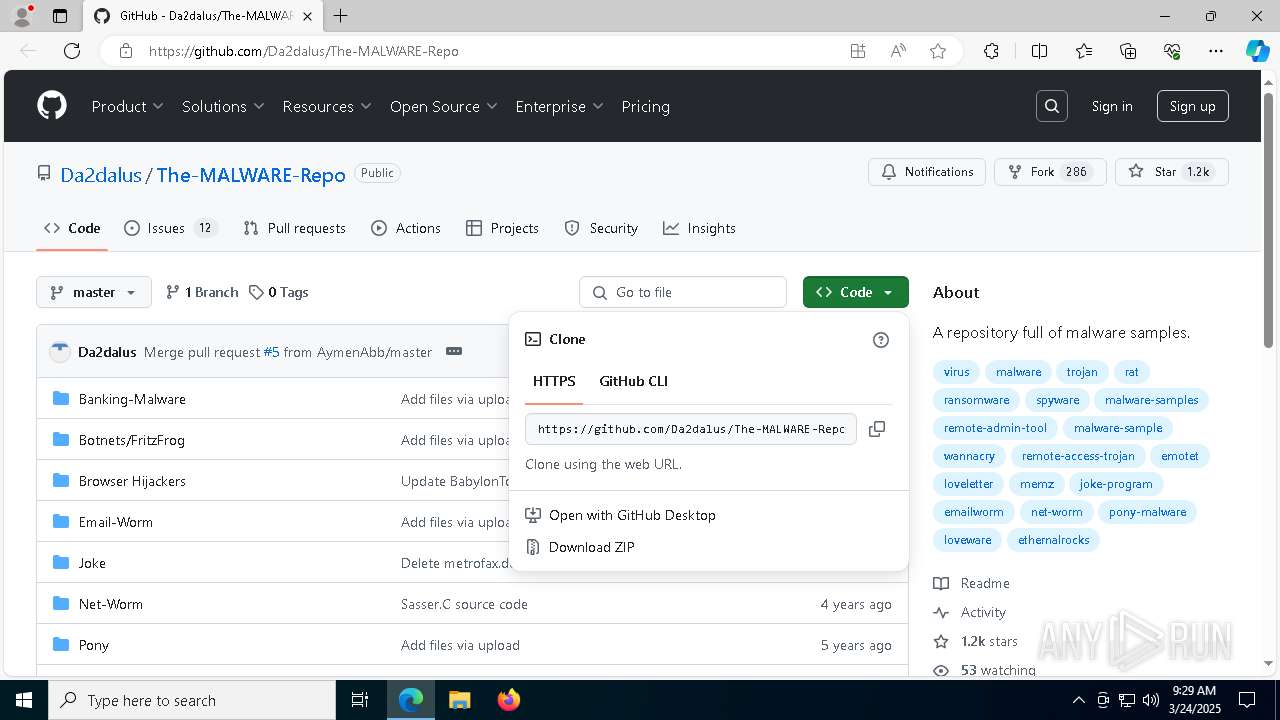
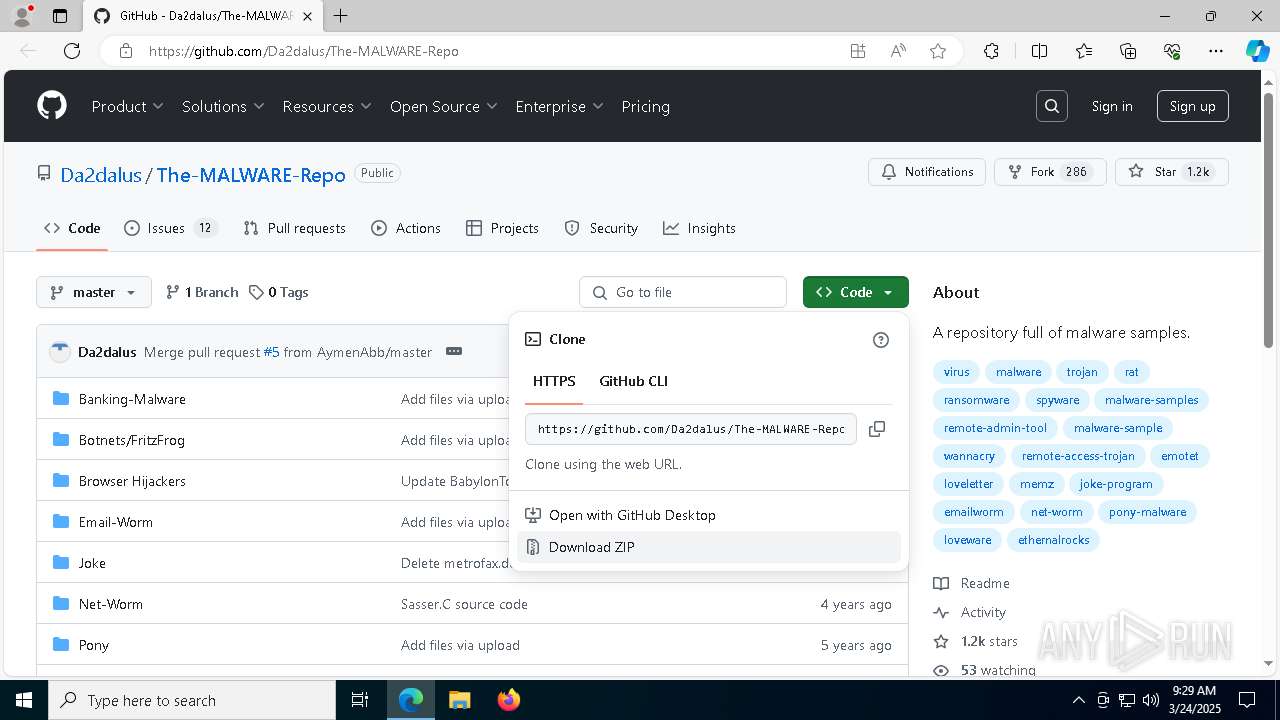
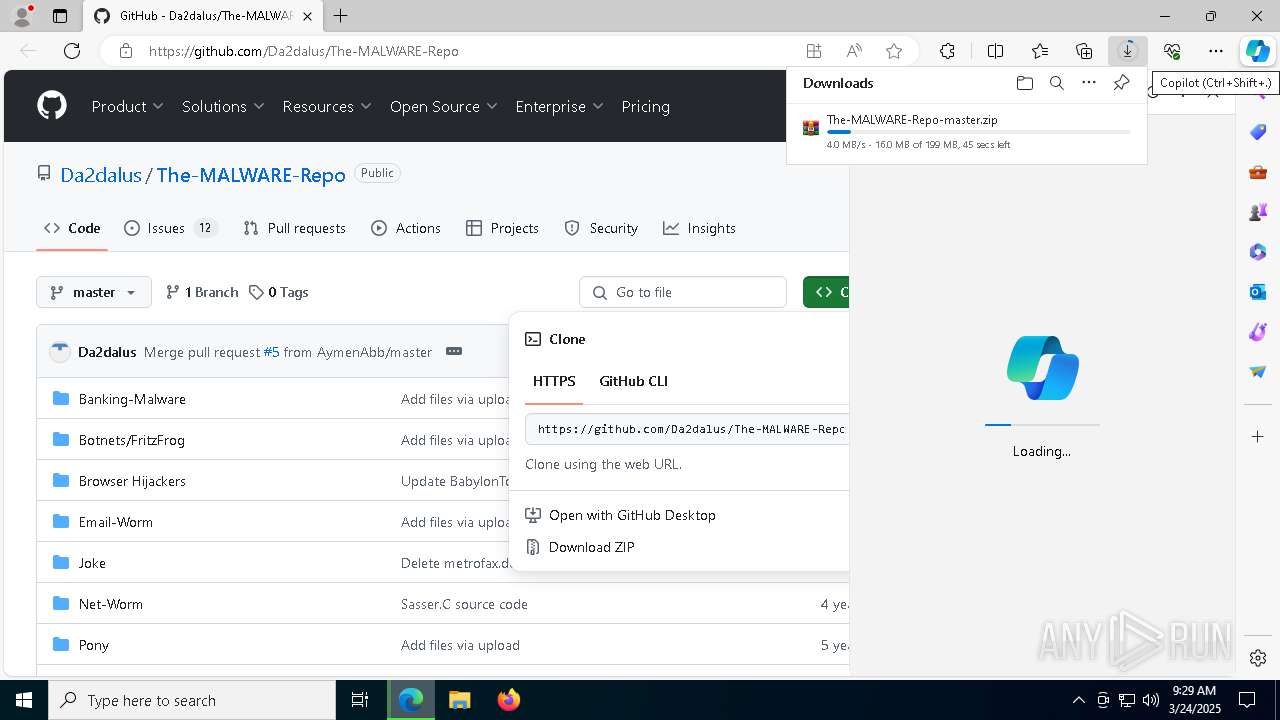
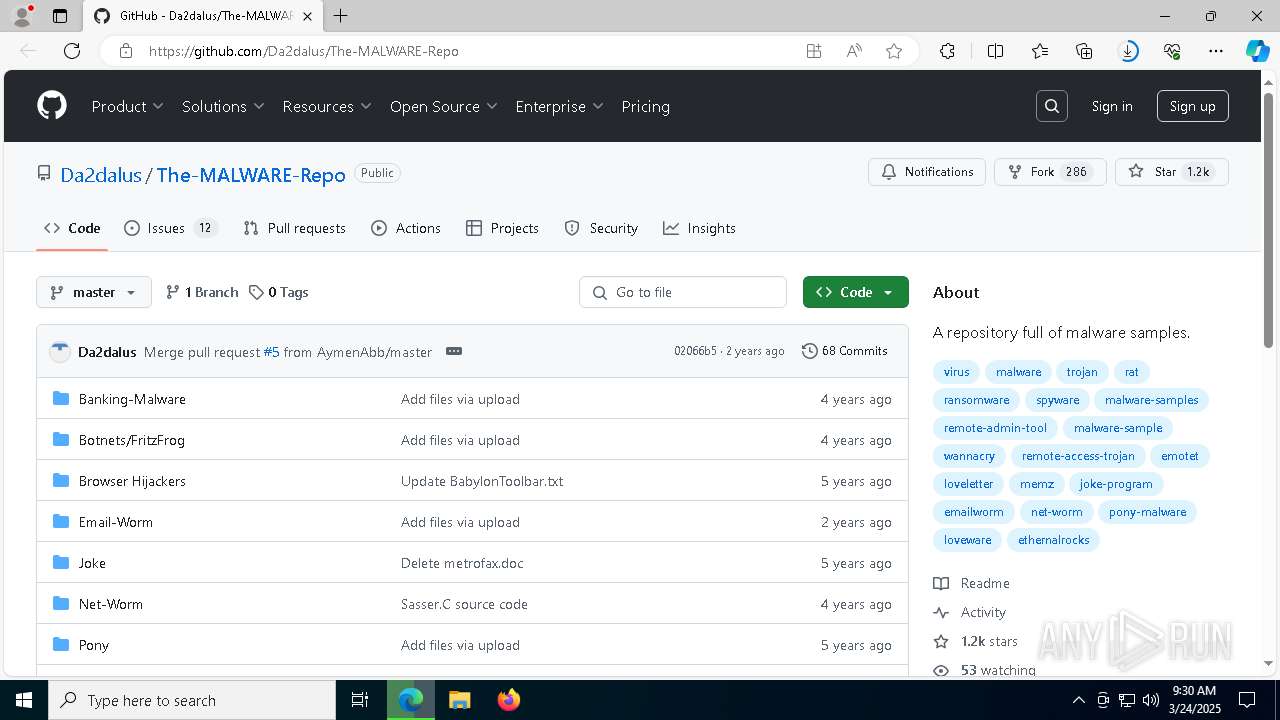
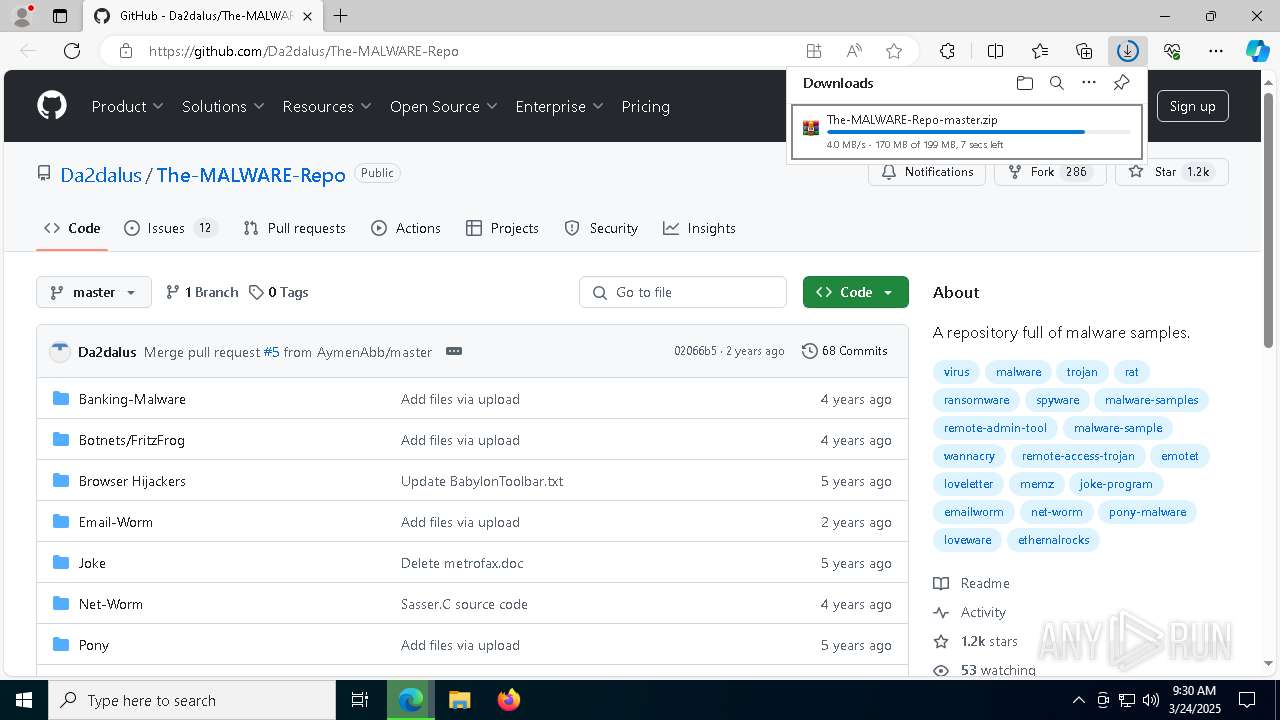
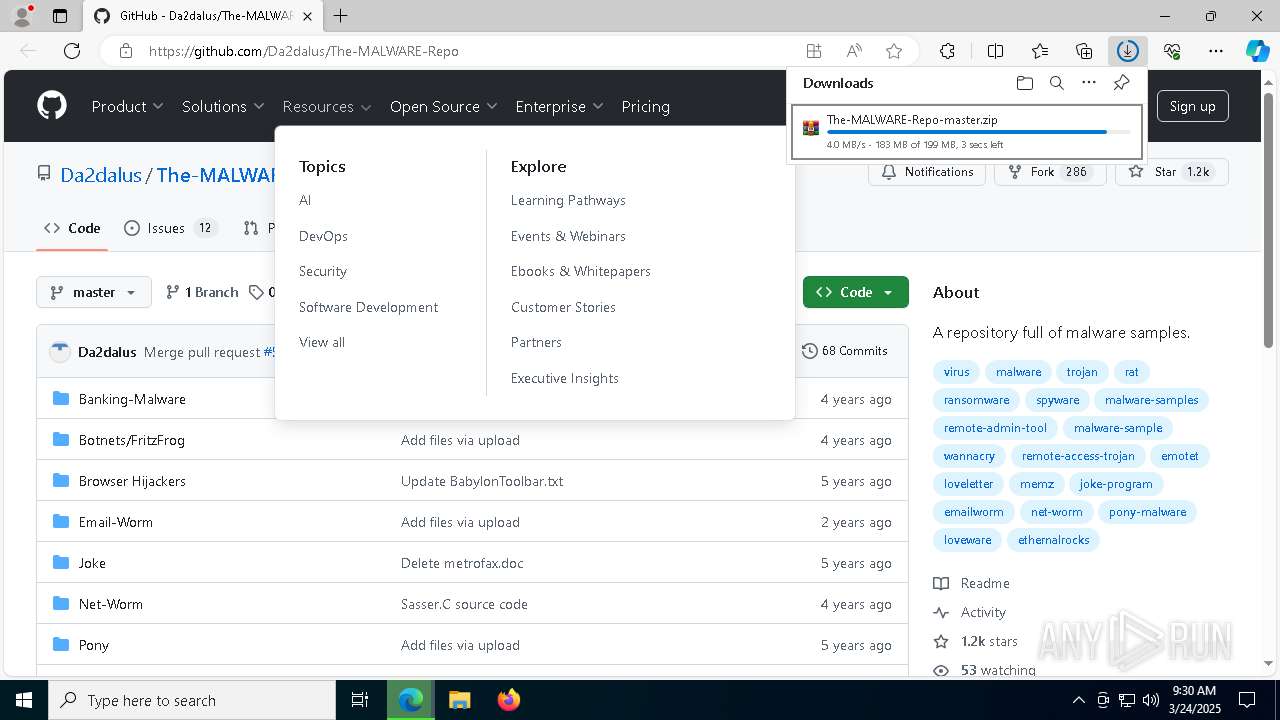
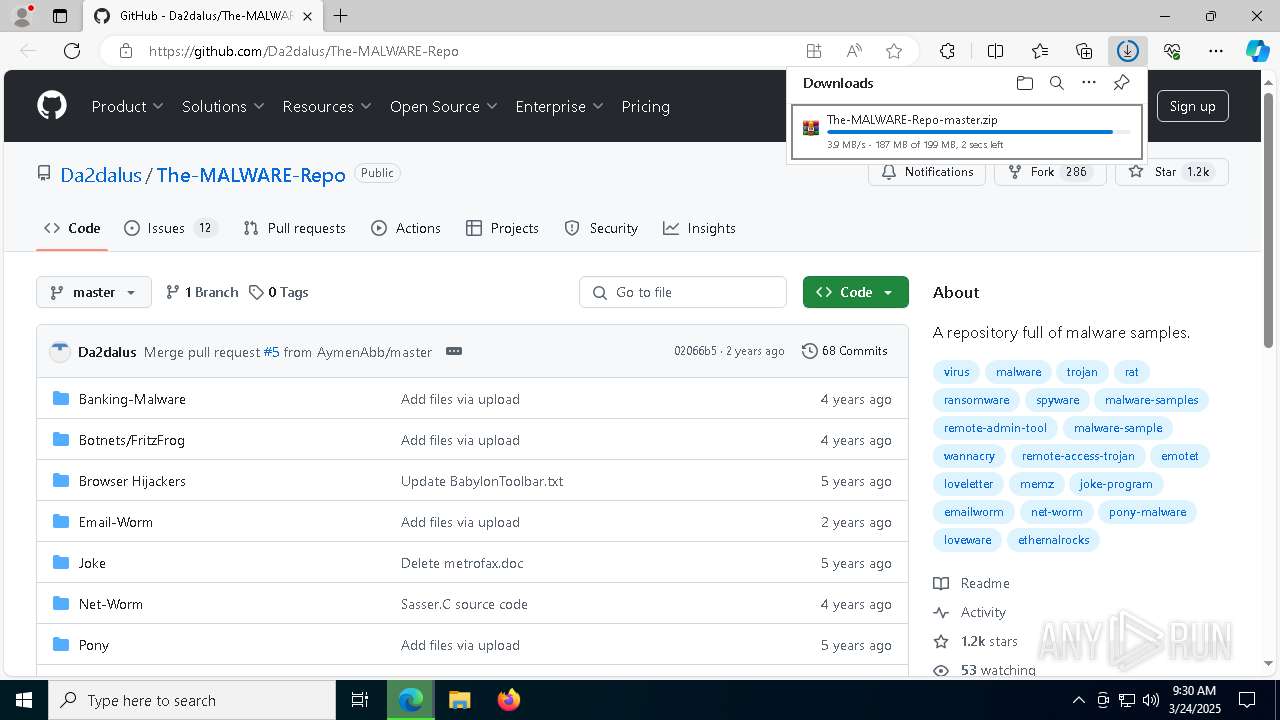
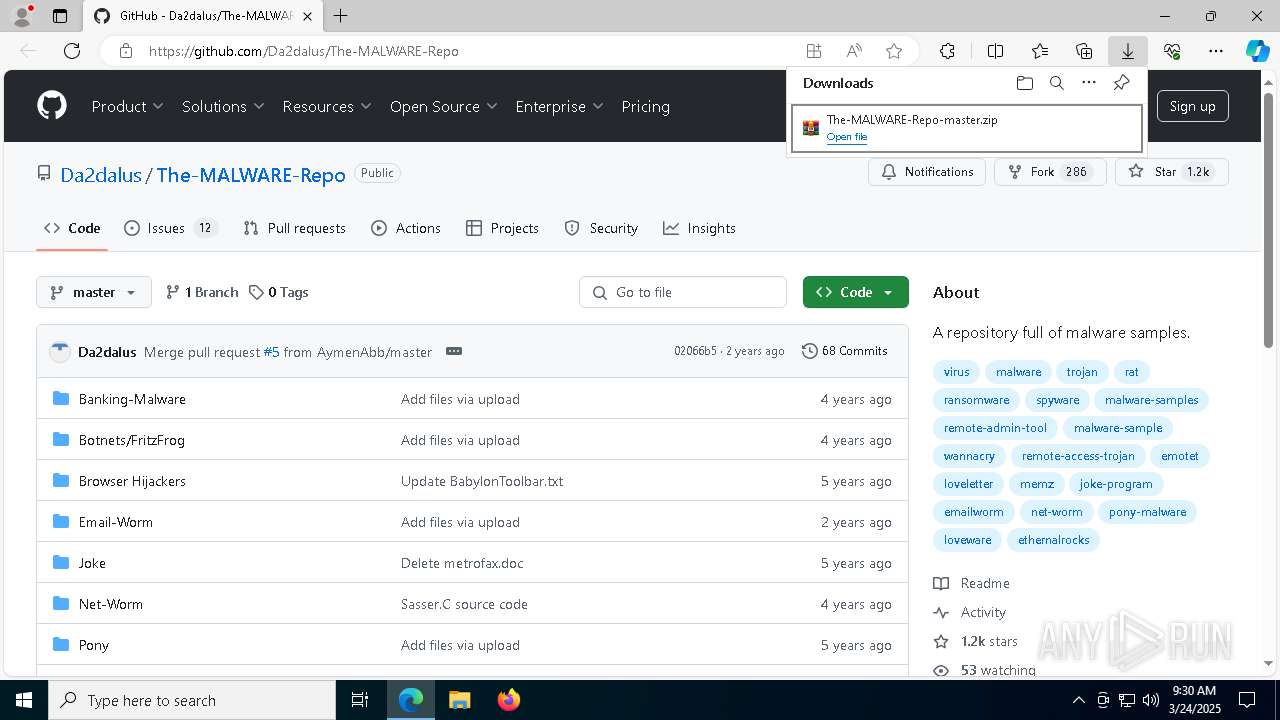
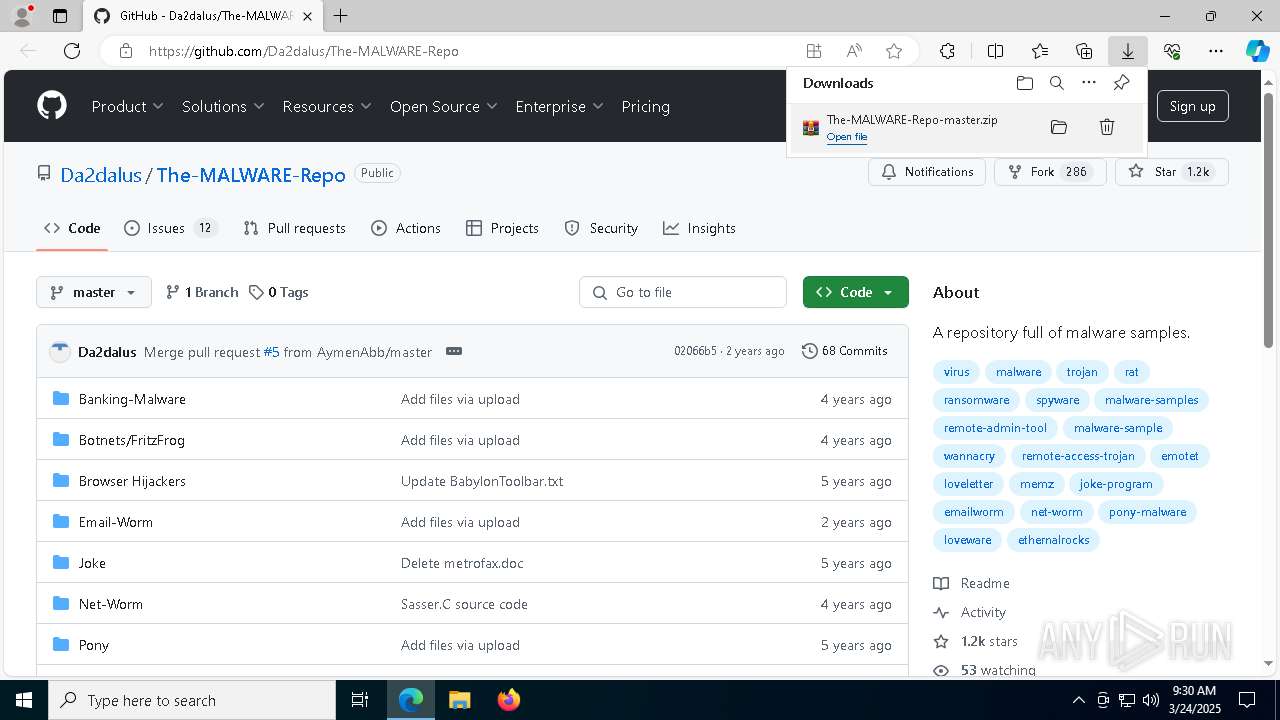
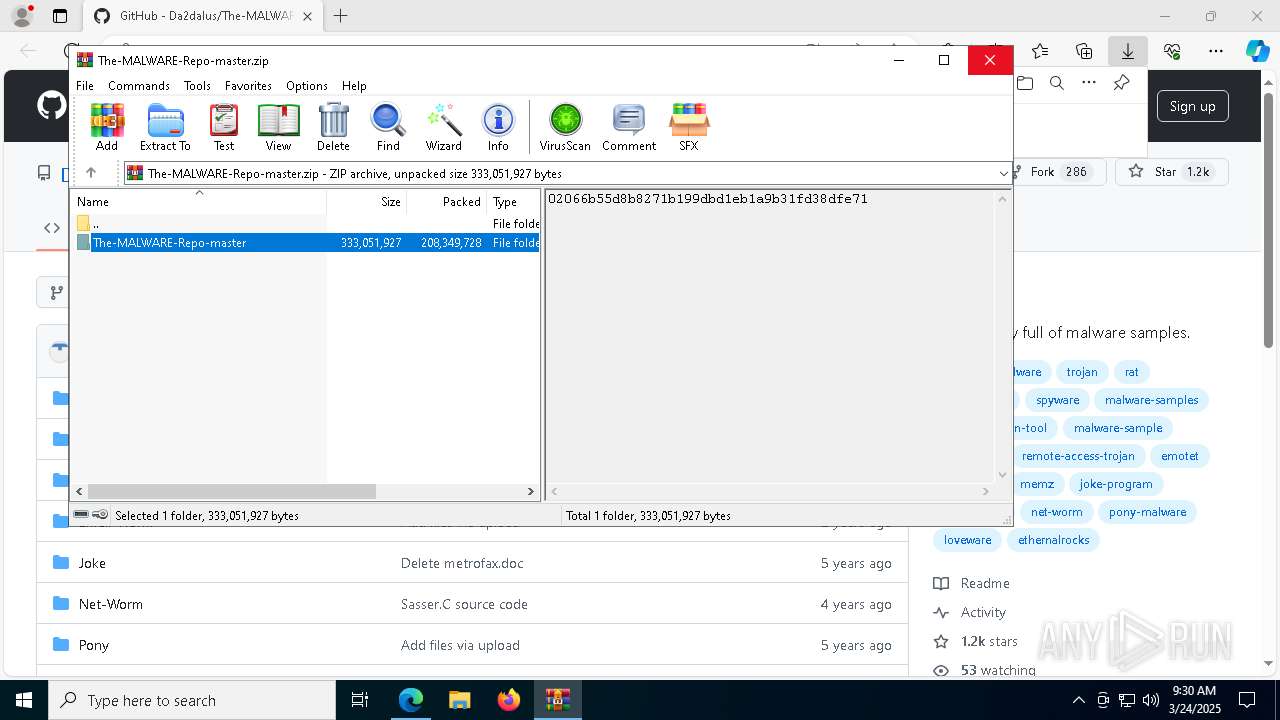
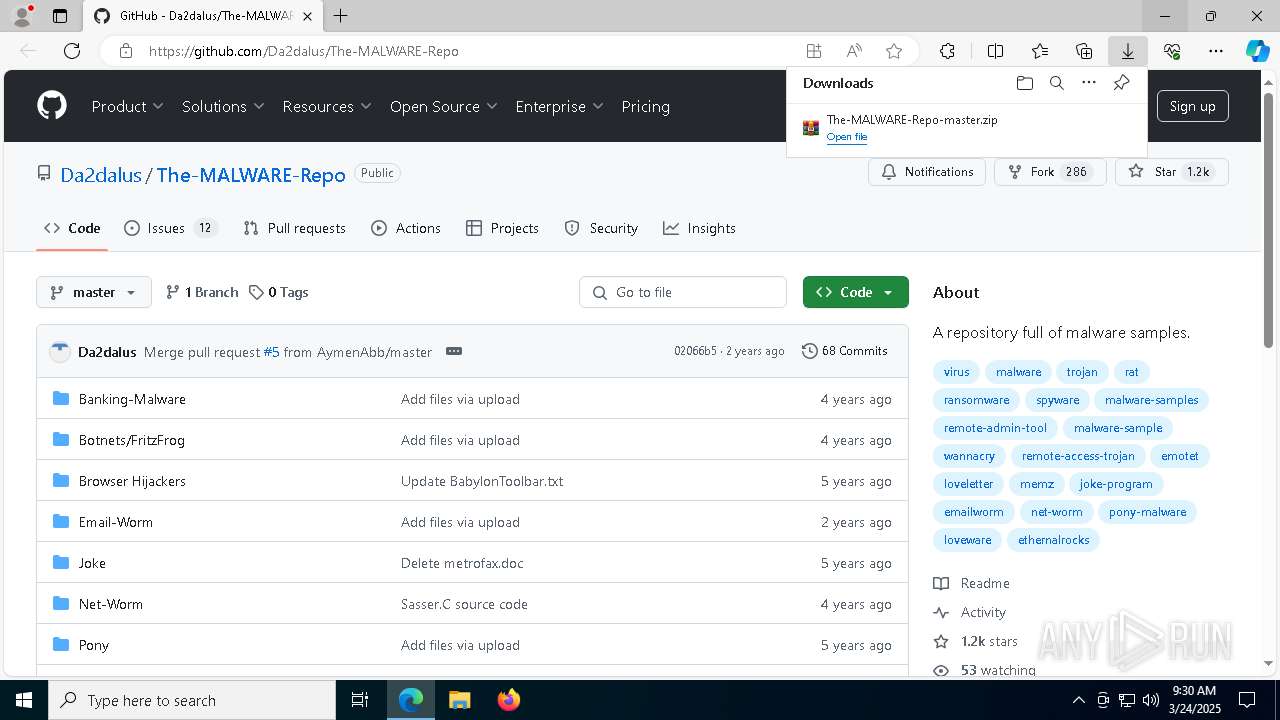
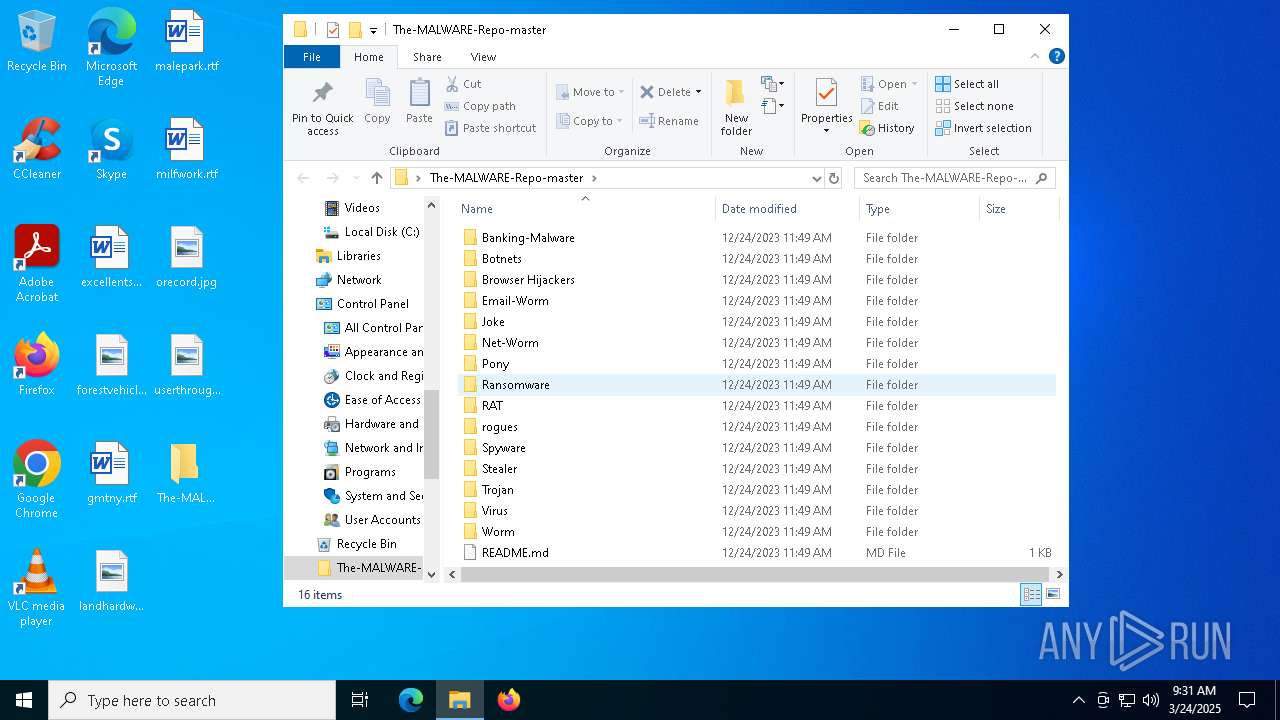
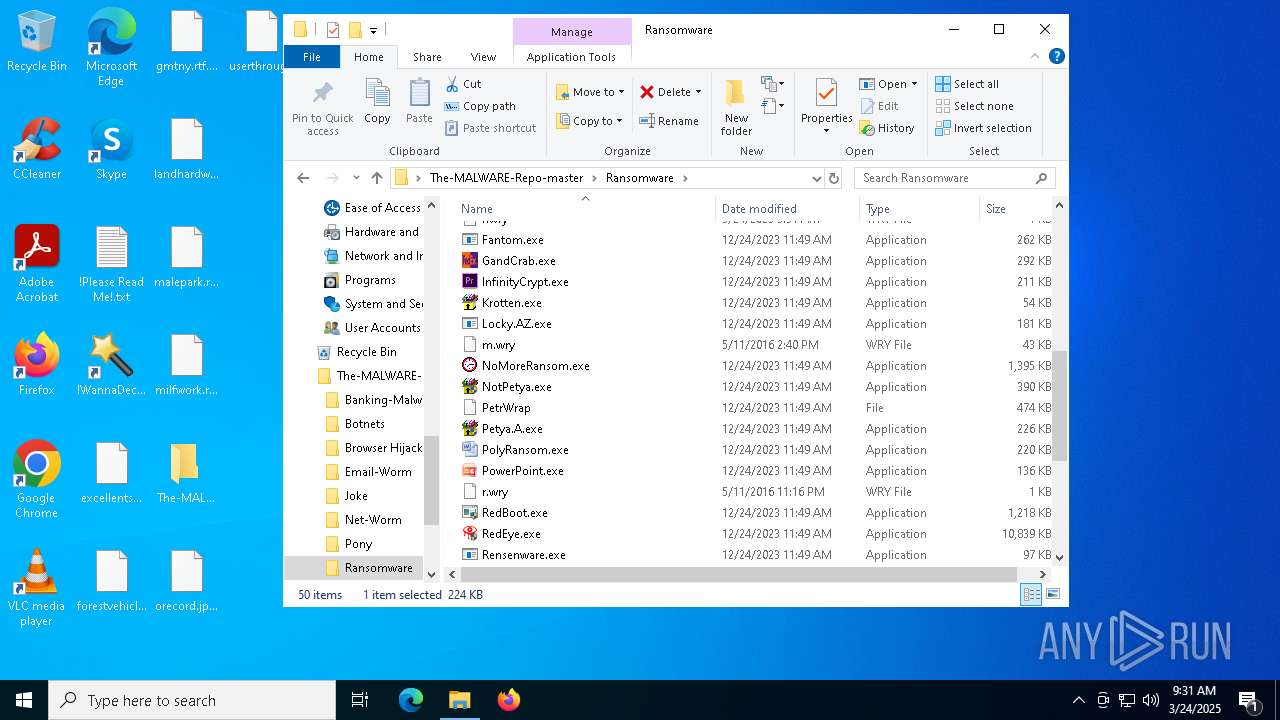
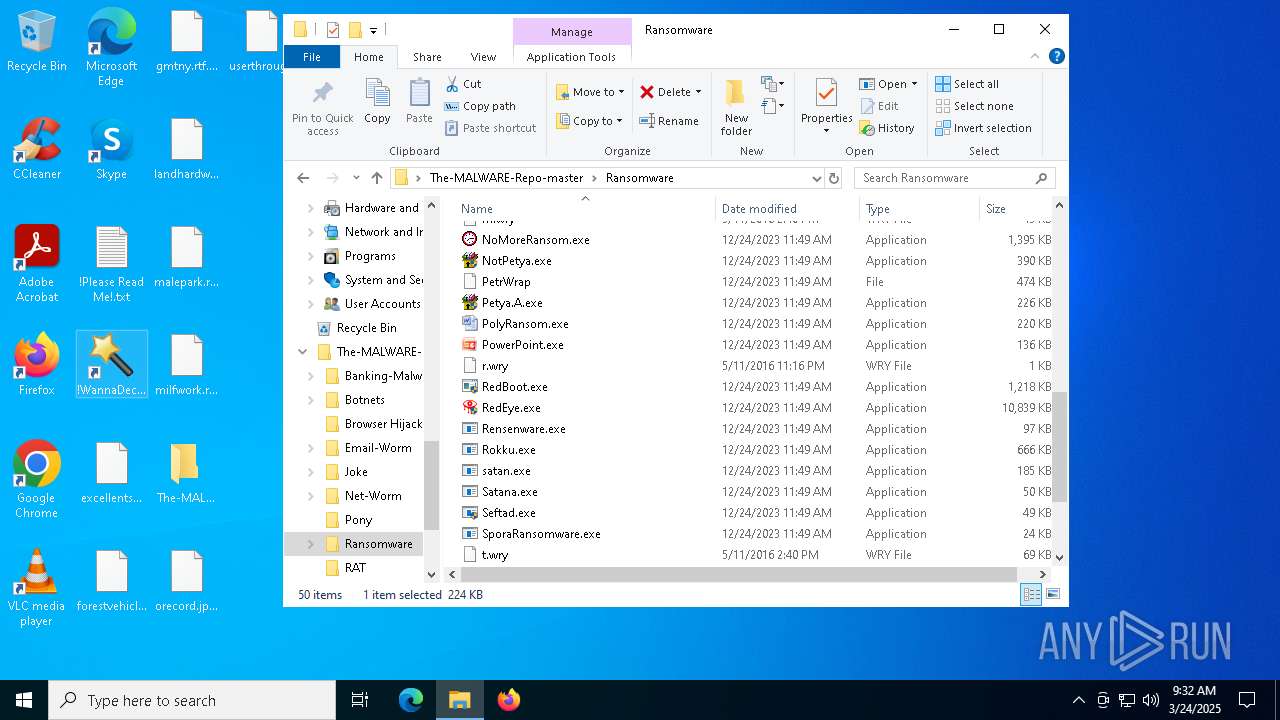
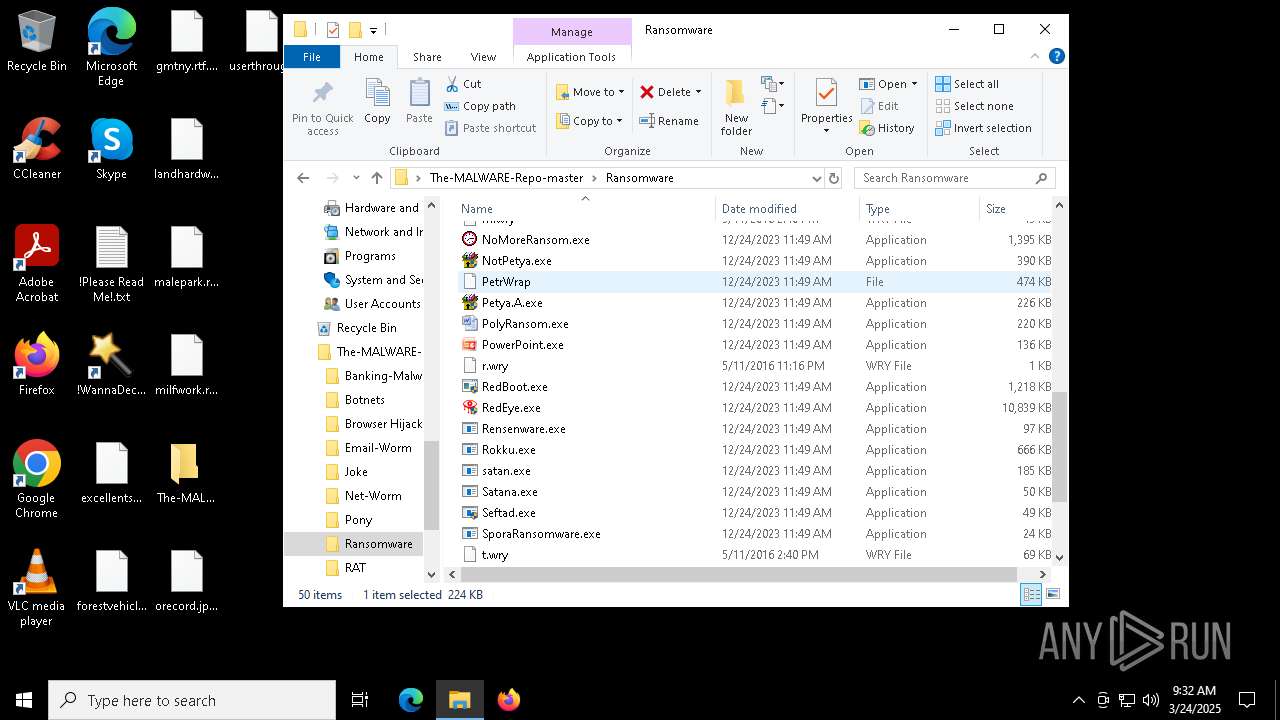
| URL: | https://github.com/Da2dalus/The-MALWARE-Repo |
| Full analysis: | https://app.any.run/tasks/5093d409-e94b-4208-b919-e7aea45e9a98 |
| Verdict: | Malicious activity |
| Threats: | Danabot is an advanced banking Trojan malware that was designed to steal financial information from victims. Out of the Trojans in the wild, this is one of the most advanced thanks to the modular design and a complex delivery method. |
| Analysis date: | March 24, 2025, 09:29:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 95DE222D86979D6785AD30792191C545 |
| SHA1: | 0328EC532FE1B34F32B83E99013C67D2B17579A1 |
| SHA256: | 6A8070F67E43F623ABA9B346120783FD9371ADBC25D2852C02BB12D9BBC6C58A |
| SSDEEP: | 3:N8tEdJejSOpykOK:2ubYSOc0 |
MALICIOUS
DESKTOPBOOM has been detected
- WinRAR.exe (PID: 644)
DARKCOMET has been found (auto)
- WinRAR.exe (PID: 644)
DANABOT has been found (auto)
- WinRAR.exe (PID: 644)
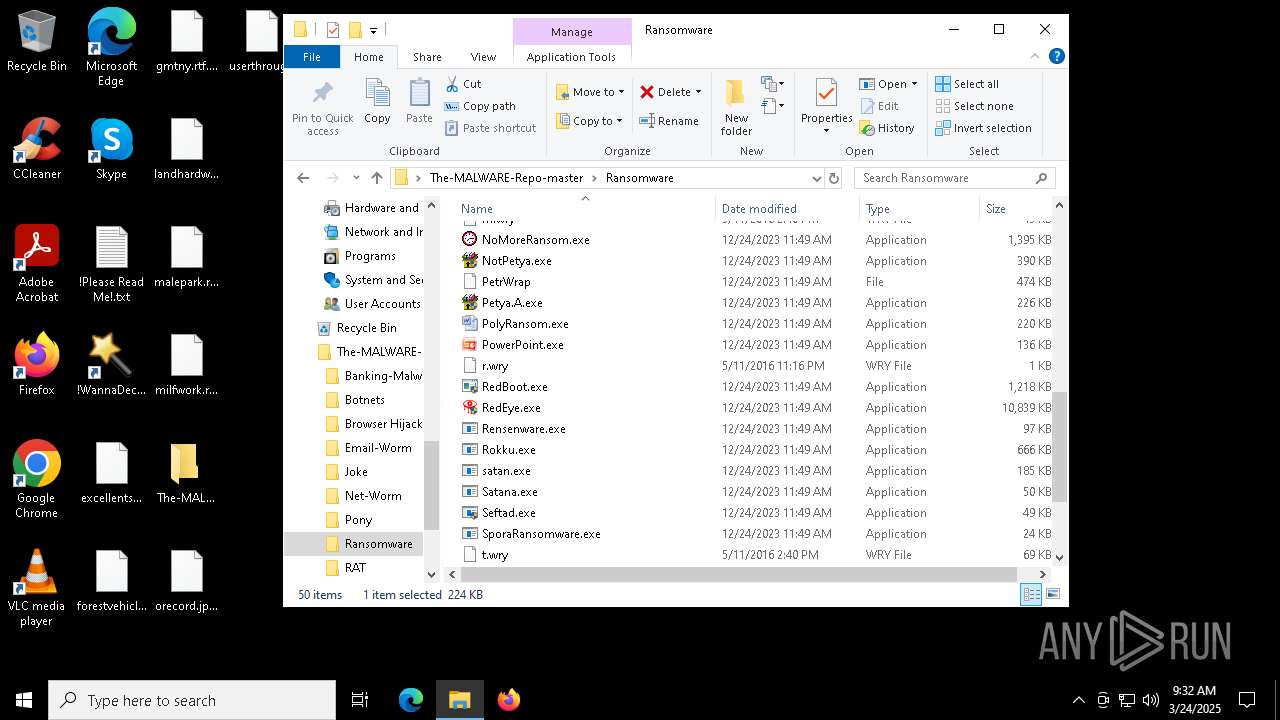
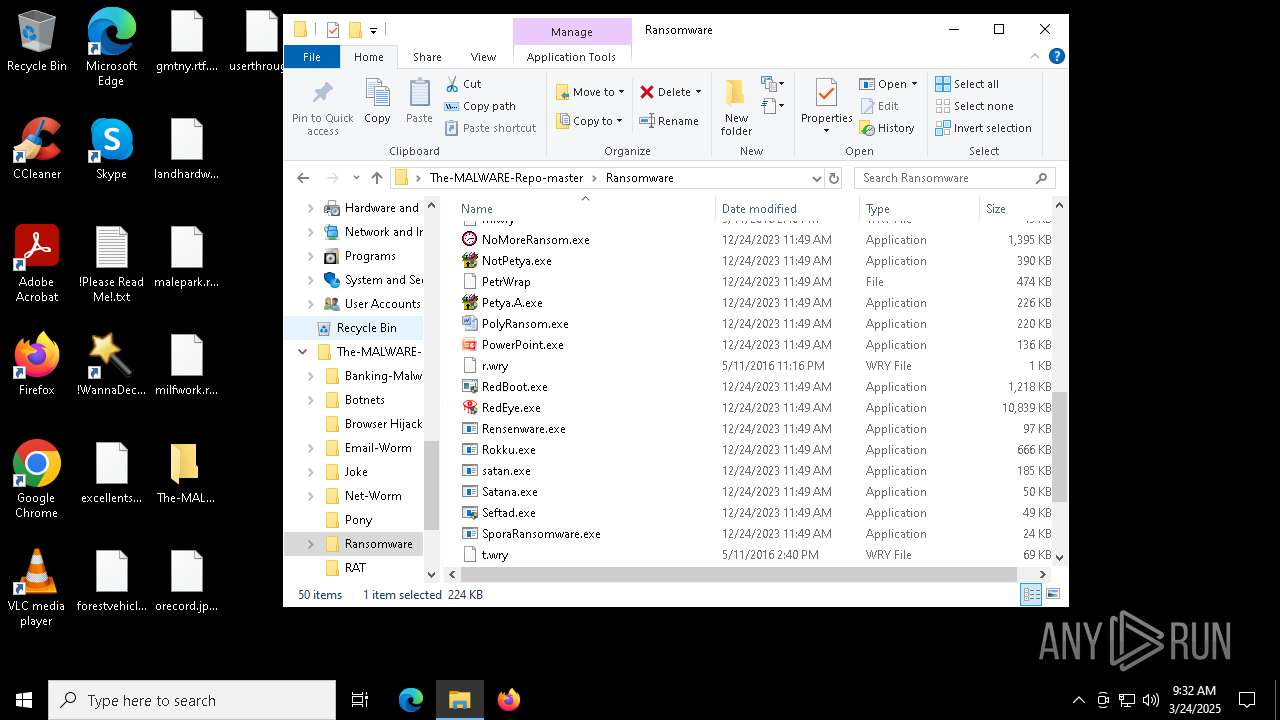
Drops known malicious document
- WinRAR.exe (PID: 644)
- WinRAR.exe (PID: 644)
Drops known malicious image
- WinRAR.exe (PID: 644)
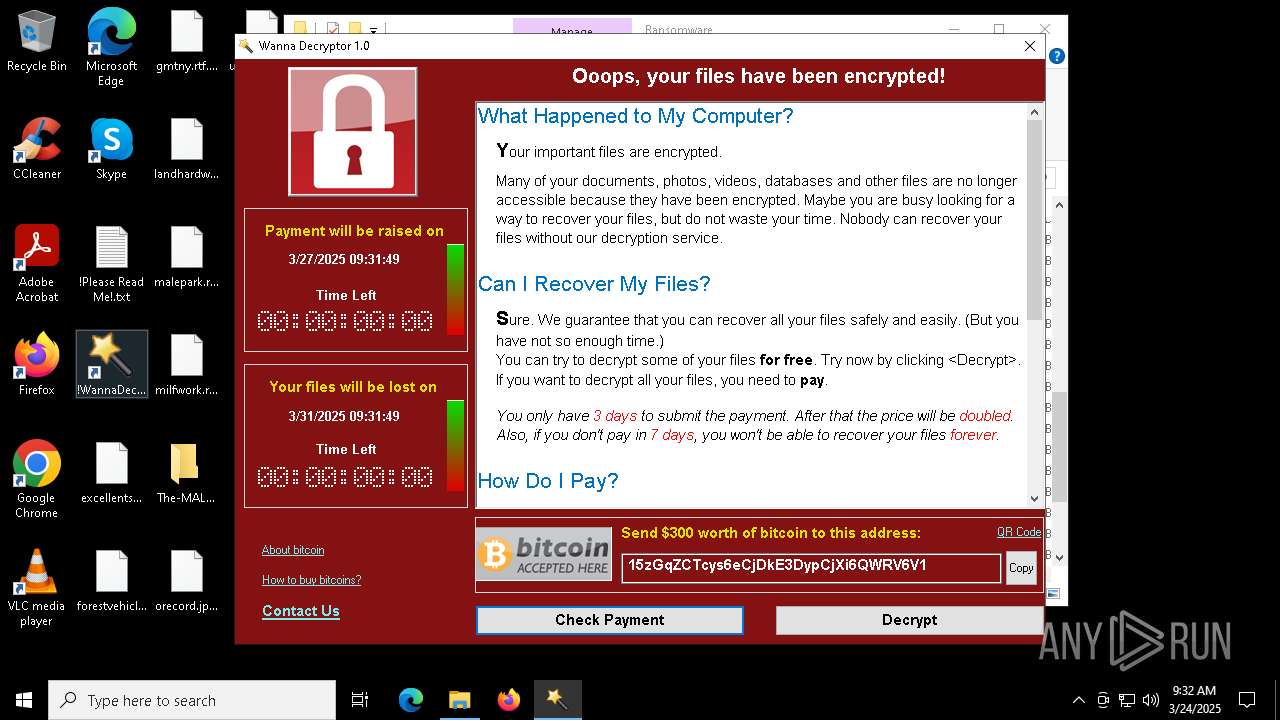
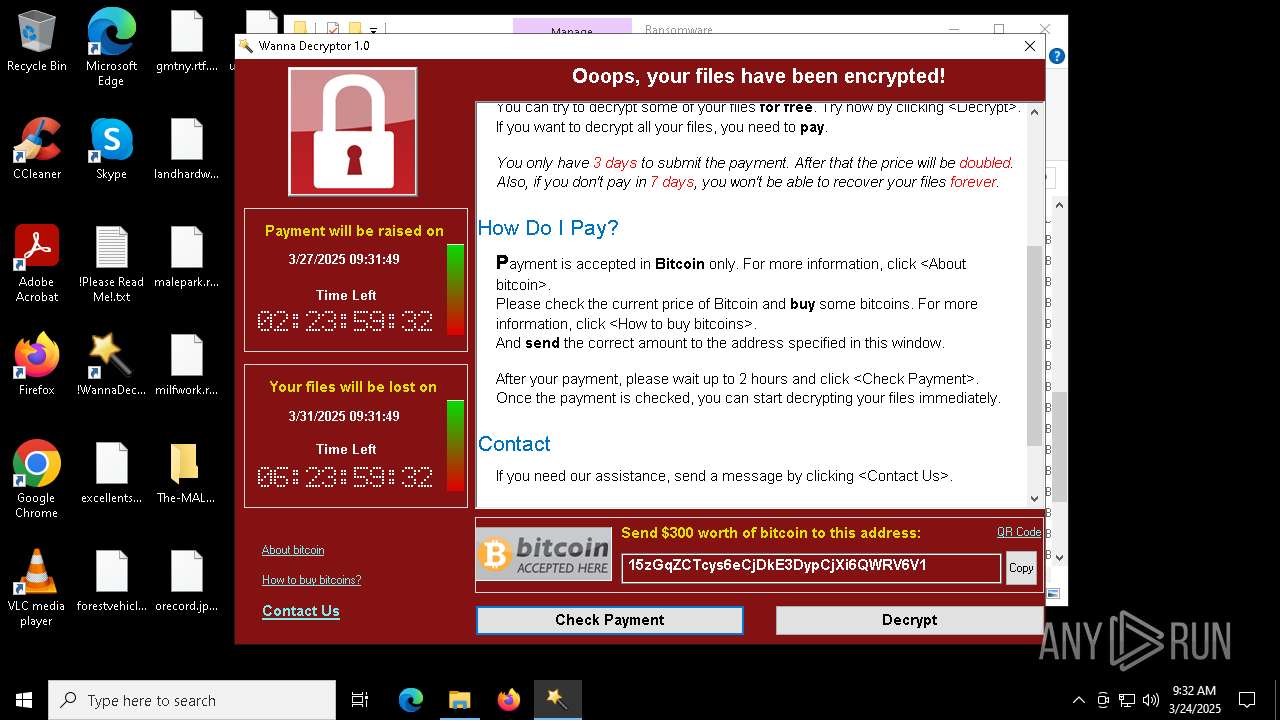
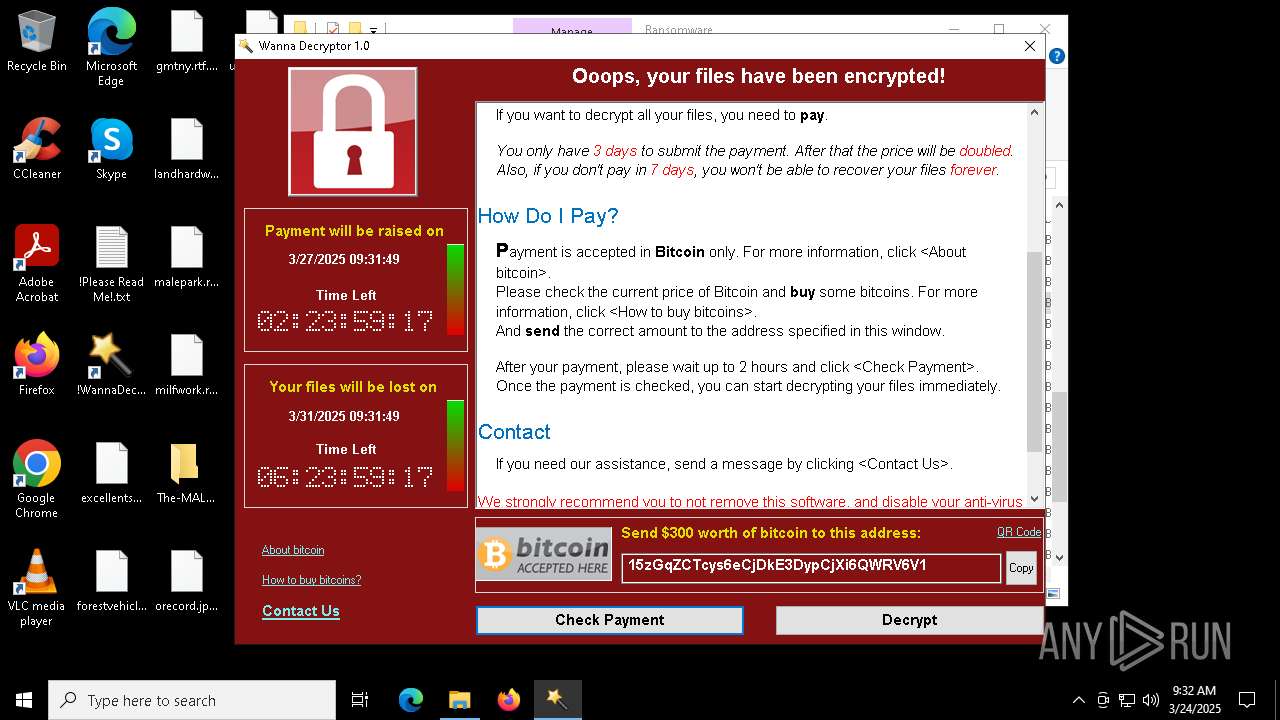
Actions looks like stealing of personal data
- WannaCry.exe (PID: 856)
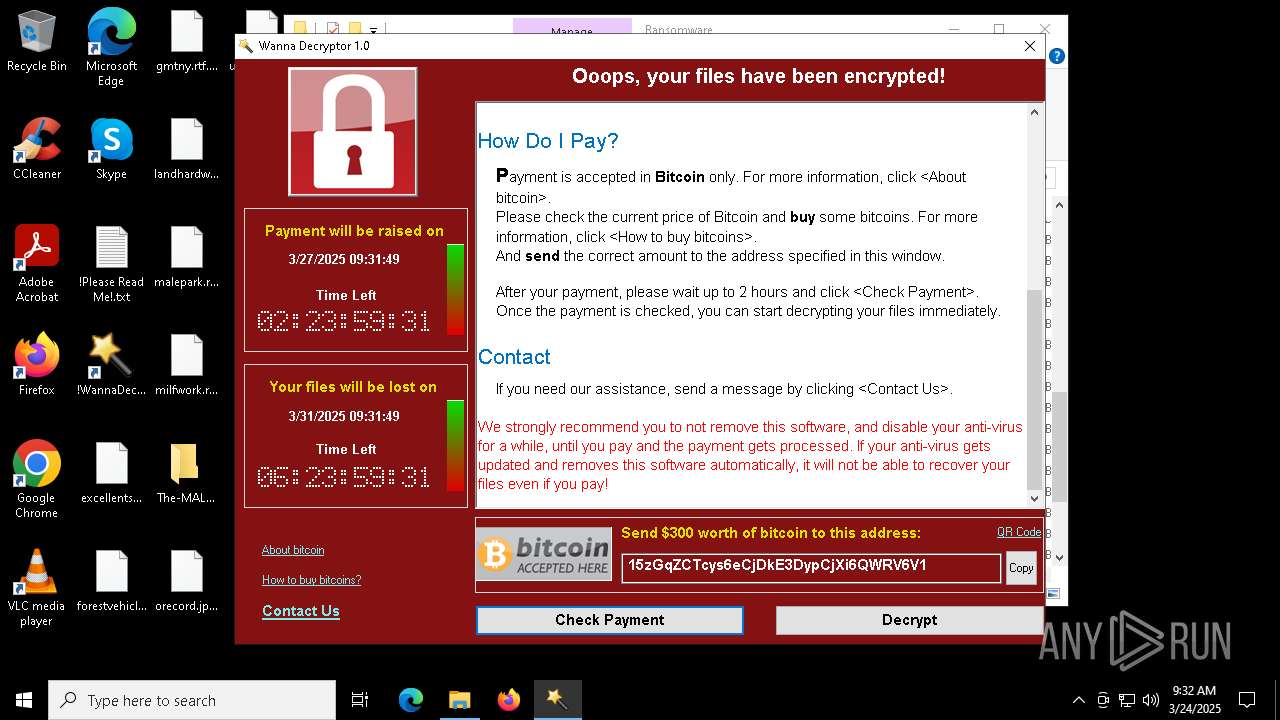
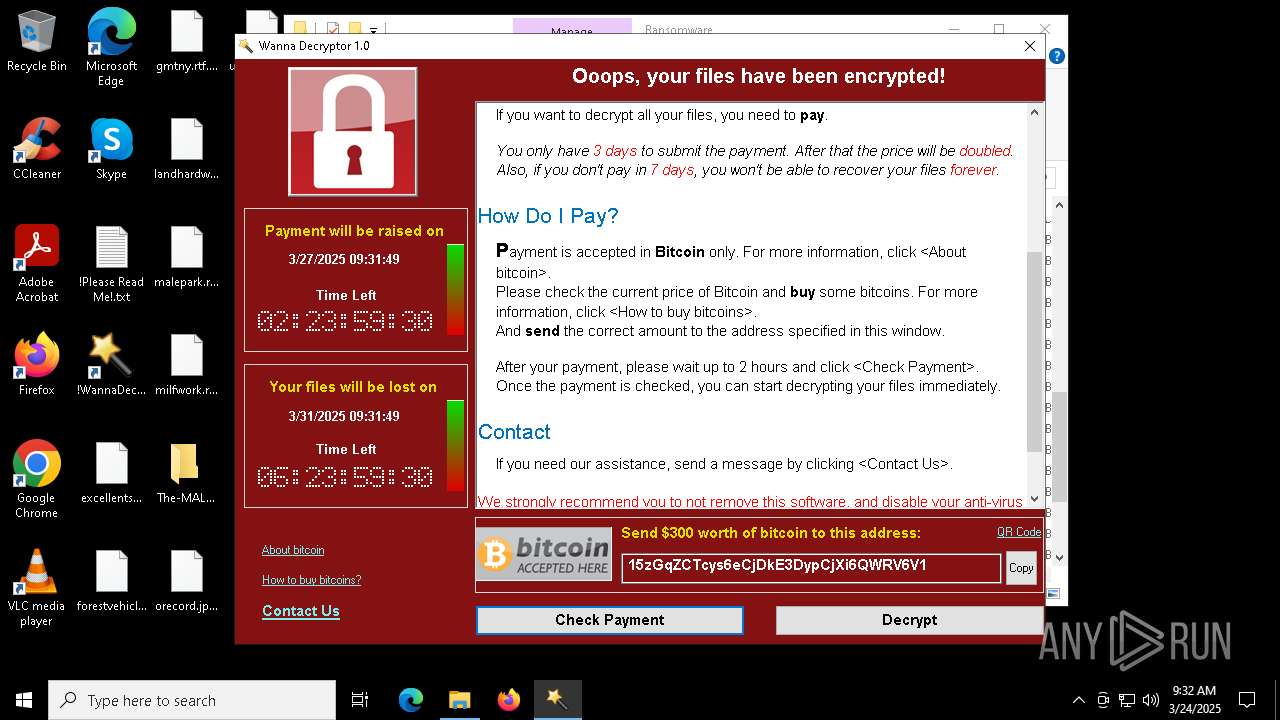
WANNACRY mutex has been found
- WannaCry.exe (PID: 856)
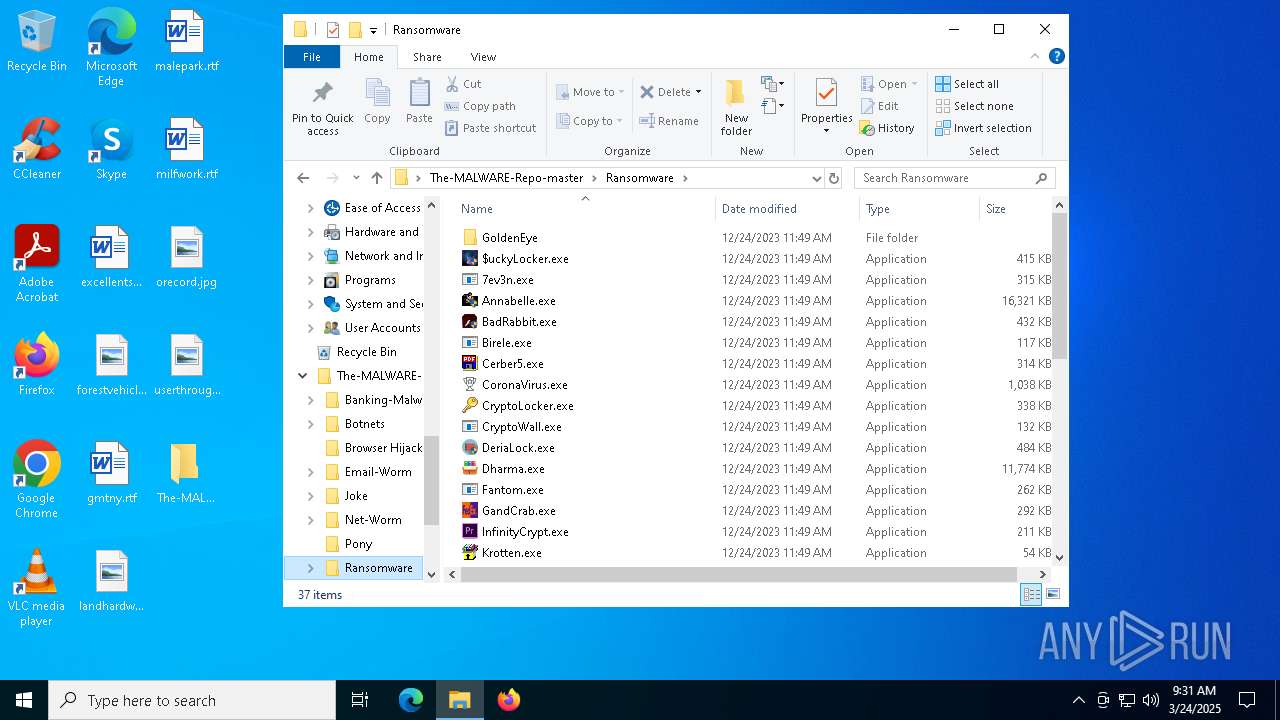
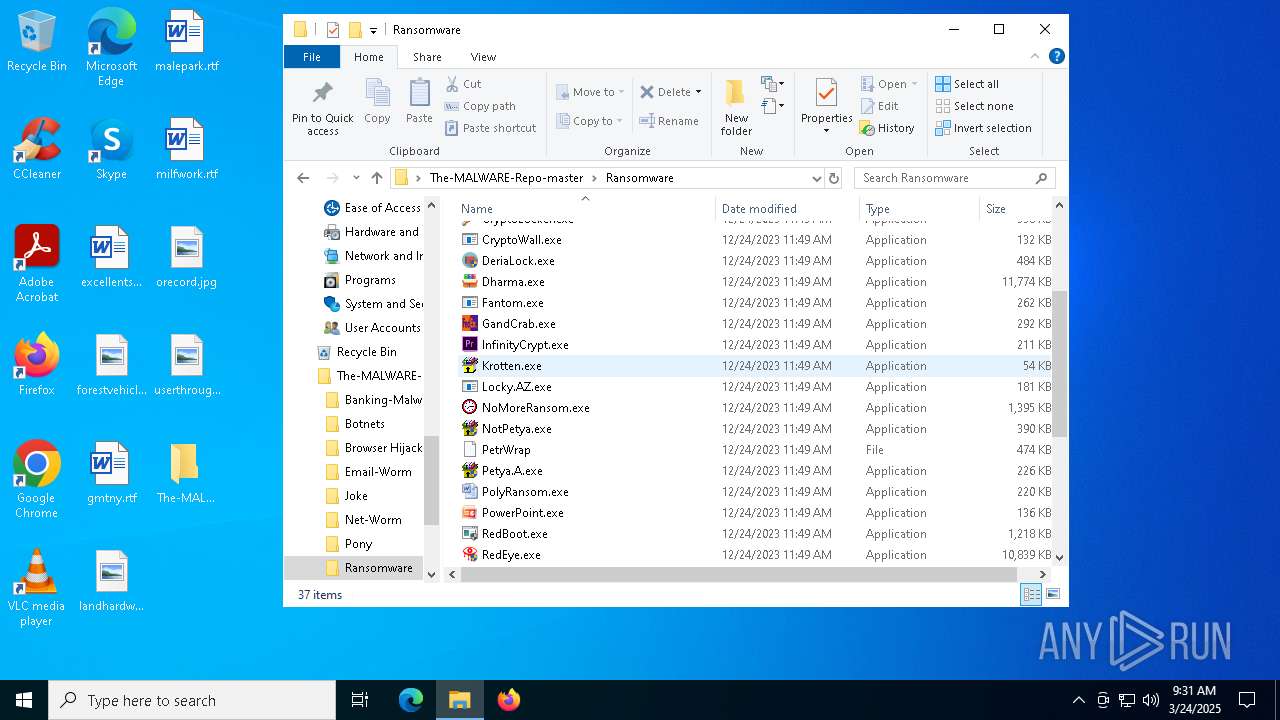
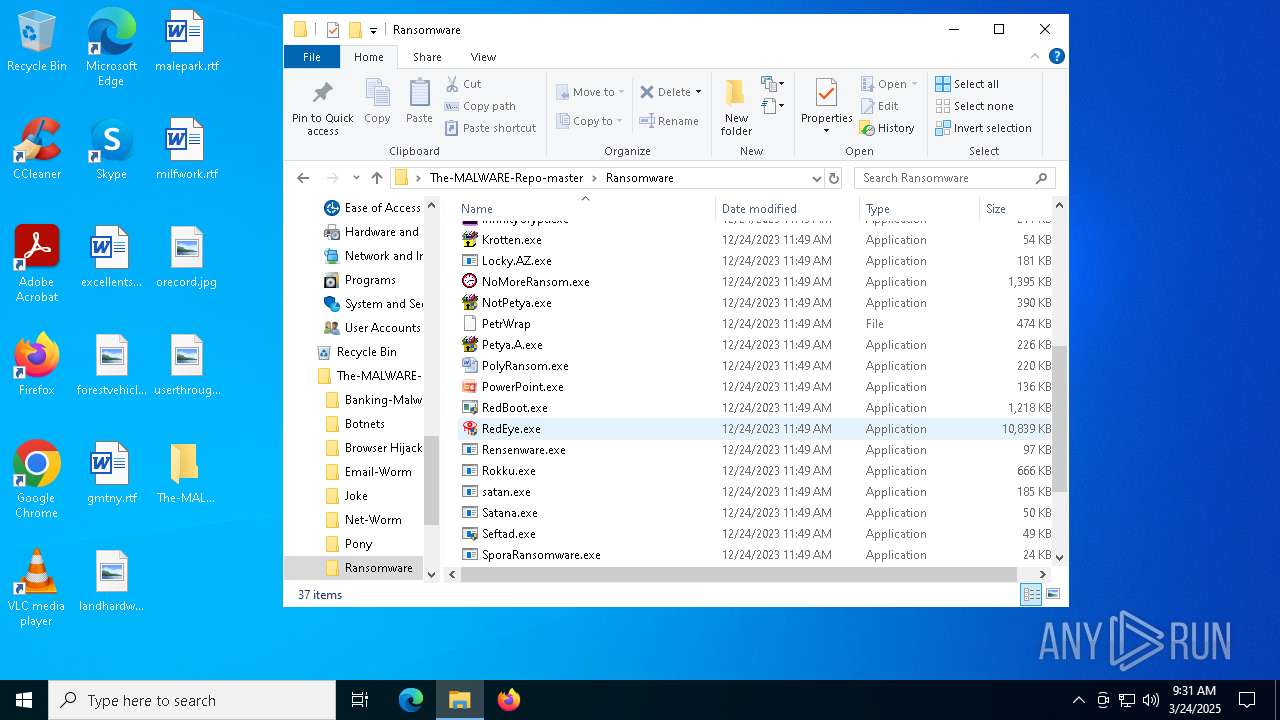
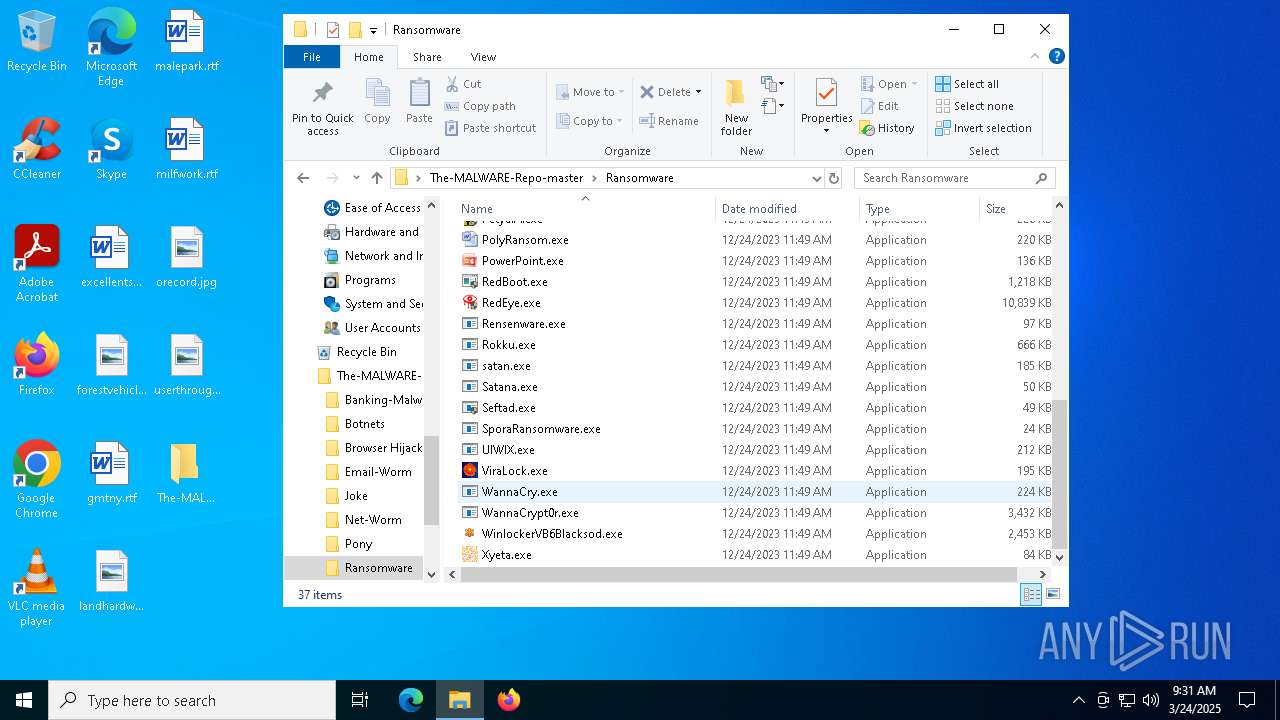
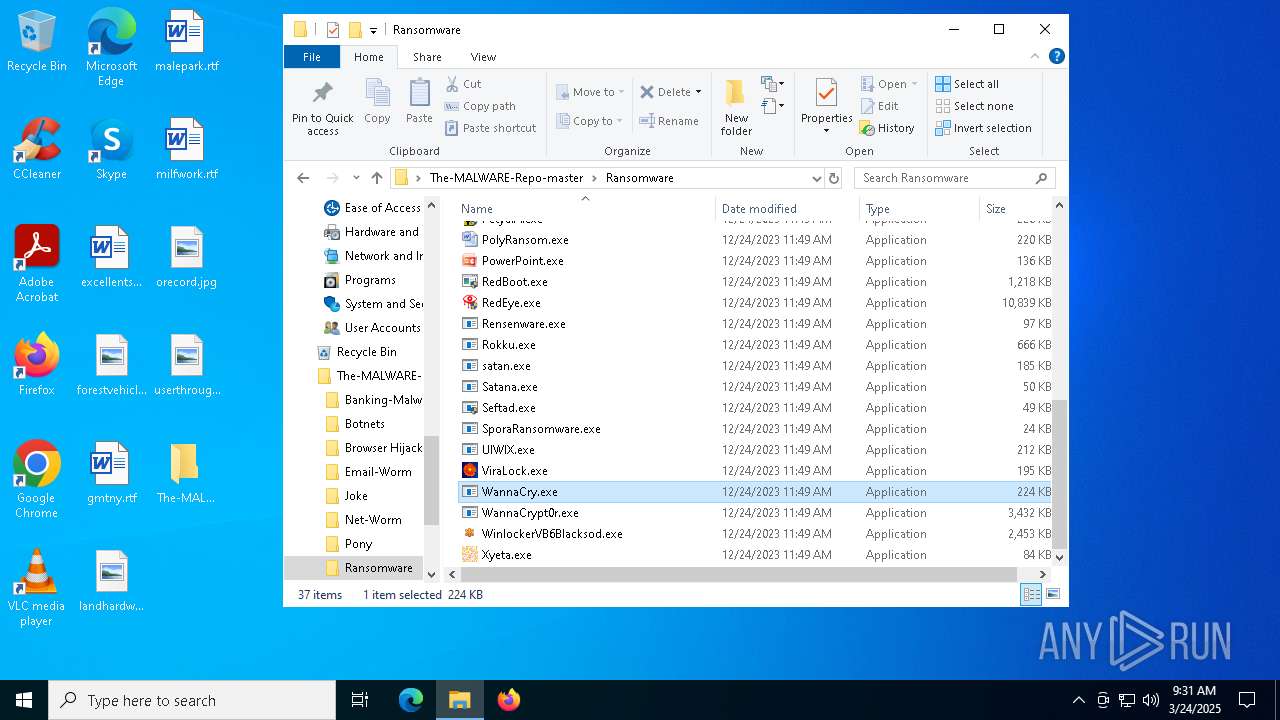
WannaCry Ransomware is detected
- WannaCry.exe (PID: 856)
RANSOMWARE has been detected
- WannaCry.exe (PID: 856)
Modifies files in the Chrome extension folder
- WannaCry.exe (PID: 856)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 644)
- WannaCry.exe (PID: 856)
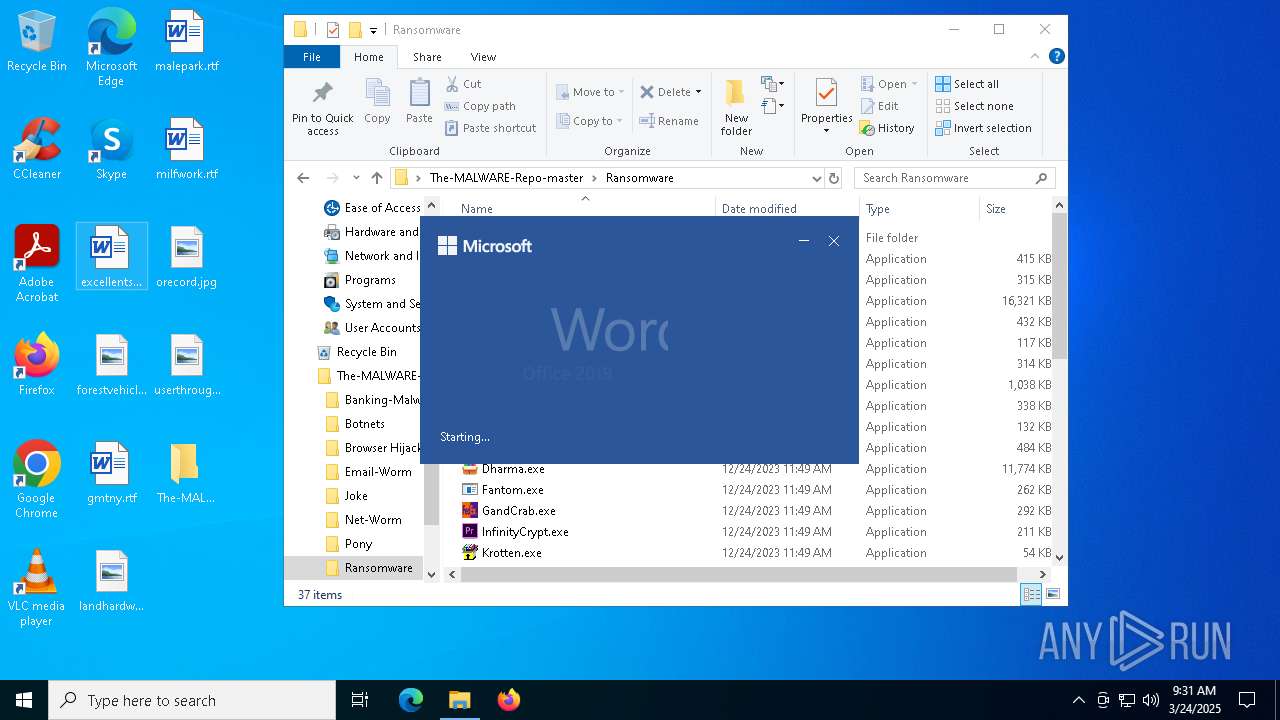
Starts a Microsoft application from unusual location
- WannaCry.exe (PID: 856)
- !WannaDecryptor!.exe (PID: 6540)
- !WannaDecryptor!.exe (PID: 8020)
Suspicious files were dropped or overwritten
- WinRAR.exe (PID: 644)
Uses TASKKILL.EXE to kill process
- WannaCry.exe (PID: 856)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 7404)
Executable content was dropped or overwritten
- WannaCry.exe (PID: 856)
Starts CMD.EXE for commands execution
- WannaCry.exe (PID: 856)
Executing commands from a ".bat" file
- WannaCry.exe (PID: 856)
The process executes VB scripts
- cmd.exe (PID: 736)
INFO
Reads Environment values
- identity_helper.exe (PID: 8164)
- identity_helper.exe (PID: 6620)
Checks supported languages
- identity_helper.exe (PID: 8164)
- WannaCry.exe (PID: 856)
- !WannaDecryptor!.exe (PID: 6540)
- ShellExperienceHost.exe (PID: 7404)
Reads the computer name
- identity_helper.exe (PID: 8164)
- identity_helper.exe (PID: 6620)
- !WannaDecryptor!.exe (PID: 8020)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 1388)
- BackgroundTransferHost.exe (PID: 8984)
- BackgroundTransferHost.exe (PID: 8436)
- BackgroundTransferHost.exe (PID: 2240)
- BackgroundTransferHost.exe (PID: 8756)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 2240)
- WannaCry.exe (PID: 856)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 2240)
- slui.exe (PID: 1052)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 2240)
- slui.exe (PID: 8204)
The sample compiled with spanish language support
- WinRAR.exe (PID: 644)
The sample compiled with german language support
- WinRAR.exe (PID: 644)
The sample compiled with korean language support
- WinRAR.exe (PID: 644)
Autorun file from Downloads
- msedge.exe (PID: 8040)
The sample compiled with english language support
- WinRAR.exe (PID: 644)
- WannaCry.exe (PID: 856)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 644)
The sample compiled with russian language support
- WinRAR.exe (PID: 644)
Application launched itself
- msedge.exe (PID: 3020)
- msedge.exe (PID: 896)
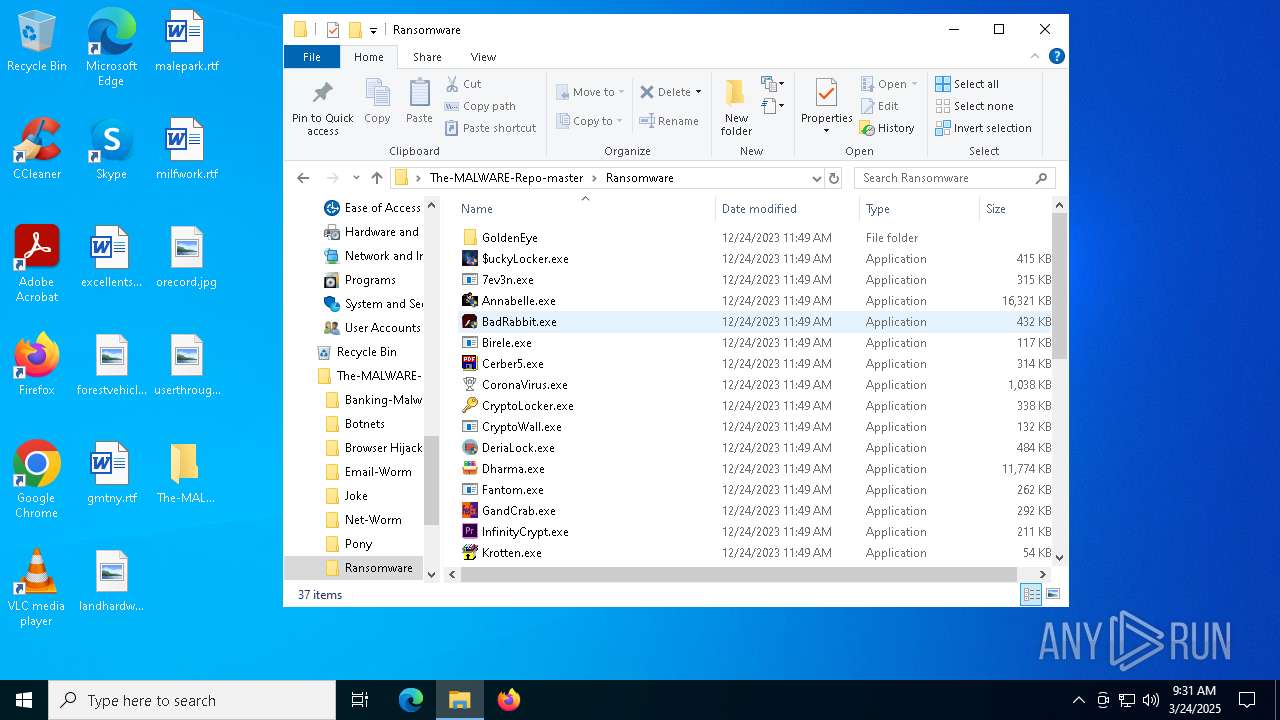
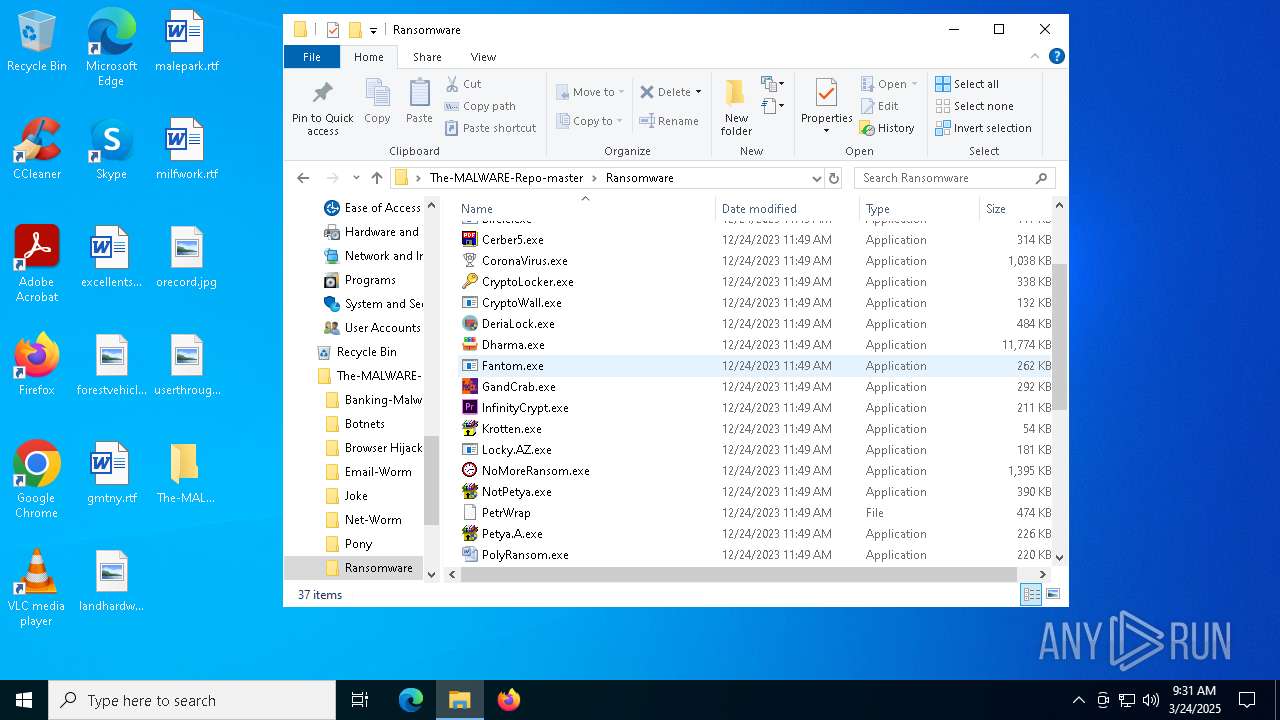
Drops a (possible) Coronavirus decoy
- WinRAR.exe (PID: 644)
The sample compiled with french language support
- WinRAR.exe (PID: 644)
The sample compiled with chinese language support
- WinRAR.exe (PID: 644)
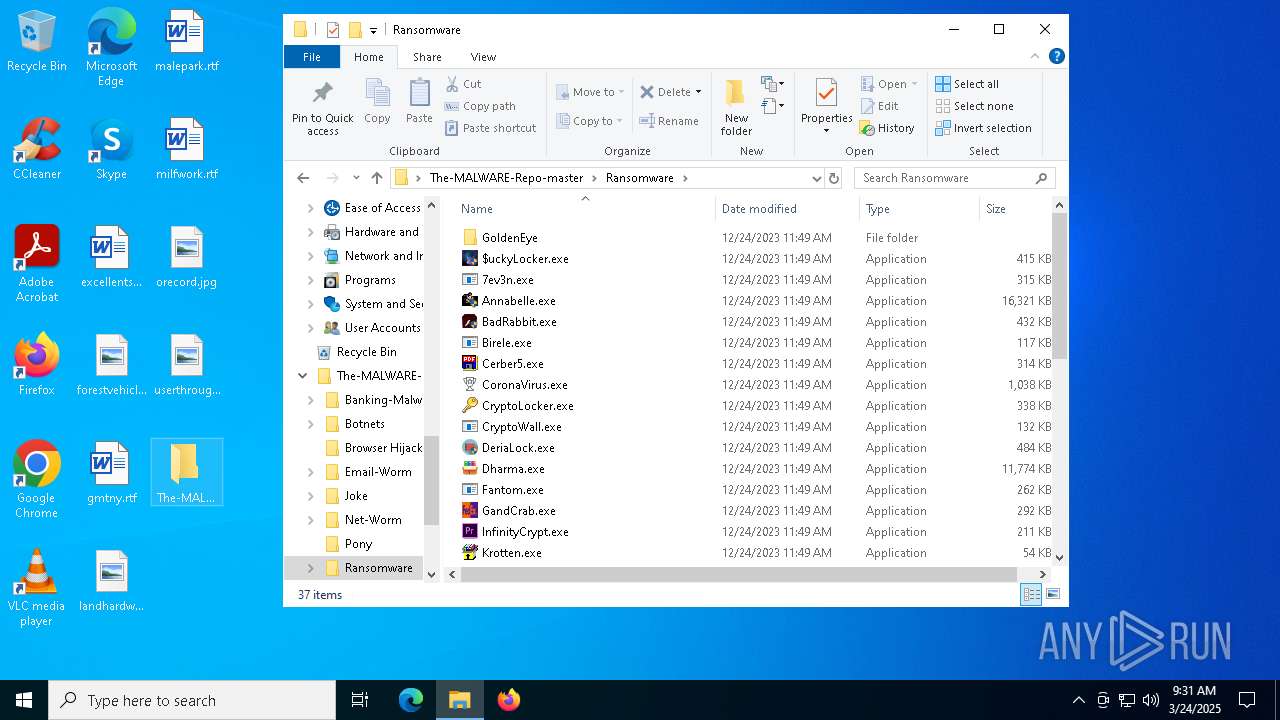
Manual execution by a user
- WINWORD.EXE (PID: 8884)
- WannaCry.exe (PID: 856)
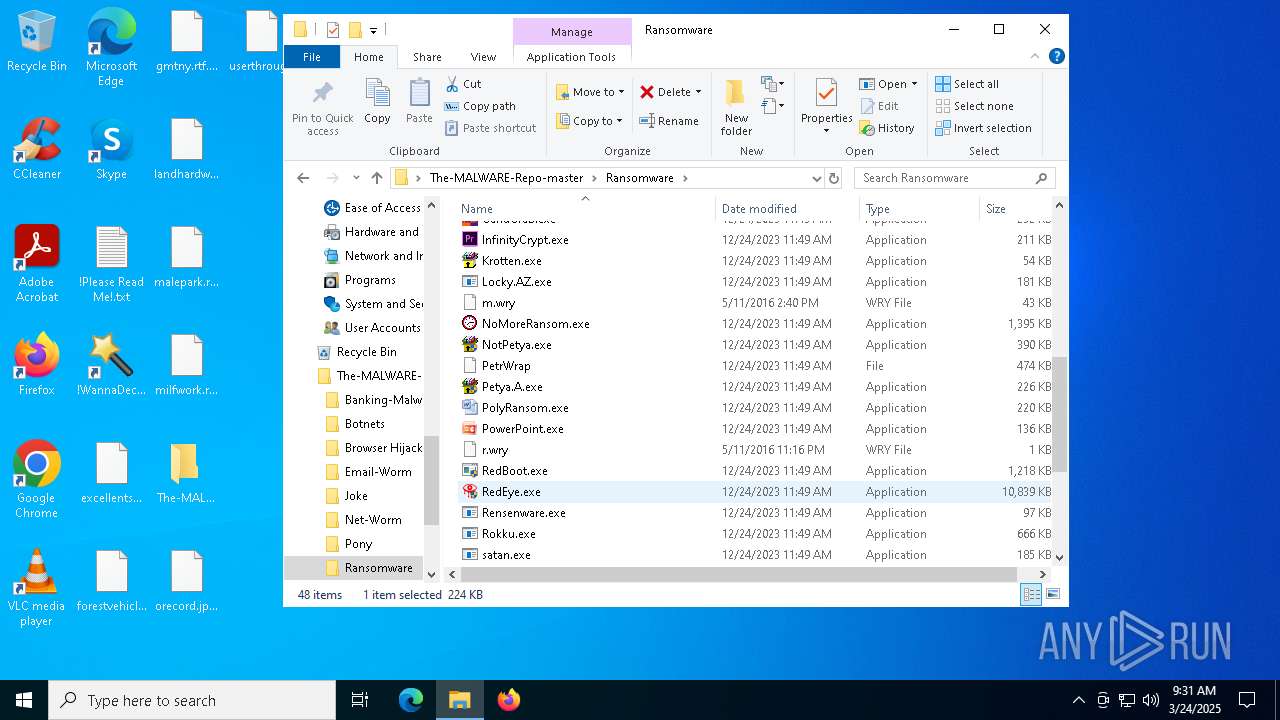
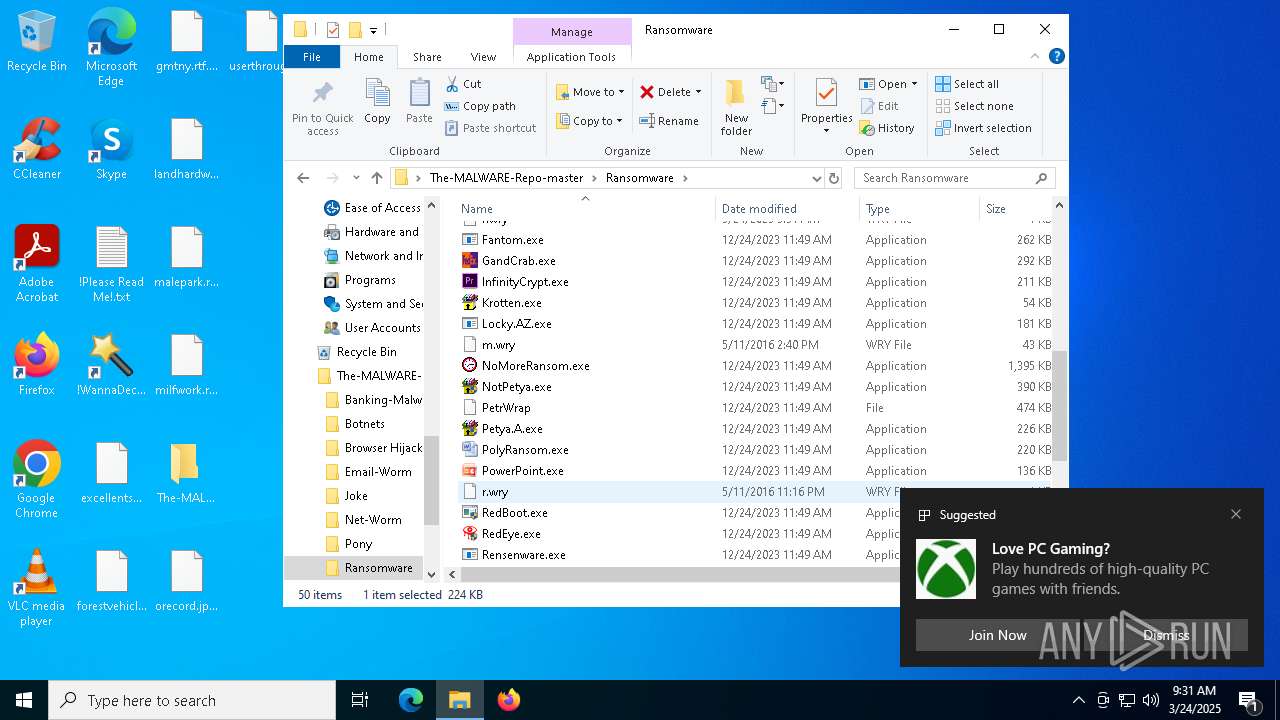
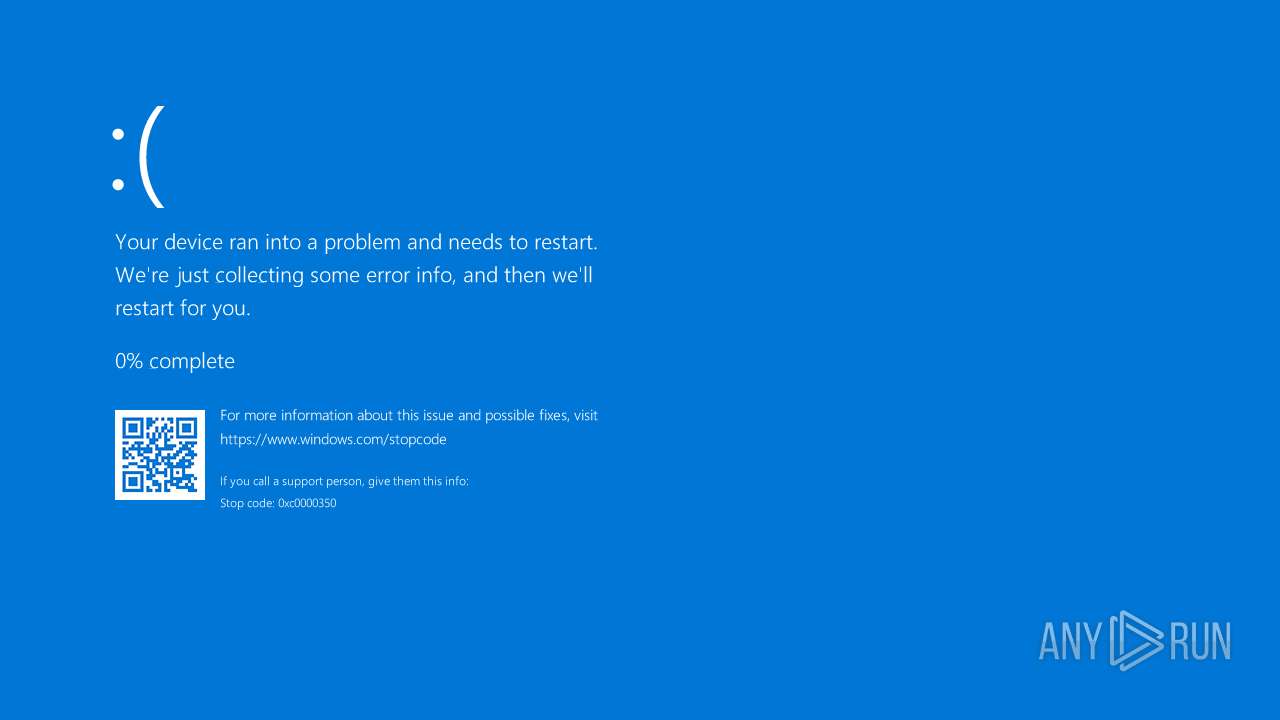
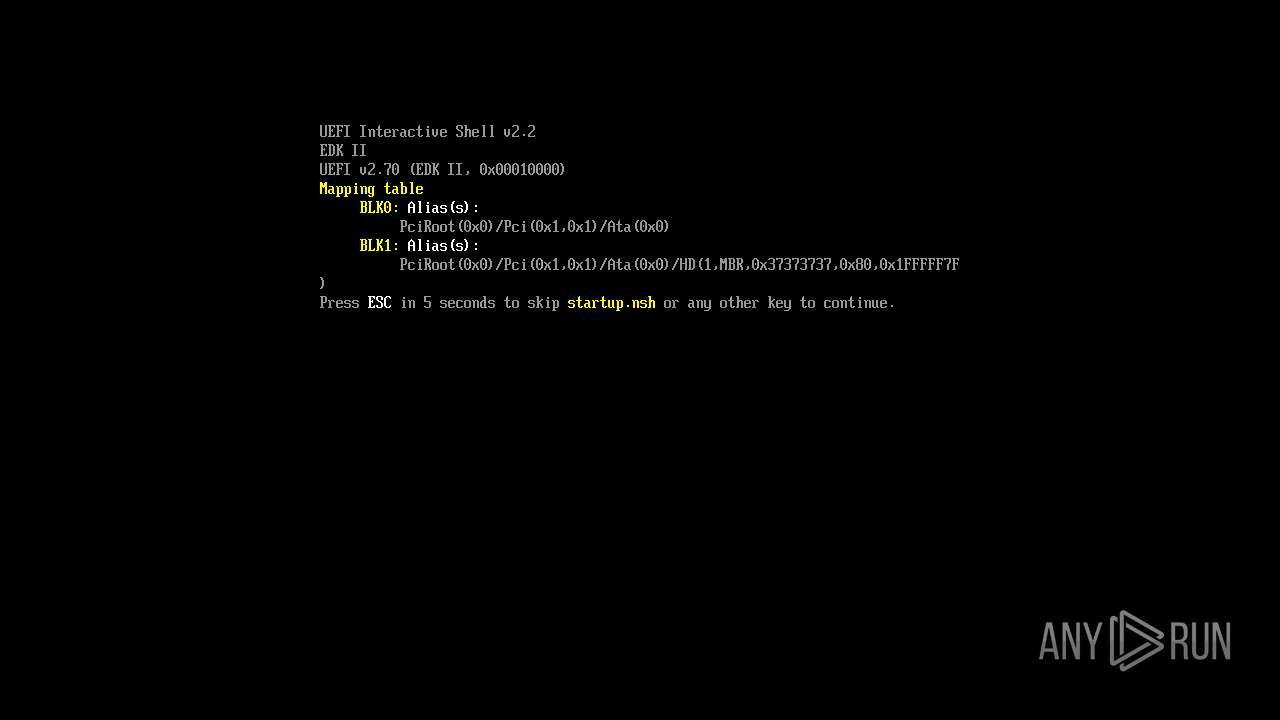
- Petya.A.exe (PID: 4380)
- !WannaDecryptor!.exe (PID: 8020)
- Petya.A.exe (PID: 924)
Reads the machine GUID from the registry
- WannaCry.exe (PID: 856)
Creates files in the program directory
- WannaCry.exe (PID: 856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
242
Monitored processes
94
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
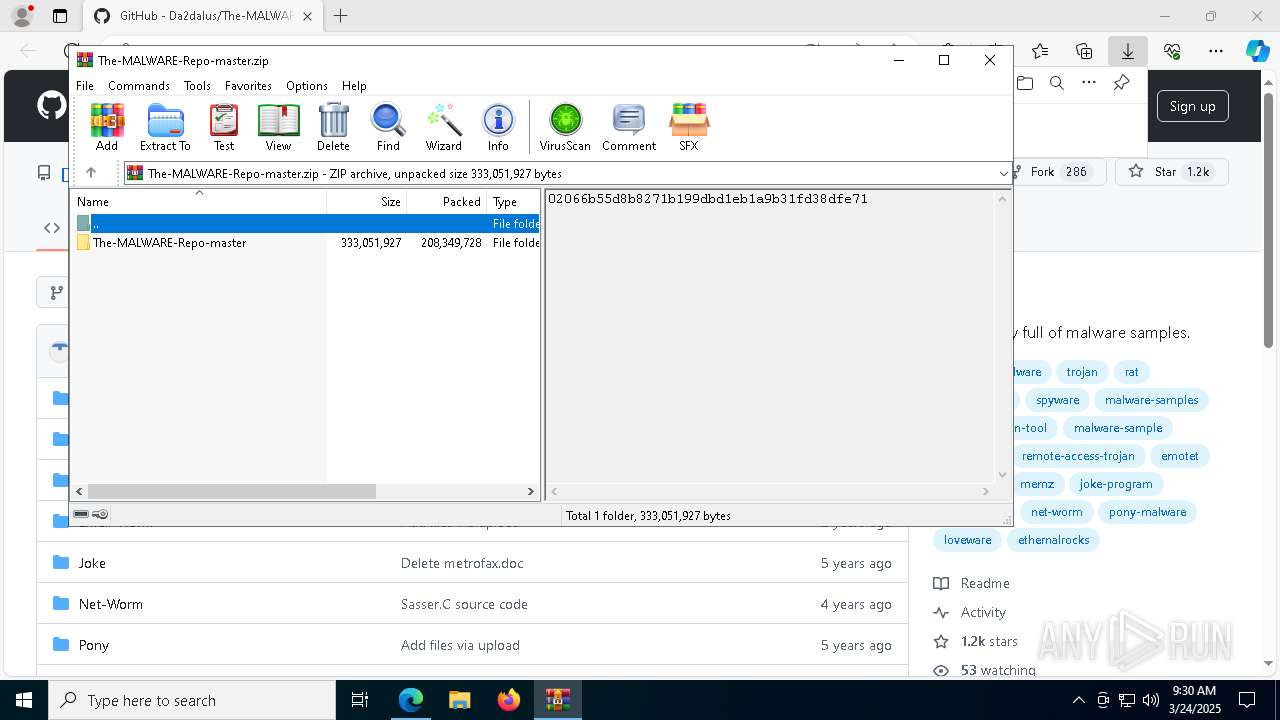
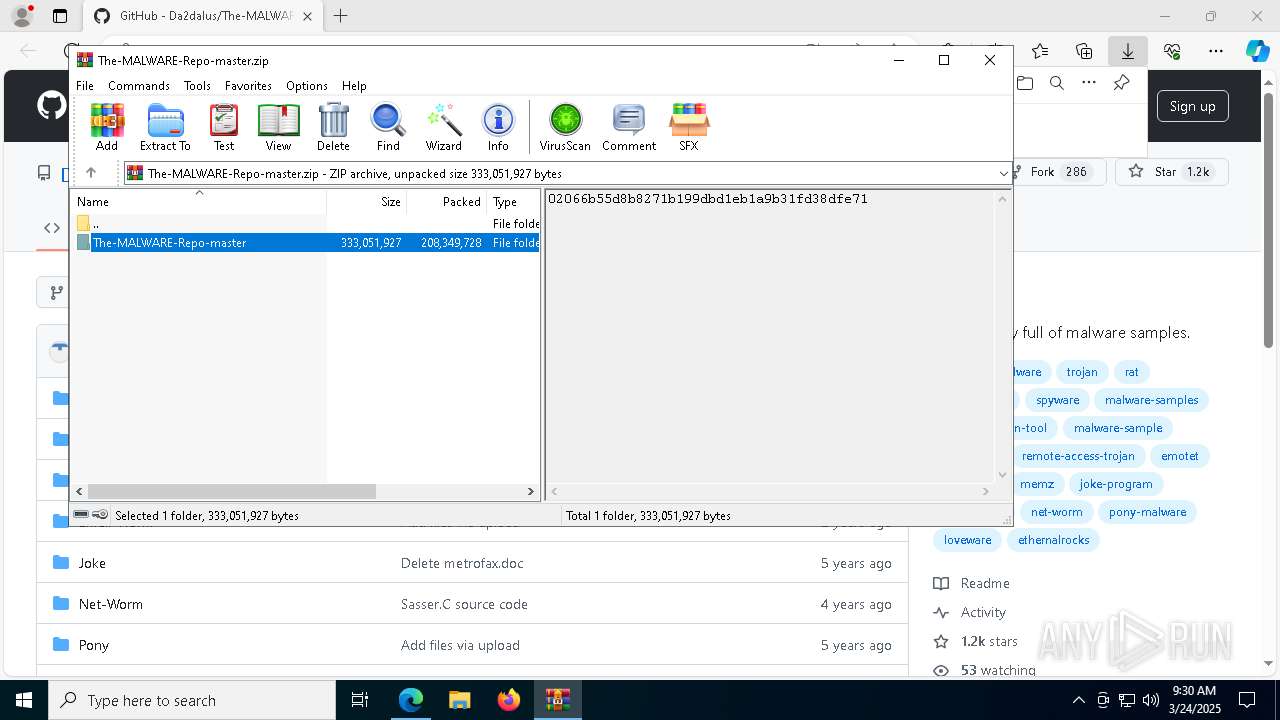
| 644 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\The-MALWARE-Repo-master.zip" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6908 --field-trial-handle=2652,i,2918662778093793649,18208600248692220213,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=6600 --field-trial-handle=2652,i,2918662778093793649,18208600248692220213,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2672 --field-trial-handle=2344,i,6589957021536499874,5305728709082263689,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | C:\WINDOWS\system32\cmd.exe /c 60921742808707.bat | C:\Windows\SysWOW64\cmd.exe | — | WannaCry.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
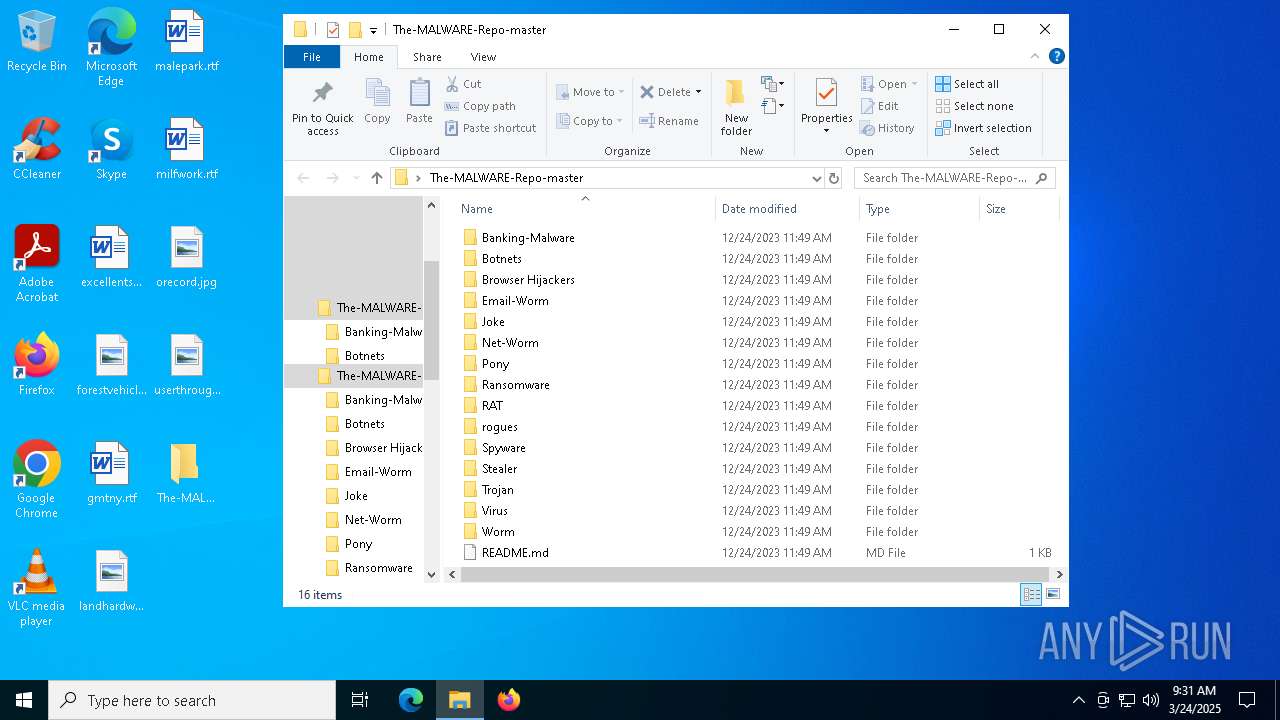
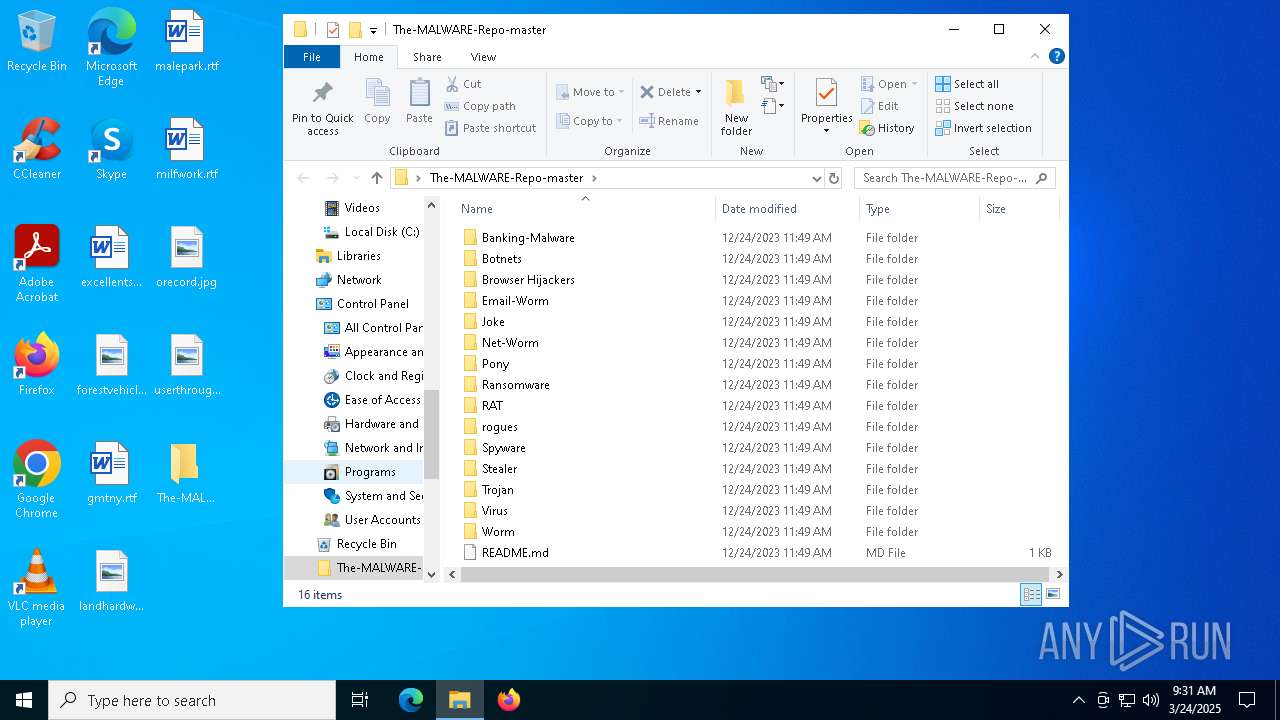
| 856 | "C:\Users\admin\Desktop\The-MALWARE-Repo-master\Ransomware\WannaCry.exe" | C:\Users\admin\Desktop\The-MALWARE-Repo-master\Ransomware\WannaCry.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: dvdplay placeholder Application Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4204 --field-trial-handle=2344,i,6589957021536499874,5305728709082263689,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/Da2dalus/The-MALWARE-Repo" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Users\admin\Desktop\The-MALWARE-Repo-master\Ransomware\Petya.A.exe" | C:\Users\admin\Desktop\The-MALWARE-Repo-master\Ransomware\Petya.A.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1052 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 474
Read events
24 113
Write events
324
Delete events
37
Modification events
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CE96B386A98F2F00 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DACCBF86A98F2F00 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262926 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {07C2B909-2358-4442-AC76-87FBDF6887F4} | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262926 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E86194BC-4B9D-4DD2-AE22-58D949D17582} | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262926 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3A9DD797-0D07-468A-B326-07AB204E1428} | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262926 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9B3A2704-E37B-4063-81EE-0E1D0F9CA5F8} | |||
Executable files
192
Suspicious files
1 297
Text files
243
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10baa7.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bab7.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bab7.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bb05.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bb24.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
102
DNS requests
107
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
9040 | svchost.exe | HEAD | 200 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742974014&P2=404&P3=2&P4=eqDYhK4daCfTkpEqMCdayfI%2bpmlHyaTGv1ZYcyxLGhlddwZyr8FalsRXERYGZIsUw25CNgyfaetK1vG5AUEANA%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4892 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1324 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2240 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
9040 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742974014&P2=404&P3=2&P4=eqDYhK4daCfTkpEqMCdayfI%2bpmlHyaTGv1ZYcyxLGhlddwZyr8FalsRXERYGZIsUw25CNgyfaetK1vG5AUEANA%3d%3d | unknown | — | — | whitelisted |
9040 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742974014&P2=404&P3=2&P4=eqDYhK4daCfTkpEqMCdayfI%2bpmlHyaTGv1ZYcyxLGhlddwZyr8FalsRXERYGZIsUw25CNgyfaetK1vG5AUEANA%3d%3d | unknown | — | — | whitelisted |
9040 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742974014&P2=404&P3=2&P4=eqDYhK4daCfTkpEqMCdayfI%2bpmlHyaTGv1ZYcyxLGhlddwZyr8FalsRXERYGZIsUw25CNgyfaetK1vG5AUEANA%3d%3d | unknown | — | — | whitelisted |
9040 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742974014&P2=404&P3=2&P4=eqDYhK4daCfTkpEqMCdayfI%2bpmlHyaTGv1ZYcyxLGhlddwZyr8FalsRXERYGZIsUw25CNgyfaetK1vG5AUEANA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
896 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7416 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7416 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7416 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7416 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7416 | msedge.exe | 13.107.253.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
github.githubassets.com |
| whitelisted |