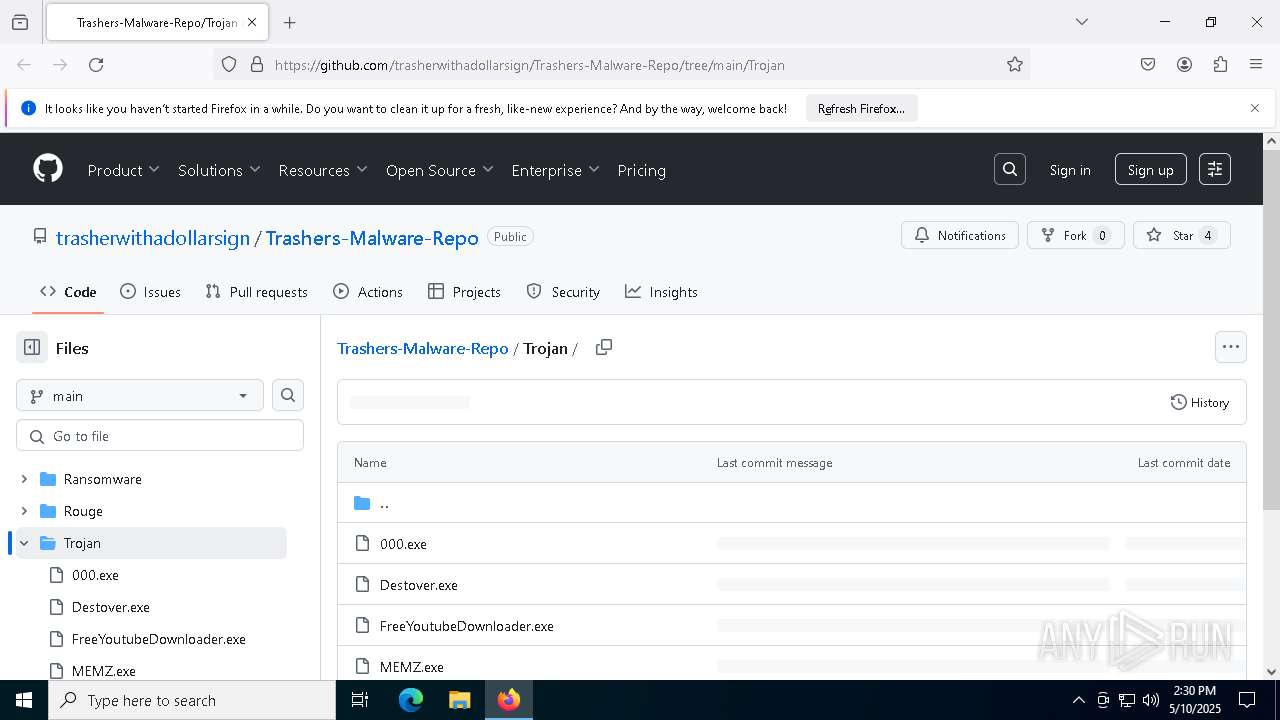
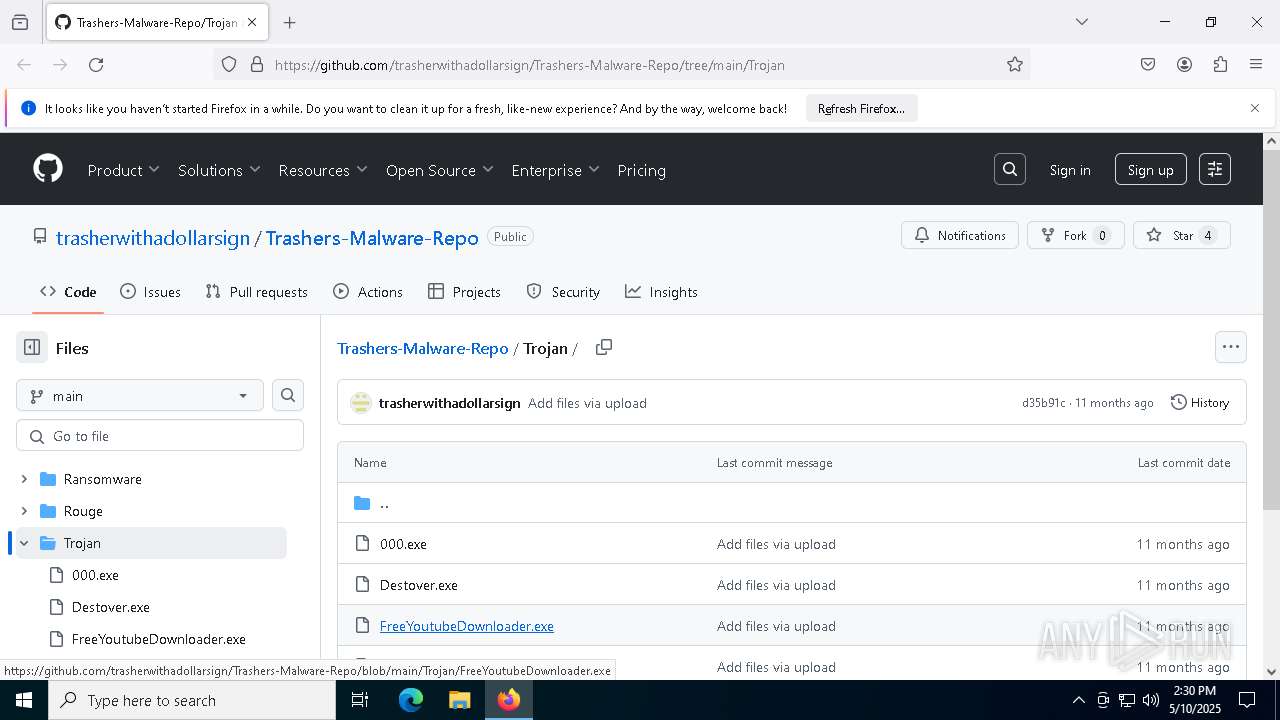
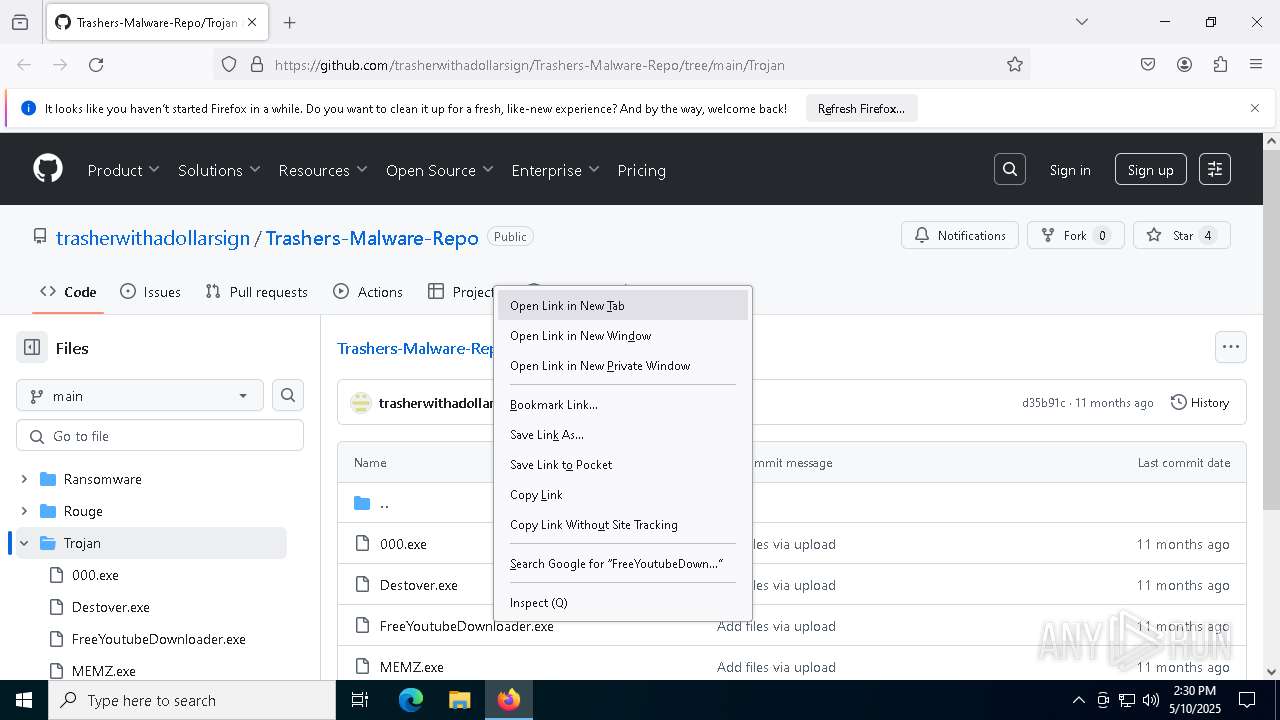
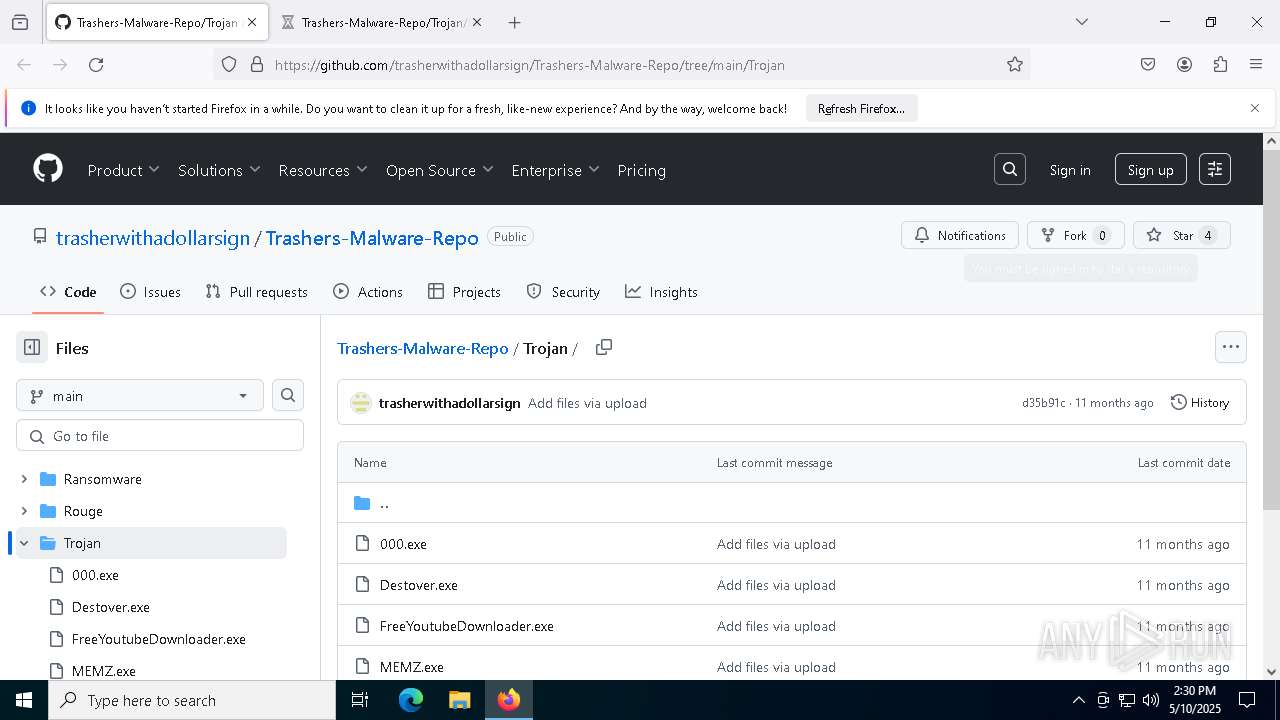
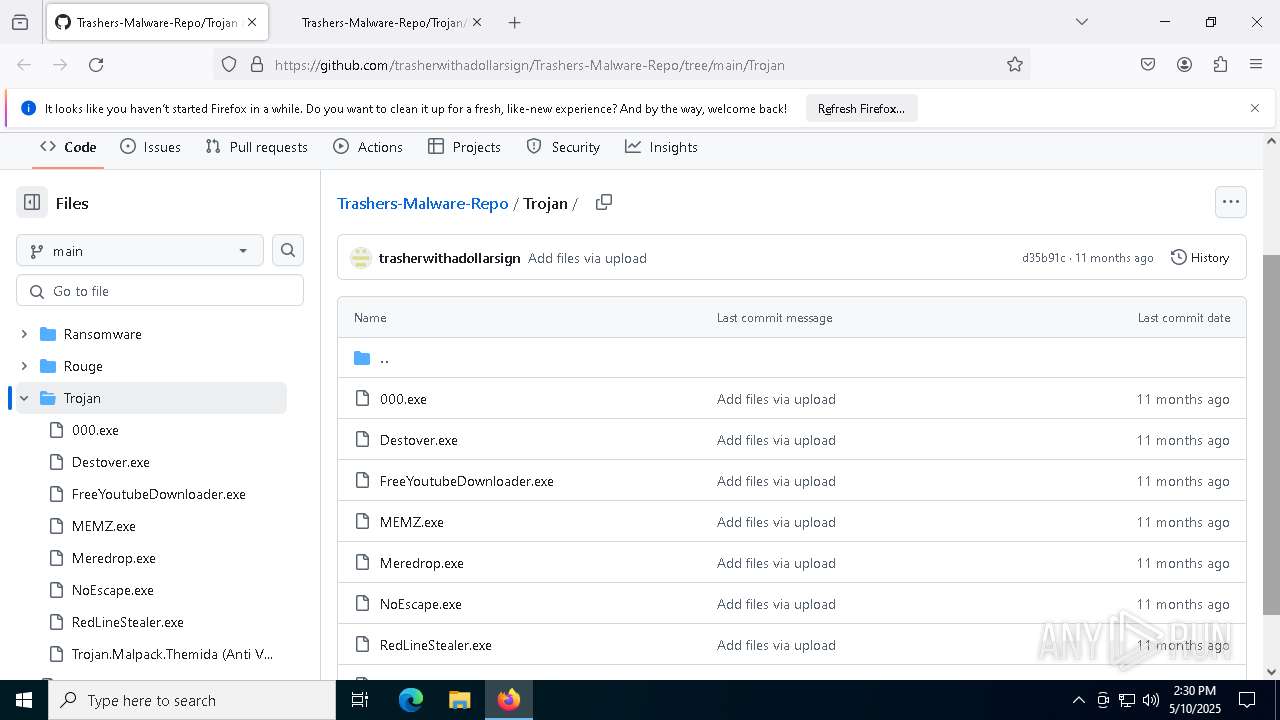
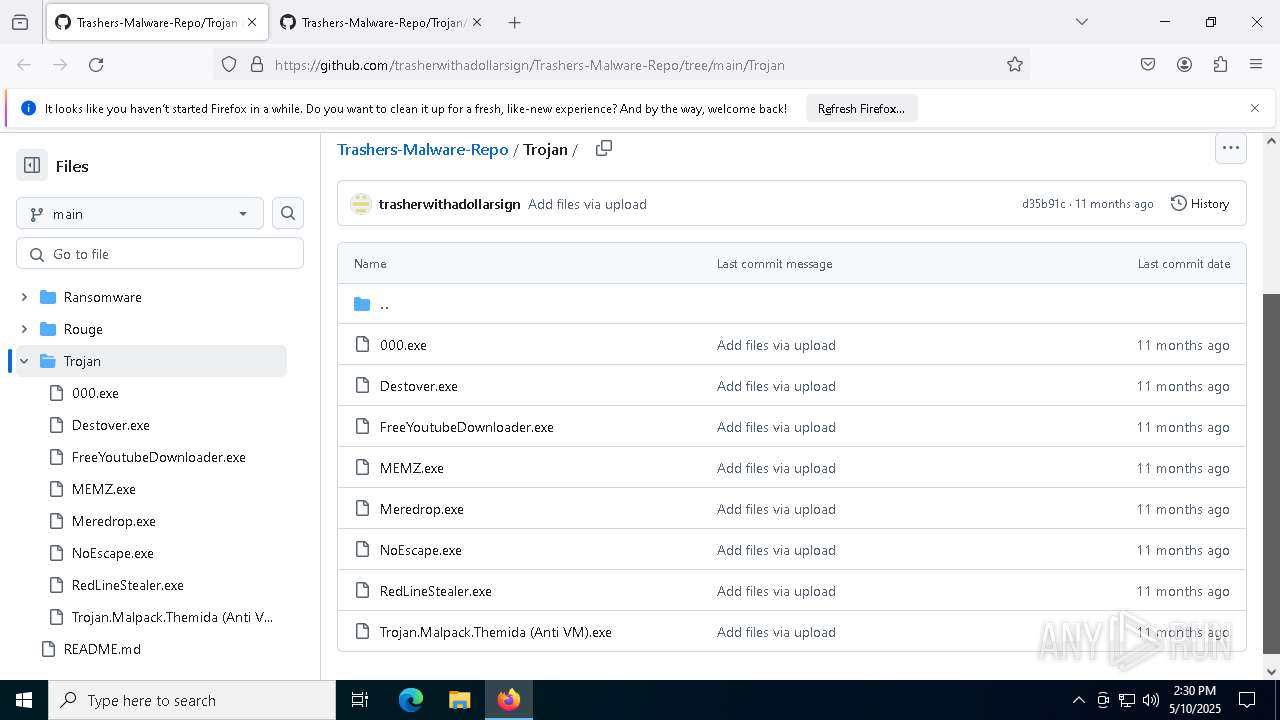
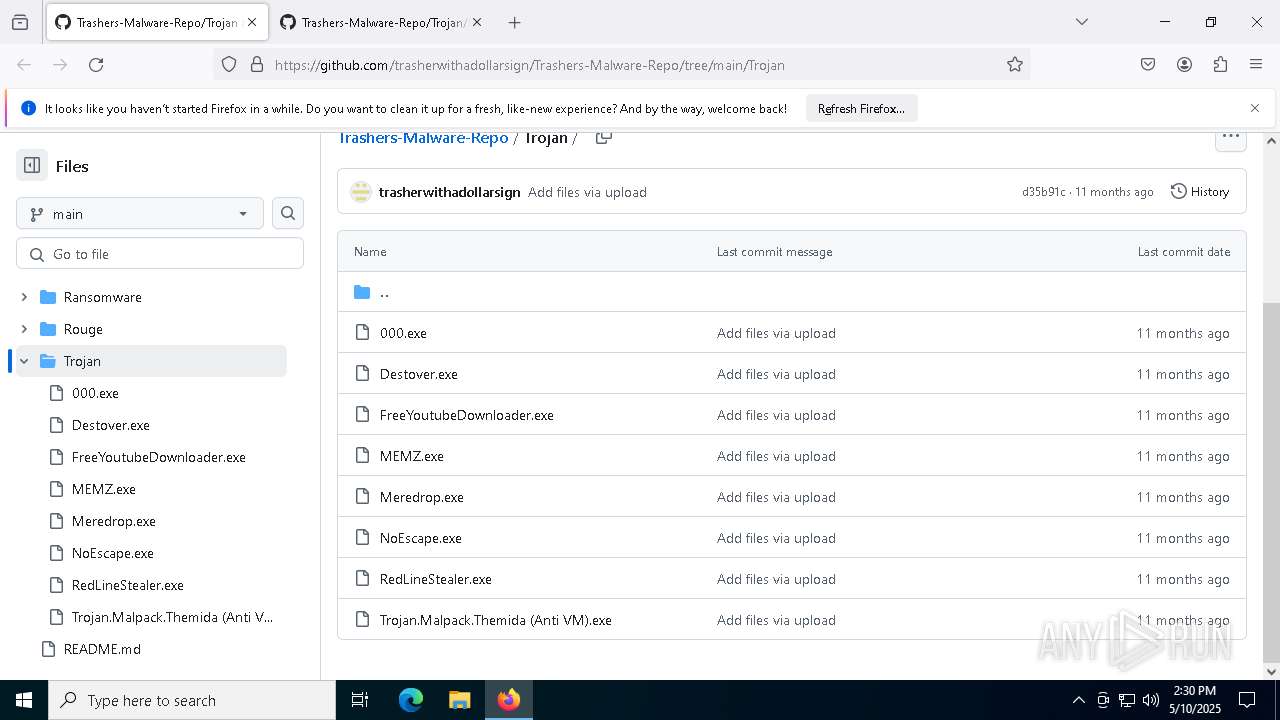
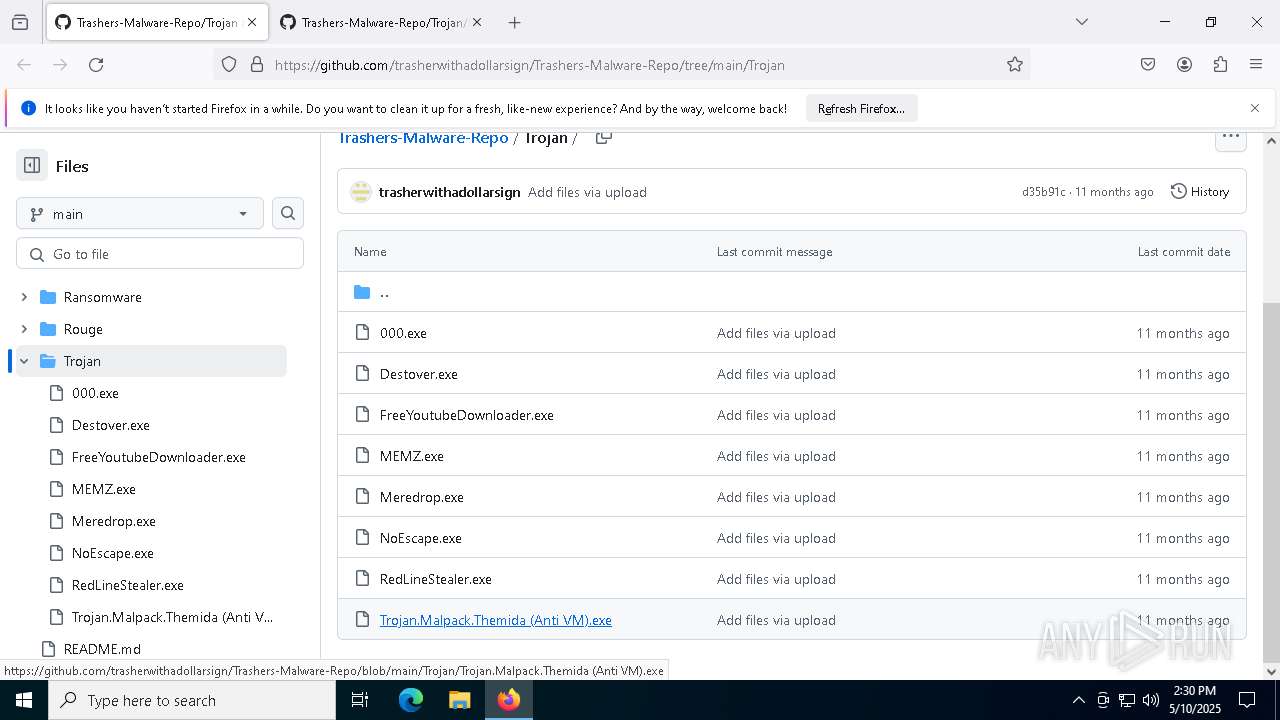
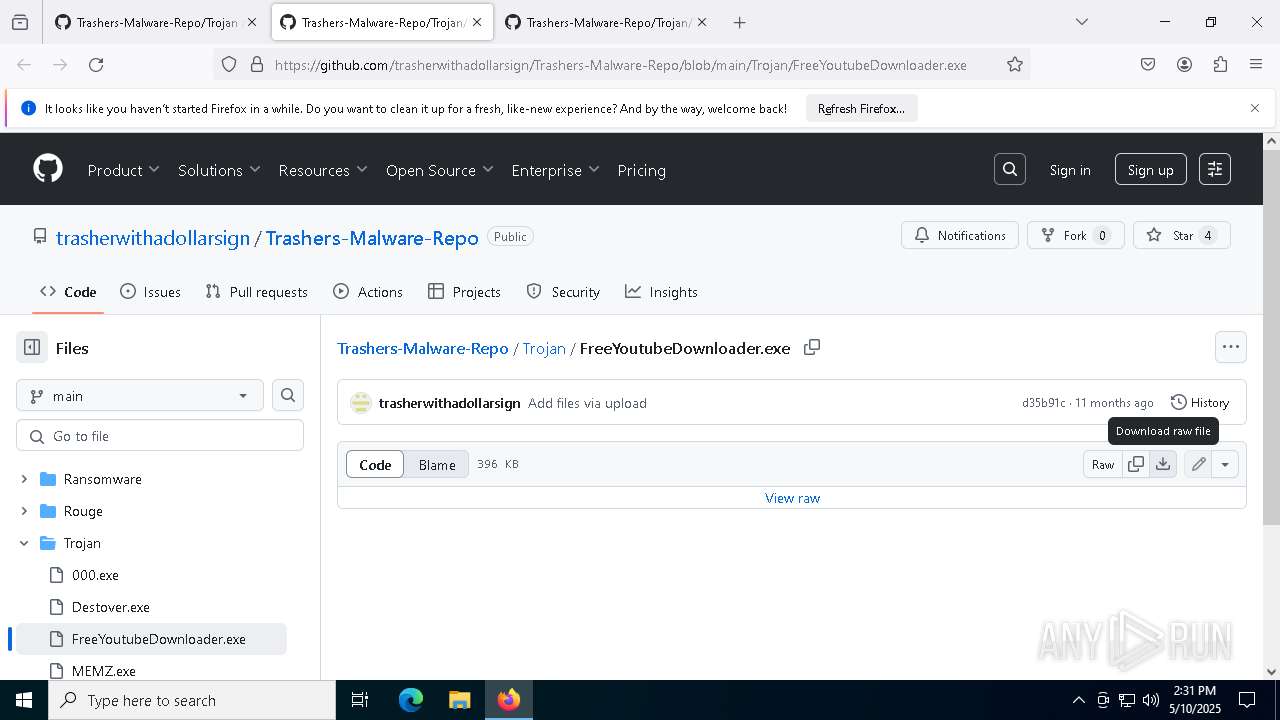
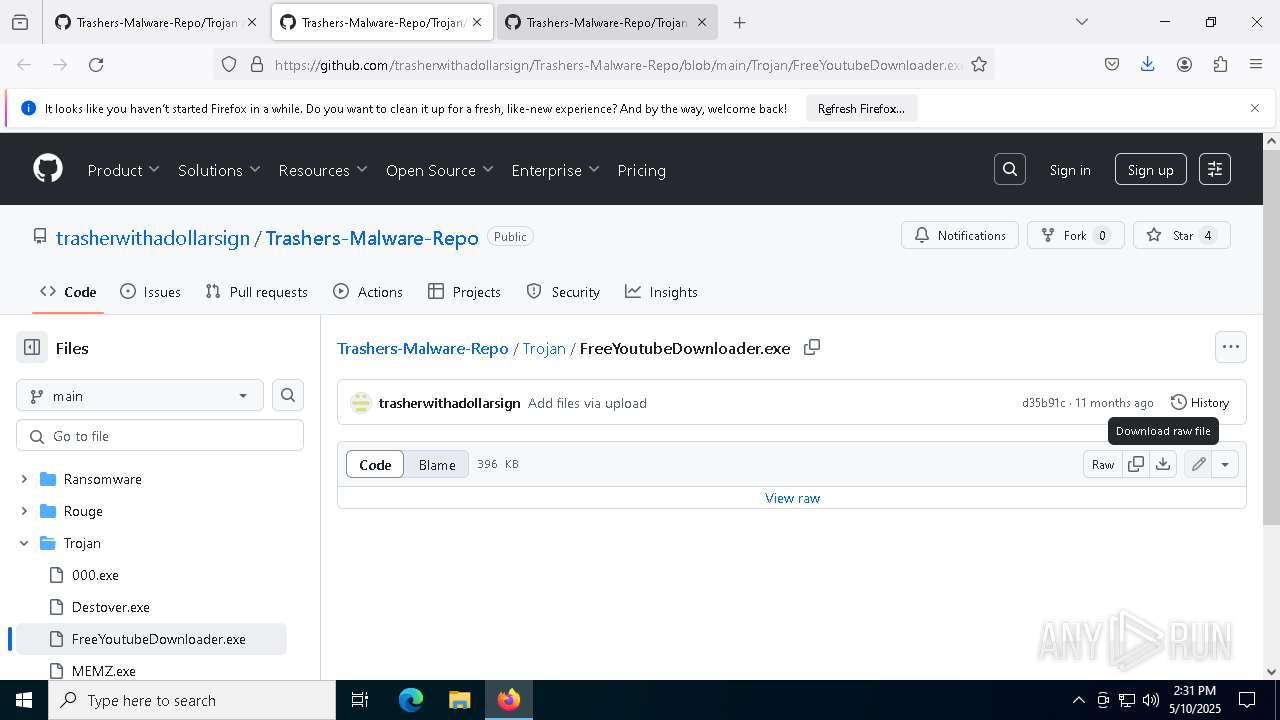
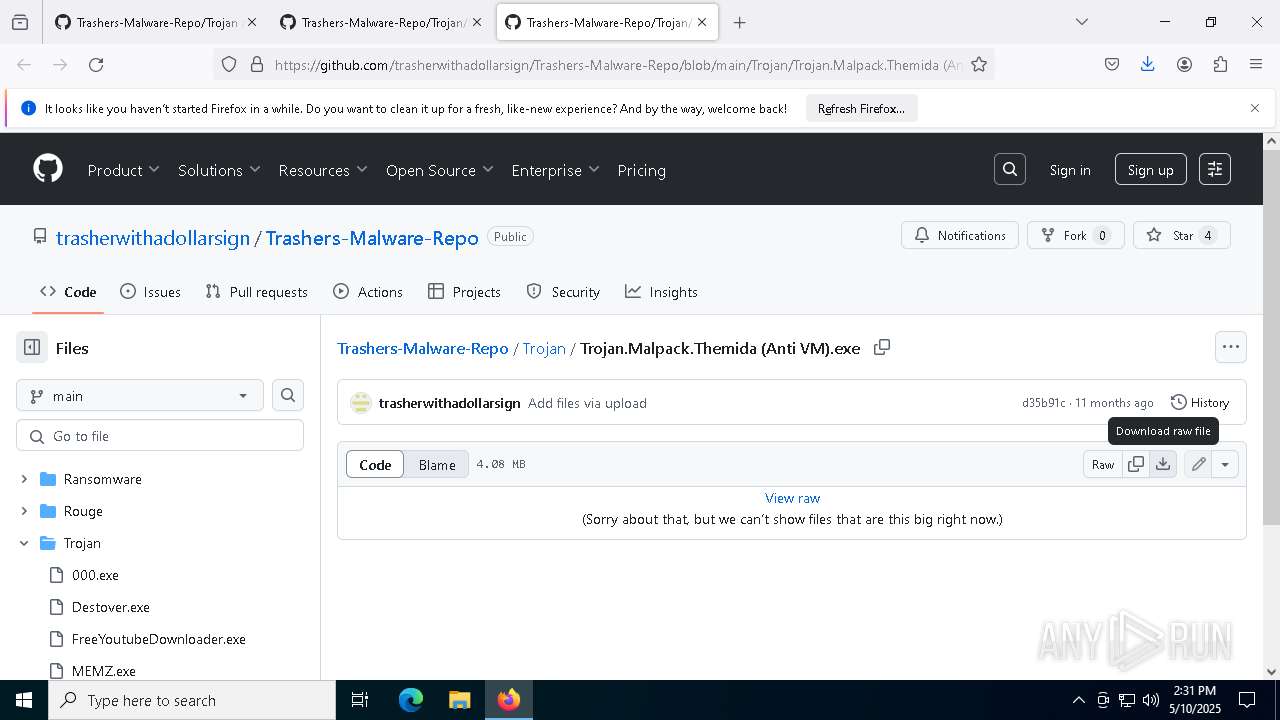
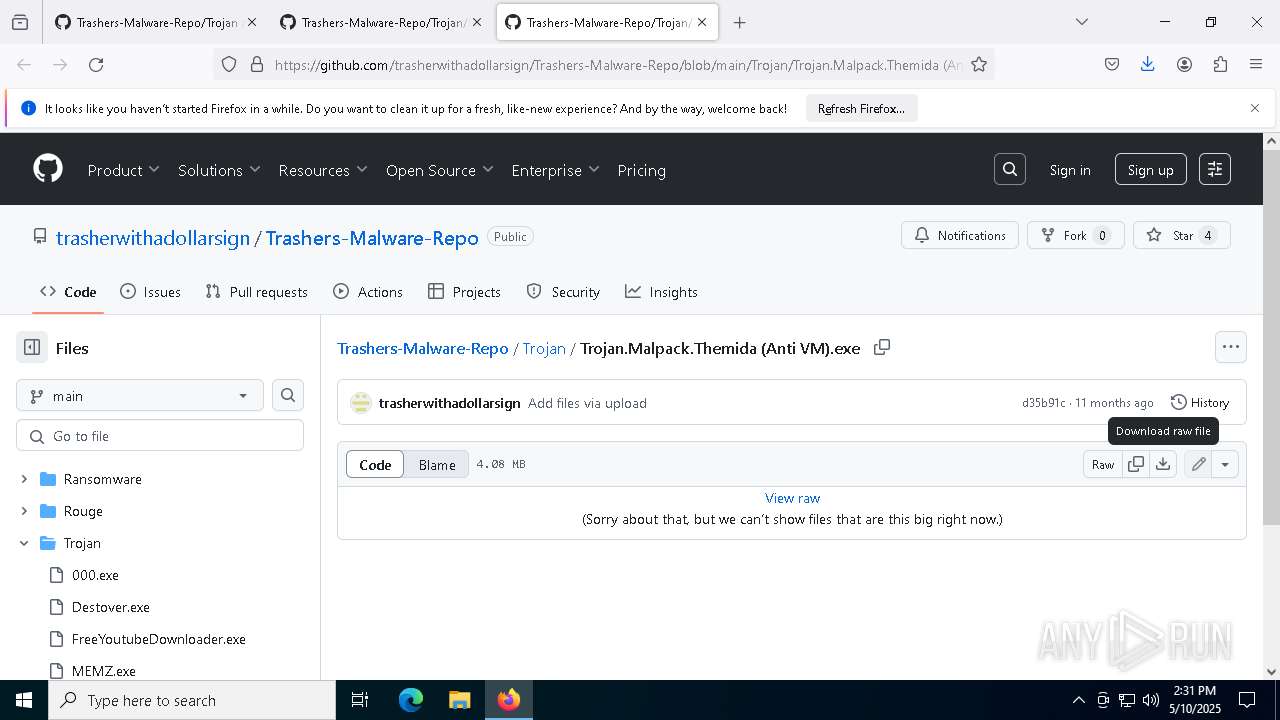
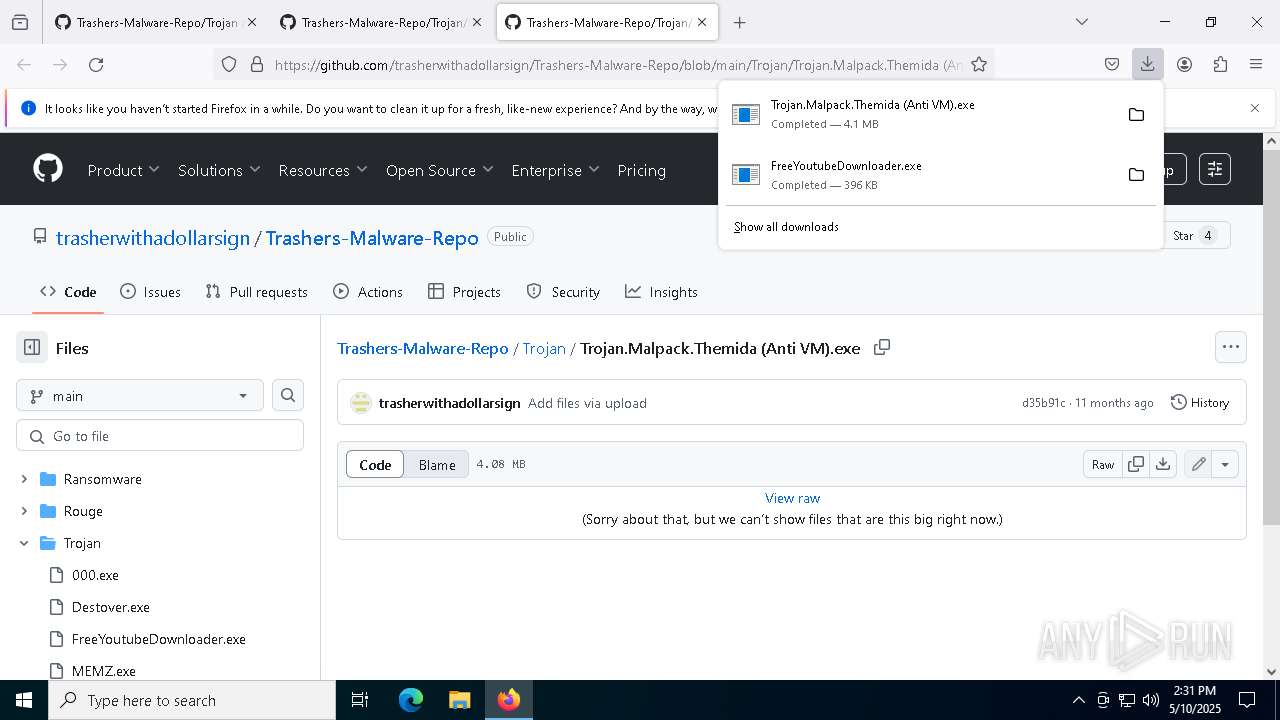
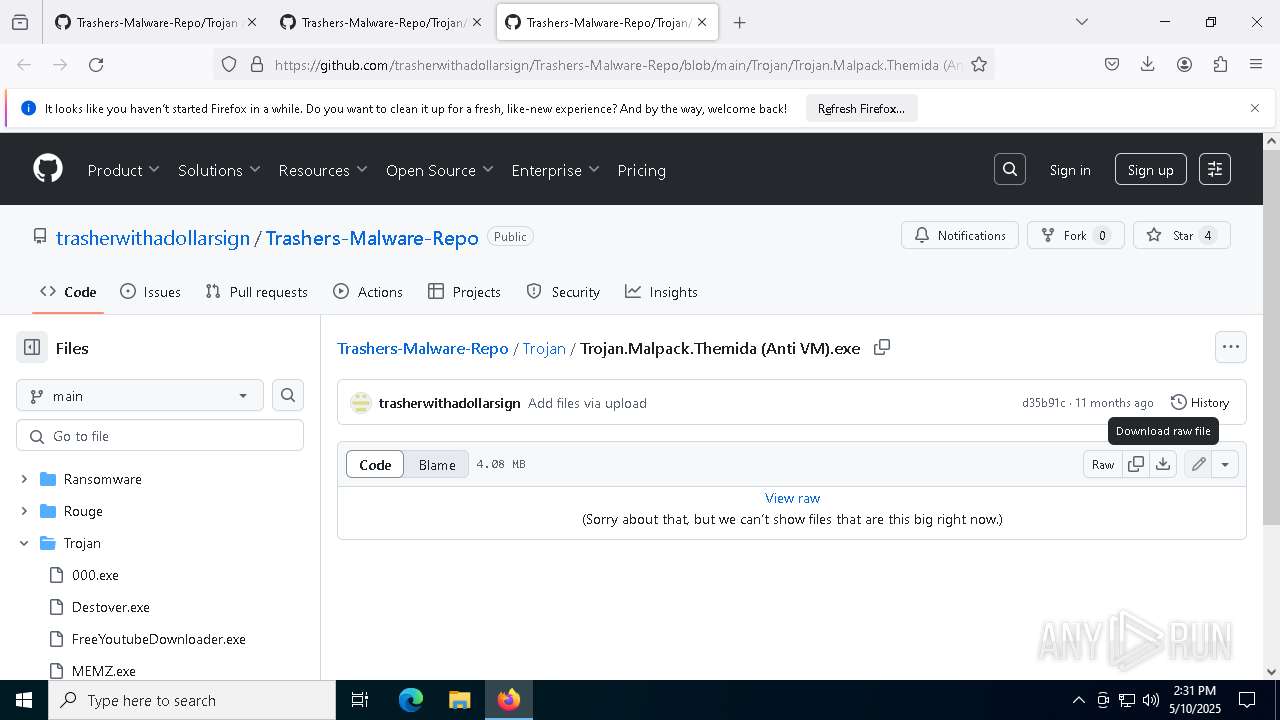
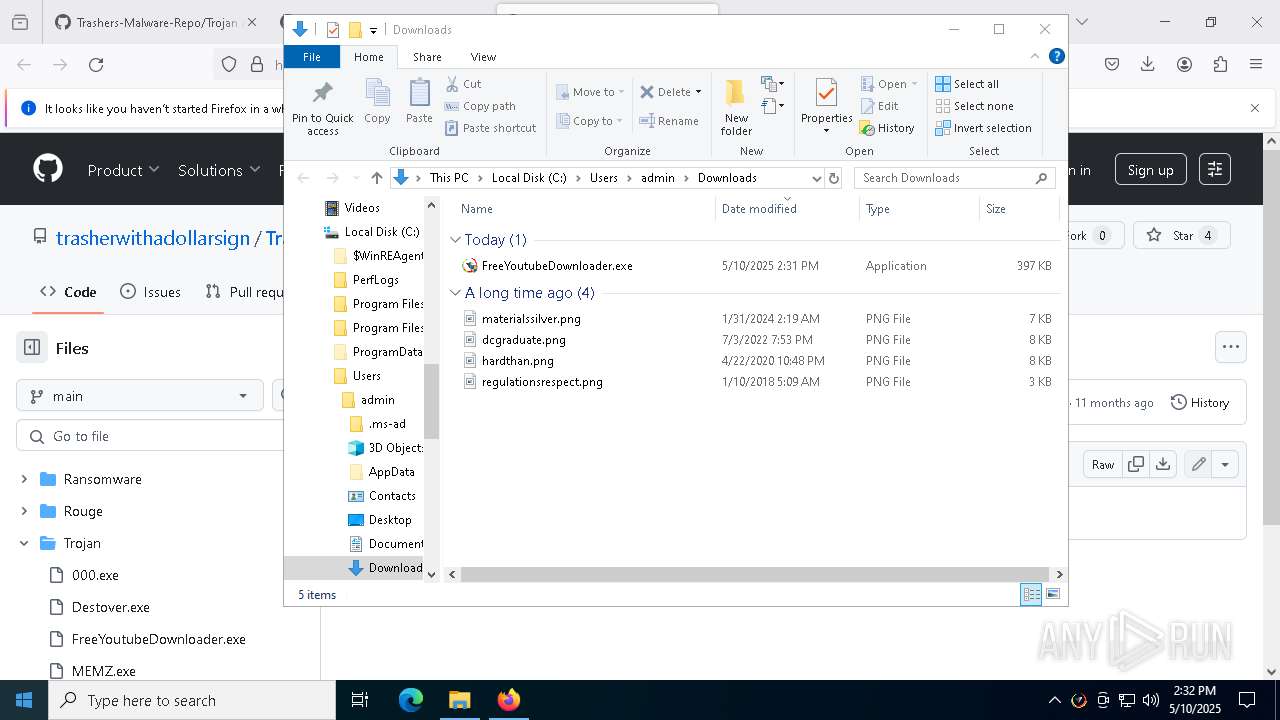
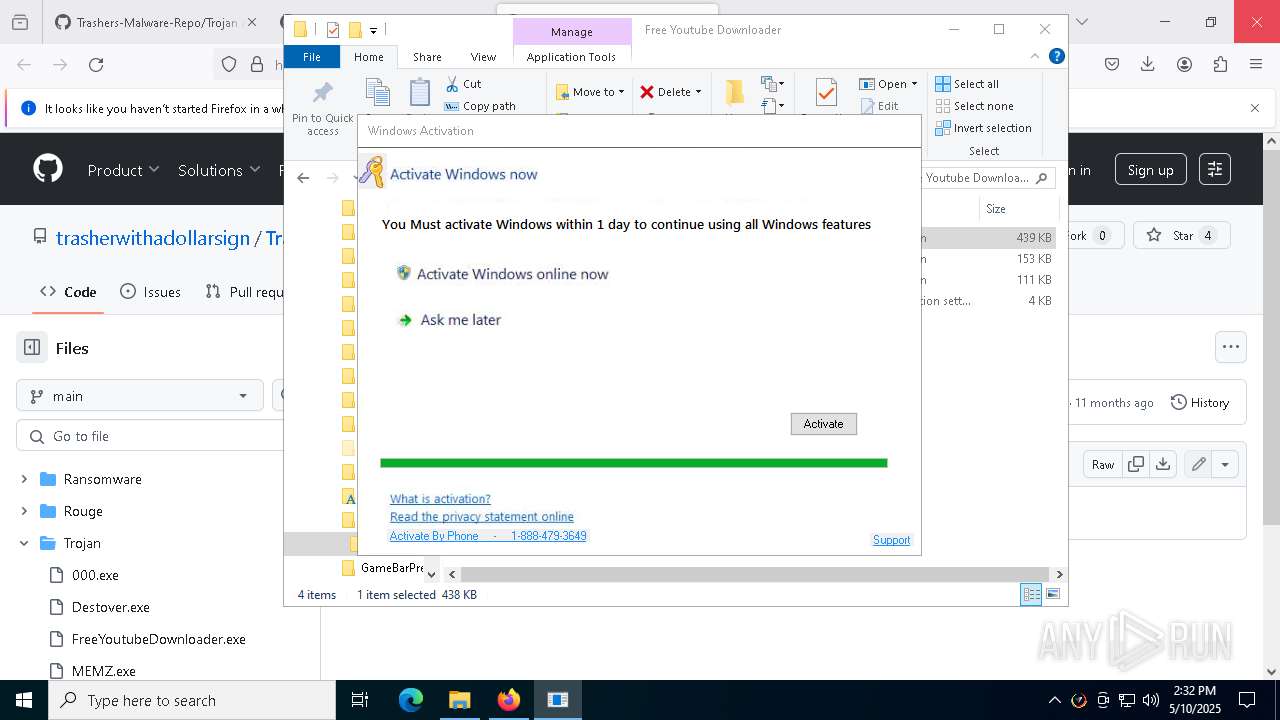
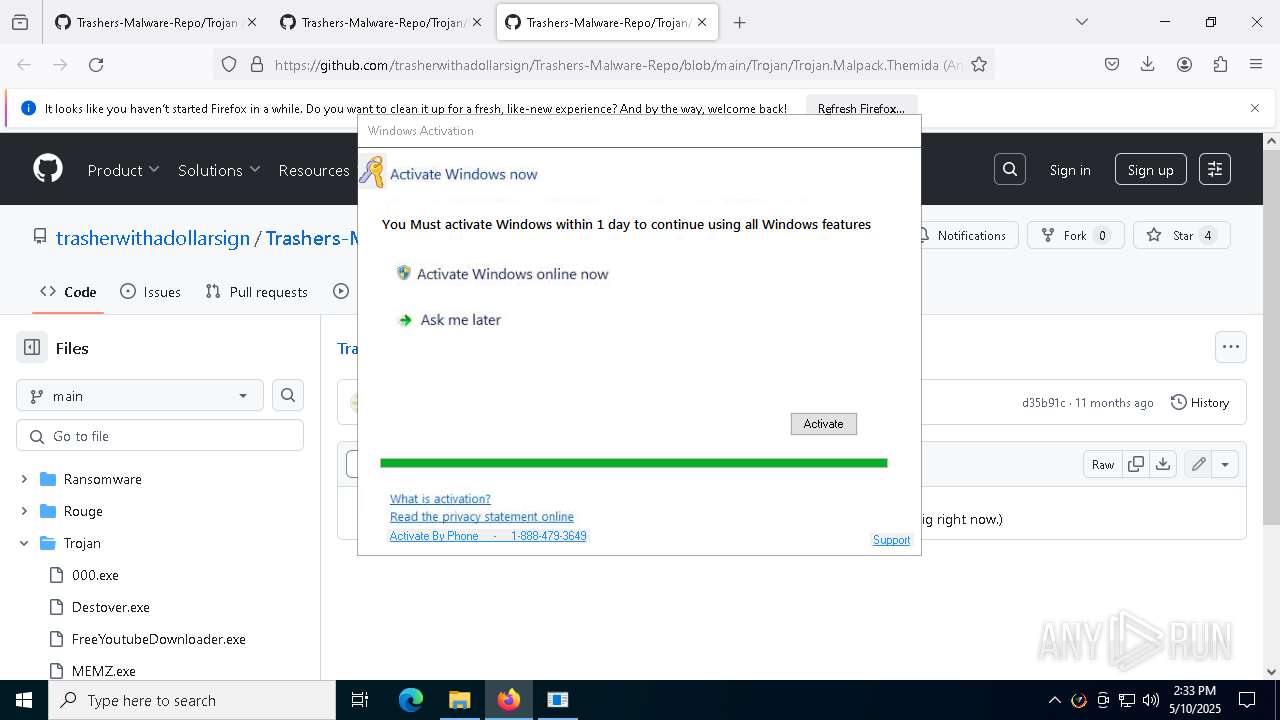
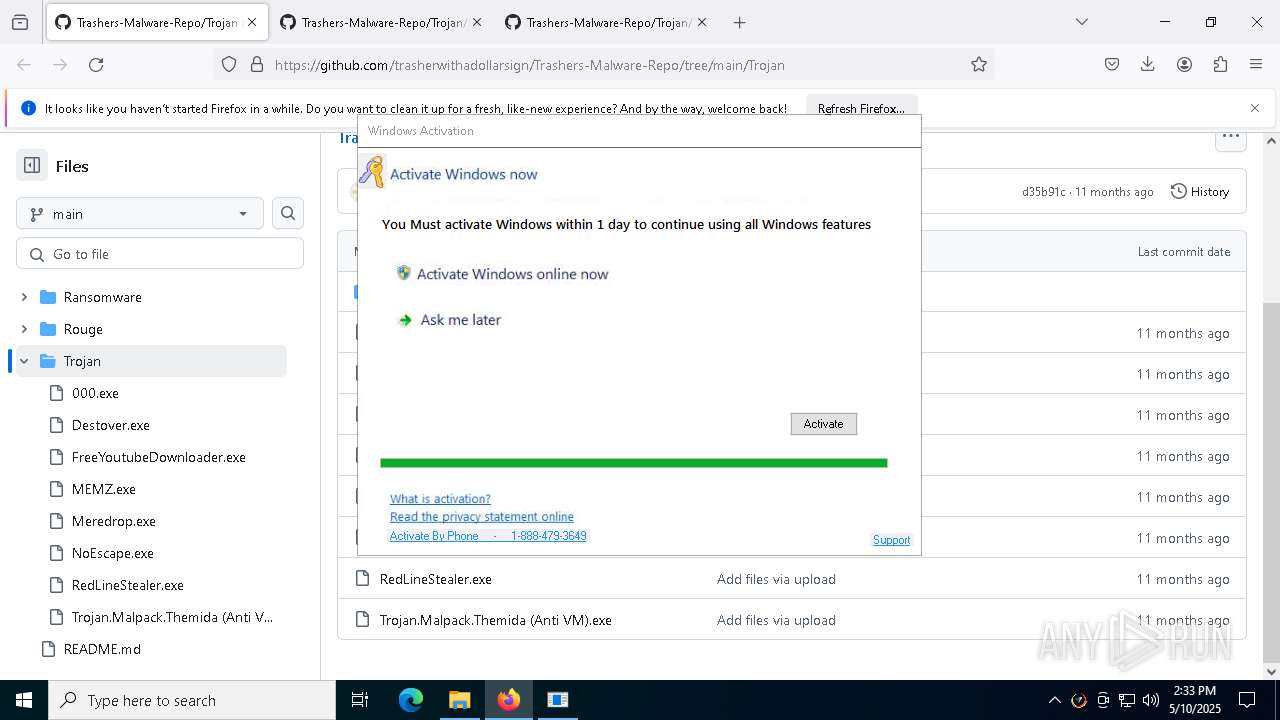
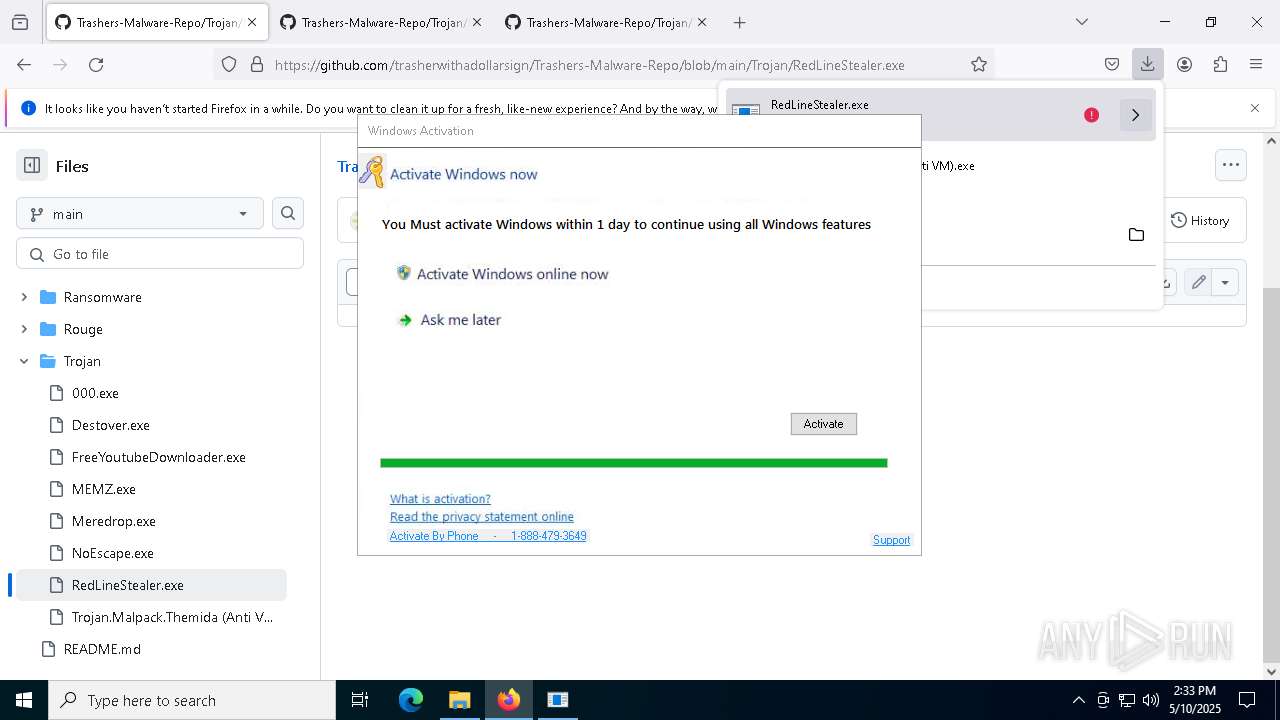
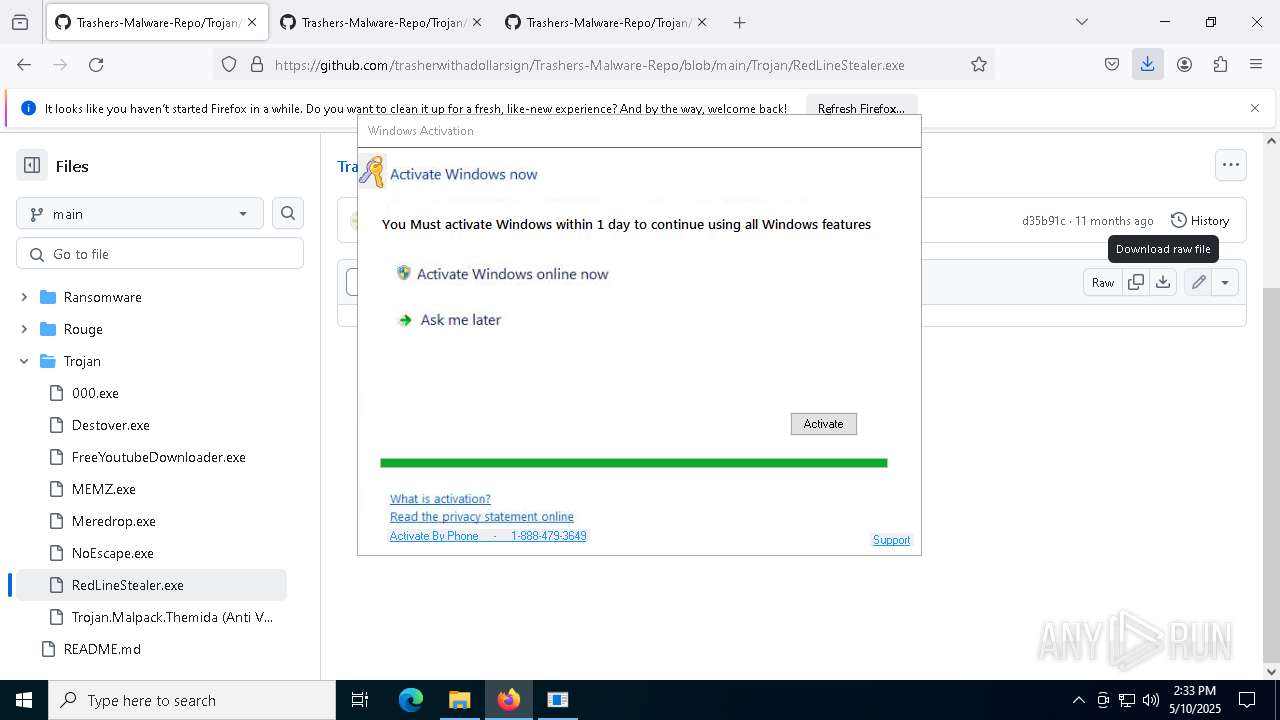
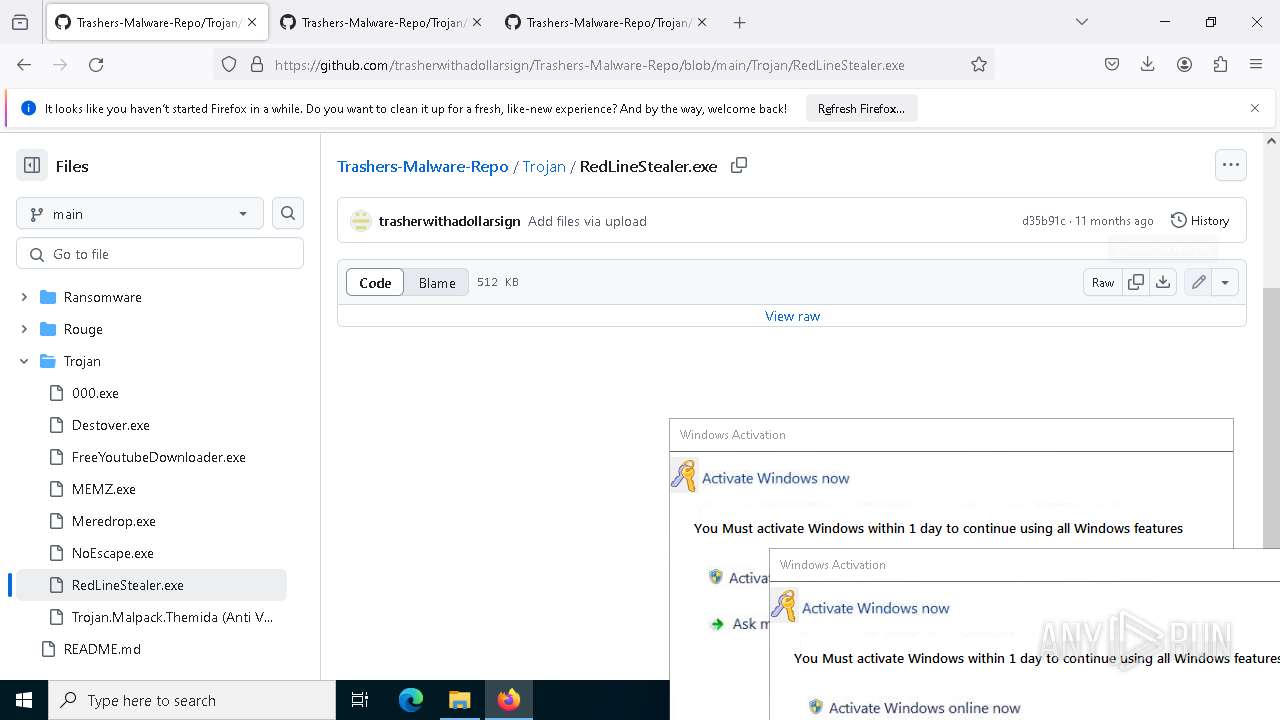
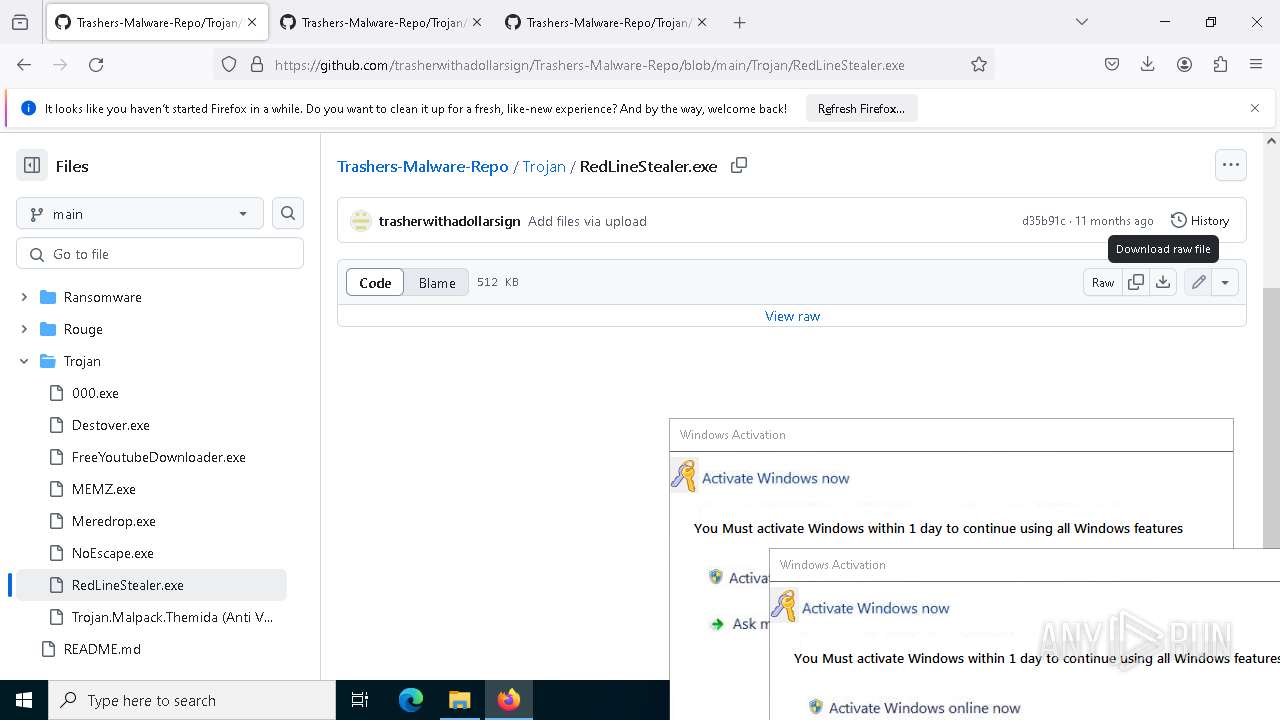
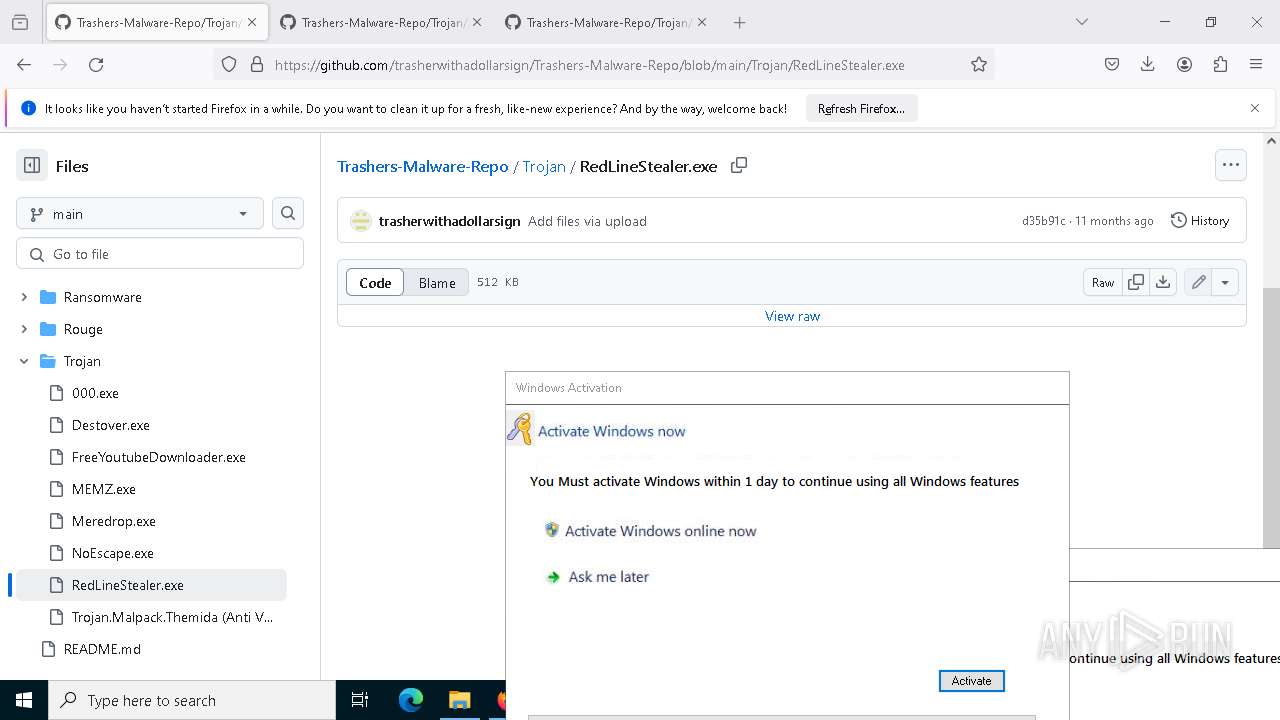
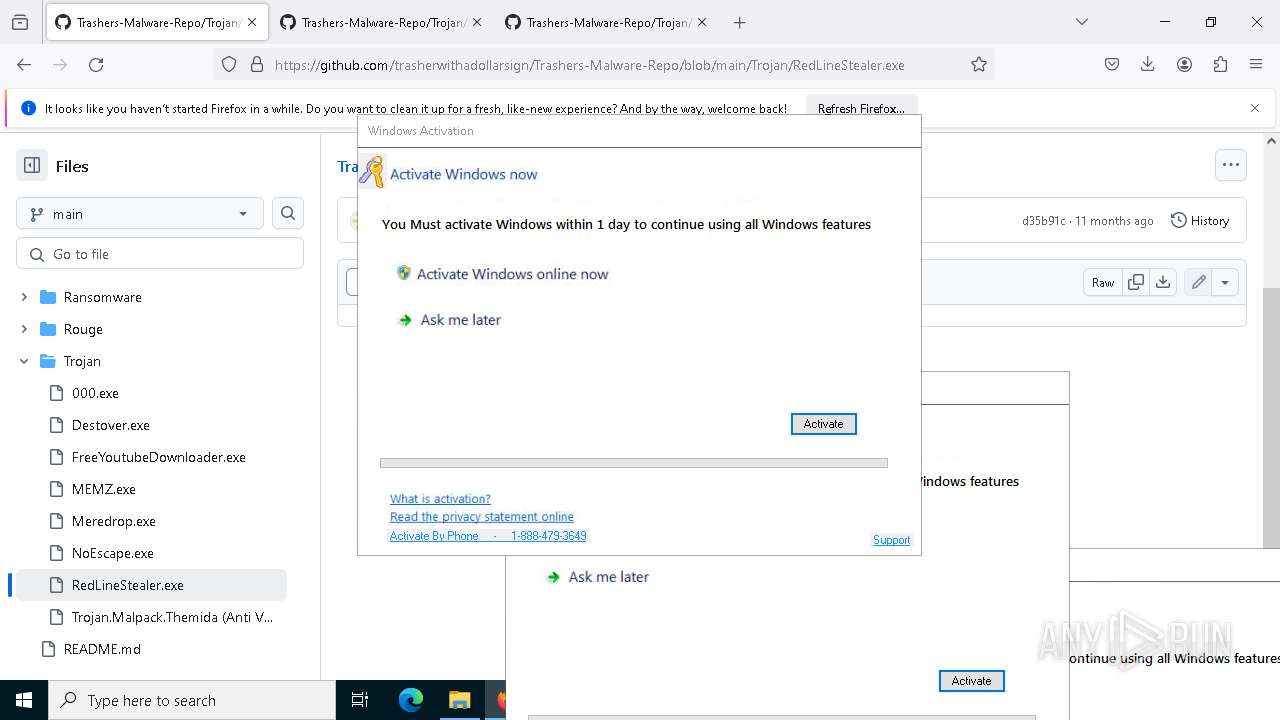
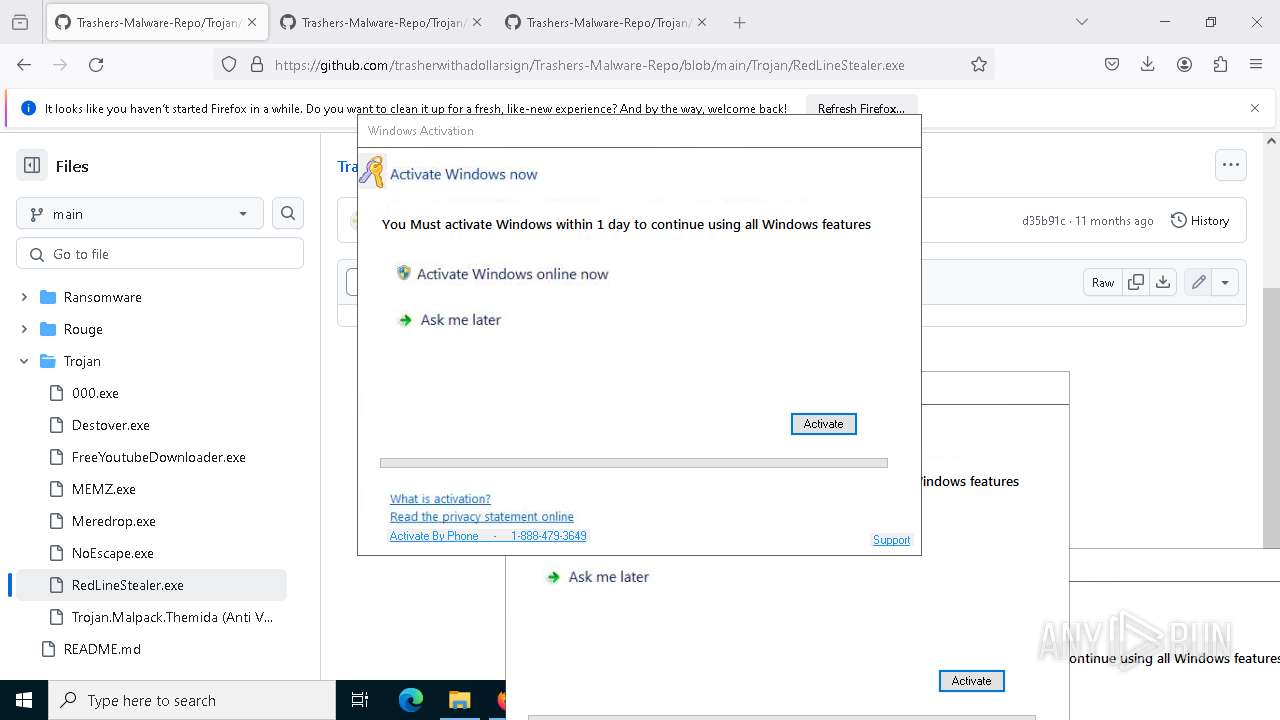
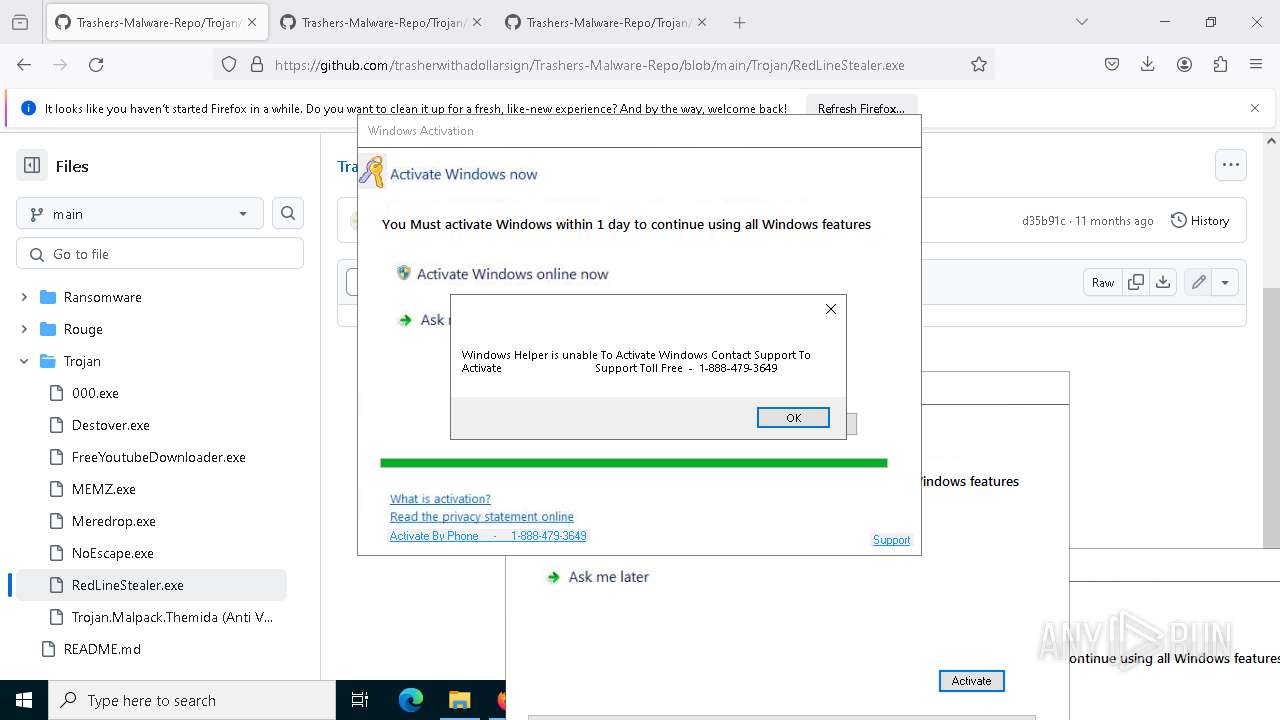
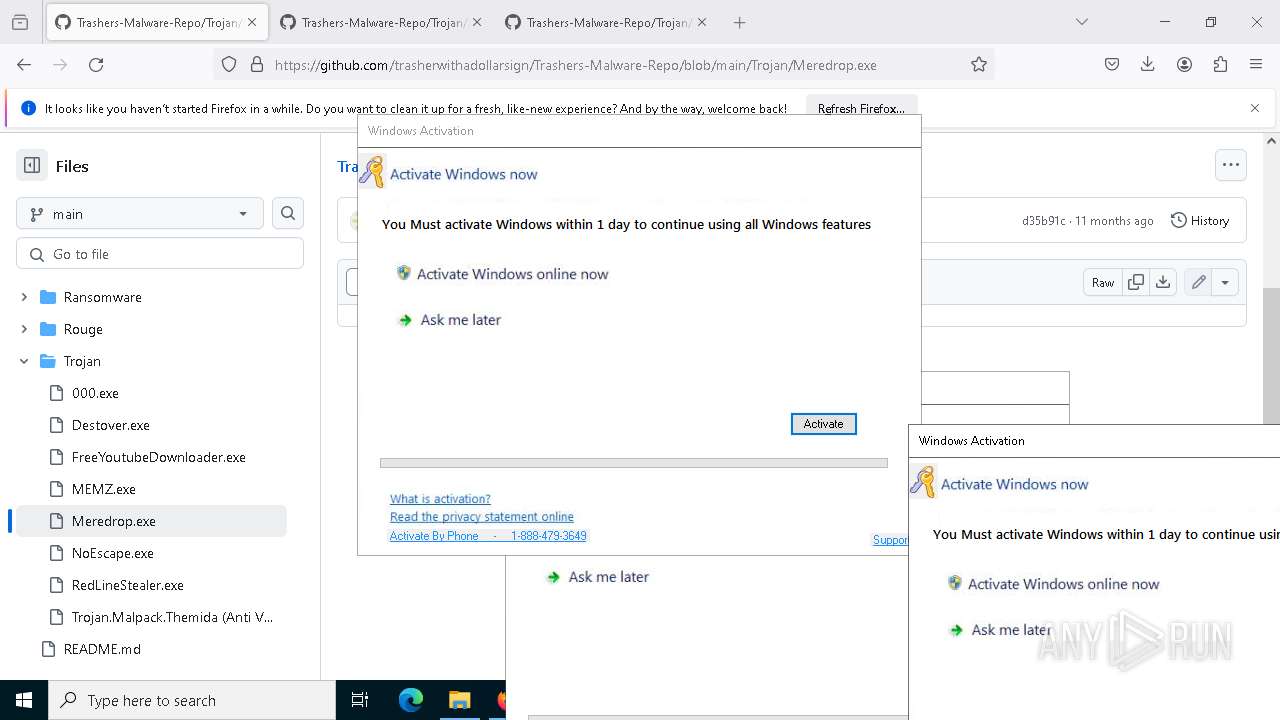
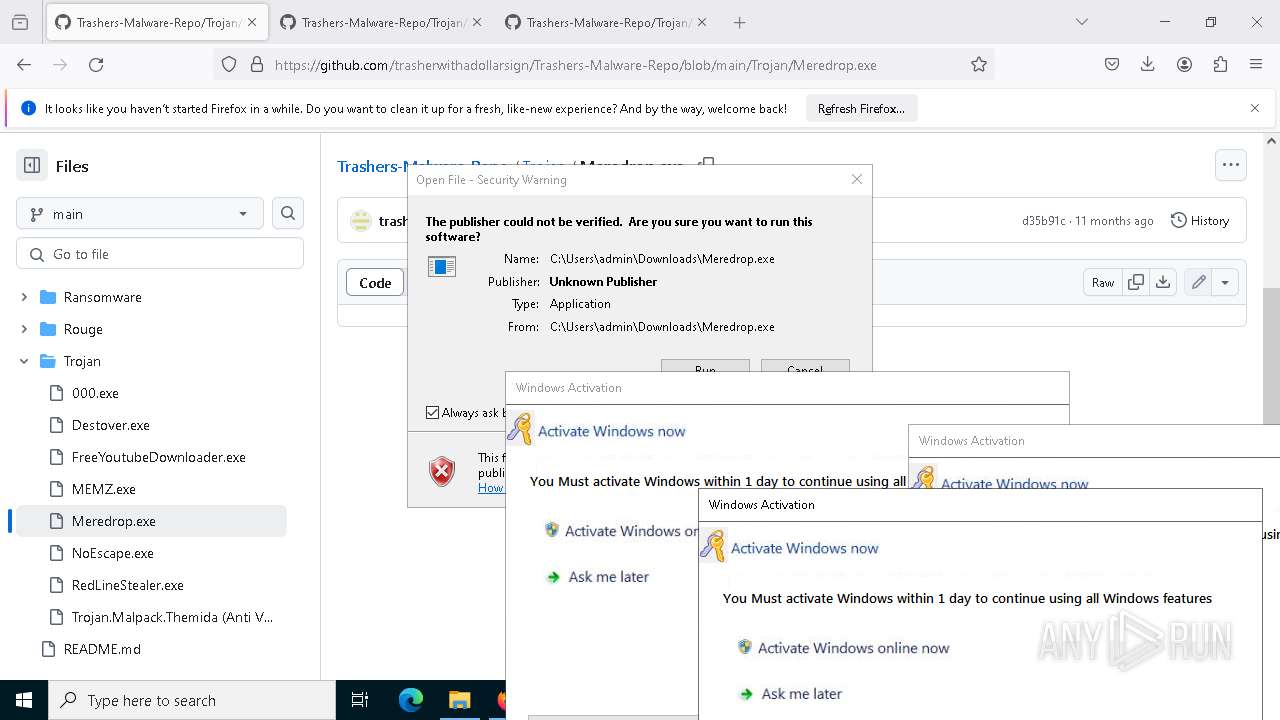
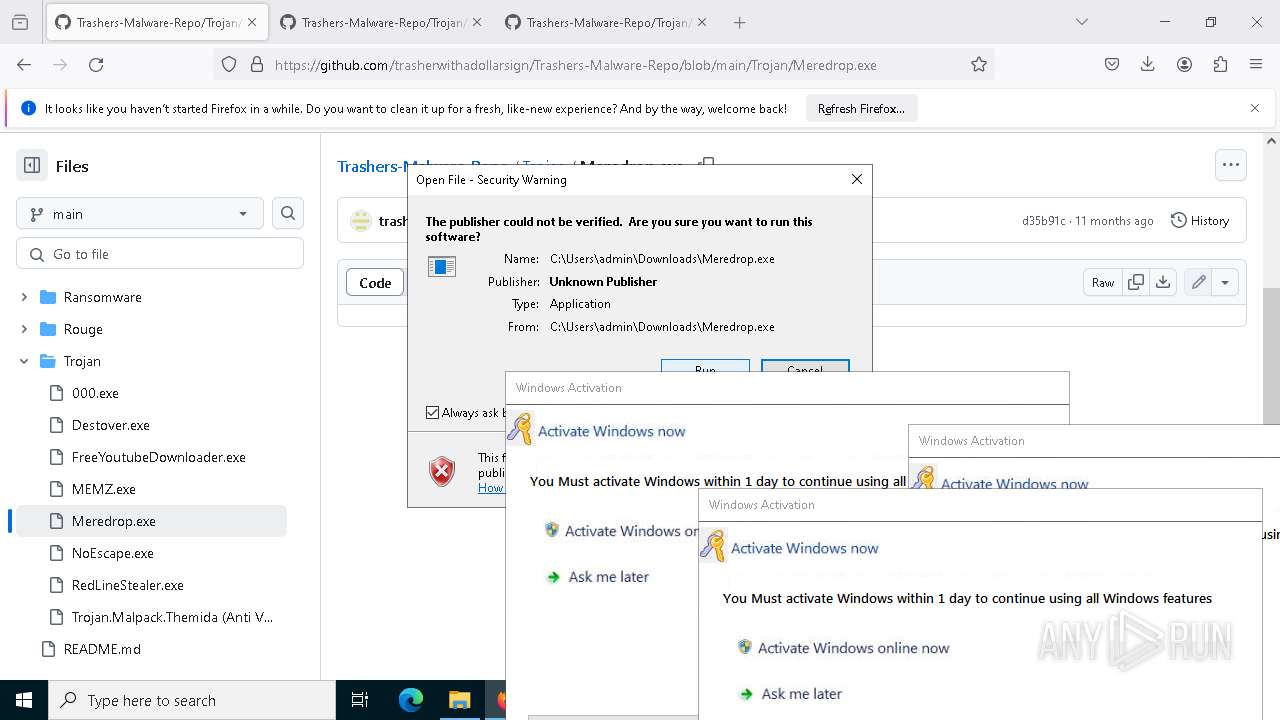
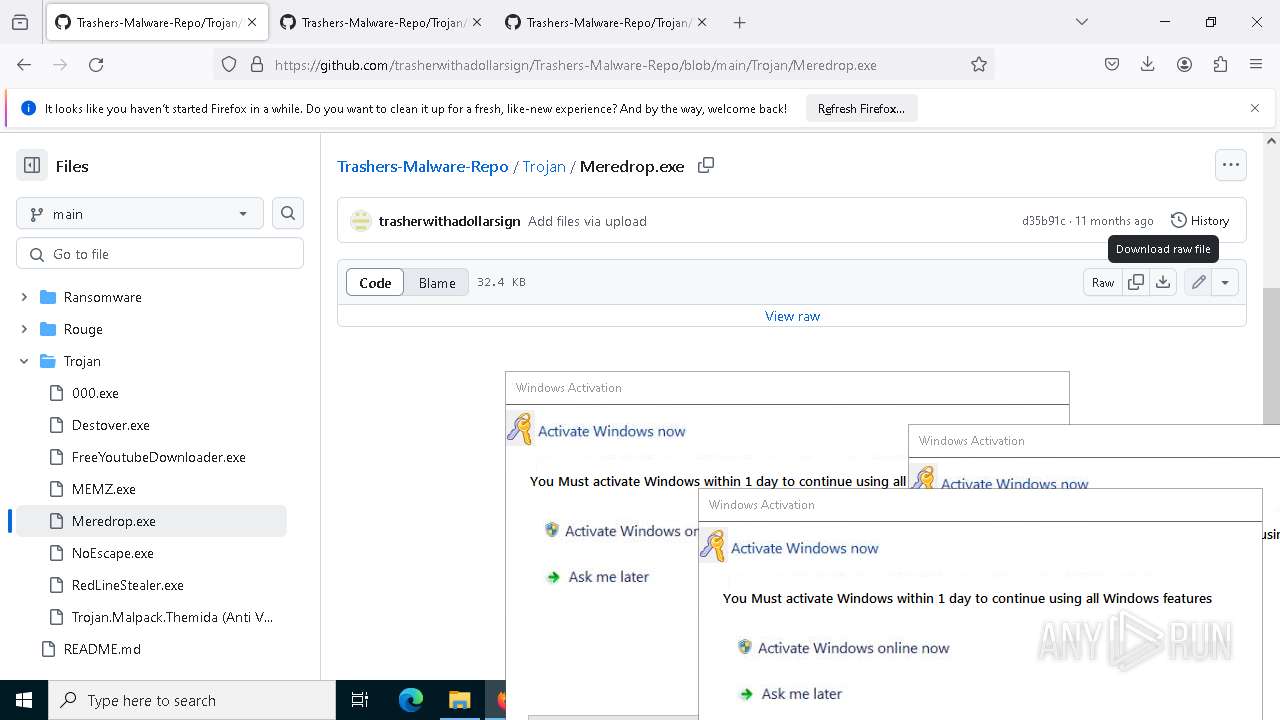
| URL: | https://github.com/trasherwithadollarsign/Trashers-Malware-Repo/tree/main/Trojan |
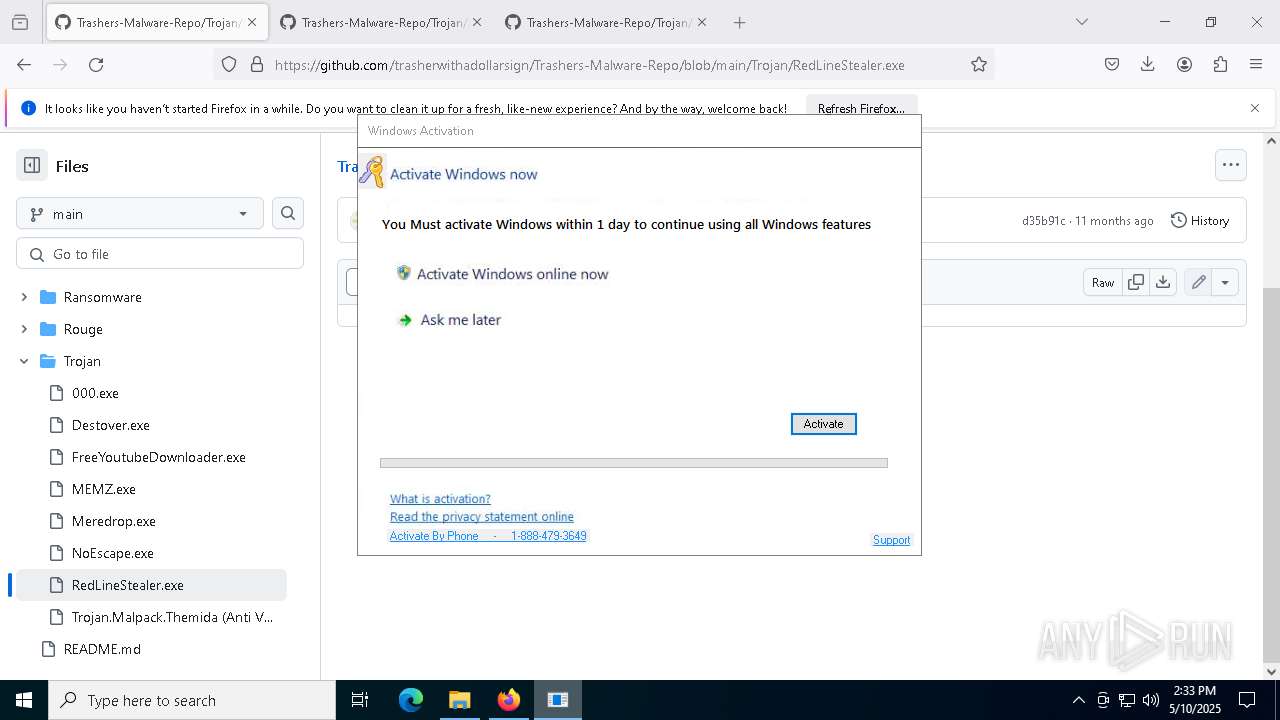
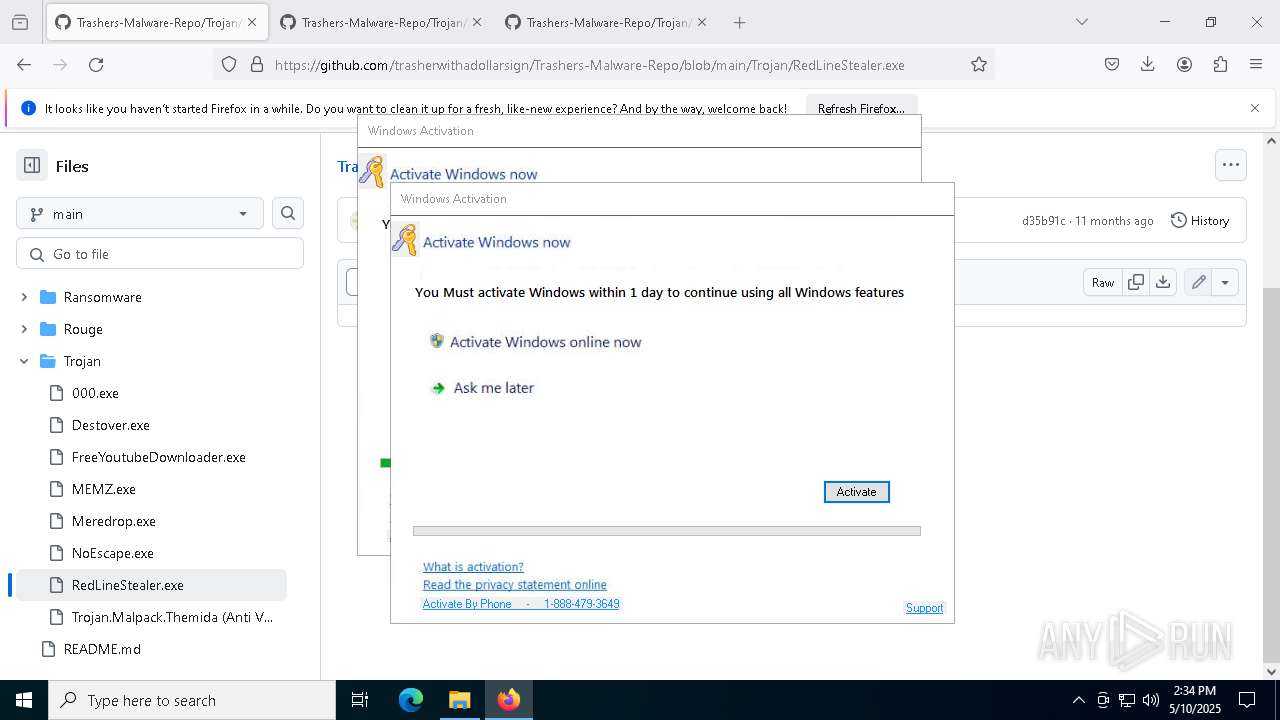
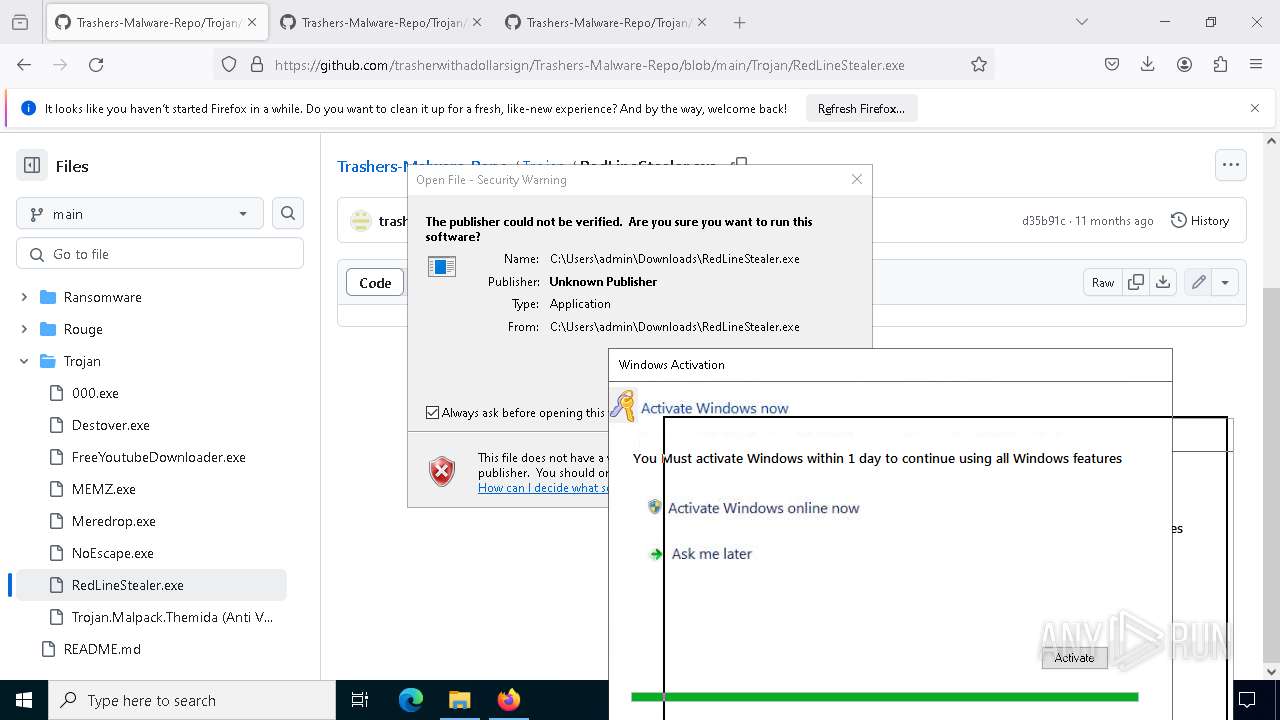
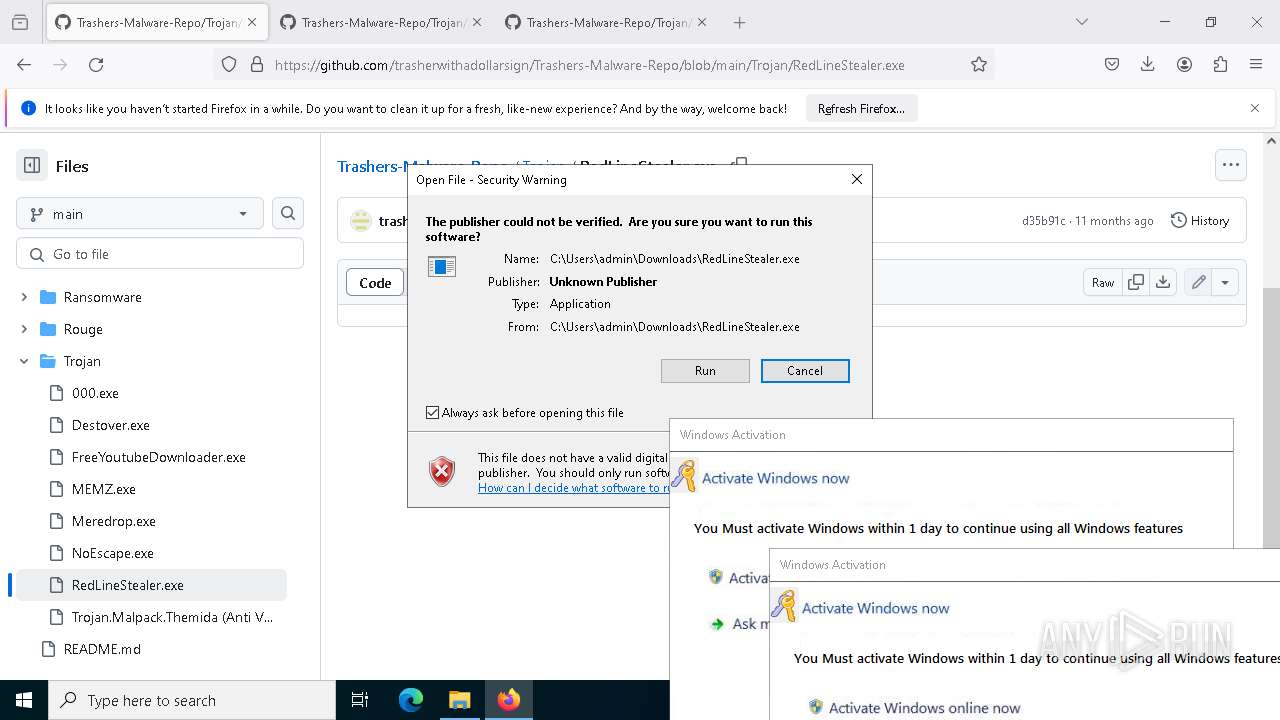
| Full analysis: | https://app.any.run/tasks/ac7cd379-b7b2-4efe-acb8-4a311941303f |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | May 10, 2025, 14:30:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 96EDDD552E98CC798E9569560B867F69 |
| SHA1: | 42F50CD27204F8F3D20177097066553601C24789 |
| SHA256: | 6DE3829C04F39924A22B5E72C1D5ED0108BFF9004B3BBE3FD4F3057D34C21523 |
| SSDEEP: | 3:N8tEdhXEWSLJMWMIq17EcEXFCRQATRKsPi:2uEWTLIq1dVTRKsPi |
MALICIOUS
UMBRAL has been detected (YARA)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Changes the autorun value in the registry
- FreeYoutubeDownloader.exe (PID: 8056)
XORed URL has been found (YARA)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Adds path to the Windows Defender exclusion list
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Changes Windows Defender settings
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7472)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7472)
Changes Controlled Folder Access settings
- powershell.exe (PID: 7472)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7472)
Changes settings for real-time protection
- powershell.exe (PID: 7472)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 7472)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7472)
UMBRALSTEALER has been detected (SURICATA)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
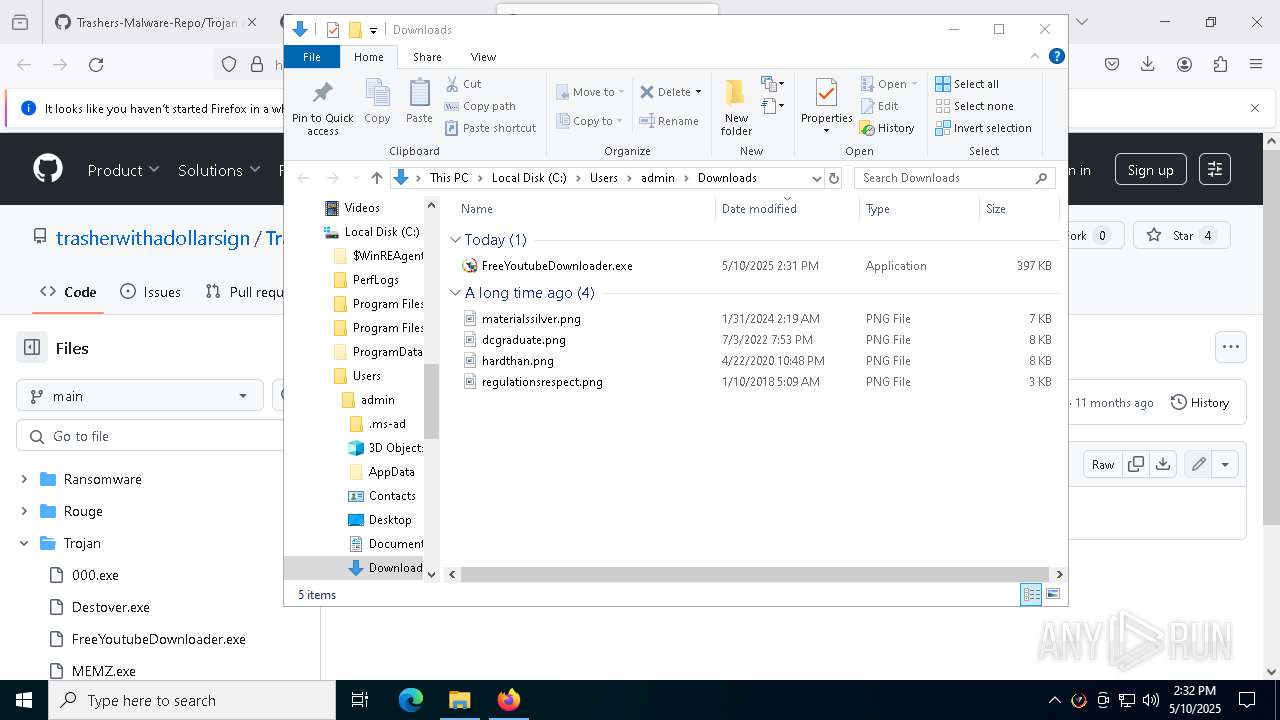
Starts CMD.EXE for self-deleting
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
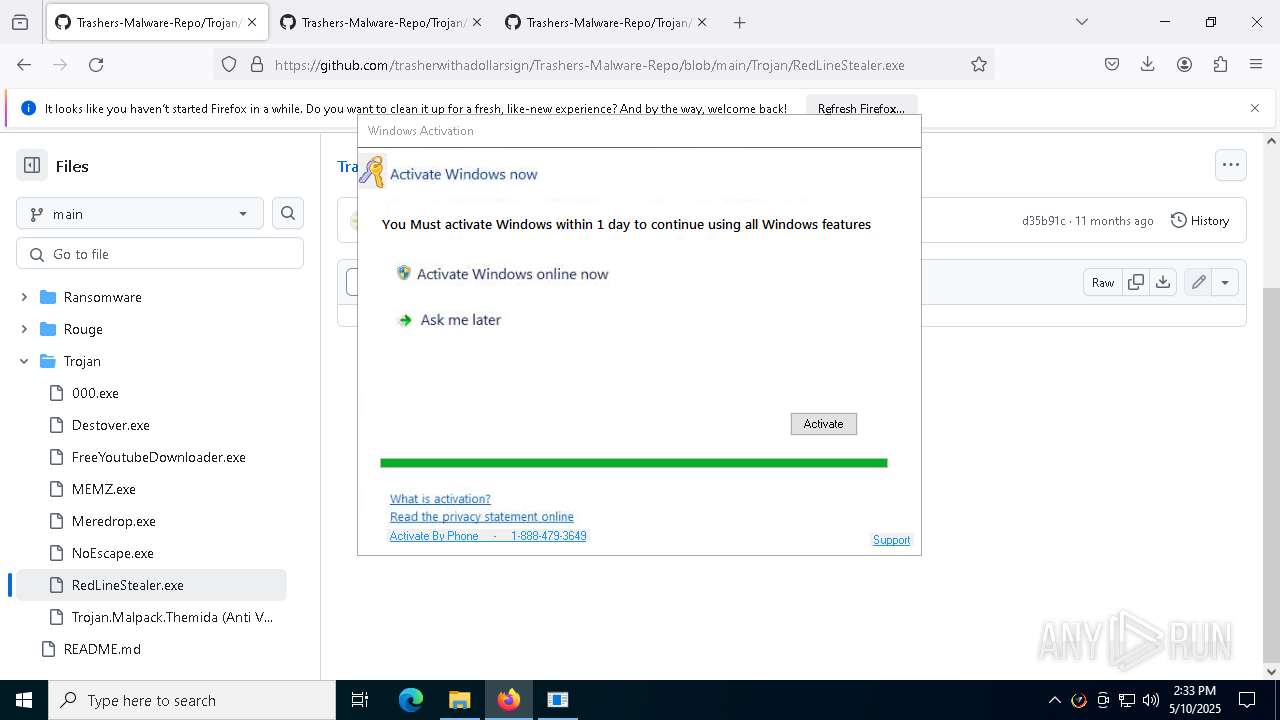
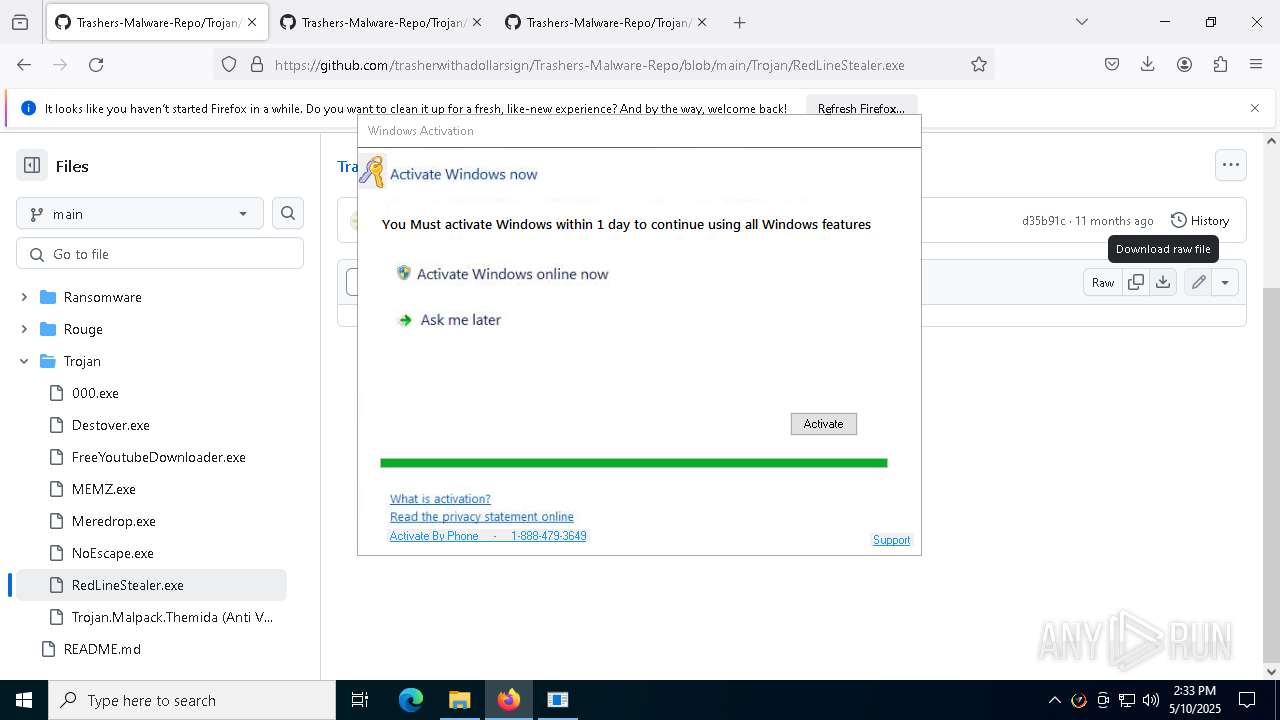
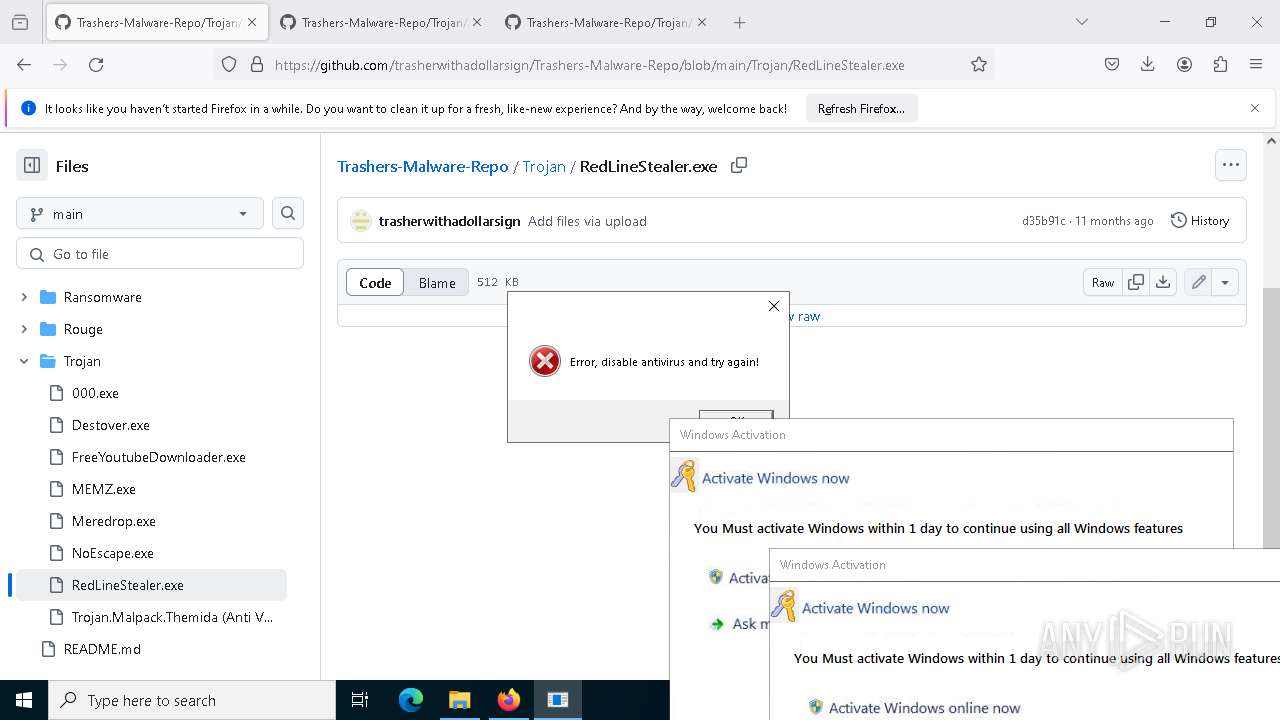
REDLINE has been detected (YARA)
- RegAsm.exe (PID: 2772)
GENERIC has been found (auto)
- firefox.exe (PID: 7272)
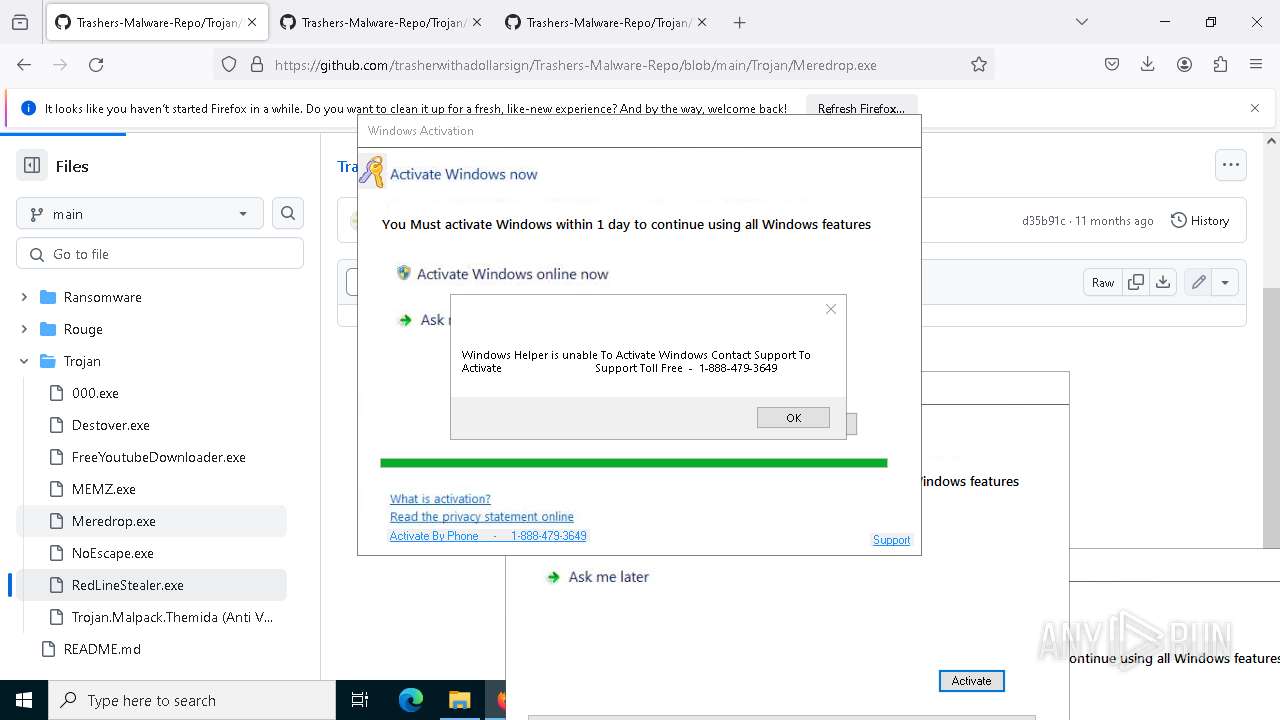
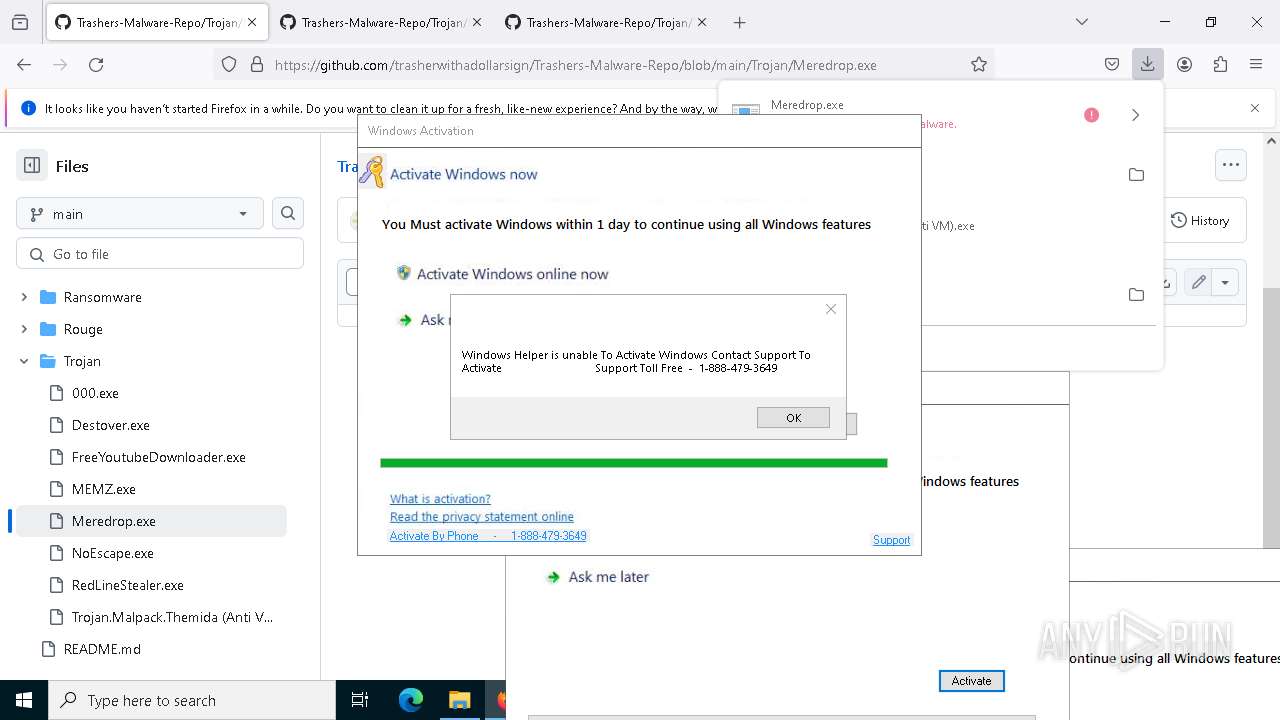
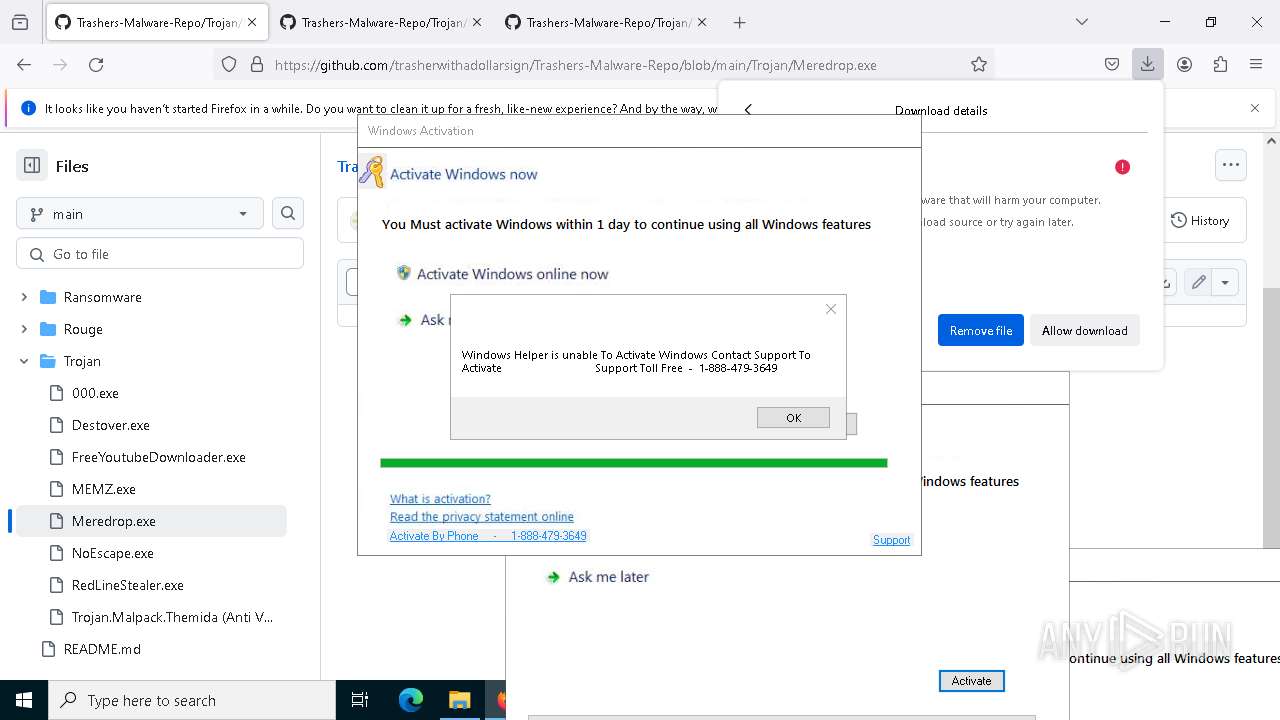
SMBSCAN has been detected (SURICATA)
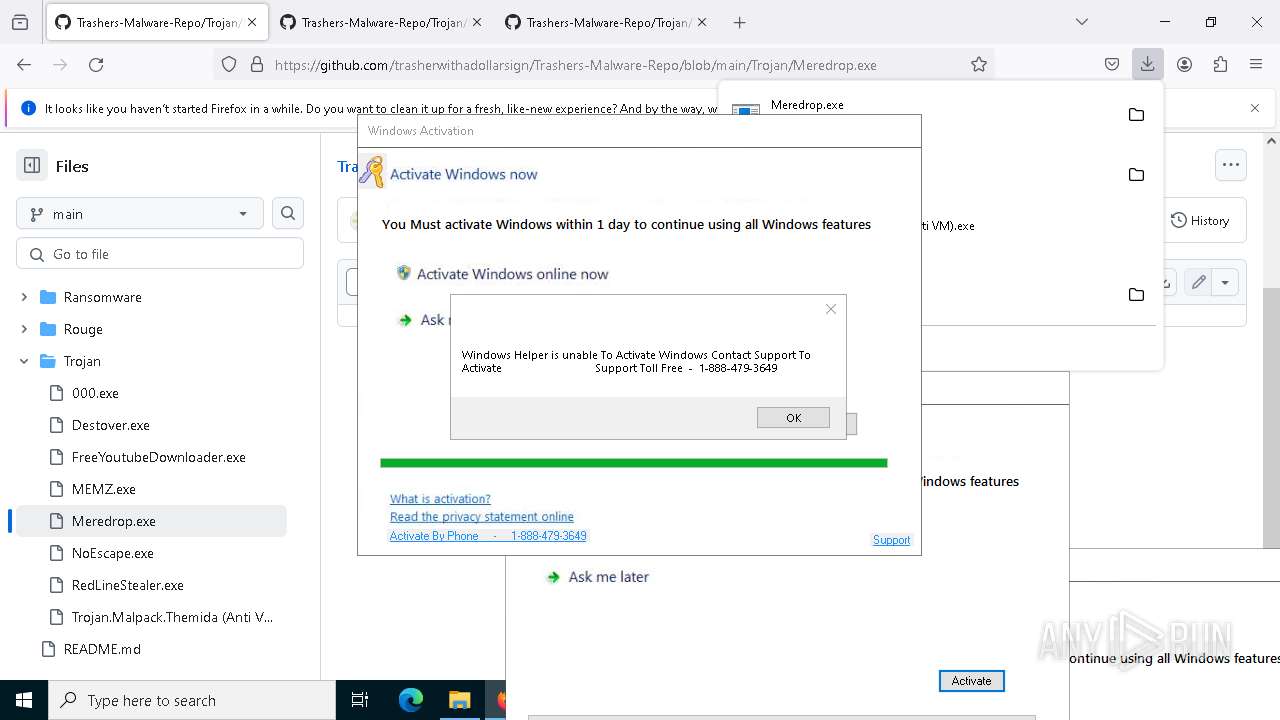
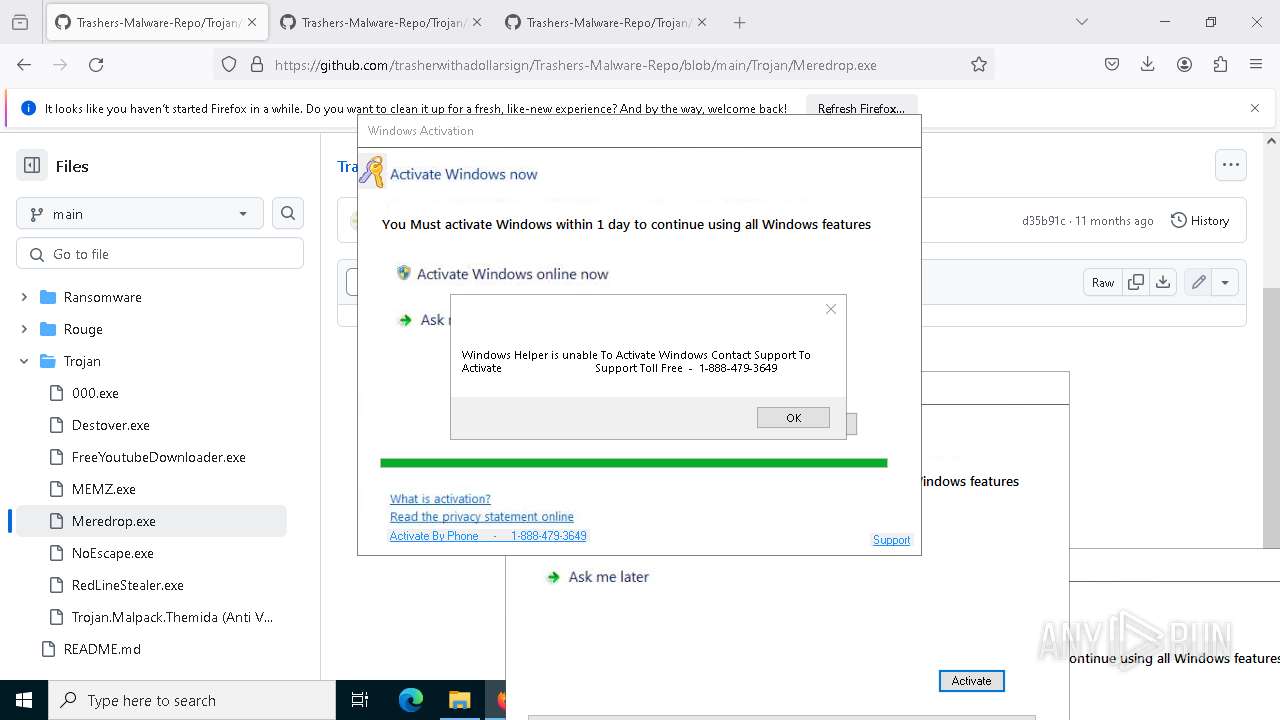
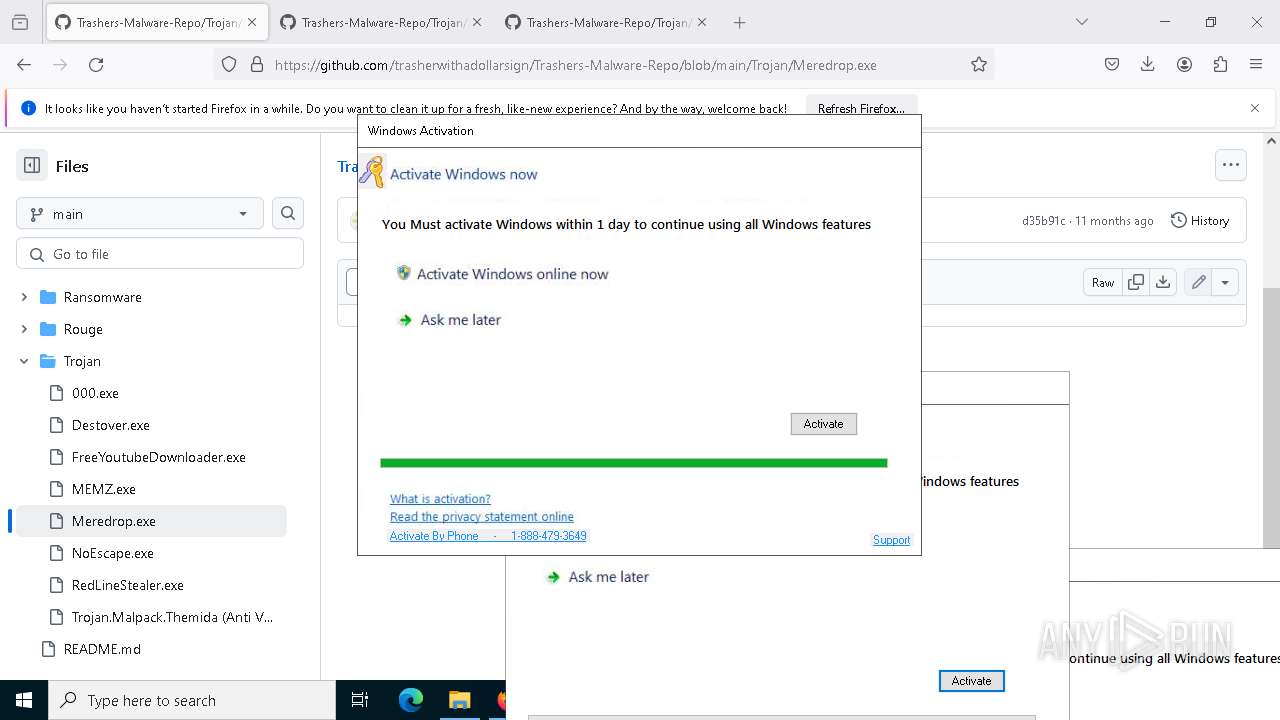
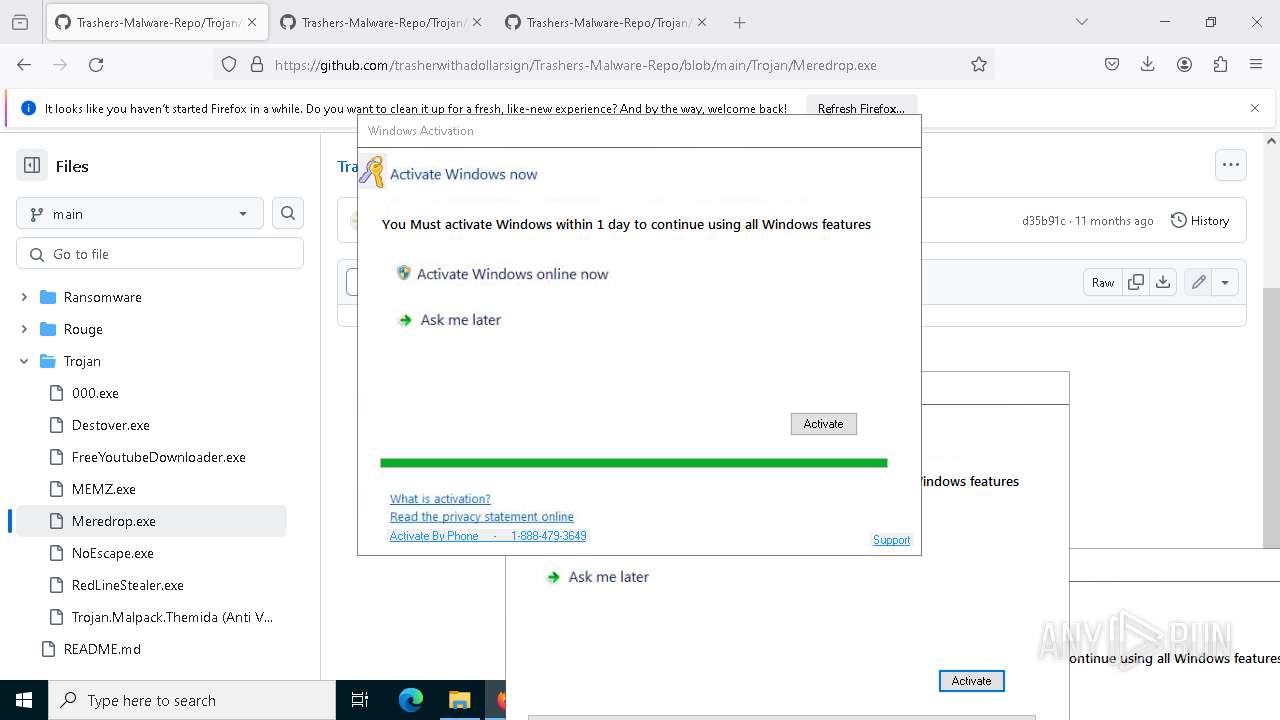
- Meredrop.exe (PID: 4224)
Attempt to connect to SMB server
- System (PID: 4)
Attempting to scan the network
- Meredrop.exe (PID: 4224)
SUSPICIOUS
Reads the BIOS version
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
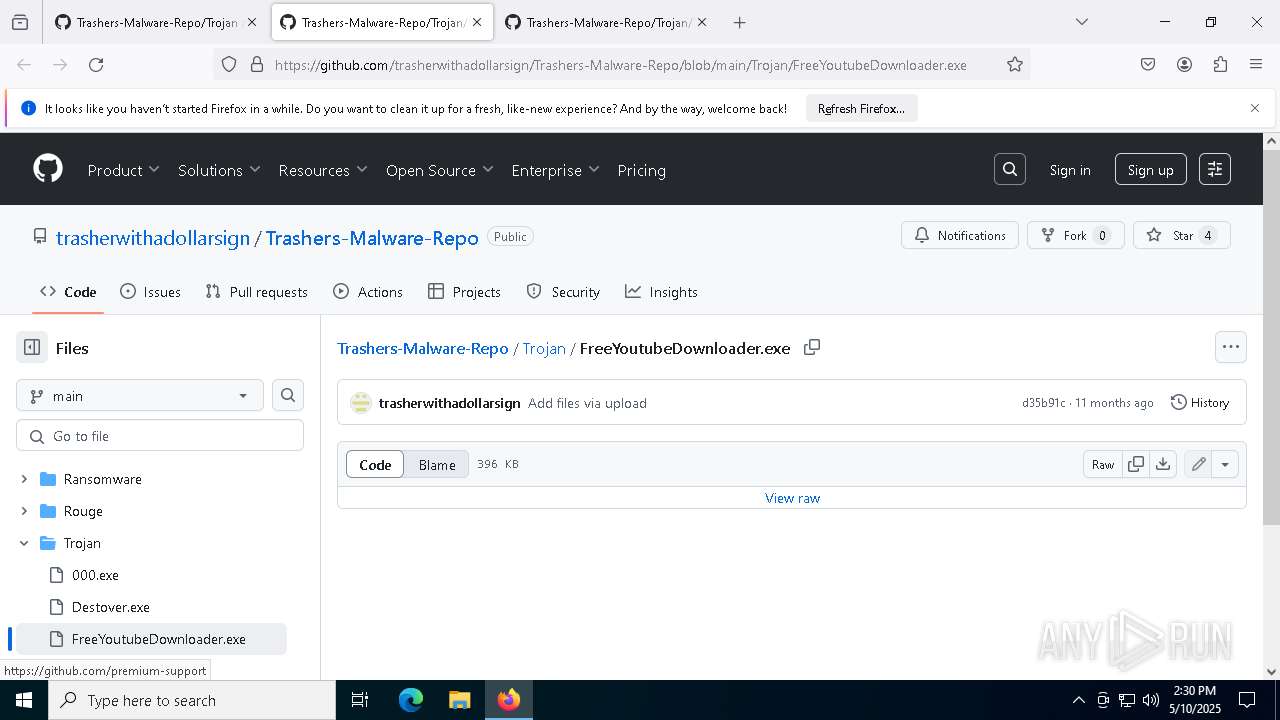
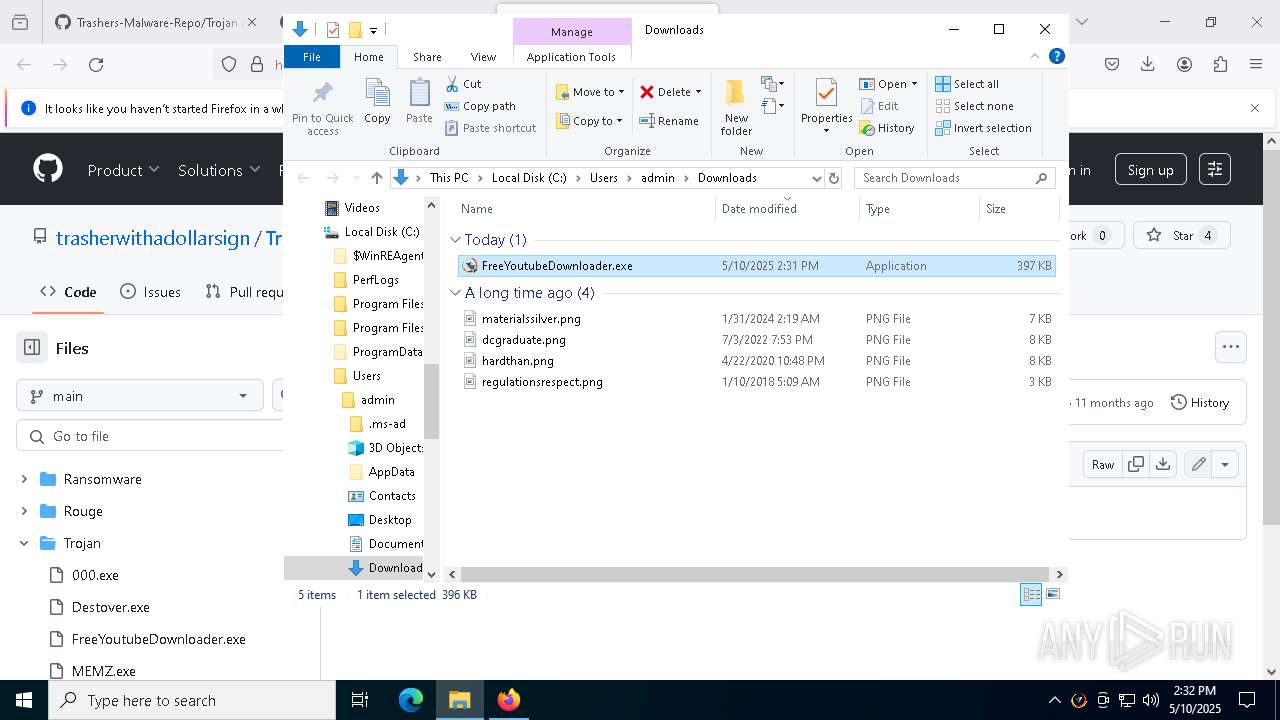
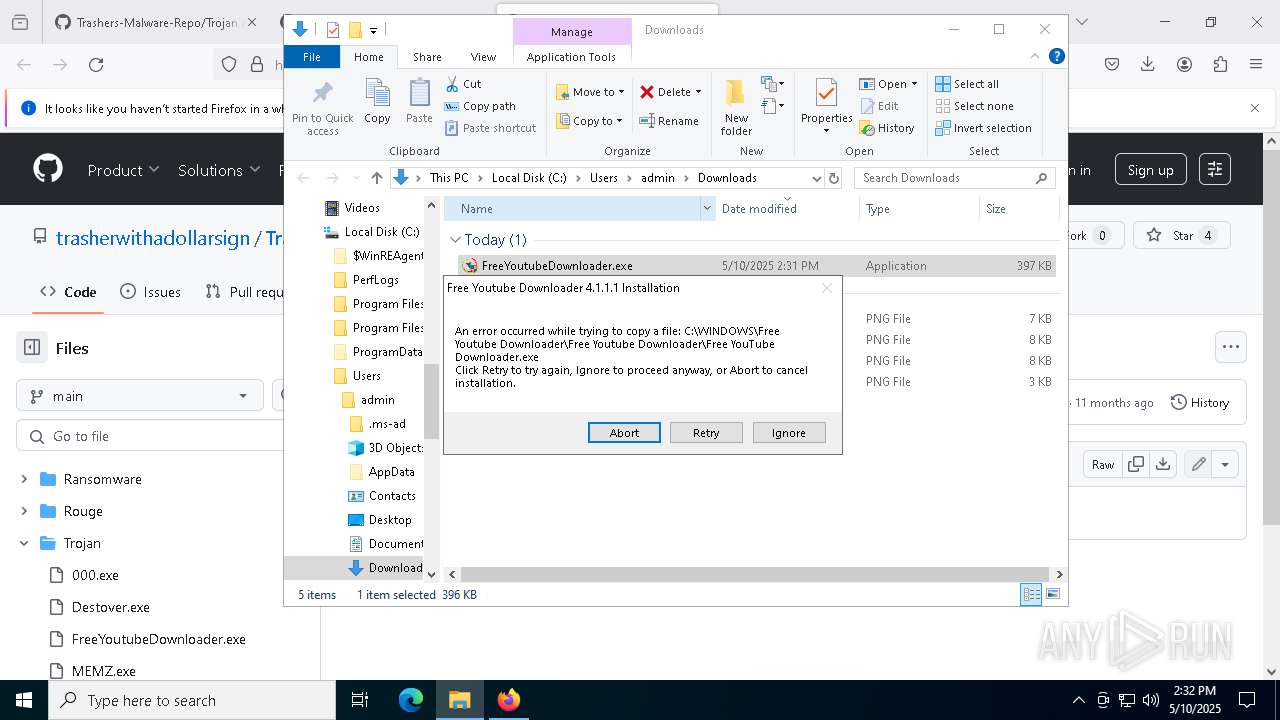
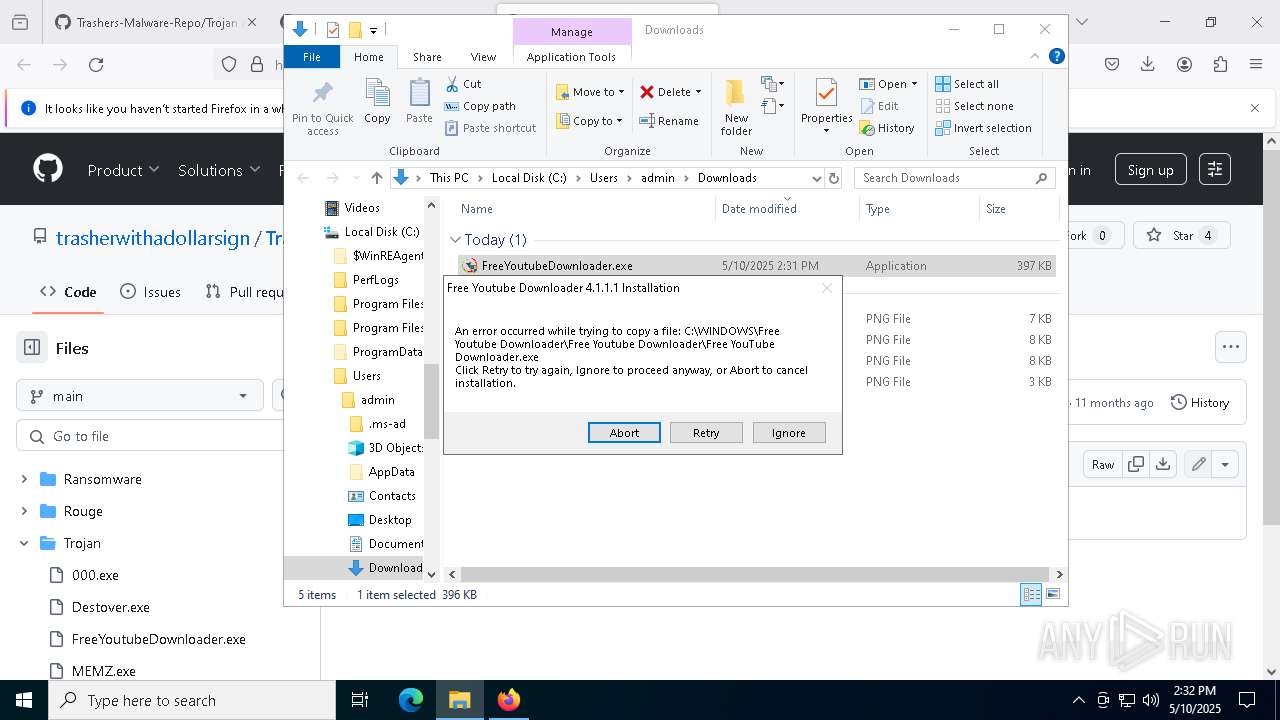
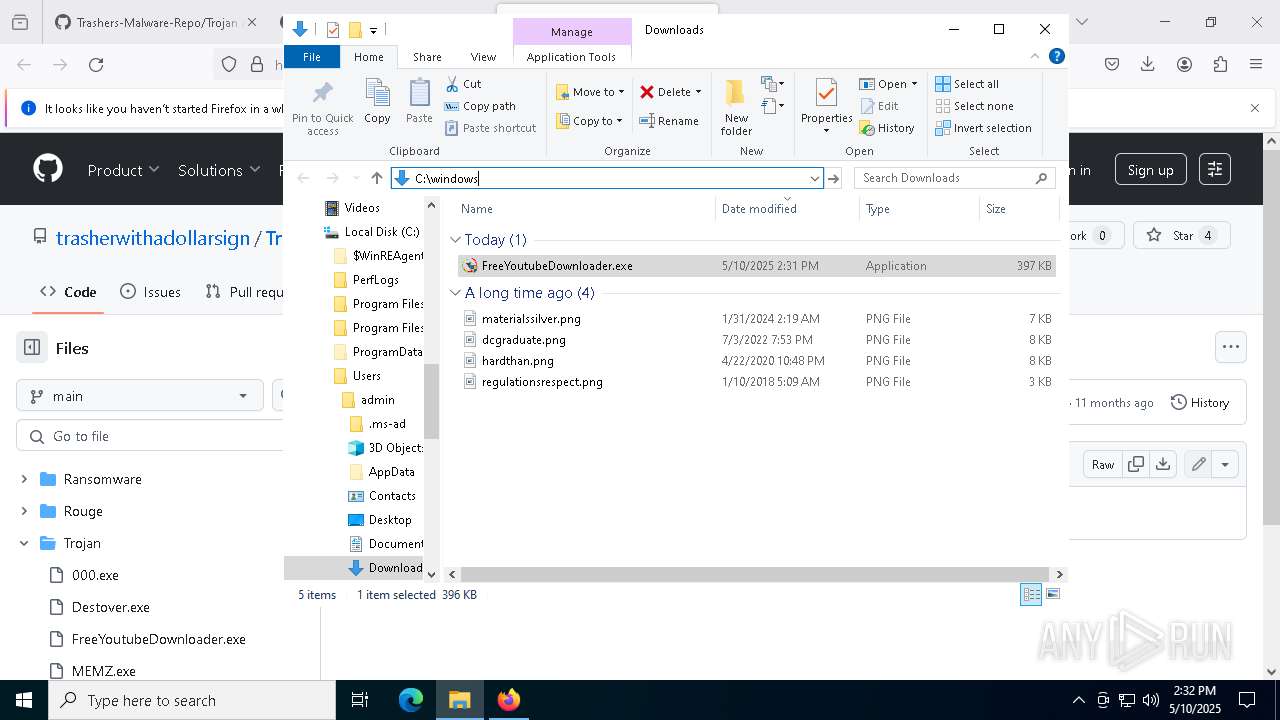
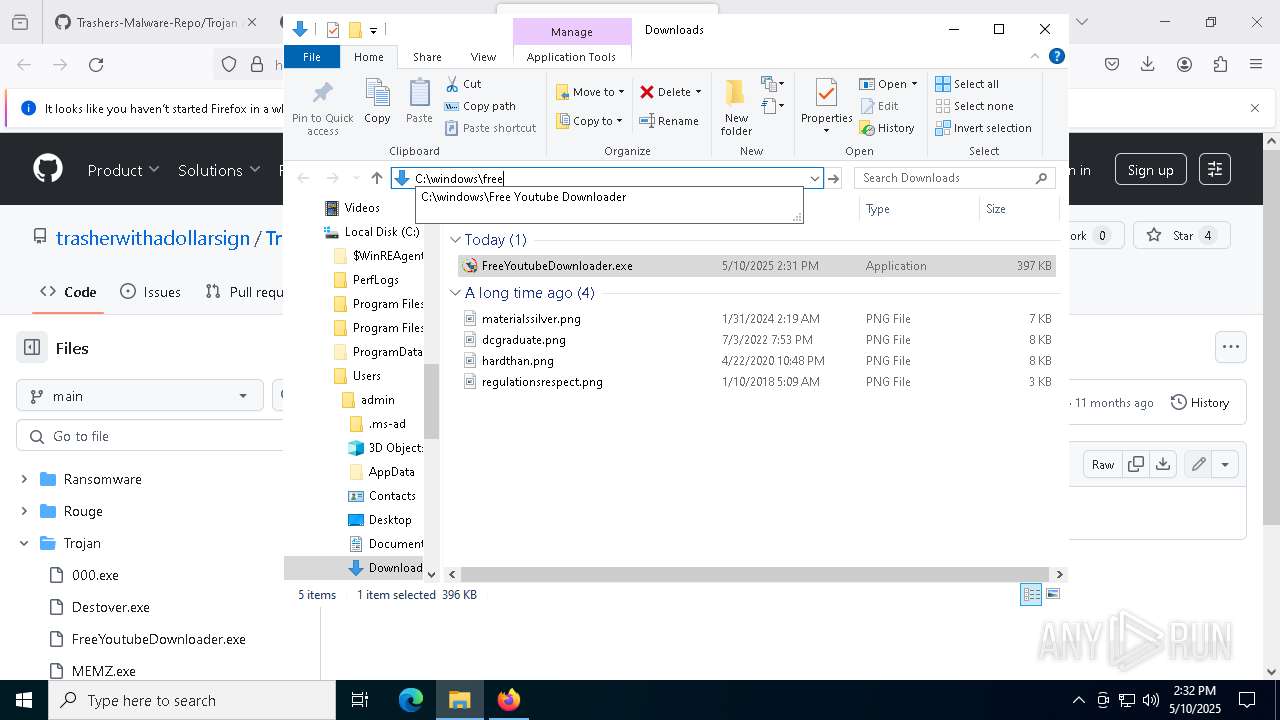
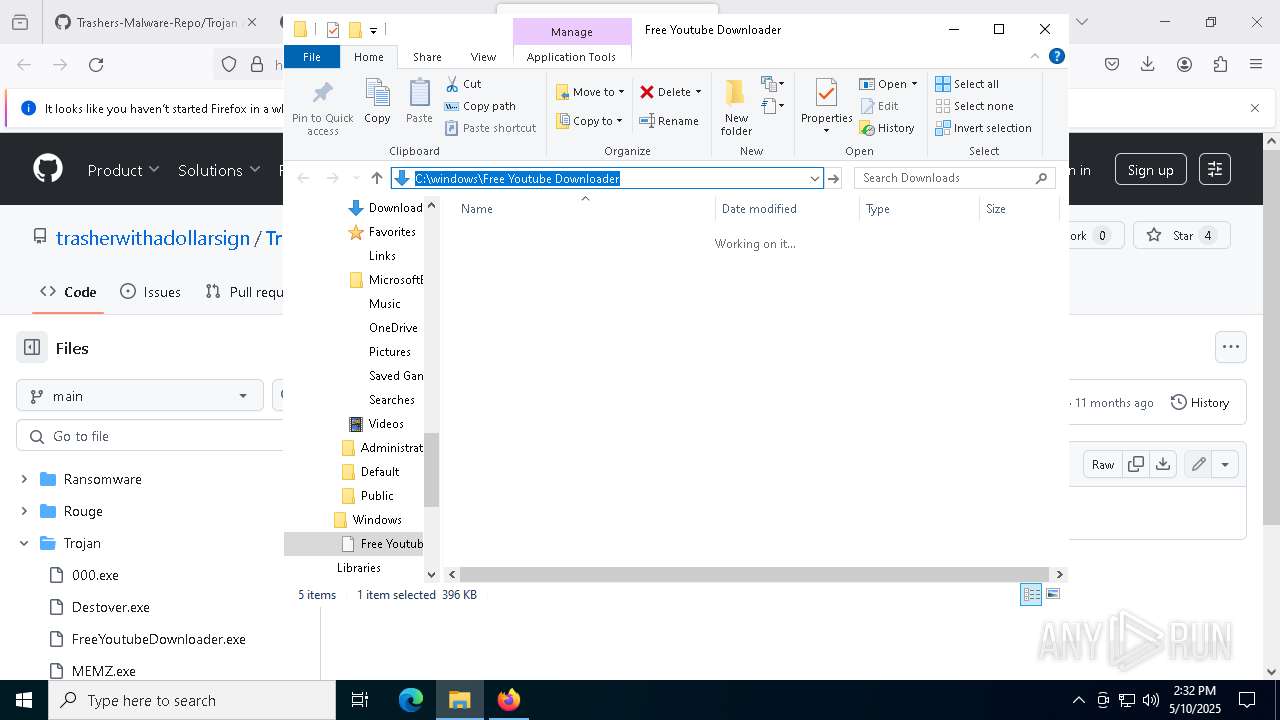
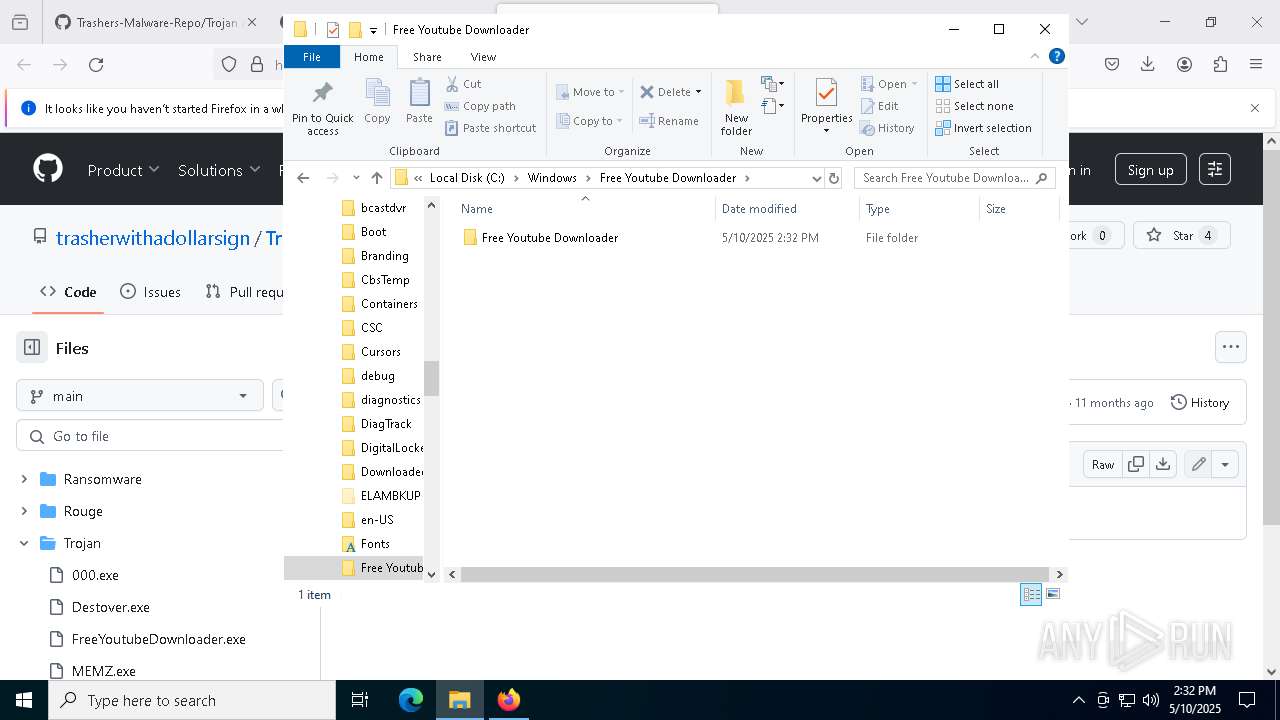
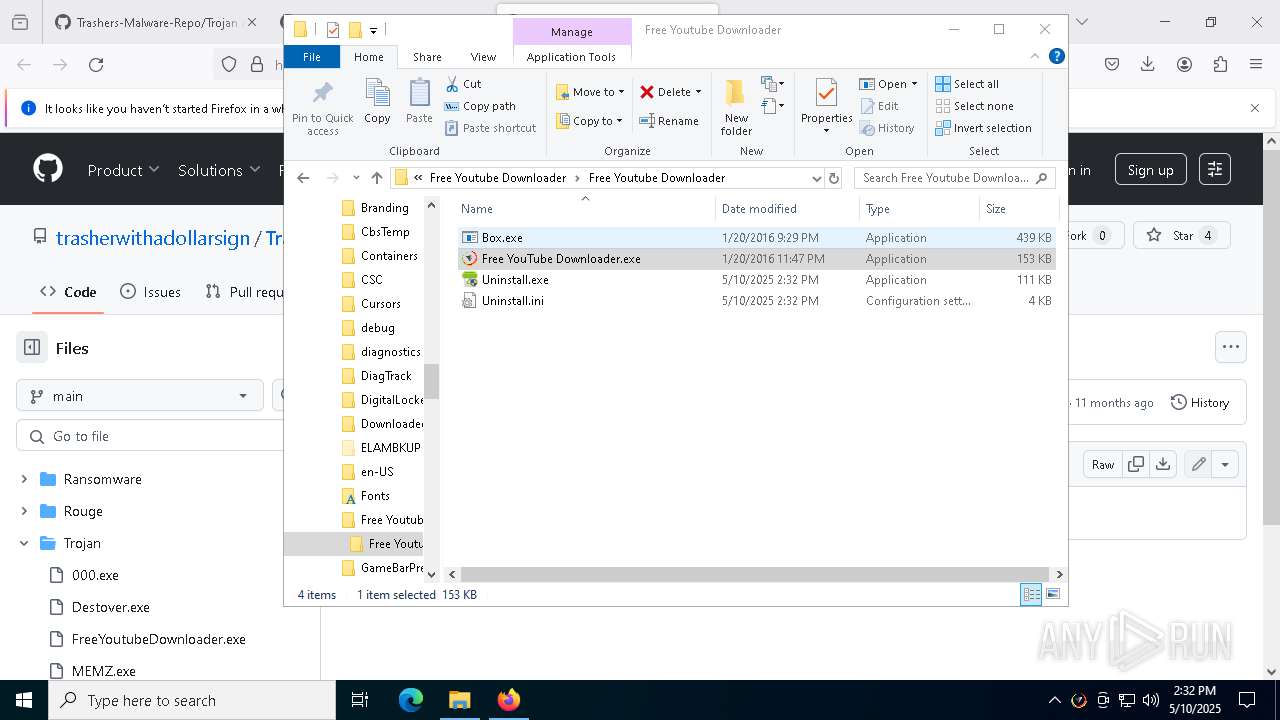
Executable content was dropped or overwritten
- FreeYoutubeDownloader.exe (PID: 8056)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
- FreeYoutubeDownloader.exe (PID: 1600)
Reads security settings of Internet Explorer
- FreeYoutubeDownloader.exe (PID: 8056)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
Creates a software uninstall entry
- FreeYoutubeDownloader.exe (PID: 8056)
Uses WMIC.EXE to obtain Windows Installer data
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 5352)
- WMIC.exe (PID: 2392)
Checks for external IP
- svchost.exe (PID: 2196)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Uses ATTRIB.EXE to modify file attributes
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Starts POWERSHELL.EXE for commands execution
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Script adds exclusion path to Windows Defender
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Script disables Windows Defender's IPS
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Script disables Windows Defender's real-time protection
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Uses WMIC.EXE to obtain operating system information
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Uses WMIC.EXE to obtain computer system information
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Uses WMIC.EXE to obtain a list of video controllers
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
The process connected to a server suspected of theft
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Starts CMD.EXE for commands execution
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Executes application which crashes
- RedLineStealer.exe (PID: 2968)
Connects to unusual port
- RegAsm.exe (PID: 2772)
Potential Corporate Privacy Violation
- System (PID: 4)
- Meredrop.exe (PID: 4224)
There is functionality for taking screenshot (YARA)
- RegAsm.exe (PID: 2772)
Application launched itself
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
INFO
Application launched itself
- firefox.exe (PID: 7272)
- firefox.exe (PID: 7252)
- msedge.exe (PID: 2236)
- msedge.exe (PID: 8248)
- msedge.exe (PID: 8480)
Reads the computer name
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- Free YouTube Downloader.exe (PID: 7020)
- FreeYoutubeDownloader.exe (PID: 8056)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
The sample compiled with english language support
- firefox.exe (PID: 7272)
Checks supported languages
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- FreeYoutubeDownloader.exe (PID: 8056)
- Free YouTube Downloader.exe (PID: 7020)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
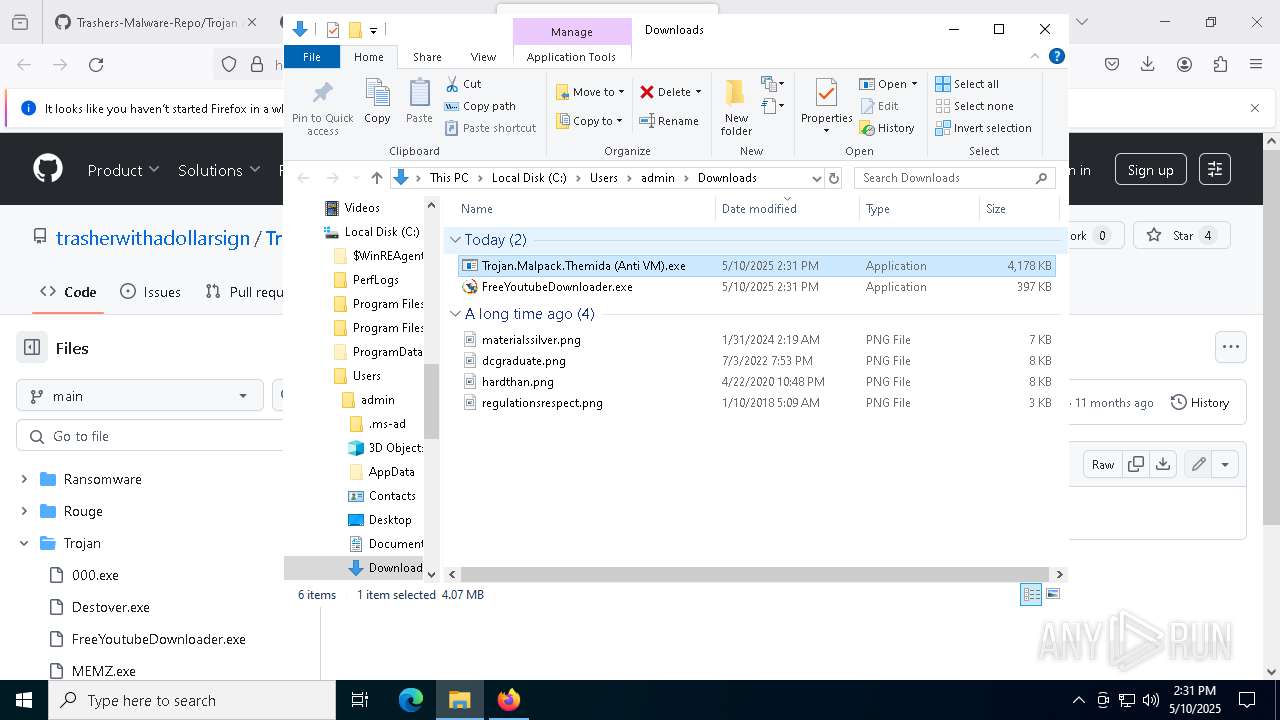
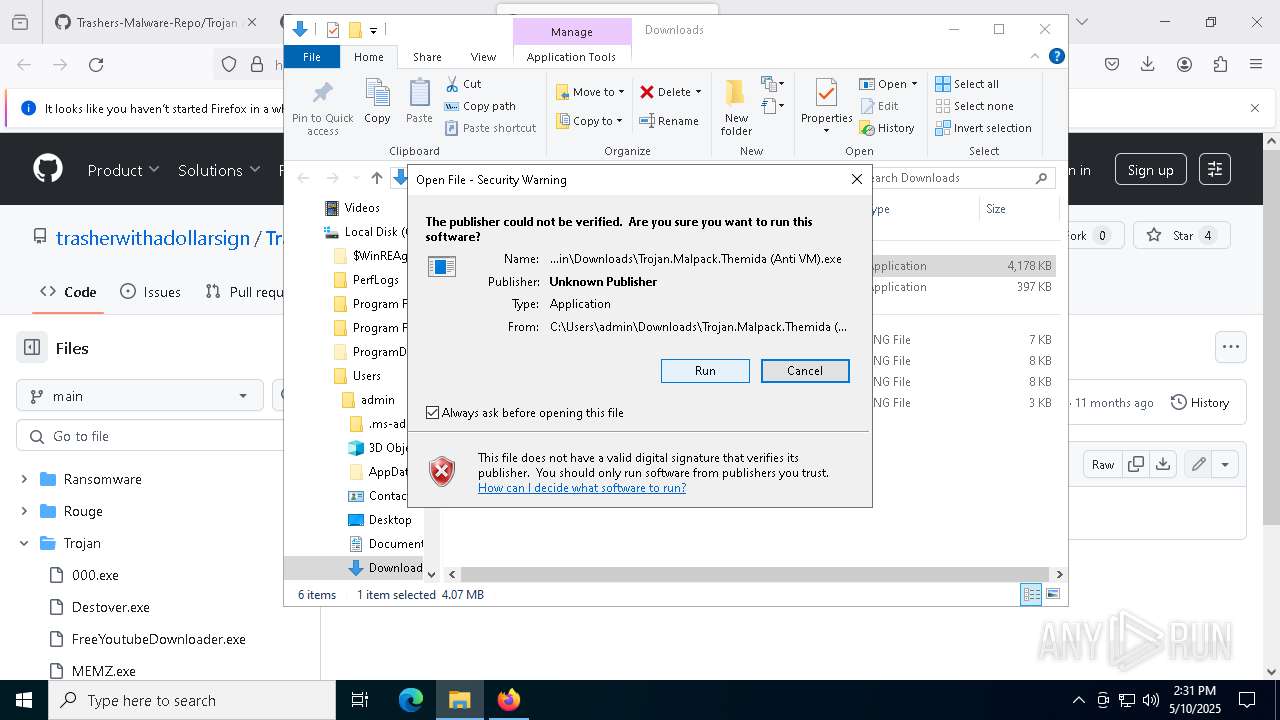
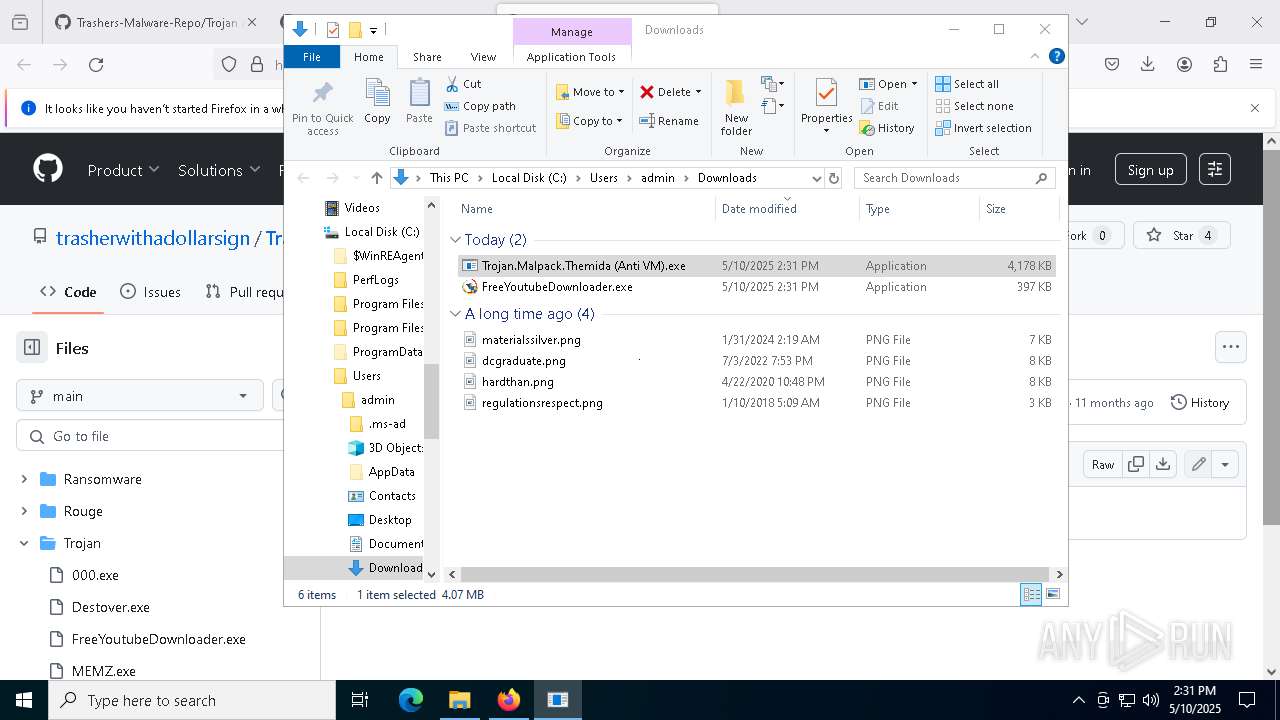
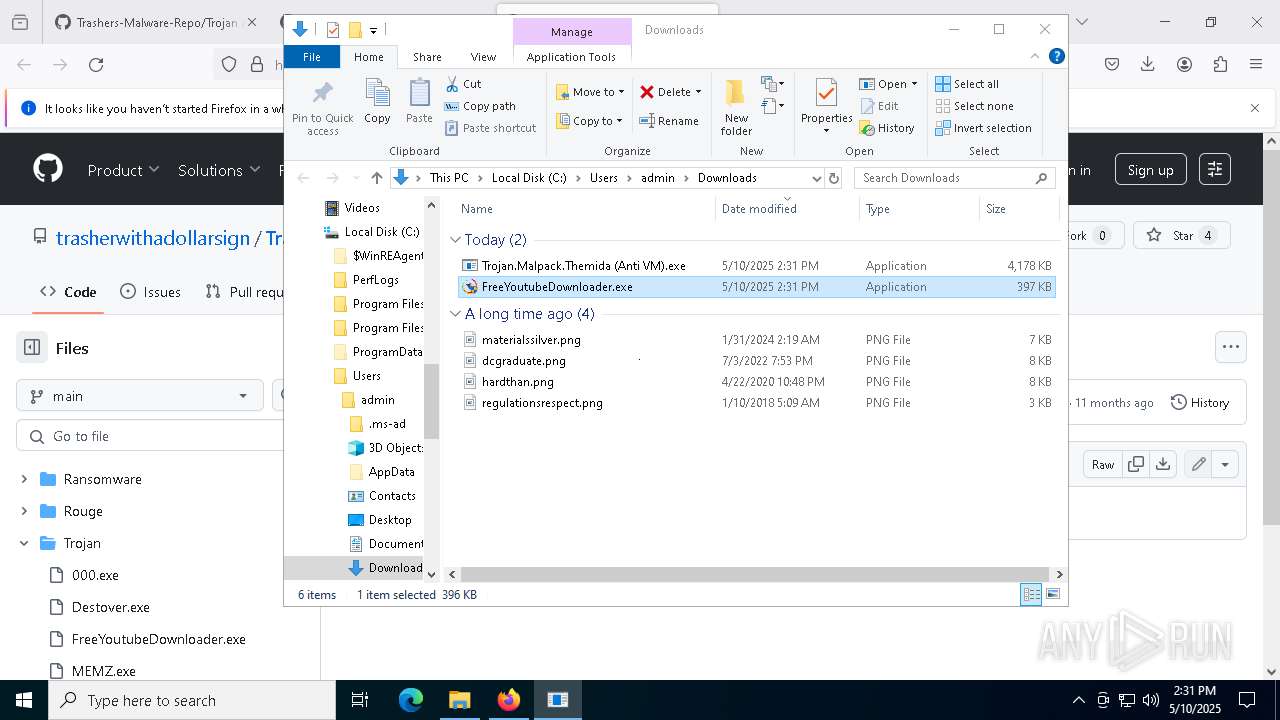
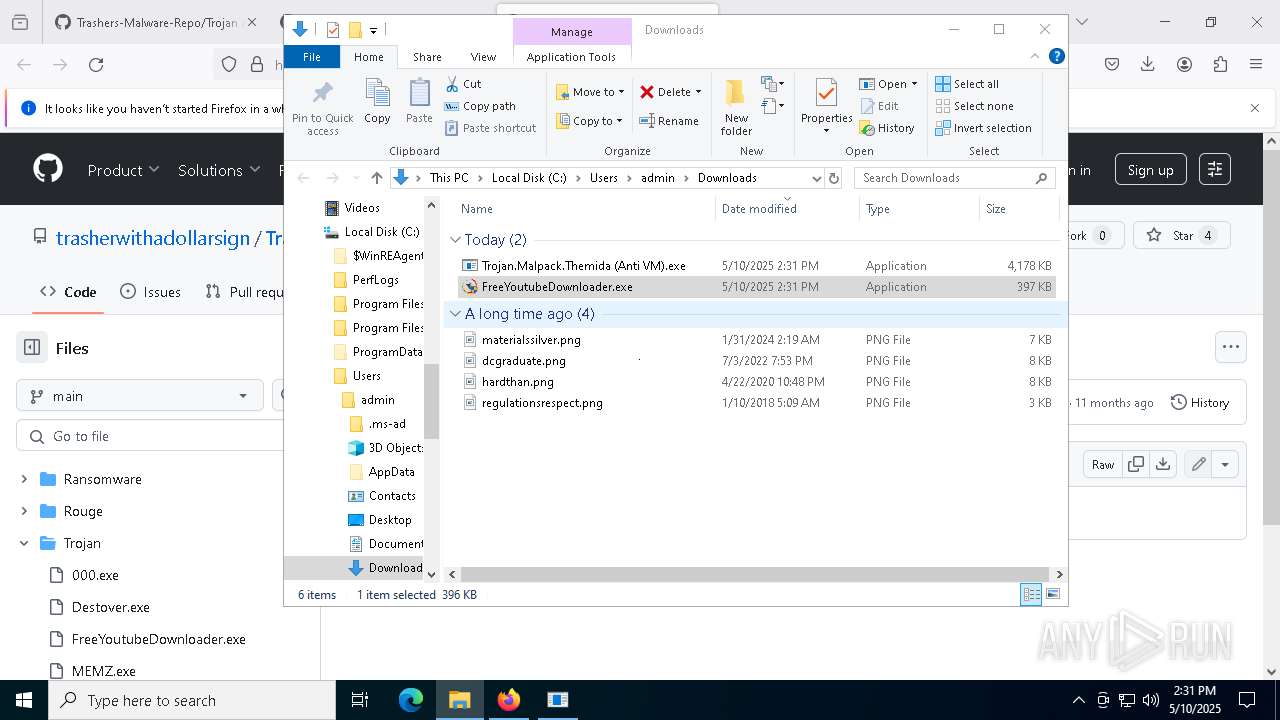
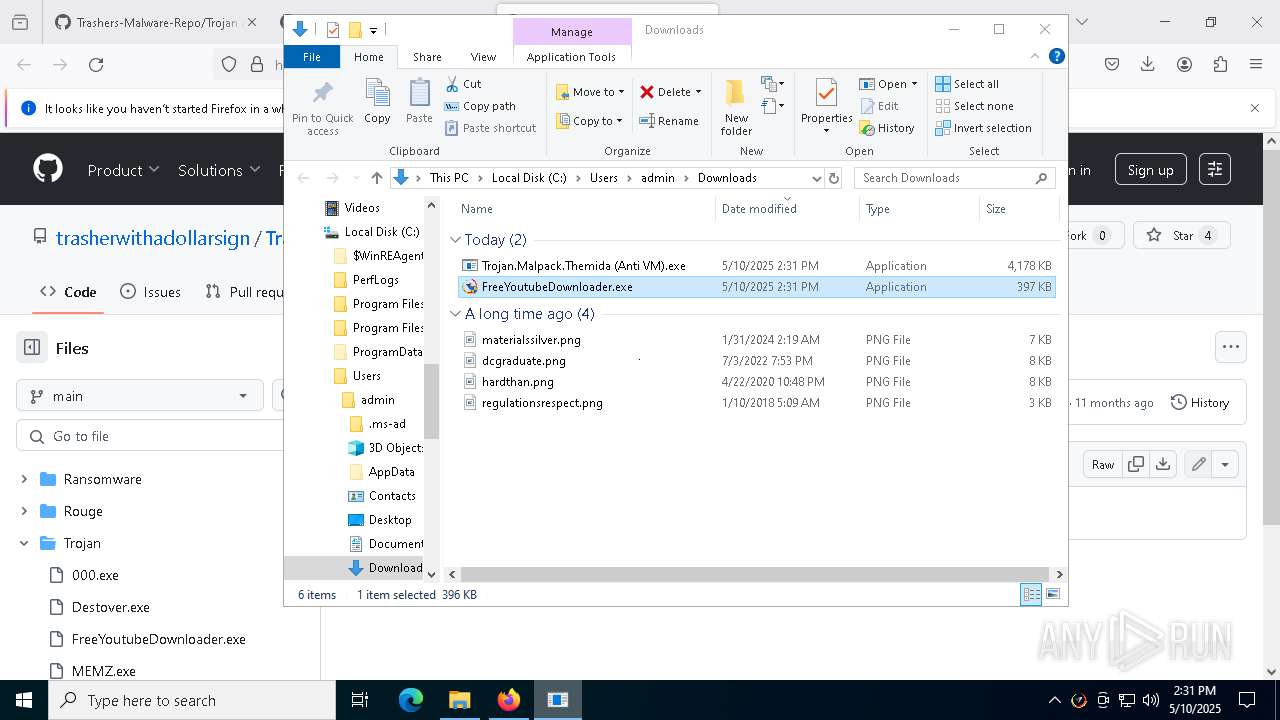
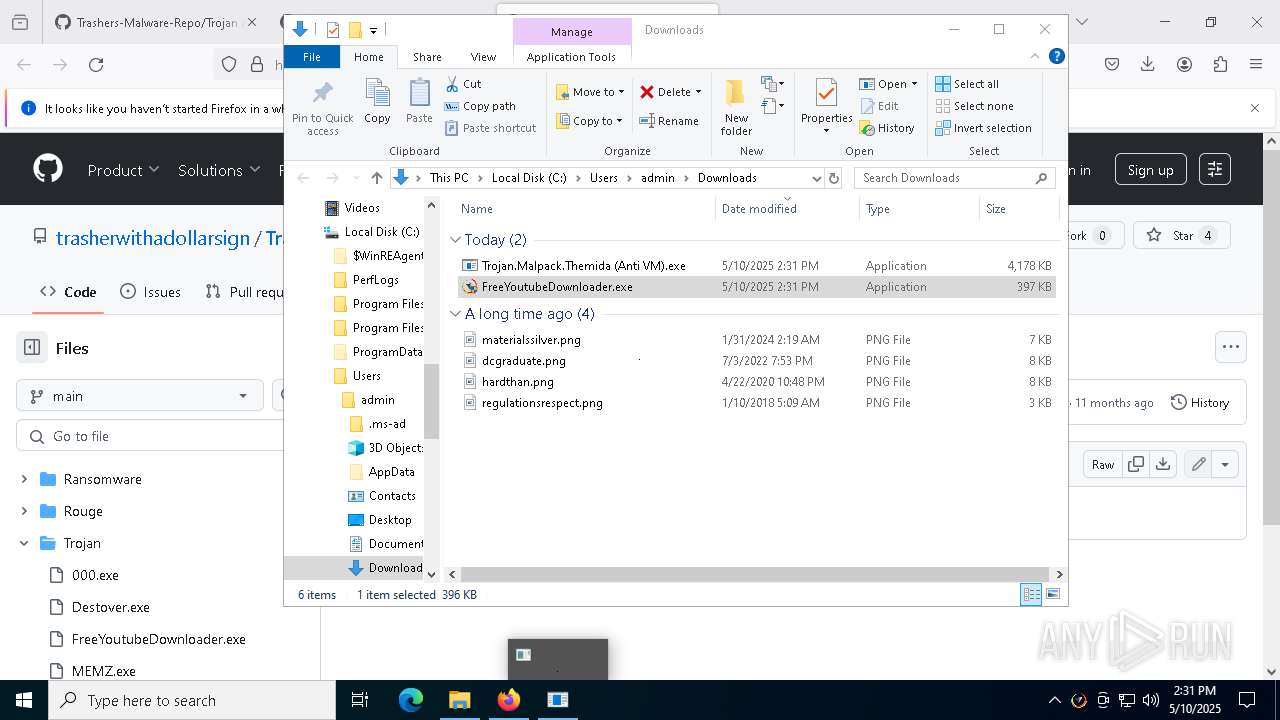
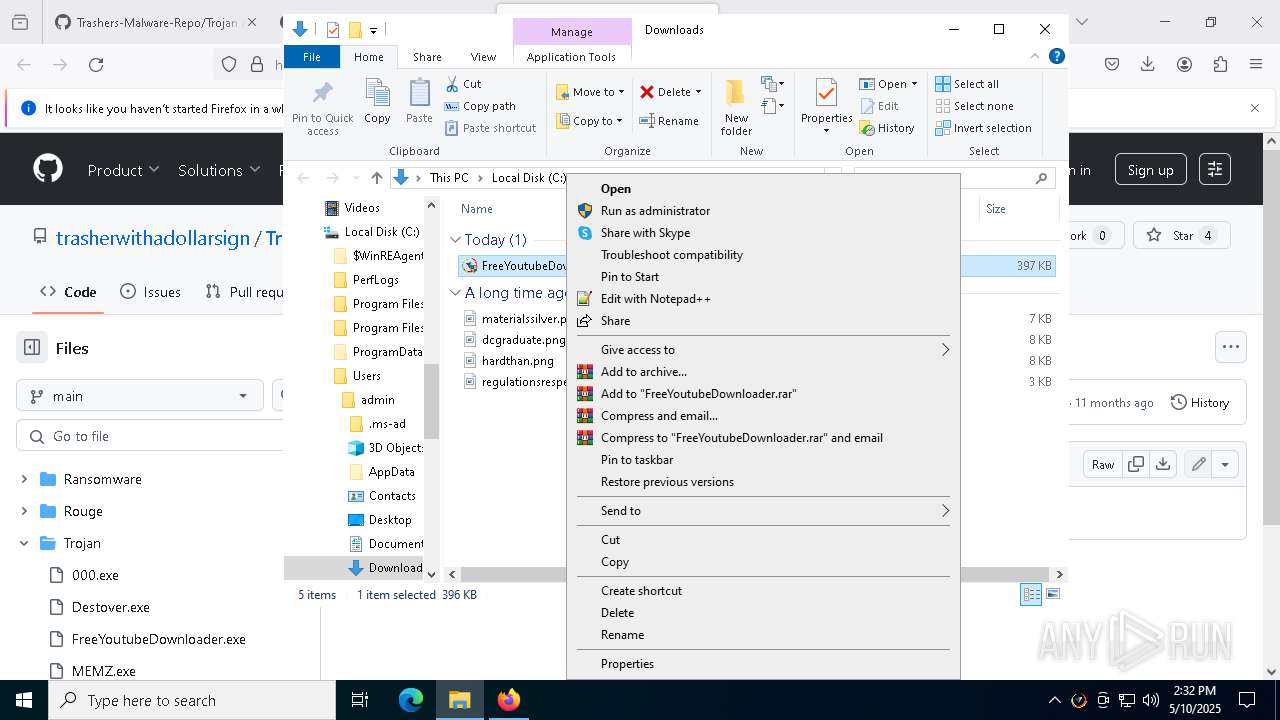
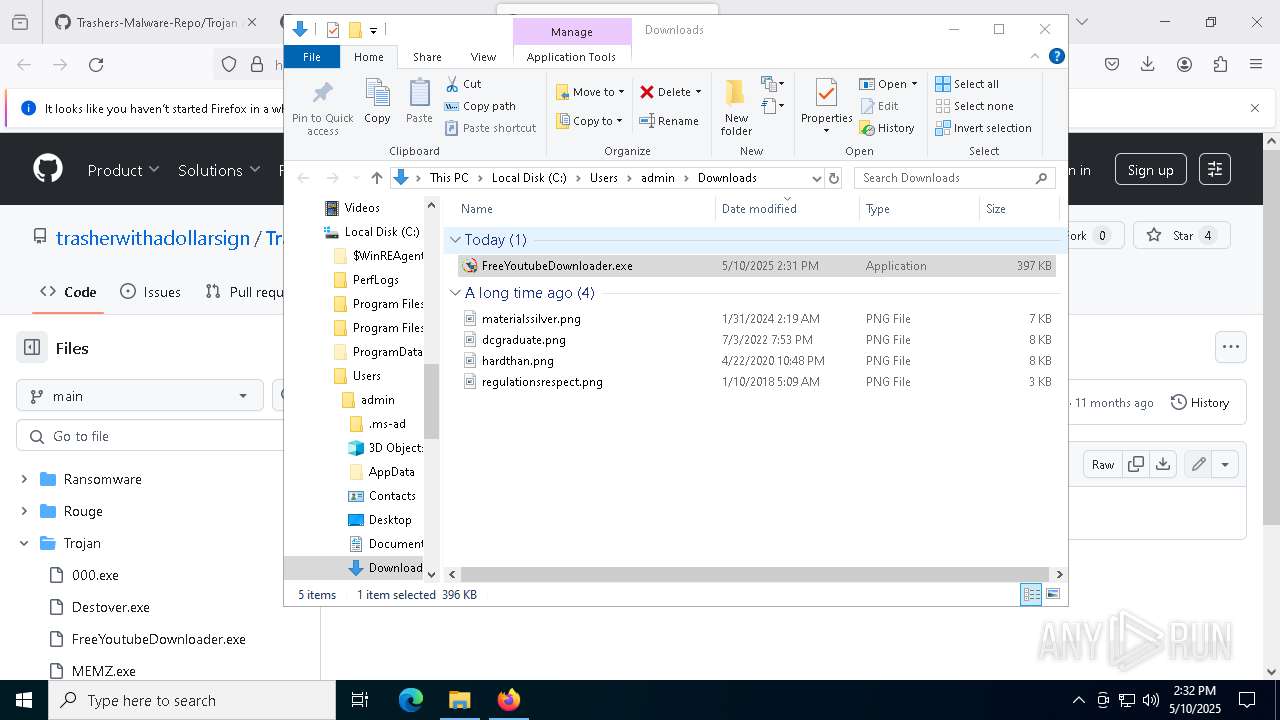
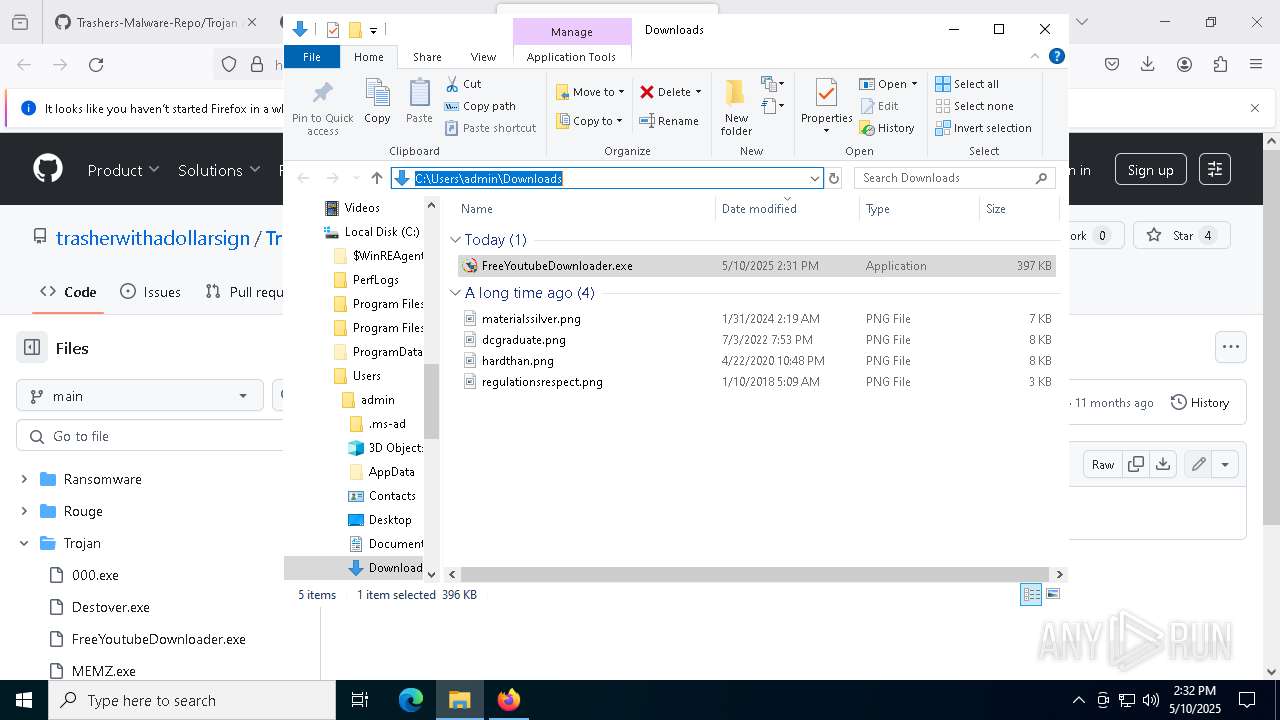
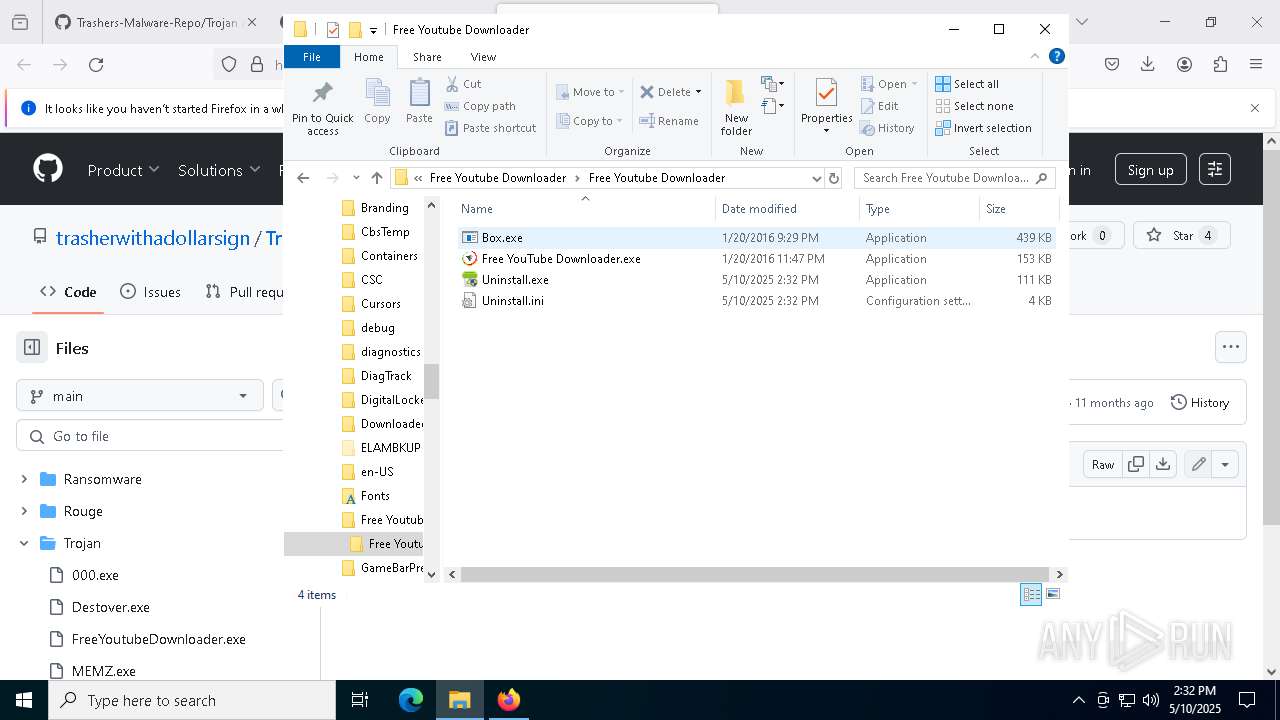
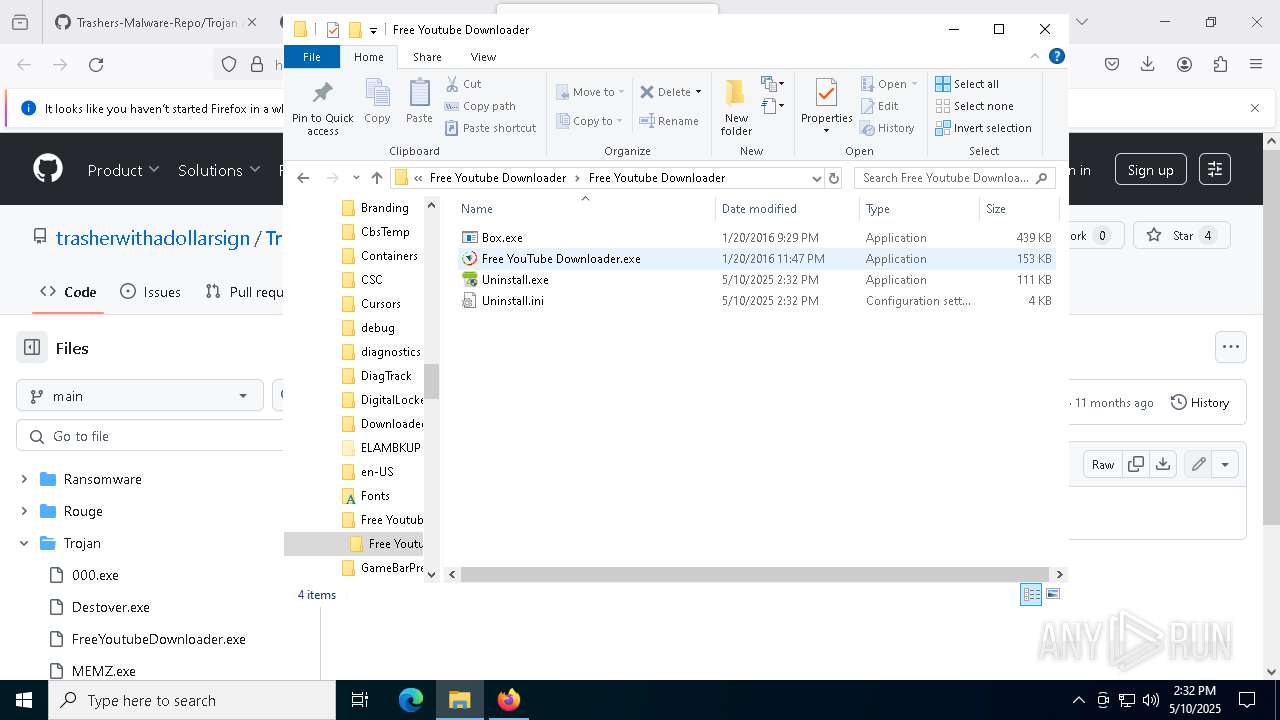
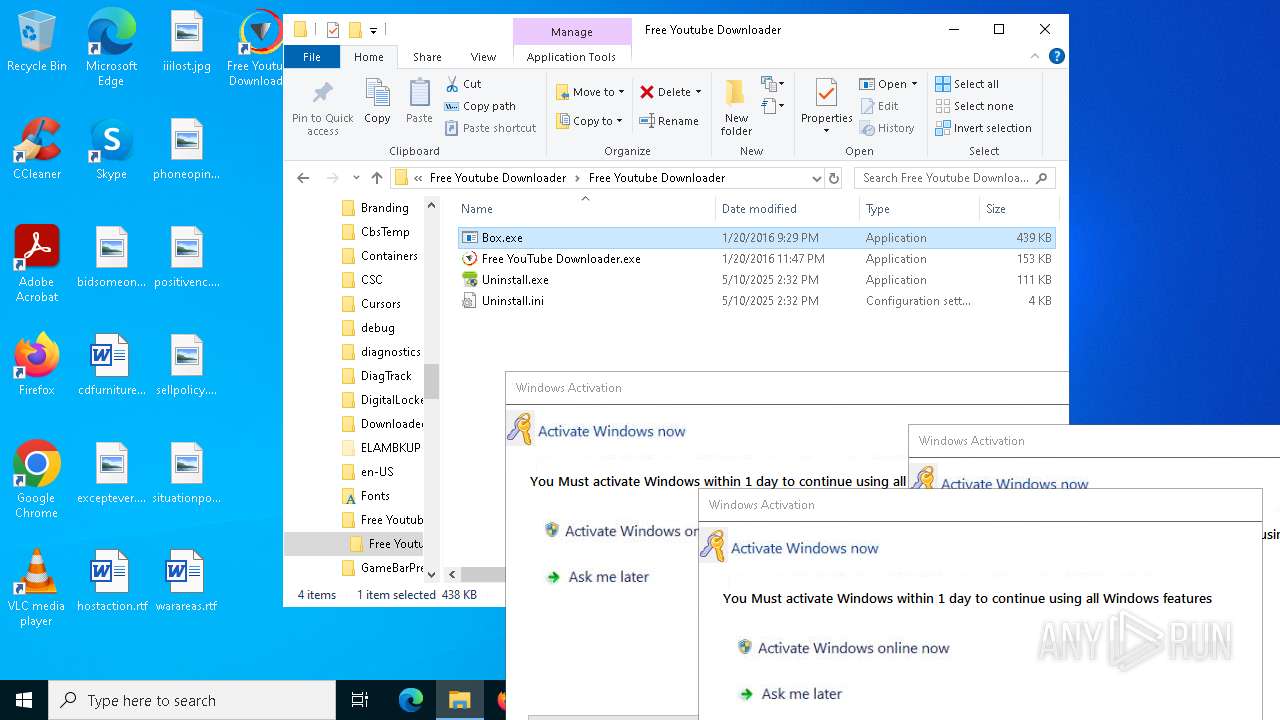
Manual execution by a user
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- FreeYoutubeDownloader.exe (PID: 8056)
- FreeYoutubeDownloader.exe (PID: 2740)
- FreeYoutubeDownloader.exe (PID: 1600)
- Free YouTube Downloader.exe (PID: 6612)
- Box.exe (PID: 4268)
Reads the machine GUID from the registry
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- Free YouTube Downloader.exe (PID: 7020)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Themida protector has been detected
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Create files in a temporary directory
- FreeYoutubeDownloader.exe (PID: 8056)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Executable content was dropped or overwritten
- firefox.exe (PID: 7272)
Process checks computer location settings
- FreeYoutubeDownloader.exe (PID: 8056)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
Reads the software policy settings
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5352)
- WMIC.exe (PID: 2392)
Process checks whether UAC notifications are on
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
Disables trace logs
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
Checks proxy server information
- Trojan.Malpack.Themida (Anti VM).exe (PID: 5132)
- Trojan.Malpack.Themida (Anti VM).exe (PID: 3300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(3300) Trojan.Malpack.Themida (Anti VM).exe
Decrypted-URLs (1)http://ip-api.com/line/?fields=hosting
(PID) Process(5132) Trojan.Malpack.Themida (Anti VM).exe
Decrypted-URLs (1)http://ip-api.com/line/?fields=hosting
RedLine
(PID) Process(2772) RegAsm.exe
C2 (1)4.185.56.82:42687
BotnetLiveTraffoc
Options
ErrorMessageError, disable antivirus and try again!
Keys
XorUglied
Total processes
294
Monitored processes
147
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4 | System | [System Process] | |||||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 208 | "C:\Windows\Free Youtube Downloader\Free Youtube Downloader\Box.exe" | C:\Windows\Free Youtube Downloader\Free Youtube Downloader\Box.exe | — | Free YouTube Downloader.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Box Version: 1.0.0.0 Modules
| |||||||||||||||
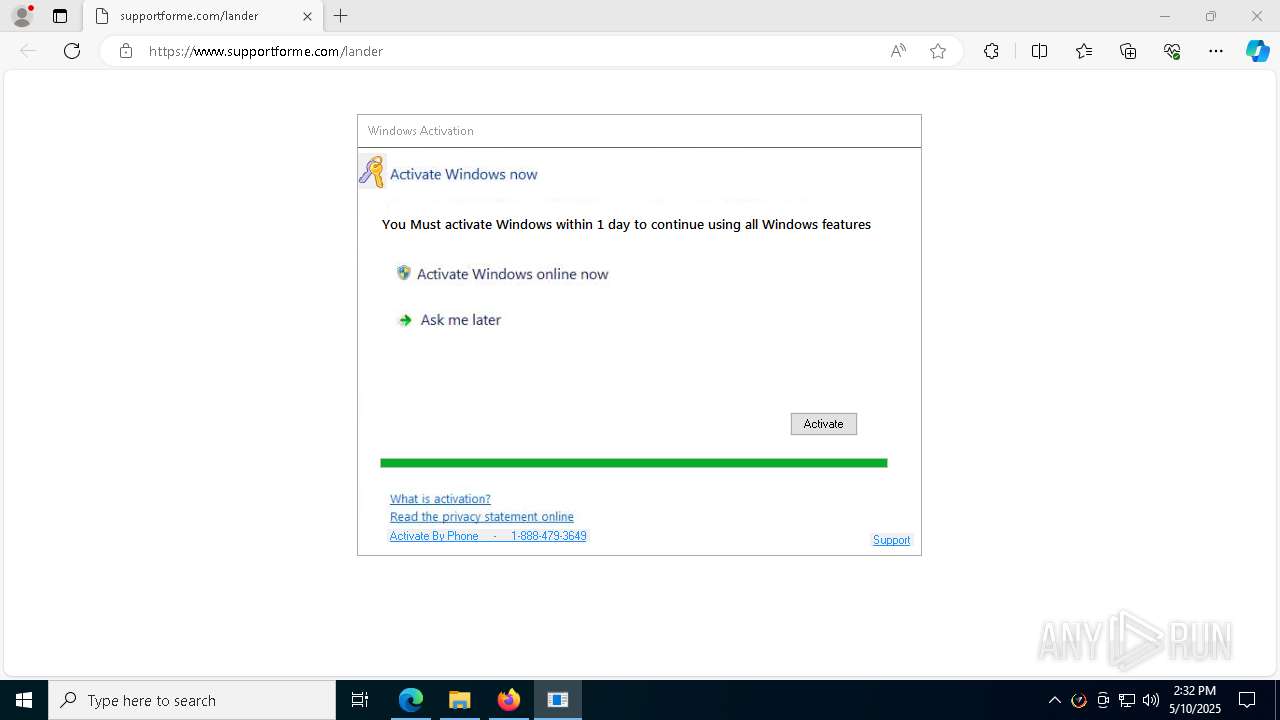
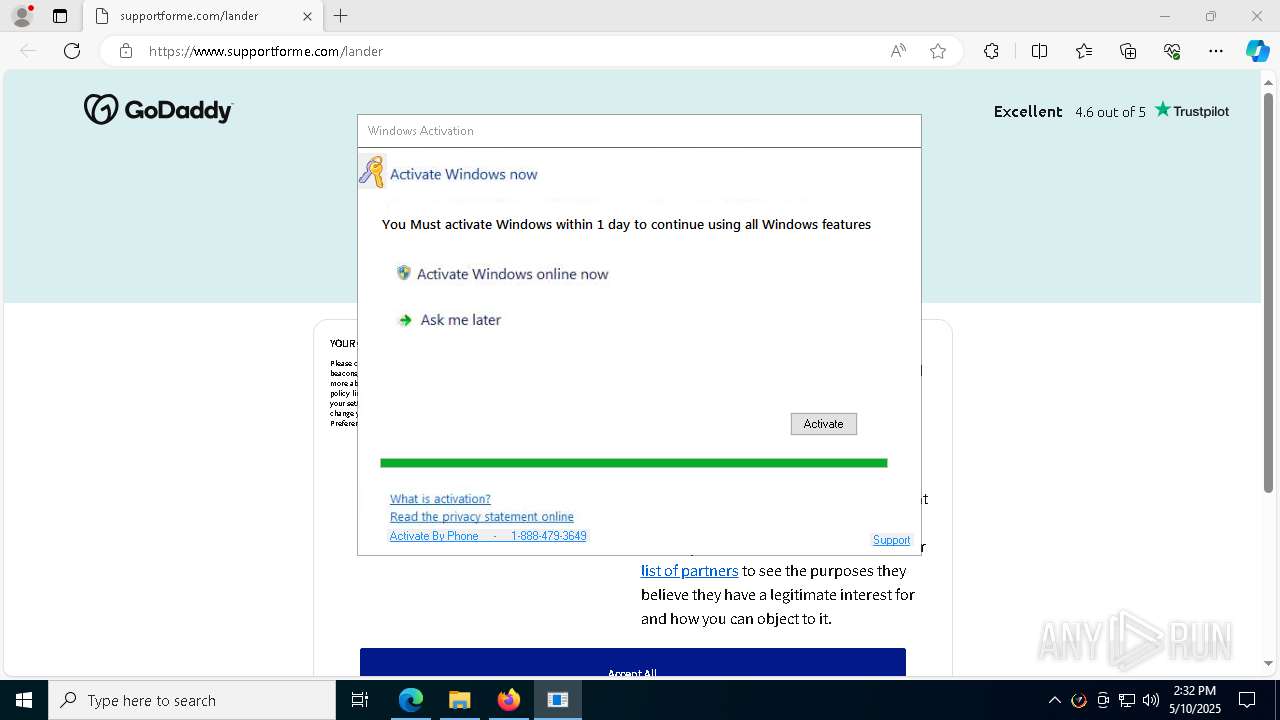
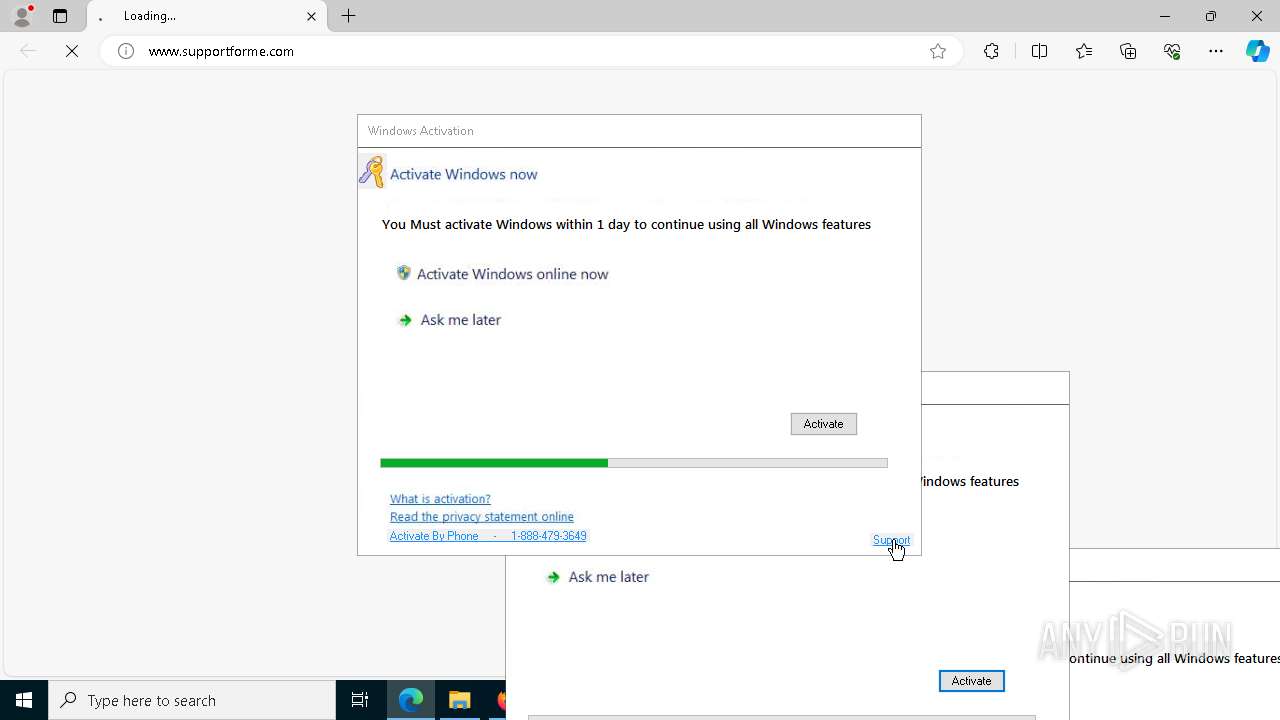
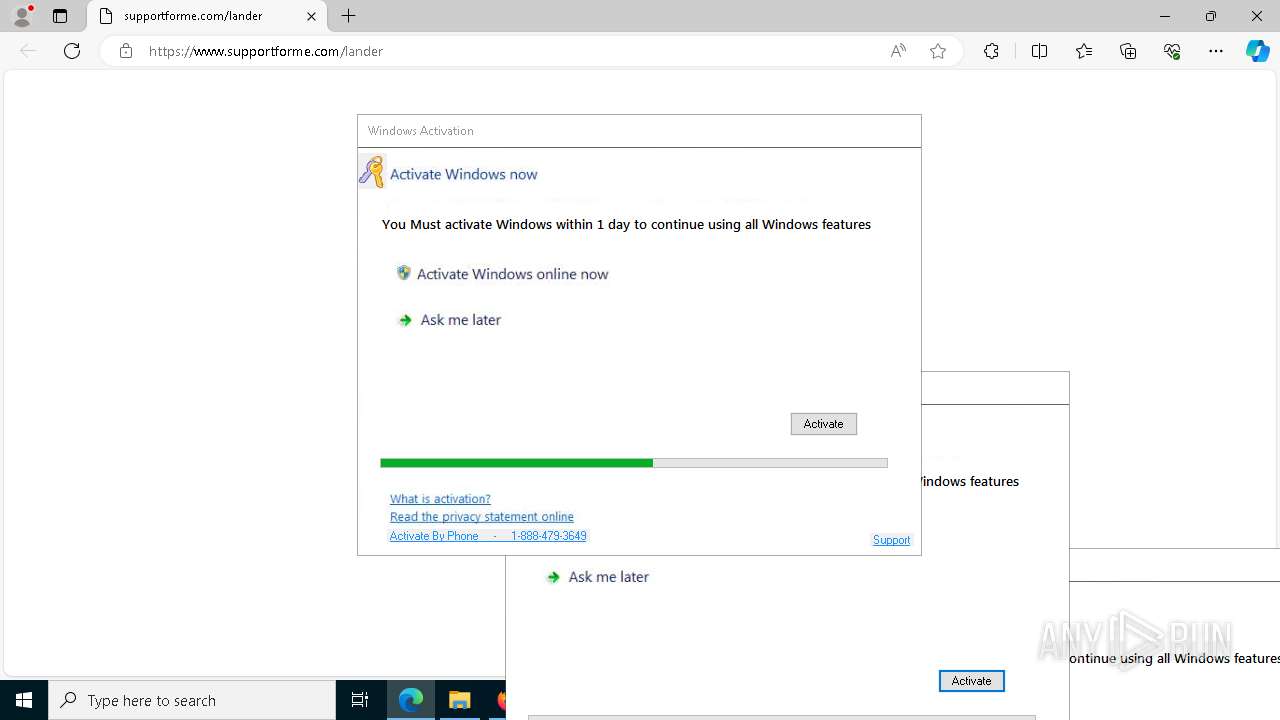
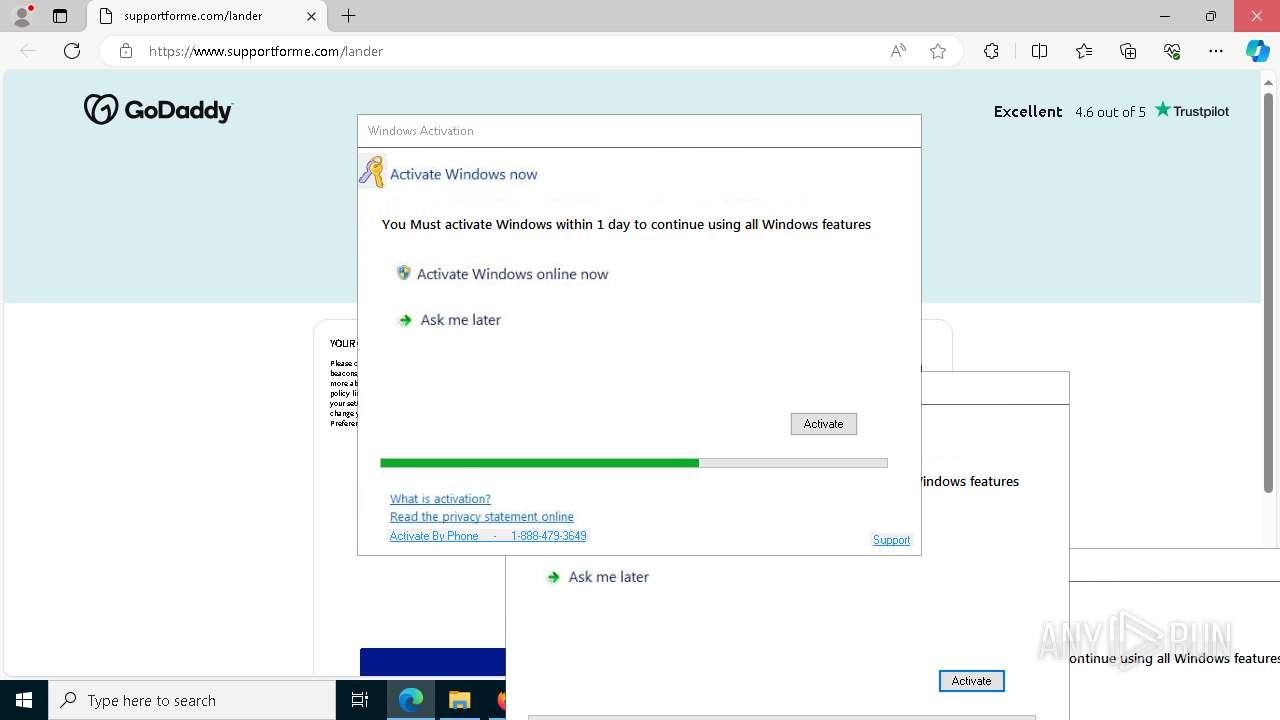
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument http://www.supportforme.com/ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | Box.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 840 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4952 --field-trial-handle=2416,i,4060441614503110180,6103366388963257759,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 928 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1004 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2412 --field-trial-handle=2416,i,4060441614503110180,6103366388963257759,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
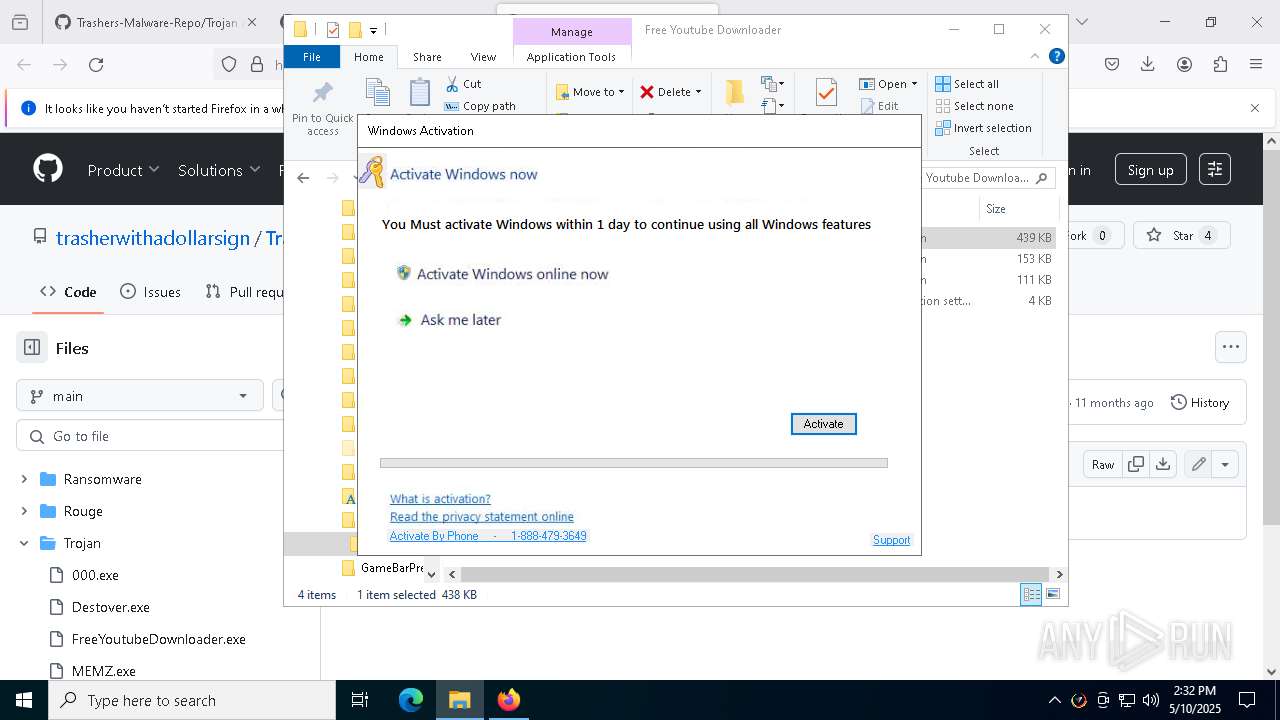
| 1184 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5336 --field-trial-handle=2412,i,5469436253746646427,17211665453461633961,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5320 --field-trial-handle=2412,i,5469436253746646427,17211665453461633961,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
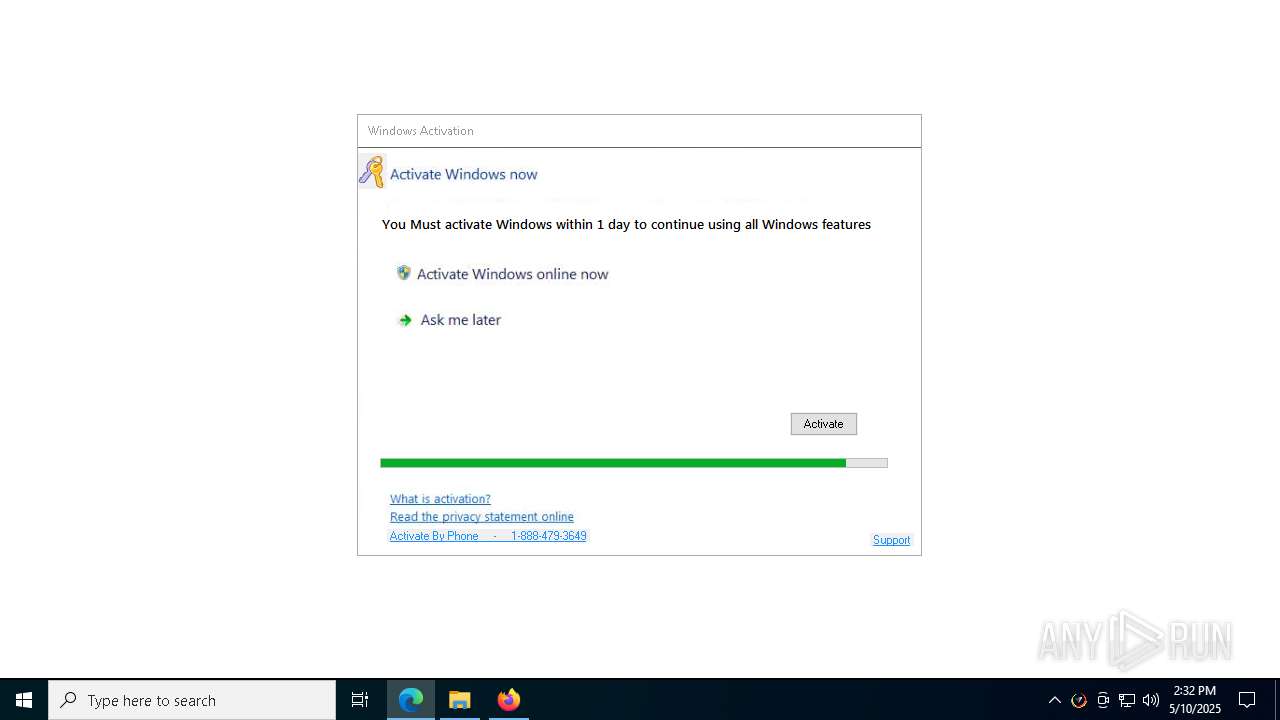
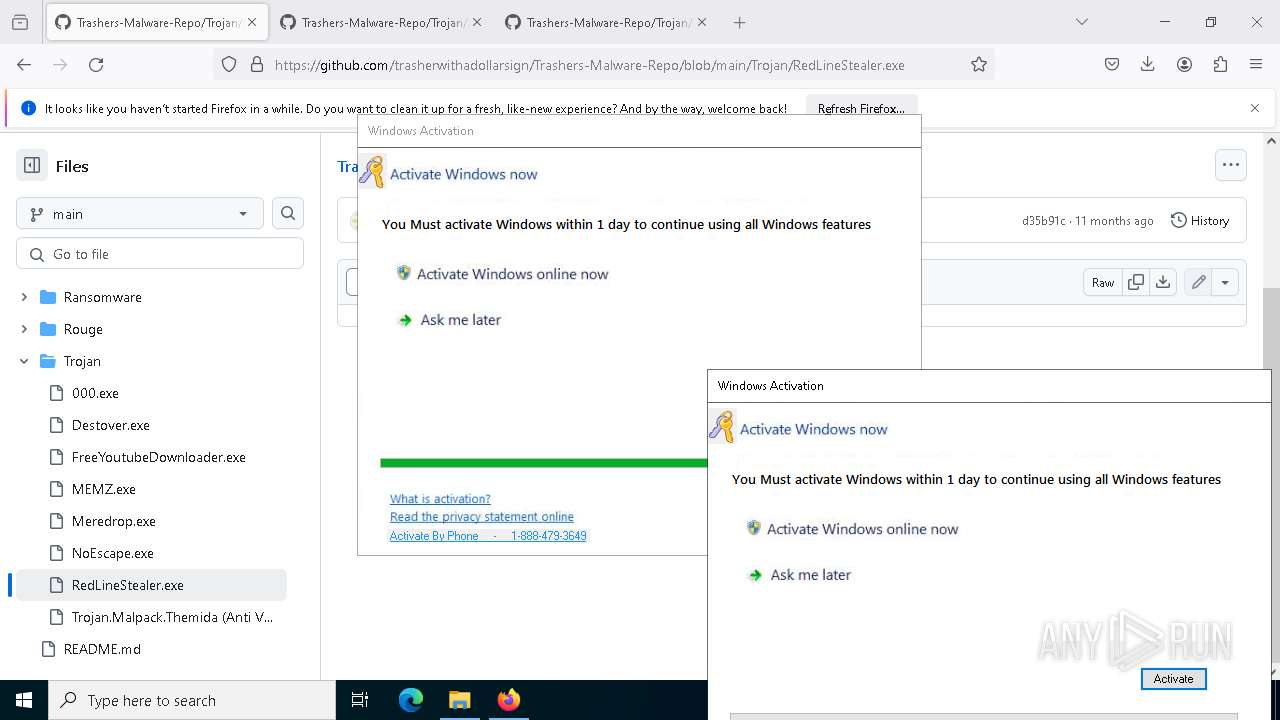
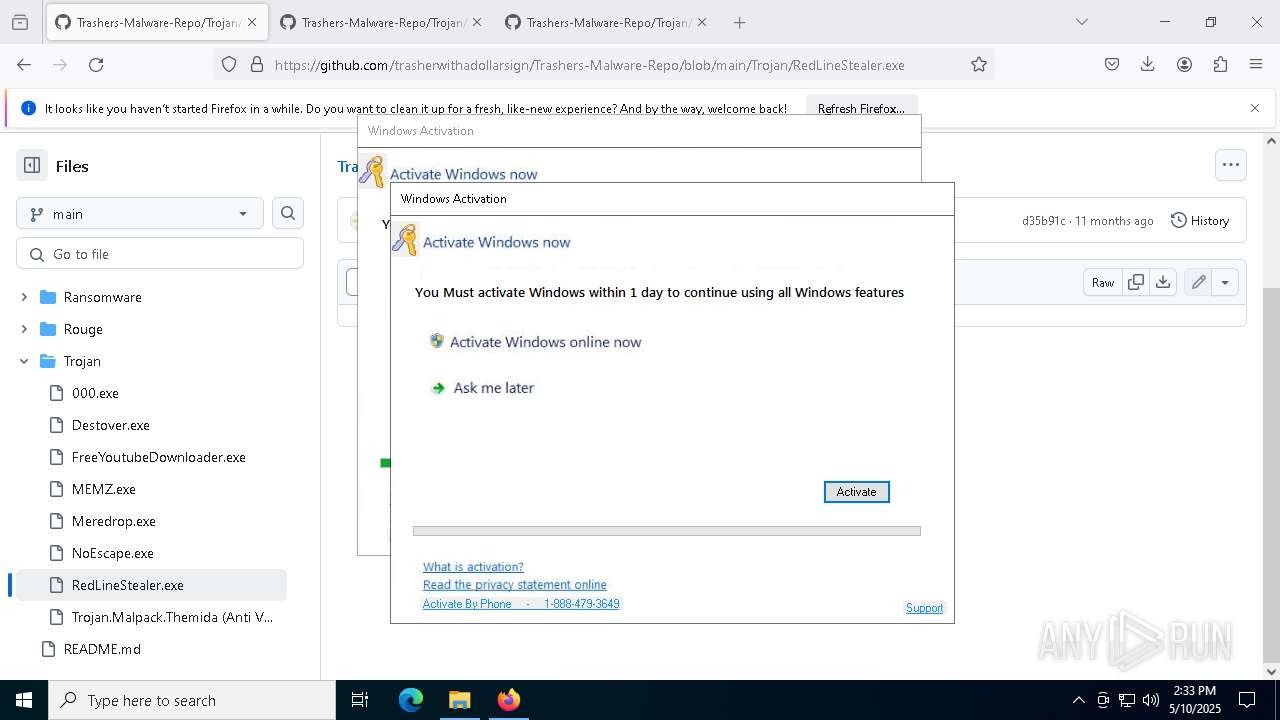
| 1532 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
61 506
Read events
61 406
Write events
100
Delete events
0
Modification events
| (PID) Process: | (7272) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
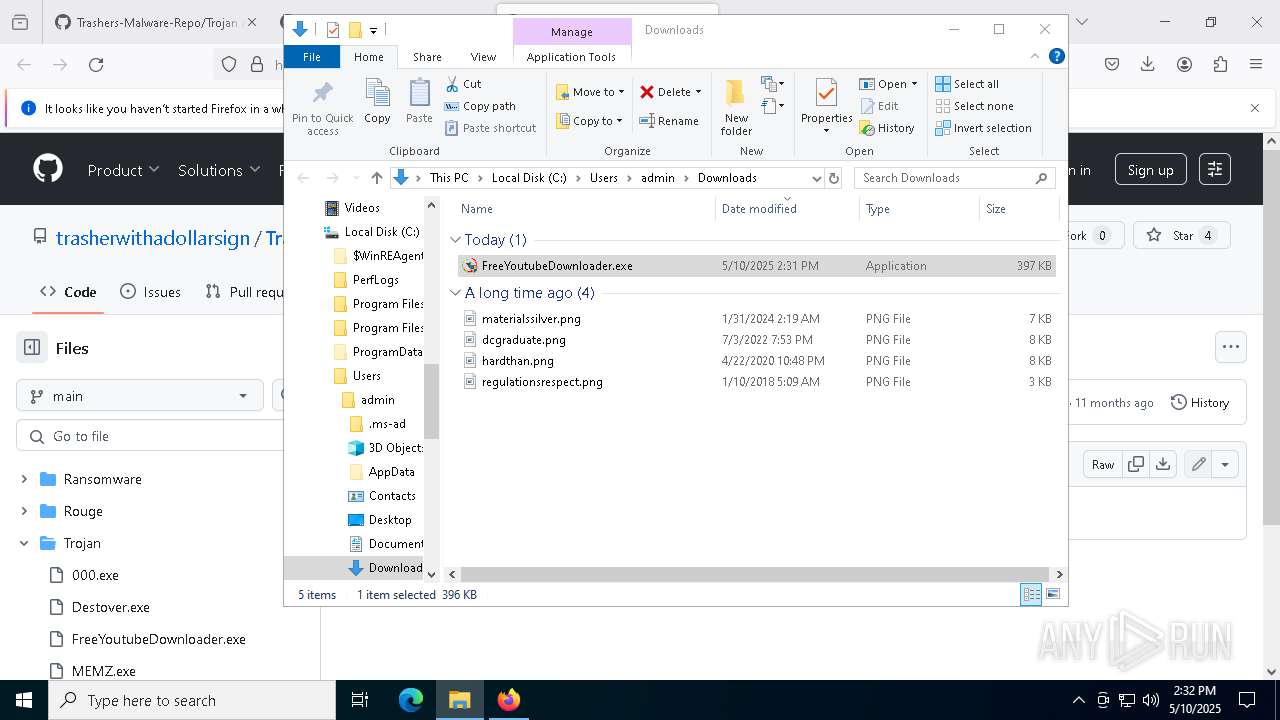
| (PID) Process: | (8056) FreeYoutubeDownloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Free Youtube Downloader |
Value: C:\WINDOWS\Free Youtube Downloader\Free Youtube Downloader\Free YouTube Downloader.exe | |||
| (PID) Process: | (8056) FreeYoutubeDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Free Youtube Downloader 4.1.1.1 |
| Operation: | write | Name: | DisplayName |
Value: Free Youtube Downloader 4.1.1.1 | |||
| (PID) Process: | (8056) FreeYoutubeDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Free Youtube Downloader 4.1.1.1 |
| Operation: | write | Name: | DisplayVersion |
Value: 4.1.1.1 | |||
| (PID) Process: | (8056) FreeYoutubeDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Free Youtube Downloader 4.1.1.1 |
| Operation: | write | Name: | VersionMajor |
Value: 4 | |||
| (PID) Process: | (8056) FreeYoutubeDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Free Youtube Downloader 4.1.1.1 |
| Operation: | write | Name: | VersionMinor |
Value: 1 | |||
| (PID) Process: | (8056) FreeYoutubeDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Free Youtube Downloader 4.1.1.1 |
| Operation: | write | Name: | Publisher |
Value: Free Youtube Downloader | |||
| (PID) Process: | (8056) FreeYoutubeDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Free Youtube Downloader 4.1.1.1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\WINDOWS\Free Youtube Downloader\Free Youtube Downloader\Uninstall.exe | |||
| (PID) Process: | (8056) FreeYoutubeDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Free Youtube Downloader 4.1.1.1 |
| Operation: | write | Name: | UninstallString |
Value: C:\WINDOWS\Free Youtube Downloader\Free Youtube Downloader\Uninstall.exe | |||
| (PID) Process: | (8056) FreeYoutubeDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Free Youtube Downloader 4.1.1.1 |
| Operation: | write | Name: | URLInfoAbout |
Value: www.youtubedownloadernew.com | |||
Executable files
36
Suspicious files
600
Text files
149
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7272 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:BAD406480E50FEC8956978F7FE331991 | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:5FCE15E971DF2AC95C3EDB3477EDC0E8 | SHA256:3F15A4A54E755FE705B3654CF81E60B1556157A24963D560FB96981FC7A4C7B4 | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:5FCE15E971DF2AC95C3EDB3477EDC0E8 | SHA256:3F15A4A54E755FE705B3654CF81E60B1556157A24963D560FB96981FC7A4C7B4 | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
7 953
DNS requests
248
Threats
43
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.145:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7272 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7272 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
7272 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7272 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7272 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7272 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7272 | firefox.exe | POST | 200 | 142.250.185.131:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.145:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7272 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
7272 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7272 | firefox.exe | 142.250.185.170:443 | safebrowsing.googleapis.com | — | — | whitelisted |
7272 | firefox.exe | 185.199.111.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
3300 | Trojan.Malpack.Themida (Anti VM).exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
3300 | Trojan.Malpack.Themida (Anti VM).exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
5132 | Trojan.Malpack.Themida (Anti VM).exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
5132 | Trojan.Malpack.Themida (Anti VM).exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
5132 | Trojan.Malpack.Themida (Anti VM).exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |