| File name: | Dokkaebi.exe |
| Full analysis: | https://app.any.run/tasks/7ac94b56-7551-4434-8e4f-c928c57327ff |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | October 18, 2023, 03:30:57 |
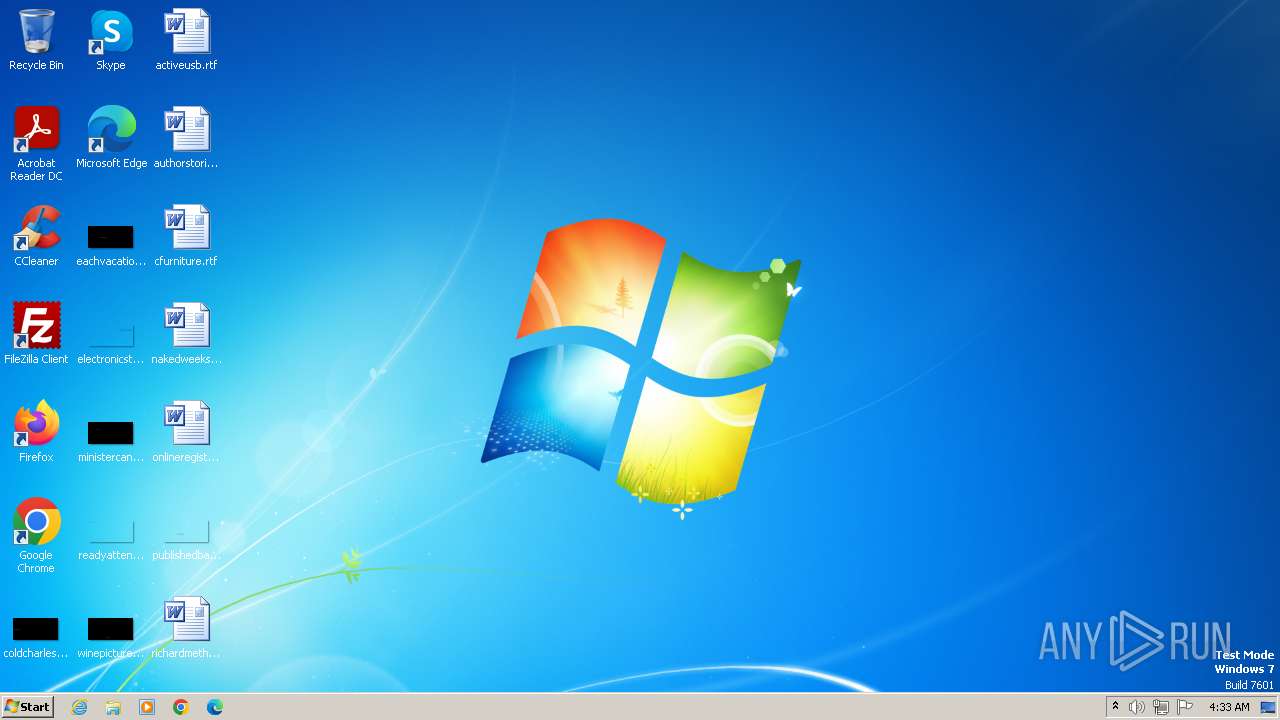
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 4FAA9CDDBC2D18B55D515B4A27AC6B89 |
| SHA1: | 3C74B66344F04C44017E114C7323B63AF13B4C69 |
| SHA256: | 6CF1314C130A41C977AAFCE4585A144762D3FB65F8FE493E836796B989B002CB |
| SSDEEP: | 49152:nvo7RPY2uikNeRyd72MlsLDil92m3GjNsz/3DgIIKIa9j7JoOXOXVttgIzvVLoGm:12uiieRyd72QsLDil92m3GJEDghgY4 |
MALICIOUS
Drops the executable file immediately after the start
- Dokkaebi.exe (PID: 4068)
Application was dropped or rewritten from another process
- Client.exe (PID: 2748)
- Dokkaebi.exe (PID: 4068)
Connects to the CnC server
- Client.exe (PID: 2748)
ASYNCRAT was detected
- Client.exe (PID: 2748)
QUASAR was detected
- Client.exe (PID: 2748)
QUASAR has been detected (YARA)
- Client.exe (PID: 2748)
SUSPICIOUS
Starts itself from another location
- Dokkaebi.exe (PID: 4068)
Reads settings of System Certificates
- Client.exe (PID: 2748)
Connects to unusual port
- Client.exe (PID: 2748)
Reads the Internet Settings
- Client.exe (PID: 2748)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 1192)
- Dokkaebi.exe (PID: 4068)
- Client.exe (PID: 2748)
Reads the computer name
- wmpnscfg.exe (PID: 1192)
- Dokkaebi.exe (PID: 4068)
- Client.exe (PID: 2748)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 1192)
- Dokkaebi.exe (PID: 4068)
- Client.exe (PID: 2748)
Reads Environment values
- Dokkaebi.exe (PID: 4068)
- Client.exe (PID: 2748)
Creates files or folders in the user directory
- Dokkaebi.exe (PID: 4068)
Create files in a temporary directory
- Client.exe (PID: 2748)
Manual execution by a user
- explorer.exe (PID: 1868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(2748) Client.exe
Version1.4.1
C2 (2)homepage-furthermore.gl.at.ply.gg:50765
Sub_DirSubDir
Install_NameClient.exe
Mutex1c419297-eca7-453e-aae9-1c36b10e131e
StartupQuasar Client Startup
Tagchecker
LogDirLogs
SignatureVhnZz47gc/gzQwt4aySfDL3H6Q8KncGNt6vObVpERseOIBAv3I2i5Wgug304Rz2KeL59i7mM+m7emZpoGMxR7hGmuiPyMt9Jm3/ahQzGynH/NoHv86lcHK5/fVlIAW1sYPEYyc3IrL+MBuX4uWgPviNuisfvRoG89ee4TU8FhsfrmQrLUaCrV6/+S4z5fbRi2w6/nLNliDy/flMWESTFvPpRUd31SNQUhIaLcdt0U4wtzeDIRdnydVzoC89xLZuRq8ydorOzYTHN2IPyqQPPtL3chvanr2nYjOowJD3o5/IM...
CertificateMIIE9DCCAtygAwIBAgIQAIZwjo/OBc5IpkMXLWNJbzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMTAxNjAzMTQxN1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAqzJT0Ya0C79JKqgXAgqlNmvMAzSCBrFIjt8d6q/Bm1R0ntcmGx0CacBM5Bi9DwabjAV7qIUu...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:12 17:16:39+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3261952 |
| InitializedDataSize: | 71168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e42e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.1.0 |
| ProductVersionNumber: | 1.4.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | 1.4.0.0 |
| FileDescription: | Application |
| FileVersion: | 1.4.1.0 |
| InternalName: | dokkaebi |
| LegalCopyright: | Dokkaebi |
| LegalTrademarks: | dokkaebi © Satoshicorp 2023 |
| OriginalFileName: | dokkaebi |
| ProductName: | Dokkaebi Server |
| ProductVersion: | 1.4.1.0 |
| AssemblyVersion: | 1.4.1.0 |
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1192 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1868 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | Dokkaebi.exe | ||||||||||||
User: admin Company: 1.4.0.0 Integrity Level: MEDIUM Description: Application Exit code: 0 Version: 1.4.1.0 Modules
Quasar(PID) Process(2748) Client.exe Version1.4.1 C2 (2)homepage-furthermore.gl.at.ply.gg:50765 Sub_DirSubDir Install_NameClient.exe Mutex1c419297-eca7-453e-aae9-1c36b10e131e StartupQuasar Client Startup Tagchecker LogDirLogs SignatureVhnZz47gc/gzQwt4aySfDL3H6Q8KncGNt6vObVpERseOIBAv3I2i5Wgug304Rz2KeL59i7mM+m7emZpoGMxR7hGmuiPyMt9Jm3/ahQzGynH/NoHv86lcHK5/fVlIAW1sYPEYyc3IrL+MBuX4uWgPviNuisfvRoG89ee4TU8FhsfrmQrLUaCrV6/+S4z5fbRi2w6/nLNliDy/flMWESTFvPpRUd31SNQUhIaLcdt0U4wtzeDIRdnydVzoC89xLZuRq8ydorOzYTHN2IPyqQPPtL3chvanr2nYjOowJD3o5/IM... CertificateMIIE9DCCAtygAwIBAgIQAIZwjo/OBc5IpkMXLWNJbzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMTAxNjAzMTQxN1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAqzJT0Ya0C79JKqgXAgqlNmvMAzSCBrFIjt8d6q/Bm1R0ntcmGx0CacBM5Bi9DwabjAV7qIUu... | |||||||||||||||
| 4068 | "C:\Users\admin\AppData\Local\Temp\Dokkaebi.exe" | C:\Users\admin\AppData\Local\Temp\Dokkaebi.exe | — | explorer.exe | |||||||||||
User: admin Company: 1.4.0.0 Integrity Level: MEDIUM Description: Application Exit code: 3 Version: 1.4.1.0 Modules
| |||||||||||||||
Total events
4 739
Read events
4 712
Write events
24
Delete events
3
Modification events
| (PID) Process: | (1192) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{DBCE4F7E-5D94-4309-B0F6-F4B1C166D2F5}\{CC168C0C-4557-483C-8541-CBF00ED61A27} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1192) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{DBCE4F7E-5D94-4309-B0F6-F4B1C166D2F5} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1192) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{30FDD517-EE35-48A0-BBB7-88CECA095FBA} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4068) Dokkaebi.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2748) Client.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4068 | Dokkaebi.exe | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | executable | |
MD5:4FAA9CDDBC2D18B55D515B4A27AC6B89 | SHA256:6CF1314C130A41C977AAFCE4585A144762D3FB65F8FE493E836796B989B002CB | |||
| 2748 | Client.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2748 | Client.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:A52733F7A3DFBFE09A874912056C16A9 | SHA256:43FDFD6E3791B25D93773185B07EB393E0854291781841FA40F9F22BBB9768CD | |||
| 2748 | Client.exe | C:\Users\admin\AppData\Local\Temp\TarD281.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 2748 | Client.exe | C:\Users\admin\AppData\Local\Temp\CabD280.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
5
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2748 | Client.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?678facec5545a1d1 | US | compressed | 61.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2748 | Client.exe | 147.185.221.16:50765 | homepage-furthermore.gl.at.ply.gg | PLAYIT-GG | US | malicious |
2748 | Client.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
2748 | Client.exe | 195.201.57.90:443 | ipwho.is | Hetzner Online GmbH | DE | unknown |
2748 | Client.exe | 172.66.40.240:443 | ipwhois.io | CLOUDFLARENET | US | unknown |
2748 | Client.exe | 104.237.62.212:443 | api.ipify.org | WEBNX | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
homepage-furthermore.gl.at.ply.gg |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ipwho.is |
| malicious |
ipwhois.io |
| unknown |
api.ipify.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2748 | Client.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (Quasar CnC) |
2748 | Client.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
1088 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
1088 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
2748 | Client.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2748 | Client.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] QuasarRAT Successful Connection (CBC_SHA384) |