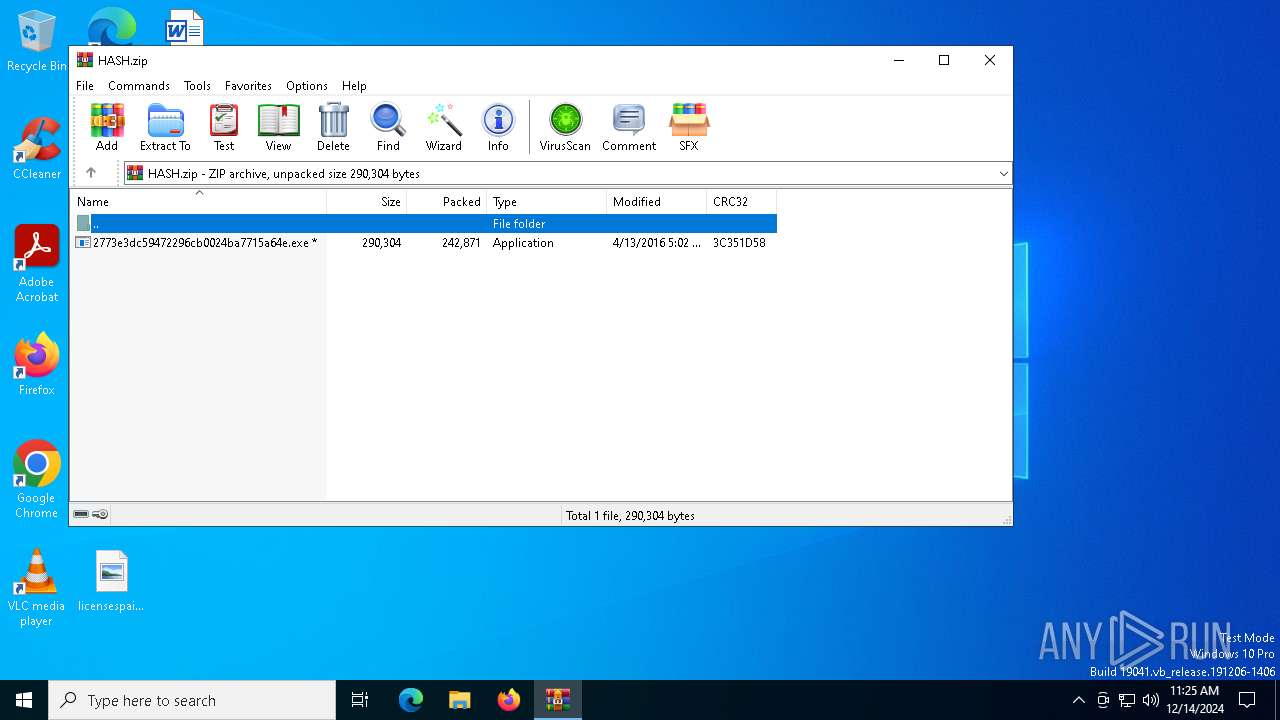
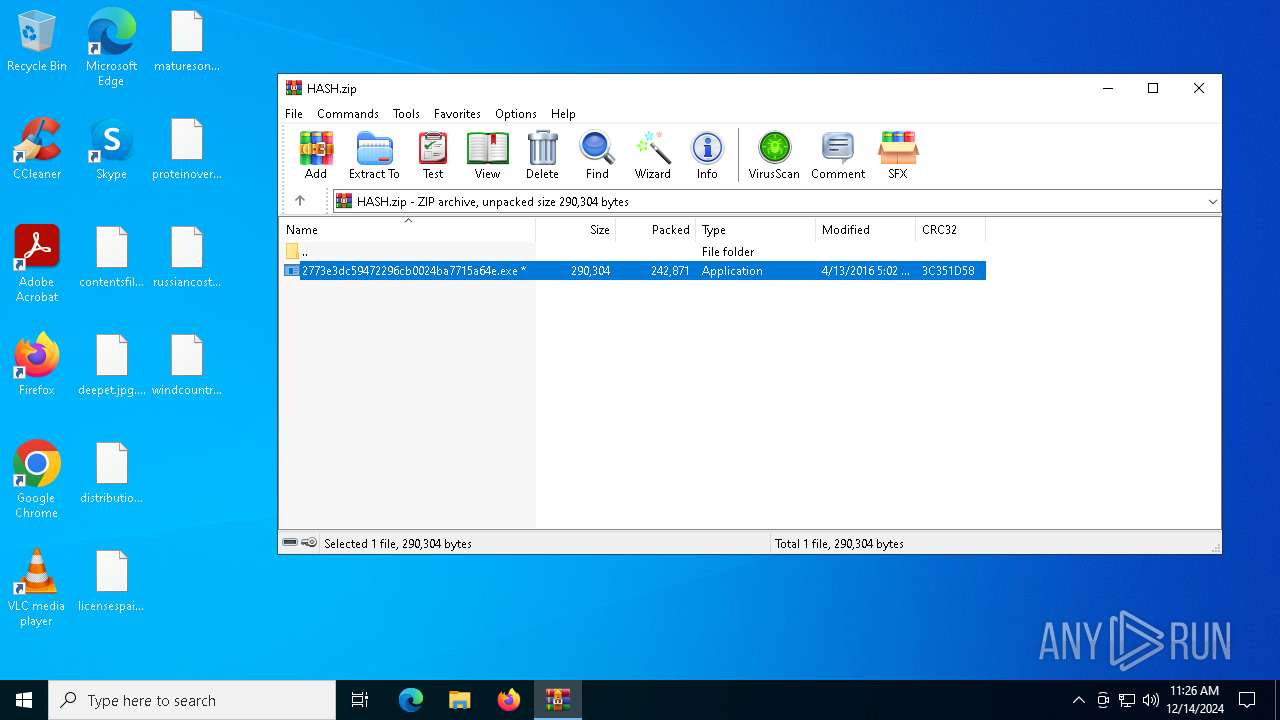
| File name: | HASH.zip |
| Full analysis: | https://app.any.run/tasks/0935f254-1097-4983-8dc6-373536cf0ac1 |
| Verdict: | Malicious activity |
| Threats: | The Jigsaw ransomware, initially detected in 2016, encrypts files on compromised systems and requires a ransom payment in Bitcoin. If the ransom is not paid, the malware starts deleting files, increasing the pressure on victims to comply. Its source code is publicly accessible, allowing various threat actors to customize and repurpose the malware for different objectives. |
| Analysis date: | December 14, 2024, 11:25:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
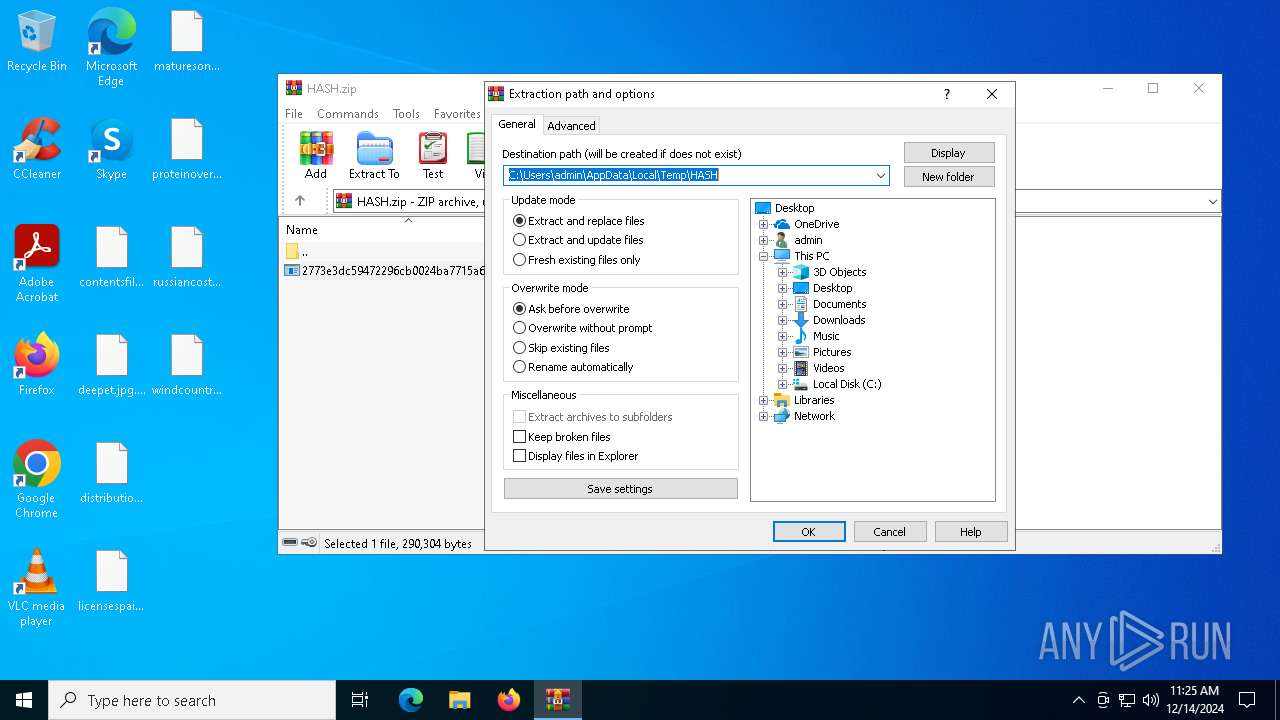
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | B877491211BFCFF842912FD055588799 |
| SHA1: | D19E7A79B08BAE01B00AC447F6CFD236EF055474 |
| SHA256: | 6D230F1F3A10F78741545A9D6FBD43BBB0A6A55FEFCA245760D5DB92AC3CC1CD |
| SSDEEP: | 6144:zY4/Ezz+ML2q7kvNcezVavJdZP/B8ccT:z2XAGmNpdccT |
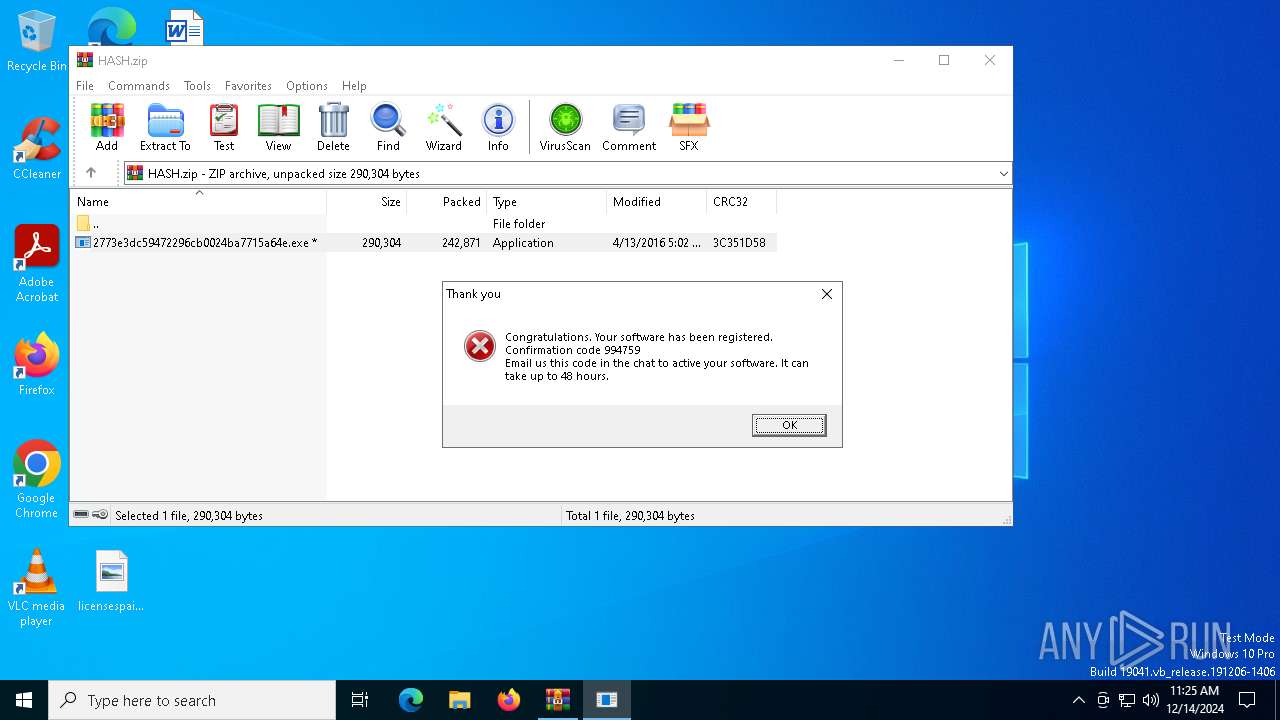
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 4864)
Changes the autorun value in the registry
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
JIGSAW has been detected
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
RANSOMWARE has been detected
- drpbx.exe (PID: 6884)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4864)
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
Executable content was dropped or overwritten
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
Reads the date of Windows installation
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
Starts itself from another location
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
Creates file in the systems drive root
- drpbx.exe (PID: 6884)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 4864)
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
Checks supported languages
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
- drpbx.exe (PID: 6884)
Creates files or folders in the user directory
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4864)
Reads the computer name
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
- drpbx.exe (PID: 6884)
Process checks computer location settings
- 2773e3dc59472296cb0024ba7715a64e.exe (PID: 6824)
Reads the machine GUID from the registry
- drpbx.exe (PID: 6884)
Creates files in the program directory
- drpbx.exe (PID: 6884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
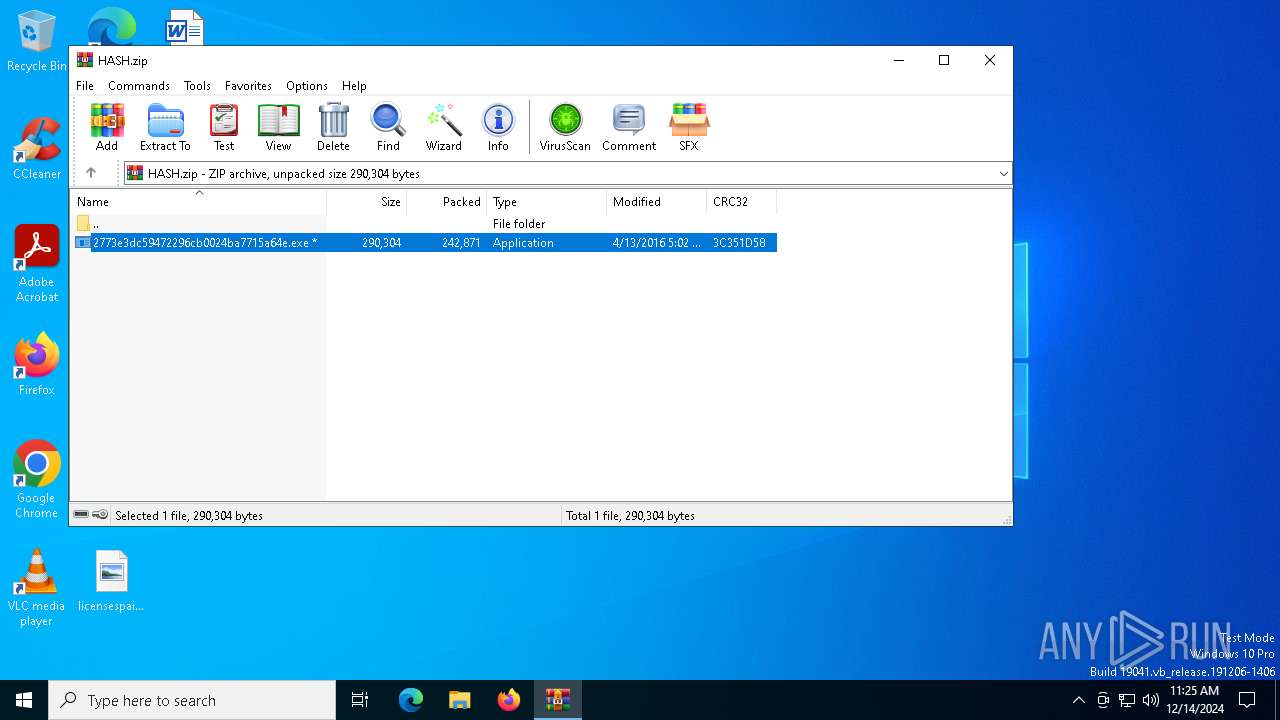
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:04:13 18:02:34 |
| ZipCRC: | 0x3c351d58 |
| ZipCompressedSize: | 242871 |
| ZipUncompressedSize: | 290304 |
| ZipFileName: | 2773e3dc59472296cb0024ba7715a64e.exe |
Total processes
129
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
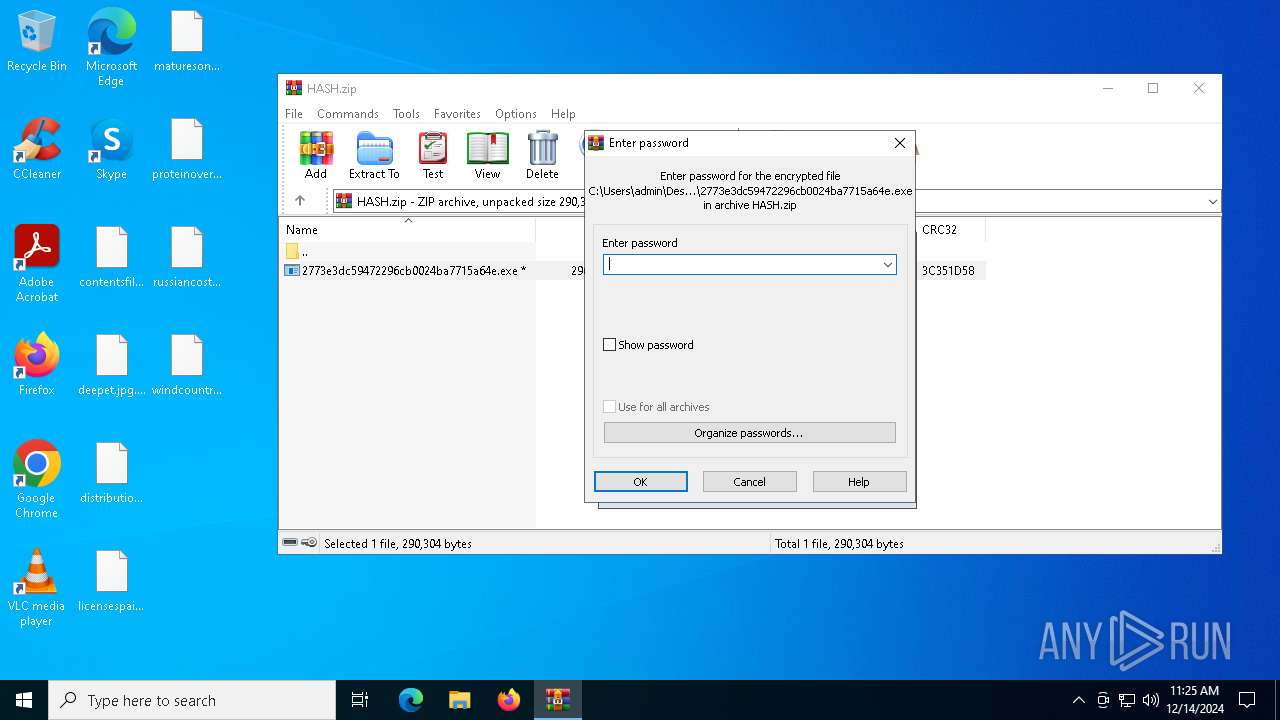
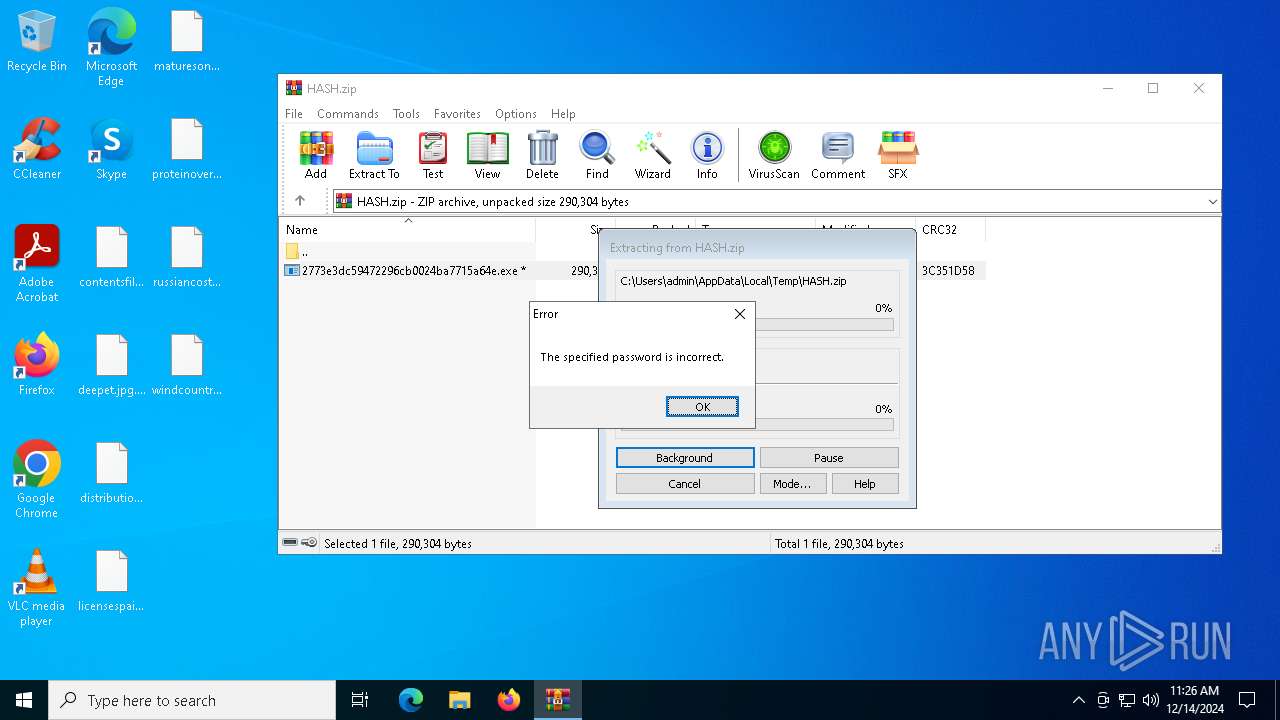
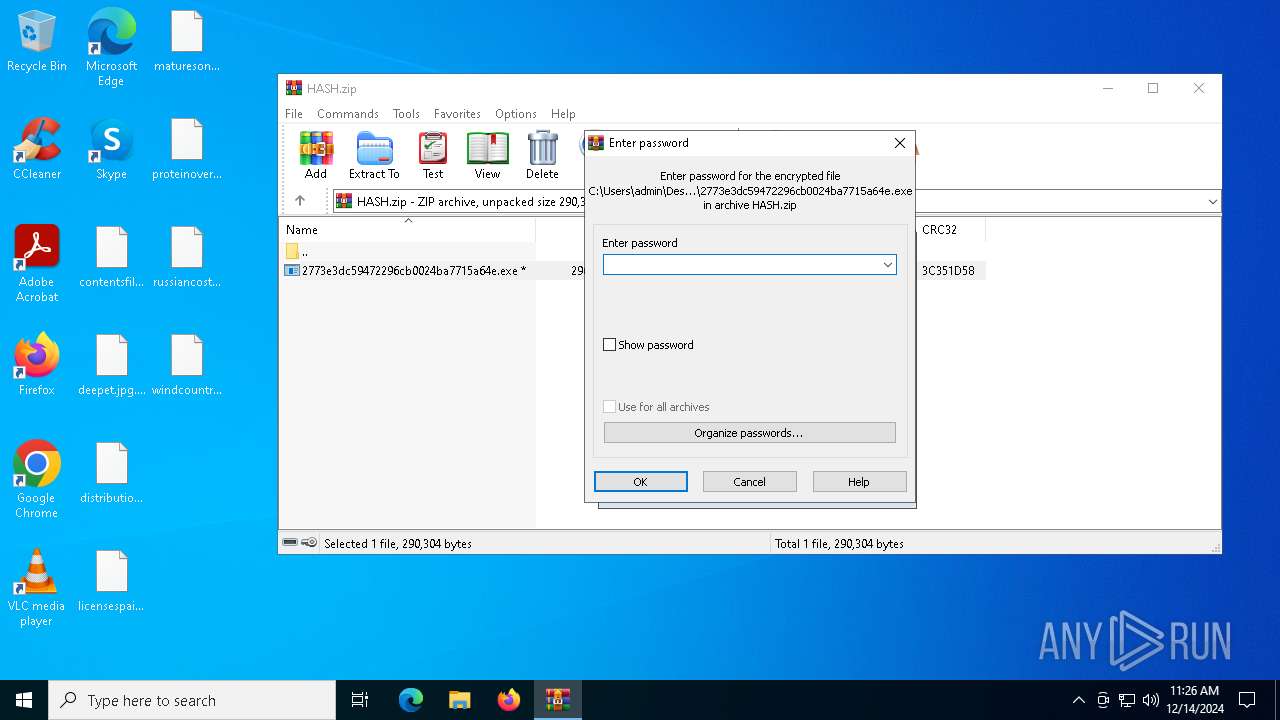
| 4864 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\HASH.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6824 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb4864.33172\2773e3dc59472296cb0024ba7715a64e.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb4864.33172\2773e3dc59472296cb0024ba7715a64e.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 6884 | "C:\Users\admin\AppData\Local\Drpbx\drpbx.exe" C:\Users\admin\AppData\Local\Temp\Rar$EXb4864.33172\2773e3dc59472296cb0024ba7715a64e.exe | C:\Users\admin\AppData\Local\Drpbx\drpbx.exe | 2773e3dc59472296cb0024ba7715a64e.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Version: 37.0.2.5583 Modules
| |||||||||||||||
Total events
10 245
Read events
10 217
Write events
15
Delete events
13
Modification events
| (PID) Process: | (4864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\HASH.zip | |||
| (PID) Process: | (4864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
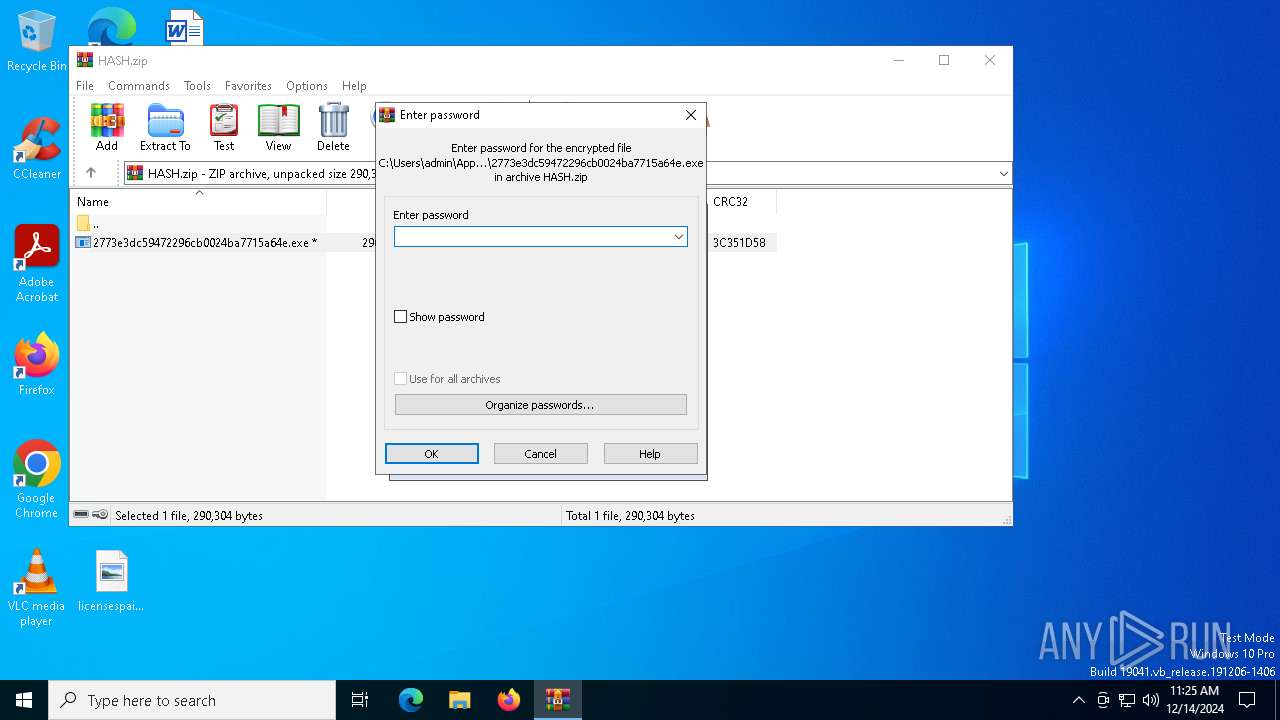
| (PID) Process: | (4864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6824) 2773e3dc59472296cb0024ba7715a64e.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | firefox.exe |
Value: C:\Users\admin\AppData\Roaming\Frfx\firefox.exe | |||
Executable files
4
Suspicious files
28
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4864.33172\2773e3dc59472296cb0024ba7715a64e.exe | executable | |
MD5:2773E3DC59472296CB0024BA7715A64E | SHA256:3AE96F73D805E1D3995253DB4D910300D8442EA603737A1428B613061E7F61E7 | |||
| 6884 | drpbx.exe | C:\Users\admin\Desktop\deepet.jpg.fun | binary | |
MD5:268E4AF1536B60B7D4CDC3B00F859E2C | SHA256:A6C17A9E5F7A3107E6673491AAA31335932D505A1AA8BBA35D2CA4152A711137 | |||
| 6884 | drpbx.exe | C:\Users\admin\Documents\alreadyaudio.rtf.fun | binary | |
MD5:5F24C64749168BB6172C1E1E5ED5EFF6 | SHA256:A156BD4BED163081AD927F4732B687496ACBDA2AA86CAA74B916BD72B5C4D605 | |||
| 6884 | drpbx.exe | C:\Users\admin\Desktop\distributionfucking.rtf.fun | binary | |
MD5:F504566A1808B0E96ACBDDD338C29ACF | SHA256:B474D1A30BC66CDB70C2DFA47404209D73146D7DE477FE894FA02B8B3F124EED | |||
| 6884 | drpbx.exe | C:\Users\admin\Desktop\contentsfile.png.fun | binary | |
MD5:EE47D3D038D5755AA91FB3C667B3E7DF | SHA256:1659160DED3A70956E426DD54669BECCF6AC0EE03DFD51A27B0ECE3F2A4E4F13 | |||
| 6884 | drpbx.exe | C:\Users\admin\Desktop\licensespain.png.fun | binary | |
MD5:04C833BD30F7136D3D284804CE48EBFC | SHA256:0BB9F7C8ADB22ECCDE45B1F964A745F144A70672D695150C2AC85B81B39C828D | |||
| 6884 | drpbx.exe | C:\Users\admin\Desktop\proteinoverall.rtf.fun | binary | |
MD5:5DF16994CCA517A4C3B91FC736C55DD2 | SHA256:765AE82ECAF6095837B3F97D88281167DF4A66E7B424E4D40D1D15298794F121 | |||
| 6884 | drpbx.exe | C:\Users\admin\Documents\Database1.accdb.fun | binary | |
MD5:EE9E047AA1E8541C84F47BC7F0B8035A | SHA256:BEAC5CD010757E313D0ED73AA9778C72533A5015AB6CDE8C82099FE43FF94DBF | |||
| 6884 | drpbx.exe | C:\Users\admin\Desktop\maturesony.rtf.fun | binary | |
MD5:8C0433C6F441B76F413772F1C90853CA | SHA256:91B489C1704CF7AAB93DC5D61058B09E544D7F547840893DC9965F674F9B8467 | |||
| 6884 | drpbx.exe | C:\Users\admin\Documents\constructione.rtf.fun | binary | |
MD5:A0A0CD75C26909DB68F9797B8E3DC4A8 | SHA256:D6BE29A30CDA3FF9B9C3A086522FCF646CDBEE08100359D6F731A3A80F1A47D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
31
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6328 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6328 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7144 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7144 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.170:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |