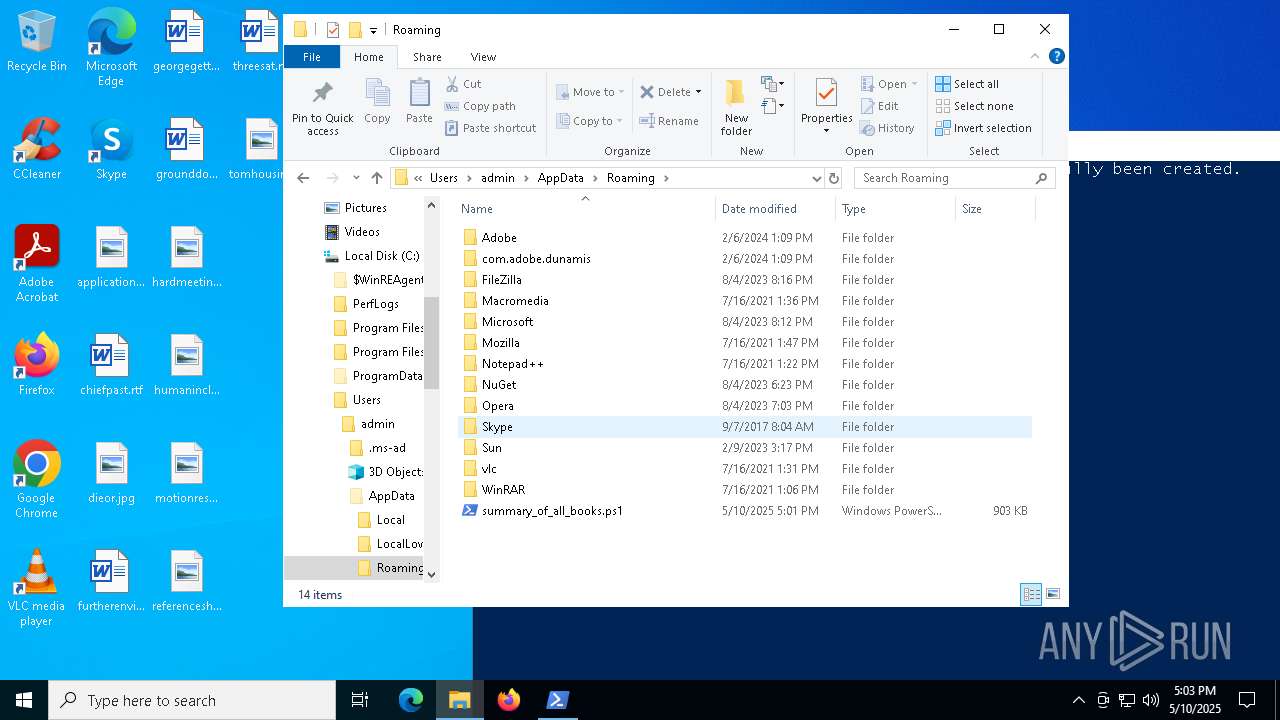
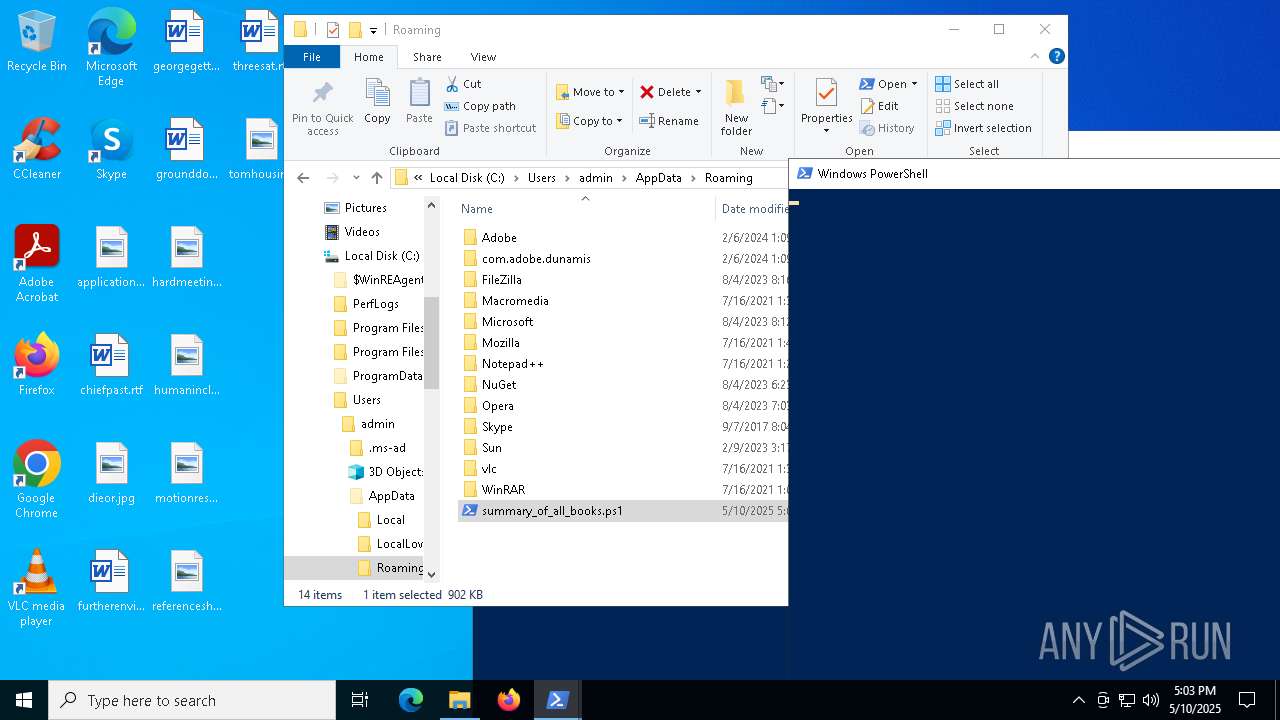
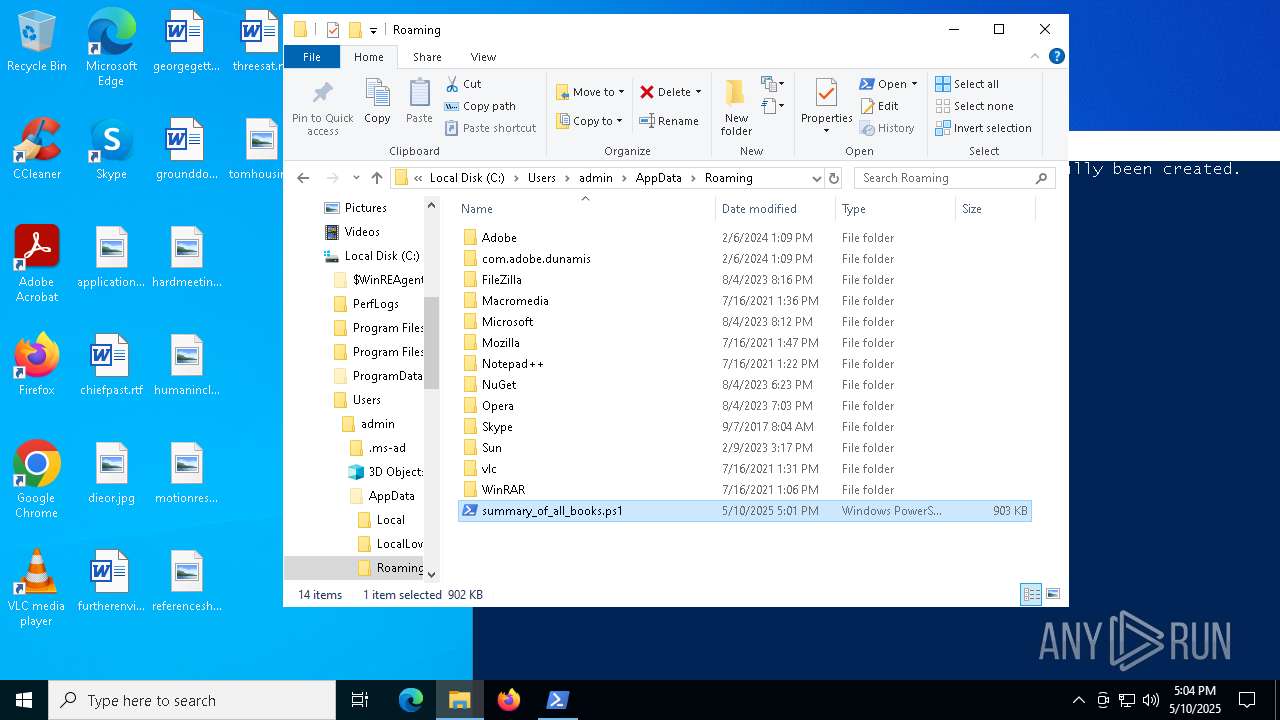
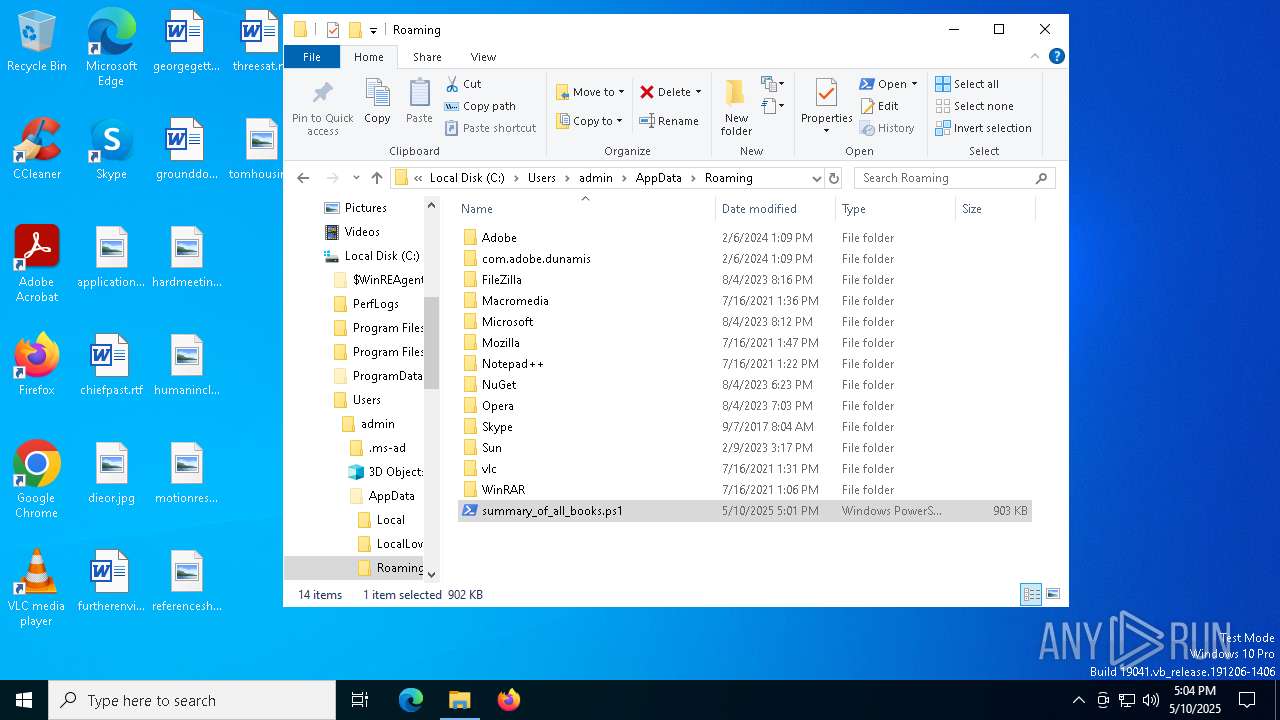
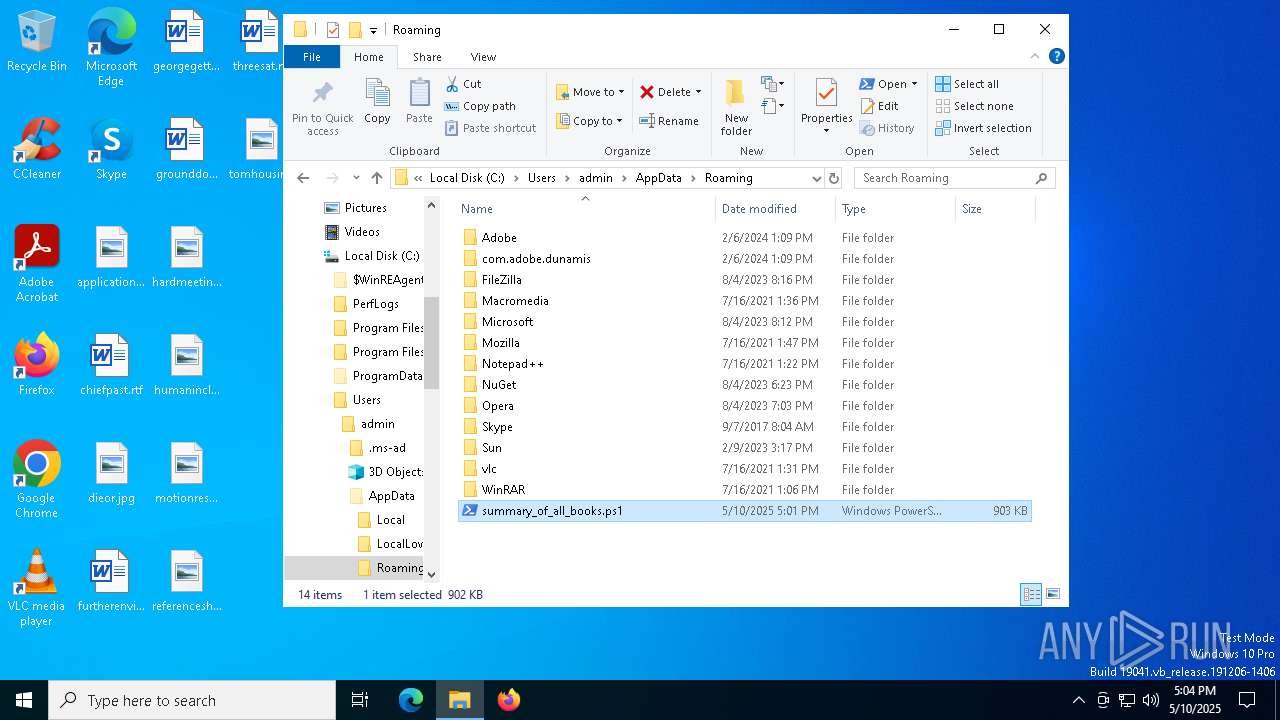
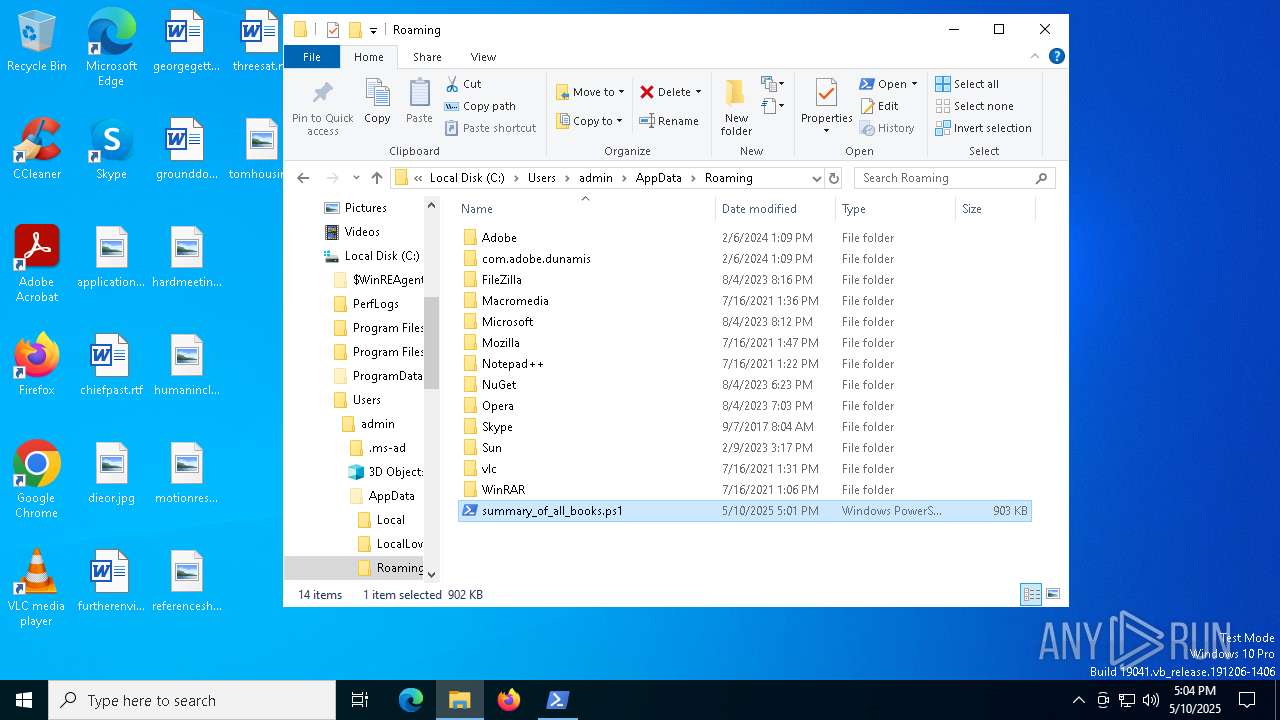
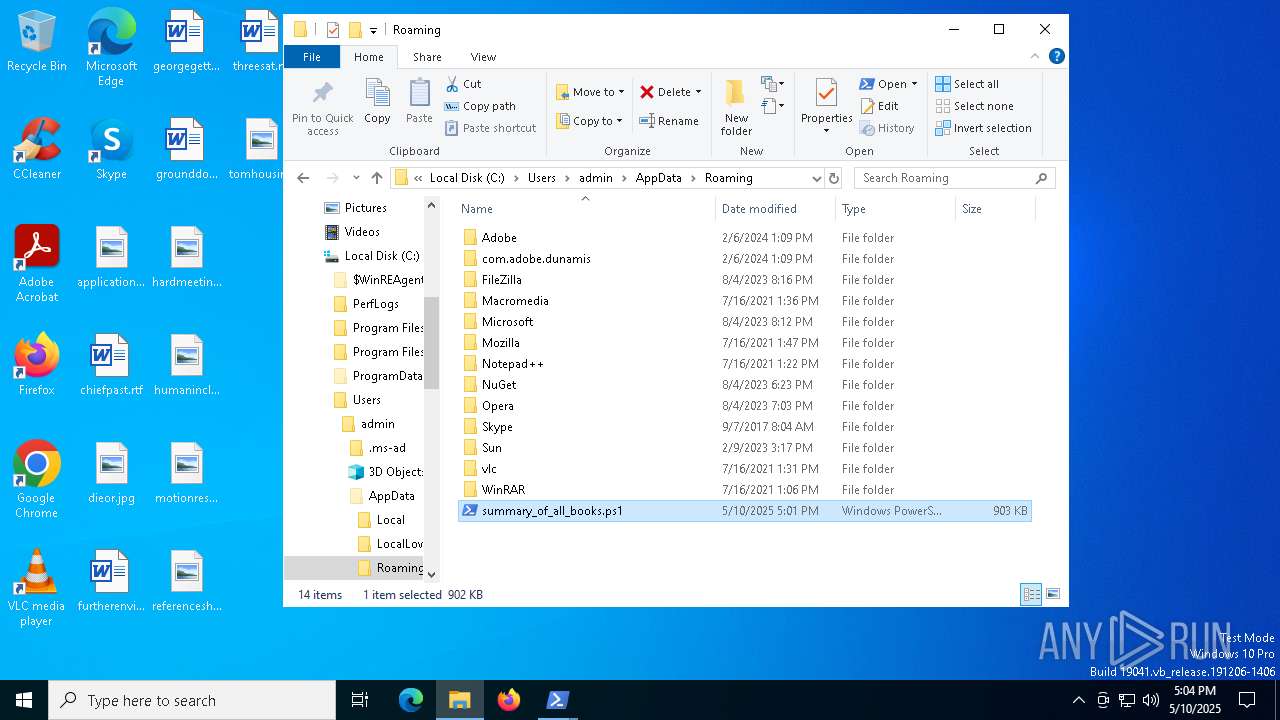
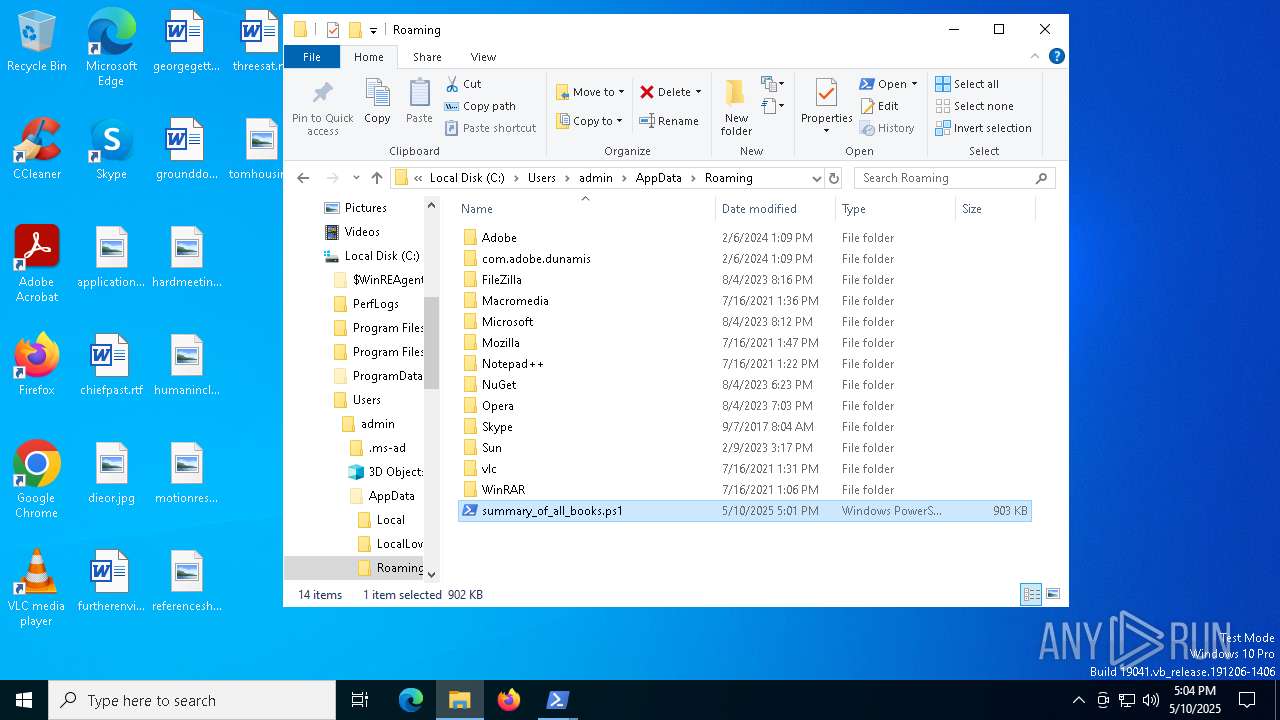
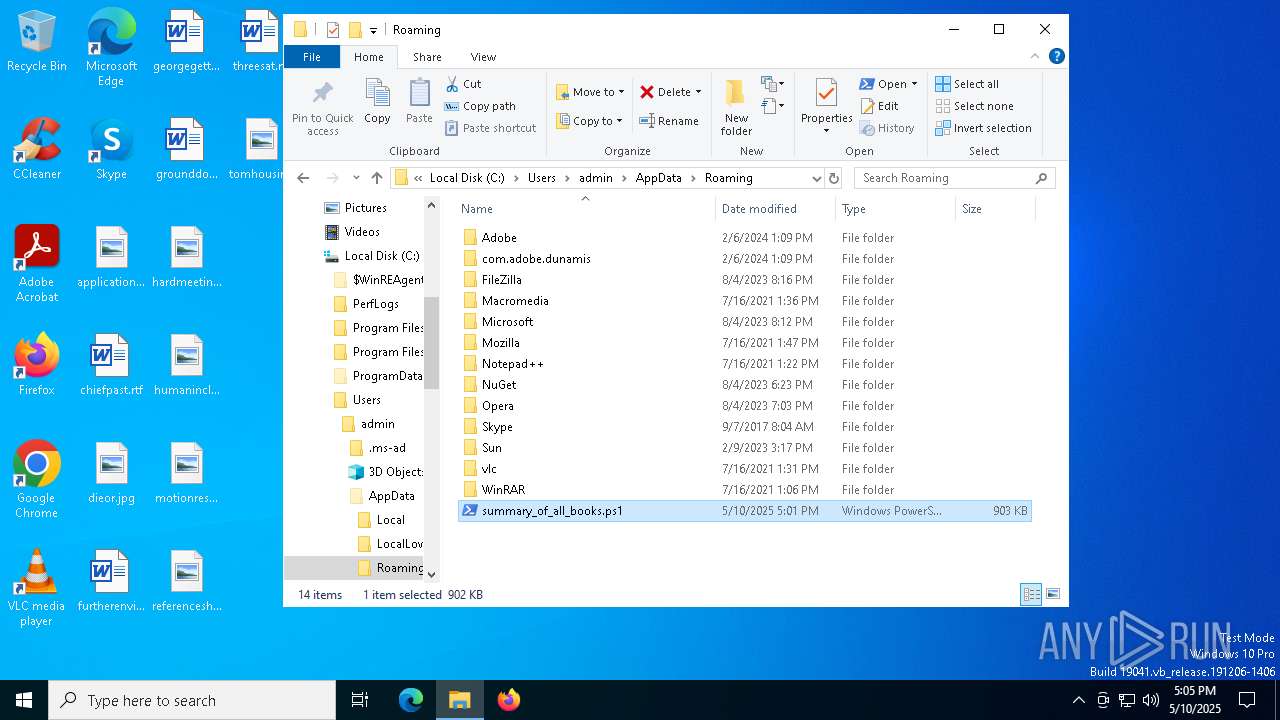
| File name: | summary_of_all_books.ps1 |
| Full analysis: | https://app.any.run/tasks/fe0fd389-acdf-4319-acb0-cc46df86f431 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 10, 2025, 17:01:26 |
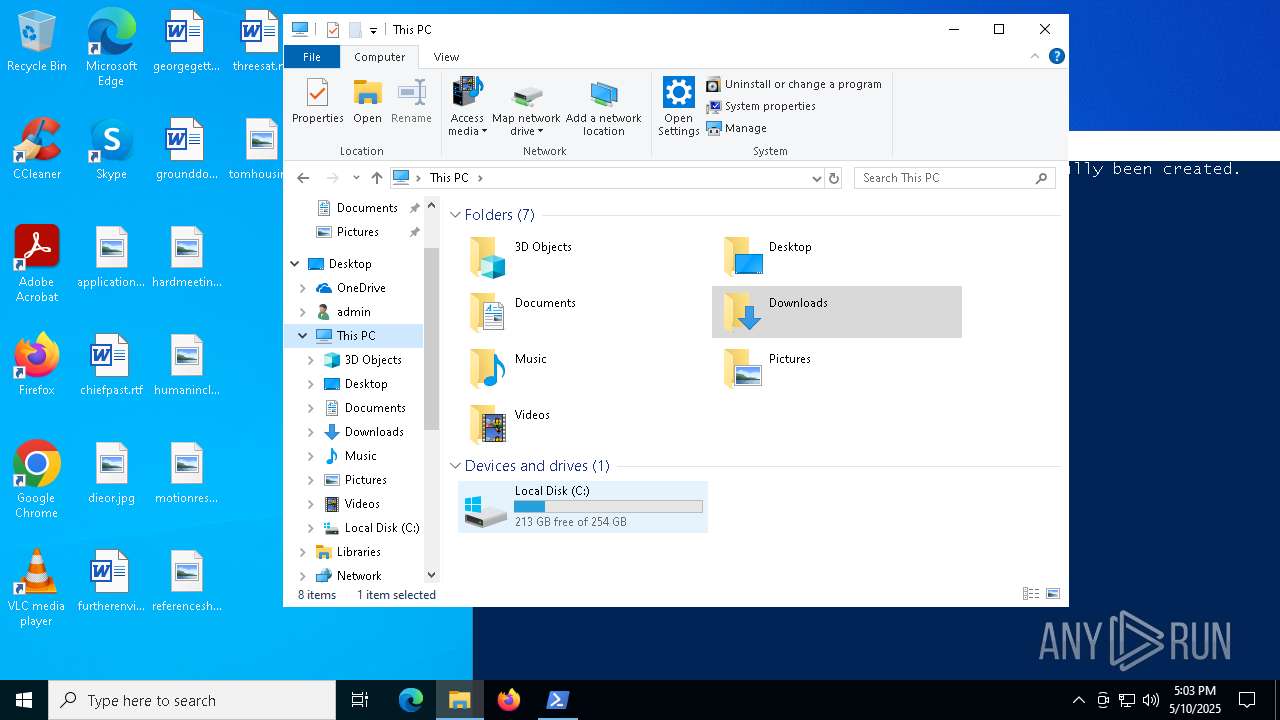
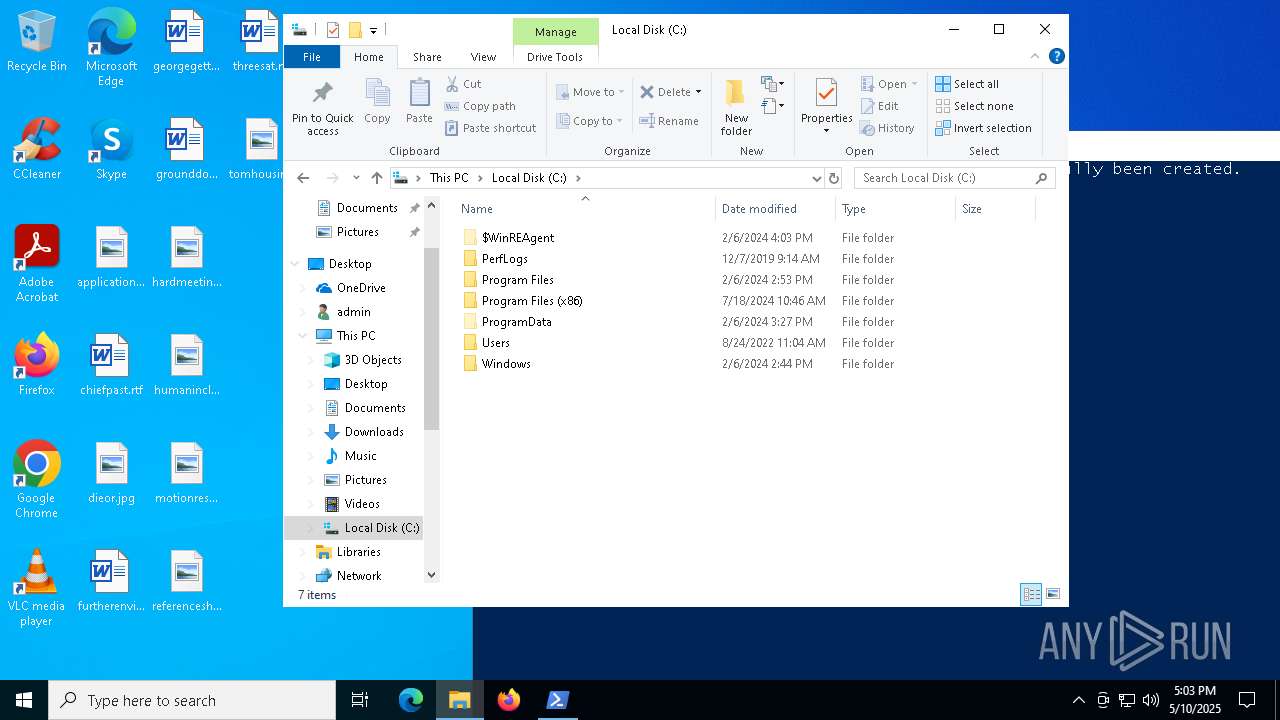
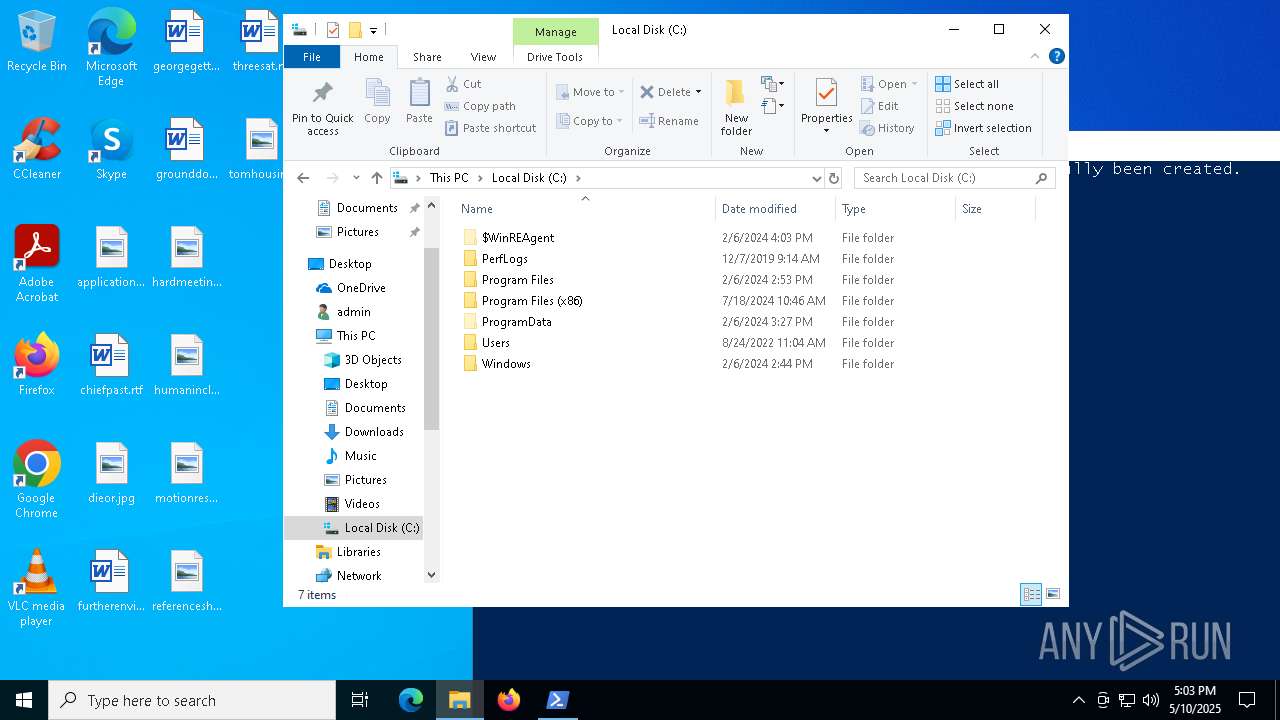
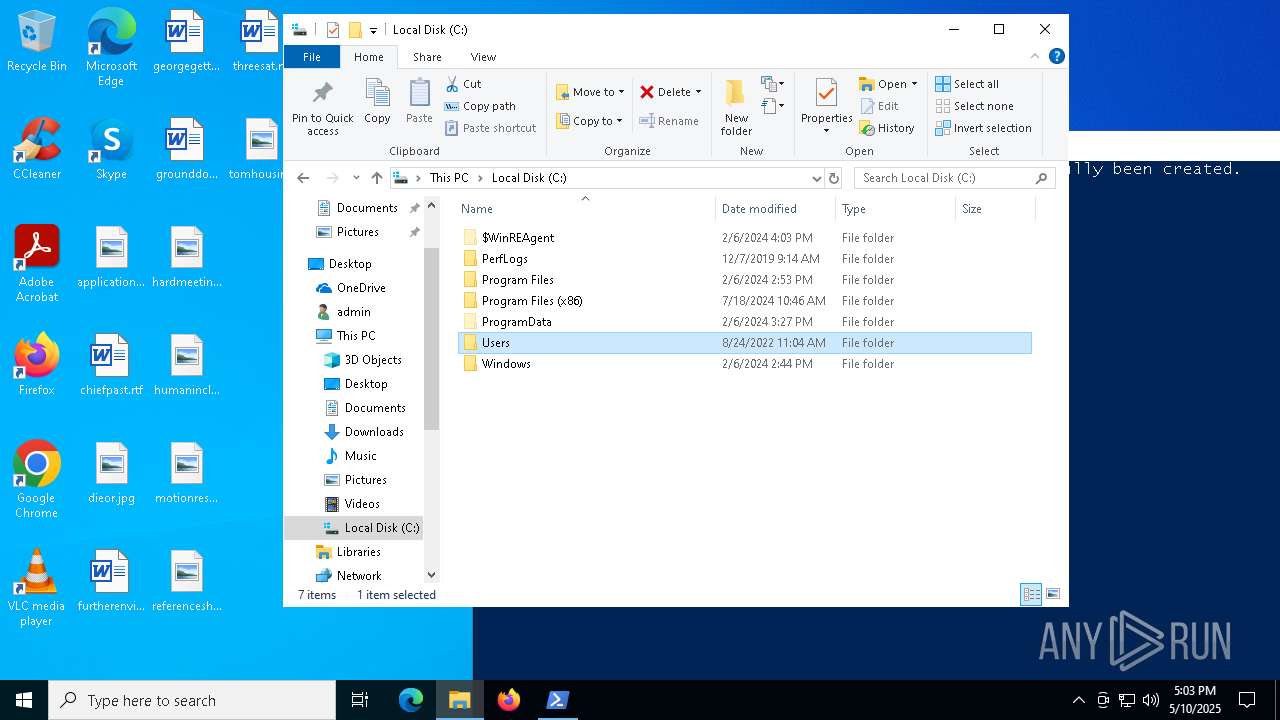
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (61290), with CRLF line terminators |
| MD5: | 571303C70CF8A208C66FD8AB072A1F19 |
| SHA1: | 83051CAEAB28A50147C64B5BC16728BE3CDB3220 |
| SHA256: | 6A95F66EFA32C8EF6AA8B68DB780CAA468C4B91A11E6833FEC664A41116122EB |
| SSDEEP: | 3072:KeX42W2OlKkzdp5rC1RJcgO37y4ydNtcLoifI3pbDZ6Fhnme8aGc/E6ncHQZ8669:K3kU7VC4xVJflRSZP46 |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7292)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 5508)
Steals credentials from Web Browsers
- aspnet_compiler.exe (PID: 8076)
Actions looks like stealing of personal data
- aspnet_compiler.exe (PID: 8076)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 7292)
ASYNCRAT has been detected (SURICATA)
- aspnet_compiler.exe (PID: 8076)
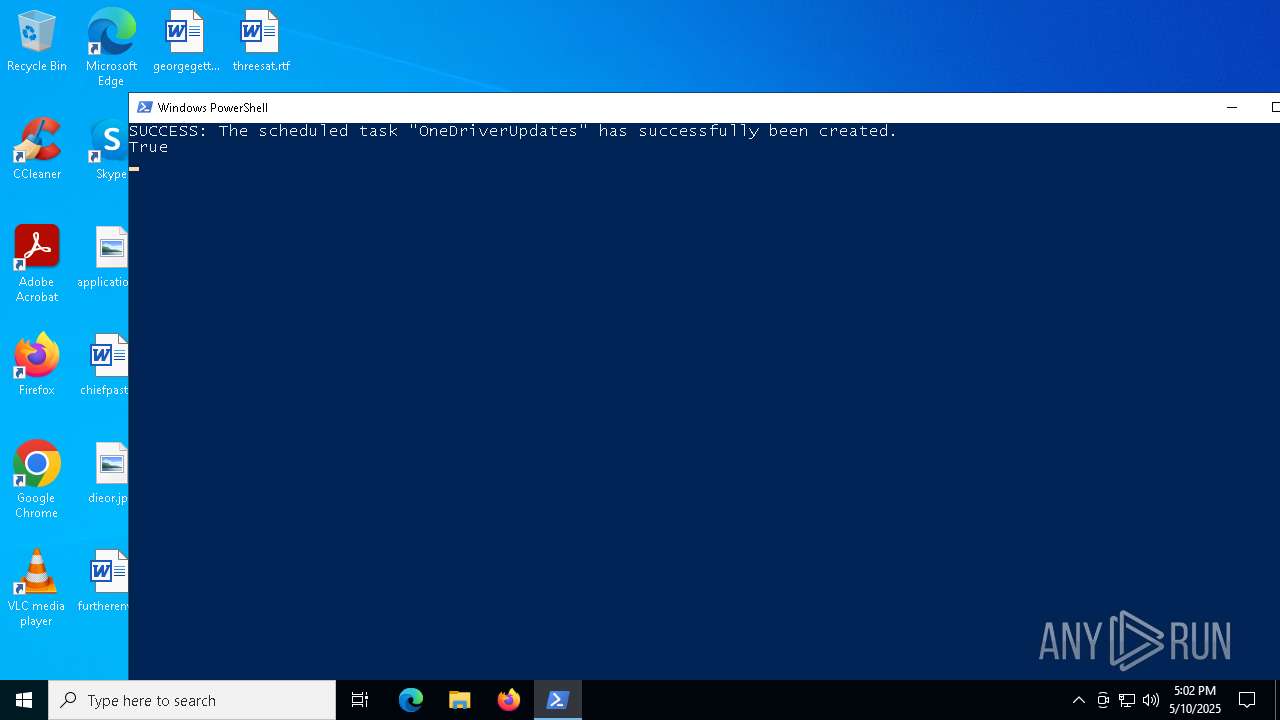
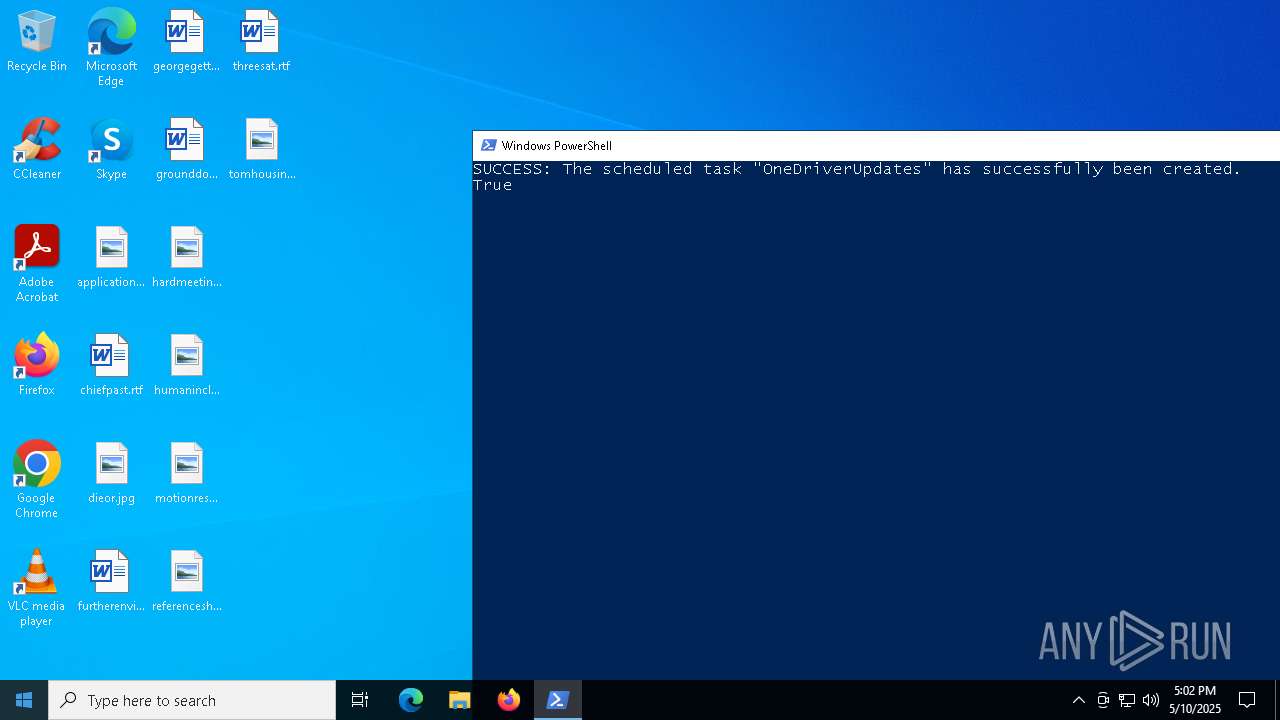
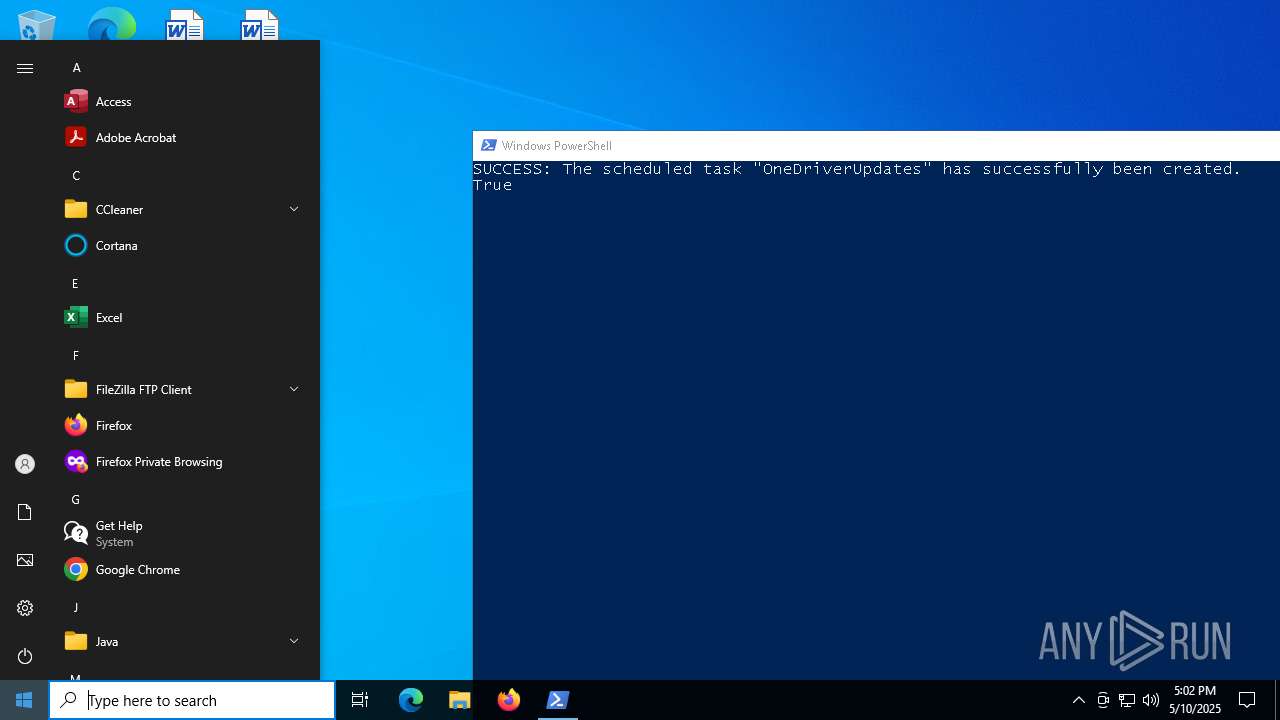
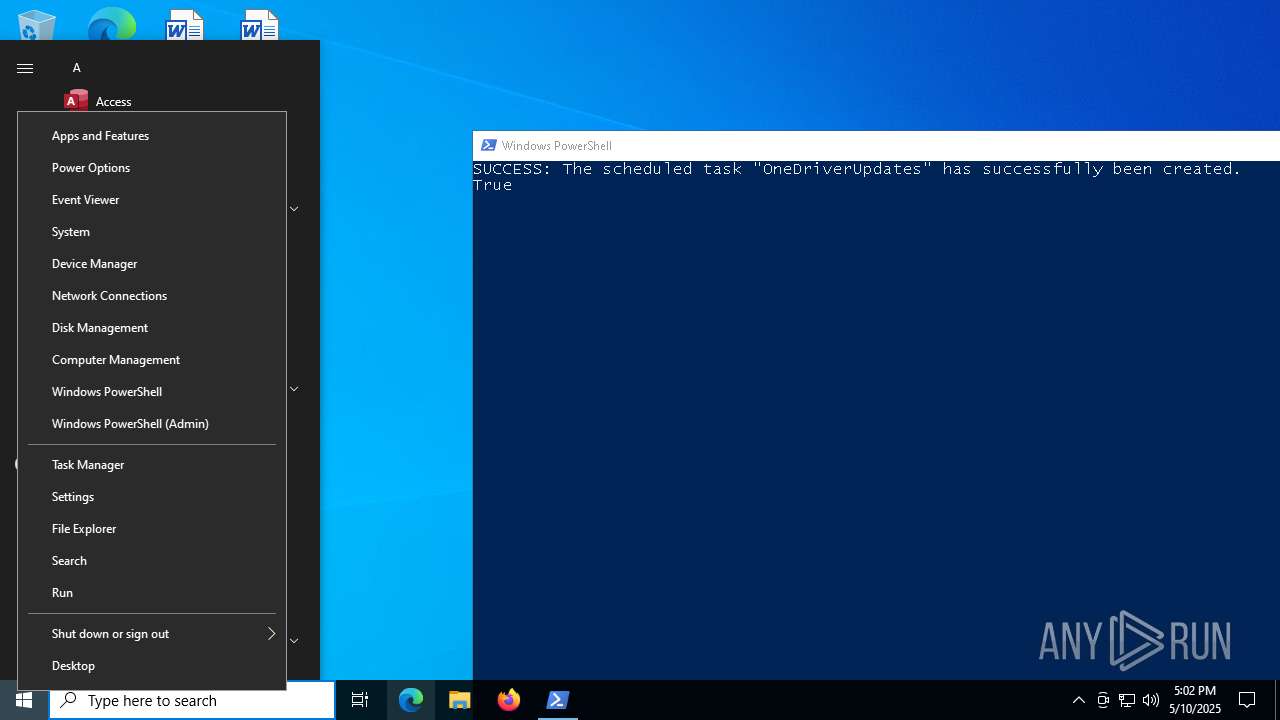
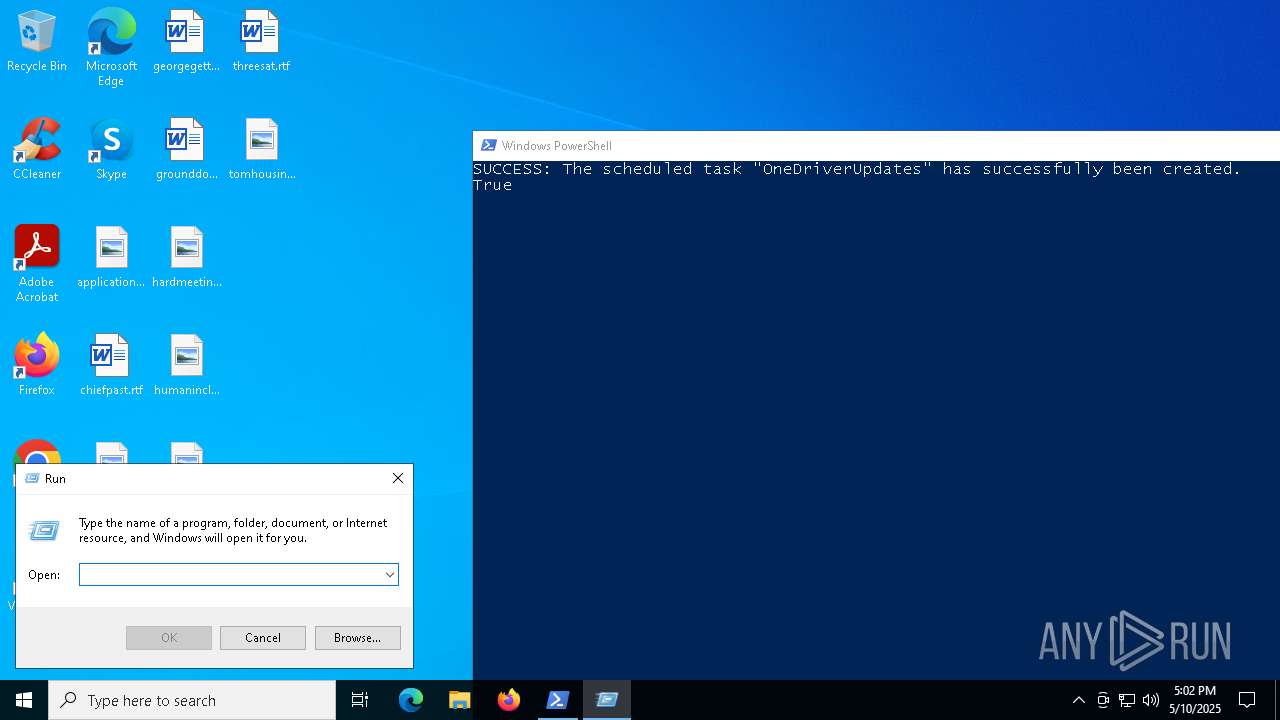
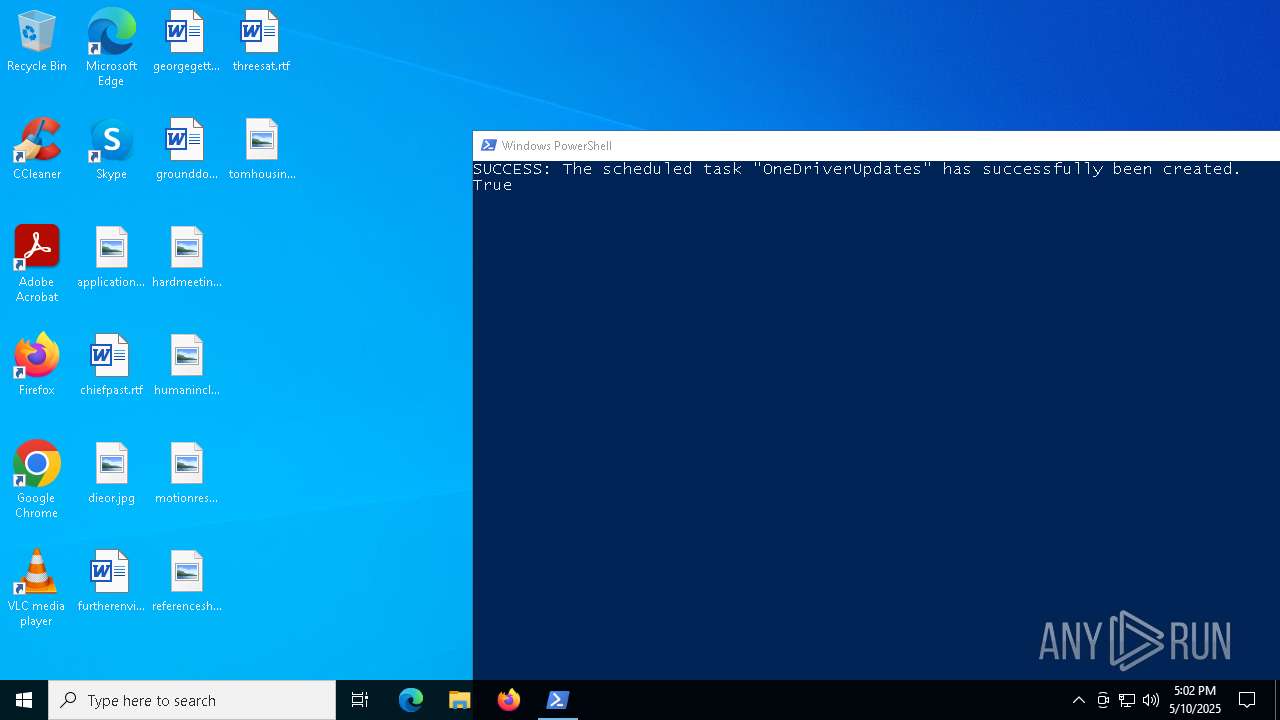
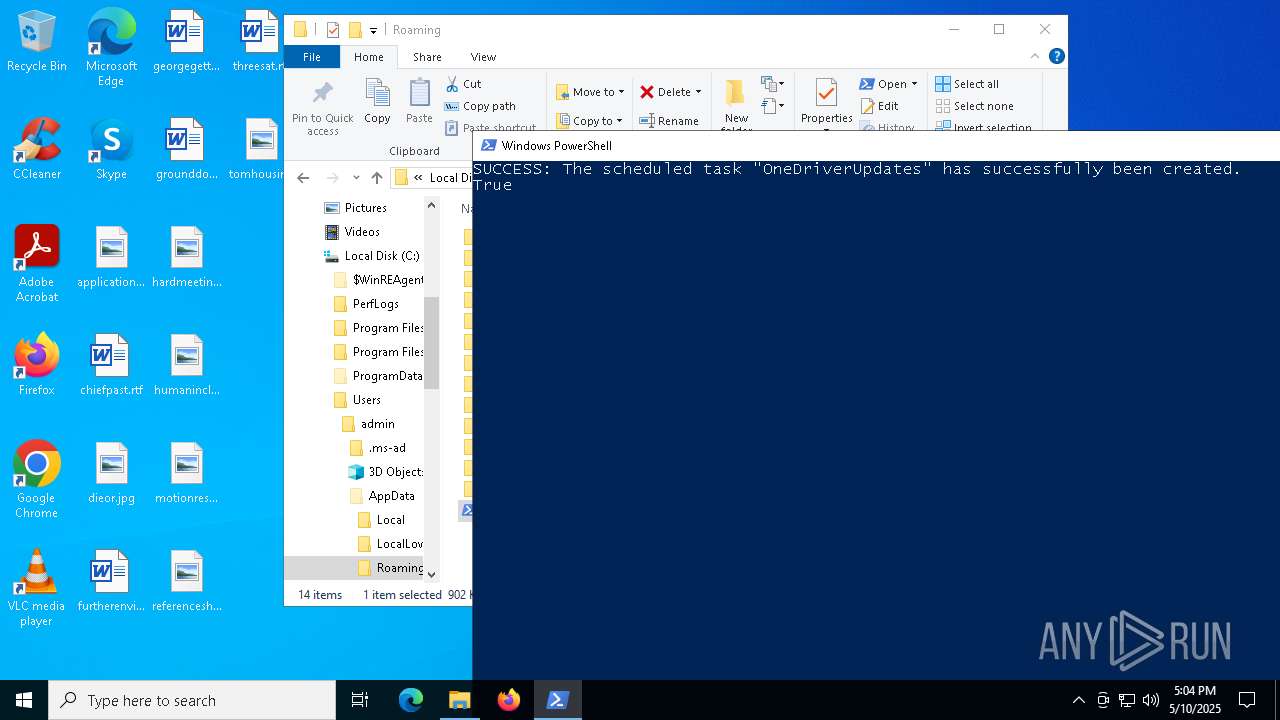
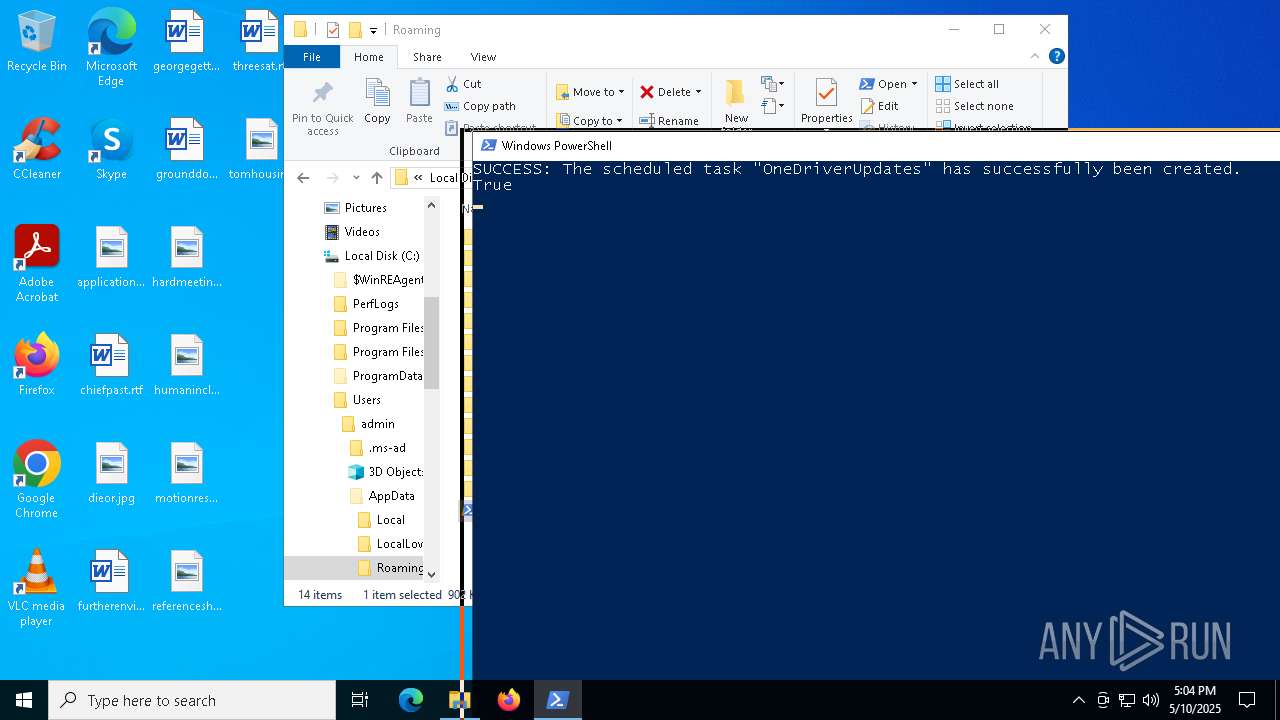
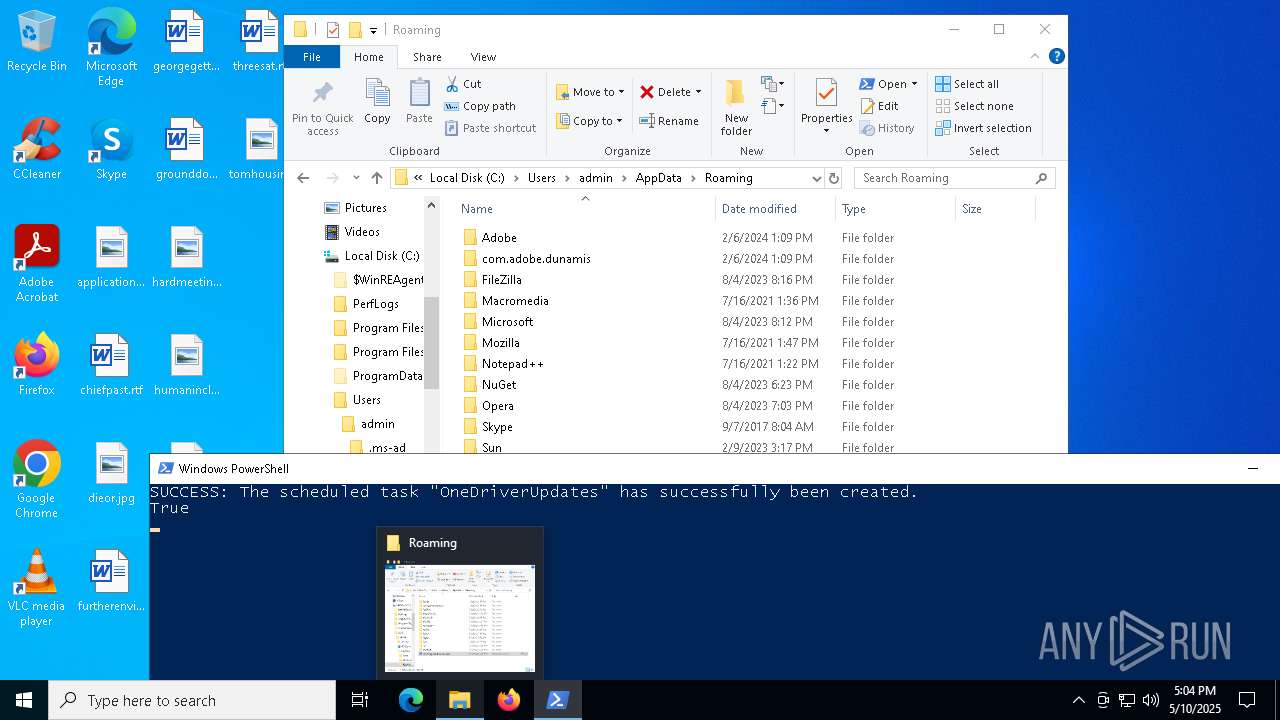
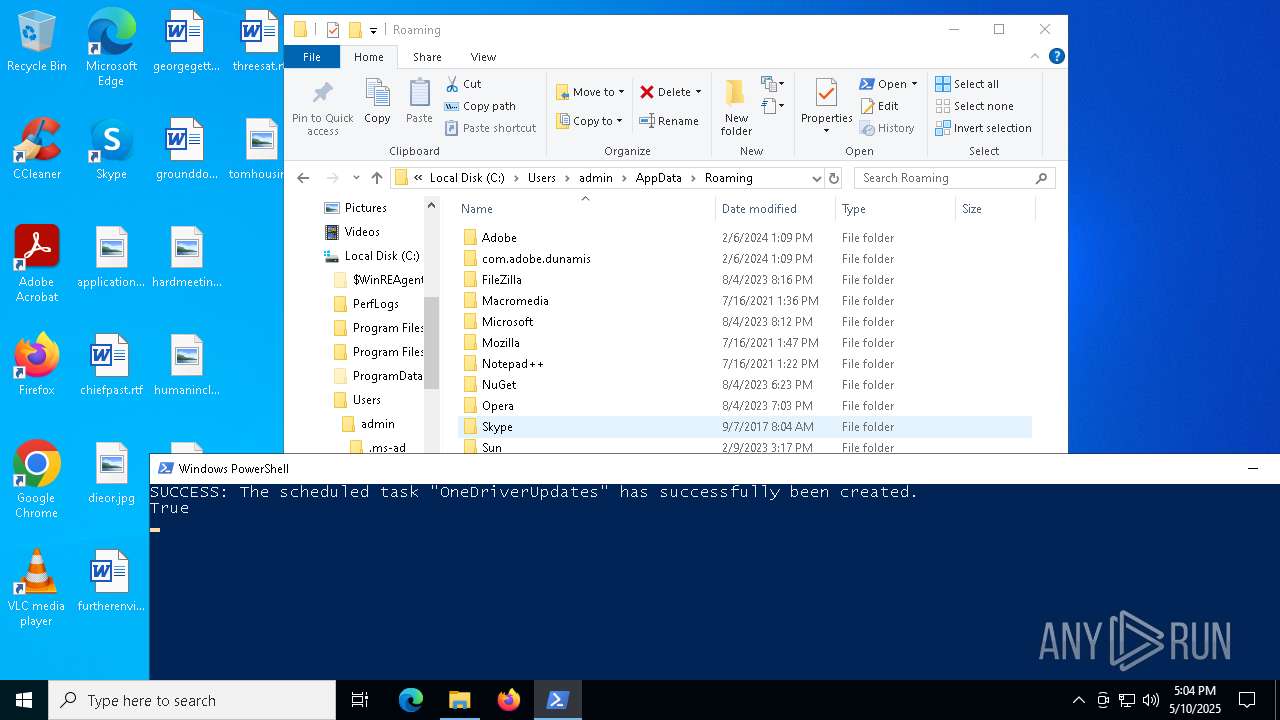
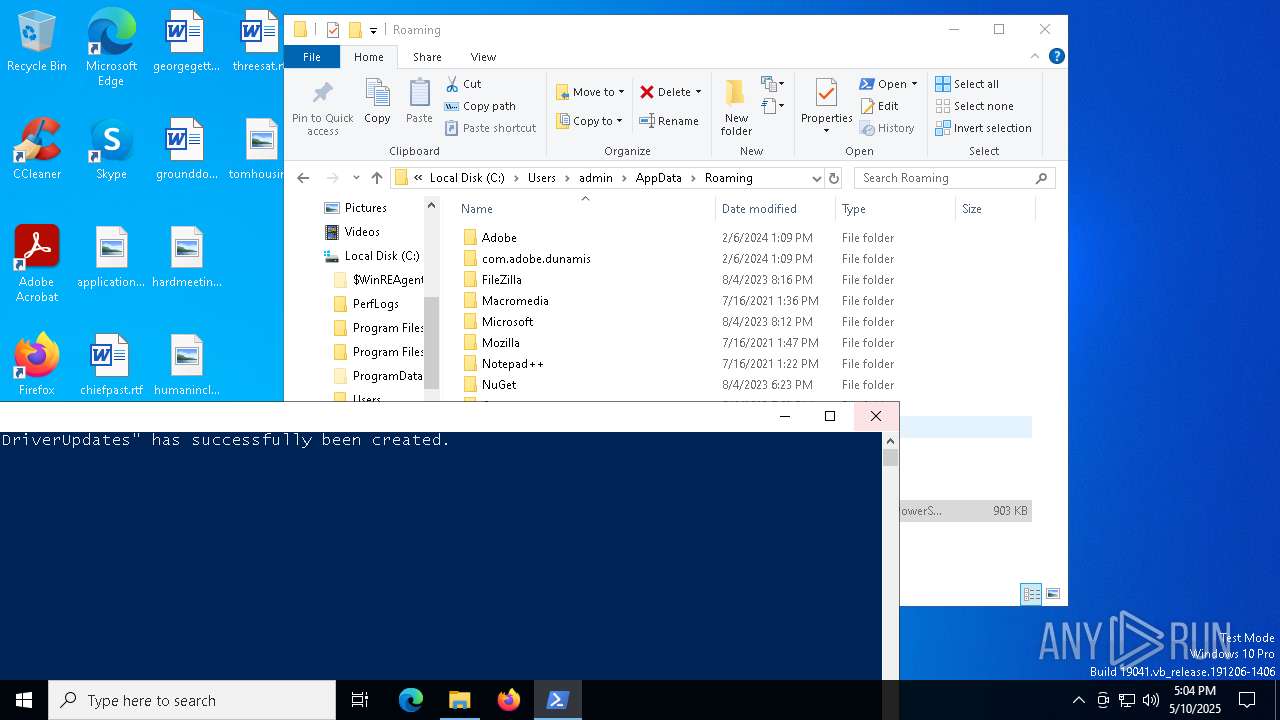
Uses Task Scheduler to run other applications
- powershell.exe (PID: 7292)
SUSPICIOUS
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 7292)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 2552)
Contacting a server suspected of hosting an CnC
- aspnet_compiler.exe (PID: 8076)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7292)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 2552)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7292)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 2552)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7292)
Lists all scheduled tasks
- schtasks.exe (PID: 7880)
- schtasks.exe (PID: 7408)
- schtasks.exe (PID: 6656)
- schtasks.exe (PID: 7172)
- schtasks.exe (PID: 7936)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 7292)
Connects to unusual port
- aspnet_compiler.exe (PID: 8076)
INFO
Checks supported languages
- aspnet_compiler.exe (PID: 8076)
- aspnet_compiler.exe (PID: 7800)
Confuser has been detected (YARA)
- aspnet_compiler.exe (PID: 8076)
Reads the machine GUID from the registry
- aspnet_compiler.exe (PID: 8076)
- aspnet_compiler.exe (PID: 7800)
Reads the computer name
- aspnet_compiler.exe (PID: 8076)
- aspnet_compiler.exe (PID: 7800)
Reads the software policy settings
- aspnet_compiler.exe (PID: 8076)
- slui.exe (PID: 7488)
- slui.exe (PID: 5008)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7292)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 2552)
Checks proxy server information
- slui.exe (PID: 5008)
Manual execution by a user
- powershell.exe (PID: 7636)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 5508)
- powershell.exe (PID: 3300)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7636)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 7292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
155
Monitored processes
26
Malicious processes
3
Suspicious processes
1
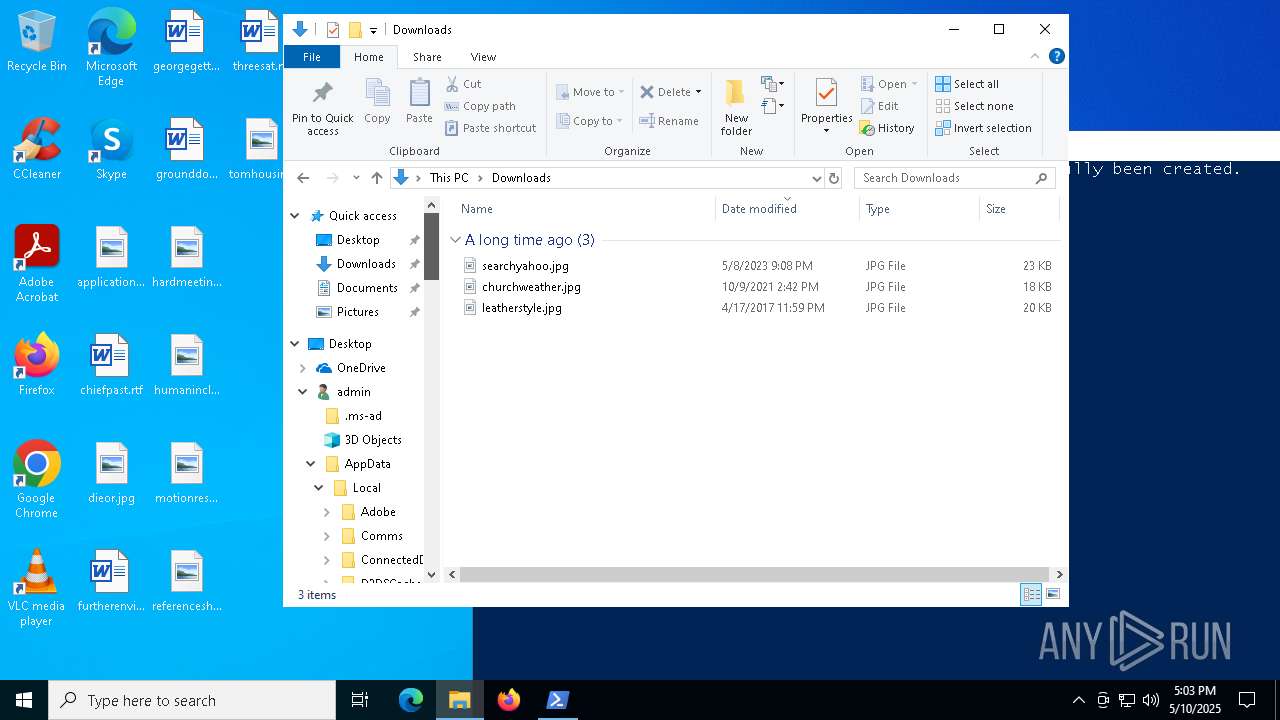
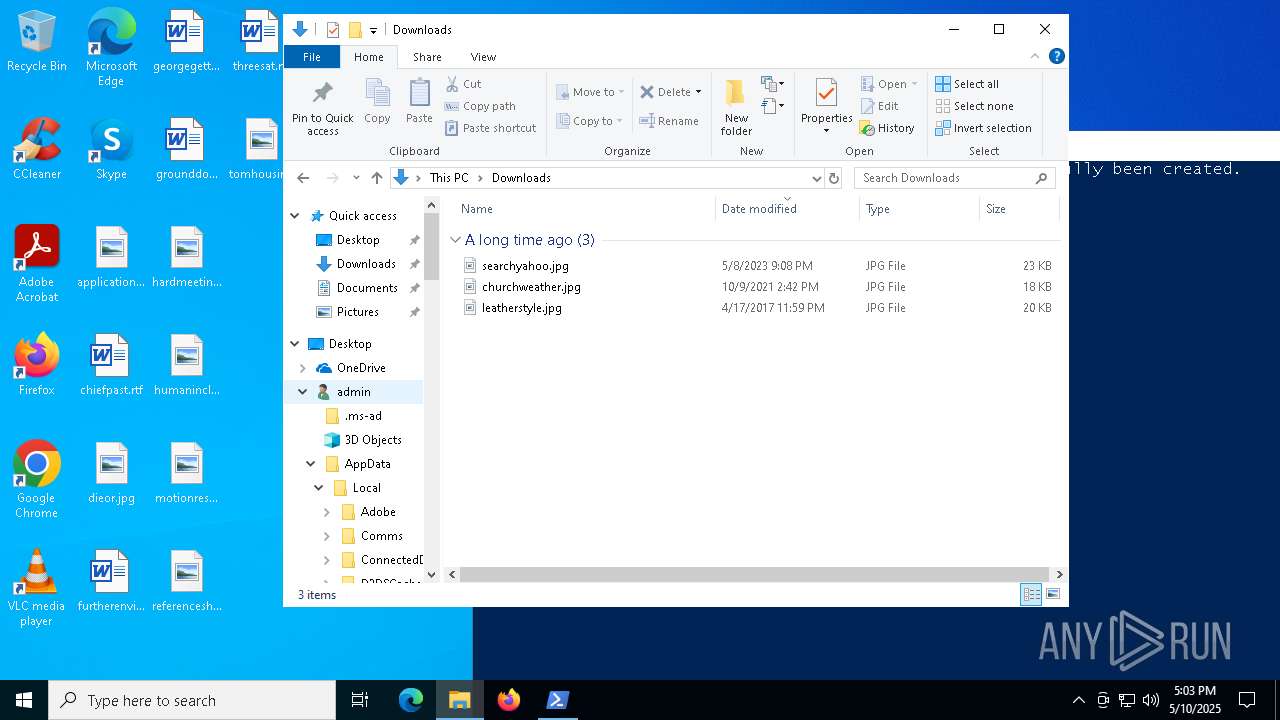
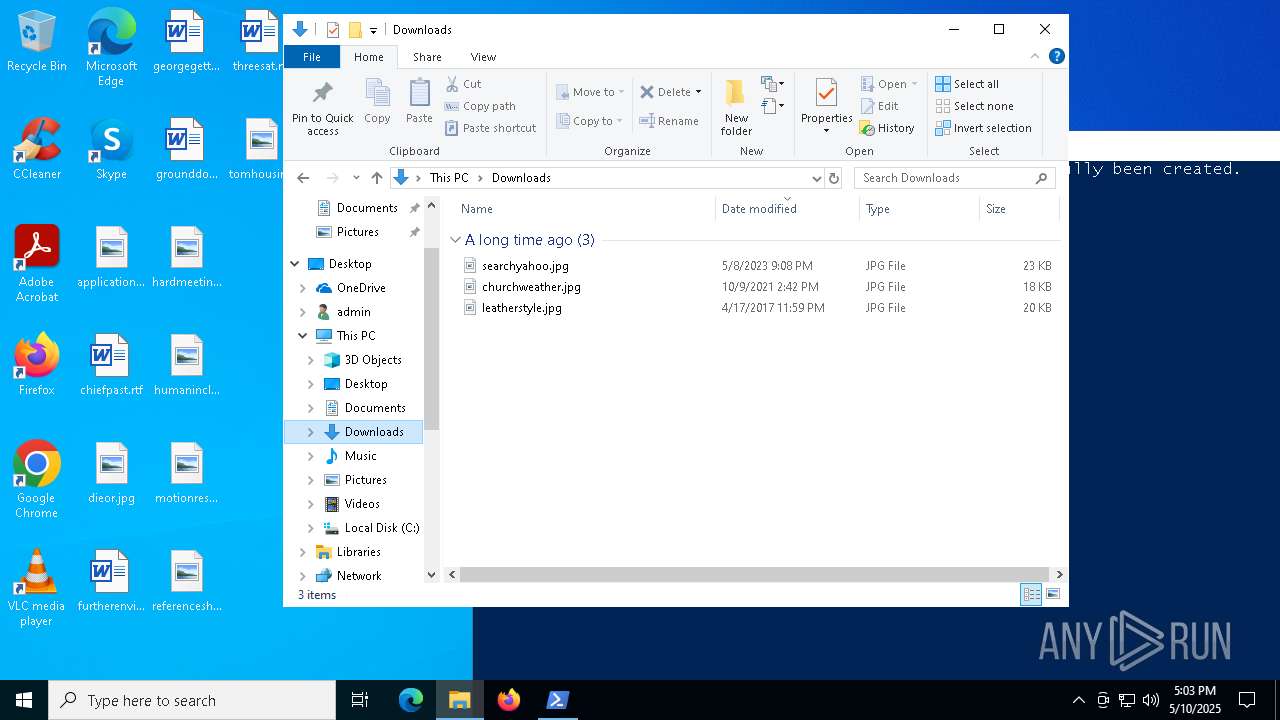
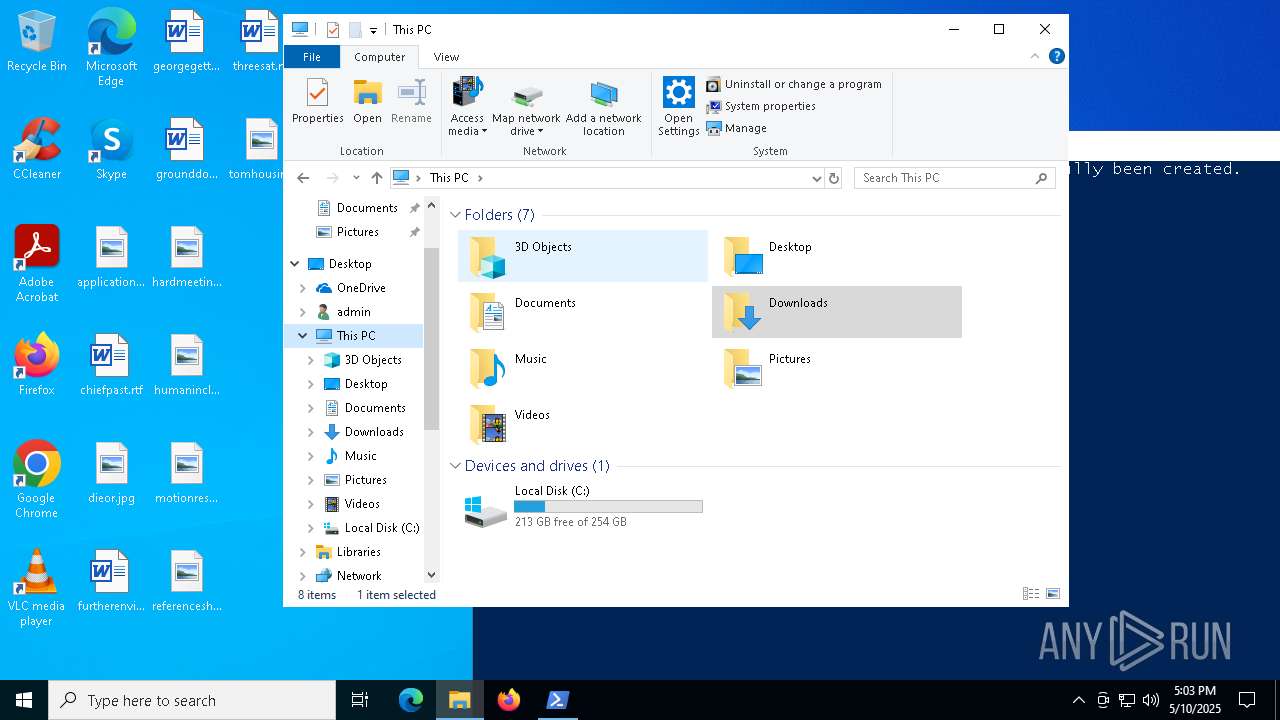
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2332 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
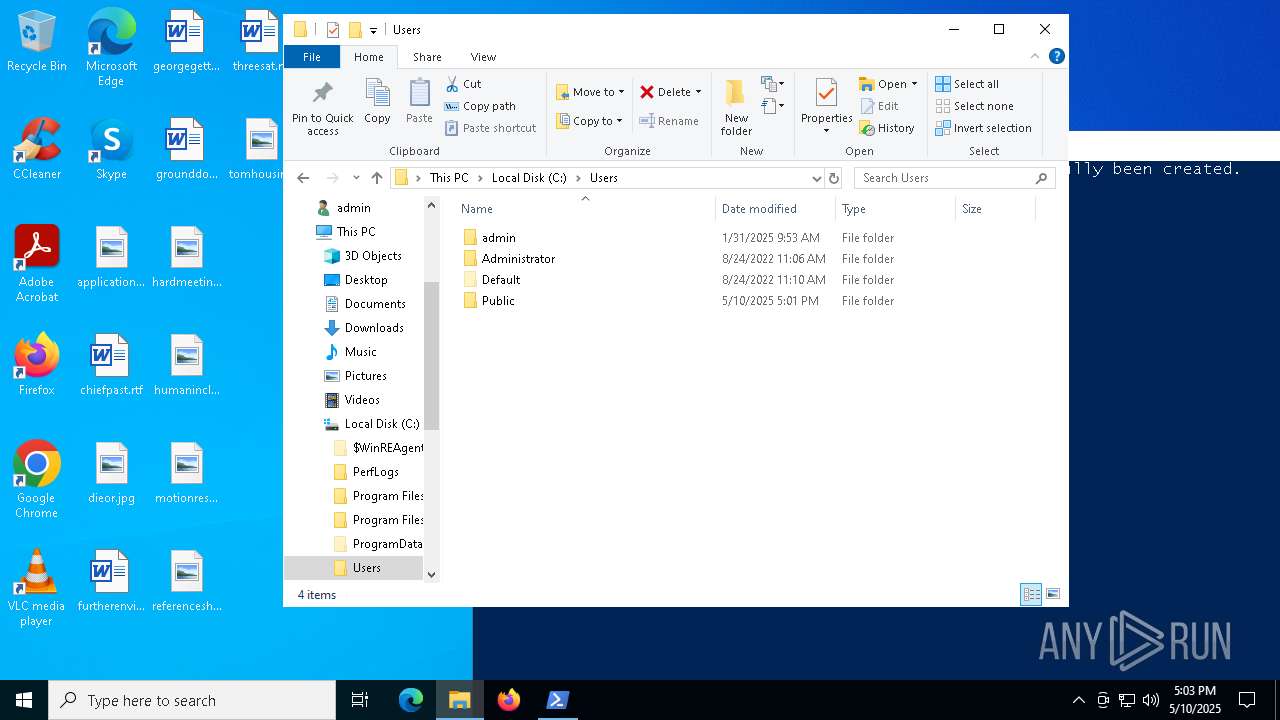
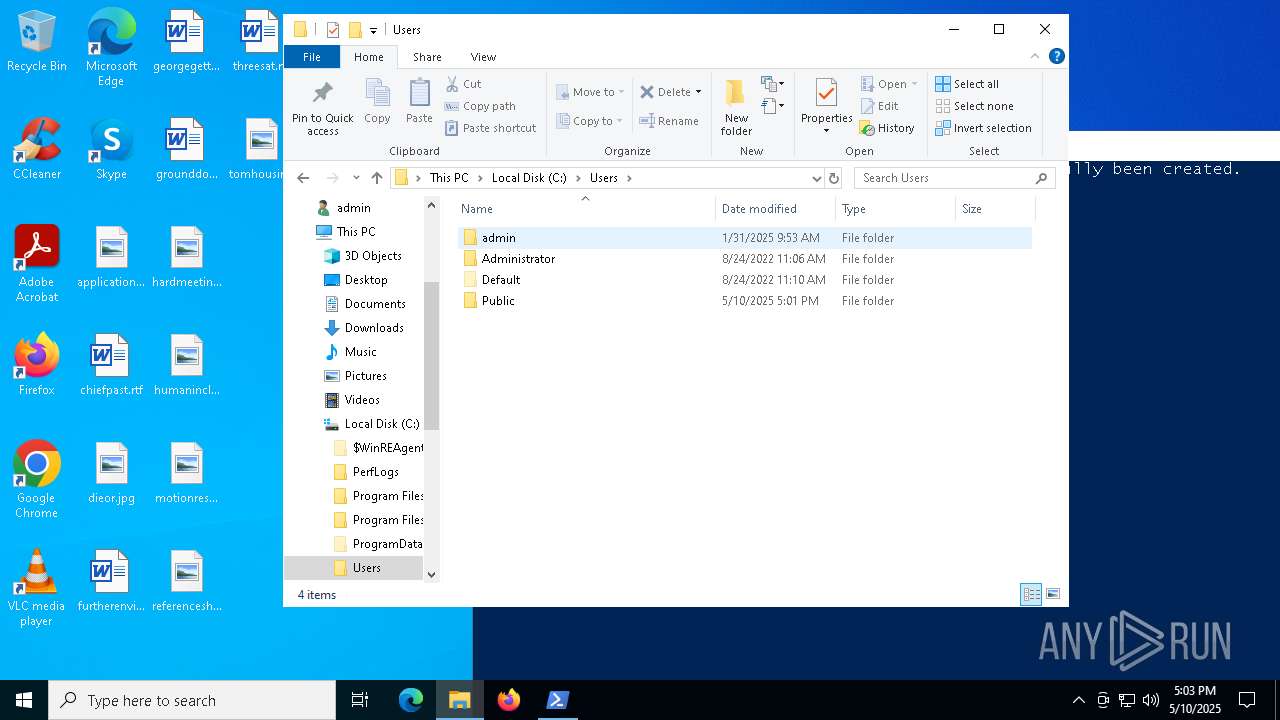
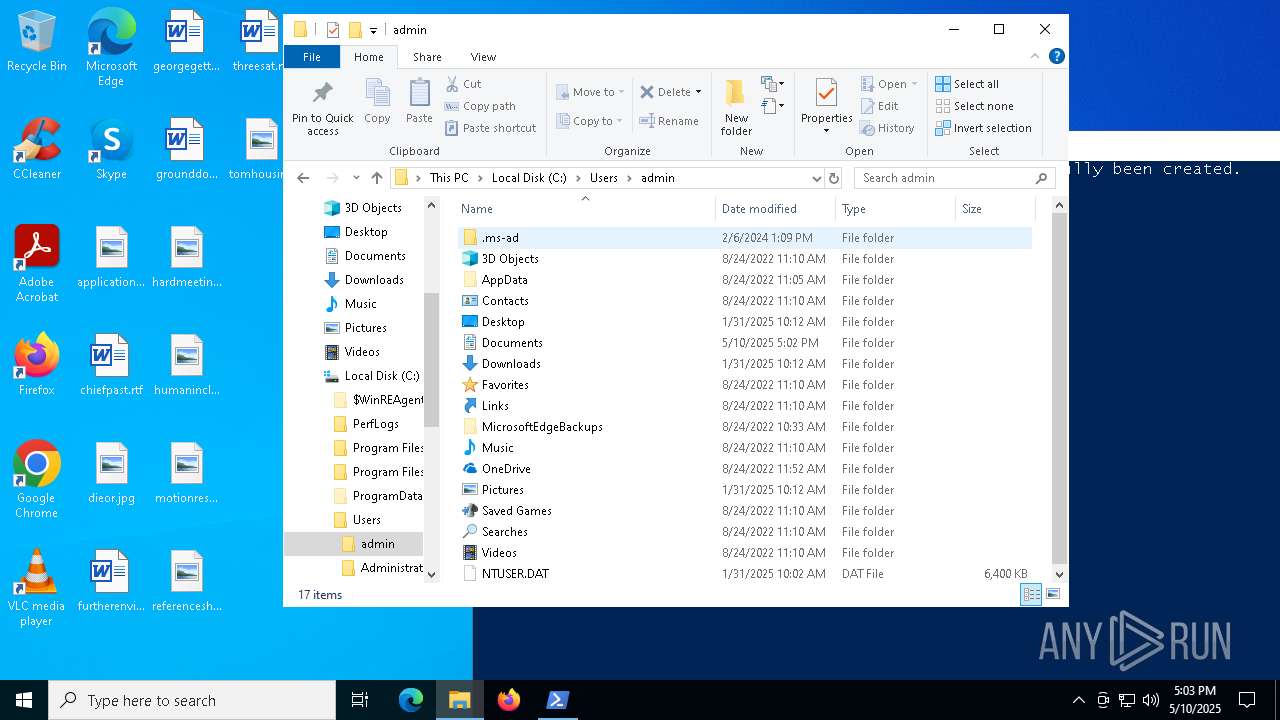
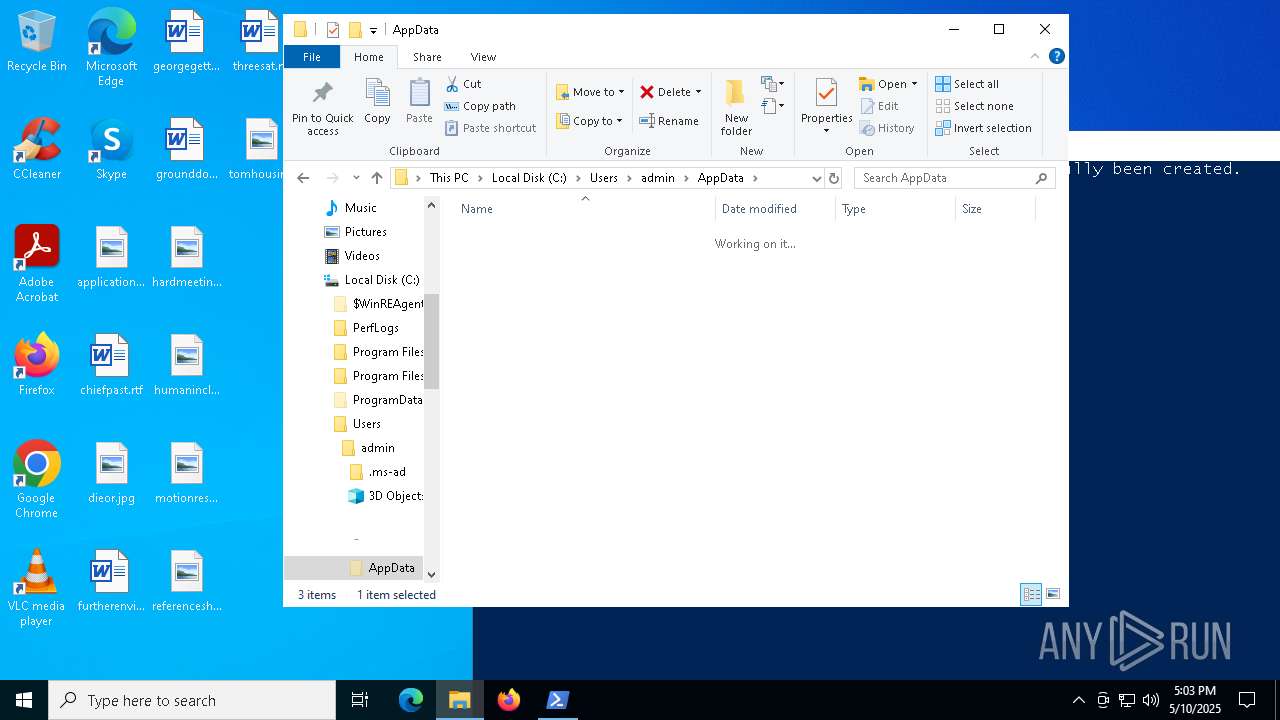
| 2552 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\AppData\Roaming\summary_of_all_books.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3300 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\AppData\Roaming\summary_of_all_books.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5408 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5508 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\AppData\Roaming\summary_of_all_books.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
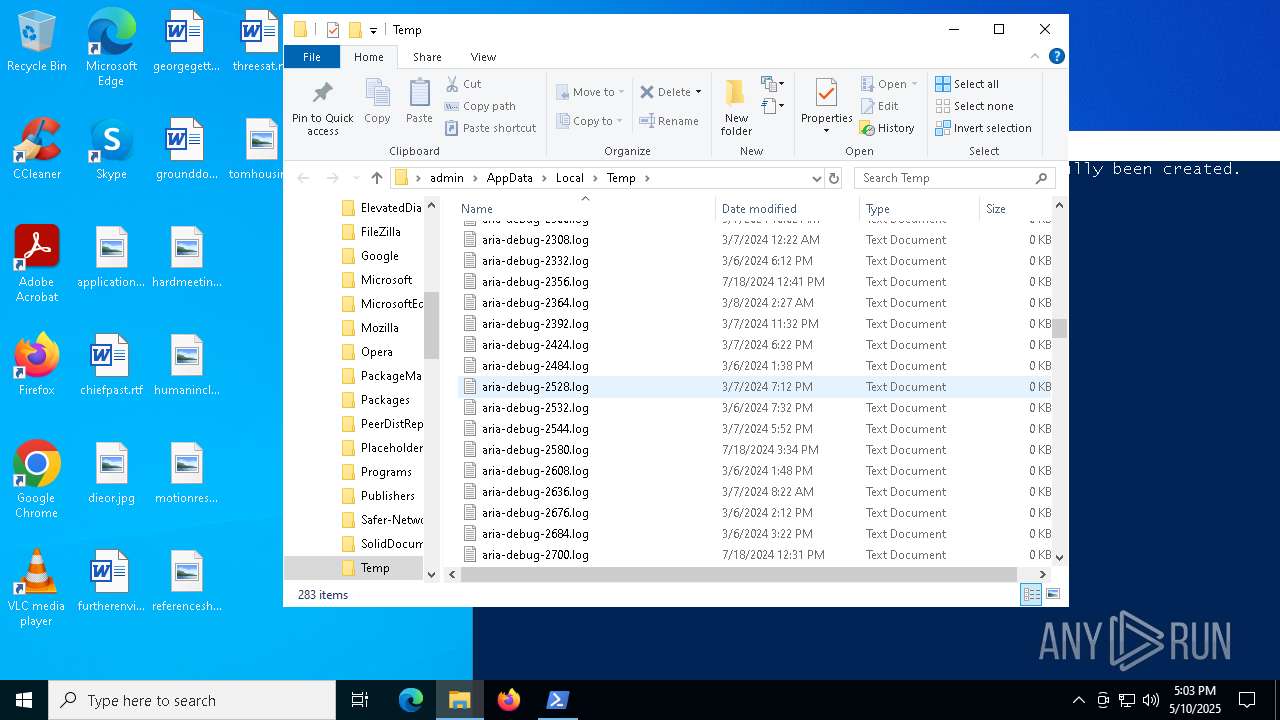
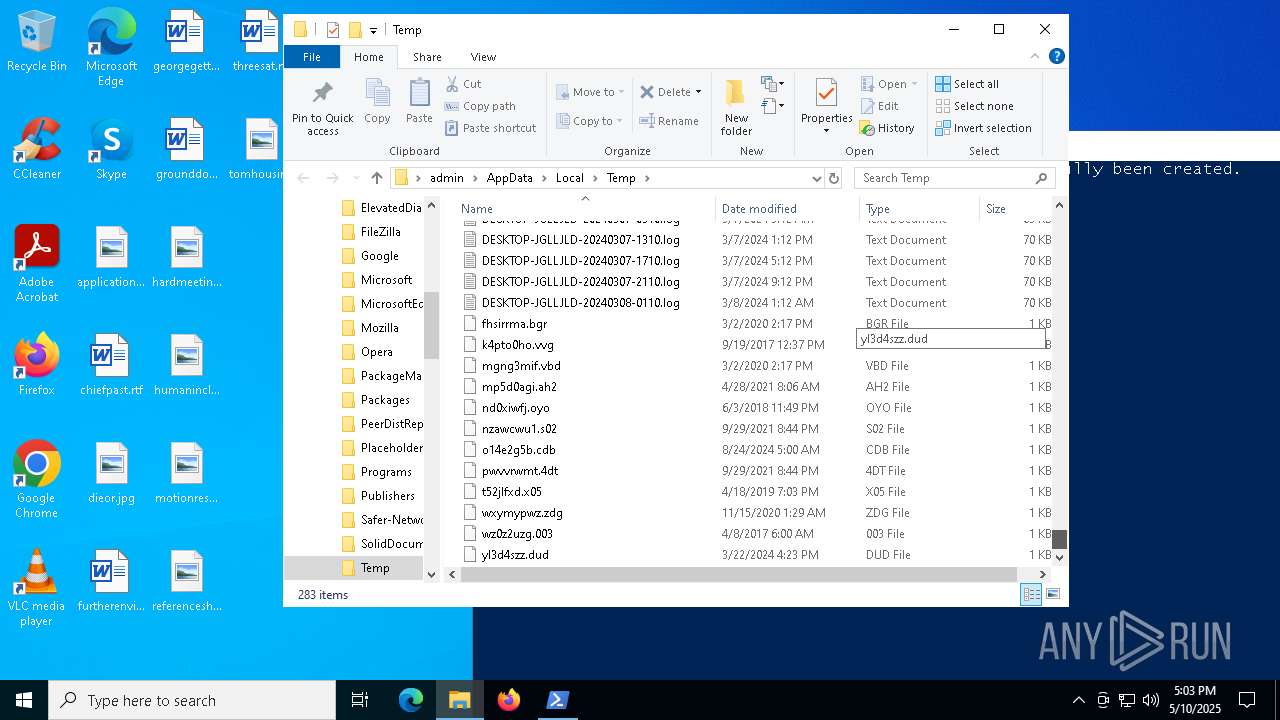
Total events
27 693
Read events
27 693
Write events
0
Delete events
0
Modification events
Executable files
0
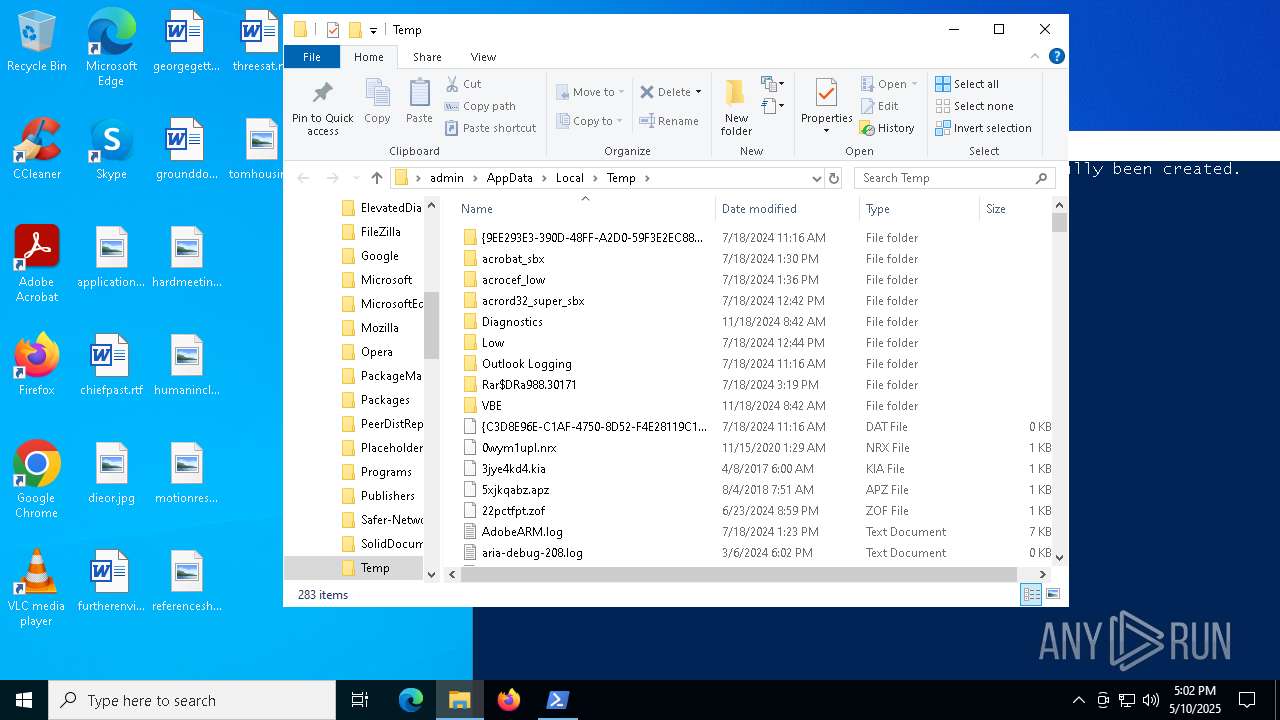
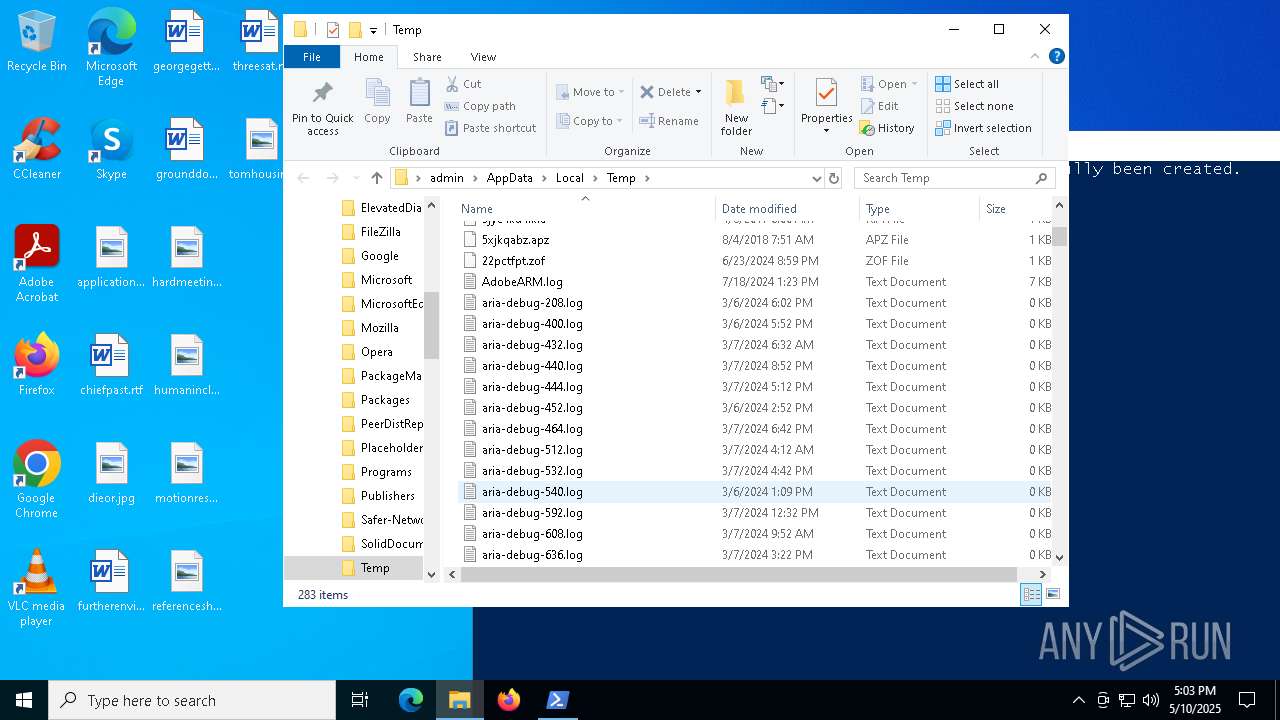
Suspicious files
16
Text files
14
Unknown types
0
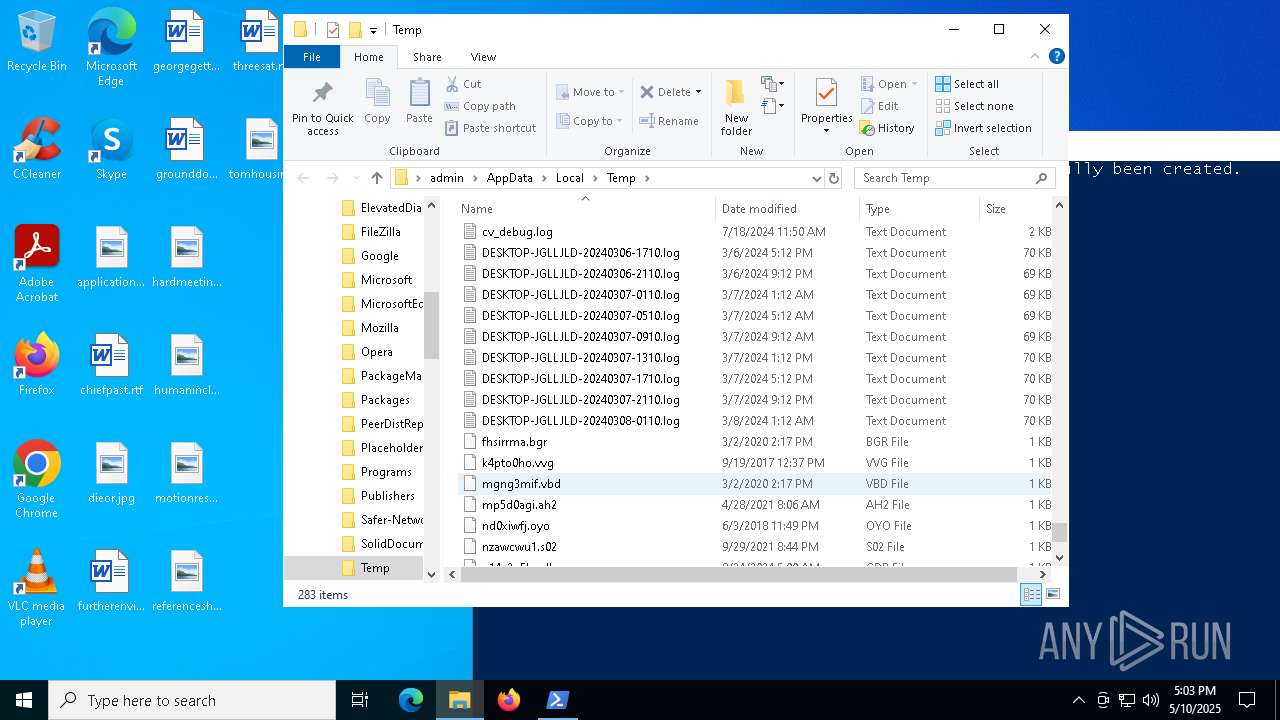
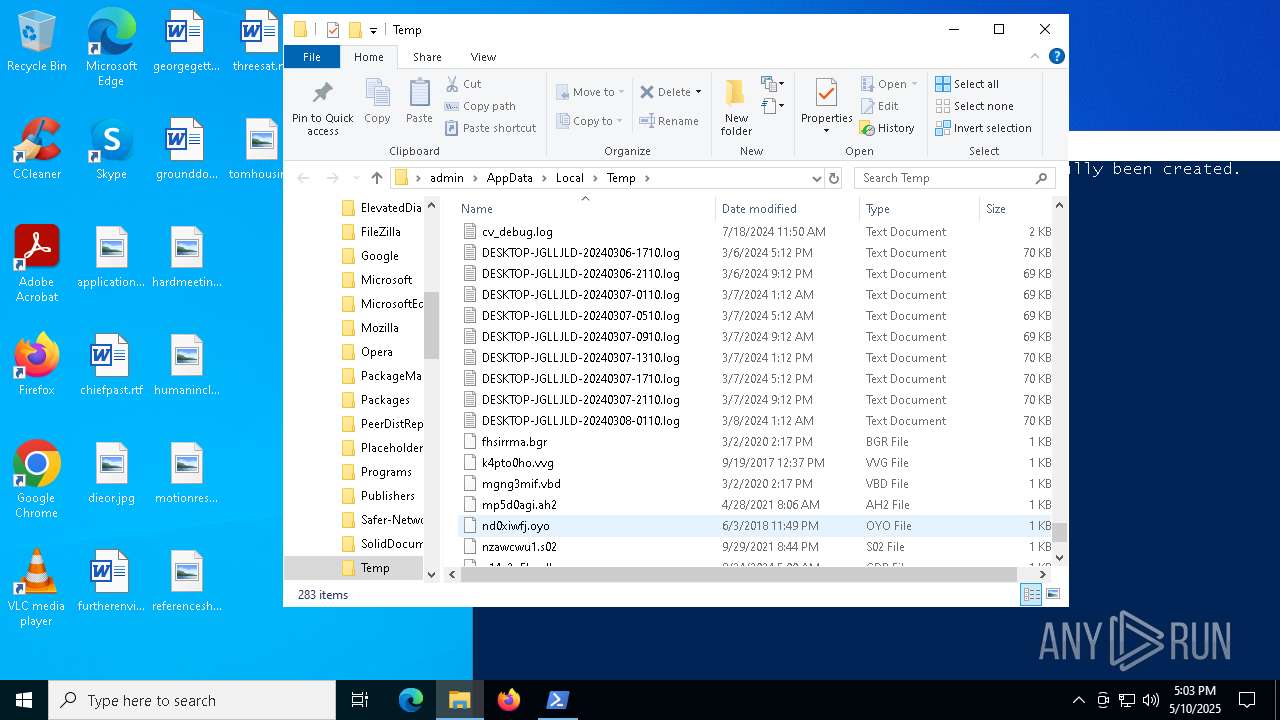
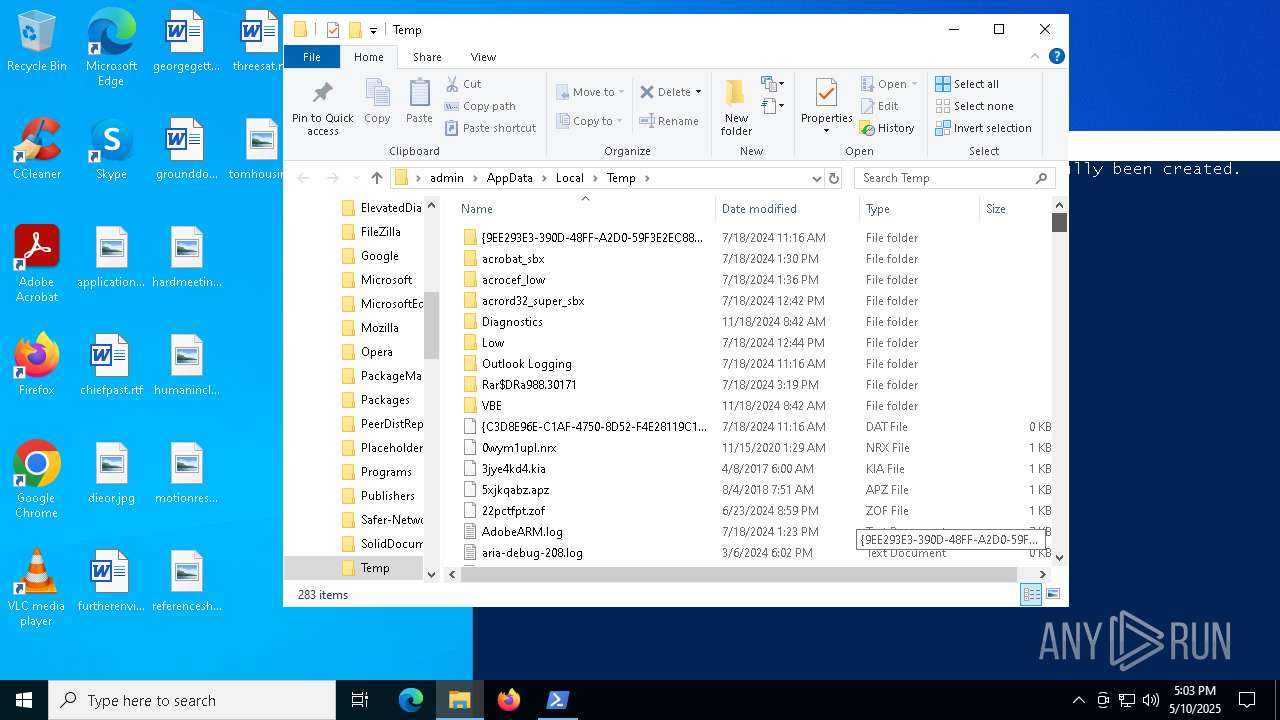
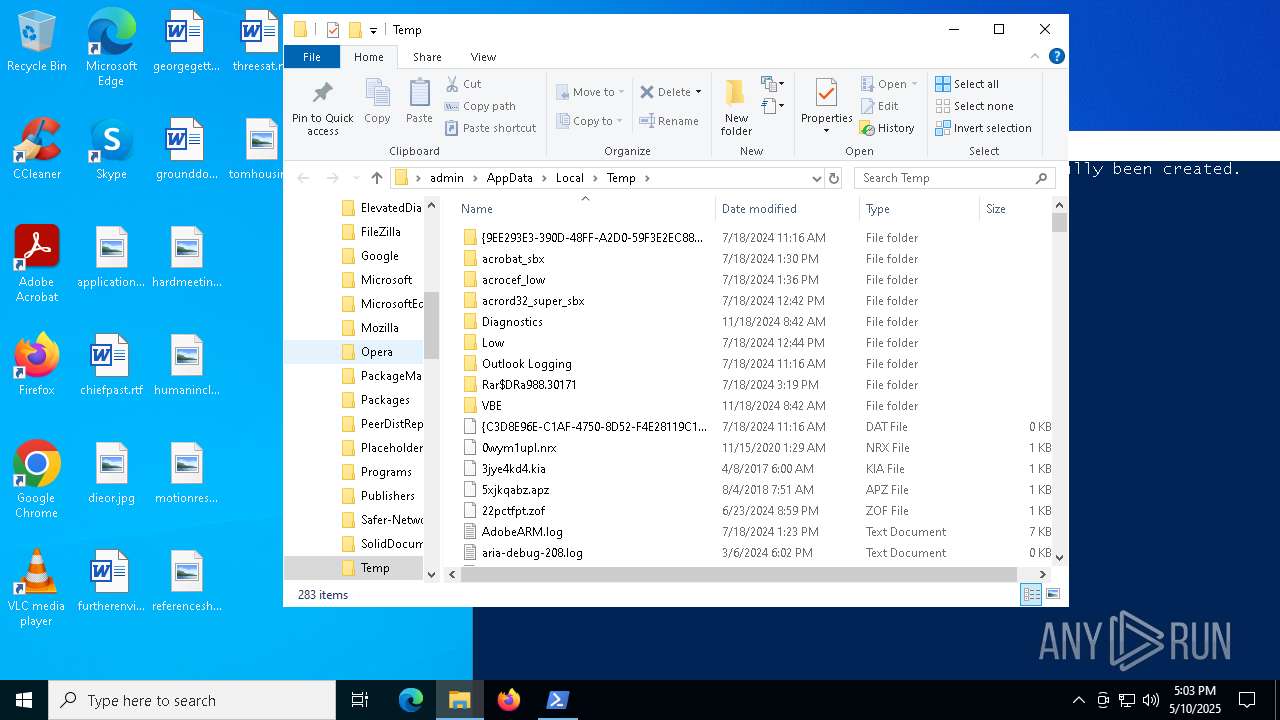
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
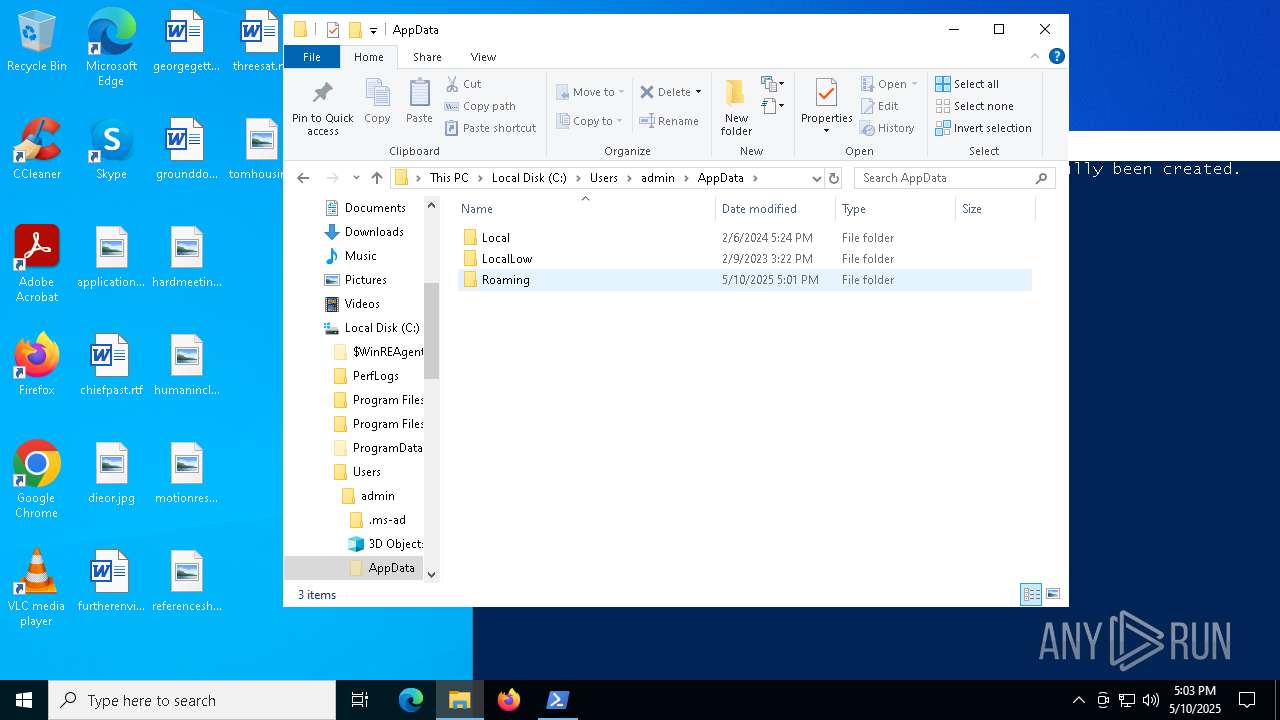
| 7292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:48FF5D4E11DE3A041DC21A74AFDD2265 | SHA256:CF7EAE01AEB7D007AB5A53A6A625FE27AAF10FC571C439CCE79D05A8789AD3F7 | |||
| 7292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\04XI0J1KEAF76WH8ALGU.temp | binary | |
MD5:48FF5D4E11DE3A041DC21A74AFDD2265 | SHA256:CF7EAE01AEB7D007AB5A53A6A625FE27AAF10FC571C439CCE79D05A8789AD3F7 | |||
| 7292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10bc5c.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7636 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1WR8ND3S8CDG58X4Z58S.temp | binary | |
MD5:55E5F158D4381EFF30BD850B466F7862 | SHA256:9B9D86F2AD5A9A8B61A6A3BF4452E5AF1C30EEA0BF43BEEF6CF557BC5D7D56F4 | |||
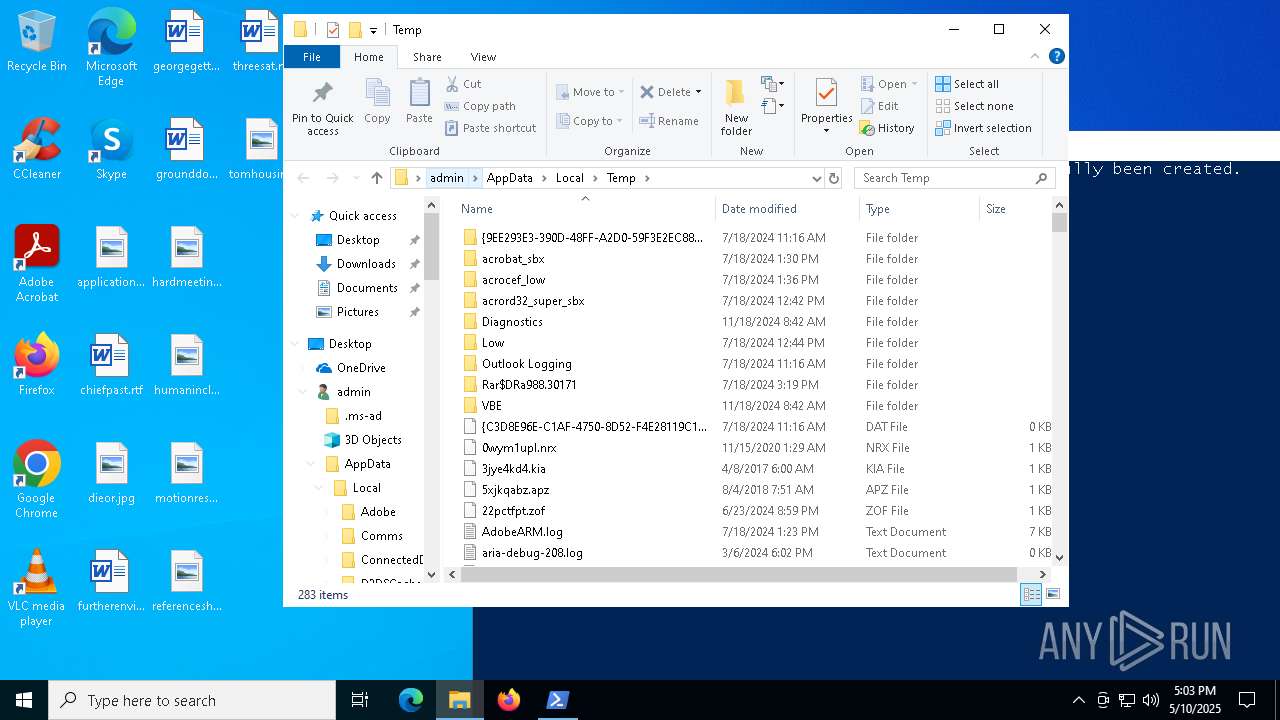
| 7292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fu2jq1po.lxu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7636 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_23rzmstu.51c.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bxtrf50s.ouy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7292 | powershell.exe | C:\Users\admin\Documents\OneDriverUpdates\OneDriverUpdates.ps1 | text | |
MD5:F34BC3B7770B97AD02FB0129B6FF237E | SHA256:6756B5D86DF9D04C471A7C288C517B9E29243BA58F59B564CE955A305D50EBC1 | |||
| 7292 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:0E4CC900C654DD0B73641F48E45E7003 | SHA256:7F9C4D4450BA30BC19B041E5047ABA74E42342D7F5D21C5FB9C56AE8E503646A | |||
| 7292 | powershell.exe | C:\Users\admin\Documents\OneDriverUpdates\OneDriverUpdates.xml | xml | |
MD5:72245DF9B76AF86688B539DCD0C8A466 | SHA256:F9955E5AD3E25320FCA9A02B01E0233A6CD5451A3E9BC3ABDE8E5EC294F76EA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
29
DNS requests
32
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5408 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ssosrr.ddns.net |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
8076 | aspnet_compiler.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |