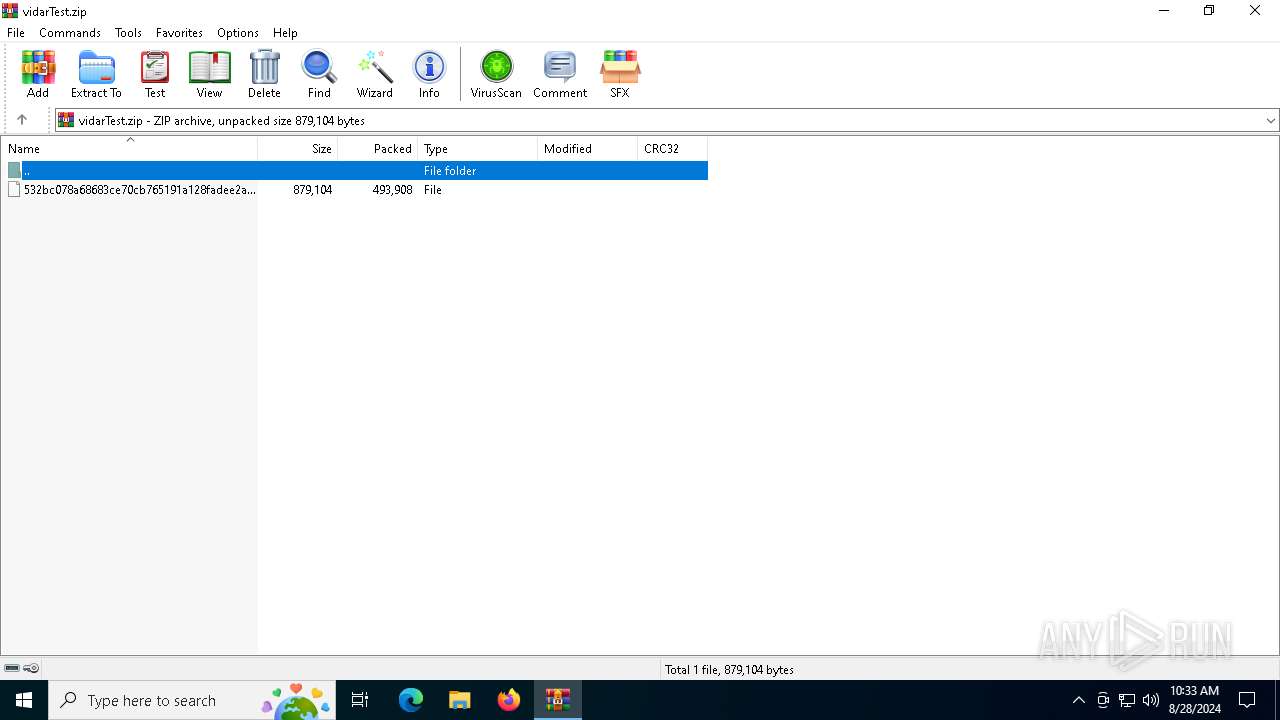
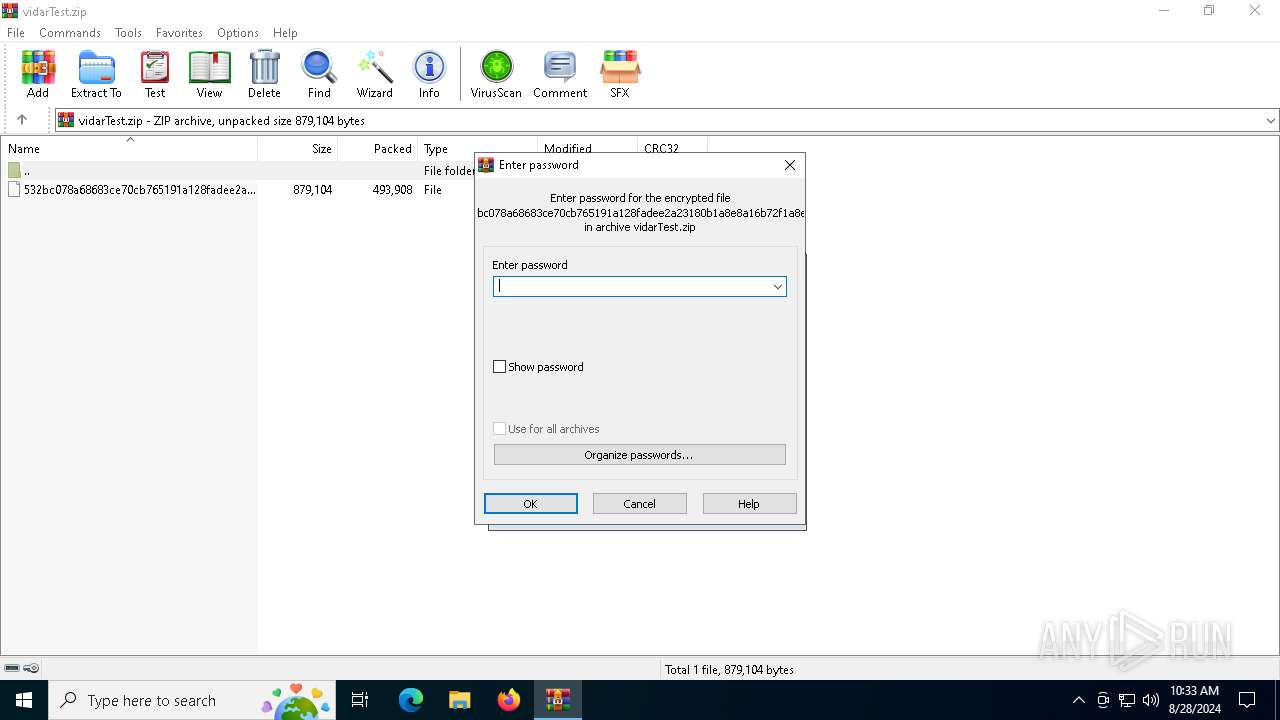
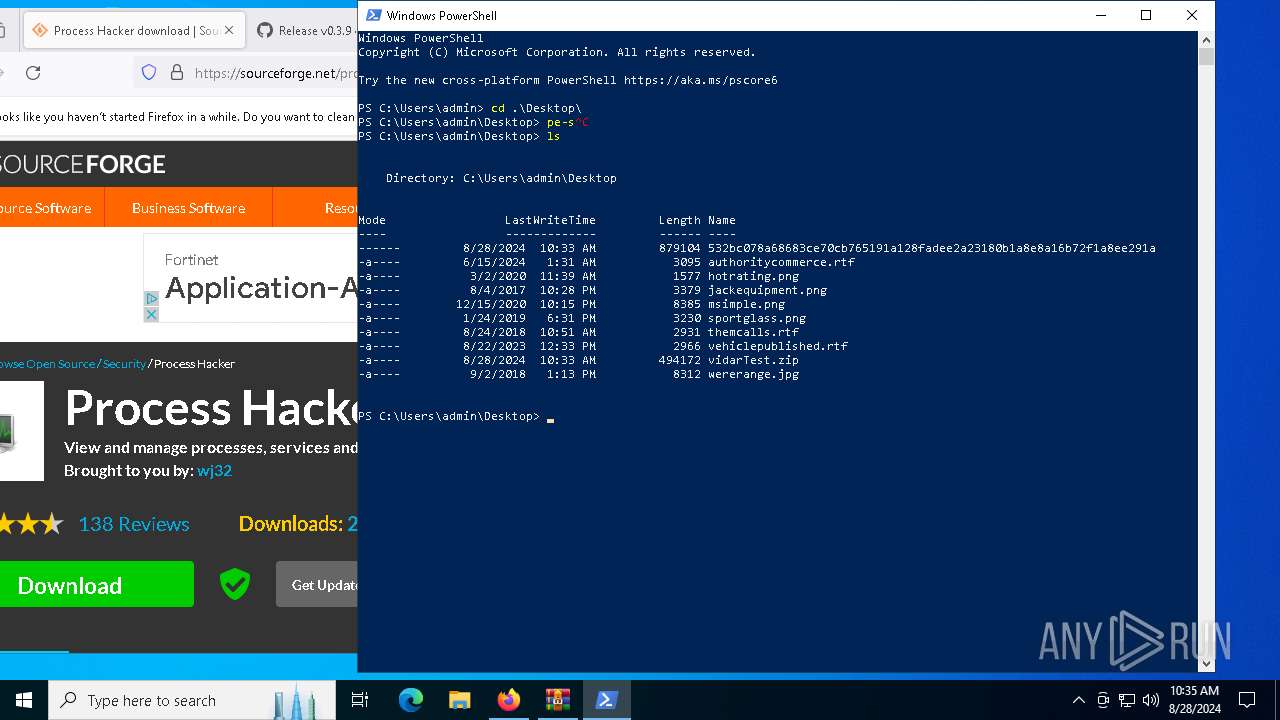
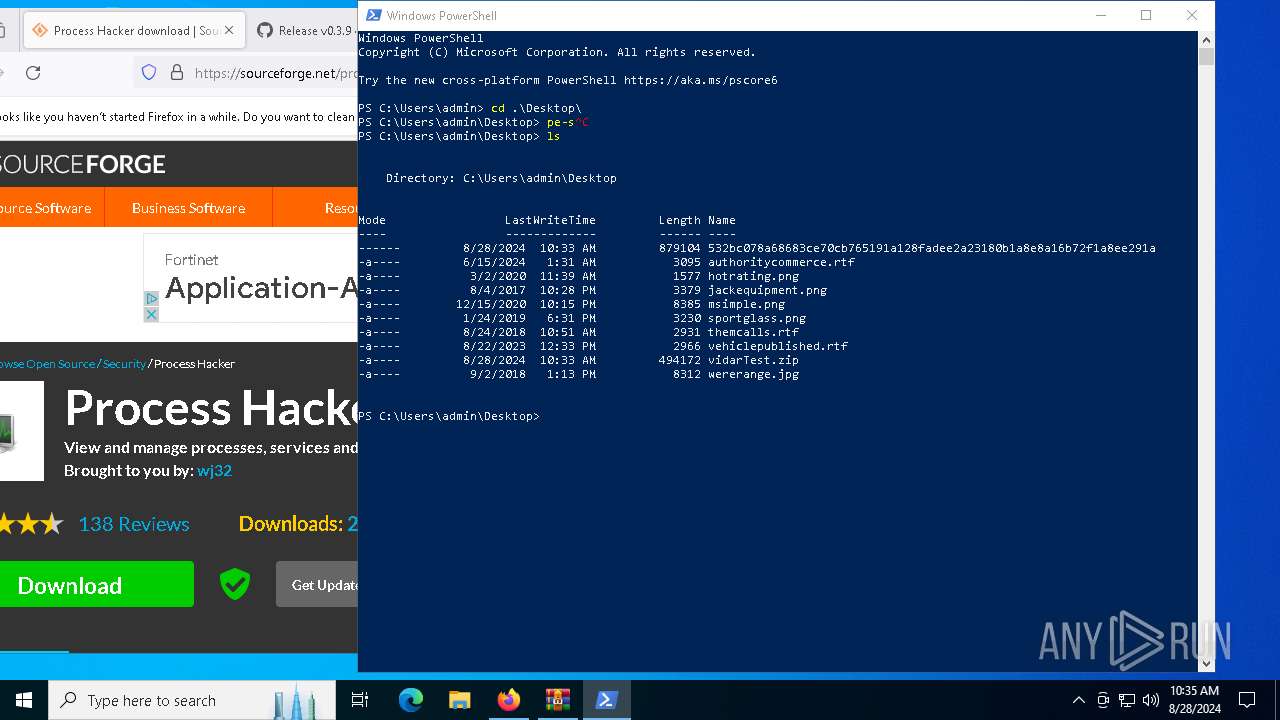
| File name: | vidarTest.zip |
| Full analysis: | https://app.any.run/tasks/a8efc85f-c388-4b90-9c29-60cda14d95d3 |
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
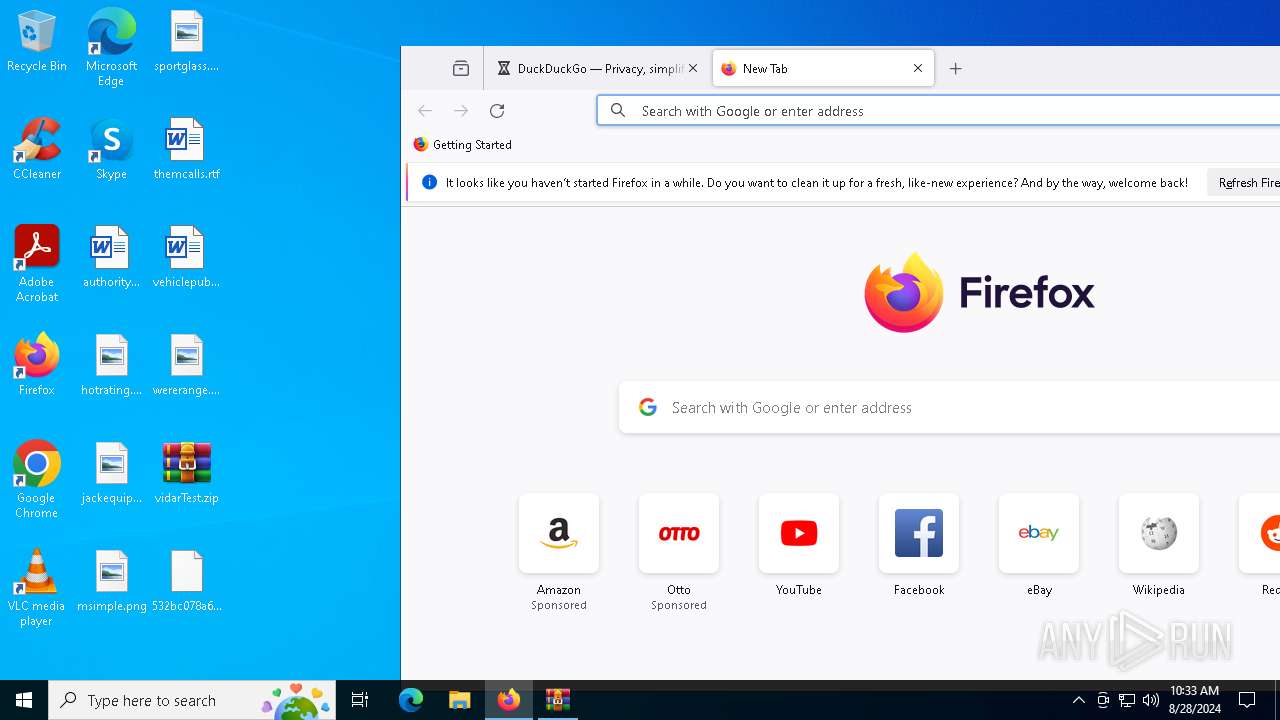
| Analysis date: | August 28, 2024, 10:33:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | 471D68755A68E1D6345F10A7269D165C |
| SHA1: | 2F7250FF7F7852E92AD9DD147DC1B6F542E45CA9 |
| SHA256: | 6A21AB98C825D09F408F540FFF7E56C242AF1883A938AB9B9A02D5CAB55219AC |
| SSDEEP: | 24576:lqN7mY4TFUV/5udfqh+MQYm83OG9bNO1EmGl2QSDA3DqaFlbF:lqN7mY4TFUV/gdfqh+MQYm83O0bNmEm4 |
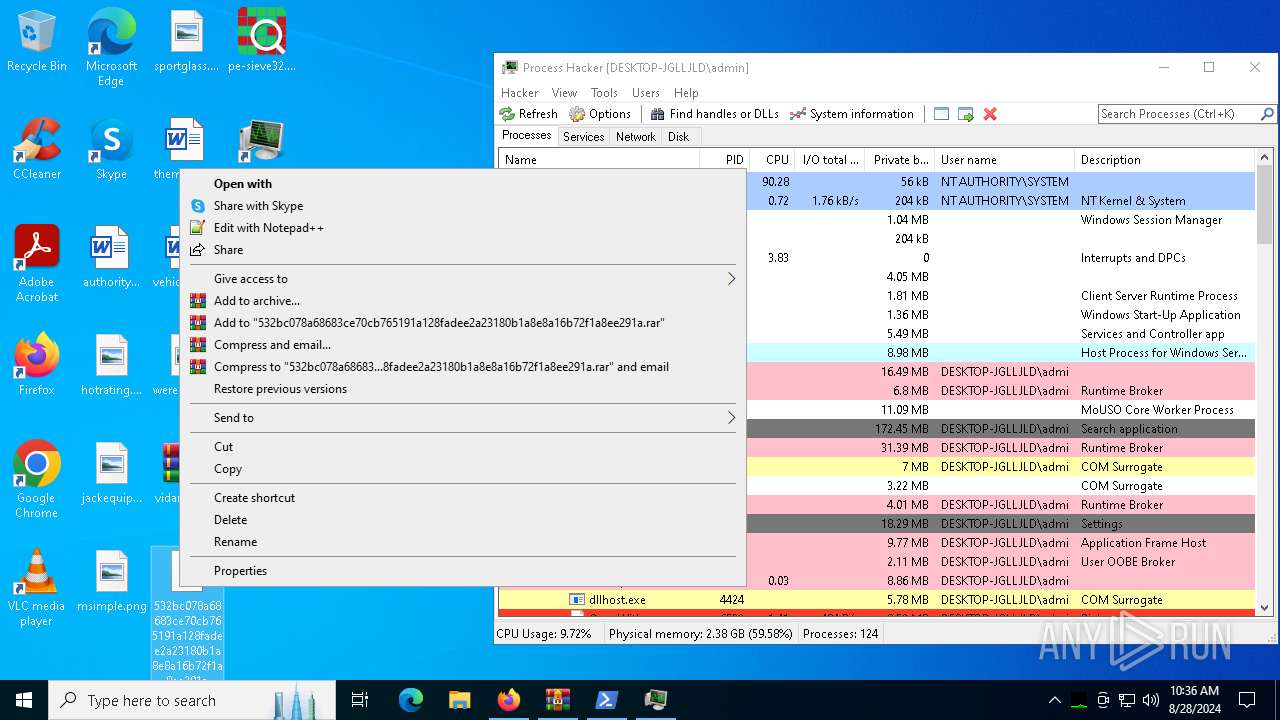
MALICIOUS
Renames files like ransomware
- explorer.exe (PID: 4552)
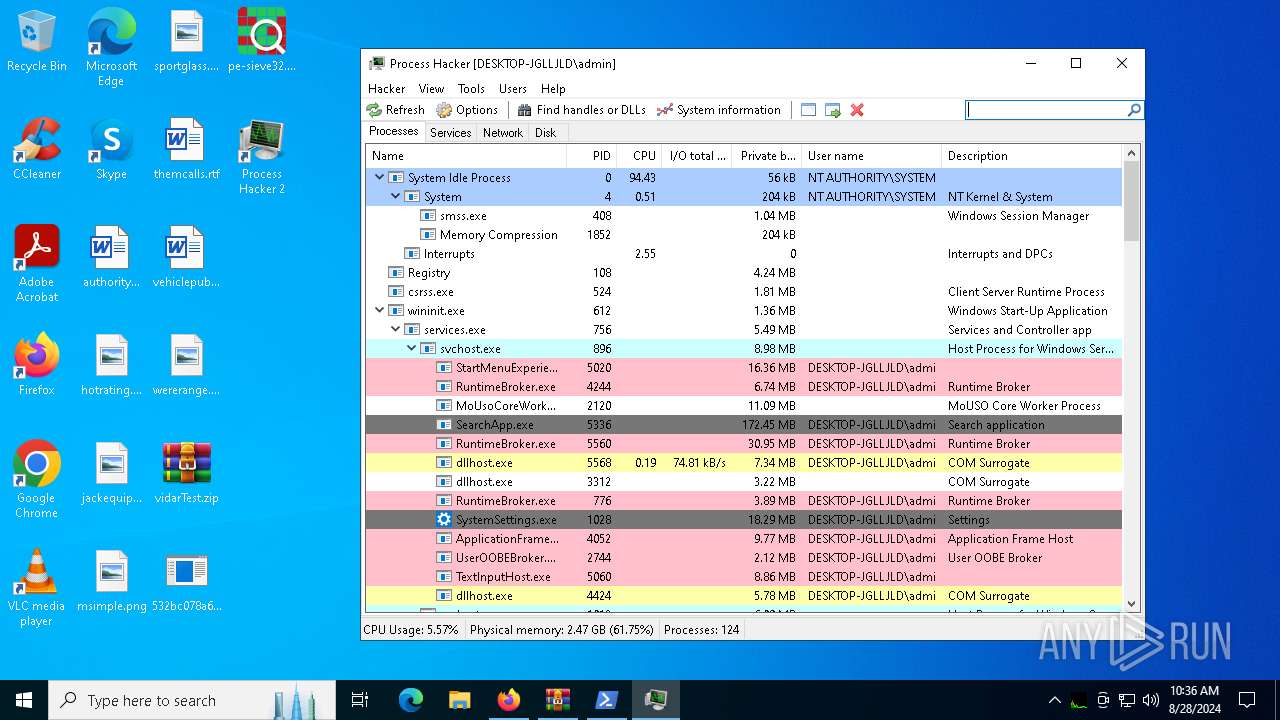
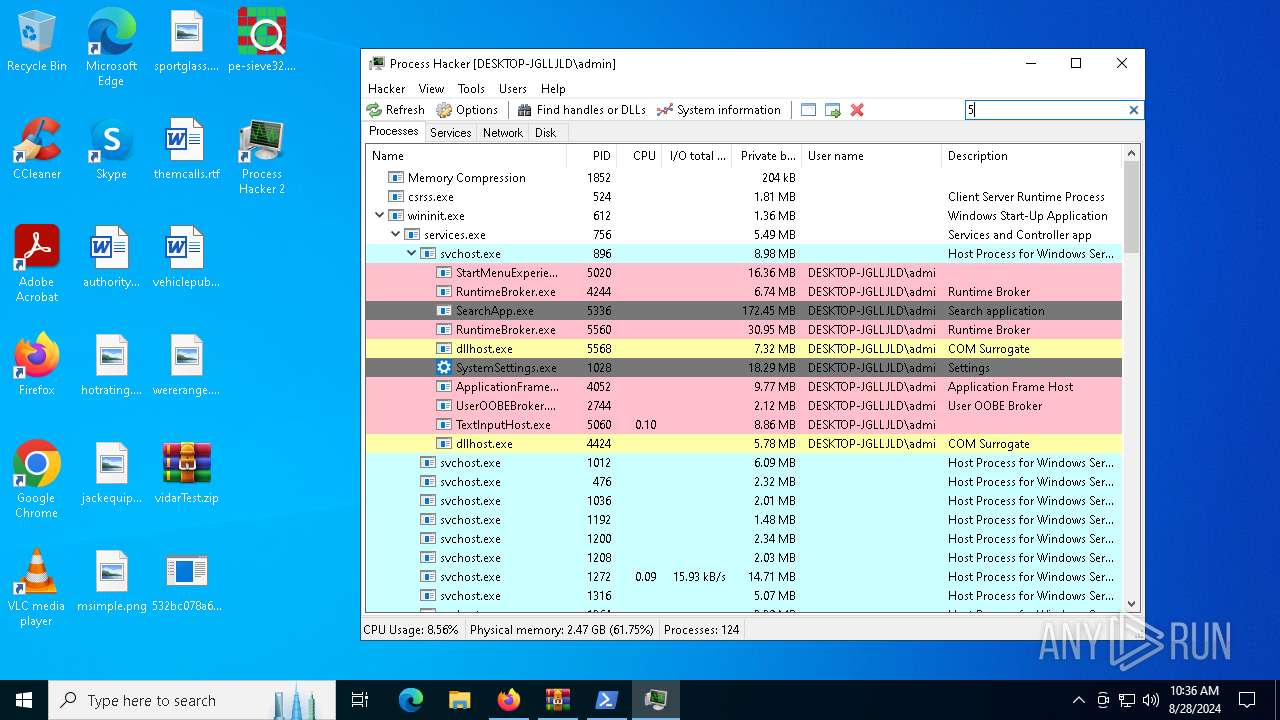
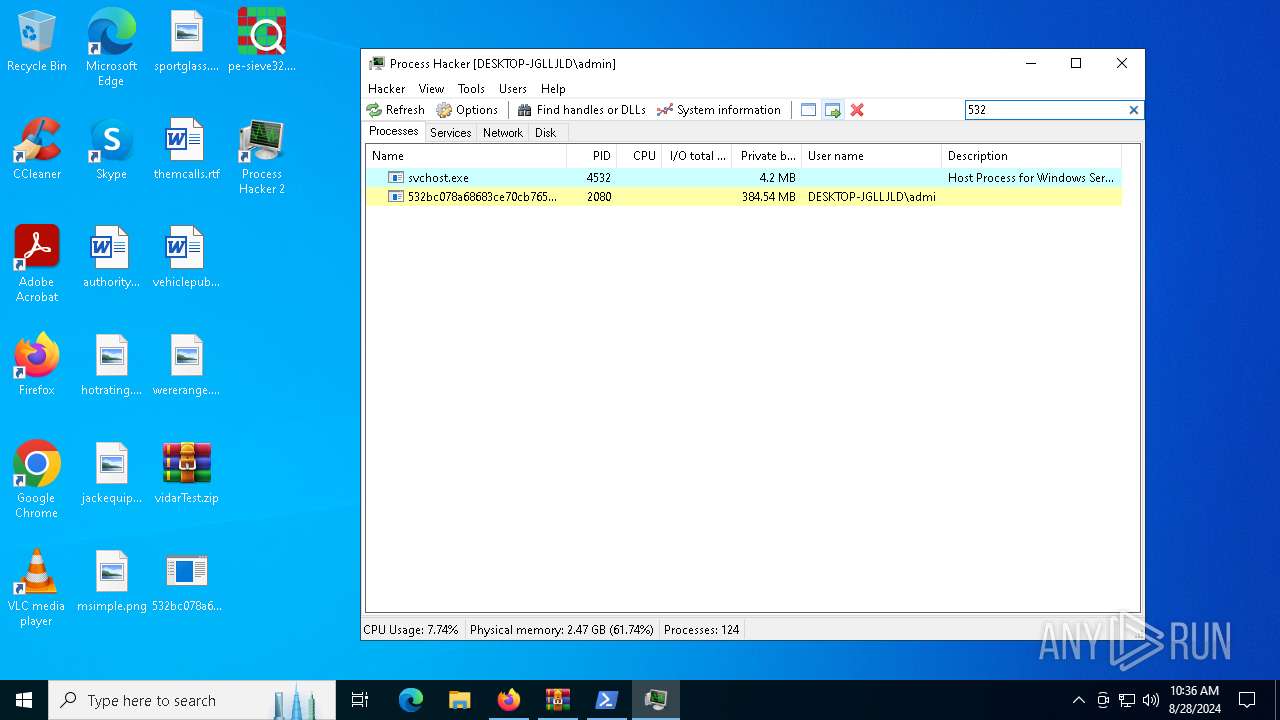
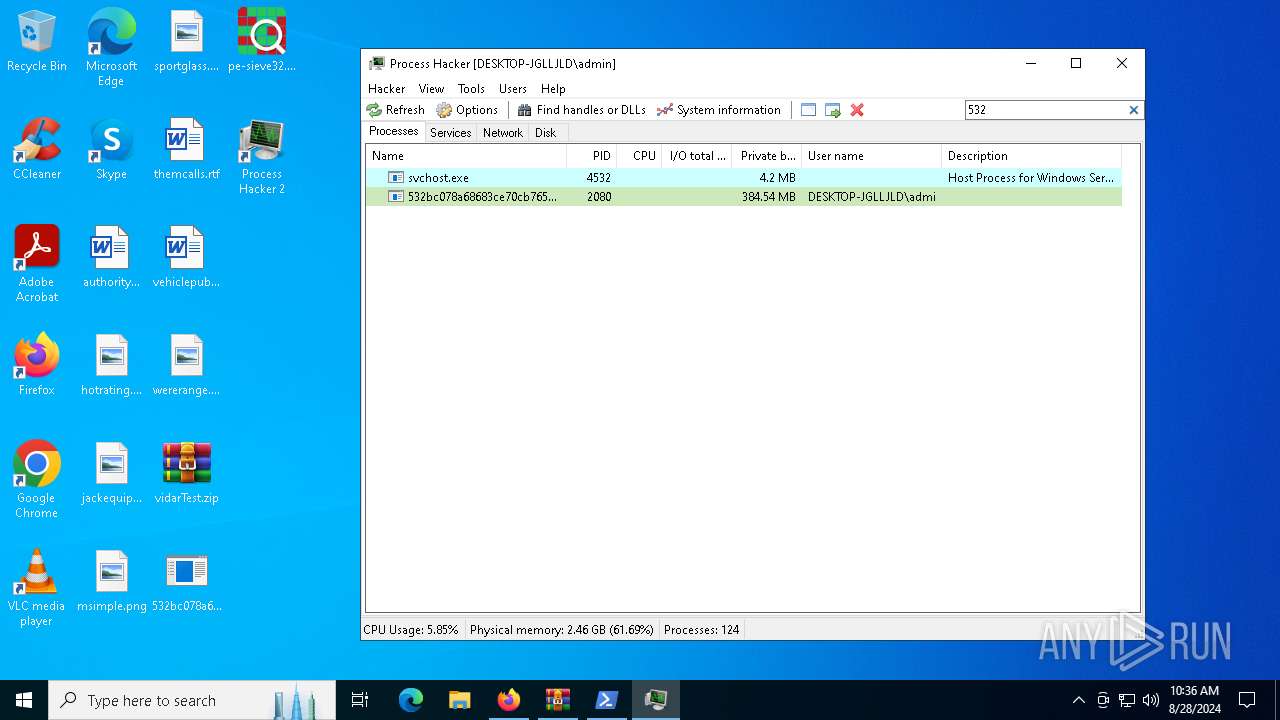
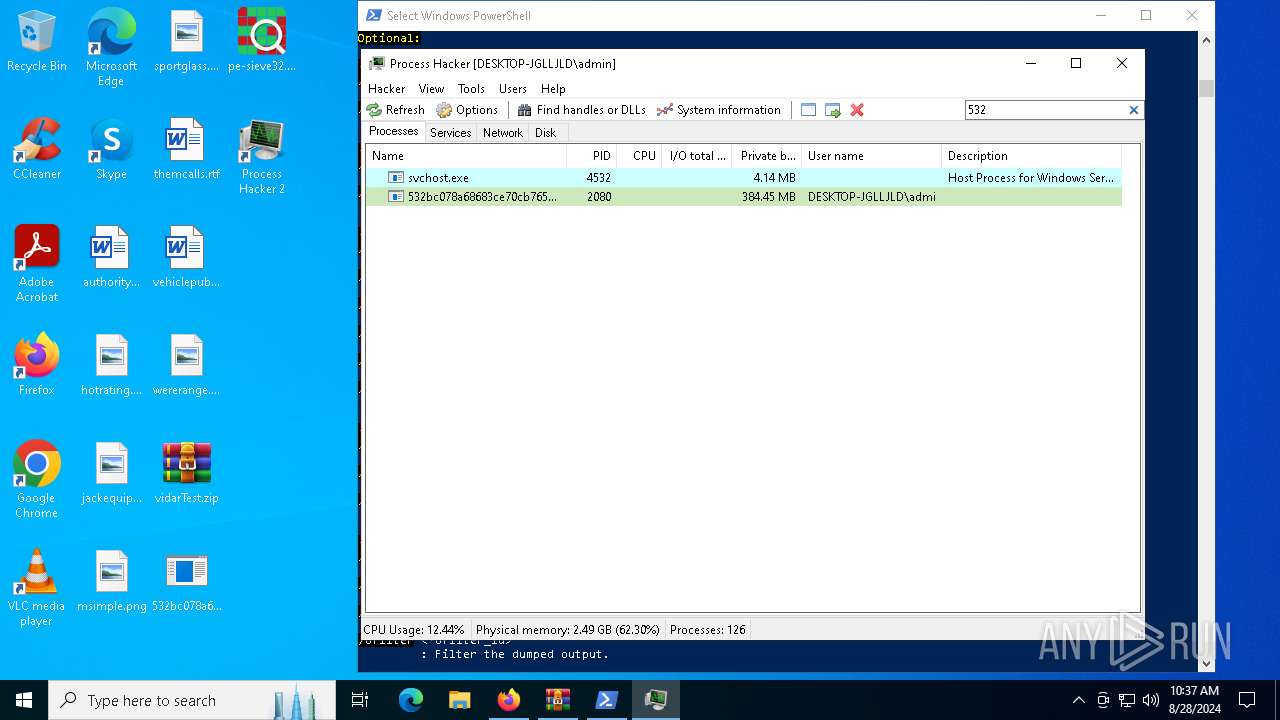
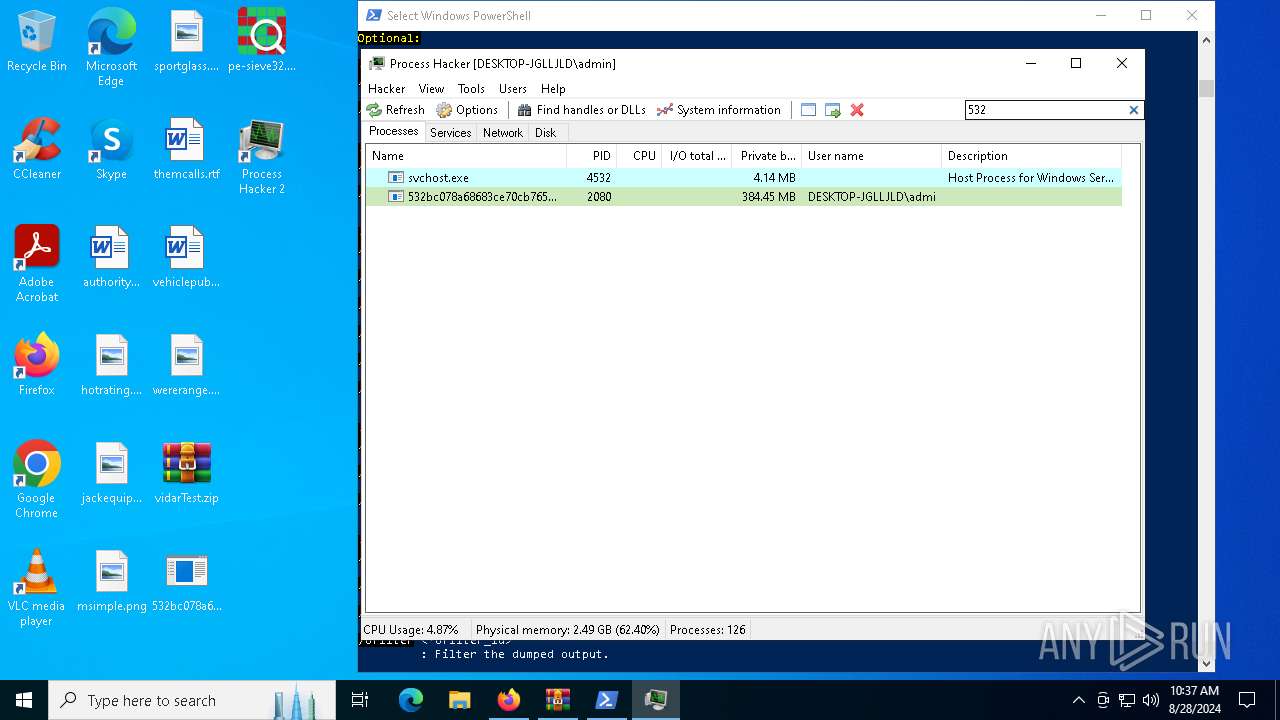
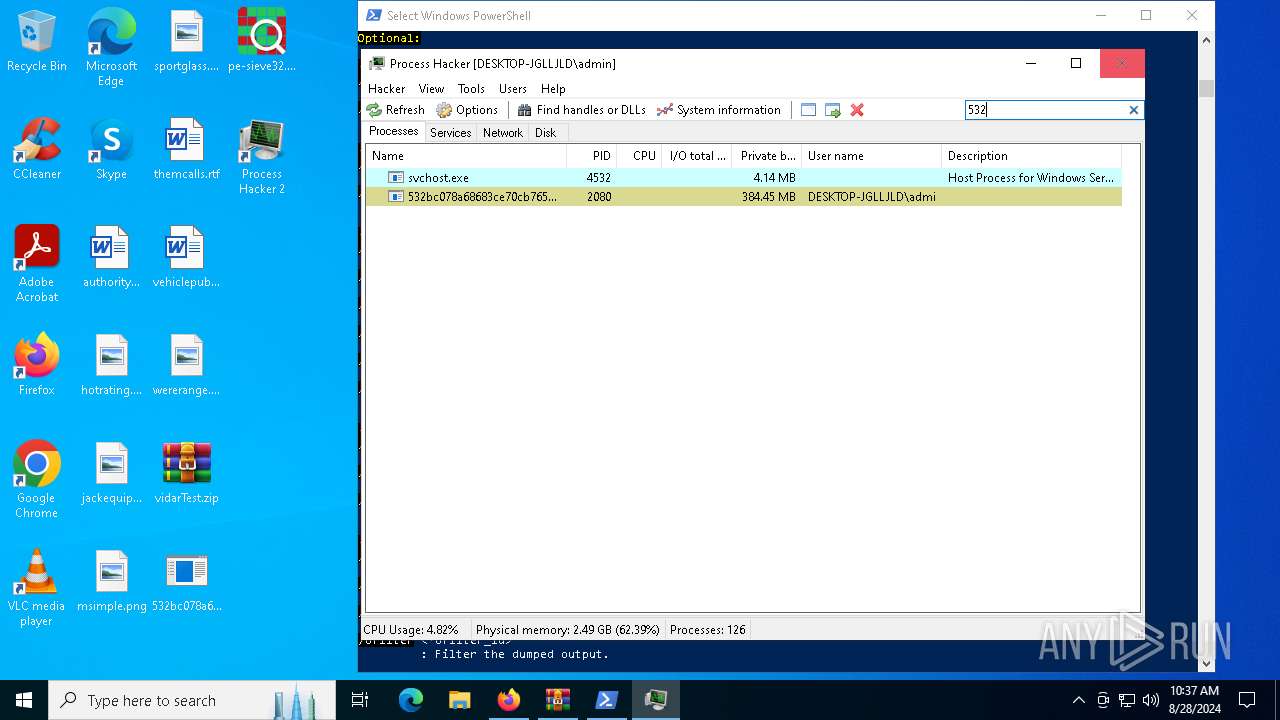
ARKEI has been detected (YARA)
- 532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a.exe (PID: 2080)
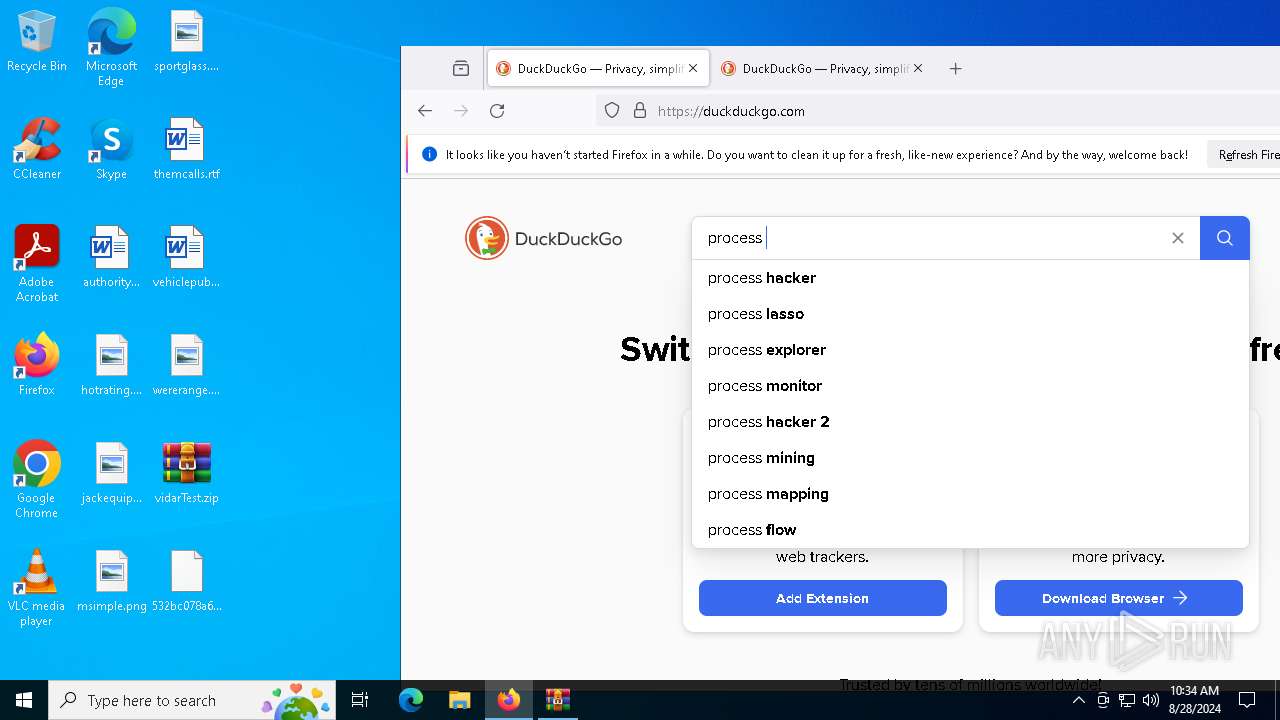
SUSPICIOUS
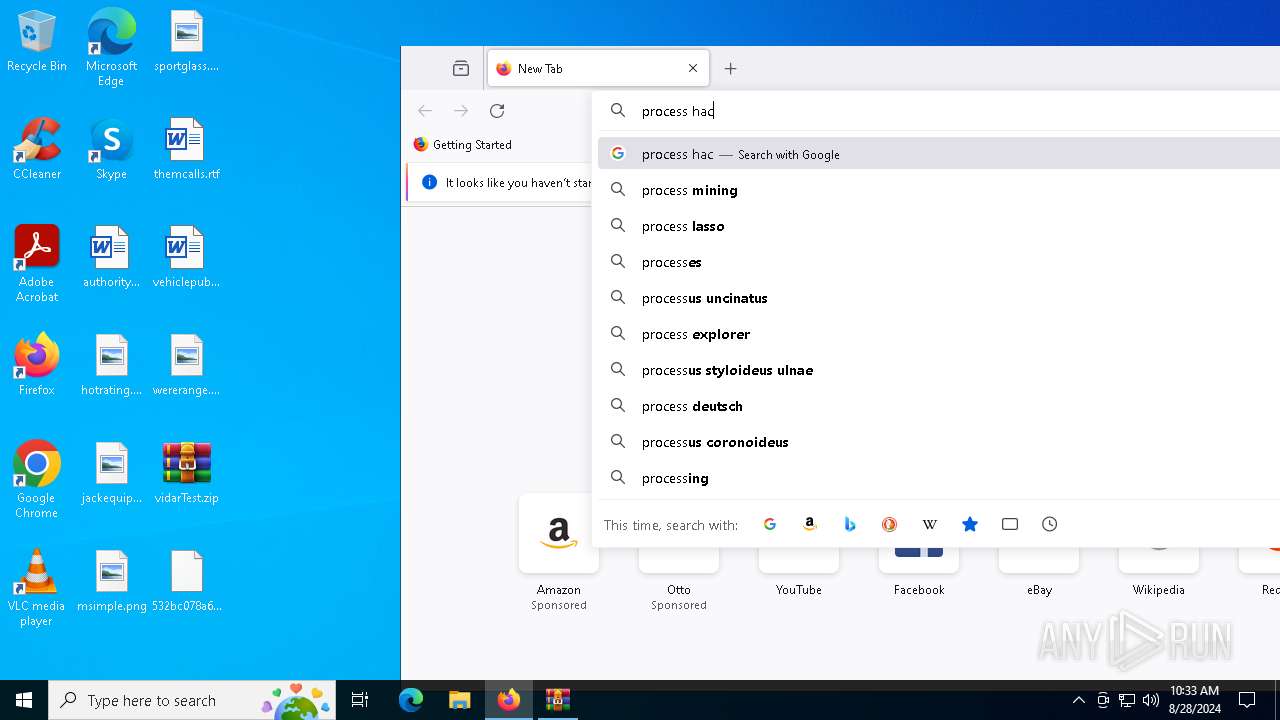
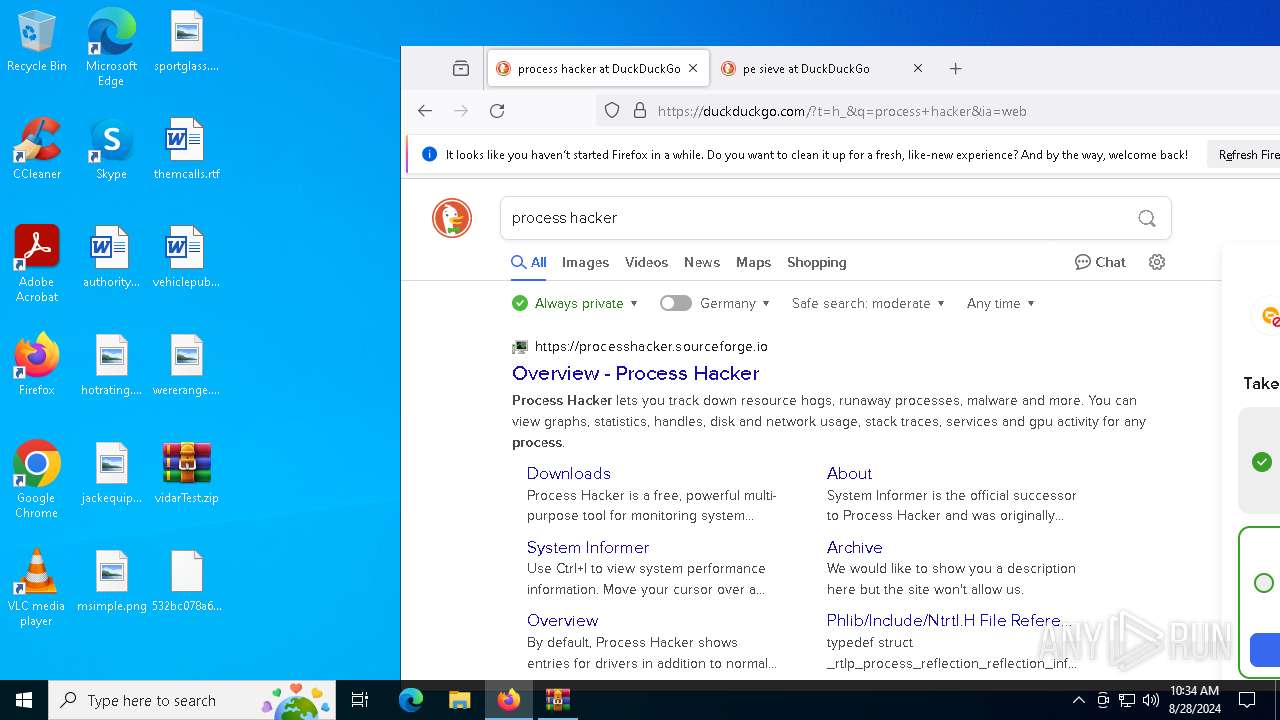
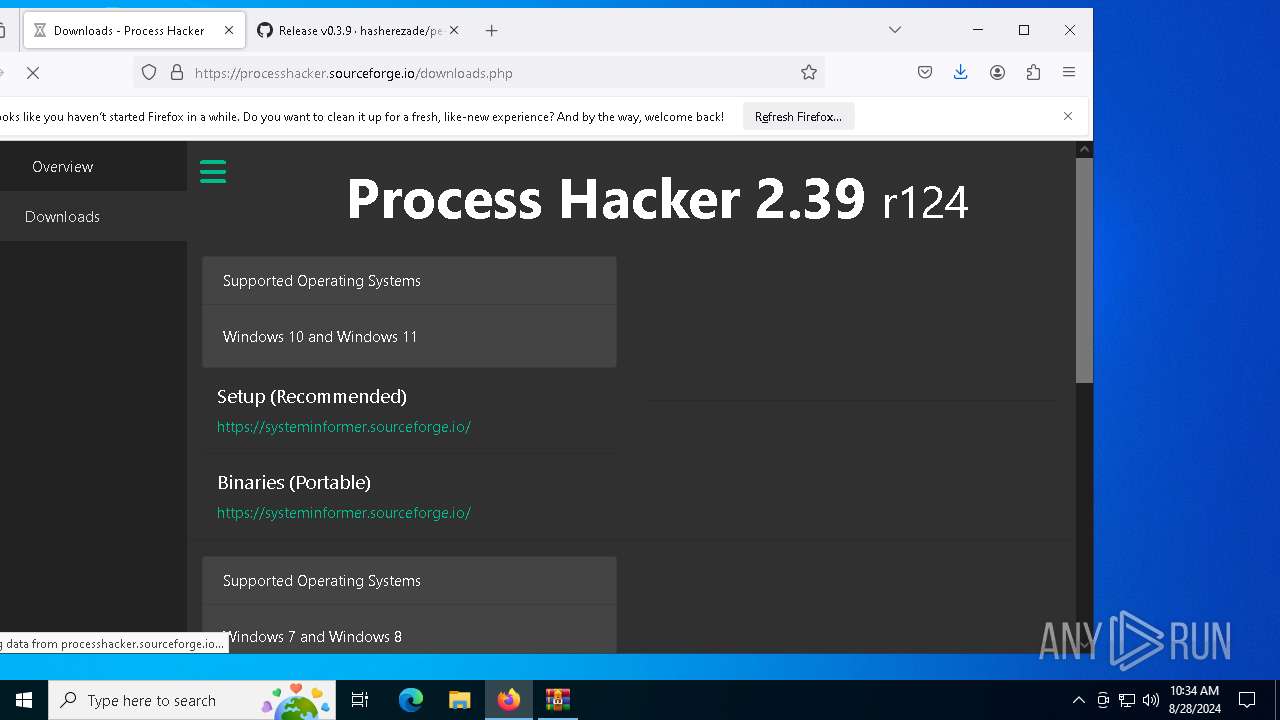
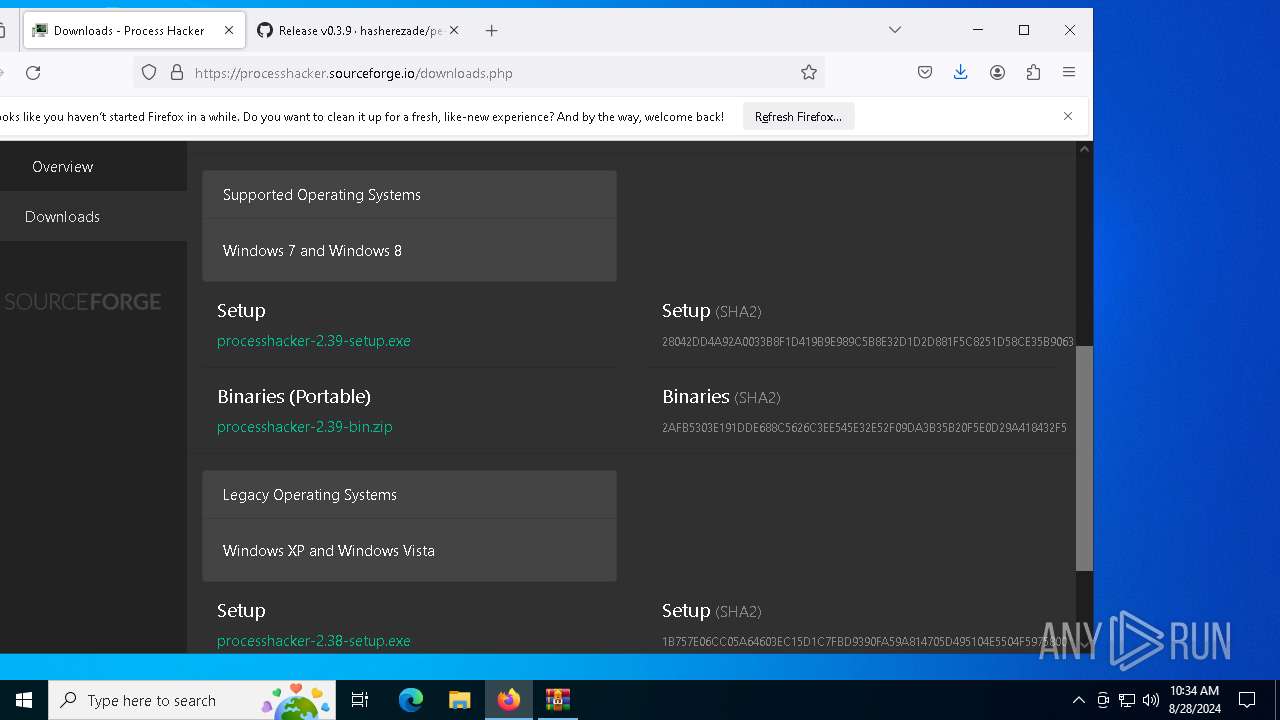
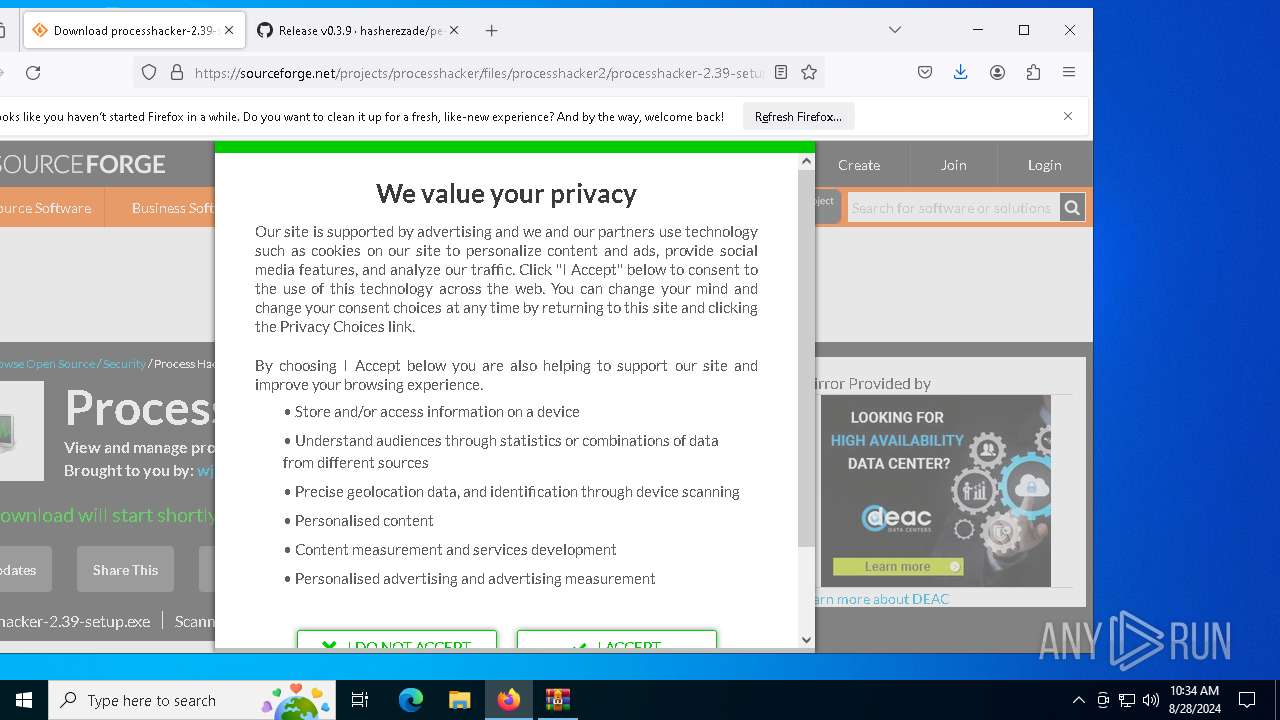
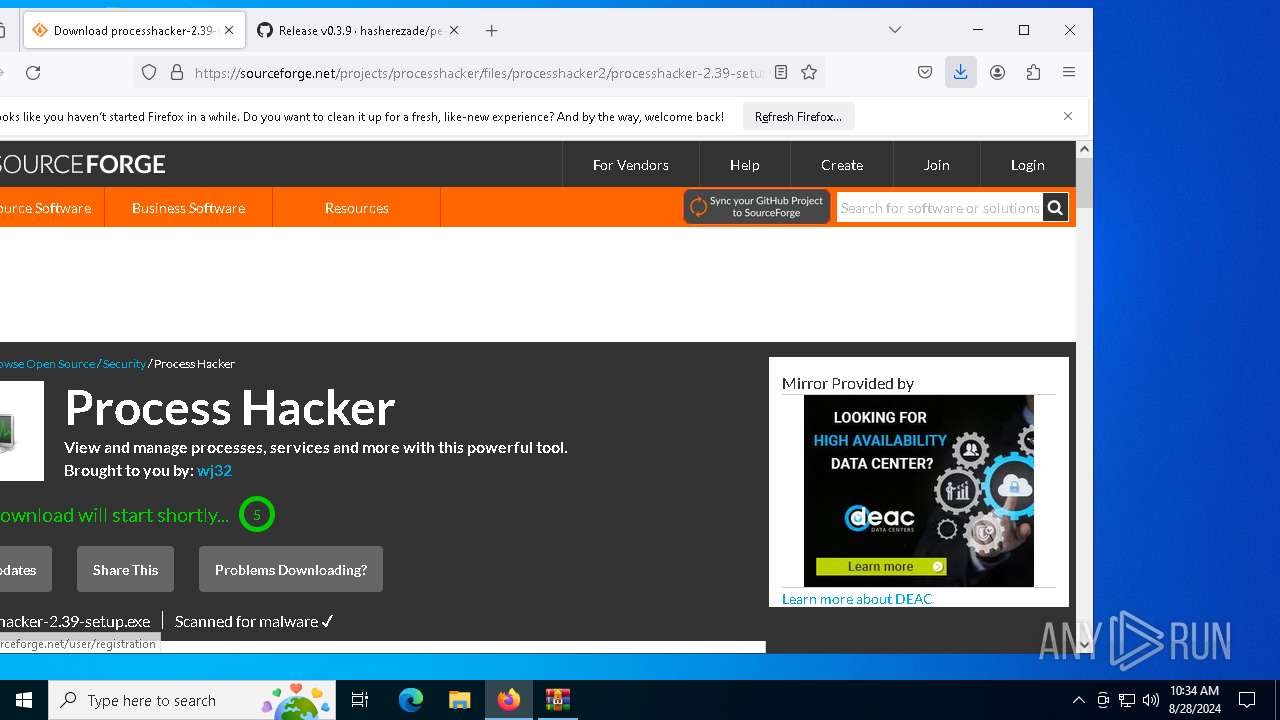
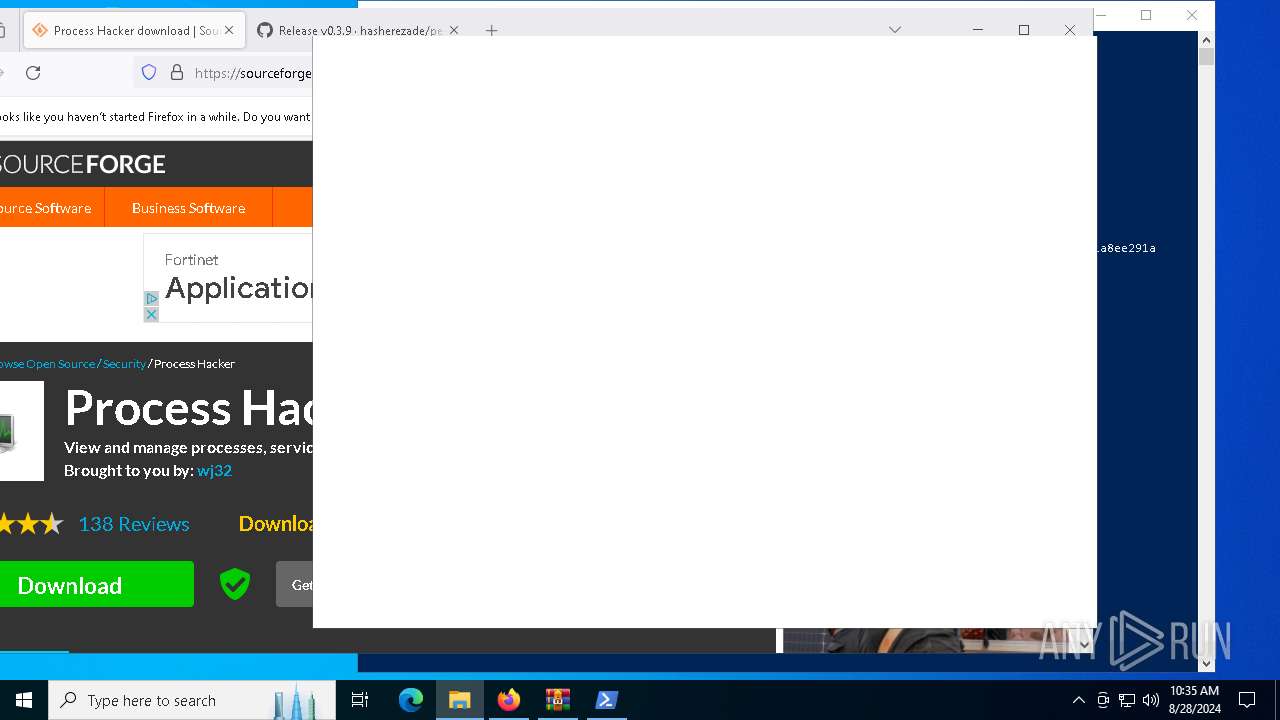
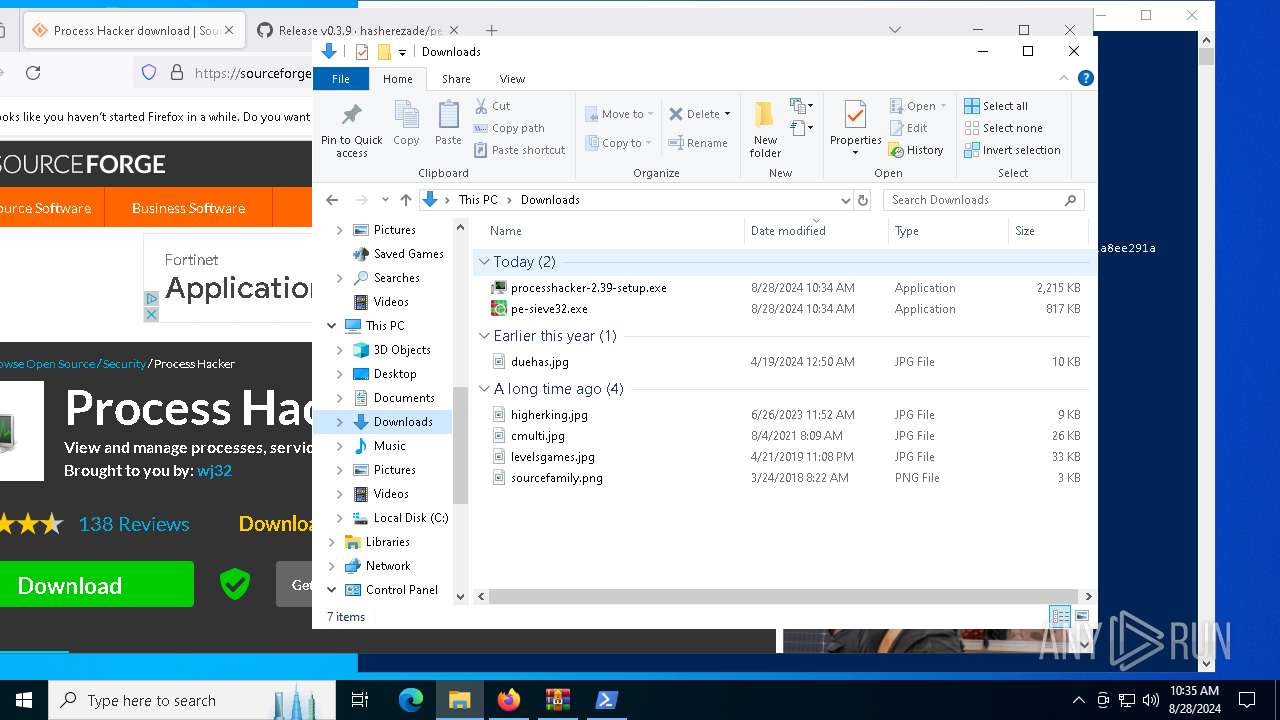
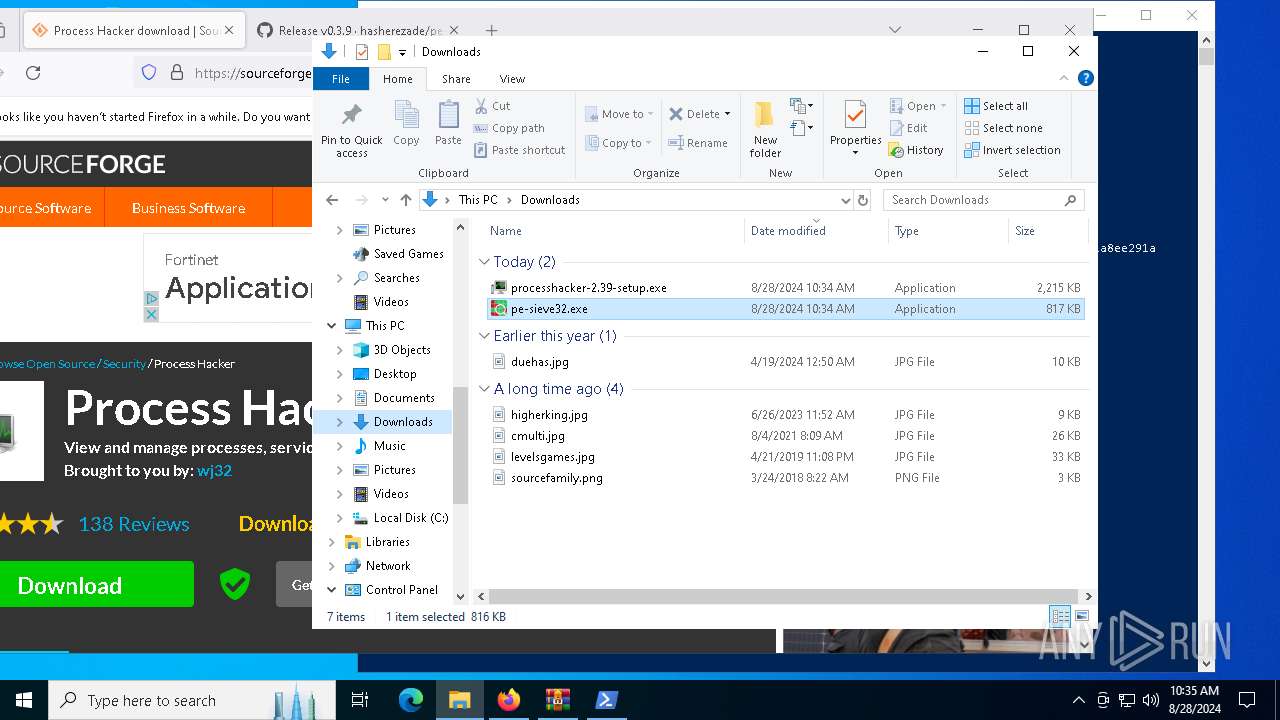
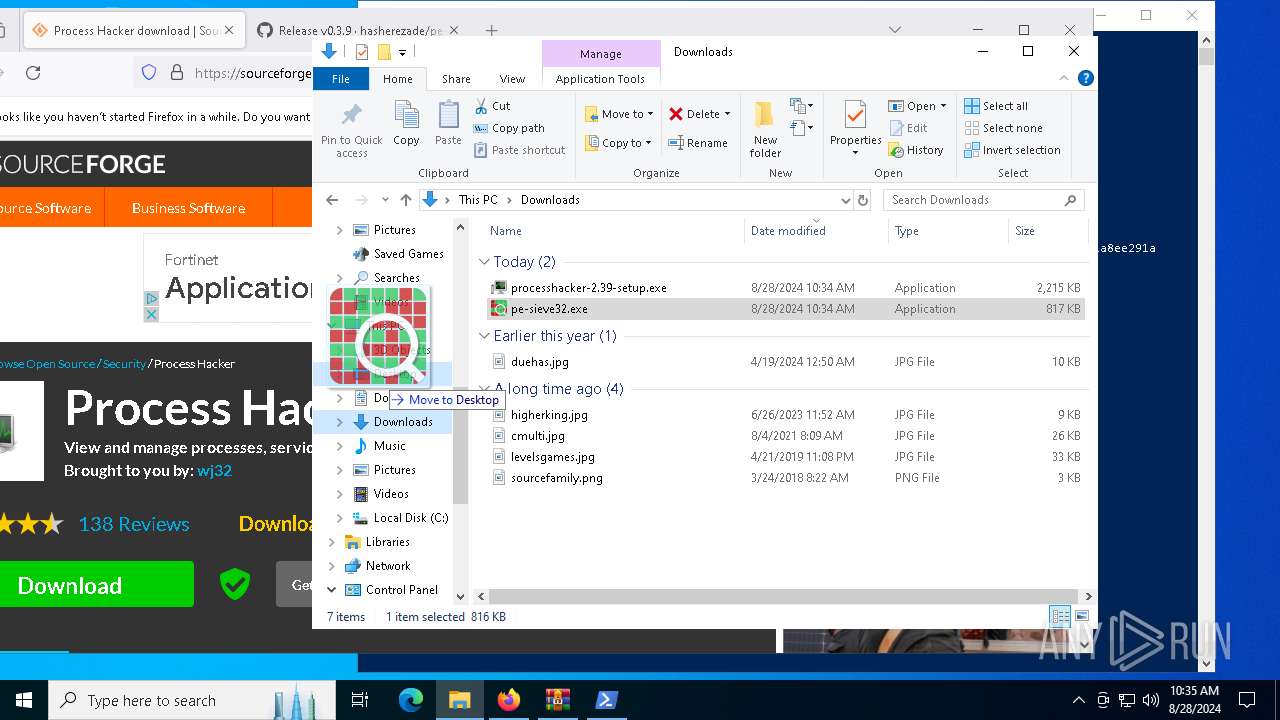
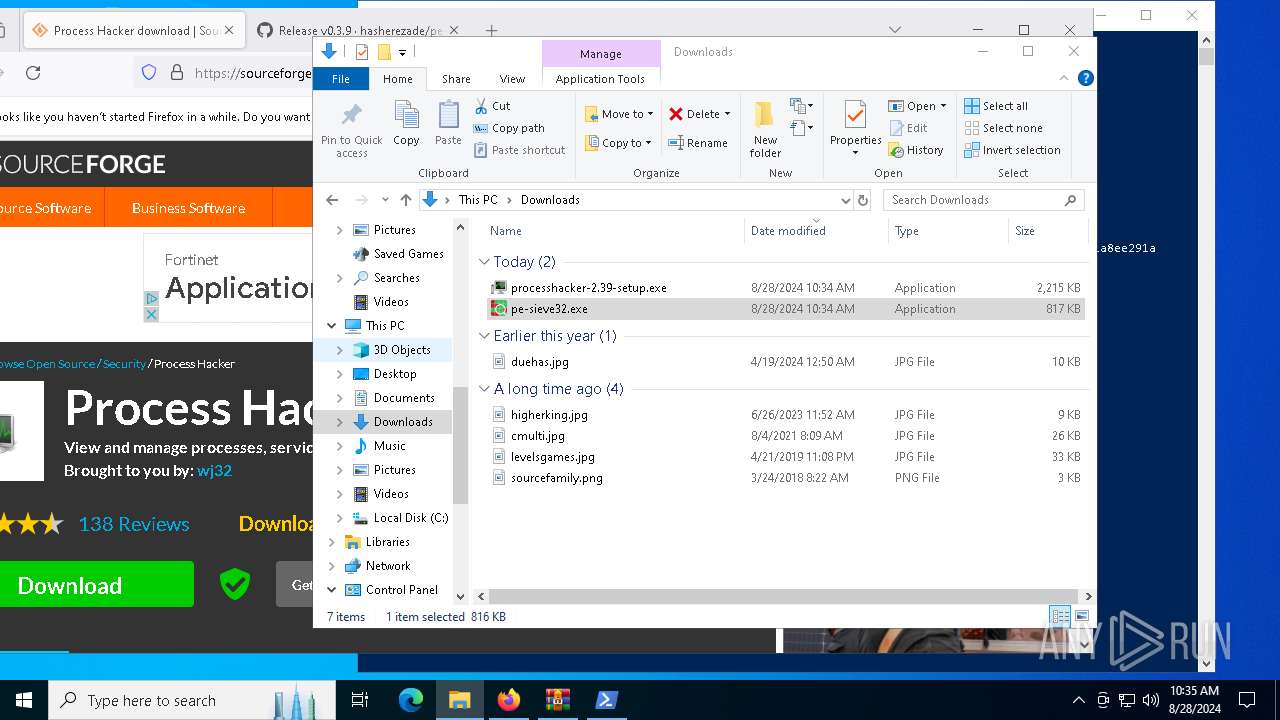
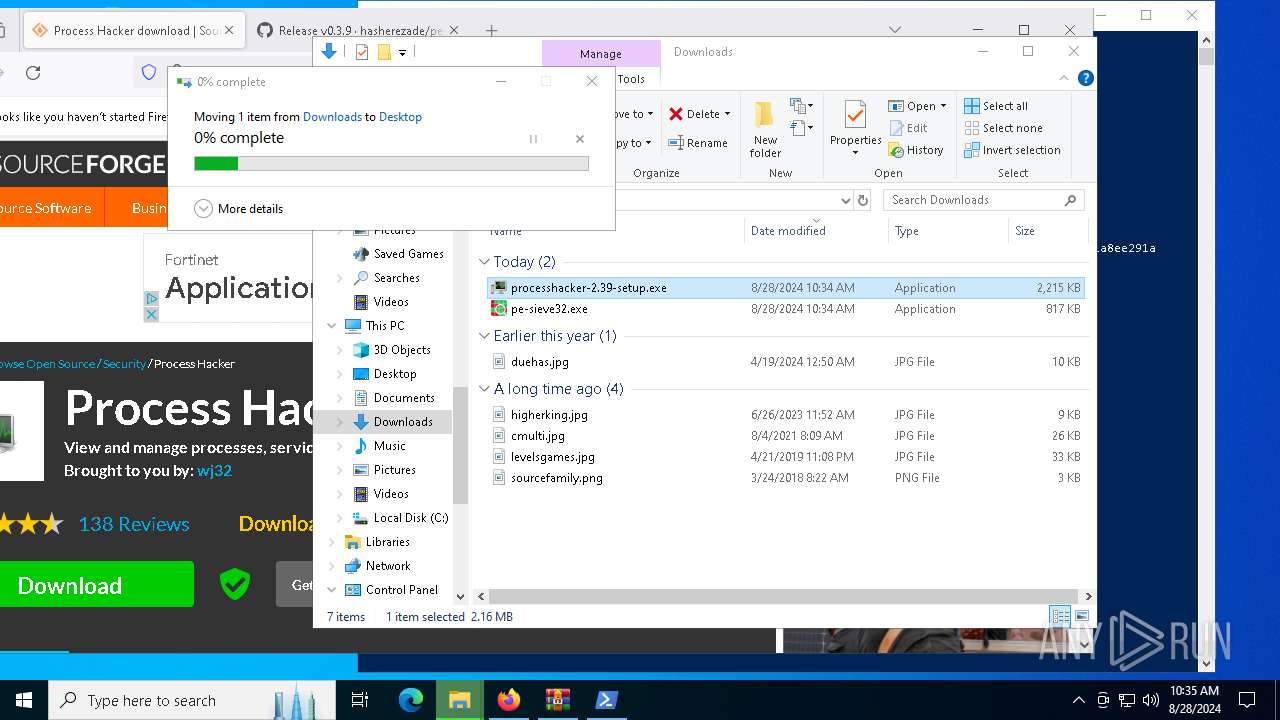
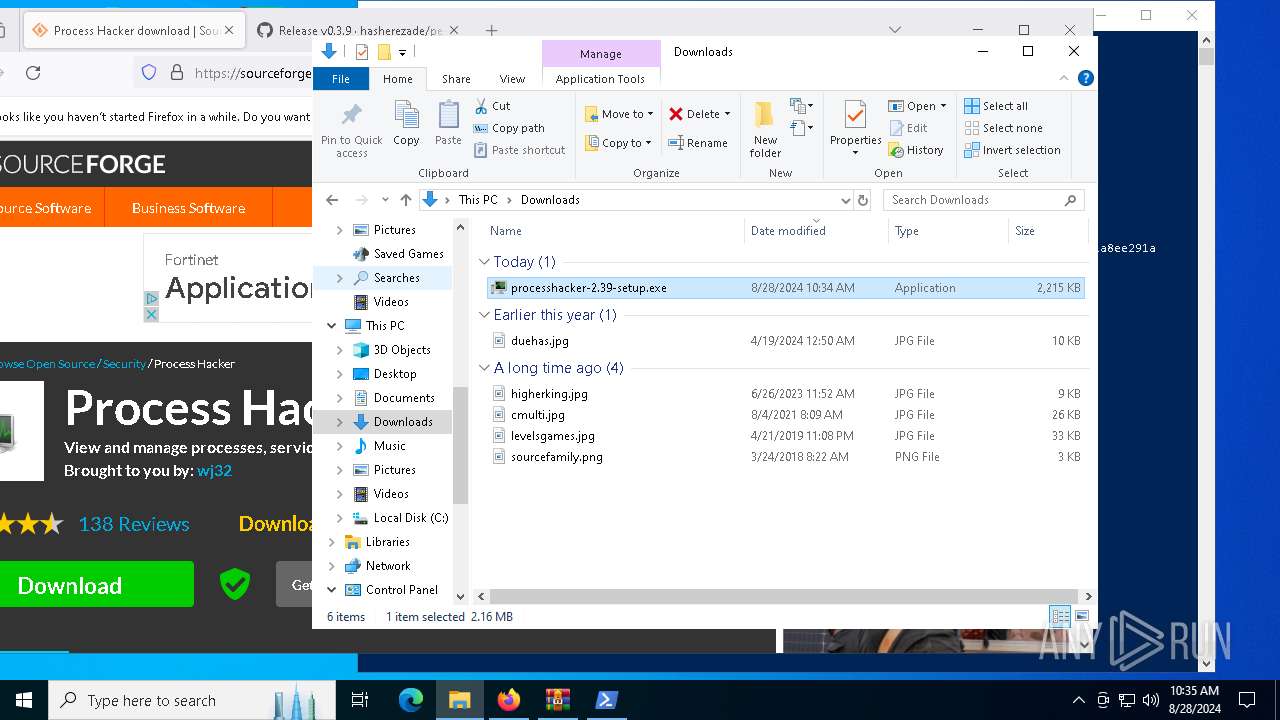
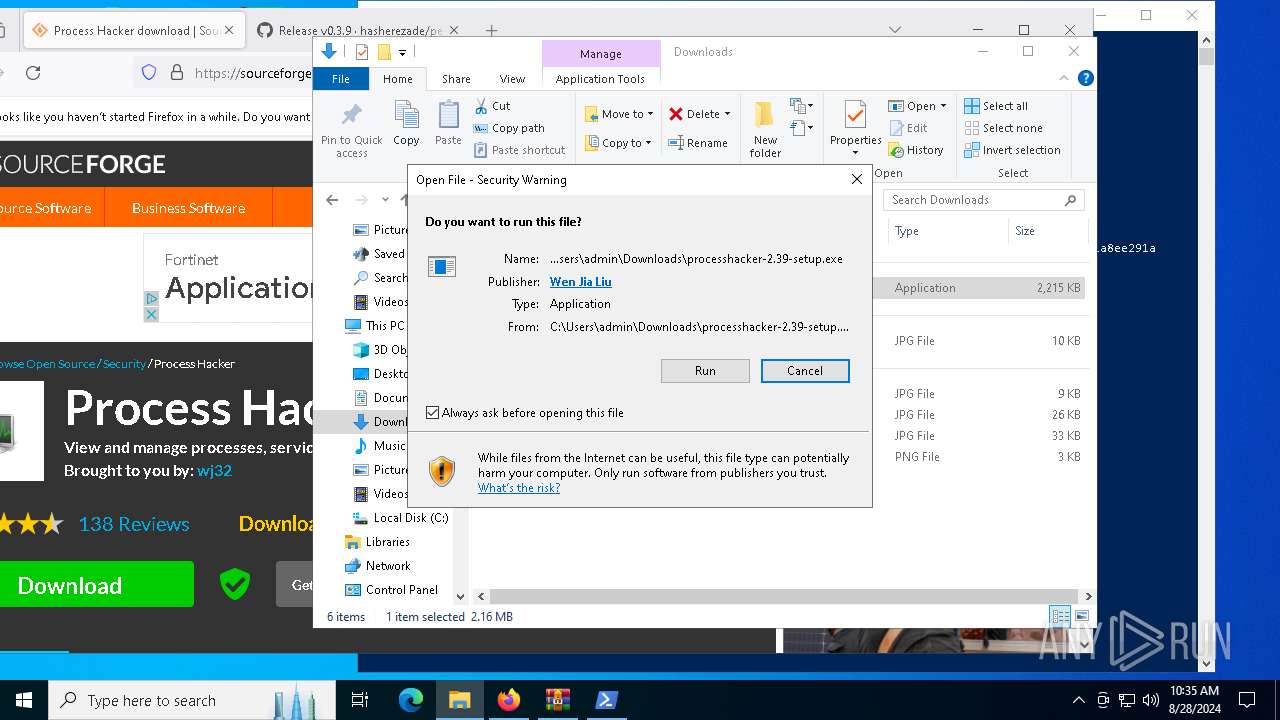
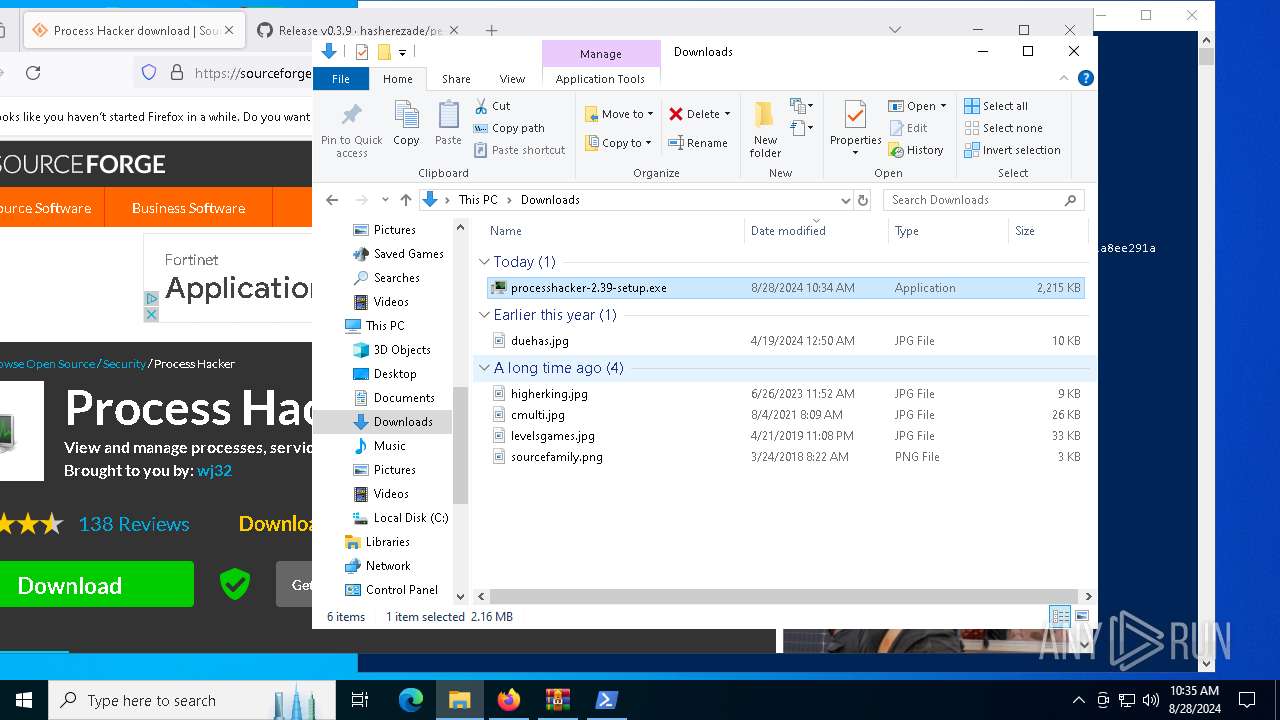
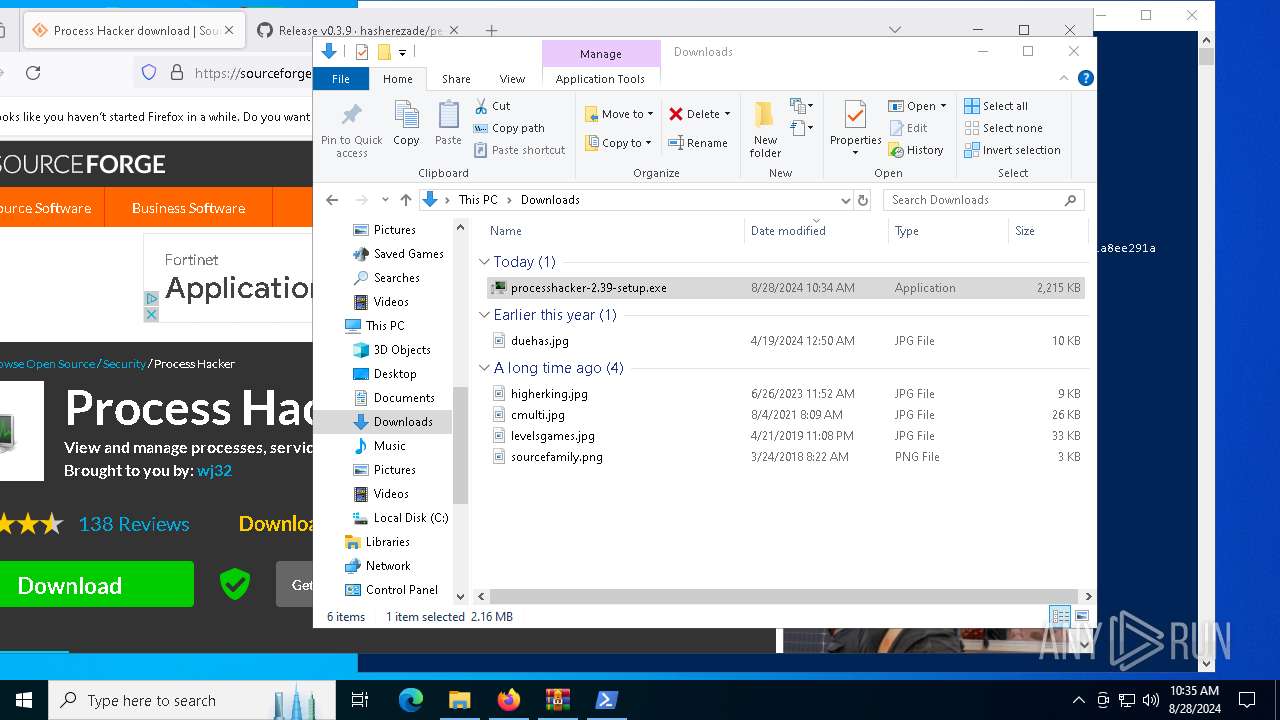
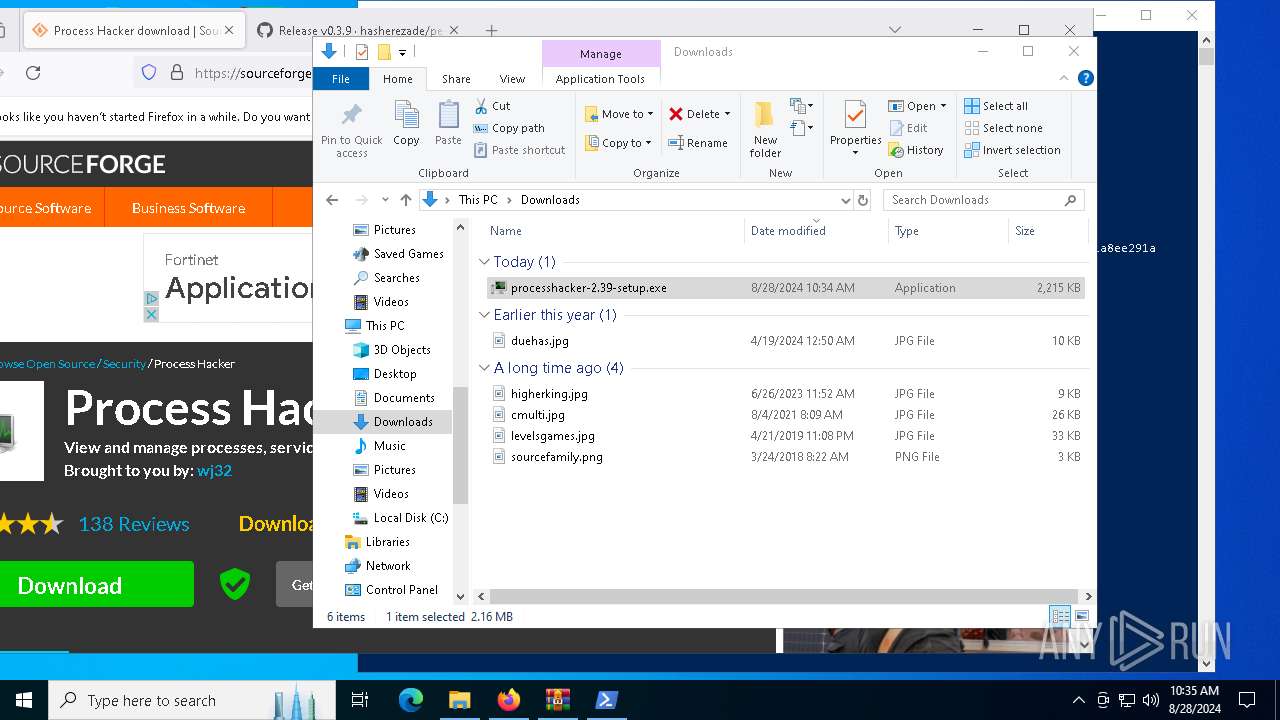
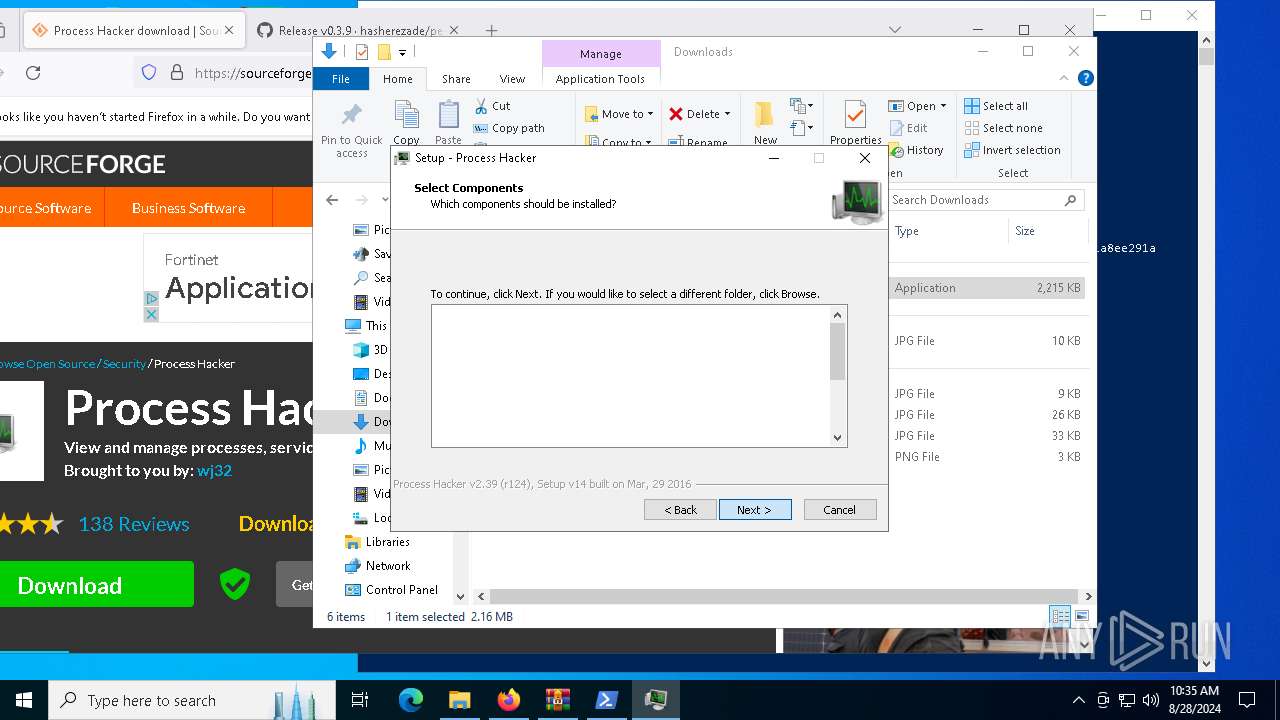
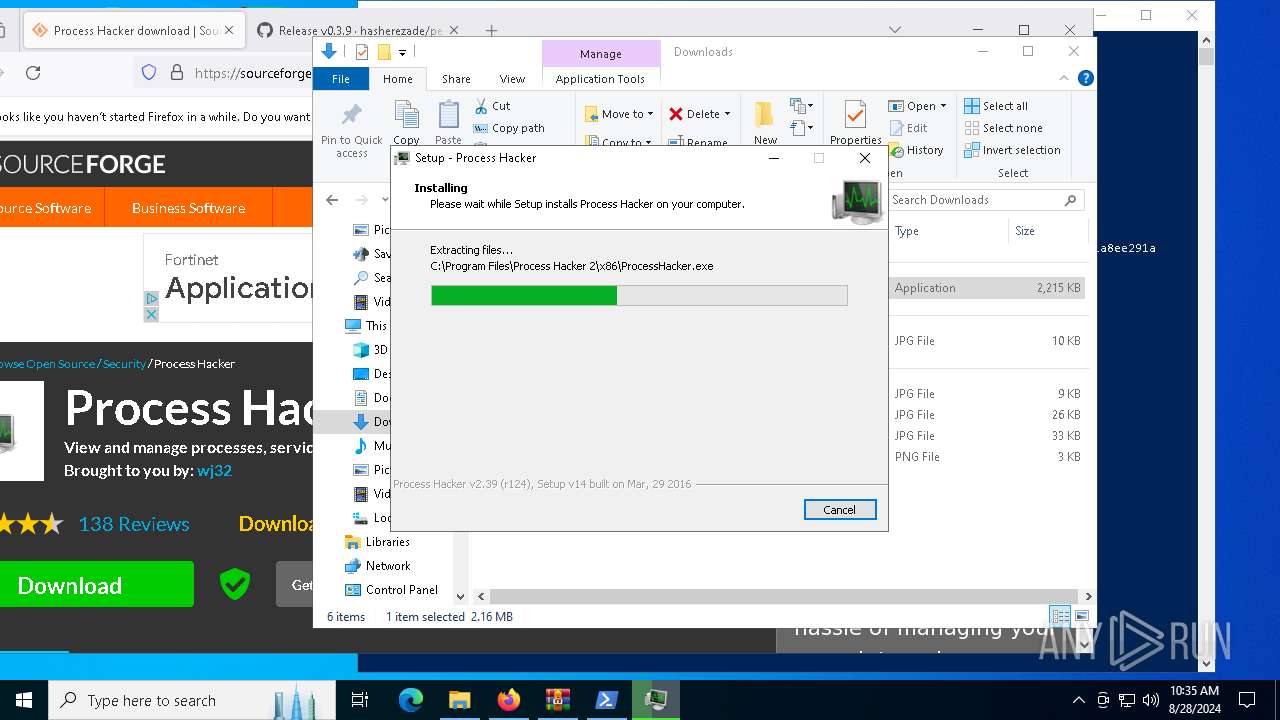
Drops the executable file immediately after the start
- WinRAR.exe (PID: 5484)
- processhacker-2.39-setup.exe (PID: 2144)
- processhacker-2.39-setup.exe (PID: 7132)
- processhacker-2.39-setup.tmp (PID: 7244)
Executable content was dropped or overwritten
- processhacker-2.39-setup.exe (PID: 2144)
- processhacker-2.39-setup.exe (PID: 7132)
- processhacker-2.39-setup.tmp (PID: 7244)
- explorer.exe (PID: 4552)
Reads security settings of Internet Explorer
- processhacker-2.39-setup.tmp (PID: 3728)
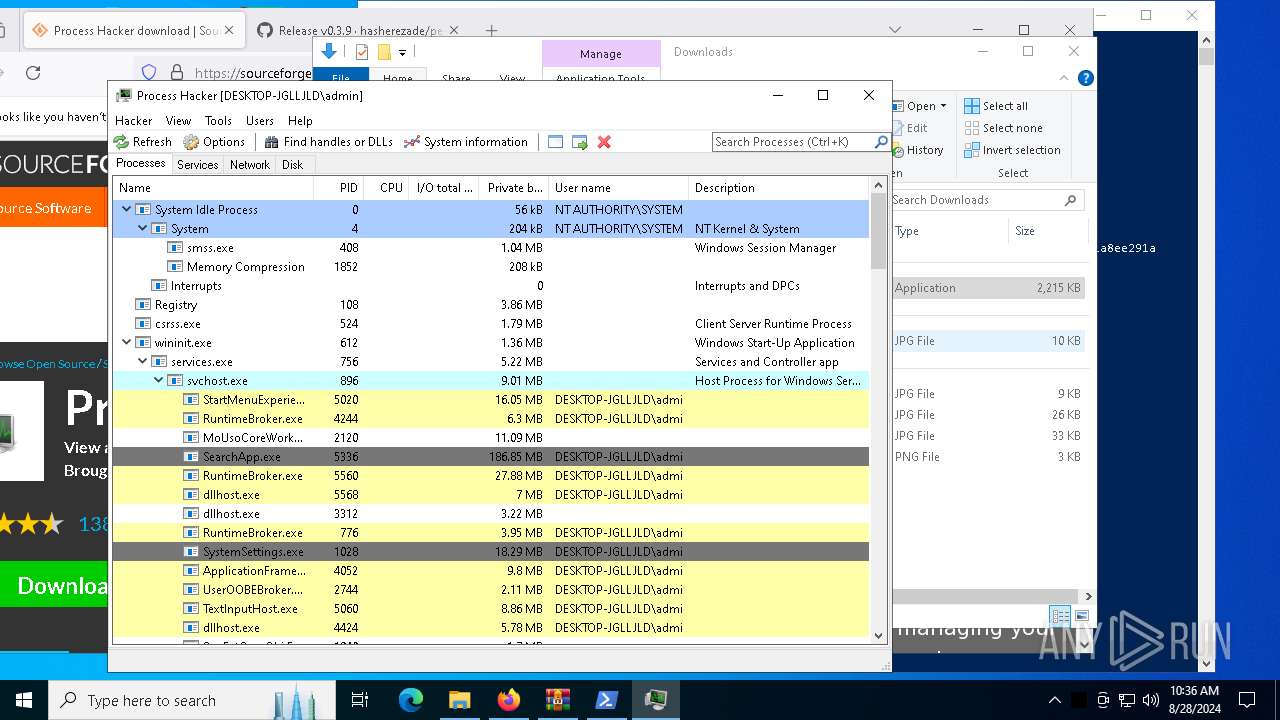
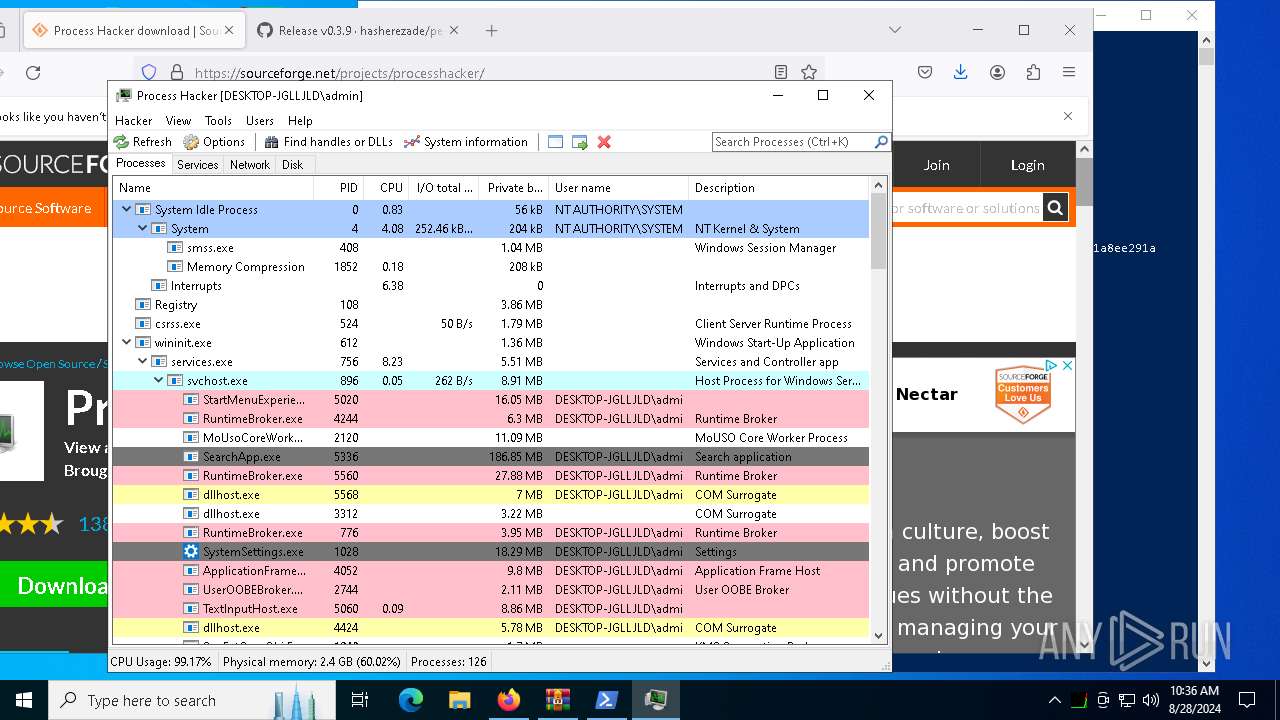
- ProcessHacker.exe (PID: 7860)
- 532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a.exe (PID: 2080)
Reads the date of Windows installation
- processhacker-2.39-setup.tmp (PID: 3728)
Reads the Windows owner or organization settings
- processhacker-2.39-setup.tmp (PID: 7244)
Process drops legitimate windows executable
- processhacker-2.39-setup.tmp (PID: 7244)
Drops a system driver (possible attempt to evade defenses)
- processhacker-2.39-setup.tmp (PID: 7244)
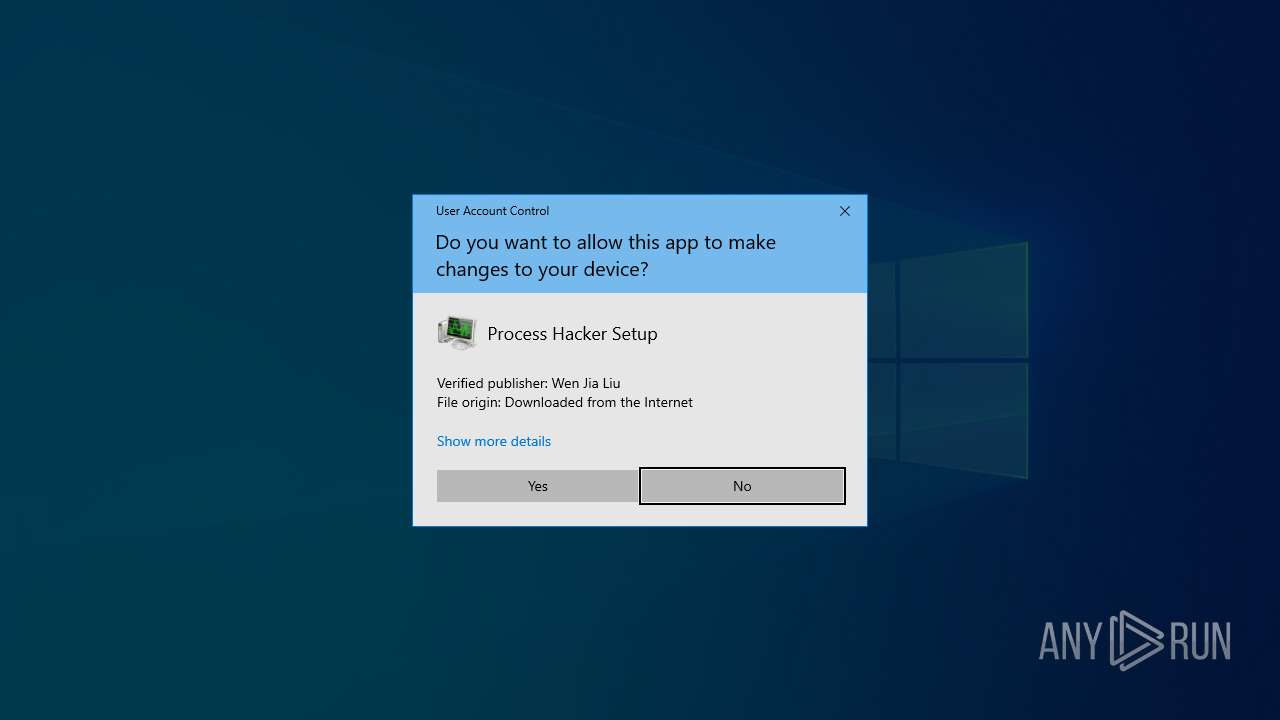
Checks Windows Trust Settings
- ProcessHacker.exe (PID: 7860)
- 532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a.exe (PID: 2080)
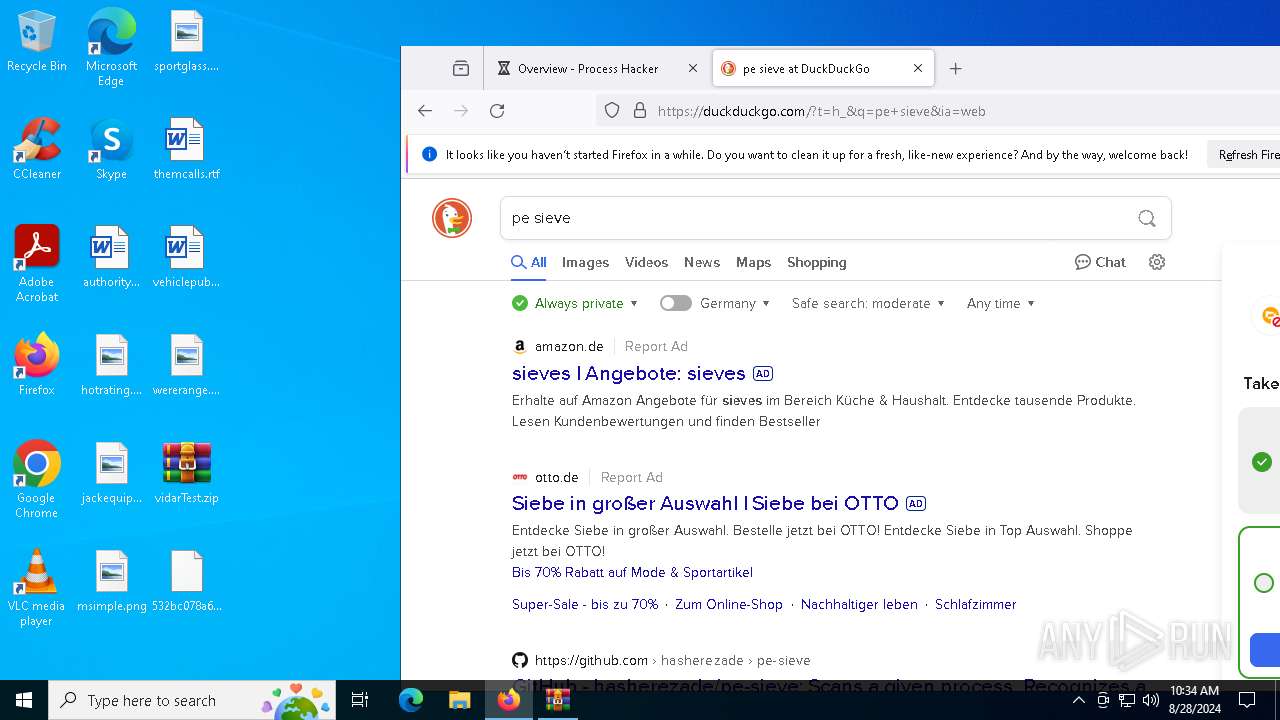
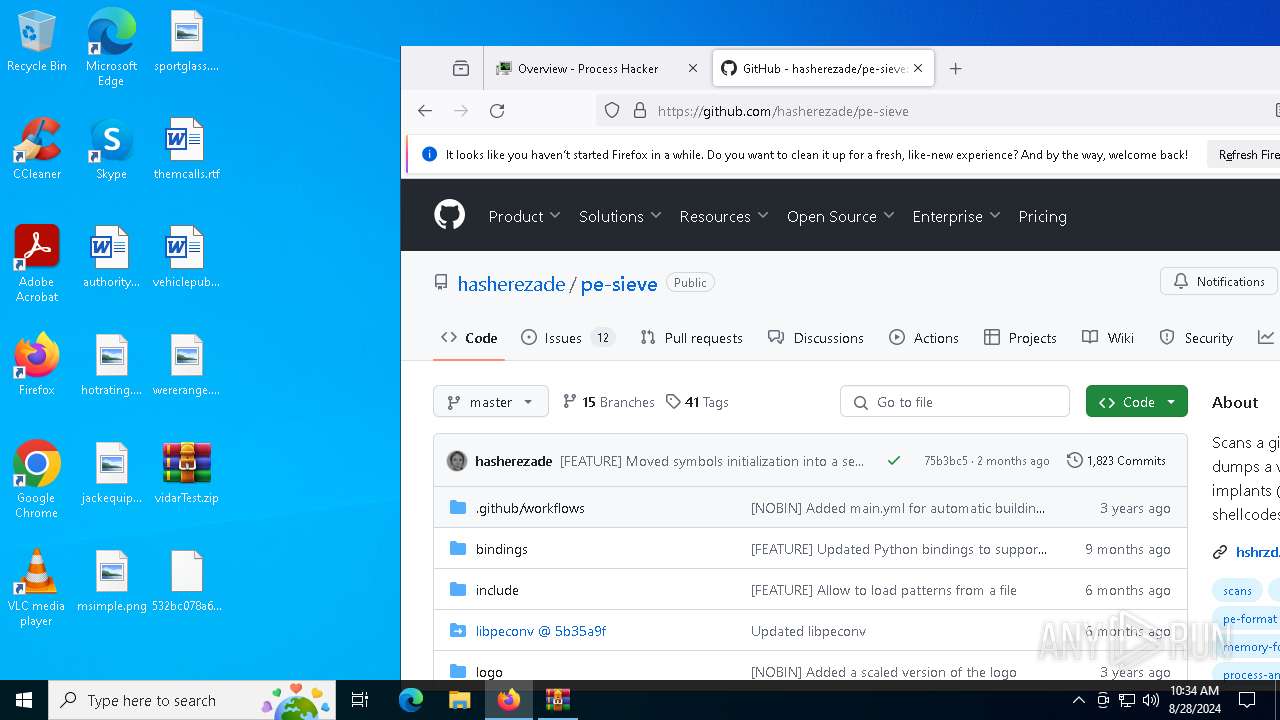
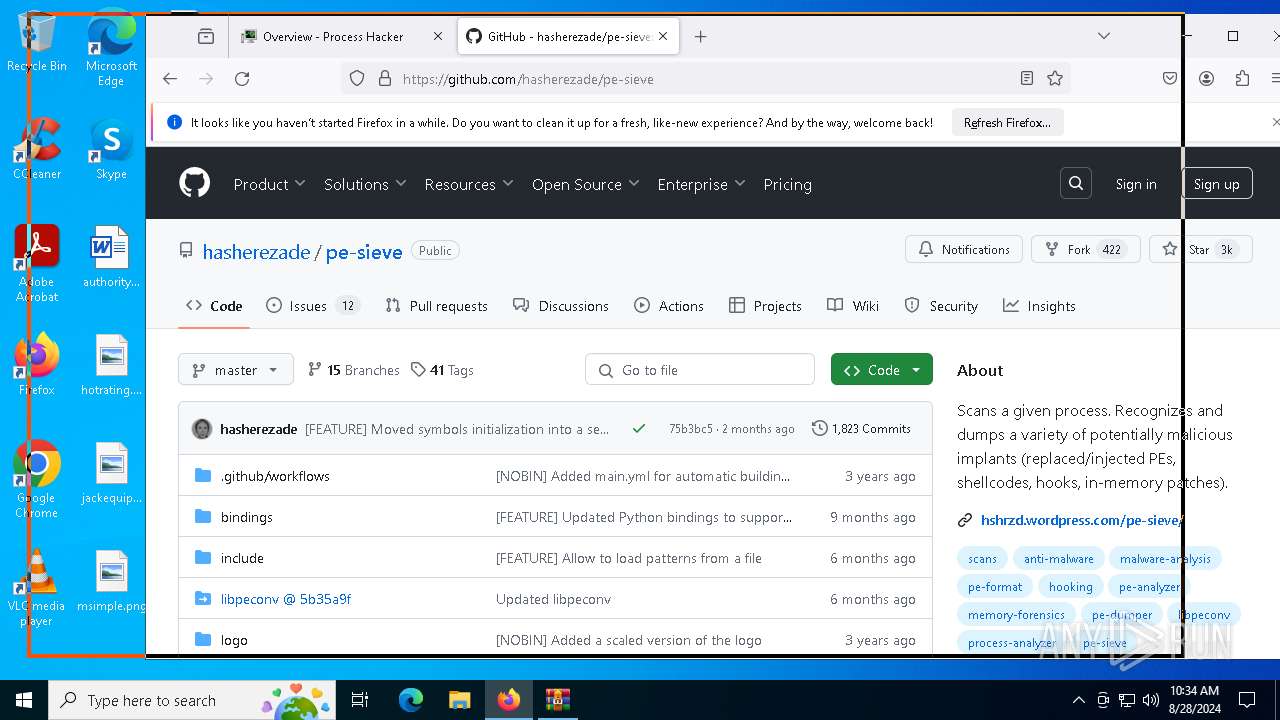
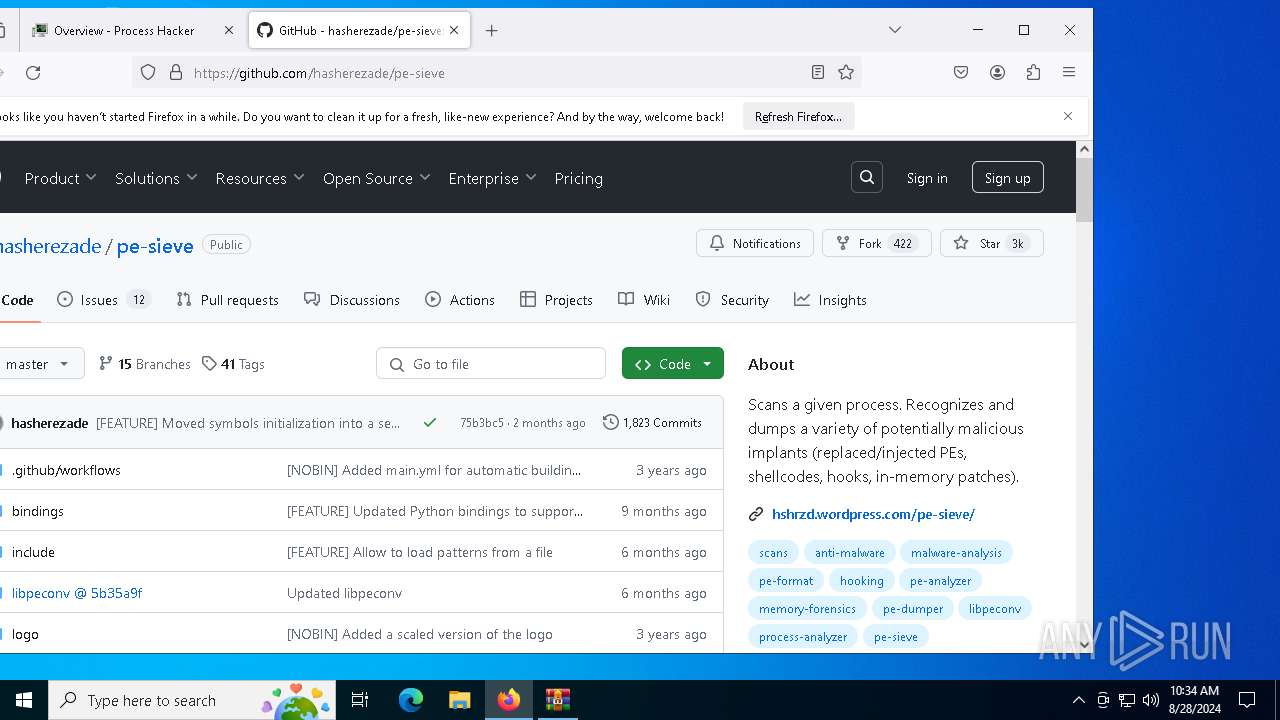
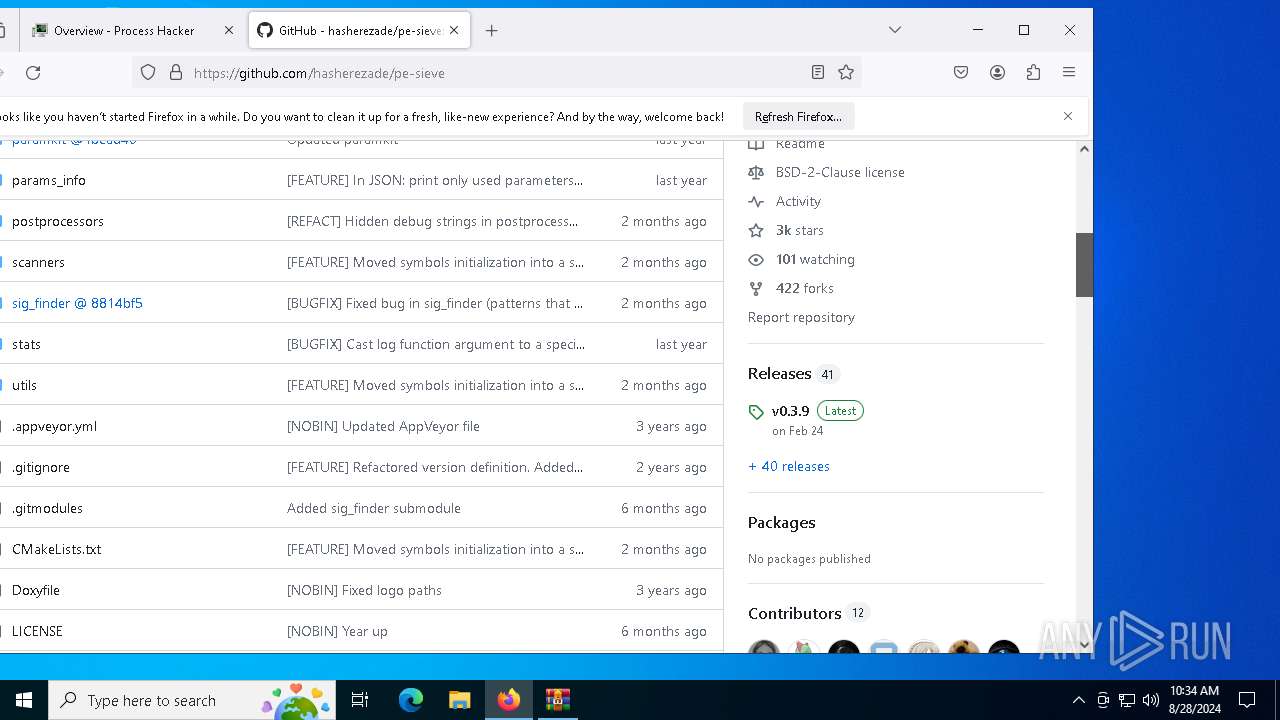
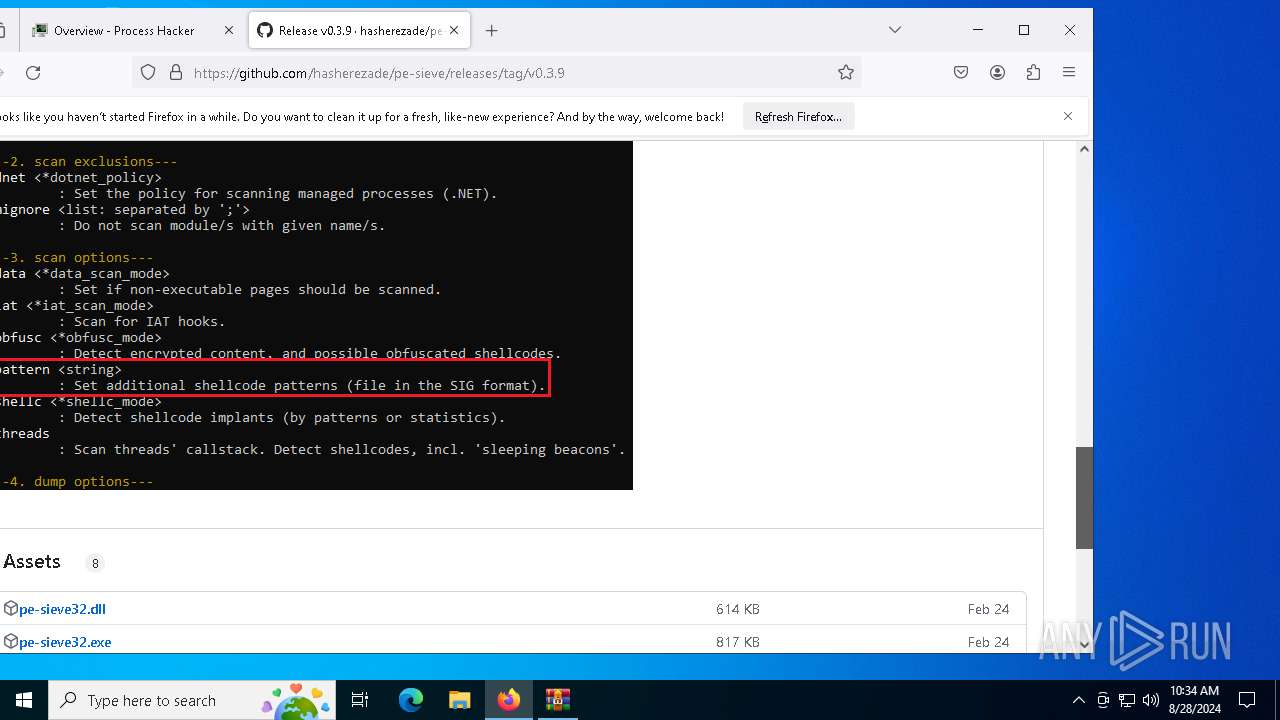
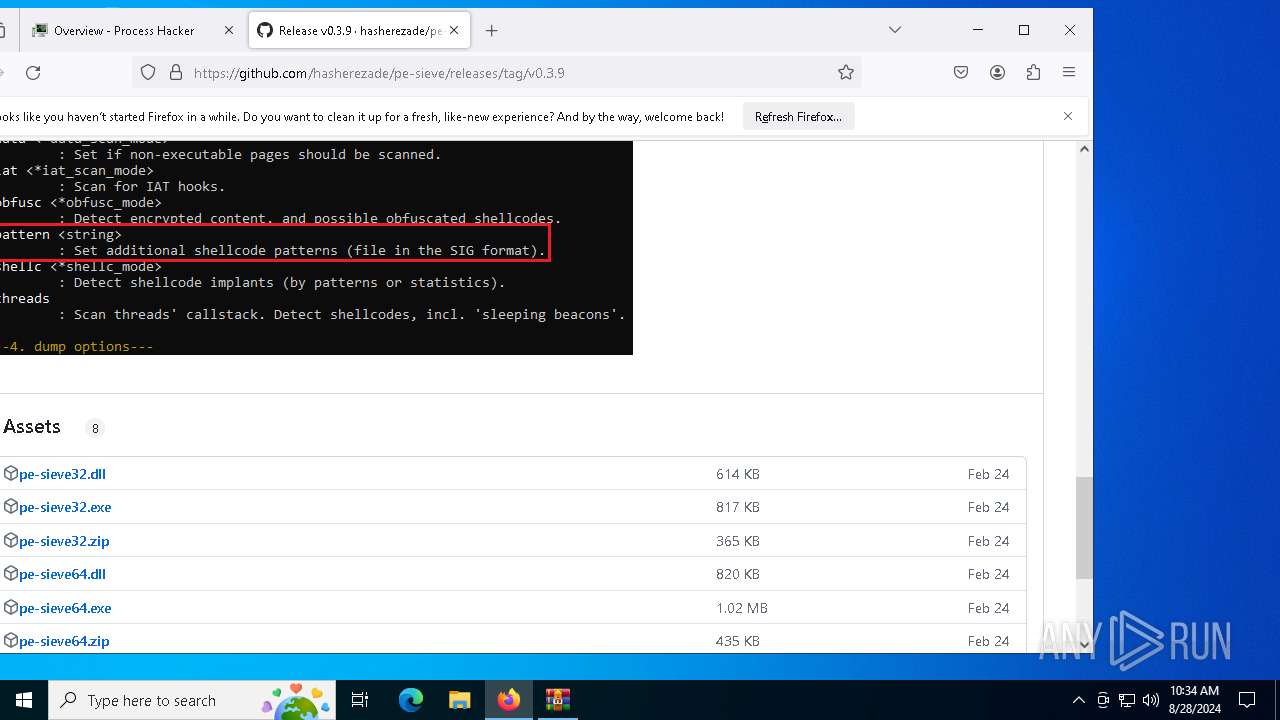
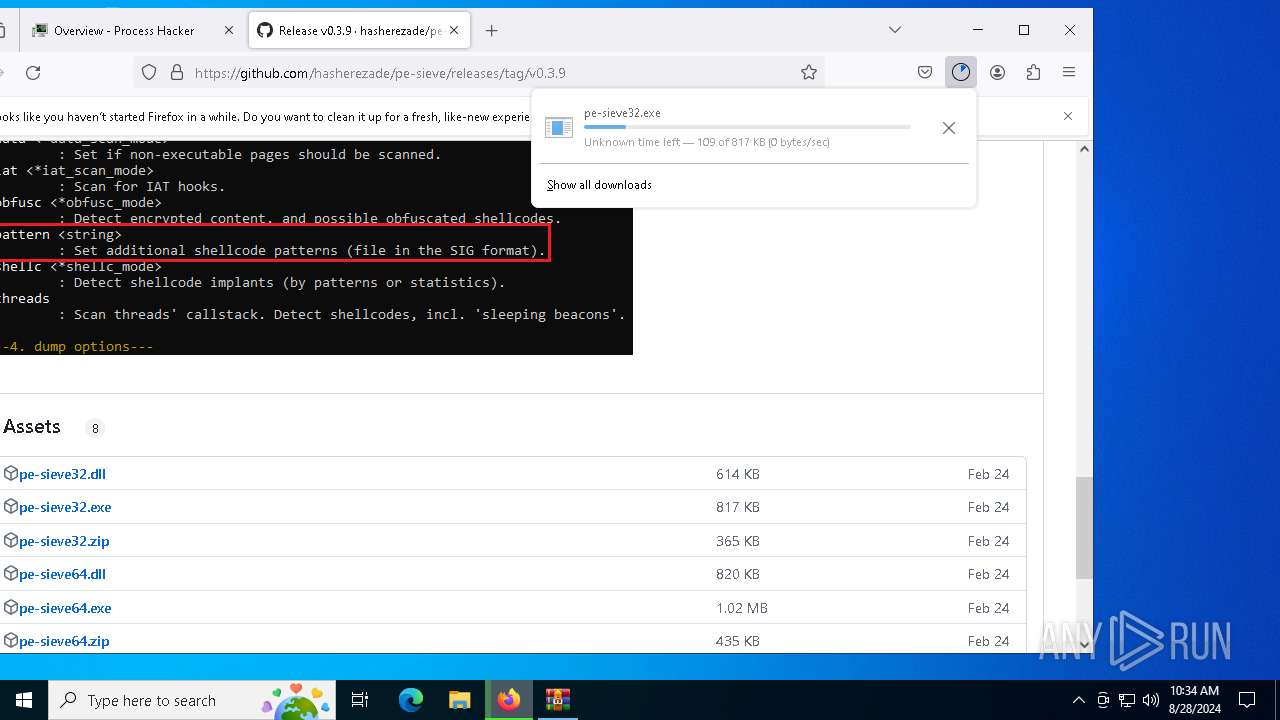
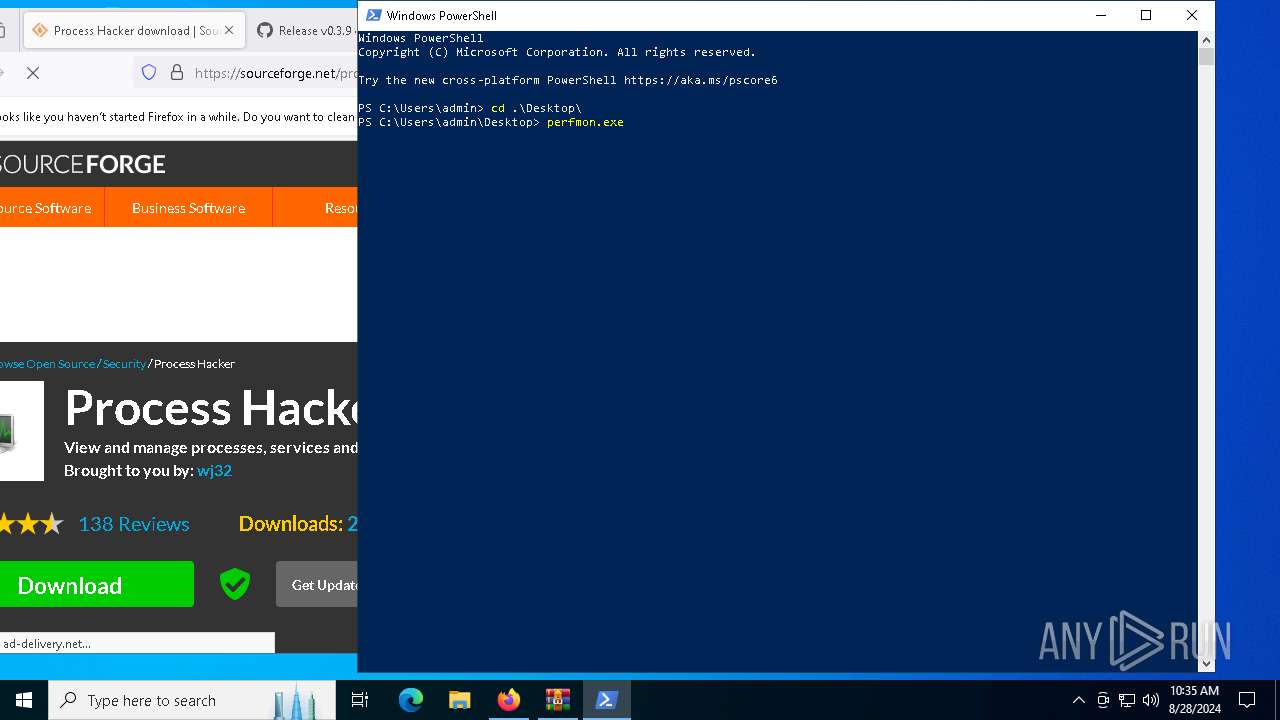
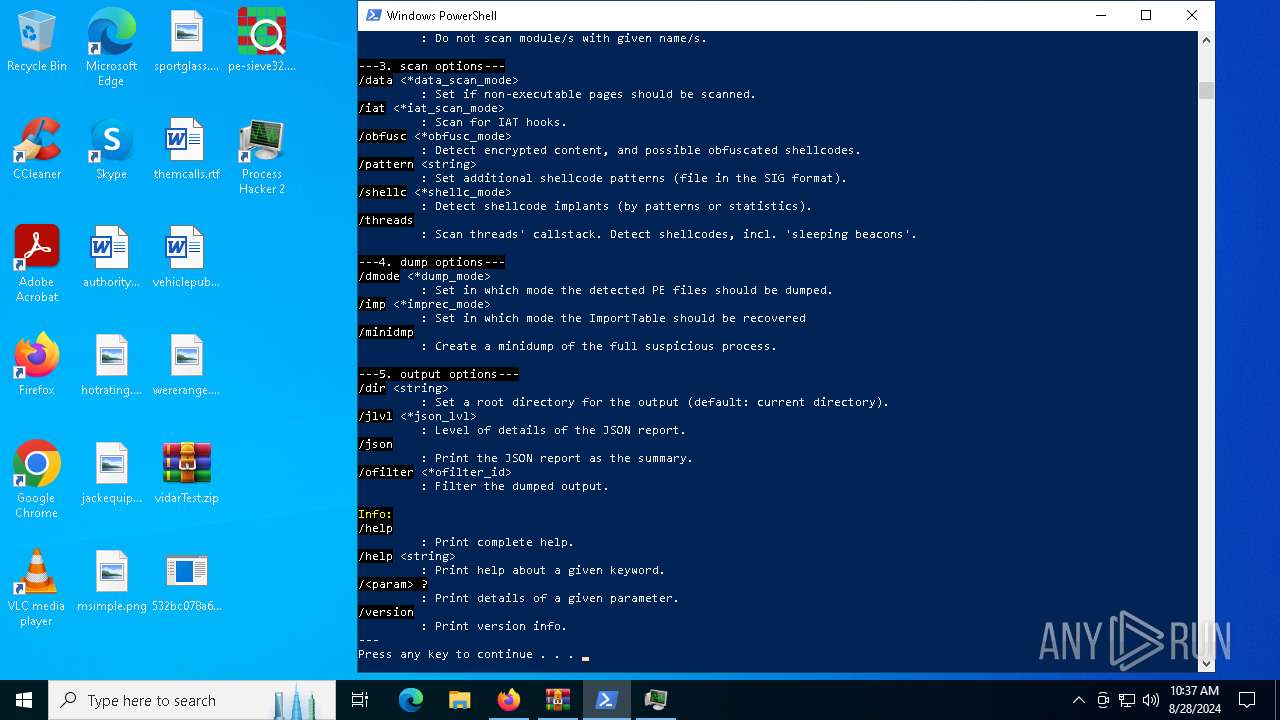
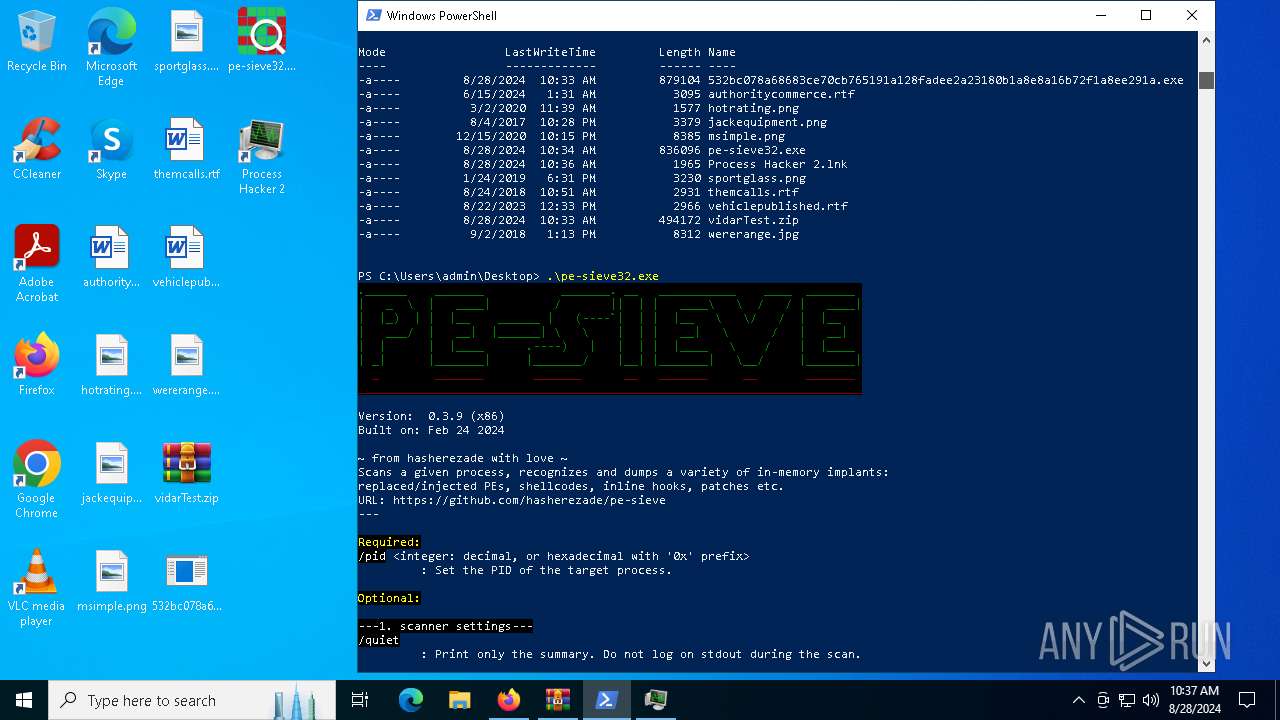
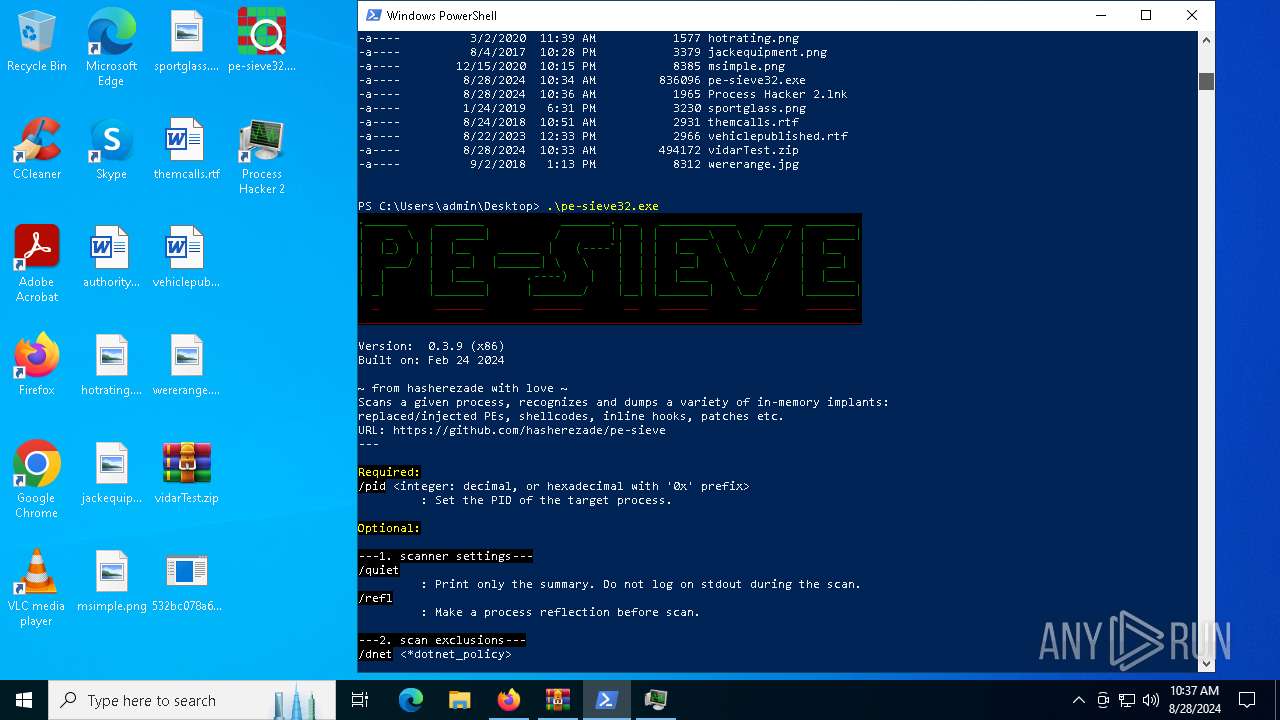
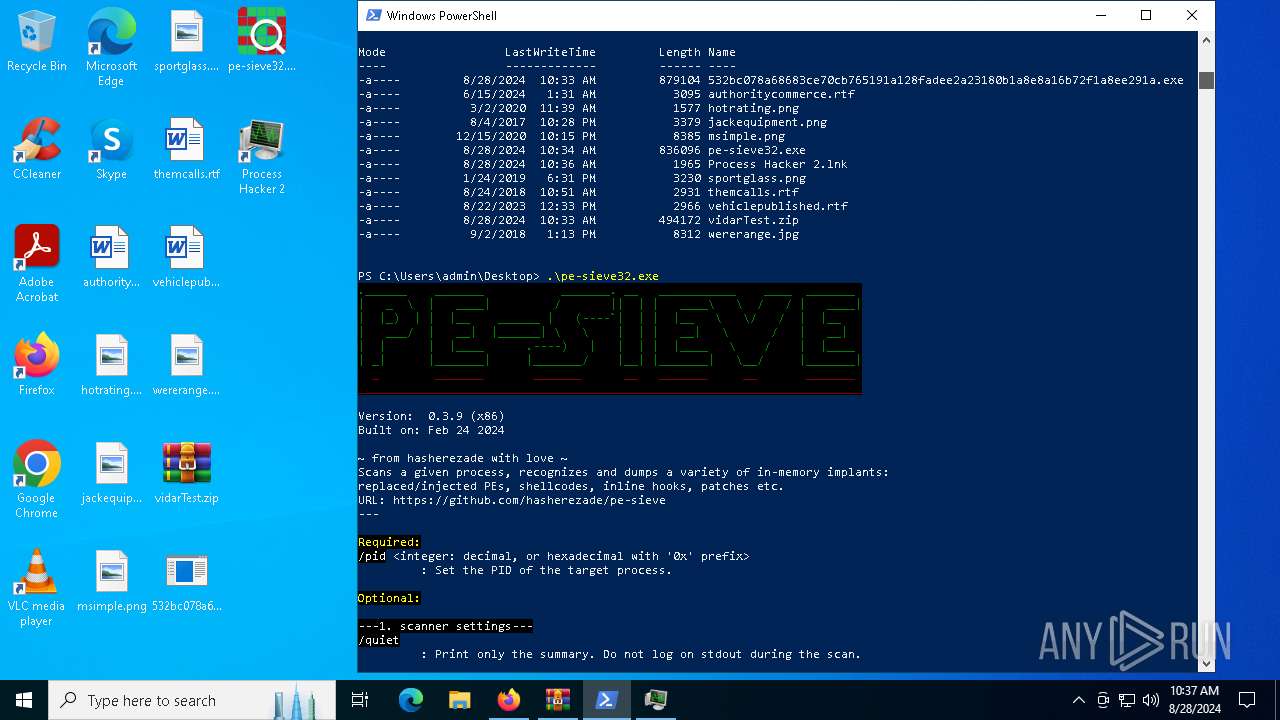
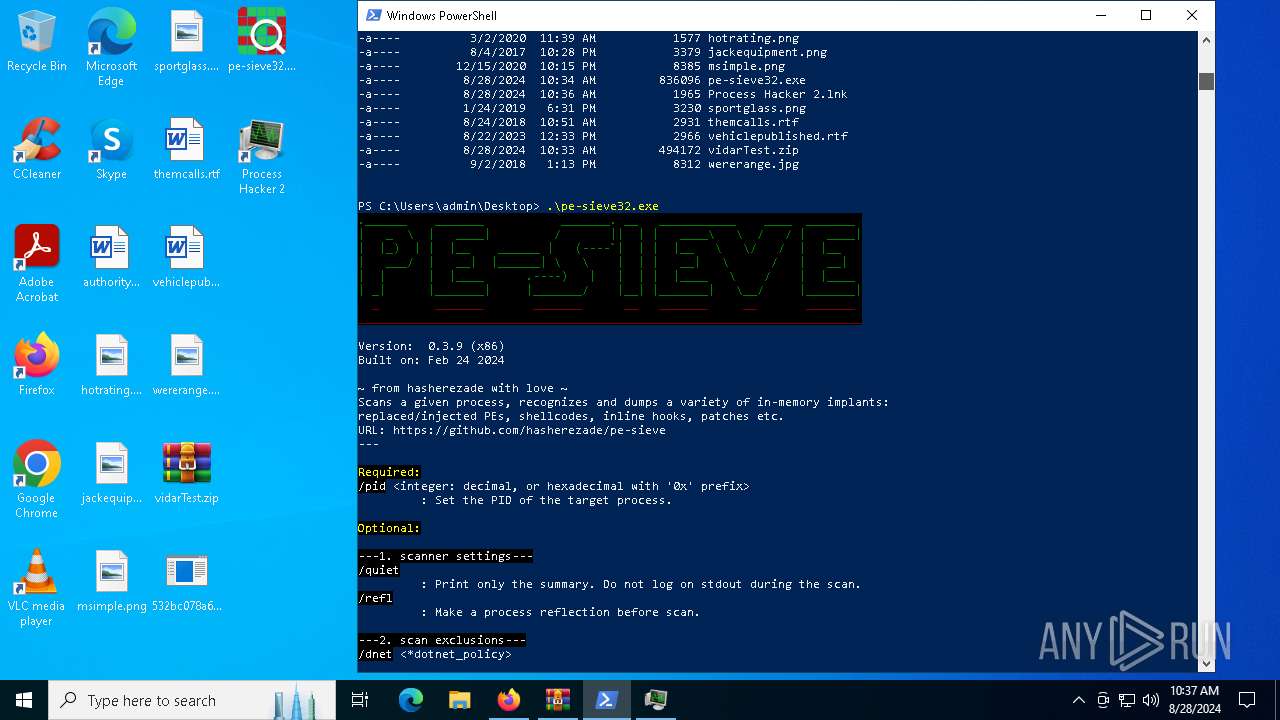
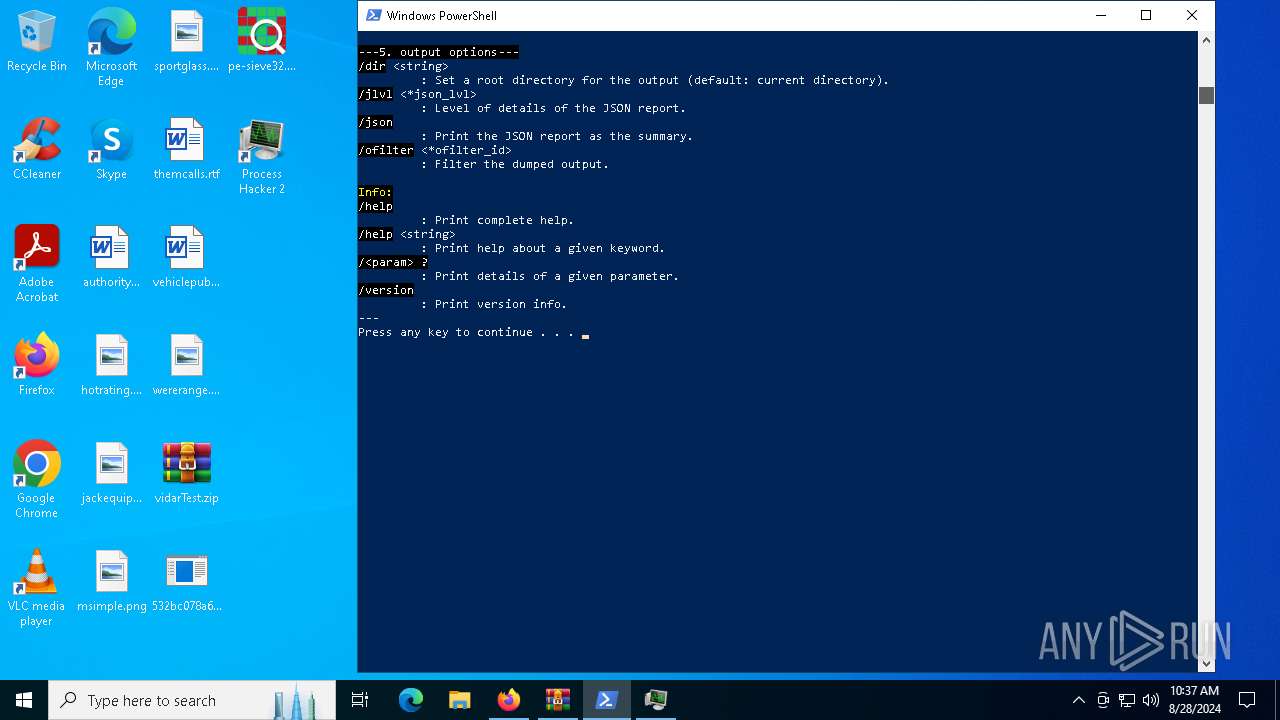
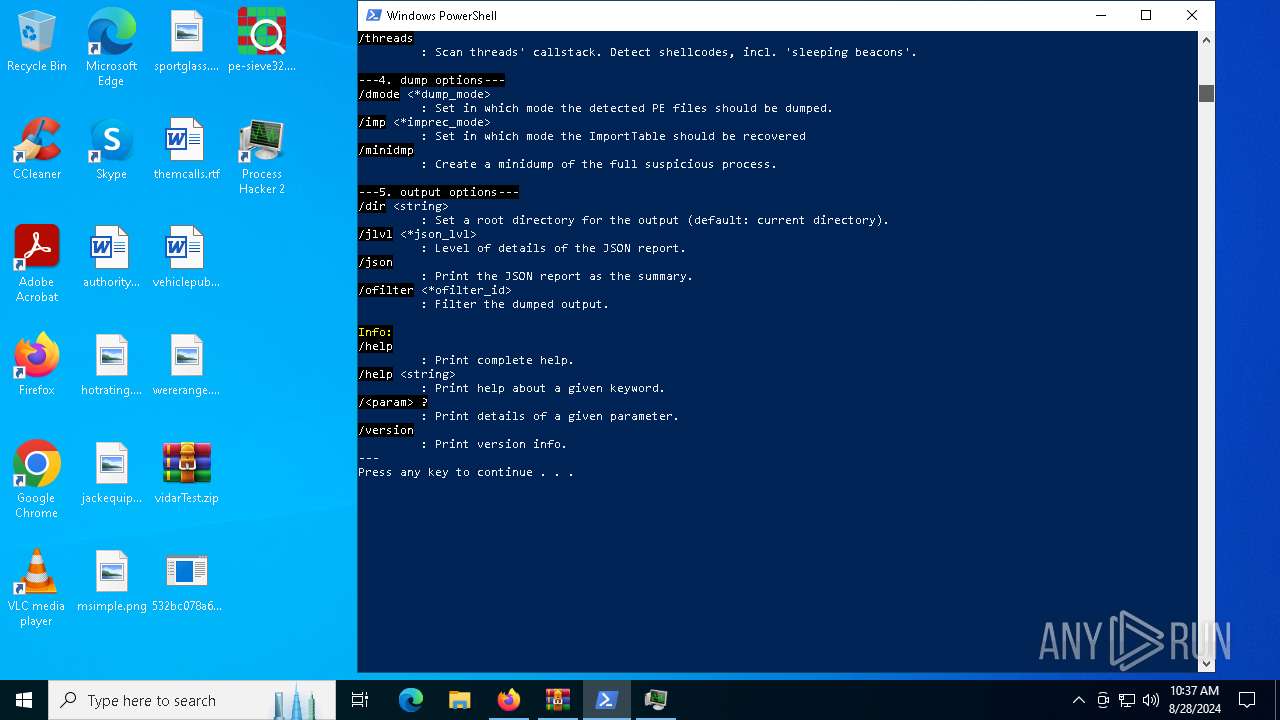
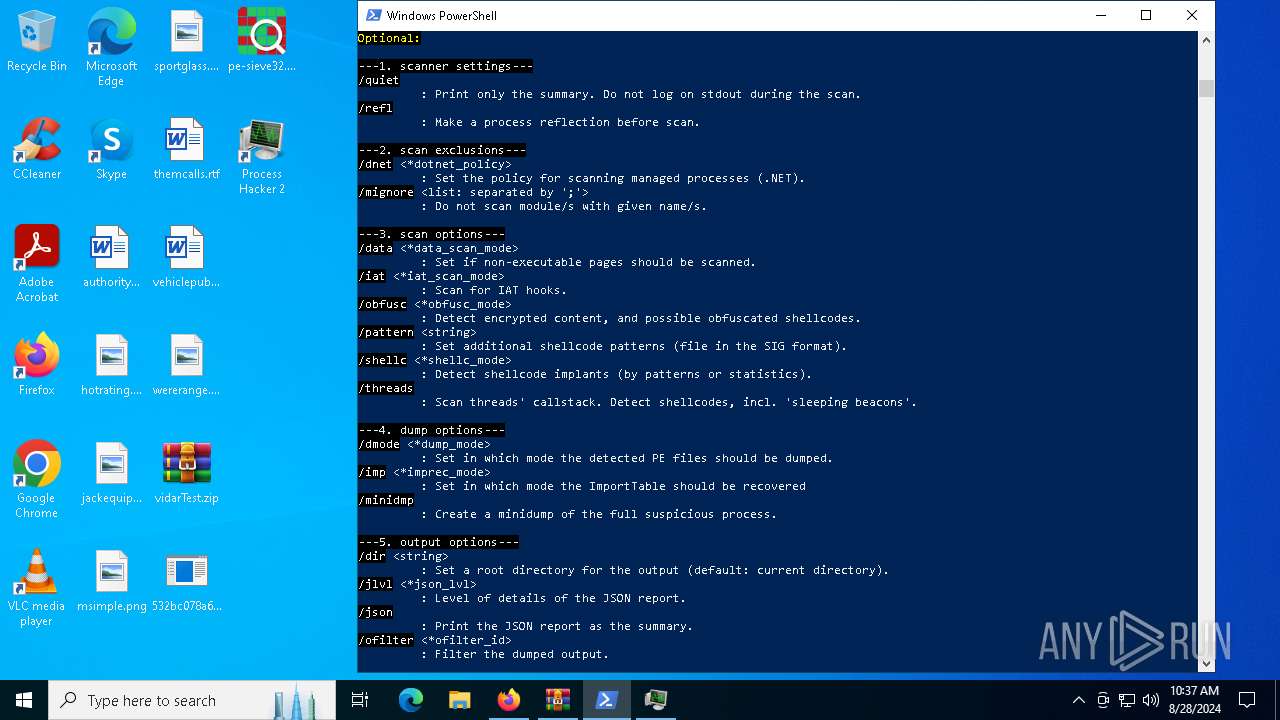
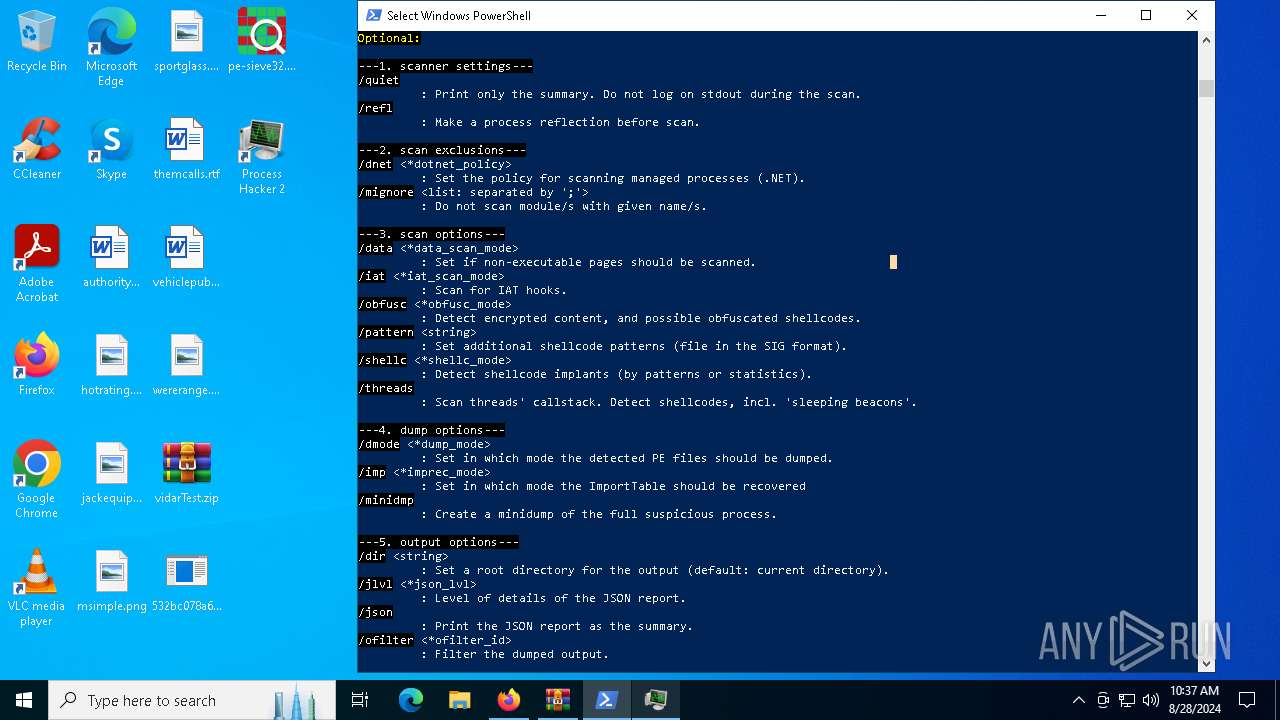
Starts CMD.EXE for commands execution
- pe-sieve32.exe (PID: 5096)
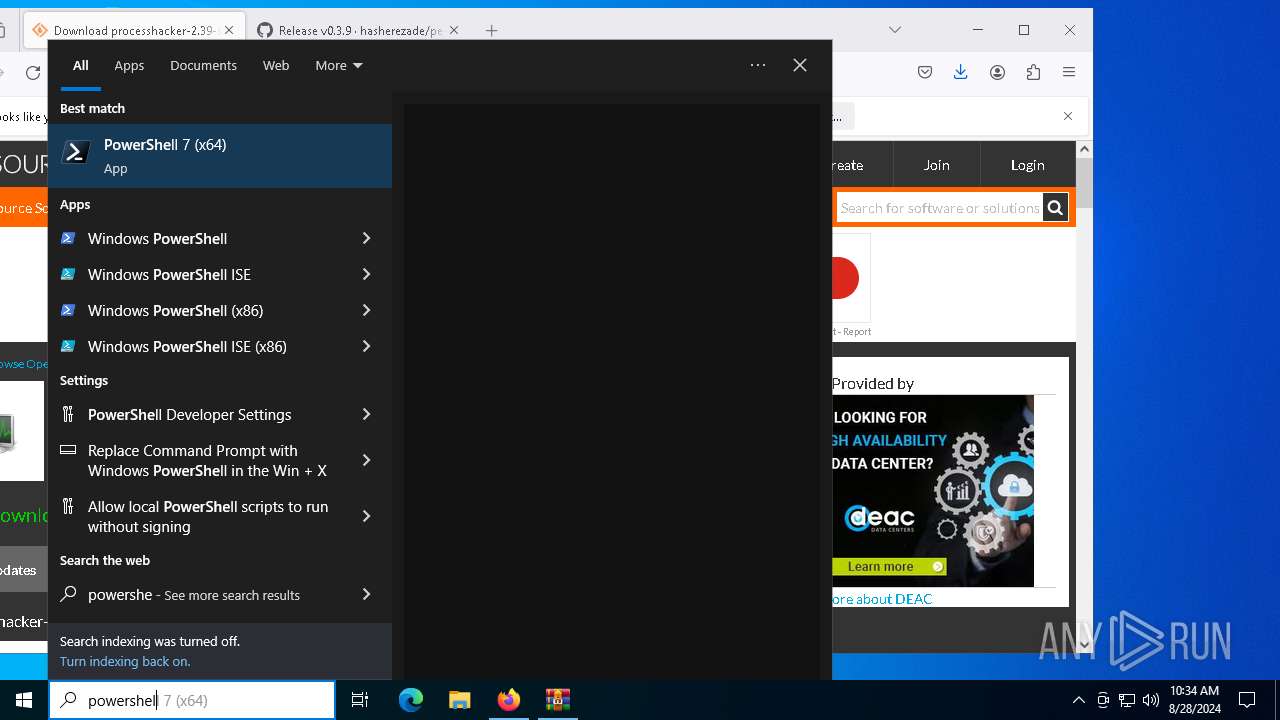
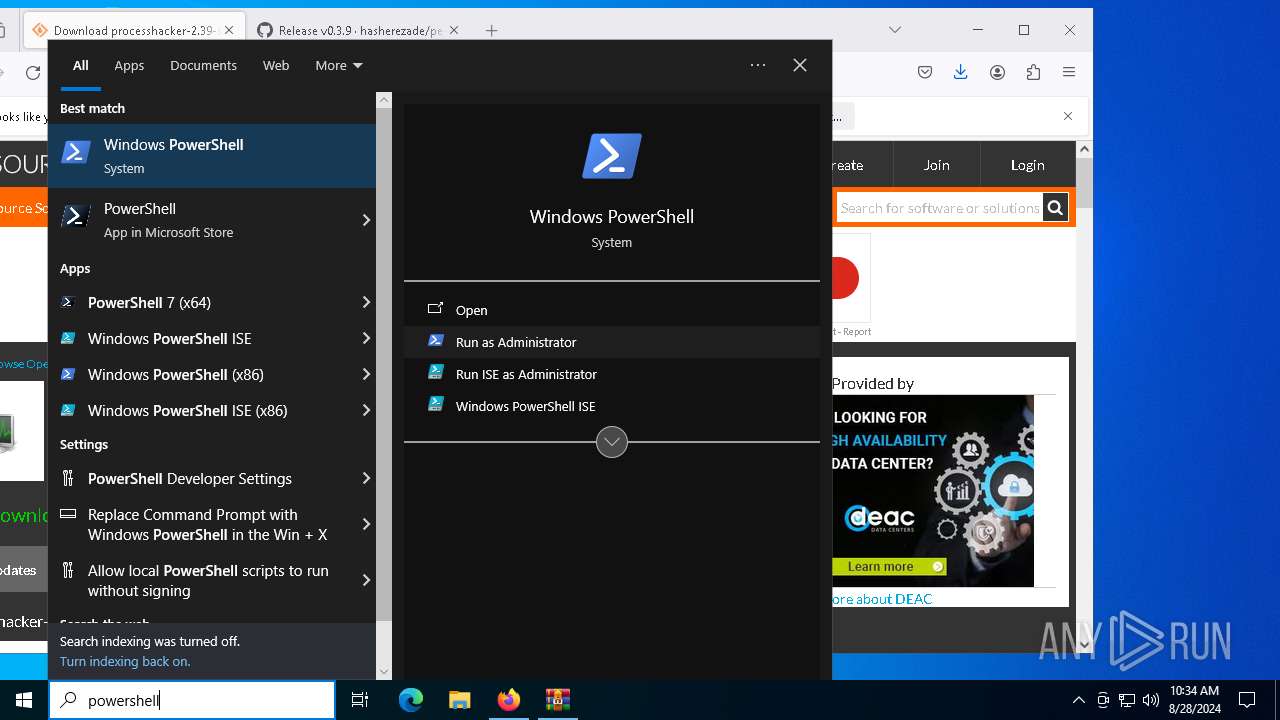
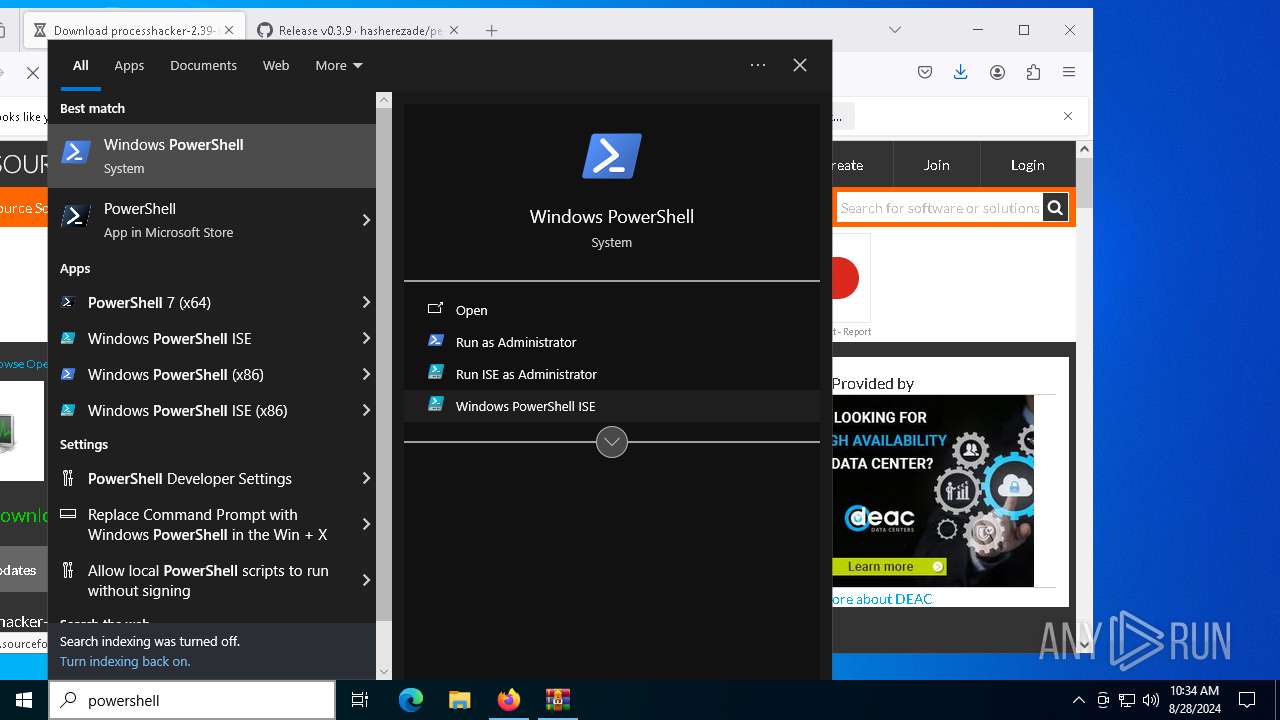
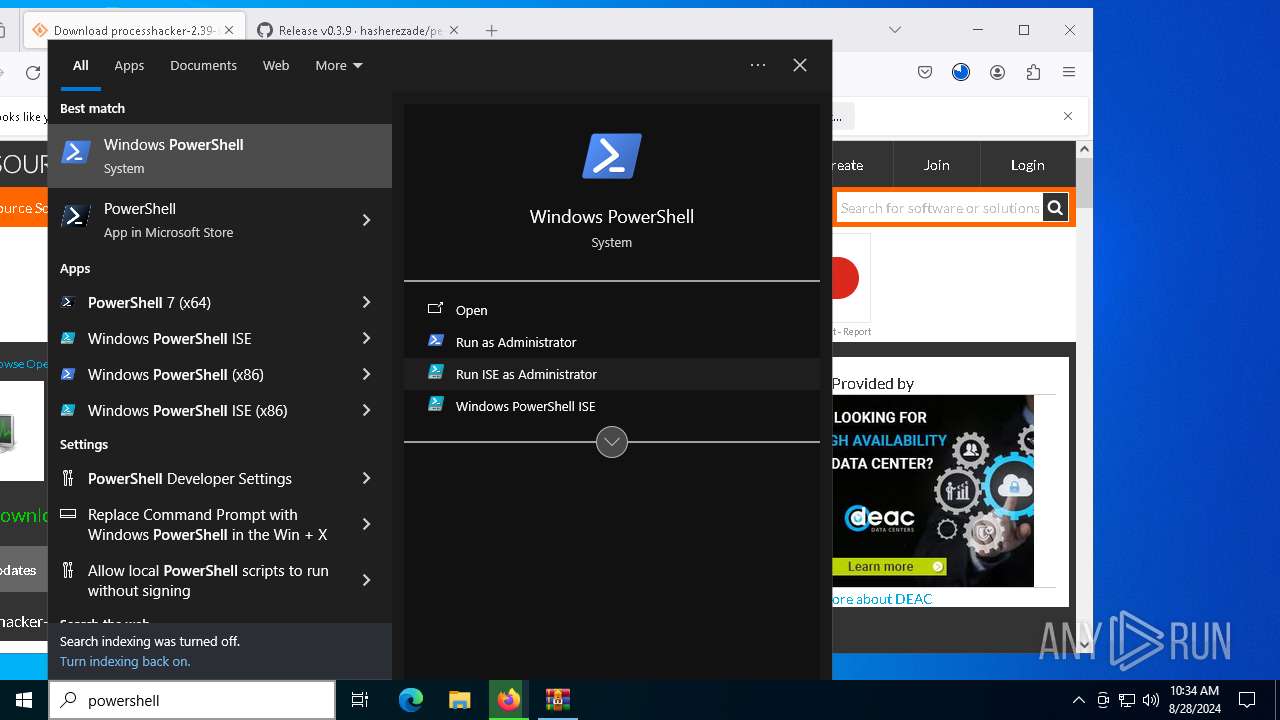
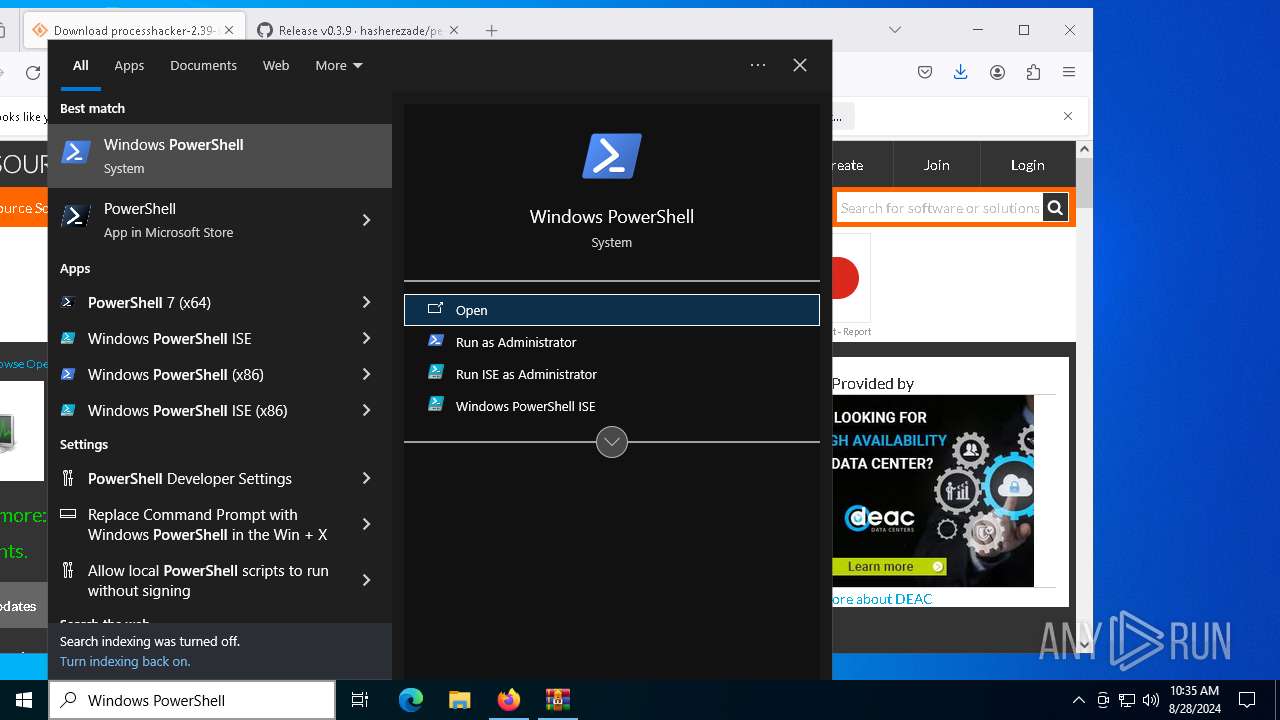
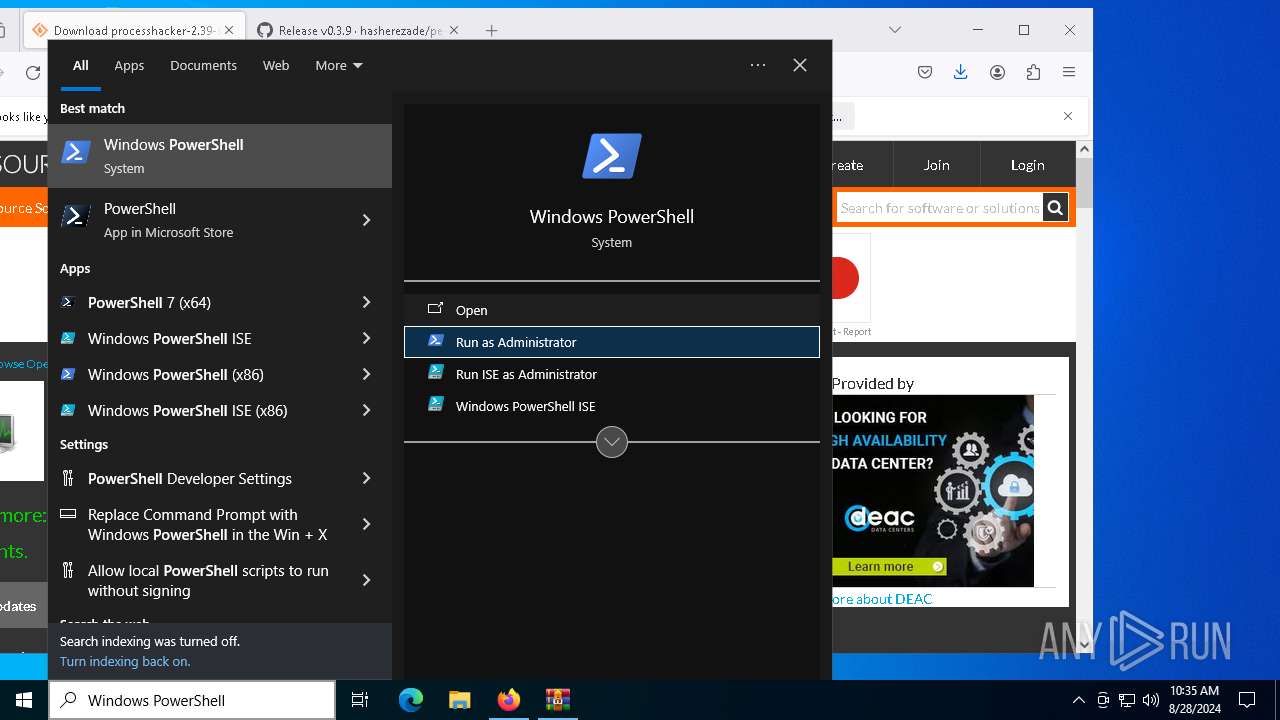
Starts POWERSHELL.EXE for commands execution
- explorer.exe (PID: 4552)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 4552)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5484)
- firefox.exe (PID: 2876)
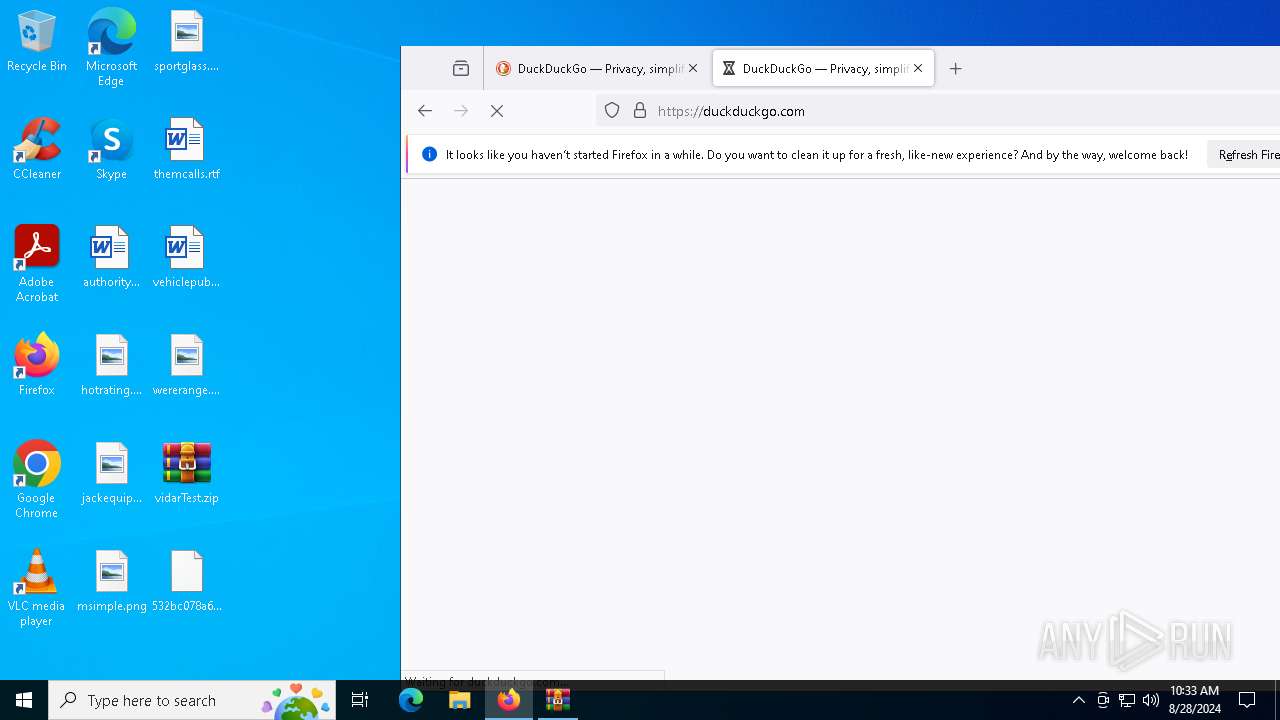
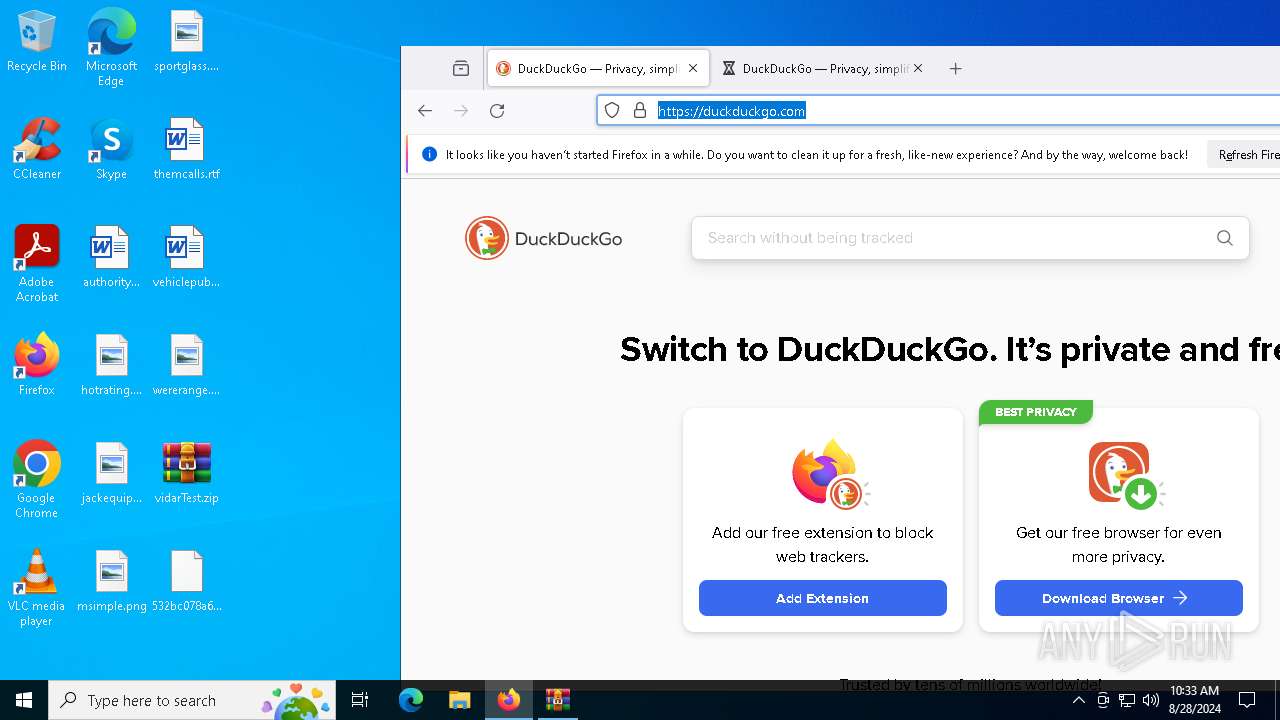
Application launched itself
- firefox.exe (PID: 2524)
- firefox.exe (PID: 2876)
Reads Microsoft Office registry keys
- firefox.exe (PID: 2876)
- OpenWith.exe (PID: 6532)
- explorer.exe (PID: 4552)
Checks current location (POWERSHELL)
- powershell.exe (PID: 4292)
Checks proxy server information
- slui.exe (PID: 7924)
- explorer.exe (PID: 4552)
- ProcessHacker.exe (PID: 7860)
- 532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a.exe (PID: 2080)
Checks supported languages
- processhacker-2.39-setup.exe (PID: 2144)
- processhacker-2.39-setup.tmp (PID: 3728)
- processhacker-2.39-setup.exe (PID: 7132)
- processhacker-2.39-setup.tmp (PID: 7244)
- ProcessHacker.exe (PID: 7860)
- 532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a.exe (PID: 2080)
- pe-sieve32.exe (PID: 7760)
- pe-sieve32.exe (PID: 5096)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4292)
Reads the software policy settings
- explorer.exe (PID: 4552)
- slui.exe (PID: 7924)
- ProcessHacker.exe (PID: 7860)
- 532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a.exe (PID: 2080)
- slui.exe (PID: 6484)
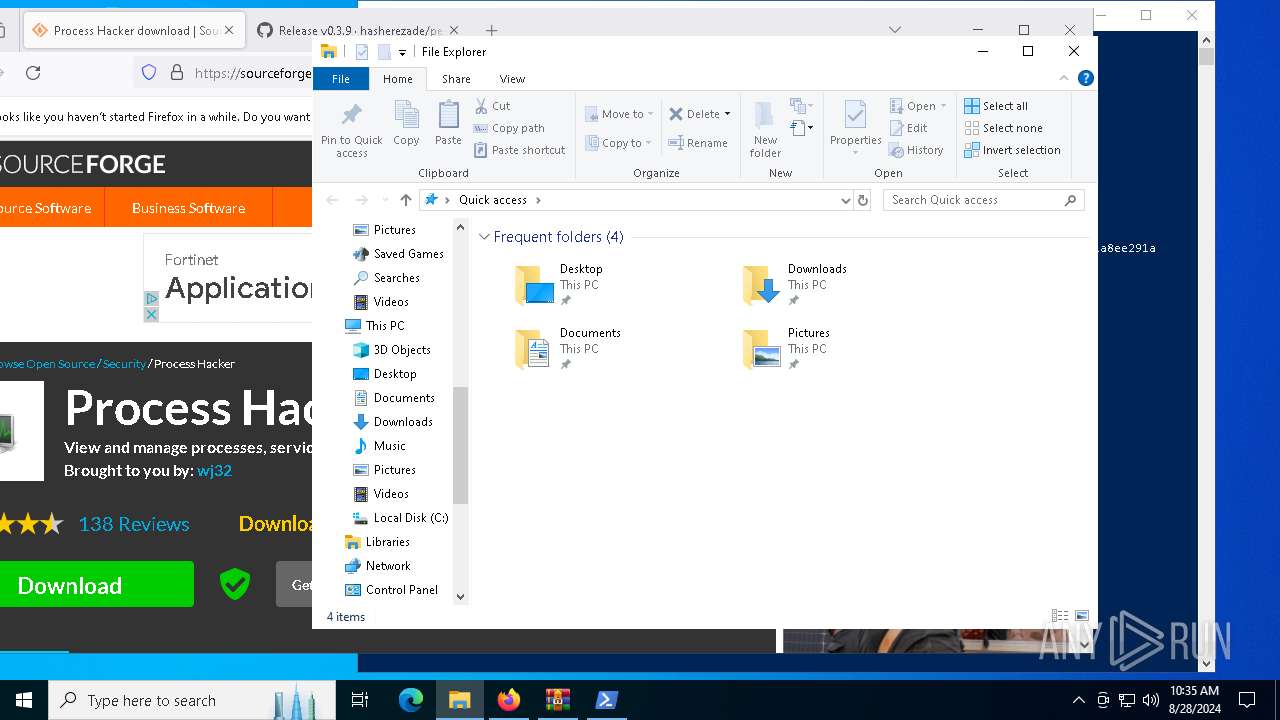
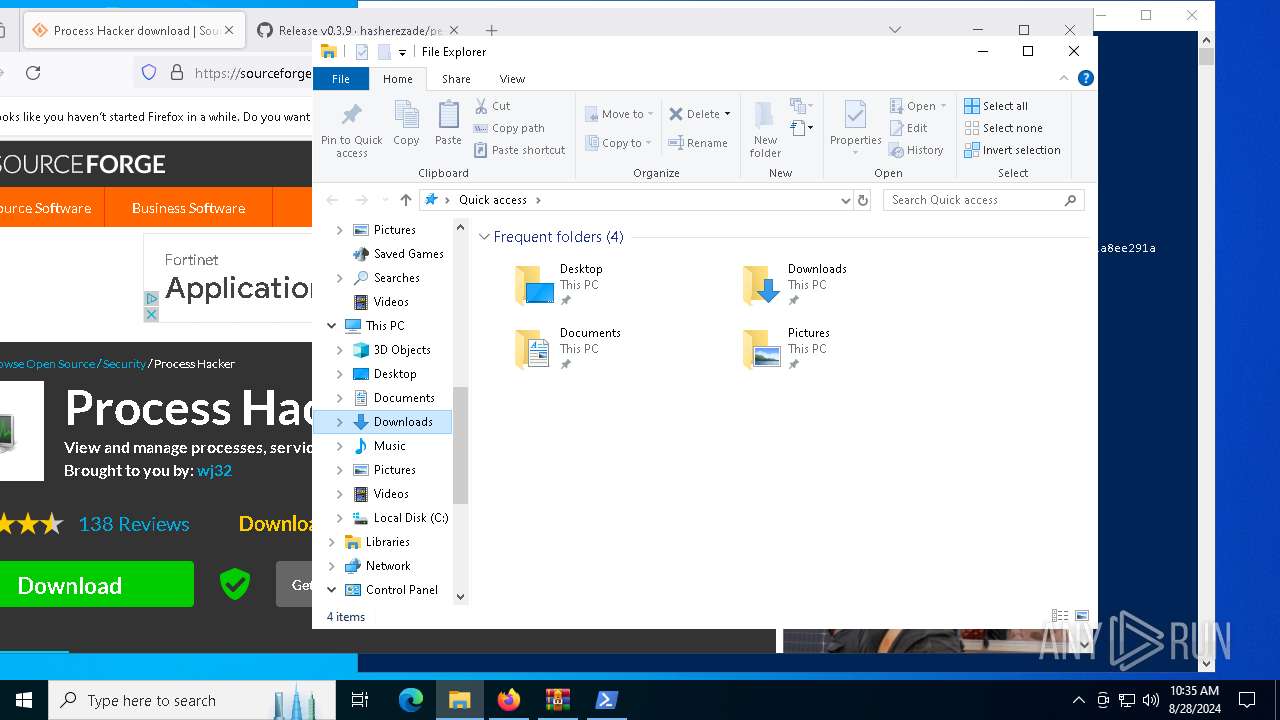
Creates files or folders in the user directory
- explorer.exe (PID: 4552)
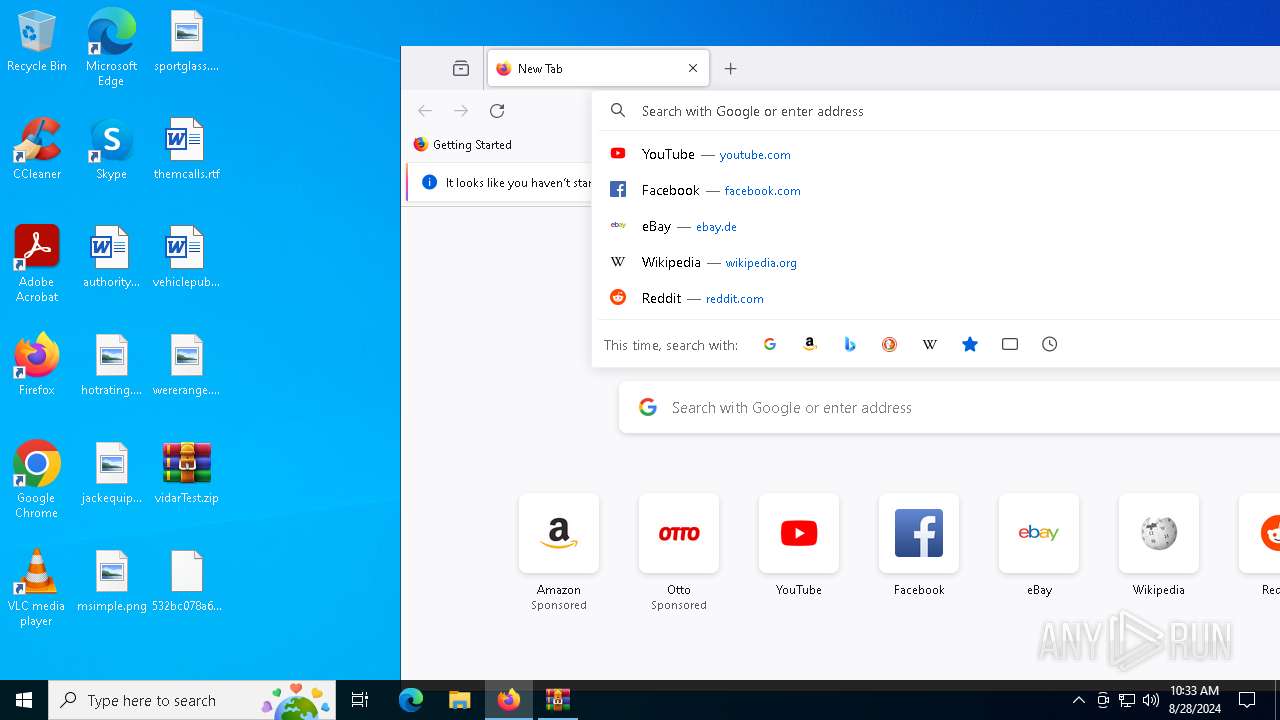
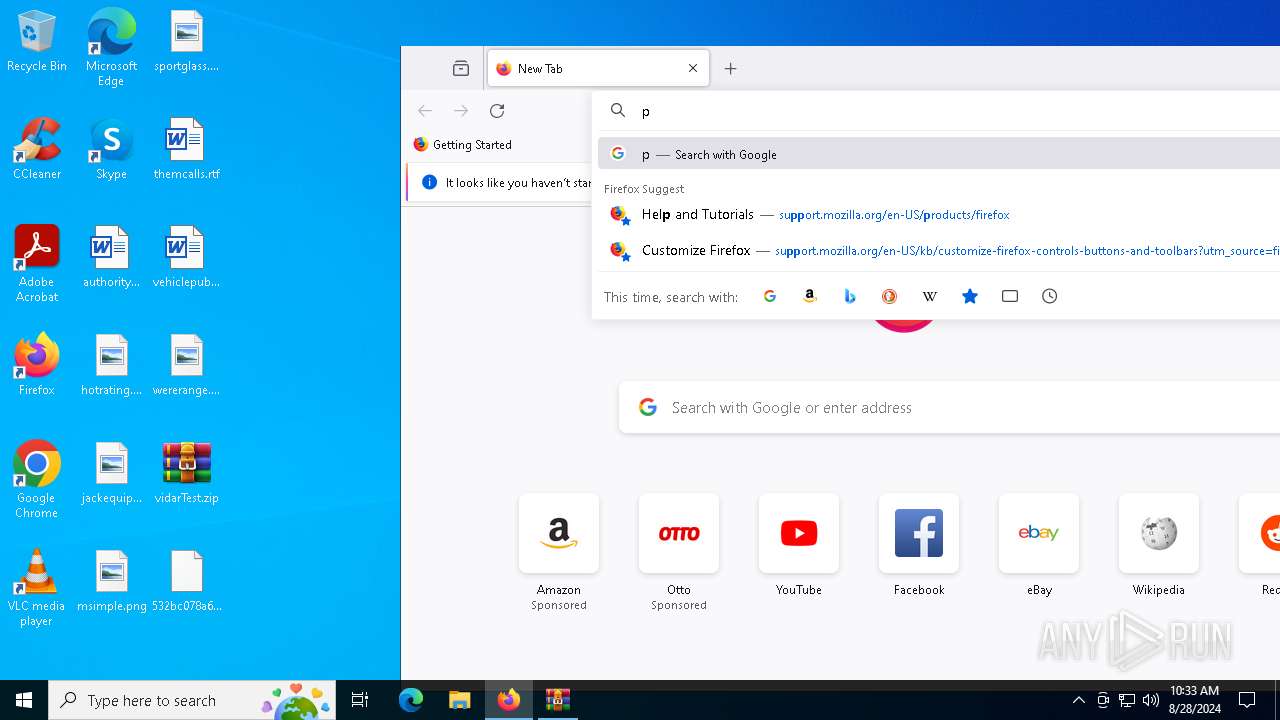
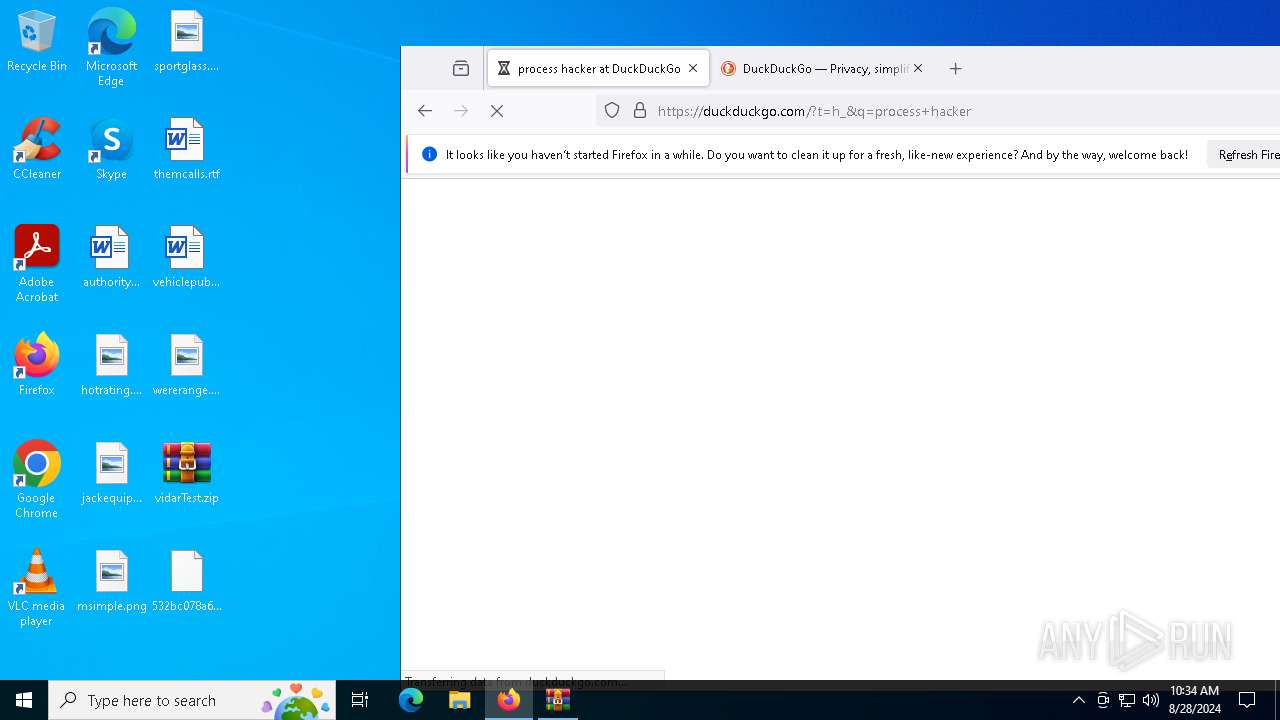
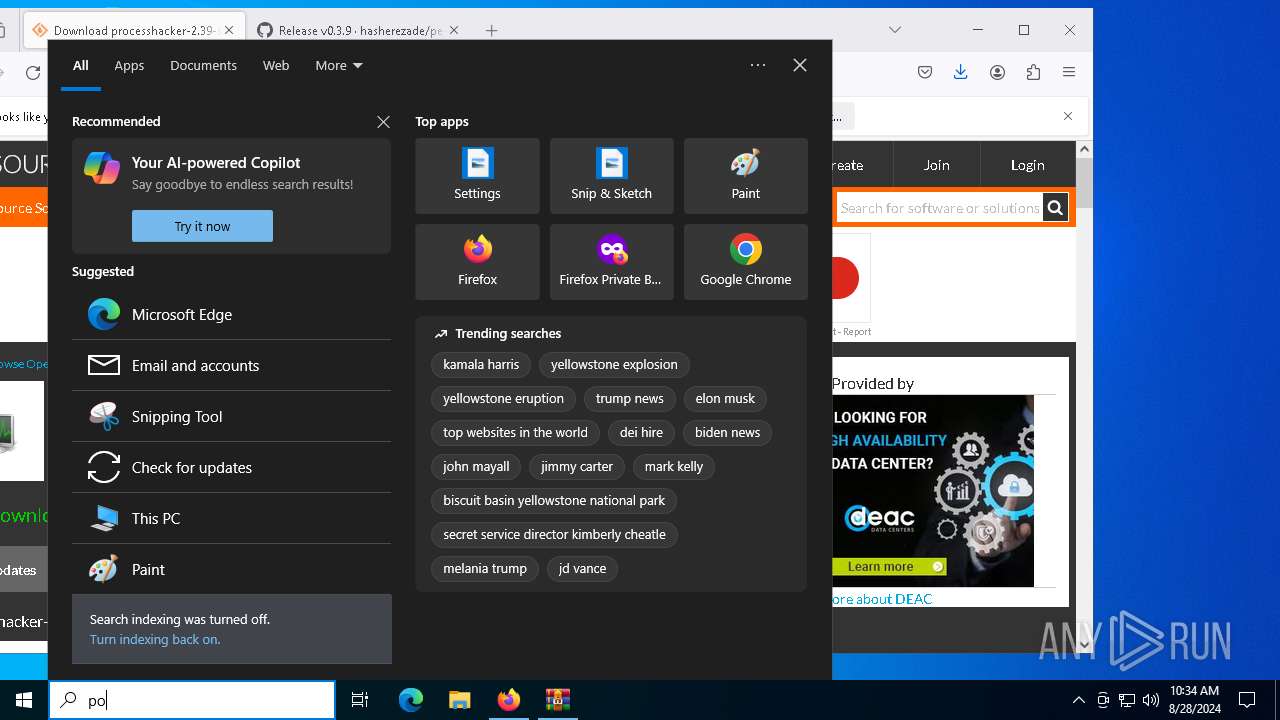
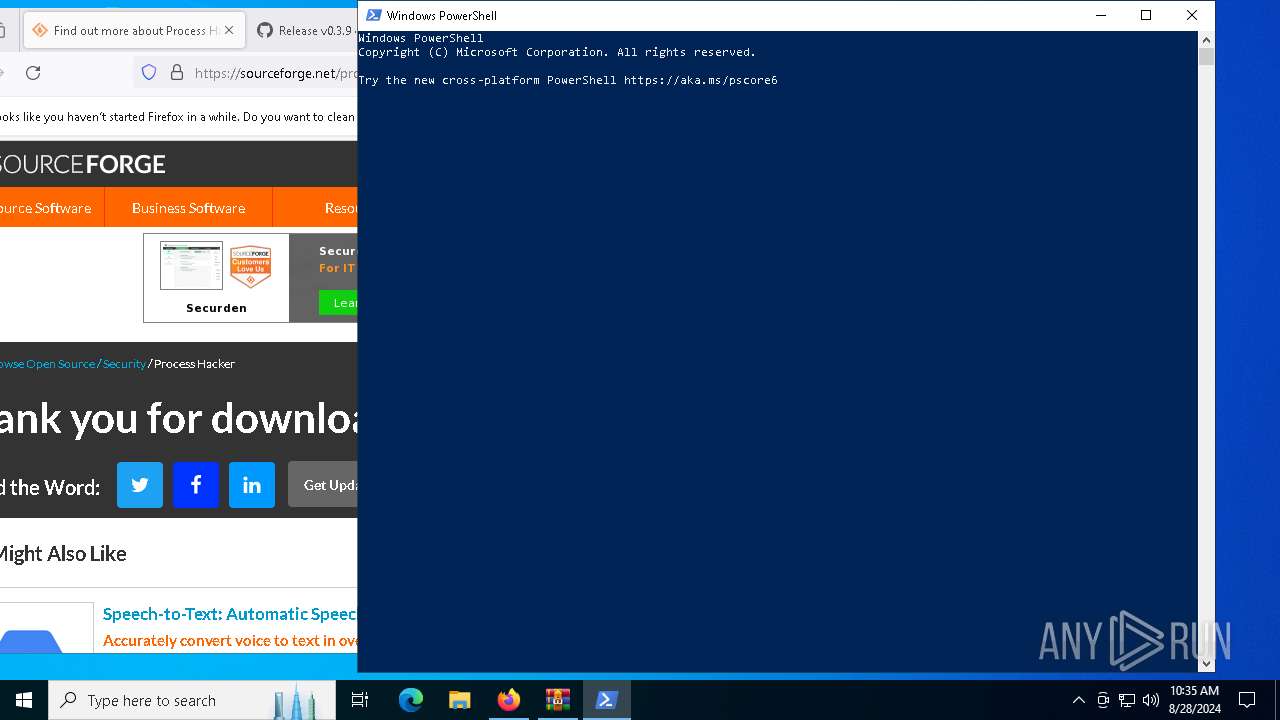
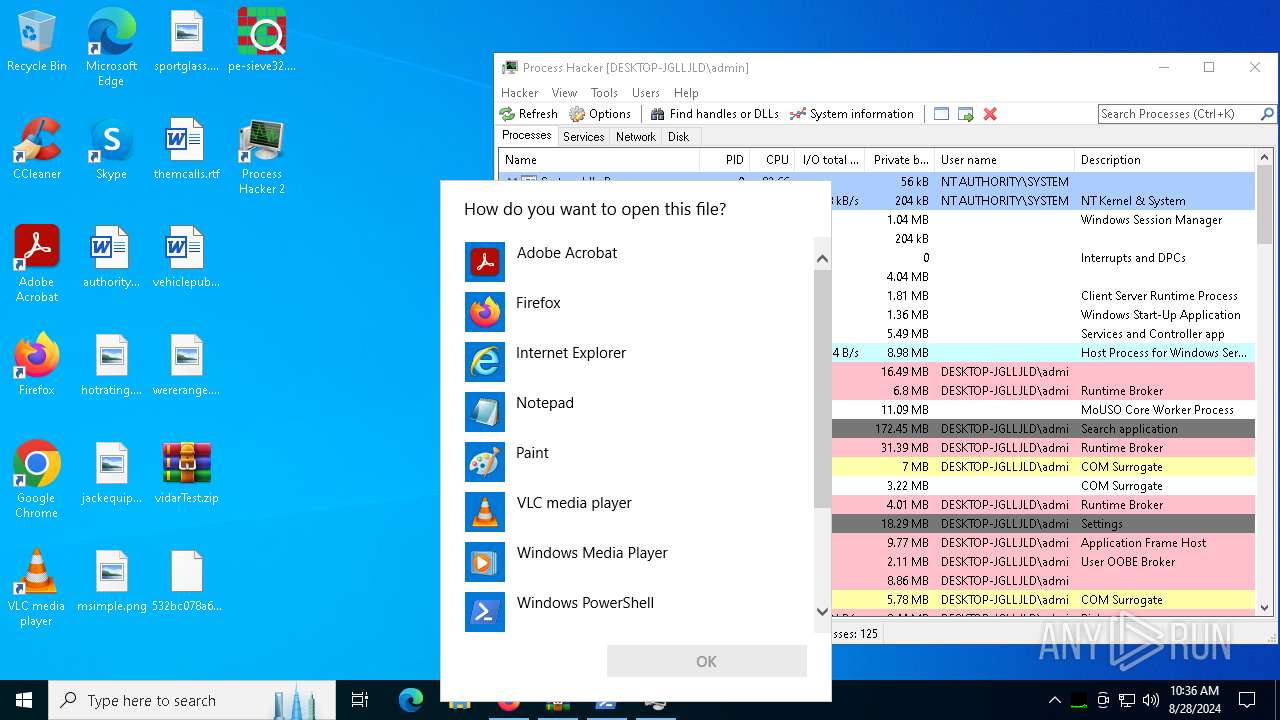
Manual execution by a user
- firefox.exe (PID: 2524)
- powershell.exe (PID: 4292)
Create files in a temporary directory
- processhacker-2.39-setup.exe (PID: 2144)
- processhacker-2.39-setup.exe (PID: 7132)
- processhacker-2.39-setup.tmp (PID: 7244)
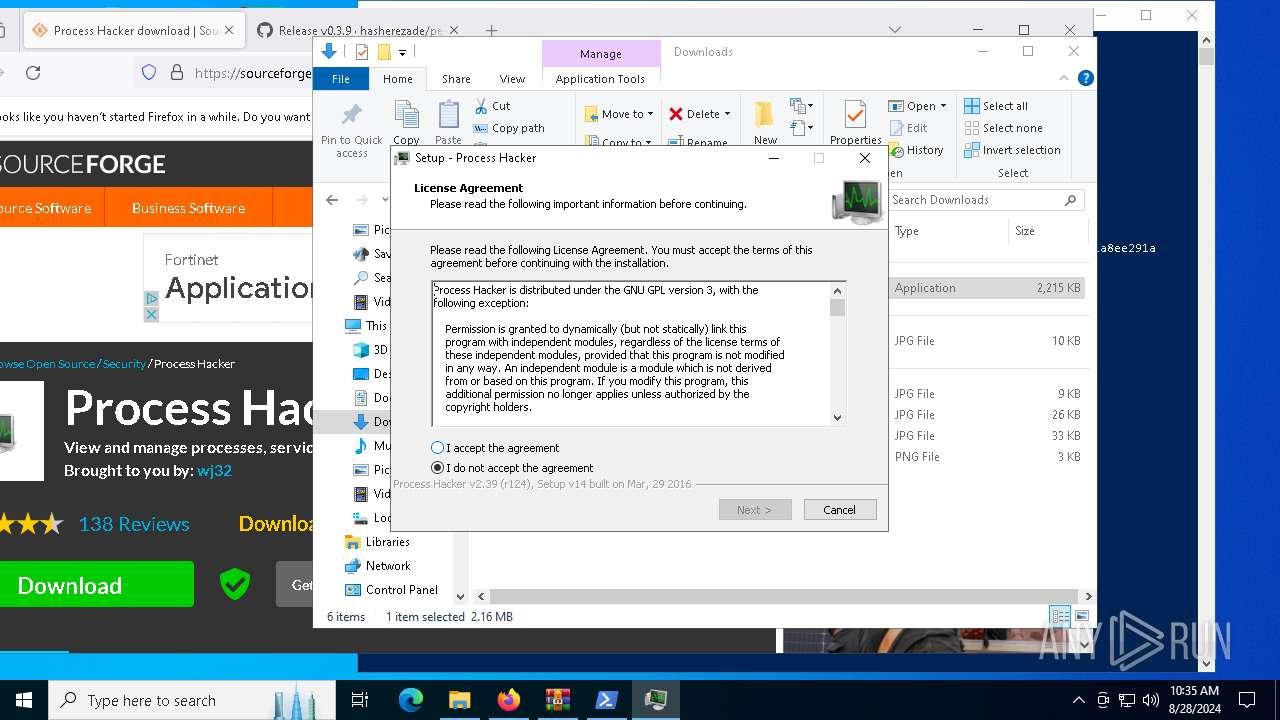
Process checks computer location settings
- processhacker-2.39-setup.tmp (PID: 3728)
Reads the computer name
- processhacker-2.39-setup.tmp (PID: 3728)
- processhacker-2.39-setup.tmp (PID: 7244)
- ProcessHacker.exe (PID: 7860)
- 532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a.exe (PID: 2080)
- pe-sieve32.exe (PID: 7760)
Creates files in the program directory
- processhacker-2.39-setup.tmp (PID: 7244)
Creates a software uninstall entry
- processhacker-2.39-setup.tmp (PID: 7244)
Reads Environment values
- ProcessHacker.exe (PID: 7860)
Reads the machine GUID from the registry
- ProcessHacker.exe (PID: 7860)
- 532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a.exe (PID: 2080)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 493908 |
| ZipUncompressedSize: | 879104 |
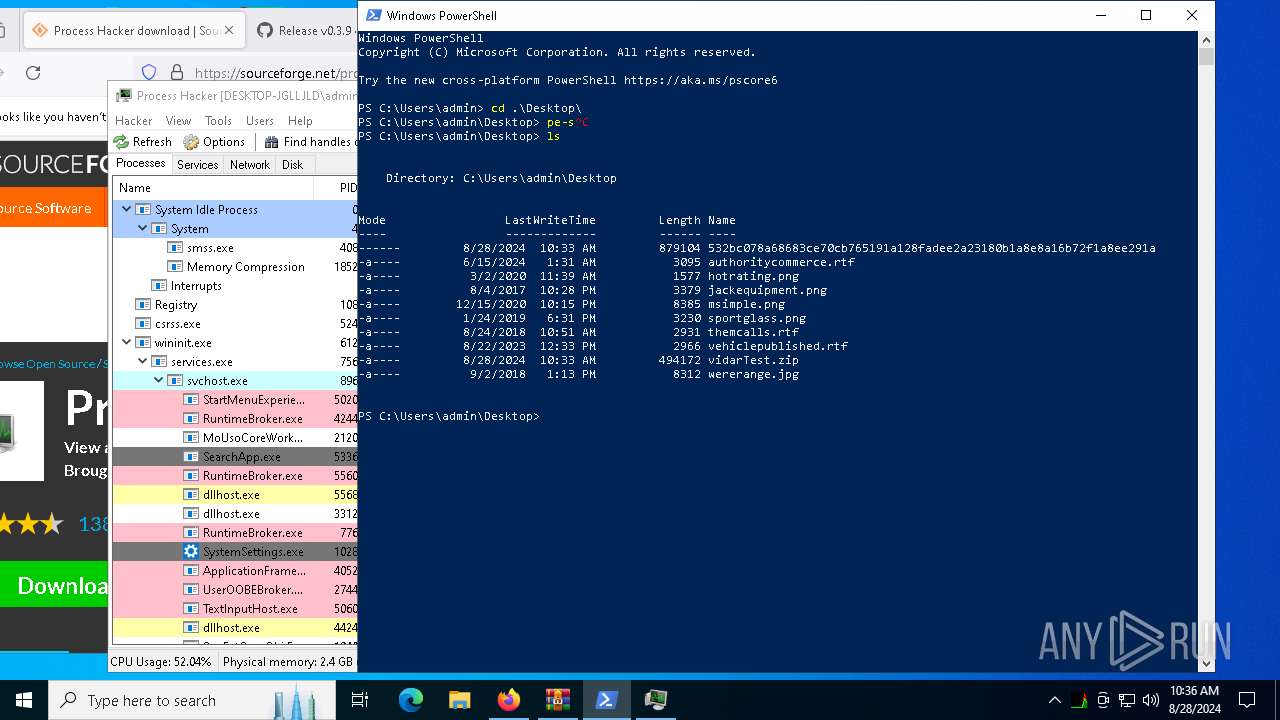
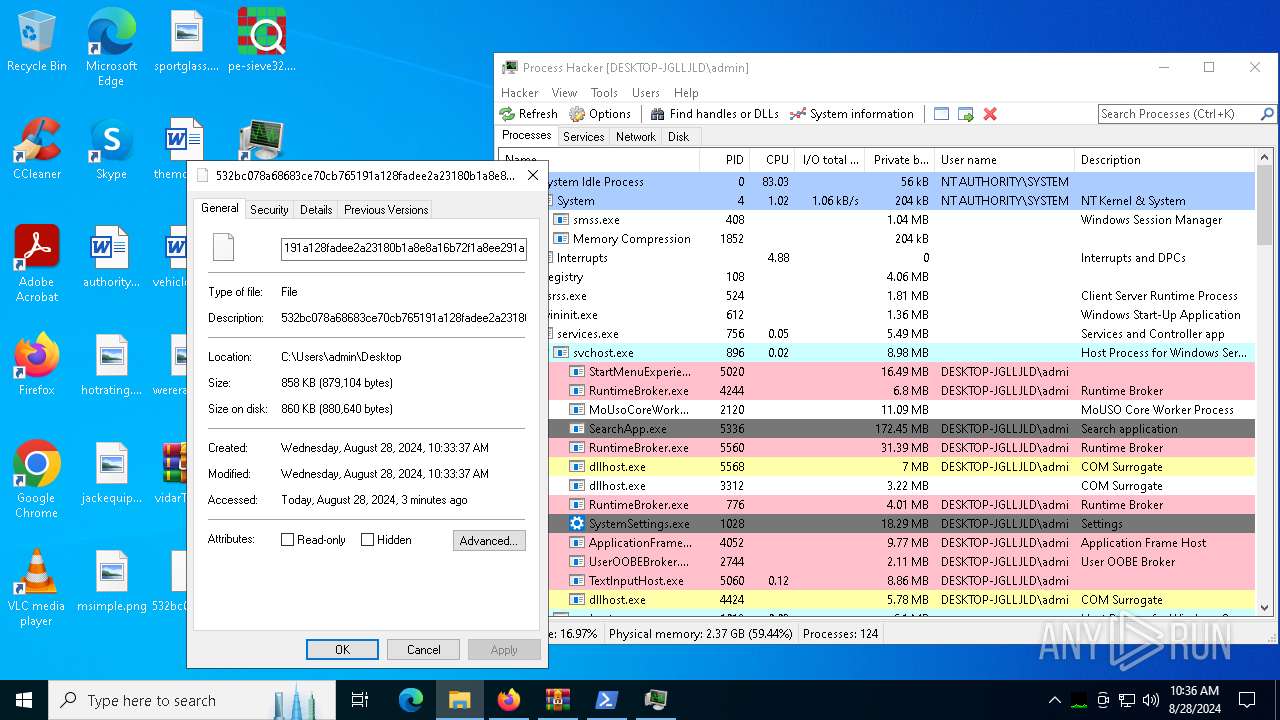
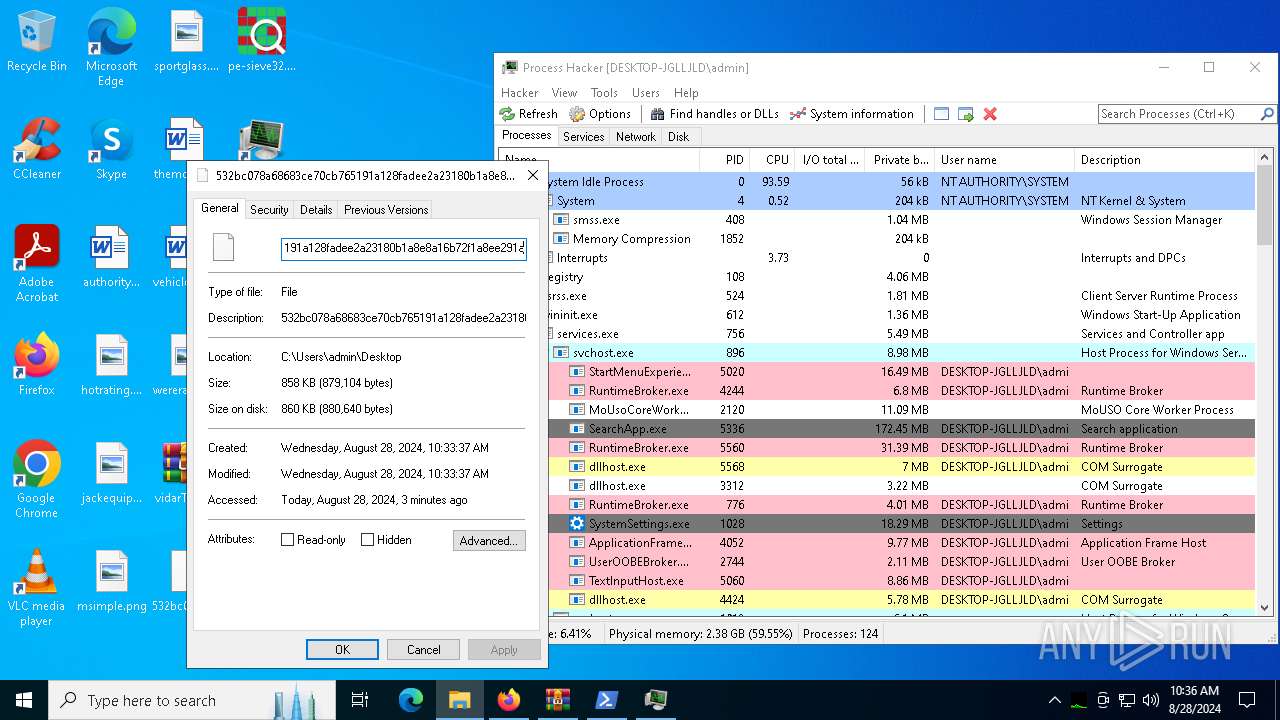
| ZipFileName: | 532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a |
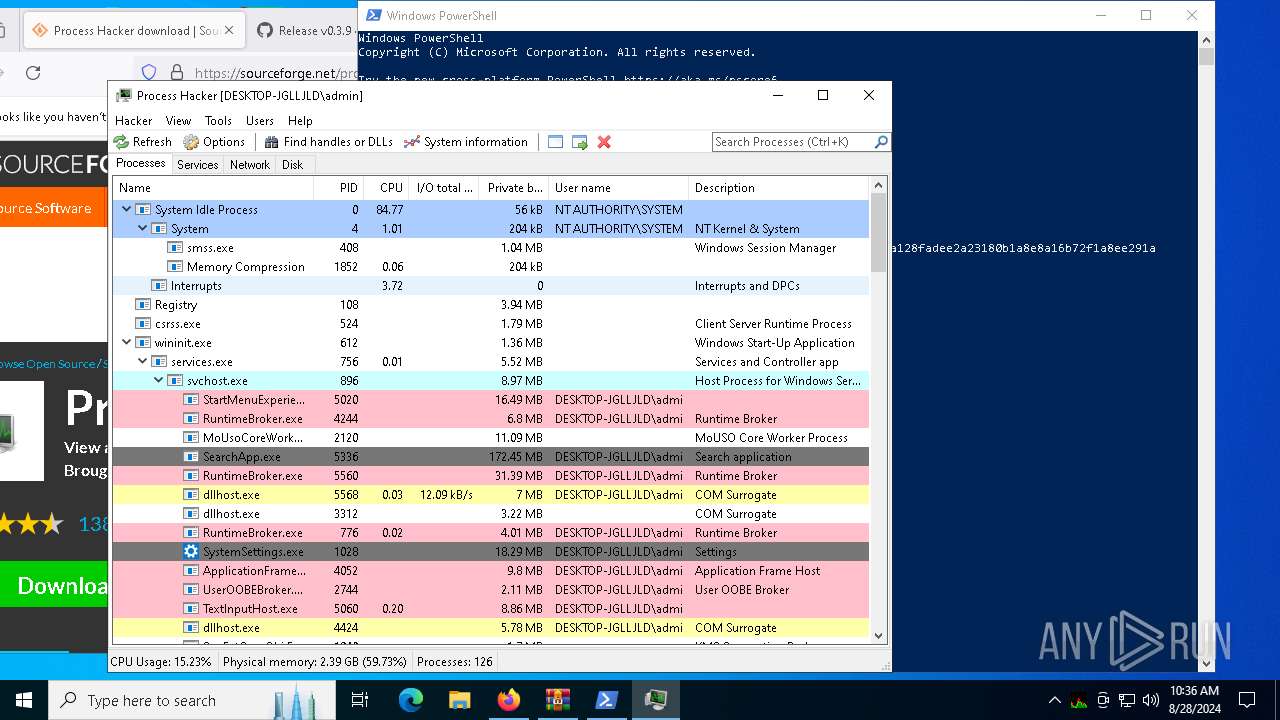
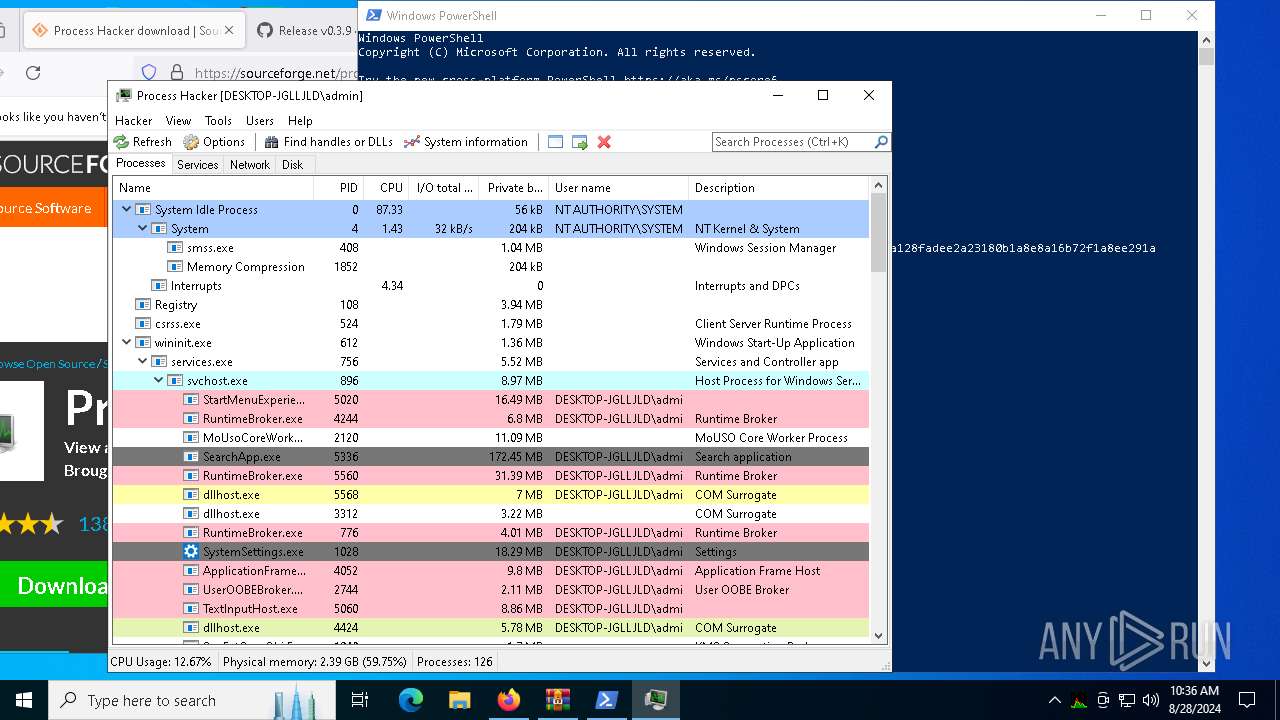
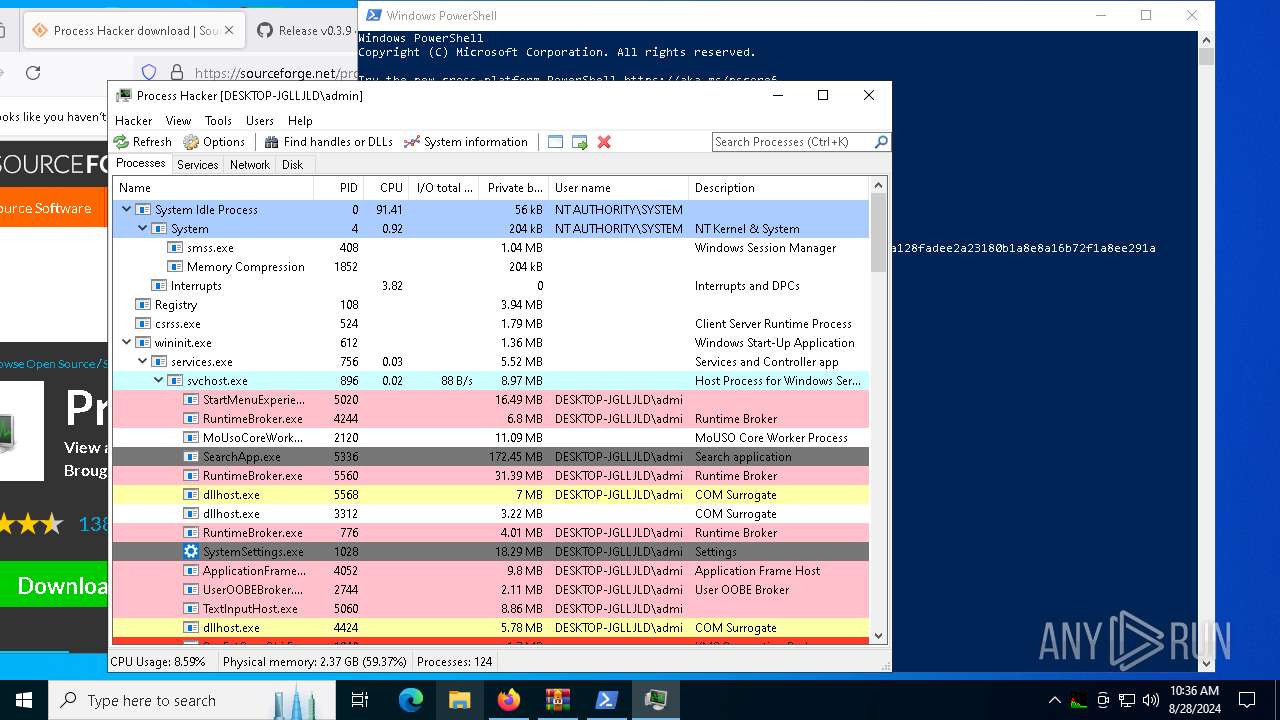
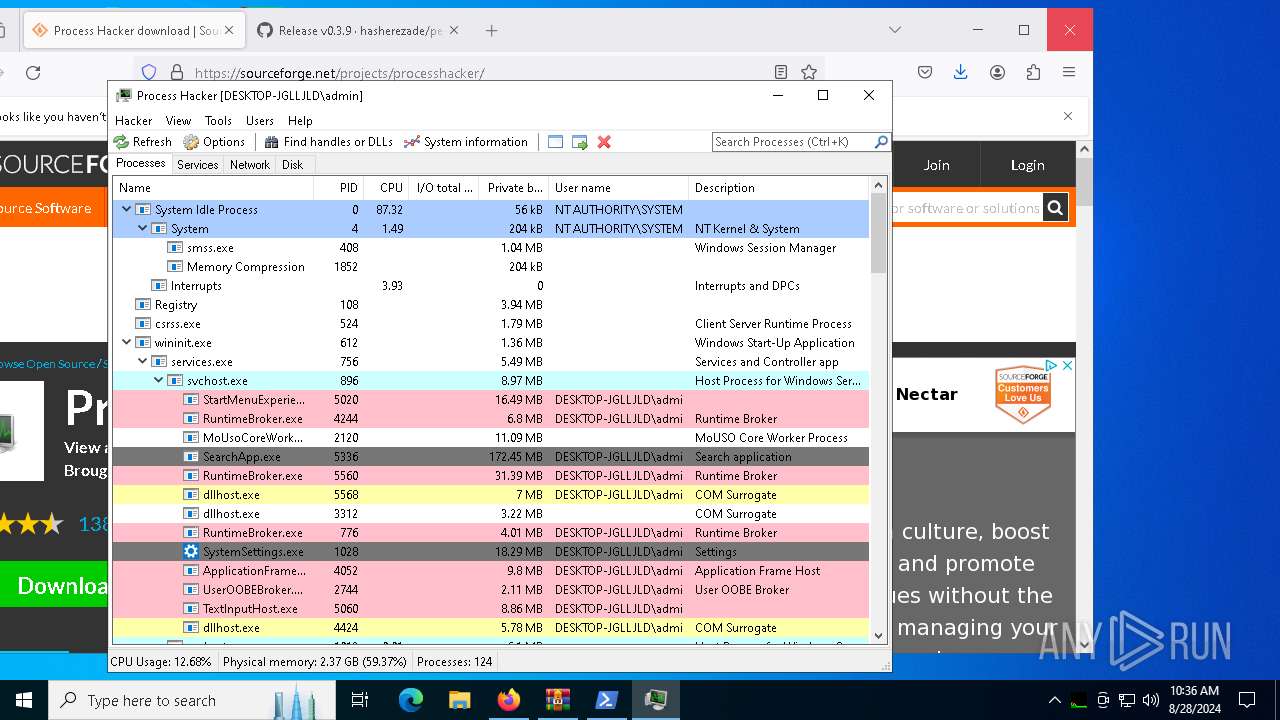
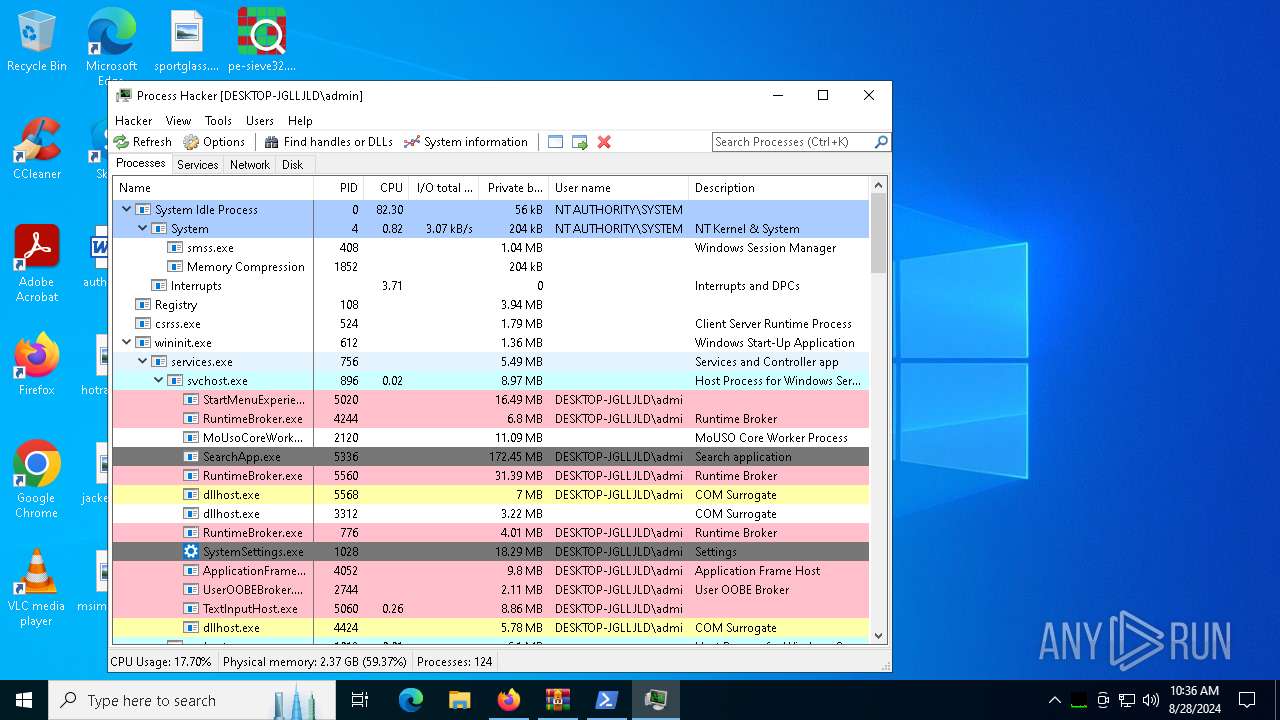
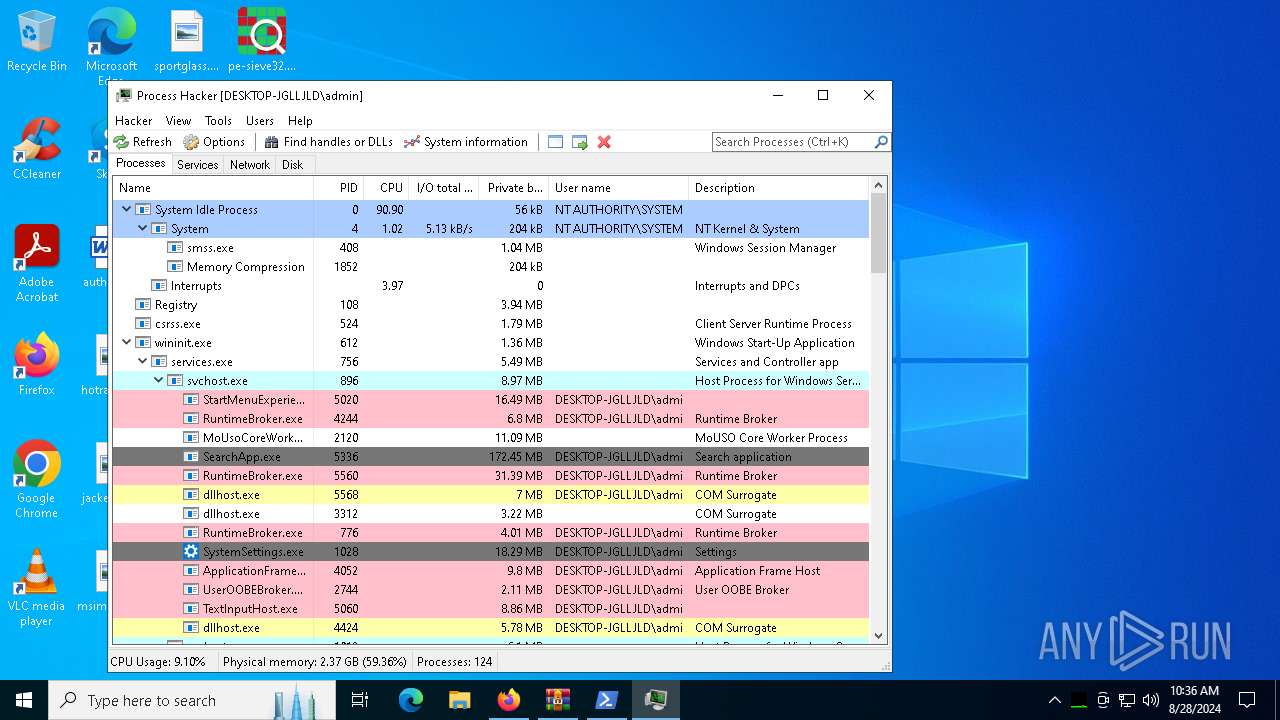
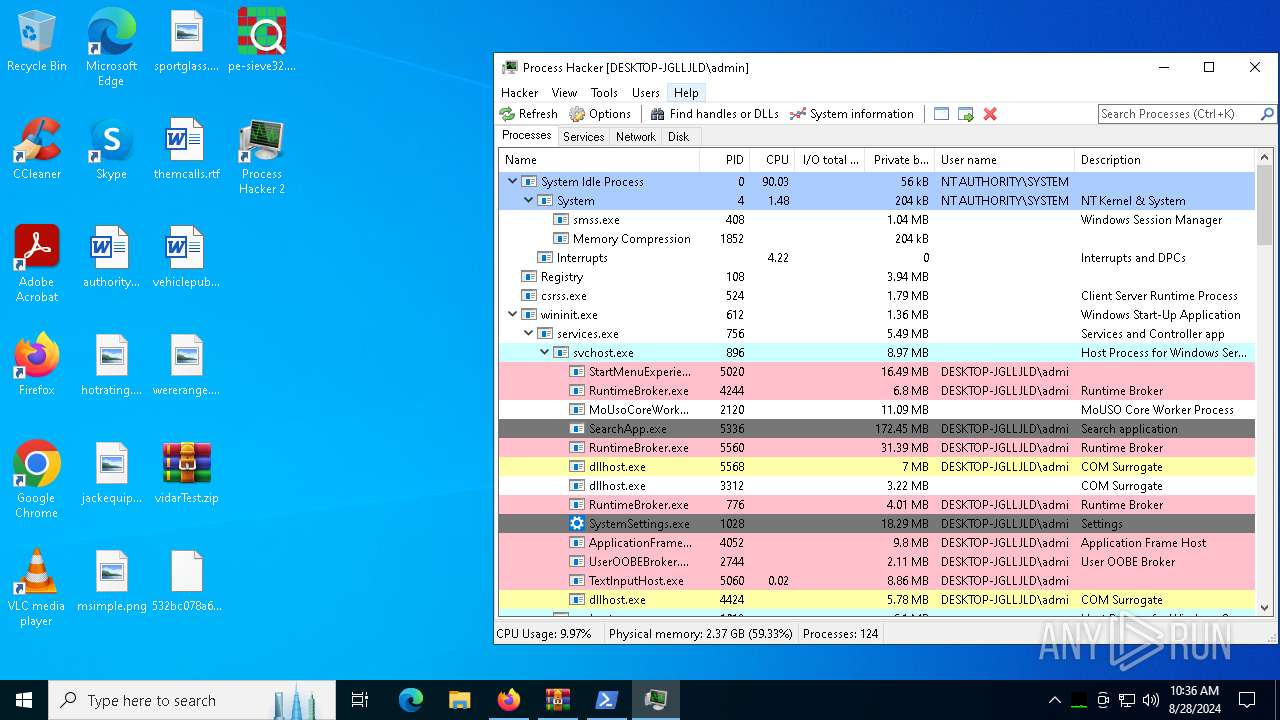
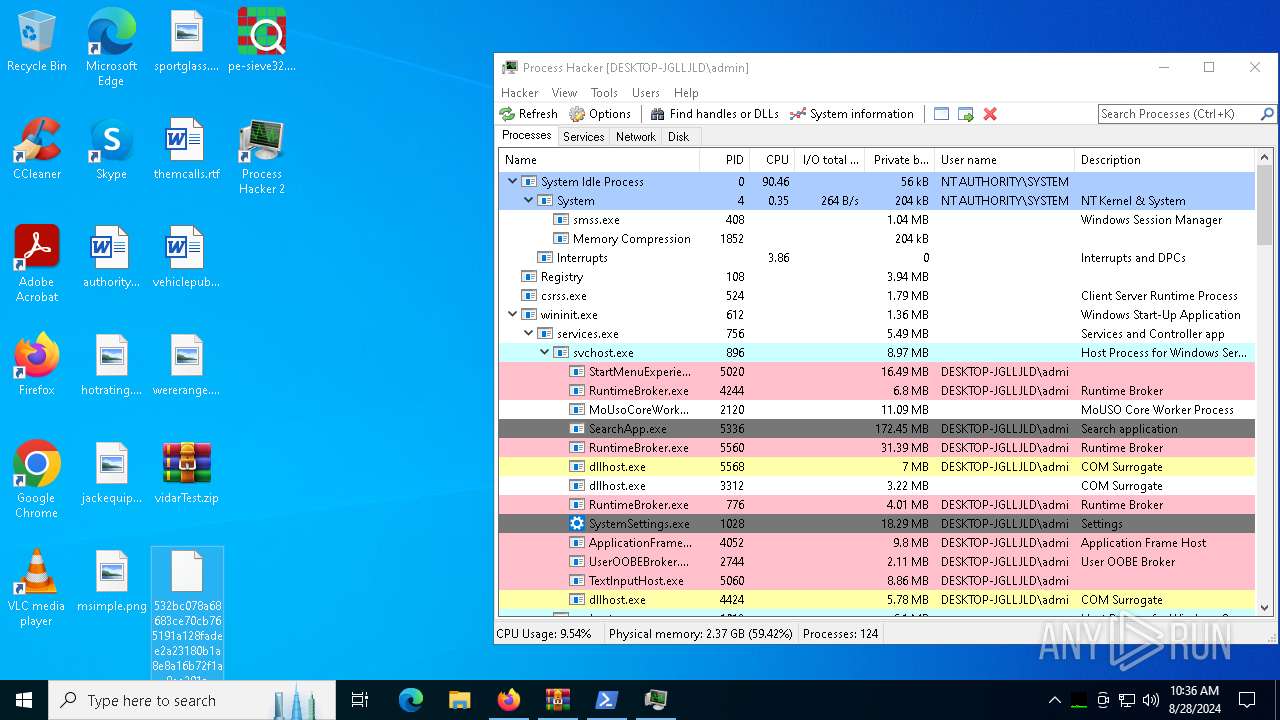
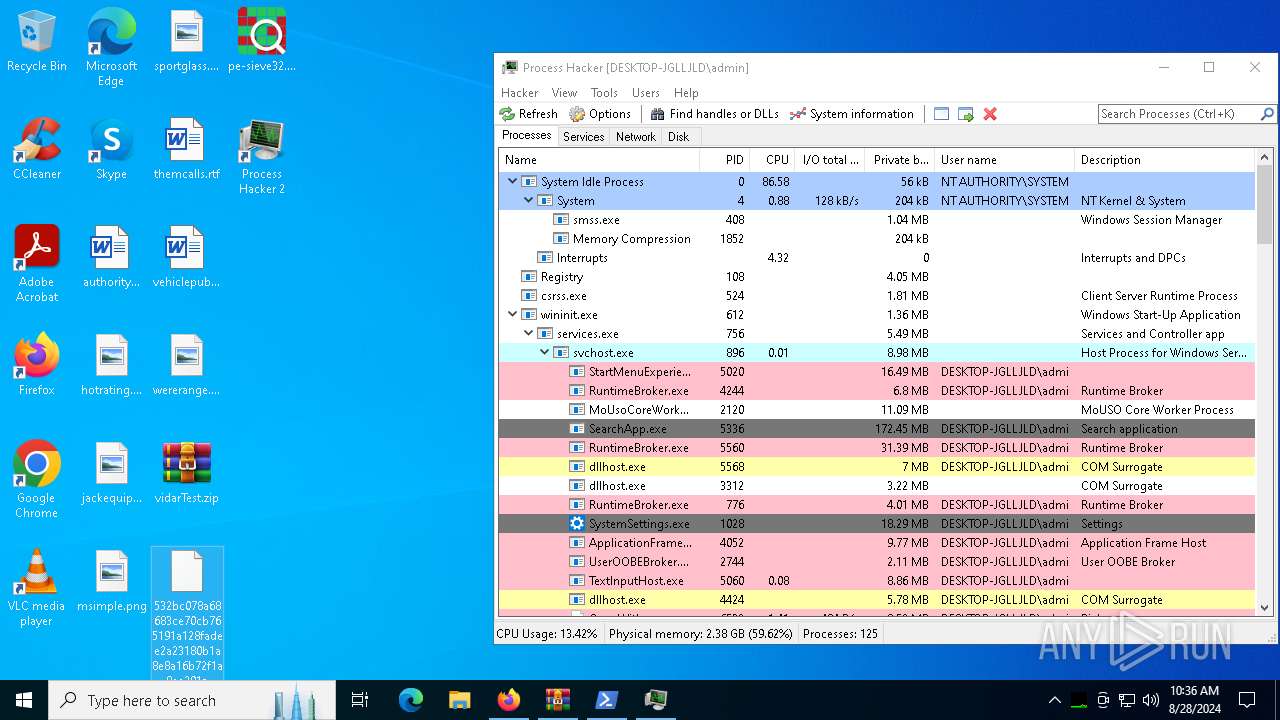
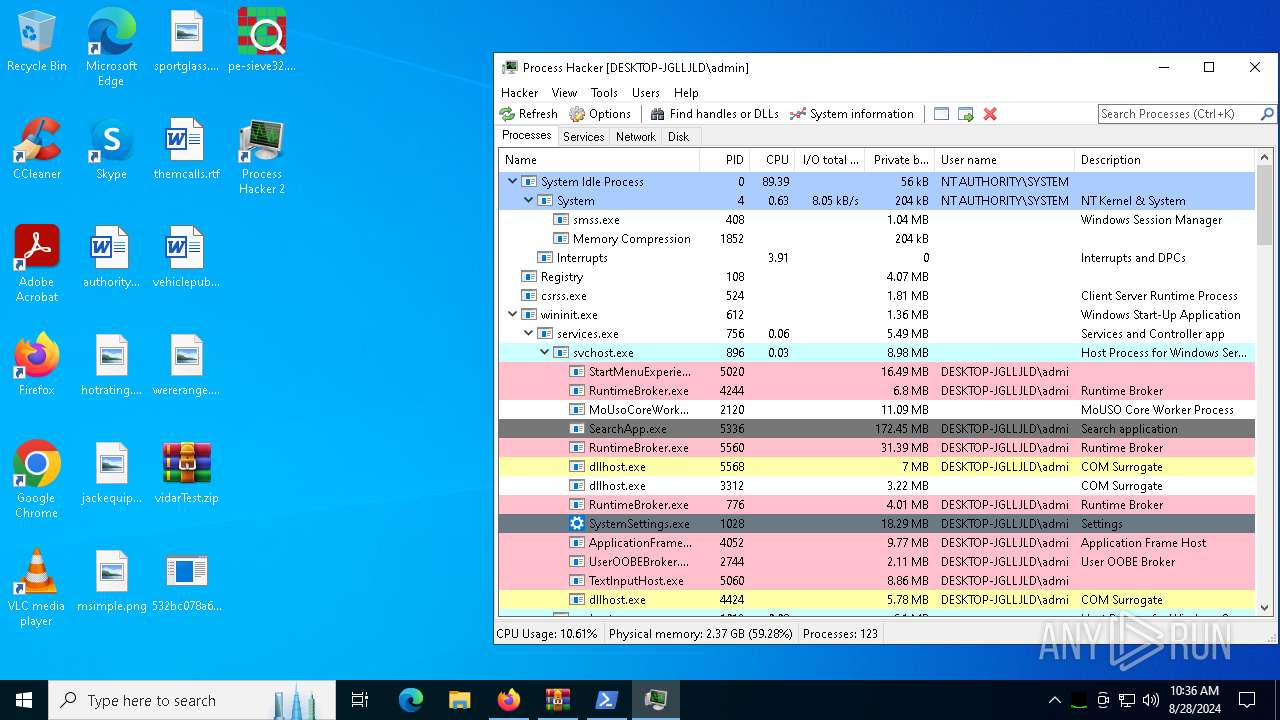
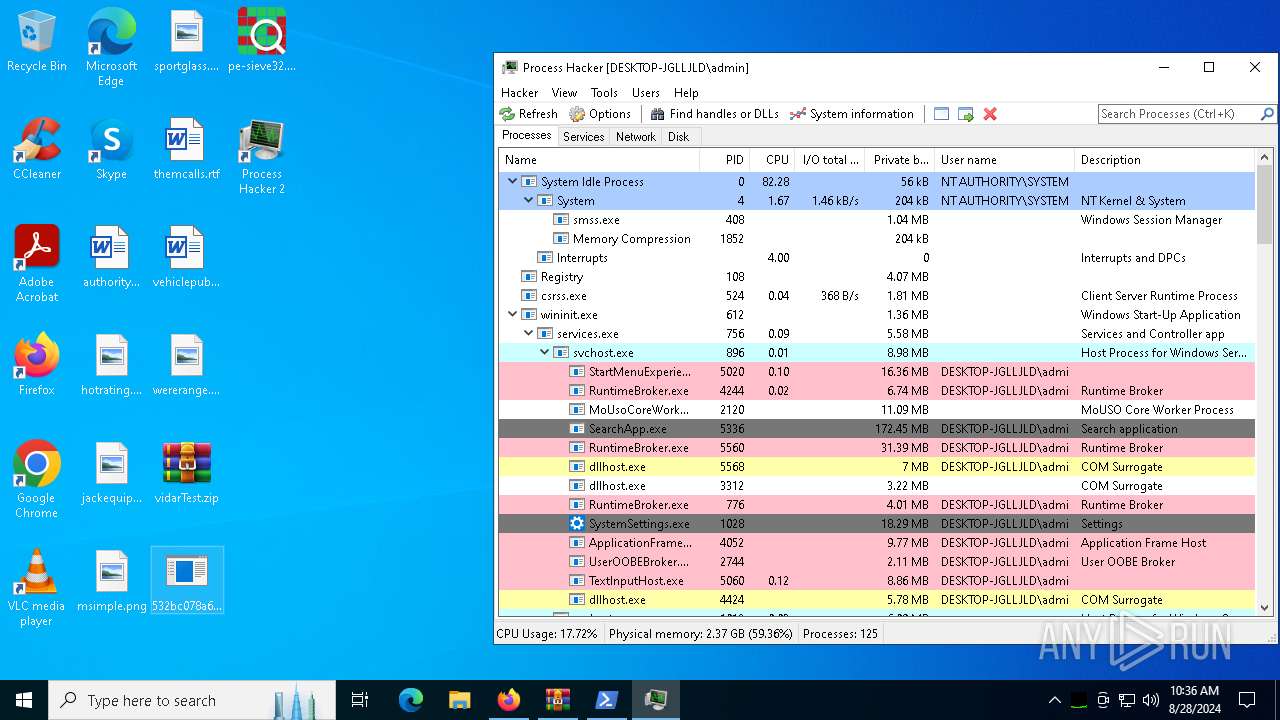
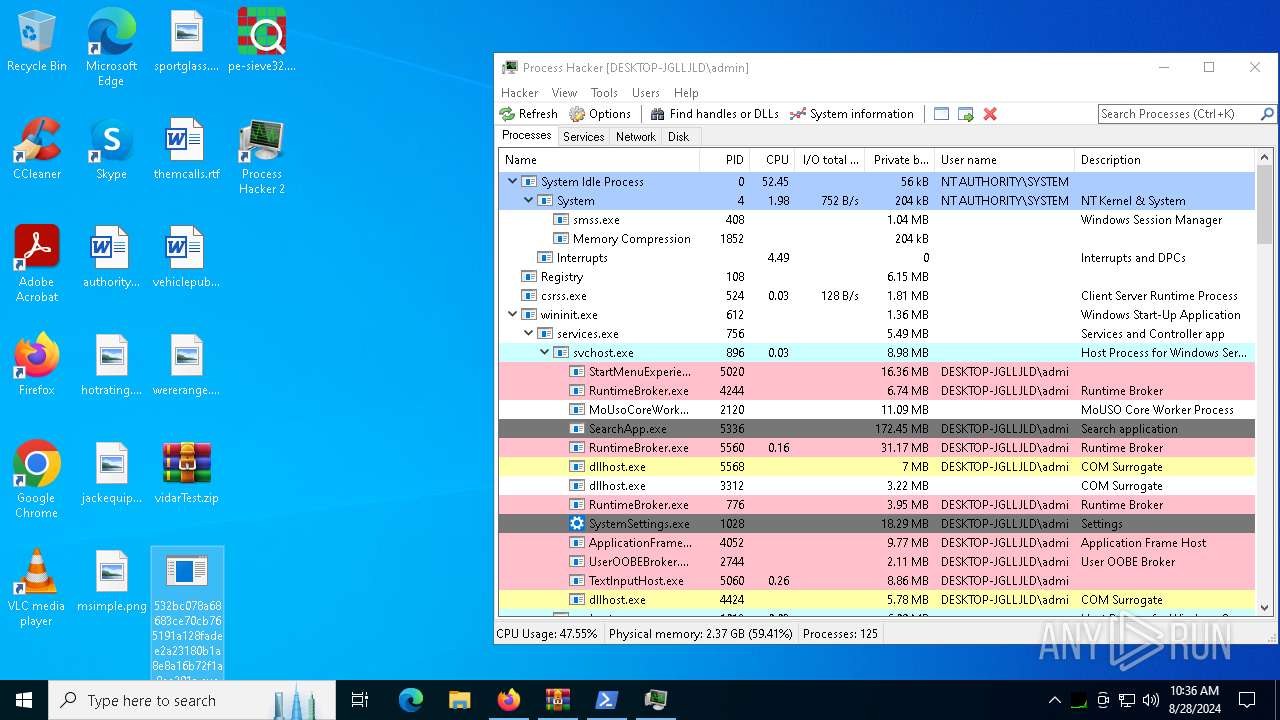
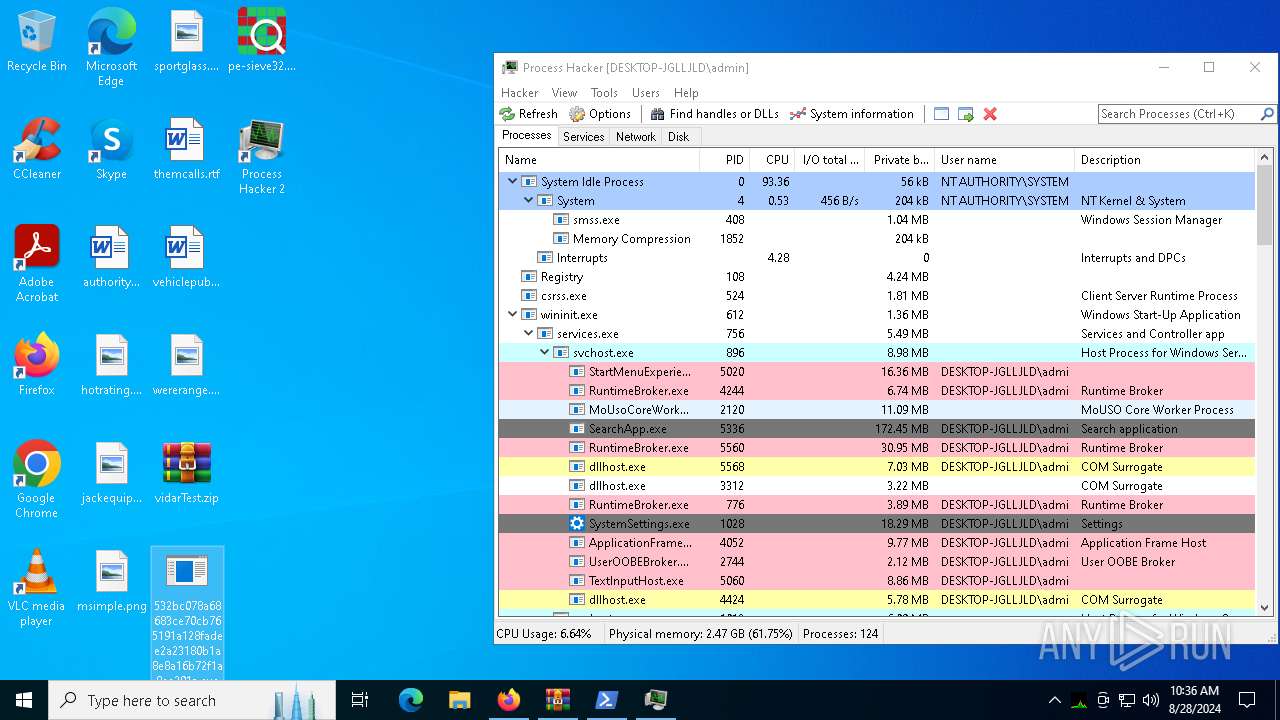
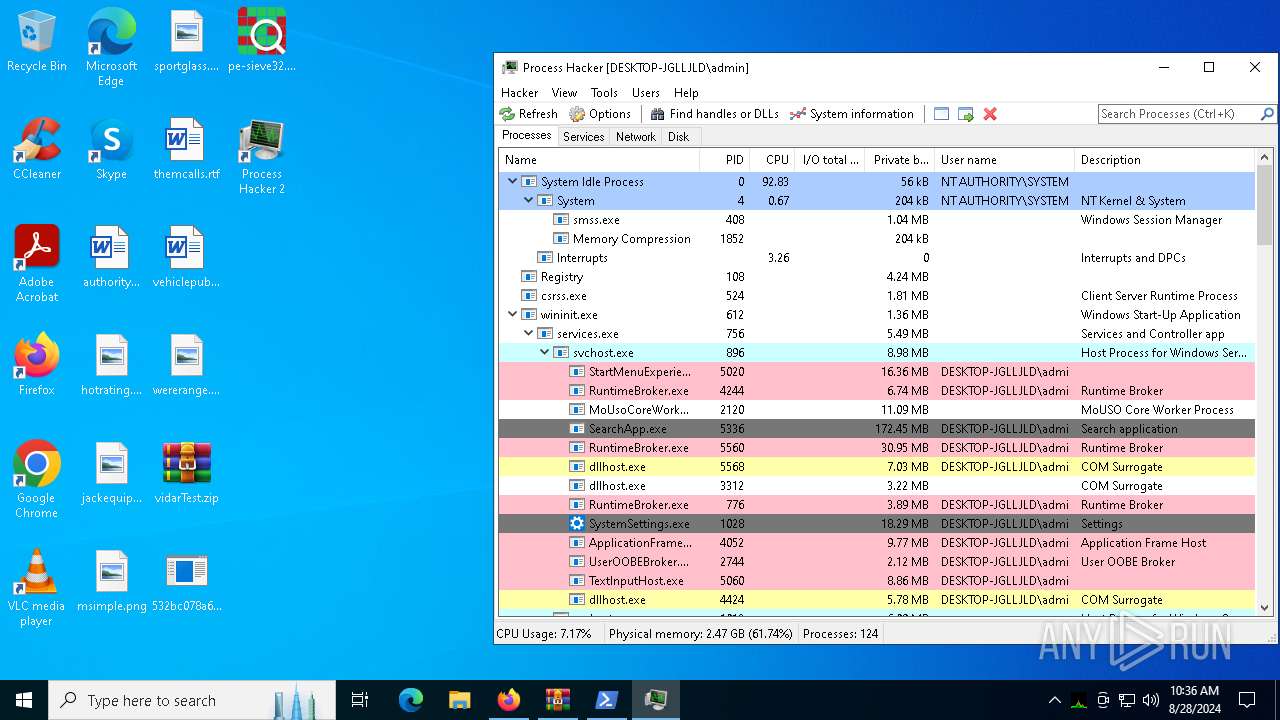
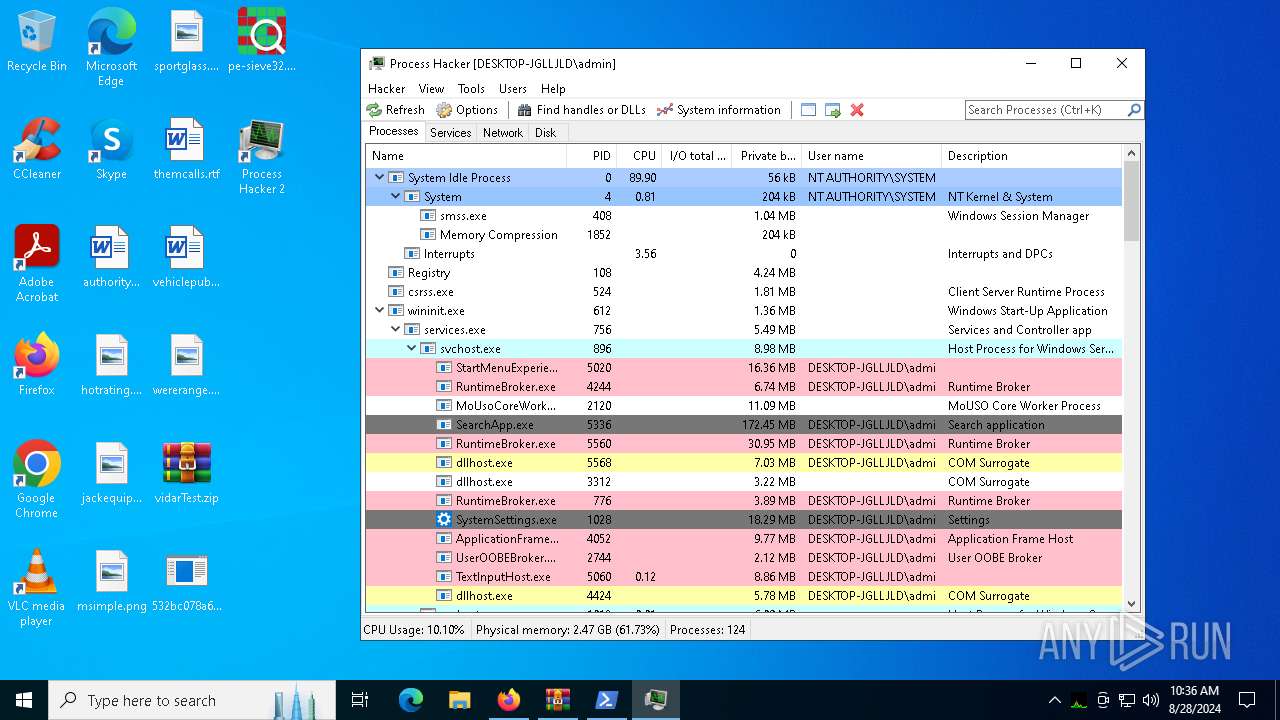
Total processes
174
Monitored processes
38
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1156 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=8108 -childID 14 -isForBrowser -prefsHandle 8024 -prefMapHandle 8028 -prefsLen 31936 -prefMapSize 244343 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {84af32d2-4022-48c6-8aea-600fe9263778} 2876 "\\.\pipe\gecko-crash-server-pipe.2876" 263726344d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1712 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5448 -childID 3 -isForBrowser -prefsHandle 5424 -prefMapHandle 2784 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {70edb802-9dd8-46b8-bb13-fc01c7bd07d0} 2876 "\\.\pipe\gecko-crash-server-pipe.2876" 2636f38fbd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1940 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
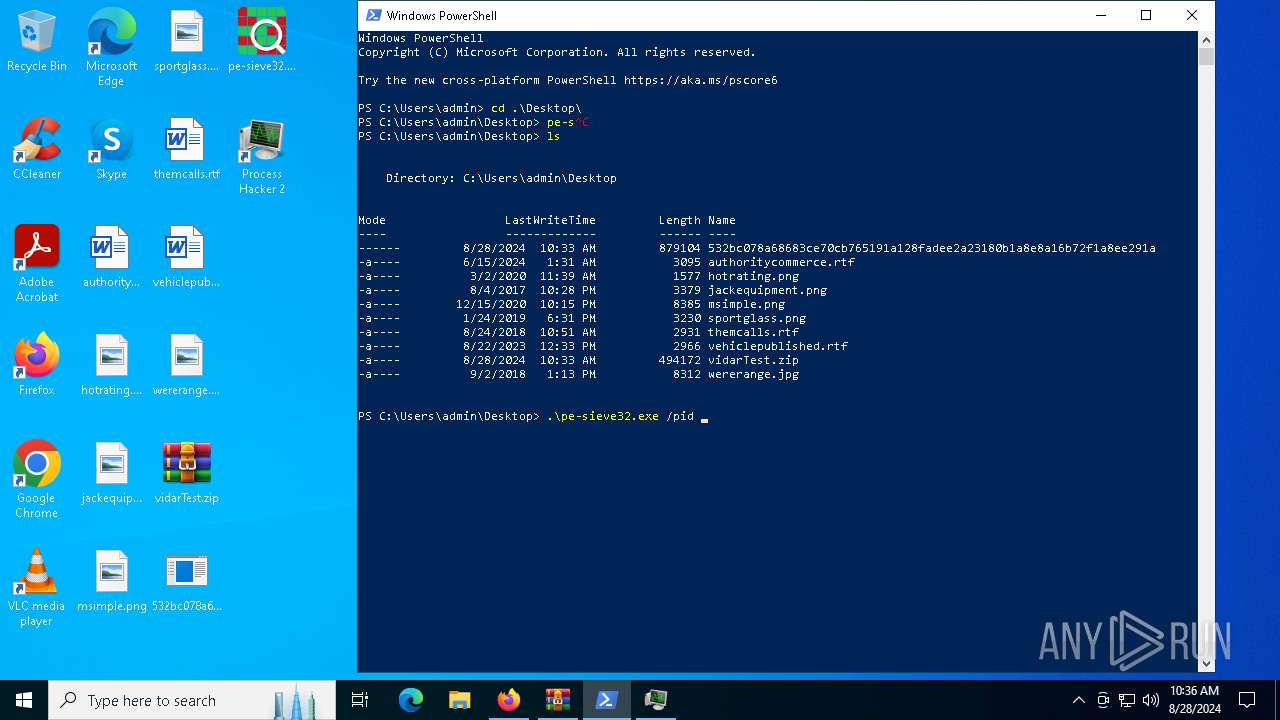
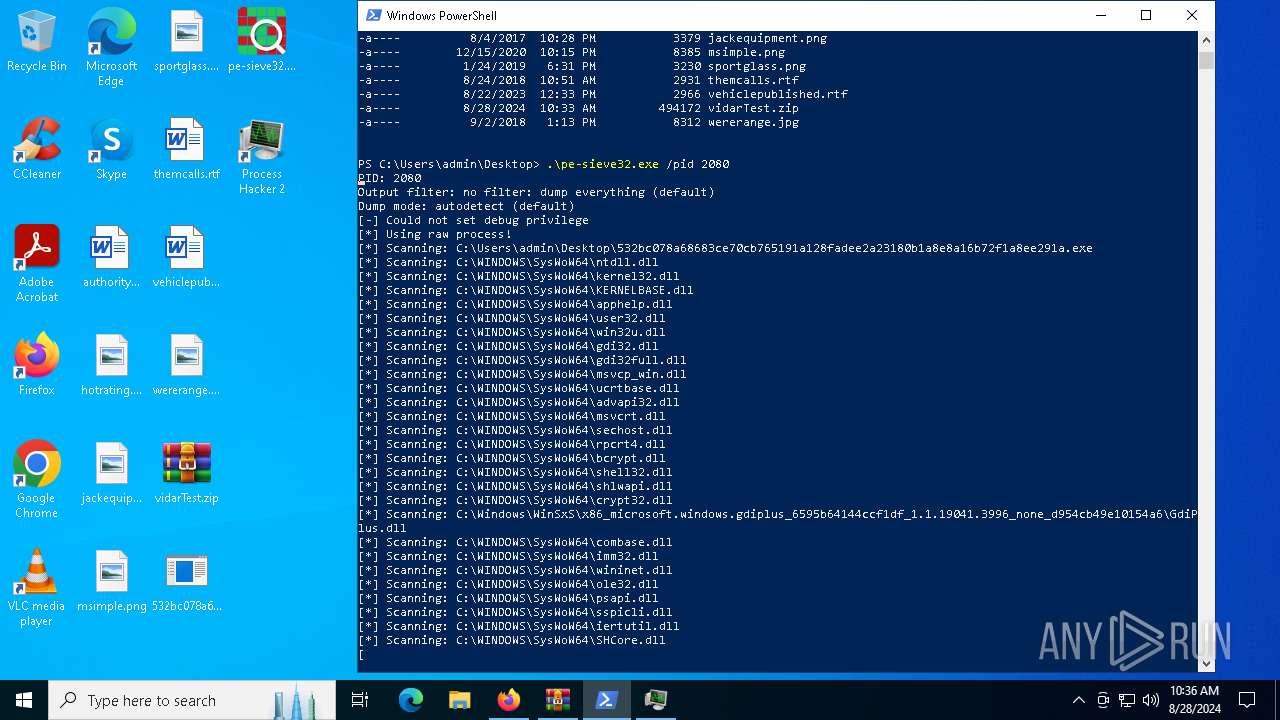
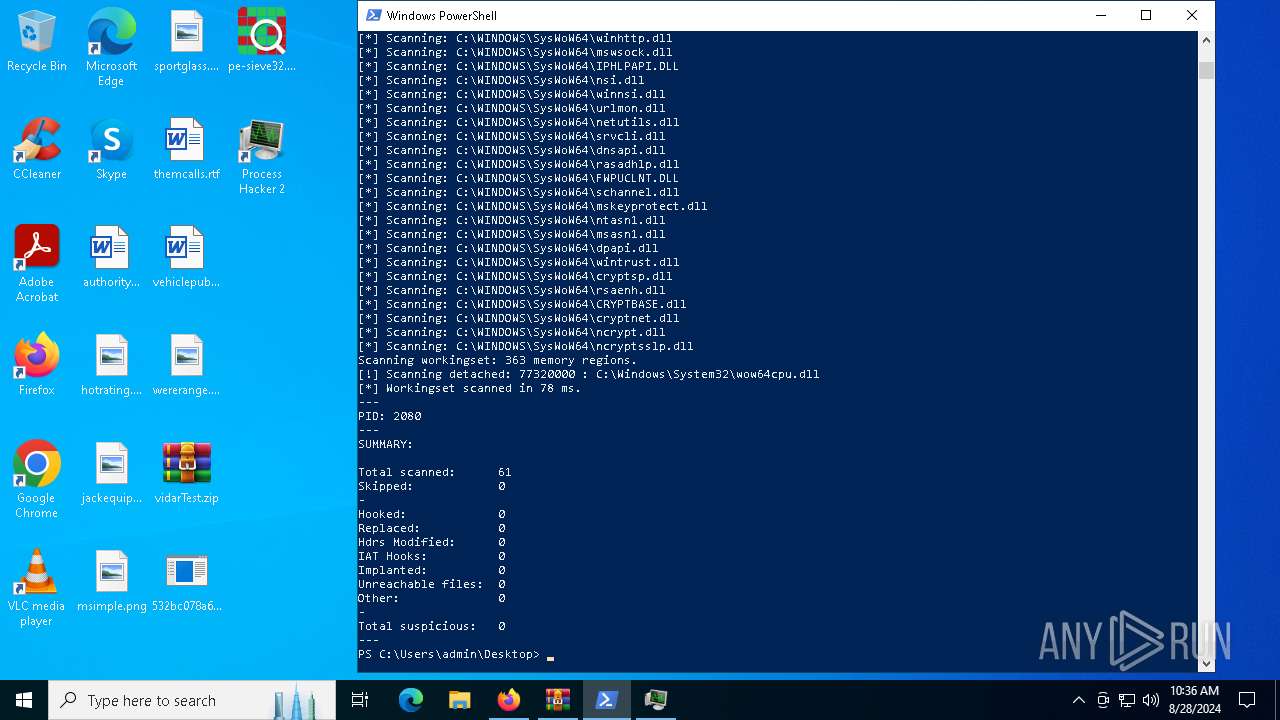
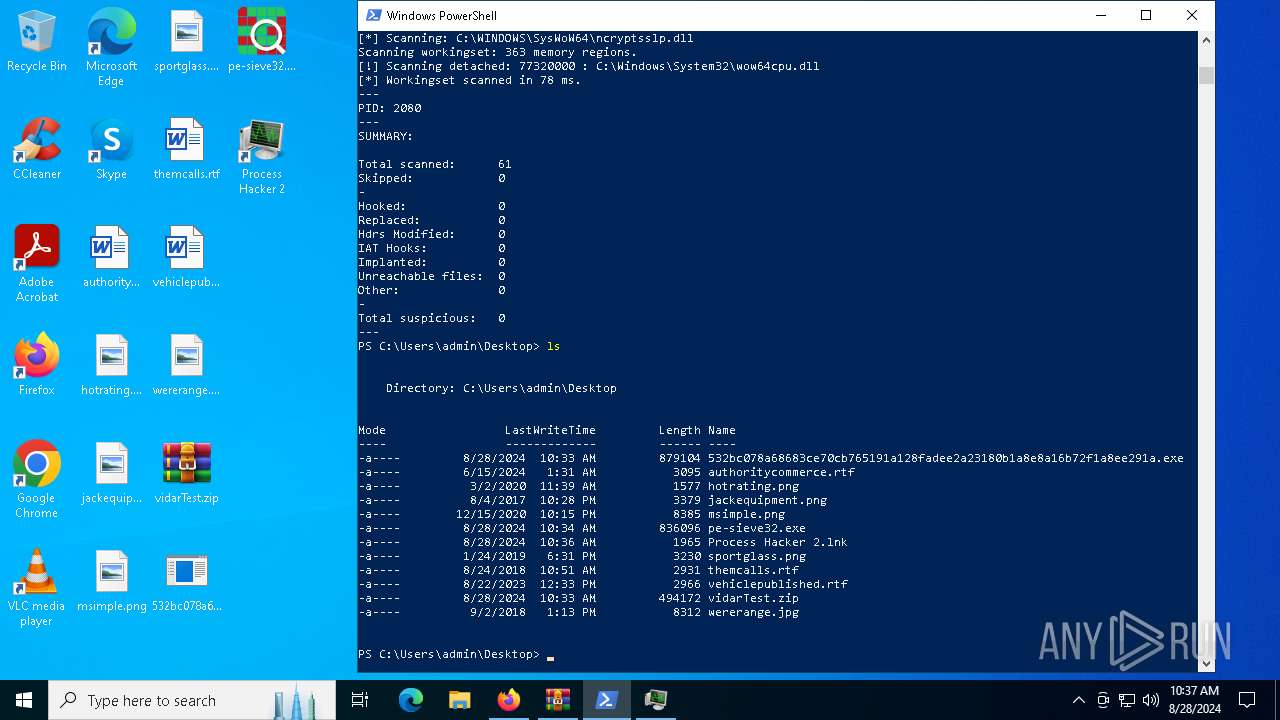
| 2080 | "C:\Users\admin\Desktop\532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a.exe" | C:\Users\admin\Desktop\532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
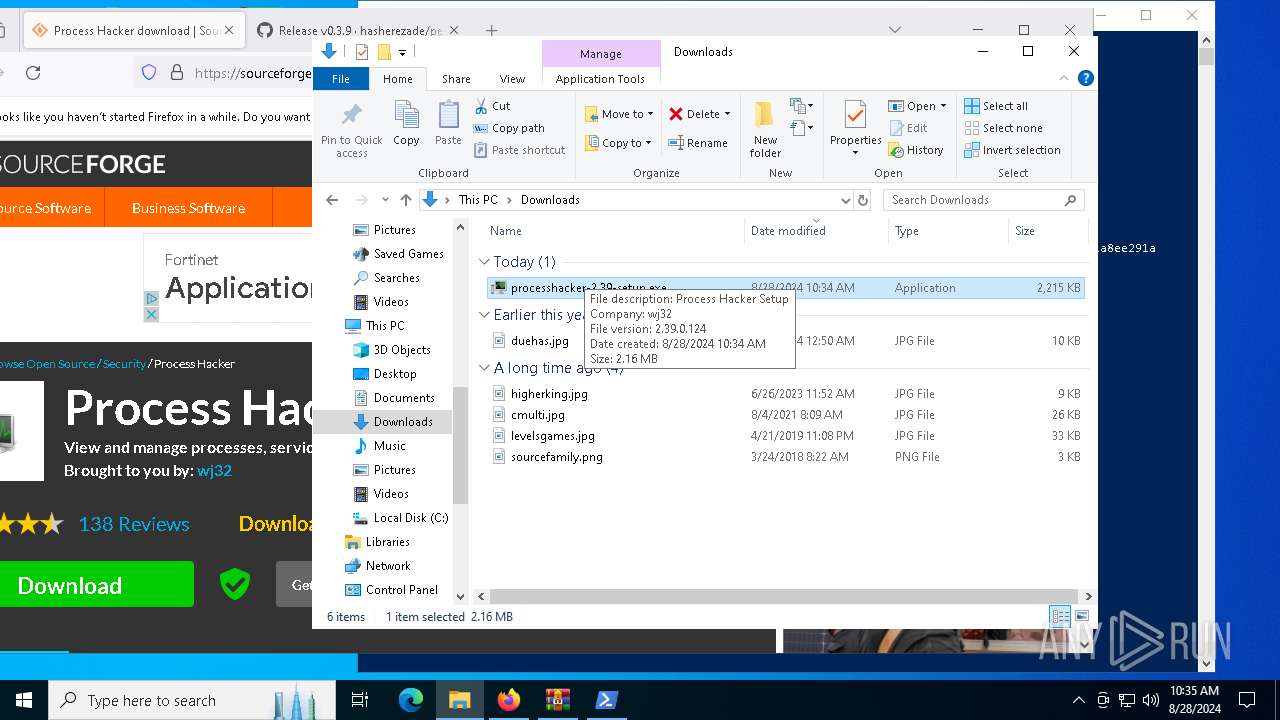
| 2144 | "C:\Users\admin\Downloads\processhacker-2.39-setup.exe" | C:\Users\admin\Downloads\processhacker-2.39-setup.exe | explorer.exe | ||||||||||||
User: admin Company: wj32 Integrity Level: MEDIUM Description: Process Hacker Setup Exit code: 0 Version: 2.39 (r124) Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2952 -childID 1 -isForBrowser -prefsHandle 2944 -prefMapHandle 2940 -prefsLen 30953 -prefMapSize 244343 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {cdc01011-ccac-48c4-aaab-4fd0c5c0b95f} 2876 "\\.\pipe\gecko-crash-server-pipe.2876" 2636cb6a150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6448 -childID 6 -isForBrowser -prefsHandle 6516 -prefMapHandle 6500 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {9ca0b6ad-d2c5-45a1-9790-a7bf8558ec2c} 2876 "\\.\pipe\gecko-crash-server-pipe.2876" 26372b084d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
79 861
Read events
79 564
Write events
283
Delete events
14
Modification events
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000701F4 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456033BCEE44DE41B4E8AEC331E84F566D2 | |||
| (PID) Process: | (5484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (5484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\vidarTest.zip | |||
| (PID) Process: | (5484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
49
Suspicious files
248
Text files
57
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4552 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 5484 | WinRAR.exe | C:\Users\admin\Desktop\532bc078a68683ce70cb765191a128fadee2a23180b1a8e8a16b72f1a8ee291a | executable | |
MD5:D305C0176DC9A1F3DAF516E6034F2B57 | SHA256:532BC078A68683CE70CB765191A128FADEE2A23180B1A8E8A16B72F1A8EE291A | |||
| 2876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:7D7EBDE5B6B5291A73AD982CC5800C8A | SHA256:F97E5FF1C76F2EBD06EFA89CEE826EC8E4C63B36EDC4E4BBC82F5FDE34D3AAAB | |||
| 2876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
79
TCP/UDP connections
269
DNS requests
345
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1752 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3568 | SIHClient.exe | GET | 200 | 23.213.169.249:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3568 | SIHClient.exe | GET | 200 | 23.213.169.249:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2876 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
2876 | firefox.exe | POST | 200 | 195.138.255.19:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
2876 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
2876 | firefox.exe | POST | 200 | 195.138.255.19:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
2876 | firefox.exe | POST | 200 | 195.138.255.19:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
2876 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
2876 | firefox.exe | POST | 200 | 195.138.255.19:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6516 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6244 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6516 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1752 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1752 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
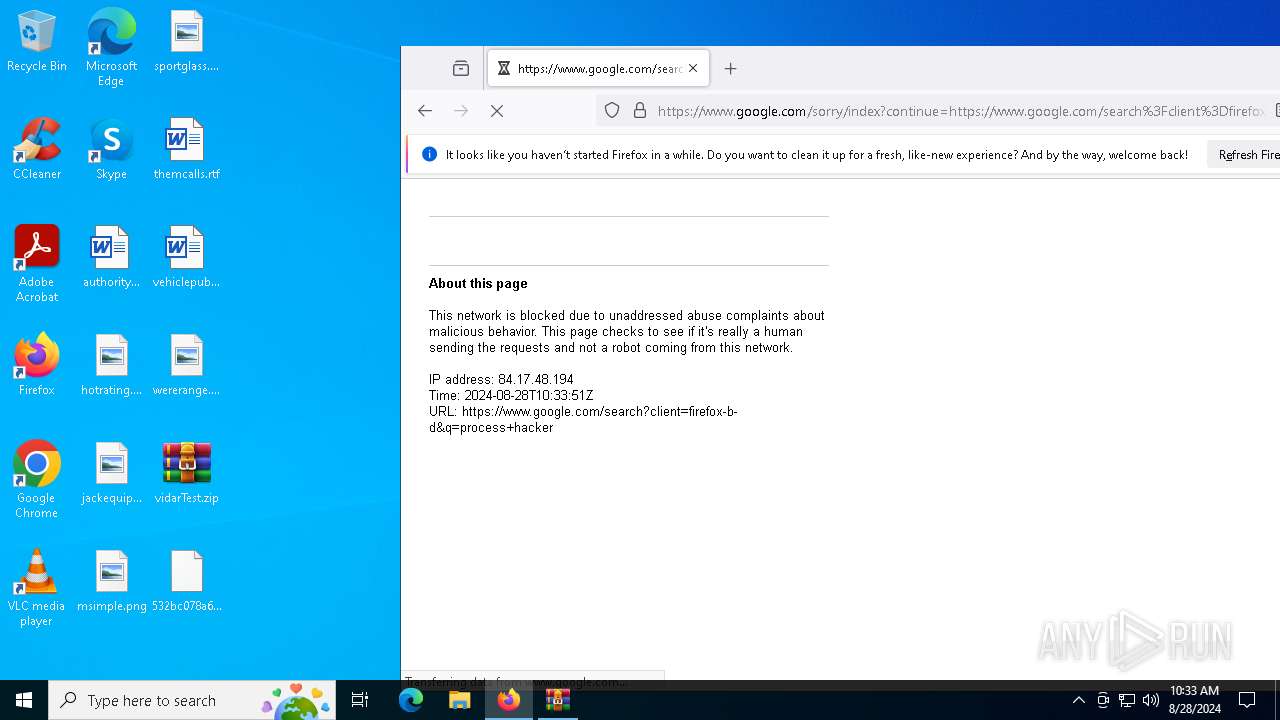
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
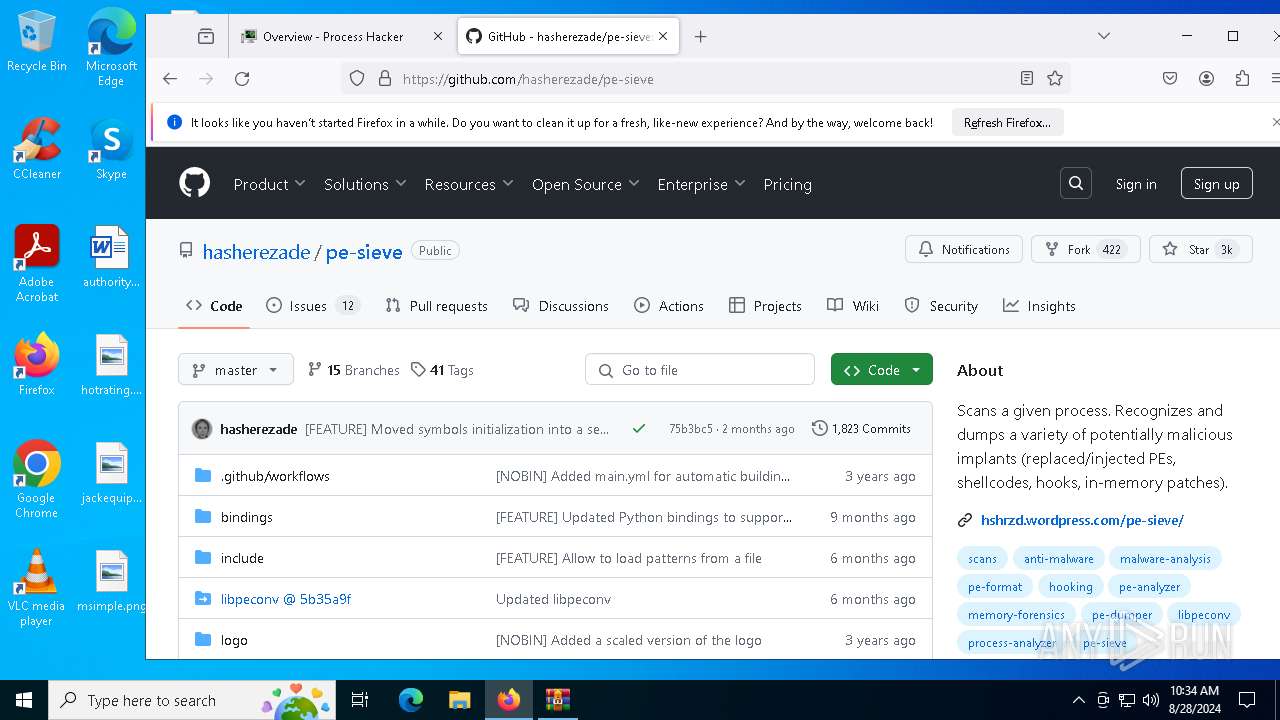
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |