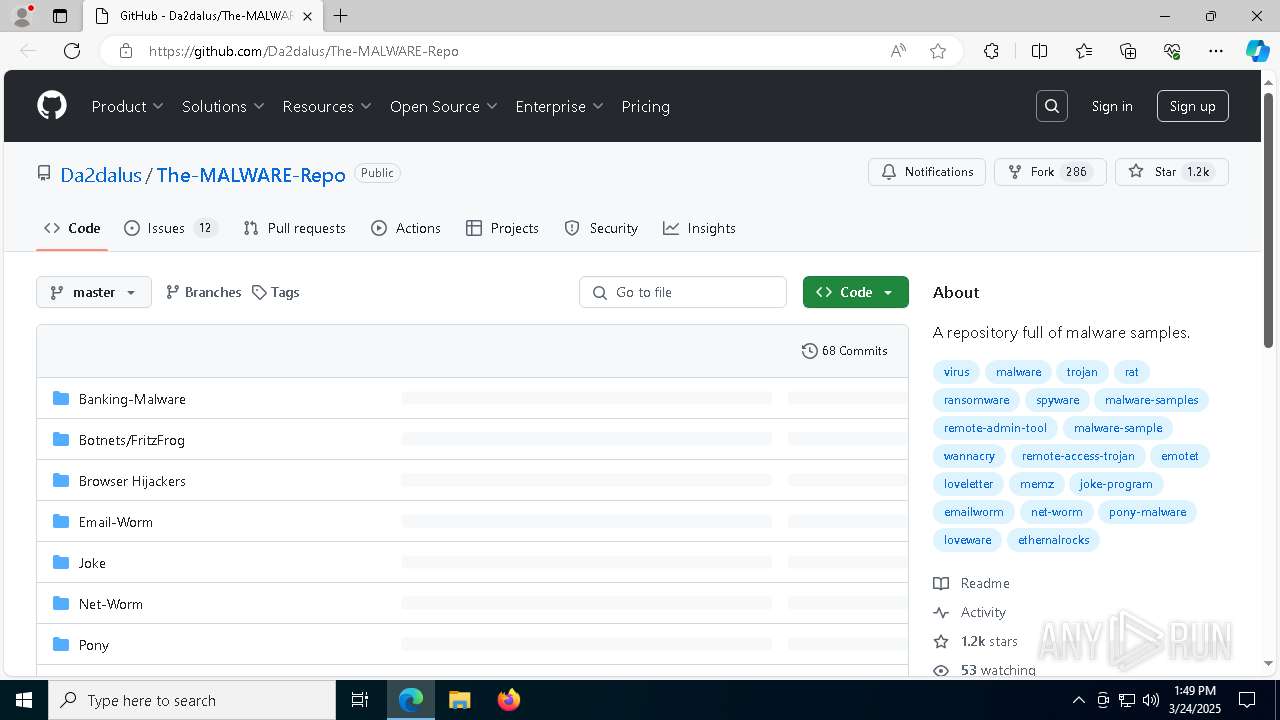
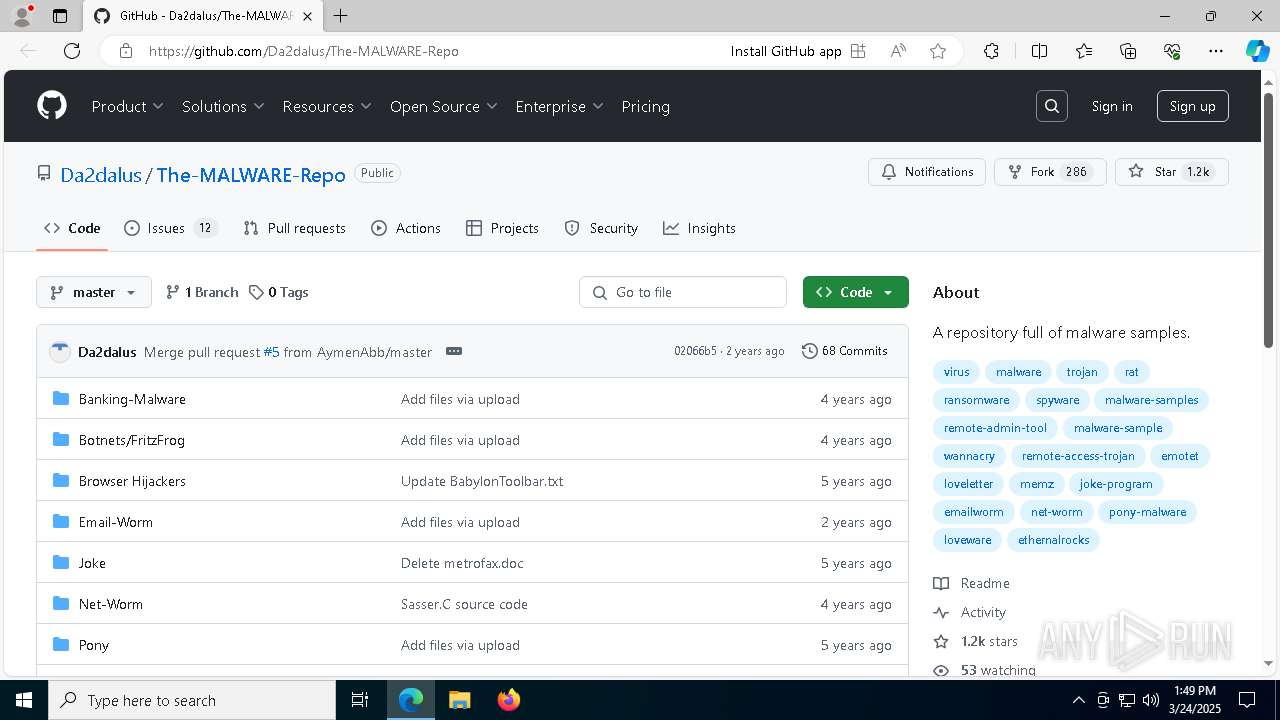
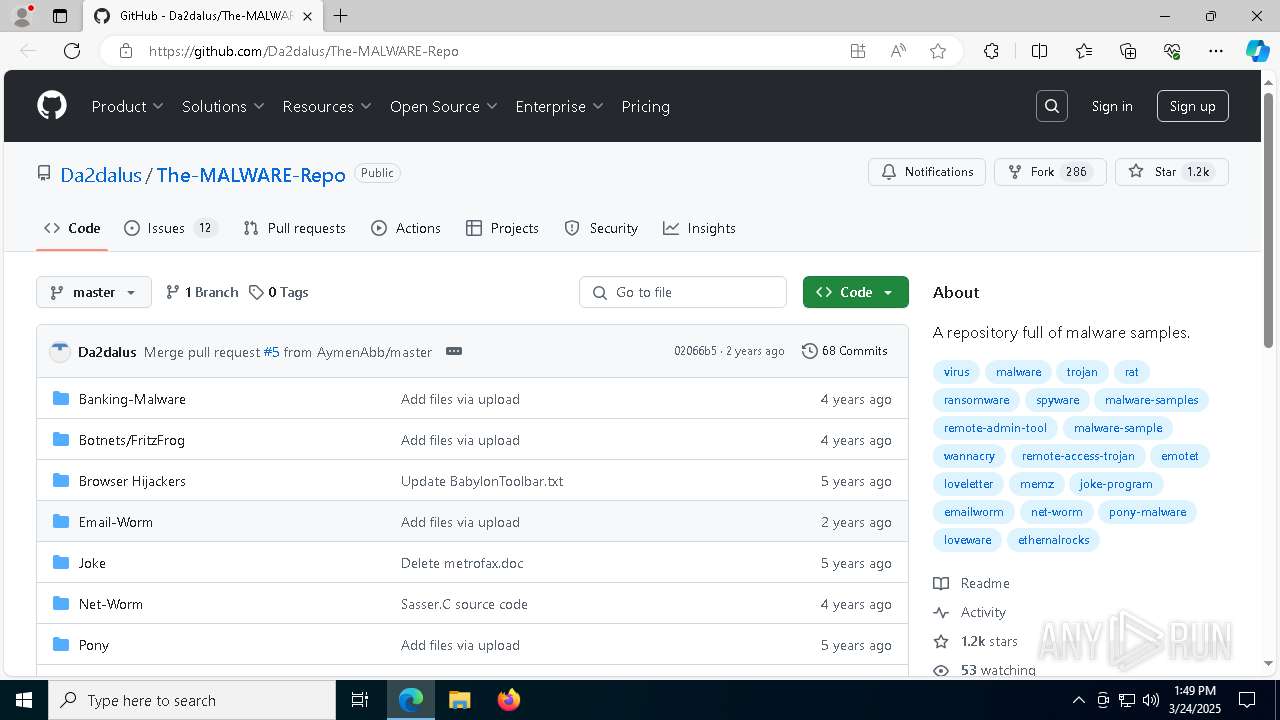
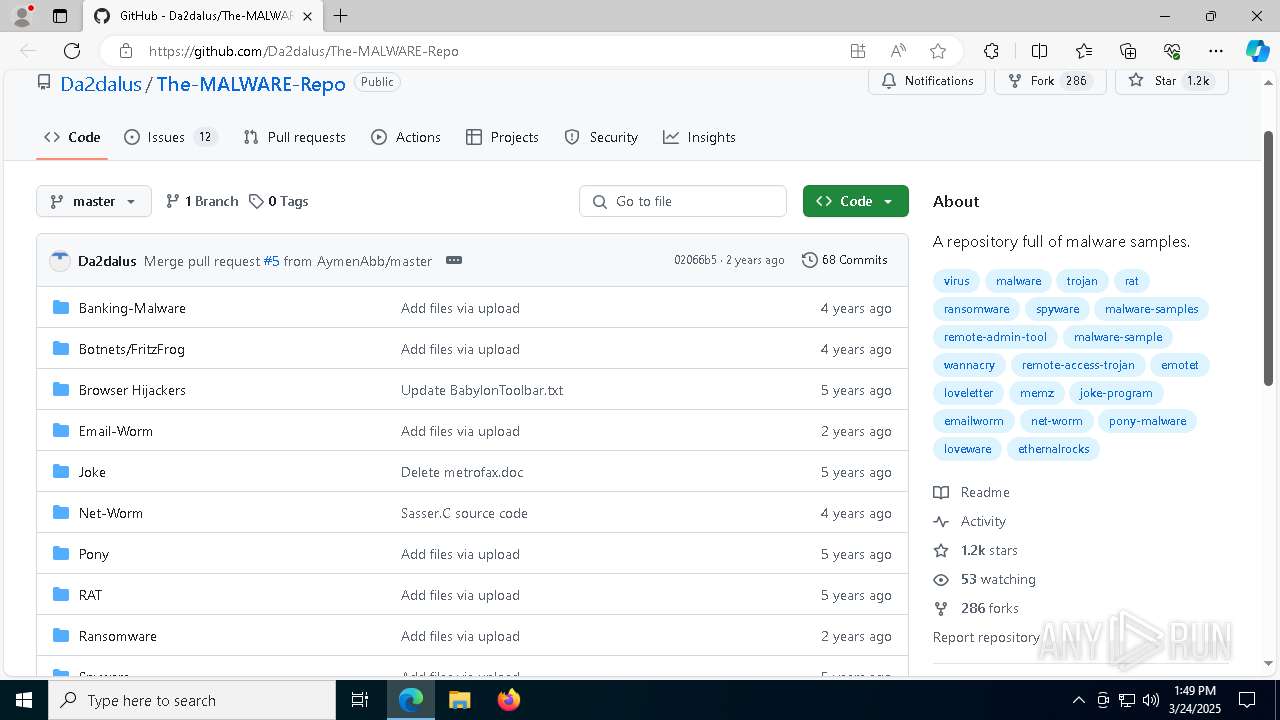
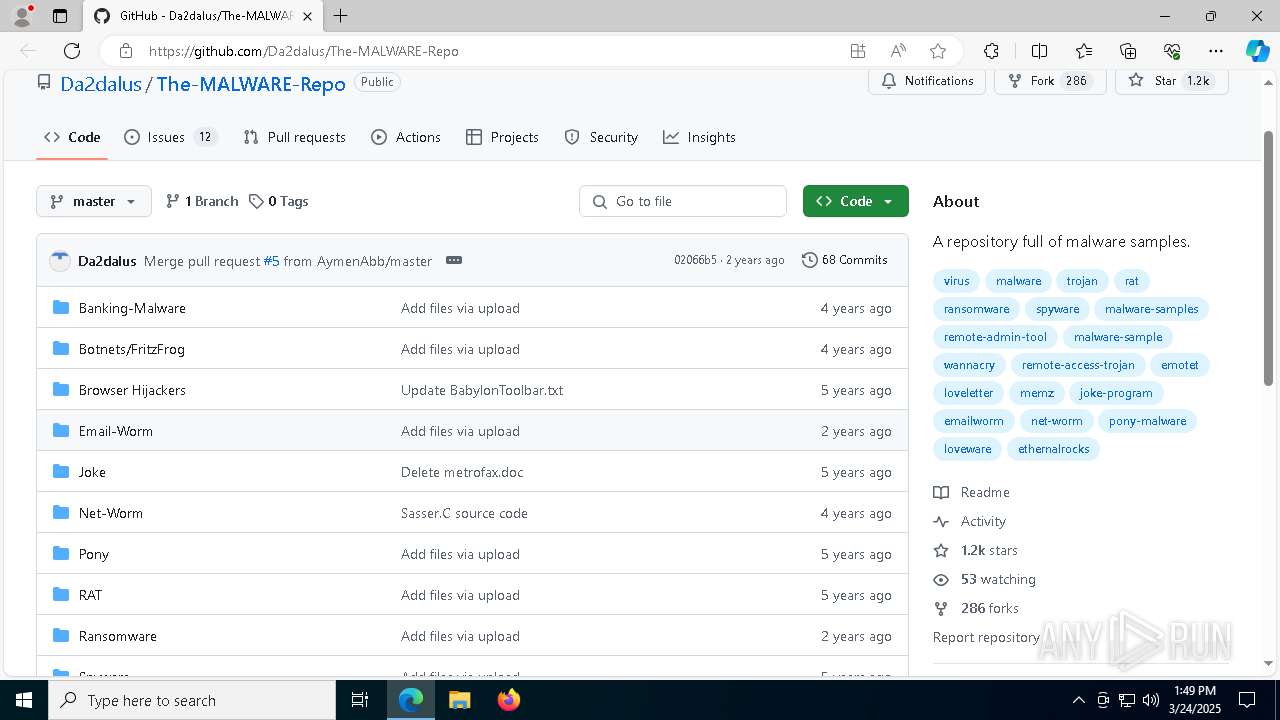
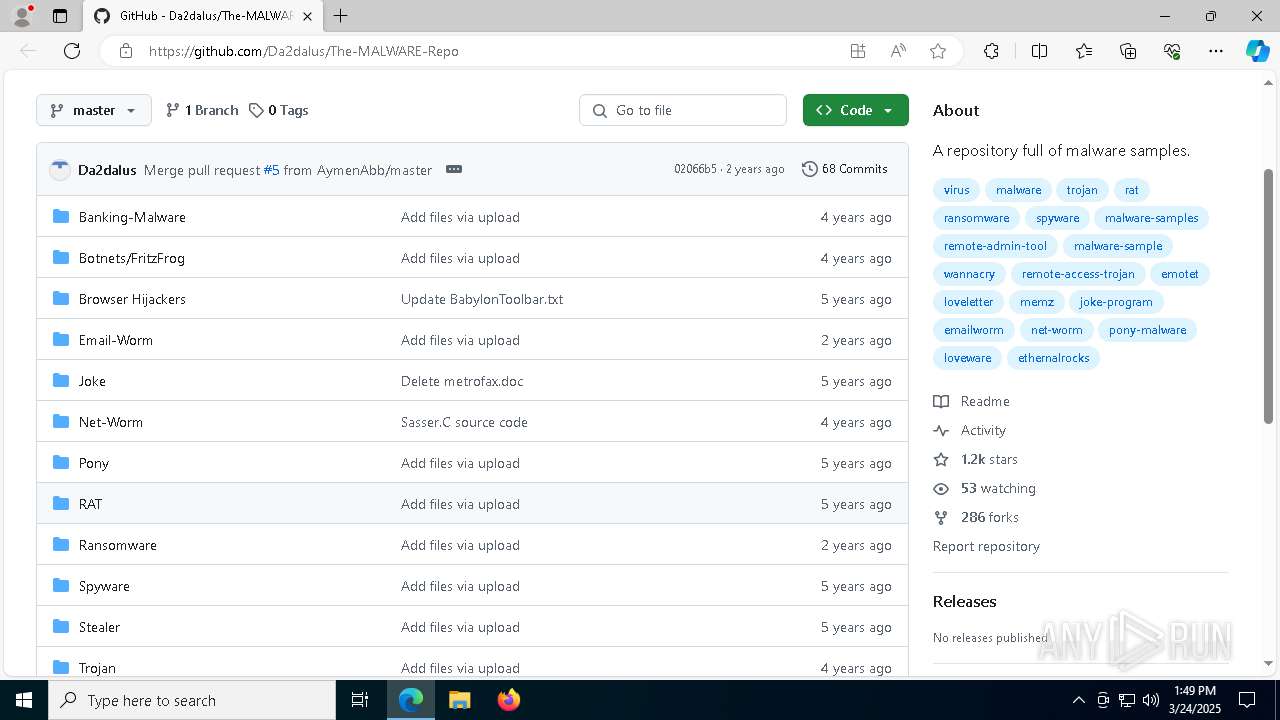
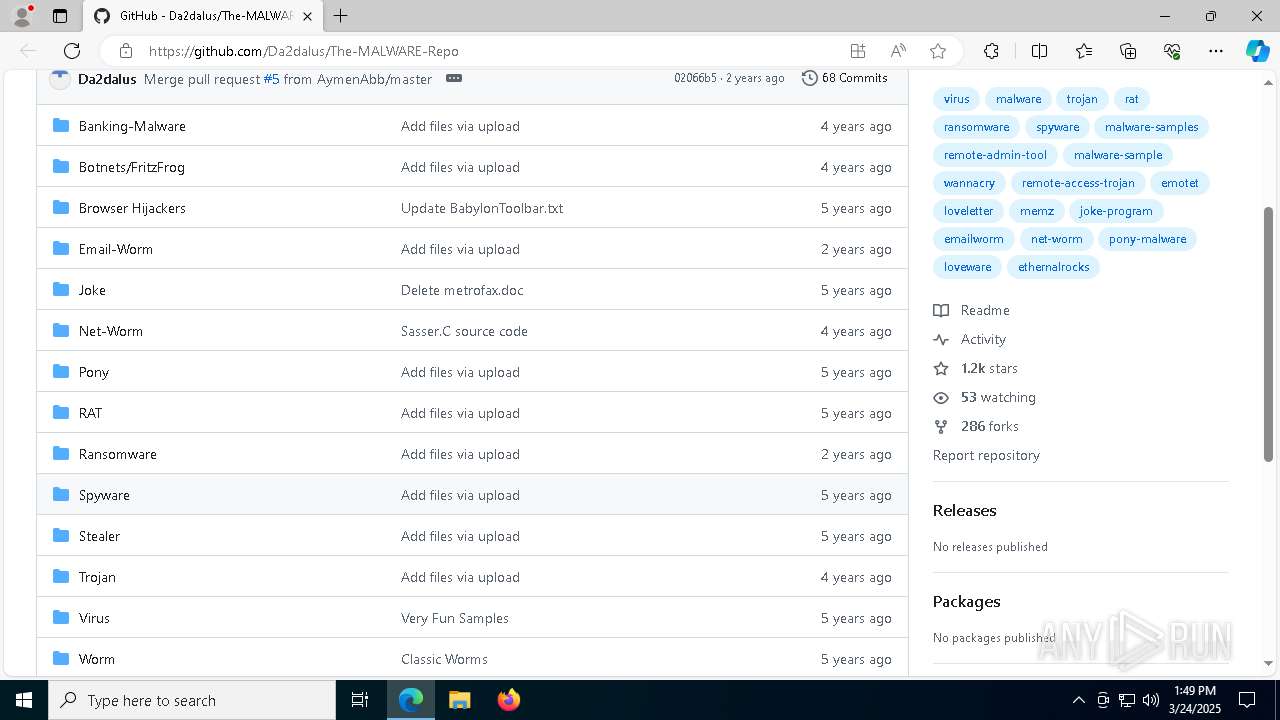
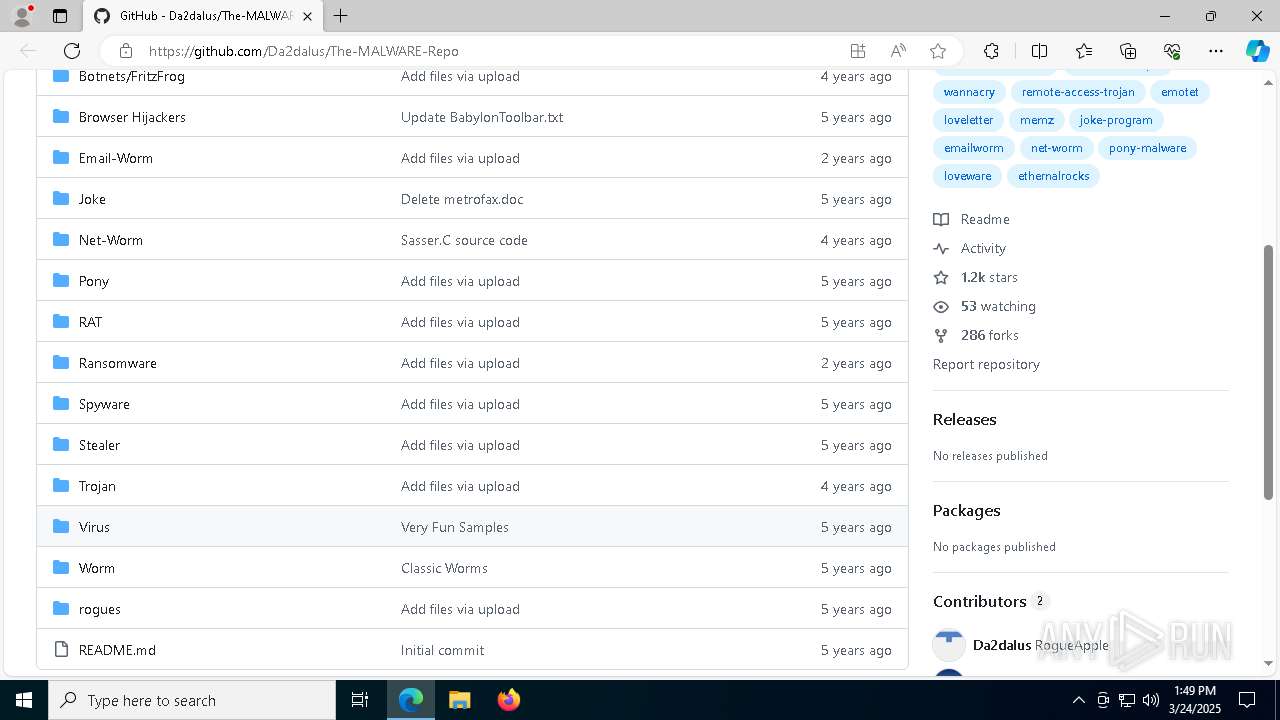
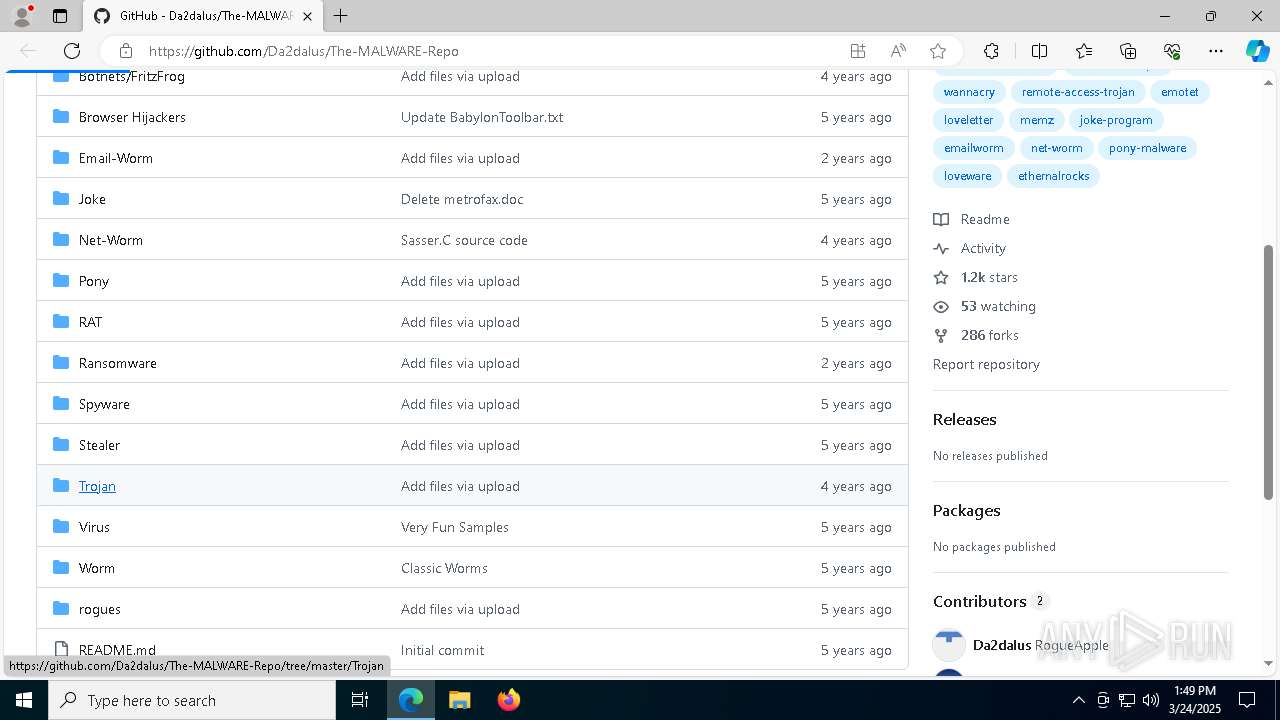
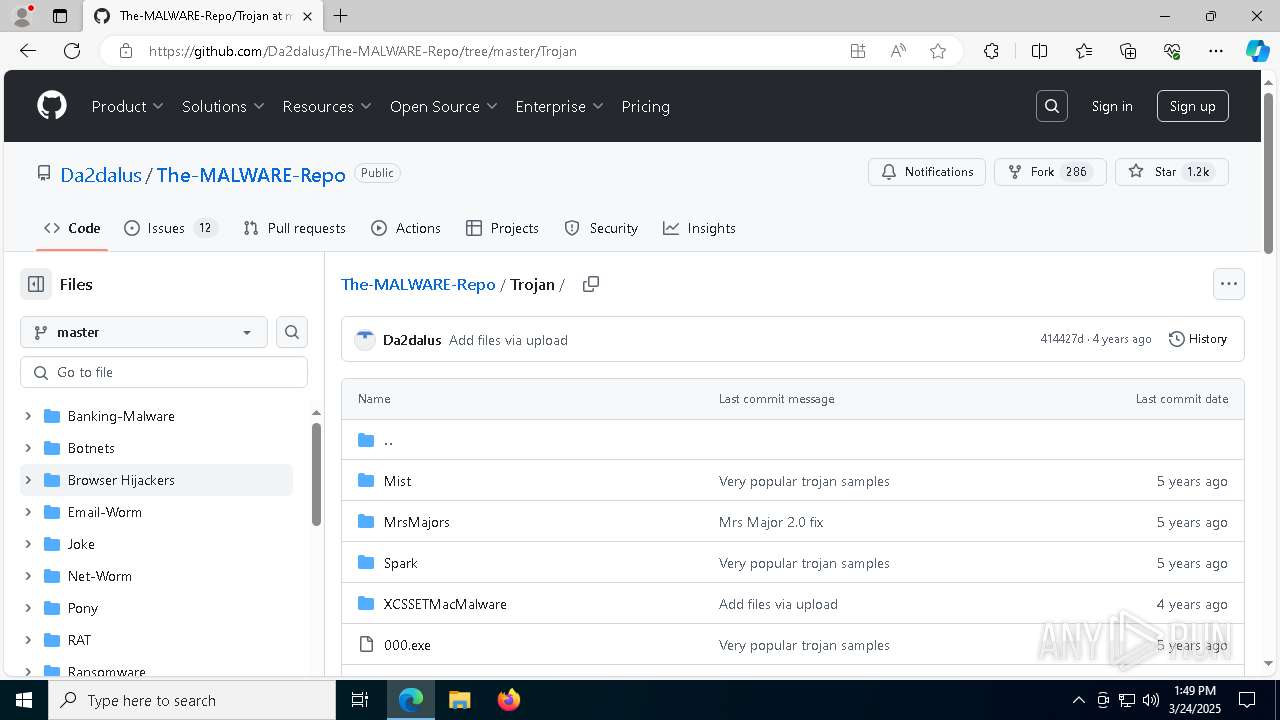
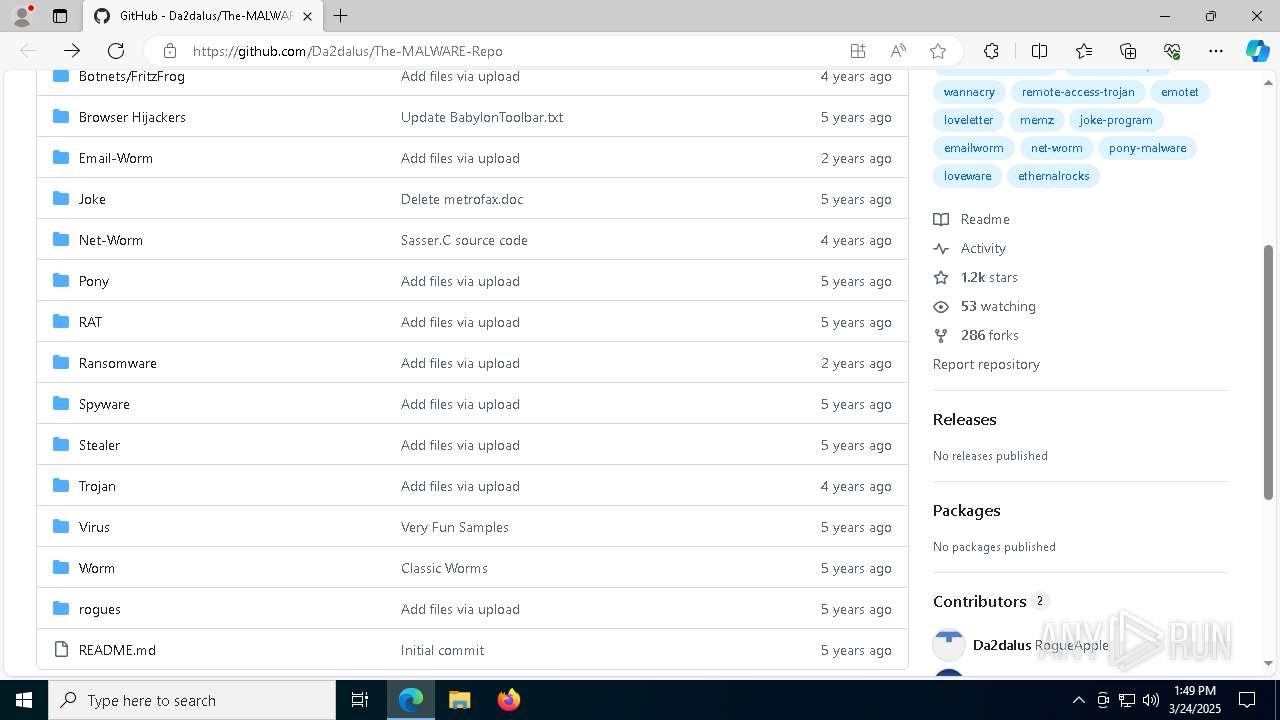
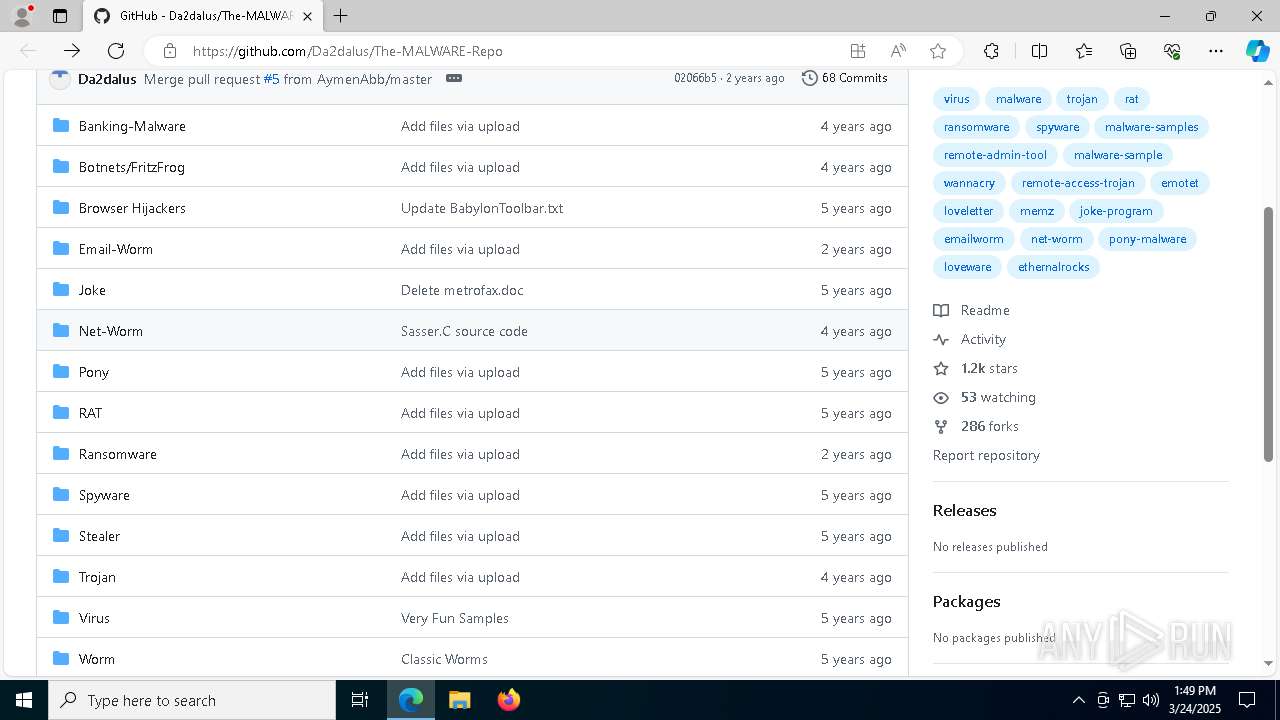
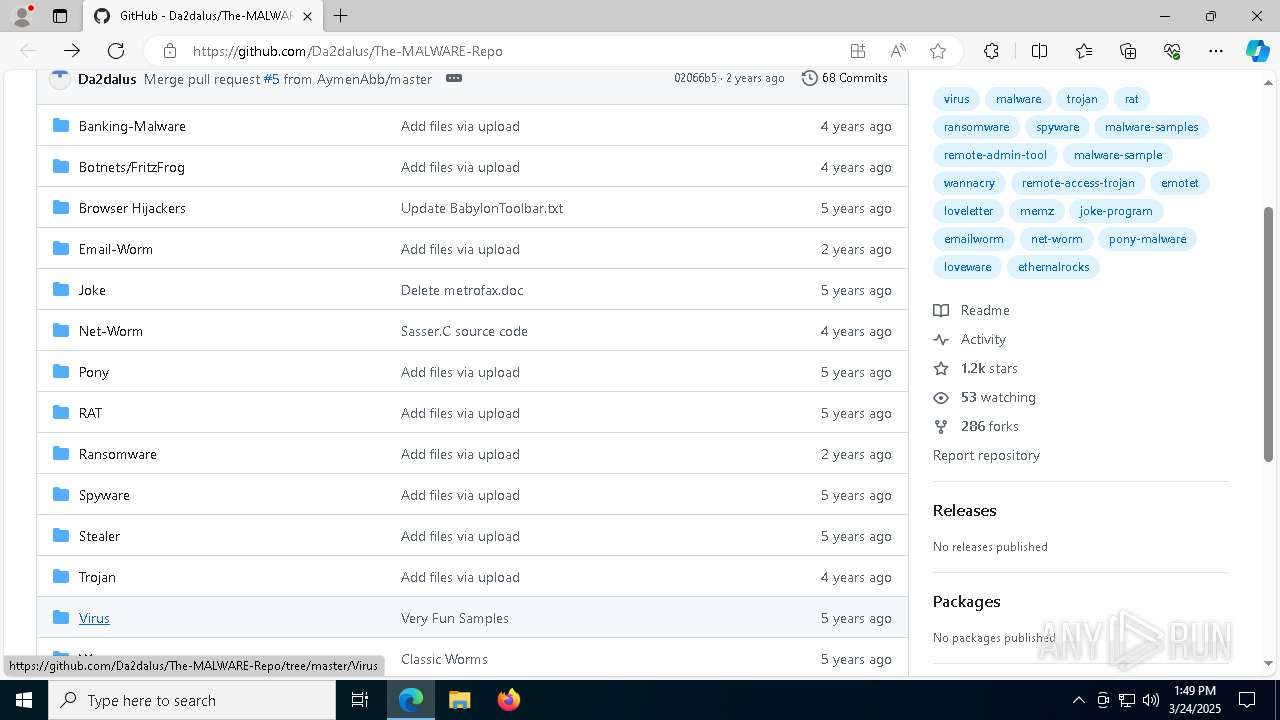
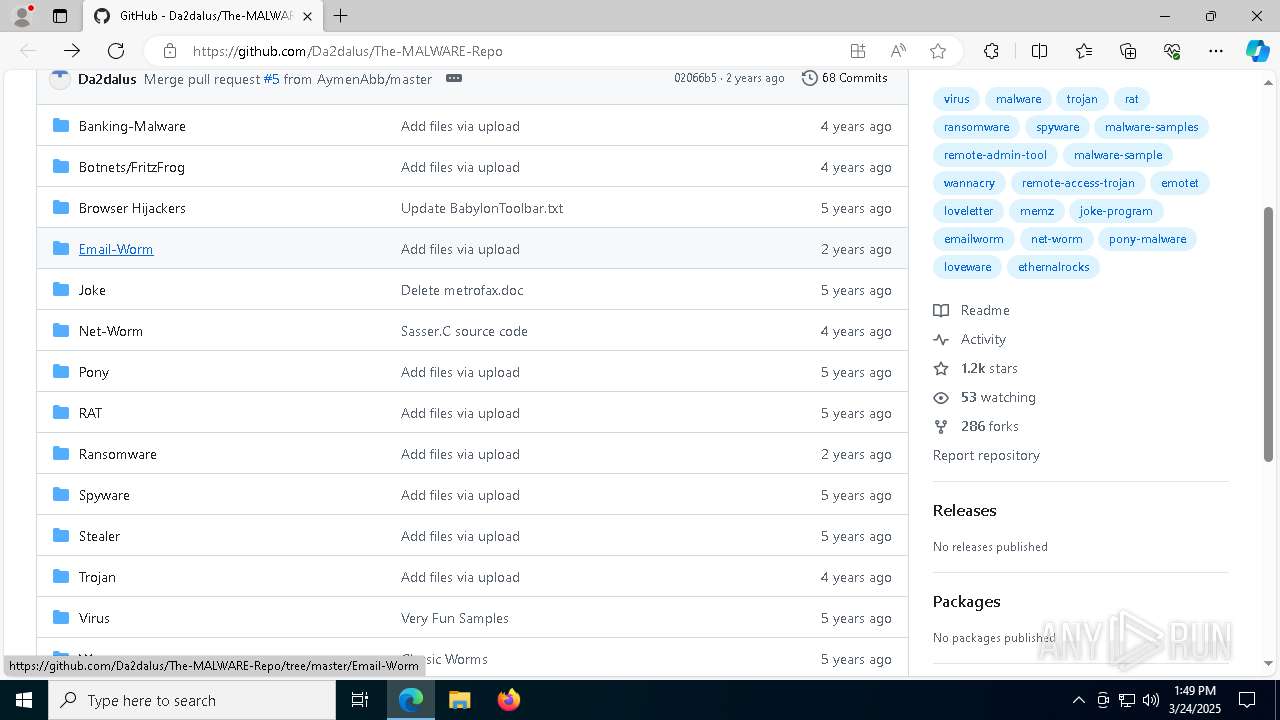
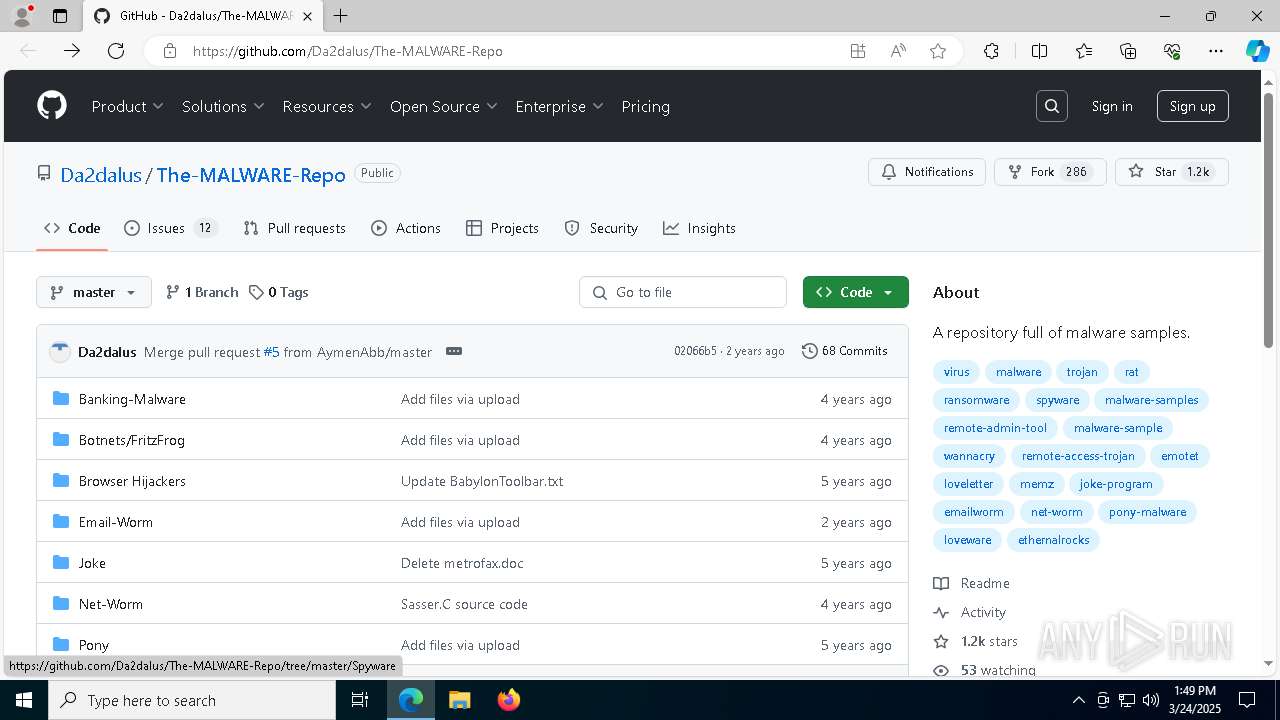
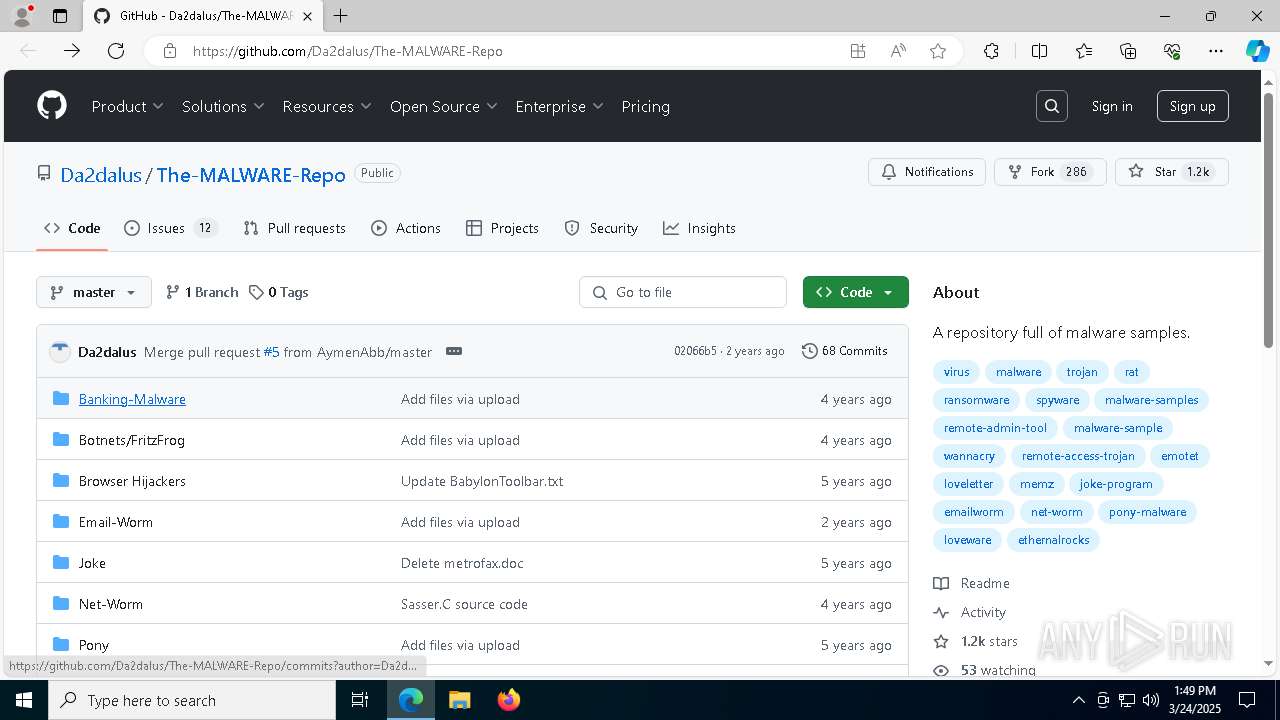
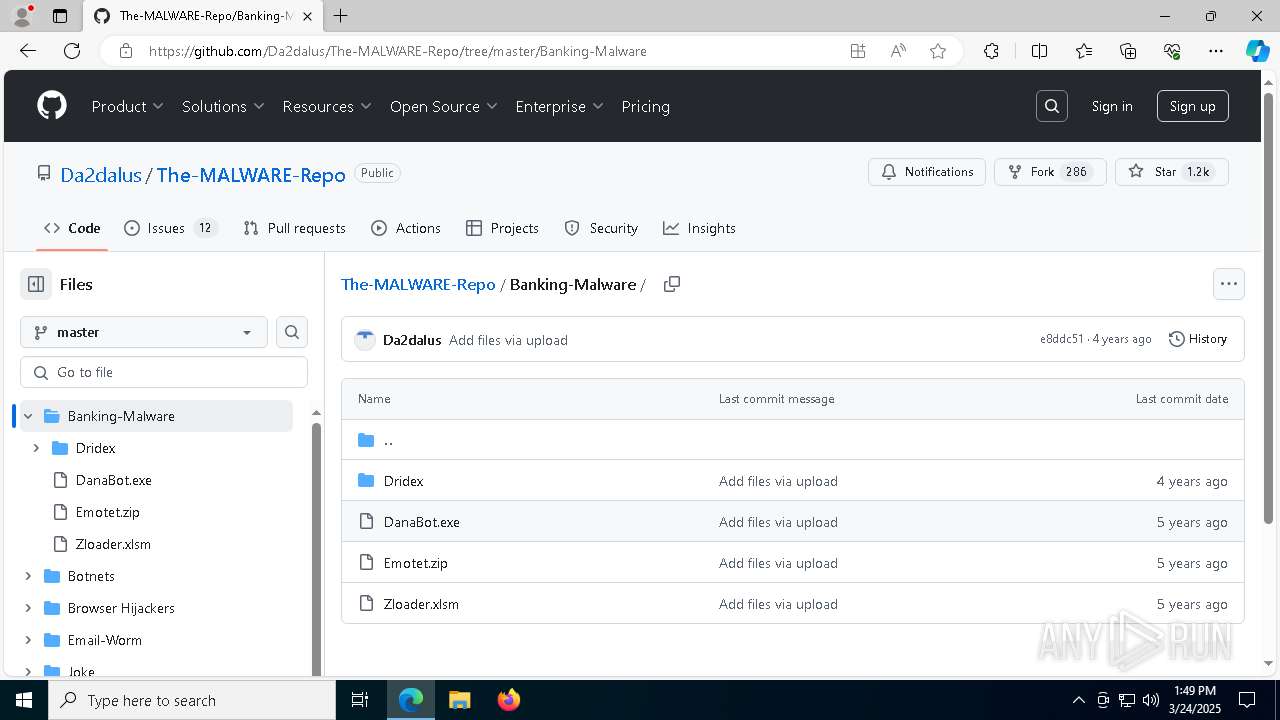
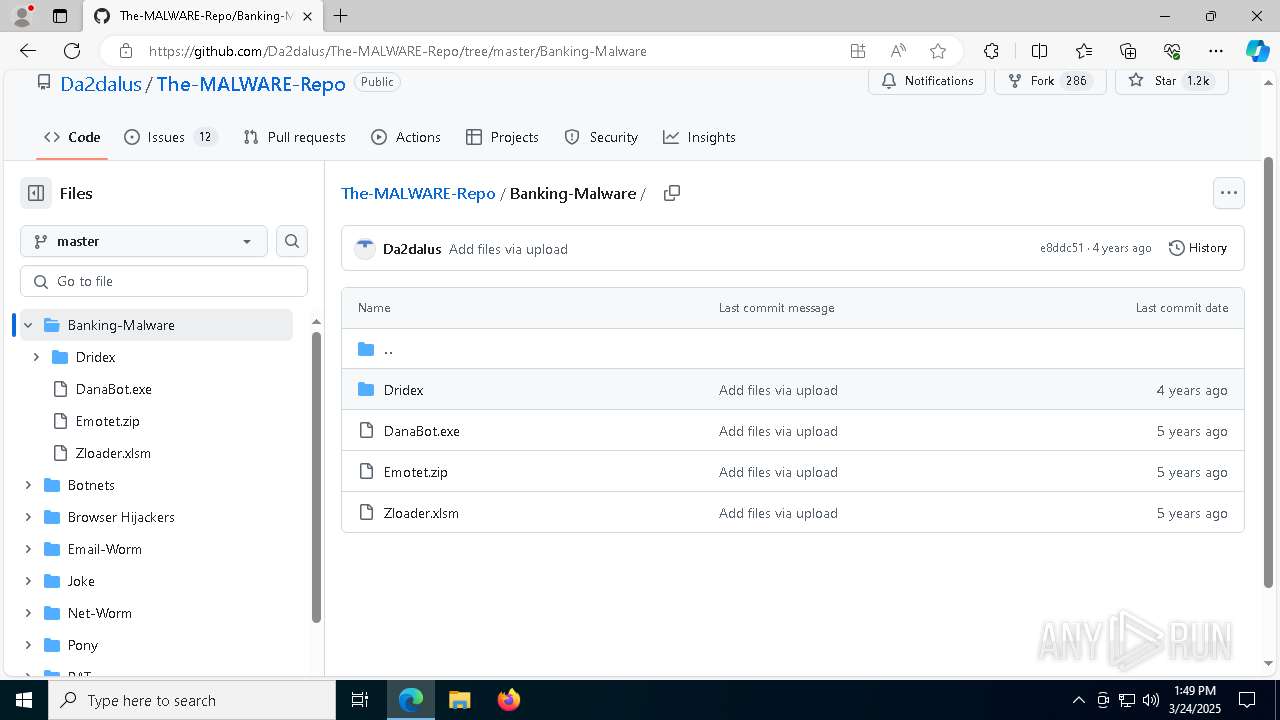
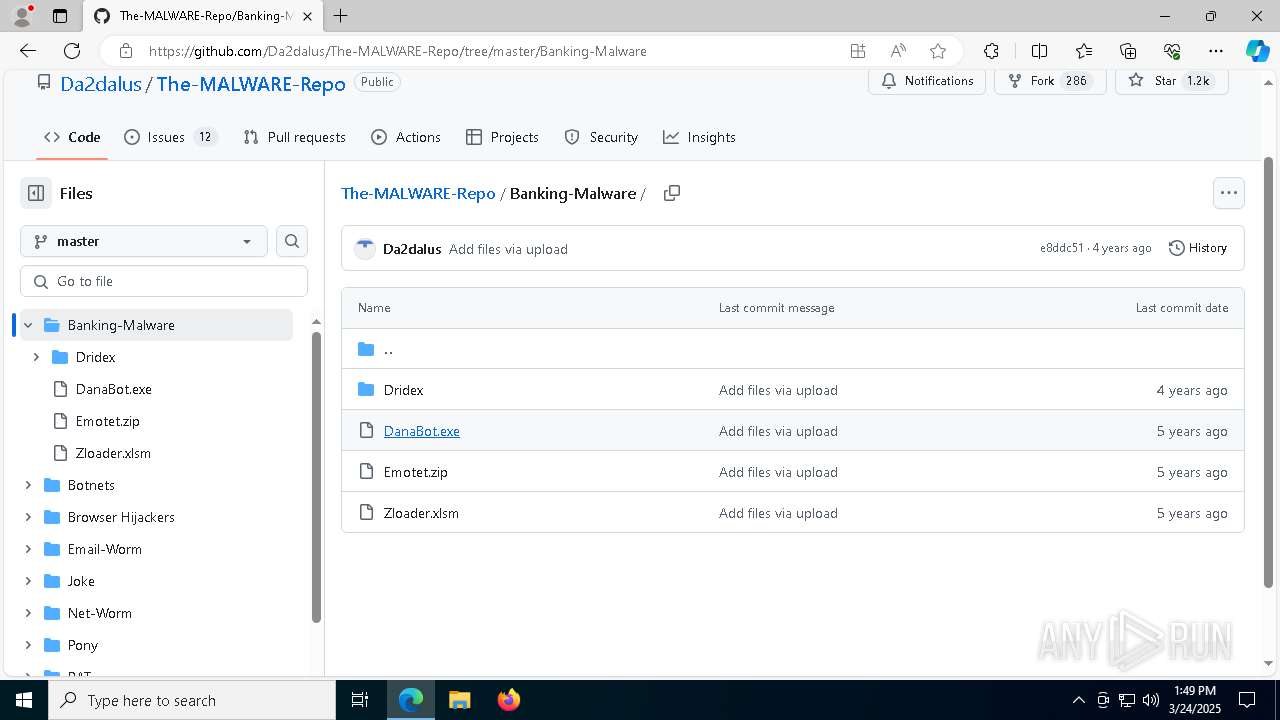
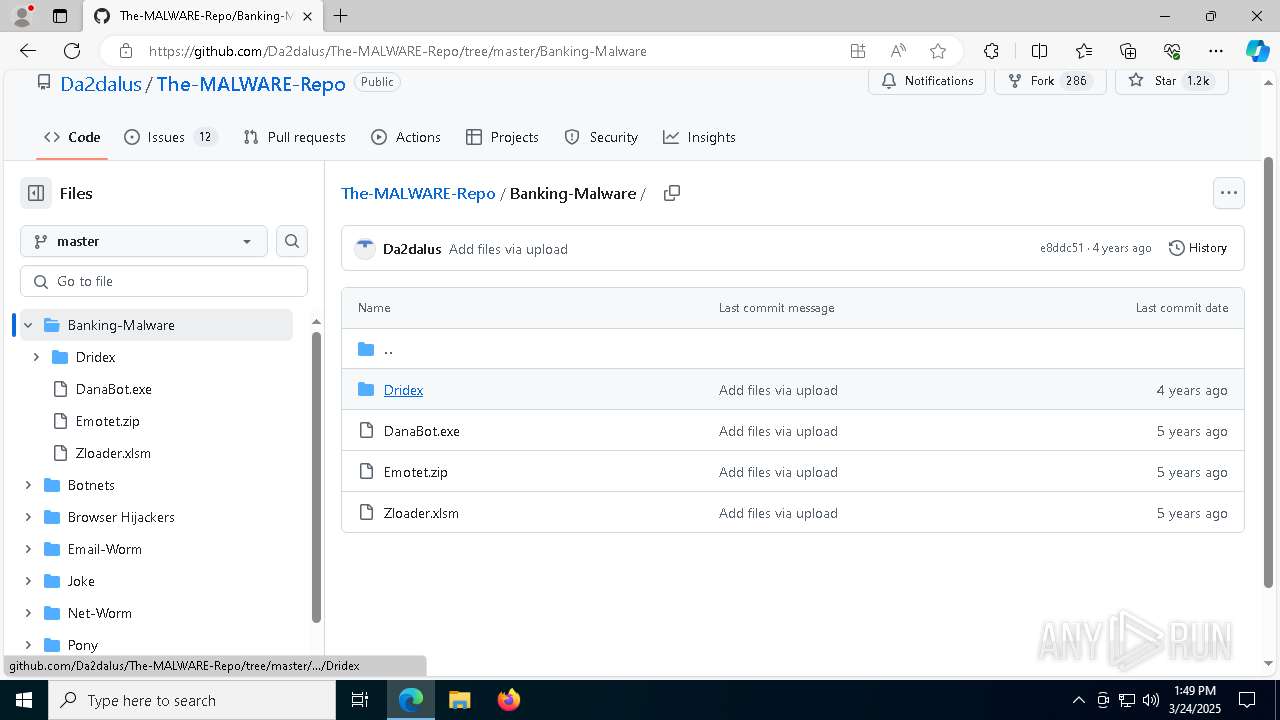
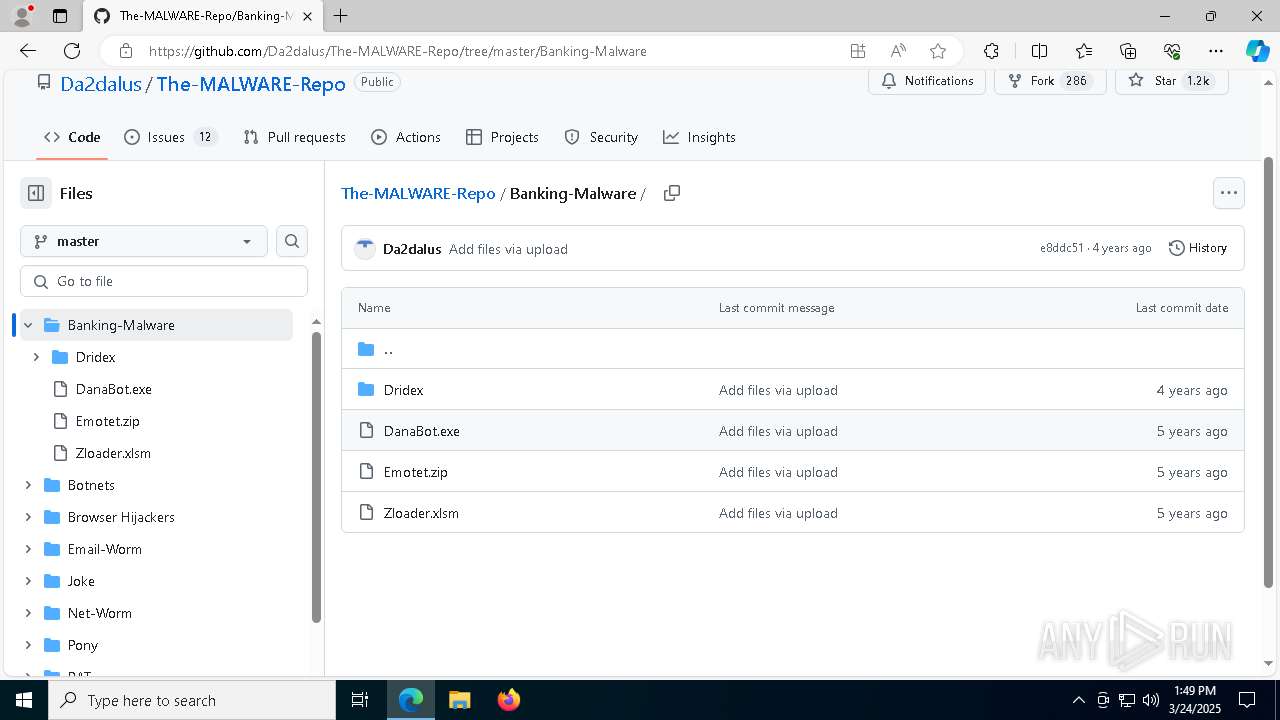
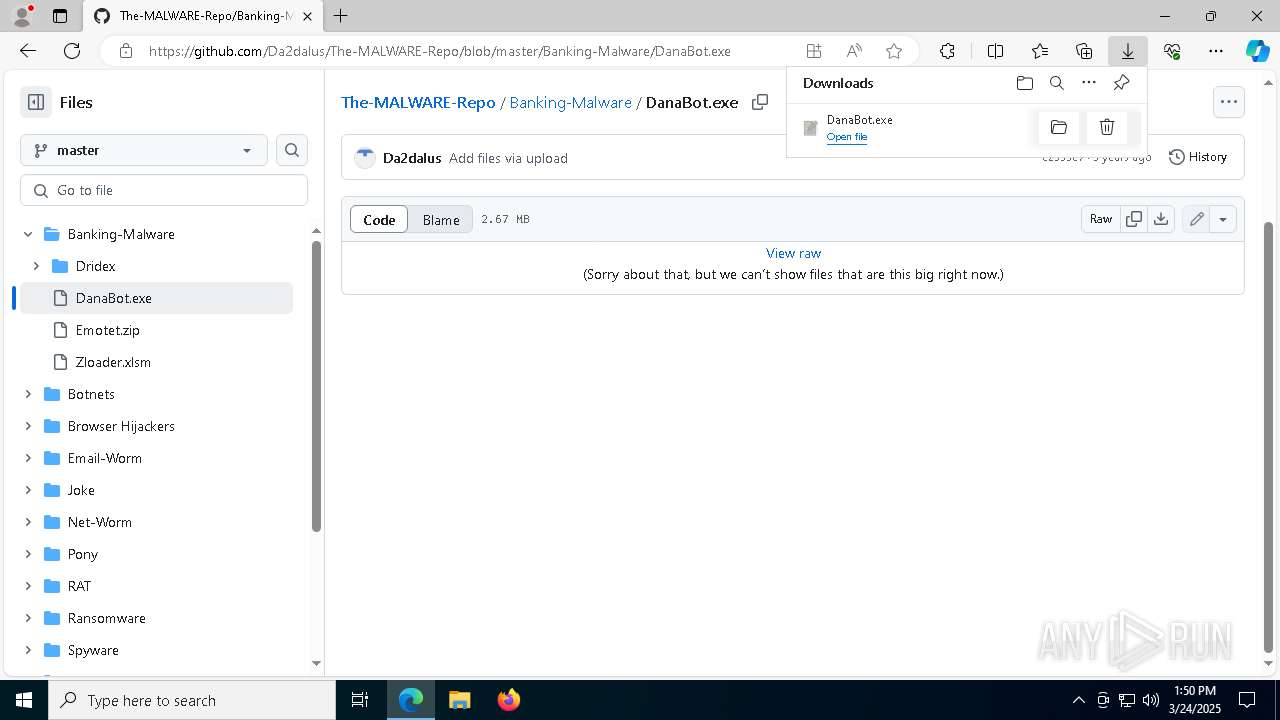
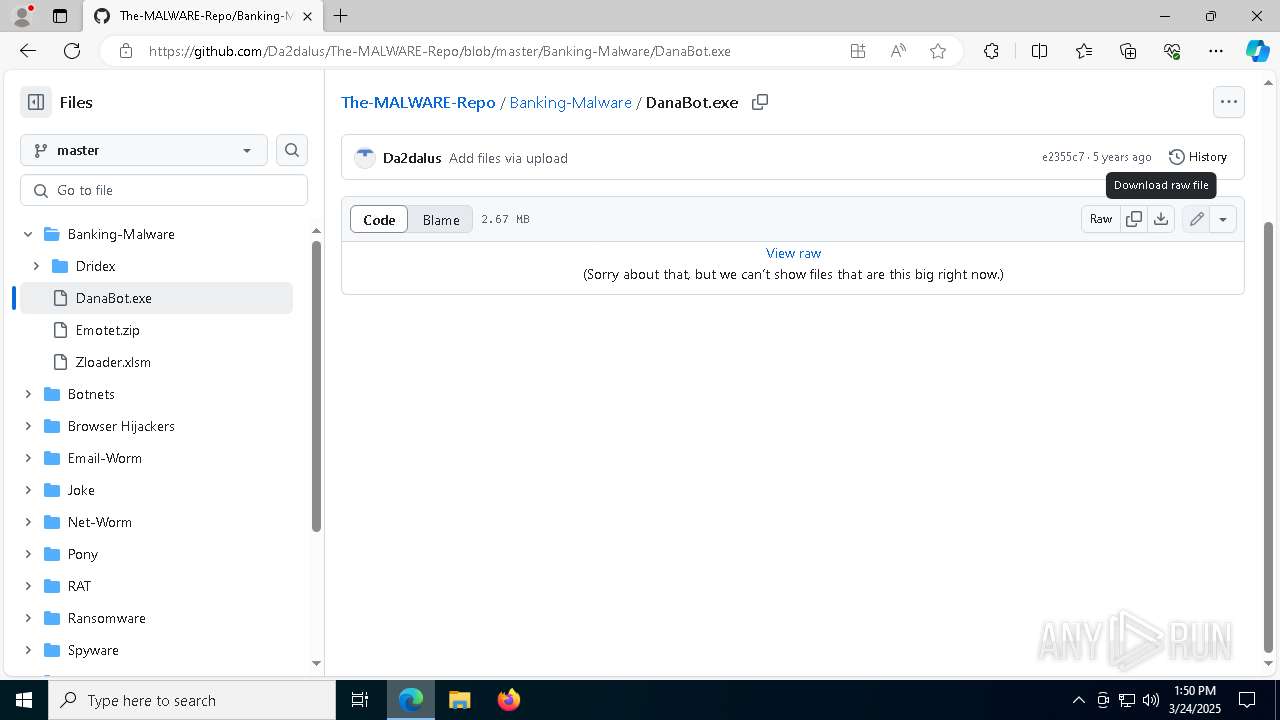
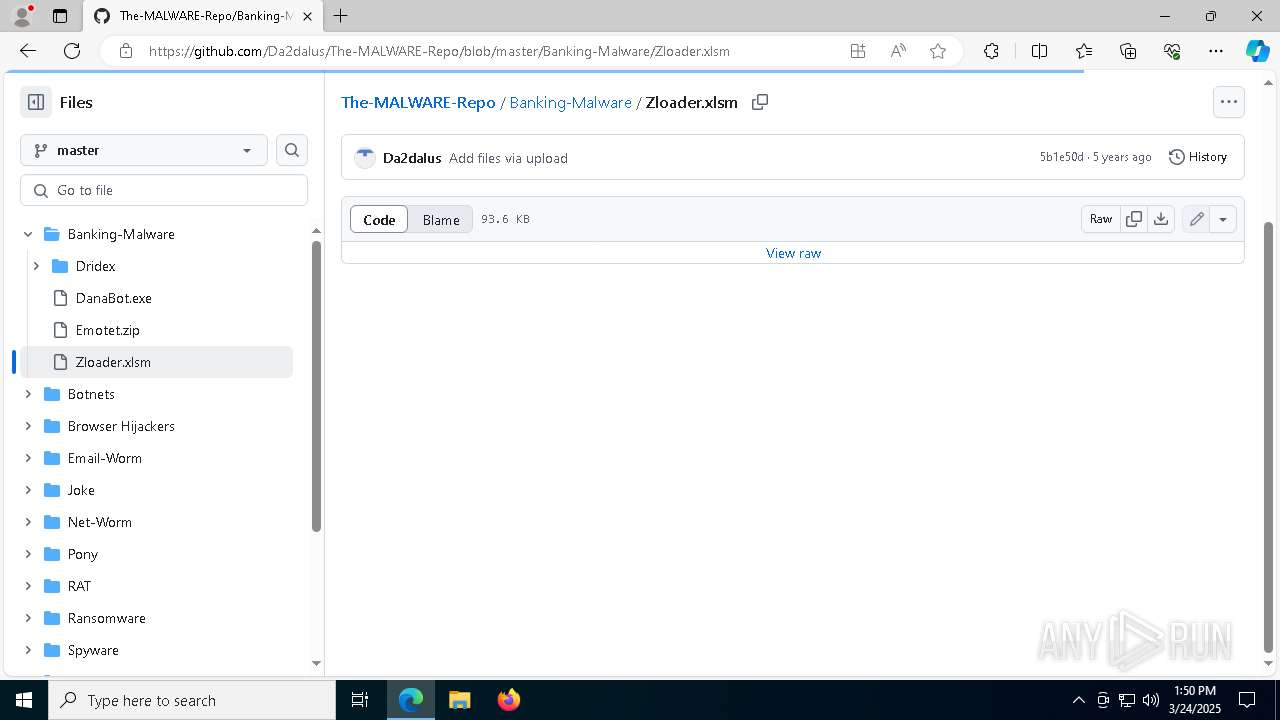
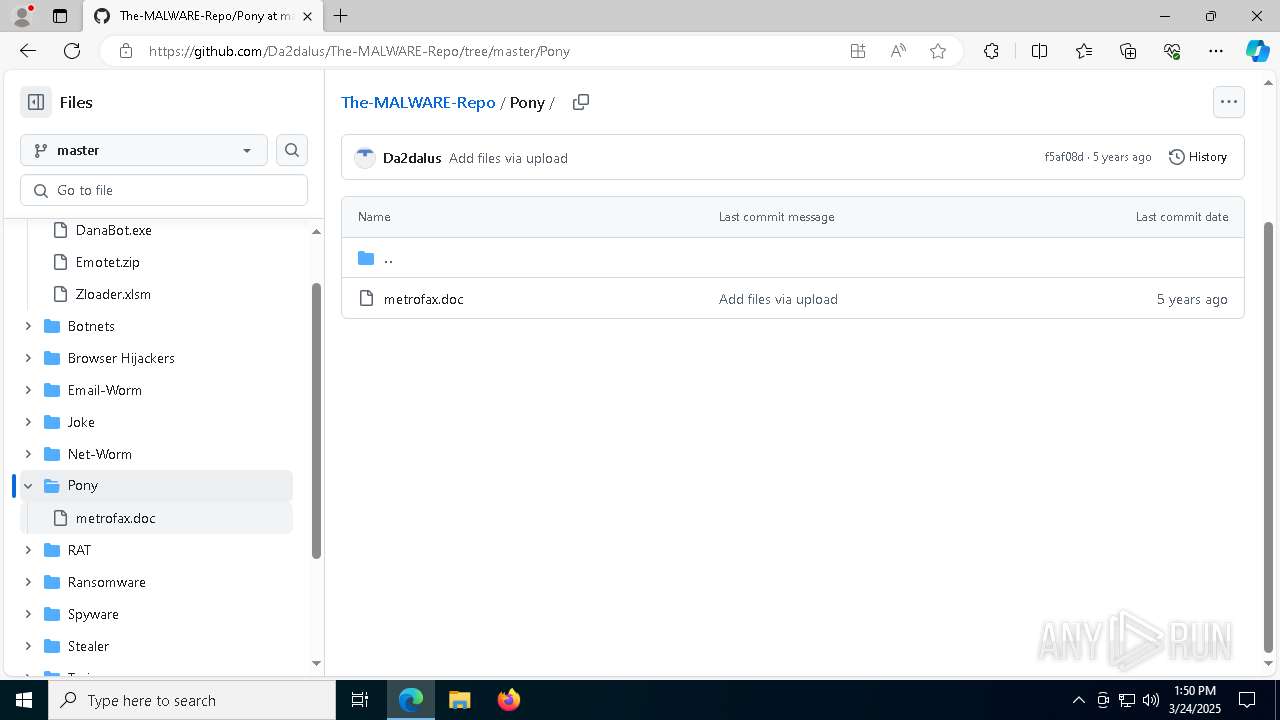
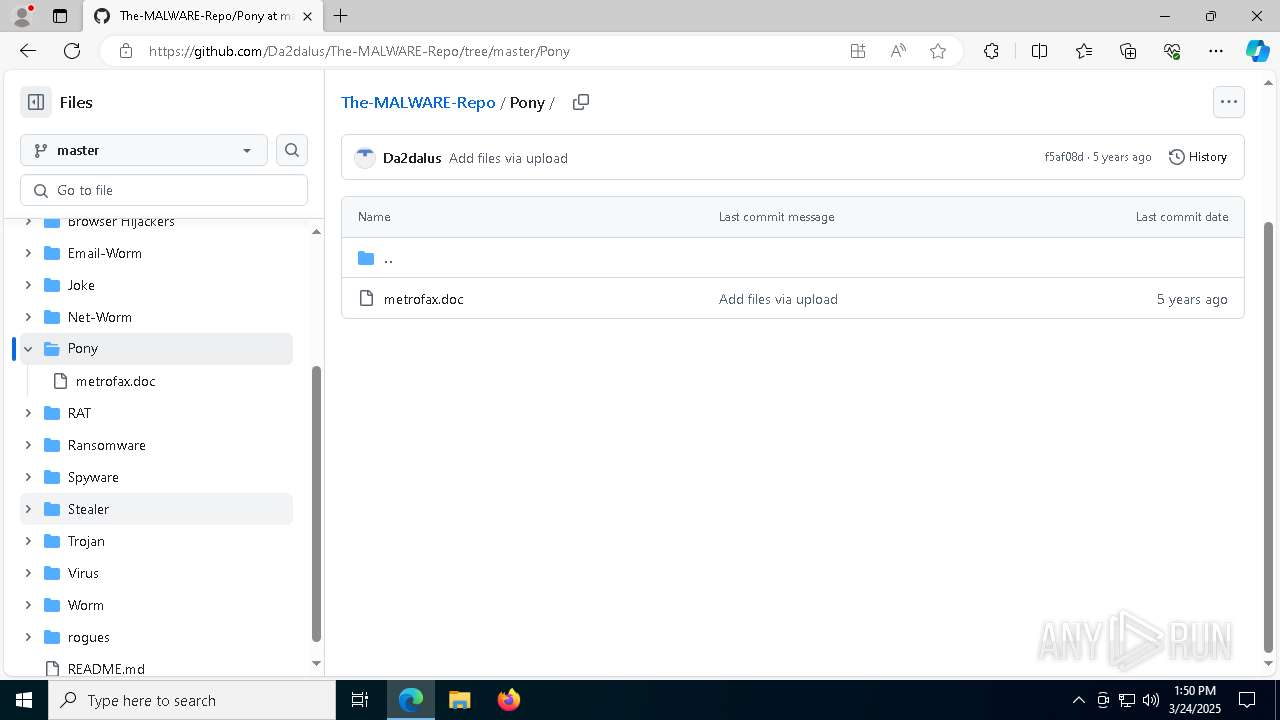
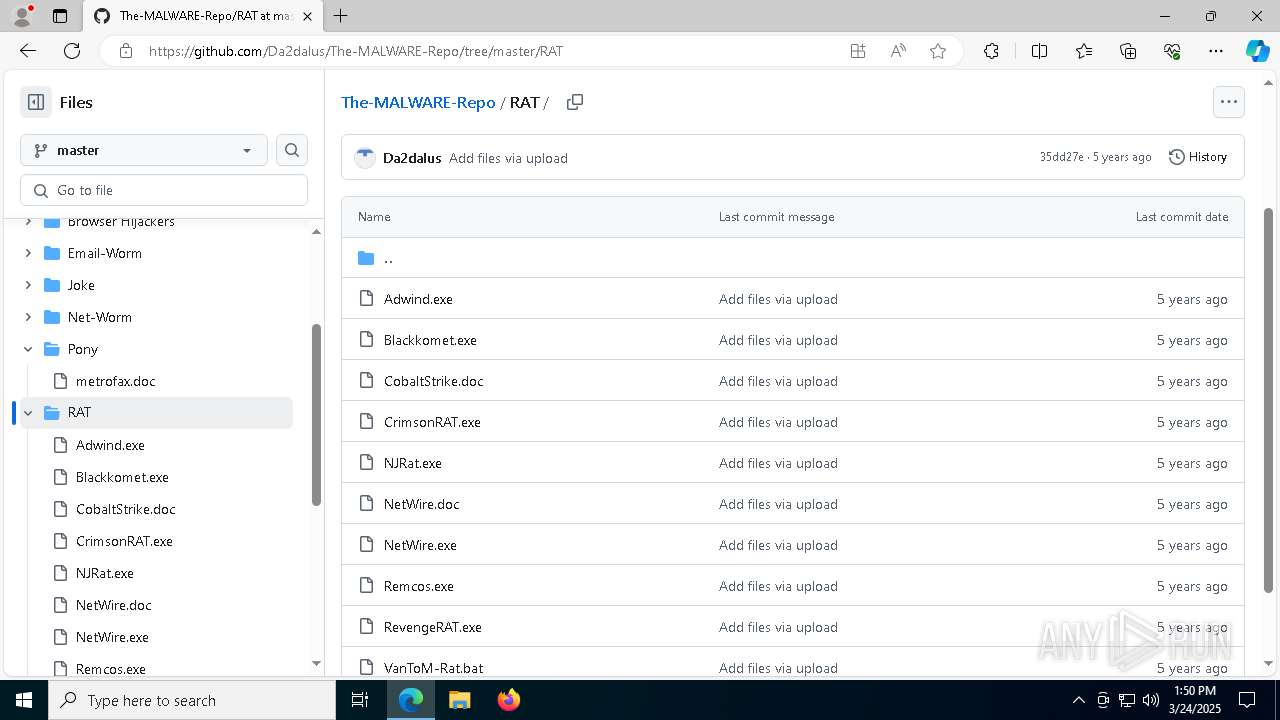
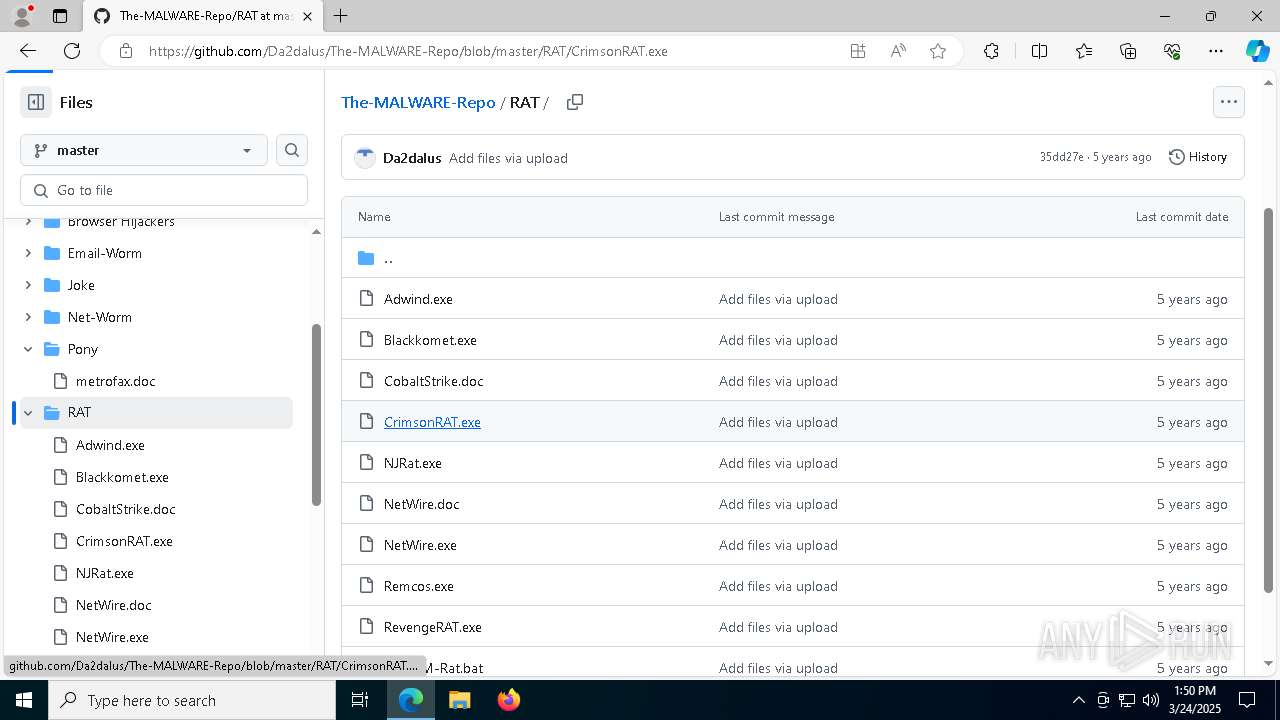
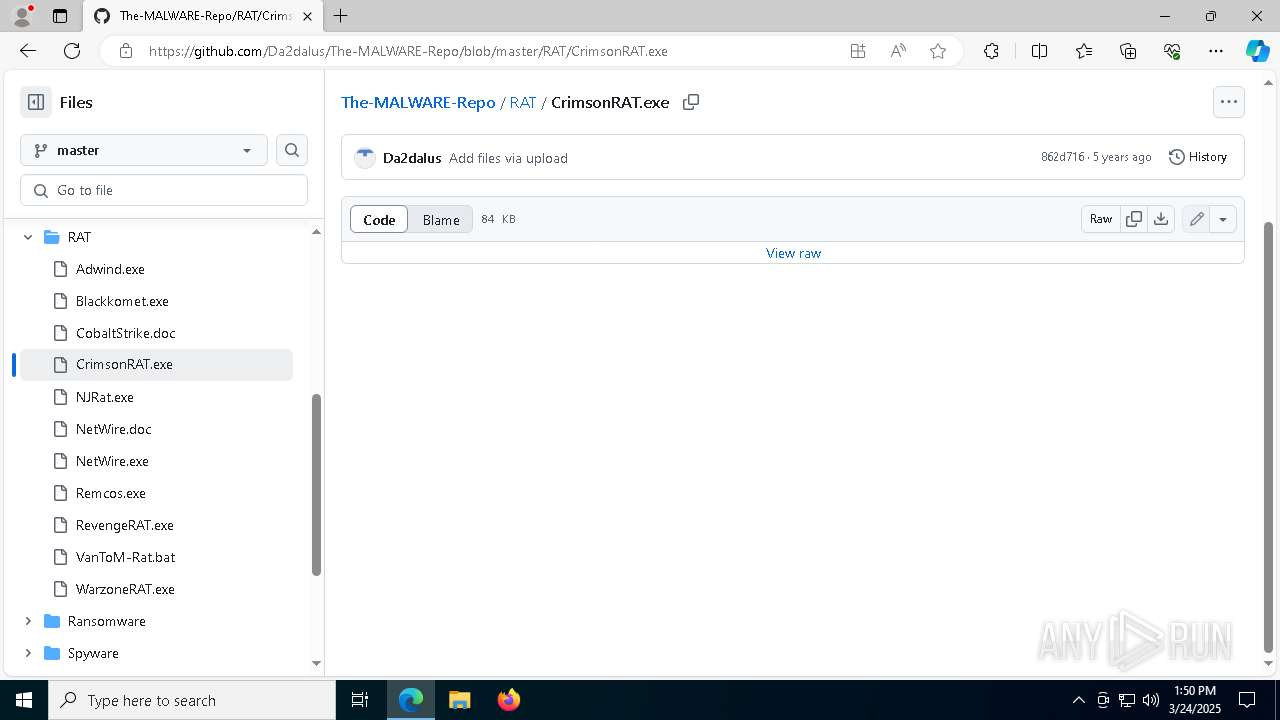
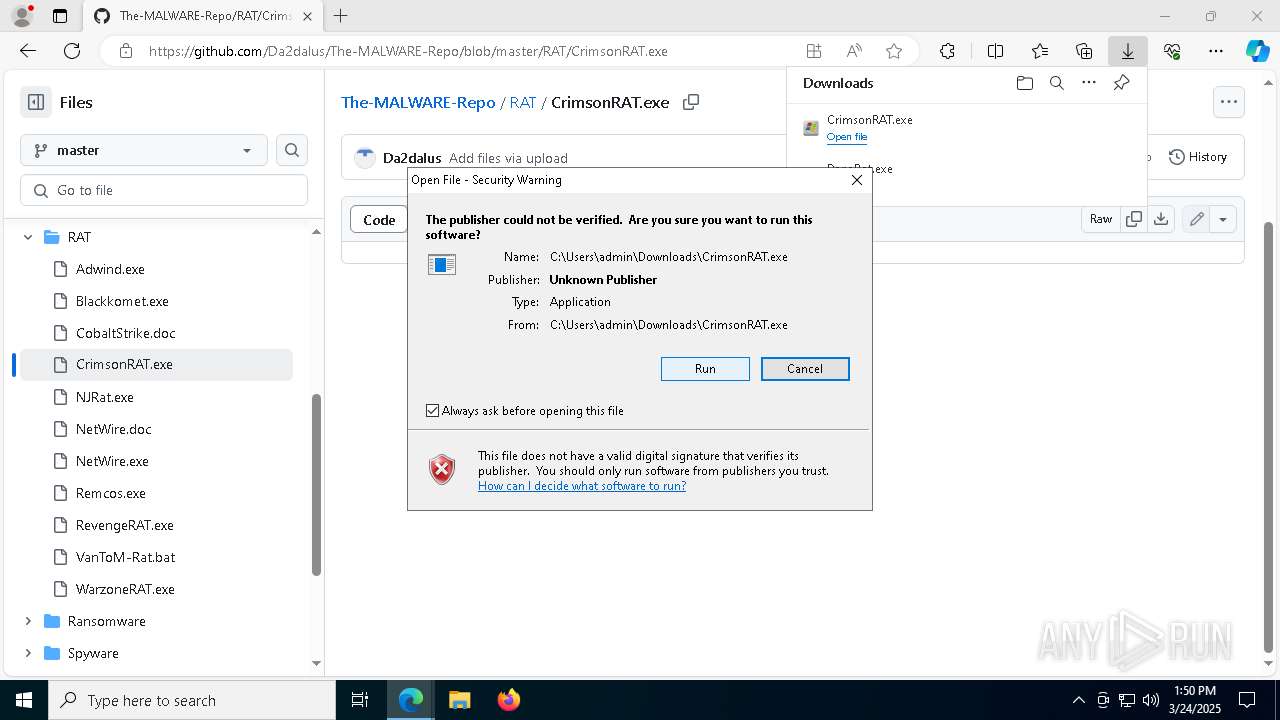
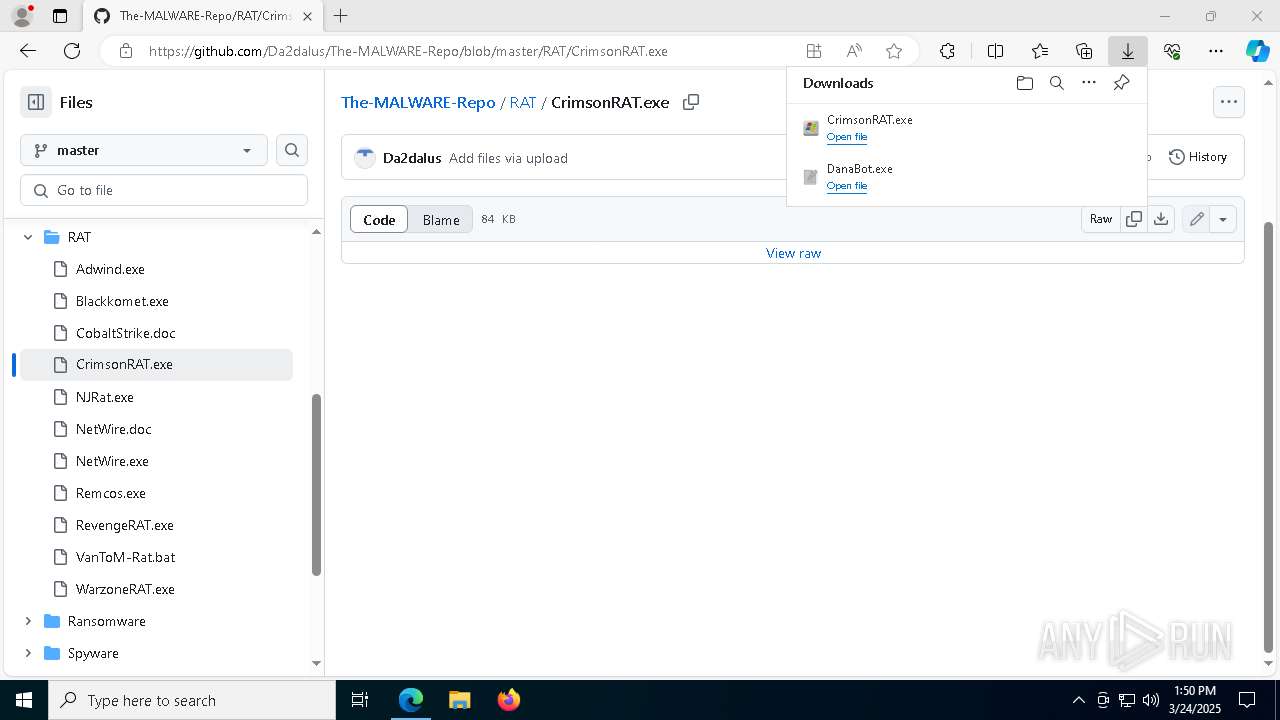
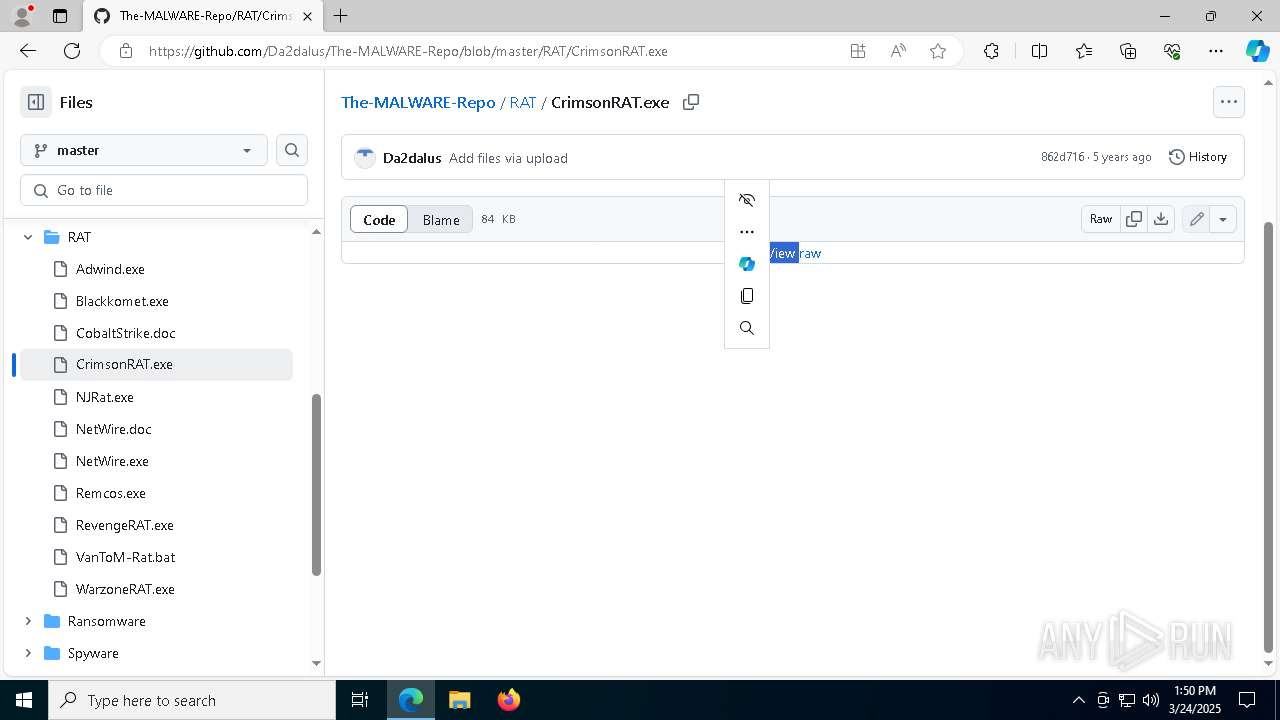
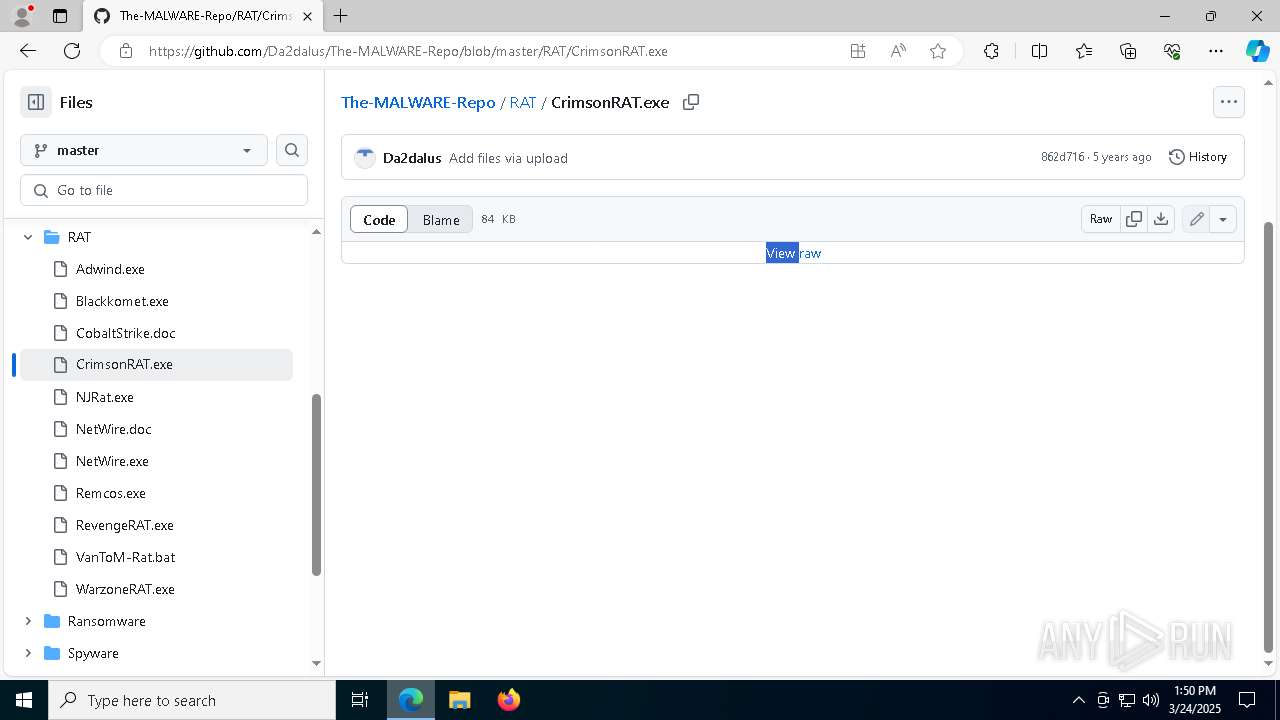
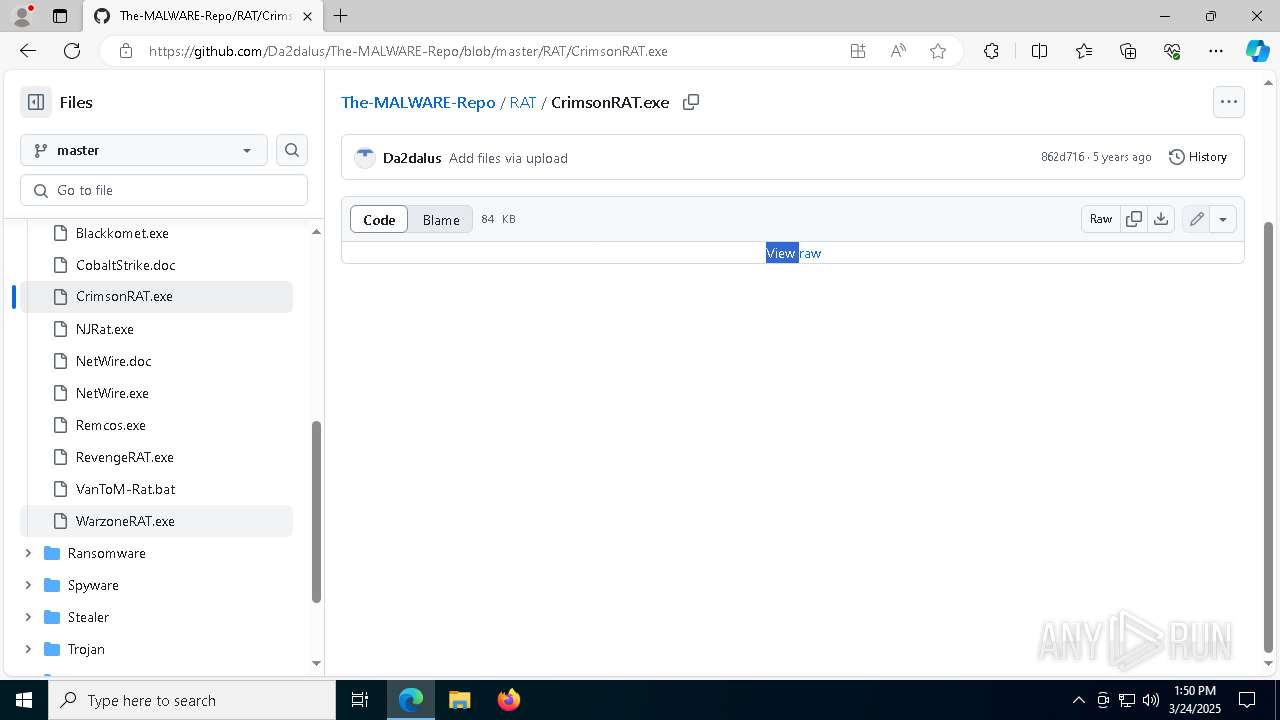
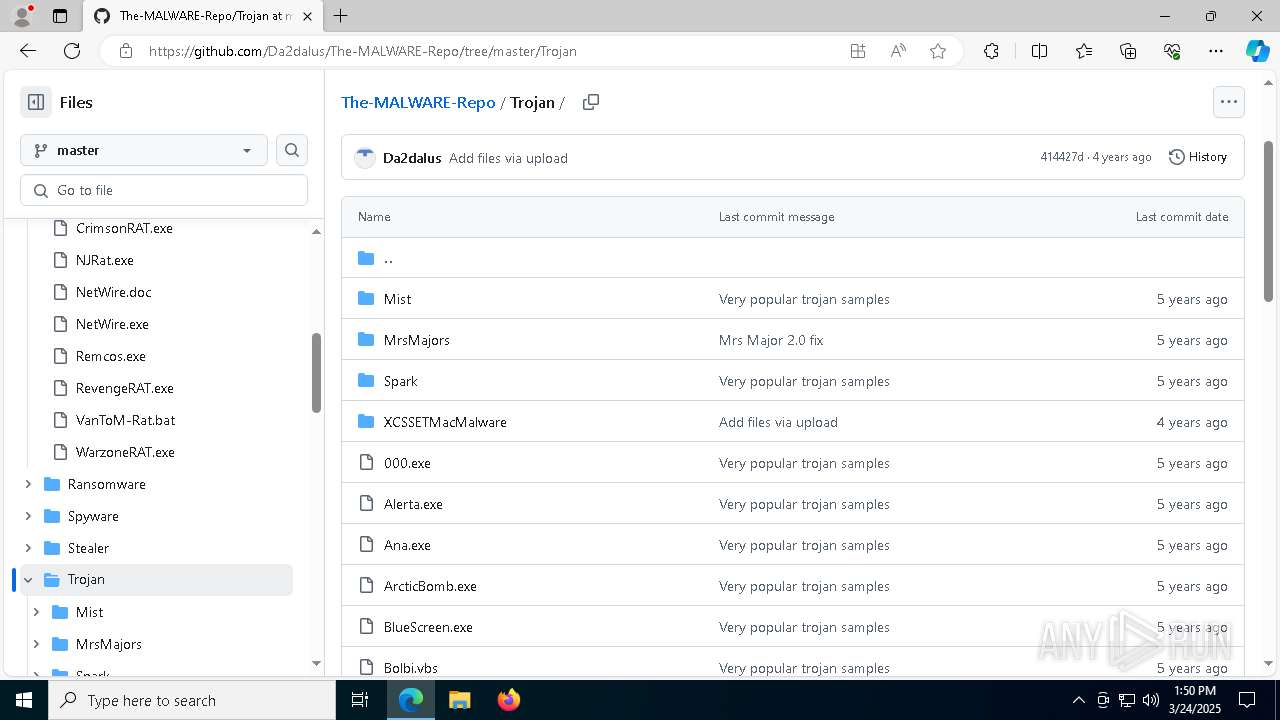
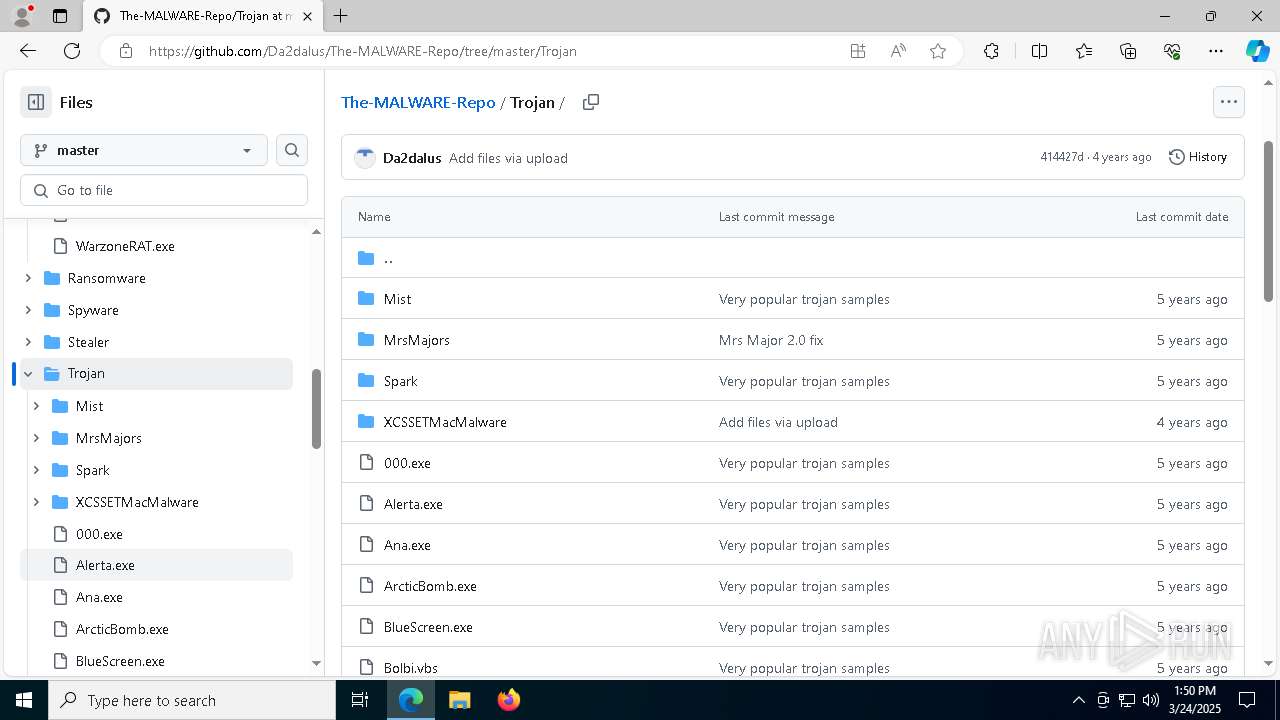
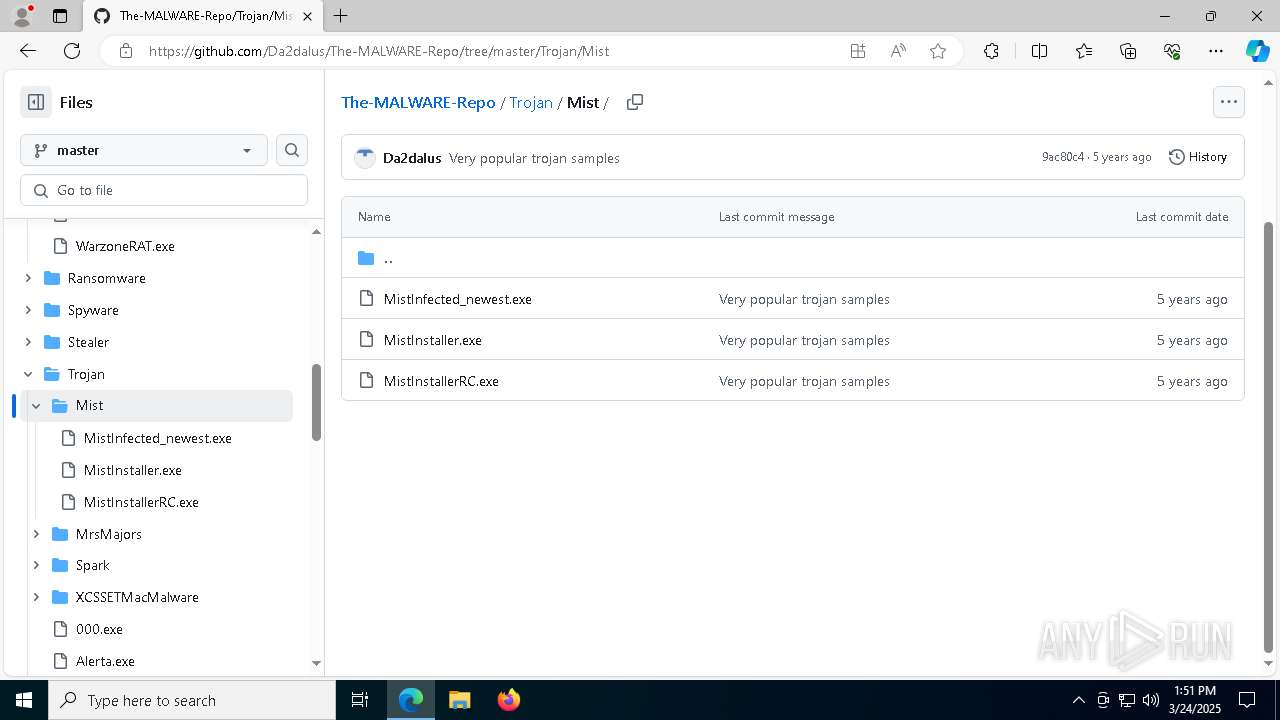
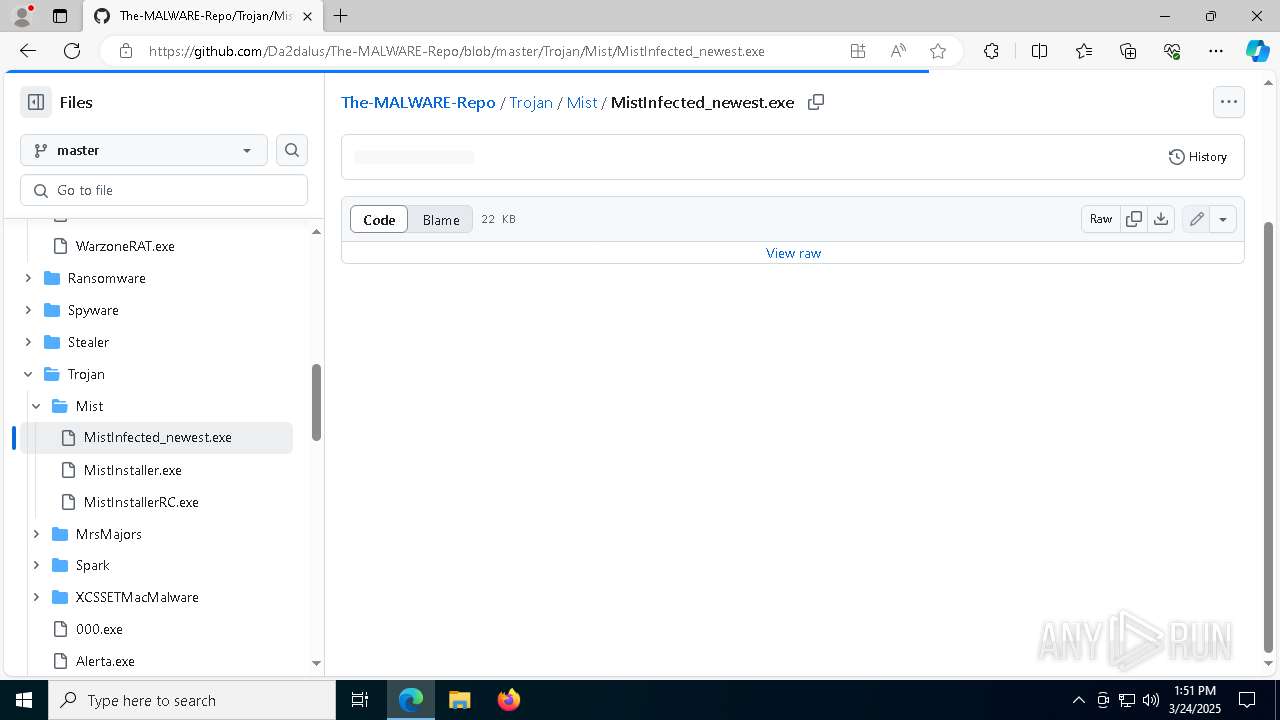
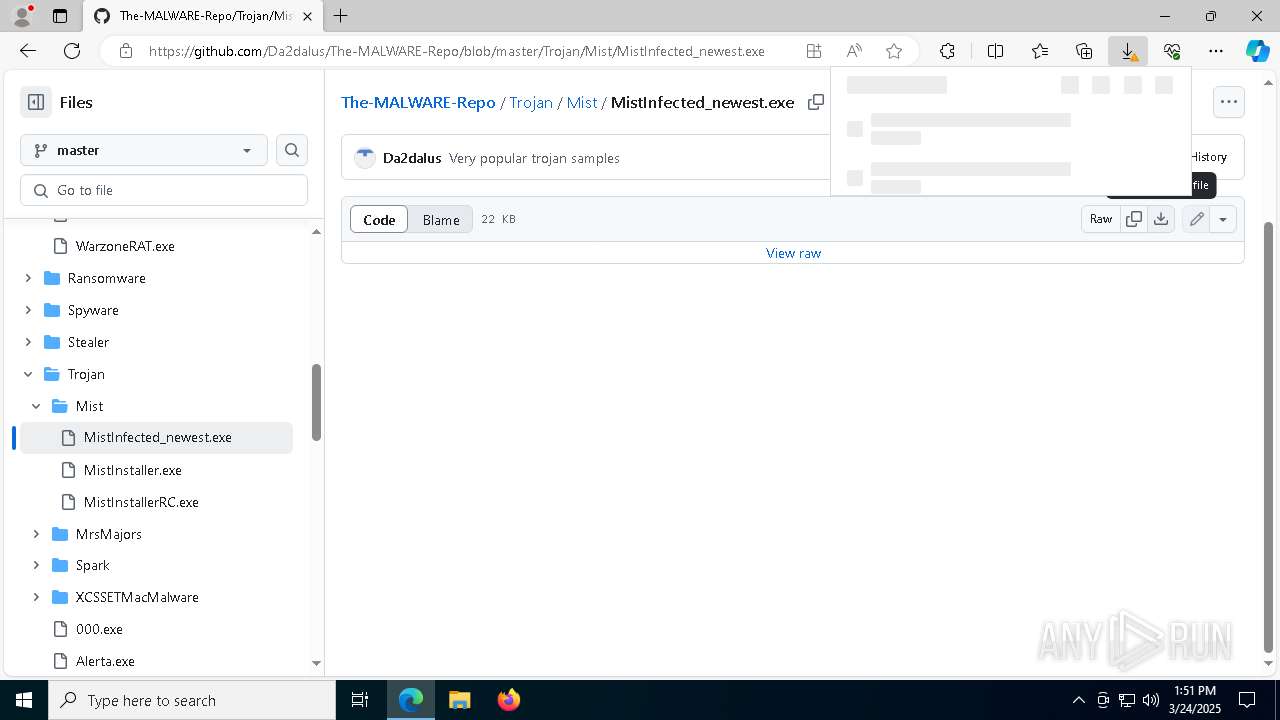
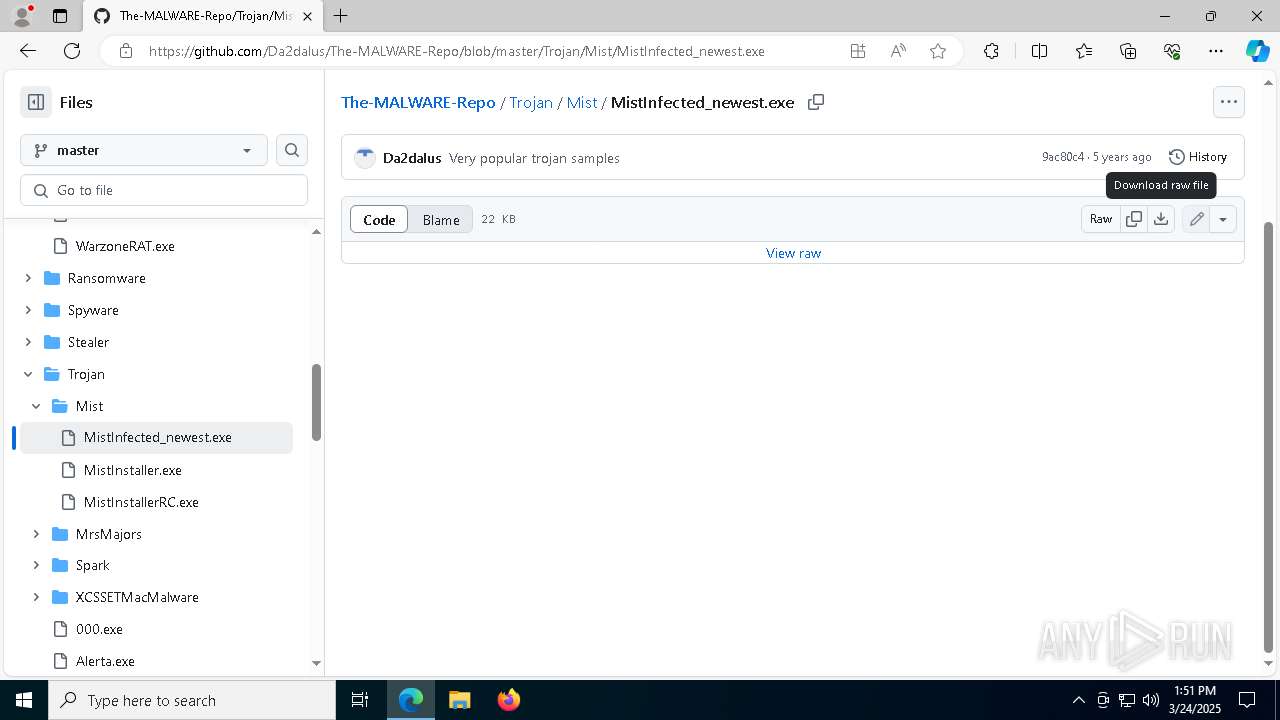
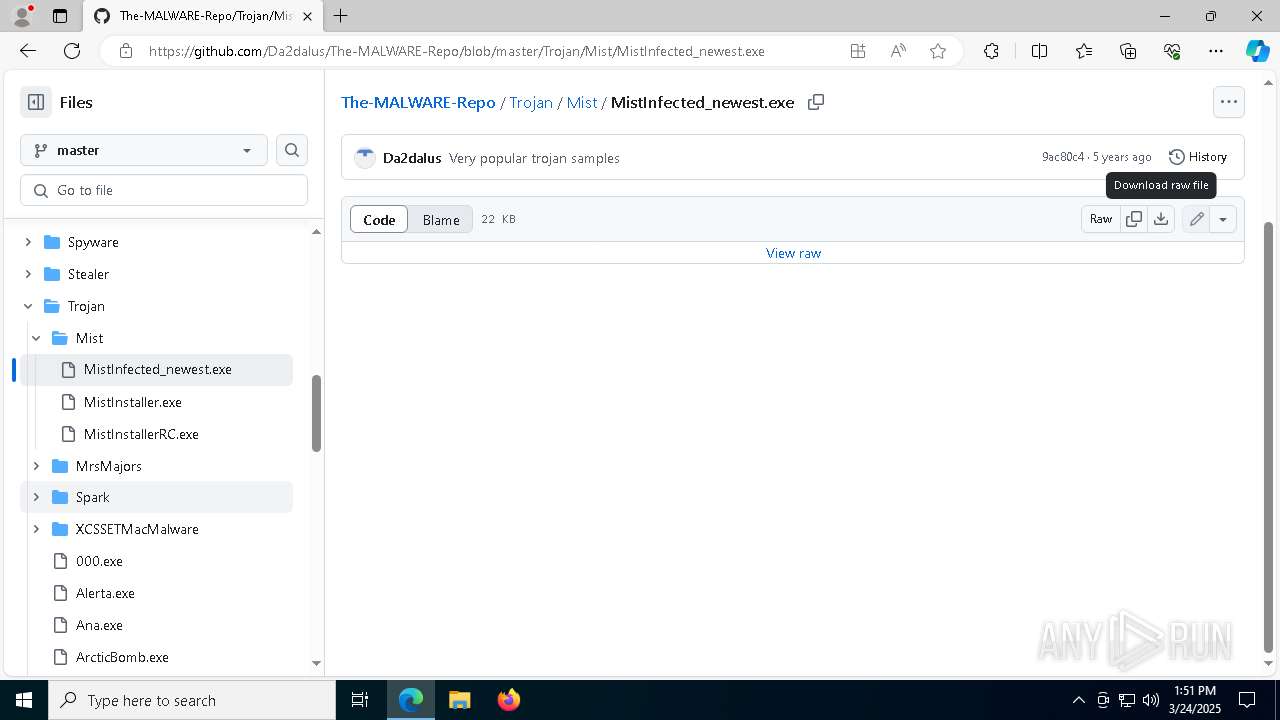
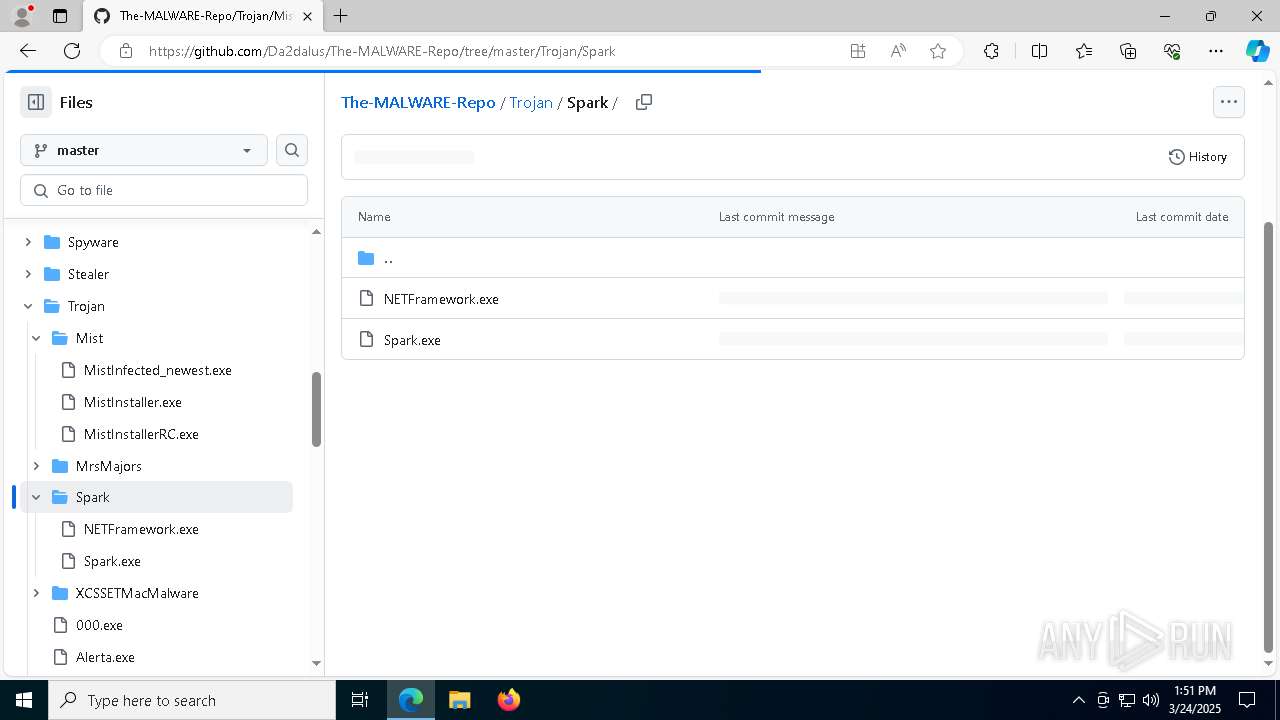
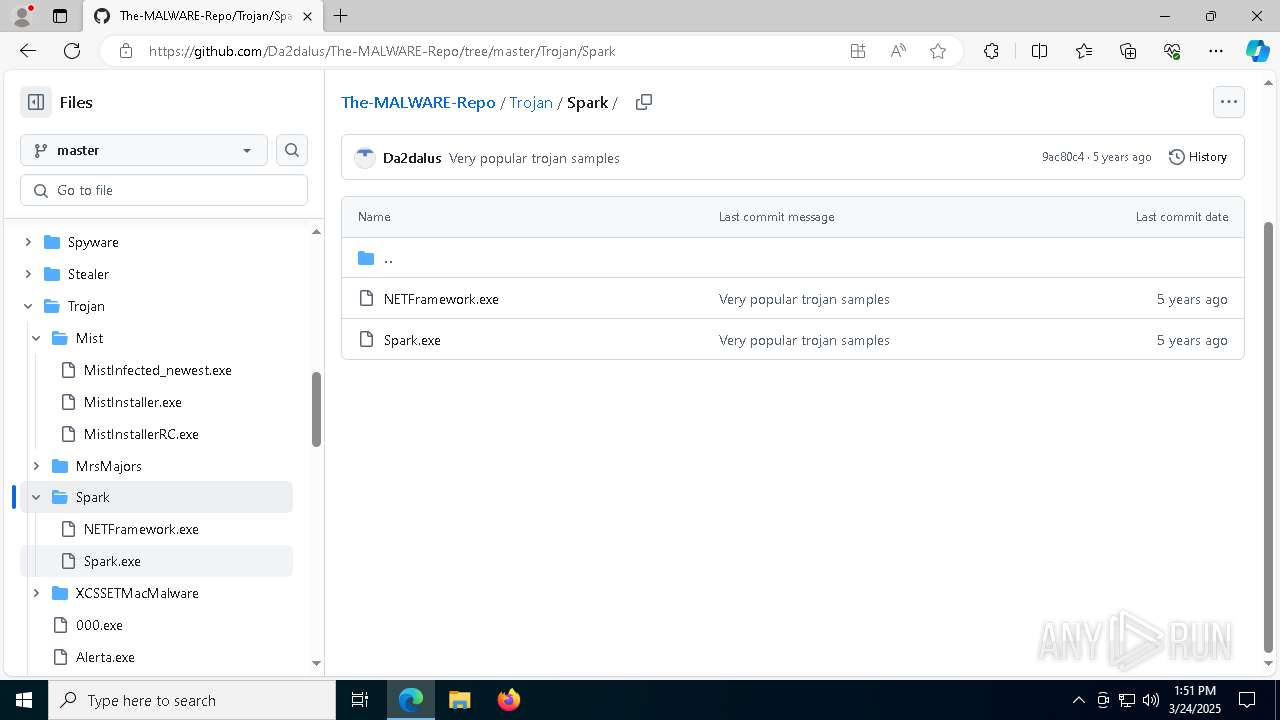
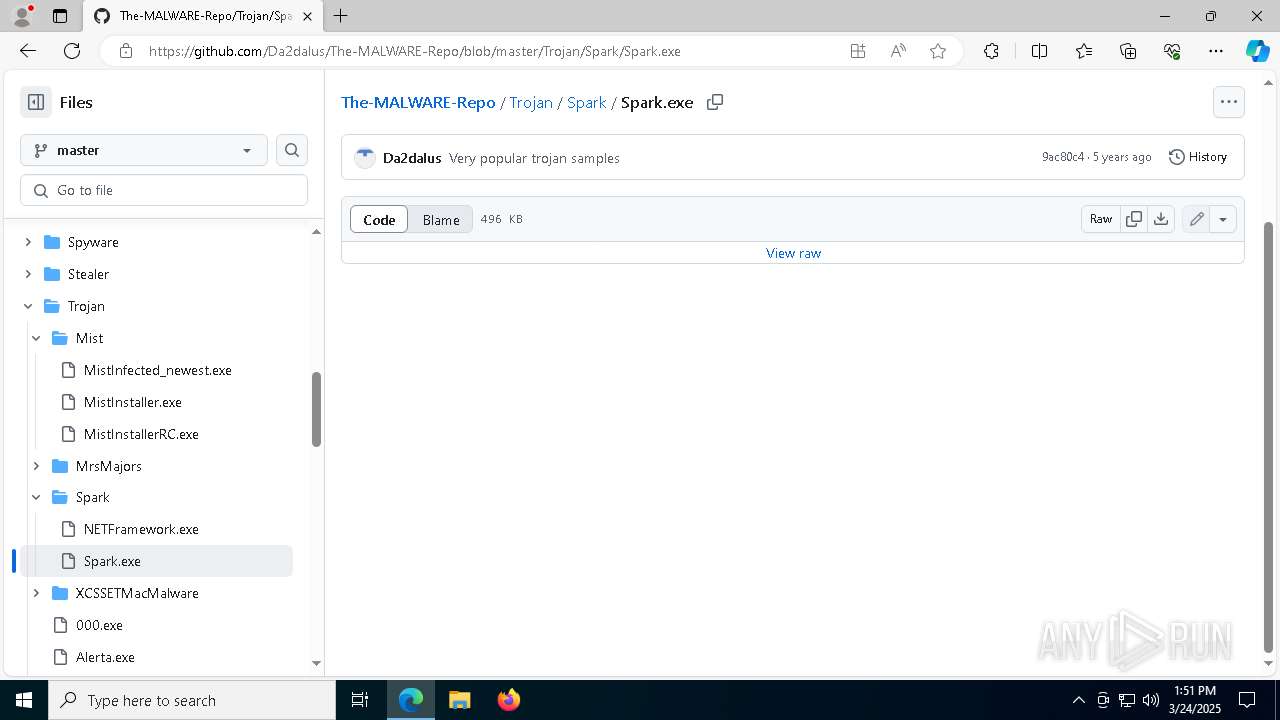
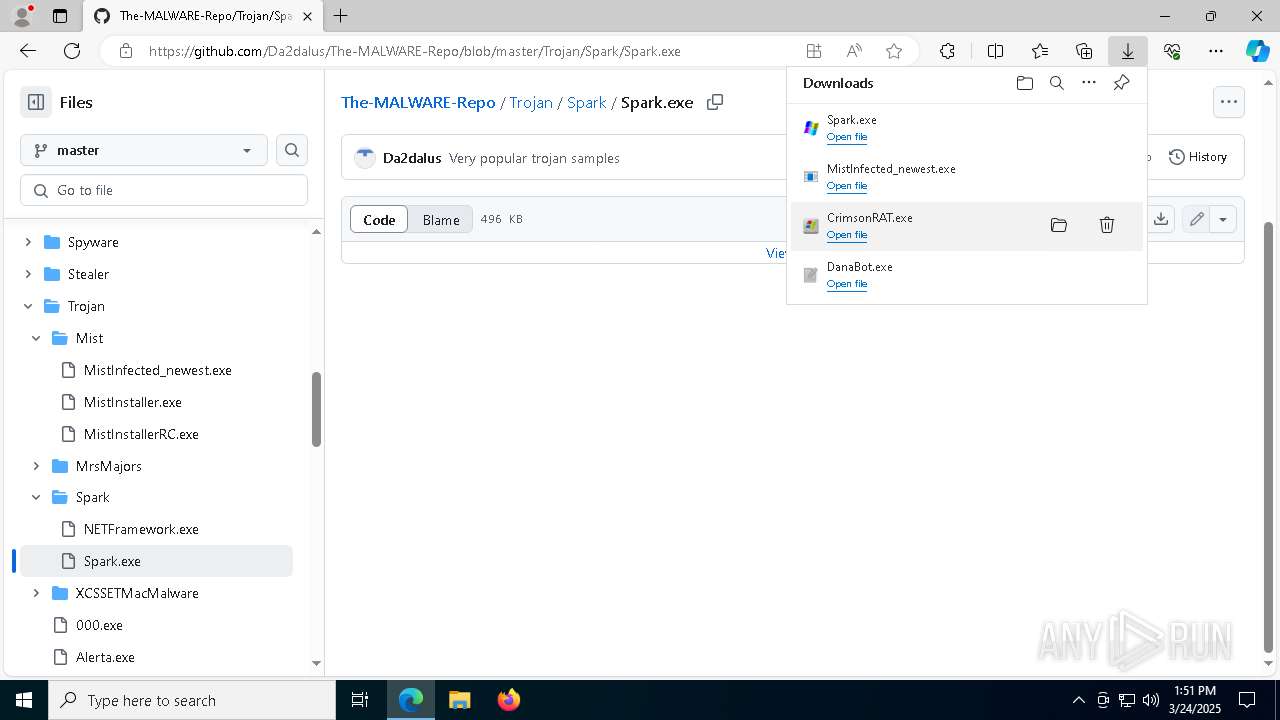
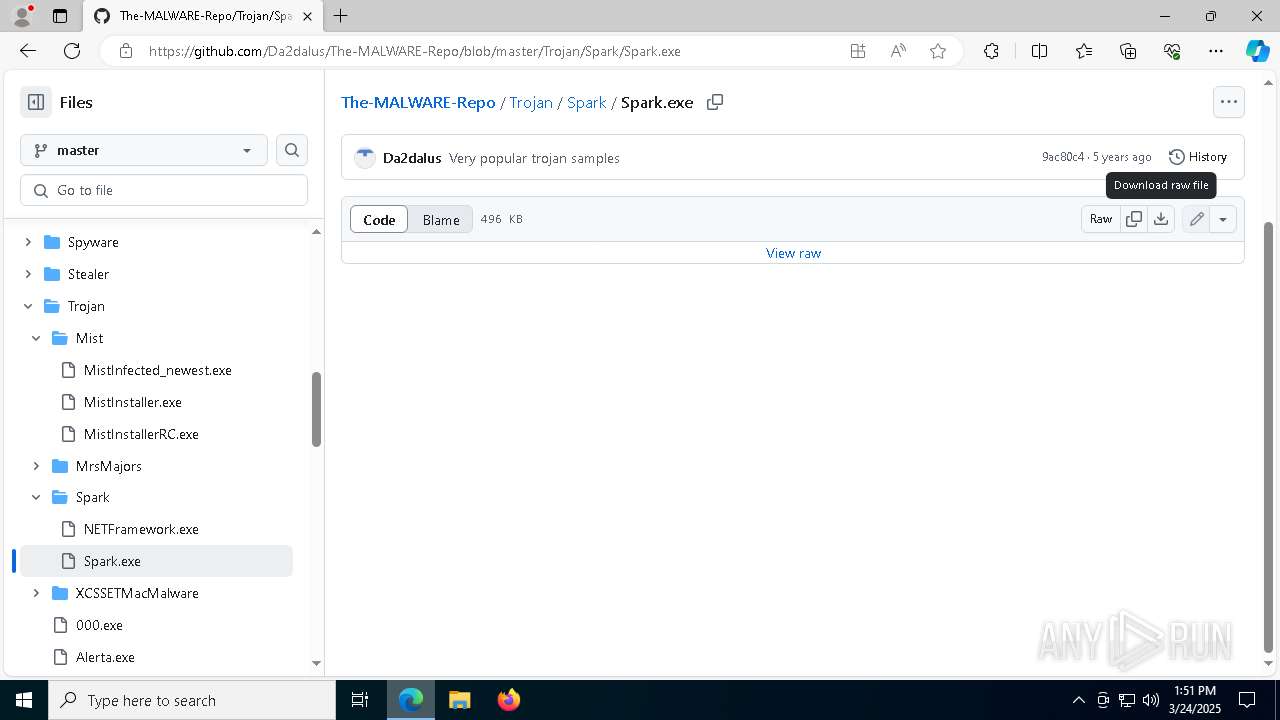
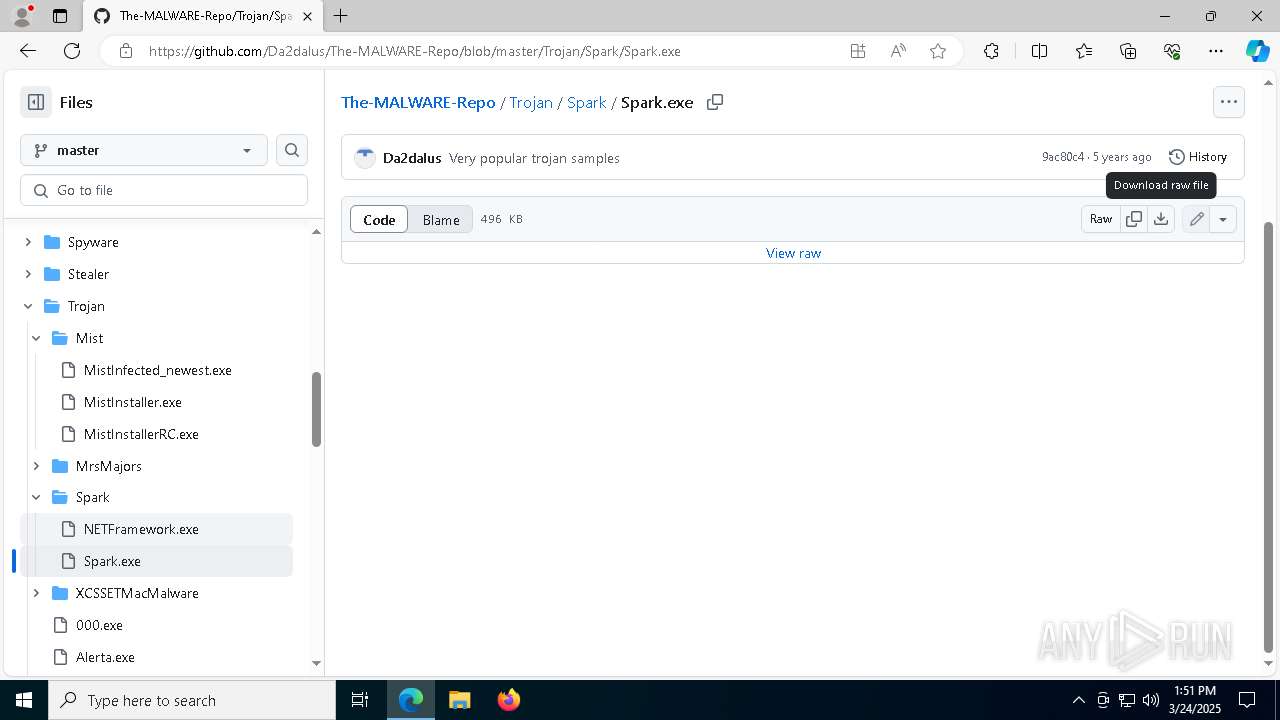
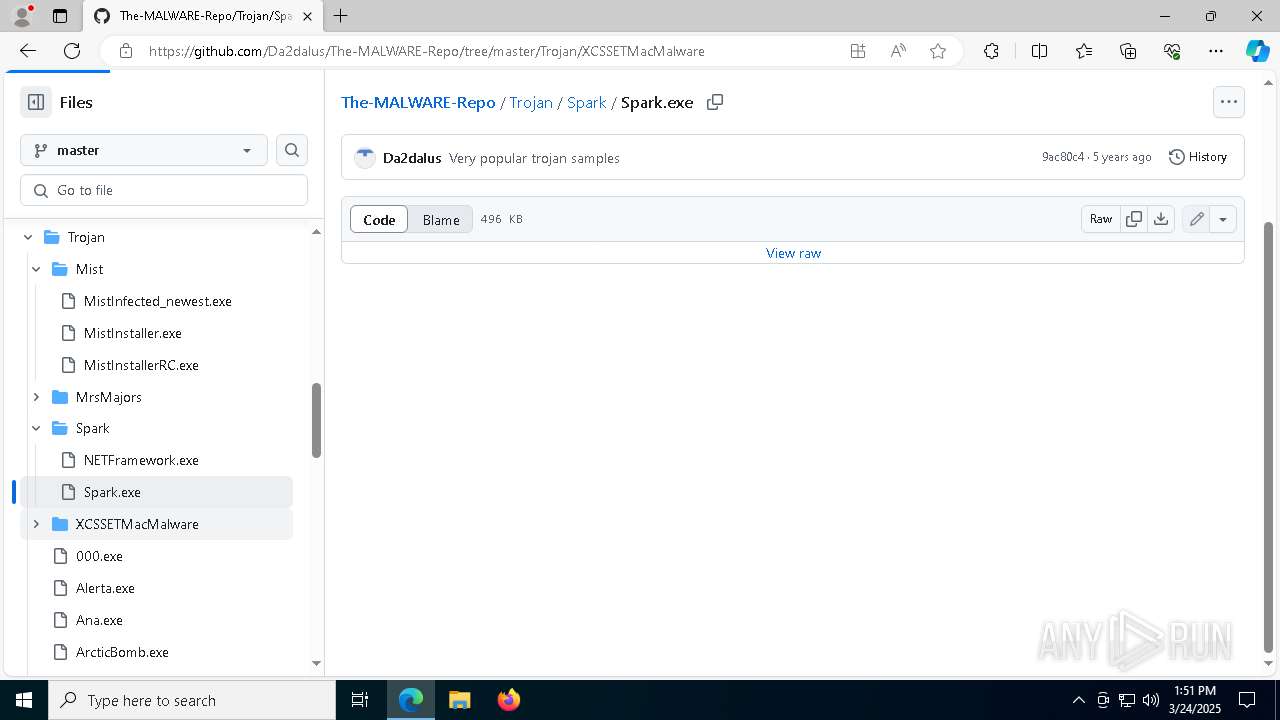
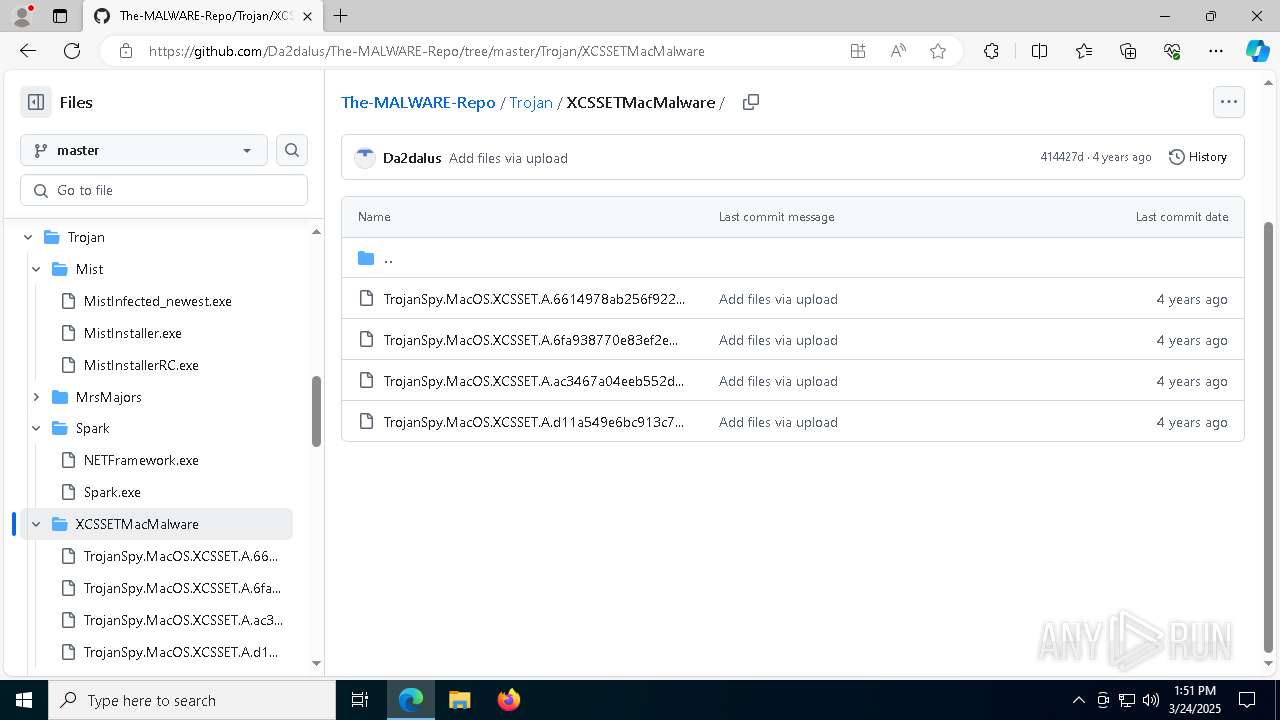
| URL: | https://github.com/Da2dalus/The-MALWARE-Repo |
| Full analysis: | https://app.any.run/tasks/819e973e-53f8-441f-aad8-0e0a8e2e6f60 |
| Verdict: | Malicious activity |
| Threats: | Danabot is an advanced banking Trojan malware that was designed to steal financial information from victims. Out of the Trojans in the wild, this is one of the most advanced thanks to the modular design and a complex delivery method. |
| Analysis date: | March 24, 2025, 13:49:20 |
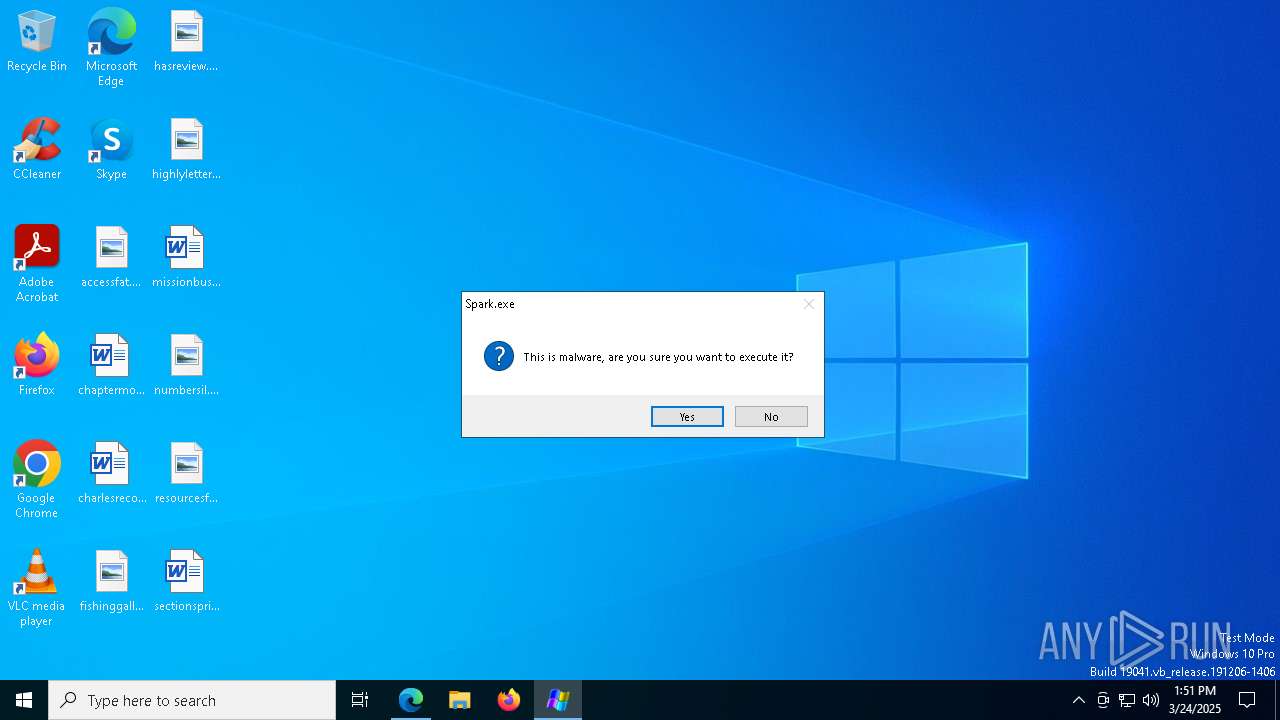
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
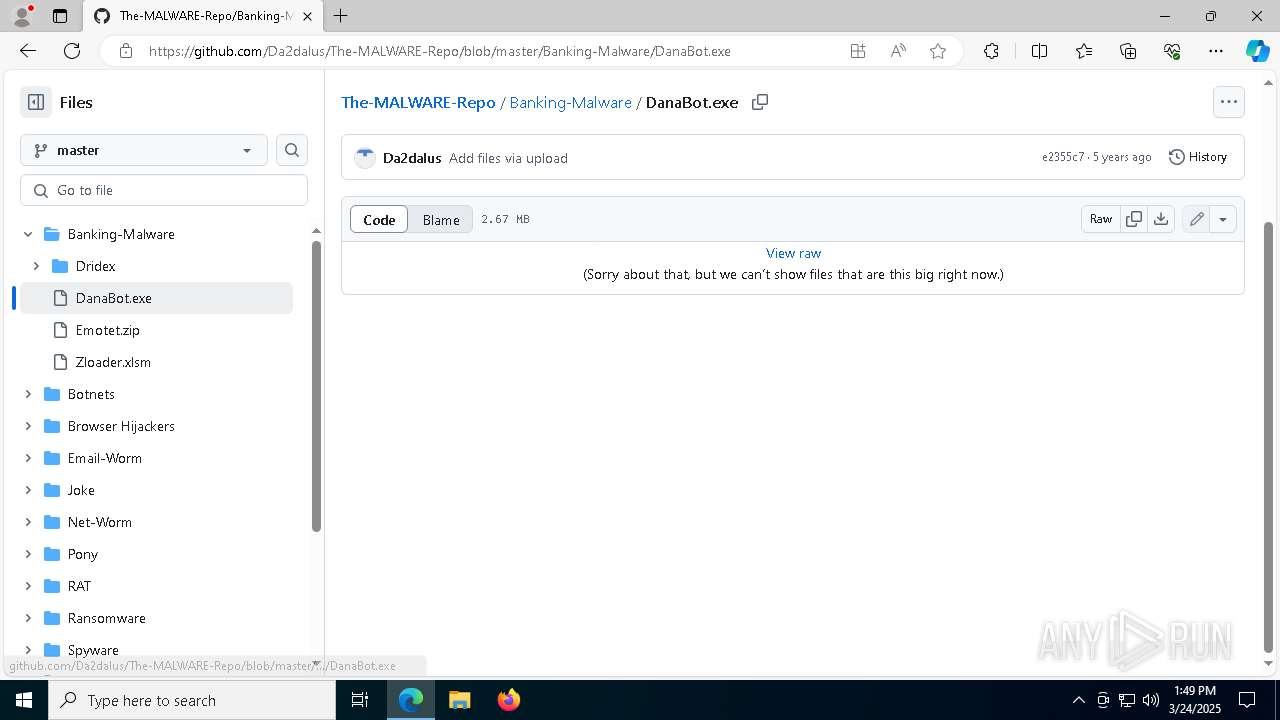
| MD5: | 95DE222D86979D6785AD30792191C545 |
| SHA1: | 0328EC532FE1B34F32B83E99013C67D2B17579A1 |
| SHA256: | 6A8070F67E43F623ABA9B346120783FD9371ADBC25D2852C02BB12D9BBC6C58A |
| SSDEEP: | 3:N8tEdJejSOpykOK:2ubYSOc0 |
MALICIOUS
DANABOT has been found (auto)
- msedge.exe (PID: 2320)
Registers / Runs the DLL via REGSVR32.EXE
- DanaBot.exe (PID: 516)
DANABOT has been detected (YARA)
- rundll32.exe (PID: 1676)
Changes image file execution options
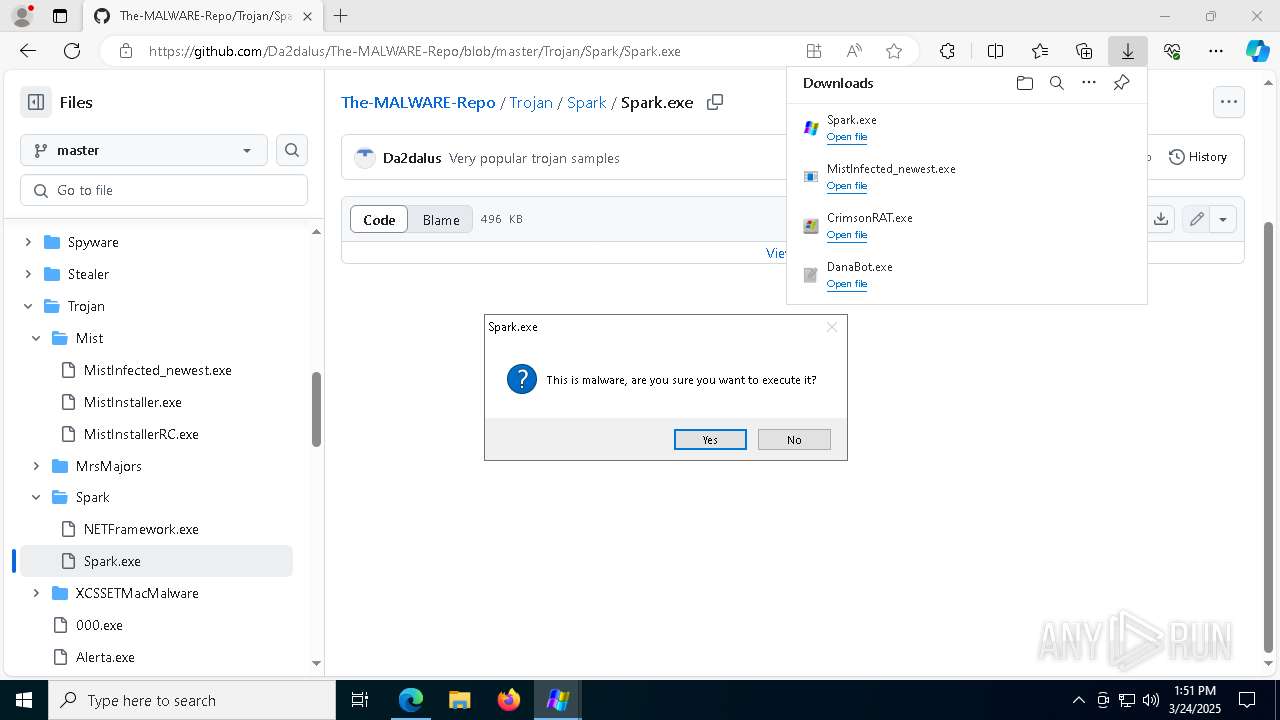
- Spark.exe (PID: 1540)
SUSPICIOUS
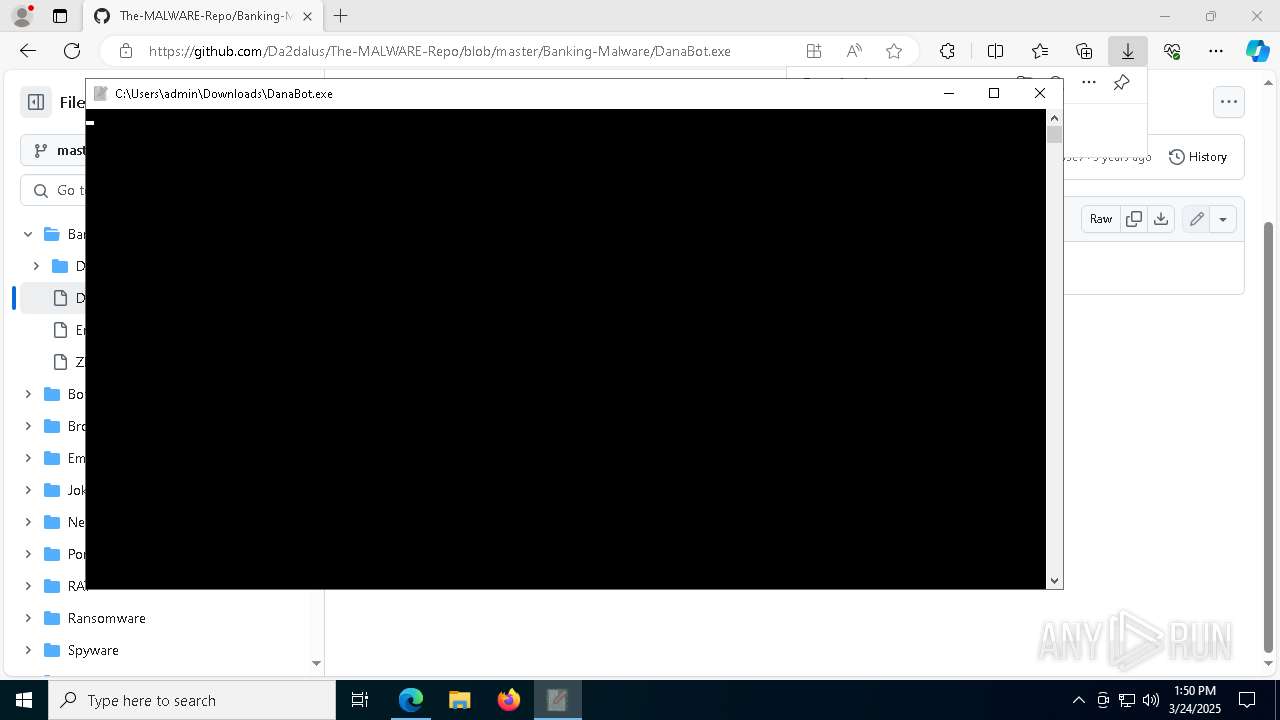
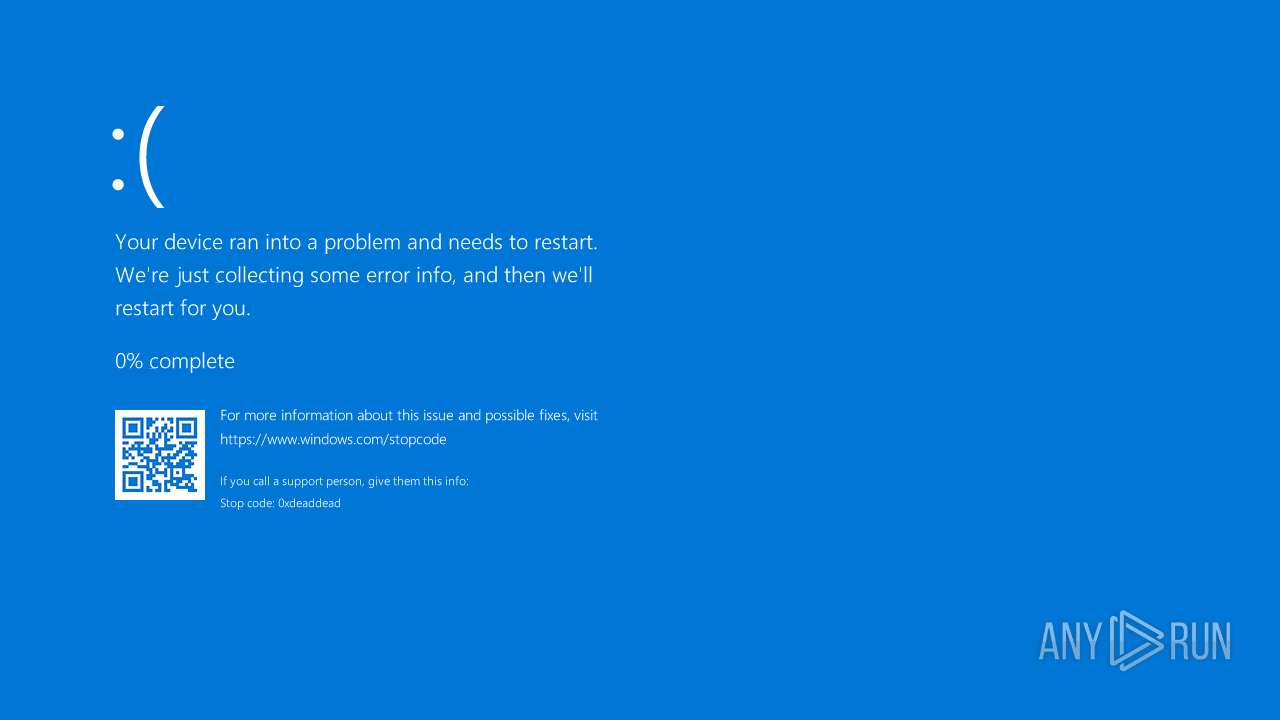
Executes application which crashes
- DanaBot.exe (PID: 516)
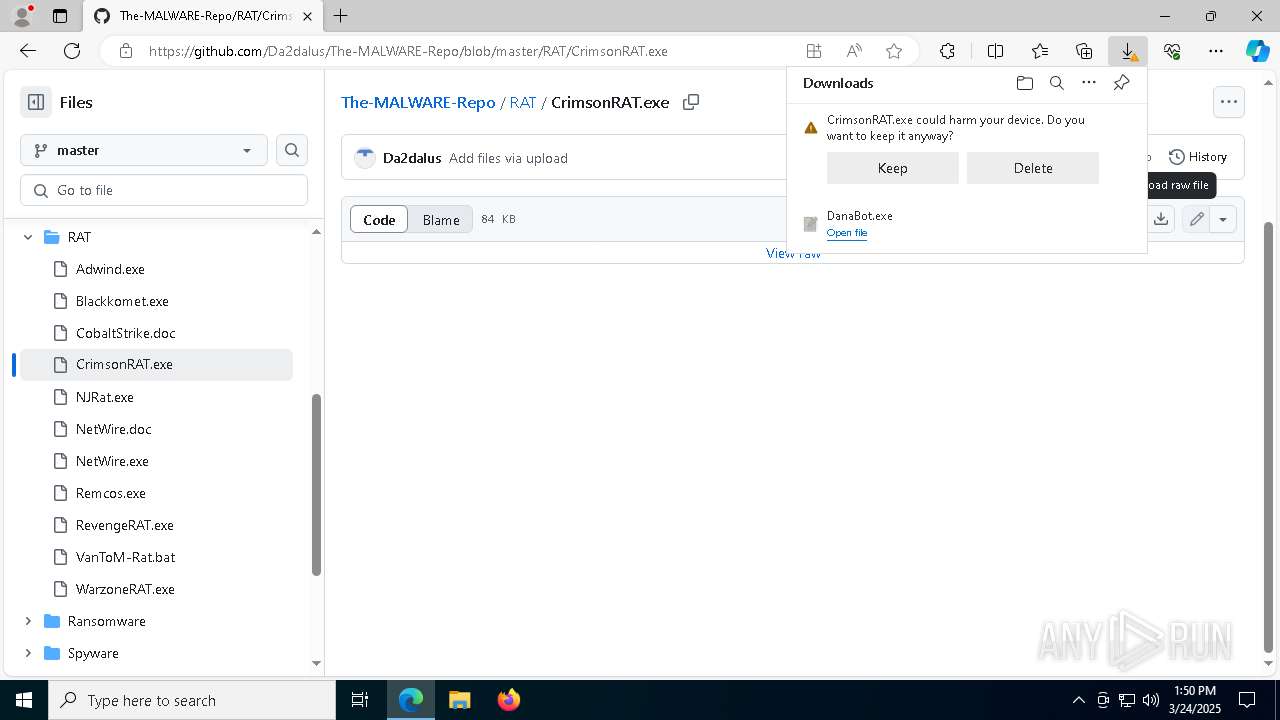
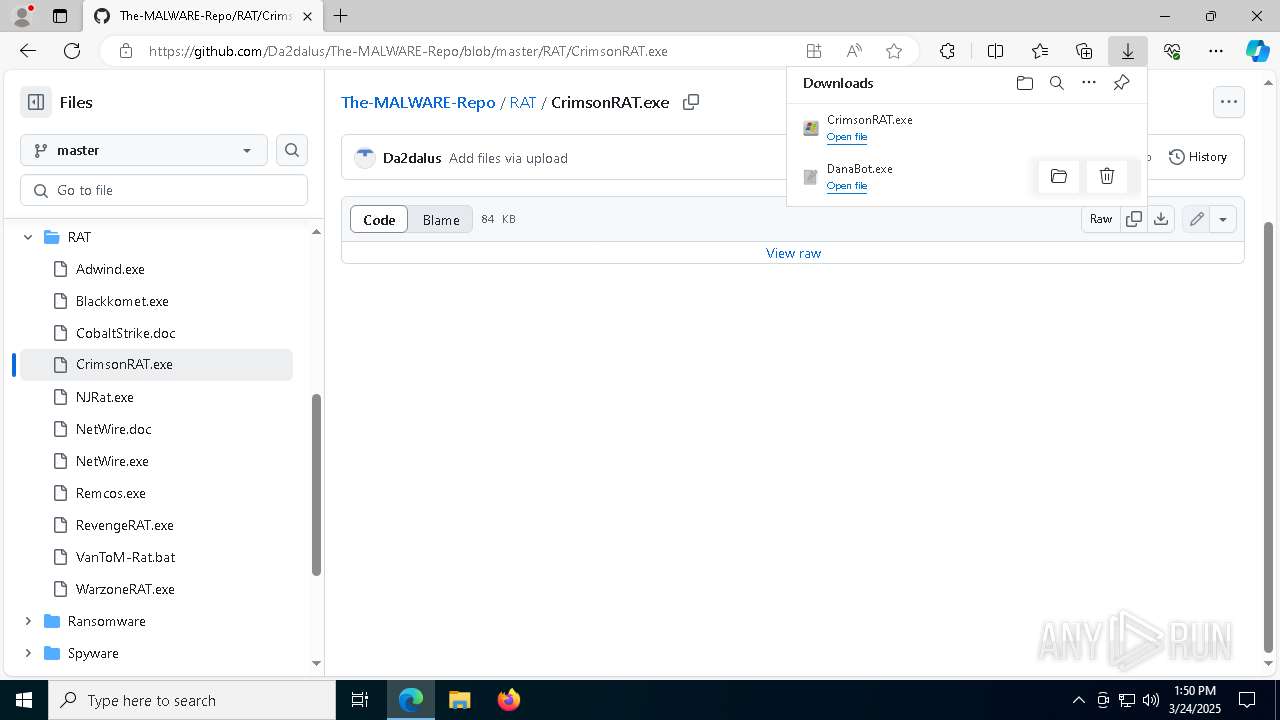
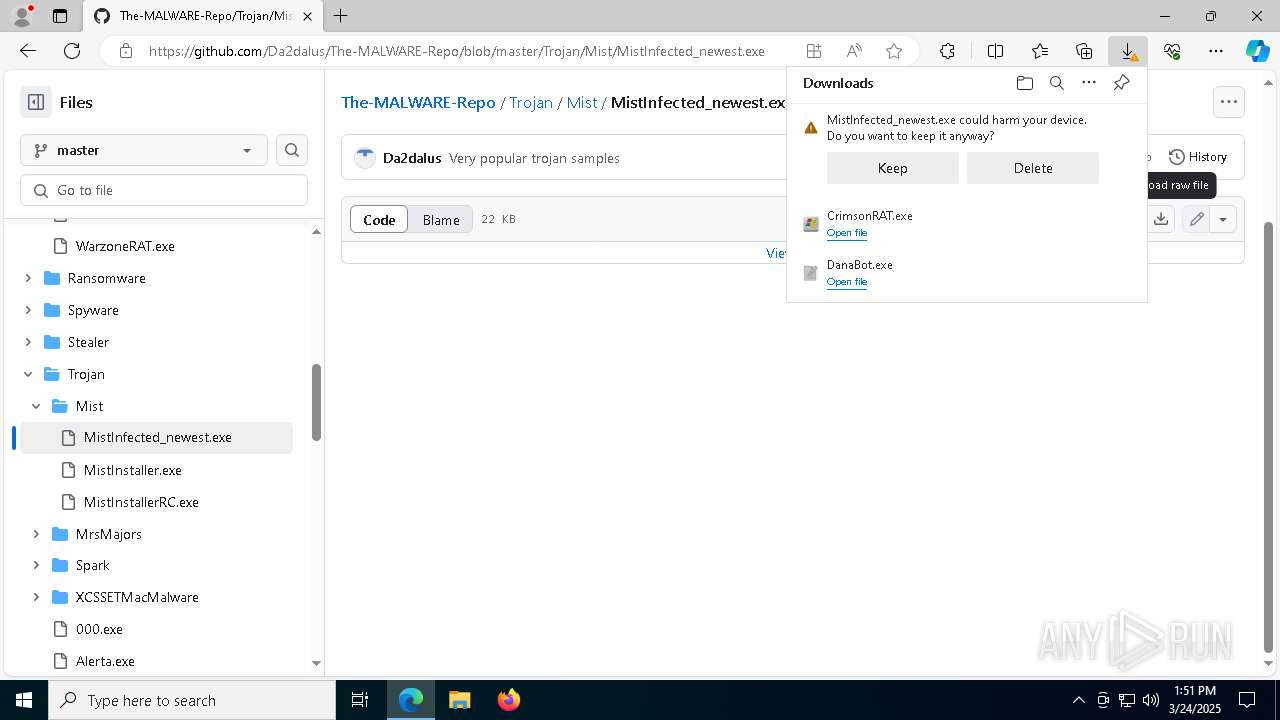
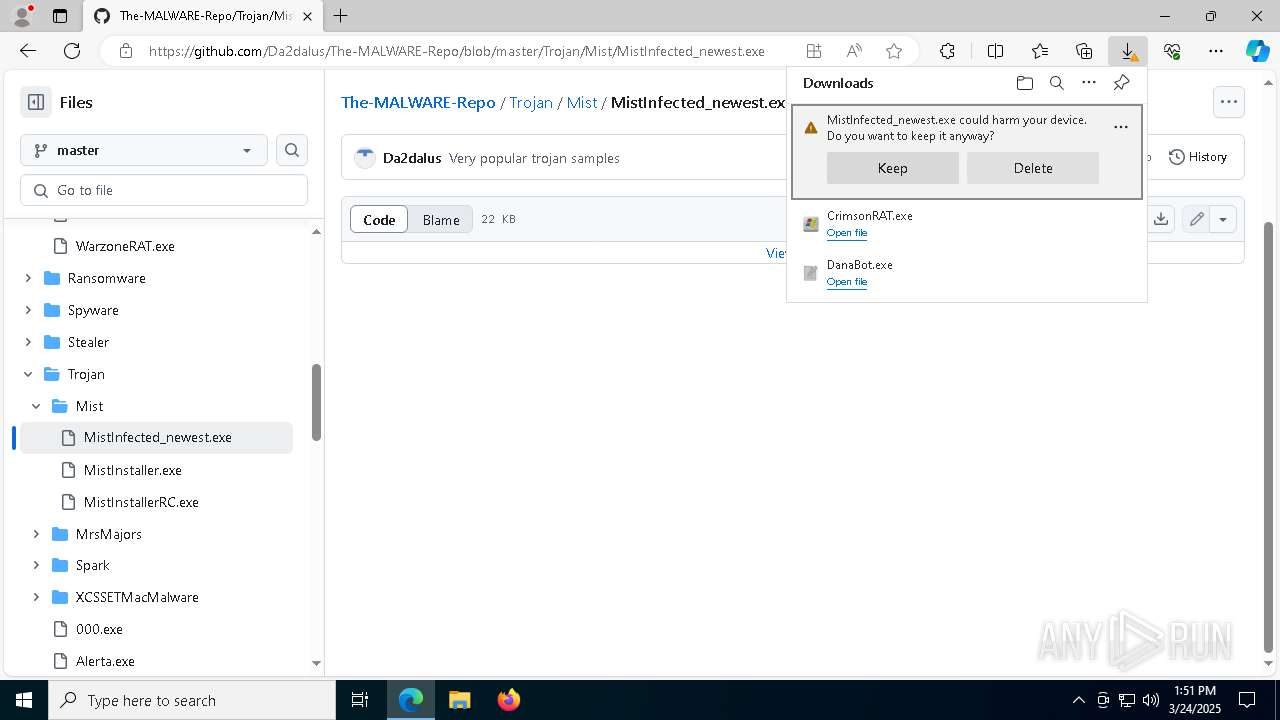
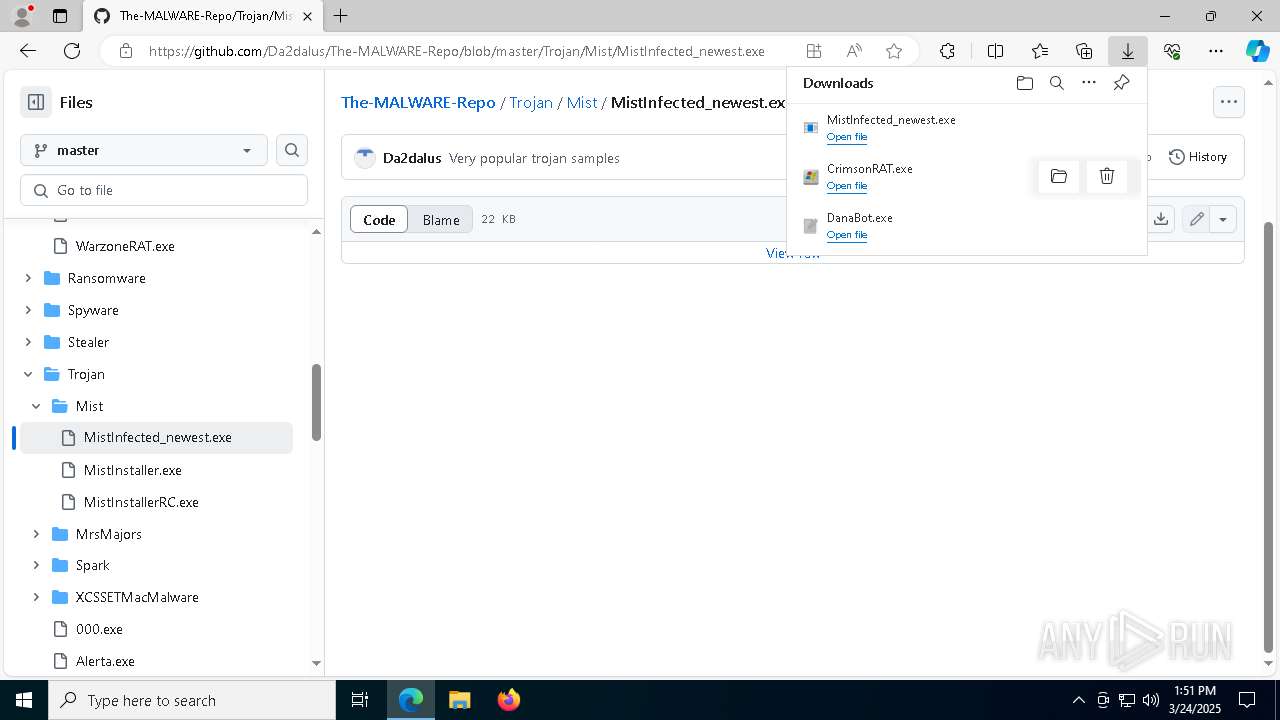
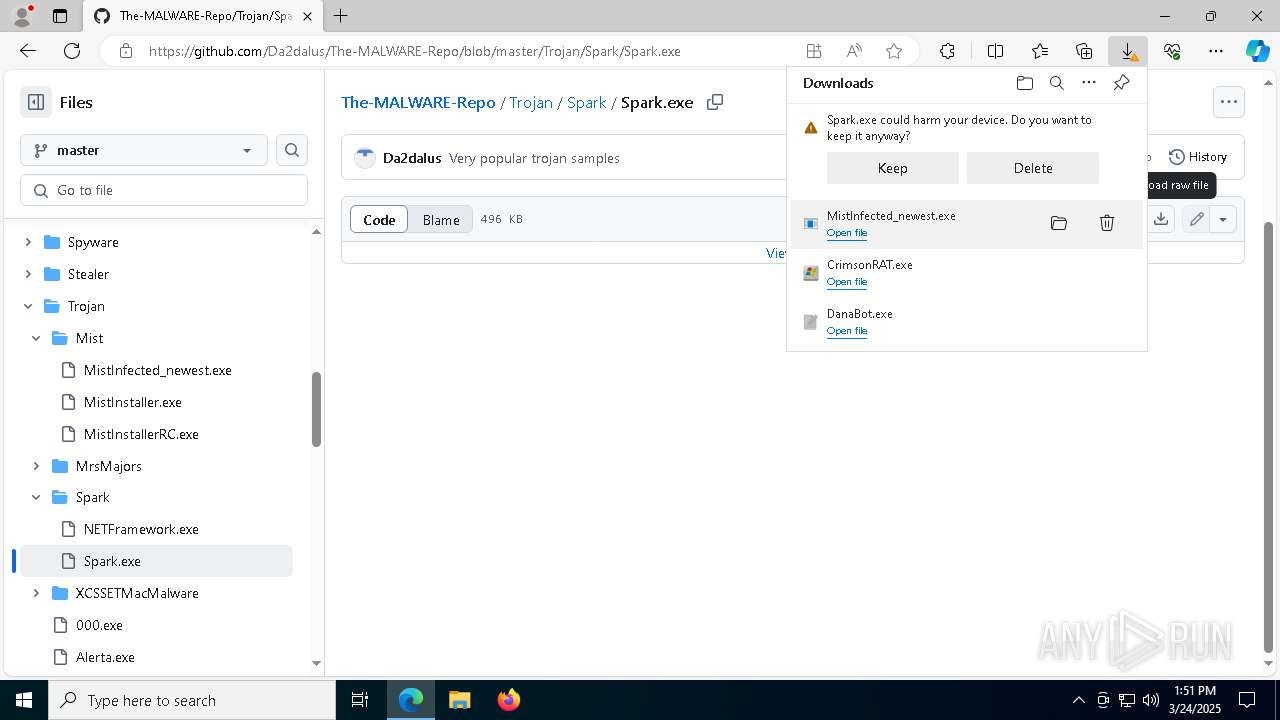
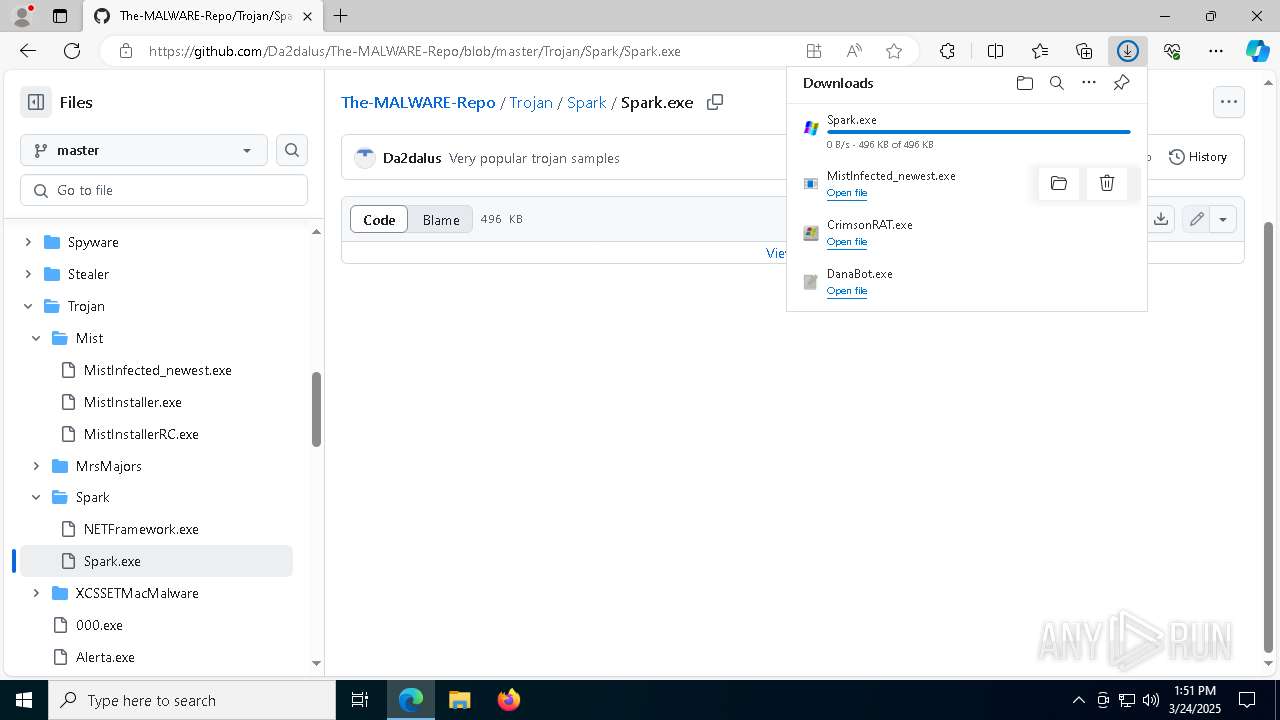
Executable content was dropped or overwritten
- DanaBot.exe (PID: 516)
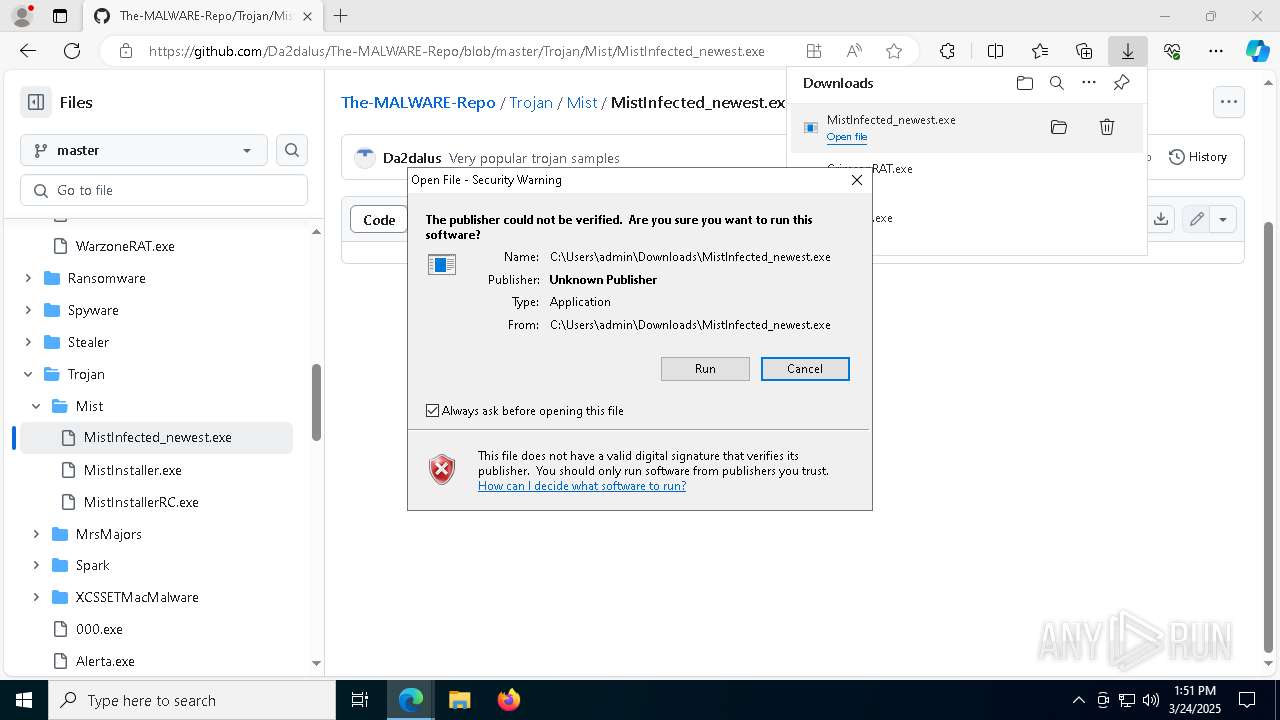
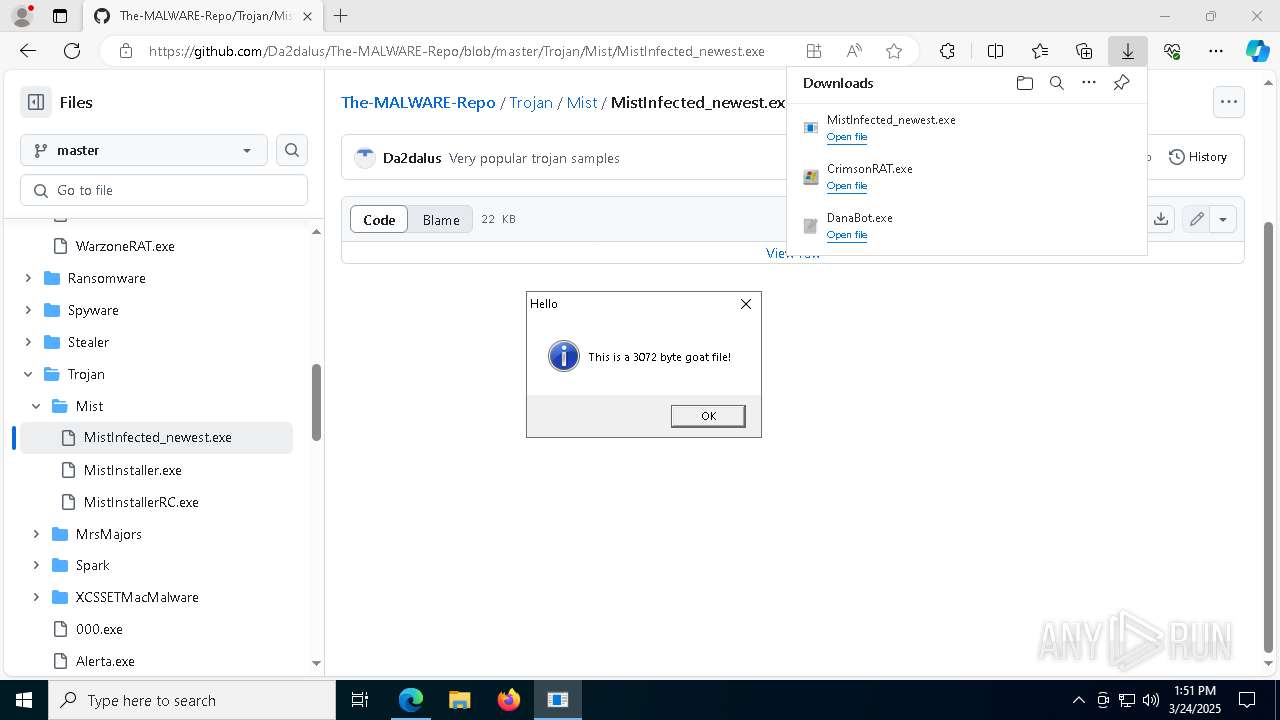
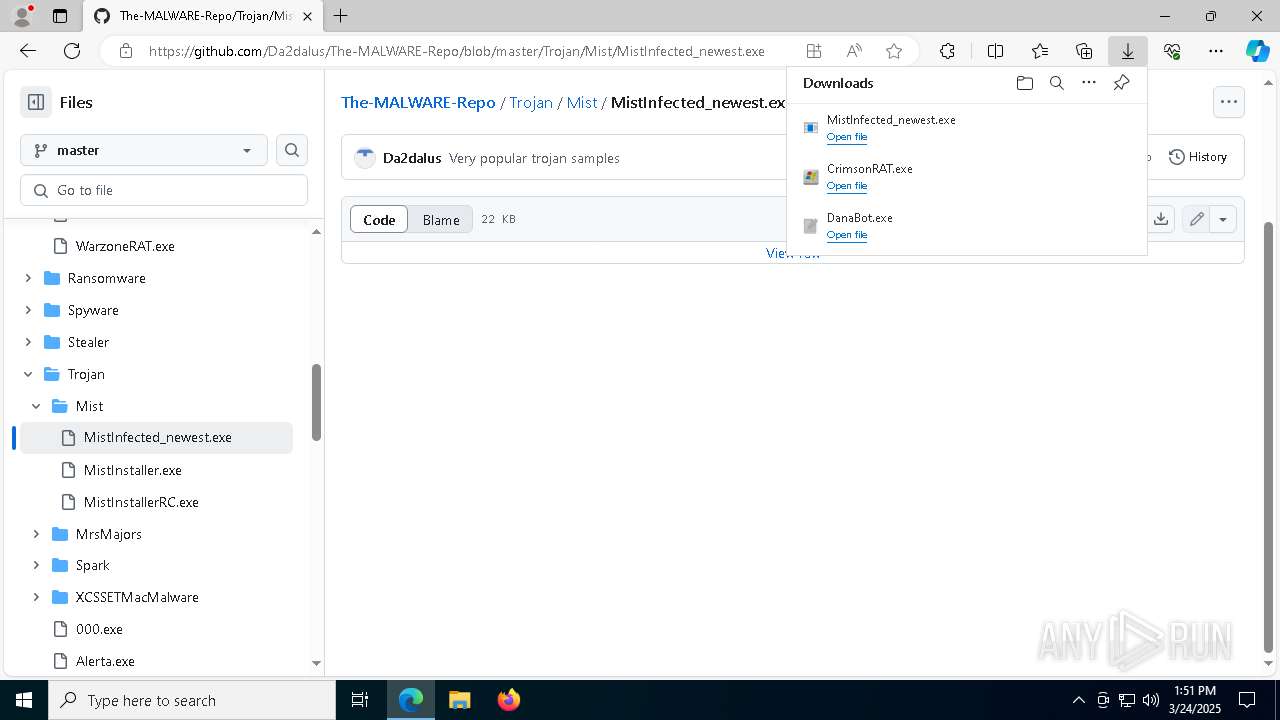
- MistInfected_newest.exe (PID: 8108)
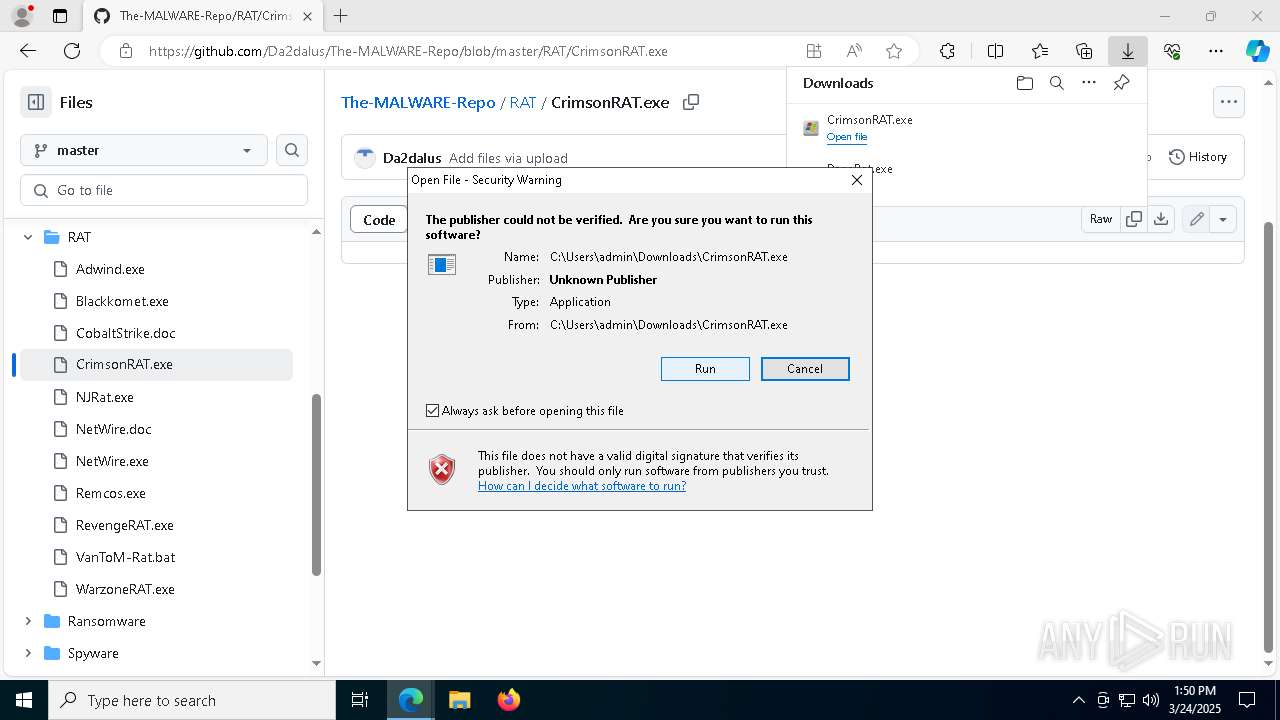
- CrimsonRAT.exe (PID: 5164)
- Spark.exe (PID: 3900)
- Spark.exe (PID: 1540)
There is functionality for taking screenshot (YARA)
- rundll32.exe (PID: 1676)
- Spark.exe (PID: 3900)
Connects to unusual port
- dlrarhsiva.exe (PID: 6972)
- dlrarhsiva.exe (PID: 9132)
Drops a system driver (possible attempt to evade defenses)
- Spark.exe (PID: 3900)
- Spark.exe (PID: 1540)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 904)
- Spark.exe (PID: 1540)
Creates or modifies Windows services
- Spark.exe (PID: 1540)
INFO
Application launched itself
- msedge.exe (PID: 2320)
- msedge.exe (PID: 5400)
Reads Environment values
- identity_helper.exe (PID: 8008)
Checks supported languages
- identity_helper.exe (PID: 8008)
- CrimsonRAT.exe (PID: 5164)
- dlrarhsiva.exe (PID: 9132)
- MistInfected_newest.exe (PID: 6032)
- Spark.exe (PID: 6572)
- DanaBot.exe (PID: 516)
Reads the computer name
- identity_helper.exe (PID: 8008)
- dlrarhsiva.exe (PID: 9132)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8568)
- BackgroundTransferHost.exe (PID: 8772)
- BackgroundTransferHost.exe (PID: 8200)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8772)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8772)
Reads the machine GUID from the registry
- DanaBot.exe (PID: 516)
- CrimsonRAT.exe (PID: 5164)
- dlrarhsiva.exe (PID: 9132)
Creates files in the program directory
- regsvr32.exe (PID: 8772)
- CrimsonRAT.exe (PID: 5164)
- CrimsonRAT.exe (PID: 6800)
Compiled with Borland Delphi (YARA)
- rundll32.exe (PID: 1676)
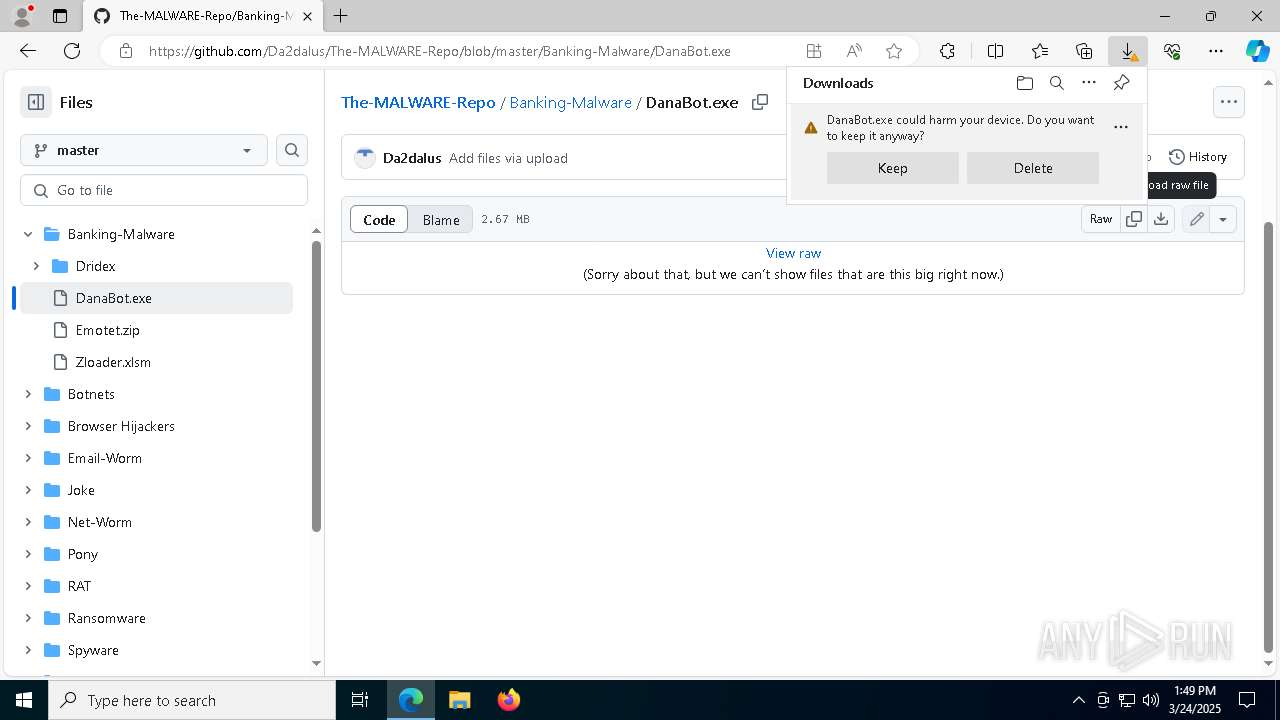
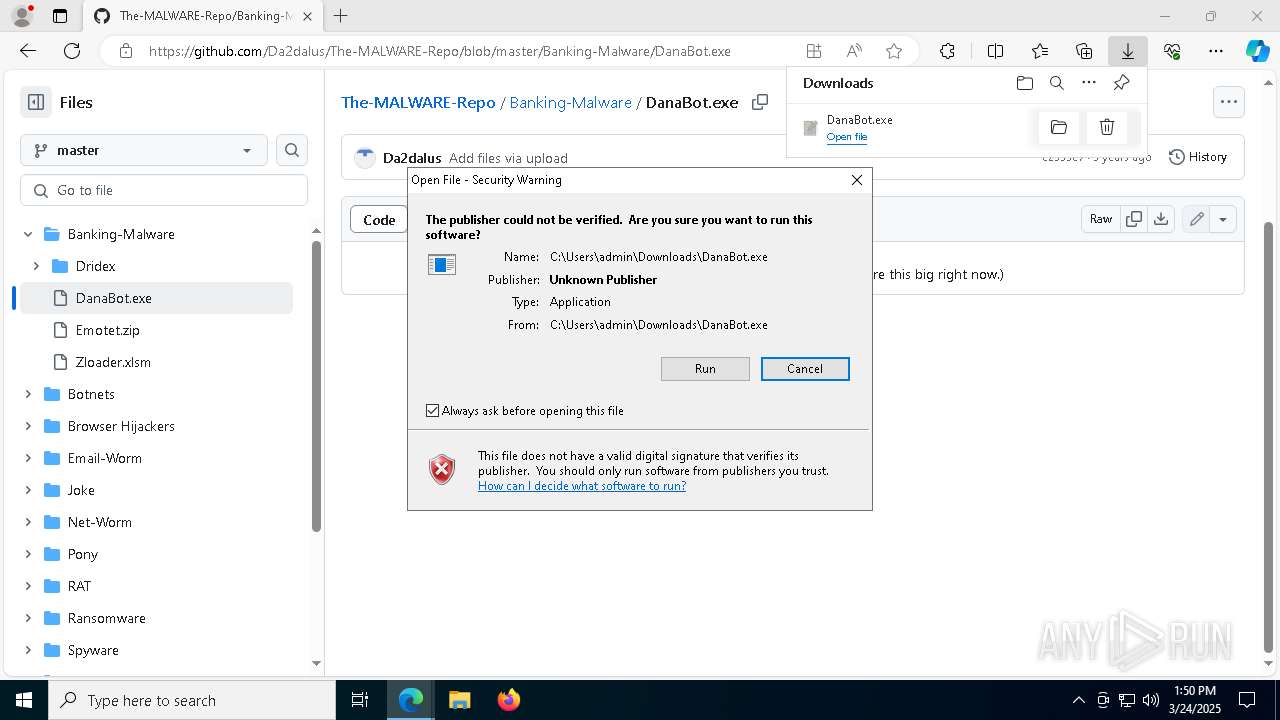
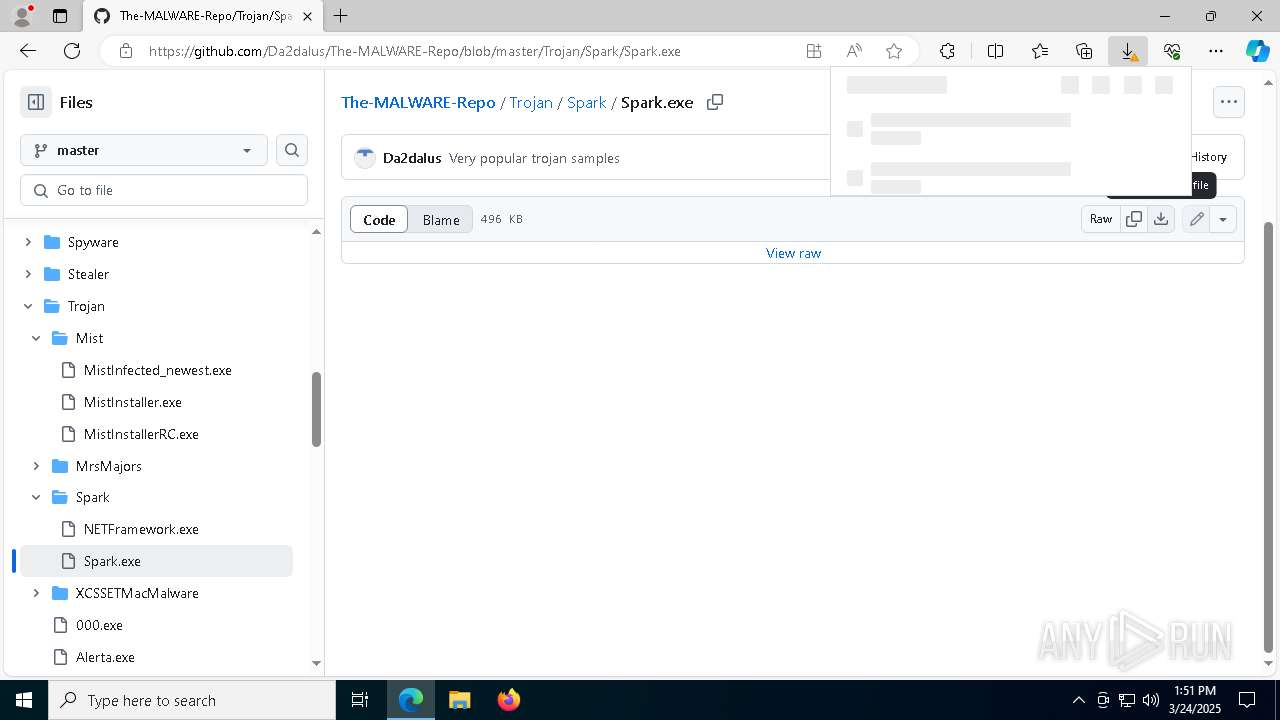
Autorun file from Downloads
- msedge.exe (PID: 2904)
- msedge.exe (PID: 2268)
- msedge.exe (PID: 9040)
- msedge.exe (PID: 2320)
- msedge.exe (PID: 8600)
Create files in a temporary directory
- MistInfected_newest.exe (PID: 8108)
Executable content was dropped or overwritten
- msedge.exe (PID: 5344)
- msedge.exe (PID: 2320)
- msedge.exe (PID: 7376)
The sample compiled with english language support
- msedge.exe (PID: 5344)
Manual execution by a user
- mspaint.exe (PID: 7064)
- msedge.exe (PID: 5400)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
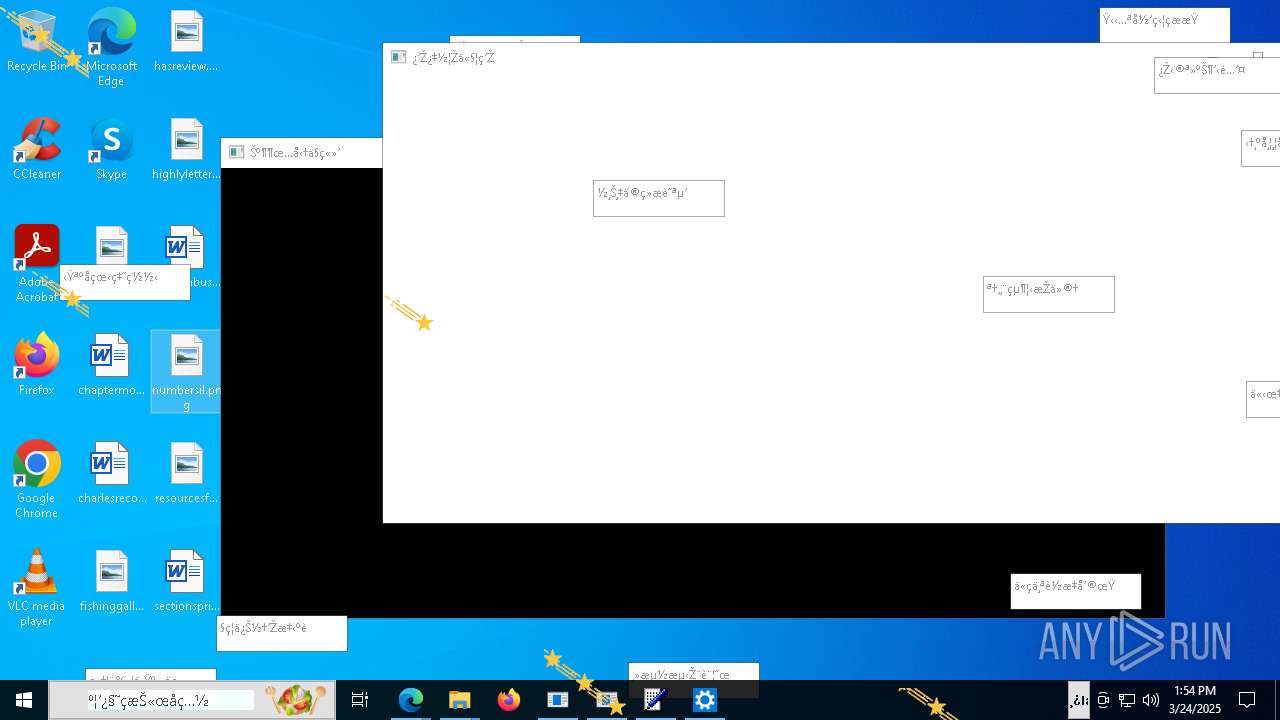
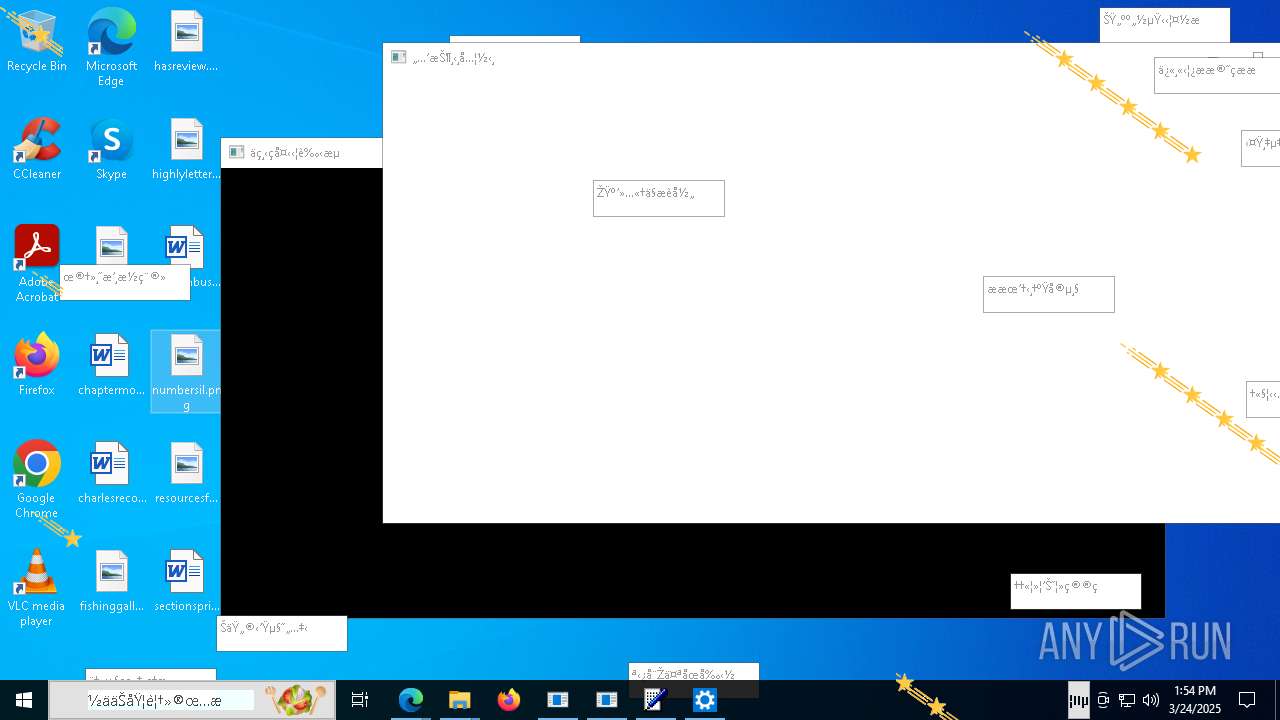
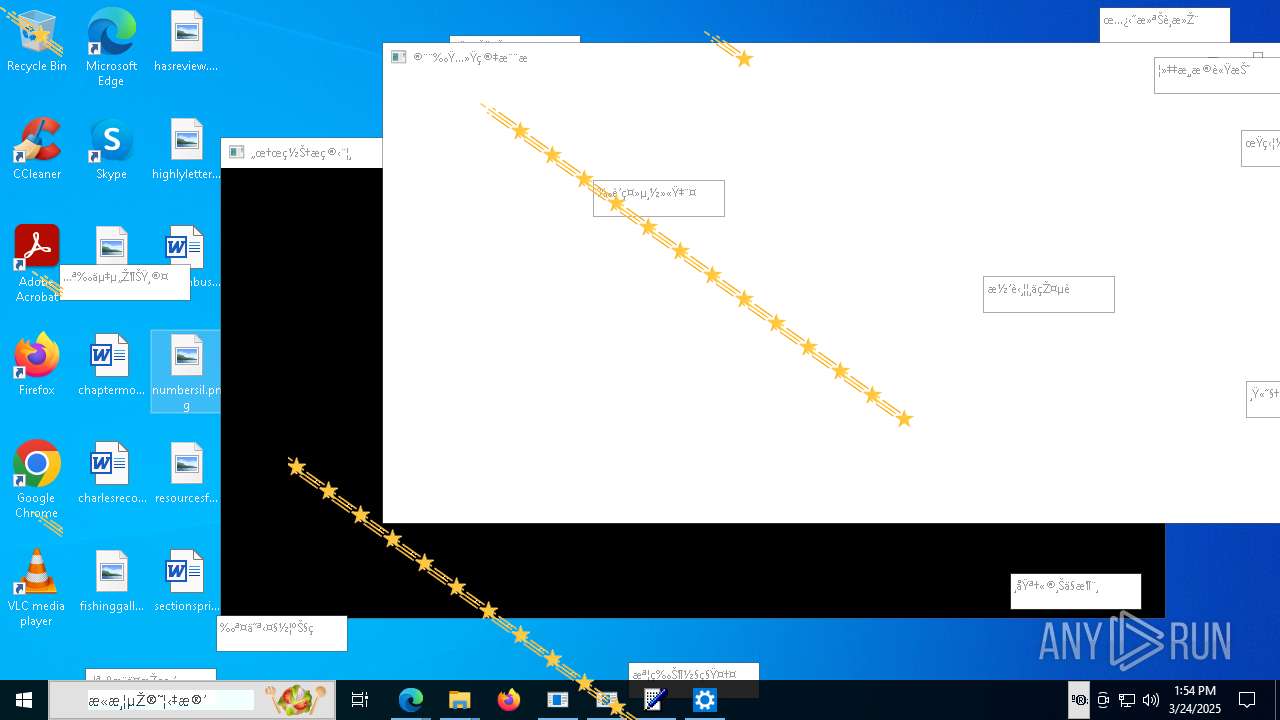
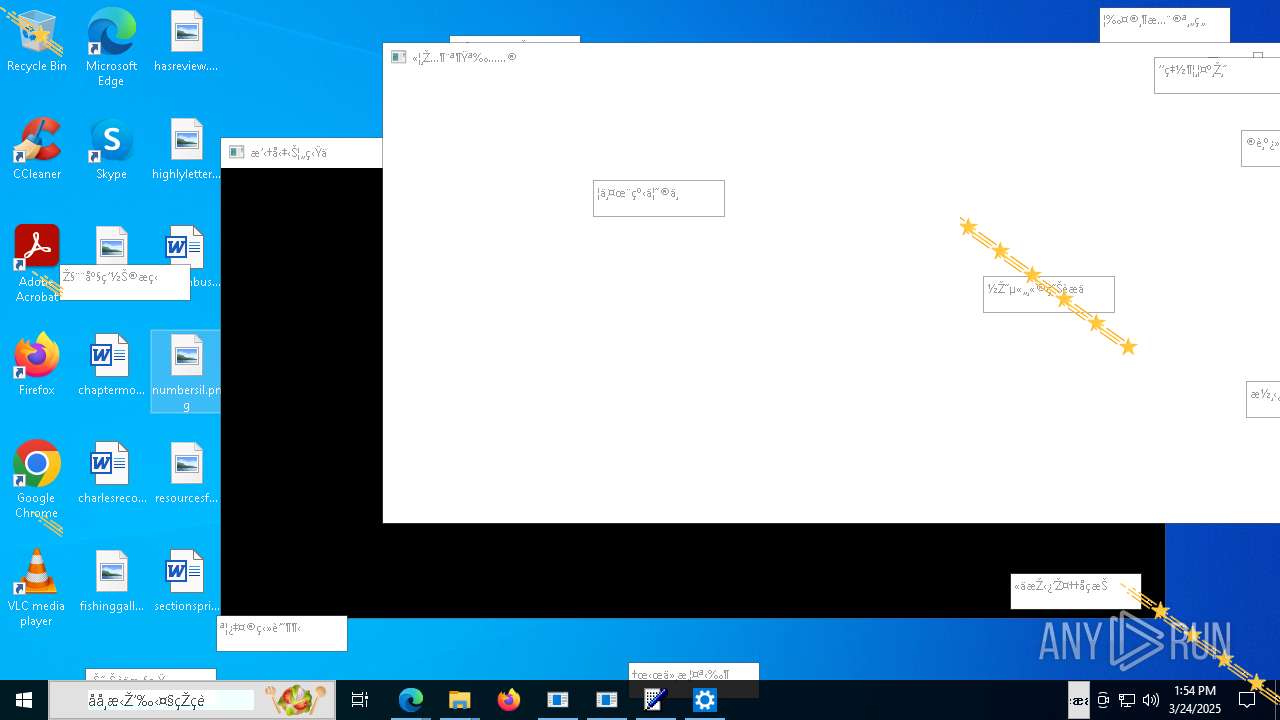
Total processes
384
Monitored processes
104
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Users\admin\Downloads\DanaBot.exe" | C:\Users\admin\Downloads\DanaBot.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225501 Modules
| |||||||||||||||
| 904 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5760 --field-trial-handle=2332,i,15017797774308176261,15165696725085001471,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5488 --field-trial-handle=2332,i,15017797774308176261,15165696725085001471,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1196 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 516 -s 496 | C:\Windows\SysWOW64\WerFault.exe | — | DanaBot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1540 | "C:\WINDOWS\File Cache\Spark.exe" | C:\Windows\File Cache\Spark.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 1676 | C:\WINDOWS\SysWOW64\rundll32.exe C:\Users\admin\DOWNLO~1\DanaBot.dll,f0 | C:\Windows\SysWOW64\rundll32.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1404 --field-trial-handle=2332,i,15017797774308176261,15165696725085001471,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1712 --field-trial-handle=2332,i,15017797774308176261,15165696725085001471,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/Da2dalus/The-MALWARE-Repo" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
18 759
Read events
18 638
Write events
120
Delete events
1
Modification events
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 32A4DF27AD8F2F00 | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F3BCE727AD8F2F00 | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197380 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {70D1E617-24BB-409A-AB34-FC4D946C2476} | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197380 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BFB2FDB0-3F46-48E1-B075-9E2AC2880C14} | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197380 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6C73912A-DDF5-4D70-8F3C-8CCB1265DBB3} | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197380 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {149621CC-DAEC-4BB5-838C-B7527813EE6B} | |||
Executable files
67
Suspicious files
734
Text files
108
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 2320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
155
DNS requests
152
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8772 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.54.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6268 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6268 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6468 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4652 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2688c6f4-afb2-4642-ac94-4d8ec3bc7e14?P1=1743410605&P2=404&P3=2&P4=hyhvE6DAwDnwobVWRxP1xSzs4pdXvYRrsjD36Brrr%2f1UJAneIiIetBBuyyAgHflE51m8%2fzjYEPiE4HmEeuld8w%3d%3d | unknown | — | — | whitelisted |
4652 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2688c6f4-afb2-4642-ac94-4d8ec3bc7e14?P1=1743410605&P2=404&P3=2&P4=hyhvE6DAwDnwobVWRxP1xSzs4pdXvYRrsjD36Brrr%2f1UJAneIiIetBBuyyAgHflE51m8%2fzjYEPiE4HmEeuld8w%3d%3d | unknown | — | — | whitelisted |
4652 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2688c6f4-afb2-4642-ac94-4d8ec3bc7e14?P1=1743410605&P2=404&P3=2&P4=hyhvE6DAwDnwobVWRxP1xSzs4pdXvYRrsjD36Brrr%2f1UJAneIiIetBBuyyAgHflE51m8%2fzjYEPiE4HmEeuld8w%3d%3d | unknown | — | — | whitelisted |
4652 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2688c6f4-afb2-4642-ac94-4d8ec3bc7e14?P1=1743410605&P2=404&P3=2&P4=hyhvE6DAwDnwobVWRxP1xSzs4pdXvYRrsjD36Brrr%2f1UJAneIiIetBBuyyAgHflE51m8%2fzjYEPiE4HmEeuld8w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.54.122:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7376 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2320 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7376 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7376 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7376 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7376 | msedge.exe | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7376 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7376 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |