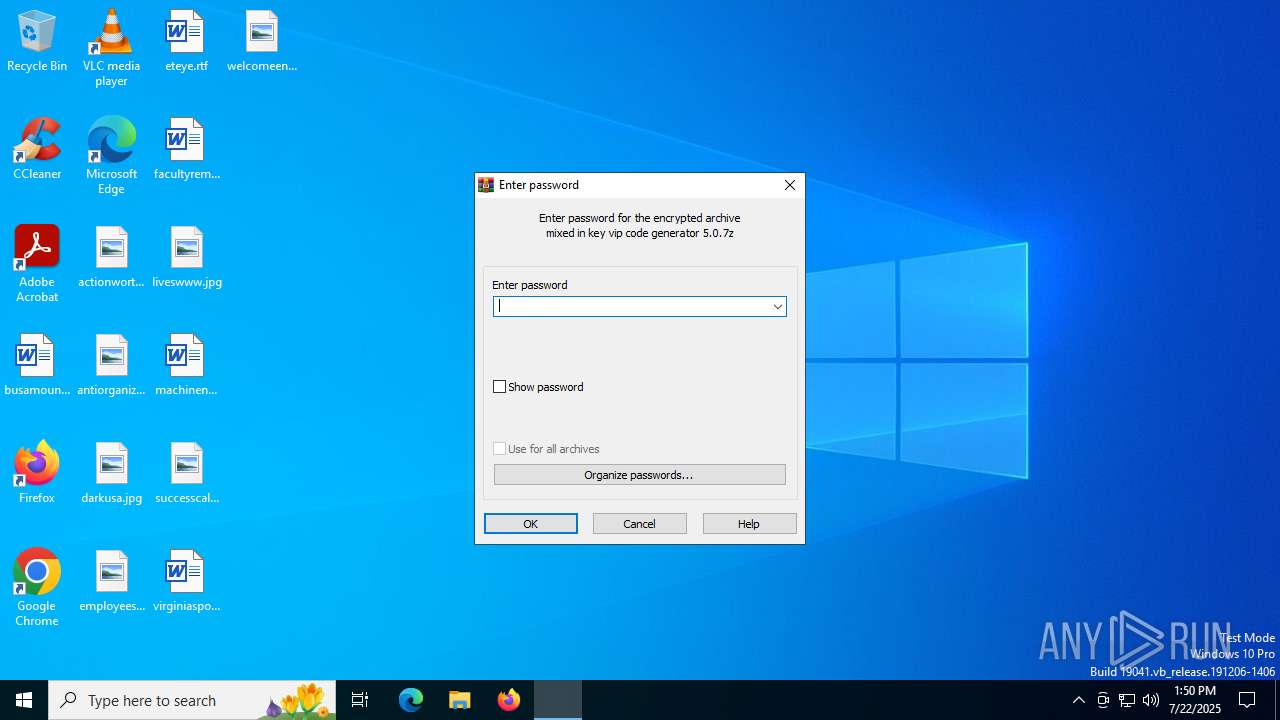
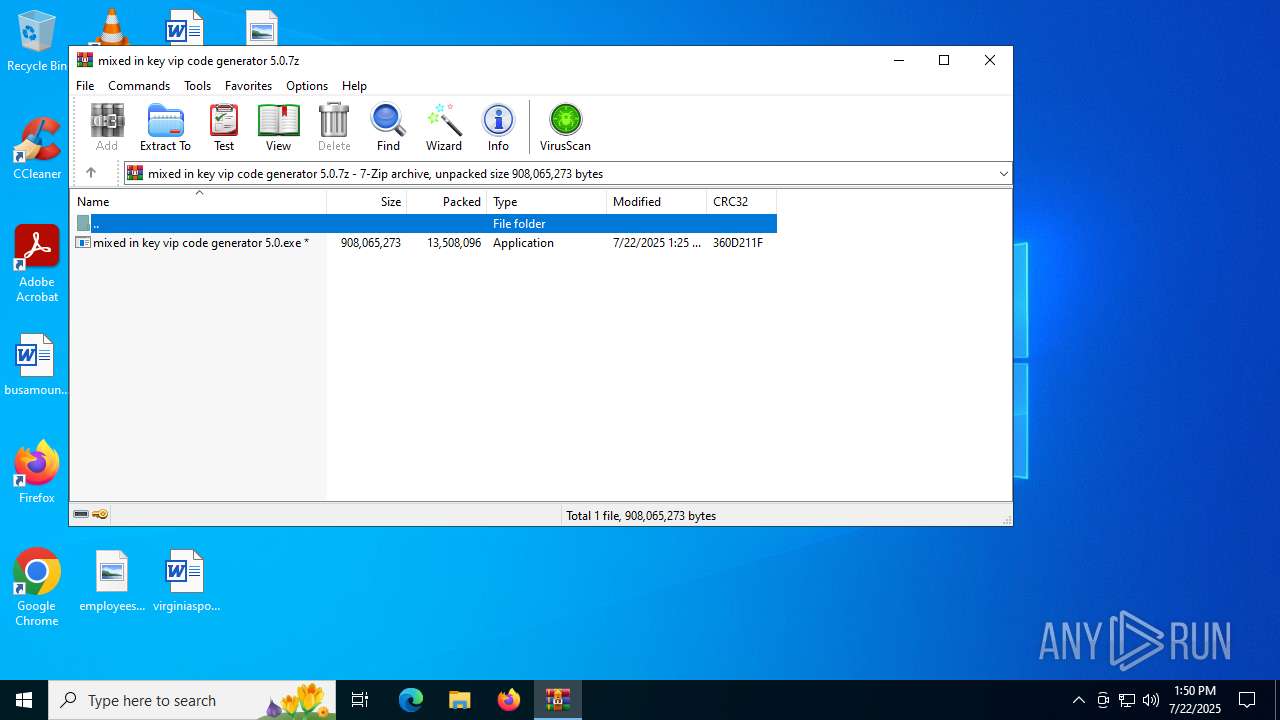
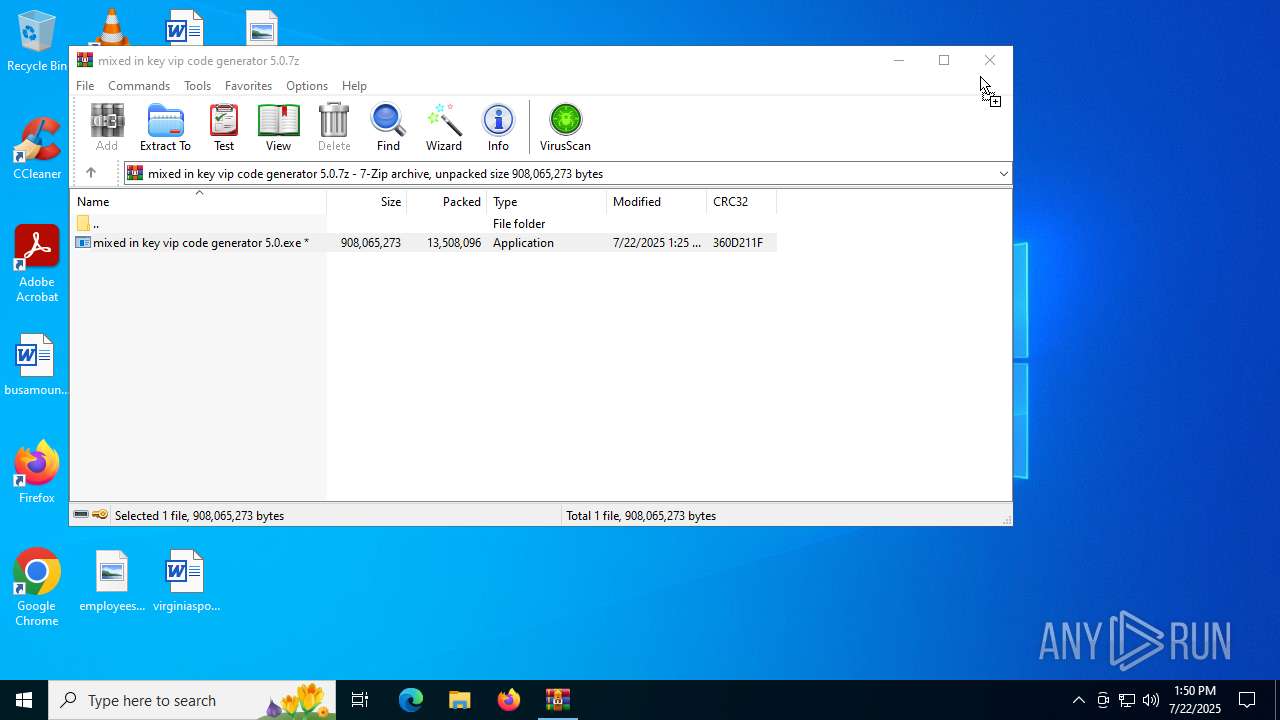
| File name: | mixed in key vip code generator 5.0.7z |
| Full analysis: | https://app.any.run/tasks/0443e86b-829e-4f03-af3d-3f989f2272b0 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | July 22, 2025, 13:50:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | E42ACF6D5AD02436843762BB443A9085 |
| SHA1: | EA8E0BA4437600E45E4579ED91792FC2E7BE0DE9 |
| SHA256: | 6E0C54734C884804D2A3CD822B60227180D0BDADBCEB09FEC24C1C9D2399396E |
| SSDEEP: | 98304:26W1p5YRWPKDzPaqeWawG5mV/QspqIwYfmRrF0wyLt/IUv/V5qqXQDmI6/pKDPmJ:mj2Ce9187HE37Z+qeKCVMYI |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2200)
LUMMA mutex has been found
- Homeless.com (PID: 1508)
SUSPICIOUS
Starts CMD.EXE for commands execution
- mixed in key vip code generator 5.0.exe (PID: 4020)
Get information on the list of running processes
- cmd.exe (PID: 3672)
Executing commands from ".cmd" file
- mixed in key vip code generator 5.0.exe (PID: 4020)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3672)
Executable content was dropped or overwritten
- mixed in key vip code generator 5.0.exe (PID: 4020)
There is functionality for taking screenshot (YARA)
- Homeless.com (PID: 1508)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3672)
Starts the AutoIt3 executable file
- cmd.exe (PID: 3672)
The executable file from the user directory is run by the CMD process
- Homeless.com (PID: 1508)
Starts application with an unusual extension
- cmd.exe (PID: 3672)
INFO
Checks supported languages
- mixed in key vip code generator 5.0.exe (PID: 4020)
- extrac32.exe (PID: 6420)
- Homeless.com (PID: 1508)
Create files in a temporary directory
- mixed in key vip code generator 5.0.exe (PID: 4020)
- extrac32.exe (PID: 6420)
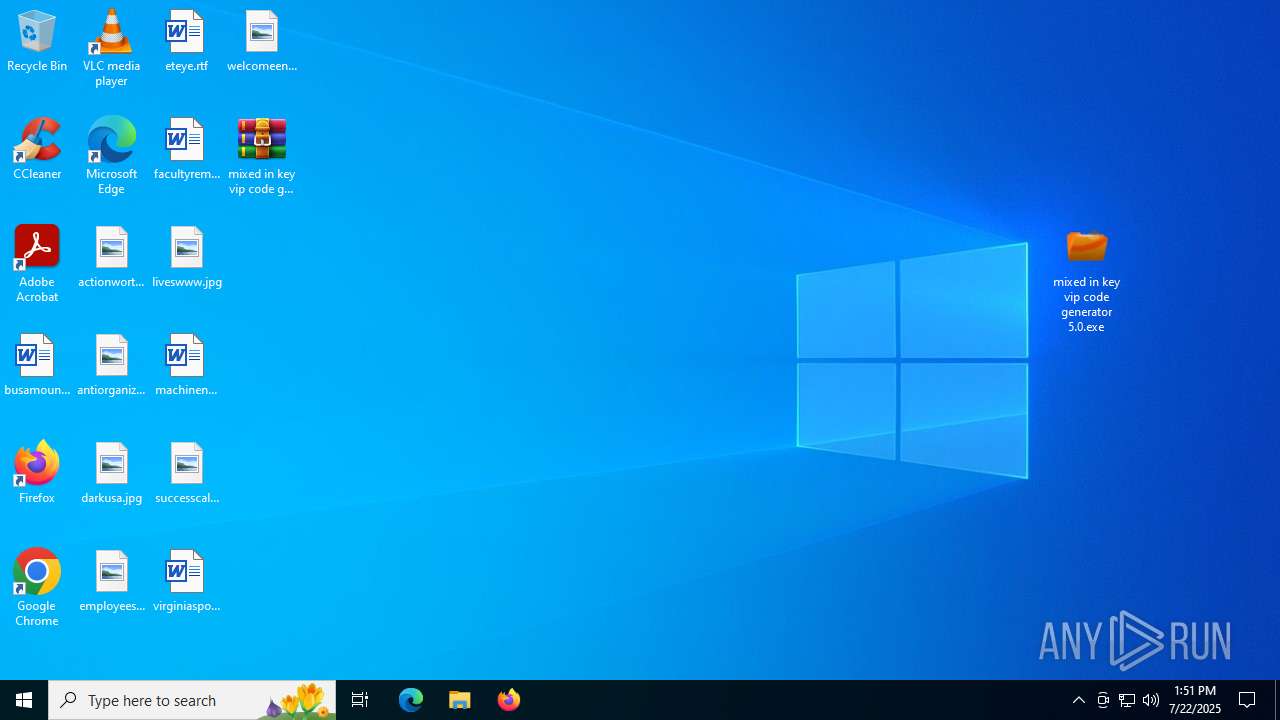
Manual execution by a user
- mixed in key vip code generator 5.0.exe (PID: 4020)
Reads the computer name
- extrac32.exe (PID: 6420)
- Homeless.com (PID: 1508)
Reads the software policy settings
- Homeless.com (PID: 1508)
Reads the machine GUID from the registry
- Homeless.com (PID: 1508)
Application launched itself
- chrome.exe (PID: 2612)
- chrome.exe (PID: 1068)
- chrome.exe (PID: 3556)
Reads mouse settings
- Homeless.com (PID: 1508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
178
Monitored processes
43
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3204,i,1924223275353117306,6404767392457572332,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2400,i,12778504712054754595,663680532851823616,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2416 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Homeless.com | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3716,i,12871479316903610513,14855684129703312212,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3768 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1508 | Homeless.com M | C:\Users\admin\AppData\Local\Temp\20711\Homeless.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Version: 3, 3, 17, 0 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4596,i,12871479316903610513,14855684129703312212,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2388 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2596 | findstr "SophosHealth nsWscSvc ekrn bdservicehost AvastUI AVGUI & if not errorlevel 1 Set GuWBGEFWWtUhgRucUscuAZeqnCQLwhxgDOaL=AutoIt3.exe & Set naWzhRxpsYYwLSjemD=.a3x & Set PaZGIXoJtJpiJCFBrPyzXgtTCNMzuXdz=300 | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2192,i,12778504712054754595,663680532851823616,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1944 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
13 718
Read events
13 684
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\mixed in key vip code generator 5.0.7z | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
1
Suspicious files
46
Text files
74
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
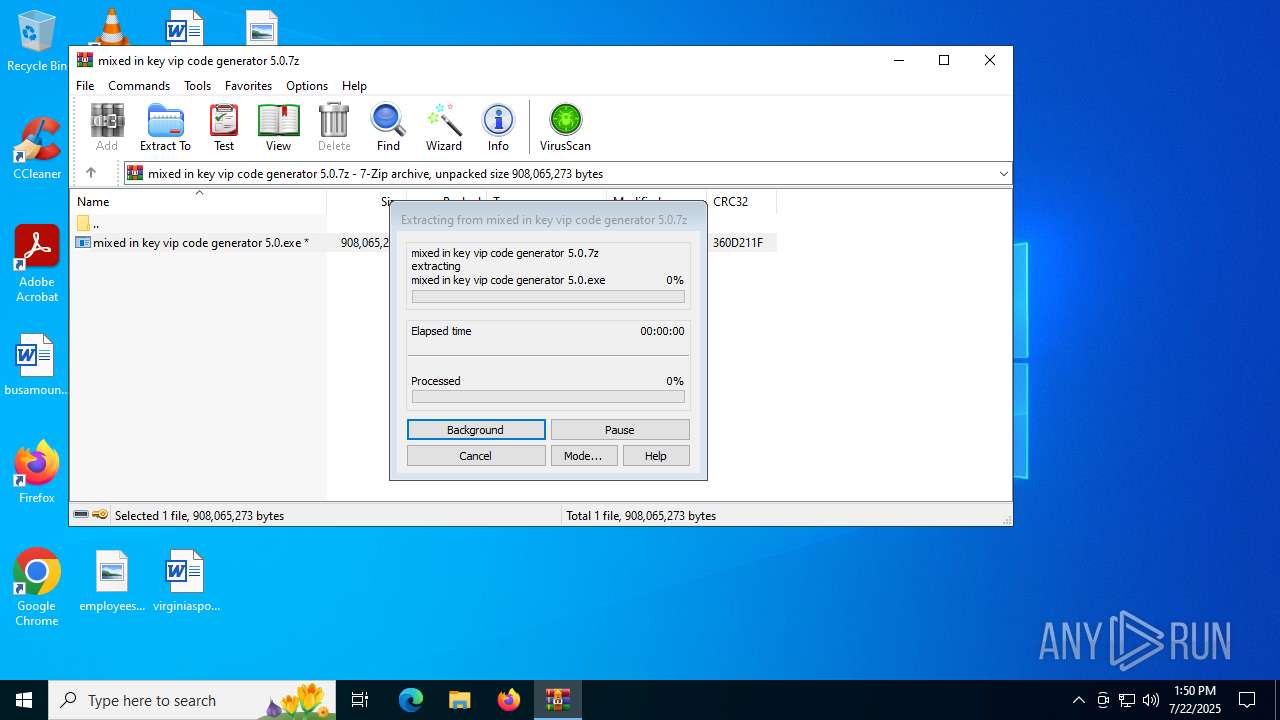
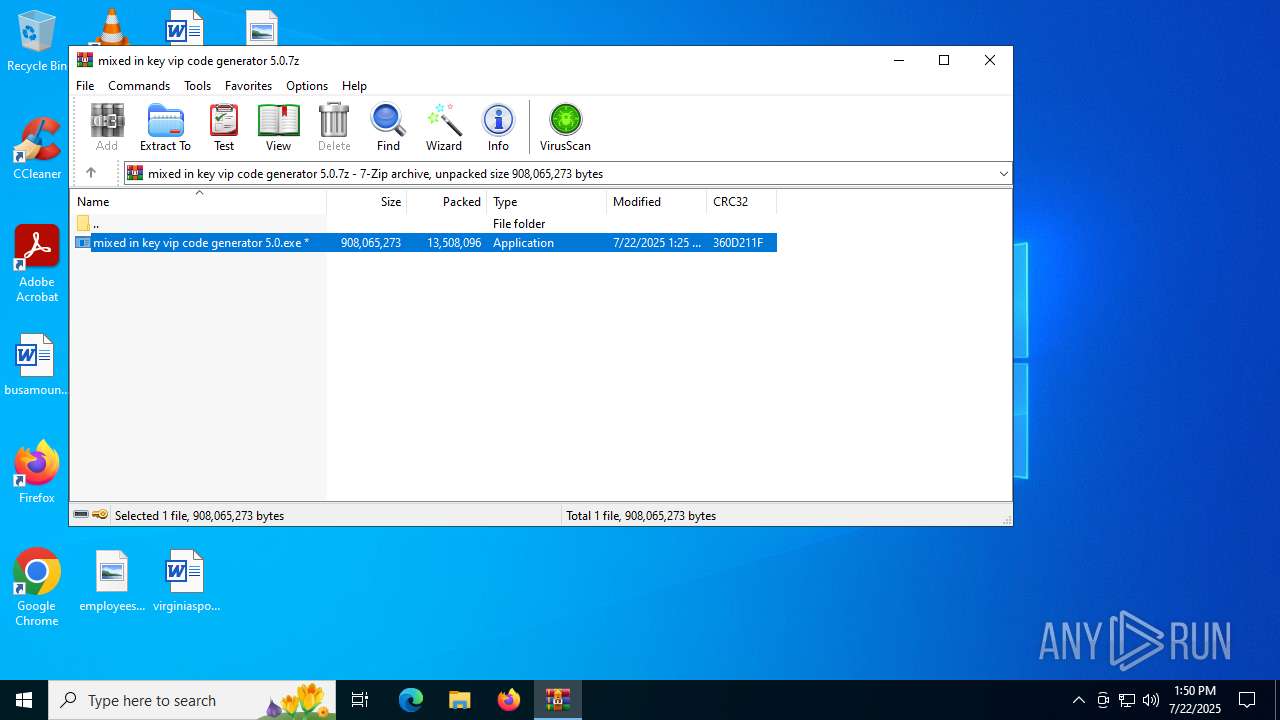
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2976.6386\mixed in key vip code generator 5.0.exe | — | |
MD5:— | SHA256:— | |||
| 4020 | mixed in key vip code generator 5.0.exe | C:\Users\admin\AppData\Local\Temp\Acrylic.wpd | binary | |
MD5:1CC47657FAB3E4230326FC919B94D190 | SHA256:C1354801B9512DB26C4DBC6D629AAC4C8F9255237AD504D81BD4992C473D22BF | |||
| 4020 | mixed in key vip code generator 5.0.exe | C:\Users\admin\AppData\Local\Temp\Housewares.wpd | binary | |
MD5:C9E986C850A1D8667AD6D14F51A88291 | SHA256:E6B2A78D7D5680A45A37D1678C5507B8CB5183191F5F1374732F2F25F321F90E | |||
| 4020 | mixed in key vip code generator 5.0.exe | C:\Users\admin\AppData\Local\Temp\Font.wpd | binary | |
MD5:C2E356C4FED1FE8E7946BB195FA5F653 | SHA256:7101646D31CDC7D262CB0ADA97AEAA85EDFD08706CB62067C2BBFDBCCB311A28 | |||
| 4020 | mixed in key vip code generator 5.0.exe | C:\Users\admin\AppData\Local\Temp\Proceeds.wpd | text | |
MD5:EFDDC80392CF1B80857187619E1298FA | SHA256:D8EB61C9E78145228B80BE16F7920F7232A3B0CEFBE12A250780F86BF696D5B0 | |||
| 4020 | mixed in key vip code generator 5.0.exe | C:\Users\admin\AppData\Local\Temp\Cliff.wpd | binary | |
MD5:4281A19D20C406D925E21A8C751C7AE9 | SHA256:ED95F9FA6D0DE0D078573565BCB40270B2BC9C5F4B1761B6080AAC09DC5CBE6B | |||
| 4020 | mixed in key vip code generator 5.0.exe | C:\Users\admin\AppData\Local\Temp\Parcel.wpd | binary | |
MD5:DABF32CA31C15BEFBCA2B49AA16417BD | SHA256:B721E25FFEC99A844C2EC47DAE85BD76EEBBC95E7E4E6B0610EB5529FB04159A | |||
| 6420 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Ellen | binary | |
MD5:1B603DFF9CE7D0115EE8DCF2E28BB954 | SHA256:1E540C96C7C87E6BD72731B09ED64668E65611E7914B3AF0A258B9D0F5C56DE4 | |||
| 6420 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Huntington | binary | |
MD5:AB271A818DCFA4F4649250BE18852BA6 | SHA256:9A0D1064BB232B36A2E74CAE0EF1B97040287E73D8CA3366845EC2EACA7CB1B6 | |||
| 4020 | mixed in key vip code generator 5.0.exe | C:\Users\admin\AppData\Local\Temp\nss2AB2.tmp\nsExec.dll | executable | |
MD5:08E9796CA20C5FC5076E3AC05FB5709A | SHA256:8165C7AEF7DE3D3E0549776535BEDC380AD9BE7BB85E60AD6436F71528D092AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
56
DNS requests
55
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7104 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5884 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5884 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5576 | chrome.exe | GET | 200 | 142.250.185.110:80 | http://clients2.google.com/time/1/current?cup2key=8:jHObAEnVa8BSS8pW6fukBtldCJpEQ-3WEVGWL0Jw8nw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2964 | chrome.exe | GET | 200 | 142.250.185.110:80 | http://clients2.google.com/time/1/current?cup2key=8:FIjT1PzKxqbJMeWK6PGbnxjB0KX2AWYUZBIDXsW3n5k&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2992 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7104 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
HIZZCPohlNyYQYc.HIZZCPohlNyYQYc |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Lumma DNS Activity observed |
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1508 | Homeless.com | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
1508 | Homeless.com | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 30 |