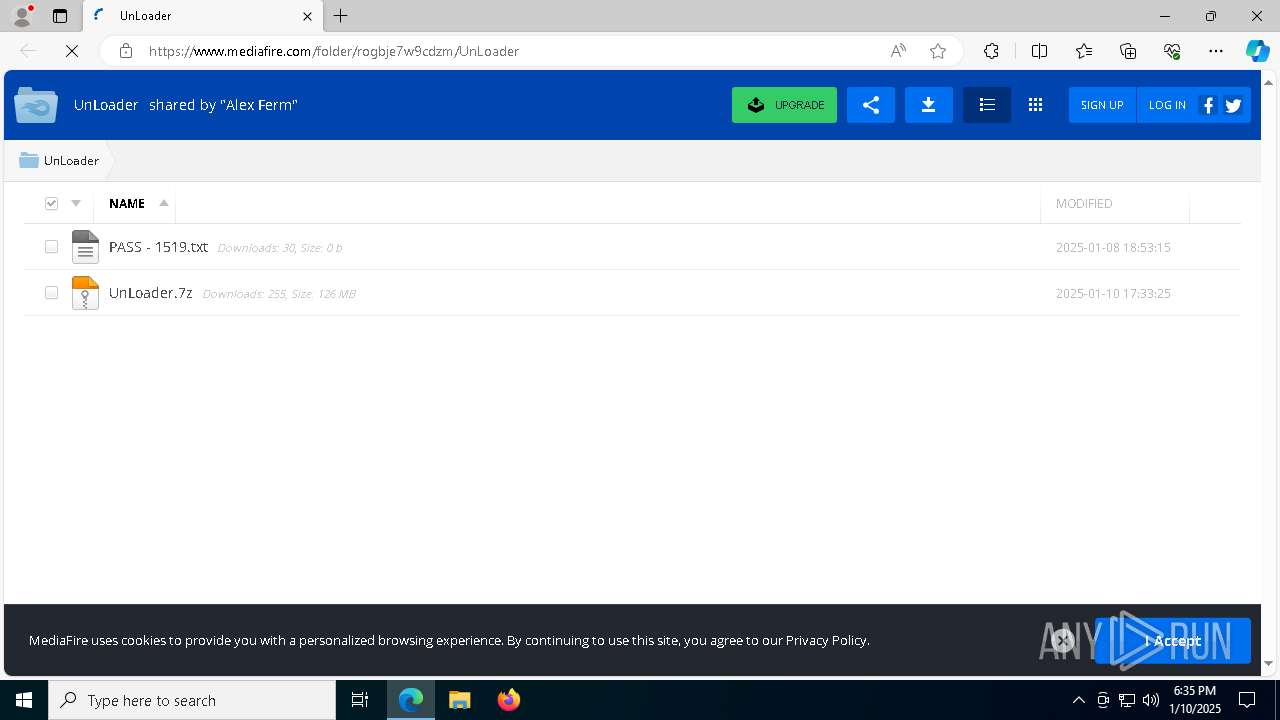
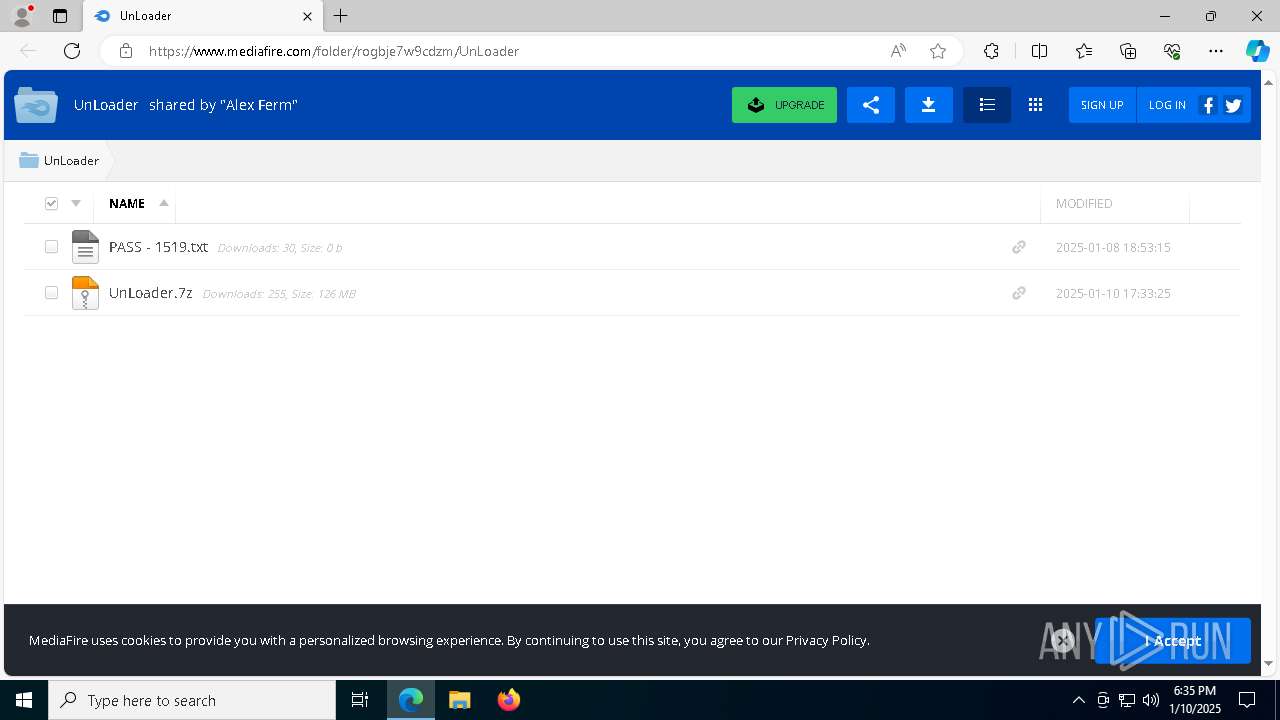
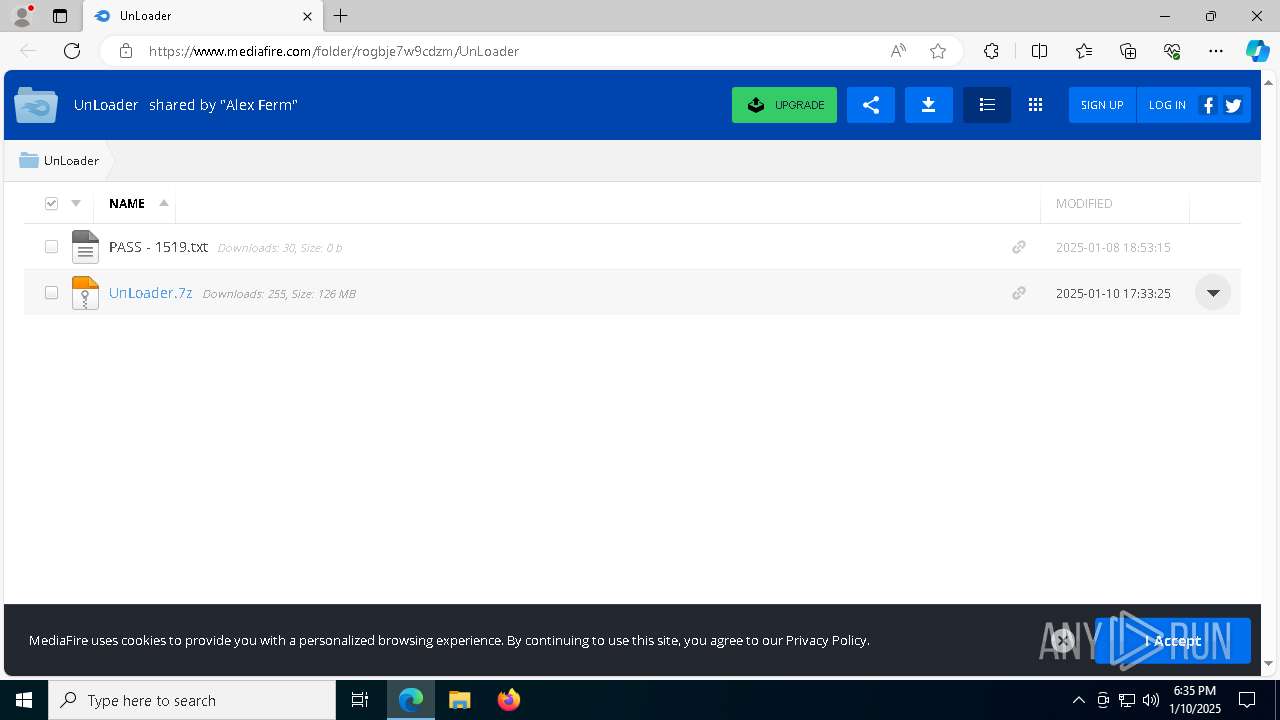
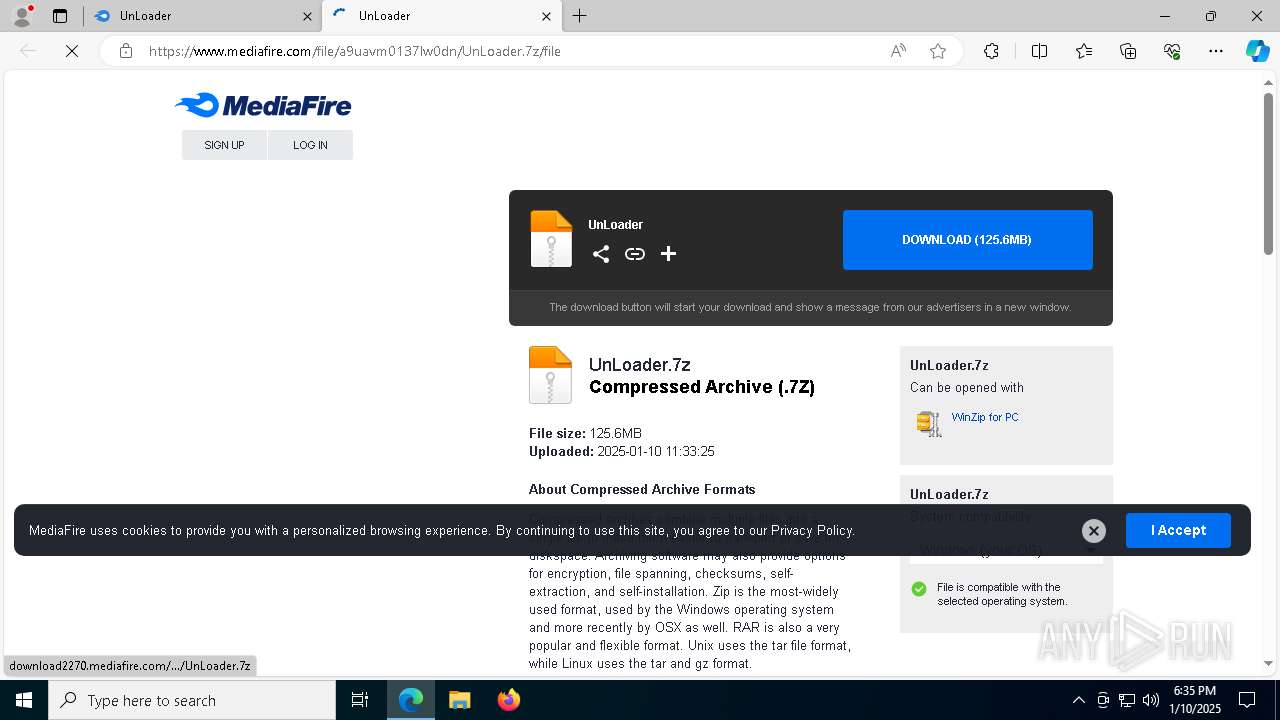
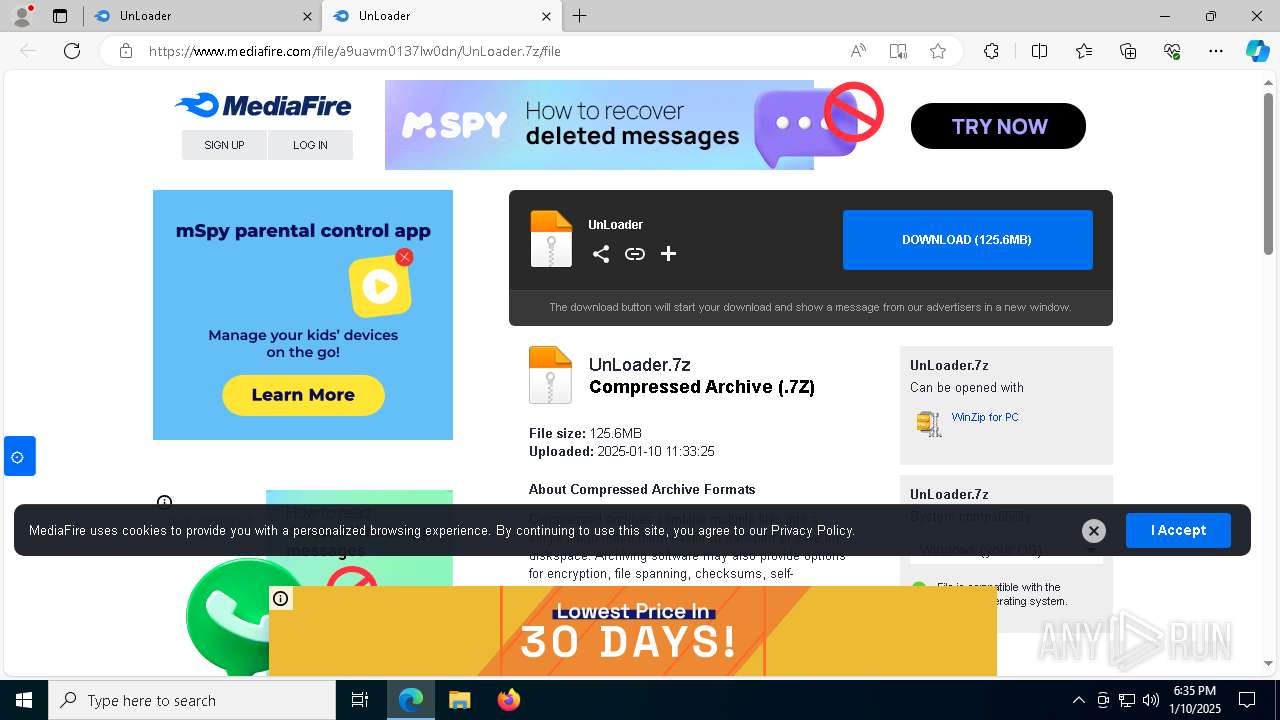
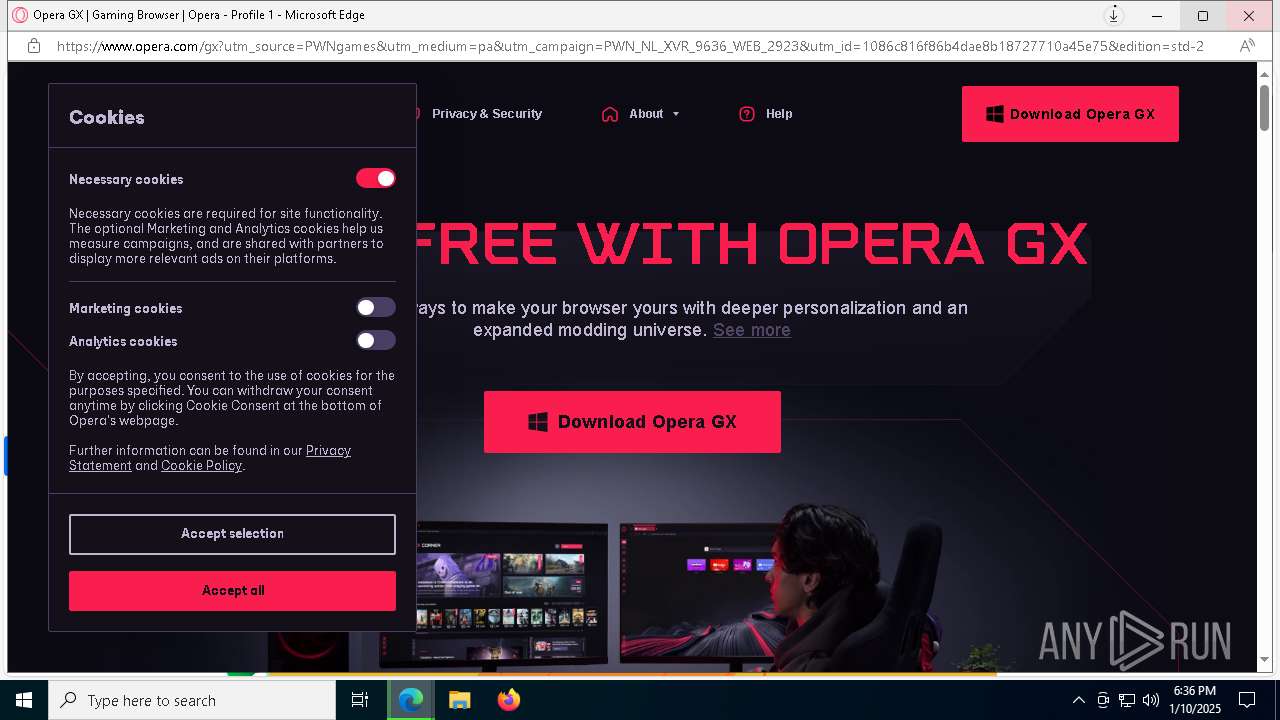
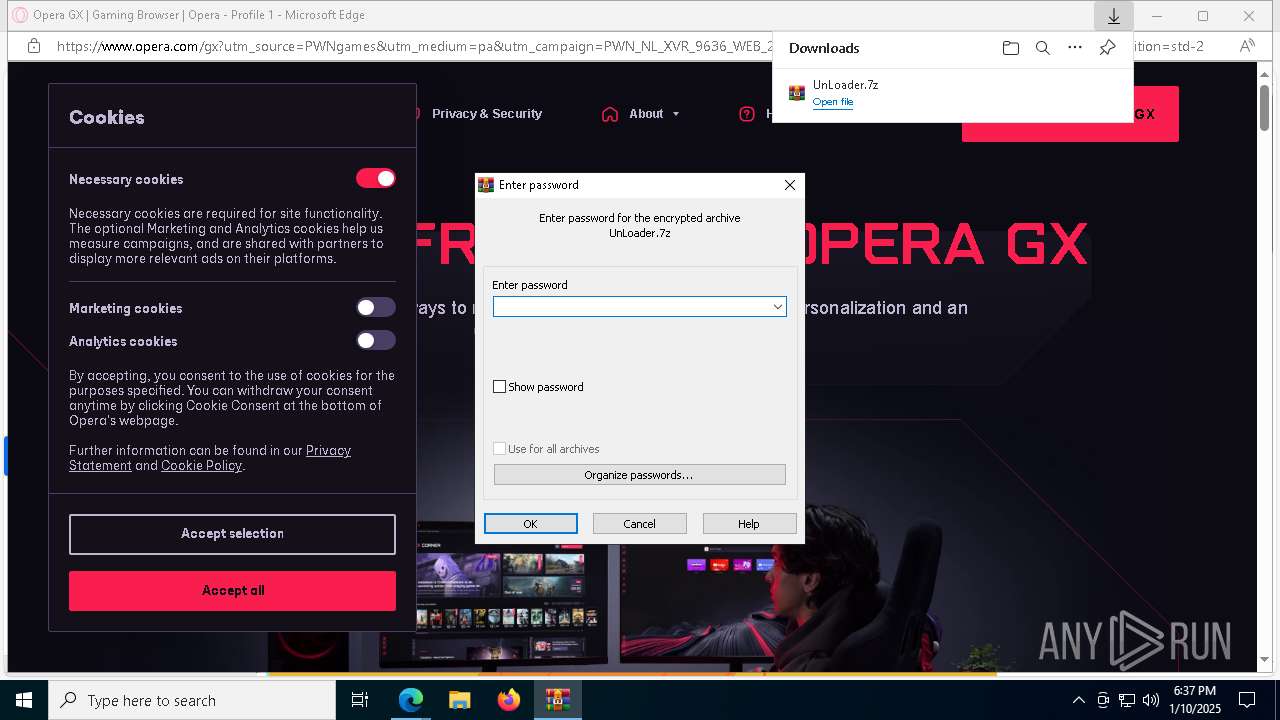
| URL: | https://loaderware.cc/unloader |
| Full analysis: | https://app.any.run/tasks/7f07aee7-d5c9-49e9-8faf-d003dc6958cb |
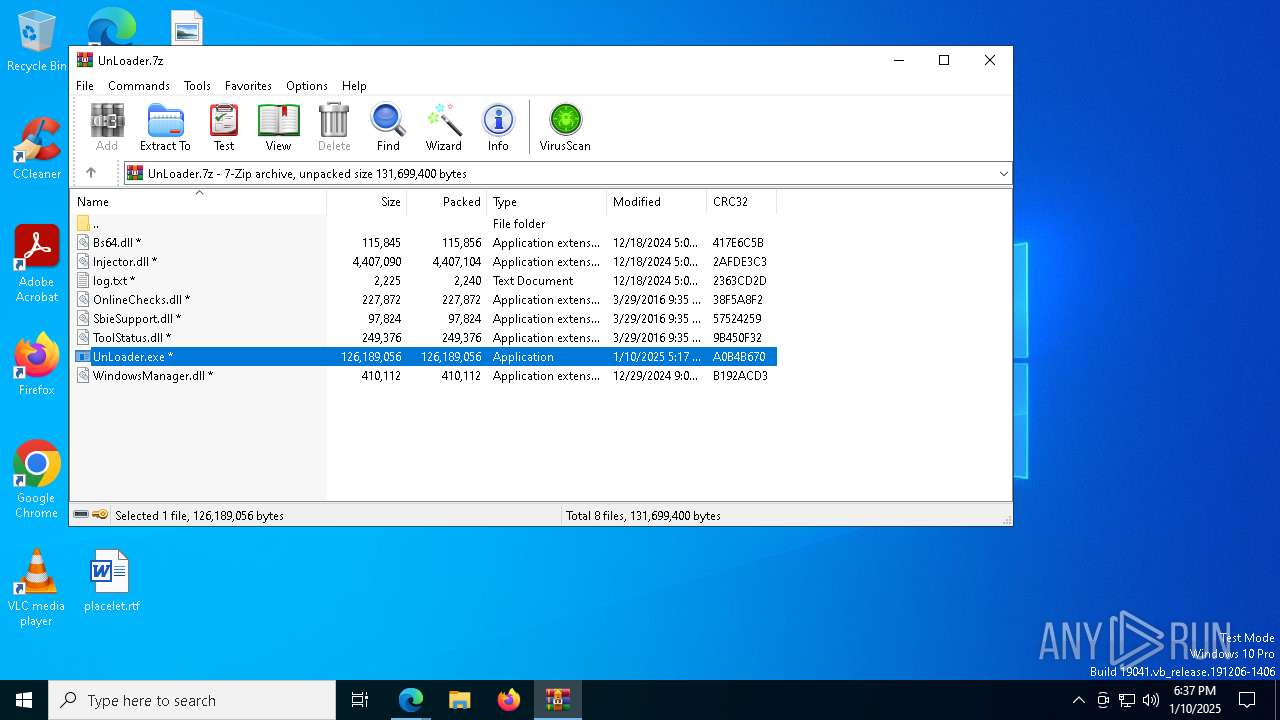
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | January 10, 2025, 18:35:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FCCE35A627E4993A26C32F922BDD6818 |
| SHA1: | 0DD4483E45F4383E32D07D967263A062B0A22A89 |
| SHA256: | 6CE8AAD34E8FAF1F7DABDA40C454B844823A7D92C77830D377539F4A9D54C04F |
| SSDEEP: | 3:N8KdCNKWpyn:2KdH |
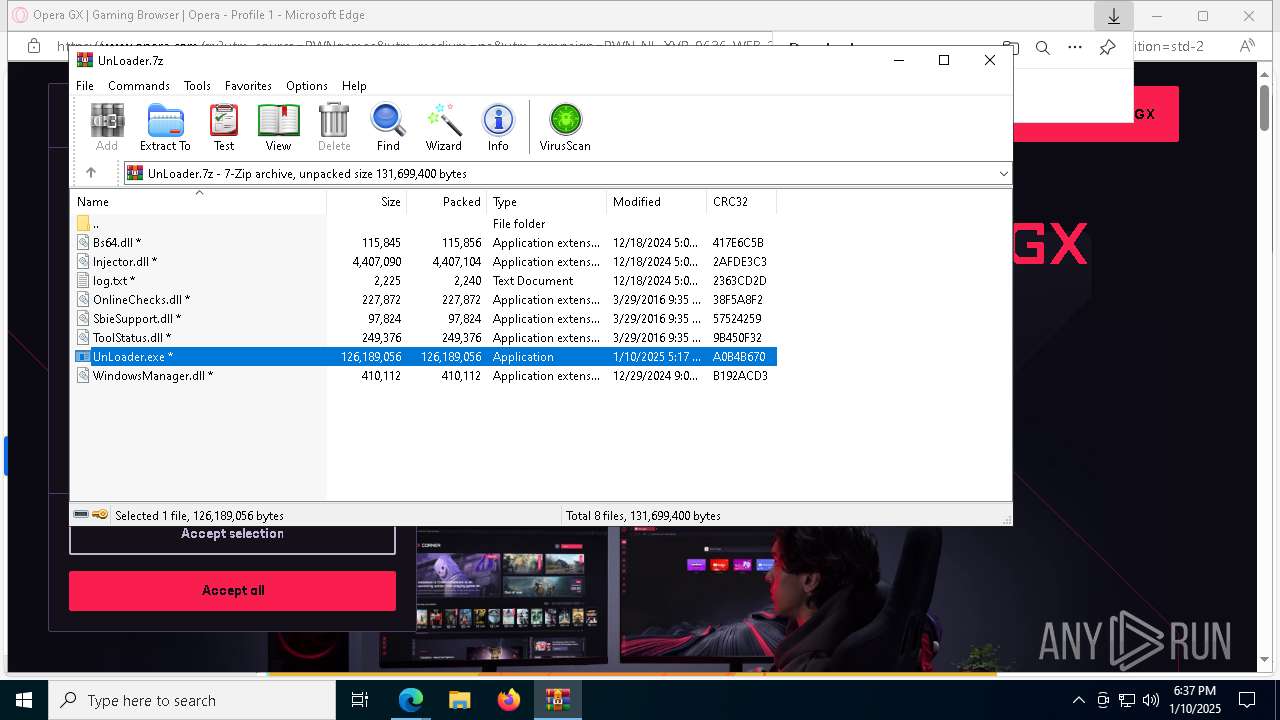
MALICIOUS
Actions looks like stealing of personal data
- UnLoader.exe (PID: 2120)
- UnLoader.exe (PID: 6068)
- UnLoader.exe (PID: 6096)
- UnLoader.exe (PID: 2428)
LUMMA has been detected (YARA)
- UnLoader.exe (PID: 2120)
LUMMA mutex has been found
- UnLoader.exe (PID: 6068)
- UnLoader.exe (PID: 6096)
- UnLoader.exe (PID: 7872)
- UnLoader.exe (PID: 7508)
- UnLoader.exe (PID: 7296)
- UnLoader.exe (PID: 2428)
- UnLoader.exe (PID: 4944)
- UnLoader.exe (PID: 7464)
- UnLoader.exe (PID: 2120)
- UnLoader.exe (PID: 7144)
- UnLoader.exe (PID: 7208)
- UnLoader.exe (PID: 8452)
- UnLoader.exe (PID: 8164)
- UnLoader.exe (PID: 7276)
- UnLoader.exe (PID: 1228)
- UnLoader.exe (PID: 8628)
- UnLoader.exe (PID: 8400)
- UnLoader.exe (PID: 9536)
- UnLoader.exe (PID: 9524)
- UnLoader.exe (PID: 9448)
- UnLoader.exe (PID: 4520)
Steals credentials from Web Browsers
- UnLoader.exe (PID: 6068)
- UnLoader.exe (PID: 2428)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5968)
Starts a Microsoft application from unusual location
- UnLoader.exe (PID: 7568)
- UnLoader.exe (PID: 2120)
- UnLoader.exe (PID: 3092)
- UnLoader.exe (PID: 6068)
- UnLoader.exe (PID: 6096)
- UnLoader.exe (PID: 7872)
- UnLoader.exe (PID: 1616)
- UnLoader.exe (PID: 4672)
- UnLoader.exe (PID: 7908)
- UnLoader.exe (PID: 3220)
- UnLoader.exe (PID: 3060)
- UnLoader.exe (PID: 7508)
- UnLoader.exe (PID: 7296)
- UnLoader.exe (PID: 4392)
- UnLoader.exe (PID: 3864)
- UnLoader.exe (PID: 2428)
- UnLoader.exe (PID: 6312)
- UnLoader.exe (PID: 7492)
- UnLoader.exe (PID: 4944)
- UnLoader.exe (PID: 7464)
- UnLoader.exe (PID: 7896)
- UnLoader.exe (PID: 6396)
- UnLoader.exe (PID: 1616)
- UnLoader.exe (PID: 4980)
- UnLoader.exe (PID: 7144)
- UnLoader.exe (PID: 7812)
- UnLoader.exe (PID: 7848)
- UnLoader.exe (PID: 4580)
- UnLoader.exe (PID: 3888)
- UnLoader.exe (PID: 4360)
- UnLoader.exe (PID: 2076)
- UnLoader.exe (PID: 3920)
- UnLoader.exe (PID: 6196)
- UnLoader.exe (PID: 4512)
- UnLoader.exe (PID: 7880)
- UnLoader.exe (PID: 1228)
- UnLoader.exe (PID: 8168)
- UnLoader.exe (PID: 640)
- UnLoader.exe (PID: 1172)
- UnLoader.exe (PID: 6440)
- UnLoader.exe (PID: 736)
- UnLoader.exe (PID: 7276)
- UnLoader.exe (PID: 7208)
- UnLoader.exe (PID: 8164)
- UnLoader.exe (PID: 4804)
- UnLoader.exe (PID: 6304)
- UnLoader.exe (PID: 6084)
- UnLoader.exe (PID: 8292)
- UnLoader.exe (PID: 8580)
- UnLoader.exe (PID: 8628)
- UnLoader.exe (PID: 8920)
- UnLoader.exe (PID: 8972)
- UnLoader.exe (PID: 8984)
- UnLoader.exe (PID: 9088)
- UnLoader.exe (PID: 8204)
- UnLoader.exe (PID: 8452)
- UnLoader.exe (PID: 9168)
- UnLoader.exe (PID: 9124)
- UnLoader.exe (PID: 9196)
- UnLoader.exe (PID: 8256)
- UnLoader.exe (PID: 8176)
- UnLoader.exe (PID: 9112)
- UnLoader.exe (PID: 6876)
- UnLoader.exe (PID: 9036)
- UnLoader.exe (PID: 8372)
- UnLoader.exe (PID: 8348)
- UnLoader.exe (PID: 8904)
- UnLoader.exe (PID: 8584)
- UnLoader.exe (PID: 7136)
- UnLoader.exe (PID: 8300)
- UnLoader.exe (PID: 3488)
- UnLoader.exe (PID: 8736)
- UnLoader.exe (PID: 6332)
- UnLoader.exe (PID: 8688)
- UnLoader.exe (PID: 7964)
- UnLoader.exe (PID: 7488)
- UnLoader.exe (PID: 4804)
- UnLoader.exe (PID: 8400)
- UnLoader.exe (PID: 8912)
- UnLoader.exe (PID: 8448)
- UnLoader.exe (PID: 1296)
- UnLoader.exe (PID: 8800)
- UnLoader.exe (PID: 7472)
- UnLoader.exe (PID: 7596)
- UnLoader.exe (PID: 8556)
- UnLoader.exe (PID: 5788)
- UnLoader.exe (PID: 7896)
- UnLoader.exe (PID: 8952)
- UnLoader.exe (PID: 6364)
- UnLoader.exe (PID: 8424)
- UnLoader.exe (PID: 7908)
- UnLoader.exe (PID: 8532)
- UnLoader.exe (PID: 7092)
- UnLoader.exe (PID: 732)
- UnLoader.exe (PID: 8796)
- UnLoader.exe (PID: 8392)
- UnLoader.exe (PID: 8908)
- UnLoader.exe (PID: 9108)
- UnLoader.exe (PID: 9232)
- UnLoader.exe (PID: 4052)
- UnLoader.exe (PID: 5720)
- UnLoader.exe (PID: 10024)
- UnLoader.exe (PID: 9956)
- UnLoader.exe (PID: 10156)
- UnLoader.exe (PID: 9264)
- UnLoader.exe (PID: 9428)
- UnLoader.exe (PID: 9604)
- UnLoader.exe (PID: 8928)
- UnLoader.exe (PID: 9832)
- UnLoader.exe (PID: 9904)
- UnLoader.exe (PID: 9940)
- UnLoader.exe (PID: 9812)
- UnLoader.exe (PID: 10200)
- UnLoader.exe (PID: 9524)
- UnLoader.exe (PID: 9236)
- UnLoader.exe (PID: 10212)
- UnLoader.exe (PID: 1520)
- UnLoader.exe (PID: 9040)
- UnLoader.exe (PID: 9388)
- UnLoader.exe (PID: 2092)
- UnLoader.exe (PID: 9952)
- UnLoader.exe (PID: 9896)
- UnLoader.exe (PID: 10120)
- UnLoader.exe (PID: 10100)
- UnLoader.exe (PID: 10044)
- UnLoader.exe (PID: 9656)
- UnLoader.exe (PID: 4520)
- UnLoader.exe (PID: 9448)
- UnLoader.exe (PID: 9768)
- UnLoader.exe (PID: 8412)
- UnLoader.exe (PID: 9380)
- UnLoader.exe (PID: 7228)
- UnLoader.exe (PID: 10228)
- UnLoader.exe (PID: 8396)
- UnLoader.exe (PID: 7088)
- UnLoader.exe (PID: 9176)
- UnLoader.exe (PID: 1684)
- UnLoader.exe (PID: 9912)
- UnLoader.exe (PID: 7096)
- UnLoader.exe (PID: 6940)
- UnLoader.exe (PID: 2012)
- UnLoader.exe (PID: 7092)
- UnLoader.exe (PID: 4980)
- UnLoader.exe (PID: 10136)
- UnLoader.exe (PID: 9888)
- UnLoader.exe (PID: 10096)
- UnLoader.exe (PID: 9744)
- UnLoader.exe (PID: 8548)
- UnLoader.exe (PID: 9552)
- UnLoader.exe (PID: 9536)
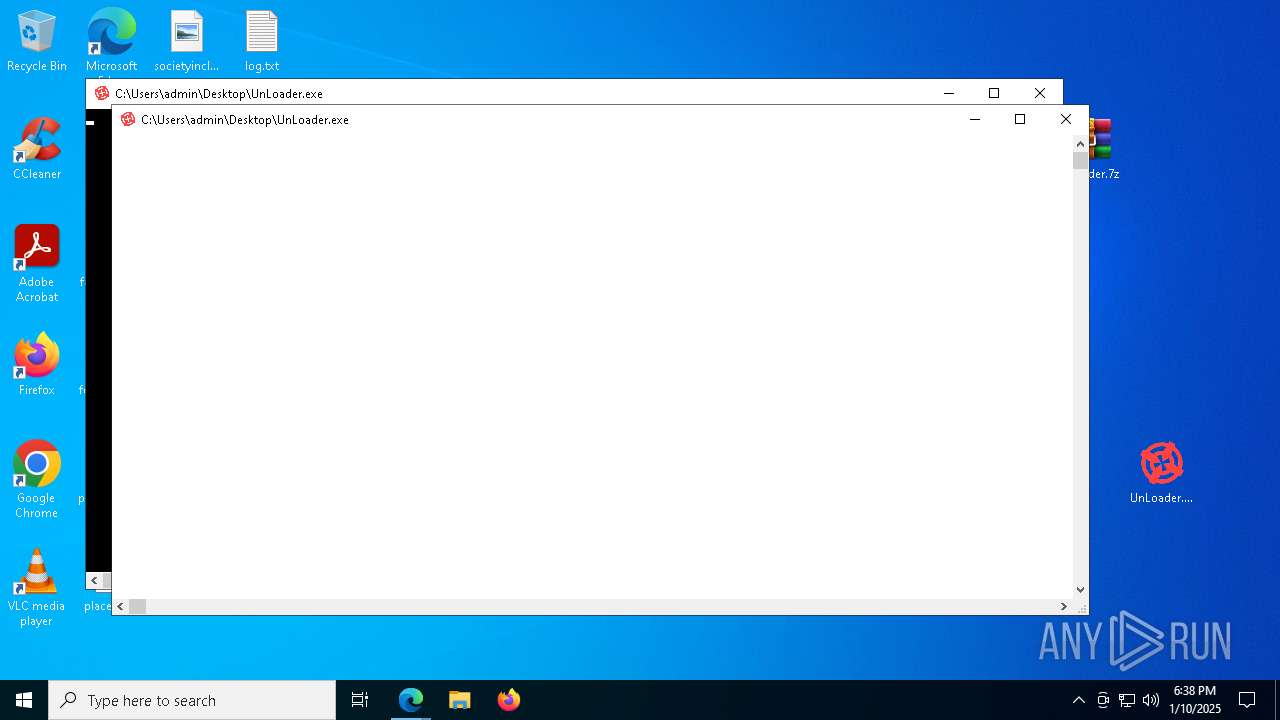
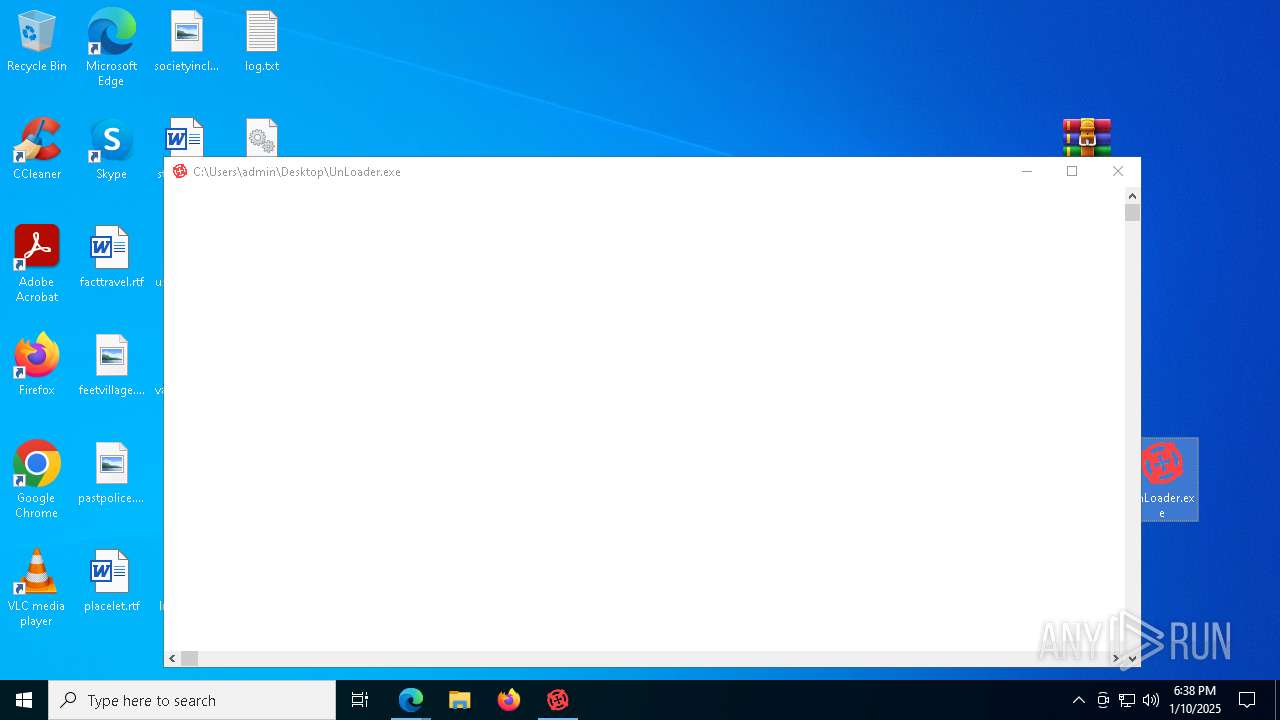
Application launched itself
- UnLoader.exe (PID: 7568)
- UnLoader.exe (PID: 3092)
- UnLoader.exe (PID: 4672)
- UnLoader.exe (PID: 1616)
- UnLoader.exe (PID: 7908)
- UnLoader.exe (PID: 3060)
- UnLoader.exe (PID: 4392)
- UnLoader.exe (PID: 6312)
- UnLoader.exe (PID: 7896)
- UnLoader.exe (PID: 4580)
- UnLoader.exe (PID: 7492)
- UnLoader.exe (PID: 4980)
- UnLoader.exe (PID: 6396)
- UnLoader.exe (PID: 8168)
- UnLoader.exe (PID: 4360)
- UnLoader.exe (PID: 3920)
- UnLoader.exe (PID: 2076)
- UnLoader.exe (PID: 6084)
- UnLoader.exe (PID: 736)
- UnLoader.exe (PID: 8204)
- UnLoader.exe (PID: 4804)
- UnLoader.exe (PID: 6304)
- UnLoader.exe (PID: 8292)
- UnLoader.exe (PID: 640)
- UnLoader.exe (PID: 8580)
- UnLoader.exe (PID: 1172)
- UnLoader.exe (PID: 9124)
- UnLoader.exe (PID: 8176)
- UnLoader.exe (PID: 7472)
- UnLoader.exe (PID: 8348)
- UnLoader.exe (PID: 8372)
- UnLoader.exe (PID: 7964)
- UnLoader.exe (PID: 9112)
- UnLoader.exe (PID: 8904)
- UnLoader.exe (PID: 8556)
- UnLoader.exe (PID: 732)
- UnLoader.exe (PID: 7908)
- UnLoader.exe (PID: 8532)
- UnLoader.exe (PID: 8424)
- UnLoader.exe (PID: 7092)
- UnLoader.exe (PID: 8796)
- UnLoader.exe (PID: 8392)
- UnLoader.exe (PID: 6364)
- UnLoader.exe (PID: 8928)
- UnLoader.exe (PID: 1520)
- UnLoader.exe (PID: 10024)
- UnLoader.exe (PID: 5720)
- UnLoader.exe (PID: 4052)
- UnLoader.exe (PID: 10156)
- UnLoader.exe (PID: 9812)
- UnLoader.exe (PID: 9380)
- UnLoader.exe (PID: 7228)
- UnLoader.exe (PID: 9656)
- UnLoader.exe (PID: 9896)
- UnLoader.exe (PID: 10044)
- UnLoader.exe (PID: 1684)
- UnLoader.exe (PID: 9744)
- UnLoader.exe (PID: 2012)
Executes application which crashes
- UnLoader.exe (PID: 7568)
- UnLoader.exe (PID: 3092)
- UnLoader.exe (PID: 4672)
- UnLoader.exe (PID: 7908)
- UnLoader.exe (PID: 1616)
- UnLoader.exe (PID: 3060)
- UnLoader.exe (PID: 4392)
- UnLoader.exe (PID: 6312)
- UnLoader.exe (PID: 4580)
- UnLoader.exe (PID: 7492)
- UnLoader.exe (PID: 7896)
- UnLoader.exe (PID: 4980)
- UnLoader.exe (PID: 9124)
- UnLoader.exe (PID: 7472)
- UnLoader.exe (PID: 8348)
- UnLoader.exe (PID: 5720)
INFO
Reads the computer name
- identity_helper.exe (PID: 5640)
- UnLoader.exe (PID: 7568)
- UnLoader.exe (PID: 6096)
- UnLoader.exe (PID: 4672)
- UnLoader.exe (PID: 7908)
- UnLoader.exe (PID: 3060)
- UnLoader.exe (PID: 6312)
- UnLoader.exe (PID: 2120)
Checks supported languages
- identity_helper.exe (PID: 5640)
- UnLoader.exe (PID: 7568)
- UnLoader.exe (PID: 2120)
- UnLoader.exe (PID: 3092)
- UnLoader.exe (PID: 6068)
- UnLoader.exe (PID: 6096)
- UnLoader.exe (PID: 7872)
- UnLoader.exe (PID: 7296)
- UnLoader.exe (PID: 6312)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6212)
Reads Environment values
- identity_helper.exe (PID: 5640)
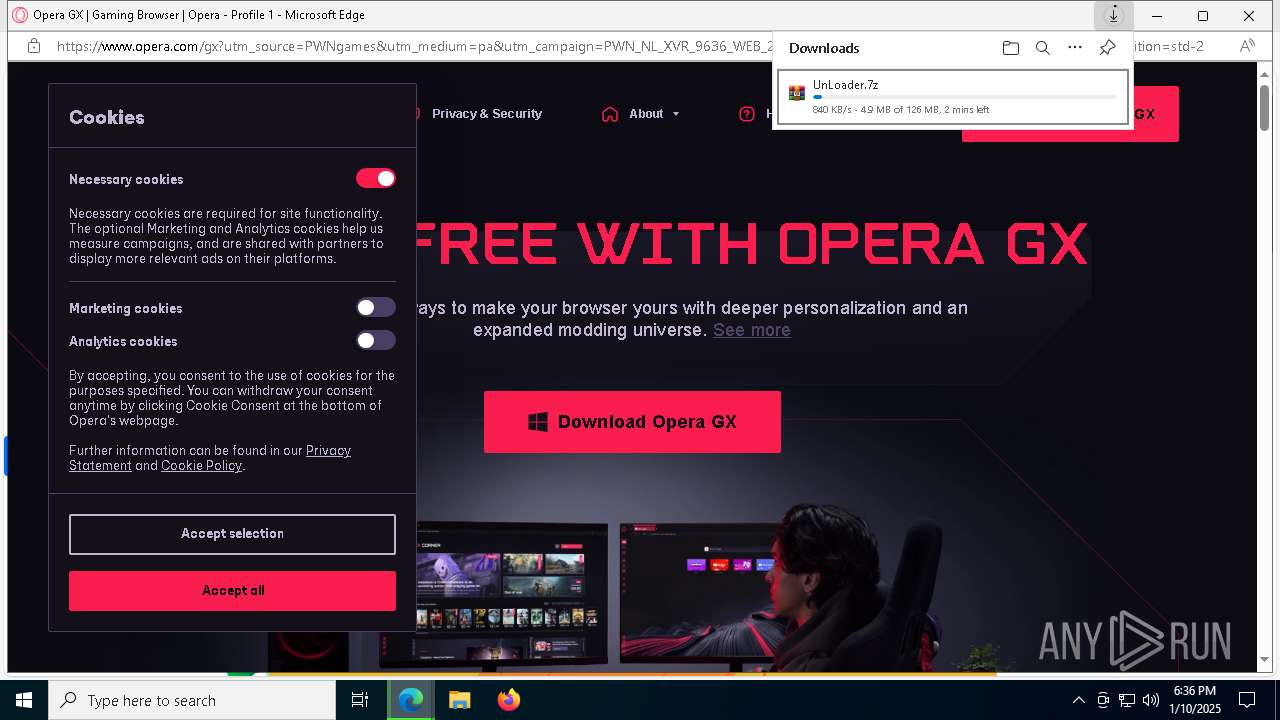
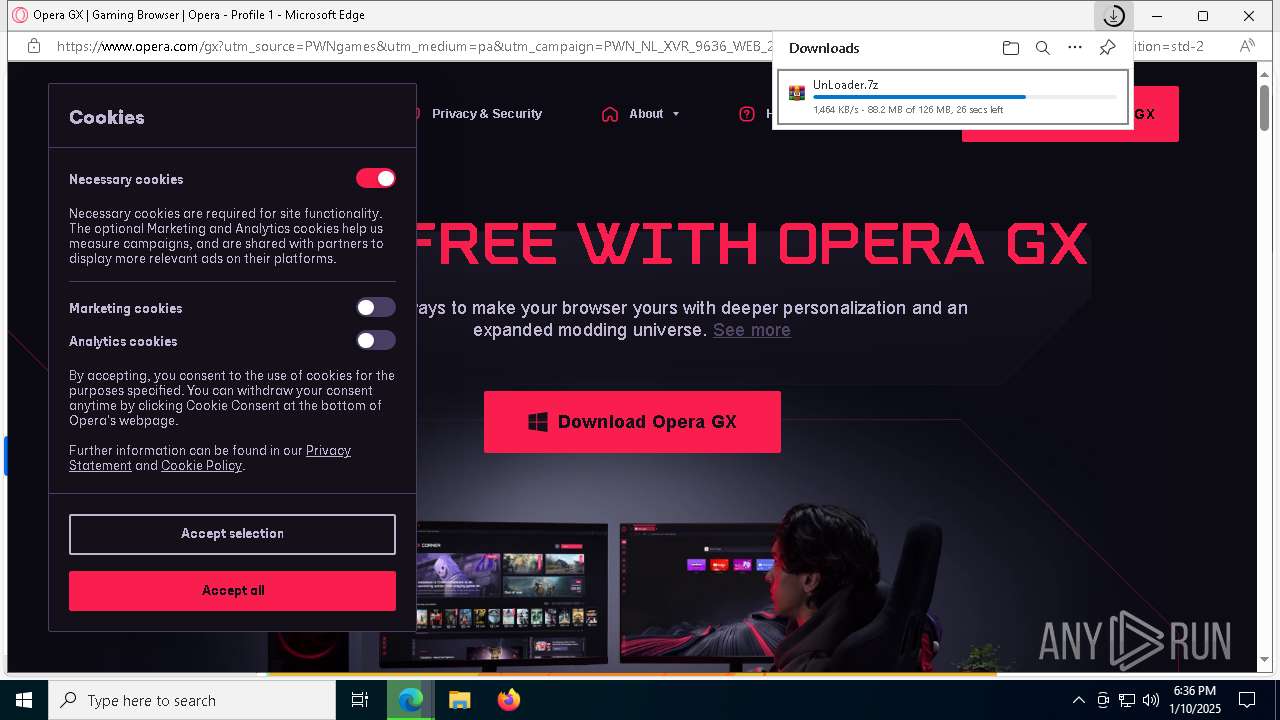
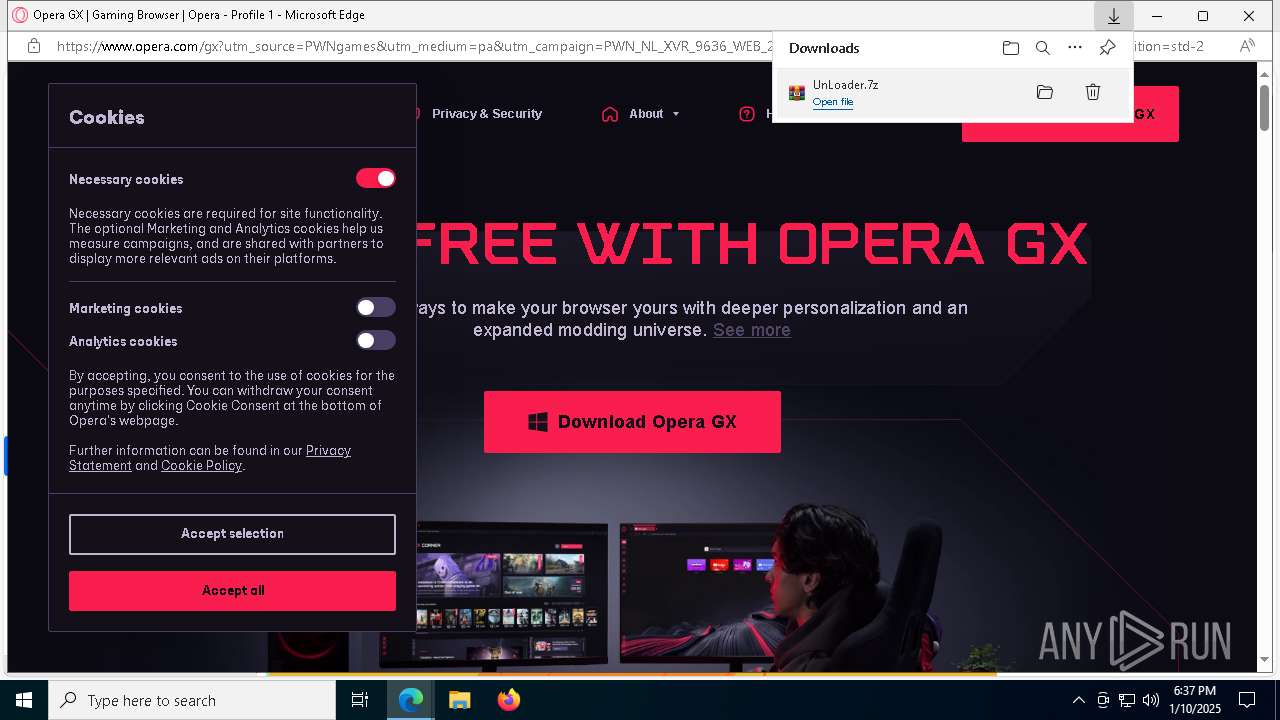
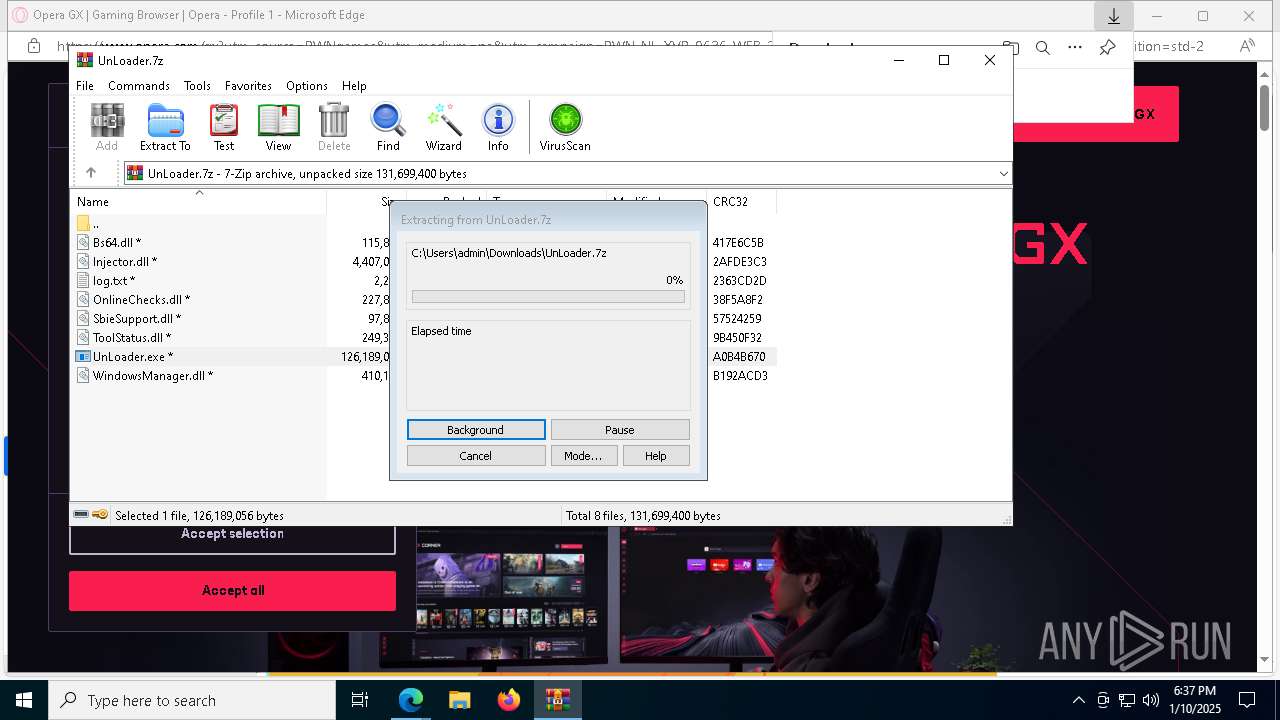
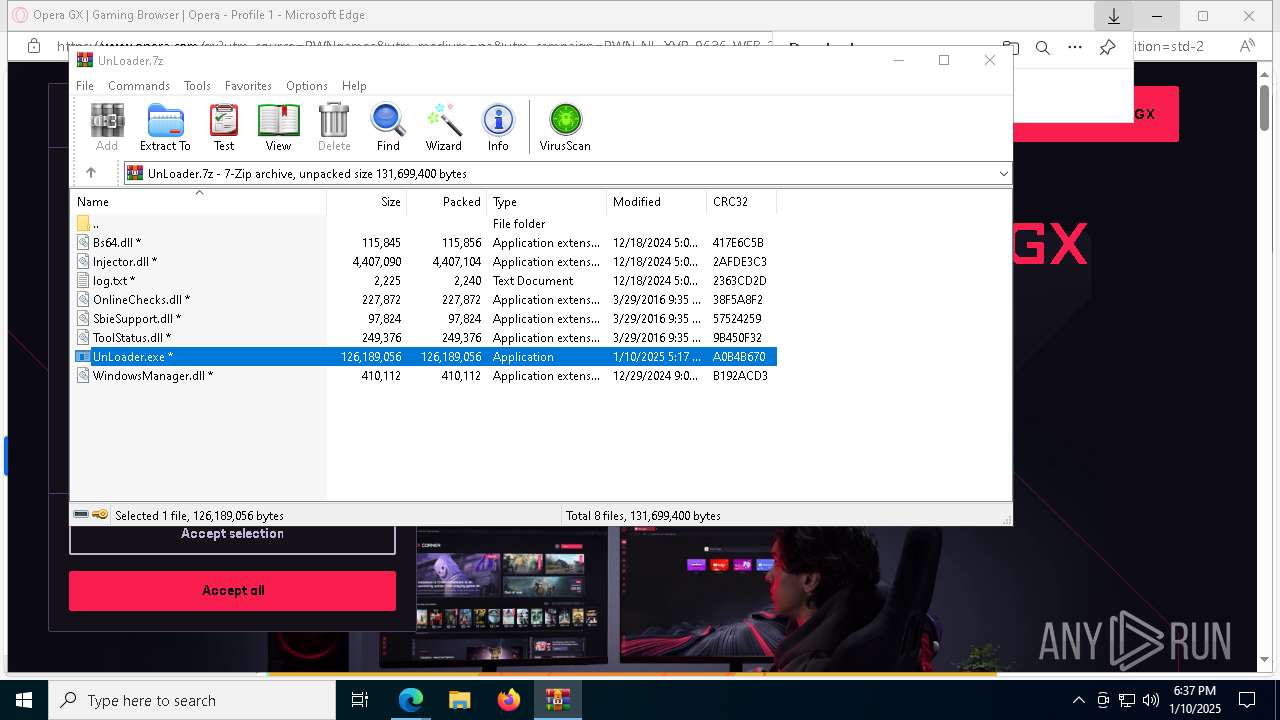
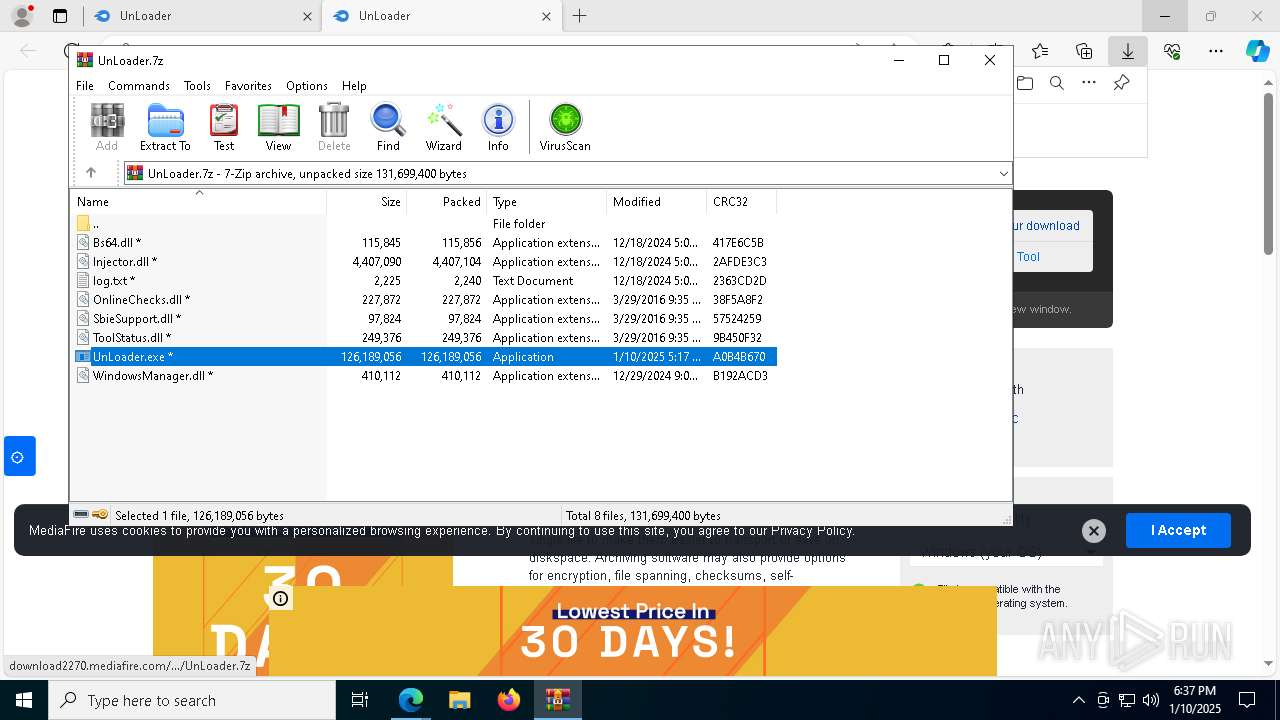
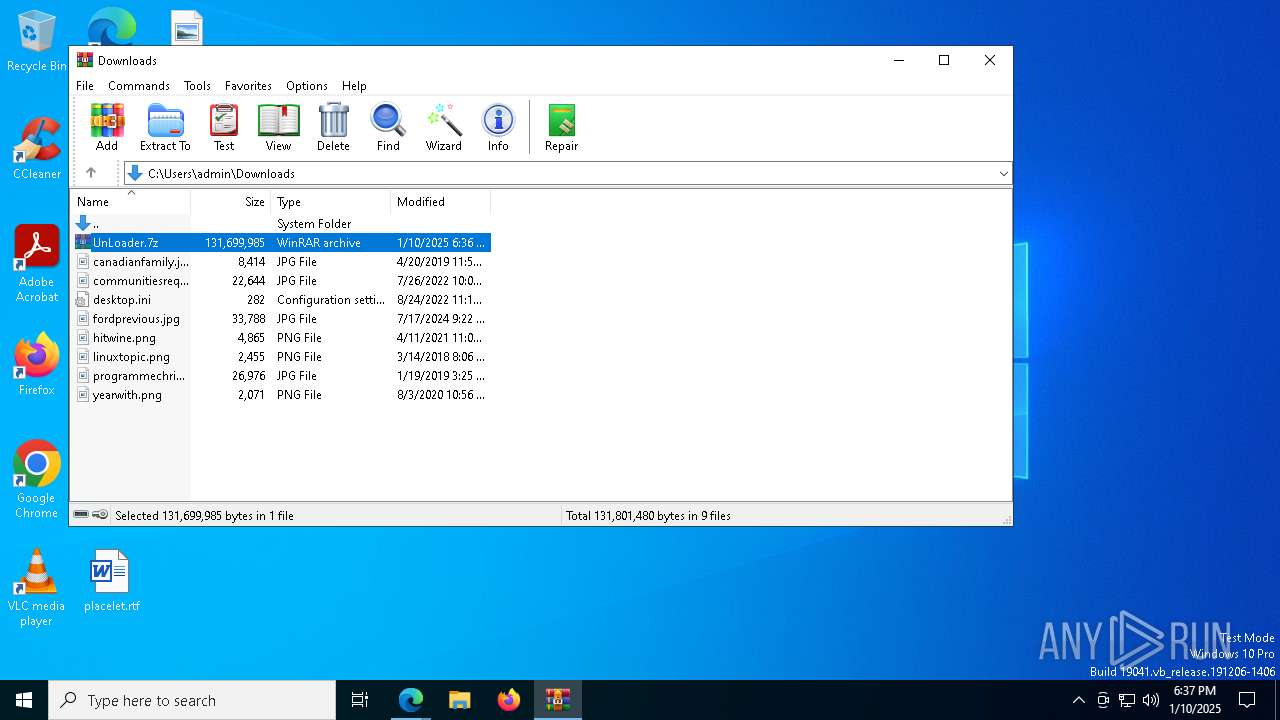
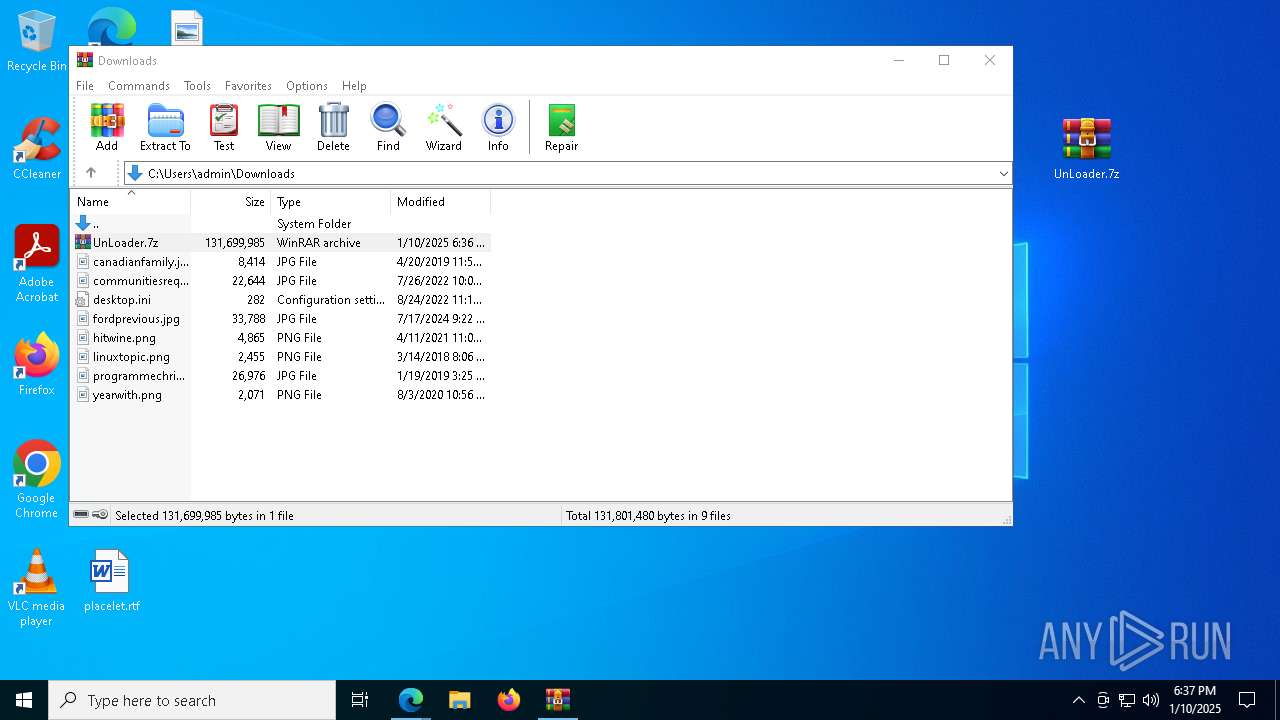
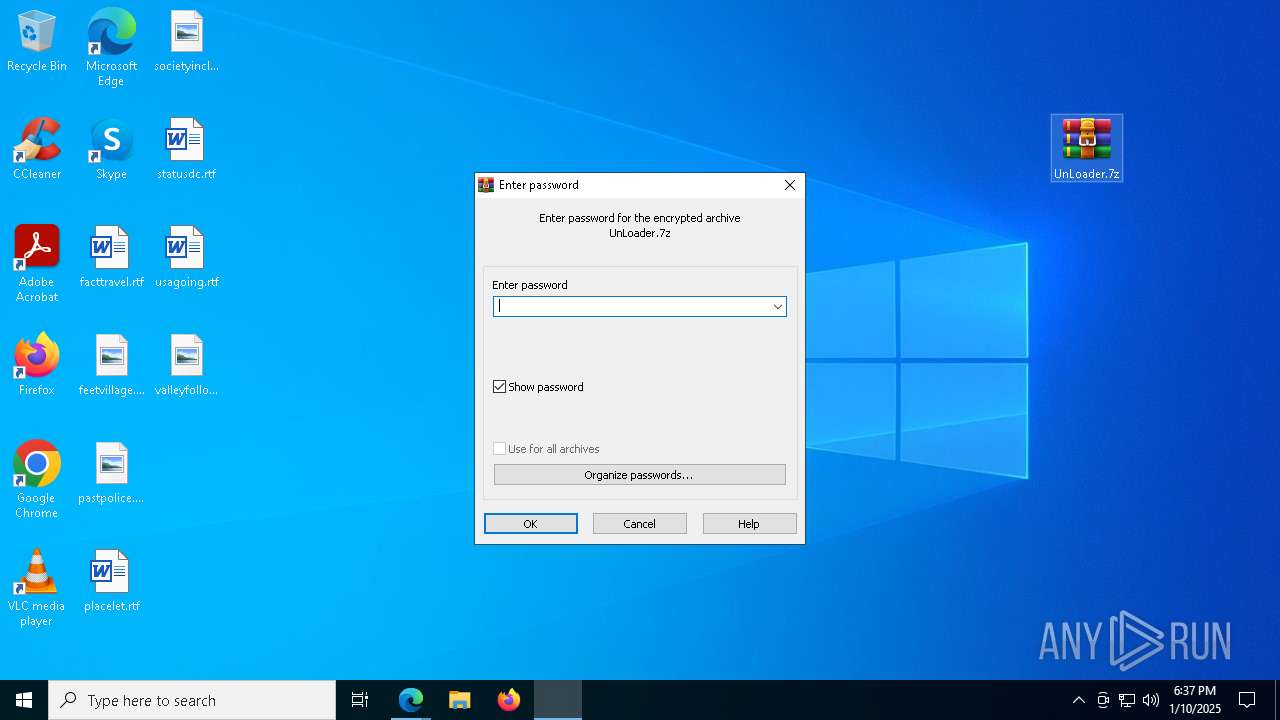
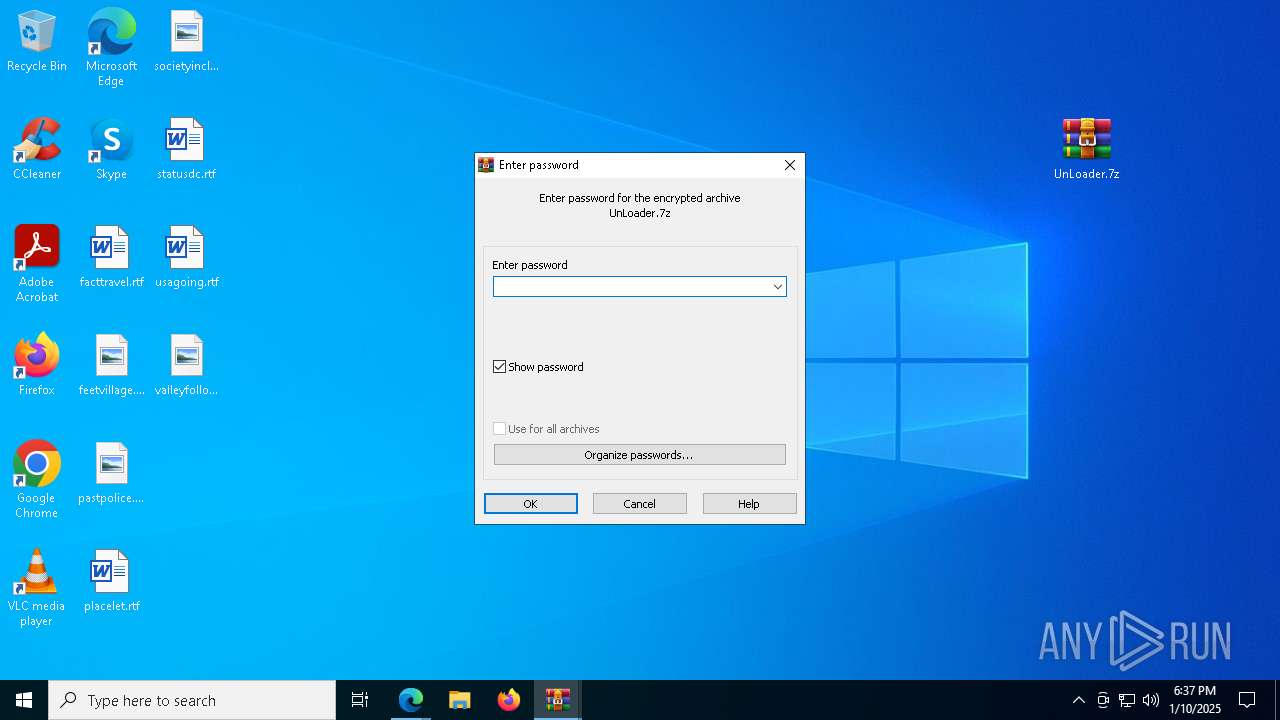
The process uses the downloaded file
- msedge.exe (PID: 3808)
- WinRAR.exe (PID: 5968)
- WinRAR.exe (PID: 5464)
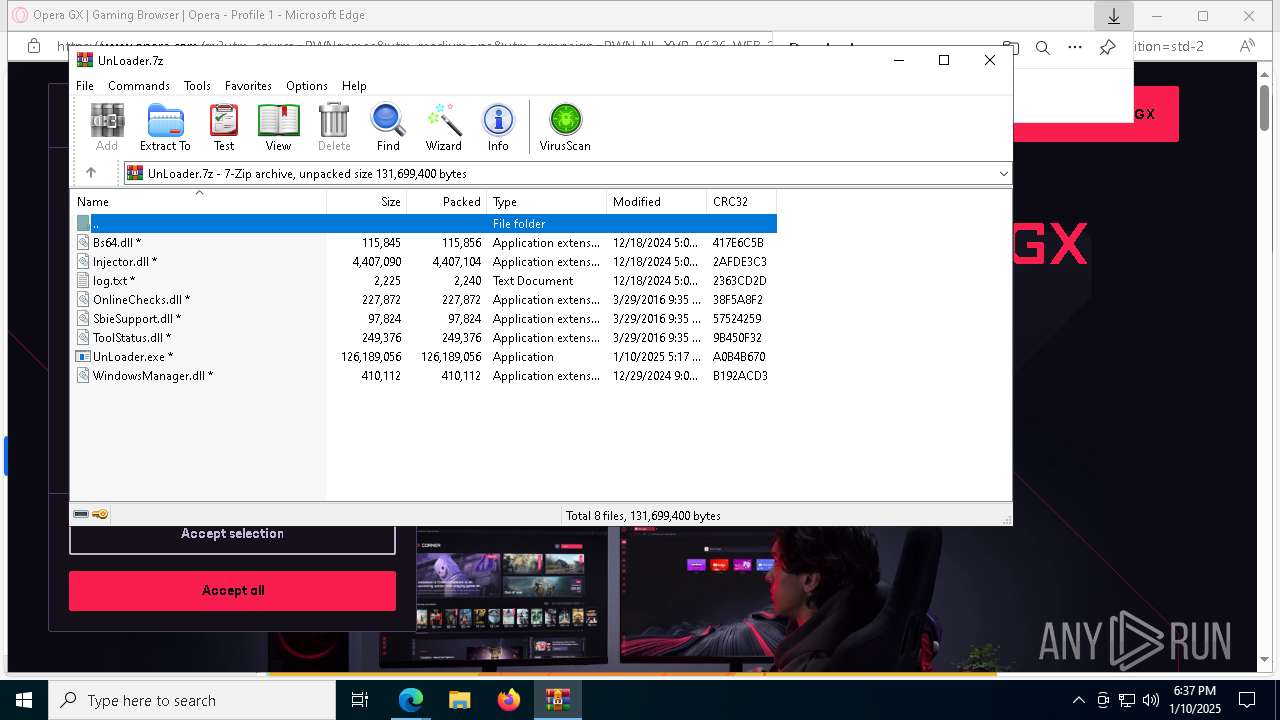
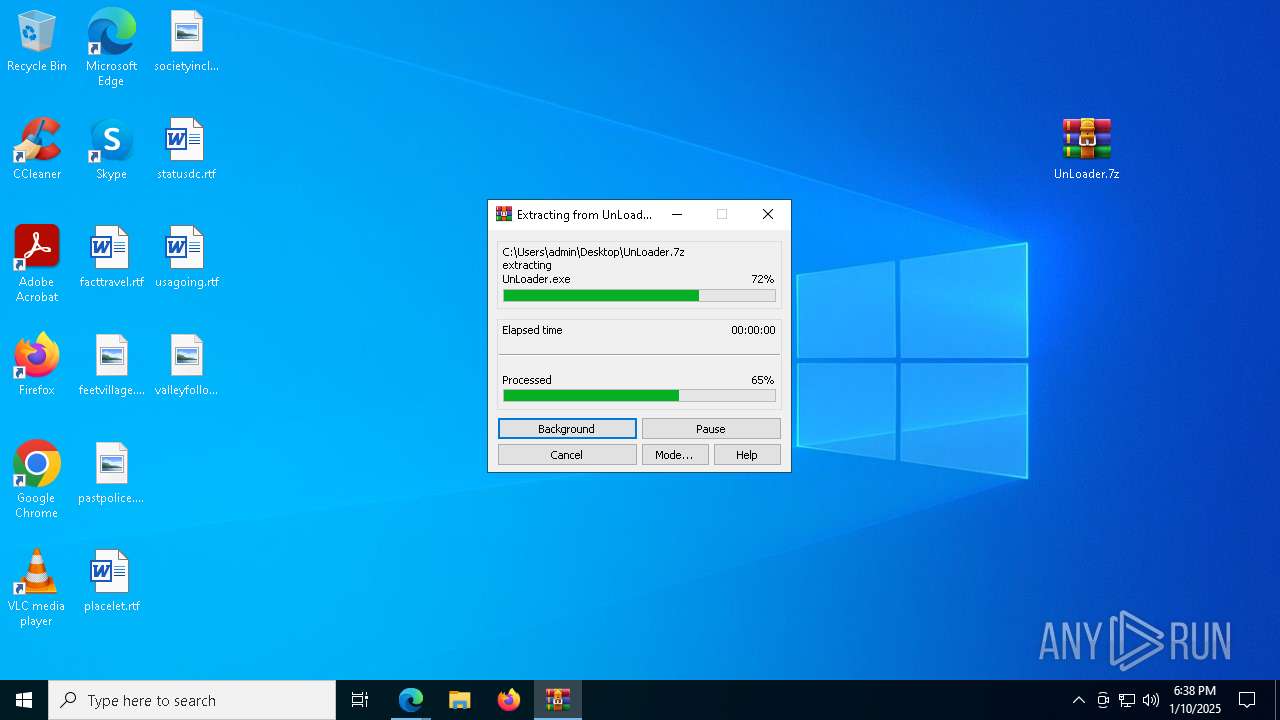
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5968)
- WinRAR.exe (PID: 5464)
The sample compiled with english language support
- WinRAR.exe (PID: 5968)
- WinRAR.exe (PID: 5464)
Application launched itself
- msedge.exe (PID: 6212)
Reads the software policy settings
- UnLoader.exe (PID: 2120)
- WerFault.exe (PID: 5856)
- UnLoader.exe (PID: 7872)
- UnLoader.exe (PID: 7508)
- UnLoader.exe (PID: 7848)
Checks proxy server information
- WerFault.exe (PID: 6084)
- WerFault.exe (PID: 8188)
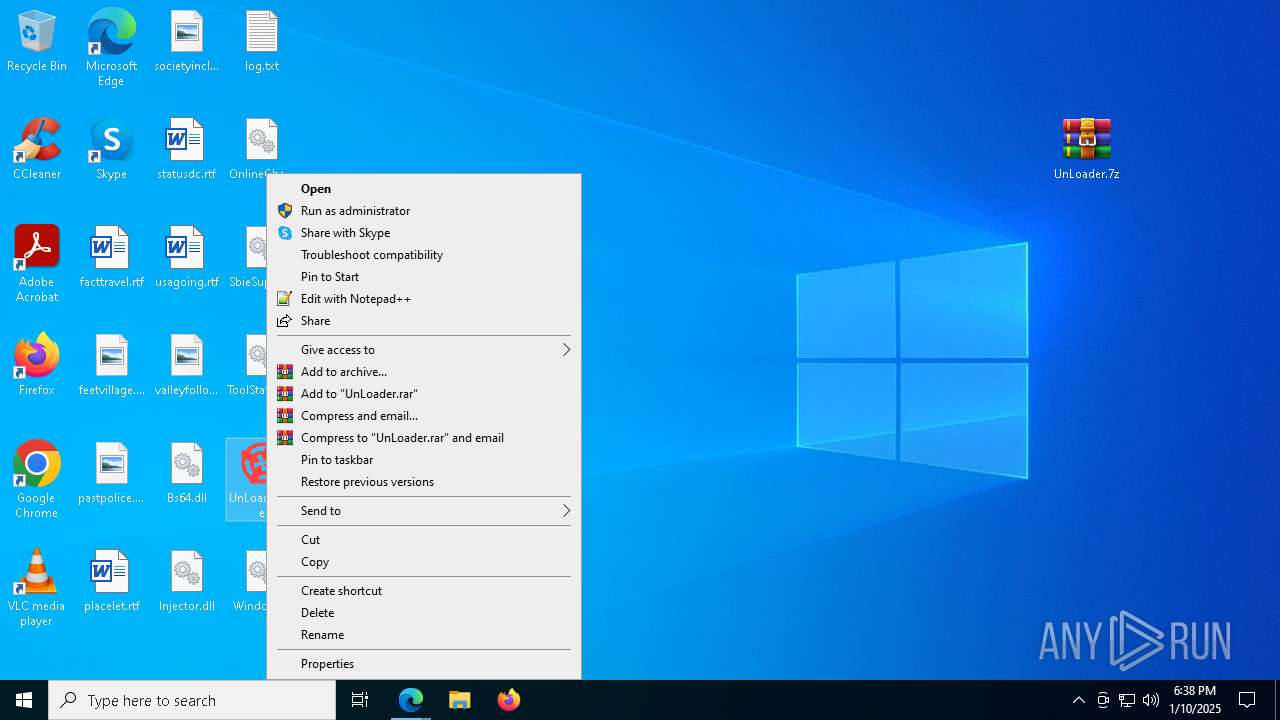
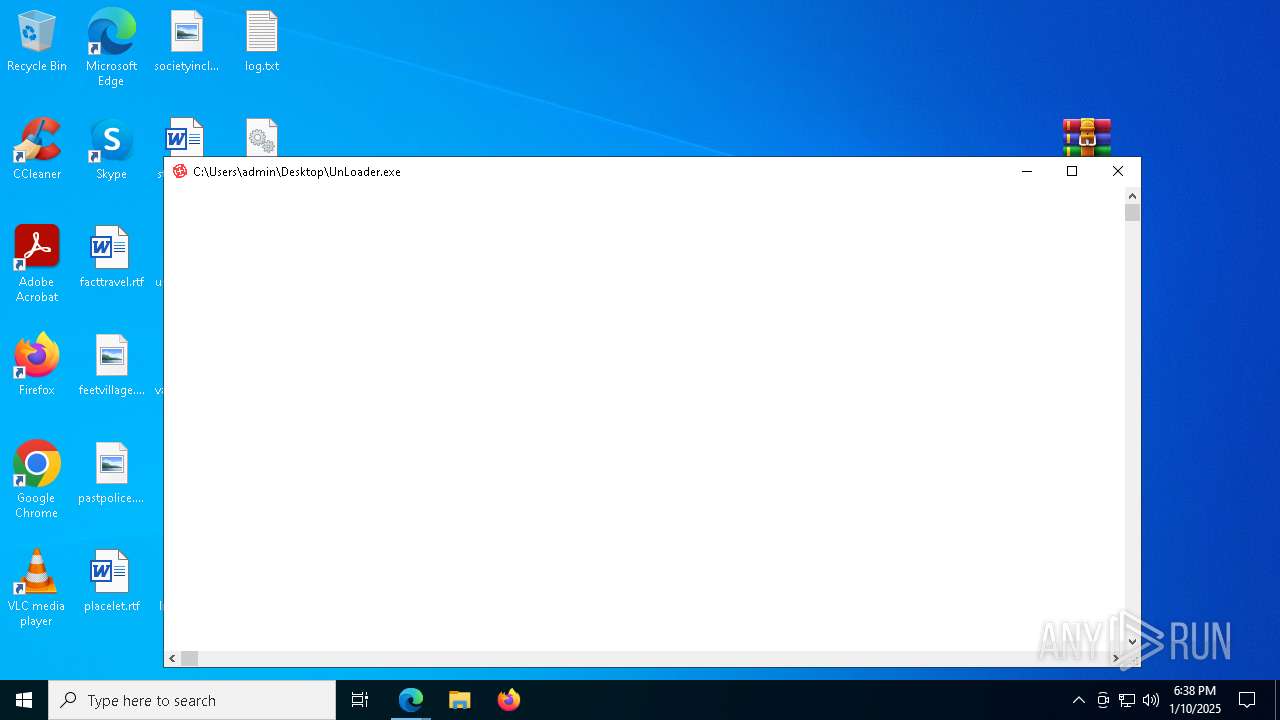
Manual execution by a user
- WinRAR.exe (PID: 5464)
- WinRAR.exe (PID: 7132)
- UnLoader.exe (PID: 3092)
- UnLoader.exe (PID: 4672)
- UnLoader.exe (PID: 1616)
- UnLoader.exe (PID: 7908)
- UnLoader.exe (PID: 3060)
- UnLoader.exe (PID: 4392)
- UnLoader.exe (PID: 6312)
- UnLoader.exe (PID: 7896)
- UnLoader.exe (PID: 4580)
- UnLoader.exe (PID: 7492)
- UnLoader.exe (PID: 8168)
- UnLoader.exe (PID: 2076)
- UnLoader.exe (PID: 3920)
- UnLoader.exe (PID: 4360)
- UnLoader.exe (PID: 6396)
- UnLoader.exe (PID: 4980)
- UnLoader.exe (PID: 640)
- UnLoader.exe (PID: 736)
- UnLoader.exe (PID: 1172)
- UnLoader.exe (PID: 4804)
- UnLoader.exe (PID: 6084)
- UnLoader.exe (PID: 8204)
- UnLoader.exe (PID: 8292)
- UnLoader.exe (PID: 8580)
- UnLoader.exe (PID: 9112)
- UnLoader.exe (PID: 6304)
- UnLoader.exe (PID: 9124)
- UnLoader.exe (PID: 8348)
- UnLoader.exe (PID: 7472)
- UnLoader.exe (PID: 8372)
- UnLoader.exe (PID: 8904)
- UnLoader.exe (PID: 8176)
- UnLoader.exe (PID: 7964)
- UnLoader.exe (PID: 732)
- UnLoader.exe (PID: 8556)
- UnLoader.exe (PID: 8532)
- UnLoader.exe (PID: 7092)
- UnLoader.exe (PID: 8424)
- UnLoader.exe (PID: 6364)
- UnLoader.exe (PID: 8928)
- UnLoader.exe (PID: 8392)
- UnLoader.exe (PID: 8796)
- UnLoader.exe (PID: 5720)
- UnLoader.exe (PID: 7908)
- UnLoader.exe (PID: 4052)
- UnLoader.exe (PID: 10024)
- UnLoader.exe (PID: 10156)
- UnLoader.exe (PID: 1520)
- UnLoader.exe (PID: 9812)
- UnLoader.exe (PID: 10044)
- UnLoader.exe (PID: 9896)
- UnLoader.exe (PID: 9656)
- UnLoader.exe (PID: 7228)
- UnLoader.exe (PID: 9380)
- UnLoader.exe (PID: 1684)
- UnLoader.exe (PID: 2012)
- UnLoader.exe (PID: 9744)
.NET Reactor protector has been detected
- UnLoader.exe (PID: 2120)
Creates files or folders in the user directory
- WerFault.exe (PID: 1228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
478
Monitored processes
288
Malicious processes
35
Suspicious processes
20
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5888 --field-trial-handle=2372,i,1874406669734519751,15790030622977255174,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7776 --field-trial-handle=2372,i,1874406669734519751,15790030622977255174,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4808 --field-trial-handle=2372,i,1874406669734519751,15790030622977255174,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 640 | "C:\Users\admin\Desktop\UnLoader.exe" | C:\Users\admin\Desktop\UnLoader.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Access Dialer Exit code: 3221226505 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\Users\admin\Desktop\UnLoader.exe" | C:\Users\admin\Desktop\UnLoader.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Access Dialer Exit code: 3221226505 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5720 -s 820 | C:\Windows\SysWOW64\WerFault.exe | UnLoader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Users\admin\Desktop\UnLoader.exe" | C:\Users\admin\Desktop\UnLoader.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Access Dialer Exit code: 3221226505 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UnLoader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UnLoader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "C:\Users\admin\Desktop\UnLoader.exe" | C:\Users\admin\Desktop\UnLoader.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Access Dialer Exit code: 3221226505 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
84 856
Read events
84 775
Write events
78
Delete events
3
Modification events
| (PID) Process: | (6212) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6212) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6212) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6212) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6212) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C54A5AA5F4892F00 | |||
| (PID) Process: | (6212) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0D7261A5F4892F00 | |||
| (PID) Process: | (6016) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6016) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6016) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6016) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
28
Suspicious files
506
Text files
119
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1355c4.TMP | — | |
MD5:— | SHA256:— | |||
| 6212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1355c4.TMP | — | |
MD5:— | SHA256:— | |||
| 6212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 6212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 6212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135612.TMP | — | |
MD5:— | SHA256:— | |||
| 6212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
352
DNS requests
233
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7232 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7232 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3736 | svchost.exe | HEAD | 200 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1736939528&P2=404&P3=2&P4=j7E7F8InWLyPPEZrzL8uXQVkvO8ngrNId2F%2bwGf0fZMSe9jknOCFbia8k3evJlETpKLmd9ythkQ%2b3nC09nQ5MQ%3d%3d | unknown | — | — | whitelisted |
3736 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1736939528&P2=404&P3=2&P4=j7E7F8InWLyPPEZrzL8uXQVkvO8ngrNId2F%2bwGf0fZMSe9jknOCFbia8k3evJlETpKLmd9ythkQ%2b3nC09nQ5MQ%3d%3d | unknown | — | — | whitelisted |
3736 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1736939528&P2=404&P3=2&P4=j7E7F8InWLyPPEZrzL8uXQVkvO8ngrNId2F%2bwGf0fZMSe9jknOCFbia8k3evJlETpKLmd9ythkQ%2b3nC09nQ5MQ%3d%3d | unknown | — | — | whitelisted |
3736 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1736939528&P2=404&P3=2&P4=j7E7F8InWLyPPEZrzL8uXQVkvO8ngrNId2F%2bwGf0fZMSe9jknOCFbia8k3evJlETpKLmd9ythkQ%2b3nC09nQ5MQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3416 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
6612 | msedge.exe | 104.21.16.1:443 | loaderware.cc | — | — | unknown |
6612 | msedge.exe | 142.250.185.196:443 | www.google.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
loaderware.cc |
| unknown |
www.bing.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6612 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6612 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6612 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6612 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6612 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6612 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |