| File name: | file |
| Full analysis: | https://app.any.run/tasks/eb27eaa4-f7ac-4c69-a30d-1f9b49deee90 |
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | September 28, 2024, 07:04:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 72025394A2450241BCE7DF7E305CD07B |
| SHA1: | 018B6C066C915BA37616661F86C09E453D58FD66 |
| SHA256: | 69B153CD6176D790D2AAE37CCC5600BDE475A0ECA6D1F6F531A1E040D44BCCD1 |
| SSDEEP: | 48:YngHEZ9NkLczlEaq/J4KK4SRcMnZbECSaM7ZHftGJr/mckuliL/qXSfbNtm:IuE5dzlwinZbqlwKy0LxzNt |
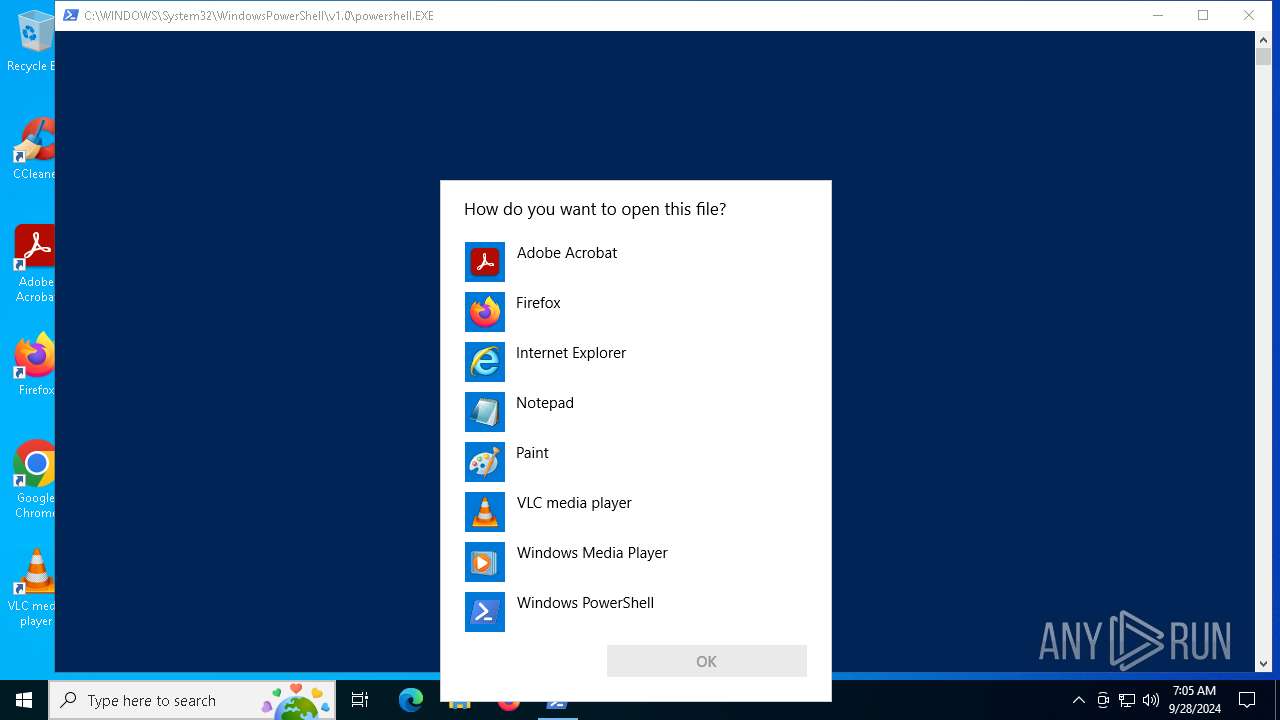
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6336)
- powershell.exe (PID: 1084)
- powershell.exe (PID: 5996)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 6308)
- powershell.exe (PID: 3448)
Uses WMIC.EXE to add exclusions to the Windows Defender
- powershell.exe (PID: 1084)
- powershell.exe (PID: 3448)
Uses Task Scheduler to run other applications
- Install.exe (PID: 2372)
- Install.exe (PID: 1652)
- xfpXgNi.exe (PID: 2008)
Application was injected by another process
- explorer.exe (PID: 4552)
Runs injected code in another process
- setup1.exe (PID: 5056)
SMOKE has been detected (SURICATA)
- explorer.exe (PID: 4552)
XORed URL has been found (YARA)
- Install.exe (PID: 2372)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2256)
- BitLockerToGo.exe (PID: 4596)
Connects to the CnC server
- svchost.exe (PID: 2256)
Stealers network behavior
- BitLockerToGo.exe (PID: 4596)
NEOREKLAMI has been detected (SURICATA)
- rundll32.exe (PID: 4472)
Uses Task Scheduler to autorun other applications
- xfpXgNi.exe (PID: 2008)
SUSPICIOUS
Executable content was dropped or overwritten
- file.exe (PID: 6968)
- setup.exe (PID: 6080)
- Install.exe (PID: 2112)
- stories.tmp (PID: 1492)
- stories.exe (PID: 5084)
- playglock.exe (PID: 2368)
- explorer.exe (PID: 4552)
- Install.exe (PID: 1652)
- xfpXgNi.exe (PID: 2008)
Reads security settings of Internet Explorer
- file.exe (PID: 6968)
Potential Corporate Privacy Violation
- file.exe (PID: 6968)
Drops 7-zip archiver for unpacking
- file.exe (PID: 6968)
- setup.exe (PID: 6080)
Creates file in the systems drive root
- file.exe (PID: 6968)
Reads the date of Windows installation
- file.exe (PID: 6968)
Process requests binary or script from the Internet
- file.exe (PID: 6968)
Connects to the server without a host name
- file.exe (PID: 6968)
Starts itself from another location
- setup.exe (PID: 6080)
Found strings related to reading or modifying Windows Defender settings
- Install.exe (PID: 2372)
- forfiles.exe (PID: 5164)
- forfiles.exe (PID: 4196)
- forfiles.exe (PID: 4888)
- forfiles.exe (PID: 7164)
- forfiles.exe (PID: 4004)
- Install.exe (PID: 1652)
- forfiles.exe (PID: 440)
- forfiles.exe (PID: 6744)
- forfiles.exe (PID: 5524)
- forfiles.exe (PID: 1504)
- powershell.exe (PID: 3360)
- powershell.exe (PID: 2836)
- xfpXgNi.exe (PID: 2008)
- forfiles.exe (PID: 4476)
- forfiles.exe (PID: 2040)
- forfiles.exe (PID: 1256)
- forfiles.exe (PID: 1252)
- forfiles.exe (PID: 1460)
Starts CMD.EXE for commands execution
- forfiles.exe (PID: 4196)
- Install.exe (PID: 2372)
- forfiles.exe (PID: 5164)
- forfiles.exe (PID: 4888)
- forfiles.exe (PID: 4004)
- forfiles.exe (PID: 4684)
- forfiles.exe (PID: 7164)
- Install.exe (PID: 1652)
- forfiles.exe (PID: 440)
- forfiles.exe (PID: 6744)
- forfiles.exe (PID: 5524)
- forfiles.exe (PID: 812)
- powershell.exe (PID: 3360)
- powershell.exe (PID: 2836)
- forfiles.exe (PID: 1504)
- xfpXgNi.exe (PID: 2008)
- forfiles.exe (PID: 4476)
- forfiles.exe (PID: 2040)
- forfiles.exe (PID: 1256)
- forfiles.exe (PID: 1252)
- forfiles.exe (PID: 5964)
- forfiles.exe (PID: 1460)
Searches and executes a command on selected files
- forfiles.exe (PID: 5164)
- forfiles.exe (PID: 4196)
- forfiles.exe (PID: 4888)
- forfiles.exe (PID: 4004)
- forfiles.exe (PID: 4684)
- forfiles.exe (PID: 7164)
- forfiles.exe (PID: 440)
- forfiles.exe (PID: 6744)
- forfiles.exe (PID: 5524)
- forfiles.exe (PID: 1504)
- forfiles.exe (PID: 812)
- forfiles.exe (PID: 4476)
- forfiles.exe (PID: 2040)
- forfiles.exe (PID: 1256)
- forfiles.exe (PID: 1252)
- forfiles.exe (PID: 1460)
- forfiles.exe (PID: 5964)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3728)
- cmd.exe (PID: 240)
- cmd.exe (PID: 5056)
- cmd.exe (PID: 4820)
- cmd.exe (PID: 188)
- cmd.exe (PID: 4440)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 2036)
- cmd.exe (PID: 2524)
- powershell.exe (PID: 3360)
- cmd.exe (PID: 2912)
- powershell.exe (PID: 2836)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 376)
- cmd.exe (PID: 4472)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4560)
- cmd.exe (PID: 2872)
- cmd.exe (PID: 908)
- Install.exe (PID: 1652)
- cmd.exe (PID: 1148)
- cmd.exe (PID: 6828)
Powershell scripting: start process
- cmd.exe (PID: 4560)
- cmd.exe (PID: 908)
- cmd.exe (PID: 1148)
Process drops legitimate windows executable
- stories.tmp (PID: 1492)
The process drops C-runtime libraries
- stories.tmp (PID: 1492)
The process executes via Task Scheduler
- Install.exe (PID: 1652)
- powershell.exe (PID: 6800)
- xfpXgNi.exe (PID: 2008)
- rundll32.exe (PID: 4748)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2256)
- BitLockerToGo.exe (PID: 4596)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 5600)
- schtasks.exe (PID: 2352)
- schtasks.exe (PID: 2360)
- schtasks.exe (PID: 1256)
- schtasks.exe (PID: 2036)
Executes application which crashes
- Install.exe (PID: 1652)
- Install.exe (PID: 2372)
- xfpXgNi.exe (PID: 2008)
Access to an unwanted program domain was detected
- rundll32.exe (PID: 4472)
INFO
Reads Environment values
- file.exe (PID: 6968)
Disables trace logs
- file.exe (PID: 6968)
Reads the machine GUID from the registry
- file.exe (PID: 6968)
Checks supported languages
- file.exe (PID: 6968)
- setup.exe (PID: 6080)
Checks proxy server information
- file.exe (PID: 6968)
Reads the computer name
- file.exe (PID: 6968)
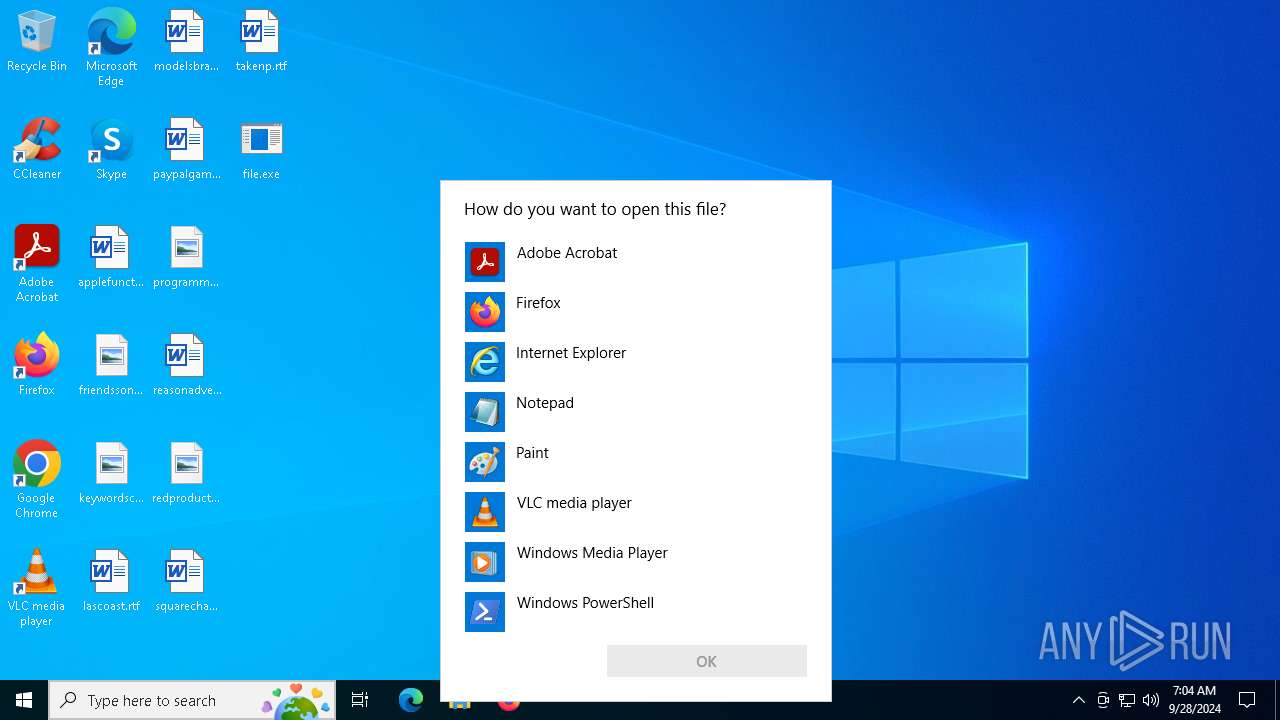
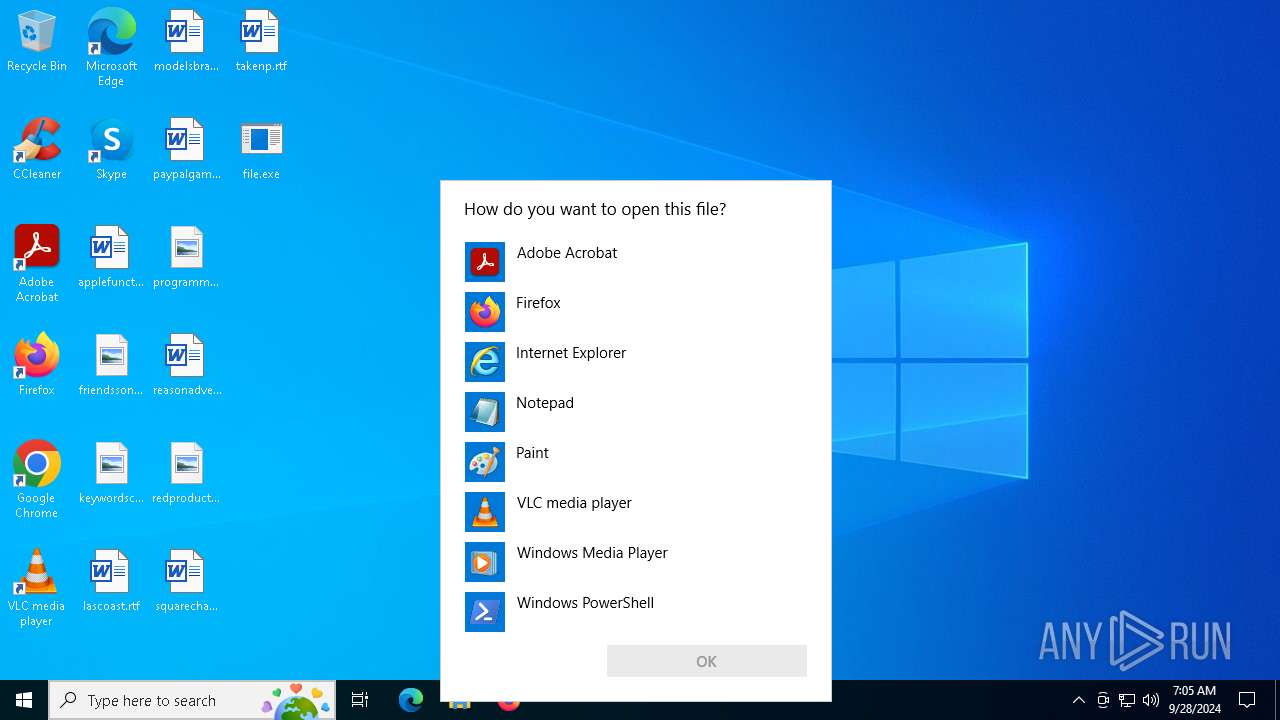
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4720)
The process uses the downloaded file
- file.exe (PID: 6968)
Process checks computer location settings
- file.exe (PID: 6968)
Create files in a temporary directory
- setup.exe (PID: 6080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(2372) Install.exe
Decrypted-URLs (29)http://api.check-data.xyz
http://api2.check-data.xyz
http://api3.check-data.xyz
http://api4.check-data.xyz
http://api5.check-data.xyz
http://helsinki-dtc.com/clrls/cl_rls.json
http://helsinki-dtc.com/updates/yd/wrtzr_yt_a_1/win/update_e.jpg
http://helsinki-dtc.com/updates/yd/wrtzr_yt_a_1/win/version.txt
http://skrptfiles.tracemonitors.com/clrls/cl_rls.json
http://skrptfiles.tracemonitors.com/updates/yd/wrtzr_yt_a_1/win/update_e.jpg3
http://skrptfiles.tracemonitors.com/updates/yd/wrtzr_yt_a_1/win/version.txt
http://www.rapidfilestorage.com/clrls/cl_rls.json
http://www.rapidfilestorage.com/updates/yd/wrtzr_yt_a_1/win/update_e.jpg
http://www.rapidfilestorage.com/updates/yd/wrtzr_yt_a_1/win/version.txt
https://api.fetch-api.comL
https://api.fetch-api.comM
https://rmtexts.fetch-api.com/google_ifi_ico.png
https://service-domain.xyz/google_ifi_ico.pngO
https://www.google.com/?h=15gfigoky0yidmgsfz0cpzkop82pv1d1kzup.prvyl0ii0
https://www.google.com/?h=42f6od641m7cwdq4el5np41md1zngfir9863.02nfw3obl
https://www.google.com/?h=4py6y4f63yomtkzthf0vliiw5g06q3fhp9h1.0uf38fx1b
https://www.google.com/?h=52x06k33mh5cdi7ed0pyobzborkaow6nxksq.5d15mfc0i
https://www.google.com/?h=5qc5etyut00x6df5nv8scd9ahvq4532s99t4.r1prjhqaj#
https://www.google.com/?h=6p0jxxs43obizbc14pxs8ve46mfh1fgyfomh.nhh4pjxu8
https://www.google.com/?h=deq16e06s1blnmuorvzzwr035pdx0vgooxkb.1xvwvg4ju
https://www.google.com/?h=jn87cg3z0mxll39u6m2q14cpn3hyrwgfklei.1qt1kyvk5
https://www.google.com/?h=jsdiq8xf7ic5mw4o3u4js81nub9a52b7im0k.bg7lsc44a
https://www.google.com/?h=md8vgx0vjeebrt7ncv.3510wvesh25r9mbx8d
https://www.google.com/?h=zhmbuwqv0cjs9i36d3gkutlvv2w22yuxgs29.qz6n4q80z?
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:09:26 19:08:17+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 2560 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x281e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | CustomDropper.exe |
| LegalCopyright: | |
| OriginalFileName: | CustomDropper.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
332
Monitored processes
186
Malicious processes
16
Suspicious processes
21
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | /C reg add "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Threats\ThreatIDDefaultAction" /f /v 2147735503 /t REG_SZ /d 6 | C:\Windows\SysWOW64\cmd.exe | — | forfiles.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | /C reg add "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Threats\ThreatIDDefaultAction" /f /v 2147814524 /t REG_SZ /d 6 | C:\Windows\SysWOW64\cmd.exe | — | forfiles.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | /C reg add "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Threats\ThreatIDDefaultAction" /f /v 2147780199 /t REG_SZ /d 6 | C:\Windows\SysWOW64\cmd.exe | — | forfiles.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | "C:\WINDOWS\system32\reg.exe" ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Exclusions\Paths" /f /v "C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extensions" /t REG_DWORD /d 0 /reg:32 | C:\Windows\SysWOW64\reg.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | forfiles /p c:\windows\system32 /m where.exe /c "cmd /C reg add \"HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Threats\ThreatIDDefaultAction\" /f /v 2147735503 /t REG_SZ /d 6" | C:\Windows\SysWOW64\forfiles.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: ForFiles - Executes a command on selected files Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | "C:\WINDOWS\system32\reg.exe" ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Threats\ThreatIDDefaultAction" /f /v 256596 /t REG_SZ /d 6 /reg:64 | C:\Windows\SysWOW64\reg.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | reg add "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Threats\ThreatIDDefaultAction" /f /v 2147814524 /t REG_SZ /d 6 | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | schtasks /CREATE /TN "CVvOFbqbJLRHBH" /F /xml "C:\Program Files (x86)\bvOaypMPnvJU2\eyWzmLT.xml" /RU "SYSTEM" | C:\Windows\SysWOW64\schtasks.exe | — | xfpXgNi.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
65 362
Read events
65 168
Write events
177
Delete events
17
Modification events
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010014000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C00000017000000000000006100700070006C006500660075006E006300740069006F006E0061006C002E007200740066003E00200020000000130000000000000066007200690065006E006400730073006F006E0067002E0070006E0067003E0020002000000017000000000000006B006500790077006F007200640073006300680069006300610067006F002E006A00700067003E0020002000000010000000000000006C006100730063006F006100730074002E007200740066003E0020002000000013000000000000006D006F00640065006C0073006200720061006E0064002E007200740066003E002000200000001200000000000000700061007900700061006C00670061006D0065002E007200740066003E002000200000001C00000000000000700072006F006700720061006D006D0069006E0067007200650073006F00750072006300650073002E0070006E0067003E00200020000000170000000000000072006500610073006F006E006100640076006500720074006900730065002E007200740066003E002000200000001500000000000000720065006400700072006F00640075006300740069006F006E002E006A00700067003E0020002000000015000000000000007300710075006100720065006300680061006E006700650073002E007200740066003E002000200000000E00000000000000740061006B0065006E0070002E007200740066003E002000200000000C00000000000000660069006C0065002E006500780065003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001400000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A040110000004040000000001200000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F0700000040400000803F1300 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 78AAF76600000000 | |||
| (PID) Process: | (6968) file.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\file_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6968) file.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\file_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6968) file.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\file_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6968) file.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\file_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6968) file.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\file_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6968) file.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\file_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6968) file.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\file_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
35
Suspicious files
58
Text files
171
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2112 | Install.exe | C:\Users\admin\AppData\Local\Temp\7zS8143.tmp\Install.exe | executable | |
MD5:75FB5F8595A2C77B6616A5DBBDFA5696 | SHA256:804534351D0EA162EECC1CEB26F7918026595EF1AFF3C6B00BEC38E1541CA6E2 | |||
| 6080 | setup.exe | C:\Users\admin\AppData\Local\Temp\7zS7EB3.tmp\__data__\config.txt | binary | |
MD5:9E0A8A3BB43F6543B2B5F71F7D37AD15 | SHA256:078058F423A02499CD971B8AD417A088375A4A9375E36A02C157F346F157A64D | |||
| 6336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kaof2p4g.uj4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6080 | setup.exe | C:\Users\admin\AppData\Local\Temp\7zS7EB3.tmp\Install.exe | executable | |
MD5:54A80AF0685D8A1774F702DB3EE8DBF5 | SHA256:CCF138DBE48D0F872D211FC33FF2DE13EDB62A74BA1C1B45A5F0D81248BC46F6 | |||
| 4552 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 6968 | file.exe | C:\Users\admin\Documents\setup.exe | executable | |
MD5:391D4A464150942614B3E6A25C1EB9DC | SHA256:518D13A8D88566E280E58CC91DD9FA1C97D82ED3B256A6504C1971114492EFD5 | |||
| 6968 | file.exe | C:\Users\admin\Documents\dl | executable | |
MD5:C05C46864AF307C06701475FA06D9CA9 | SHA256:87338960977EB02308FE965EDF8B001C2CD60D81C4EF3192E97B4427FFF20B45 | |||
| 1492 | stories.tmp | C:\Users\admin\AppData\Local\Play Glock\uninstall\unins000.exe | executable | |
MD5:5A94849E9977B873F74342EB3FCF1FDD | SHA256:C2A9F622686BD8EB3E66A1A211EE89784E670E03B9353D39233CD8C947E6B218 | |||
| 1492 | stories.tmp | C:\Users\admin\AppData\Local\Temp\is-D163H.tmp\_isetup\_iscrypt.dll | executable | |
MD5:A69559718AB506675E907FE49DEB71E9 | SHA256:2F6294F9AA09F59A574B5DCD33BE54E16B39377984F3D5658CDA44950FA0F8FC | |||
| 1492 | stories.tmp | C:\Users\admin\AppData\Local\Play Glock\uninstall\is-FR5SP.tmp | executable | |
MD5:5A94849E9977B873F74342EB3FCF1FDD | SHA256:C2A9F622686BD8EB3E66A1A211EE89784E670E03B9353D39233CD8C947E6B218 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
56
DNS requests
32
Threats
71
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7108 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6968 | file.exe | GET | 200 | 103.130.147.211:80 | http://103.130.147.211/Files/setup.exe | unknown | — | — | unknown |
6968 | file.exe | GET | 200 | 80.66.75.114:80 | http://80.66.75.114/dl?name=mixnine.exe | unknown | — | — | unknown |
6968 | file.exe | GET | — | 103.130.147.211:80 | http://103.130.147.211/Files/Channel2.exe | unknown | — | — | unknown |
6968 | file.exe | GET | 200 | 147.45.60.44:80 | http://marafon.in/dergrherg/setup1.exe | unknown | — | — | unknown |
6968 | file.exe | GET | 200 | 176.113.115.95:80 | http://176.113.115.95/thebig/stories.exe | unknown | — | — | unknown |
4552 | explorer.exe | POST | 404 | 116.58.10.60:80 | http://nwgrus.ru/tmp/index.php | unknown | — | — | malicious |
6968 | file.exe | GET | 200 | 103.130.147.211:80 | http://103.130.147.211/Files/CheckTool.exe | unknown | — | — | unknown |
6968 | file.exe | GET | 404 | 103.130.147.211:80 | http://103.130.147.211/Files/Channel2.exe | unknown | — | — | unknown |
4472 | rundll32.exe | POST | 200 | 44.235.67.161:80 | http://api3.check-data.xyz/api2/google_api_ifi | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7108 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6968 | file.exe | 80.66.75.114:80 | — | Kakharov Orinbassar Maratuly | RU | malicious |
7108 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6968 | file.exe | 103.130.147.211:80 | — | — | TR | malicious |
6968 | file.exe | 176.113.115.95:80 | — | Red Bytes LLC | RU | malicious |
6968 | file.exe | 147.45.60.44:80 | marafon.in | OOO FREEnet Group | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
marafon.in |
| unknown |
nwgrus.ru |
| malicious |
keennylrwmqlw.shop |
| malicious |
watson.events.data.microsoft.com |
| whitelisted |
licenseodqwmqn.shop |
| malicious |
tendencctywop.shop |
| malicious |
tesecuuweqo.shop |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6968 | file.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 8 |
6968 | file.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6968 | file.exe | Misc activity | ET INFO Packed Executable Download |
6968 | file.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6968 | file.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6968 | file.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
6968 | file.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6968 | file.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6968 | file.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6968 | file.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |