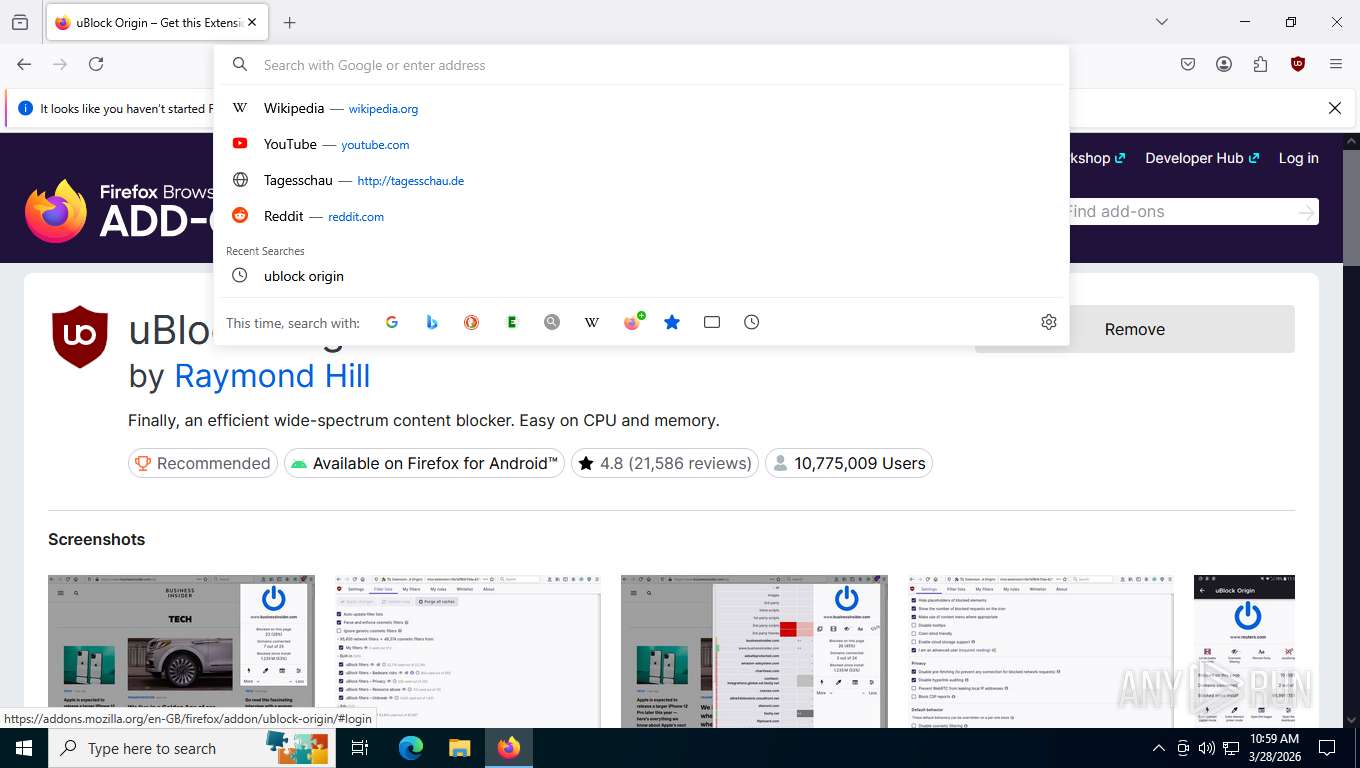
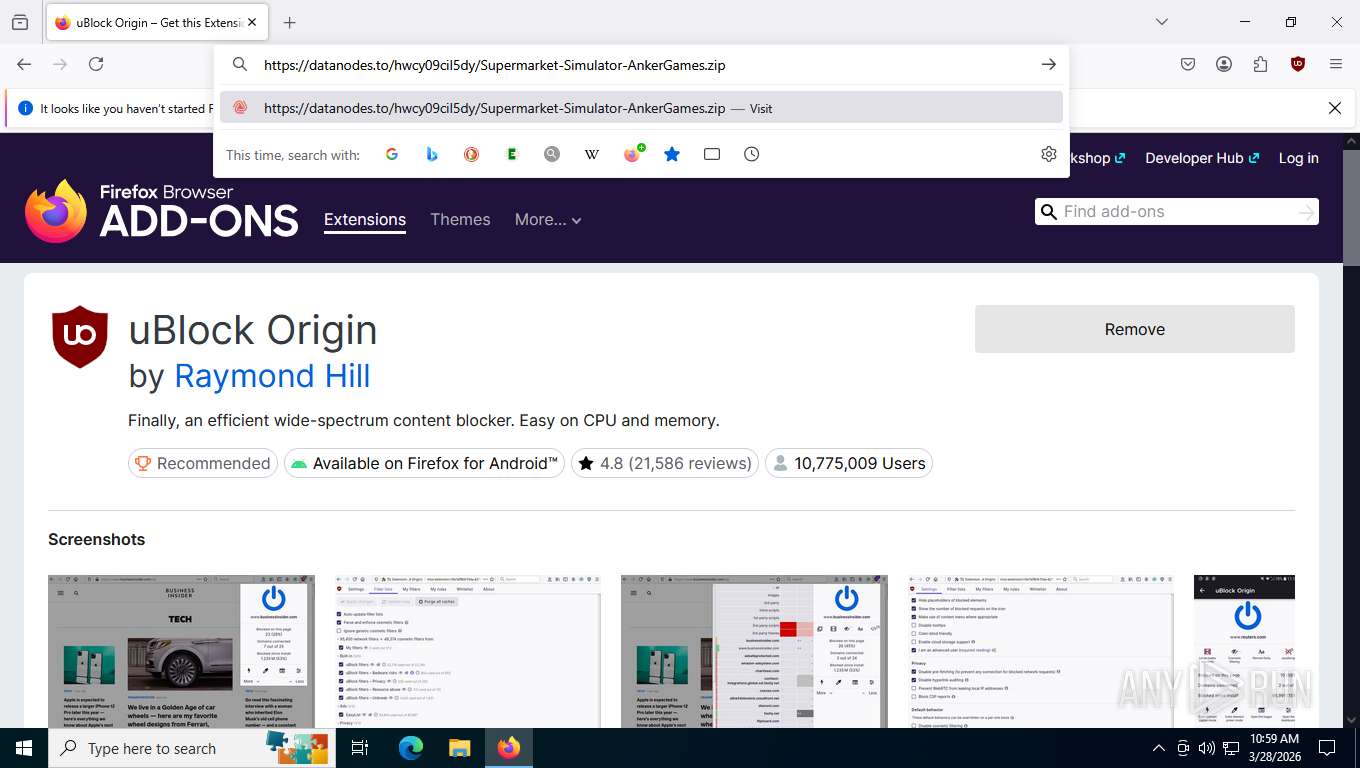
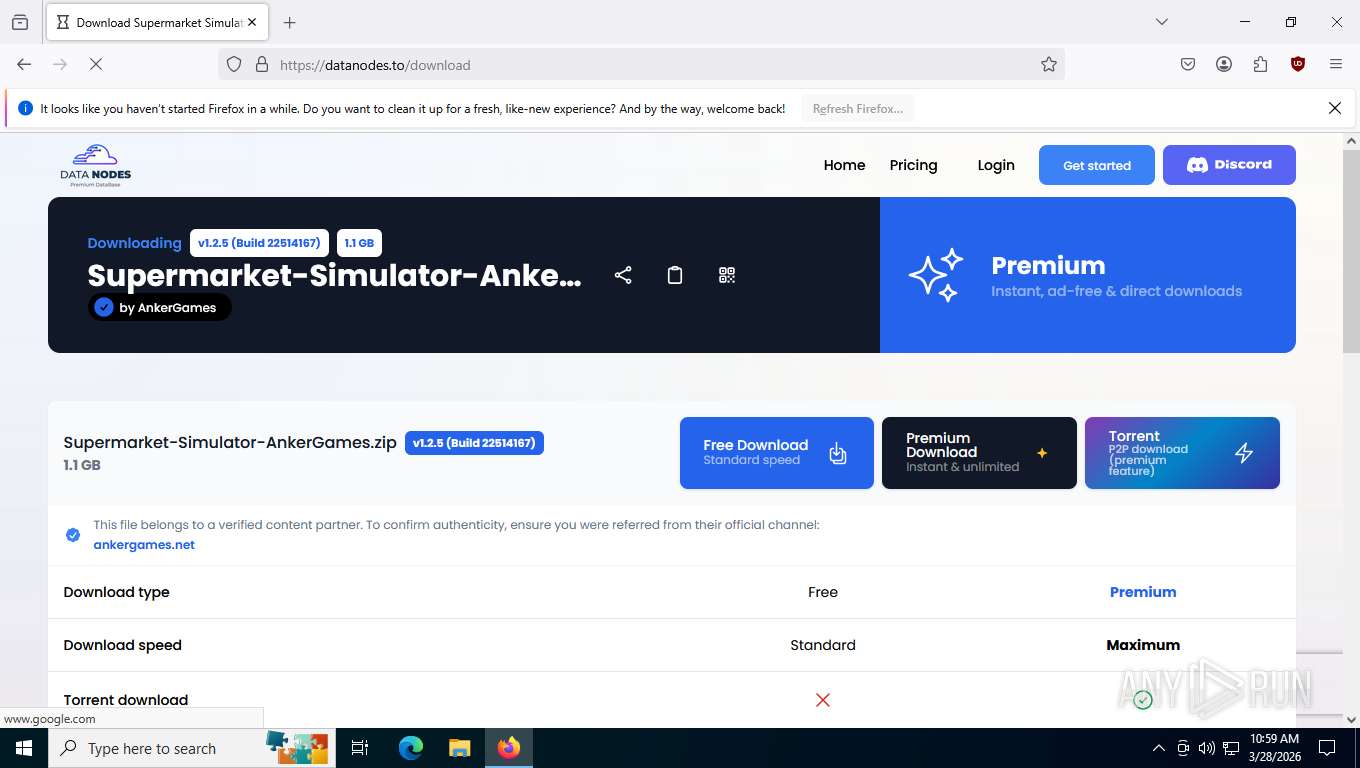
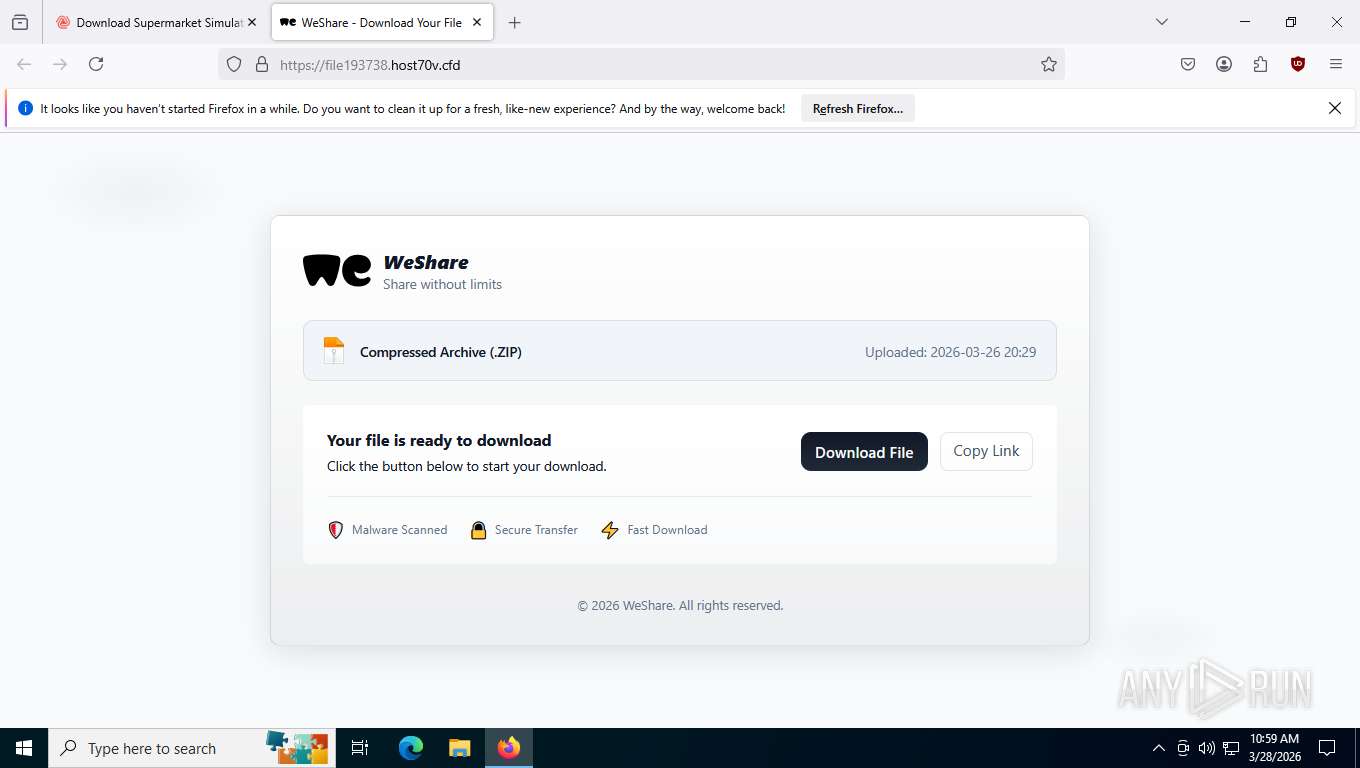
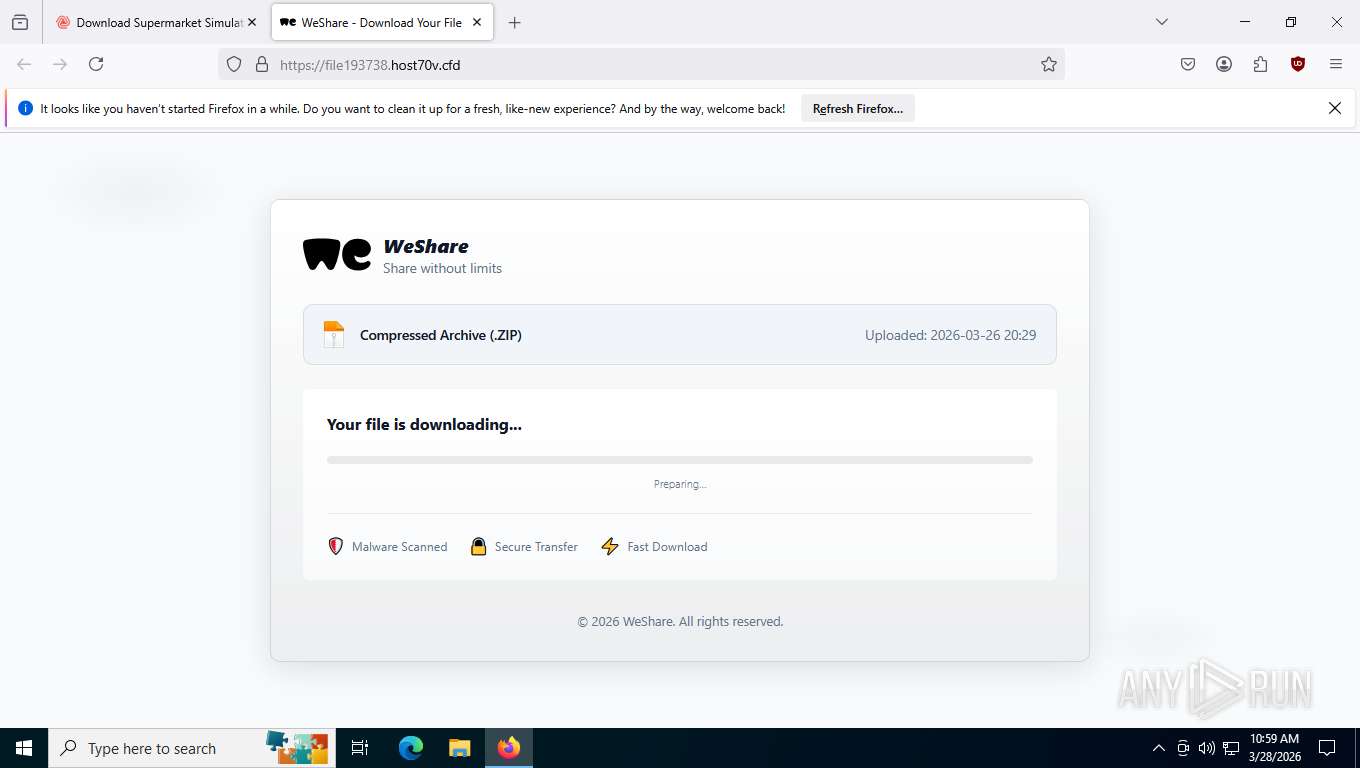
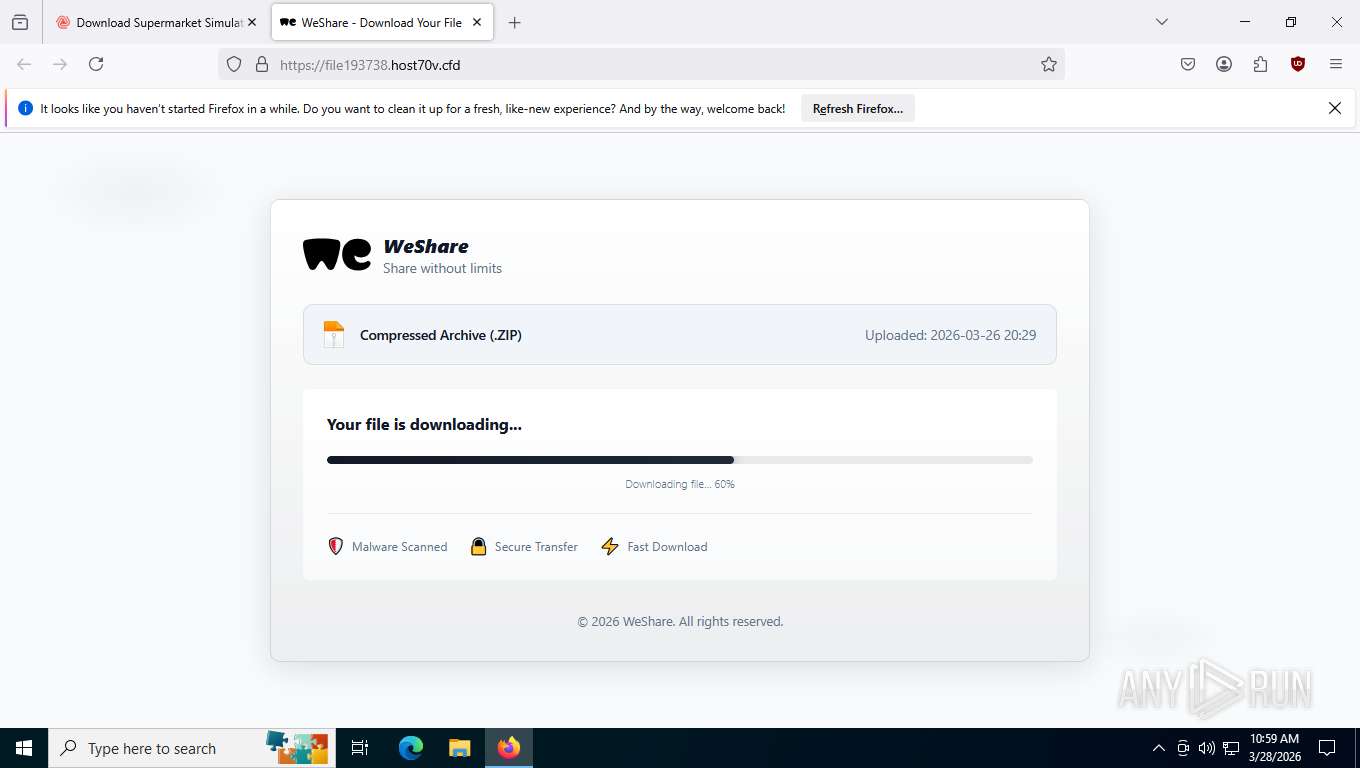
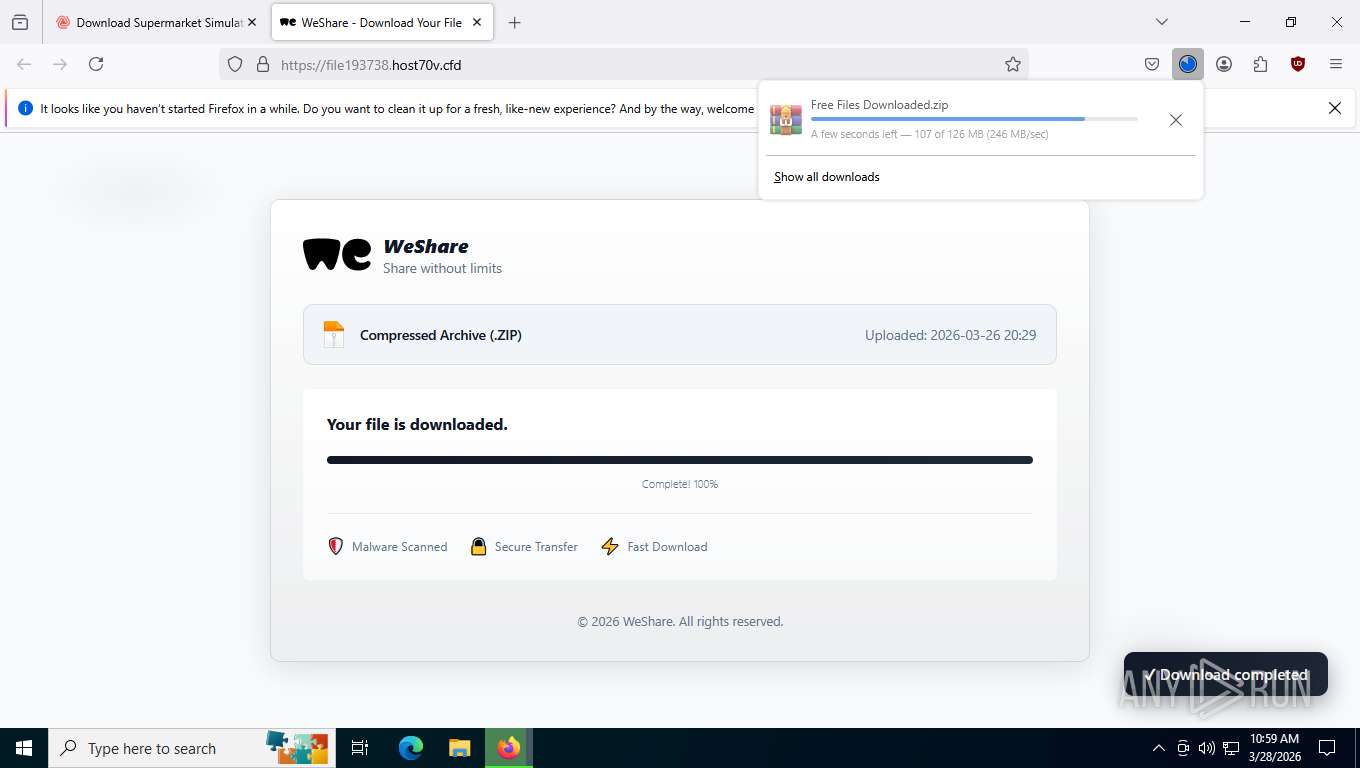
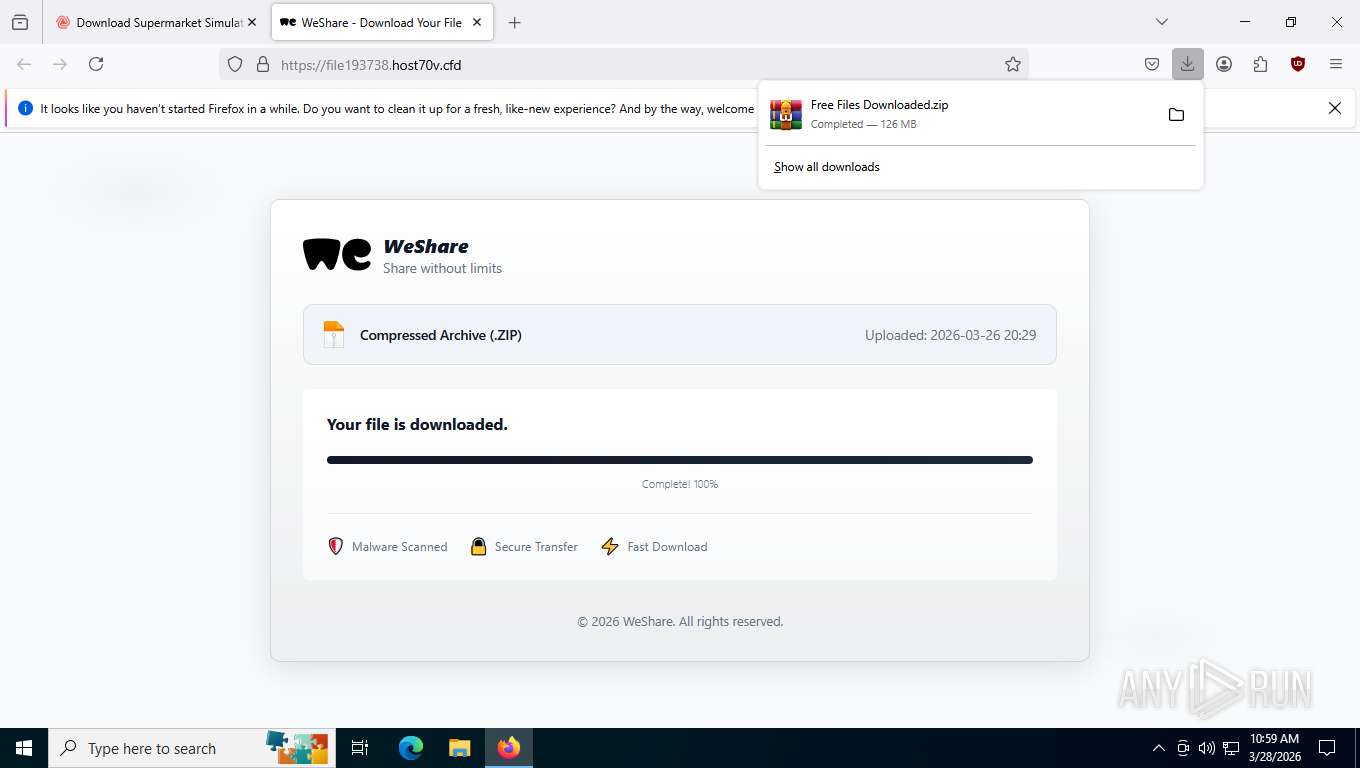
| URL: | https://datanodes.to/download |
| Full analysis: | https://app.any.run/tasks/116c24d2-d393-418a-b35c-6649c57ca576 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 28, 2026, 14:58:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C2FC4ABAD54C7ED8AB463C3AC384EB4E |
| SHA1: | B842C79B54C6DCB652A06944FF0A00017A572BEE |
| SHA256: | 6CA7251F7D69459BA9D072597DB3D2422AE57D07CE779416B5A241E7860810C0 |
| SSDEEP: | 3:N8ci+BAWlRBKSLz:2cXBAiD/ |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2232)
Executing a file with an untrusted certificate
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
Actions looks like stealing of personal data
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
Steals credentials from Web Browsers
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2232)
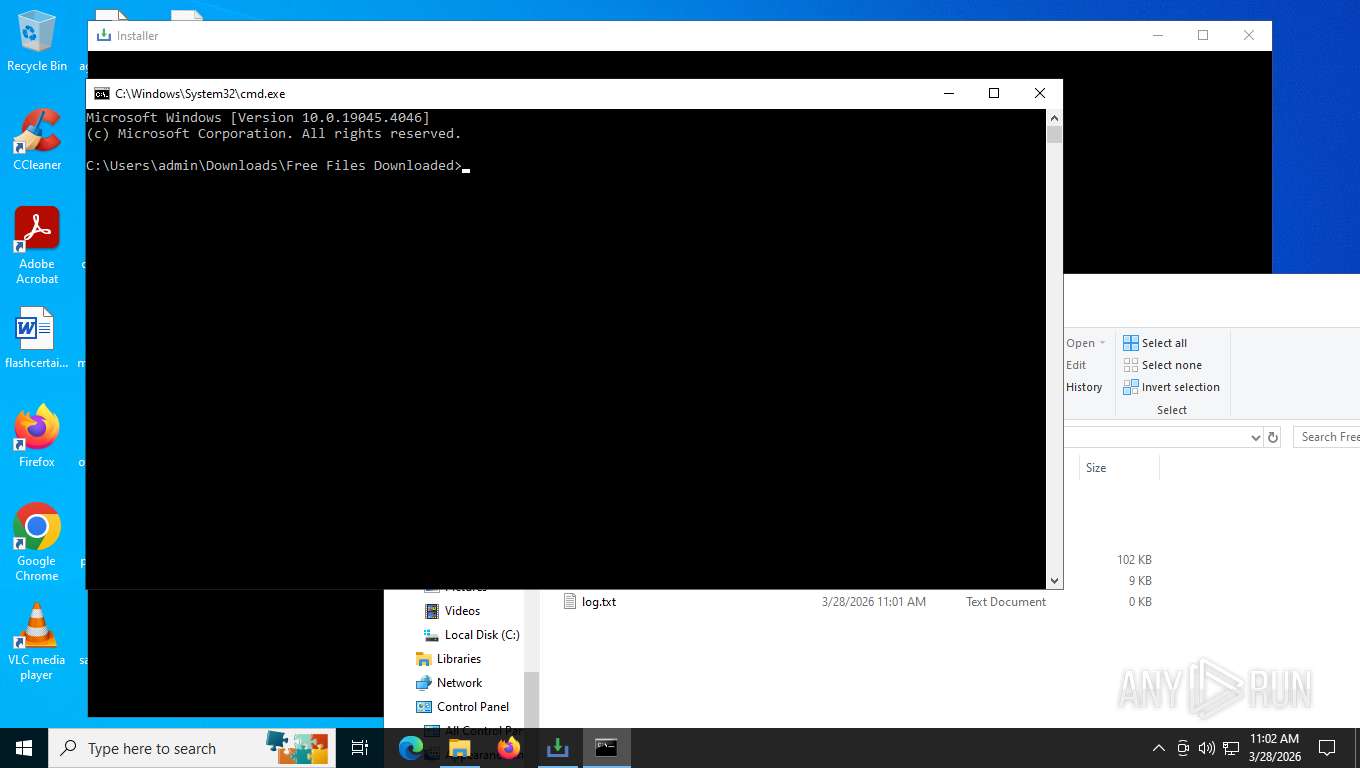
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4396)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 8076)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 8496)
- cmd.exe (PID: 900)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 4104)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 8228)
- cmd.exe (PID: 7412)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 7324)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7184)
- cmd.exe (PID: 900)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 8496)
- cmd.exe (PID: 4308)
- 8blgSOjBe.exe (PID: 4944)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 8228)
- cmd.exe (PID: 7412)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 2032)
- 8blgSOjBe.exe (PID: 420)
Accesses local storage devices (Win32_LogicalDisk) (SCRIPT)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 5404)
Checks for external IP
- lnstaIer.exe (PID: 664)
- svchost.exe (PID: 2232)
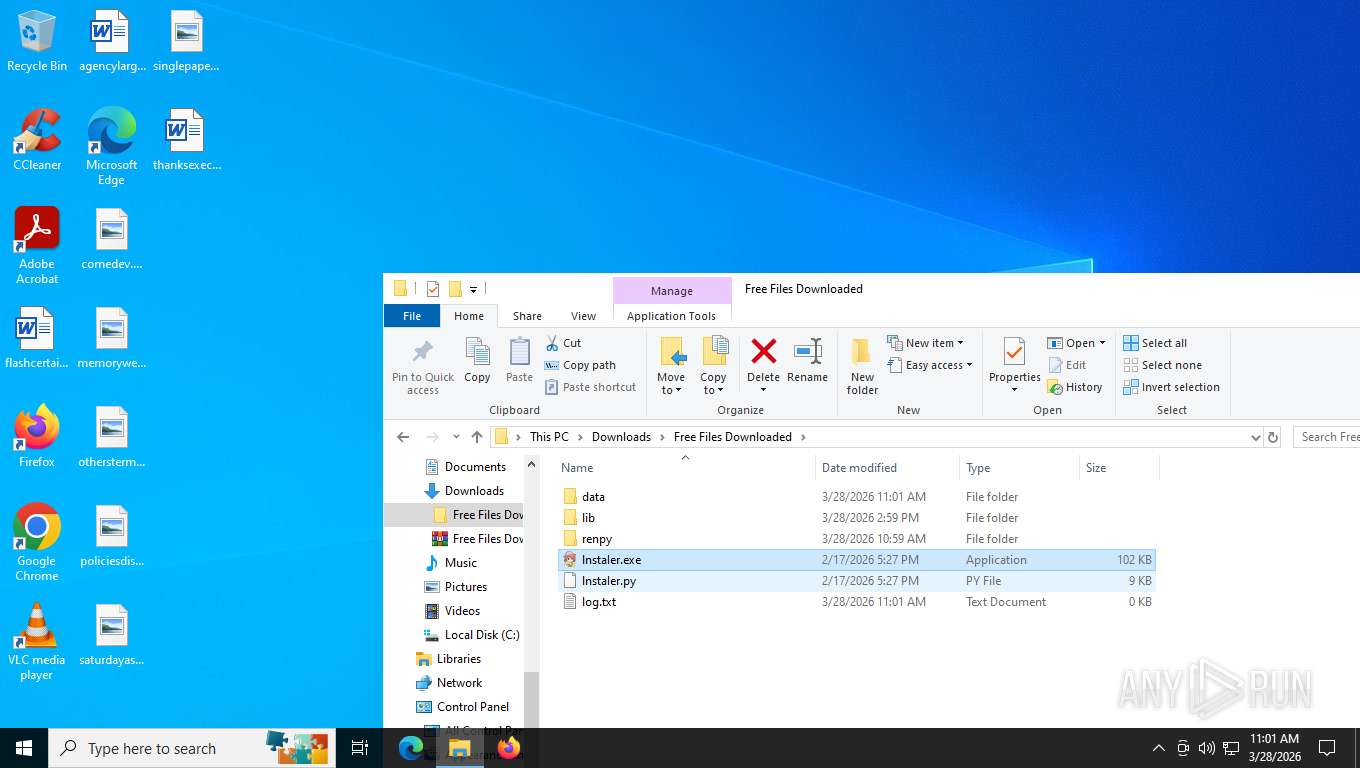
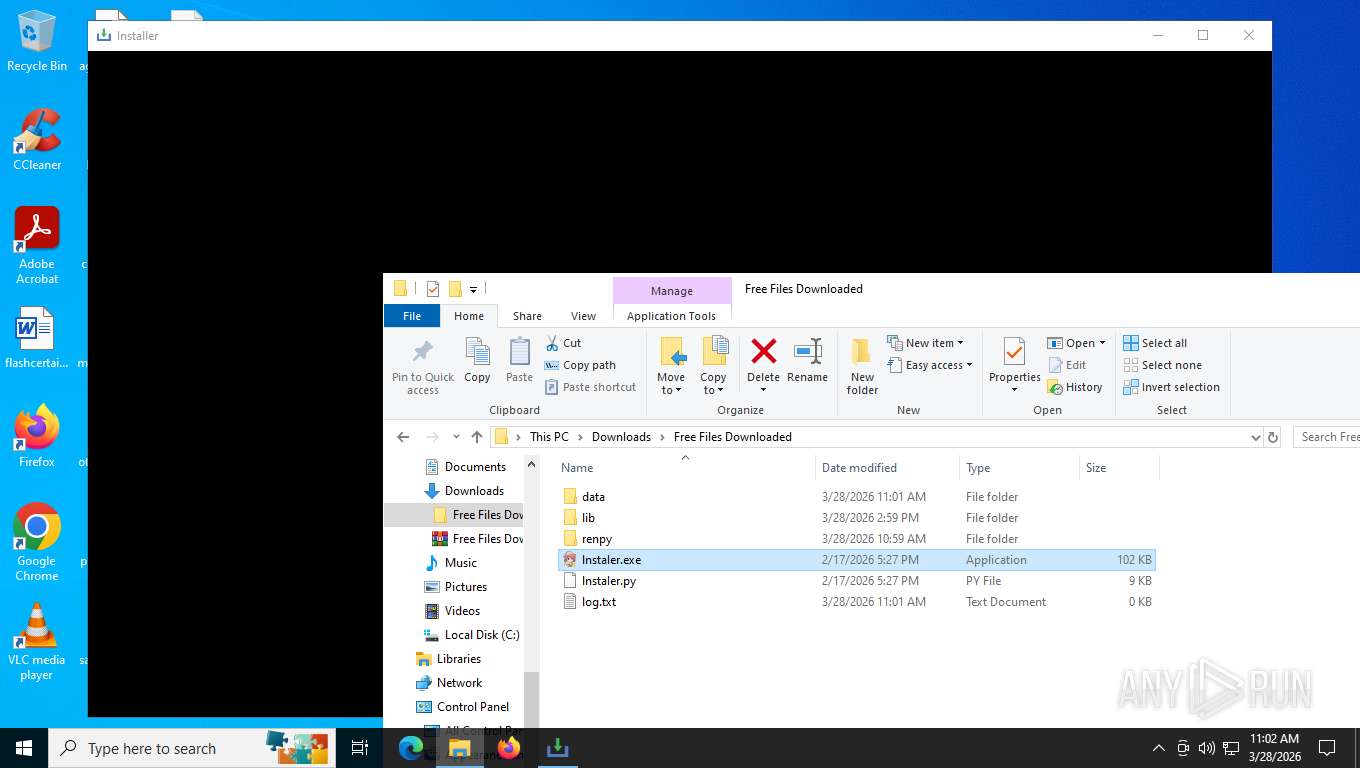
Executable content was dropped or overwritten
- lnstaIer.exe (PID: 664)
- 8blgSOjBe.exe (PID: 4944)
- CircuitPilot.exe (PID: 8528)
Possible stealing from browsers
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
Possible stealing from crypto wallets
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
Searches for installed software
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
Possible stealing of email data
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
Possible stealing from password managers
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
The process bypasses the loading of PowerShell profile settings
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
Executes script without checking the security policy
- powershell.exe (PID: 9136)
- powershell.exe (PID: 7960)
The process hide an interactive prompt from the user
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
The process hides Powershell's copyright startup banner
- 8blgSOjBe.exe (PID: 4944)
- 8blgSOjBe.exe (PID: 420)
Starts itself from another location
- CircuitPilot.exe (PID: 8528)
INFO
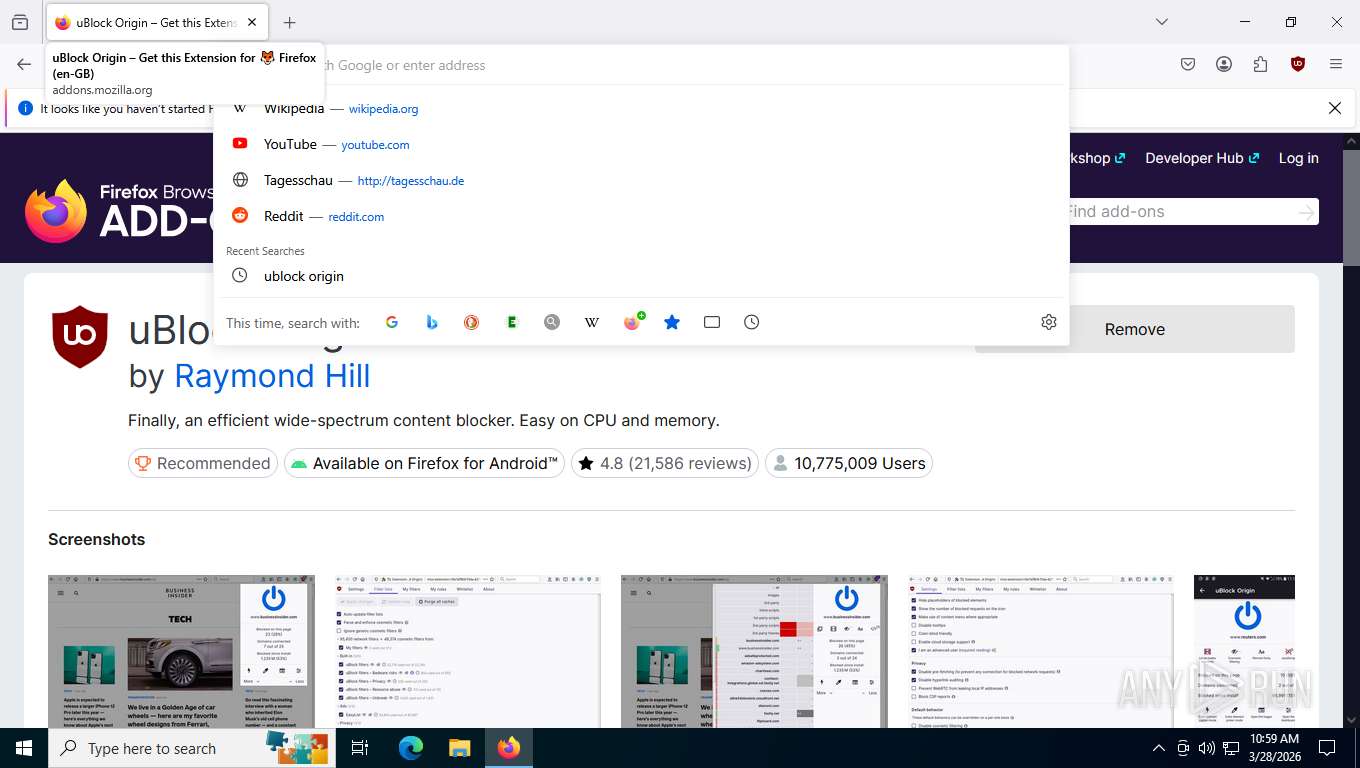
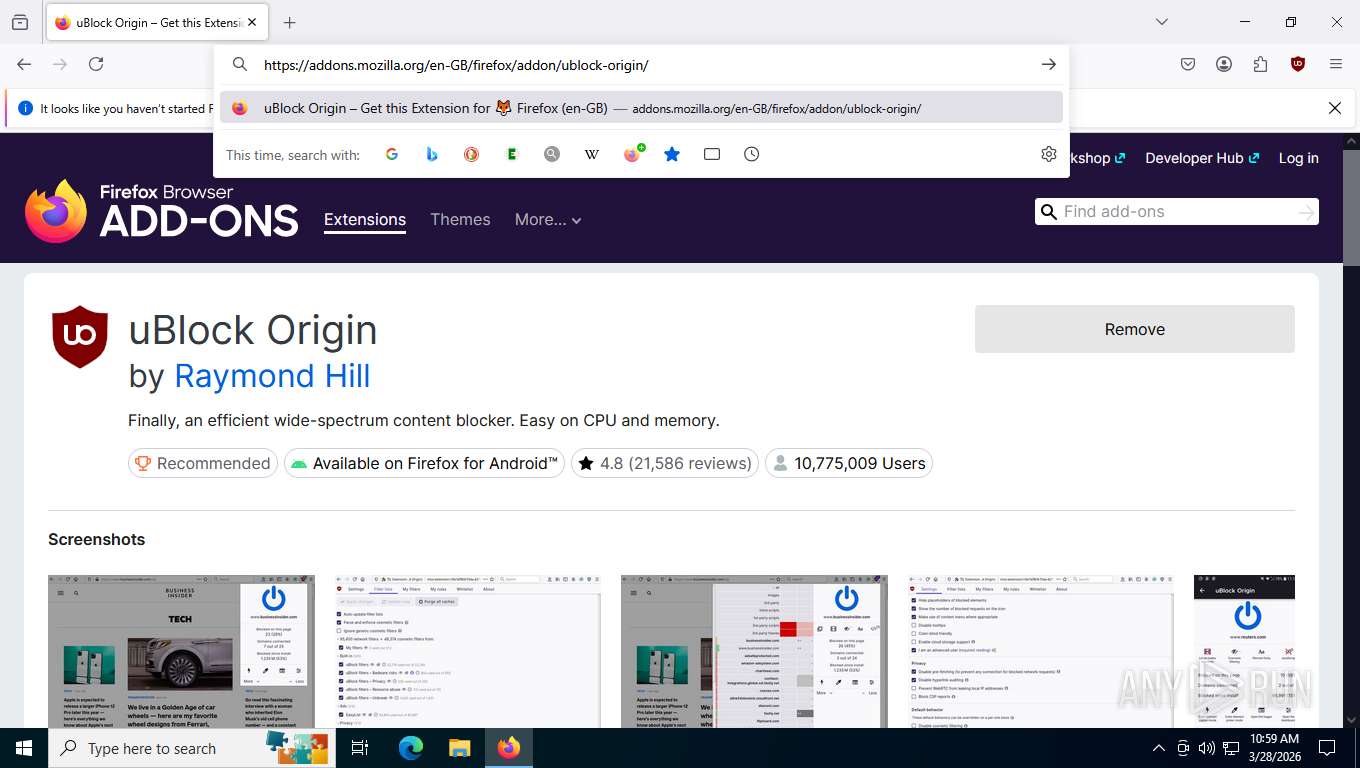
Application launched itself
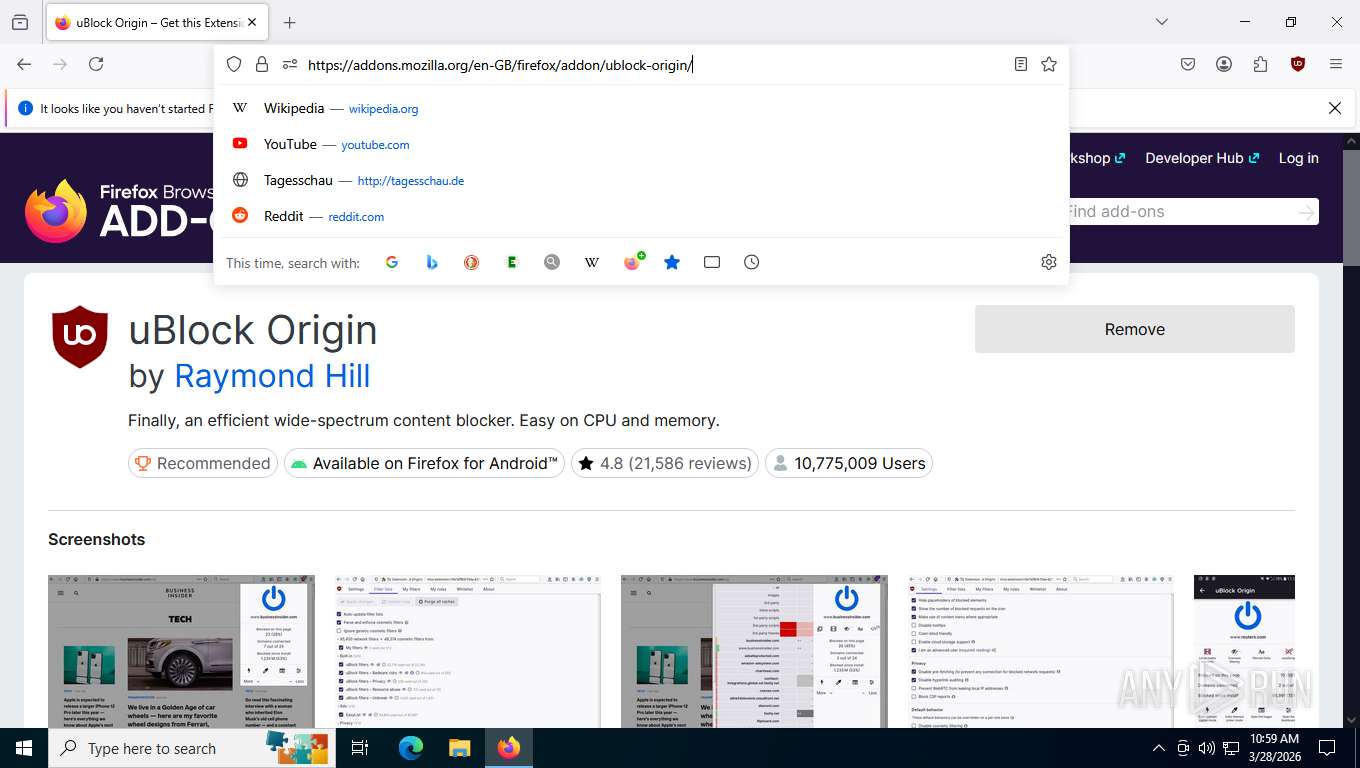
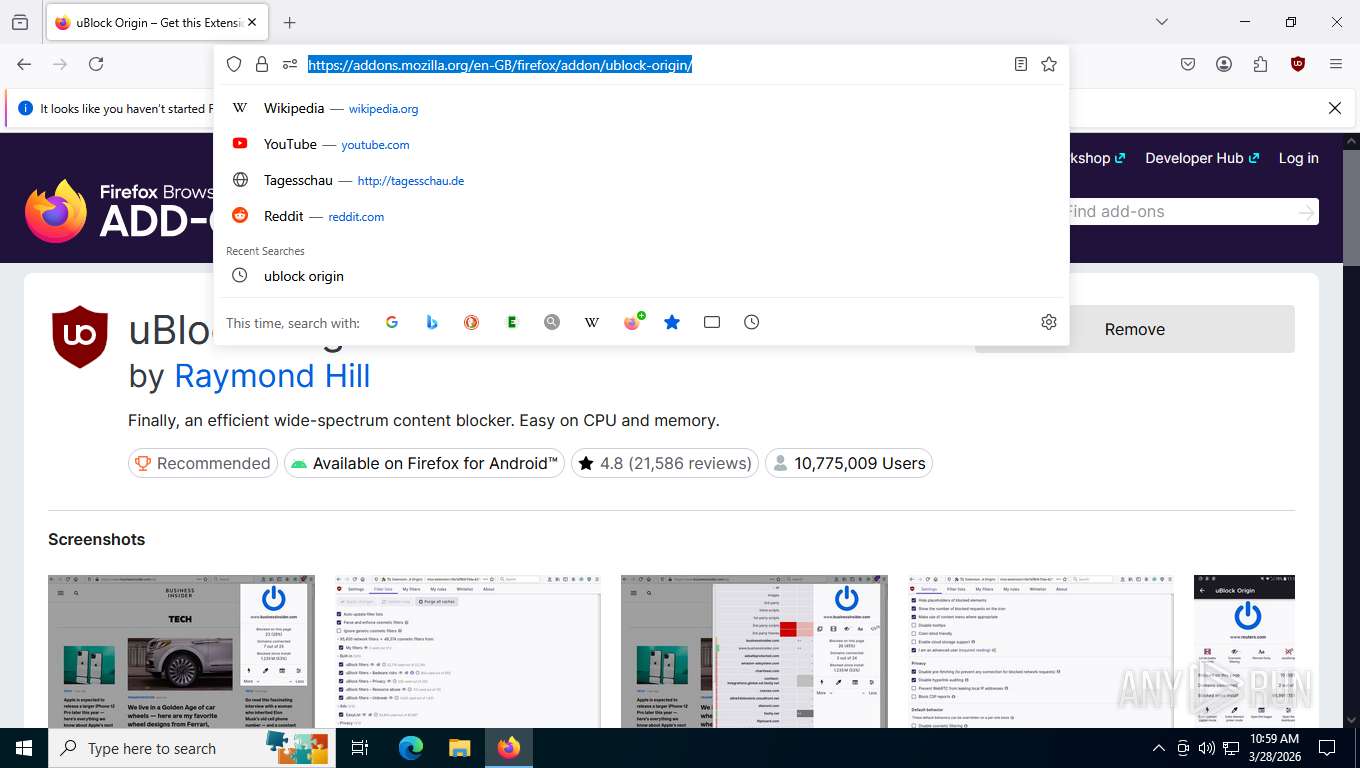
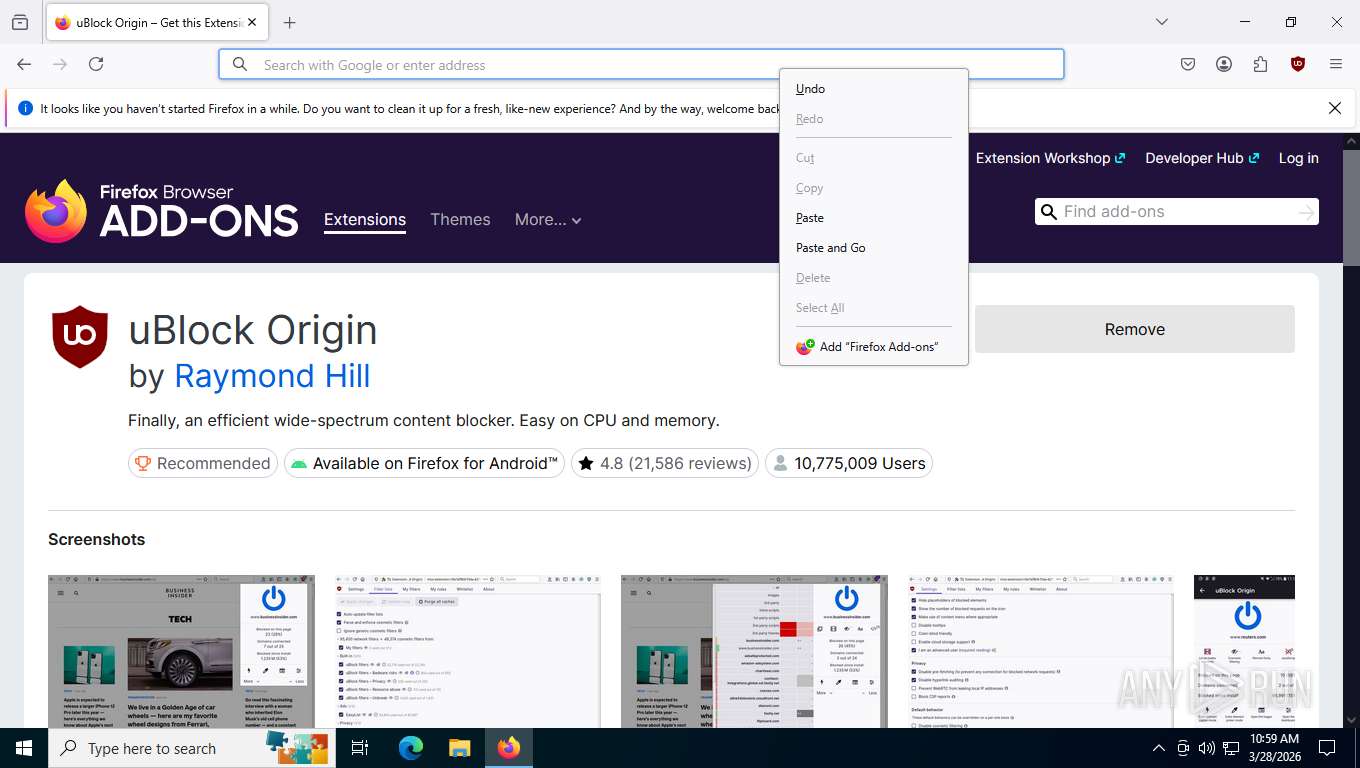
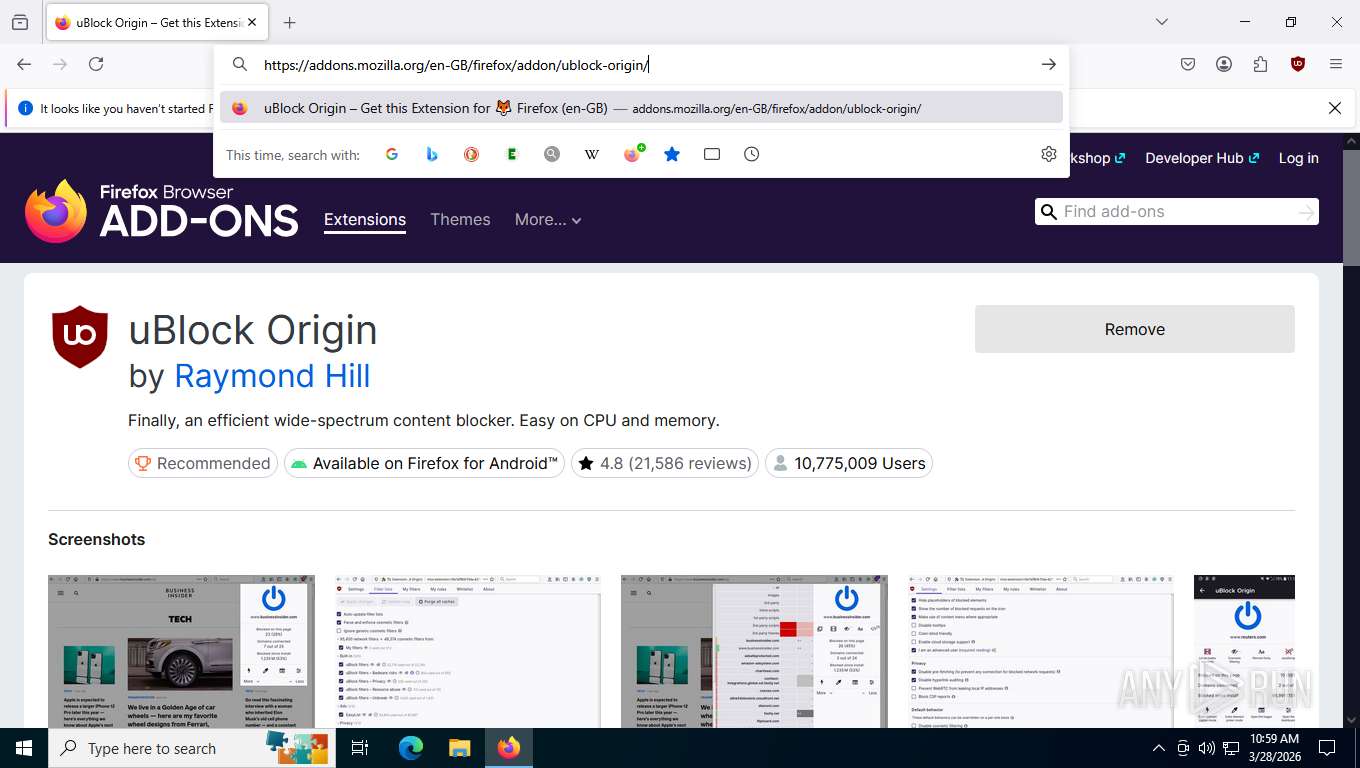
- firefox.exe (PID: 4968)
- firefox.exe (PID: 8020)
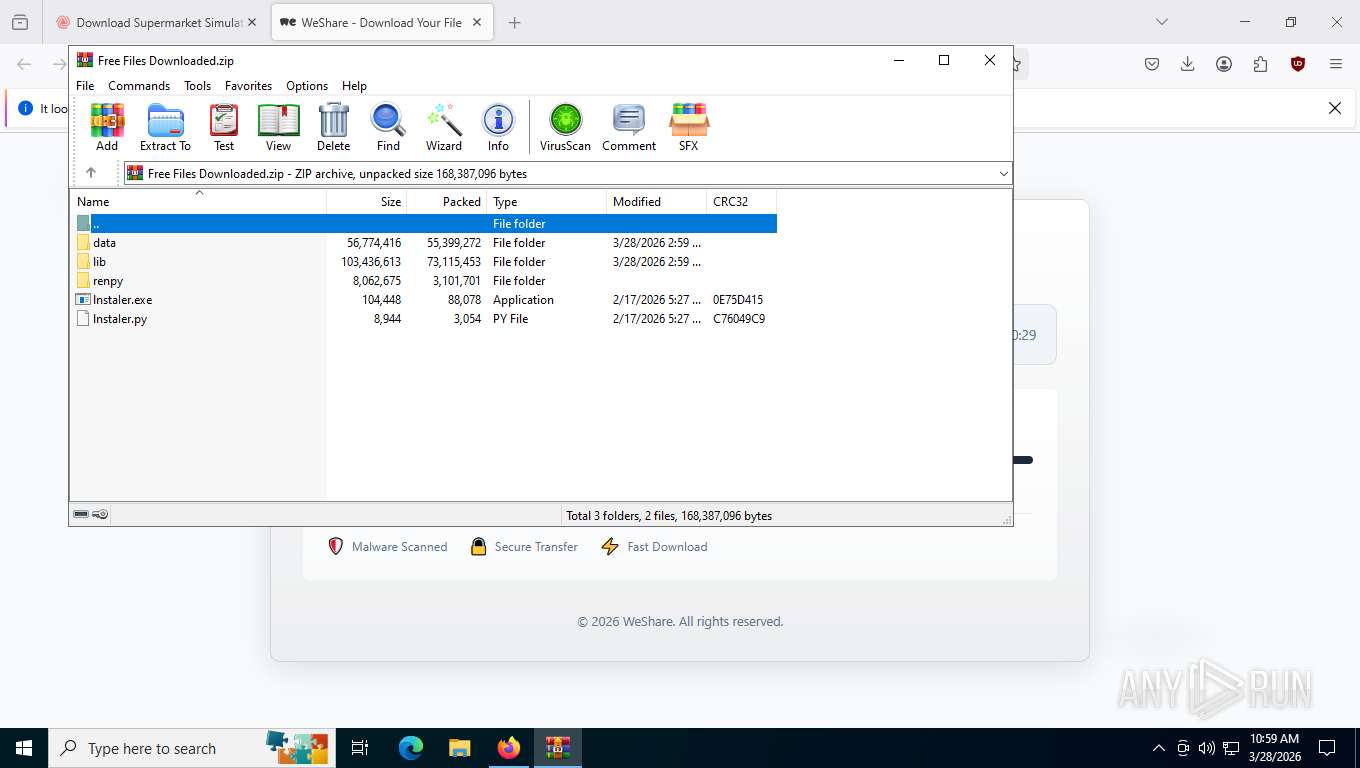
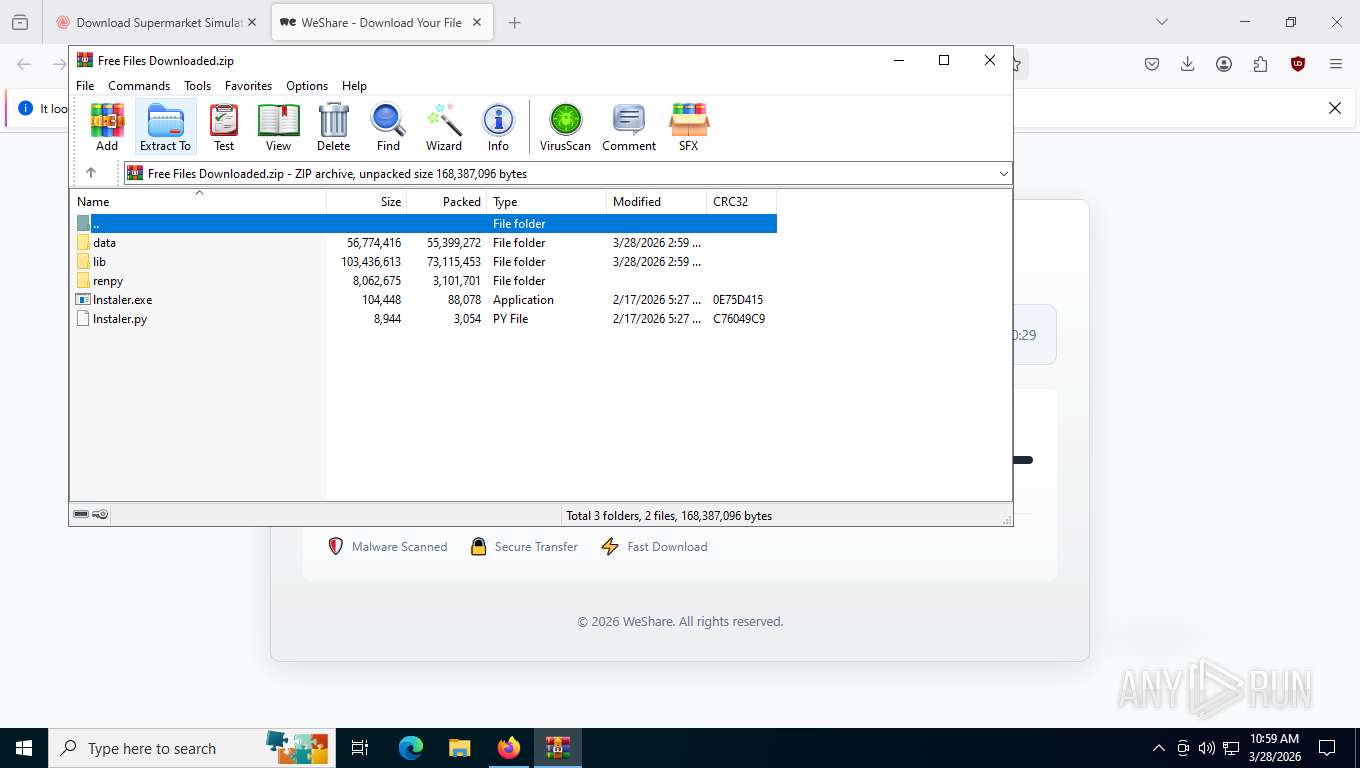
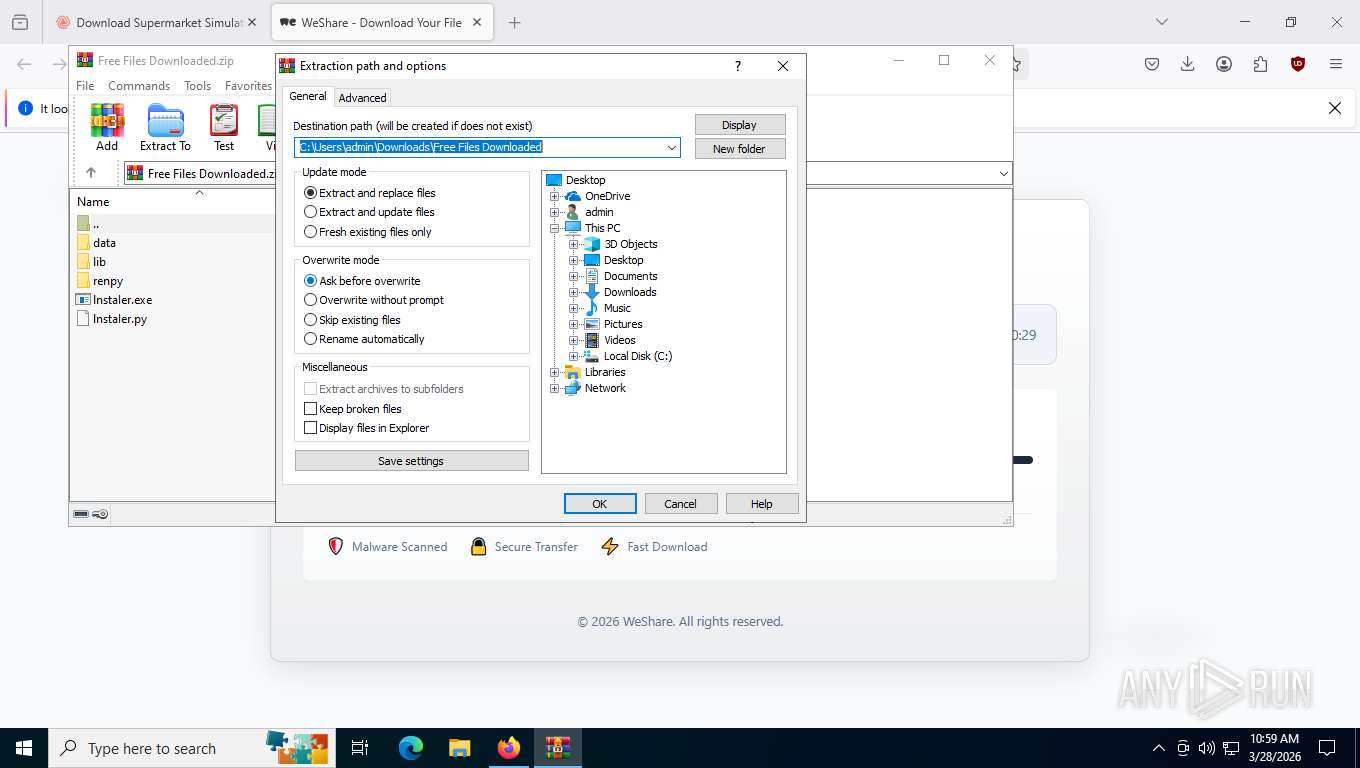
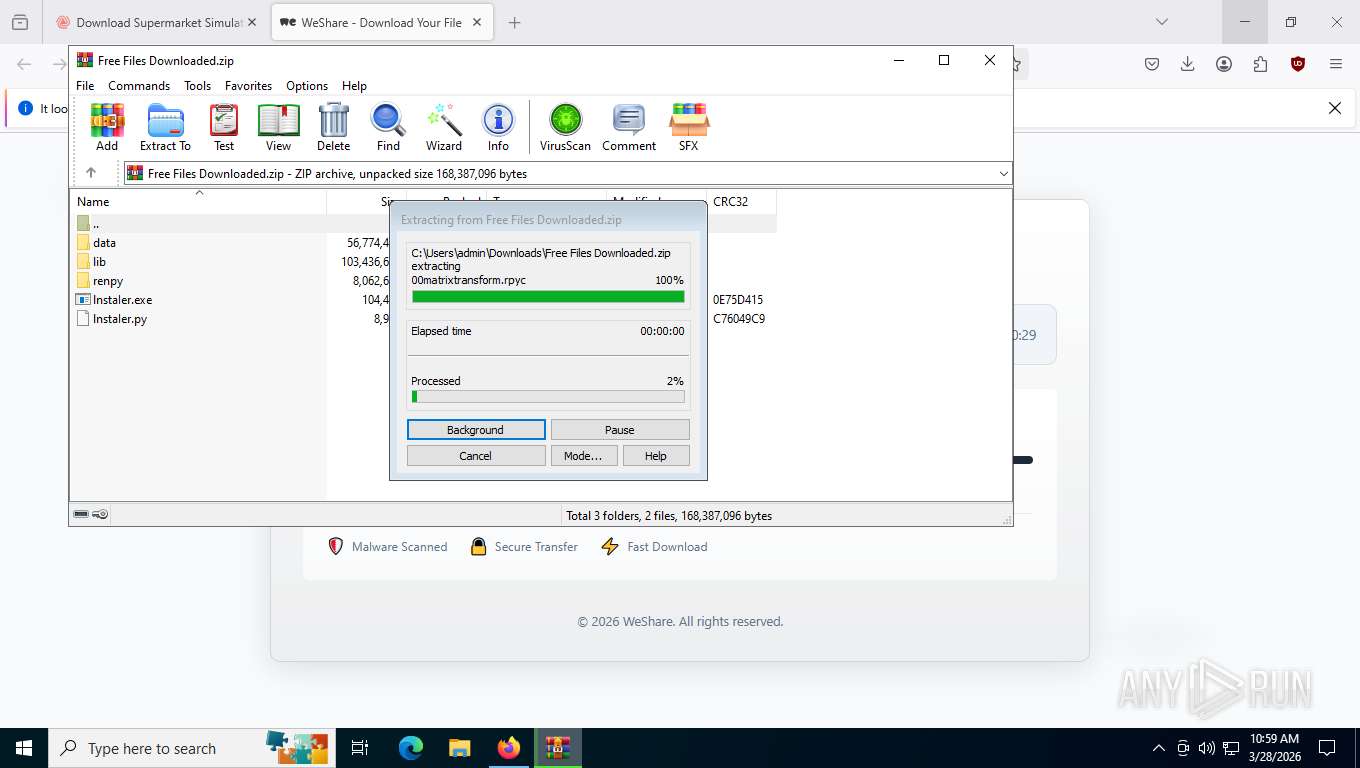
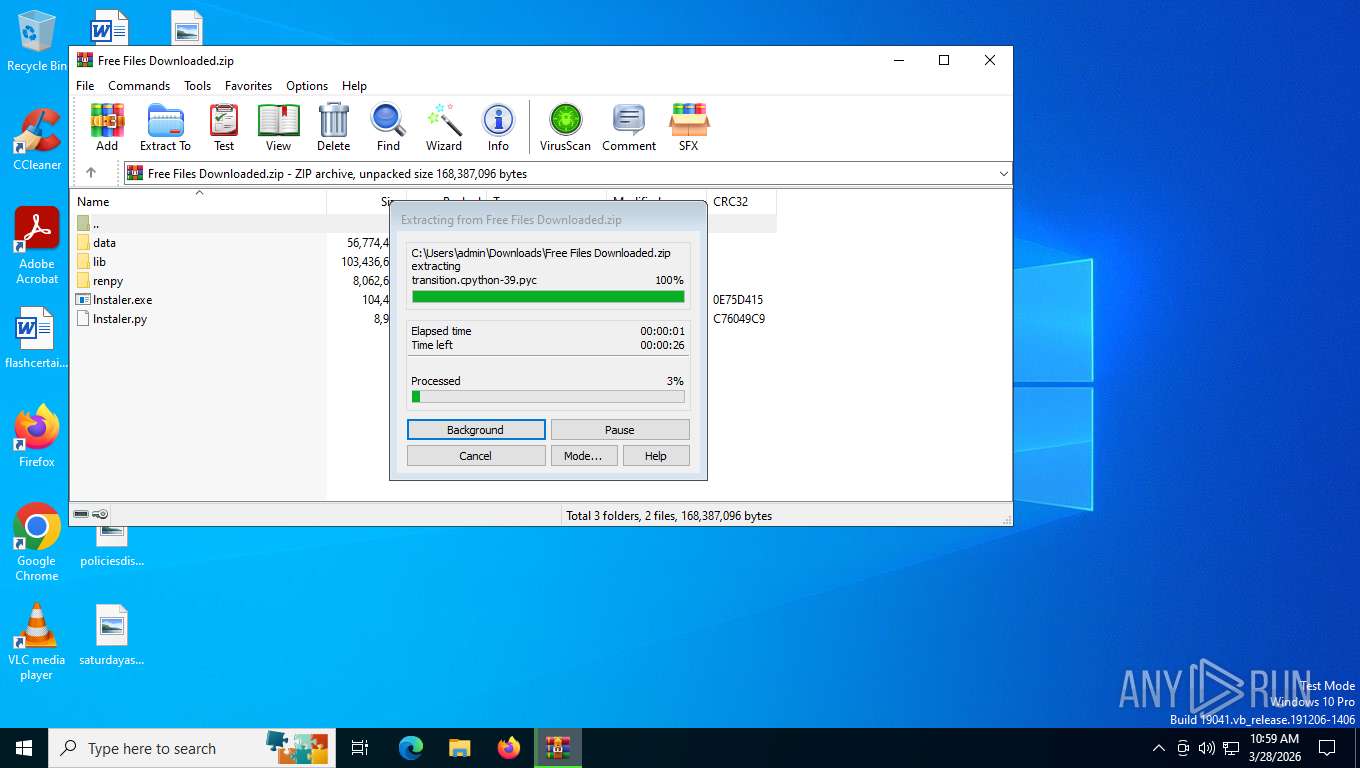
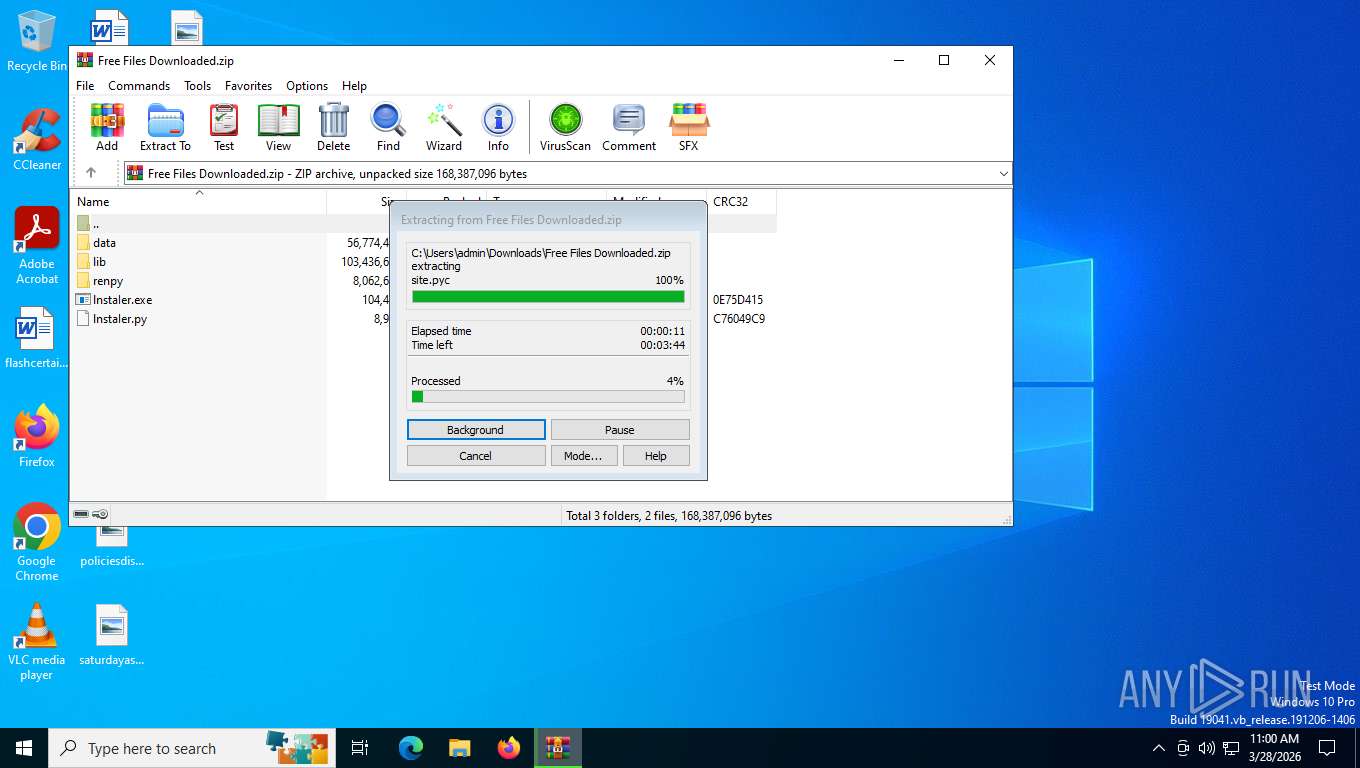
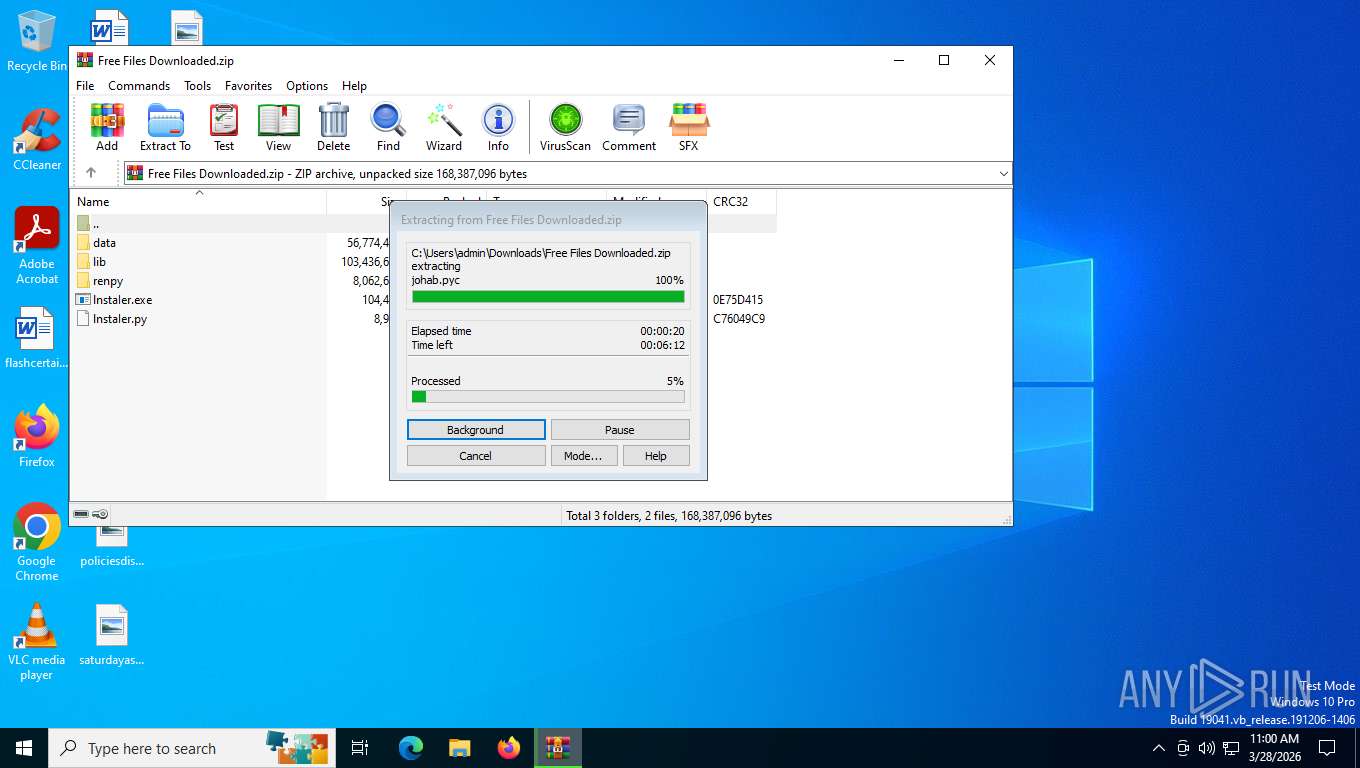
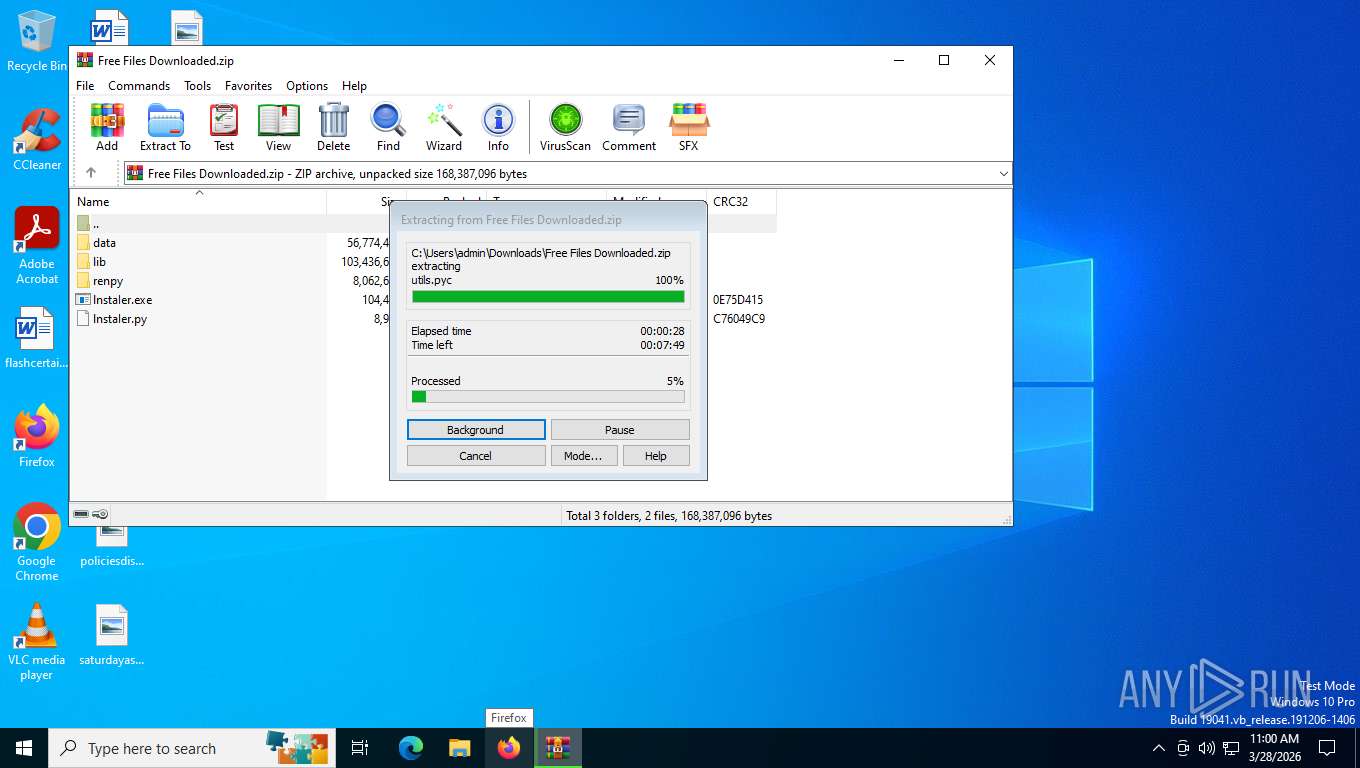
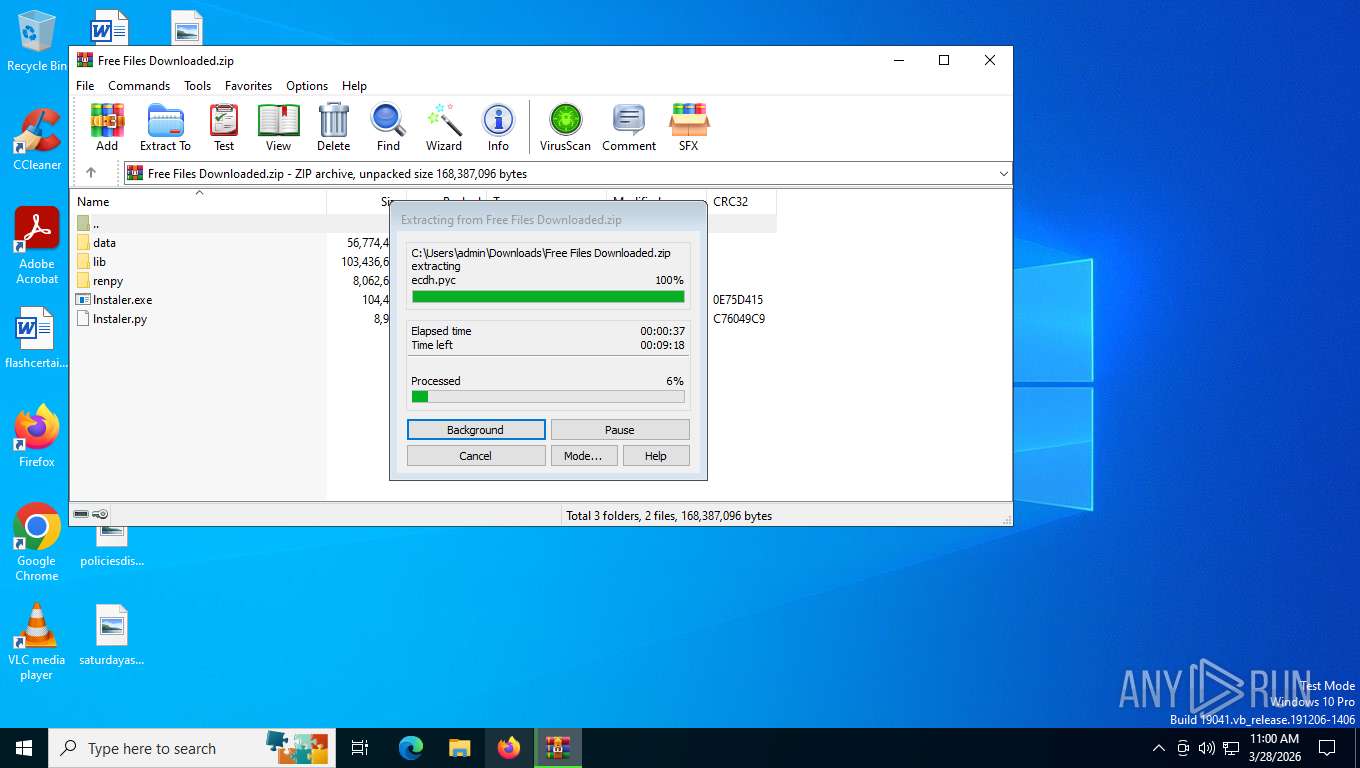
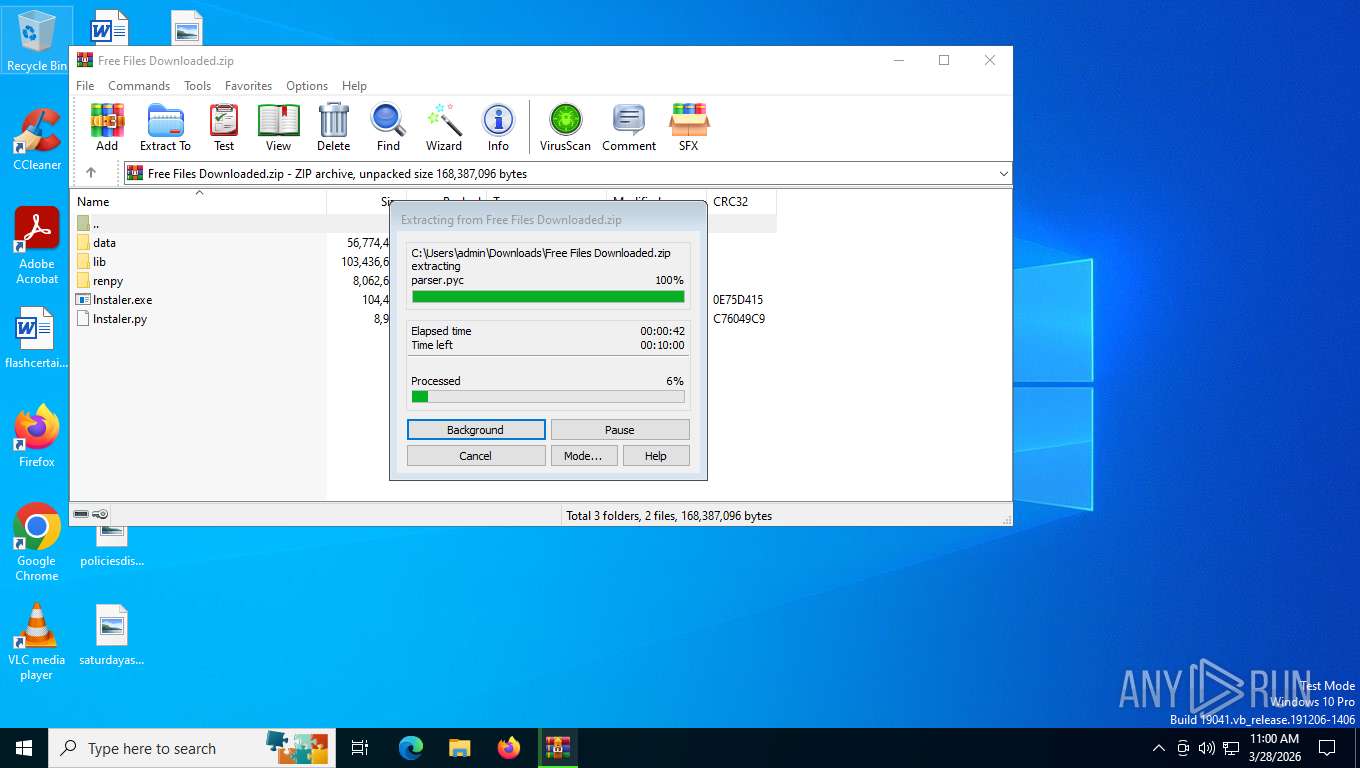
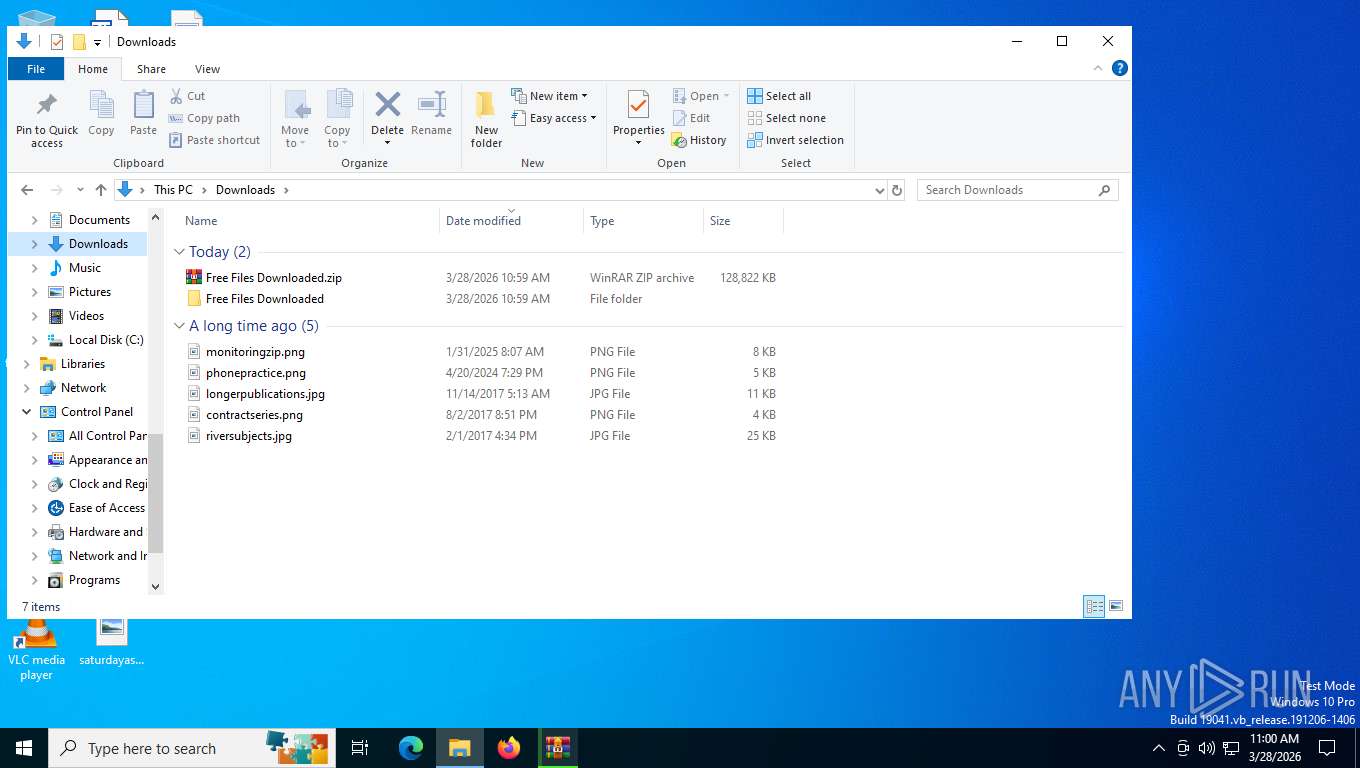
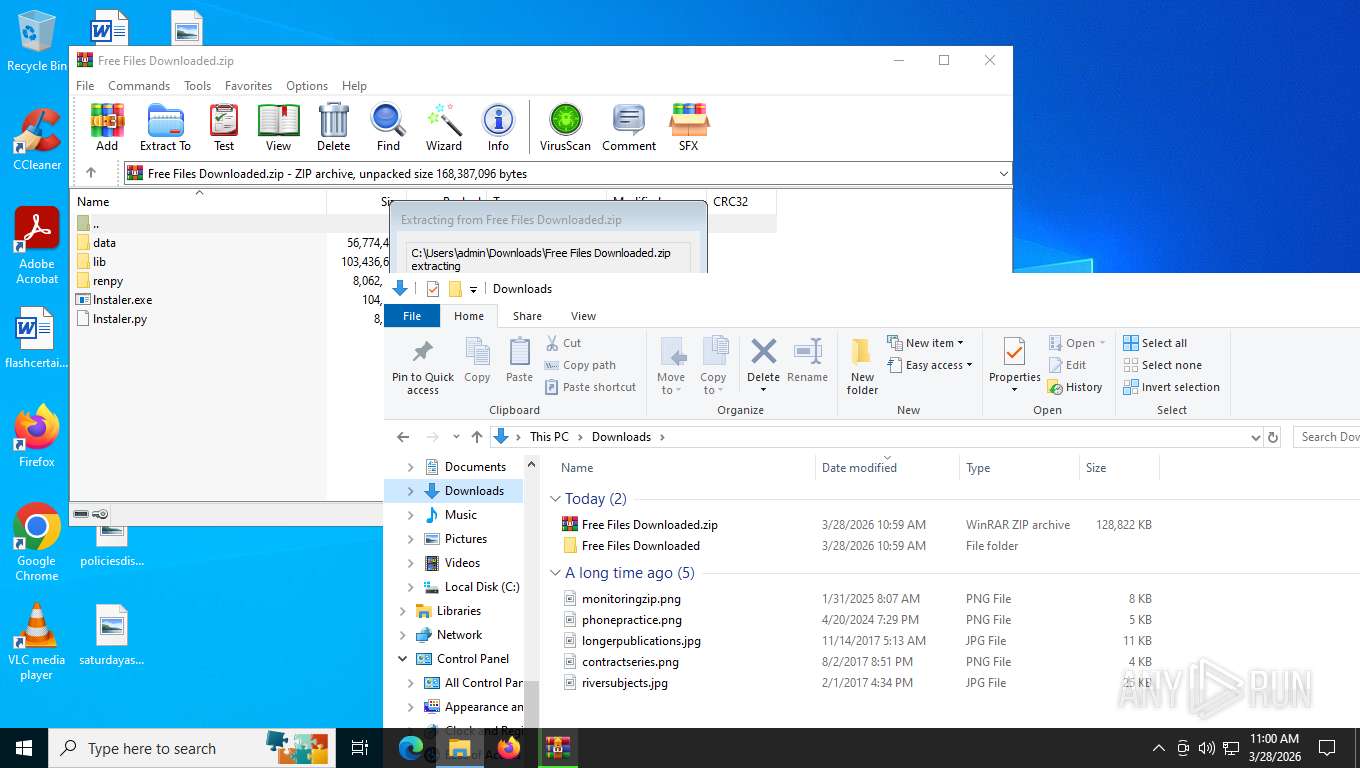
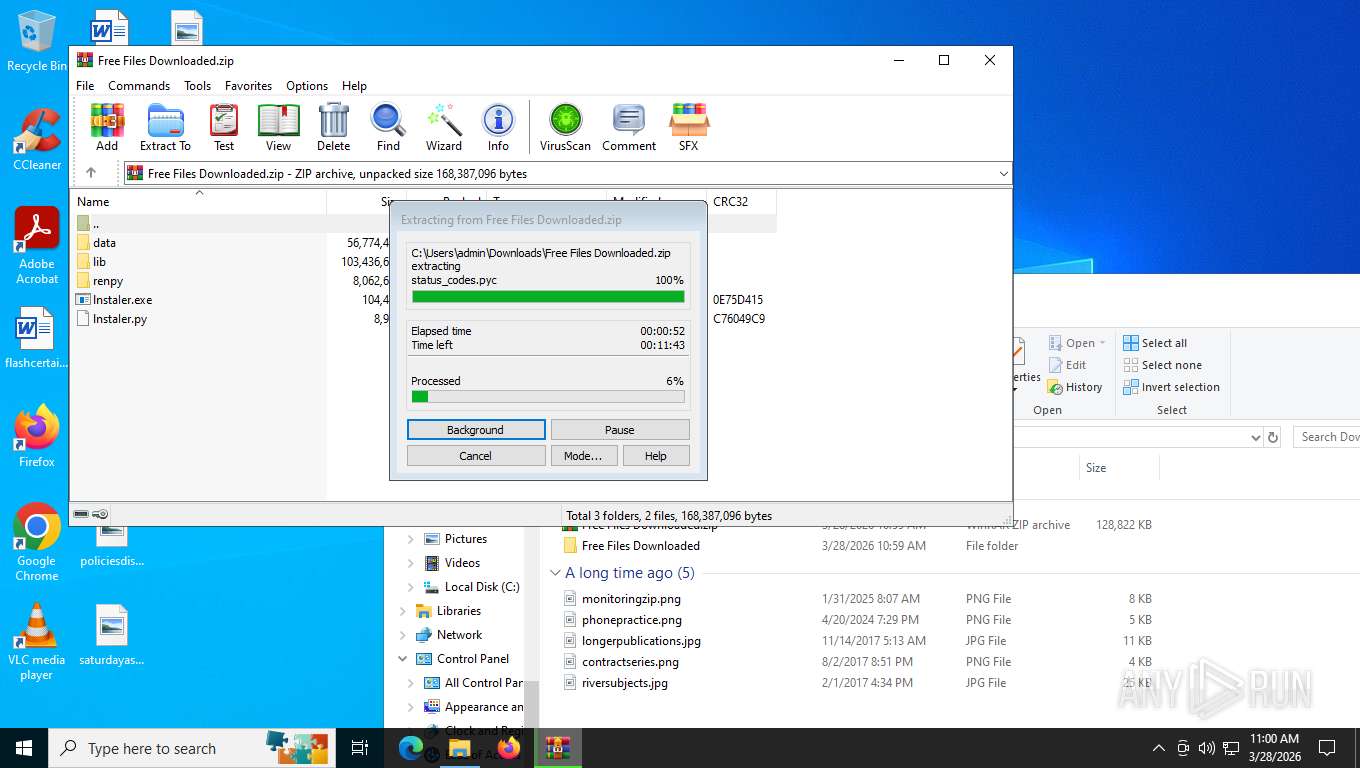
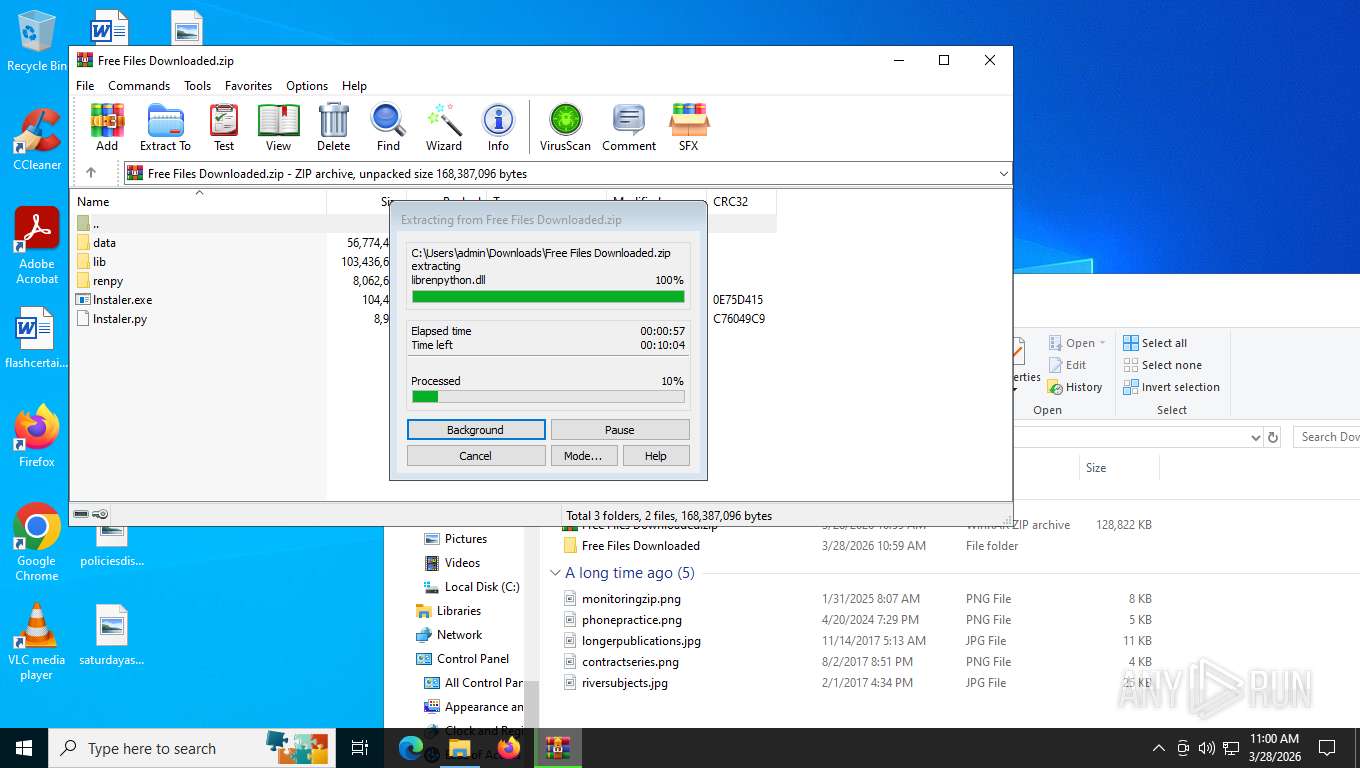
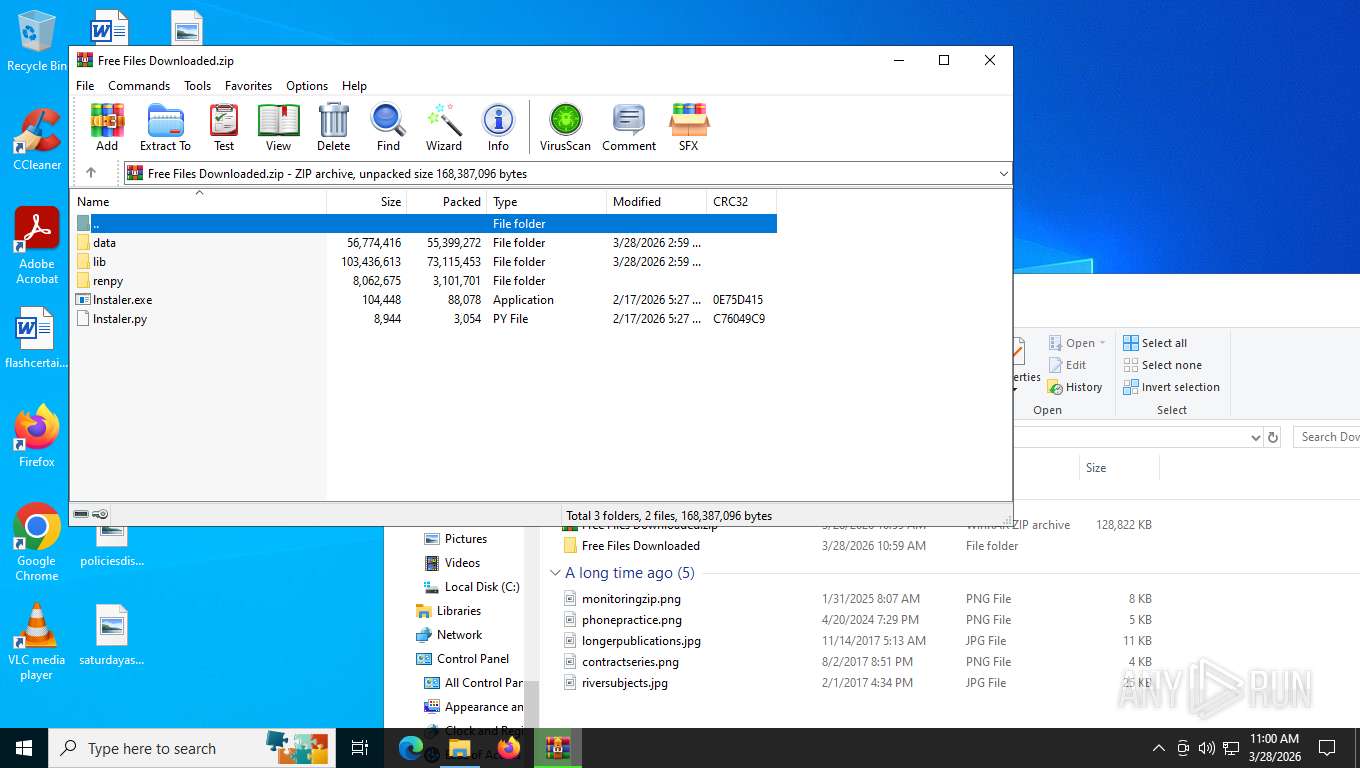
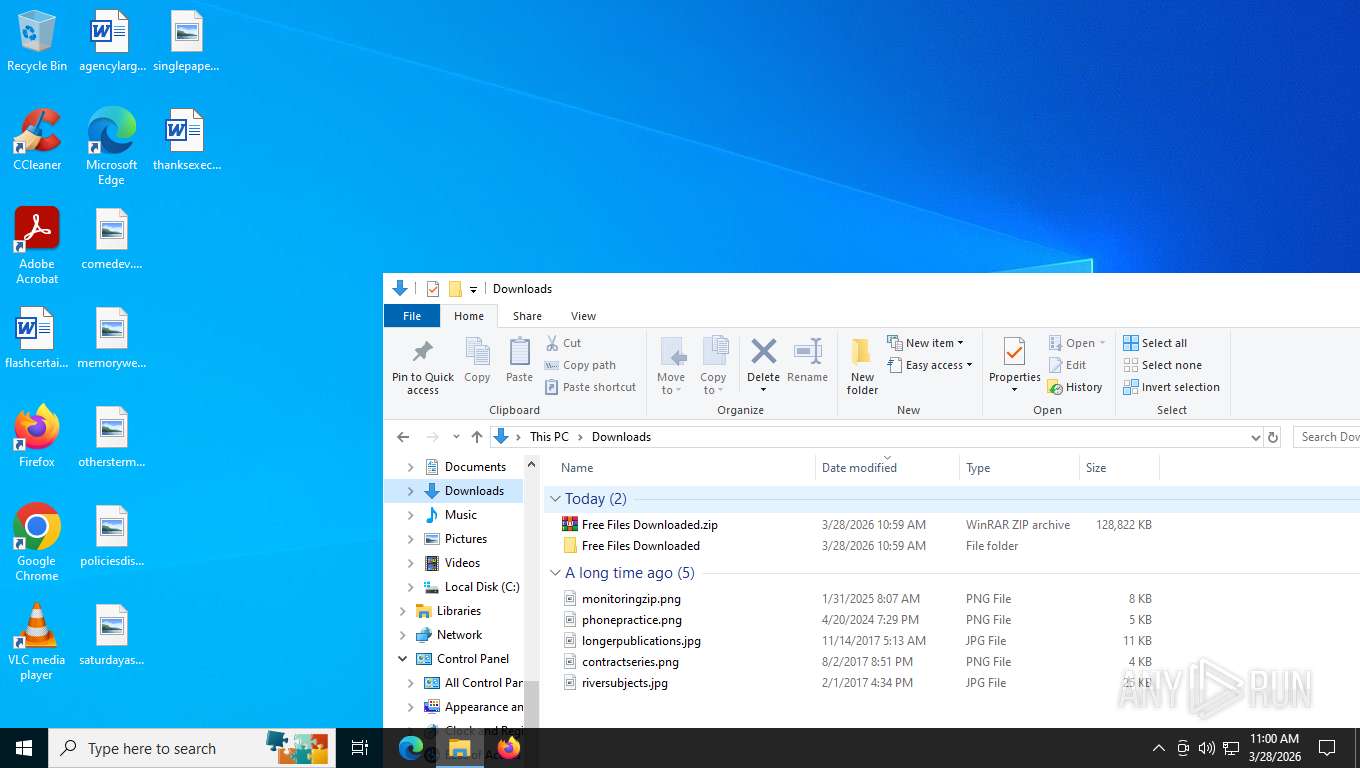
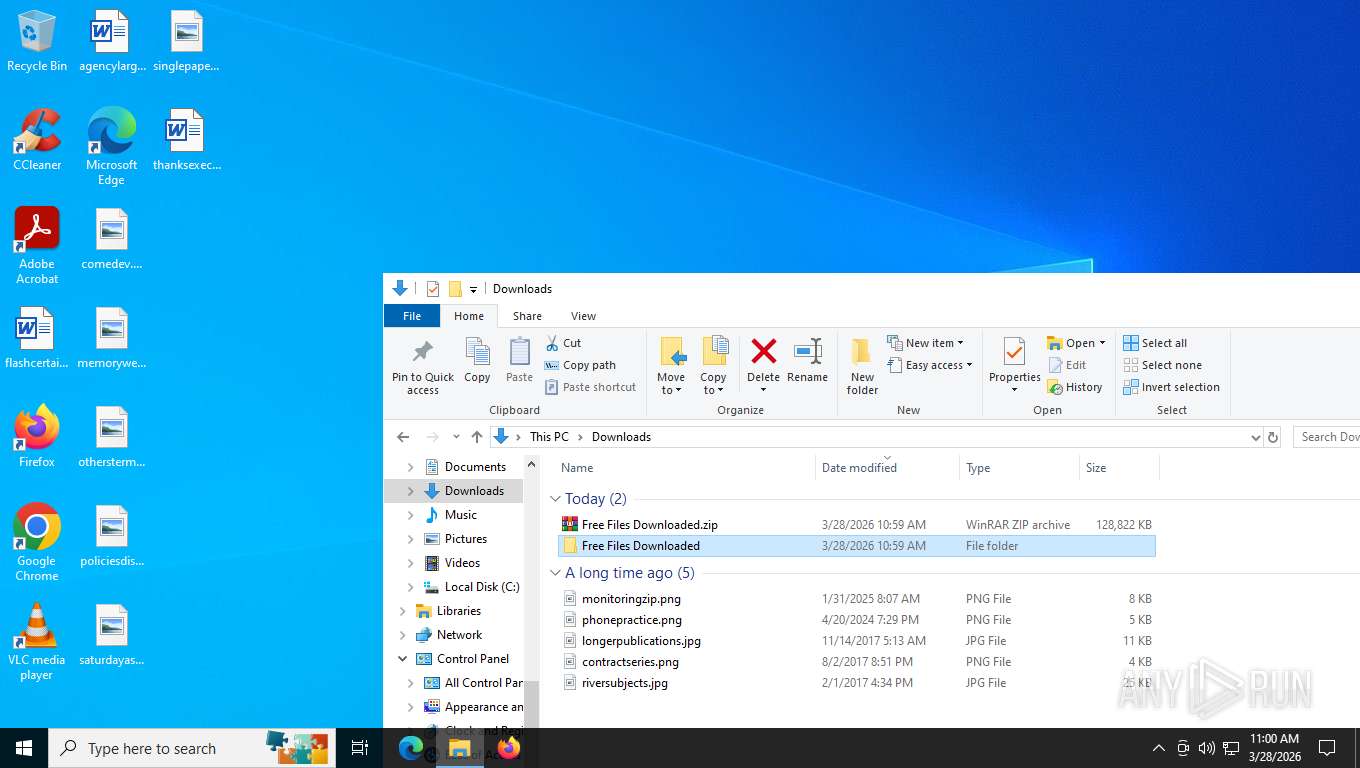
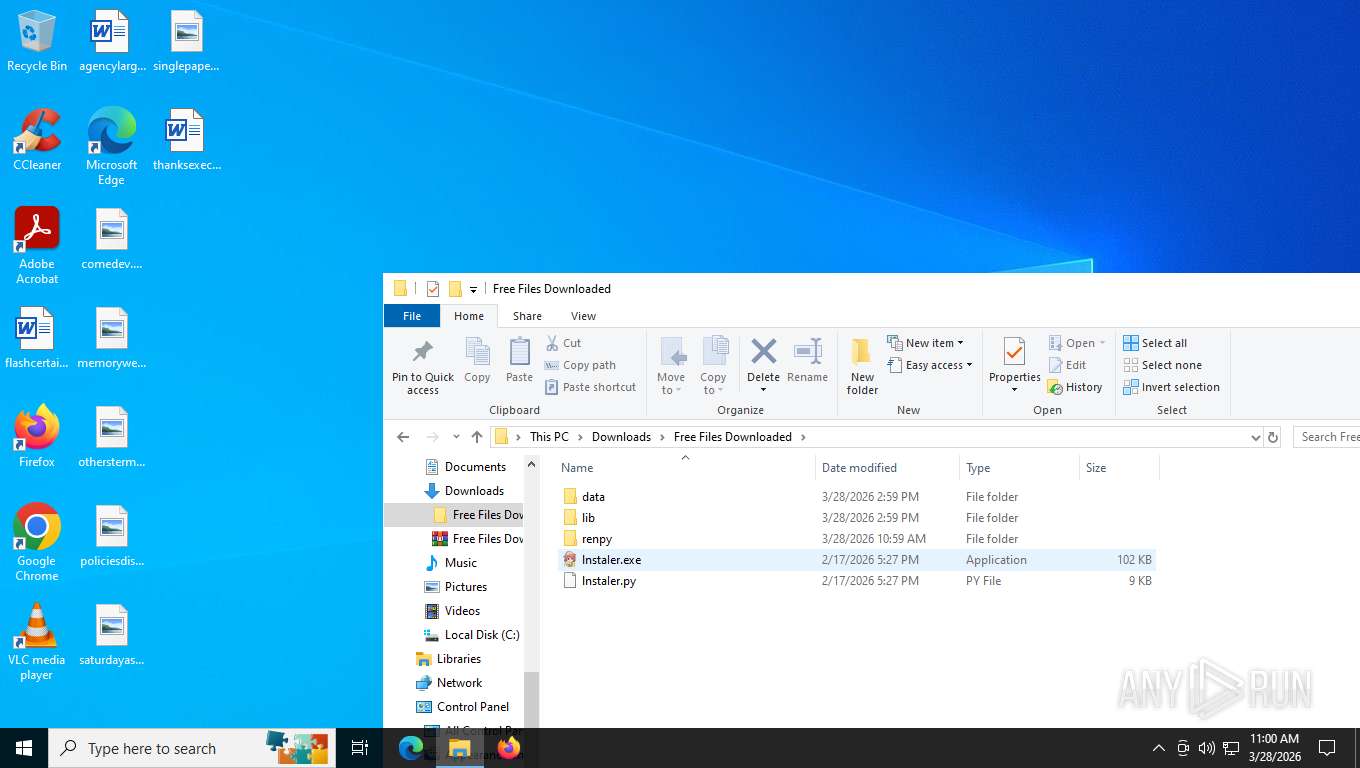
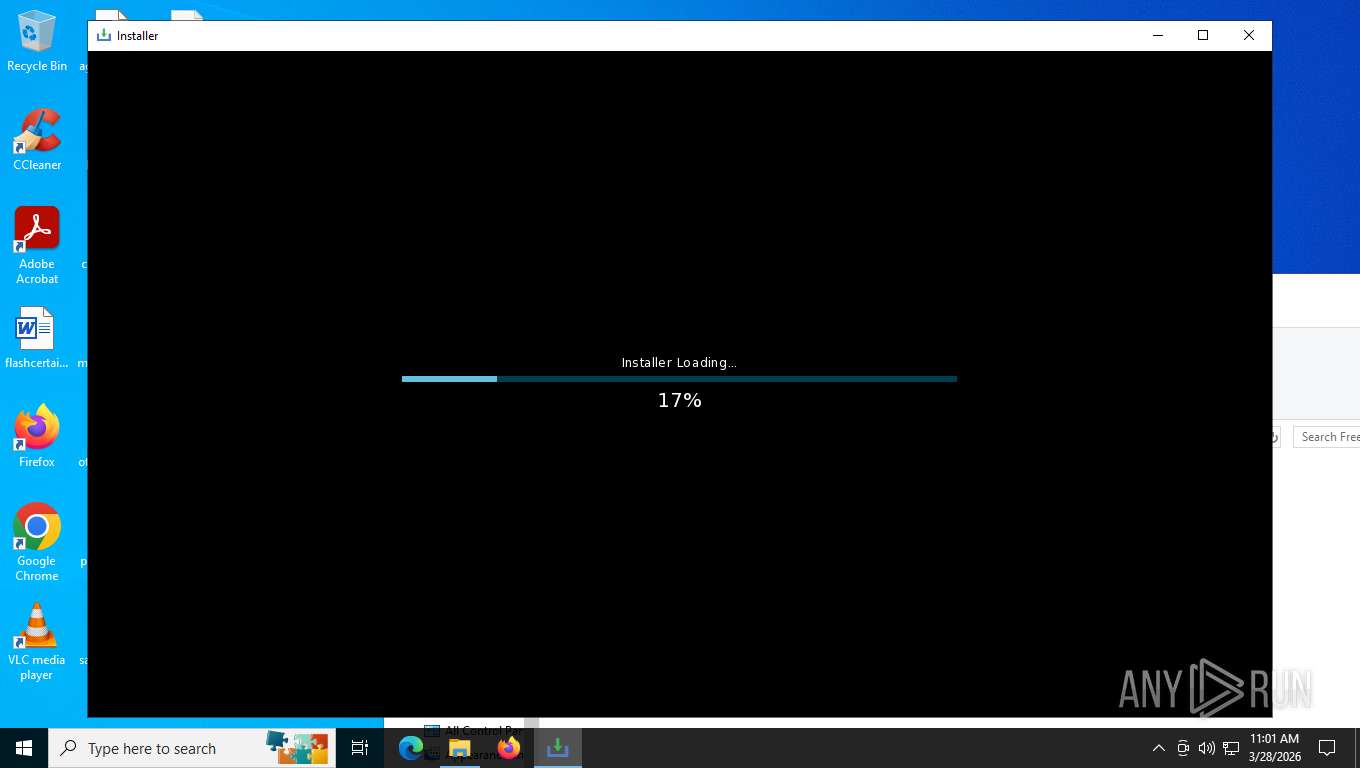
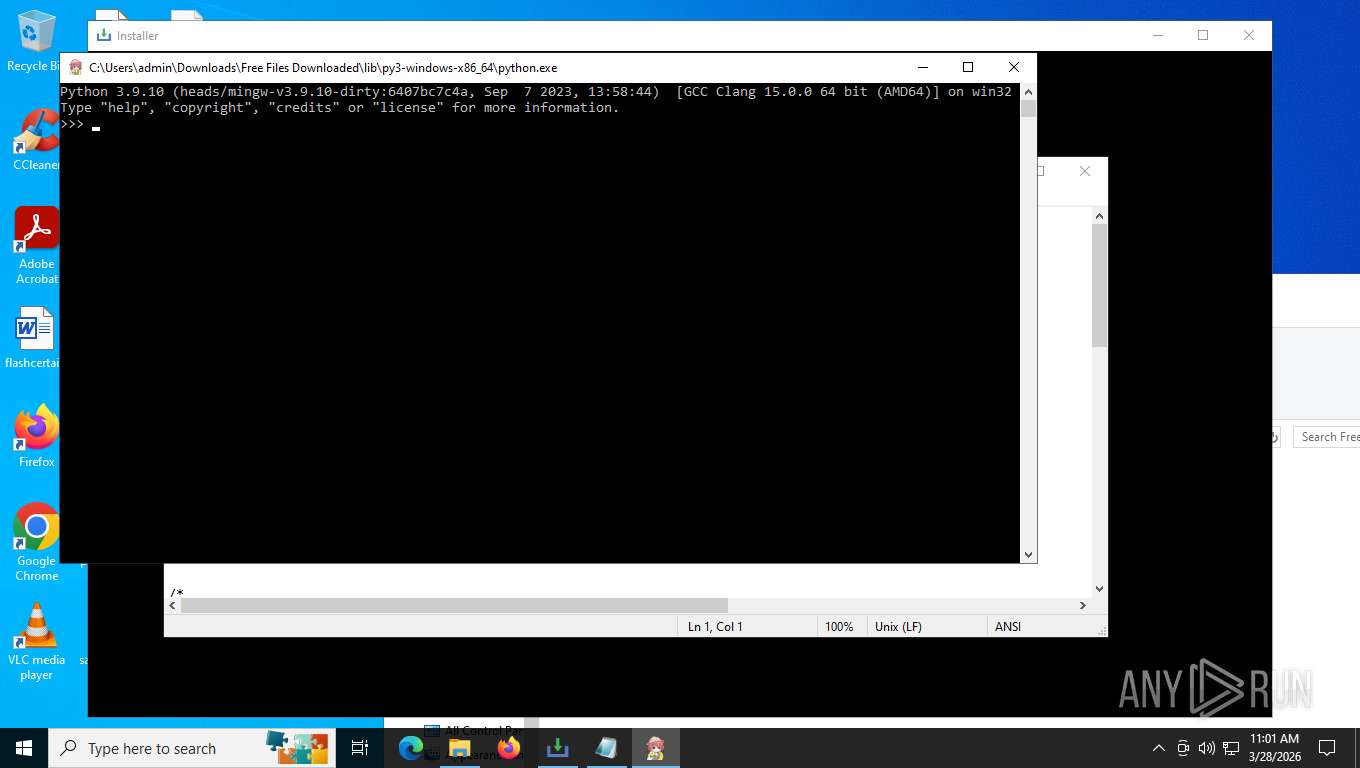
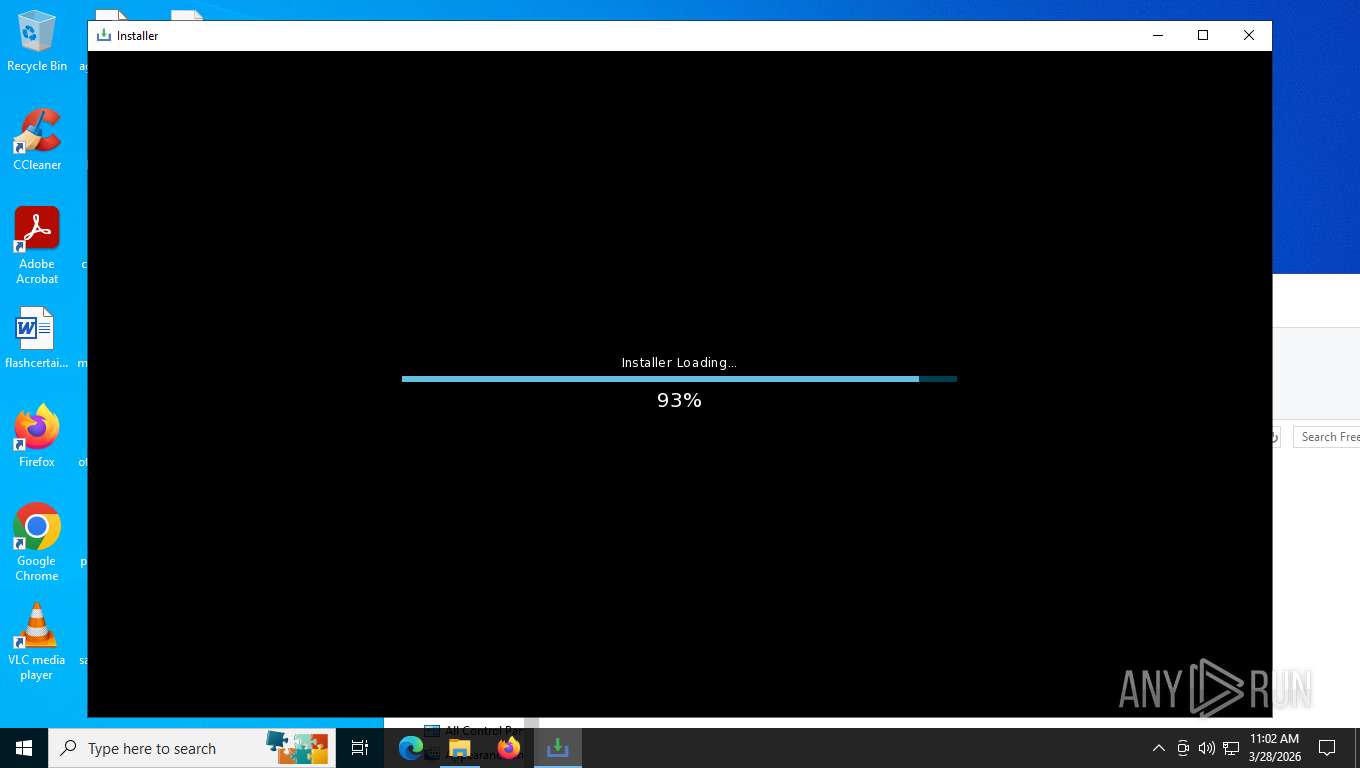
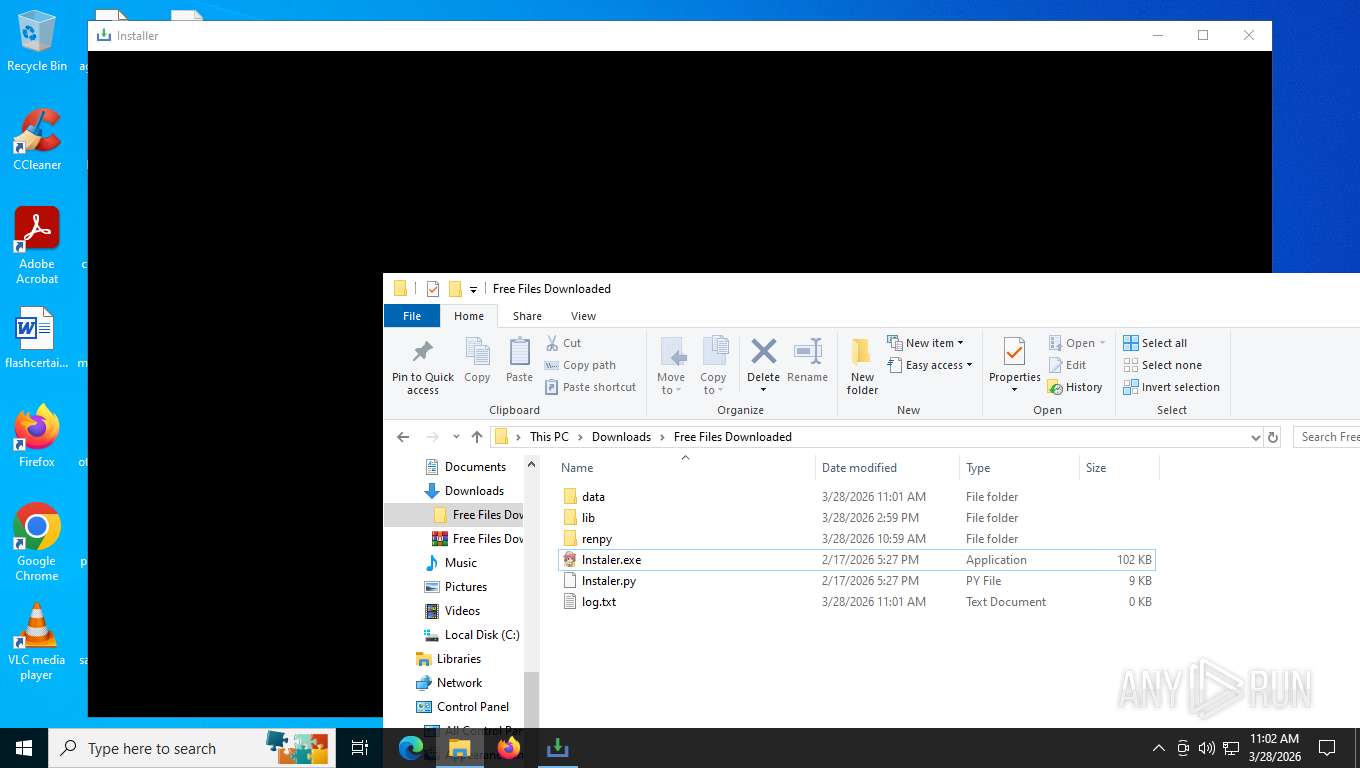
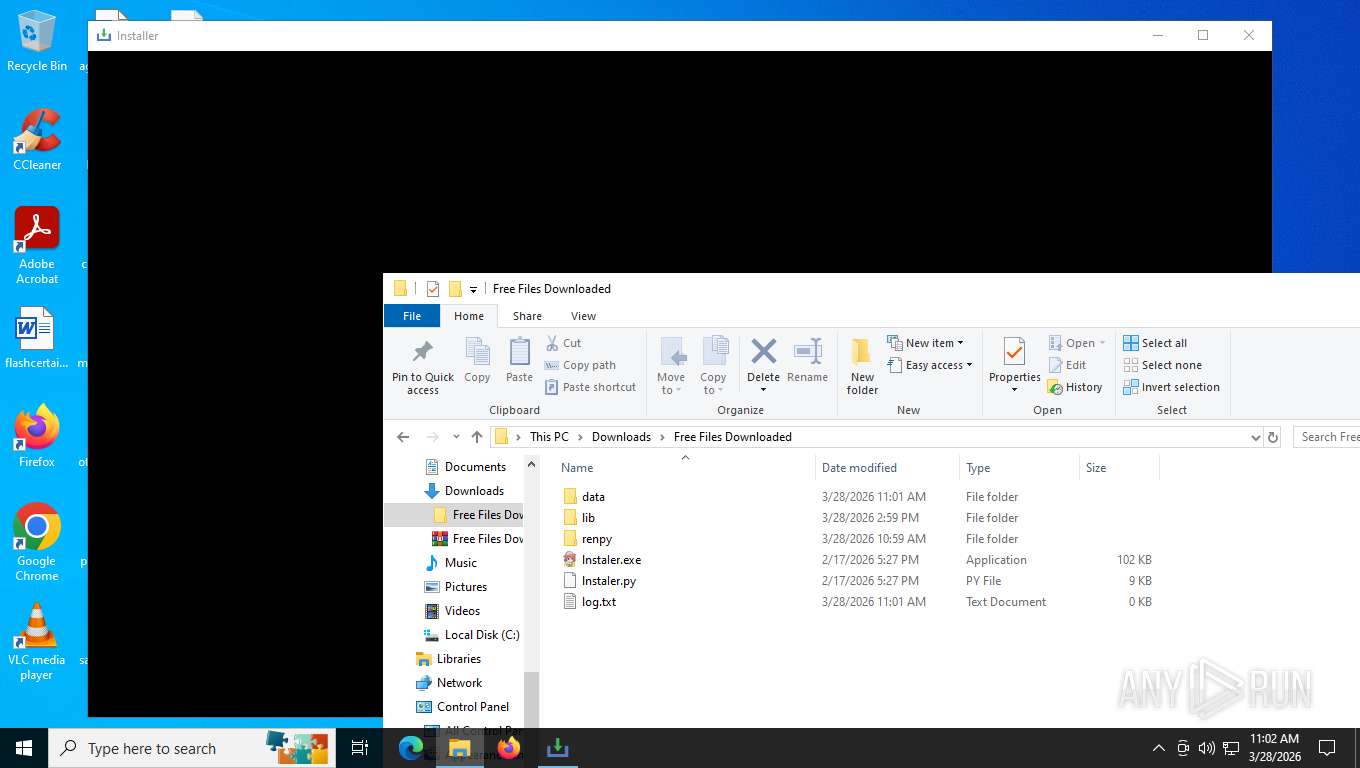
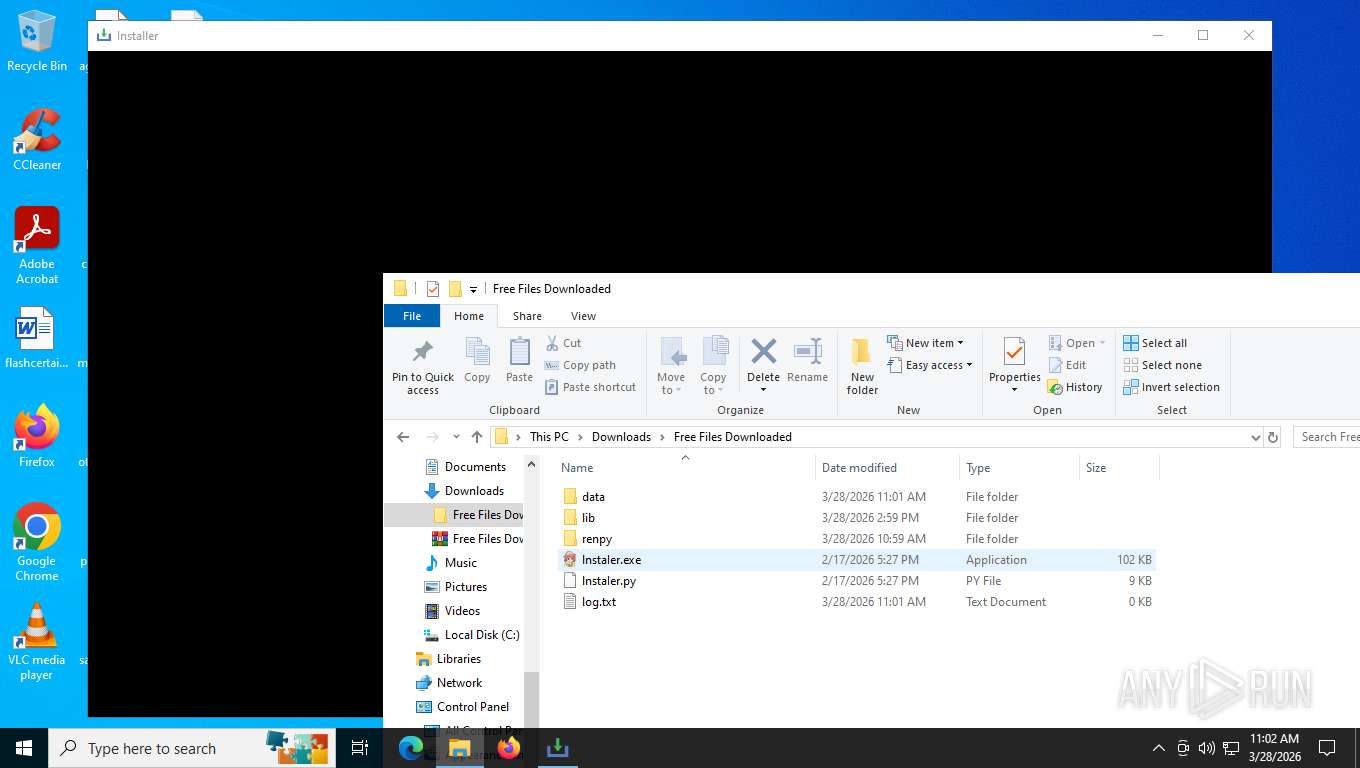
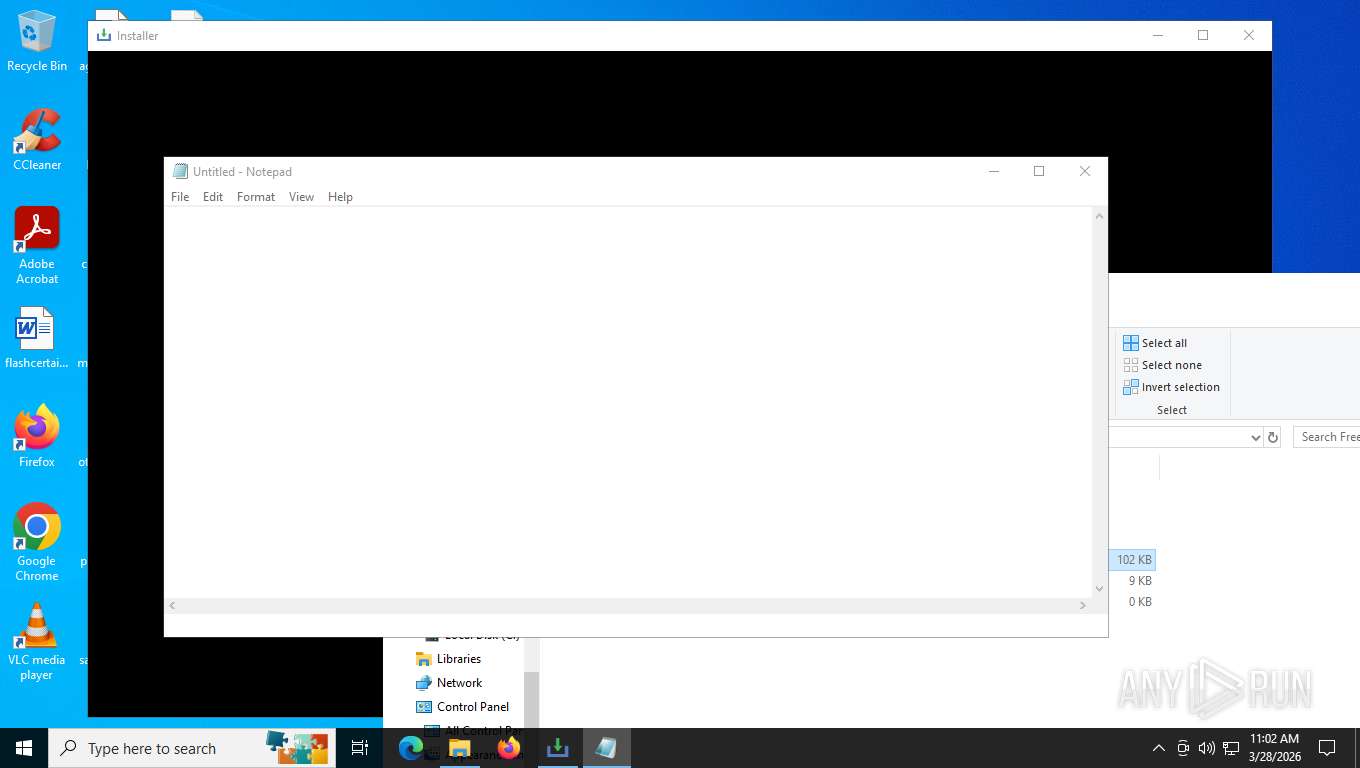
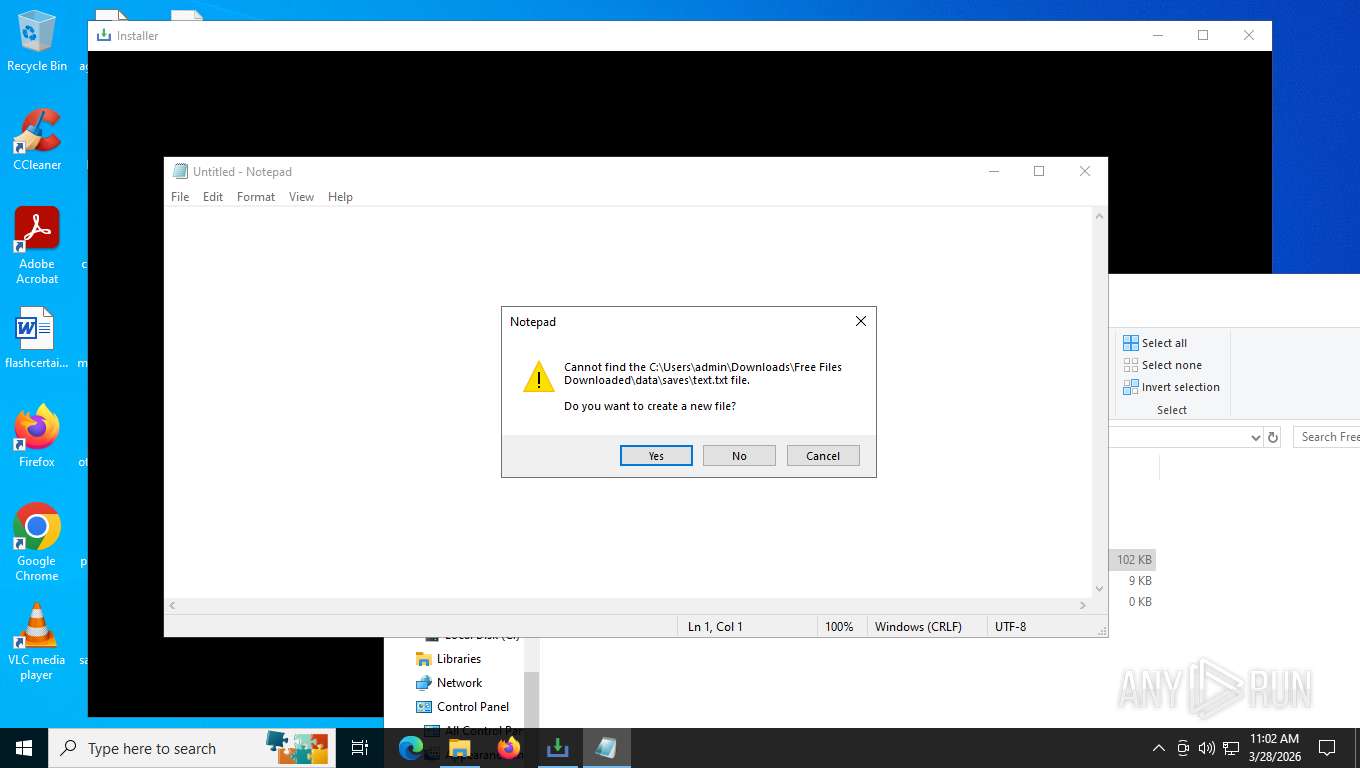
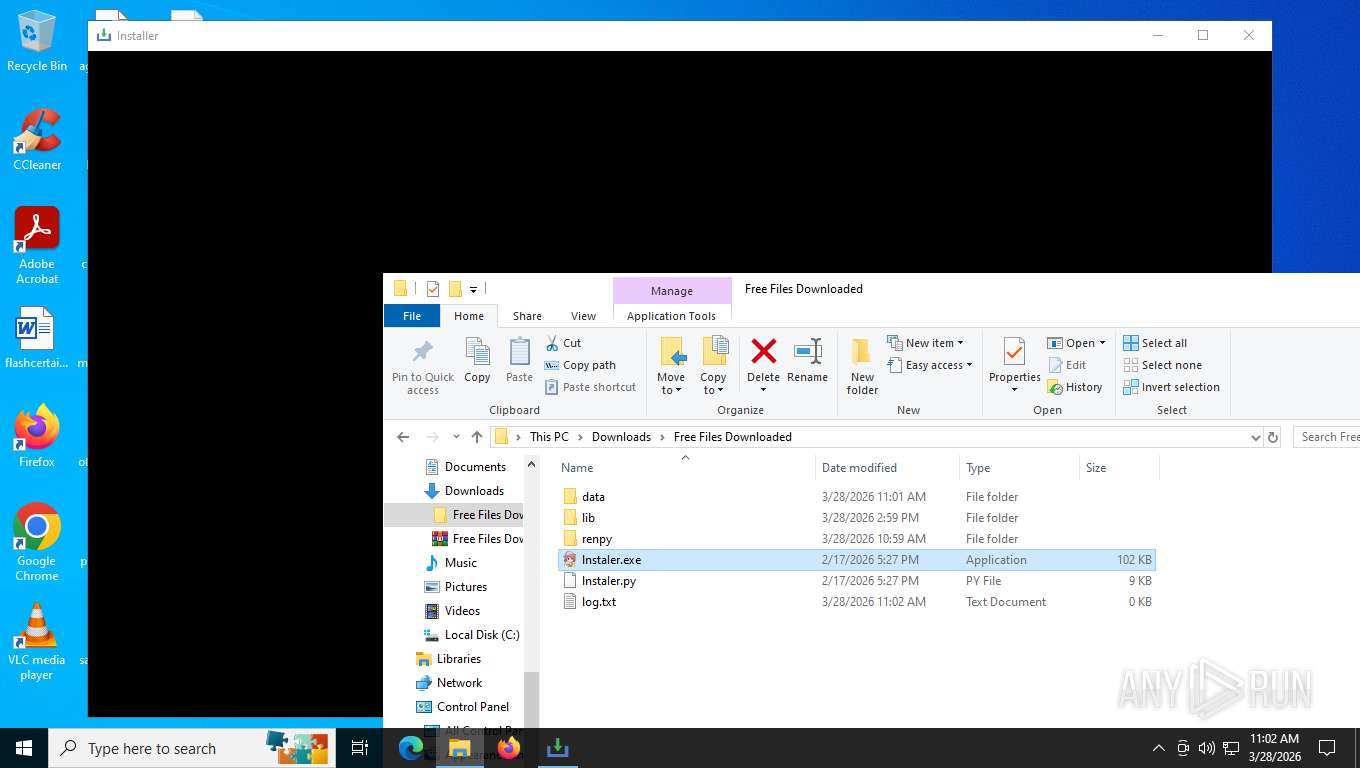
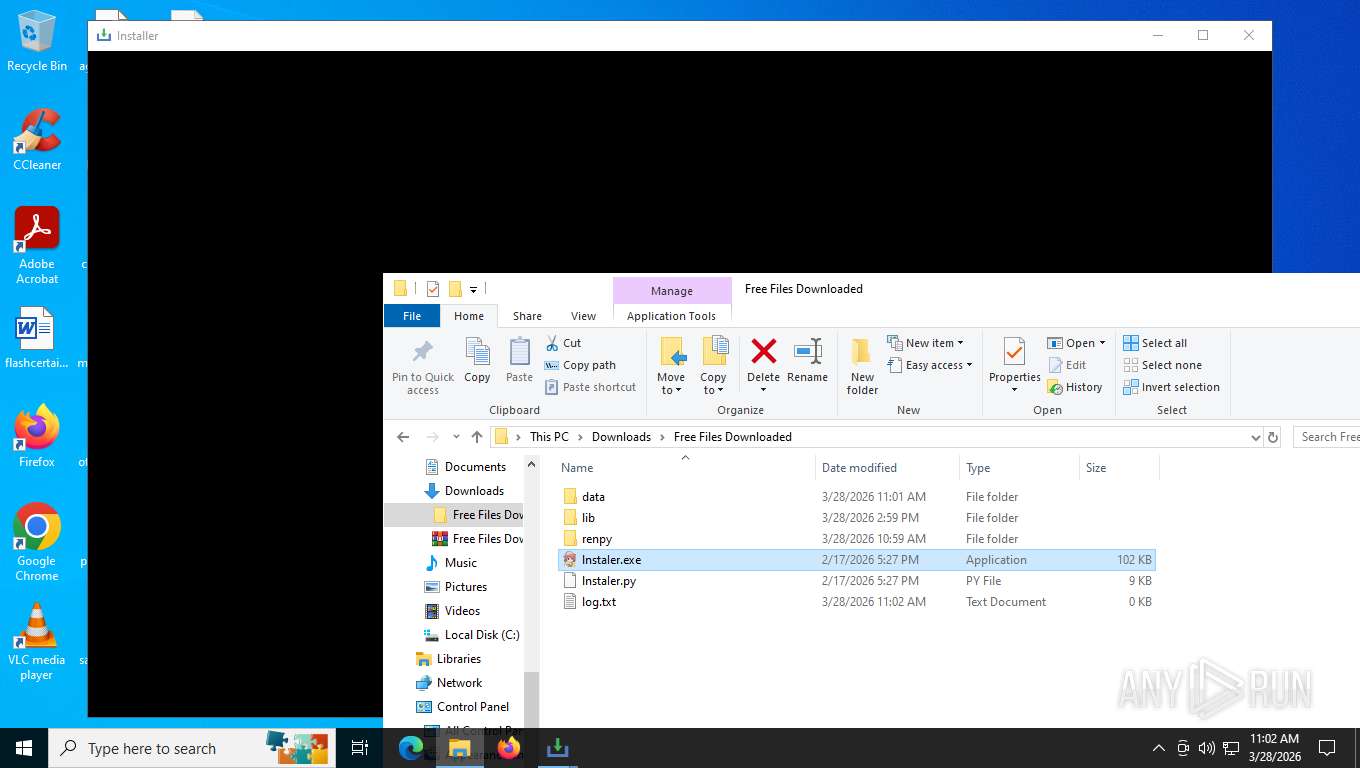
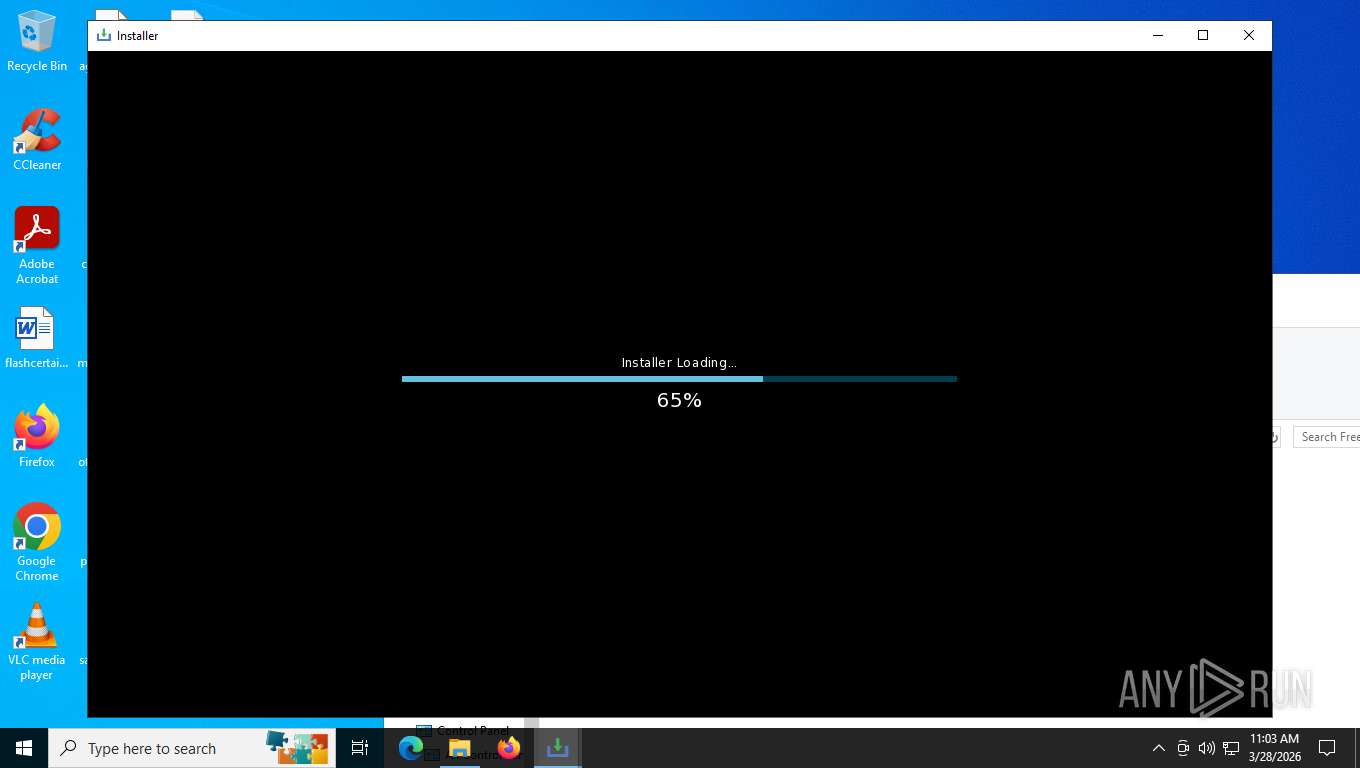
Manual execution by a user
- WinRAR.exe (PID: 3508)
- lnstaIer.exe (PID: 664)
- notepad.exe (PID: 8040)
- python.exe (PID: 5696)
- pythonw.exe (PID: 4592)
- cmd.exe (PID: 3076)
- lnstaIer.exe (PID: 6424)
- 8blgSOjBe.exe (PID: 420)
- notepad.exe (PID: 8748)
The sample compiled with english language support
- WinRAR.exe (PID: 3508)
- 8blgSOjBe.exe (PID: 4944)
- CircuitPilot.exe (PID: 8528)
Checks operating system version
- lnstaIer.exe (PID: 664)
- lnstaIer.exe (PID: 6424)
Reads the machine GUID from the registry
- lnstaIer.exe (PID: 664)
- 8blgSOjBe.exe (PID: 4944)
- python.exe (PID: 5696)
- pythonw.exe (PID: 4592)
- lnstaIer.exe (PID: 6424)
- 8blgSOjBe.exe (PID: 420)
Checks supported languages
- lnstaIer.exe (PID: 664)
- 8blgSOjBe.exe (PID: 4944)
- python.exe (PID: 5696)
- pythonw.exe (PID: 4592)
- lnstaIer.exe (PID: 6424)
- 8blgSOjBe.exe (PID: 420)
- CircuitPilot.exe (PID: 8528)
- CircuitPilot.exe (PID: 7944)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3508)
Create files in a temporary directory
- lnstaIer.exe (PID: 664)
- powershell.exe (PID: 9136)
- lnstaIer.exe (PID: 6424)
- powershell.exe (PID: 7960)
Creates files or folders in the user directory
- lnstaIer.exe (PID: 664)
- lnstaIer.exe (PID: 6424)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 5404)
Reads the computer name
- 8blgSOjBe.exe (PID: 4944)
- lnstaIer.exe (PID: 664)
- 8blgSOjBe.exe (PID: 420)
- lnstaIer.exe (PID: 6424)
- CircuitPilot.exe (PID: 8528)
There is functionality for taking screenshot (YARA)
- lnstaIer.exe (PID: 664)
Application based on Golang
- 8blgSOjBe.exe (PID: 4944)
Disables trace logs
- powershell.exe (PID: 9136)
- powershell.exe (PID: 7960)
Reads security settings of Internet Explorer
- powershell.exe (PID: 9136)
- notepad.exe (PID: 8040)
- powershell.exe (PID: 7960)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 9136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
87
Malicious processes
4
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5684 -prefsLen 39429 -prefMapHandle 5688 -prefMapSize 273045 -jsInitHandle 5692 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 2412 -initialChannelId {12292a74-cef8-4c05-936c-a547098ca143} -parentPid 8020 -crashReporter "\\.\pipe\gecko-crash-server-pipe.8020" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 11 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 420 | "C:\Users\admin\Downloads\Free Files Downloaded\data\.temp\8blgSOjBe.exe" | C:\Users\admin\Downloads\Free Files Downloaded\data\.temp\8blgSOjBe.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 664 | "C:\Users\admin\Downloads\Free Files Downloaded\lnstaIer.exe" | C:\Users\admin\Downloads\Free Files Downloaded\lnstaIer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | python.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | C:\WINDOWS\system32\cmd.exe /c "powershell -Command "Get-CimInstance Win32_ComputerSystem | Select-Object TotalPhysicalMemory"" | C:\Windows\System32\cmd.exe | — | lnstaIer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1656 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | 8blgSOjBe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1980 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | C:\WINDOWS\system32\cmd.exe /c "powershell -Command "Get-CimInstance Win32_ComputerSystem | Select-Object Model"" | C:\Windows\System32\cmd.exe | — | lnstaIer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2100 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -sandboxingKind 0 -prefsHandle 4016 -prefsLen 45425 -prefMapHandle 5008 -prefMapSize 273045 -ipcHandle 5056 -initialChannelId {ba545094-0091-4ad3-9822-e02570ac8414} -parentPid 8020 -crashReporter "\\.\pipe\gecko-crash-server-pipe.8020" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 6 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 136.0 Modules
| |||||||||||||||
Total events
64 568
Read events
64 532
Write events
23
Delete events
13
Modification events
| (PID) Process: | (8700) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Free Files Downloaded.zip | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
Executable files
17
Suspicious files
1 573
Text files
446
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 8020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:73A2E89AF4D3D52D0167E7B3805E20E5 | SHA256:AB2871B600E4E7A13DF4552B1172DA5EEA32C9BA8E3D2153F1987FE2B124CFC4 | |||
| 8020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 8020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
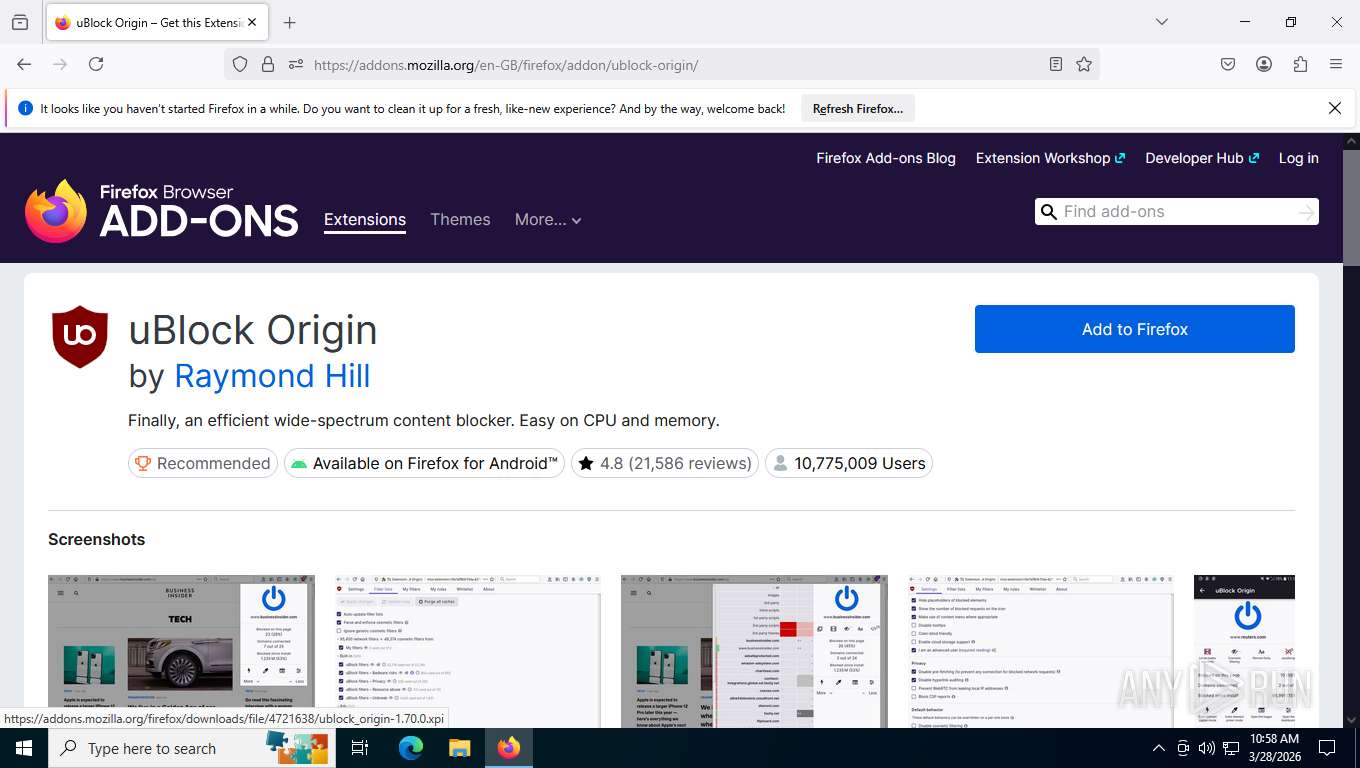
| 8020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\extensions\addon@example.com.xpi | compressed | |
MD5:1C6752C0C855D40F73C80D9EB2E29989 | SHA256:365BE5C9BE5E58BCB2E40006B80D777C59D7BFA22015CA9309A13B7ABBAF58F9 | |||
| 8020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:74762609A221B9A369385A317DF47CF9 | SHA256:CD7B42D64B7F42912CEFFD9CB71D4D792E0480BFB5EF87F9C6A5F862571F2093 | |||
| 8020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:74762609A221B9A369385A317DF47CF9 | SHA256:CD7B42D64B7F42912CEFFD9CB71D4D792E0480BFB5EF87F9C6A5F862571F2093 | |||
| 8020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 8020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 8020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
399
TCP/UDP connections
161
DNS requests
191
Threats
41
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8020 | firefox.exe | GET | 200 | 151.101.193.91:443 | https://firefox.settings.services.mozilla.com/v1/buckets/monitor/collections/changes/changeset?collection=url-parser-default-unknown-schemes-interventions&bucket=main&_expected=0 | US | text | 274 b | whitelisted |
8020 | firefox.exe | GET | 200 | 151.101.193.91:443 | https://firefox.settings.services.mozilla.com/v1/buckets/main/collections/url-parser-default-unknown-schemes-interventions/changeset?_expected=1743513175300&_since=%221726769128879%22 | US | text | 1.76 Kb | whitelisted |
8020 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
8020 | firefox.exe | GET | 404 | 104.26.14.76:443 | https://datanodes.to/download | US | html | 17.8 Kb | unknown |
8020 | firefox.exe | GET | 200 | 151.101.193.91:443 | https://firefox.settings.services.mozilla.com/v1/ | US | text | 1.20 Kb | whitelisted |
8020 | firefox.exe | GET | 302 | 104.26.14.76:443 | https://datanodes.to/cdn-cgi/challenge-platform/scripts/jsd/main.js | US | — | — | unknown |
8020 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
8020 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2026-05-07-11-22-02.chain | US | text | 5.18 Kb | whitelisted |
8020 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2026-03-08-09-54-23.chain | US | text | 5.18 Kb | whitelisted |
8020 | firefox.exe | POST | 200 | 151.101.129.91:443 | https://spocs.getpocket.com/spocs | US | text | 1.16 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4044 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3536 | slui.exe | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8020 | firefox.exe | 151.101.193.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
8020 | firefox.exe | 104.26.14.76:443 | datanodes.to | CLOUDFLARENET | US | whitelisted |
8020 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
8020 | firefox.exe | 151.101.129.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
8020 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
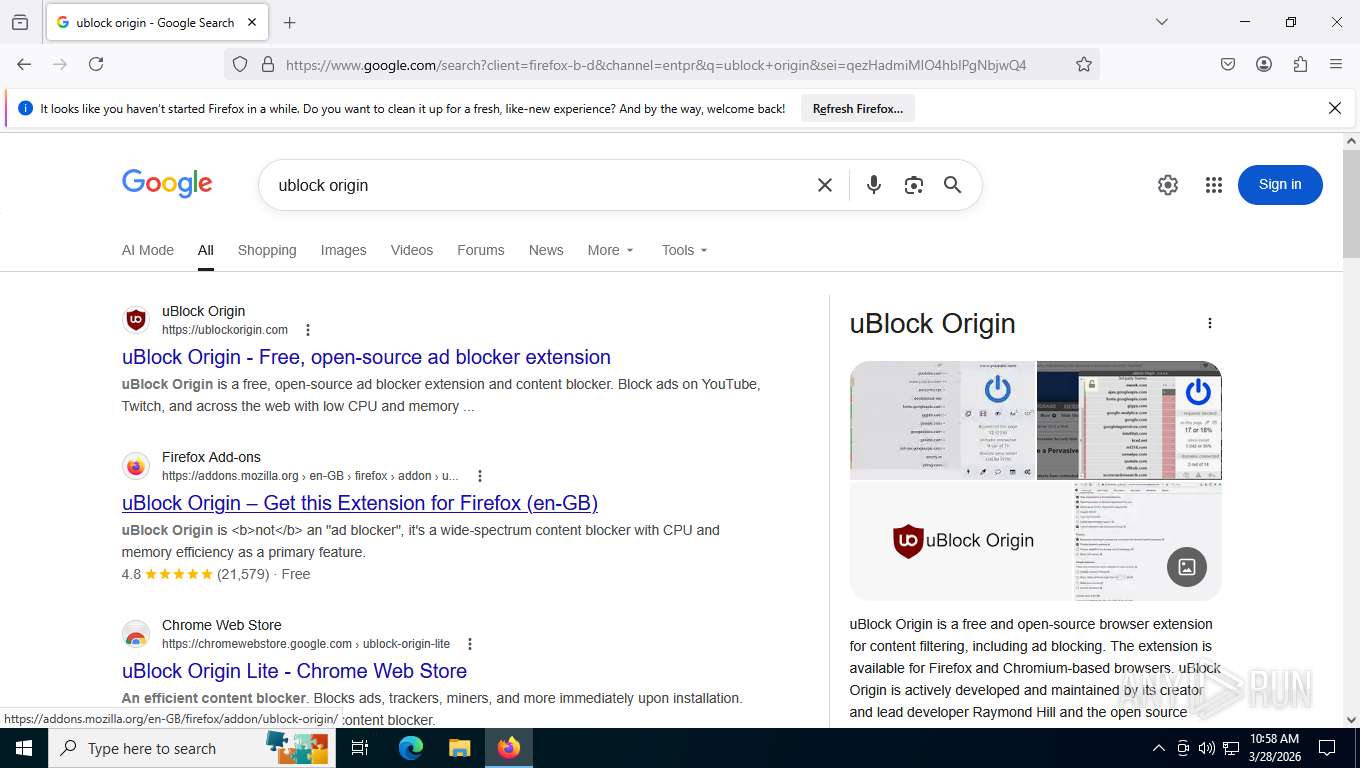
google.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
mozilla.map.fastly.net |
| whitelisted |
datanodes.to |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2232 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2232 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2232 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5276 | MoUsoCoreWorker.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2232 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
2232 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
2232 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
2232 | svchost.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
8020 | firefox.exe | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
2232 | svchost.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |