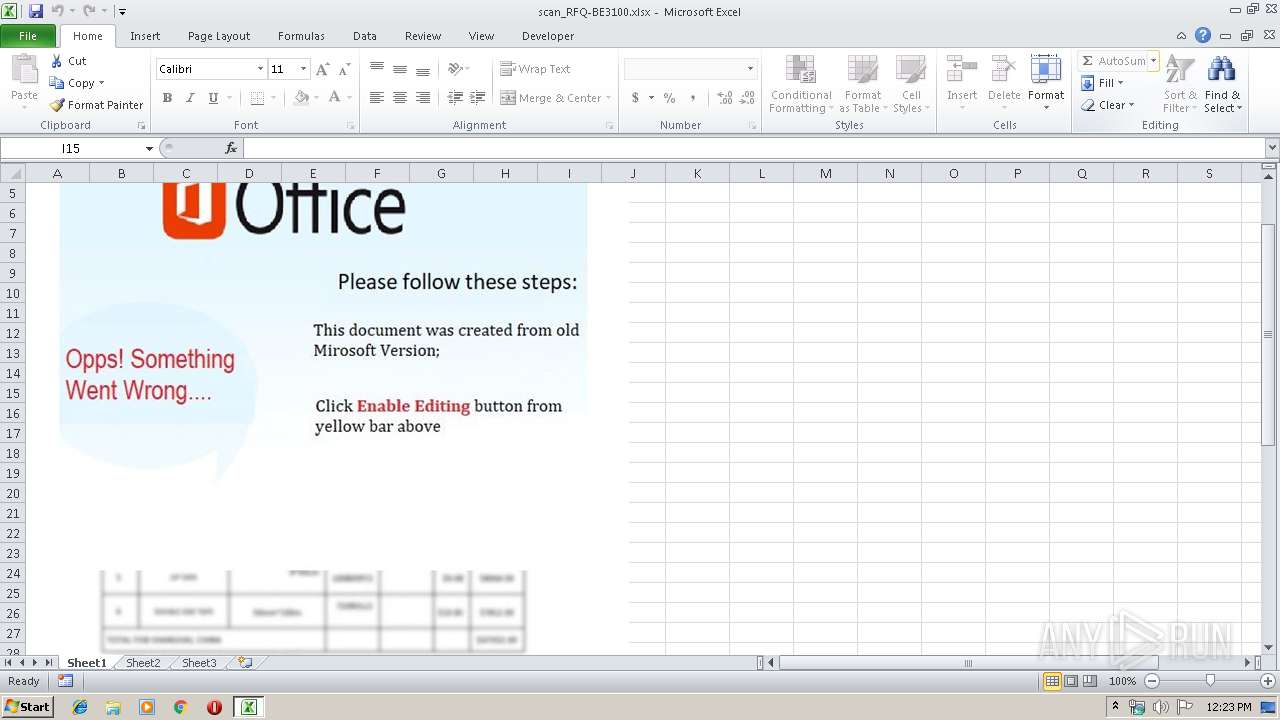
| File name: | scan_RFQ-BE3100.xlsx |
| Full analysis: | https://app.any.run/tasks/ab27140f-47e2-4d42-bac7-6d35399bb544 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | December 06, 2019, 12:23:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | 98F5B739247E5051A4964B469BC1ED4B |
| SHA1: | 5A3A0B0ADF48173748E3B9AD31FAD56A0B57B12A |
| SHA256: | 69FED657536E7E792031CF9D9CA05D38E8599317EA27F6E733AA309749D7BFB5 |
| SSDEEP: | 24576:BEk1rkfwKSsrrB01BcR/rRSYG2JGEuUkobQqXWcAU7d8inmTYJ:BEKkYHqrlx8VGZ0qGlUhLBJ |
MALICIOUS
Application was dropped or rewritten from another process
- vbc.exe (PID: 884)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2496)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 2496)
Changes the autorun value in the registry
- vbc.exe (PID: 884)
Actions looks like stealing of personal data
- vbc.exe (PID: 884)
AGENTTESLA detected
- vbc.exe (PID: 884)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 2496)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 2496)
Connects to SMTP port
- vbc.exe (PID: 884)
Reads Environment values
- vbc.exe (PID: 884)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 884 | "C:\Users\Public\vbc.exe" | C:\Users\Public\vbc.exe | EQNEDT32.EXE | ||||||||||||
User: admin Company: Rickard Johansson Integrity Level: MEDIUM Description: Supply Place Paid Apogee Exit code: 0 Version: 7.6.1.5 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
697
Read events
623
Write events
63
Delete events
11
Modification events
| (PID) Process: | (2572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | s6> |
Value: 73363E000C0A0000010000000000000000000000 | |||
| (PID) Process: | (2572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2572) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1334181913 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRAA73.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 884 | vbc.exe | C:\Users\admin\AppData\Local\Temp\74ae133c-e340-4f58-9b26-56d760ae1cd2 | sqlite | |
MD5:— | SHA256:— | |||
| 2496 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\vbc[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2496 | EQNEDT32.EXE | C:\Users\Public\vbc.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2496 | EQNEDT32.EXE | 216.170.118.183:80 | globalsharesecurefilesgood.duckdns.org | ColoCrossing | US | malicious |
884 | vbc.exe | 208.91.199.225:587 | us2.smtp.mailhostbox.com | PDR | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
globalsharesecurefilesgood.duckdns.org |
| malicious |
us2.smtp.mailhostbox.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2496 | EQNEDT32.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2496 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |