| File name: | E6D5DE0F24C9E8CE95EC860FDF075B29.exe |
| Full analysis: | https://app.any.run/tasks/f5fd399e-1ebc-4e79-9934-6d44f7edbfe8 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | August 01, 2025, 05:06:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | E6D5DE0F24C9E8CE95EC860FDF075B29 |
| SHA1: | 337EE2092A62EFC052A5BD47EBAE21309D6D3B43 |
| SHA256: | 6D2B844AD0114DD3EC1731FA828132DC70AD045004C9C643279F71E774E14E14 |
| SSDEEP: | 98304:ln2h5aq9PFsQRW0FlA70GU/zAQn/g/LKKL/lC0iyUXheMd2NWXHr8seMSvMKif9v:7Zn866FoGm |
MALICIOUS
REDLINE has been found (auto)
- Mj7TYuJI.exe (PID: 2276)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2388)
AMADEY mutex has been found
- jAk6FVw8.exe (PID: 504)
- amnew.exe (PID: 7260)
- huran.exe (PID: 7356)
- huran.exe (PID: 7476)
- huran.exe (PID: 4312)
Bypass execution policy to execute commands
- powershell.exe (PID: 7004)
- powershell.exe (PID: 7396)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1036)
- ls1FDZl.exe (PID: 7560)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 5460)
- NSudoLG.exe (PID: 5764)
- cmd.exe (PID: 4088)
- NSudoLG.exe (PID: 6868)
Changes Windows Defender settings
- NSudoLG.exe (PID: 5764)
- NSudoLG.exe (PID: 6868)
Changes the autorun value in the registry
- jAk6FVw8.exe (PID: 504)
- ls1FDZl.exe (PID: 7560)
Changes the Windows auto-update feature
- reg.exe (PID: 4400)
AMADEY has been detected (YARA)
- jAk6FVw8.exe (PID: 504)
Run PowerShell with an invisible window
- powershell.exe (PID: 7396)
STEALC has been detected
- MSBuild.exe (PID: 7916)
LUMMA mutex has been found
- MSBuild.exe (PID: 7228)
QUASAR has been found (auto)
- jAk6FVw8.exe (PID: 504)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 6332)
SUSPICIOUS
Starts a Microsoft application from unusual location
- E6D5DE0F24C9E8CE95EC860FDF075B29.exe (PID: 6340)
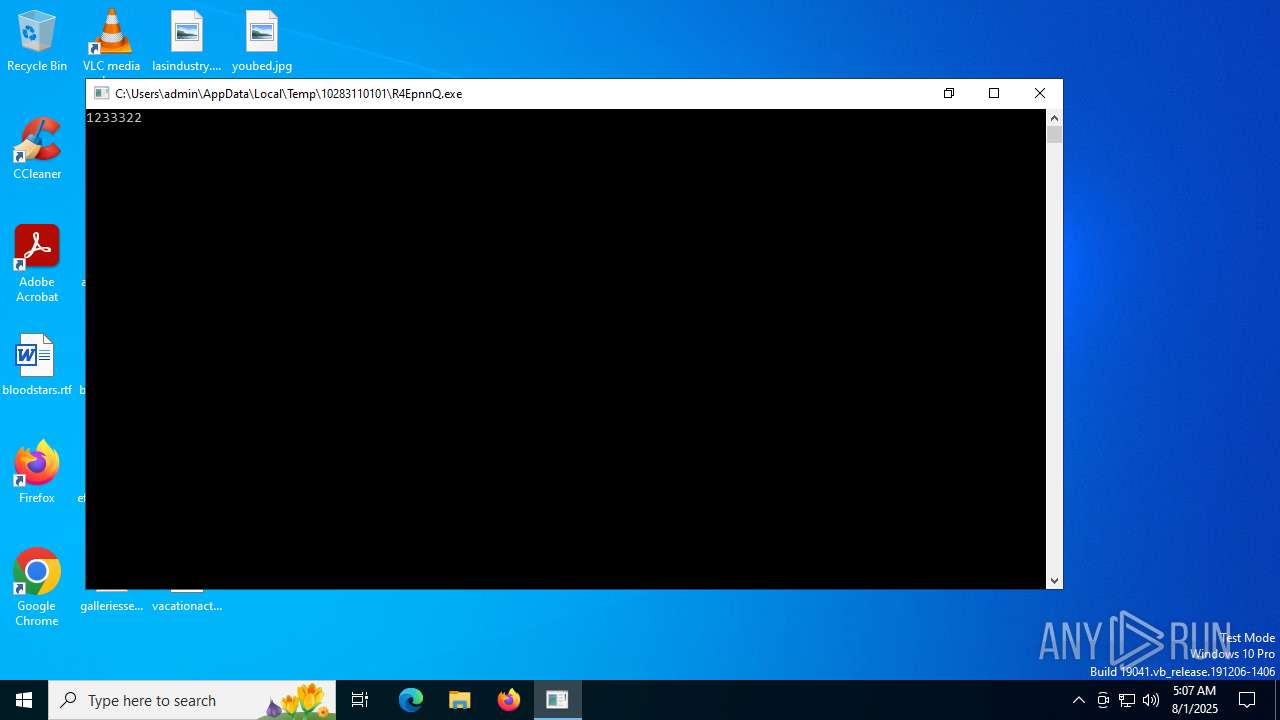
Process drops legitimate windows executable
- E6D5DE0F24C9E8CE95EC860FDF075B29.exe (PID: 6340)
- R4EpnnQ.exe (PID: 5240)
Reads the BIOS version
- 1E08s6.exe (PID: 512)
- ee7efab4f3.exe (PID: 6452)
- ee7efab4f3.exe (PID: 7796)
Executable content was dropped or overwritten
- E6D5DE0F24C9E8CE95EC860FDF075B29.exe (PID: 6340)
- DNqCKF65.exe (PID: 3720)
- Mj7TYuJI.exe (PID: 2276)
- 2g8113.exe (PID: 7048)
- jAk6FVw8.exe (PID: 504)
- 7z.exe (PID: 2716)
- Unlocker.exe (PID: 6620)
- Unlocker.exe (PID: 6392)
- 6olpur0.exe (PID: 8016)
- amnew.exe (PID: 7260)
- ls1FDZl.exe (PID: 7560)
- R4EpnnQ.exe (PID: 5240)
- 1NjnoxK.exe (PID: 6736)
Drops 7-zip archiver for unpacking
- DNqCKF65.exe (PID: 3720)
- 2g8113.exe (PID: 7048)
Starts CMD.EXE for commands execution
- fSMYR68E.exe (PID: 1040)
- DNqCKF65.exe (PID: 3720)
- nircmd.exe (PID: 2504)
- 2g8113.exe (PID: 7048)
- NSudoLG.exe (PID: 684)
- cmd.exe (PID: 5460)
- 76995f989d.exe (PID: 4164)
- nircmd.exe (PID: 2312)
- NSudoLG.exe (PID: 2716)
- cmd.exe (PID: 4088)
- Unlocker.exe (PID: 1232)
- Unlocker.exe (PID: 6620)
- Unlocker.exe (PID: 6392)
- 76995f989d.exe (PID: 3624)
- nircmd.exe (PID: 6236)
- NSudoLG.exe (PID: 7348)
- cmd.exe (PID: 7368)
- 6olpur0.exe (PID: 8016)
- cmd.exe (PID: 8060)
- ls1FDZl.exe (PID: 7560)
Reads security settings of Internet Explorer
- DNqCKF65.exe (PID: 3720)
- nircmd.exe (PID: 2504)
- 2g8113.exe (PID: 7048)
- jAk6FVw8.exe (PID: 504)
- 76995f989d.exe (PID: 4164)
- nircmd.exe (PID: 2312)
- Unlocker.exe (PID: 1232)
- Unlocker.exe (PID: 6620)
- Unlocker.exe (PID: 6392)
- 76995f989d.exe (PID: 3624)
- nircmd.exe (PID: 6236)
- huran.exe (PID: 7356)
- amnew.exe (PID: 7260)
- ls1FDZl.exe (PID: 7560)
- R4EpnnQ.exe (PID: 7940)
- MSBuild.exe (PID: 7916)
- svchost015.exe (PID: 7872)
- MSBuild.exe (PID: 6332)
The process creates files with name similar to system file names
- DNqCKF65.exe (PID: 3720)
Executing commands from a ".bat" file
- DNqCKF65.exe (PID: 3720)
- nircmd.exe (PID: 2504)
- NSudoLG.exe (PID: 684)
- 76995f989d.exe (PID: 4164)
- nircmd.exe (PID: 2312)
- NSudoLG.exe (PID: 2716)
- 76995f989d.exe (PID: 3624)
- nircmd.exe (PID: 6236)
- NSudoLG.exe (PID: 7348)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1036)
- NSudoLG.exe (PID: 5764)
- NSudoLG.exe (PID: 6868)
- ls1FDZl.exe (PID: 7560)
- MSBuild.exe (PID: 6332)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1036)
- ls1FDZl.exe (PID: 7560)
- MSBuild.exe (PID: 6332)
Starts application with an unusual extension
- cmd.exe (PID: 4412)
- cmd.exe (PID: 5460)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 2848)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 2400)
- cmd.exe (PID: 7368)
The executable file from the user directory is run by the CMD process
- nircmd.exe (PID: 3608)
- nircmd.exe (PID: 2504)
- nircmd.exe (PID: 1508)
- NSudoLG.exe (PID: 684)
- nircmd.exe (PID: 1800)
- NSudoLG.exe (PID: 5764)
- nircmd.exe (PID: 2716)
- nircmd.exe (PID: 2312)
- nircmd.exe (PID: 6356)
- nircmd.exe (PID: 3896)
- NSudoLG.exe (PID: 2716)
- 7z.exe (PID: 2716)
- Unlocker.exe (PID: 1232)
- NSudoLG.exe (PID: 6868)
- Unlocker.exe (PID: 6620)
- Unlocker.exe (PID: 6392)
- nircmd.exe (PID: 5240)
- nircmd.exe (PID: 6236)
- nircmd.exe (PID: 7260)
- NSudoLG.exe (PID: 7348)
- nircmd.exe (PID: 7440)
Reads the date of Windows installation
- nircmd.exe (PID: 2504)
- nircmd.exe (PID: 2312)
- Unlocker.exe (PID: 1232)
- Unlocker.exe (PID: 6620)
- Unlocker.exe (PID: 6392)
- nircmd.exe (PID: 6236)
- ls1FDZl.exe (PID: 7560)
- R4EpnnQ.exe (PID: 7940)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2848)
- cmd.exe (PID: 5460)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 7368)
Application launched itself
- cmd.exe (PID: 5460)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 8060)
- R4EpnnQ.exe (PID: 7940)
- vlc-cache-gen.exe (PID: 6332)
- vlc-cache-gen.exe (PID: 6756)
- vlc-cache-gen.exe (PID: 6084)
- vlc-cache-gen.exe (PID: 7280)
Get information on the list of running processes
- cmd.exe (PID: 5460)
- cmd.exe (PID: 4264)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 2628)
Script adds exclusion path to Windows Defender
- NSudoLG.exe (PID: 5764)
- NSudoLG.exe (PID: 6868)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 4692)
Connects to the server without a host name
- jAk6FVw8.exe (PID: 504)
- huran.exe (PID: 7356)
- svchost015.exe (PID: 7872)
Process requests binary or script from the Internet
- jAk6FVw8.exe (PID: 504)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5460)
Starts SC.EXE for service management
- cmd.exe (PID: 4688)
- cmd.exe (PID: 5460)
- cmd.exe (PID: 1880)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 5808)
Windows service management via SC.EXE
- sc.exe (PID: 4544)
- sc.exe (PID: 3760)
- sc.exe (PID: 3100)
- sc.exe (PID: 3628)
- sc.exe (PID: 2356)
- sc.exe (PID: 6720)
- sc.exe (PID: 5808)
- sc.exe (PID: 1268)
- sc.exe (PID: 5032)
Stops a currently running service
- sc.exe (PID: 5824)
- sc.exe (PID: 3756)
- sc.exe (PID: 6452)
- sc.exe (PID: 4748)
- sc.exe (PID: 6176)
- sc.exe (PID: 6832)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1128)
- cmd.exe (PID: 4844)
Creates or modifies Windows services
- reg.exe (PID: 5780)
- Unlocker.exe (PID: 6620)
Drops a system driver (possible attempt to evade defenses)
- Unlocker.exe (PID: 6620)
- Unlocker.exe (PID: 6392)
The process verifies whether the antivirus software is installed
- Unlocker.exe (PID: 6392)
- IObitUnlocker.exe (PID: 7572)
There is functionality for enable RDP (YARA)
- jAk6FVw8.exe (PID: 504)
There is functionality for taking screenshot (YARA)
- jAk6FVw8.exe (PID: 504)
Starts itself from another location
- amnew.exe (PID: 7260)
The process executes via Task Scheduler
- huran.exe (PID: 7476)
- vlc-cache-gen.exe (PID: 7280)
- huran.exe (PID: 4312)
BASE64 encoded PowerShell command has been detected
- ls1FDZl.exe (PID: 7560)
- MSBuild.exe (PID: 6332)
Uses powercfg.exe to modify the power settings
- ls1FDZl.exe (PID: 7560)
Base64-obfuscated command line is found
- ls1FDZl.exe (PID: 7560)
- MSBuild.exe (PID: 6332)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 7228)
- MSBuild.exe (PID: 6332)
Connects to unusual port
- vlc-cache-gen.exe (PID: 7236)
- vlc-cache-gen.exe (PID: 7352)
- vlc-cache-gen.exe (PID: 8168)
Executes application which crashes
- YT1For2.exe (PID: 5800)
The process hide an interactive prompt from the user
- MSBuild.exe (PID: 6332)
Searches for installed software
- MSBuild.exe (PID: 6332)
INFO
The sample compiled with english language support
- E6D5DE0F24C9E8CE95EC860FDF075B29.exe (PID: 6340)
- 2g8113.exe (PID: 7048)
- DNqCKF65.exe (PID: 3720)
- Unlocker.exe (PID: 6620)
- Unlocker.exe (PID: 6392)
- jAk6FVw8.exe (PID: 504)
- R4EpnnQ.exe (PID: 5240)
- 1NjnoxK.exe (PID: 6736)
Checks supported languages
- fSMYR68E.exe (PID: 1040)
- E6D5DE0F24C9E8CE95EC860FDF075B29.exe (PID: 6340)
- 1E08s6.exe (PID: 512)
- 2g8113.exe (PID: 7048)
- jAk6FVw8.exe (PID: 504)
- Mj7TYuJI.exe (PID: 2276)
- DNqCKF65.exe (PID: 3720)
- nircmd.exe (PID: 3608)
- chcp.com (PID: 2384)
- nircmd.exe (PID: 2504)
- chcp.com (PID: 1880)
- nircmd.exe (PID: 1800)
- NSudoLG.exe (PID: 684)
- chcp.com (PID: 2388)
- mode.com (PID: 6868)
- NSudoLG.exe (PID: 5764)
- nircmd.exe (PID: 1508)
- 76995f989d.exe (PID: 4164)
- nircmd.exe (PID: 2716)
- chcp.com (PID: 5904)
- nircmd.exe (PID: 2312)
- nircmd.exe (PID: 3896)
- chcp.com (PID: 2728)
- mode.com (PID: 1056)
- chcp.com (PID: 1880)
- NSudoLG.exe (PID: 2716)
- nircmd.exe (PID: 6356)
- 7z.exe (PID: 2716)
- Unlocker.exe (PID: 1232)
- NSudoLG.exe (PID: 6868)
- Unlocker.exe (PID: 6620)
- Unlocker.exe (PID: 6392)
- 76995f989d.exe (PID: 3624)
- ee7efab4f3.exe (PID: 6452)
- nircmd.exe (PID: 5240)
- nircmd.exe (PID: 6236)
- nircmd.exe (PID: 7260)
- chcp.com (PID: 7284)
- chcp.com (PID: 4552)
- NSudoLG.exe (PID: 7348)
- chcp.com (PID: 7460)
- mode.com (PID: 7520)
- nircmd.exe (PID: 7440)
- ee7efab4f3.exe (PID: 7796)
- 6olpur0.exe (PID: 8016)
- IObitUnlocker.exe (PID: 7572)
- huran.exe (PID: 7356)
- huran.exe (PID: 7476)
- ls1FDZl.exe (PID: 7560)
- amnew.exe (PID: 7260)
- G4gtDRI.exe (PID: 2348)
- MSBuild.exe (PID: 7916)
- R4EpnnQ.exe (PID: 5240)
- RenT7Wg.exe (PID: 7576)
- R4EpnnQ.exe (PID: 7940)
- vlc-cache-gen.exe (PID: 6084)
- vlc-cache-gen.exe (PID: 7280)
- vlc-cache-gen.exe (PID: 6332)
- vlc-cache-gen.exe (PID: 6756)
- vlc-cache-gen.exe (PID: 7352)
- vlc-cache-gen.exe (PID: 8168)
- vlc-cache-gen.exe (PID: 7236)
- MSBuild.exe (PID: 7228)
- huran.exe (PID: 4312)
- svchost015.exe (PID: 7872)
- 8PdcY8X.exe (PID: 4664)
- v9d9d.exe (PID: 1324)
- 1NjnoxK.exe (PID: 6736)
- YT1For2.exe (PID: 5800)
- MSBuild.exe (PID: 6332)
- OTIWCUm.exe (PID: 5248)
Reads the computer name
- 1E08s6.exe (PID: 512)
- 2g8113.exe (PID: 7048)
- DNqCKF65.exe (PID: 3720)
- Mj7TYuJI.exe (PID: 2276)
- jAk6FVw8.exe (PID: 504)
- nircmd.exe (PID: 2504)
- NSudoLG.exe (PID: 684)
- NSudoLG.exe (PID: 5764)
- 76995f989d.exe (PID: 4164)
- nircmd.exe (PID: 2312)
- NSudoLG.exe (PID: 2716)
- 7z.exe (PID: 2716)
- Unlocker.exe (PID: 1232)
- NSudoLG.exe (PID: 6868)
- Unlocker.exe (PID: 6620)
- Unlocker.exe (PID: 6392)
- 76995f989d.exe (PID: 3624)
- ee7efab4f3.exe (PID: 6452)
- nircmd.exe (PID: 6236)
- NSudoLG.exe (PID: 7348)
- IObitUnlocker.exe (PID: 7572)
- ee7efab4f3.exe (PID: 7796)
- 6olpur0.exe (PID: 8016)
- amnew.exe (PID: 7260)
- huran.exe (PID: 7356)
- ls1FDZl.exe (PID: 7560)
- R4EpnnQ.exe (PID: 7940)
- MSBuild.exe (PID: 7916)
- R4EpnnQ.exe (PID: 5240)
- vlc-cache-gen.exe (PID: 6332)
- vlc-cache-gen.exe (PID: 7352)
- MSBuild.exe (PID: 7228)
- svchost015.exe (PID: 7872)
- vlc-cache-gen.exe (PID: 8168)
- vlc-cache-gen.exe (PID: 7236)
- YT1For2.exe (PID: 5800)
- MSBuild.exe (PID: 6332)
Create files in a temporary directory
- E6D5DE0F24C9E8CE95EC860FDF075B29.exe (PID: 6340)
- DNqCKF65.exe (PID: 3720)
- jAk6FVw8.exe (PID: 504)
- 76995f989d.exe (PID: 4164)
- 7z.exe (PID: 2716)
- 76995f989d.exe (PID: 3624)
- 6olpur0.exe (PID: 8016)
- amnew.exe (PID: 7260)
- R4EpnnQ.exe (PID: 5240)
- vlc-cache-gen.exe (PID: 7352)
- 1NjnoxK.exe (PID: 6736)
- powershell.exe (PID: 3580)
- powershell.exe (PID: 1392)
Reads the software policy settings
- 1E08s6.exe (PID: 512)
- ee7efab4f3.exe (PID: 6452)
- ee7efab4f3.exe (PID: 7796)
- R4EpnnQ.exe (PID: 5240)
- MSBuild.exe (PID: 7228)
- svchost015.exe (PID: 7872)
- WerFault.exe (PID: 6068)
- MSBuild.exe (PID: 6332)
- powershell.exe (PID: 1392)
Process checks computer location settings
- DNqCKF65.exe (PID: 3720)
- nircmd.exe (PID: 2504)
- 2g8113.exe (PID: 7048)
- jAk6FVw8.exe (PID: 504)
- 76995f989d.exe (PID: 4164)
- nircmd.exe (PID: 2312)
- 76995f989d.exe (PID: 3624)
- nircmd.exe (PID: 6236)
- amnew.exe (PID: 7260)
- R4EpnnQ.exe (PID: 7940)
- ls1FDZl.exe (PID: 7560)
NirSoft software is detected
- nircmd.exe (PID: 3608)
- nircmd.exe (PID: 2504)
- nircmd.exe (PID: 1800)
- nircmd.exe (PID: 1508)
- nircmd.exe (PID: 2716)
- nircmd.exe (PID: 2312)
- nircmd.exe (PID: 6356)
- nircmd.exe (PID: 3896)
- nircmd.exe (PID: 5240)
- nircmd.exe (PID: 6236)
- nircmd.exe (PID: 7260)
- nircmd.exe (PID: 7440)
Changes the display of characters in the console
- cmd.exe (PID: 4412)
- cmd.exe (PID: 5460)
- cmd.exe (PID: 2848)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 2400)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 7368)
Reads mouse settings
- fSMYR68E.exe (PID: 1040)
Starts MODE.COM to configure console settings
- mode.com (PID: 6868)
- mode.com (PID: 1056)
- mode.com (PID: 7520)
Checks proxy server information
- jAk6FVw8.exe (PID: 504)
- huran.exe (PID: 7356)
- MSBuild.exe (PID: 7916)
- svchost015.exe (PID: 7872)
- MSBuild.exe (PID: 6332)
- WerFault.exe (PID: 6068)
Checks operating system version
- cmd.exe (PID: 5460)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 7368)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7004)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 7396)
Creates files or folders in the user directory
- jAk6FVw8.exe (PID: 504)
- ls1FDZl.exe (PID: 7560)
- svchost015.exe (PID: 7872)
- WerFault.exe (PID: 6068)
- MSBuild.exe (PID: 6332)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 7396)
Reads the machine GUID from the registry
- Unlocker.exe (PID: 1232)
- Unlocker.exe (PID: 6620)
- Unlocker.exe (PID: 6392)
- ee7efab4f3.exe (PID: 6452)
- ee7efab4f3.exe (PID: 7796)
- R4EpnnQ.exe (PID: 5240)
- svchost015.exe (PID: 7872)
- MSBuild.exe (PID: 6332)
Launching a file from a Registry key
- jAk6FVw8.exe (PID: 504)
- ls1FDZl.exe (PID: 7560)
Manual execution by a user
- 76995f989d.exe (PID: 3624)
- ee7efab4f3.exe (PID: 7796)
Application launched itself
- chrome.exe (PID: 1560)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 7020)
- chrome.exe (PID: 7388)
- chrome.exe (PID: 848)
Reads Environment values
- MSBuild.exe (PID: 6332)
Reads product name
- MSBuild.exe (PID: 6332)
Creates files in the program directory
- MSBuild.exe (PID: 6332)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3580)
- powershell.exe (PID: 1392)
Reads CPU info
- MSBuild.exe (PID: 6332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(504) jAk6FVw8.exe
C294.154.35.25
URLhttp://94.154.35.25/di9ku38f/index.php
Version5.55
Options
Drop directory96a319e745
Drop nameSrxelqcif.exe
Strings (125)os:
" && timeout 1 && del
\App
&&
|
shutdown -s -t 0
Panda Security
r=
:::
" && ren
pc:
random
ProductName
bi:
#
POST
2016
msi
Content-Type: application/x-www-form-urlencoded
0123456789
0000043f
un:
st=s
S-%lu-
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
AVAST Software
cmd
Content-Disposition: form-data; name="data"; filename="
SOFTWARE\Microsoft\Windows NT\CurrentVersion
lv:
<c>
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
00000423
<d>
cred.dll|clip.dll|
exe
og:
Srxelqcif.exe
Powershell.exe
Comodo
5.55
&& Exit"
Startup
%-lu
DefaultSettings.YResolution
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
00000422
rundll32
2019
ps1
ar:
%USERPROFILE%
vs:
-executionpolicy remotesigned -File "
shell32.dll
/k
WinDefender
------
http://
cred.dll
Main
Bitdefender
.jpg
?scr=1
"taskkill /f /im "
rb
CurrentBuild
id:
Doctor Web
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
94.154.35.25
ESET
Sophos
00000419
VideoID
dm:
96a319e745
Keyboard Layout\Preload
AVG
------
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
2025
--
"
DefaultSettings.XResolution
/quiet
Norton
SYSTEM\ControlSet001\Services\BasicDisplay\Video
dll
zip
=
ProgramData\
cmd /C RMDIR /s/q
/Plugins/
e1
Programs
d1
&unit=
Rem
ComputerName
2022
rundll32.exe
e3
e2
Content-Type: multipart/form-data; boundary=----
-%lu
clip.dll
av:
kernel32.dll
GetNativeSystemInfo
360TotalSecurity
\0000
"
Content-Type: application/octet-stream
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
+++
Kaspersky Lab
Avira
\
GET
/di9ku38f/index.php
sd:
abcdefghijklmnopqrstuvwxyz0123456789-_
wb
https://
-unicode-
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:05:24 22:49:06+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 25600 |
| InitializedDataSize: | 4925952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a60 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.17763.1 |
| ProductVersionNumber: | 11.0.17763.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.17763.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.17763.1 |
Total processes
406
Monitored processes
260
Malicious processes
32
Suspicious processes
20
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | reg query "HKU\S-1-5-19" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | reg query "HKLM\System\CurrentControlSet\Services\MDCoreSvc" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | C:\Windows\SysWOW64\explorer.exe | C:\Windows\SysWOW64\explorer.exe | — | 8PdcY8X.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 504 | "C:\w0HZ6G0\jAk6FVw8.exe" | C:\w0HZ6G0\jAk6FVw8.exe | fSMYR68E.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
Amadey(PID) Process(504) jAk6FVw8.exe C294.154.35.25 URLhttp://94.154.35.25/di9ku38f/index.php Version5.55 Options Drop directory96a319e745 Drop nameSrxelqcif.exe Strings (125)os: " && timeout 1 && del \App && | shutdown -s -t 0 Panda Security r= ::: " && ren pc: random ProductName bi: # POST 2016 msi Content-Type: application/x-www-form-urlencoded 0123456789 0000043f un: st=s S-%lu- SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName AVAST Software cmd Content-Disposition: form-data; name="data"; filename=" SOFTWARE\Microsoft\Windows NT\CurrentVersion lv: <c> SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders 00000423 <d> cred.dll|clip.dll| exe og: Srxelqcif.exe Powershell.exe Comodo 5.55 && Exit" Startup %-lu DefaultSettings.YResolution SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\ 00000422 rundll32 2019 ps1 ar: %USERPROFILE% vs: -executionpolicy remotesigned -File " shell32.dll /k WinDefender ------ http:// cred.dll Main Bitdefender .jpg ?scr=1 "taskkill /f /im " rb CurrentBuild id: Doctor Web SOFTWARE\Microsoft\Windows\CurrentVersion\Run 94.154.35.25 ESET Sophos 00000419 VideoID dm: 96a319e745 Keyboard Layout\Preload AVG ------ SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce 2025 -- " DefaultSettings.XResolution /quiet Norton SYSTEM\ControlSet001\Services\BasicDisplay\Video dll zip = ProgramData\ cmd /C RMDIR /s/q /Plugins/ e1 Programs d1 &unit= Rem ComputerName 2022 rundll32.exe e3 e2 Content-Type: multipart/form-data; boundary=---- -%lu clip.dll av: kernel32.dll GetNativeSystemInfo 360TotalSecurity \0000 "
Content-Type: application/octet-stream SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders +++ Kaspersky Lab Avira \ GET /di9ku38f/index.php sd: abcdefghijklmnopqrstuvwxyz0123456789-_ wb https:// -unicode- | |||||||||||||||
| 512 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\1E08s6.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\1E08s6.exe | E6D5DE0F24C9E8CE95EC860FDF075B29.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3064,i,10569411956637408946,7925708704977106550,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 620 | /x -standby-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | ls1FDZl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Power Settings Command-Line Tool Exit code: 3221226324 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | NSudoLG -U:T -P:E -UseCurrentConsole C:\Users\admin\AppData\Local\Temp\y9Hto7f.bat any_word | C:\Users\admin\AppData\Local\Temp\Work\NSudoLG.exe | — | cmd.exe | |||||||||||
User: admin Company: M2-Team Integrity Level: HIGH Description: NSudo Launcher Exit code: 0 Version: 9.0.2676.0 Modules
| |||||||||||||||
| 768 | reg query "HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System" /v "EnableLUA" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
73 921
Read events
73 842
Write events
76
Delete events
3
Modification events
| (PID) Process: | (5436) reg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize |
| Operation: | write | Name: | AppsUseLightTheme |
Value: 0 | |||
| (PID) Process: | (2504) nircmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (2504) nircmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (6332) reg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize |
| Operation: | write | Name: | AppsUseLightTheme |
Value: 0 | |||
| (PID) Process: | (504) jAk6FVw8.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (504) jAk6FVw8.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (504) jAk6FVw8.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4164) reg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize |
| Operation: | write | Name: | AppsUseLightTheme |
Value: 0 | |||
| (PID) Process: | (4856) reg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize |
| Operation: | write | Name: | AppsUseLightTheme |
Value: 0 | |||
| (PID) Process: | (504) jAk6FVw8.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 76995f989d.exe |
Value: C:\Users\admin\AppData\Local\Temp\10283040101\76995f989d.exe | |||
Executable files
91
Suspicious files
52
Text files
77
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7048 | 2g8113.exe | C:\w0HZ6G0\pQSzSyAf.zip | compressed | |
MD5:AB6EE96E141005500BE31BCA28023E34 | SHA256:CF152AD95D4E8ACA519A31776F3B010B3540ADC27A1AA6E041724A2EEA115D9B | |||
| 7048 | 2g8113.exe | C:\w0HZ6G0\Mj7TYuJI.exe | executable | |
MD5:426CCB645E50A3143811CFA0E42E2BA6 | SHA256:CF878BFBD9ED93DC551AC038AFF8A8BBA4C935DDF8D48E62122BDDFDB3E08567 | |||
| 7048 | 2g8113.exe | C:\w0HZ6G0\DNqCKF65.exe | executable | |
MD5:F2932E15E61344AD196E3B478C088350 | SHA256:05680A9BB2B08D0CCD25D1D274F78C971609AE2C95D3427F780C46ECFBC296C1 | |||
| 3720 | DNqCKF65.exe | C:\Users\admin\AppData\Local\Temp\y9Hto7f.bat | text | |
MD5:C2DF80F14AD294A279ED4F4F251960A5 | SHA256:D6E5A4BFA17BC9B9D9AF48FB6CEE2024477F309B48E670F8F49B7720205AAA43 | |||
| 3720 | DNqCKF65.exe | C:\Users\admin\AppData\Local\Temp\Work\nircmd.exe | executable | |
MD5:4A9DA765FD91E80DECFD2C9FE221E842 | SHA256:2E81E048AB419FDC6E5F4336A951BD282ED6B740048DC38D7673678EE3490CDA | |||
| 6340 | E6D5DE0F24C9E8CE95EC860FDF075B29.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\2g8113.exe | executable | |
MD5:2DAC651DF2196423BF3E5296CEB93A61 | SHA256:D7AB100EEC217AE7EDDE5AD39EC0775E7EBCA760ED758C63C412A6253DE6A9D5 | |||
| 7048 | 2g8113.exe | C:\w0HZ6G0\fSMYR68E.exe | executable | |
MD5:F108EEC016FC381866F431CB9BEDE311 | SHA256:3D5FEFCAE2589CEF6B68954167FCA4851FBD74AAD3228D6FAB4347D6ED95047F | |||
| 3720 | DNqCKF65.exe | C:\Users\admin\AppData\Local\Temp\Work\7z.exe | executable | |
MD5:426CCB645E50A3143811CFA0E42E2BA6 | SHA256:CF878BFBD9ED93DC551AC038AFF8A8BBA4C935DDF8D48E62122BDDFDB3E08567 | |||
| 3720 | DNqCKF65.exe | C:\Users\admin\AppData\Local\Temp\Work\cecho.exe | executable | |
MD5:E783BC59D0ED6CFBD8891F94AE23D1B3 | SHA256:5C1211559DDA10592CFEDD57681F18F4A702410816D36EDA95AEE6C74E3C6A47 | |||
| 3720 | DNqCKF65.exe | C:\Users\admin\AppData\Local\Temp\Work\NSudoLG.exe | executable | |
MD5:423129DDB24FB923F35B2DD5787B13DD | SHA256:5094AD359D8CF6DC5324598605C35F68519CC5AF9C7ED5427E02A6B28121E4C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
102
DNS requests
73
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
504 | jAk6FVw8.exe | POST | 200 | 94.154.35.25:80 | http://94.154.35.25/di9ku38f/index.php | US | text | 8 b | malicious |
504 | jAk6FVw8.exe | GET | 200 | 45.141.233.196:80 | http://45.141.233.196/newdef/random.exe | DE | executable | 2.12 Mb | unknown |
4520 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
504 | jAk6FVw8.exe | GET | 200 | 45.141.233.196:80 | http://45.141.233.196/luma/random.exe | DE | executable | 1.72 Mb | unknown |
504 | jAk6FVw8.exe | POST | 200 | 94.154.35.25:80 | http://94.154.35.25/di9ku38f/index.php | US | text | 4 b | malicious |
504 | jAk6FVw8.exe | GET | 200 | 45.141.233.196:80 | http://45.141.233.196/files/7677226784/6olpur0.exe | DE | executable | 825 Kb | unknown |
504 | jAk6FVw8.exe | POST | 200 | 94.154.35.25:80 | http://94.154.35.25/di9ku38f/index.php | US | text | 4 b | malicious |
504 | jAk6FVw8.exe | GET | 200 | 45.141.233.196:80 | http://45.141.233.196/test/amnew.exe | DE | executable | 416 Kb | unknown |
504 | jAk6FVw8.exe | GET | 200 | 45.141.233.196:80 | http://45.141.233.196/files/7002513081/ls1FDZl.exe | DE | executable | 7.53 Mb | unknown |
7356 | huran.exe | POST | 200 | 45.141.233.196:80 | http://45.141.233.196/ho4lu3dk/index.php | DE | text | 7 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5288 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
512 | 1E08s6.exe | 104.102.49.106:443 | steamcommunity.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
504 | jAk6FVw8.exe | 94.154.35.25:80 | — | WINDSTREAM | US | malicious |
504 | jAk6FVw8.exe | 45.141.233.196:80 | — | Euro Crypt EOOD | DE | unknown |
4520 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4520 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
perpenab.icu |
| malicious |
royaltbn.xyz |
| malicious |
columnez.shop |
| malicious |
mixp.digital |
| malicious |
woodenso.top |
| malicious |
foundrr.bet |
| malicious |
onyxistn.bet |
| malicious |
keulkgl.fun |
| malicious |
Threats
Process | Message |
|---|---|
1E08s6.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
ee7efab4f3.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
IObitUnlocker.exe | PostAction_Delete |
IObitUnlocker.exe | FileCount:264 |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender Advanced Threat Protection-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Security Health-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Storage Health-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender Advanced Threat Protection-------- |