| File name: | Malware_ZIP_6a325f9d37769f16f3a5e656fb7b380c6f477b39ec7604d11ad9ec67125ce029 |
| Full analysis: | https://app.any.run/tasks/a4e360c7-1139-493a-be79-d00d86ab158b |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | February 25, 2019, 14:54:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
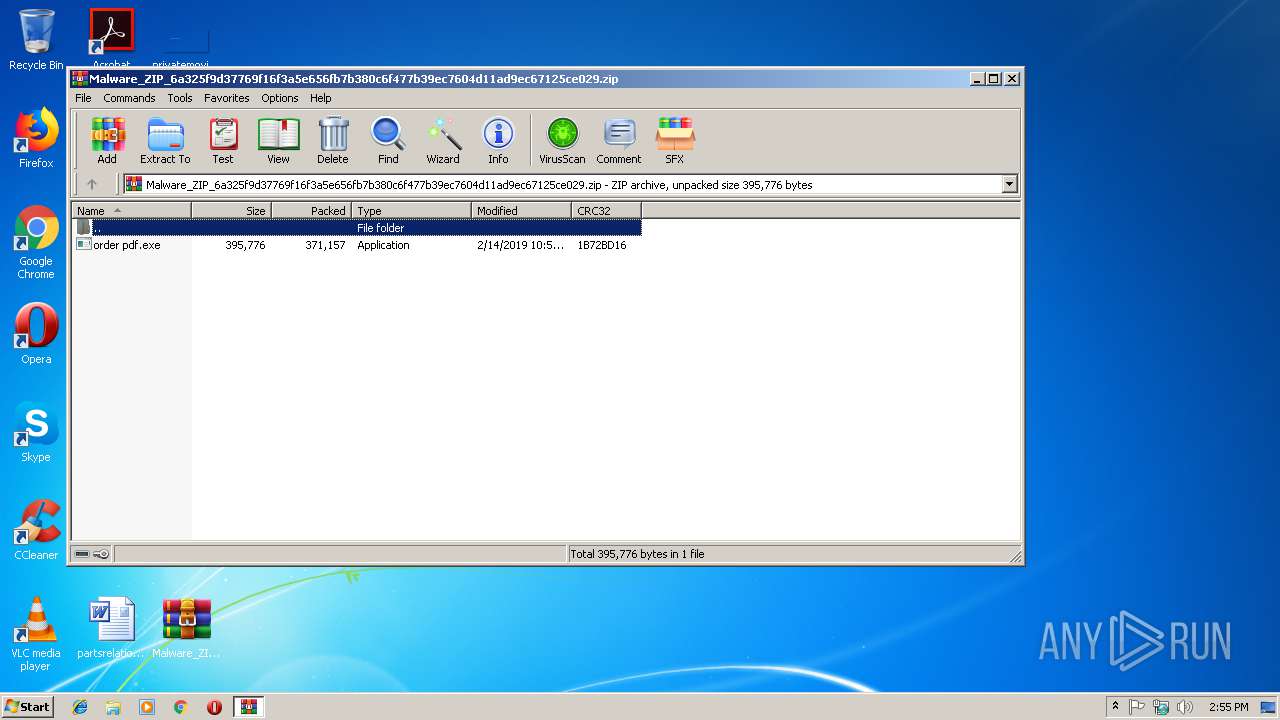
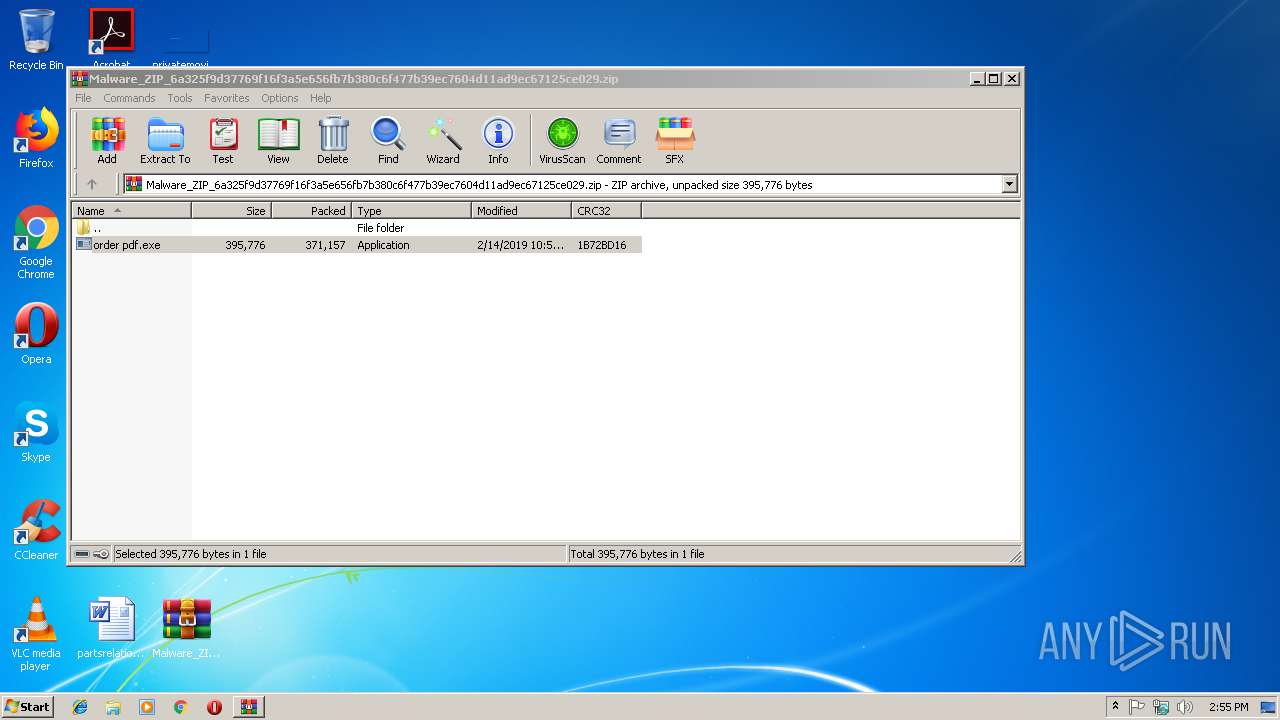
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6D8E8167B6CAC928681BA320852B3340 |
| SHA1: | 6829A52EA906DCB9F9C2FEEAC18D1E19847F1EC5 |
| SHA256: | 6A325F9D37769F16F3A5E656FB7B380C6F477B39EC7604D11AD9EC67125CE029 |
| SSDEEP: | 6144:WwJ187NGUPKTs9PybMDzd7SU3ejjQcRq3U1hv63/Fz0jThbr9Om+wyFAoF4pcv:WwuiwF6MN7ezDm/Fotf9P9yFAouU |
MALICIOUS
Connects to CnC server
- explorer.exe (PID: 116)
Application was dropped or rewritten from another process
- order pdf.exe (PID: 3016)
- gdim628.exe (PID: 2220)
FORMBOOK was detected
- explorer.exe (PID: 116)
Actions looks like stealing of personal data
- cmmon32.exe (PID: 3676)
Changes the autorun value in the registry
- cmmon32.exe (PID: 3676)
Formbook was detected
- cmmon32.exe (PID: 3676)
- Firefox.exe (PID: 3776)
Stealing of credential data
- cmmon32.exe (PID: 3676)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 116)
- cmmon32.exe (PID: 3676)
Reads Internet Cache Settings
- explorer.exe (PID: 116)
Executable content was dropped or overwritten
- explorer.exe (PID: 116)
- DllHost.exe (PID: 3568)
Starts CMD.EXE for commands execution
- cmmon32.exe (PID: 3676)
Loads DLL from Mozilla Firefox
- cmmon32.exe (PID: 3676)
Creates files in the program directory
- DllHost.exe (PID: 3568)
INFO
Creates files in the user directory
- Firefox.exe (PID: 3776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:02:14 10:59:27 |
| ZipCRC: | 0x1b72bd16 |
| ZipCompressedSize: | 371157 |
| ZipUncompressedSize: | 395776 |
| ZipFileName: | order pdf.exe |
Total processes
42
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1464 | "C:\Windows\System32\dwm.exe" | C:\Windows\System32\dwm.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Hth2d\gdim628.exe" | C:\Program Files\Hth2d\gdim628.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2372 | /c del "C:\Users\admin\Desktop\order pdf.exe" | C:\Windows\System32\cmd.exe | — | cmmon32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2984 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Malware_ZIP_6a325f9d37769f16f3a5e656fb7b380c6f477b39ec7604d11ad9ec67125ce029.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3016 | "C:\Users\admin\Desktop\order pdf.exe" | C:\Users\admin\Desktop\order pdf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3568 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3676 | "C:\Windows\System32\cmmon32.exe" | C:\Windows\System32\cmmon32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Monitor Exit code: 0 Version: 7.02.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3776 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | cmmon32.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
Total events
3 039
Read events
3 001
Write events
36
Delete events
2
Modification events
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Malware_ZIP_6a325f9d37769f16f3a5e656fb7b380c6f477b39ec7604d11ad9ec67125ce029.zip | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
3
Suspicious files
72
Text files
1
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2984.1628\order pdf.exe | — | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\Desktop\order pdf.exe | executable | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Malware_ZIP_6a325f9d37769f16f3a5e656fb7b380c6f477b39ec7604d11ad9ec67125ce029.zip.lnk | lnk | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Hth2d\gdim628.exe | executable | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019022520190226\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3676 | cmmon32.exe | C:\Users\admin\AppData\Roaming\J-2289B8\J-2logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 3676 | cmmon32.exe | C:\Users\admin\AppData\Roaming\J-2289B8\J-2logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 3776 | Firefox.exe | C:\Users\admin\AppData\Roaming\J-2289B8\J-2logrf.ini | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
13
DNS requests
13
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | explorer.exe | GET | — | 154.84.67.48:80 | http://www.luba5.com/nk7/?NVDPll=bvHxsUjdAQTTZLTQFzM8qo+z4k71ySQD2pm/ae9rQm6yCe6ugG+SAoiYYZZrIoTNCWPxpQ==&Wz=H2g49vWHQZclu | US | — | — | malicious |
116 | explorer.exe | GET | 301 | 94.23.249.36:80 | http://www.lasticsazanshargh.com/nk7/?NVDPll=J2t8P7/V+6SS/5Ezsd9B/E+Mxs6fWePiM12cLMScUbRHENmaJurYldAWbaLy7NlGpccRzw==&Wz=H2g49vWHQZclu | FR | — | — | malicious |
116 | explorer.exe | GET | — | 198.185.159.144:80 | http://www.flowwithshell.com/nk7/?NVDPll=dhGY612UfOma2NYYuCtmXqNqGb9IK96LezDUPUa8HeiG4C0rjLxE60SVvgA8m2EEX6R7Tw==&Wz=H2g49vWHQZclu | US | — | — | malicious |
116 | explorer.exe | GET | 404 | 198.187.30.187:80 | http://www.regular123.com/nk7/?NVDPll=/N3OmBPston5LJJZeKOgbT6QfhDWZNOQ3TsffSOvWqMccli+ipx2VvhISP5Ak1G/iefMRw==&Wz=H2g49vWHQZclu&sql=1 | US | html | 327 b | malicious |
116 | explorer.exe | POST | — | 198.187.30.187:80 | http://www.regular123.com/nk7/ | US | — | — | malicious |
116 | explorer.exe | POST | — | 94.23.249.36:80 | http://www.lasticsazanshargh.com/nk7/ | FR | — | — | malicious |
116 | explorer.exe | POST | — | 94.23.249.36:80 | http://www.lasticsazanshargh.com/nk7/ | FR | — | — | malicious |
116 | explorer.exe | POST | — | 94.23.249.36:80 | http://www.lasticsazanshargh.com/nk7/ | FR | — | — | malicious |
116 | explorer.exe | POST | — | 198.185.159.144:80 | http://www.flowwithshell.com/nk7/ | US | — | — | malicious |
116 | explorer.exe | POST | — | 198.185.159.144:80 | http://www.flowwithshell.com/nk7/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
116 | explorer.exe | 198.187.30.187:80 | www.regular123.com | Namecheap, Inc. | US | malicious |
116 | explorer.exe | 154.84.67.48:80 | www.luba5.com | MULTACOM CORPORATION | US | suspicious |
116 | explorer.exe | 94.23.249.36:80 | www.lasticsazanshargh.com | OVH SAS | FR | malicious |
116 | explorer.exe | 198.185.159.144:80 | www.flowwithshell.com | Squarespace, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.baar-co.com |
| malicious |
www.ggluav18.com |
| unknown |
www.luba5.com |
| malicious |
www.regular123.com |
| malicious |
www.phototipsforagents.com |
| unknown |
www.qlmzrr.info |
| unknown |
www.tawandachitsinde.com |
| unknown |
www.inveystor.com |
| unknown |
www.ughbb.com |
| unknown |
www.golfapitude.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
10 ETPRO signatures available at the full report