| File name: | infected.elf |
| Full analysis: | https://app.any.run/tasks/11a6a93c-55a9-4537-8be9-50cd6f953eb5 |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | April 21, 2025, 04:13:32 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MIME: | application/x-executable |
| File info: | ELF 64-bit LSB executable, x86-64, version 1 (SYSV), statically linked, stripped |
| MD5: | D8689CC8FAC18781286F567D27CFEA0A |
| SHA1: | 693B41E72E82BE77289584DBD00CF9A960B7A5F8 |
| SHA256: | 6B3A20FEF3FF1544248FC1EB75D80C40F271A4D36FF1ACA707999B328E50A29B |
| SSDEEP: | 768:kMsJFhMxvp7oeVKF05LMls06e1qNeIG/FGdlXhjm6I:kMsGxhvTLJnTNS/UjhZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies file or directory owner
- sudo (PID: 39551)
Checks DMI information (probably VM detection)
- pipewire (PID: 39609)
- pulseaudio (PID: 39611)
- gnome-shell (PID: 39706)
Executes commands using command-line interpreter
- sudo (PID: 39554)
Reads profile file
- infected.elf (PID: 39556)
Reads passwd file
- gdm-session-worker (PID: 39566)
- infected.elf (PID: 39556)
- pipewire (PID: 39609)
- pipewire-media-session (PID: 39610)
- dbus-daemon (PID: 39620)
- dbus-daemon (PID: 39647)
- dbus-daemon (PID: 39737)
- gvfs-udisks2-volume-monitor (PID: 39744)
- ibus-daemon (PID: 39805)
- gnome-shell (PID: 39706)
- gsd-media-keys (PID: 39840)
- ibus-daemon (PID: 39953)
- gsd-power (PID: 39854)
- whoopsie (PID: 39994)
- whoopsie (PID: 39783)
- gsd-print-notifications (PID: 39816)
- gdm-session-worker (PID: 40094)
Reads /proc/mounts (likely used to find writable filesystems)
- dbus-daemon (PID: 39620)
- dbus-daemon (PID: 39647)
- dbus-daemon (PID: 39737)
- gnome-shell (PID: 39706)
- gjs-console (PID: 39957)
- snapd-desktop-integration (PID: 40001)
- gjs-console (PID: 39796)
Check the Environment Variables Related to System Identification (os-release)
- snapd-desktop-integration (PID: 40001)
- snapctl (PID: 40043)
- snapctl (PID: 40051)
Connects to unusual port
- infected.elf (PID: 39559)
Executes the "rm" command to delete files or directories
- snapd-desktop-integration (PID: 40001)
INFO
Checks timezone
- gdm-session-worker (PID: 39566)
- dbus-daemon (PID: 39620)
- gnome-shell (PID: 39706)
- whoopsie (PID: 39783)
- gnome-session-binary (PID: 39655)
- python3.10 (PID: 39694)
- tracker-miner-fs-3 (PID: 39715)
- python3.10 (PID: 39687)
- spice-vdagent (PID: 39951)
- gsd-color (PID: 39814)
- python3.10 (PID: 39807)
- gsd-print-notifications (PID: 39816)
- whoopsie (PID: 39994)
Creates file in the temporary folder
- gnome-shell (PID: 39706)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (100) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Executable file |
| CPUType: | AMD x86-64 |
Total processes
414
Monitored processes
187
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 39550 | /bin/sh -c "sudo chown user /home/user/Downloads/infected\.elf && chmod +x /home/user/Downloads/infected\.elf && DISPLAY=:0 sudo -iu user /home/user/Downloads/infected\.elf " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39551 | sudo chown user /home/user/Downloads/infected.elf | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39552 | chown user /home/user/Downloads/infected.elf | /usr/bin/chown | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39553 | chmod +x /home/user/Downloads/infected.elf | /usr/bin/chmod | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39554 | sudo -iu user /home/user/Downloads/infected.elf | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39556 | /home/user/Downloads/infected.elf | /home/user/Downloads/infected.elf | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39557 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | infected.elf |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39558 | /home/user/Downloads/infected.elf | /home/user/Downloads/infected.elf | — | infected.elf |
User: user Integrity Level: UNKNOWN | ||||
| 39559 | (sd-pam) r/Downloads/infected.elf | /home/user/Downloads/infected.elf | infected.elf | |
User: user Integrity Level: UNKNOWN | ||||
| 39565 | /bin/sh /etc/gdm3/PostSession/Default | /usr/bin/dash | — | gdm-session-worker |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
83
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 39673 | session-migration | /var/lib/gdm3/.local/share/session_migration-(null) | text | |
MD5:— | SHA256:— | |||
| 39611 | pulseaudio | /var/lib/gdm3/.cache/gstreamer-1.0/registry.x86_64.bin (deleted) | binary | |
MD5:— | SHA256:— | |||
| 39611 | pulseaudio | /var/lib/gdm3/.config/pulse/cookie | binary | |
MD5:— | SHA256:— | |||
| 39613 | tracker-extract-3 | /var/lib/gdm3/.cache/gstreamer-1.0/registry.x86_64.bin | binary | |
MD5:— | SHA256:— | |||
| 39715 | tracker-miner-fs-3 | /var/lib/gdm3/.cache/tracker3/files/meta.db | binary | |
MD5:— | SHA256:— | |||
| 39715 | tracker-miner-fs-3 | /var/lib/gdm3/.cache/tracker3/files/meta.db-journal (deleted) | binary | |
MD5:— | SHA256:— | |||
| 39706 | gnome-shell | /tmp/.X1024-lock | text | |
MD5:— | SHA256:— | |||
| 39706 | gnome-shell | /tmp/.X1025-lock | text | |
MD5:— | SHA256:— | |||
| 39715 | tracker-miner-fs-3 | /var/lib/gdm3/.cache/tracker3/files/ontologies.gvdb | binary | |
MD5:— | SHA256:— | |||
| 39715 | tracker-miner-fs-3 | /var/lib/gdm3/.cache/tracker3/files/meta.db-shm | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
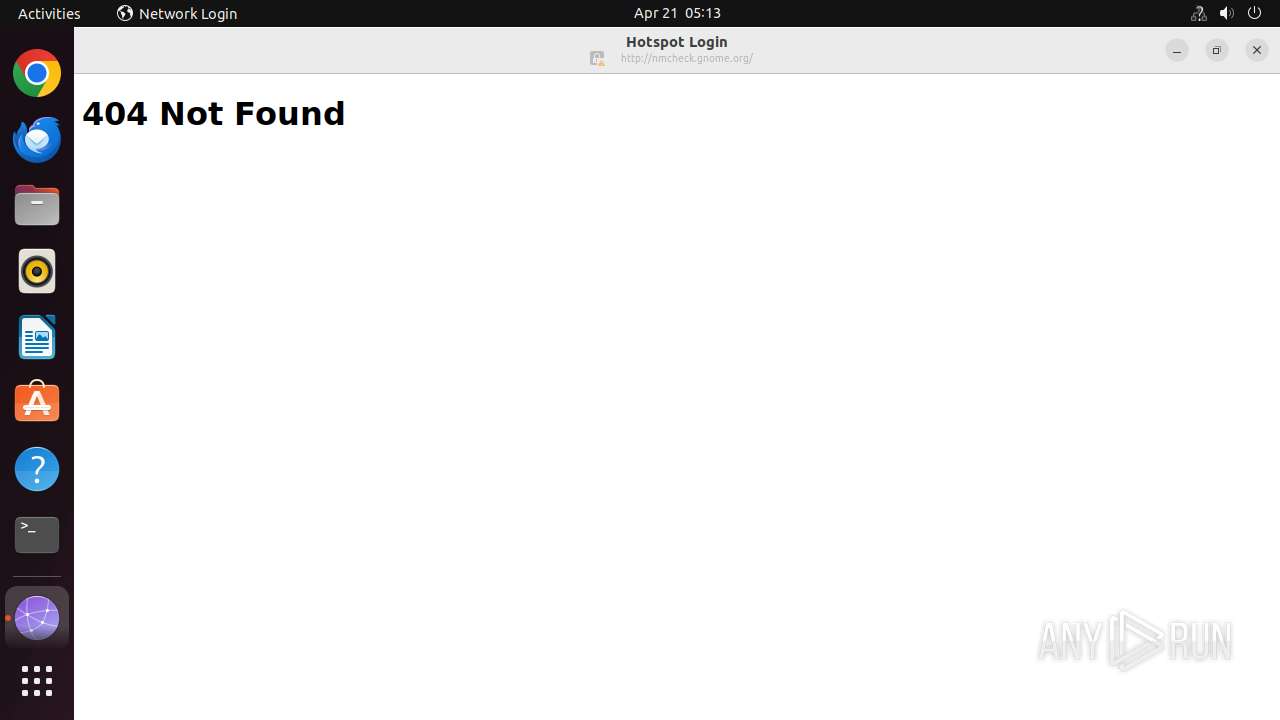
HTTP(S) requests
6
TCP/UDP connections
12
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 404 | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 404 | 151.101.193.91:80 | http://nmcheck.gnome.org/ | unknown | — | — | whitelisted |
— | — | GET | 404 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
488 | NetworkManager | GET | 404 | 185.125.190.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
488 | NetworkManager | GET | 404 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
488 | NetworkManager | GET | 404 | 91.189.91.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 91.189.91.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 185.125.190.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 91.189.91.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 151.101.193.91:80 | nmcheck.gnome.org | FASTLY | US | whitelisted |
39559 | infected.elf | 196.251.71.29:41277 | fdh32fsdfhs.shop | — | SC | malicious |
488 | NetworkManager | 185.125.190.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
488 | NetworkManager | 185.125.190.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
488 | NetworkManager | 91.189.91.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
nmcheck.gnome.org |
| whitelisted |
fdh32fsdfhs.shop |
| malicious |
connectivity-check.ubuntu.com |
| whitelisted |
5.100.168.192.in-addr.arpa |
| unknown |