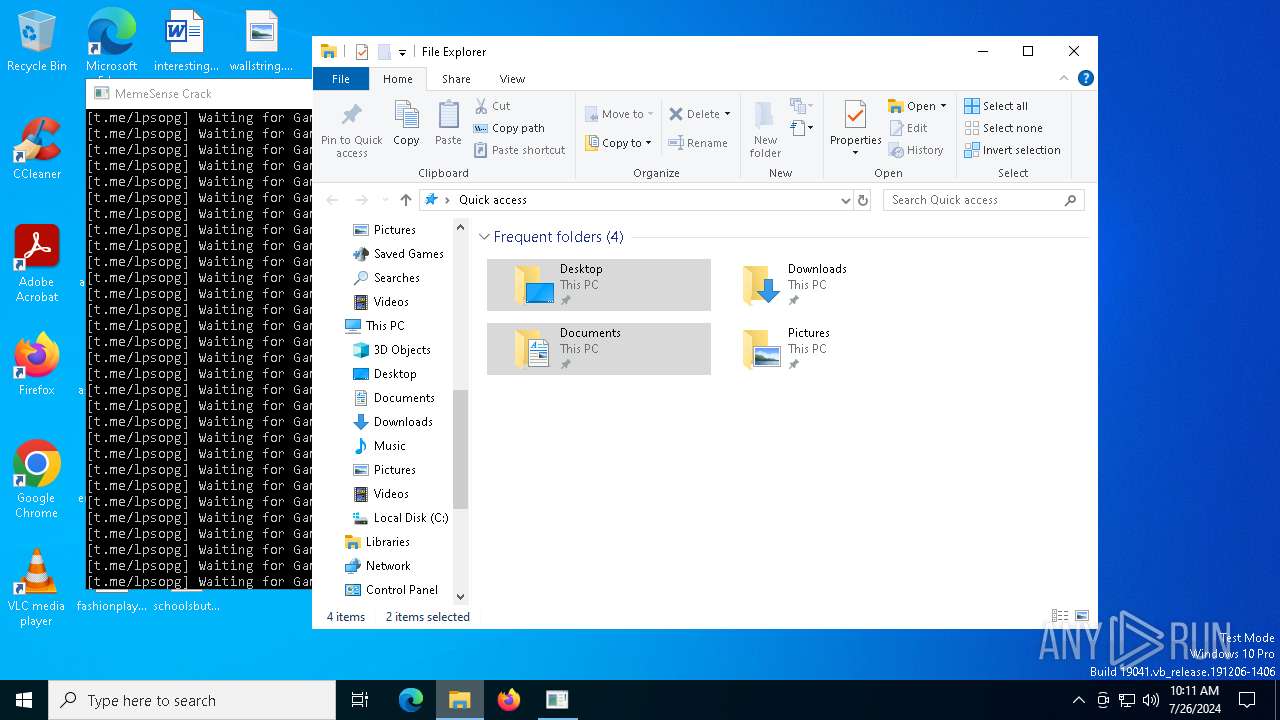
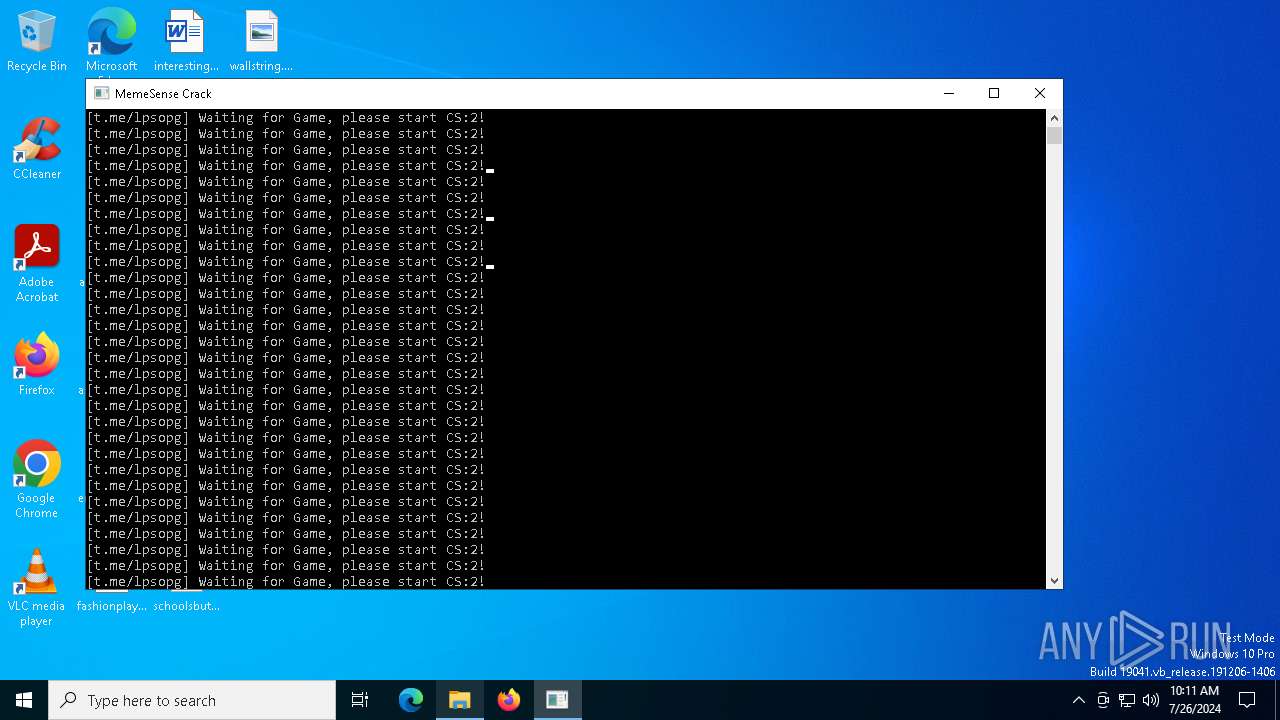
| File name: | MemeSense Crack.exe |
| Full analysis: | https://app.any.run/tasks/27cb630f-a620-4563-a535-172f237fdca8 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | July 26, 2024, 10:10:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8C7DC697B3BE09F1D66A29A31A8C6C46 |
| SHA1: | B3DAF07A8634E244943B7E55322C31D40F3FA788 |
| SHA256: | 6E947E57938D8A76586839227EA7942A06E4BC597A7667769F753AC3ECAC42E3 |
| SSDEEP: | 98304:sKkI464ckHCW3TeG13wjLl86CjRR6cLz3zyt6rjfGKa7StGsZBdVlT+IzyxyDhNt:LmZimjhJ4iWIaRL3 |
MALICIOUS
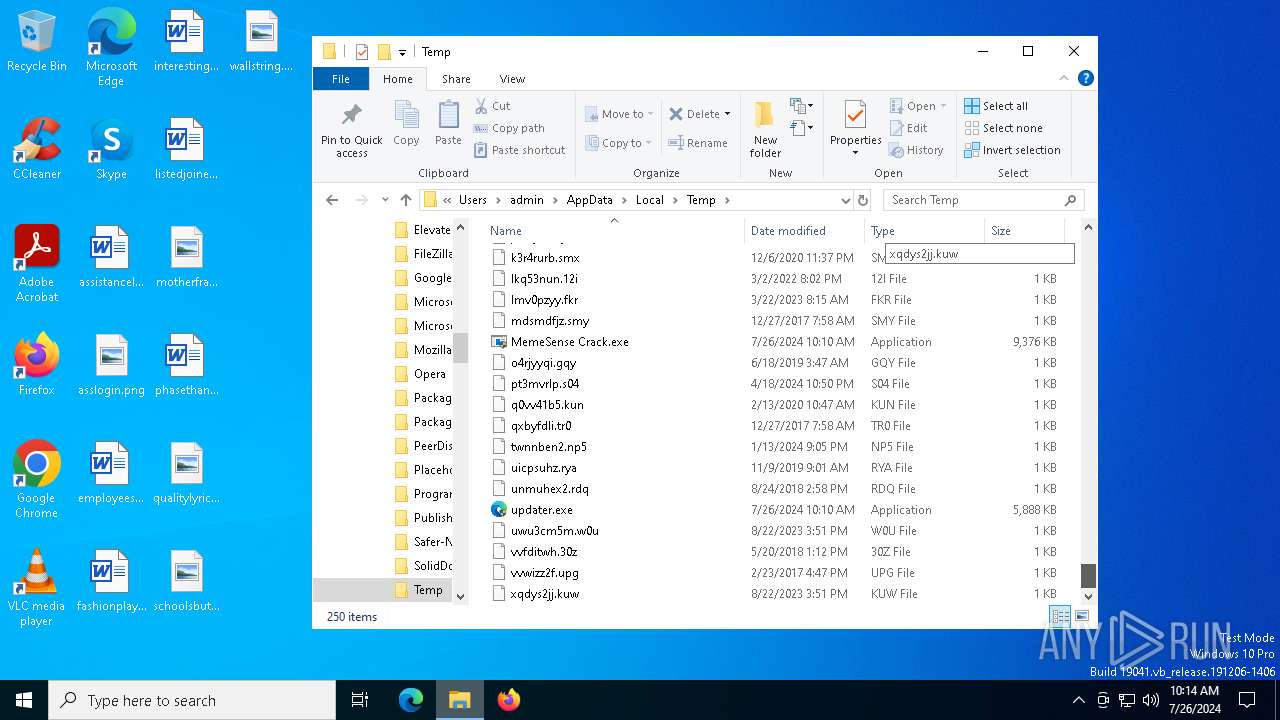
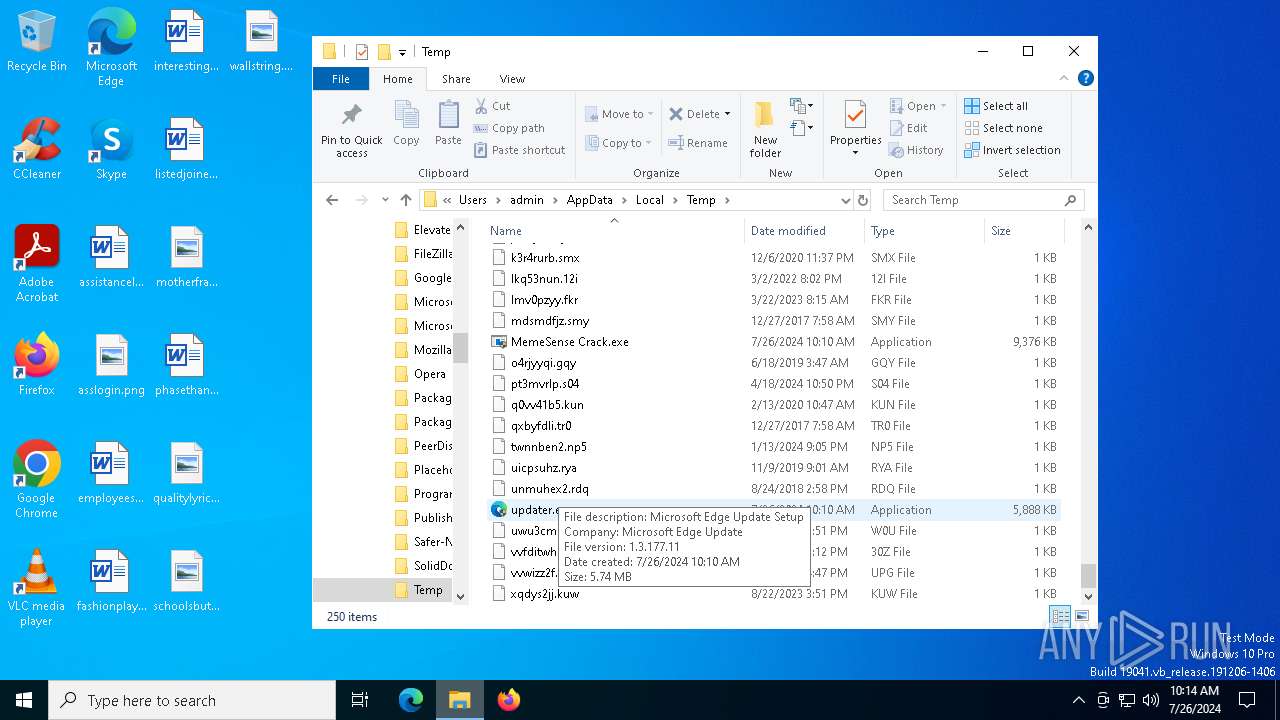
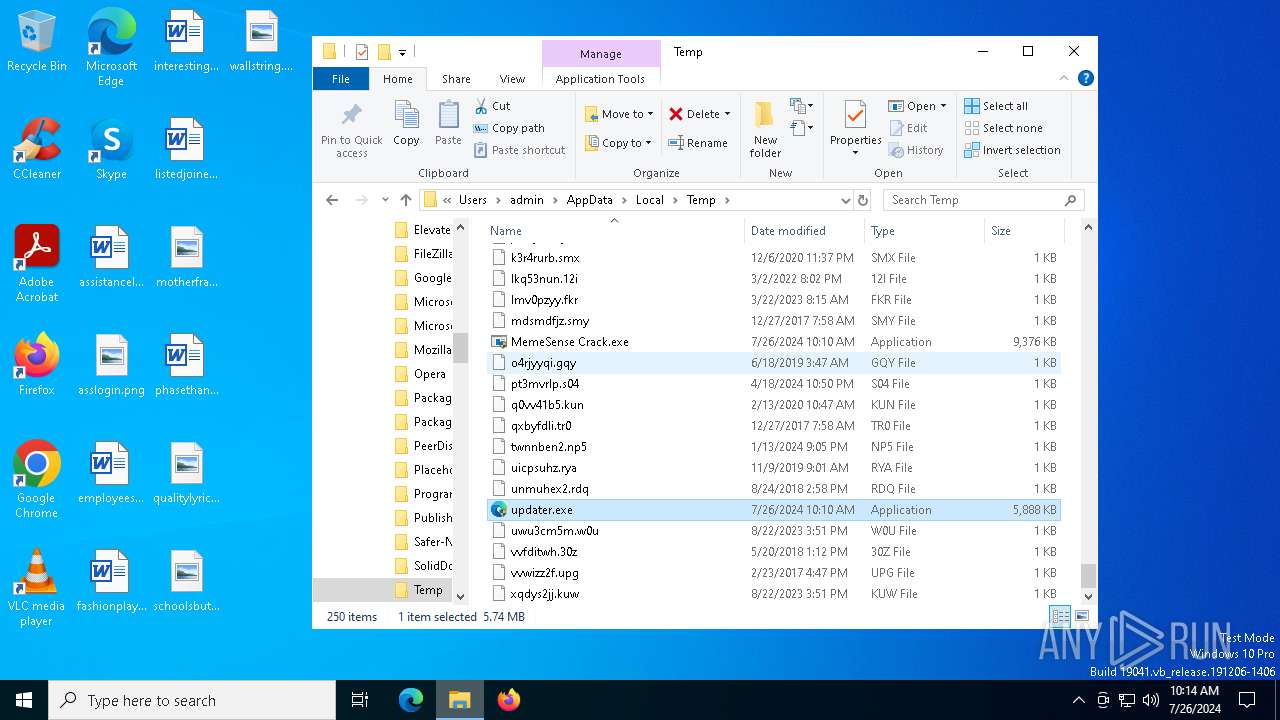
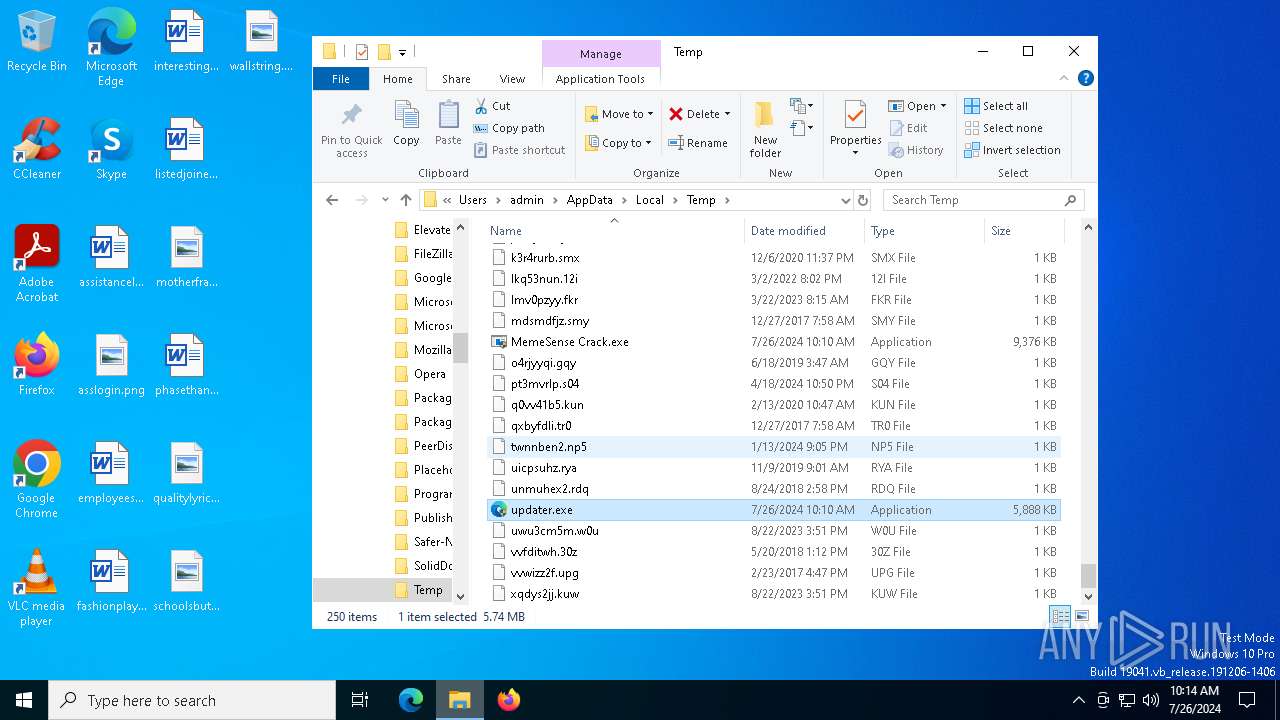
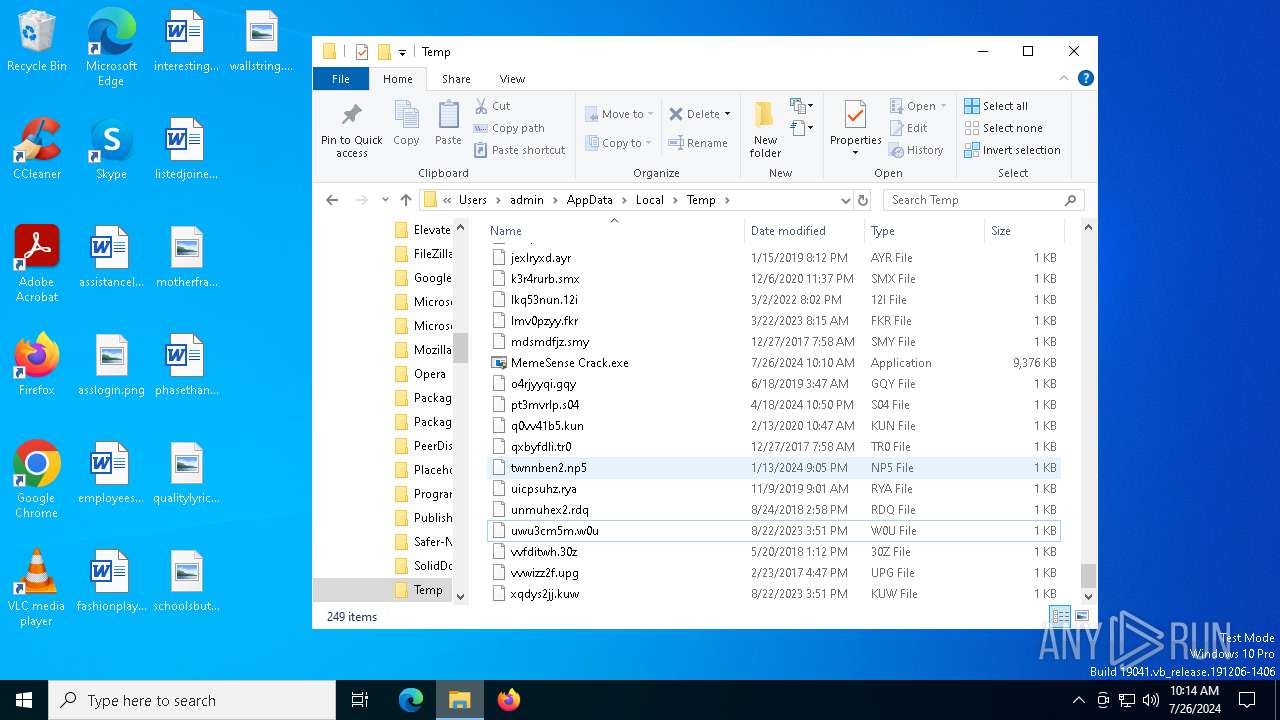
Drops the executable file immediately after the start
- MemeSense Crack.exe (PID: 2932)
- updater.exe (PID: 7132)
- updater.exe (PID: 2188)
Adds path to the Windows Defender exclusion list
- explorer.exe (PID: 5016)
Application was injected by another process
- svchost.exe (PID: 452)
- svchost.exe (PID: 1032)
- winlogon.exe (PID: 692)
- svchost.exe (PID: 1088)
- svchost.exe (PID: 1212)
- svchost.exe (PID: 1224)
- lsass.exe (PID: 760)
- svchost.exe (PID: 1372)
- svchost.exe (PID: 1412)
- svchost.exe (PID: 1284)
- svchost.exe (PID: 1232)
- svchost.exe (PID: 1456)
- svchost.exe (PID: 1492)
- svchost.exe (PID: 1656)
- svchost.exe (PID: 1604)
- svchost.exe (PID: 1664)
- svchost.exe (PID: 1680)
- svchost.exe (PID: 1916)
- svchost.exe (PID: 1876)
- svchost.exe (PID: 1740)
- svchost.exe (PID: 1928)
- svchost.exe (PID: 1944)
- svchost.exe (PID: 2076)
- svchost.exe (PID: 2180)
- svchost.exe (PID: 2412)
- svchost.exe (PID: 2284)
- svchost.exe (PID: 2524)
- svchost.exe (PID: 2312)
- spoolsv.exe (PID: 2640)
- svchost.exe (PID: 2848)
- svchost.exe (PID: 2600)
- svchost.exe (PID: 2372)
- svchost.exe (PID: 2436)
- svchost.exe (PID: 2912)
- svchost.exe (PID: 2532)
- svchost.exe (PID: 3176)
- svchost.exe (PID: 2948)
- svchost.exe (PID: 3540)
- svchost.exe (PID: 2712)
- svchost.exe (PID: 3156)
- svchost.exe (PID: 2832)
- svchost.exe (PID: 3260)
- svchost.exe (PID: 3268)
- dasHost.exe (PID: 3404)
- svchost.exe (PID: 3296)
- svchost.exe (PID: 3952)
- svchost.exe (PID: 4204)
- svchost.exe (PID: 3640)
- sihost.exe (PID: 4504)
- dwm.exe (PID: 588)
- svchost.exe (PID: 4528)
- svchost.exe (PID: 4280)
- svchost.exe (PID: 4716)
- ctfmon.exe (PID: 4756)
- svchost.exe (PID: 4924)
- svchost.exe (PID: 4572)
- svchost.exe (PID: 4668)
- RuntimeBroker.exe (PID: 5504)
- explorer.exe (PID: 5016)
- RuntimeBroker.exe (PID: 5248)
- dllhost.exe (PID: 5652)
- svchost.exe (PID: 6104)
- RuntimeBroker.exe (PID: 2108)
- MoUsoCoreWorker.exe (PID: 6012)
- svchost.exe (PID: 4372)
- ApplicationFrameHost.exe (PID: 824)
- svchost.exe (PID: 6212)
- uhssvc.exe (PID: 6796)
- svchost.exe (PID: 4888)
- UserOOBEBroker.exe (PID: 5328)
- dllhost.exe (PID: 4216)
- svchost.exe (PID: 2092)
- svchost.exe (PID: 4424)
- svchost.exe (PID: 6208)
- OfficeClickToRun.exe (PID: 4132)
- svchost.exe (PID: 6988)
- svchost.exe (PID: 7144)
- svchost.exe (PID: 2236)
- svchost.exe (PID: 6660)
- svchost.exe (PID: 6840)
- dllhost.exe (PID: 1132)
- RuntimeBroker.exe (PID: 3600)
- PLUGScheduler.exe (PID: 6836)
- SppExtComObj.Exe (PID: 4068)
- slui.exe (PID: 1328)
- taskhostw.exe (PID: 4792)
- RUXIMICS.exe (PID: 6572)
- WaaSMedicAgent.exe (PID: 3336)
- RUXIMICS.exe (PID: 7640)
- MusNotification.exe (PID: 6940)
- slui.exe (PID: 1156)
- svchost.exe (PID: 4348)
- conhost.exe (PID: 4304)
- UsoClient.exe (PID: 1296)
- svchost.exe (PID: 3348)
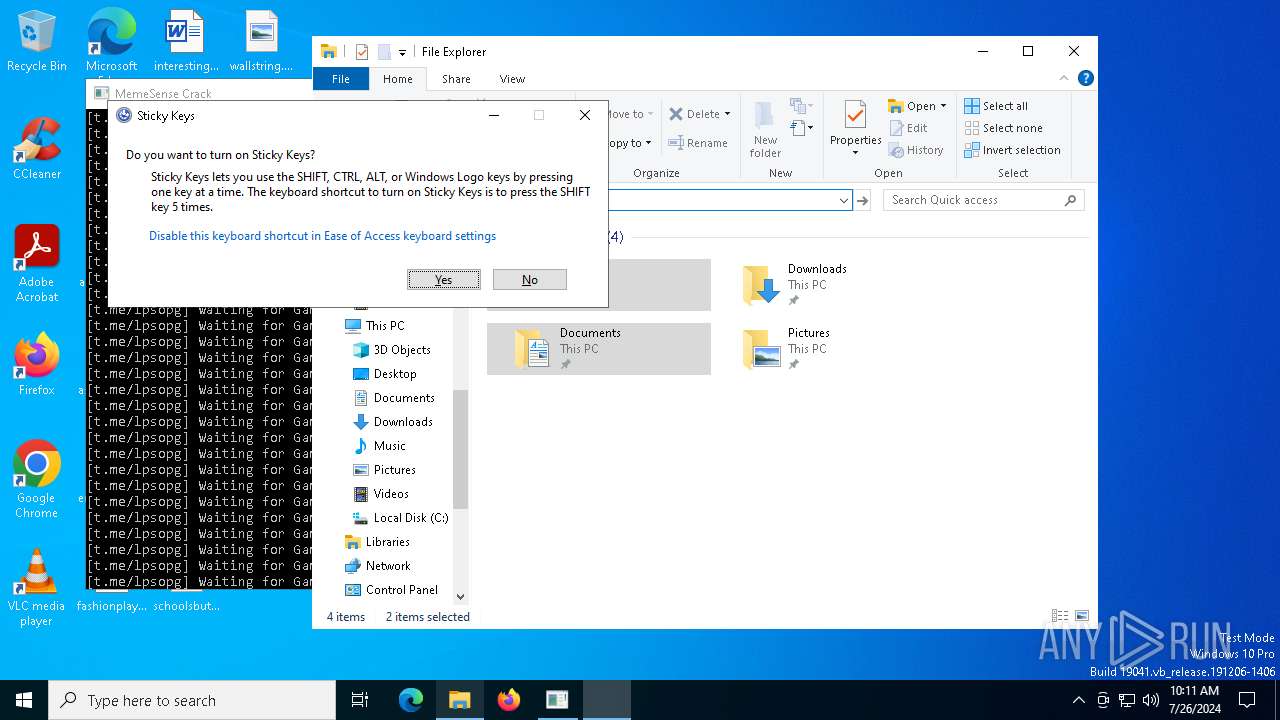
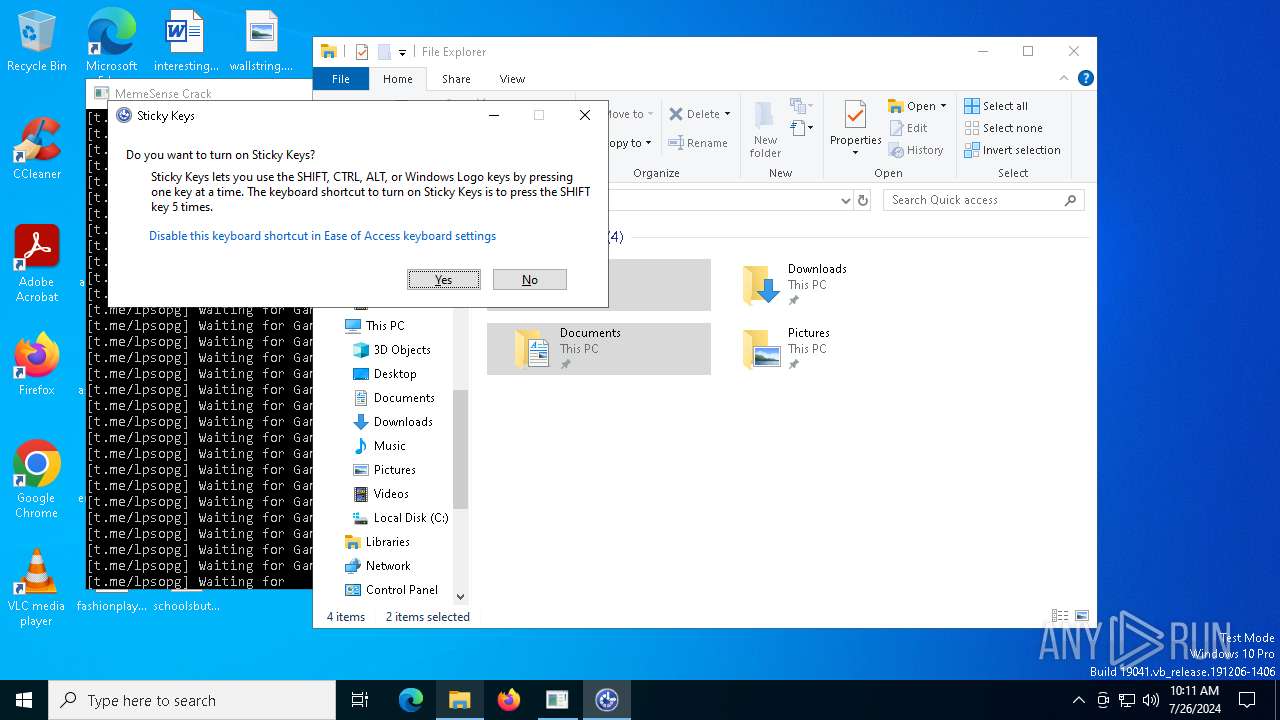
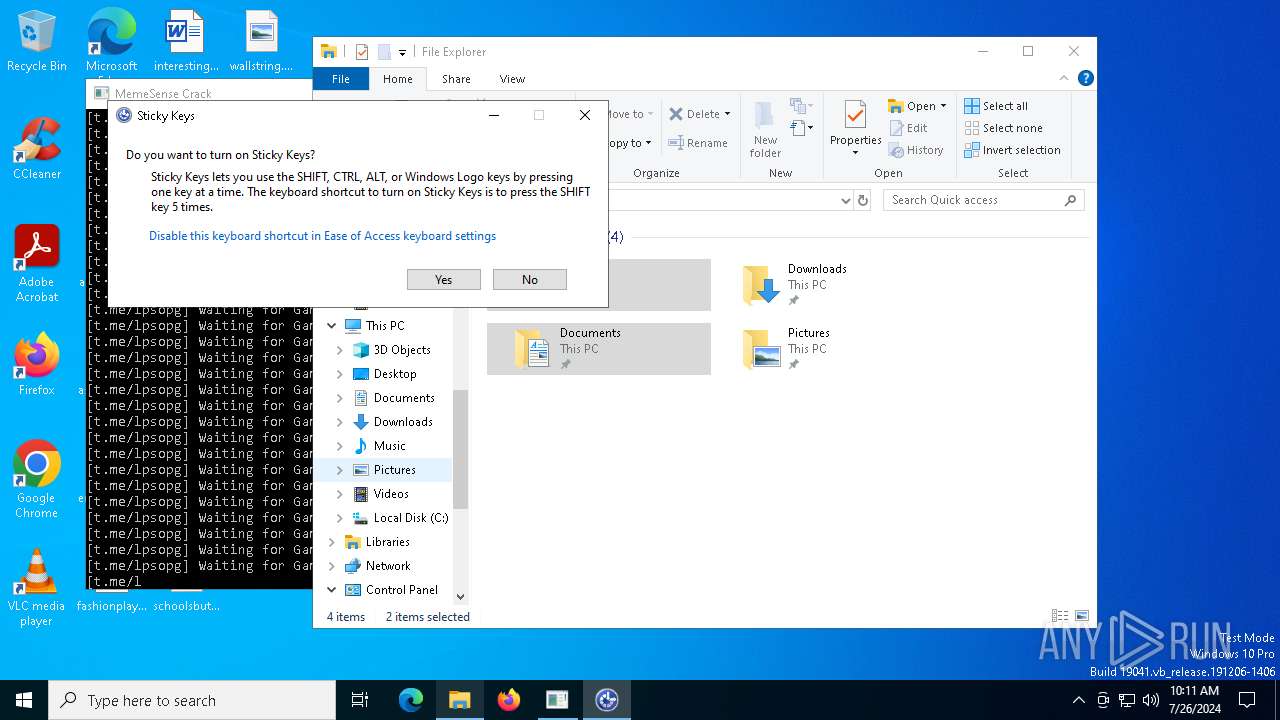
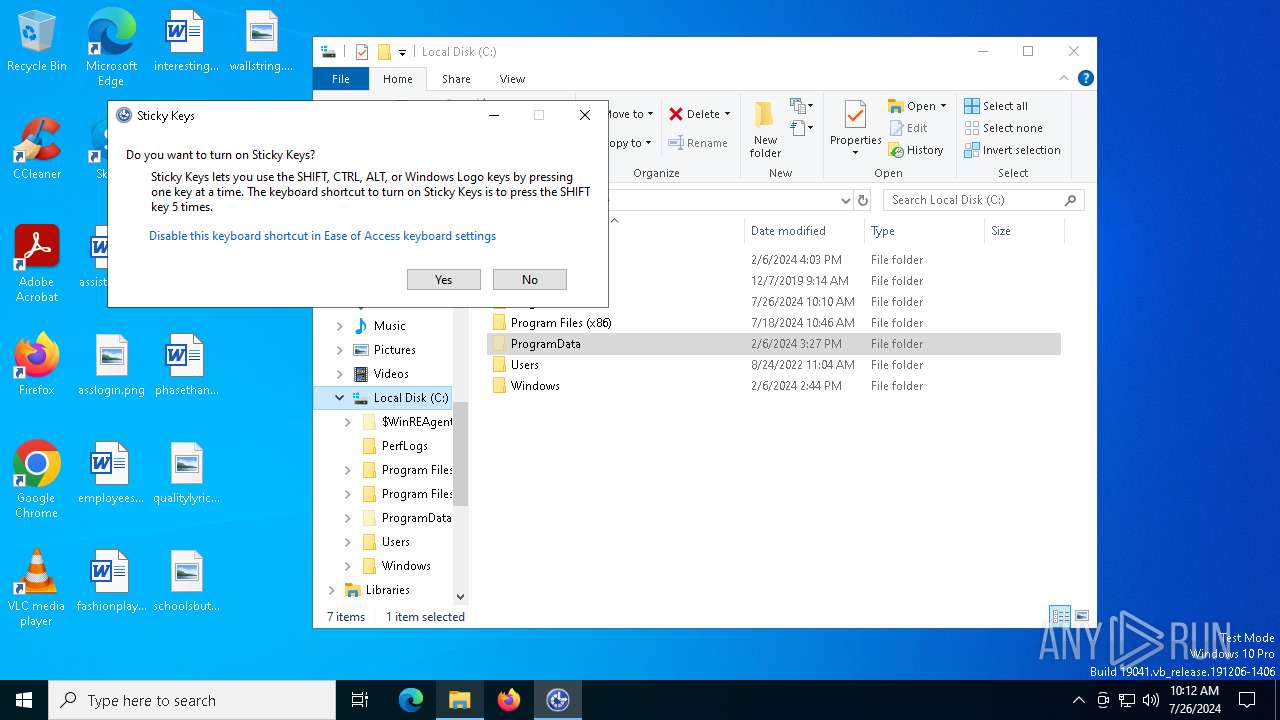
- sethc.exe (PID: 3332)
- sethc.exe (PID: 7728)
- audiodg.exe (PID: 6468)
- consent.exe (PID: 7756)
- sethc.exe (PID: 8084)
- EaseOfAccessDialog.exe (PID: 6512)
- consent.exe (PID: 7988)
- sethc.exe (PID: 5032)
- consent.exe (PID: 7040)
- consent.exe (PID: 6876)
- sethc.exe (PID: 2508)
- EaseOfAccessDialog.exe (PID: 2348)
- sethc.exe (PID: 8164)
- sethc.exe (PID: 7752)
- sethc.exe (PID: 6836)
- sethc.exe (PID: 5744)
- consent.exe (PID: 1176)
- RuntimeBroker.exe (PID: 5776)
- RuntimeBroker.exe (PID: 5592)
- consent.exe (PID: 2100)
- sethc.exe (PID: 5740)
- sethc.exe (PID: 7976)
- consent.exe (PID: 4260)
- EaseOfAccessDialog.exe (PID: 7028)
- sethc.exe (PID: 1772)
- consent.exe (PID: 4340)
- sethc.exe (PID: 8104)
- consent.exe (PID: 6308)
- consent.exe (PID: 8124)
- EaseOfAccessDialog.exe (PID: 6608)
- consent.exe (PID: 2308)
- consent.exe (PID: 5692)
- EaseOfAccessDialog.exe (PID: 6364)
- consent.exe (PID: 4152)
- EaseOfAccessDialog.exe (PID: 7664)
- EaseOfAccessDialog.exe (PID: 6020)
- consent.exe (PID: 1884)
- EaseOfAccessDialog.exe (PID: 2872)
- EaseOfAccessDialog.exe (PID: 5700)
- EaseOfAccessDialog.exe (PID: 7628)
- EaseOfAccessDialog.exe (PID: 7564)
- EaseOfAccessDialog.exe (PID: 4092)
- EaseOfAccessDialog.exe (PID: 3336)
- consent.exe (PID: 7588)
- sethc.exe (PID: 5320)
- EaseOfAccessDialog.exe (PID: 6464)
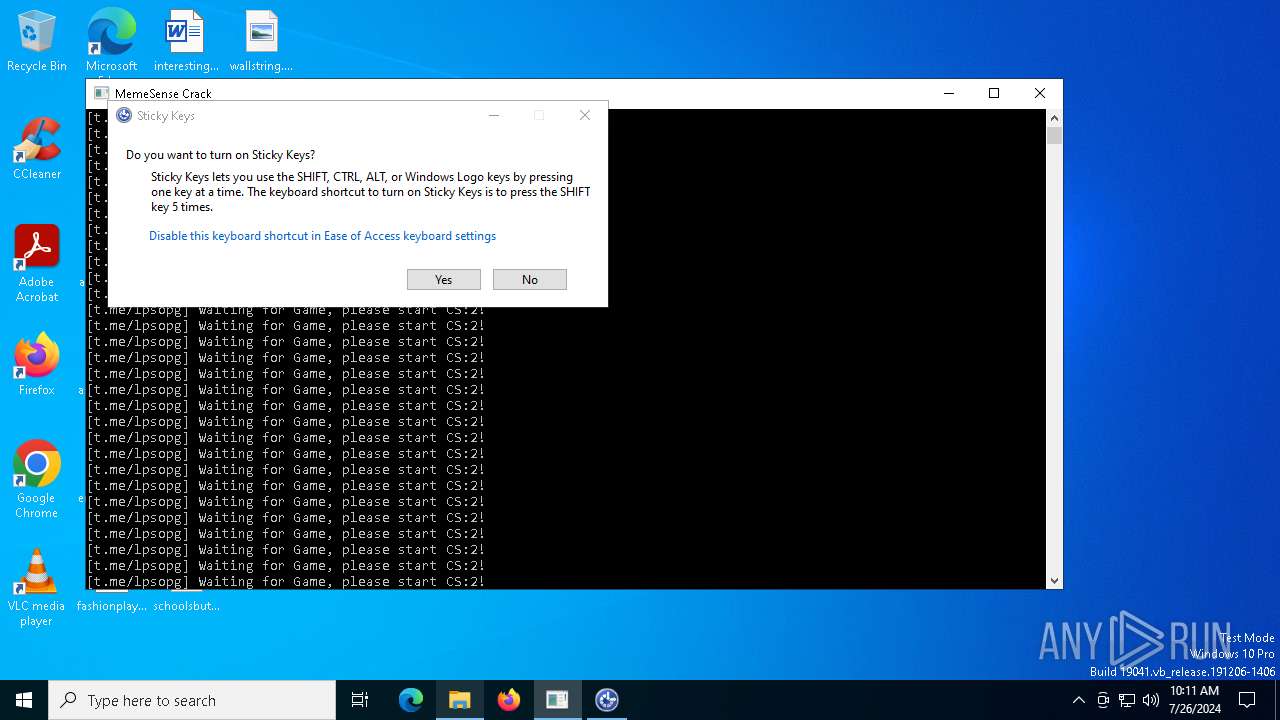
Runs injected code in another process
- dialer.exe (PID: 7116)
- dialer.exe (PID: 7584)
Actions looks like stealing of personal data
- svchost.exe (PID: 1664)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2284)
SUSPICIOUS
Reads security settings of Internet Explorer
- MemeSense Crack.exe (PID: 2932)
- cli_gui.exe (PID: 2132)
Starts POWERSHELL.EXE for commands execution
- explorer.exe (PID: 5016)
Script adds exclusion path to Windows Defender
- explorer.exe (PID: 5016)
Executable content was dropped or overwritten
- MemeSense Crack.exe (PID: 2932)
- updater.exe (PID: 7132)
- updater.exe (PID: 2188)
- explorer.exe (PID: 5016)
Reads the date of Windows installation
- MemeSense Crack.exe (PID: 2932)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 5016)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 4076)
- cmd.exe (PID: 7664)
Starts SC.EXE for service management
- cmd.exe (PID: 3168)
- cmd.exe (PID: 2376)
The process executes via Task Scheduler
- updater.exe (PID: 2188)
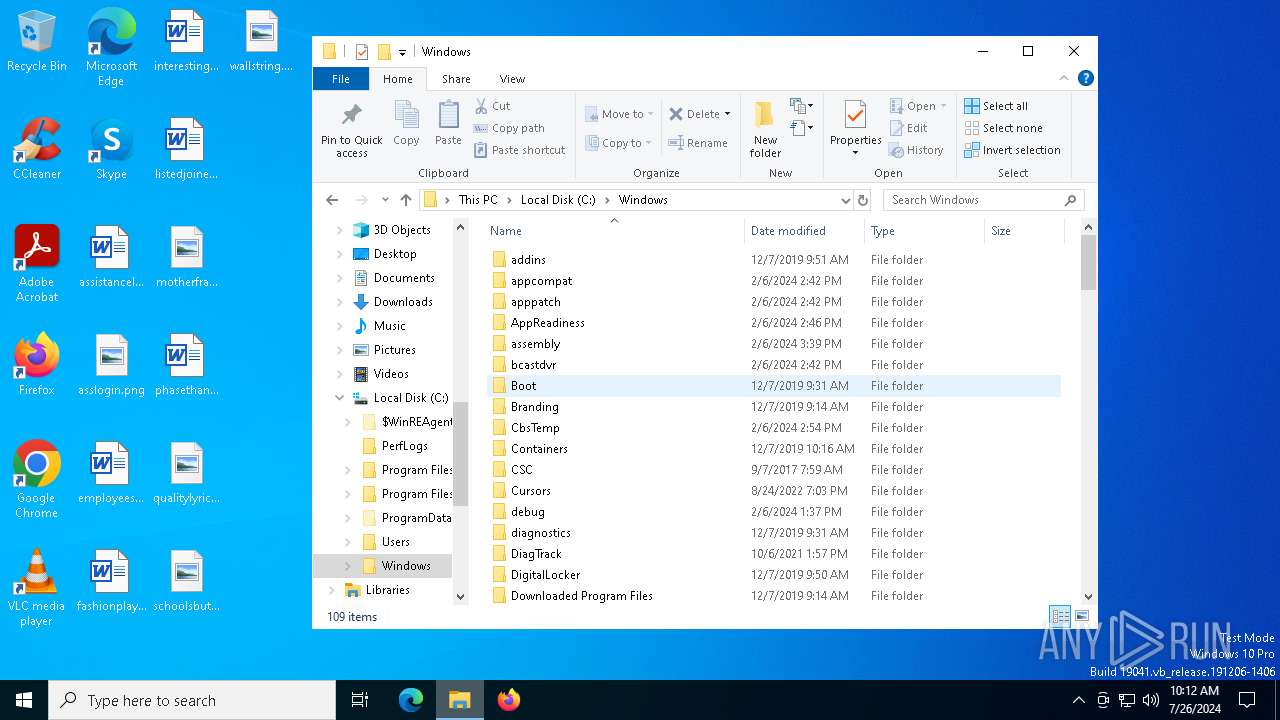
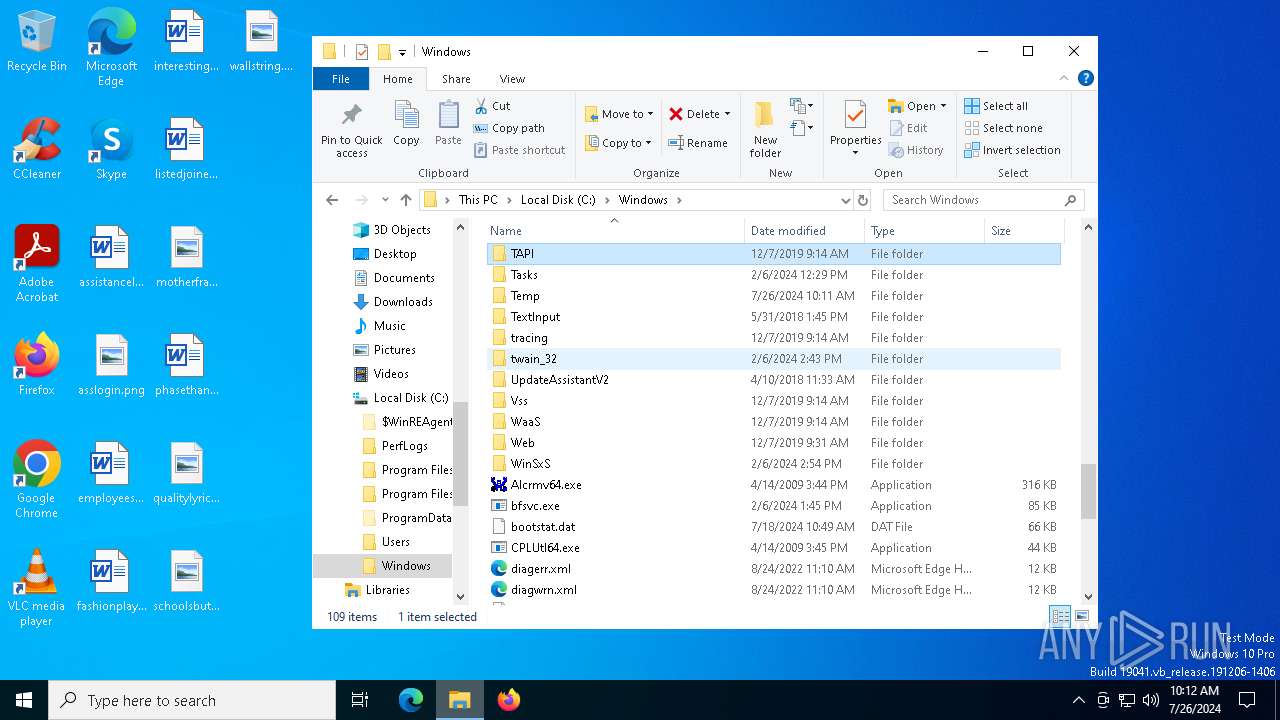
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 2188)
Creates or modifies Windows services
- WaaSMedicAgent.exe (PID: 3336)
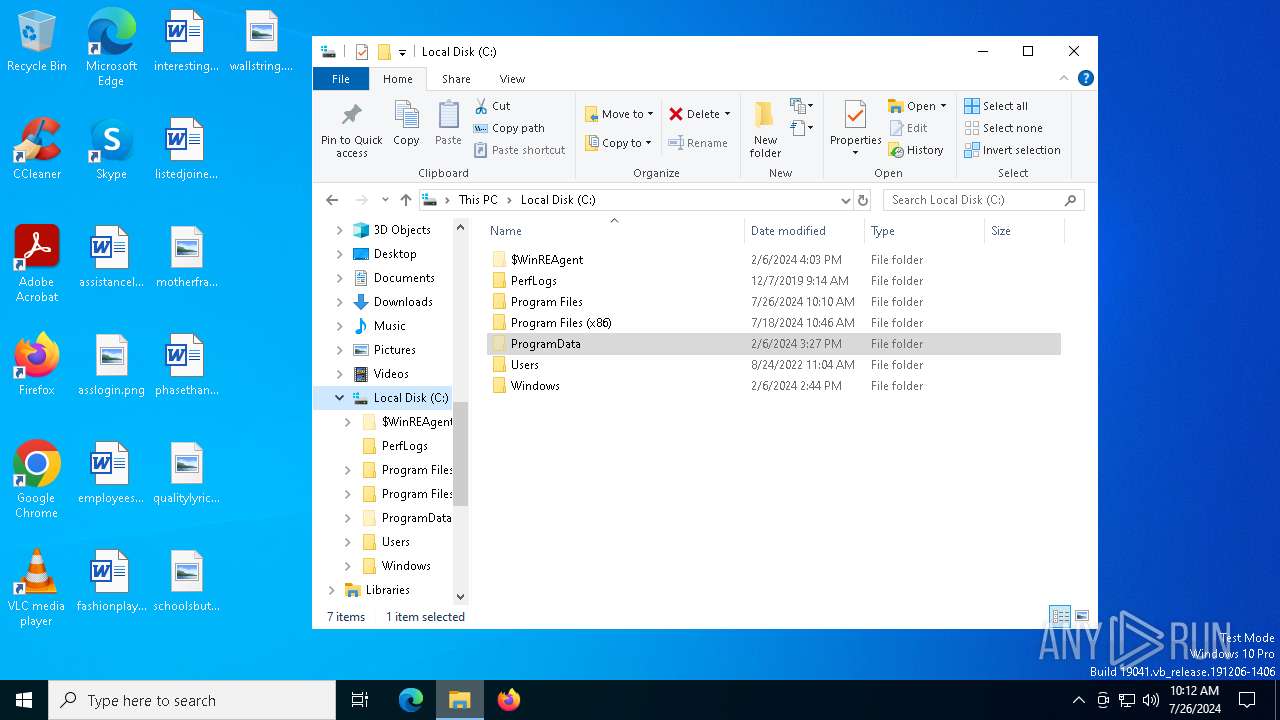
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2284)
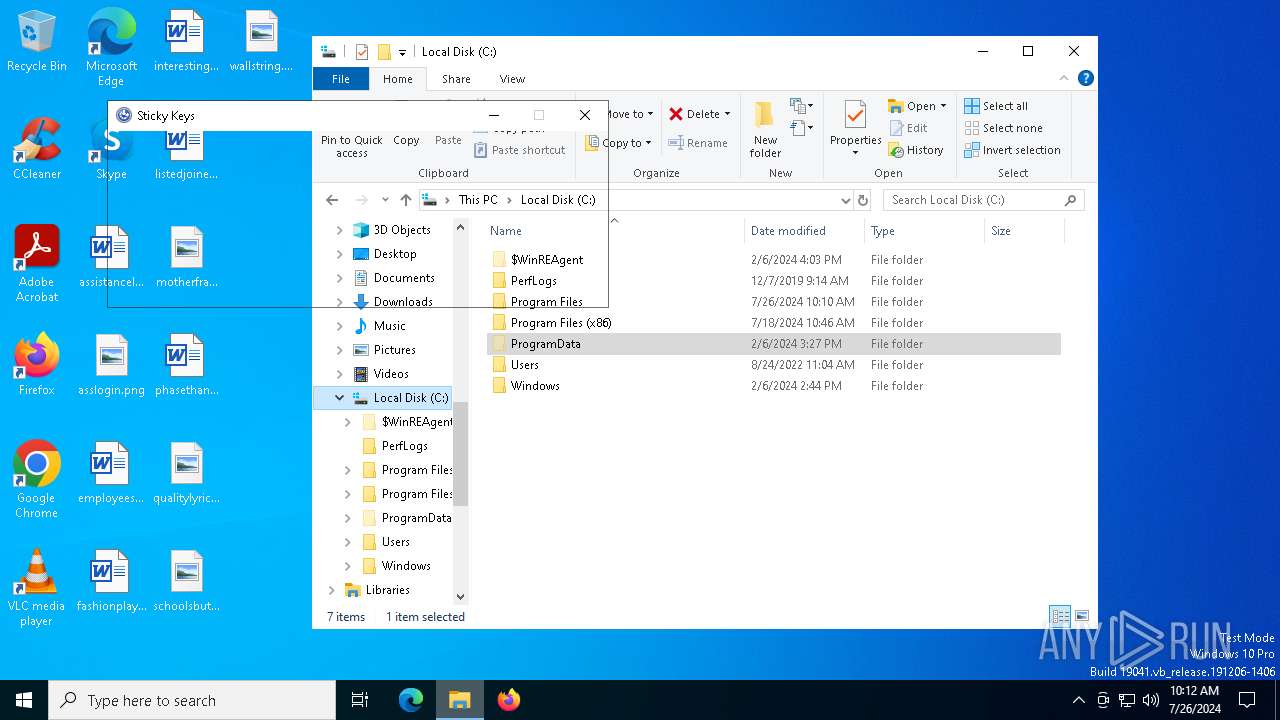
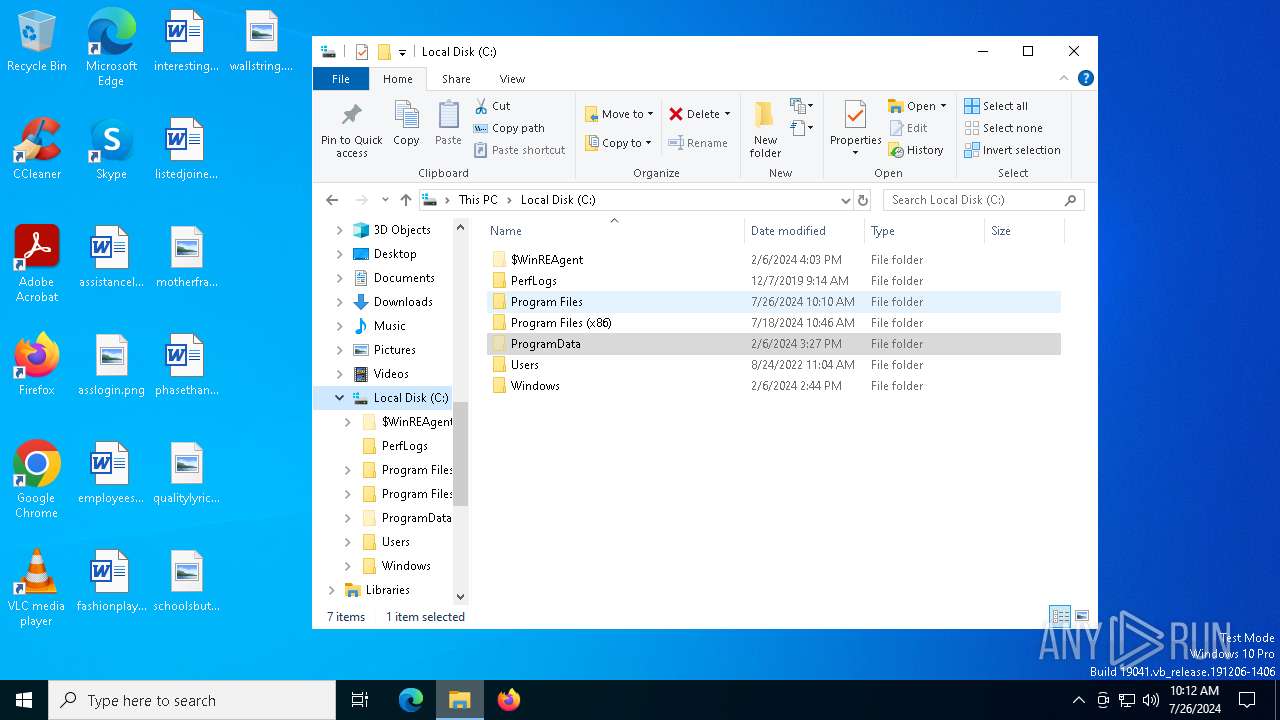
Creates file in the systems drive root
- explorer.exe (PID: 5016)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 5016)
- sethc.exe (PID: 3332)
- sethc.exe (PID: 5320)
- sethc.exe (PID: 7728)
- sethc.exe (PID: 8084)
- sethc.exe (PID: 5032)
- sethc.exe (PID: 7752)
- sethc.exe (PID: 2508)
- sethc.exe (PID: 6836)
- sethc.exe (PID: 8164)
- sethc.exe (PID: 7976)
- sethc.exe (PID: 5744)
- sethc.exe (PID: 5740)
- sethc.exe (PID: 1772)
- sethc.exe (PID: 8104)
Reads the computer name
- MemeSense Crack.exe (PID: 2932)
- cli_gui.exe (PID: 2132)
- PLUGScheduler.exe (PID: 6836)
Checks supported languages
- MemeSense Crack.exe (PID: 2932)
- updater.exe (PID: 7132)
- cli_gui.exe (PID: 2132)
- PLUGScheduler.exe (PID: 6836)
- RUXIMICS.exe (PID: 7640)
- RUXIMICS.exe (PID: 6572)
- updater.exe (PID: 2188)
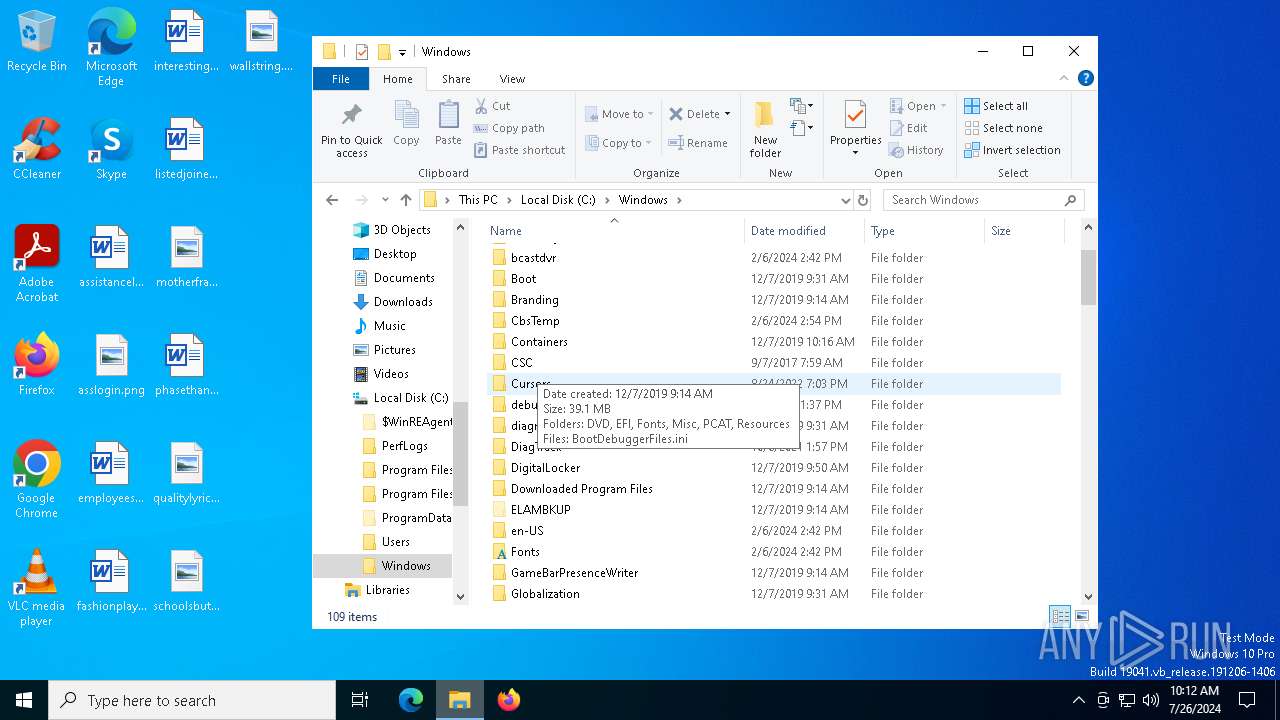
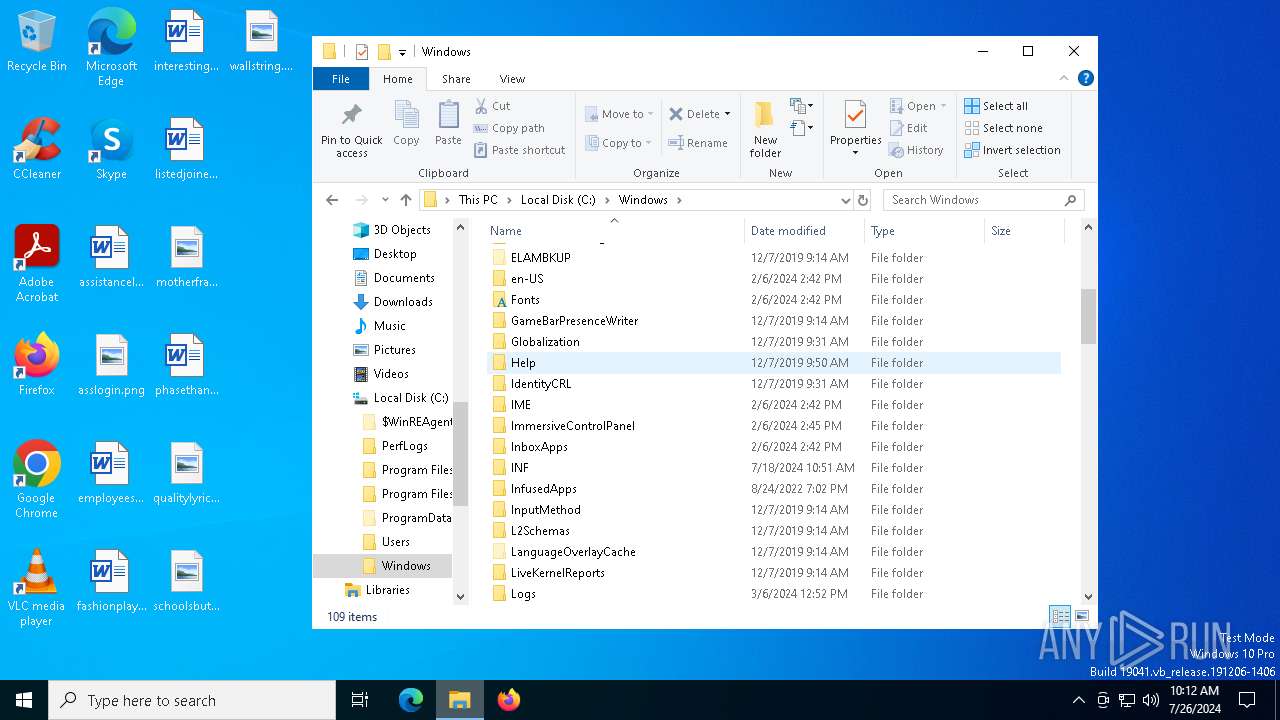
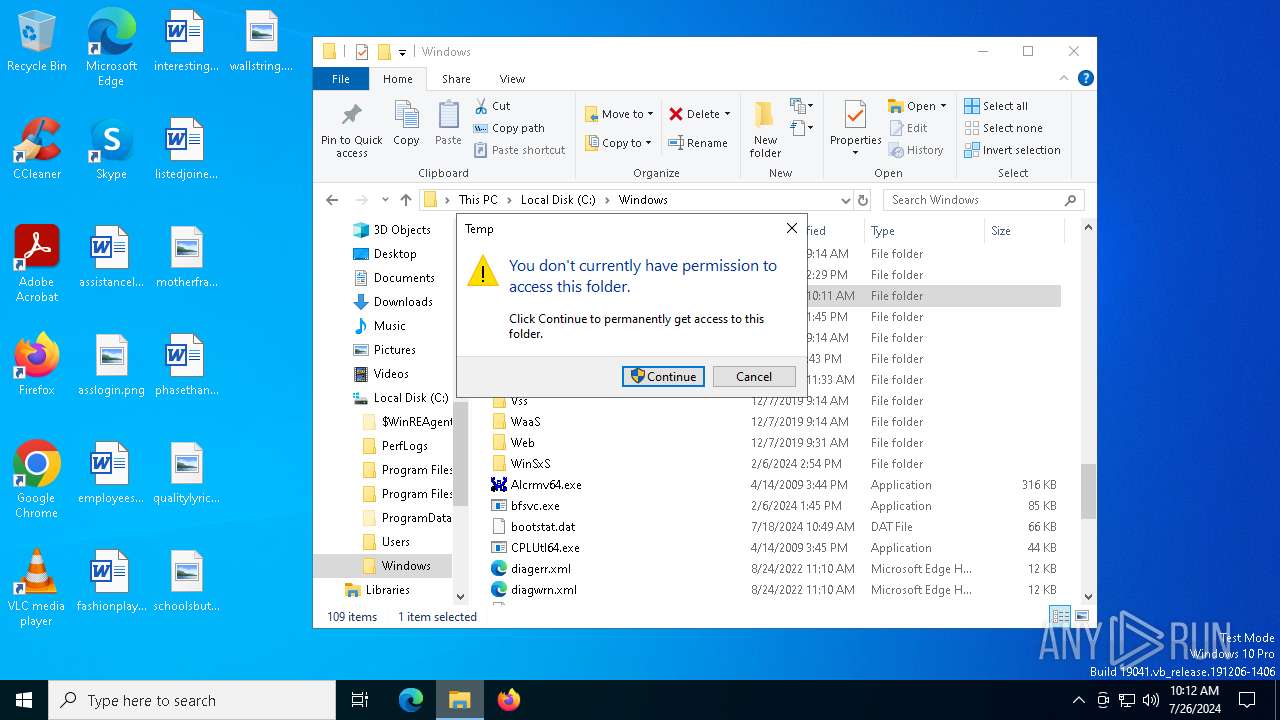
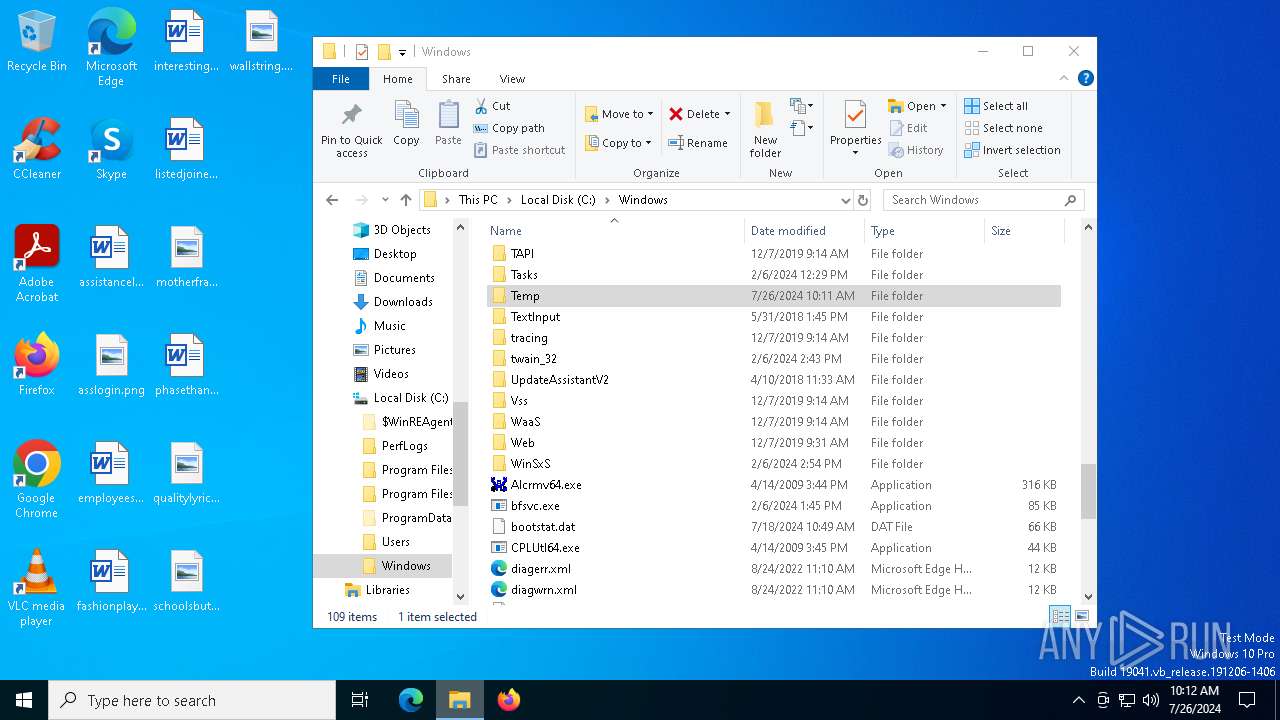
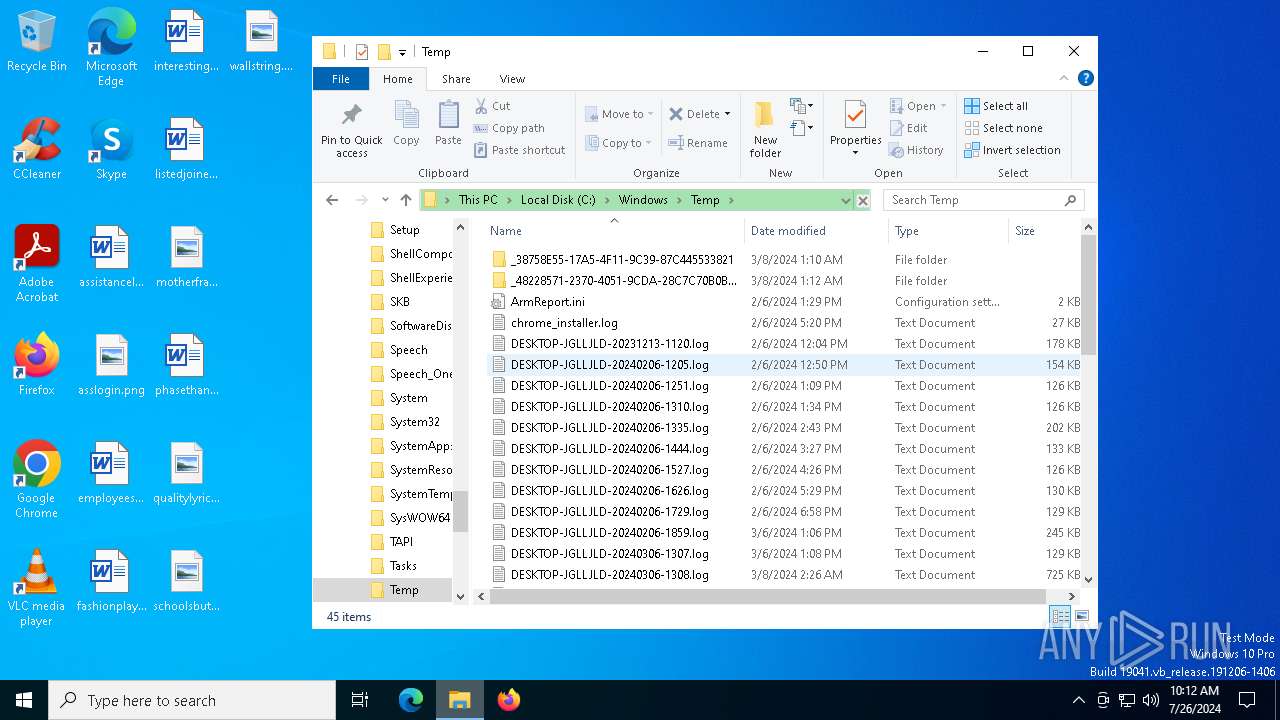
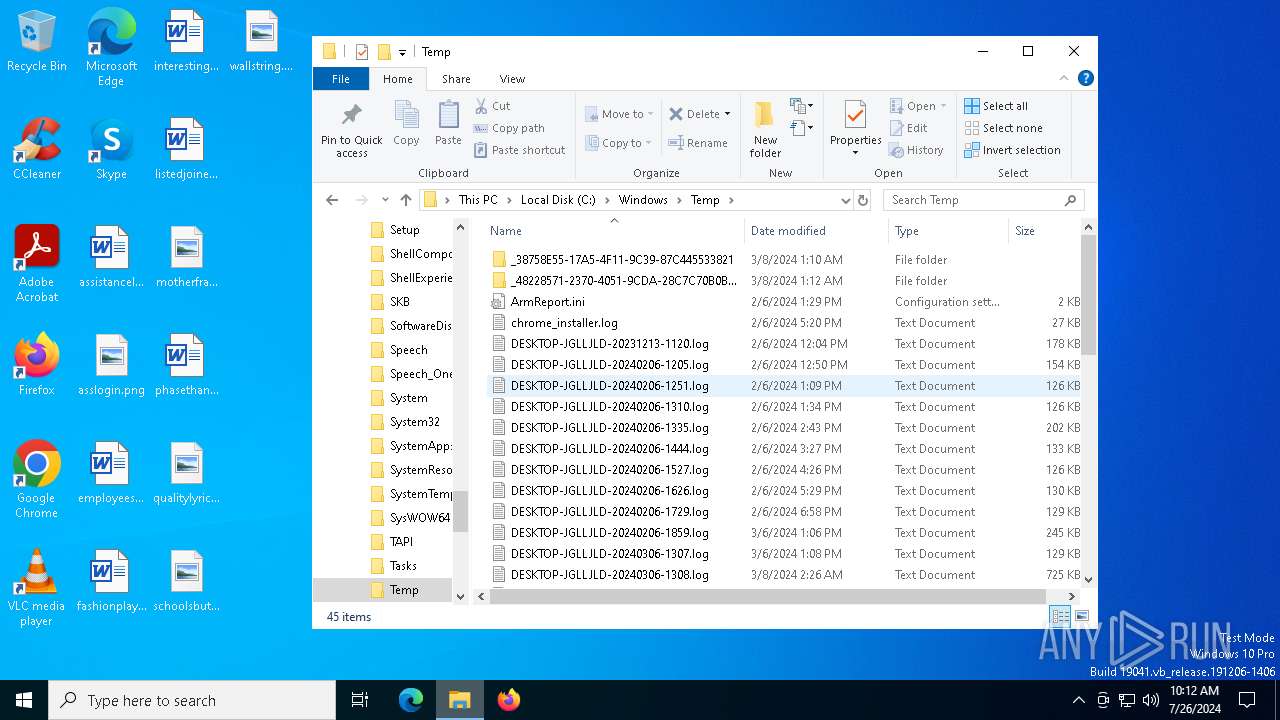
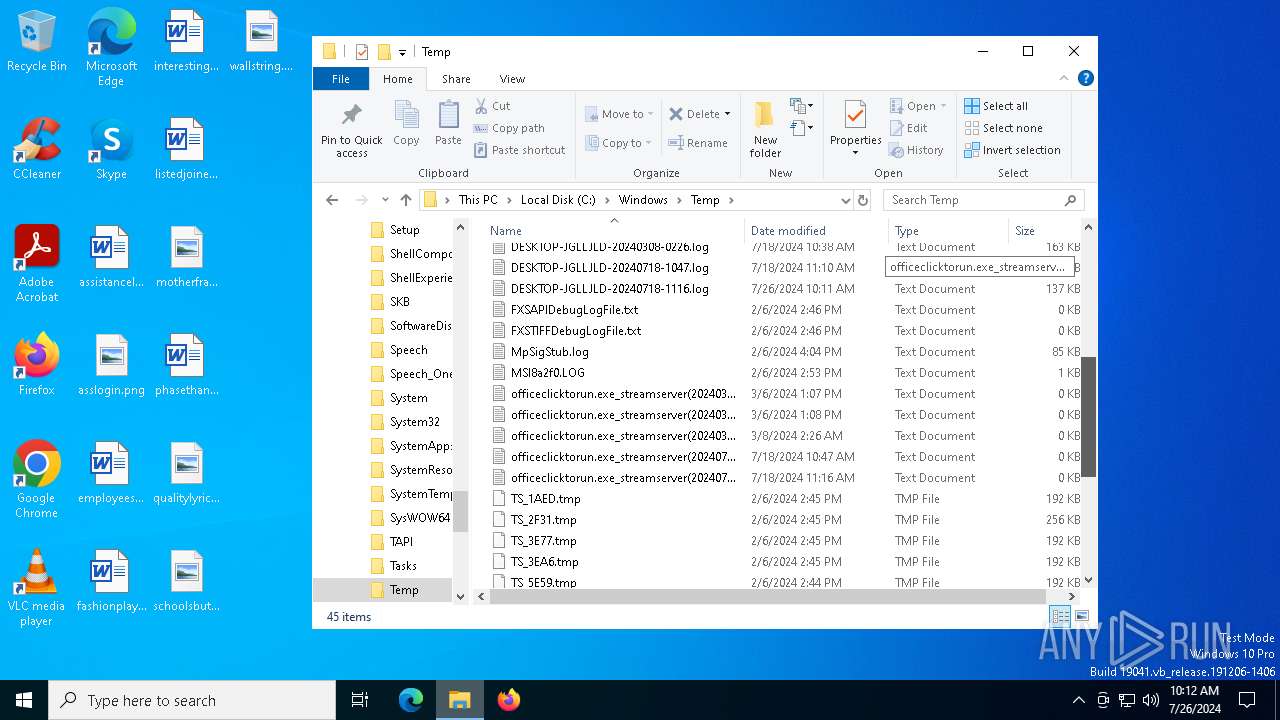
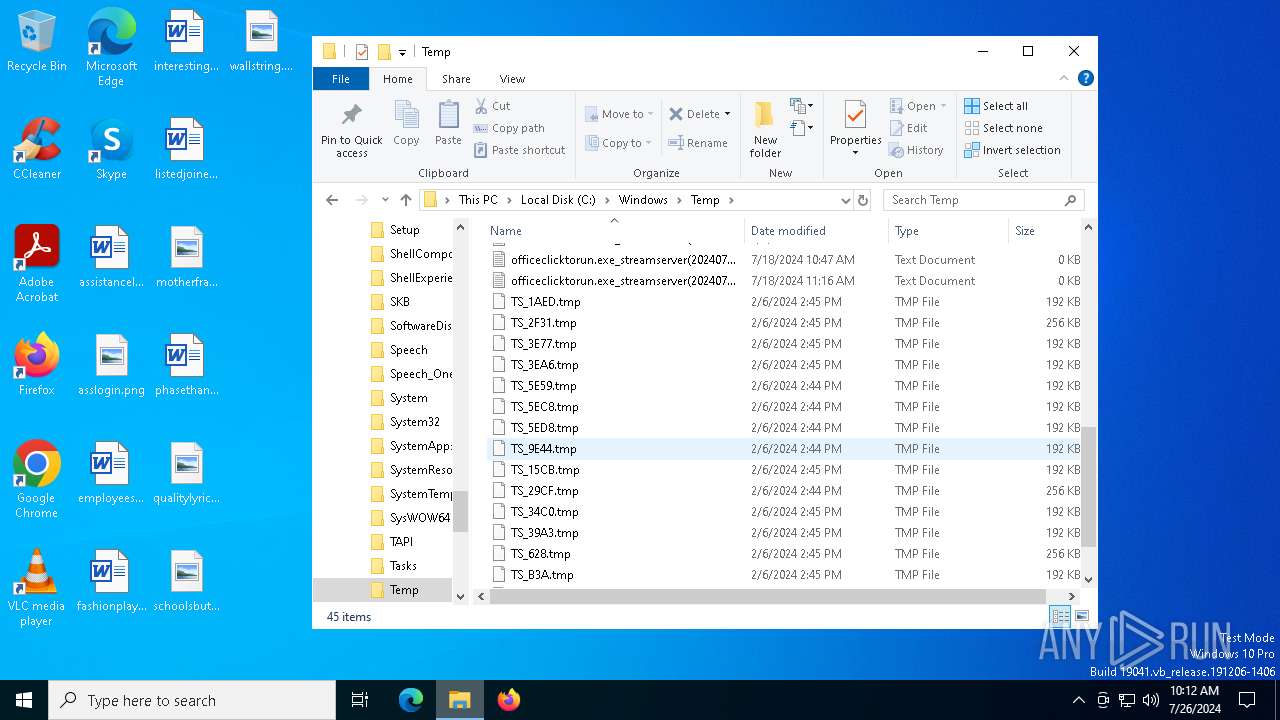
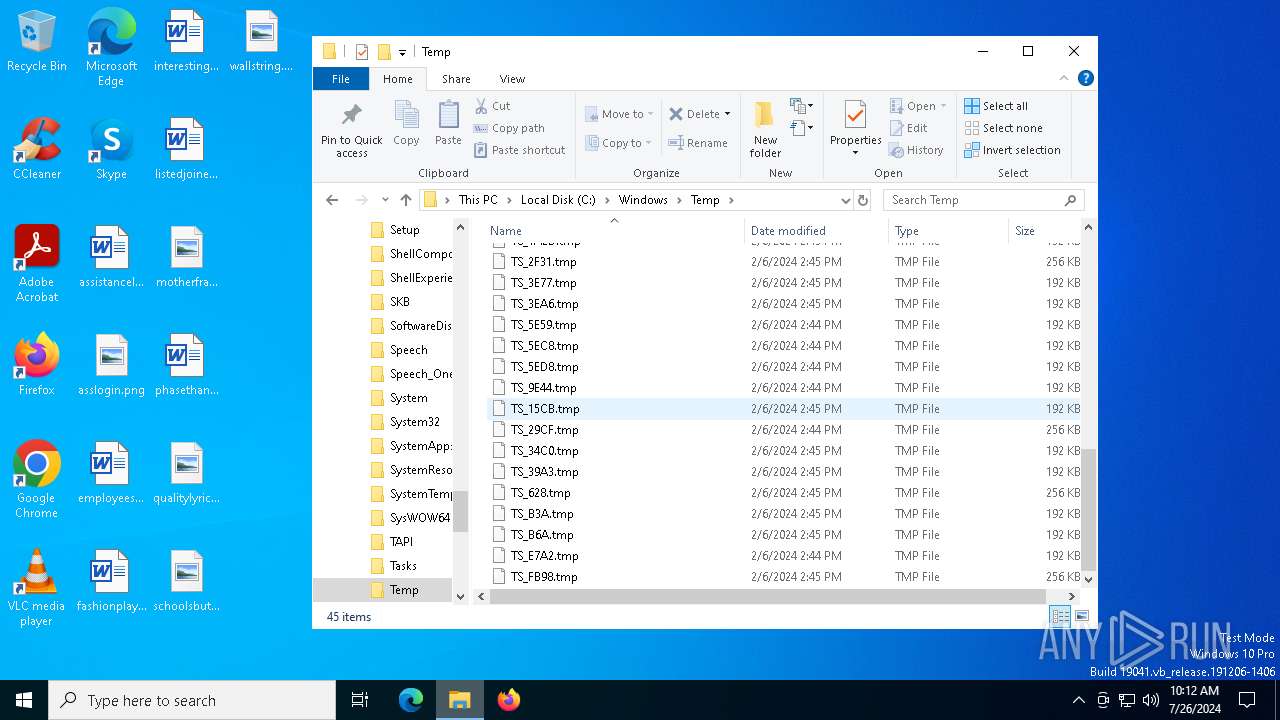
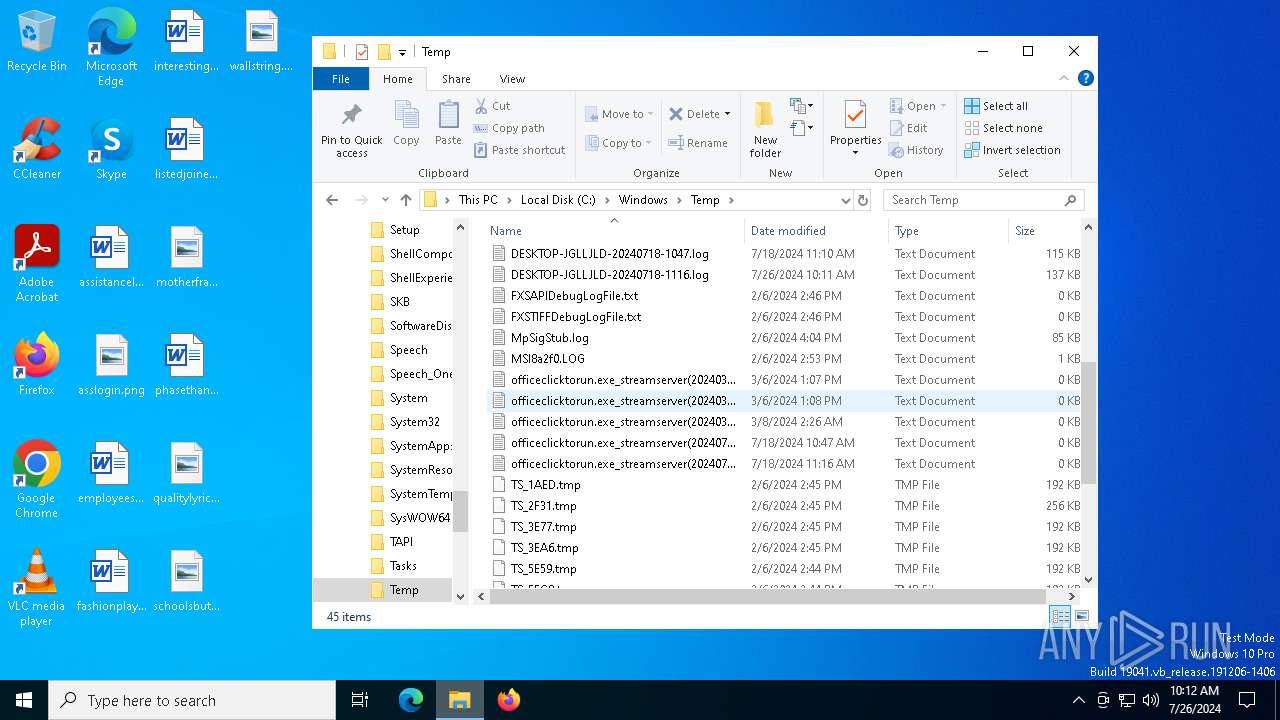
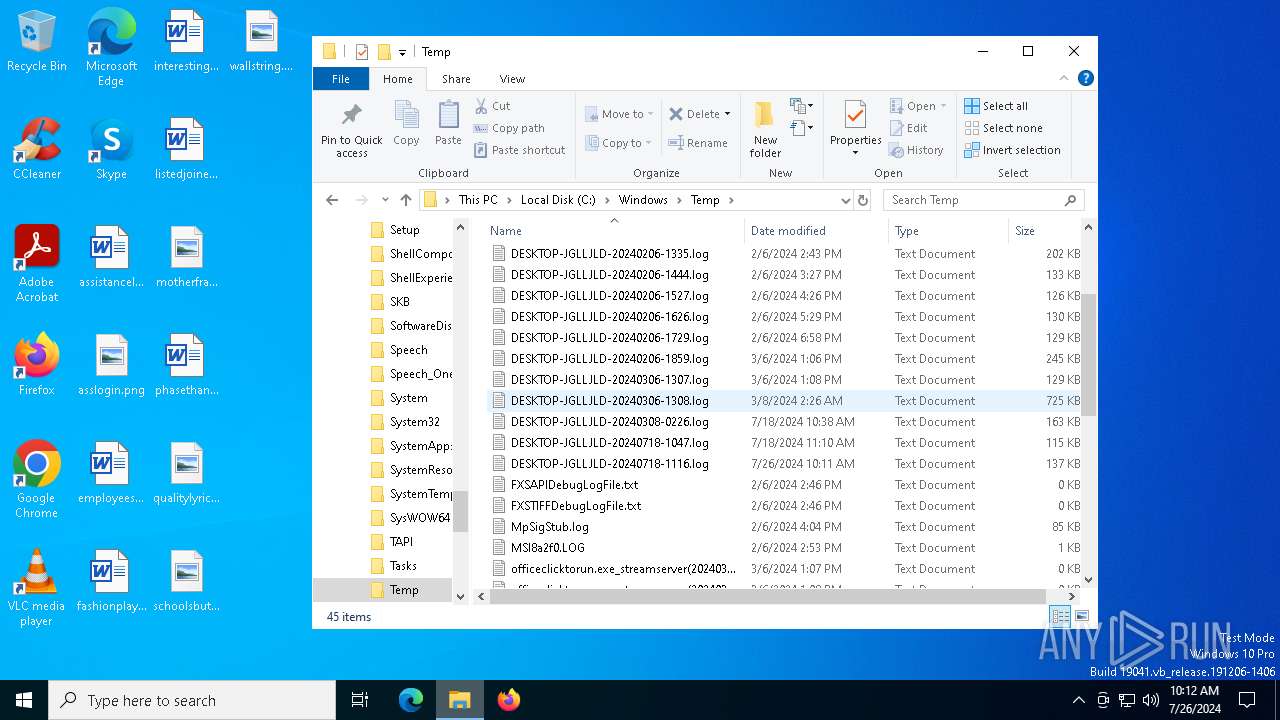
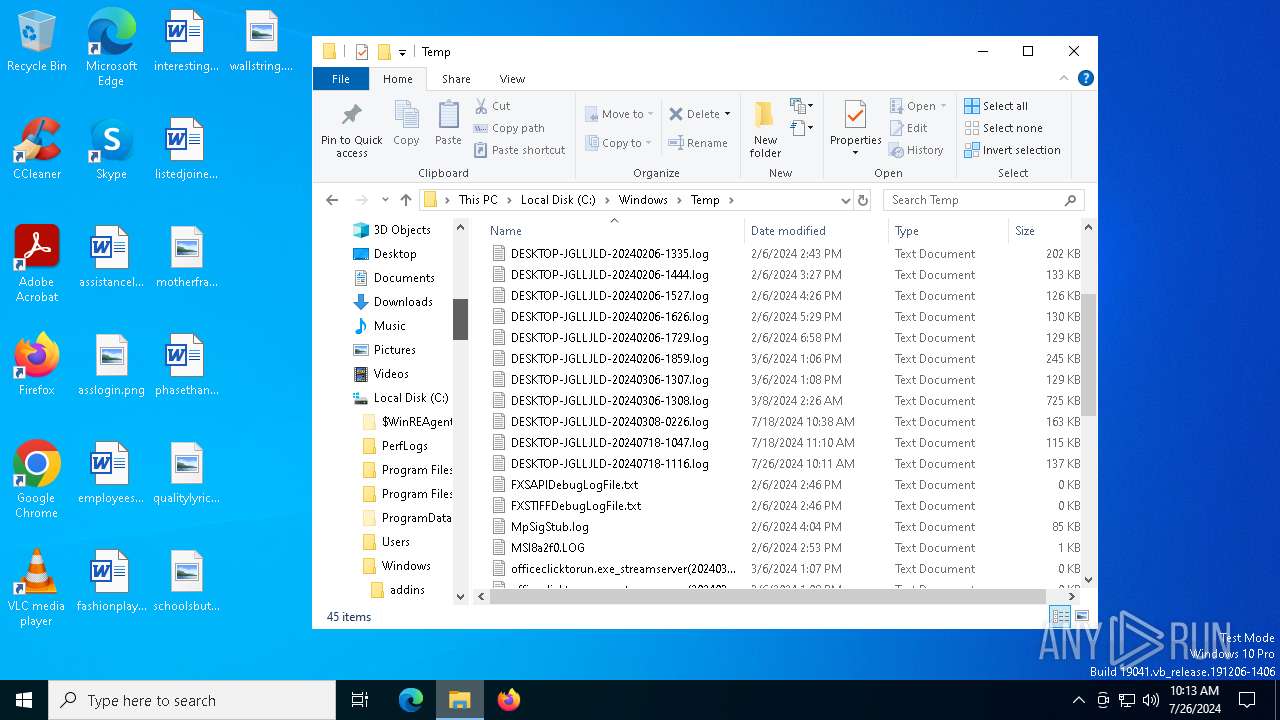
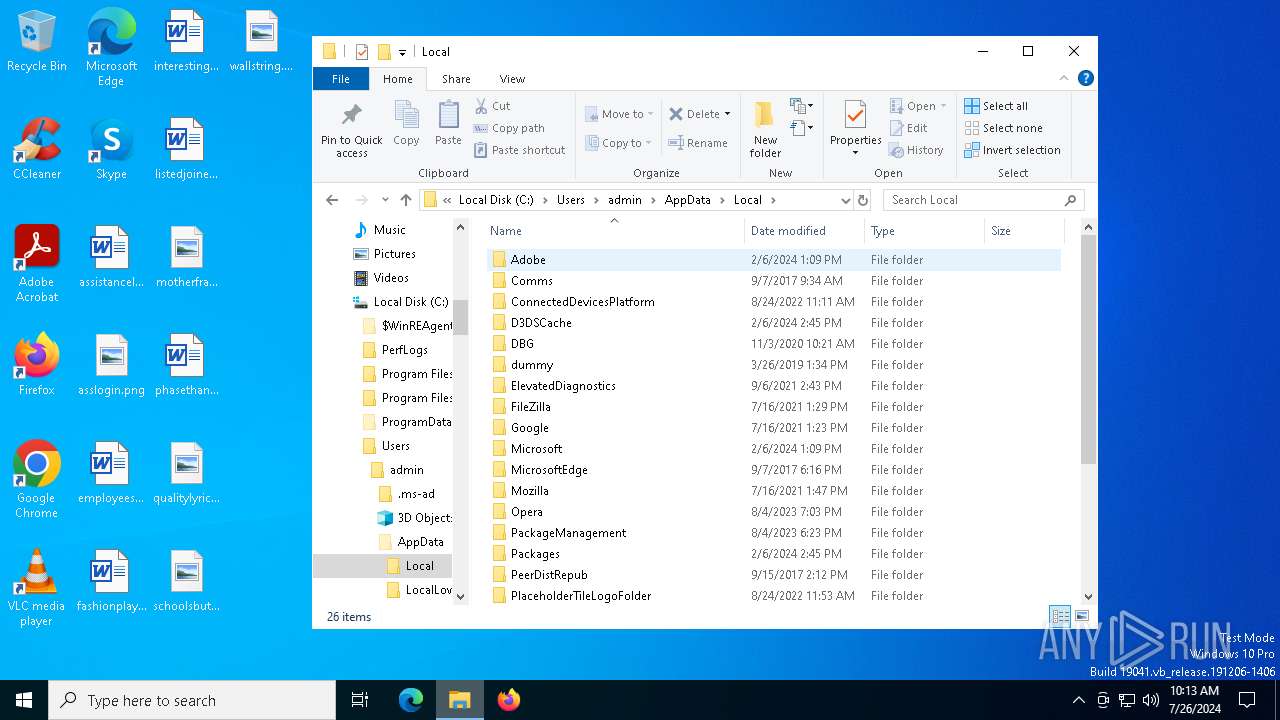
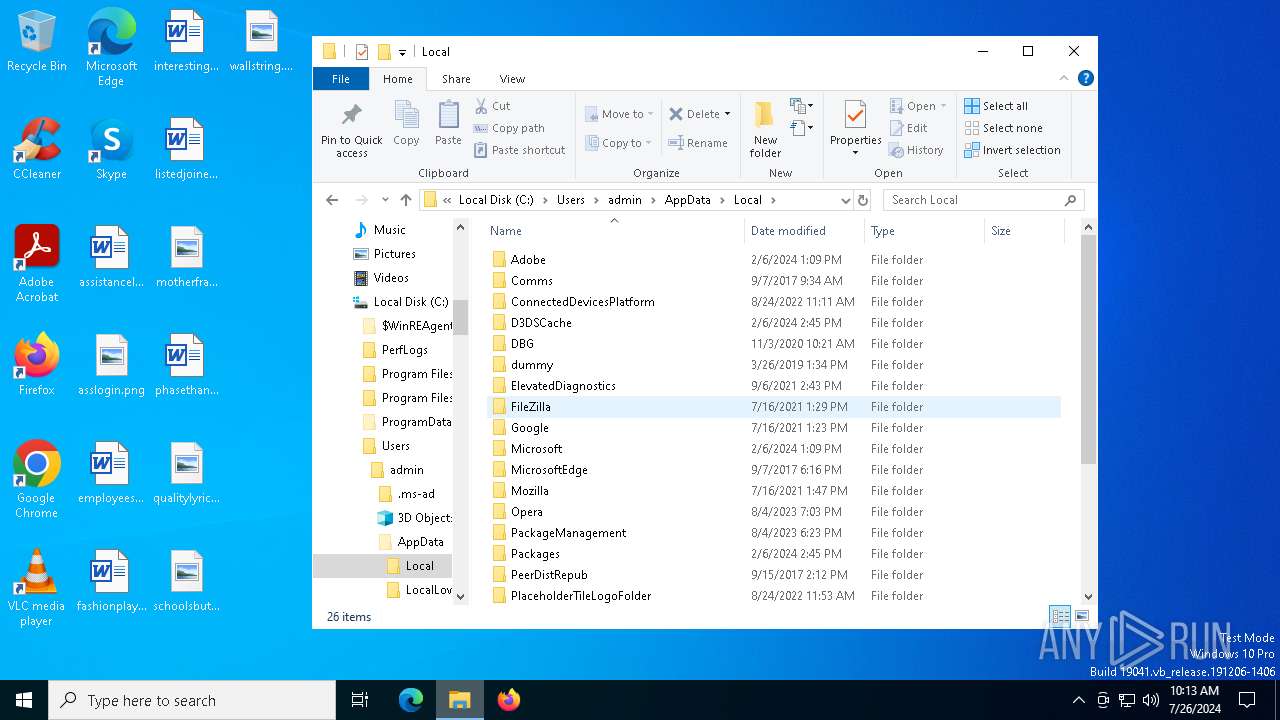
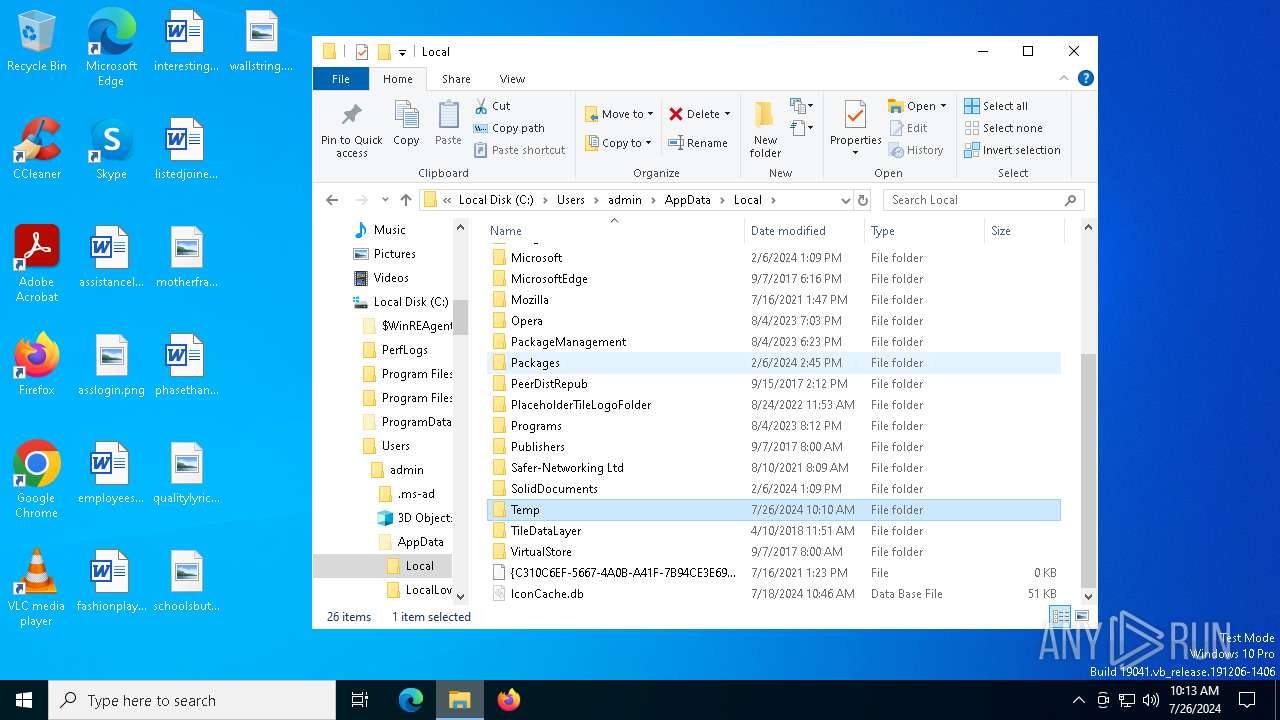
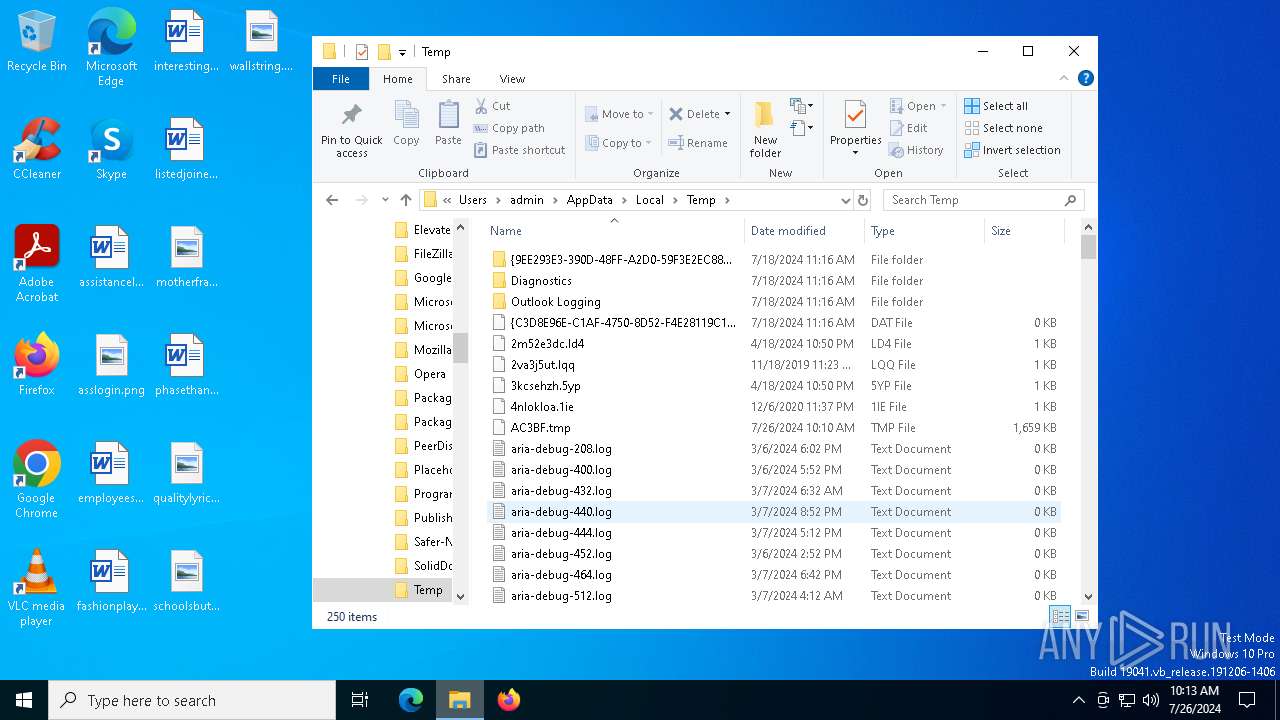
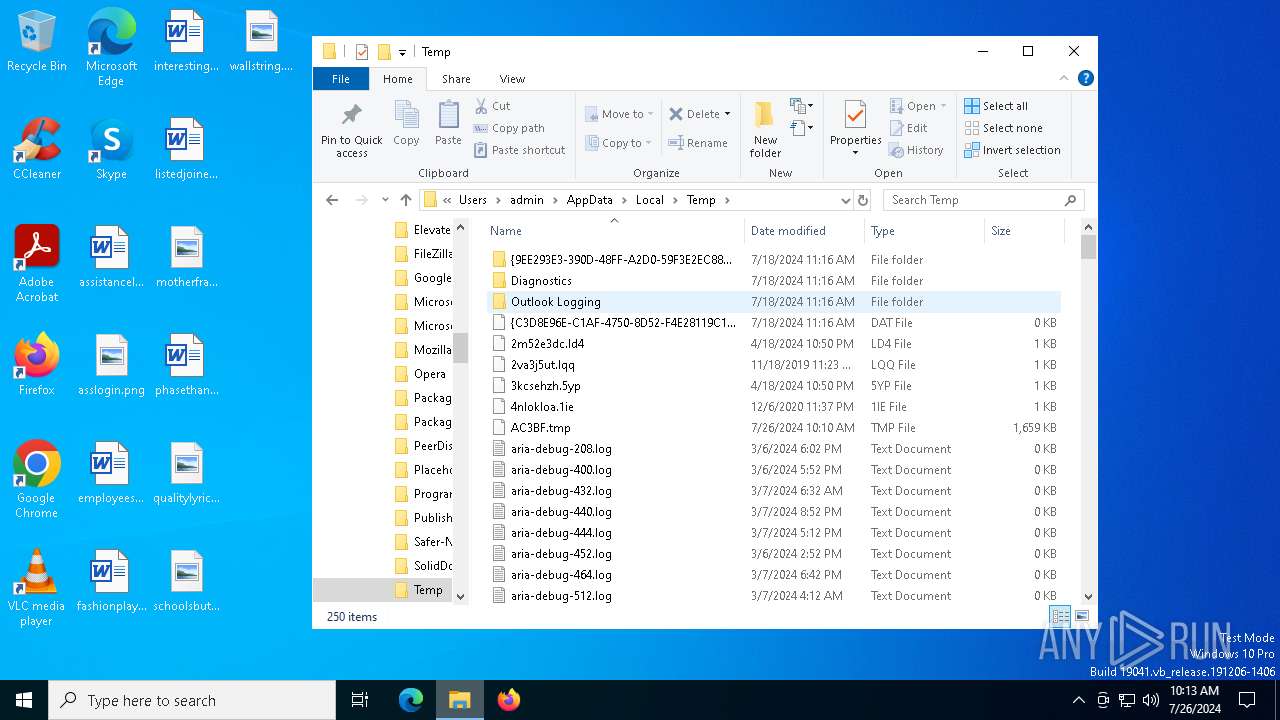
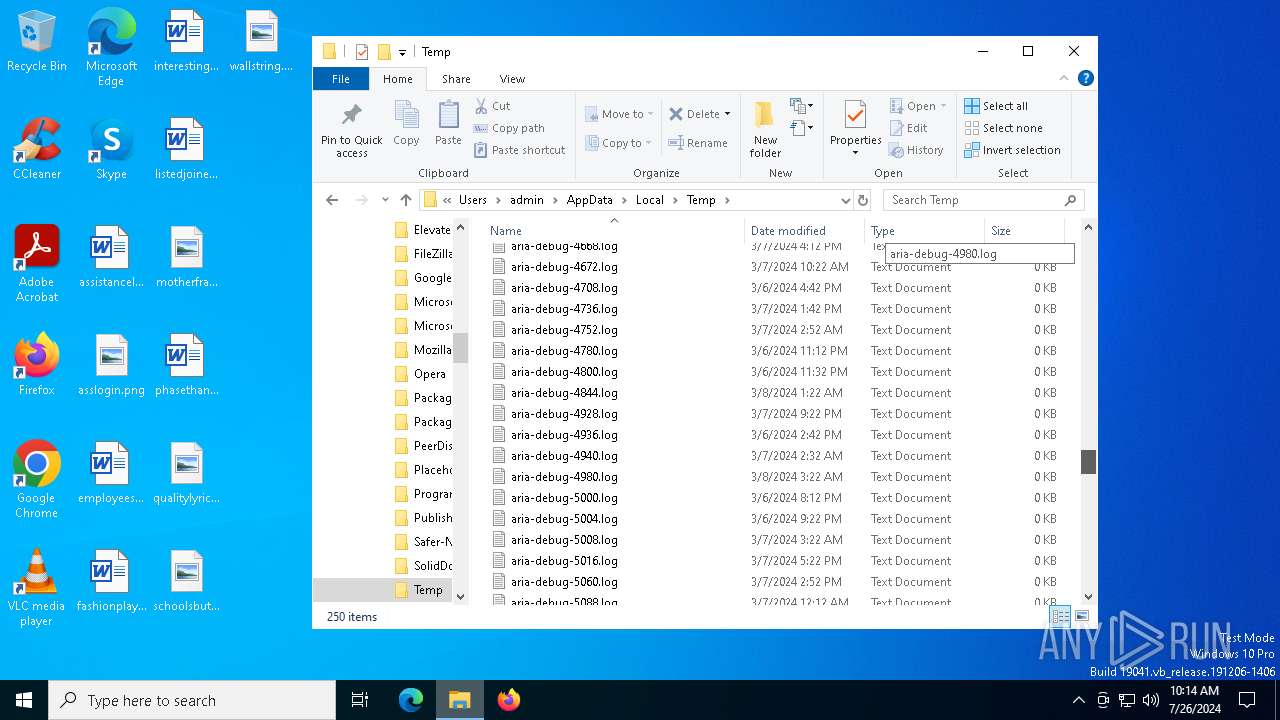
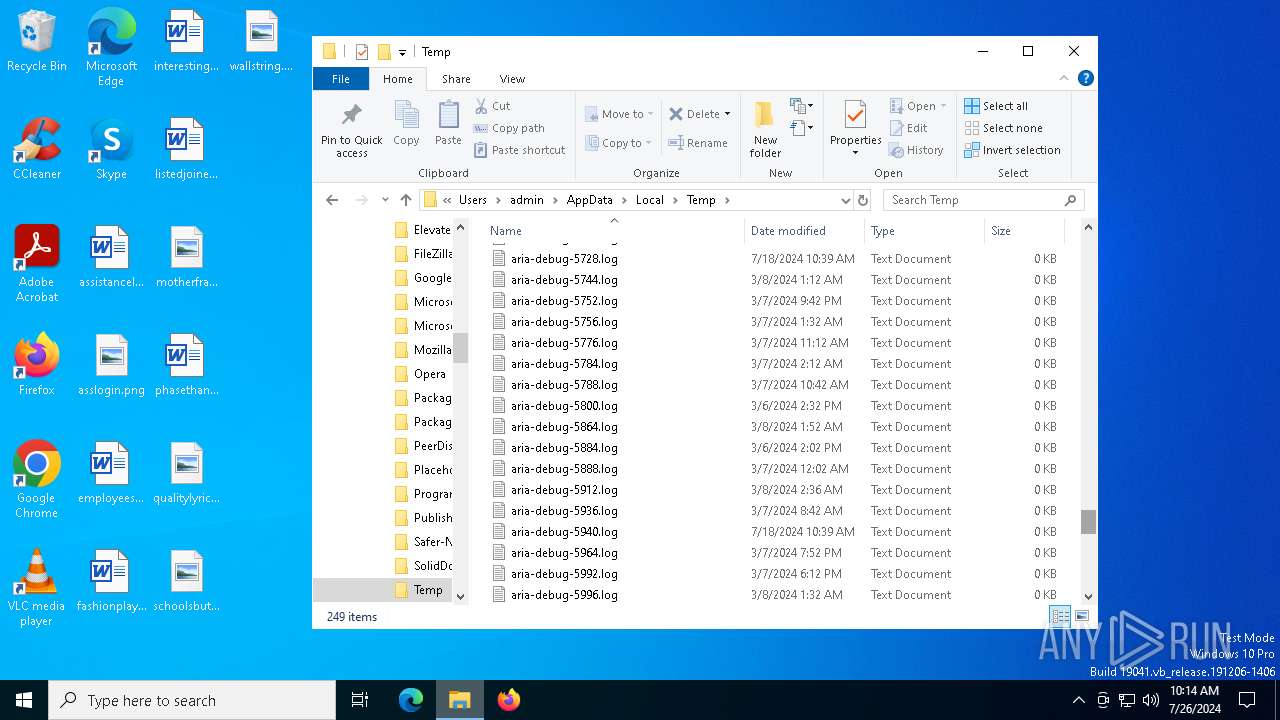
Create files in a temporary directory
- MemeSense Crack.exe (PID: 2932)
- updater.exe (PID: 7132)
Process checks computer location settings
- MemeSense Crack.exe (PID: 2932)
Manual execution by a user
- powershell.exe (PID: 6676)
- cmd.exe (PID: 4076)
- dialer.exe (PID: 7116)
- powershell.exe (PID: 1884)
- cmd.exe (PID: 3168)
- schtasks.exe (PID: 8124)
- powershell.exe (PID: 6076)
- cmd.exe (PID: 2376)
- cmd.exe (PID: 7664)
- powershell.exe (PID: 5392)
- dialer.exe (PID: 7584)
- dialer.exe (PID: 256)
- dialer.exe (PID: 5024)
Checks proxy server information
- cli_gui.exe (PID: 2132)
- slui.exe (PID: 6952)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6676)
- powershell.exe (PID: 6076)
Reads the software policy settings
- lsass.exe (PID: 760)
- WaaSMedicAgent.exe (PID: 3336)
- OfficeClickToRun.exe (PID: 4132)
- consent.exe (PID: 7040)
- consent.exe (PID: 7756)
- consent.exe (PID: 7988)
- consent.exe (PID: 6876)
- consent.exe (PID: 2100)
- consent.exe (PID: 4260)
- consent.exe (PID: 6308)
- consent.exe (PID: 4340)
- consent.exe (PID: 8124)
- consent.exe (PID: 5692)
- consent.exe (PID: 2308)
- consent.exe (PID: 4152)
- consent.exe (PID: 1884)
- slui.exe (PID: 6952)
- consent.exe (PID: 7588)
- consent.exe (PID: 1176)
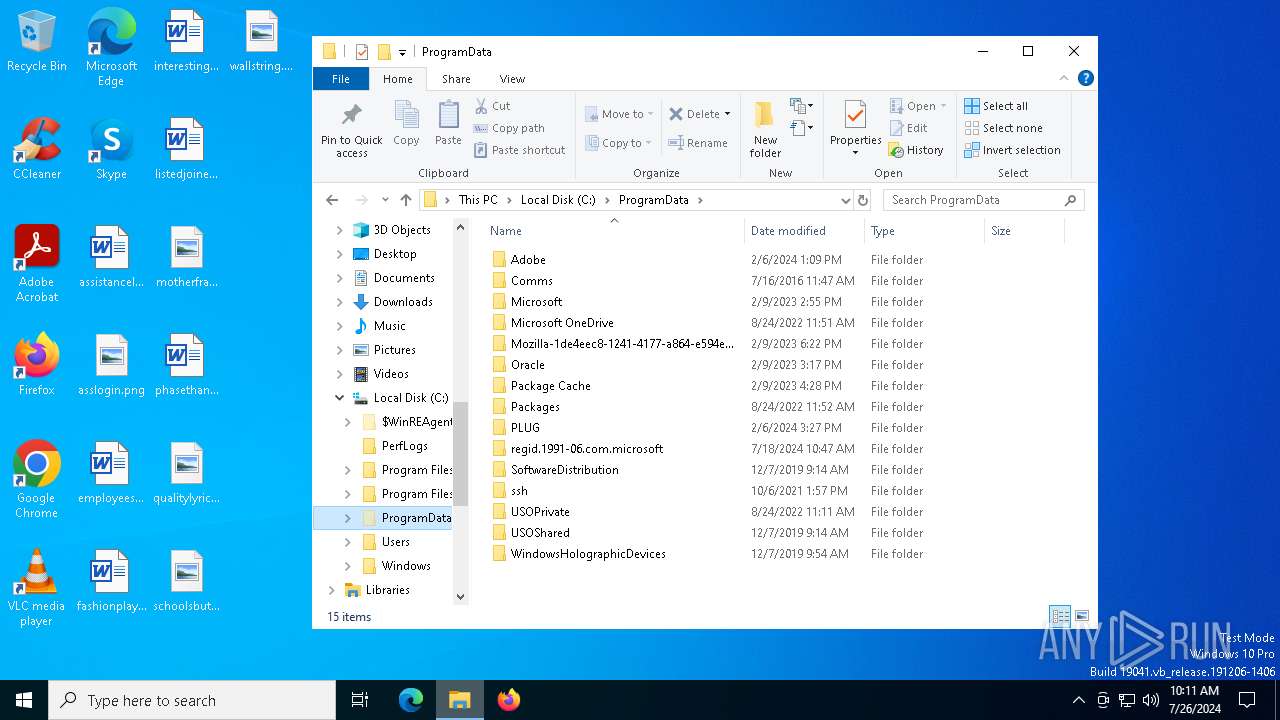
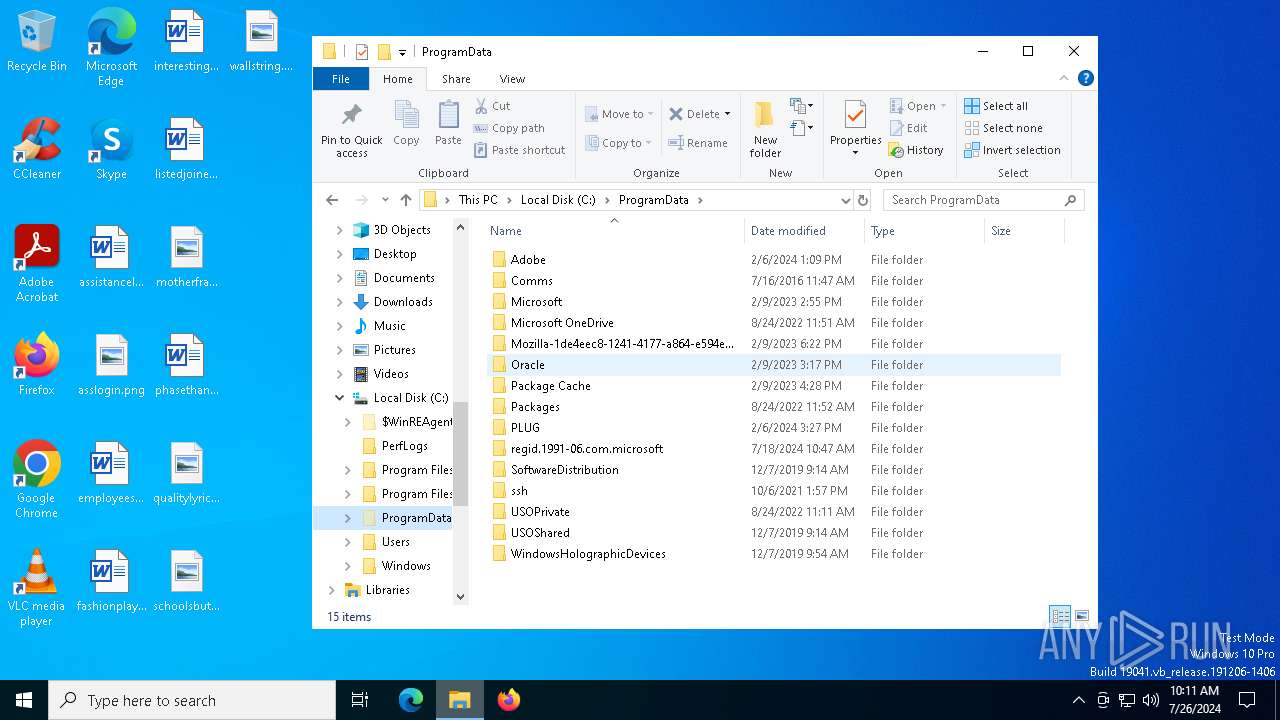
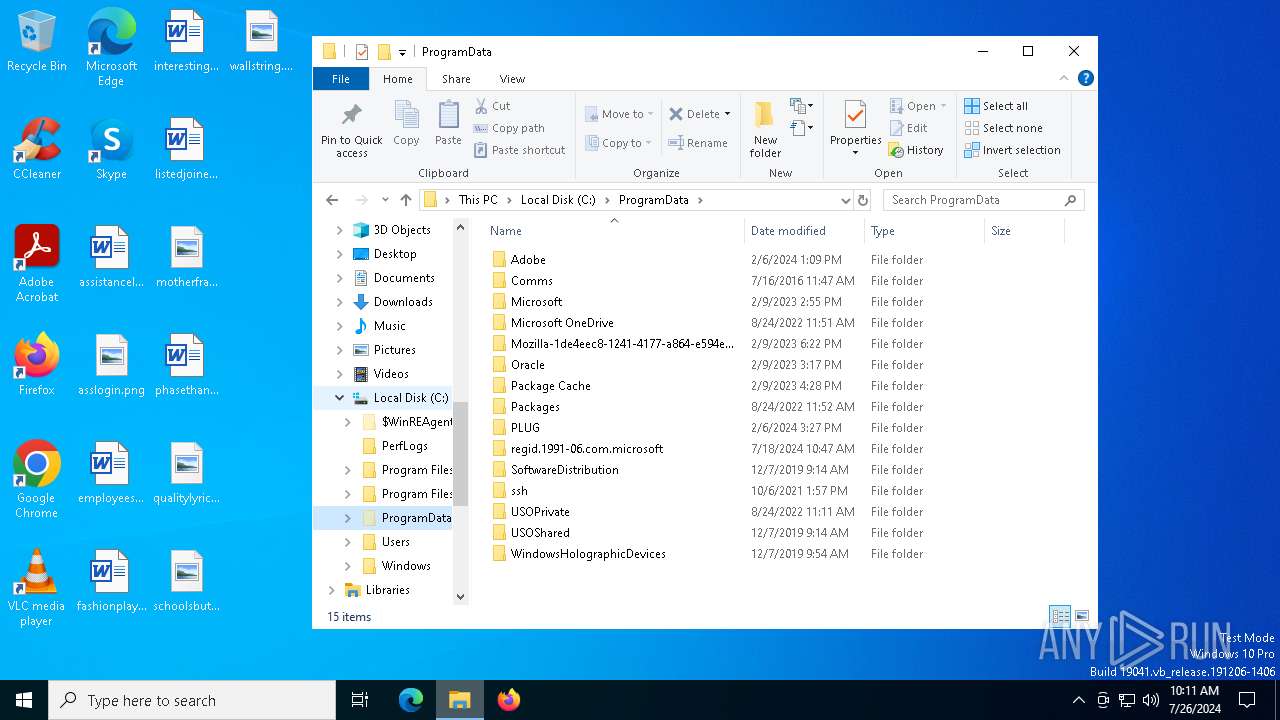
Creates files in the program directory
- RUXIMICS.exe (PID: 7640)
- MoUsoCoreWorker.exe (PID: 6012)
- updater.exe (PID: 7132)
- updater.exe (PID: 2188)
Reads the machine GUID from the registry
- OfficeClickToRun.exe (PID: 4132)
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 4132)
Checks transactions between databases Windows and Oracle
- explorer.exe (PID: 5016)
Drops the executable file immediately after the start
- explorer.exe (PID: 5016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.4) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.8) |
| .exe | | | DOS Executable Generic (18.8) |
| .vxd | | | VXD Driver (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:06:14 07:32:31+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 8482816 |
| InitializedDataSize: | 1536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6100fc |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
244
Monitored processes
189
Malicious processes
133
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | C:\WINDOWS\System32\dialer.exe | C:\Windows\System32\dialer.exe | explorer.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Phone Dialer Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 452 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p -s LSM | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 484 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 488 | powercfg /x -standby-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 588 | "dwm.exe" | C:\Windows\System32\dwm.exe | winlogon.exe | ||||||||||||
User: DWM-1 Company: Microsoft Corporation Integrity Level: SYSTEM Description: Desktop Window Manager Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | winlogon.exe | C:\Windows\System32\winlogon.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Logon Application Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 704 | sc stop dosvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 760 | C:\WINDOWS\system32\lsass.exe | C:\Windows\System32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 824 | C:\WINDOWS\system32\ApplicationFrameHost.exe -Embedding | C:\Windows\System32\ApplicationFrameHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Application Frame Host Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1032 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s gpsvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
211 094
Read events
210 123
Write events
863
Delete events
108
Modification events
| (PID) Process: | (5016) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000002E00720074006600 | |||
| (PID) Process: | (5016) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000001B0180 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456B6826A20153C39478F3B4E3026BED1E8 | |||
| (PID) Process: | (1284) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{C2AF3602-9179-4BAE-85B3-74A4EF5CF51F} |
| Operation: | write | Name: | DynamicInfo |
Value: 03000000BDCB09F80A59DA018C77B60644DFDA01000000000000000060DD360944DFDA01 | |||
| (PID) Process: | (1372) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileService\References\S-1-5-21-1693682860-607145093-2874071422-1001 |
| Operation: | write | Name: | RefCount |
Value: 0A000000 | |||
| (PID) Process: | (1372) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileService\References\S-1-5-21-1693682860-607145093-2874071422-1001 |
| Operation: | write | Name: | RefCount |
Value: 09000000 | |||
| (PID) Process: | (2932) MemeSense Crack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2932) MemeSense Crack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2932) MemeSense Crack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2932) MemeSense Crack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6212) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Compatibility Assistant\Store |
| Operation: | write | Name: | C:\Users\admin\AppData\Local\Temp\MemeSense Crack.exe |
Value: 5341435001000000000000000700000028000000008092008C27820001000000000000000000000A5122000050BB64EDDDACD5010000000000000000 | |||
Executable files
10
Suspicious files
61
Text files
18
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5016 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 1664 | svchost.exe | C:\Windows\Prefetch\SVCHOST.EXE-AD0331FB.pf | binary | |
MD5:8850CD66B53F207D6A2D34478FBA3C2A | SHA256:D423EA24132AE21C0124C5244EA0A22221D4E745126D82E983038853A621760F | |||
| 2932 | MemeSense Crack.exe | C:\Users\admin\AppData\Local\Temp\AC3BF.tmp | executable | |
MD5:C46F14685E2BB0266704B217574FA23F | SHA256:4C22A9CE0EA00DE759BEADFF482088106D06D6C6BF93B833A743E999E775D636 | |||
| 1664 | svchost.exe | C:\Windows\Prefetch\CLI_GUI.EXE-80C70FDA.pf | binary | |
MD5:2259D12FF74AE2E081B1FD28E80D8FB0 | SHA256:04719FB61A70D63DF5B93C8763D24BCFF15569D54343AC84F3438858D448ACBE | |||
| 2932 | MemeSense Crack.exe | C:\Users\admin\AppData\Local\Temp\cli_gui.exe | executable | |
MD5:82EE19ED134912BE0FE2000CAF6421C5 | SHA256:B225ED38C3C08087B806AAD5609A4F1DDE1DD7CB3C3E99C235E72DC150159AAC | |||
| 6676 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:8F5CEA3A3C85C7A3B958EA6975C84ABF | SHA256:793ABCF7C92EE5036FA6ECE04B5052FE343D4863AA1E207EA9E0A3C30FBB7BFC | |||
| 1664 | svchost.exe | C:\Windows\Prefetch\SC.EXE-945D79AE.pf | binary | |
MD5:B00F1C26D63FD18E5E05C5284DC5657F | SHA256:96F7F1B79F6C6A877B076759CCAB5DE7881535FE4A2BA222E2F061E06147B2FC | |||
| 1884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_afqzcbdu.zft.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4216 | dllhost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AppData\Indexed DB\edb.chk | binary | |
MD5:E1434DC4596936E37A0D360F210FC233 | SHA256:CC8EEC8B9CB689A8BD6E7AB450CA6301678F88503CCDCF720CC3AC4A8068E93B | |||
| 1664 | svchost.exe | C:\Windows\Prefetch\POWERCFG.EXE-668FA411.pf | binary | |
MD5:26F334CAAA64470719CDCC90DE1F9771 | SHA256:2BD804FAE3F852D71CC7F419AF7C8BA25D62178D9FFDE70942B901CBC5BEA5BA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
44
DNS requests
31
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
7720 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
996 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5368 | SearchApp.exe | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5368 | SearchApp.exe | 92.123.104.33:443 | www.bing.com | Akamai International B.V. | DE | unknown |
1156 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6572 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1328 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
a-ring-fallback.msedge.net |
| unknown |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |