| File name: | 476f79302805d2a27bc717f6d95dcd3c.exe |
| Full analysis: | https://app.any.run/tasks/56165f44-6fc6-4e6a-a35c-9be81c848d29 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
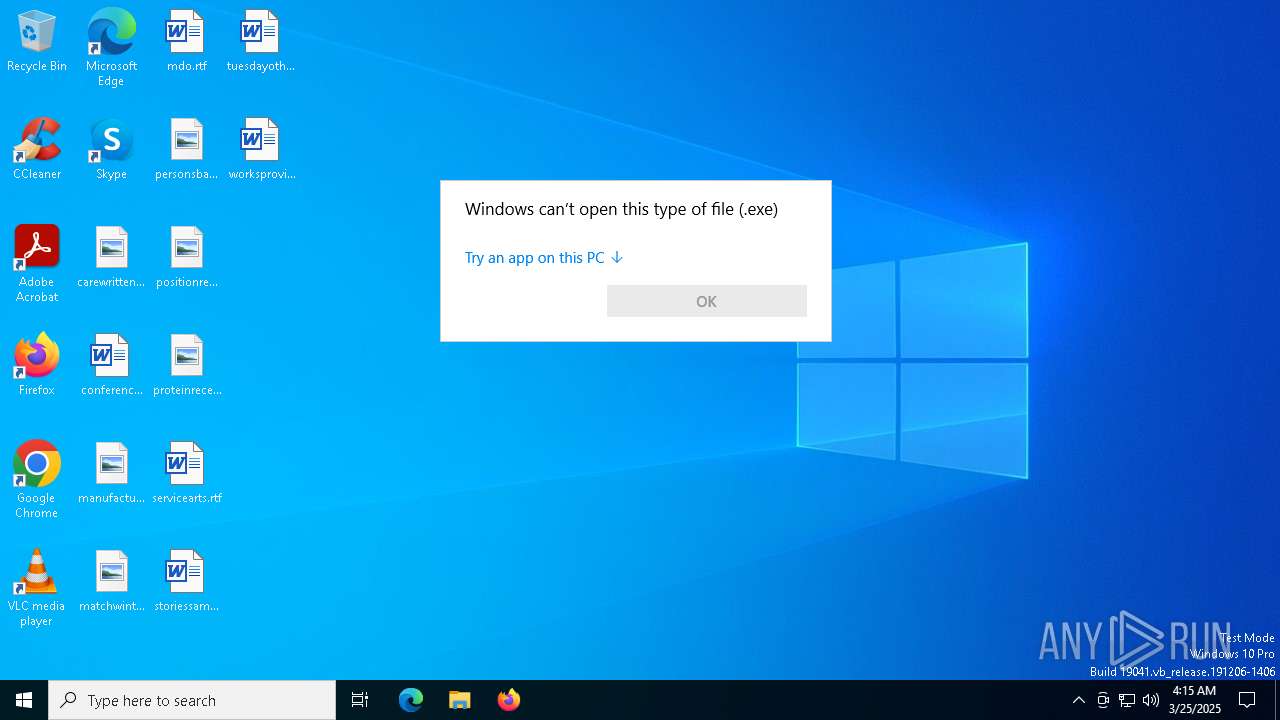
| Analysis date: | March 25, 2025, 04:15:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 3 sections |
| MD5: | 476F79302805D2A27BC717F6D95DCD3C |
| SHA1: | 3172AE3F101A86B29FB610B290E85C99E3EC5502 |
| SHA256: | 6A5023A19B2A5D0A27253C6A8DEBB2A490A3975F4C4F5C8D254ED691F4301184 |
| SSDEEP: | 24576:i97XCs/kn4ApU1uOPk9XTr2Myn3N1DxrmXIMaVTr/mHuAQ:i97XCs/kn4ApU1u2k9XTr2Myn3N1Dxrx |
MALICIOUS
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 7416)
Modifies registry startup key (SCRIPT)
- wscript.exe (PID: 7416)
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 7416)
Detects the decoding of a binary file from Base64 (SCRIPT)
- wscript.exe (PID: 7416)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 7244)
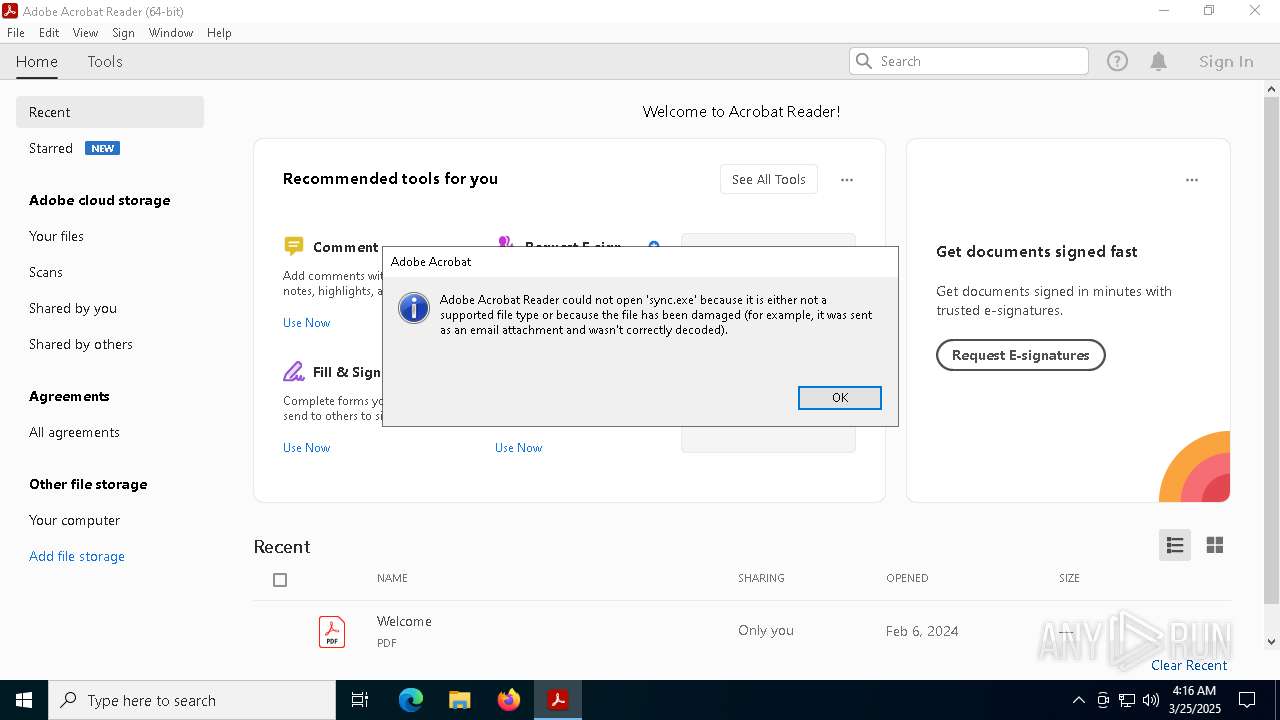
Actions looks like stealing of personal data
- sync.exe (PID: 3140)
Steals credentials from Web Browsers
- sync.exe (PID: 3140)
ASYNCRAT has been detected (SURICATA)
- sync.exe (PID: 3140)
SUSPICIOUS
Reads security settings of Internet Explorer
- 476f79302805d2a27bc717f6d95dcd3c.exe (PID: 7256)
- NiSync.exe (PID: 7512)
- ShellExperienceHost.exe (PID: 920)
Reads the date of Windows installation
- 476f79302805d2a27bc717f6d95dcd3c.exe (PID: 7256)
The process executes VB scripts
- 476f79302805d2a27bc717f6d95dcd3c.exe (PID: 7256)
Runs WScript without displaying logo
- wscript.exe (PID: 7416)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 7416)
Starts a Microsoft application from unusual location
- NiSync.exe (PID: 7512)
- sync.exe (PID: 3140)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7416)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7416)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 7416)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 7416)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 7416)
Executable content was dropped or overwritten
- wscript.exe (PID: 7416)
- NiSync.exe (PID: 7512)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 7416)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 664)
The executable file from the user directory is run by the CMD process
- sync.exe (PID: 3140)
Starts CMD.EXE for commands execution
- NiSync.exe (PID: 7512)
Executing commands from a ".bat" file
- NiSync.exe (PID: 7512)
Connects to unusual port
- sync.exe (PID: 3140)
Contacting a server suspected of hosting an CnC
- sync.exe (PID: 3140)
INFO
Create files in a temporary directory
- 476f79302805d2a27bc717f6d95dcd3c.exe (PID: 7256)
- NiSync.exe (PID: 7512)
The sample compiled with english language support
- 476f79302805d2a27bc717f6d95dcd3c.exe (PID: 7256)
Process checks computer location settings
- 476f79302805d2a27bc717f6d95dcd3c.exe (PID: 7256)
- NiSync.exe (PID: 7512)
Checks supported languages
- 476f79302805d2a27bc717f6d95dcd3c.exe (PID: 7256)
- NiSync.exe (PID: 7512)
- sync.exe (PID: 3140)
- ShellExperienceHost.exe (PID: 920)
Reads the computer name
- 476f79302805d2a27bc717f6d95dcd3c.exe (PID: 7256)
- NiSync.exe (PID: 7512)
- sync.exe (PID: 3140)
- ShellExperienceHost.exe (PID: 920)
Reads the machine GUID from the registry
- NiSync.exe (PID: 7512)
- sync.exe (PID: 3140)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 1132)
- BackgroundTransferHost.exe (PID: 5304)
- BackgroundTransferHost.exe (PID: 7884)
- OpenWith.exe (PID: 4620)
- BackgroundTransferHost.exe (PID: 7744)
- BackgroundTransferHost.exe (PID: 1040)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5304)
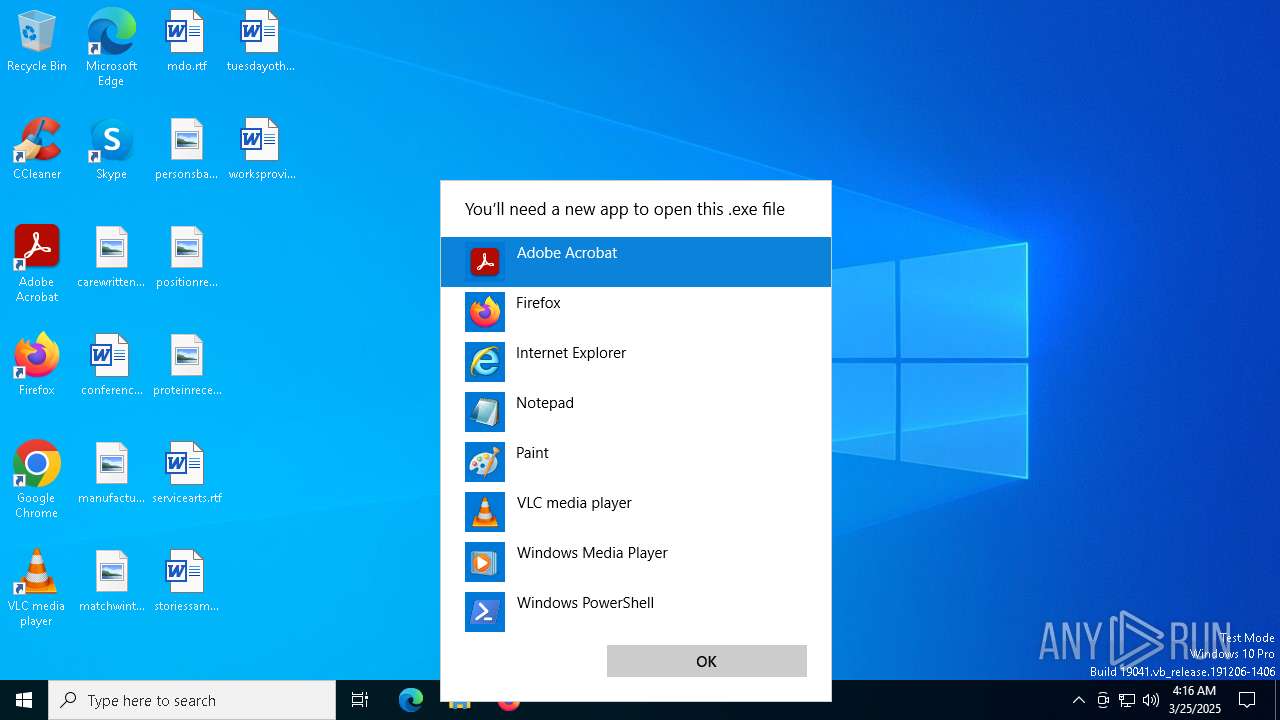
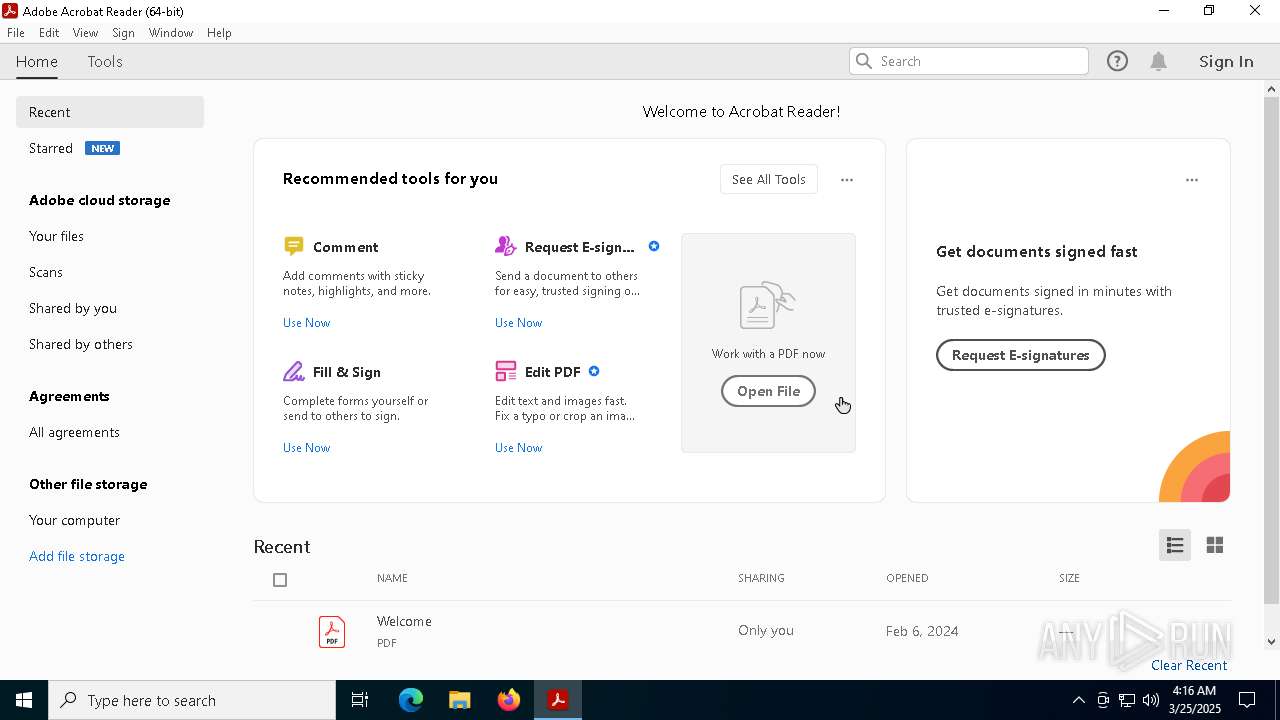
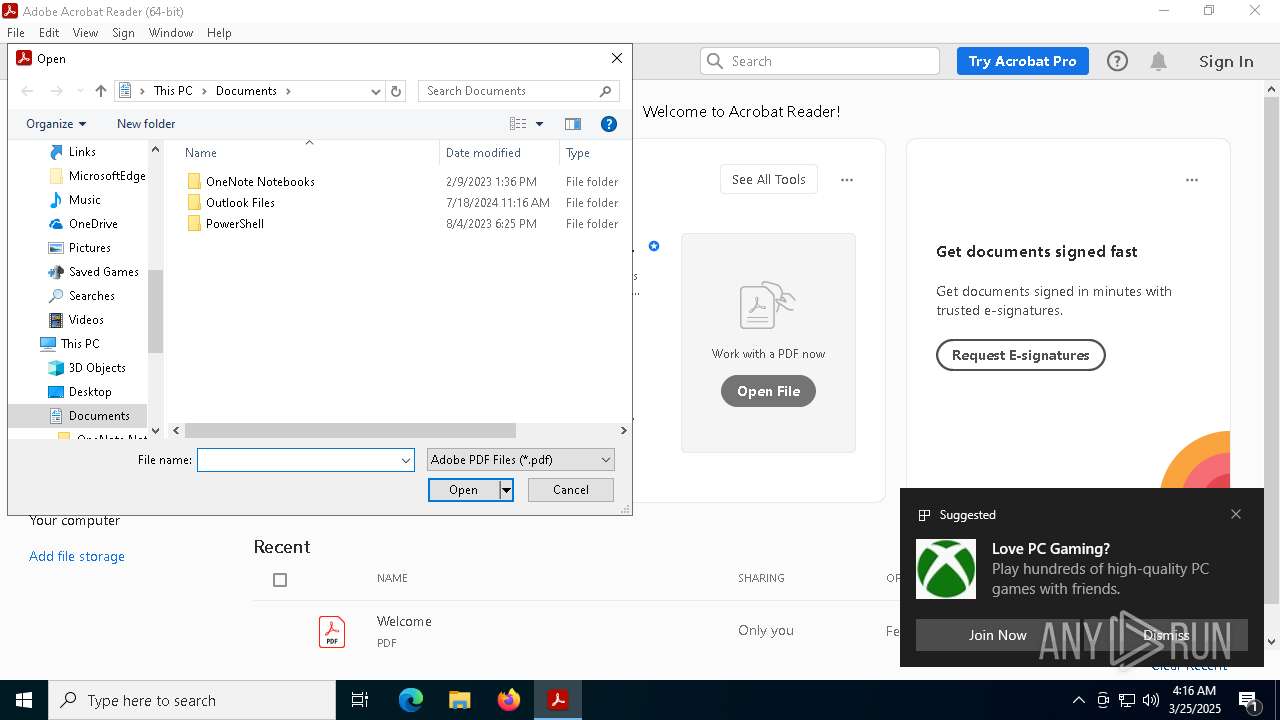
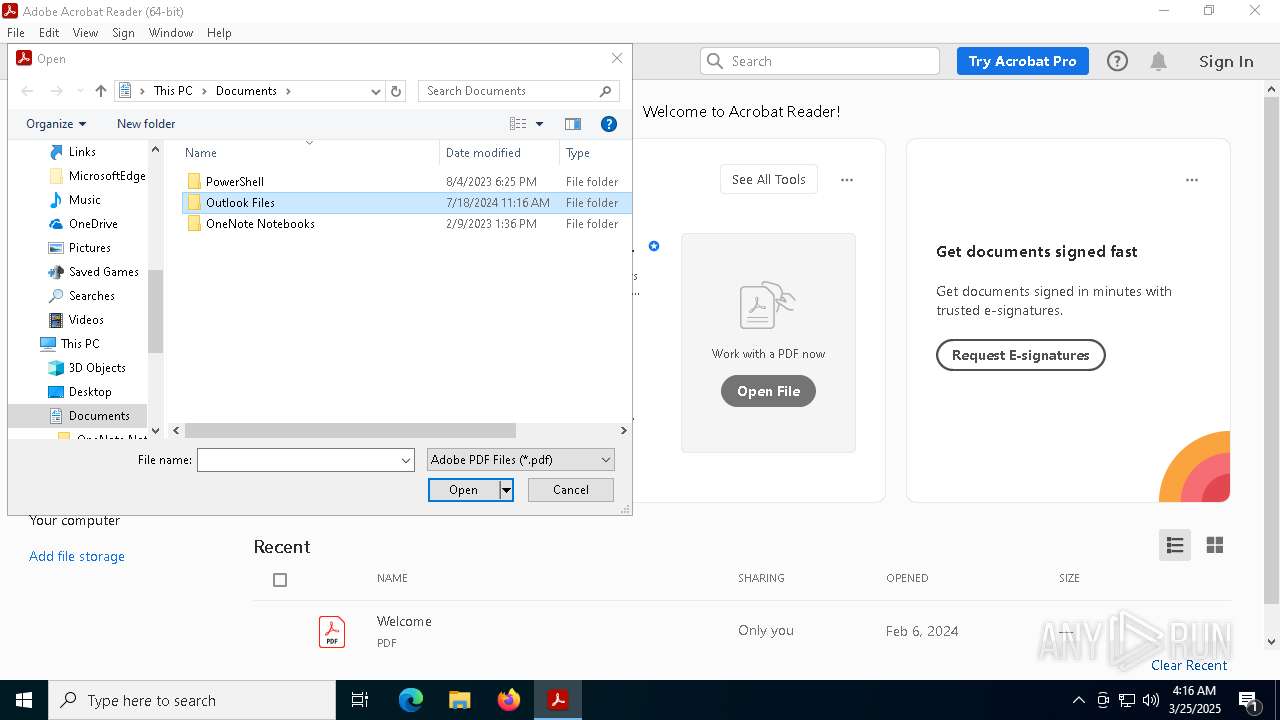
Manual execution by a user
- OpenWith.exe (PID: 4620)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4620)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5304)
- sync.exe (PID: 3140)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5304)
- sync.exe (PID: 3140)
- slui.exe (PID: 7596)
Disables trace logs
- sync.exe (PID: 3140)
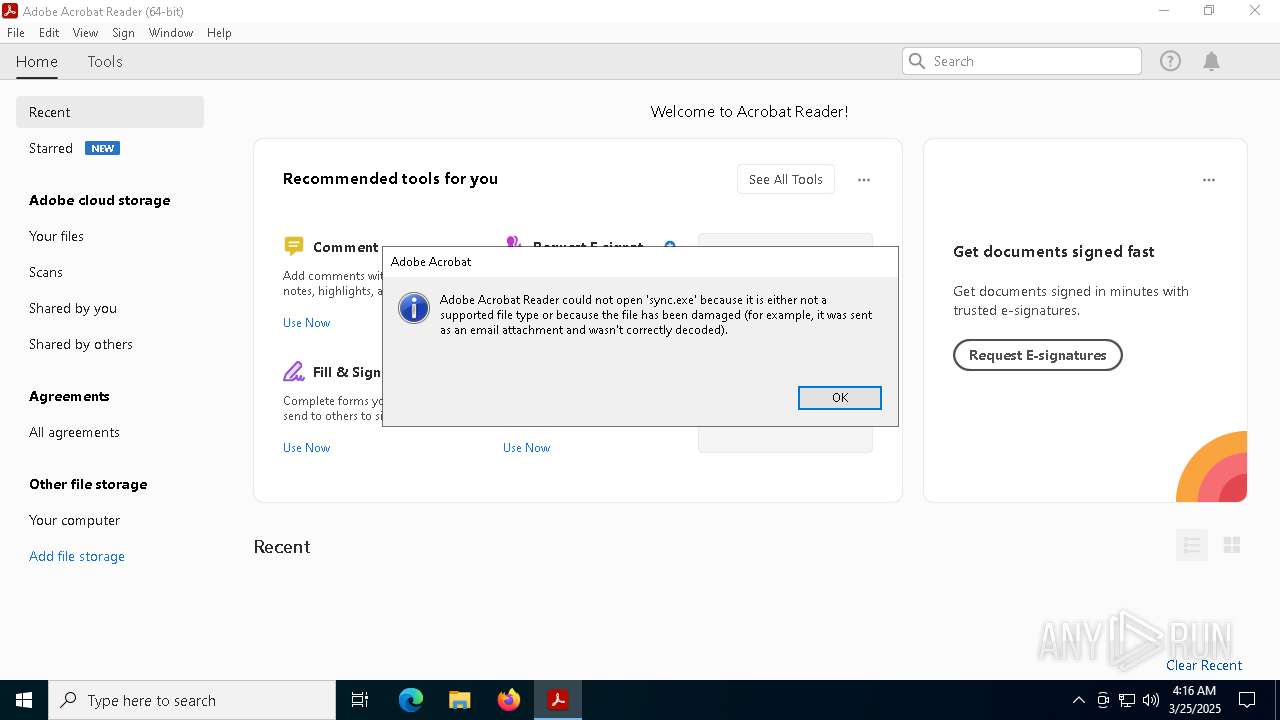
Application launched itself
- Acrobat.exe (PID: 2908)
- AcroCEF.exe (PID: 8068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2018:02:01 20:47:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.5 |
| CodeSize: | 483328 |
| InitializedDataSize: | 73728 |
| UninitializedDataSize: | 155648 |
| EntryPoint: | 0x9b880 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.2.63.1 |
| ProductVersionNumber: | 6.2.63.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | Comments: |
| ProductVersion: | 6.2.63.1 |
| ProductName: | 6.2.63.1 |
| OriginalFileName: | steams |
| InternalName: | NIsync.exe |
| FileDescription: | NIsync.exe |
| CompanyName: | DFS Command Line |
| LegalTrademarks: | OpenAI |
| LegalCopyright: | Openai (R) Windows (R) Operating System |
| PrivateBuild: | Copyright (c) Corporation. All rights reserved. |
Total processes
171
Monitored processes
31
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmpE820.tmp.bat"" | C:\Windows\SysWOW64\cmd.exe | — | NiSync.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | timeout 3 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1492 --field-trial-handle=1648,i,9306837682598110338,990182851337525416,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 2096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
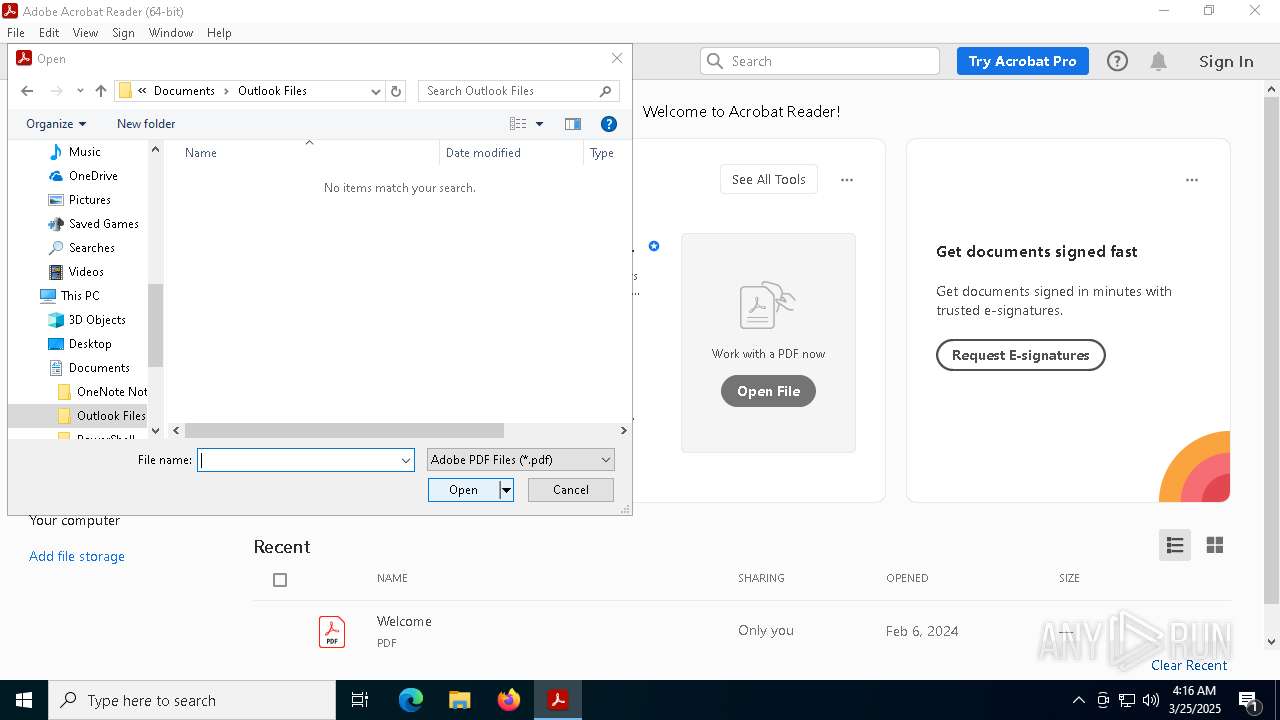
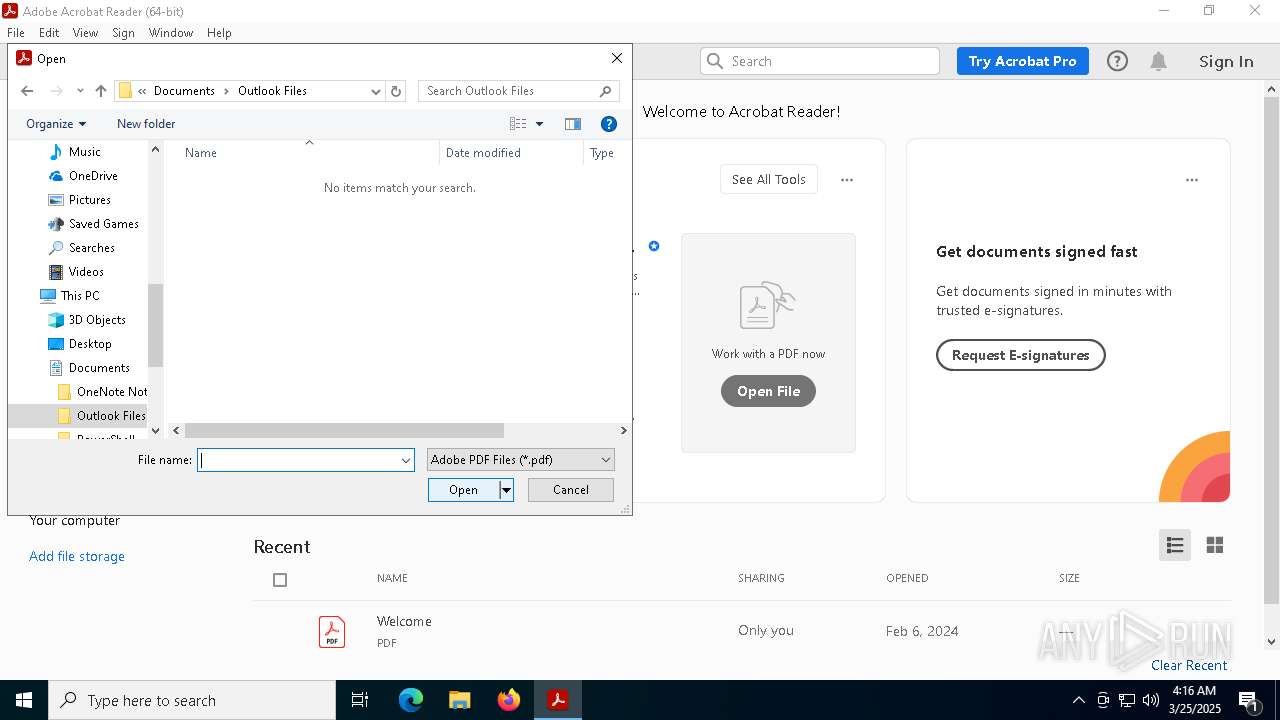
| 2908 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" "C:\Users\admin\AppData\Local\Temp\sync.exe" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Version: 23.1.20093.0 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\AppData\Local\Temp\sync.exe" | C:\Users\admin\AppData\Local\Temp\sync.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft blue Realtime Inspection Service Version: 4.18.1807.16386 Modules
| |||||||||||||||
| 4620 | "C:\WINDOWS\System32\OpenWith.exe" "C:\Users\admin\AppData\Local\Temp\sync.exe" | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 425
Read events
22 324
Write events
97
Delete events
4
Modification events
| (PID) Process: | (7416) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MyScript |
Value: C:\Users\admin\AppData\Local\Temp\C1EA.tmp\C1EB.tmp\C1EC.vbs | |||
| (PID) Process: | (1132) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1132) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1132) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5304) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5304) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5304) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4620) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.exe\OpenWithProgids |
| Operation: | write | Name: | exefile |
Value: | |||
| (PID) Process: | (7884) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7884) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
2
Suspicious files
108
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5304 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\8f18630b-a4e8-4199-841b-c08d769043a3.down_data | — | |
MD5:— | SHA256:— | |||
| 7512 | NiSync.exe | C:\Users\admin\AppData\Local\Temp\tmpE820.tmp.bat | text | |
MD5:9A2271FC8234557F761A252BDF5A221B | SHA256:3CE3B44C78415FB5E3EDC194B3C6A33353E323E99768CCBF8654147A27F3DD8D | |||
| 5304 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\8f18630b-a4e8-4199-841b-c08d769043a3.1b25d3b1-d9a1-4f16-bf20-416e4ea84d2d.down_meta | binary | |
MD5:F66256F3F2500134ECD9A4AAB07FA7DA | SHA256:E7210FEBFBB3EA291811F8D44D582E26D5EC2FBC391E2C330E801194976AB0A1 | |||
| 7416 | wscript.exe | C:\Windows\Temp\NiSync.exe | executable | |
MD5:659F500226209752645D4BDA888737EF | SHA256:A5962B778B57B55880C1A42FBA21B78C1B26552CB19967EEFC77646AECDE32FD | |||
| 5304 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 5328 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\SOPHIA.json | binary | |
MD5:837C1211E392A24D64C670DC10E8DA1B | SHA256:8013AC030684B86D754BBFBAB8A9CEC20CAA4DD9C03022715FF353DC10E14031 | |||
| 8068 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\LOG.old | text | |
MD5:2EF1F7C0782D1A46974286420D24F629 | SHA256:D3A9BB7E09E1F4B0C41FF7808E930DDACF5DB3BACD98ECCF5BC7DB4863D1FCF5 | |||
| 5304 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\3f2b03c5-6898-4400-a667-a5563a6d0a8f.1b25d3b1-d9a1-4f16-bf20-416e4ea84d2d.down_meta | binary | |
MD5:F66256F3F2500134ECD9A4AAB07FA7DA | SHA256:E7210FEBFBB3EA291811F8D44D582E26D5EC2FBC391E2C330E801194976AB0A1 | |||
| 5304 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\3f2b03c5-6898-4400-a667-a5563a6d0a8f.up_meta_secure | binary | |
MD5:AD4363361D33C73ECDB4F8B7C8054C1D | SHA256:FFBF85E13A63B2677D770D58275E596C2259DBE1E8FE9C95941EB188FDE651EF | |||
| 8068 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Local Storage\leveldb\LOG.old~RF1204da.TMP | text | |
MD5:ED7D8AAE48211E2BFAF557130572C62A | SHA256:A5CF8D8ADC86DCA357396AF7E3A24A116072D5C1E5552EEB76601AE2673DED6E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
30
DNS requests
20
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7384 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5304 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4756 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4756 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1616 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7384 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7384 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
pastebin.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
3140 | sync.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
3140 | sync.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
3140 | sync.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
3140 | sync.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |