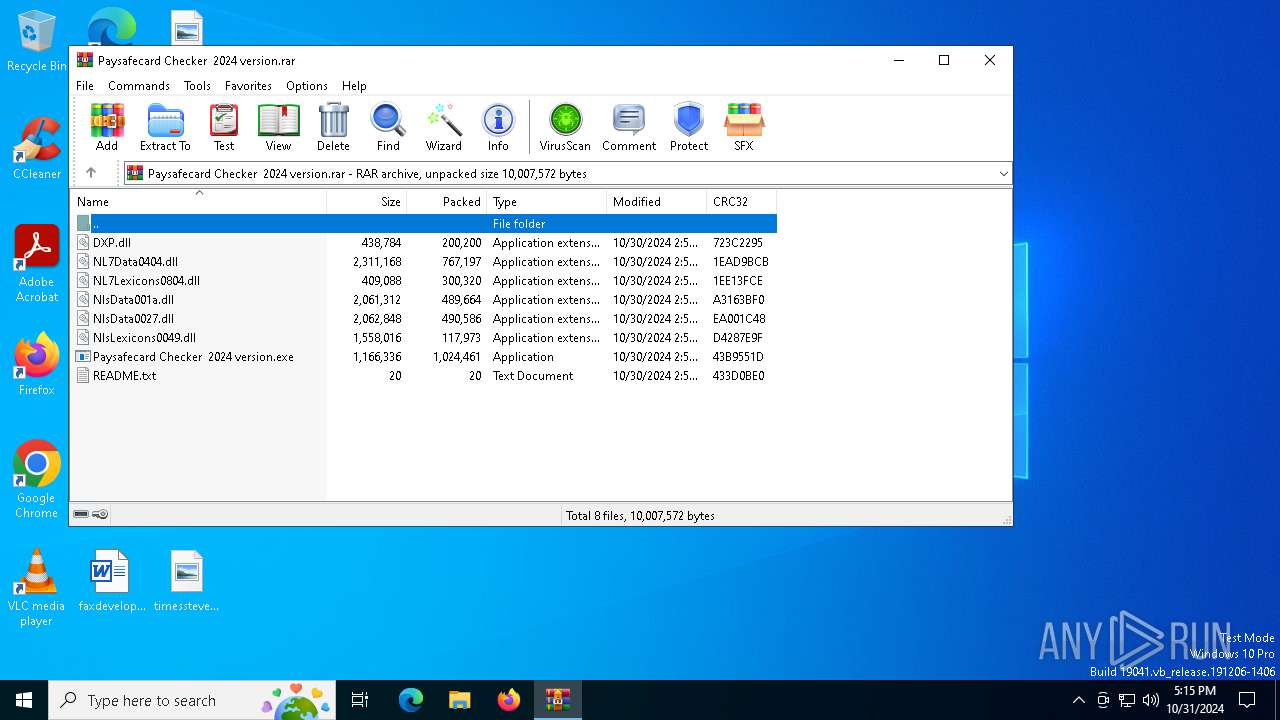
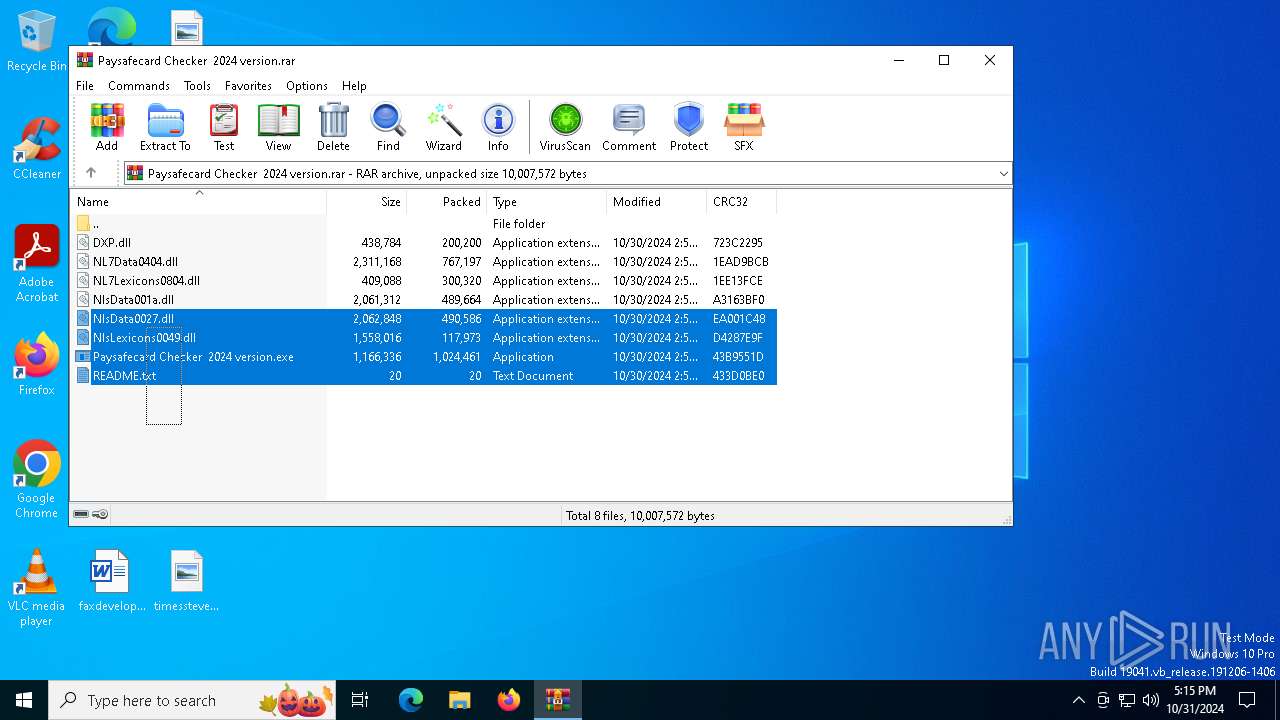
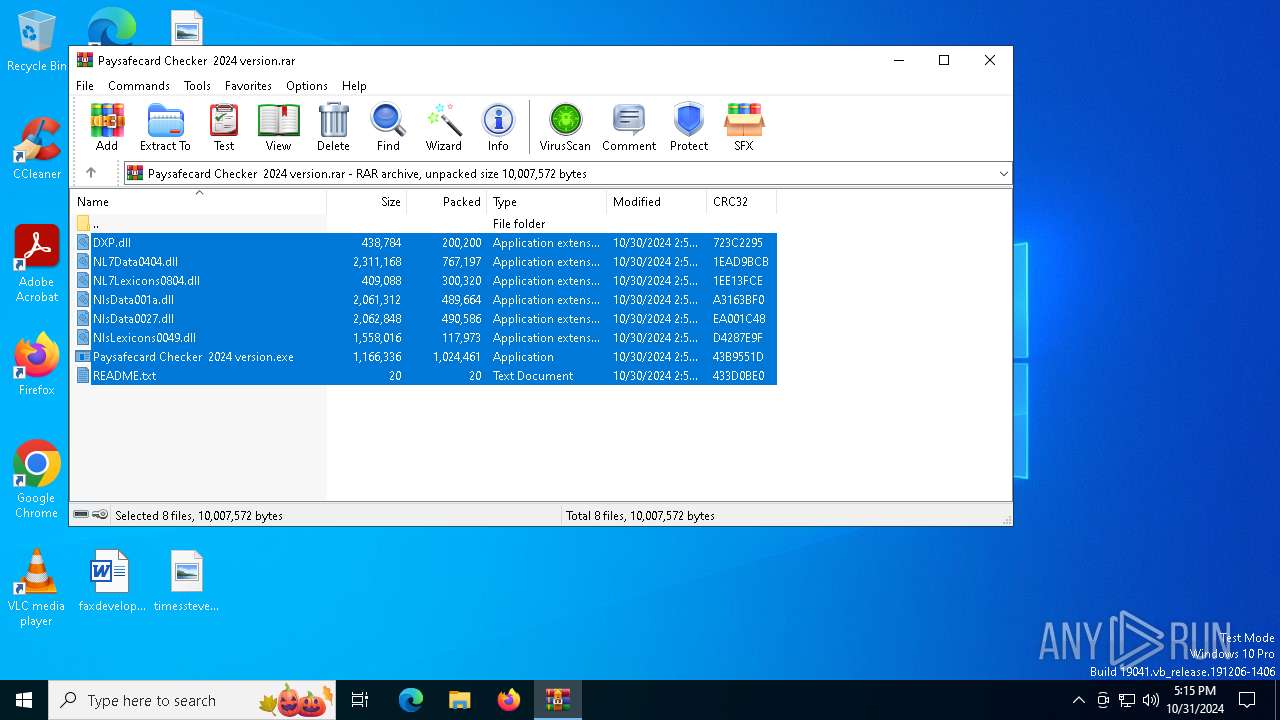
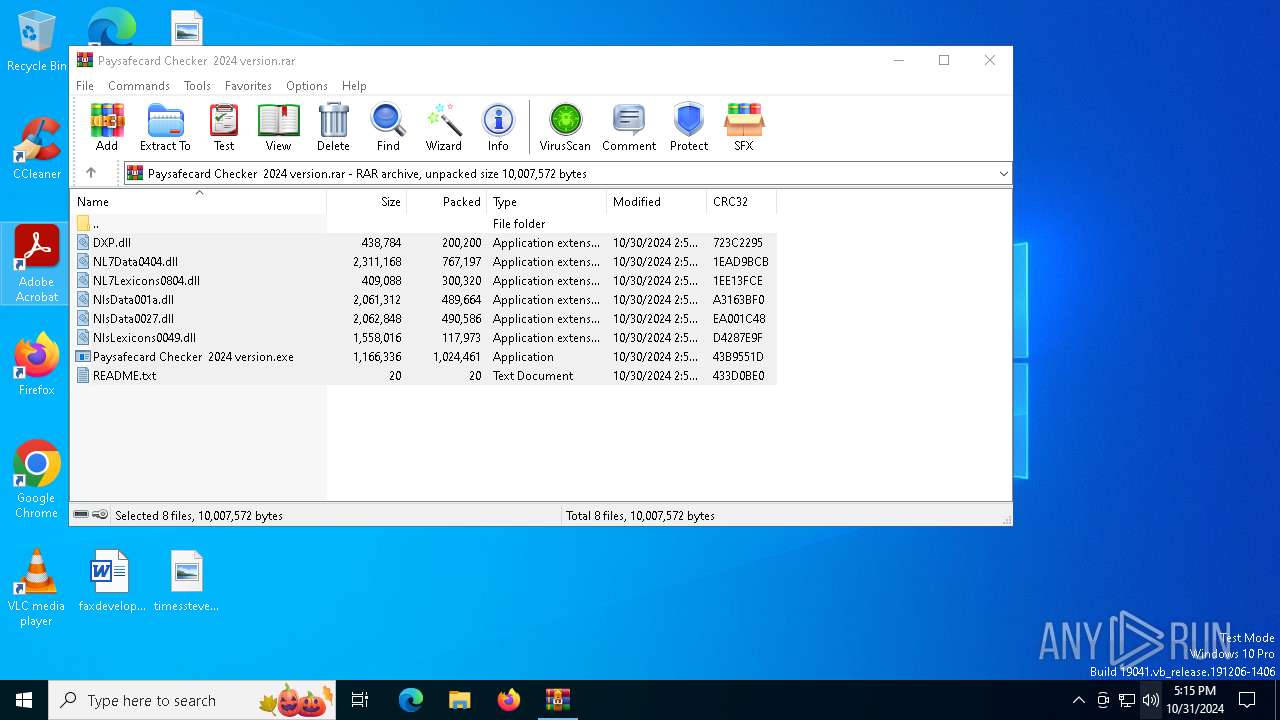
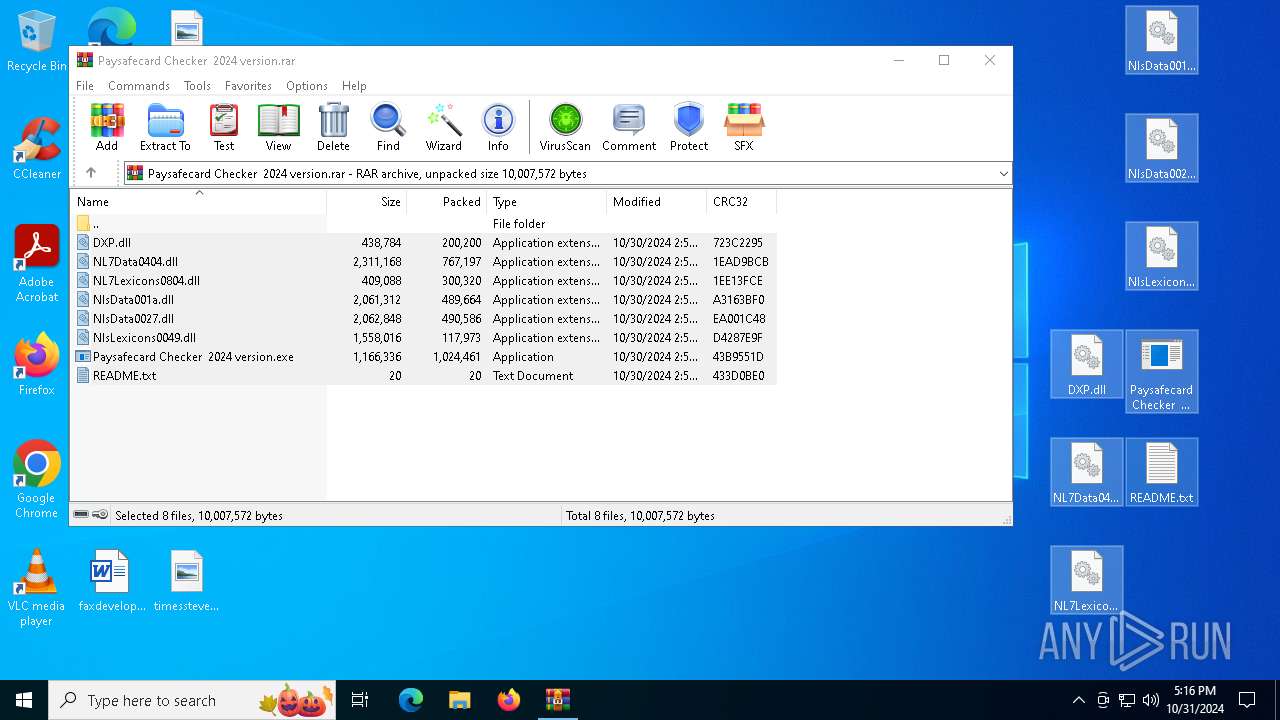
| File name: | Paysafecard Checker 2024 version.rar |
| Full analysis: | https://app.any.run/tasks/820d920b-08dc-48b2-862f-c97c5f5450e2 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | October 31, 2024, 17:15:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A70E87316FC171B16F5367AC32C232C9 |
| SHA1: | 49DD491863739292062C34A2EF961D95B3D48E98 |
| SHA256: | 69C431E7D4674465021B555CAF283684AC79B716471095D9A41BF1F8B1C1FADE |
| SSDEEP: | 98304:OIWrNlSVOBOGCEEuHdZMYW4DrzFehjVNfggalm56rMjWSv5tZP0p8uRyVA1LEuFN:cHsZxw |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2172)
- x9p7W6fjsZ.exe (PID: 6368)
Connects to the CnC server
- svchost.exe (PID: 2172)
Stealers network behavior
- x9p7W6fjsZ.exe (PID: 6368)
SUSPICIOUS
Application launched itself
- Paysafecard Checker 2024 version.exe (PID: 1452)
- x9p7W6fjsZ.exe (PID: 4680)
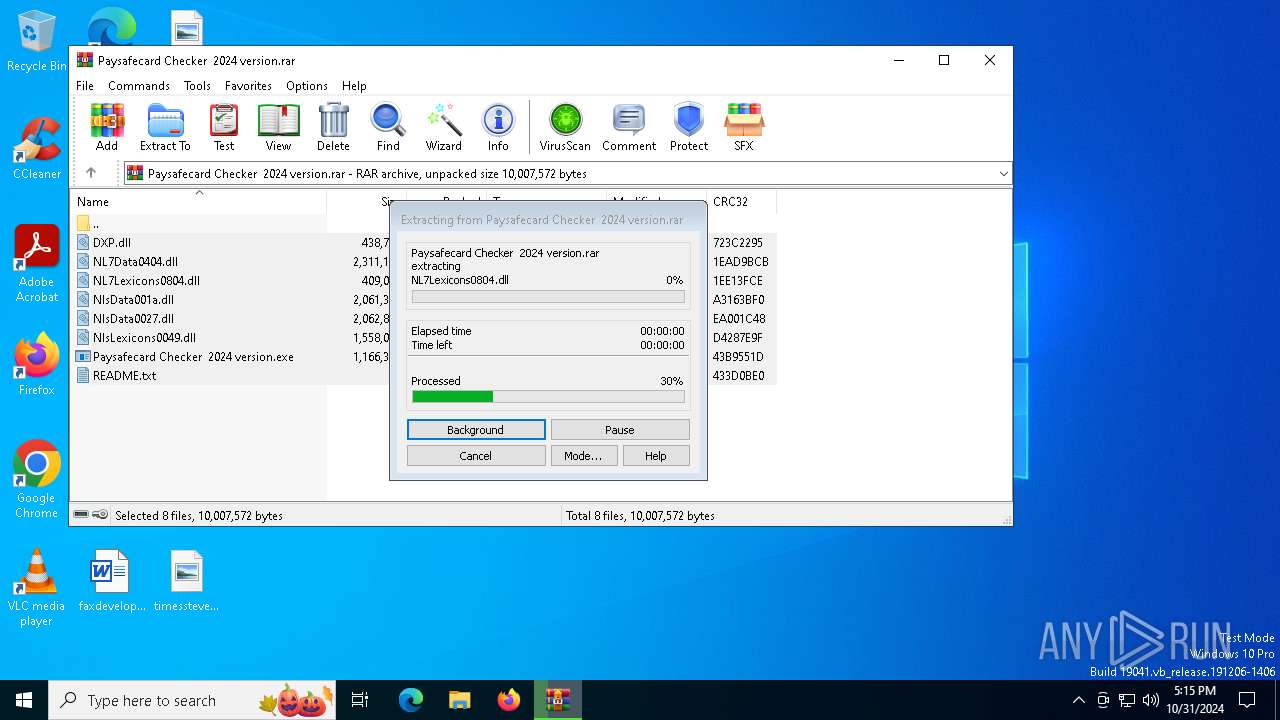
Process drops legitimate windows executable
- WinRAR.exe (PID: 6284)
Executes application which crashes
- x9p7W6fjsZ.exe (PID: 4680)
- Paysafecard Checker 2024 version.exe (PID: 1452)
Executable content was dropped or overwritten
- A93GkGBzOg.exe (PID: 6192)
- Paysafecard Checker 2024 version.exe (PID: 3644)
Contacting a server suspected of hosting an CnC
- x9p7W6fjsZ.exe (PID: 6368)
- svchost.exe (PID: 2172)
INFO
Manual execution by a user
- Paysafecard Checker 2024 version.exe (PID: 1452)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 1024461 |
| UncompressedSize: | 1166336 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Paysafecard Checker 2024 version.exe |
Total processes
148
Monitored processes
18
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1440 | "C:\Users\admin\Desktop\Paysafecard Checker 2024 version.exe" | C:\Users\admin\Desktop\Paysafecard Checker 2024 version.exe | — | Paysafecard Checker 2024 version.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1452 | "C:\Users\admin\Desktop\Paysafecard Checker 2024 version.exe" | C:\Users\admin\Desktop\Paysafecard Checker 2024 version.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1748 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | x9p7W6fjsZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3396 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3644 | "C:\Users\admin\Desktop\Paysafecard Checker 2024 version.exe" | C:\Users\admin\Desktop\Paysafecard Checker 2024 version.exe | Paysafecard Checker 2024 version.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3792 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 4680 -s 340 | C:\Windows\SysWOW64\WerFault.exe | x9p7W6fjsZ.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3844 | "C:\Users\admin\Desktop\Paysafecard Checker 2024 version.exe" | C:\Users\admin\Desktop\Paysafecard Checker 2024 version.exe | — | Paysafecard Checker 2024 version.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4348 | "C:\Users\admin\AppData\Roaming\x9p7W6fjsZ.exe" | C:\Users\admin\AppData\Roaming\x9p7W6fjsZ.exe | — | x9p7W6fjsZ.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4436 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 1452 -s 400 | C:\Windows\SysWOW64\WerFault.exe | Paysafecard Checker 2024 version.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 971
Read events
8 965
Write events
6
Delete events
0
Modification events
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Paysafecard Checker 2024 version.rar | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
10
Suspicious files
7
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6284.26903\Paysafecard Checker 2024 version.exe | executable | |
MD5:2ABFF13CFDBB439B7BD63D3BE7727689 | SHA256:61AEEB5A4A82B1083D1378EEFDB77AB7D30FC0B89566E6400387DEBAEDD64C37 | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6284.26903\DXP.dll | executable | |
MD5:9415D8364F64C603853D4CA27CECB3BA | SHA256:6D22ECE460948AEE682E72269C2907E2C04474FEE8ADFC4AC4619690F5DE7680 | |||
| 3792 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_x9p7W6fjsZ.exe_dacb4cb09bb283648456686373dca6e36ea6227_d1d90591_f0e3f311-e665-415b-81e8-68f27b73fb0d\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6284.26903\NlsLexicons0049.dll | executable | |
MD5:E502D97A5B970F25C49E9ACE1836FC80 | SHA256:2B931B863FB178271A17AE1F0567C1CF53F359753A7D7E716EE34CF0C8B18925 | |||
| 4436 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_Paysafecard Chec_9824be943f6e9f36a622739b5f4748f8eb9dcf_10c85bbc_8618ea32-fd70-475f-8d35-6c34b7f68cdb\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6284.26903\NlsData001a.dll | executable | |
MD5:2270A07CB2DA2660E7A50F8A697B2626 | SHA256:2BC32C88B35E61E614FD9ACF9F57C0C521941A9053254216AF84767075FC17CD | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6284.26903\NL7Data0404.dll | executable | |
MD5:81B14FD1C9D2B830E55C93C4C38AFA2F | SHA256:878E2DBAC4B6A6BCCE54742F3C7BFD87AA93A6637CCCC1E5D18AB65215D81BEE | |||
| 3644 | Paysafecard Checker 2024 version.exe | C:\Users\admin\AppData\Roaming\x9p7W6fjsZ.exe | executable | |
MD5:BED4B2D79AF6CAA405DDD29FB2626D85 | SHA256:AD05233BC1E74F41438D36F1EEA331DCC75EB08B2D939272098A93A8380F5C2D | |||
| 3644 | Paysafecard Checker 2024 version.exe | C:\Users\admin\AppData\Roaming\A93GkGBzOg.exe | executable | |
MD5:5AFB8CE4DD3923219BD69BD7B5168D91 | SHA256:F727BBA8D917FA3F129D71745E0741A8511F940B1A6817FF5130AA2F3AE85C79 | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6284.26903\NlsData0027.dll | executable | |
MD5:DD7B568F7B0DDCB39862485DF11B7758 | SHA256:DED1FBD837BE8BF6DC429035D13792C902CEA5A5AF6BAE847E4BE3BFF7258FFD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
53
DNS requests
25
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4436 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5196 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
3792 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1440 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
1440 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4700 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4436 | WerFault.exe | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
3792 | WerFault.exe | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4700 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
servicedny.site |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (seallysl .site) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (goalyfeastz .site) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (servicedny .site) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (opposezmny .site) |
6368 | x9p7W6fjsZ.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (goalyfeastz .site in TLS SNI) |
6368 | x9p7W6fjsZ.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
6368 | x9p7W6fjsZ.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (goalyfeastz .site in TLS SNI) |
6368 | x9p7W6fjsZ.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (goalyfeastz .site in TLS SNI) |
6368 | x9p7W6fjsZ.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (goalyfeastz .site in TLS SNI) |
6368 | x9p7W6fjsZ.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (goalyfeastz .site in TLS SNI) |