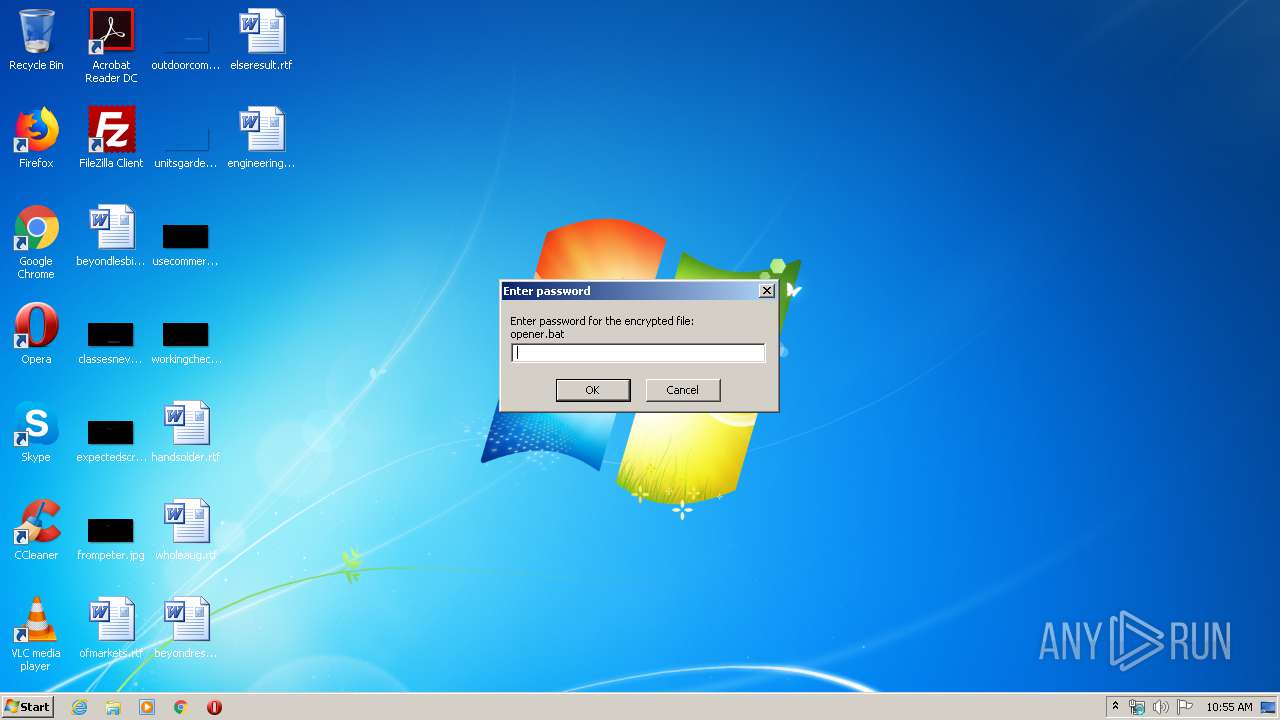
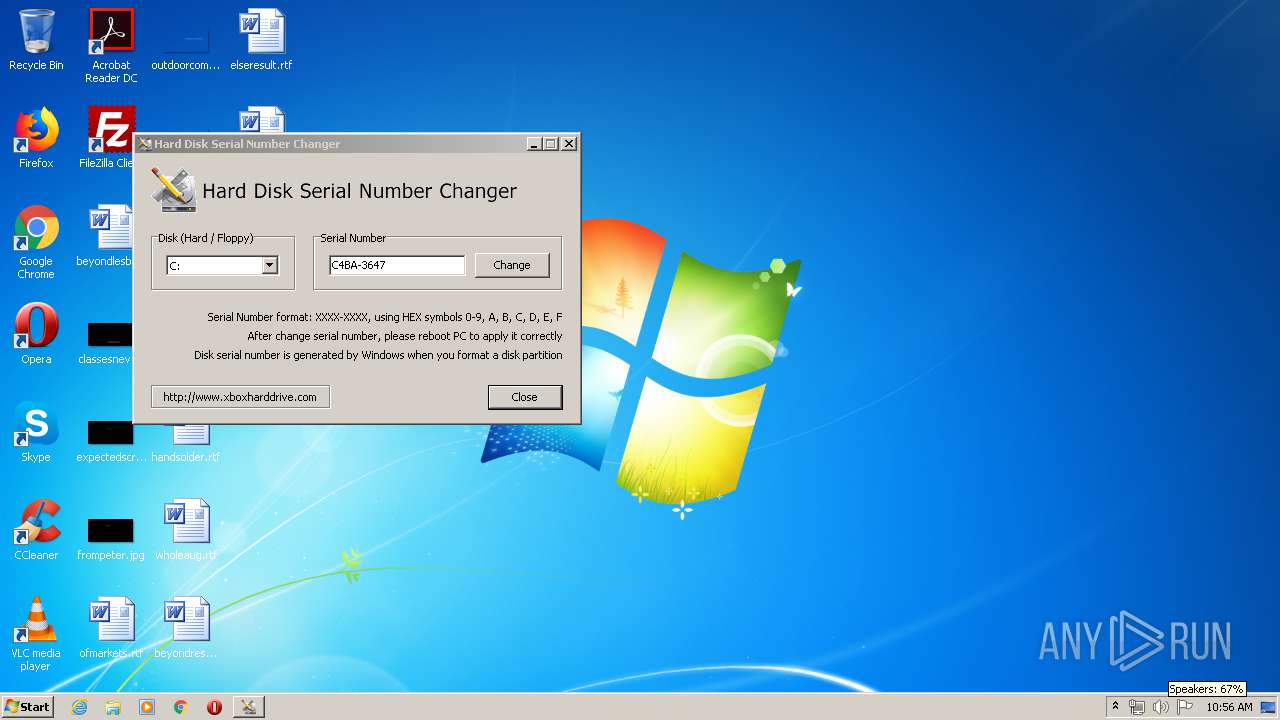
| File name: | Rolex-Hwid-Changer.exe |
| Full analysis: | https://app.any.run/tasks/76dc386b-0c4d-4fb3-ba71-4cf86a116228 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | March 31, 2020, 09:55:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1EC007BB3C836938037AC8A599C43451 |
| SHA1: | C00A7FC65ABAED5EB0A7C5D637ACD72500DC2A7A |
| SHA256: | 6D0C2BCEB8B1171E2424C96F61A7CCA961E1D6E14BB749724A2827D0217226D0 |
| SSDEEP: | 12288:9crNS33L10QdrXP/X+tGfnOFTJkFCzPZCZexDW7DS1UAvm+jXtea6UupSis92PDQ:ANA3R5drXPrfOFFvzPZ7pWy11OQc+CSz |
MALICIOUS
Application was dropped or rewritten from another process
- LogCleaner.exe (PID: 3044)
- LogCleaner.exe (PID: 2992)
- Pibeko6.exe (PID: 3440)
- Pibeko6.exe (PID: 2904)
- hwid.exe (PID: 3400)
Disables Windows Defender
- reg.exe (PID: 3164)
- reg.exe (PID: 3220)
- reg.exe (PID: 660)
- reg.exe (PID: 304)
- reg.exe (PID: 548)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3192)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2868)
- schtasks.exe (PID: 2652)
- schtasks.exe (PID: 3084)
- schtasks.exe (PID: 3008)
- schtasks.exe (PID: 3508)
Modifies Windows Defender service settings
- reg.exe (PID: 1604)
Changes the autorun value in the registry
- RegAsm.exe (PID: 2884)
- RegAsm.exe (PID: 3560)
QUASAR was detected
- RegAsm.exe (PID: 2884)
SUSPICIOUS
Starts CMD.EXE for commands execution
- LogCleaner.exe (PID: 2992)
- Rolex-Hwid-Changer.exe (PID: 3728)
Executable content was dropped or overwritten
- Rolex-Hwid-Changer.exe (PID: 3728)
- RegAsm.exe (PID: 2884)
- Pibeko6.sfx.exe (PID: 2356)
- Pibeko6.sfx.exe (PID: 3112)
- RegAsm.exe (PID: 3560)
Creates or modifies windows services
- reg.exe (PID: 3324)
- reg.exe (PID: 3468)
- reg.exe (PID: 576)
- reg.exe (PID: 3252)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3192)
Reads Internet Cache Settings
- RegAsm.exe (PID: 2884)
- RegAsm.exe (PID: 3560)
Checks for external IP
- RegAsm.exe (PID: 2884)
Starts itself from another location
- Rolex-Hwid-Changer.exe (PID: 3728)
Creates files in the user directory
- RegAsm.exe (PID: 2884)
- RegAsm.exe (PID: 3560)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:27 22:03:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 242176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d759 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2019 20:03:27 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 27-Apr-2019 20:03:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E854 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69231 |
.rdata | 0x00030000 | 0x00009A9C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13286 |
.data | 0x0003A000 | 0x000213D0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.25381 |
.gfids | 0x0005C000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.11154 |
.rsrc | 0x0005D000 | 0x0000DFD0 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63679 |
.reloc | 0x0006B000 | 0x00001FCC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64554 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
83
Monitored processes
42
Malicious processes
6
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender" /v "DisableAntiSpyware" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\Real-Time Protection" /v "DisableScanOnRealtimeEnable" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender" /v "DisableAntiVirus" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | reg add "HKLM\System\CurrentControlSet\Services\WdFilter" /v "Start" /t REG_DWORD /d "4" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | reg delete "HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run" /v "SecurityHealth" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 660 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\Real-Time Protection" /v "DisableOnAccessProtection" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 780 | reg delete "HKCR\Directory\shellex\ContextMenuHandlers\EPP" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1604 | reg add "HKLM\System\CurrentControlSet\Services\WinDefend" /v "Start" /t REG_DWORD /d "4" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1756 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\Real-Time Protection" /v "DisableRealtimeMonitoring" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2052 | reg delete "HKCR\Drive\shellex\ContextMenuHandlers\EPP" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 270
Read events
1 185
Write events
83
Delete events
2
Modification events
| (PID) Process: | (3728) Rolex-Hwid-Changer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3728) Rolex-Hwid-Changer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3112) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3112) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3164) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableIOAVProtection |
Value: 1 | |||
| (PID) Process: | (660) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (1756) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableRealtimeMonitoring |
Value: 1 | |||
| (PID) Process: | (548) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
| (PID) Process: | (2784) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Reporting |
| Operation: | write | Name: | DisableEnhancedNotifications |
Value: 1 | |||
| (PID) Process: | (3592) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\SpyNet |
| Operation: | write | Name: | DisableBlockAtFirstSeen |
Value: 1 | |||
Executable files
7
Suspicious files
7
Text files
5
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\CabB3E7.tmp | — | |
MD5:— | SHA256:— | |||
| 2884 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\TarB3E8.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\CabFF38.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\TarFF39.tmp | — | |
MD5:— | SHA256:— | |||
| 3728 | Rolex-Hwid-Changer.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Pibeko6.sfx.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_0B97942EE72A6E3F514E8E84F294CC72 | binary | |
MD5:— | SHA256:— | |||
| 2884 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 3112 | Pibeko6.sfx.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\Pibeko6.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | RegAsm.exe | C:\Users\admin\Norlan\Ibenho.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BE8B021F9E811DFC8C8A28572A17C05A_0B97942EE72A6E3F514E8E84F294CC72 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
13
DNS requests
6
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2884 | RegAsm.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | text | 321 b | malicious |
2884 | RegAsm.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDL%2FQslYWVuogIAAAAAXGdc | US | der | 472 b | whitelisted |
2884 | RegAsm.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2884 | RegAsm.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFOOHQjK5IlqCAAAAAAyCmA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3560 | RegAsm.exe | 172.217.23.142:443 | drive.google.com | Google Inc. | US | whitelisted |
2884 | RegAsm.exe | 216.38.7.246:6794 | — | GigeNET | US | malicious |
2884 | RegAsm.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
3560 | RegAsm.exe | 172.217.16.193:443 | doc-10-8k-docs.googleusercontent.com | Google Inc. | US | whitelisted |
— | — | 216.38.7.246:6794 | — | GigeNET | US | malicious |
3560 | RegAsm.exe | 216.58.206.14:443 | docs.google.com | Google Inc. | US | whitelisted |
2884 | RegAsm.exe | 172.217.16.193:443 | doc-10-8k-docs.googleusercontent.com | Google Inc. | US | whitelisted |
2884 | RegAsm.exe | 172.217.16.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2884 | RegAsm.exe | 172.217.23.142:443 | drive.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
drive.google.com |
| shared |
ocsp.pki.goog |
| whitelisted |
doc-10-8k-docs.googleusercontent.com |
| shared |
ip-api.com |
| malicious |
doc-0s-40-docs.googleusercontent.com |
| shared |
docs.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2884 | RegAsm.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2884 | RegAsm.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2884 | RegAsm.exe | A Network Trojan was detected | REMOTE [PTsecurity] Quasar.RAT IP Lookup |
1 ETPRO signatures available at the full report