| download: | mrdfile.exe |
| Full analysis: | https://app.any.run/tasks/523e31ae-68e8-4c5a-b83c-72a89d46147a |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | October 14, 2019, 14:12:34 |
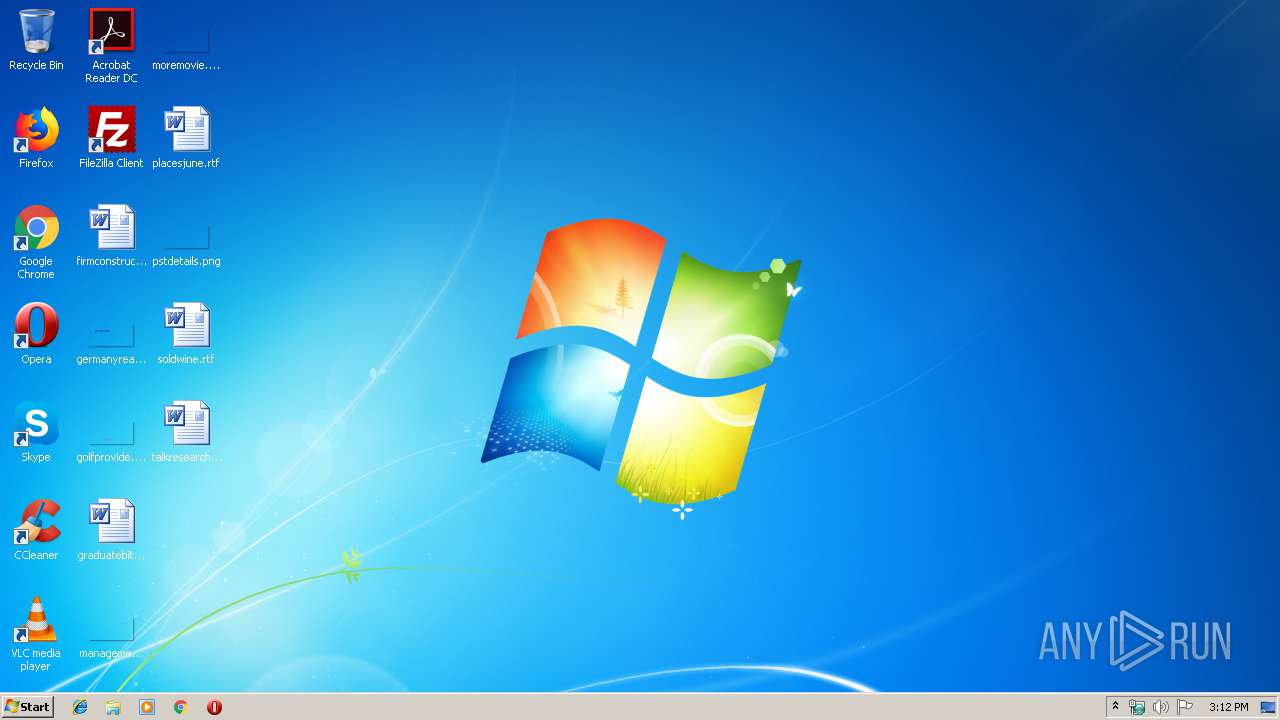
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0E6DCC976AA7A11A1FF74DDA918BDE06 |
| SHA1: | D0AF99ABAA71D1F1DBC37C95F2265883C54AEEDF |
| SHA256: | 6D27DB5B928684A2CBD0A00CD142F7ED1C0976DCB90EDA15A35797FEE7D90F53 |
| SSDEEP: | 12288:e7W1A0cUJTMXabFFqYOQ2c+2iitv4NXmVW0oViaegs4rilzWpSxTmJrK:cWX3JTMqvjv2miit+aZ4wv4OlUI0rK |
MALICIOUS
Detected Hawkeye Keylogger
- mrdnk.exe (PID: 2816)
Actions looks like stealing of personal data
- vbc.exe (PID: 328)
Connects to CnC server
- mrdnk.exe (PID: 2816)
SUSPICIOUS
Starts itself from another location
- mrdfile.exe (PID: 2172)
Executable content was dropped or overwritten
- mrdfile.exe (PID: 2172)
Application launched itself
- mrdnk.exe (PID: 640)
Creates files in the user directory
- mrdnk.exe (PID: 2816)
- mrdfile.exe (PID: 2172)
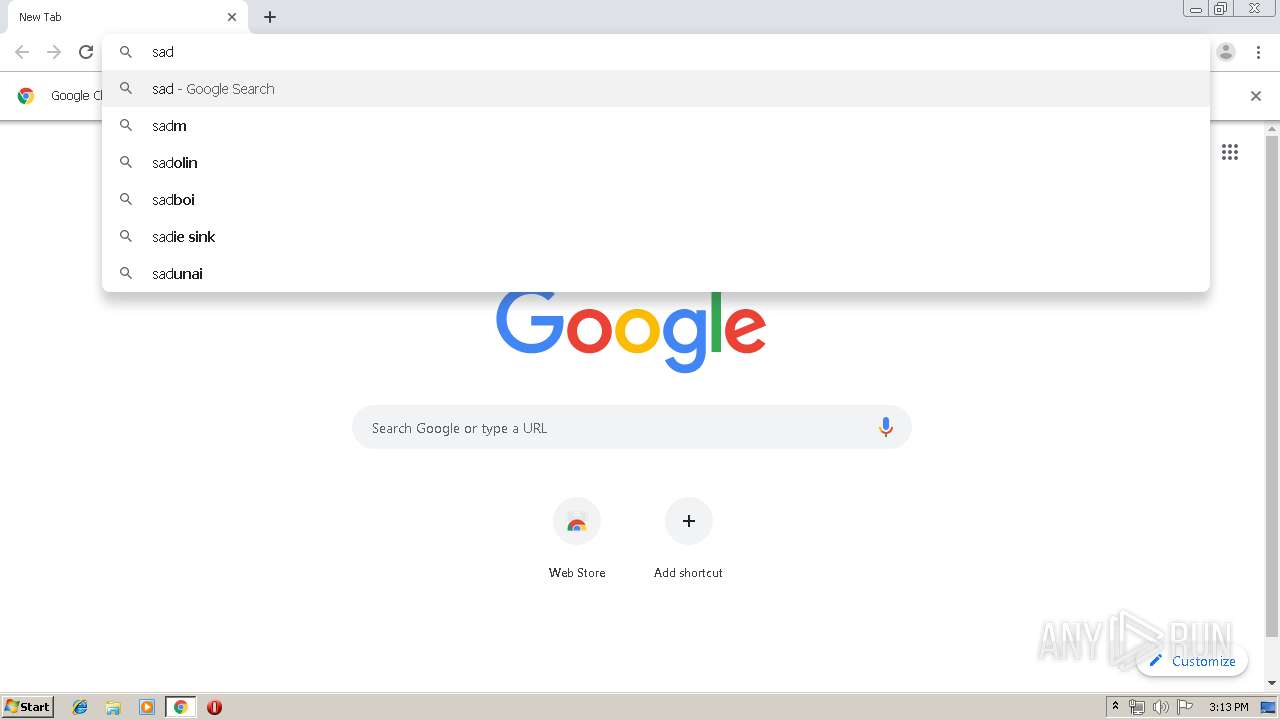
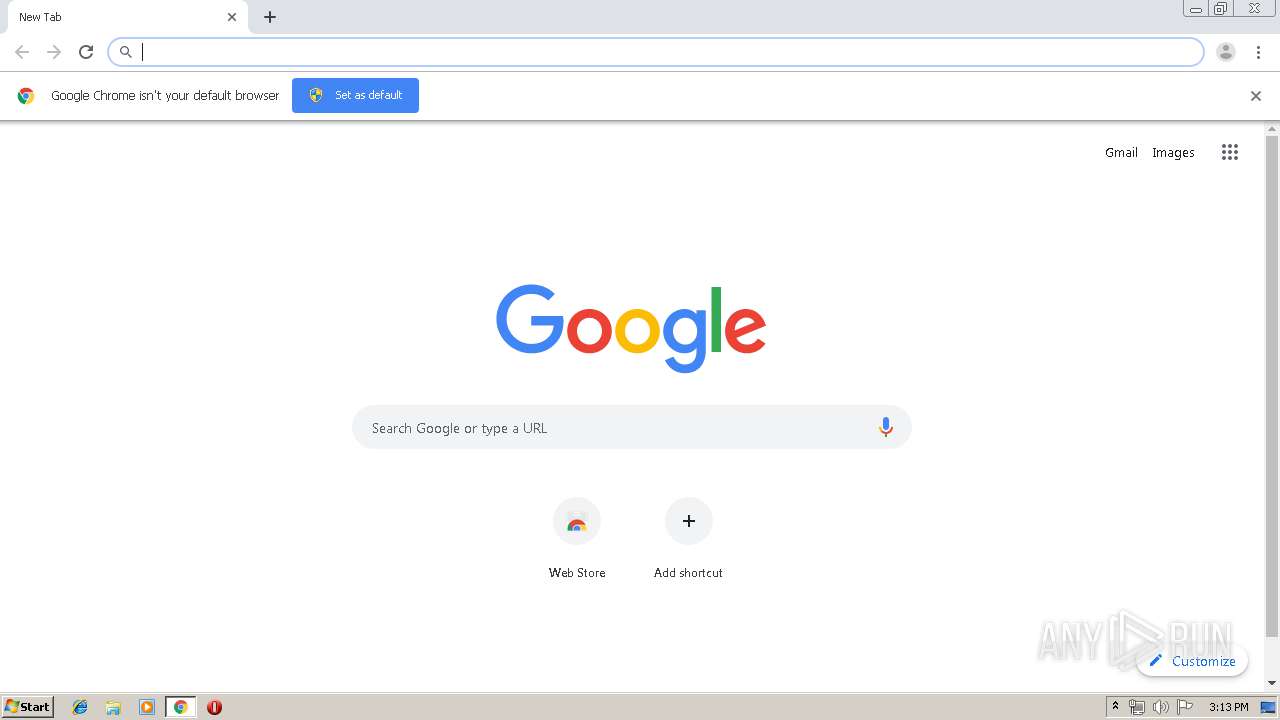
Modifies files in Chrome extension folder
- chrome.exe (PID: 3092)
Checks for external IP
- mrdnk.exe (PID: 2816)
Executes scripts
- mrdnk.exe (PID: 2816)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 2712)
INFO
Reads the hosts file
- chrome.exe (PID: 3092)
- chrome.exe (PID: 2696)
Manual execution by user
- chrome.exe (PID: 3092)
Application launched itself
- chrome.exe (PID: 3092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:04:09 04:38:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 400896 |
| InitializedDataSize: | 441856 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x62ce0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Apr-1992 02:38:05 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 09-Apr-1992 02:38:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00061D28 | 0x00061E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52684 |
DATA | 0x00063000 | 0x00009630 | 0x00009800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.83679 |
BSS | 0x0006D000 | 0x00000DBD | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0006E000 | 0x00002176 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.00378 |
.tls | 0x00071000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00072000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.199108 |
.reloc | 0x00073000 | 0x00006DF0 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.65421 |
.rsrc | 0x0007A000 | 0x000592BC | 0x00059400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.54569 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.79138 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 2.80231 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
861 | 7.54537 | 9408 | Latin 1 / Western European | English - United States | RT_DIALOG |
862 | 7.6215 | 9408 | Latin 1 / Western European | English - United States | RT_DIALOG |
863 | 7.62886 | 9408 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
mpr.dll |
oleaut32.dll |
user32.dll |
Total processes
76
Monitored processes
40
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,2830967663116472932,2698218472910155244,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12735241615972032283 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 328 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holdermail.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | mrdnk.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,2830967663116472932,2698218472910155244,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6015237849241583816 --mojo-platform-channel-handle=568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Users\admin\AppData\Roaming\mrdgfh\mrdnk.exe" | C:\Users\admin\AppData\Roaming\mrdgfh\mrdnk.exe | — | mrdfile.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,2830967663116472932,2698218472910155244,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17650287186353323840 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,2830967663116472932,2698218472910155244,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5115570421098008973 --mojo-platform-channel-handle=3288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,2830967663116472932,2698218472910155244,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16648879336377681925 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,2830967663116472932,2698218472910155244,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11201479048522344819 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3688 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,2830967663116472932,2698218472910155244,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17650129973334248613 --mojo-platform-channel-handle=912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,2830967663116472932,2698218472910155244,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4000797313948870598 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
744
Read events
616
Write events
123
Delete events
5
Modification events
| (PID) Process: | (2816) mrdnk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mrdnk_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2816) mrdnk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mrdnk_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2816) mrdnk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mrdnk_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2816) mrdnk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mrdnk_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2816) mrdnk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mrdnk_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2816) mrdnk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mrdnk_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2816) mrdnk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mrdnk_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2816) mrdnk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mrdnk_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2816) mrdnk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mrdnk_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2816) mrdnk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mrdnk_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
30
Text files
271
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2172 | mrdfile.exe | C:\Users\admin\AppData\Roaming\mrdgfh\mrdnk.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\feca4f26-b913-416f-8fb6-75446ca7222c.tmp | — | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2172 | mrdfile.exe | C:\Users\admin\AppData\Roaming\mrdgfh\mrdnk.exe | executable | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2816 | mrdnk.exe | C:\Users\admin\AppData\Roaming\pidloc.txt | text | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39e828.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
38
DNS requests
27
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
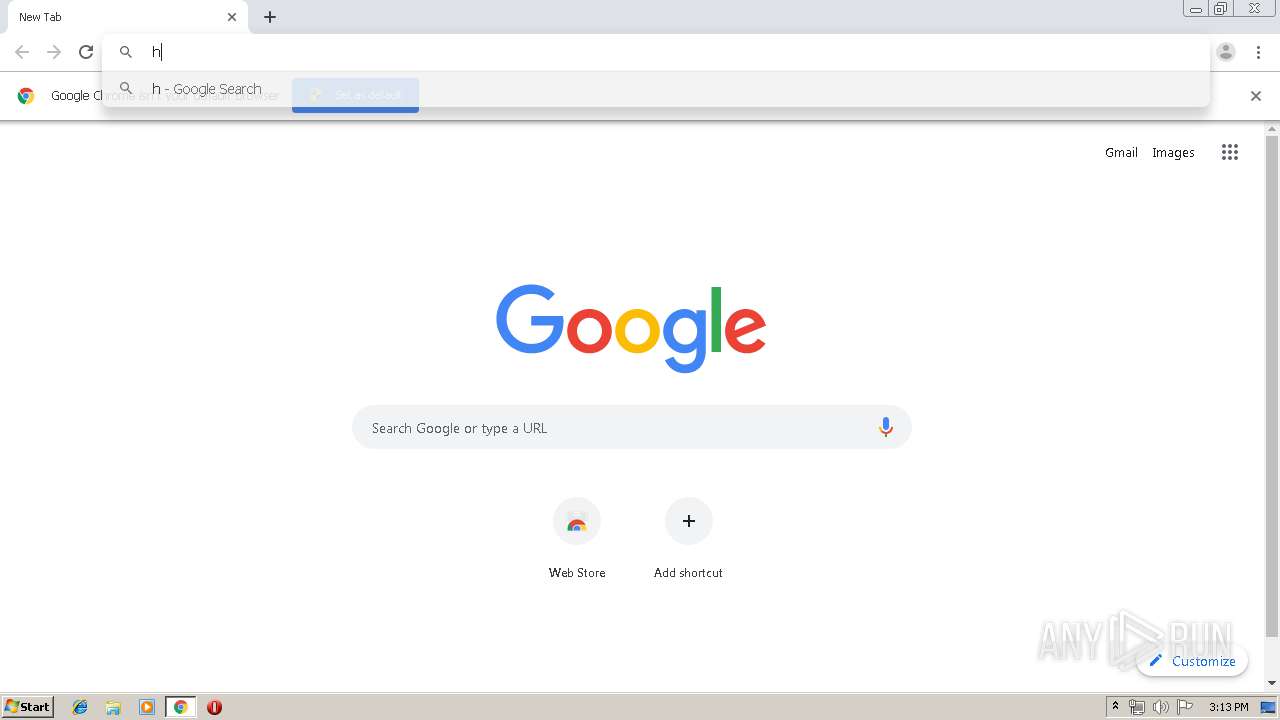
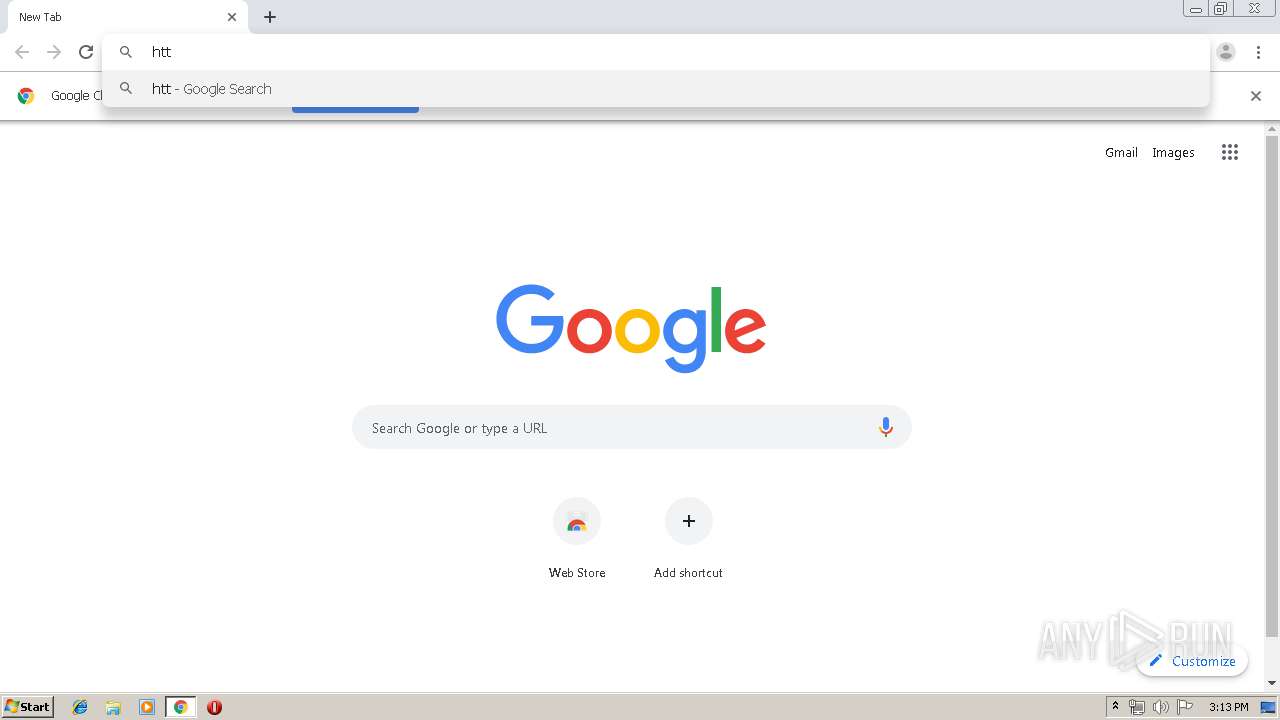
2816 | mrdnk.exe | GET | 301 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | — | — | shared |
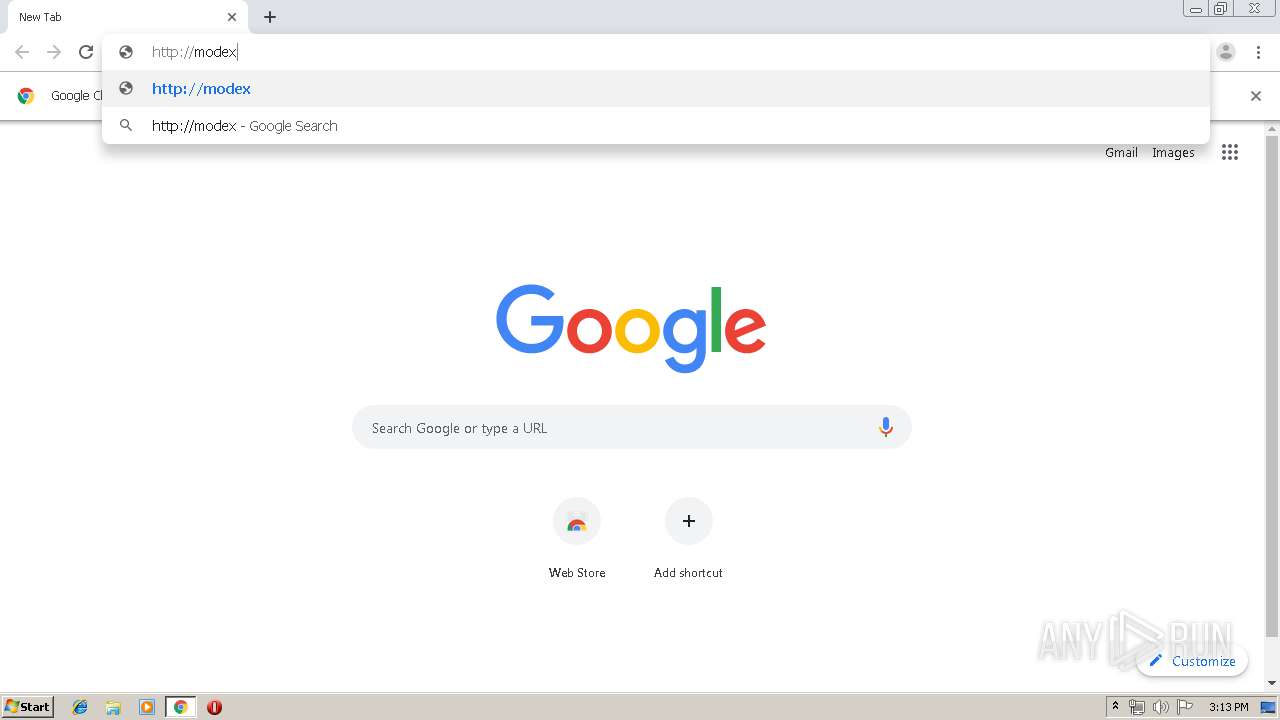
2696 | chrome.exe | GET | — | 162.144.128.116:80 | http://modexcourier.eu/mrdfile/mrdfile.exe | US | — | — | malicious |
2696 | chrome.exe | GET | 200 | 84.15.64.13:80 | http://r2---sn-cpux-8ovs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.206.175.219&mm=28&mn=sn-cpux-8ovs&ms=nvh&mt=1571061900&mv=u&mvi=1&pl=21&shardbypass=yes | LT | crx | 862 Kb | whitelisted |
2696 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 512 b | whitelisted |
2696 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 517 b | whitelisted |
2696 | chrome.exe | GET | 200 | 84.15.64.13:80 | http://r2---sn-cpux-8ovs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.206.175.219&mm=28&mn=sn-cpux-8ovs&ms=nvh&mt=1571062337&mv=m&mvi=1&pl=21&shardbypass=yes | LT | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2816 | mrdnk.exe | 104.16.155.36:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
2696 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.16.131:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2816 | mrdnk.exe | 104.16.155.36:443 | whatismyipaddress.com | Cloudflare Inc | US | shared |
2696 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.22.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.23.174:443 | ogs.google.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.22.99:443 | www.google.lt | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
smtp.reportlog.top |
| malicious |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2816 | mrdnk.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
2816 | mrdnk.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spyware.HawkEyeKeyLogger (IP Chck) |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2816 | mrdnk.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2816 | mrdnk.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3 ETPRO signatures available at the full report