| File name: | WP#9996.html |
| Full analysis: | https://app.any.run/tasks/7857930b-1049-4ea5-b383-02f38f6eef61 |
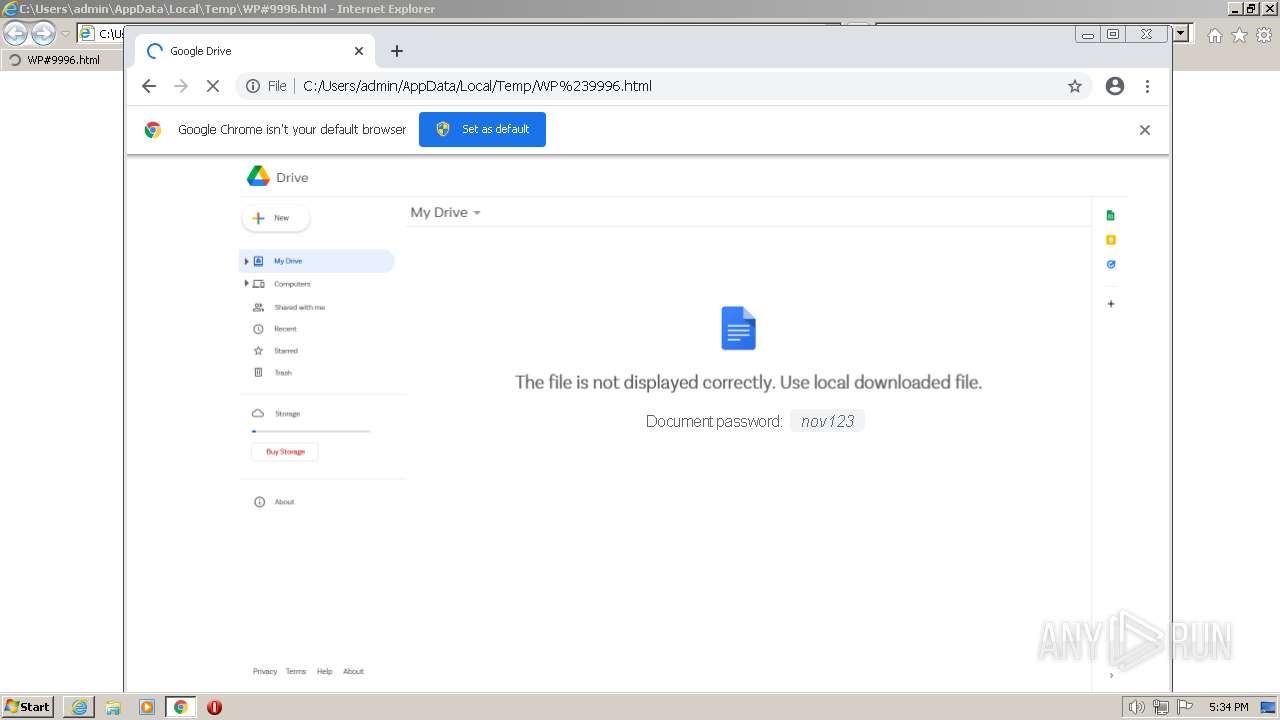
| Verdict: | Malicious activity |
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
| Analysis date: | December 05, 2022, 17:33:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | 714D715ABAEA4441DA9E17E8533A964F |
| SHA1: | 0050C3FA41D6CA74F4F899DF924AE636809D1429 |
| SHA256: | 6BDD7B55DAB764135395363D2FB4C9F1691005FC4D366A9676E68950573A2041 |
| SSDEEP: | 12288:swiSePqm2NQpC1nKAuQi/+EXbdMsJ2KP8SBkAE0txSy1Q9gA9r3Umiafu273a9bo:mJ2NiAKVd5BiexTegUULafPSbEDbWet |
MALICIOUS
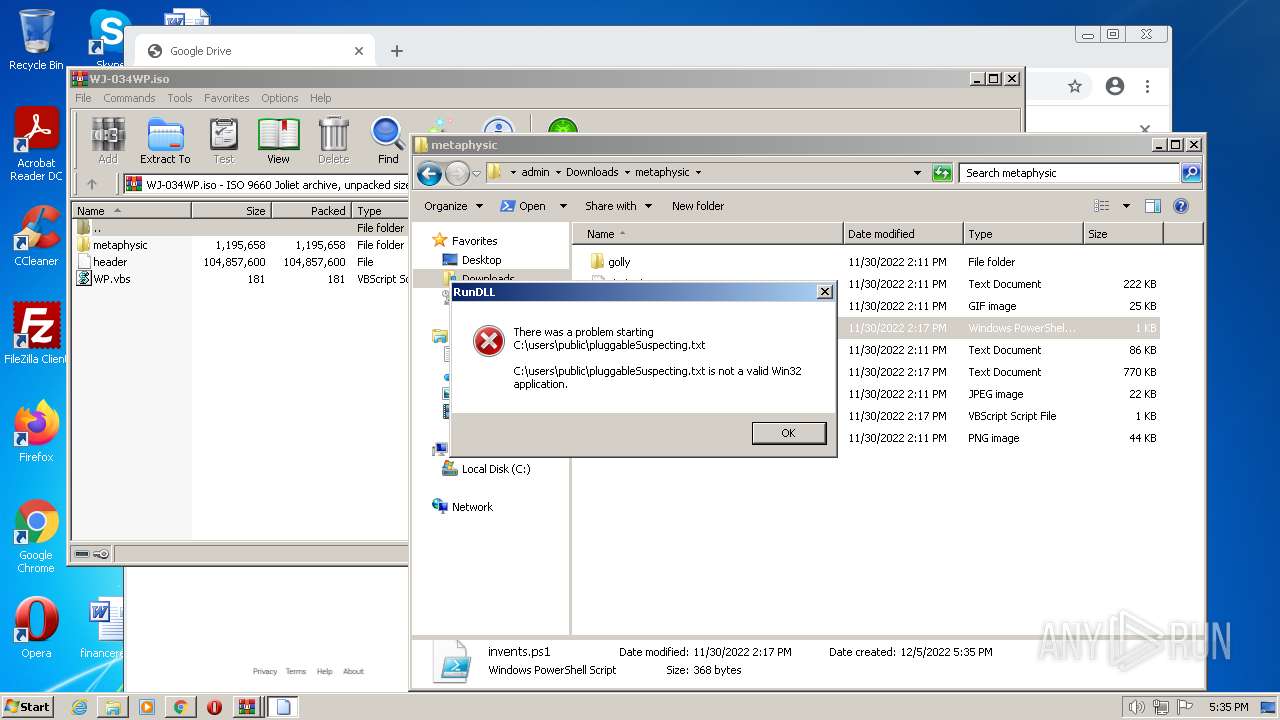
Loads dropped or rewritten executable
- rundll32.exe (PID: 3400)
- rundll32.exe (PID: 3652)
QBOT detected by memory dumps
- wermgr.exe (PID: 2640)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 2896)
- powershell.exe (PID: 692)
- powershell.exe (PID: 2940)
INFO
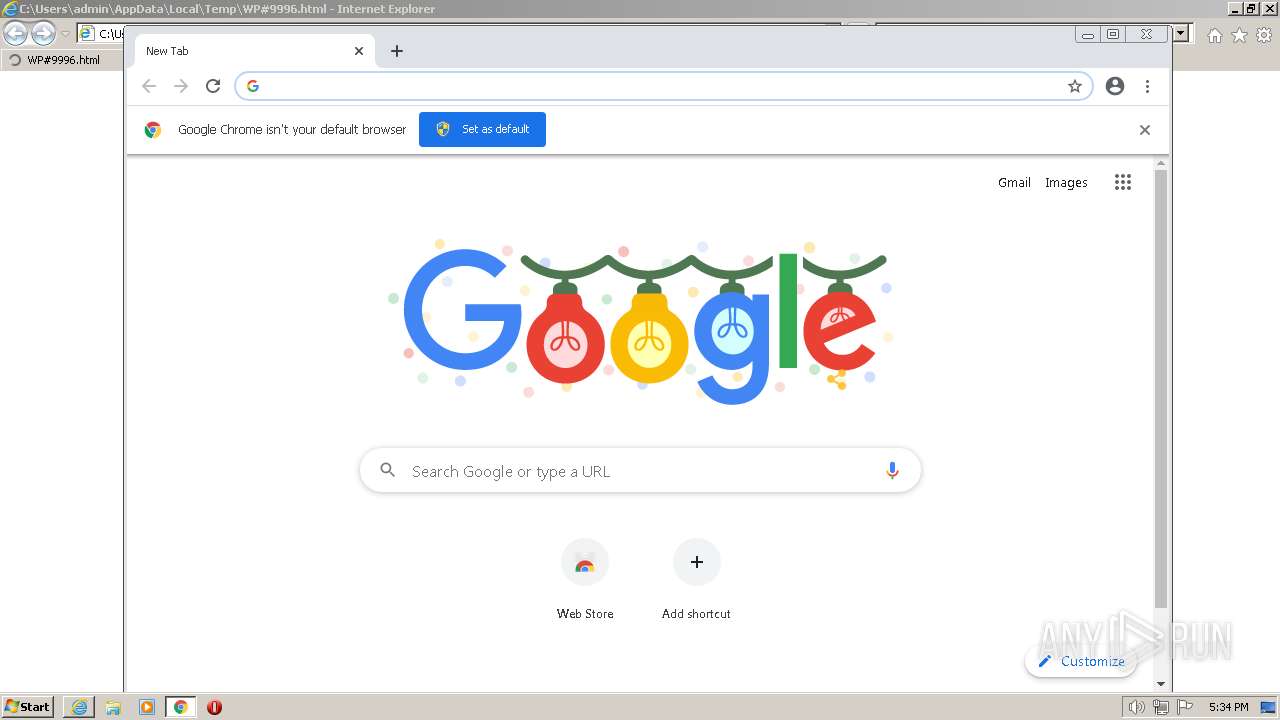
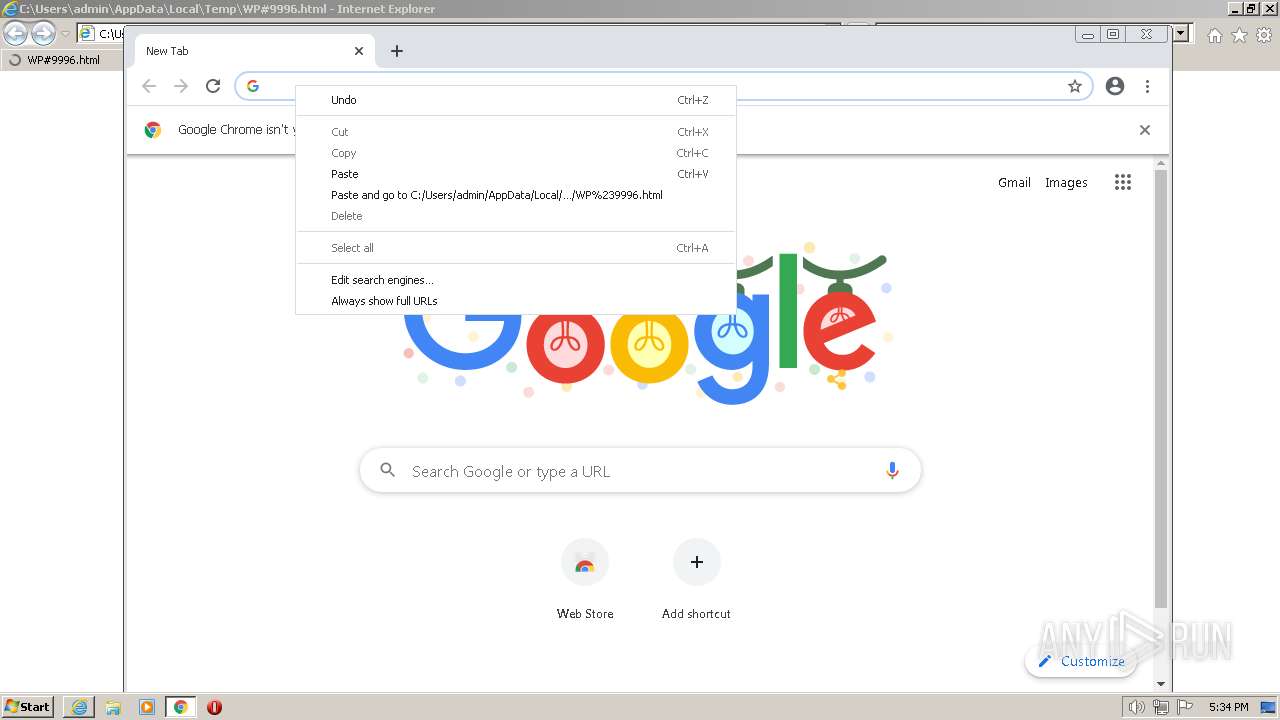
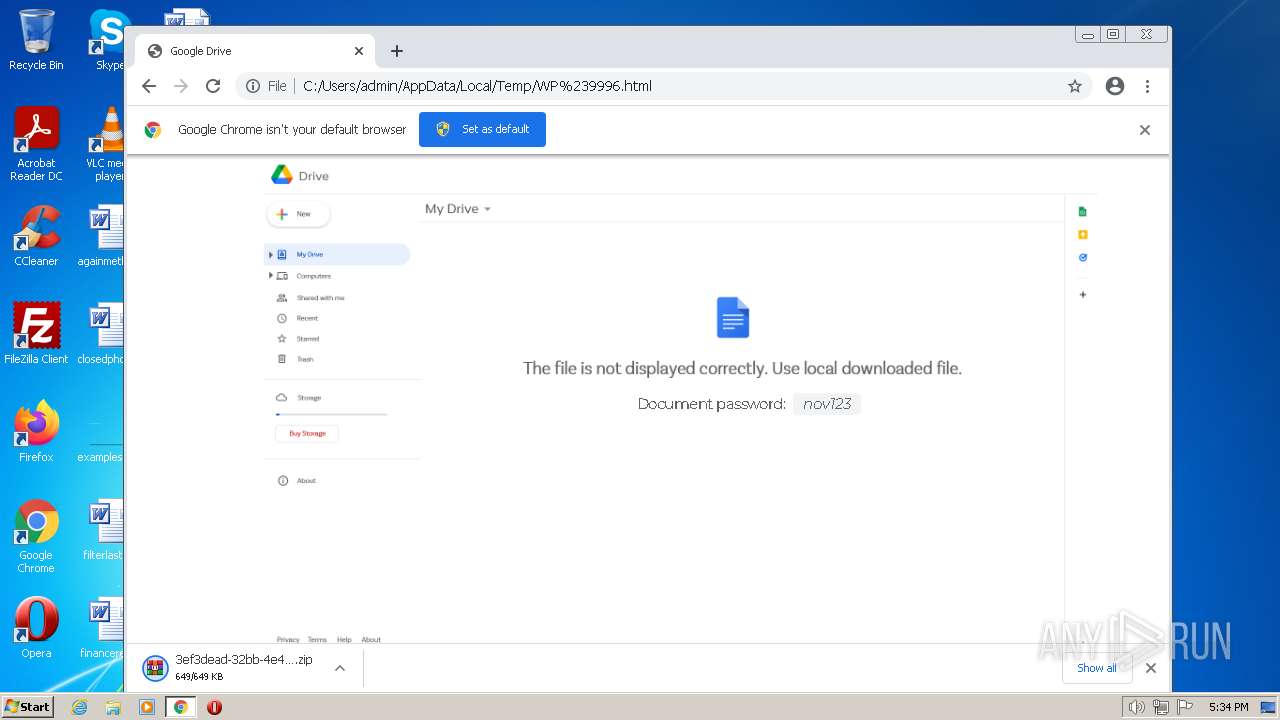
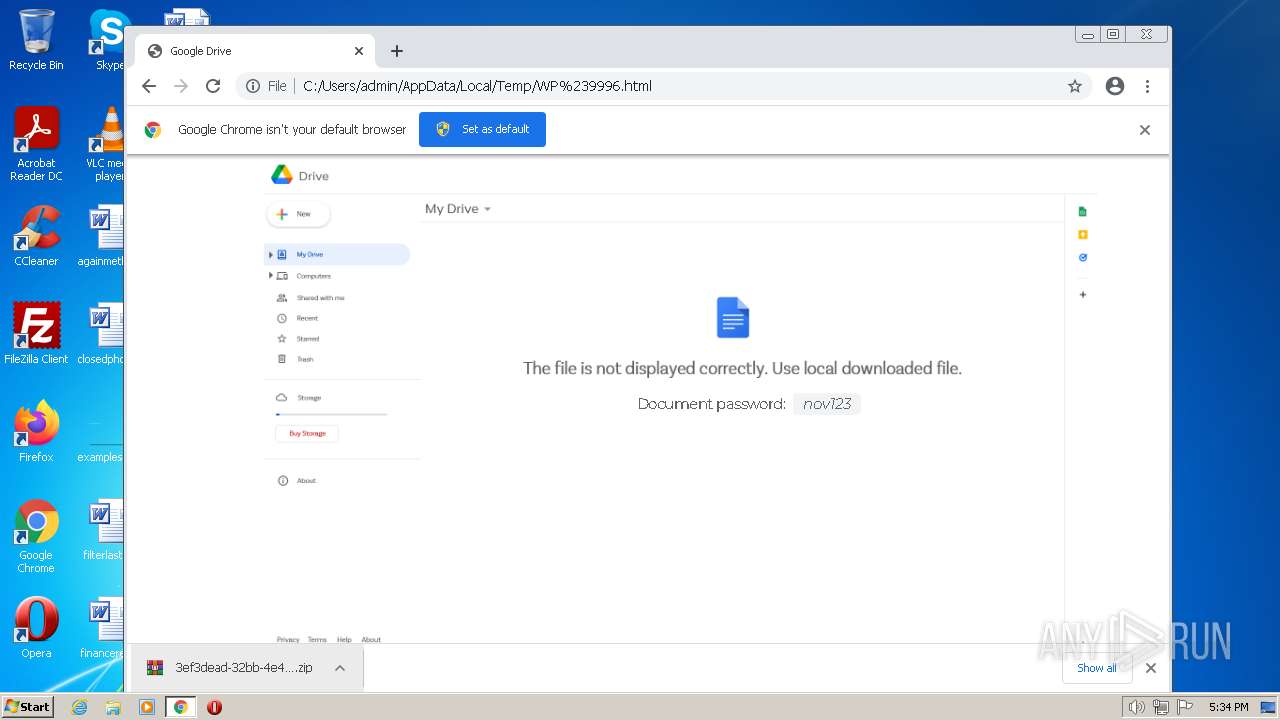
Application launched itself
- iexplore.exe (PID: 1580)
- chrome.exe (PID: 2904)
Manual execution by a user
- explorer.exe (PID: 1752)
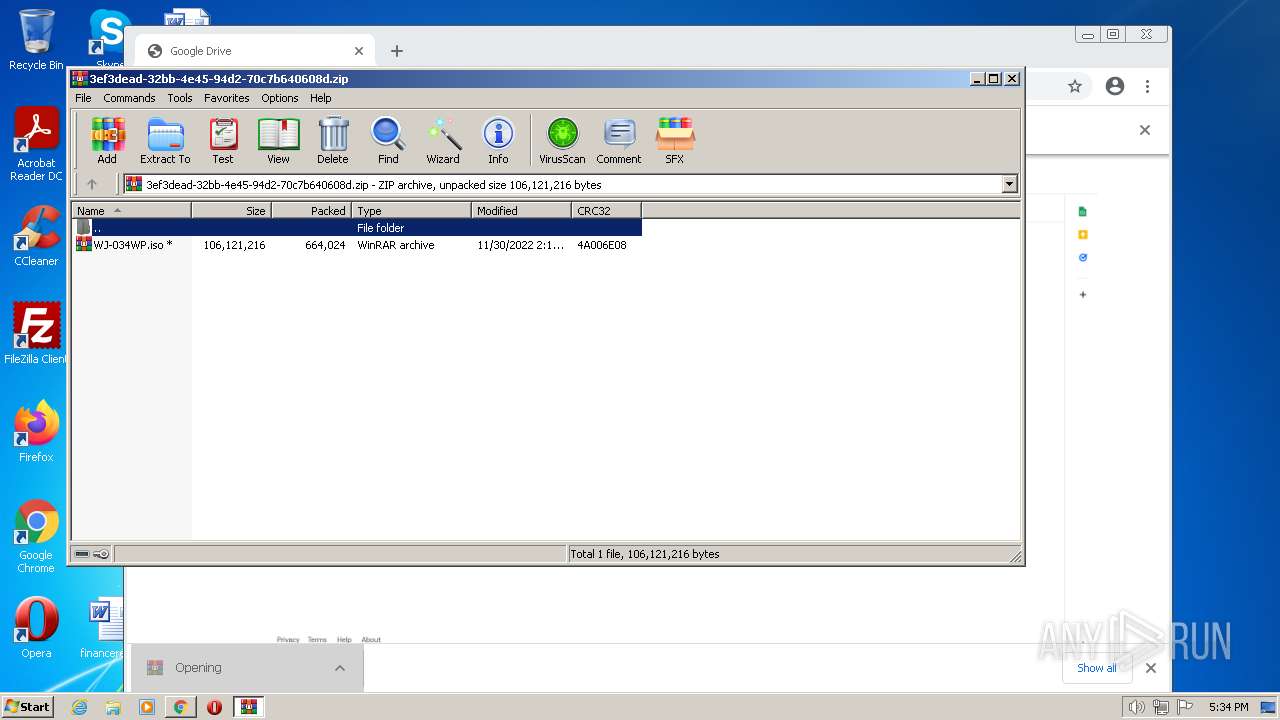
- WinRAR.exe (PID: 860)
- WScript.exe (PID: 3948)
- chrome.exe (PID: 2904)
- WScript.exe (PID: 1528)
- powershell.exe (PID: 692)
- WScript.exe (PID: 760)
Reads security settings of Internet Explorer
- powershell.exe (PID: 2896)
- powershell.exe (PID: 2940)
- powershell.exe (PID: 692)
- powershell.exe (PID: 2096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Qbot
(PID) Process(2640) wermgr.exe
Botnetobama224
Campaign1669794048
Version404.46
C2 (137)75.161.233.194:995
1.216.82.134:55809
1.1.174.104:47253
187.1.1.173:4734
1.187.1.1:22474
164.195.80.1:428
139.138.8.174:257
153.132.82.1:47873
185.135.120.81:443
1.24.228.132:57352
1.1.87.223:21694
187.0.1.178:39363
1.187.0.1:6208
59.8.174.1:333
81.208.1.187:257
99.125.235.8:44545
173.239.94.212:443
1.98.145.23:17153
1.1.24.64:29243
174.1.1.109:45557
8.174.0.1:18632
104.1.187.1:268
173.82.3.225:257
11.242.219.1:47872
92.149.205.238:2222
1.183.82.100:28168
1.1.176.142:53055
187.1.1.92:6344
3.227.1.1:17783
159.8.174.1:347
12.198.125.100:257
121.161.102.1:47873
124.122.55.68:443
1.12.172.173:20995
1.1.85.231:26929
174.0.1.94:16193
1.187.1.1:45189
230.3.227.0:469
255.57.8.174:257
89.95.158.8:44545
156.217.158.177:995
1.88.126.94:1219
1.1.87.57:3543
187.1.1.102:40787
1.187.0.1:31098
223.3.227.1:472
245.102.8.174:257
172.173.82.1:53505
78.69.251.252:2222
1.76.80.180:39427
1.1.75.143:60565
187.1.1.109:2991
8.174.1.1:56737
6.1.187.1:330
243.113.195.80:257
98.154.19.1:47873
47.41.154.250:443
1.49.175.72:14337
1.1.81.229:30047
174.1.1.92:48598
8.174.1.1:21340
93.1.187.1:364
6.34.1.187:257
35.26.14.3:58113
136.232.184.134:995
1.188.54.99:62211
0.1.93.24:49294
20.1.1.75:21738
1.187.1.1:18207
183.1.187.1:336
179.151.8.174:257
155.91.69.1:47873
76.100.159.250:443
1.24.64.114:15117
1.1.46.246:62872
227.0.1.70:29544
3.227.1.1:50434
208.3.227.0:306
249.161.1.187:257
66.199.12.1:47873
216.196.245.102:2083
1.182.66.197:8961
1.1.142.161:7144
174.1.1.76:32704
1.187.1.1:23759
174.8.174.1:430
209.5.1.187:257
172.173.82.0:5377
199.83.165.233:443
1.74.66.134:6145
1.1.77.86:25324
187.1.1.90:26646
8.174.1.1:18423
63.195.83.1:364
249.139.1.187:257
176.154.83.3:58113
81.198.136.151:995
1.80.0.74:42241
1.1.71.247:2623
227.1.1.174:14994
1.187.1.1:17797
35.1.187.1:306
204.71.3.227:257
64.114.59.239:4609
47.34.30.133:443
1.12.172.173:21187
1.1.75.158:4051
187.1.1.216:50421
8.30.1.1:46500
228.1.187.1:449
207.221.1.187:257
191.164.70.1:47873
197.92.135.188:443
1.172.117.139:36355
1.1.76.20:10797
187.1.1.24:16498
8.30.1.1:18724
11.1.187.1:314
115.126.3.227:257
155.10.79.1:47873
92.98.72.220:2222
1.84.113.121:26369
1.1.2.50:12141
187.0.1.12:44205
3.222.1.1:27348
255.3.227.0:354
155.235.1.187:257
106.70.62.8:44545
108.44.207.232:443
1.24.206.27:9985
1.1.130.43:25447
227.1.1.50:17612
3.225.1.1:18222
171.1.187.0:364
6.34.3.227:257
142.218.202.1:47873
166.62.145.54:443
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
90
Monitored processes
43
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,689834893751507277,16686241370786346278,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2976 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6debd988,0x6debd998,0x6debd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1004,689834893751507277,16686241370786346278,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1276 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
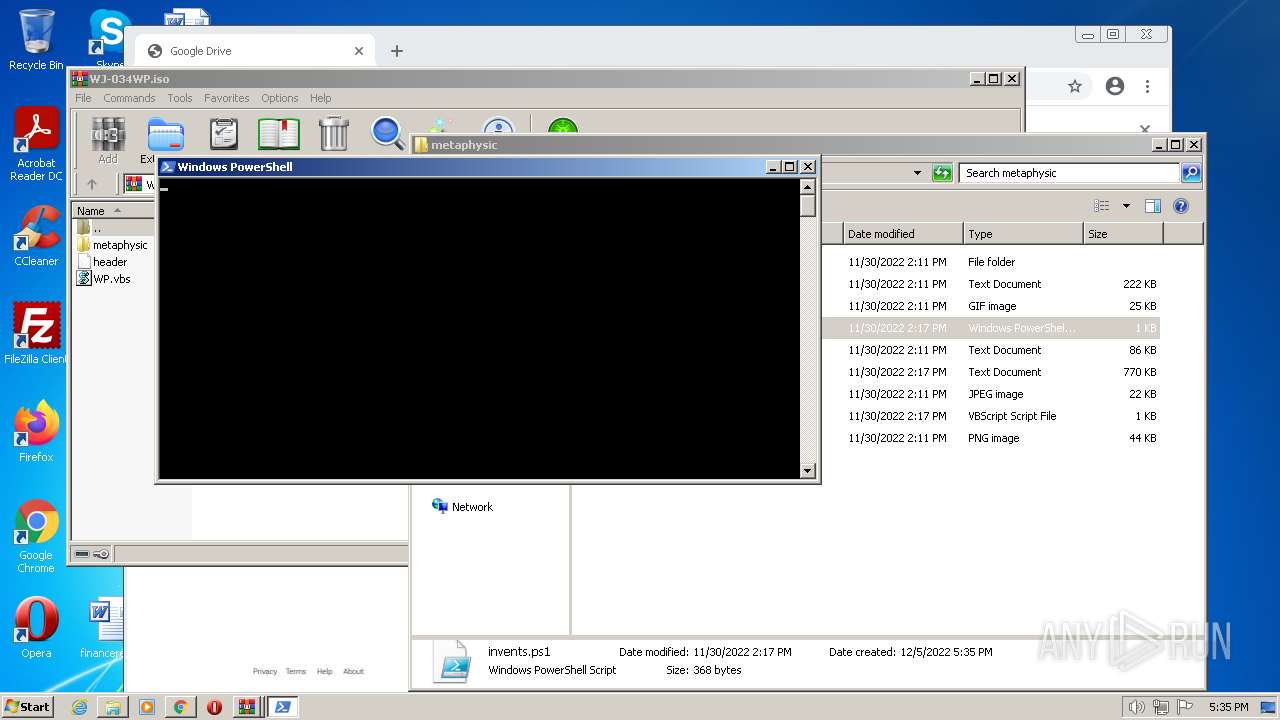
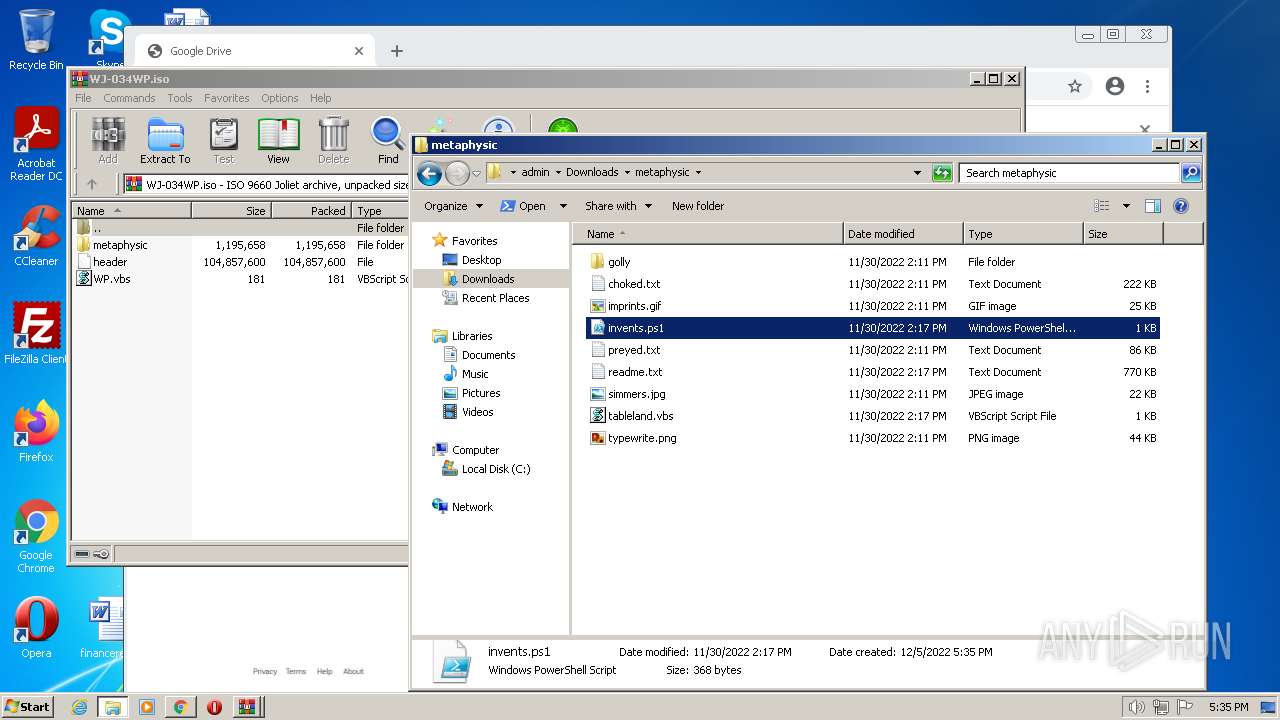
| 692 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Downloads\metaphysic\invents.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
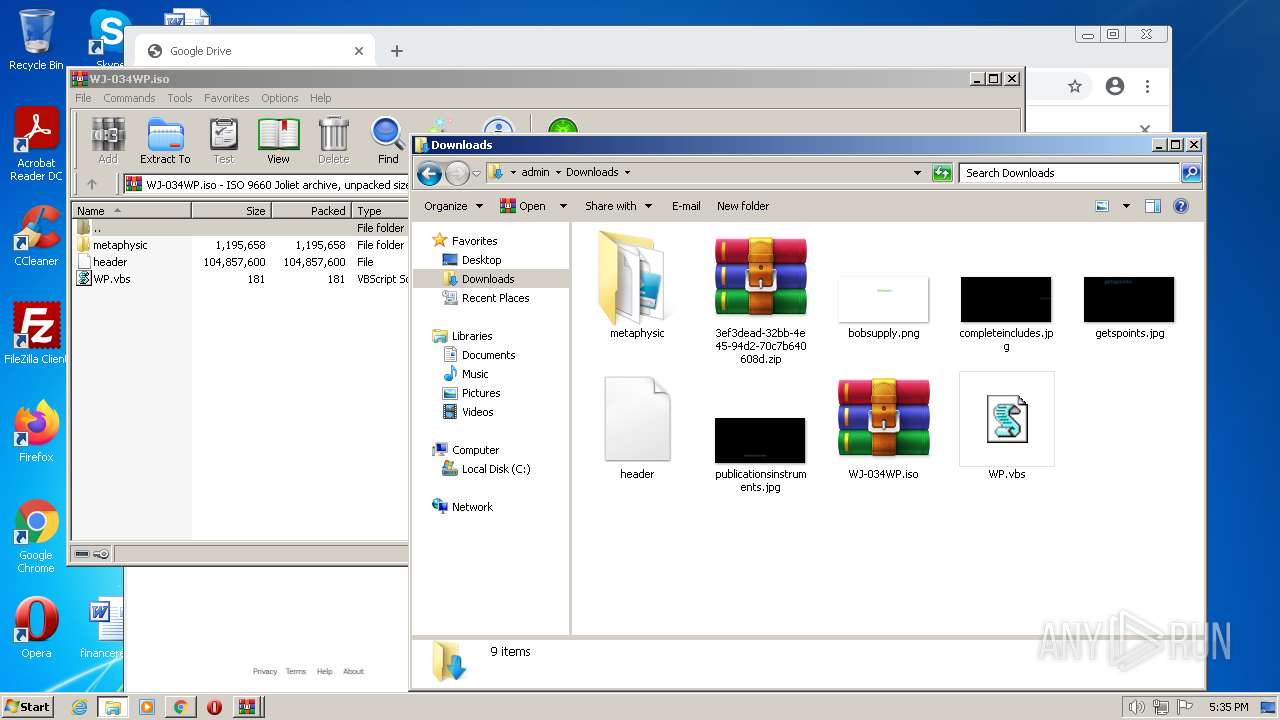
| 760 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\metaphysic\tableland.vbs" | C:\Windows\System32\WScript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
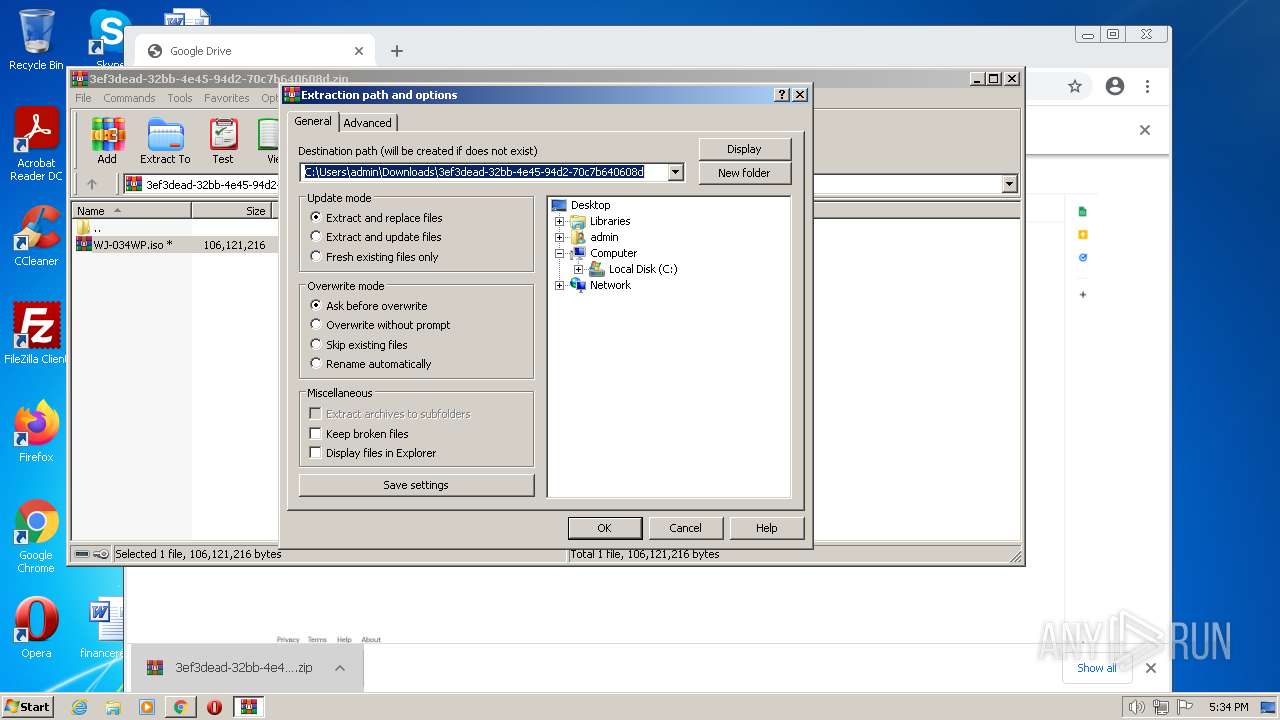
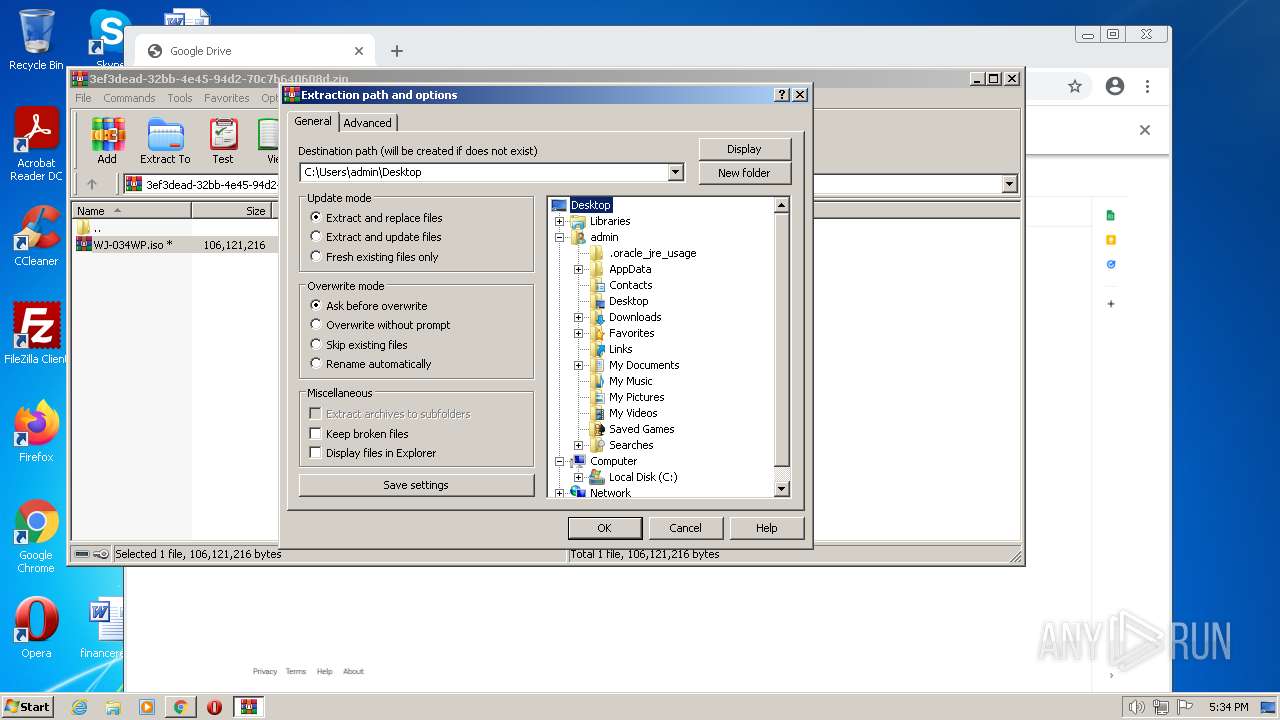
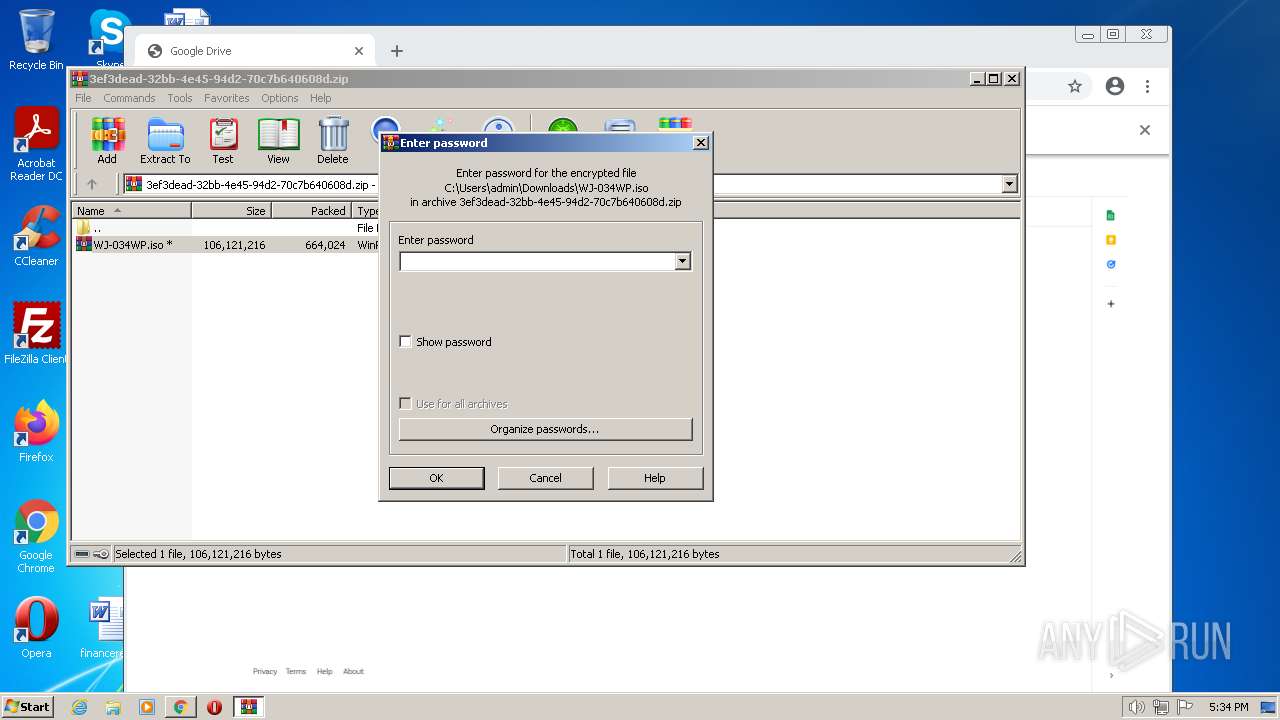
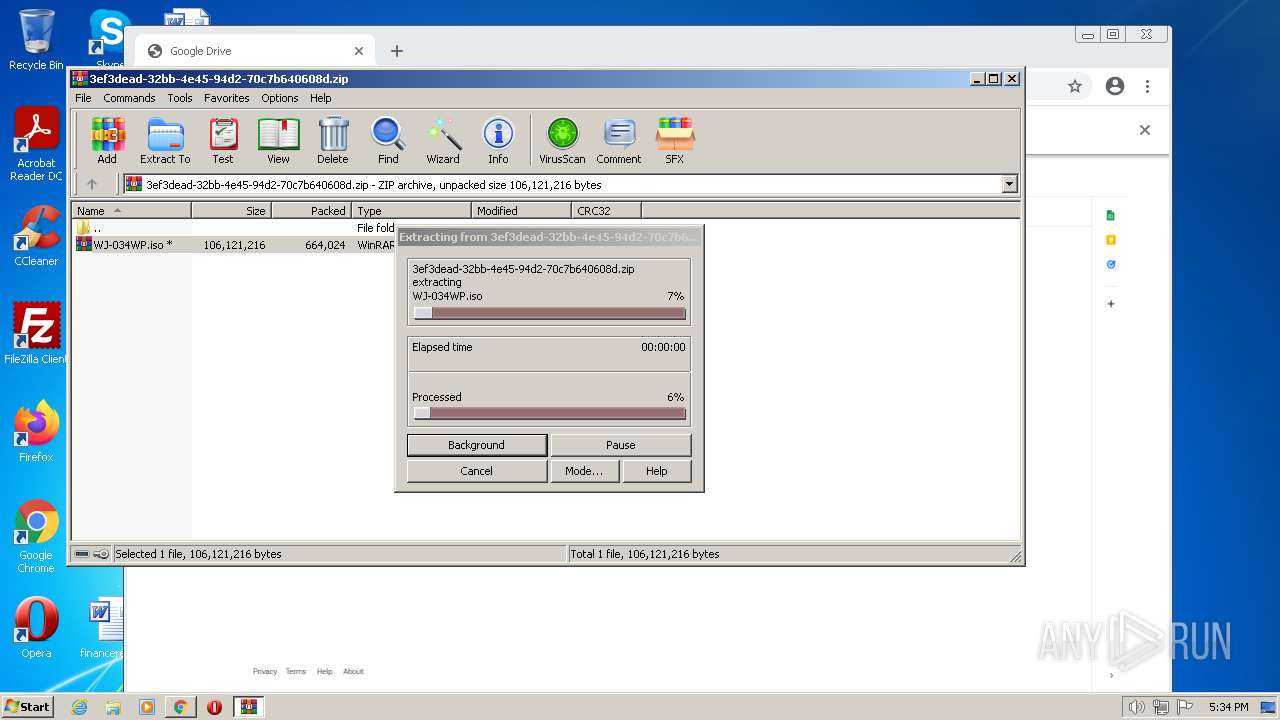
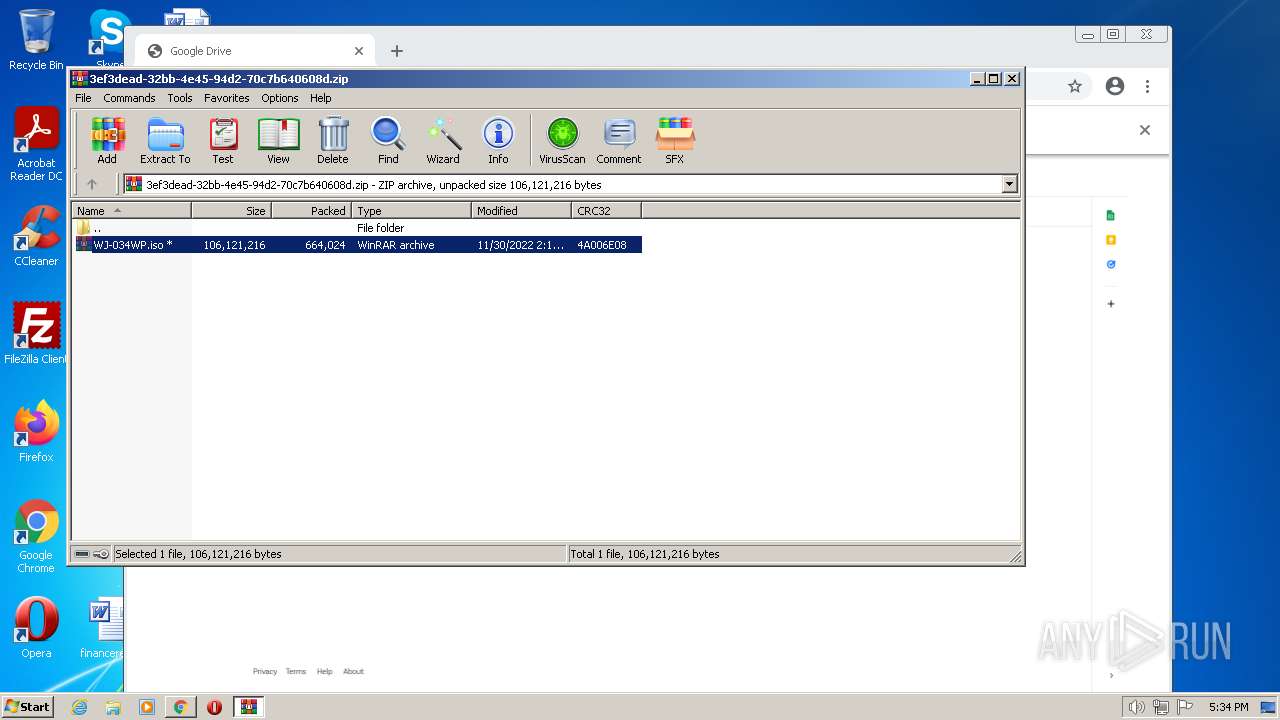
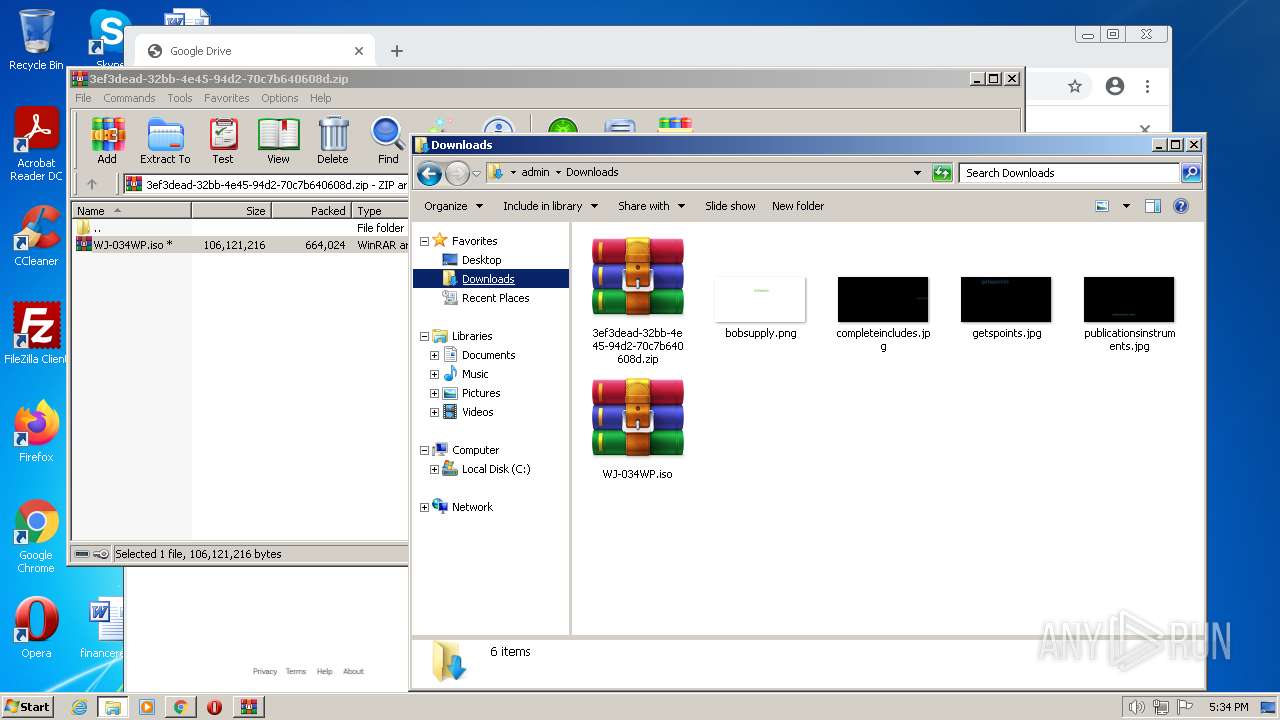
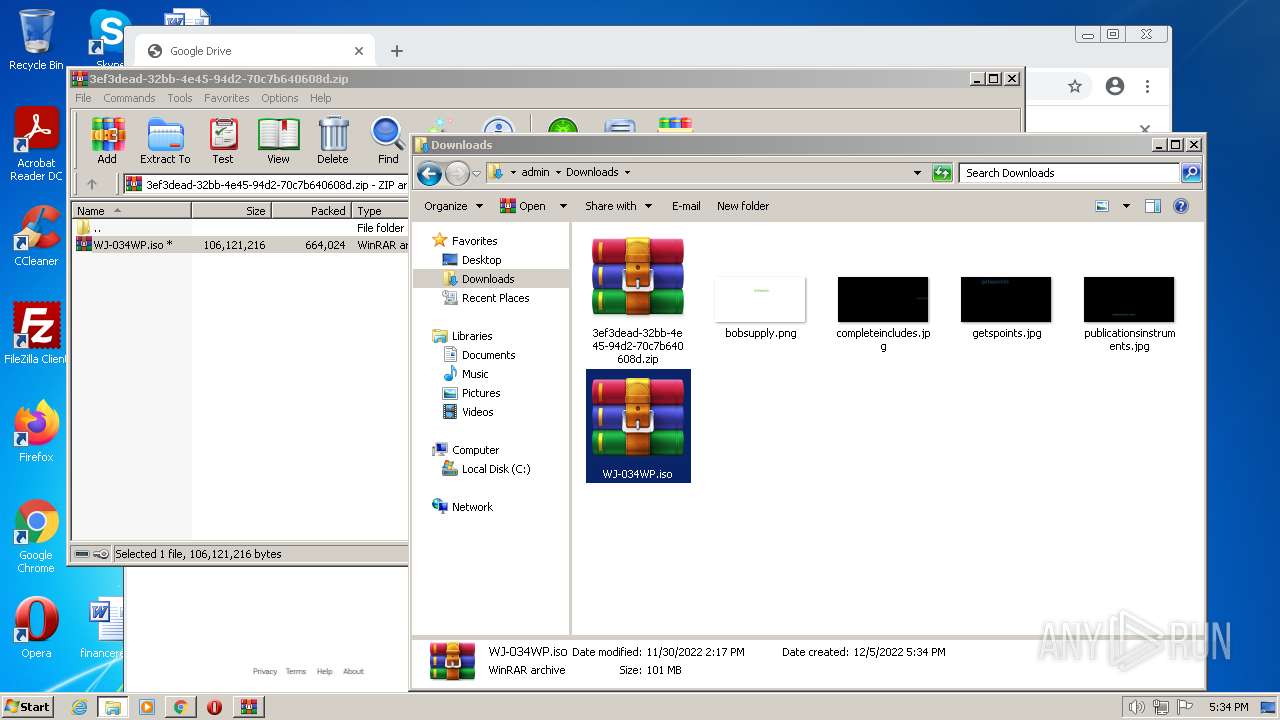
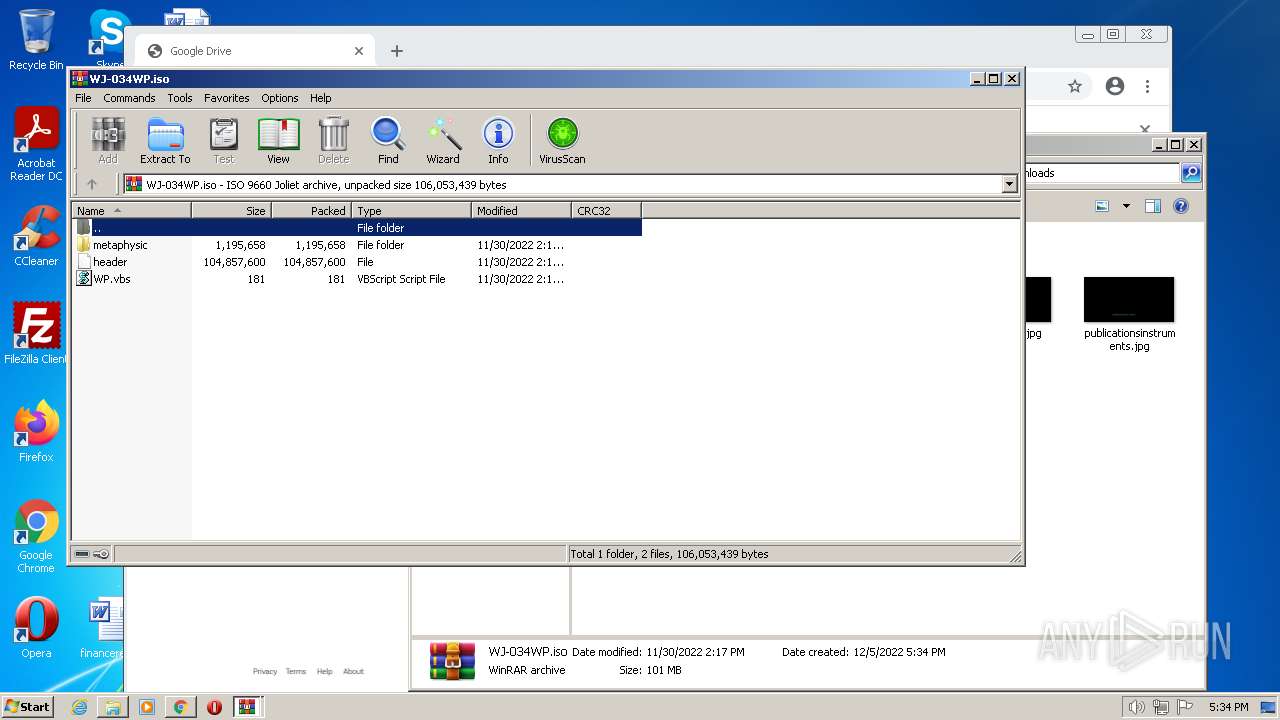
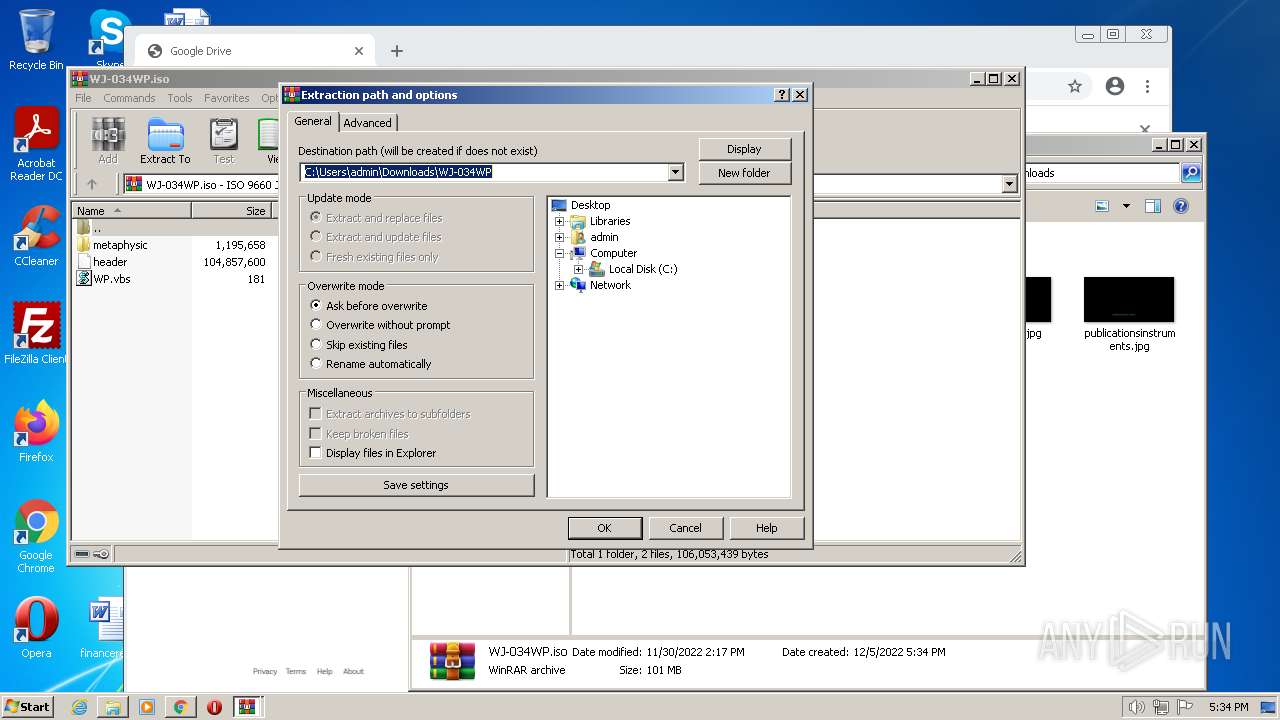
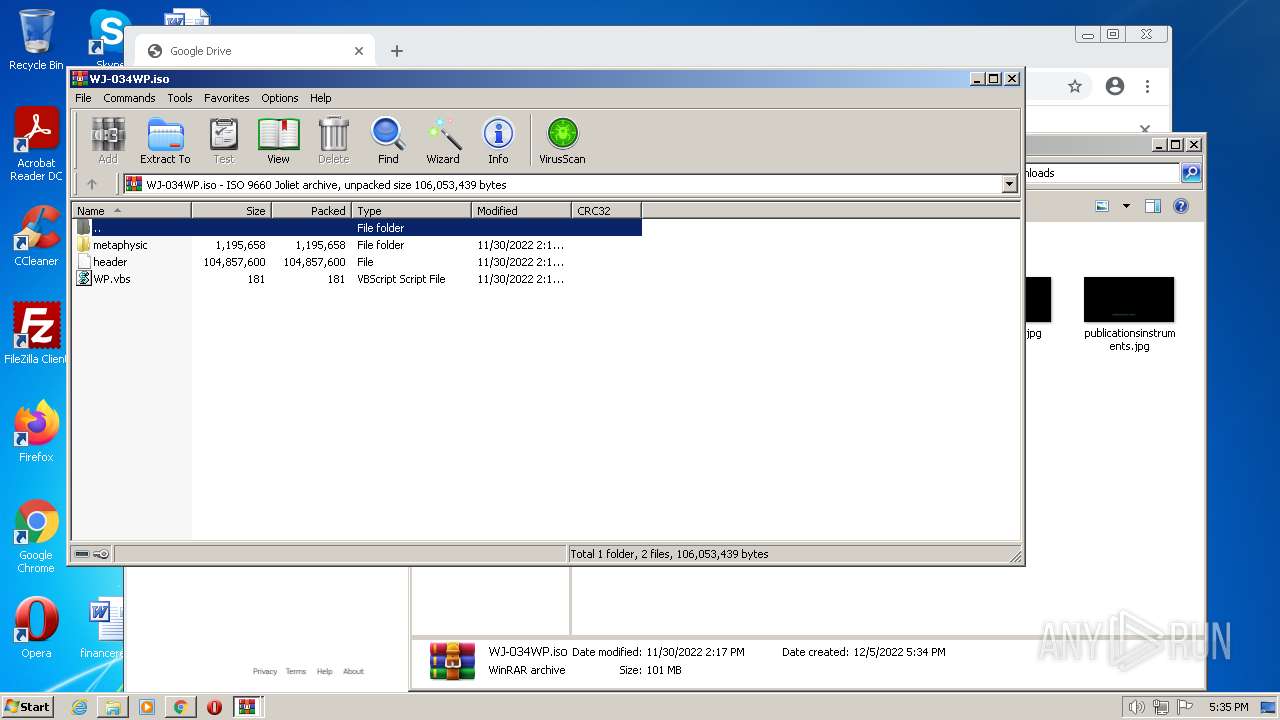
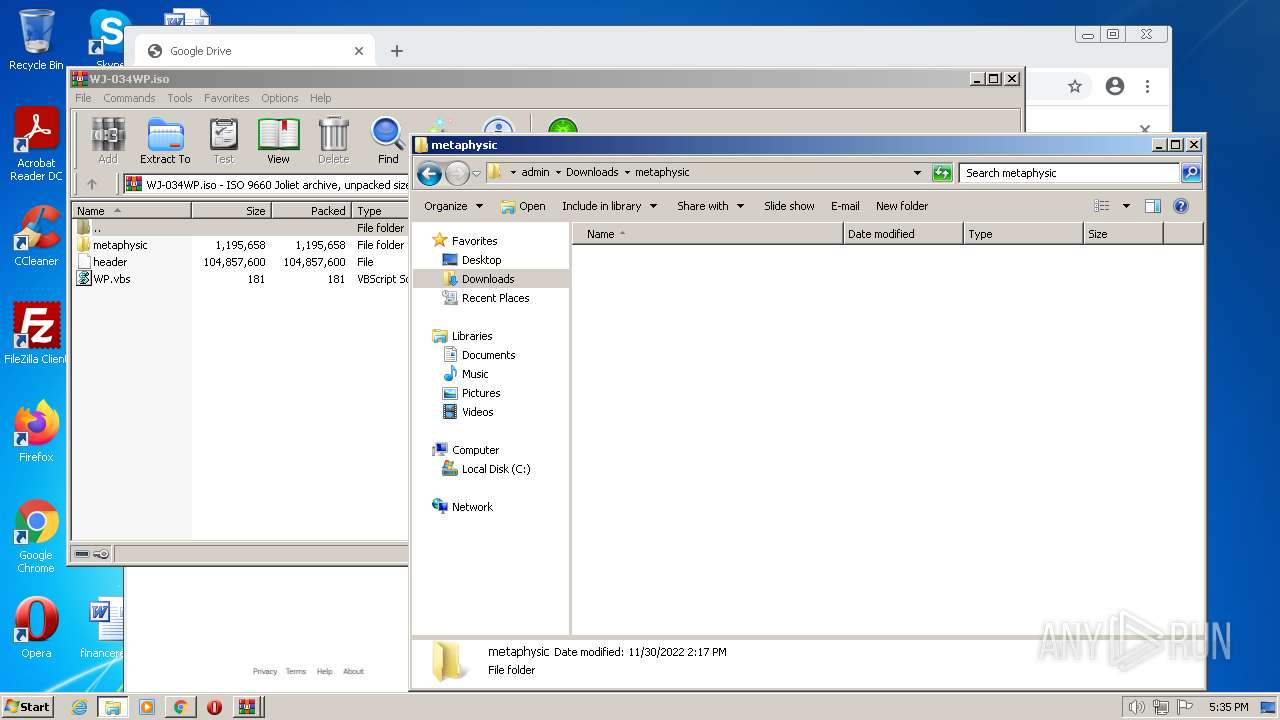
| 860 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\WJ-034WP.iso" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,689834893751507277,16686241370786346278,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1024 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1004,689834893751507277,16686241370786346278,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3480 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1528 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\WP.vbs" | C:\Windows\System32\WScript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\AppData\Local\Temp\WP#9996.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
31 277
Read events
30 801
Write events
464
Delete events
12
Modification events
| (PID) Process: | (1580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31000783 | |||
| (PID) Process: | (1580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31000783 | |||
| (PID) Process: | (1580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
159
Text files
144
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-638E2B89-B58.pma | — | |
MD5:— | SHA256:— | |||
| 320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:AD55BD80EE59AB8391FA9E5E43F56B30 | SHA256:1D0CEFA75DFDA6ED48F90F66719D2BDAFAFD5CC6BF81185F5069364D50AFD40E | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1076aff.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1076c47.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
61
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
868 | svchost.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
1580 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://crl.pki.goog/gsr1/gsr1.crl | US | der | 1.70 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 779 b | whitelisted |
1936 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDreCS75DAIaRKqvCi%2FvL9c | US | der | 472 b | whitelisted |
— | — | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 591 b | whitelisted |
1580 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1580 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 10.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
320 | chrome.exe | 142.250.185.78:443 | clients2.google.com | GOOGLE | US | whitelisted |
320 | chrome.exe | 172.217.16.193:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
320 | chrome.exe | 216.58.212.170:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
320 | chrome.exe | 142.250.186.99:443 | www.gstatic.com | GOOGLE | US | whitelisted |
320 | chrome.exe | 142.250.185.131:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
320 | chrome.exe | 172.217.18.99:443 | update.googleapis.com | GOOGLE | US | whitelisted |
1936 | iexplore.exe | 142.250.186.138:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
1580 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1580 | iexplore.exe | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fonts.googleapis.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |