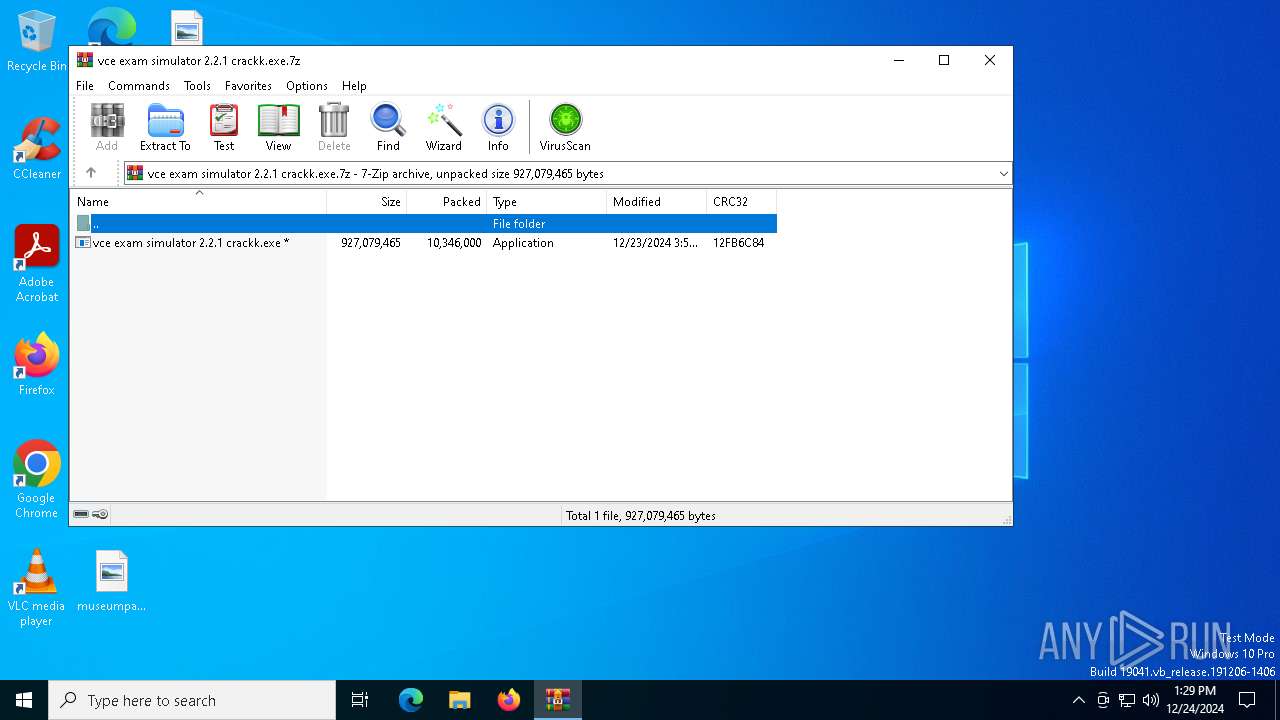
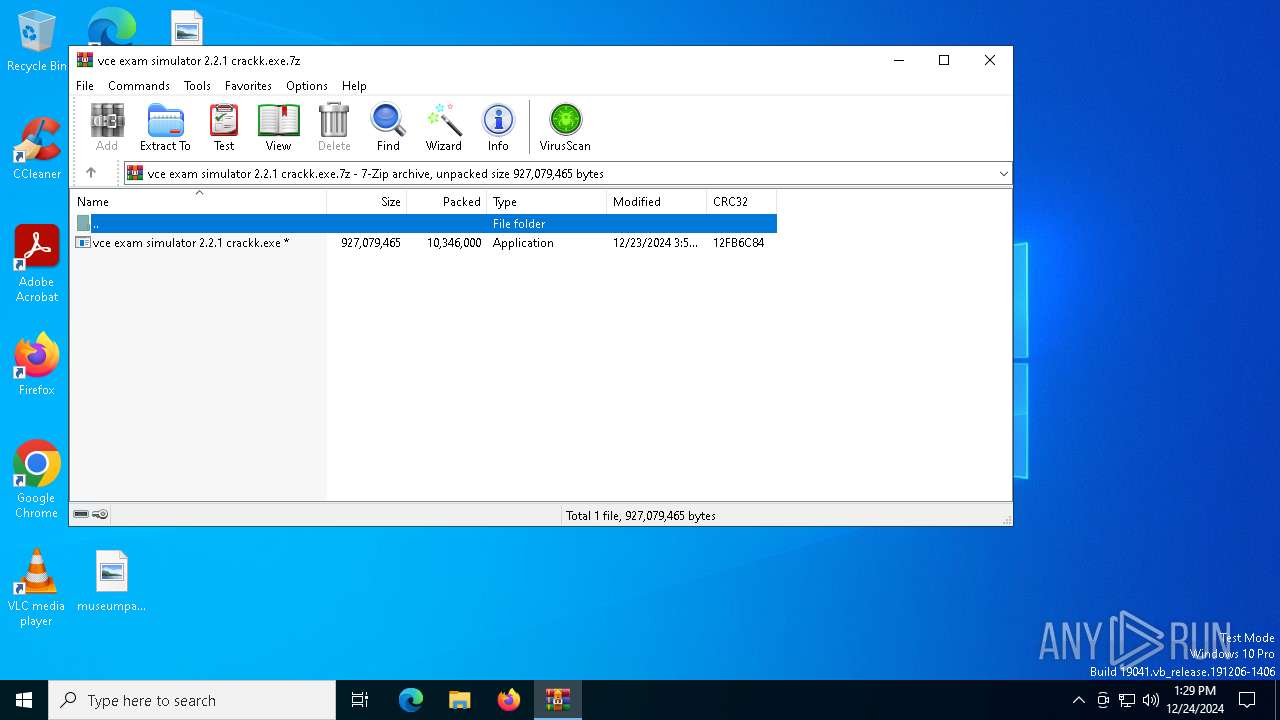
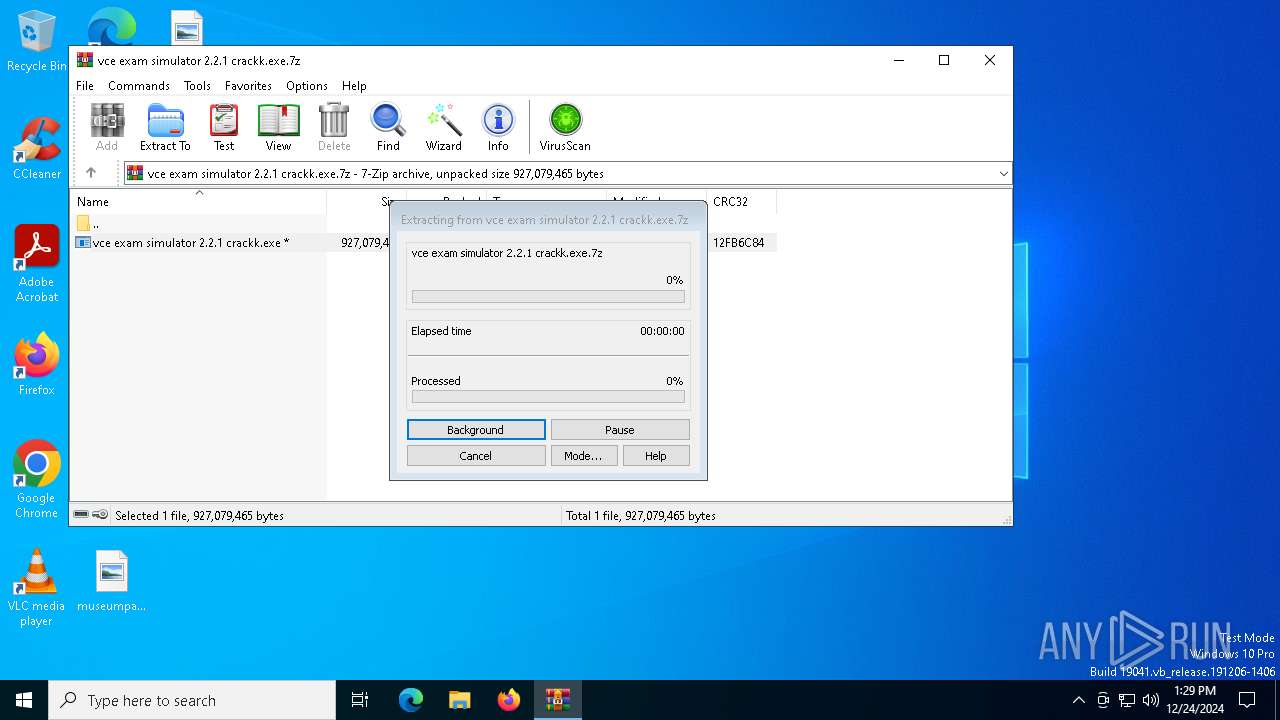
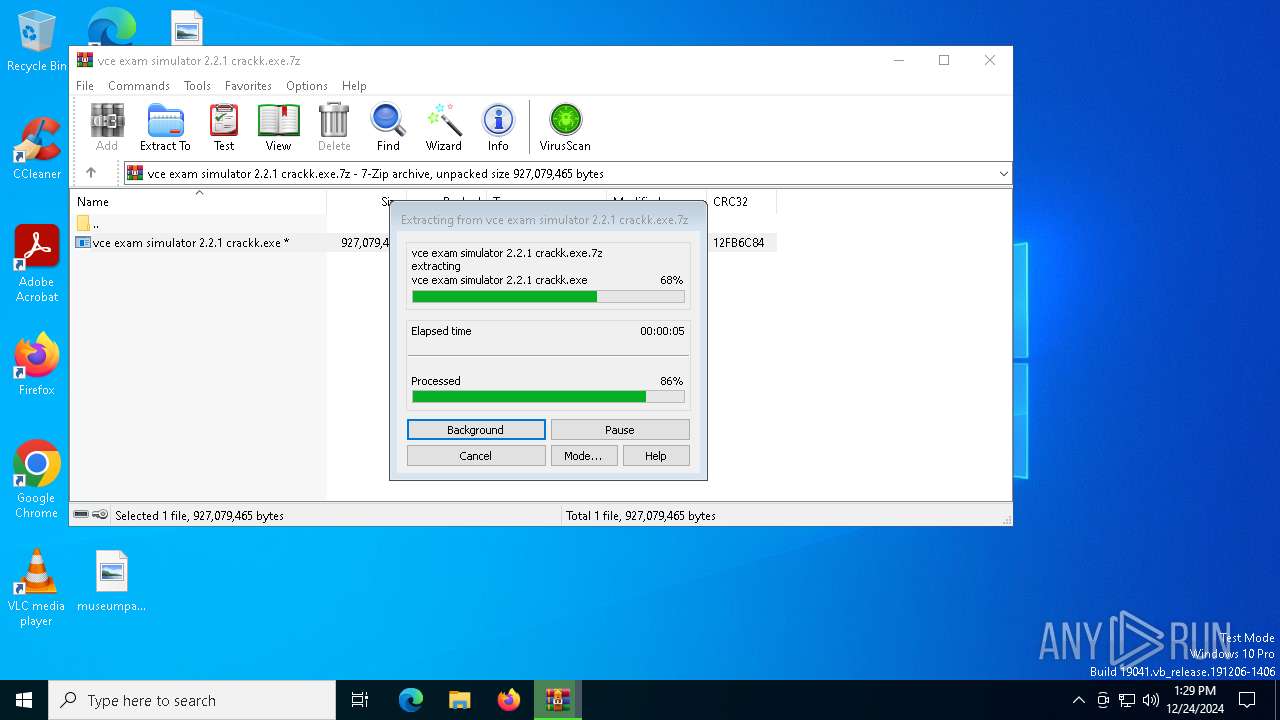
| File name: | vce exam simulator 2.2.1 crackk.exe.7z |
| Full analysis: | https://app.any.run/tasks/9228a23a-03c7-4a85-a5de-4affa7b99152 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 24, 2024, 13:28:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 378A971A95BB276C228672FDC2A1E595 |
| SHA1: | 661A1A821E6315956129D35937097E44C585CB02 |
| SHA256: | 69AC649458FA7302CF7DBFD117B8C8852396C000A40BBEB77623AA4DD6DD695A |
| SSDEEP: | 98304:bQU9iF3Wt84qz9xW/AY3+lFFJhBn05Ij8eiGc6QMQjTAraFjgwT3CCrt7iOIVTez:/S9wMJyh8pFDbgqz0I |
MALICIOUS
AutoIt loader has been detected (YARA)
- Spa.com (PID: 4952)
LUMMA mutex has been found
- Spa.com (PID: 4952)
Steals credentials from Web Browsers
- Spa.com (PID: 4952)
Actions looks like stealing of personal data
- Spa.com (PID: 4952)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6244)
- vce exam simulator 2.2.1 crackk.exe (PID: 7136)
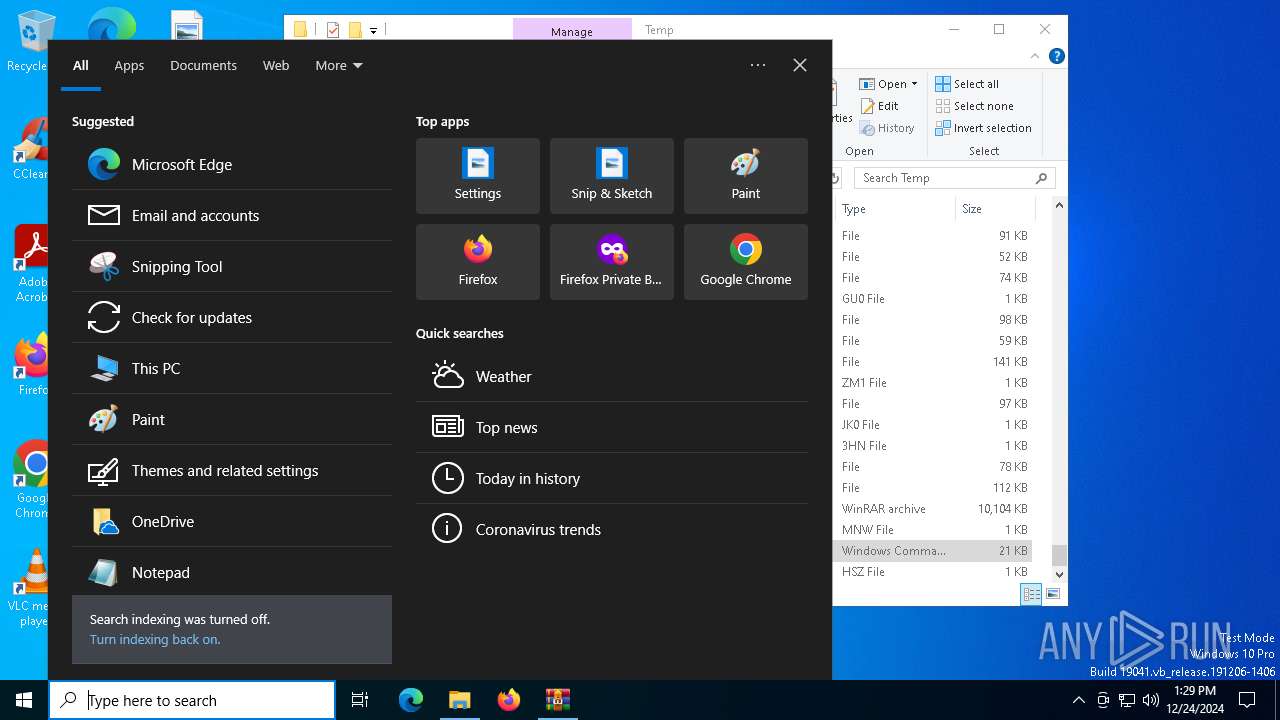
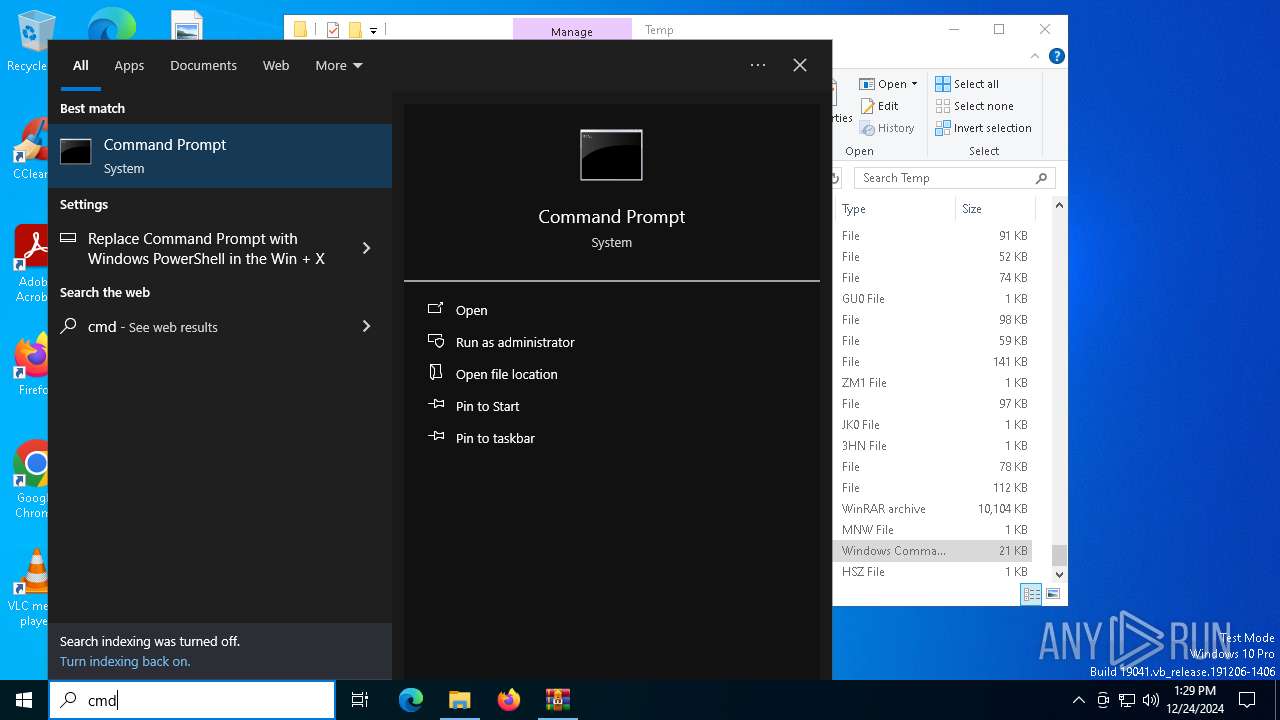
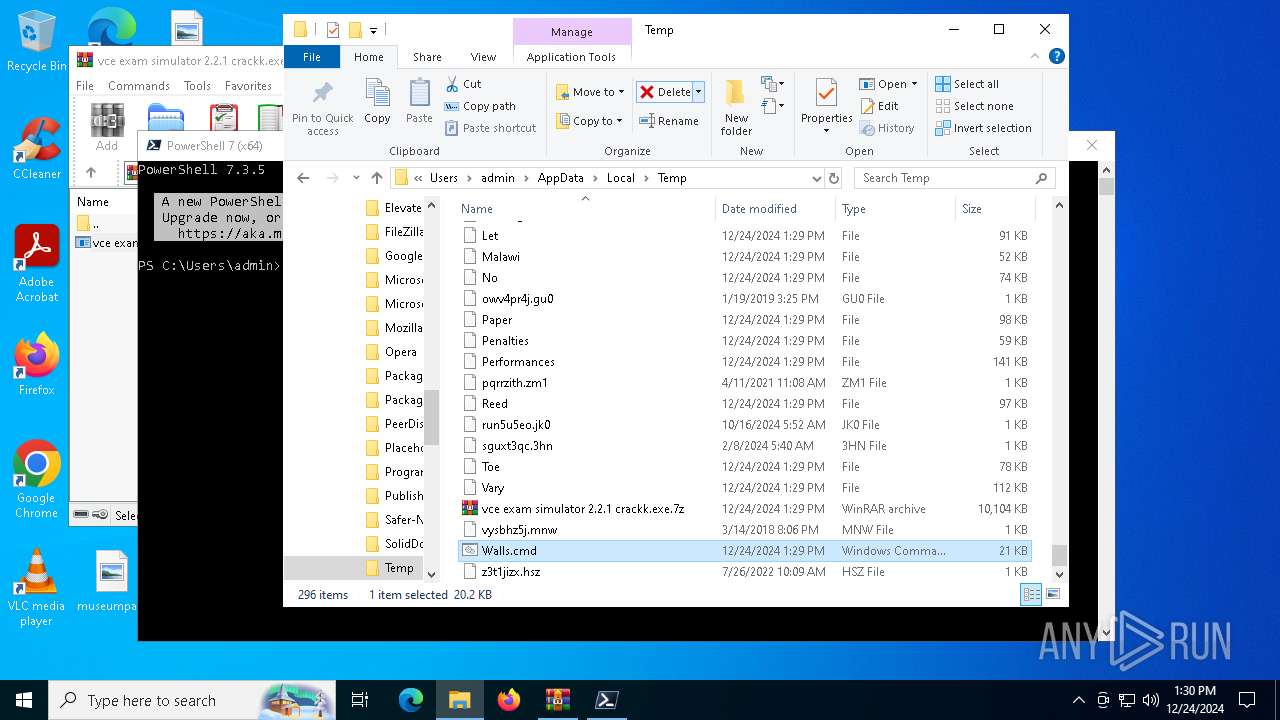
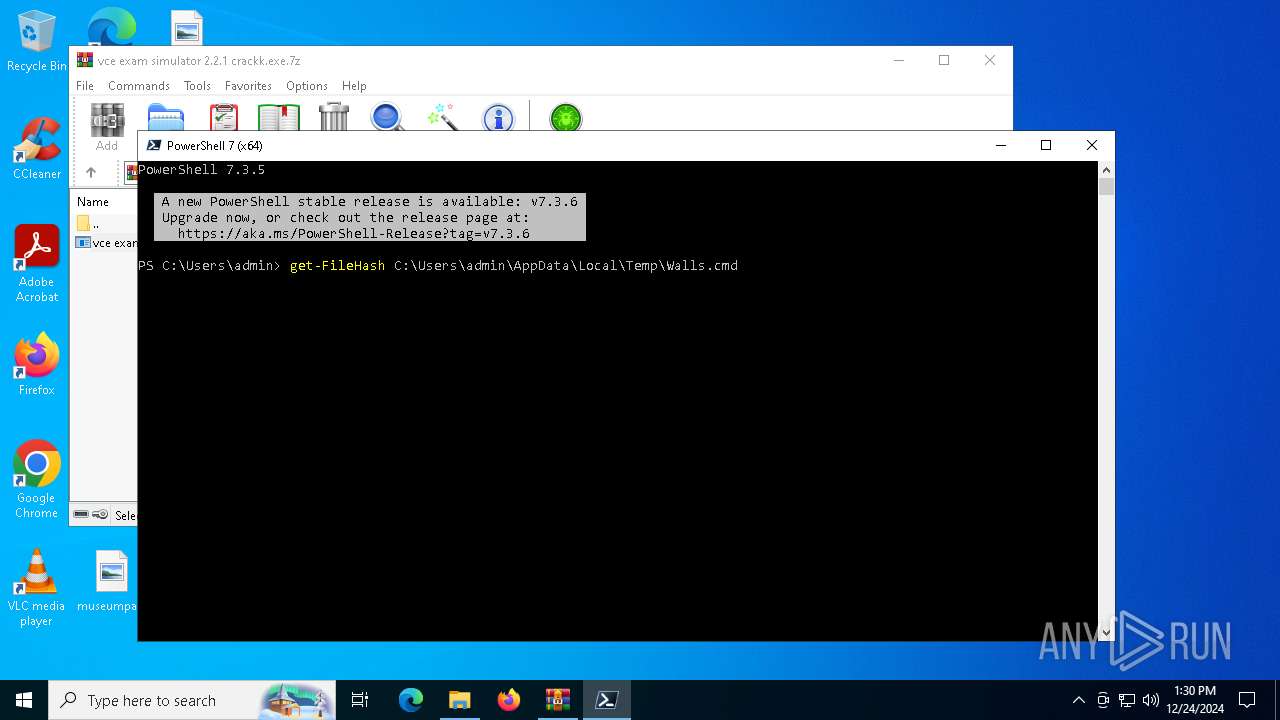
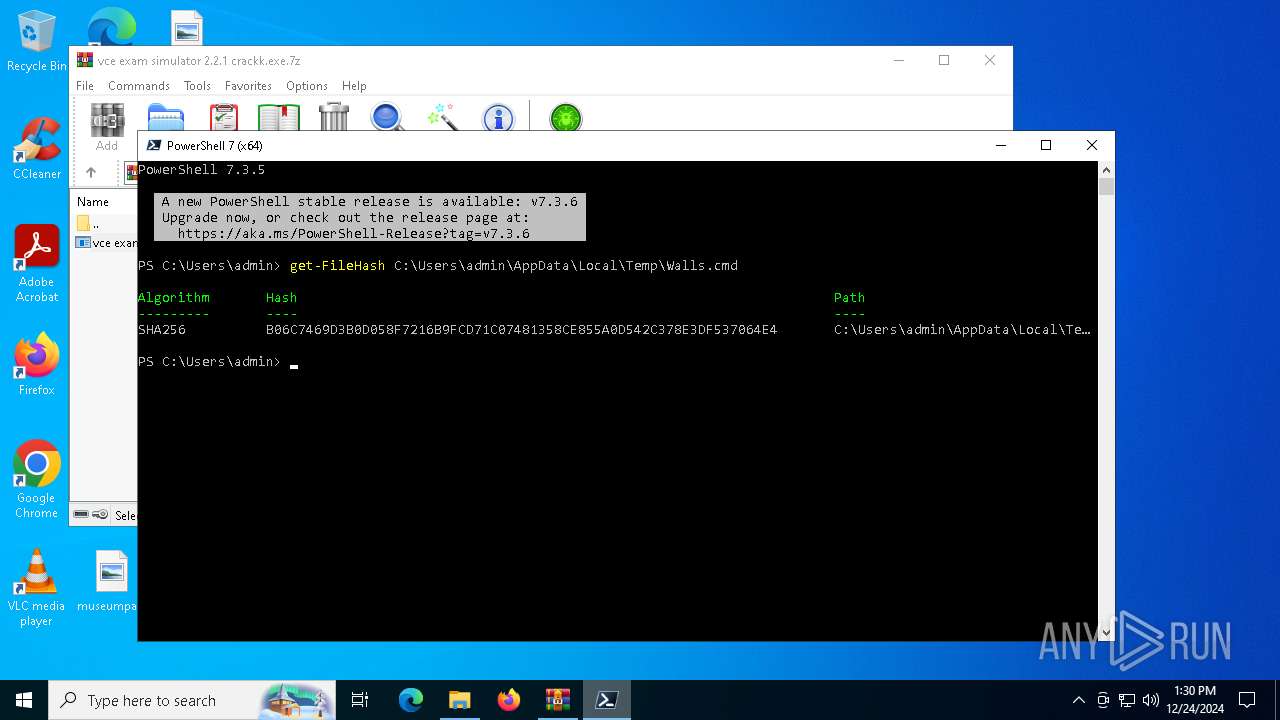
Executing commands from ".cmd" file
- vce exam simulator 2.2.1 crackk.exe (PID: 7136)
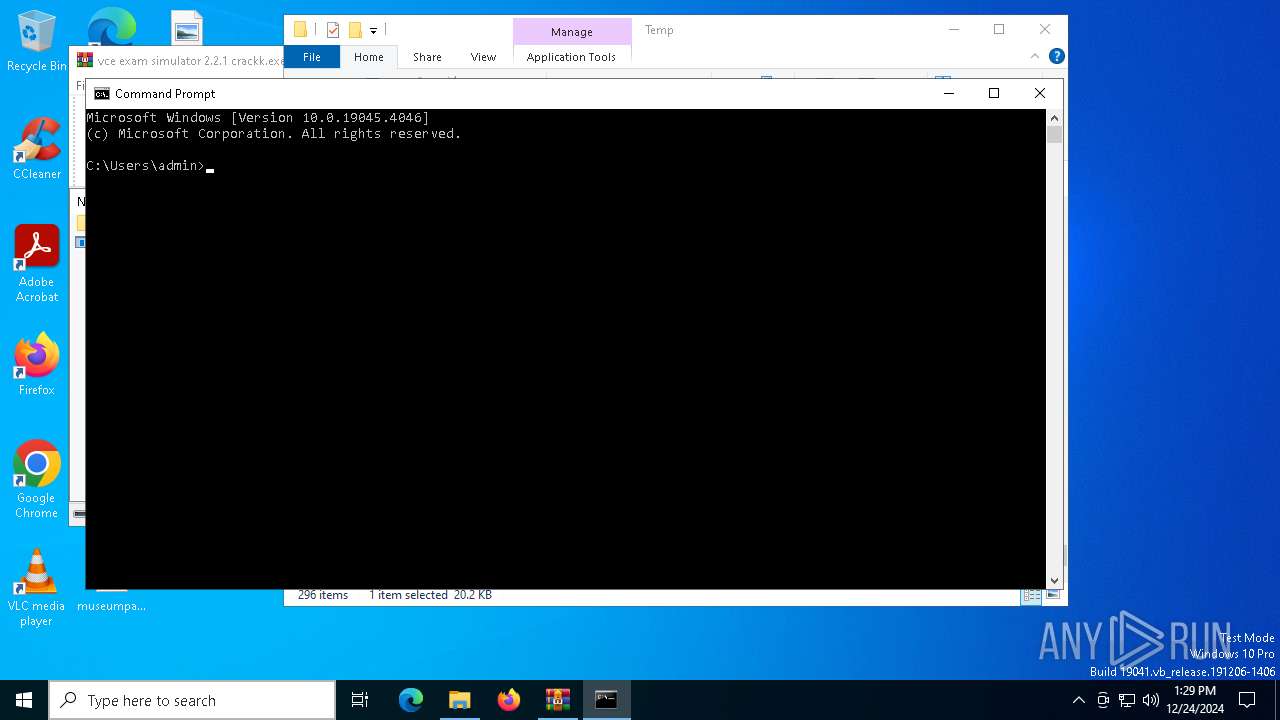
Starts CMD.EXE for commands execution
- vce exam simulator 2.2.1 crackk.exe (PID: 7136)
- cmd.exe (PID: 5192)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5192)
Get information on the list of running processes
- cmd.exe (PID: 5192)
Starts application with an unusual extension
- cmd.exe (PID: 5192)
Application launched itself
- cmd.exe (PID: 5192)
The executable file from the user directory is run by the CMD process
- Spa.com (PID: 4952)
Starts the AutoIt3 executable file
- cmd.exe (PID: 5192)
INFO
Checks supported languages
- vce exam simulator 2.2.1 crackk.exe (PID: 7136)
- Spa.com (PID: 4952)
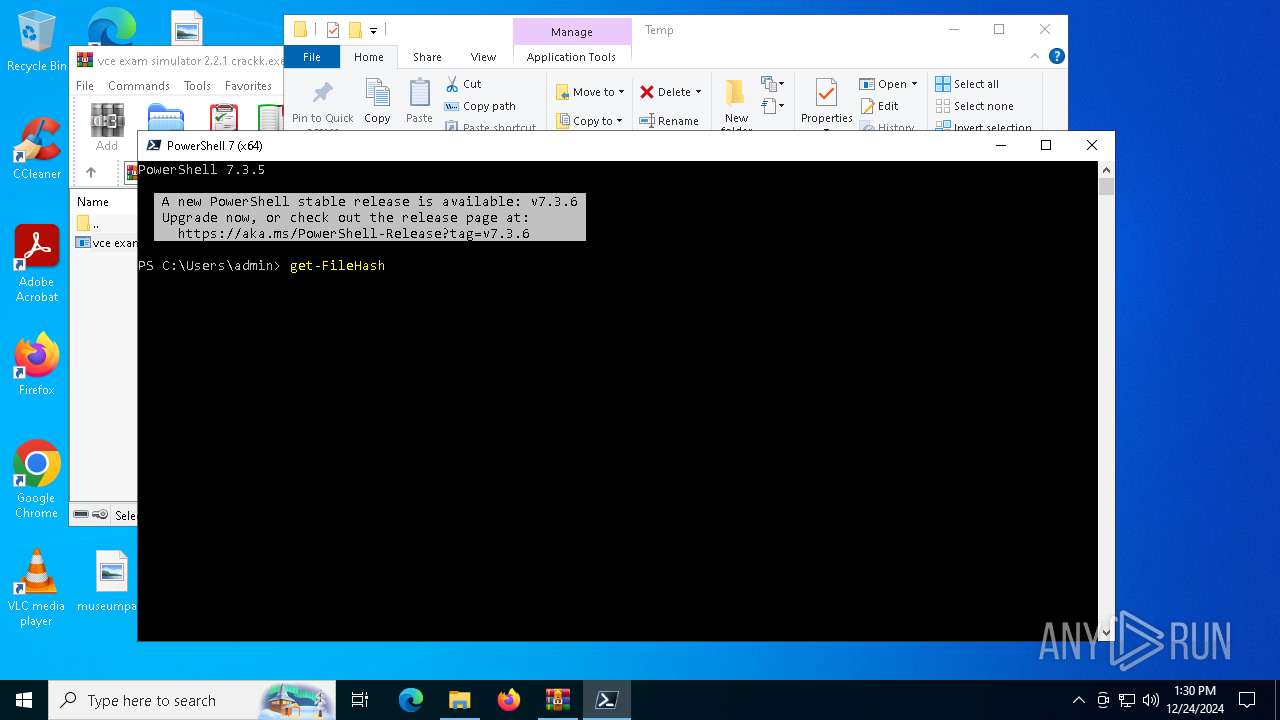
- pwsh.exe (PID: 6948)
The process uses the downloaded file
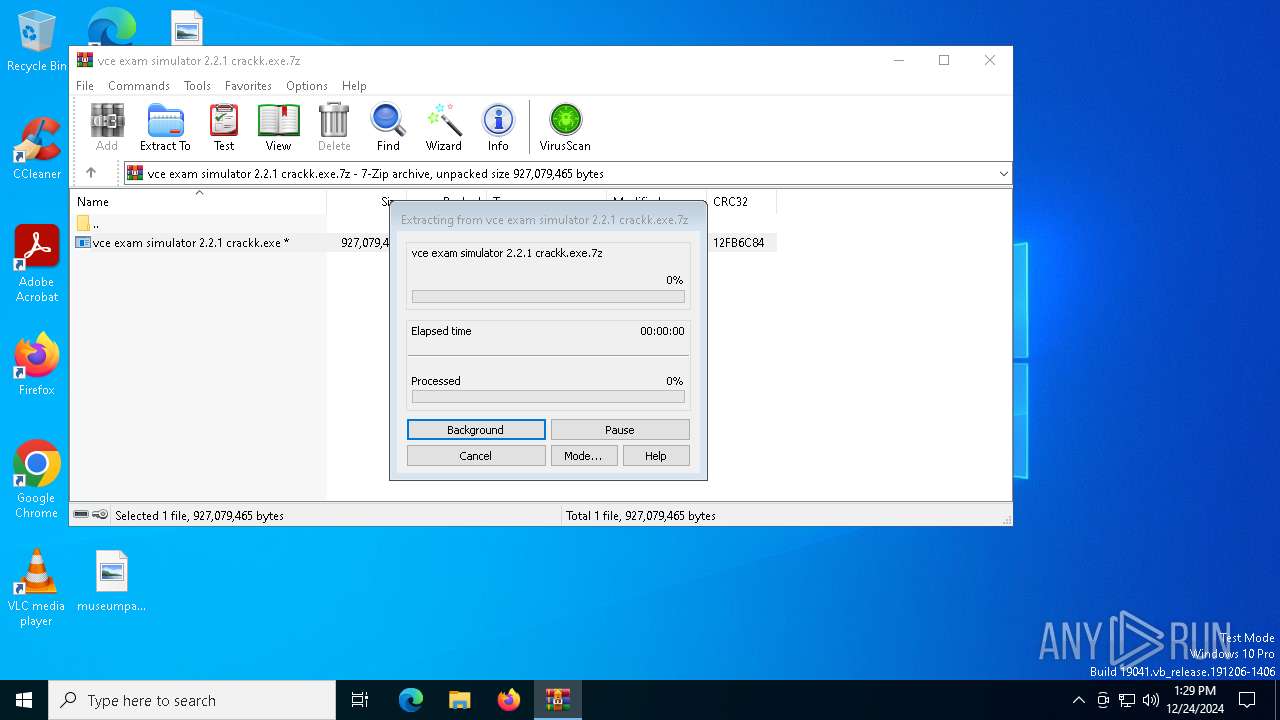
- WinRAR.exe (PID: 6244)
- vce exam simulator 2.2.1 crackk.exe (PID: 7136)
Reads the computer name
- vce exam simulator 2.2.1 crackk.exe (PID: 7136)
- Spa.com (PID: 4952)
- pwsh.exe (PID: 6948)
Process checks computer location settings
- vce exam simulator 2.2.1 crackk.exe (PID: 7136)
- pwsh.exe (PID: 6948)
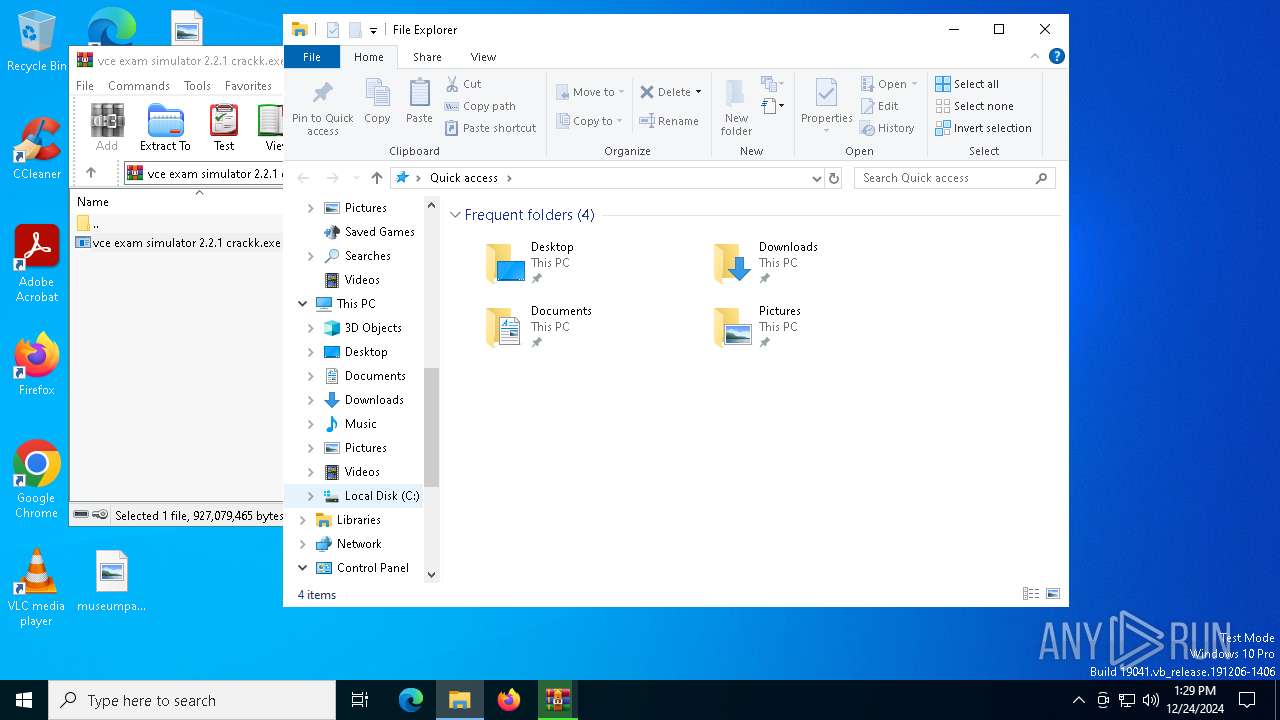
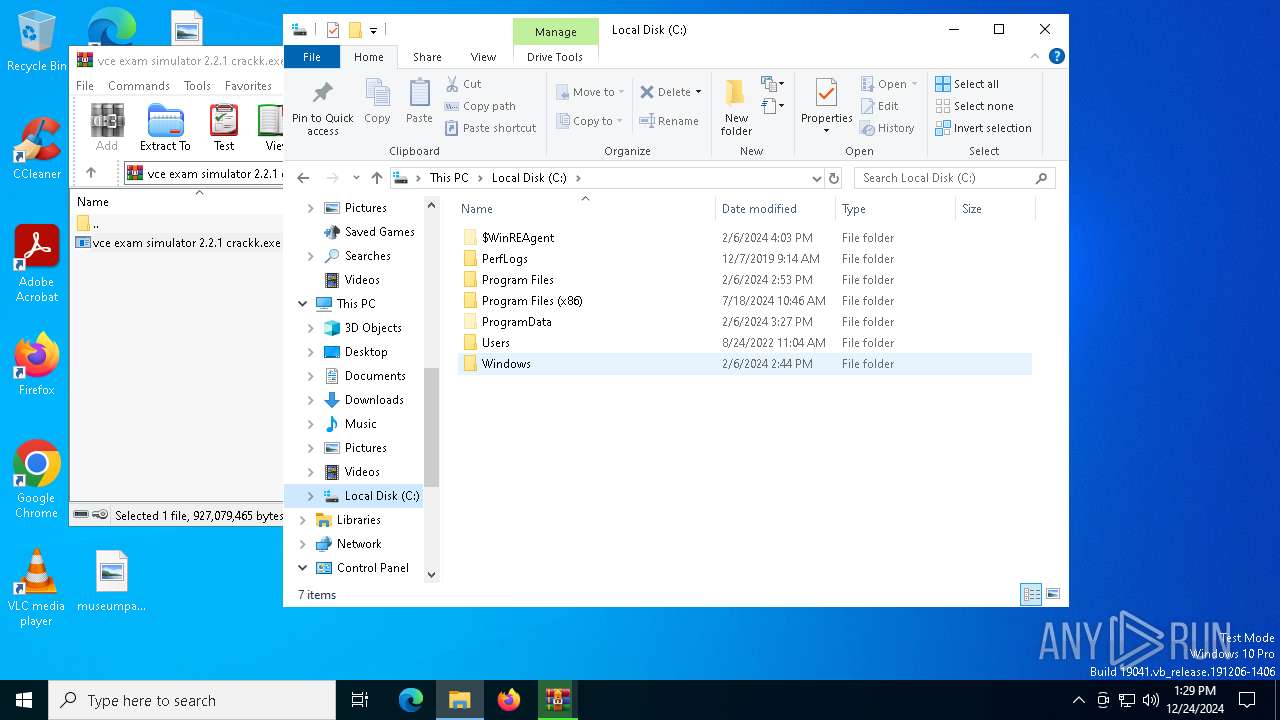
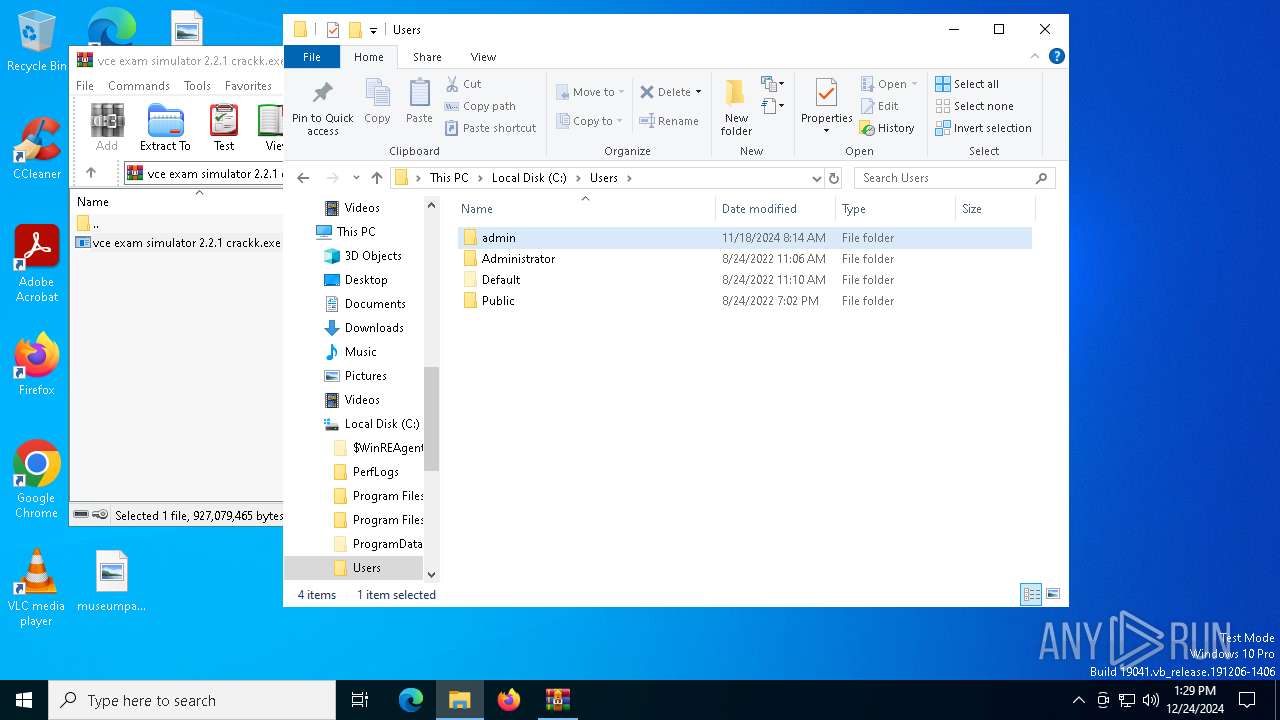
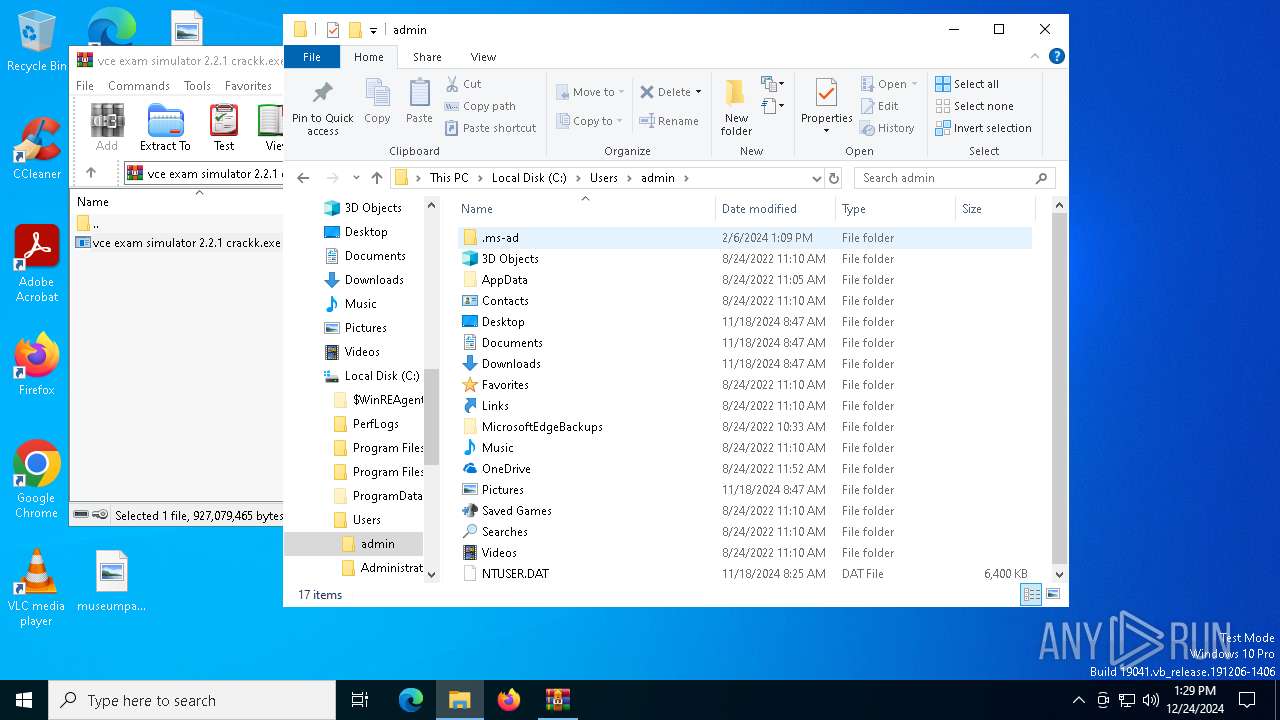
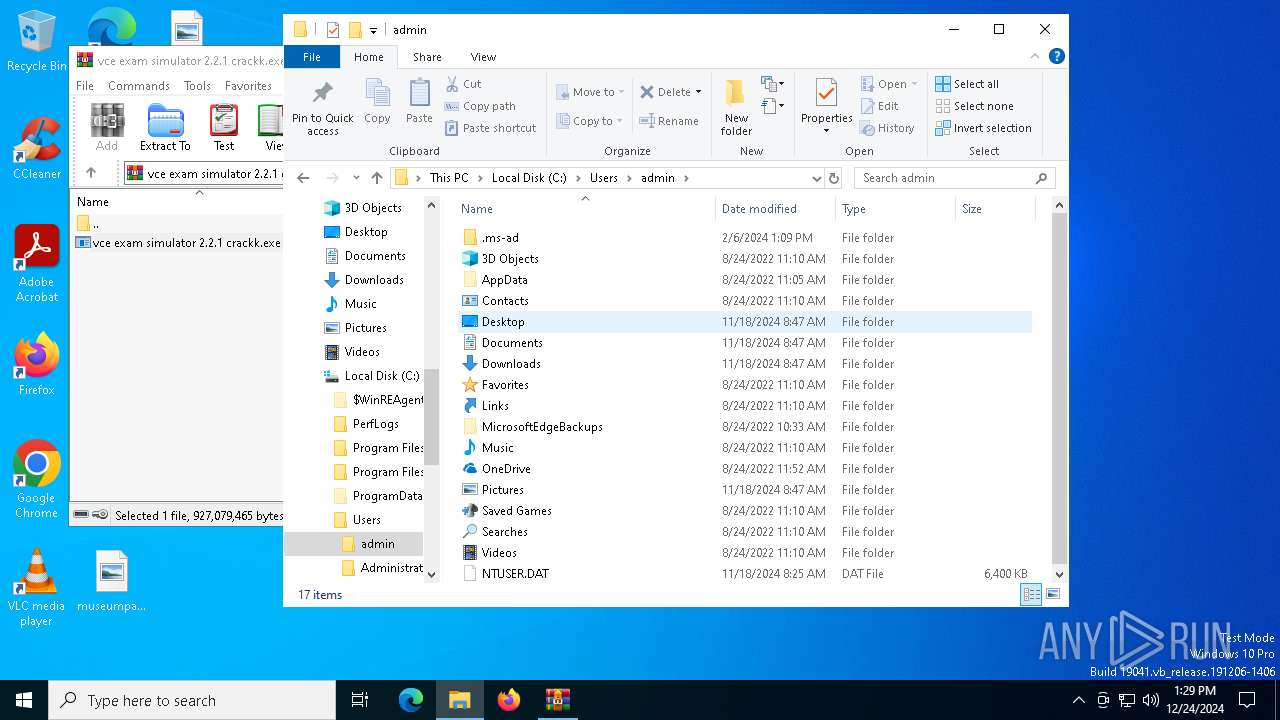
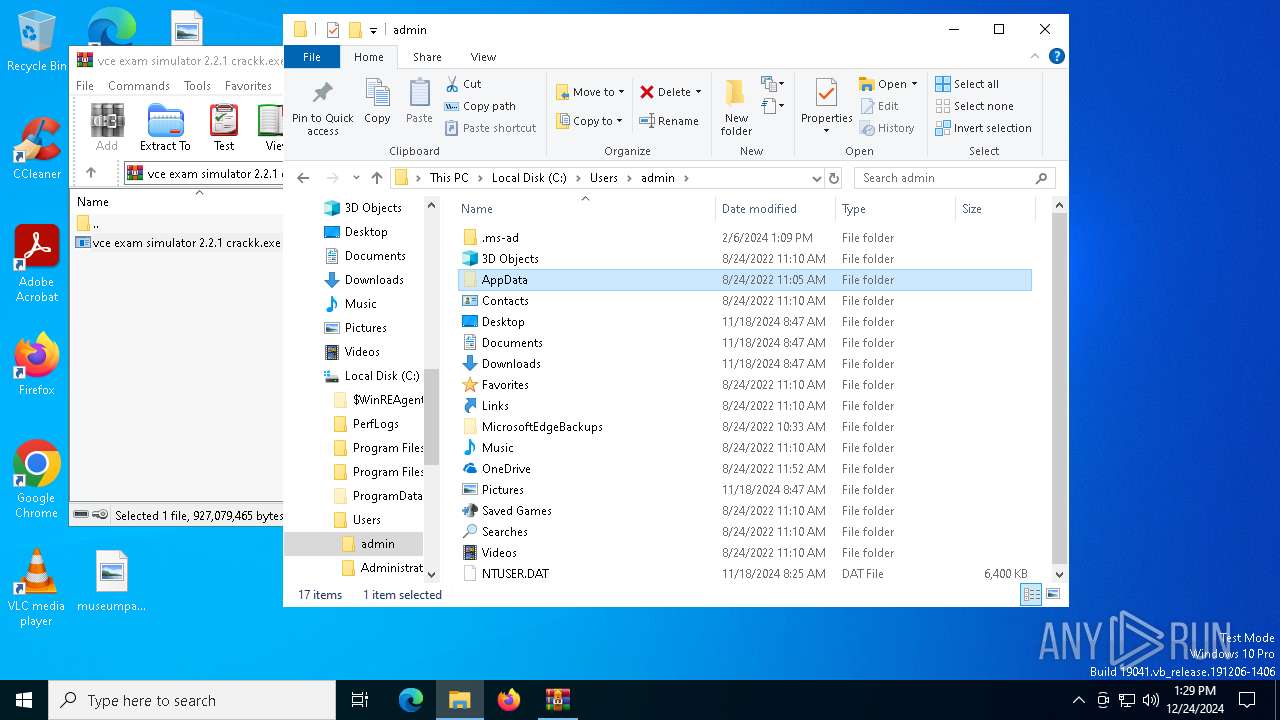
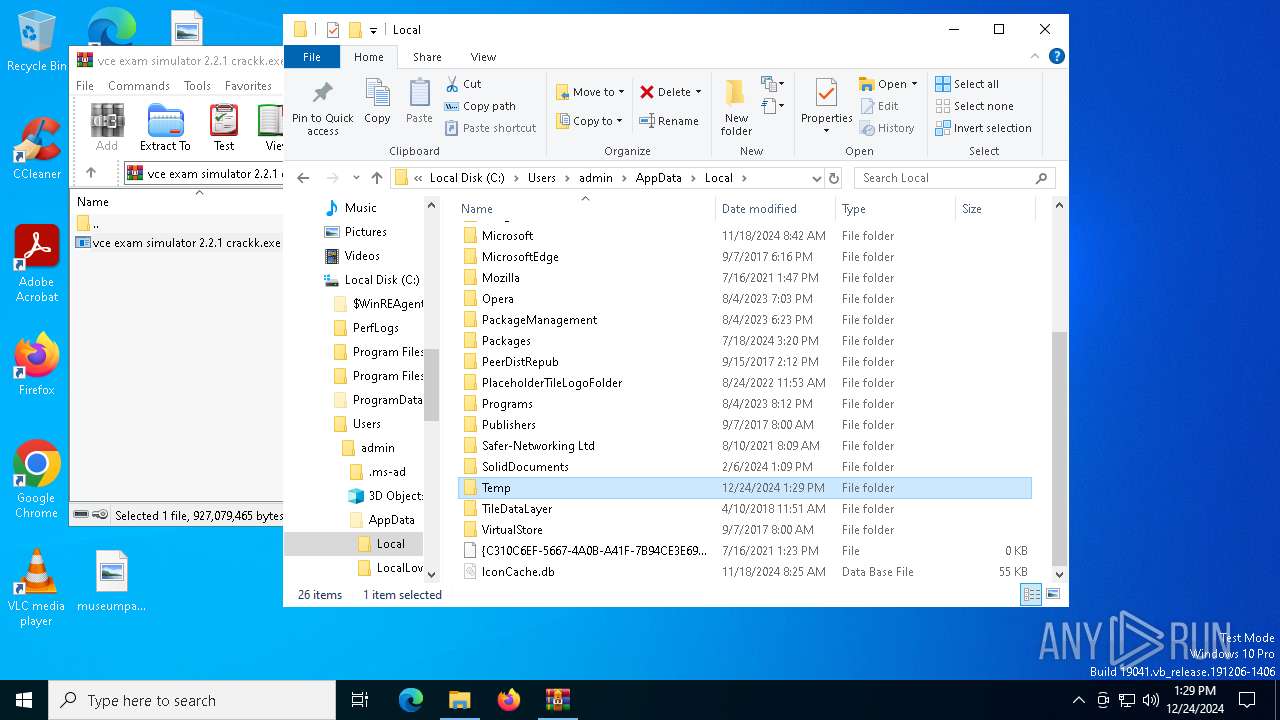
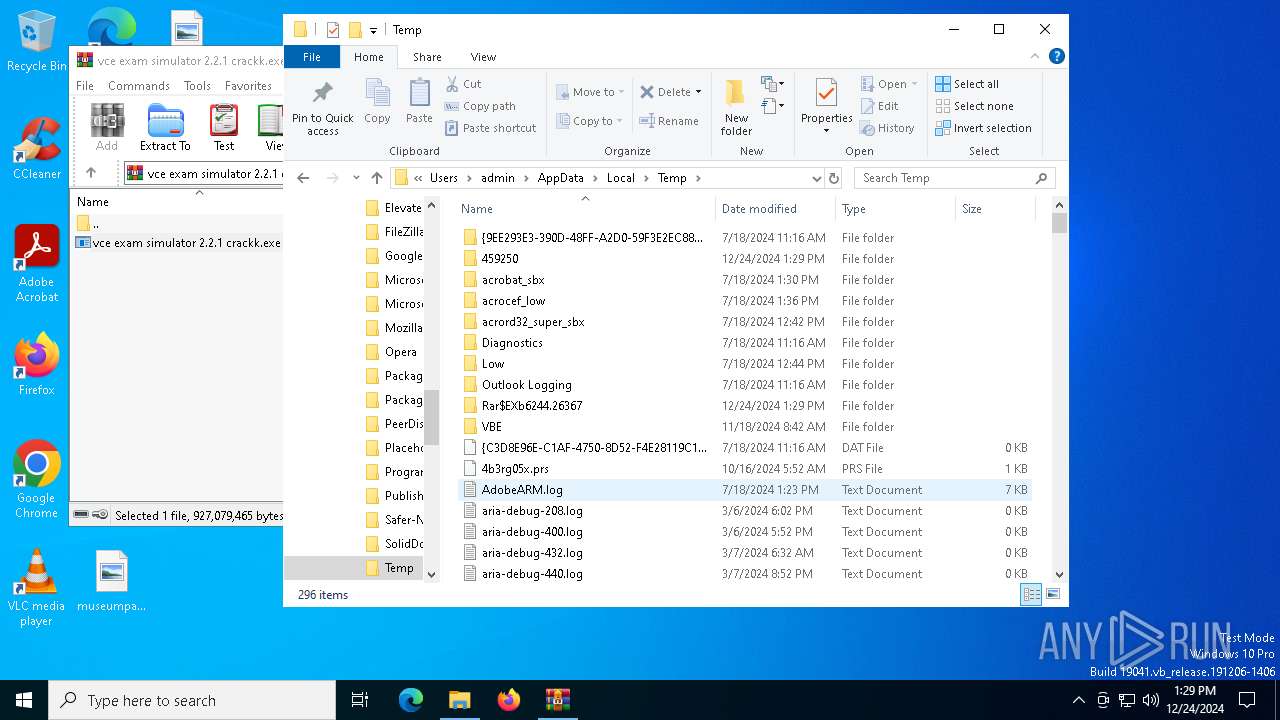
Creates a new folder
- cmd.exe (PID: 5076)
Reads mouse settings
- Spa.com (PID: 4952)
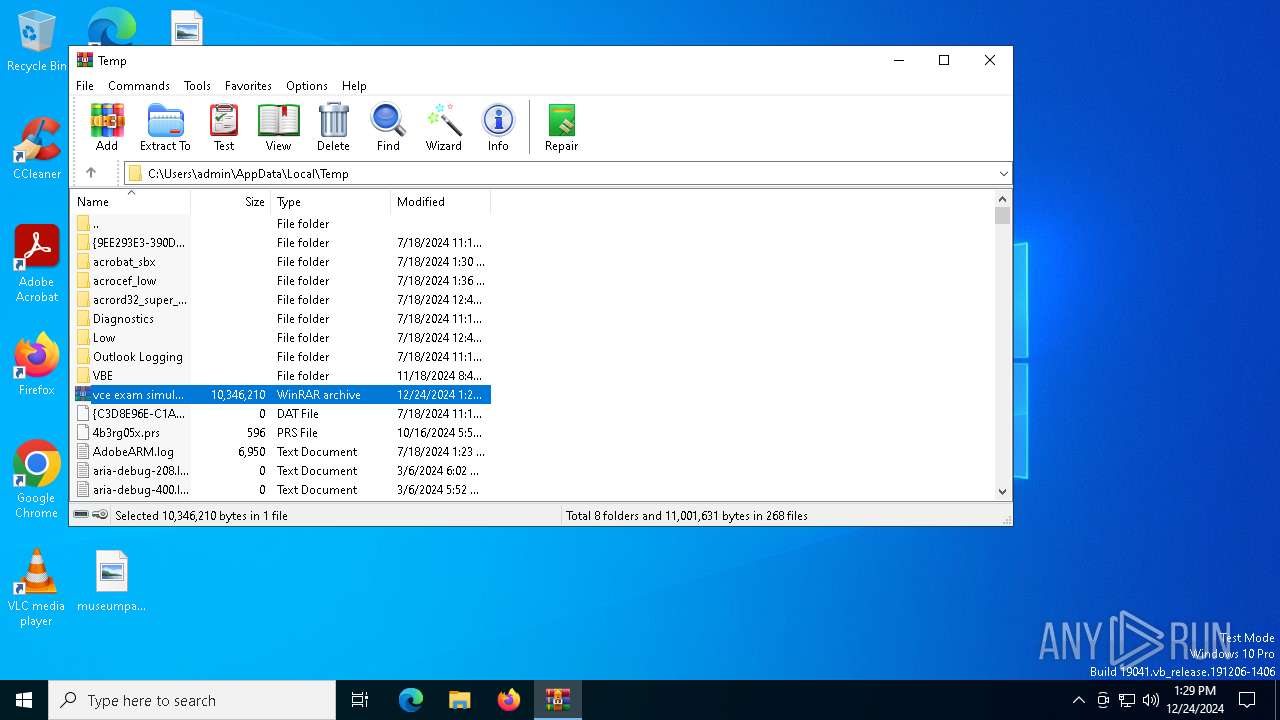
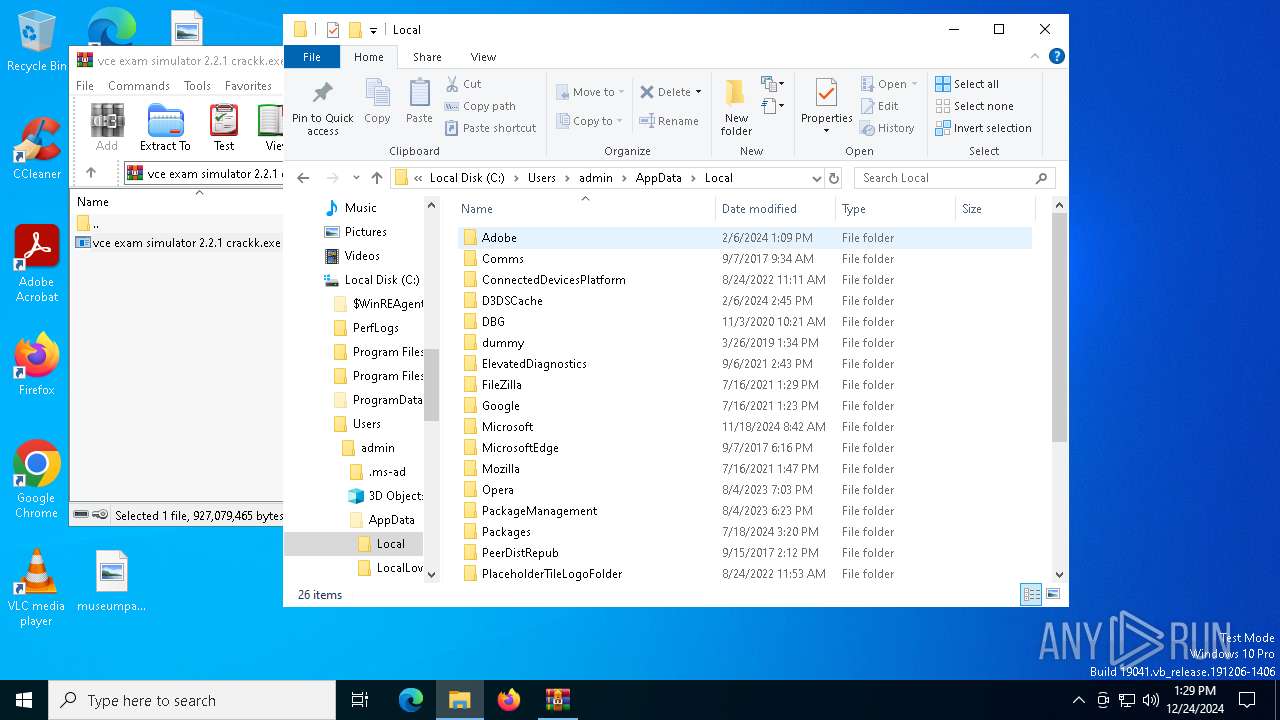
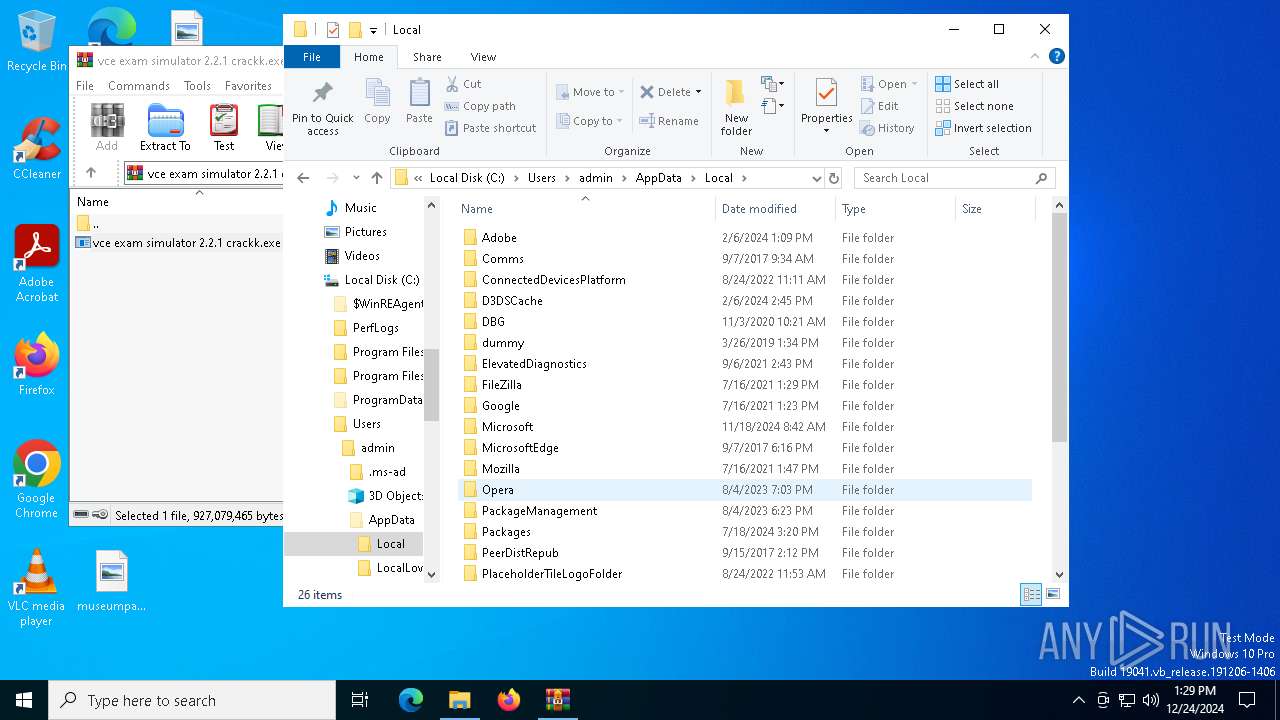
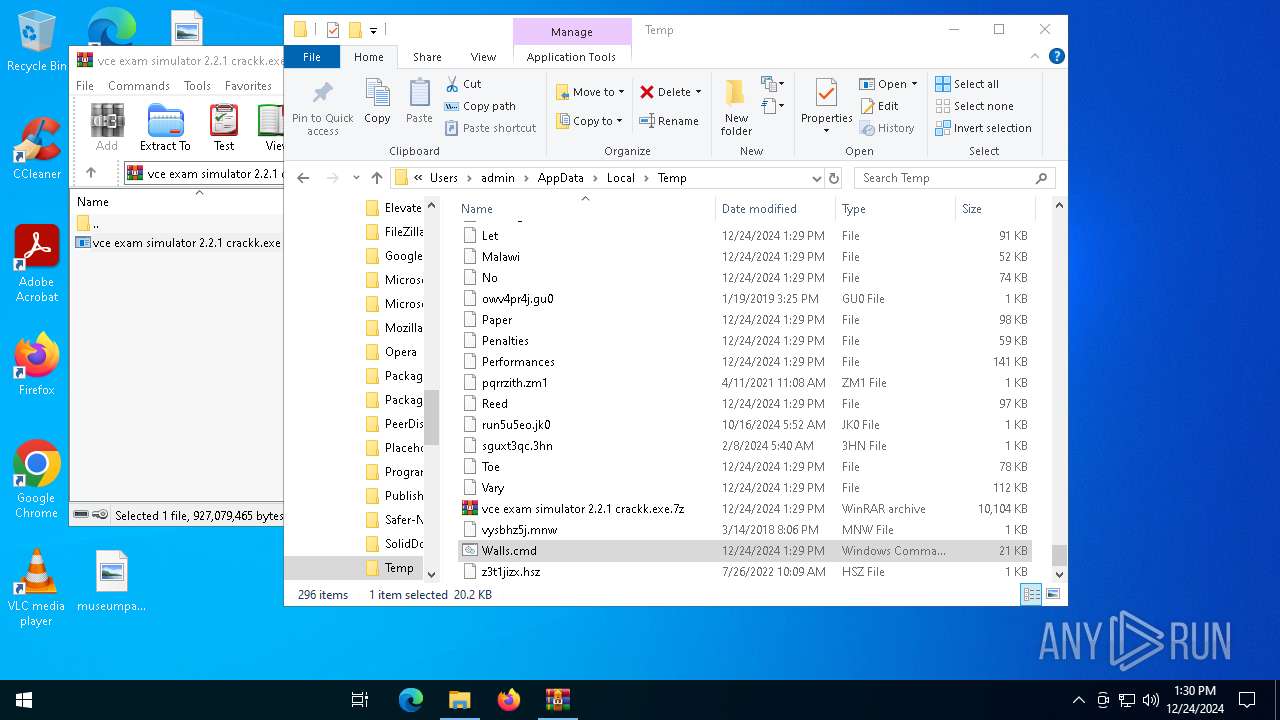
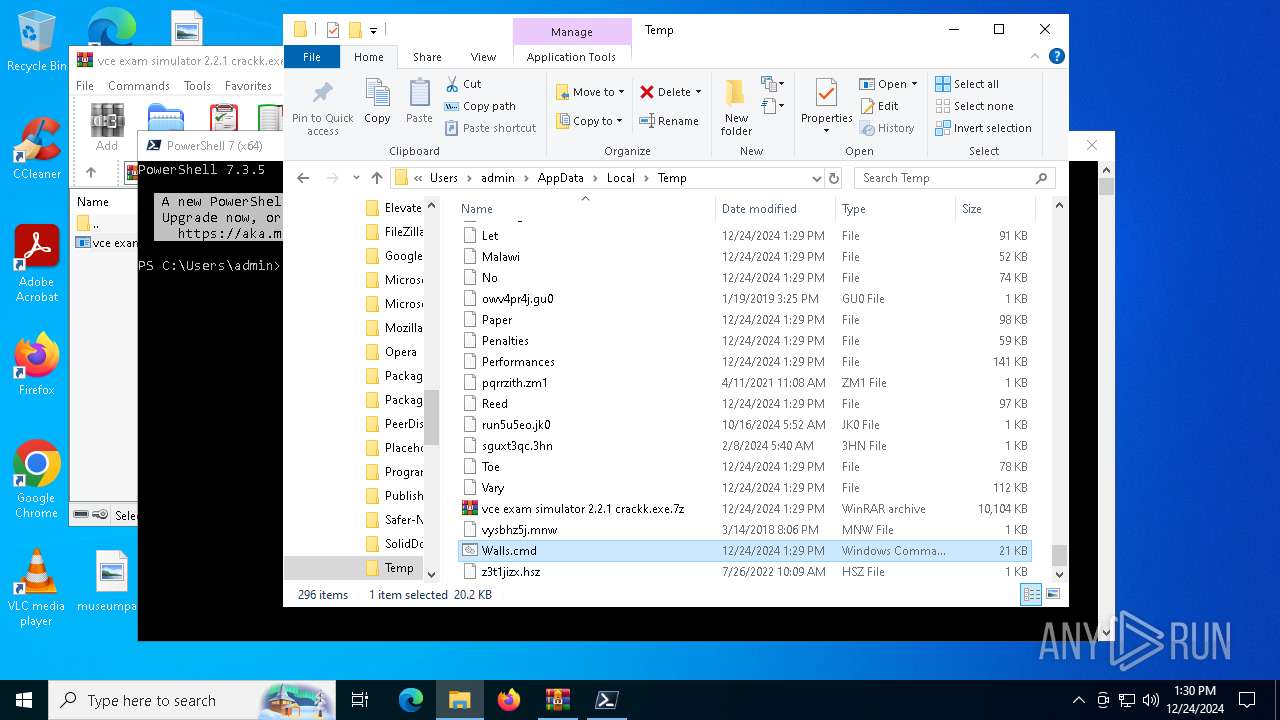
Create files in a temporary directory
- vce exam simulator 2.2.1 crackk.exe (PID: 7136)
Reads the software policy settings
- Spa.com (PID: 4952)
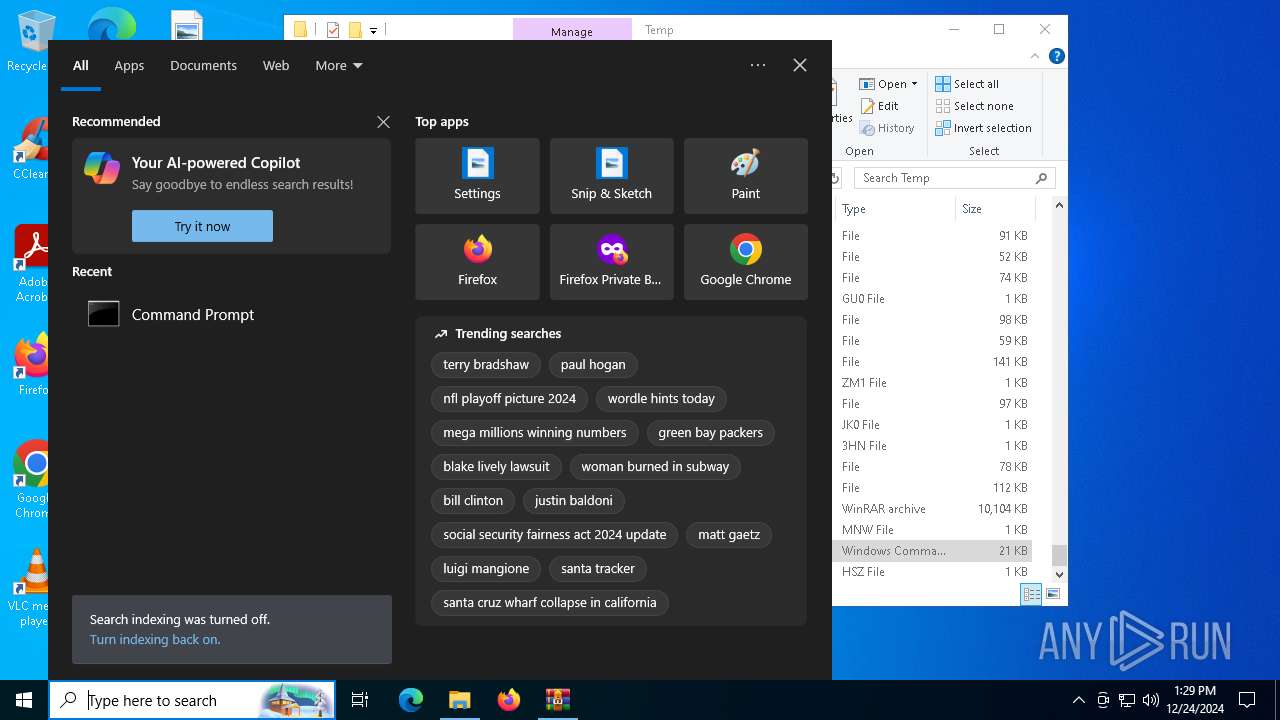
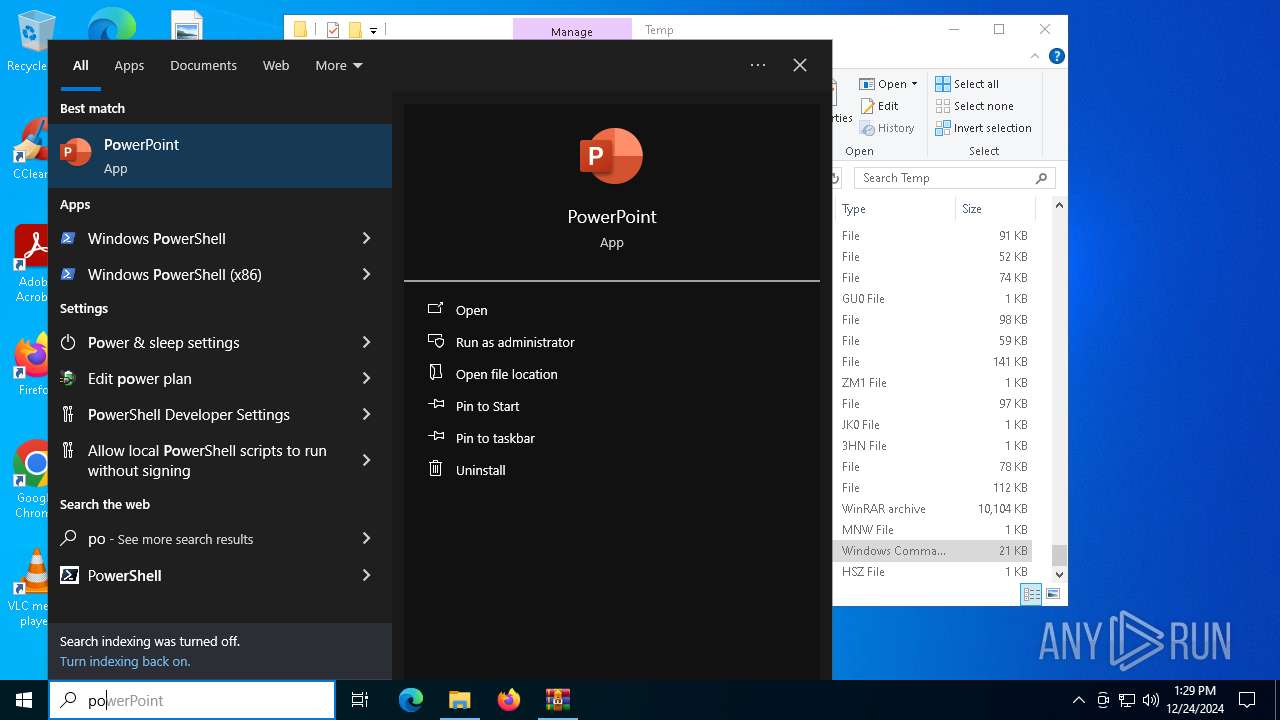
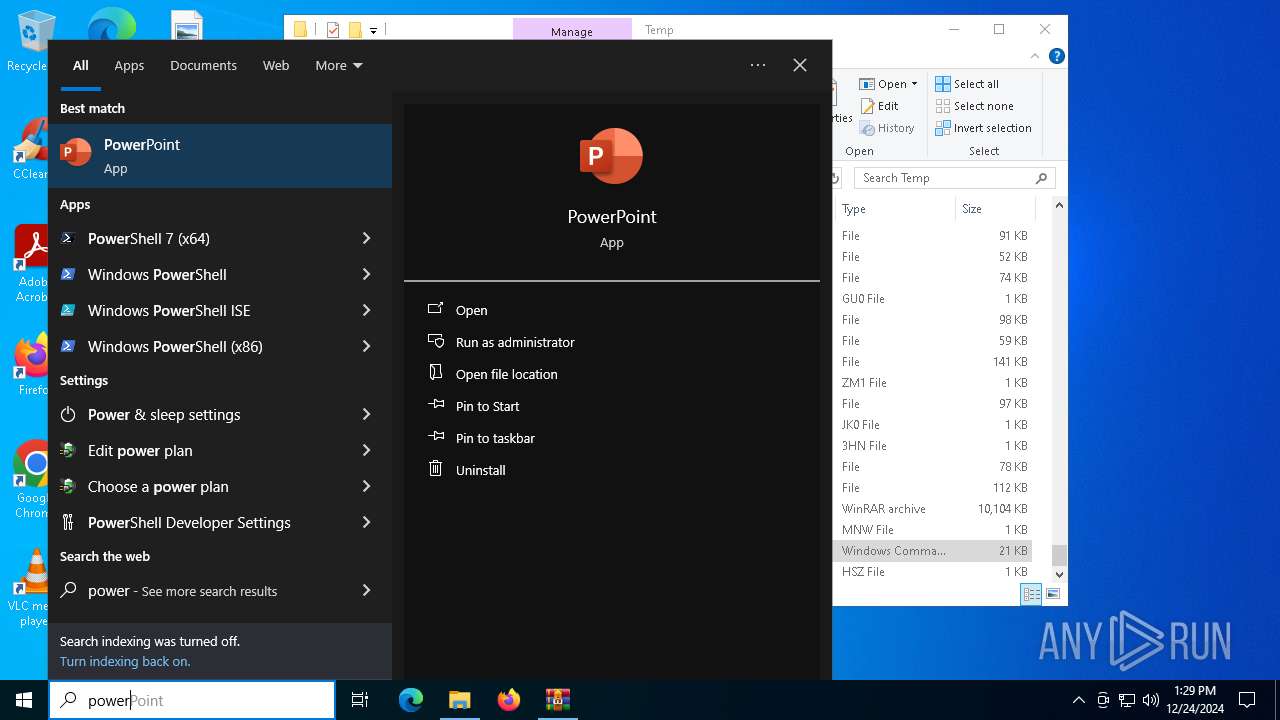
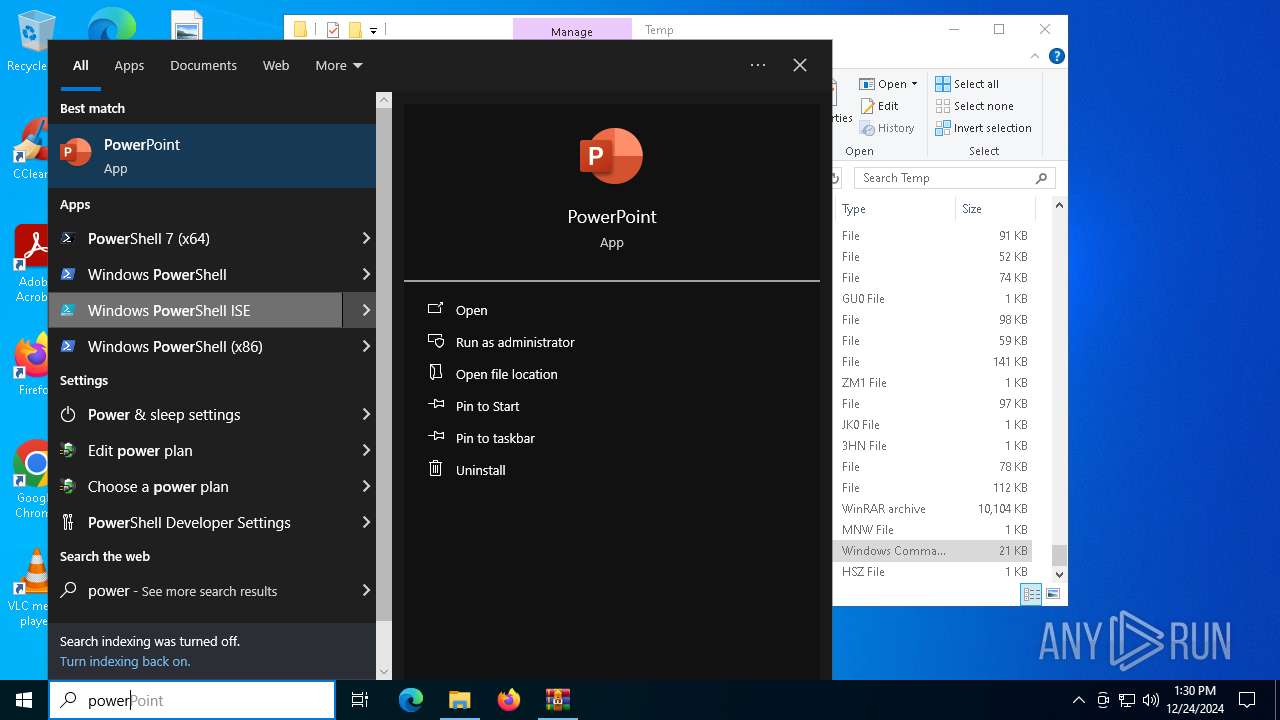
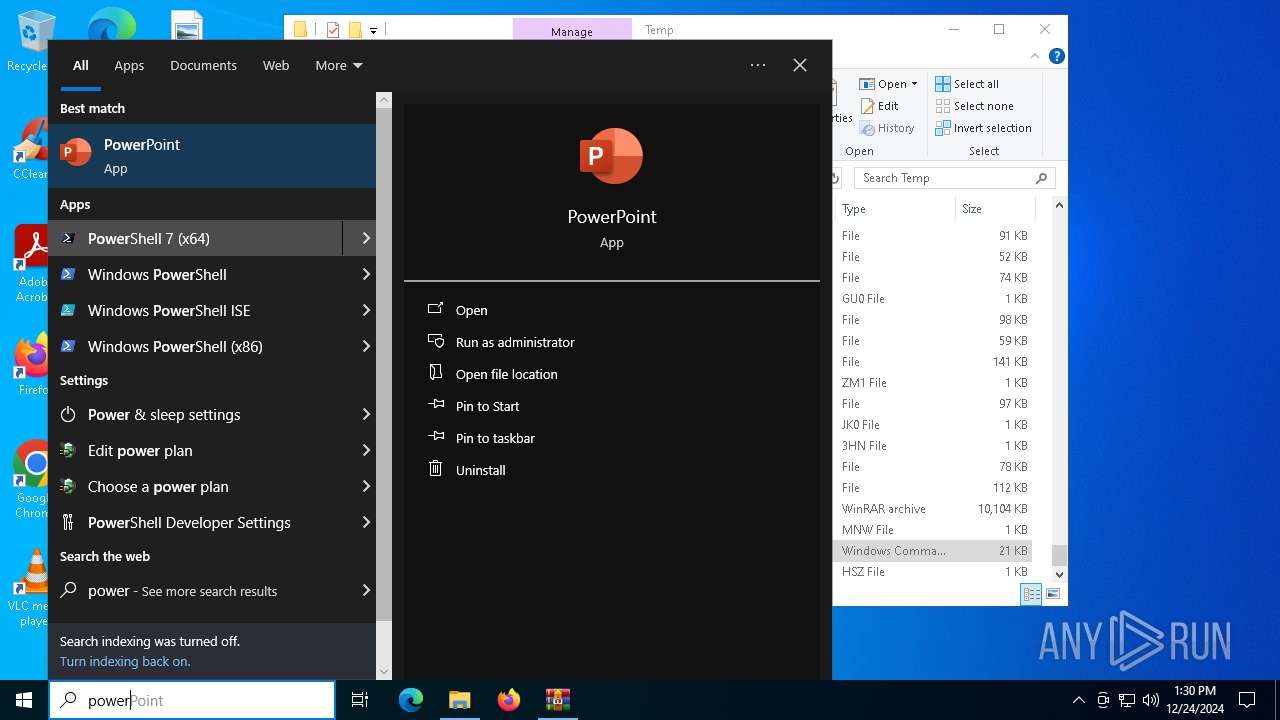
Manual execution by a user
- pwsh.exe (PID: 6948)
- cmd.exe (PID: 2736)
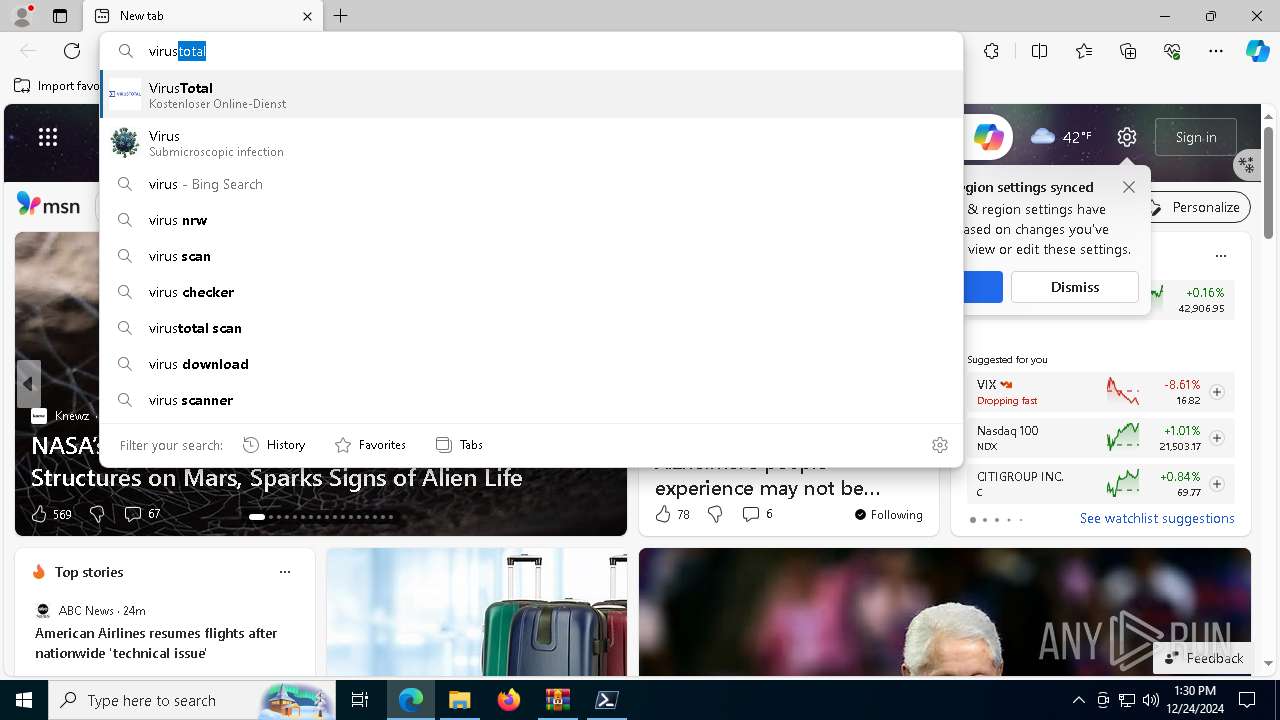
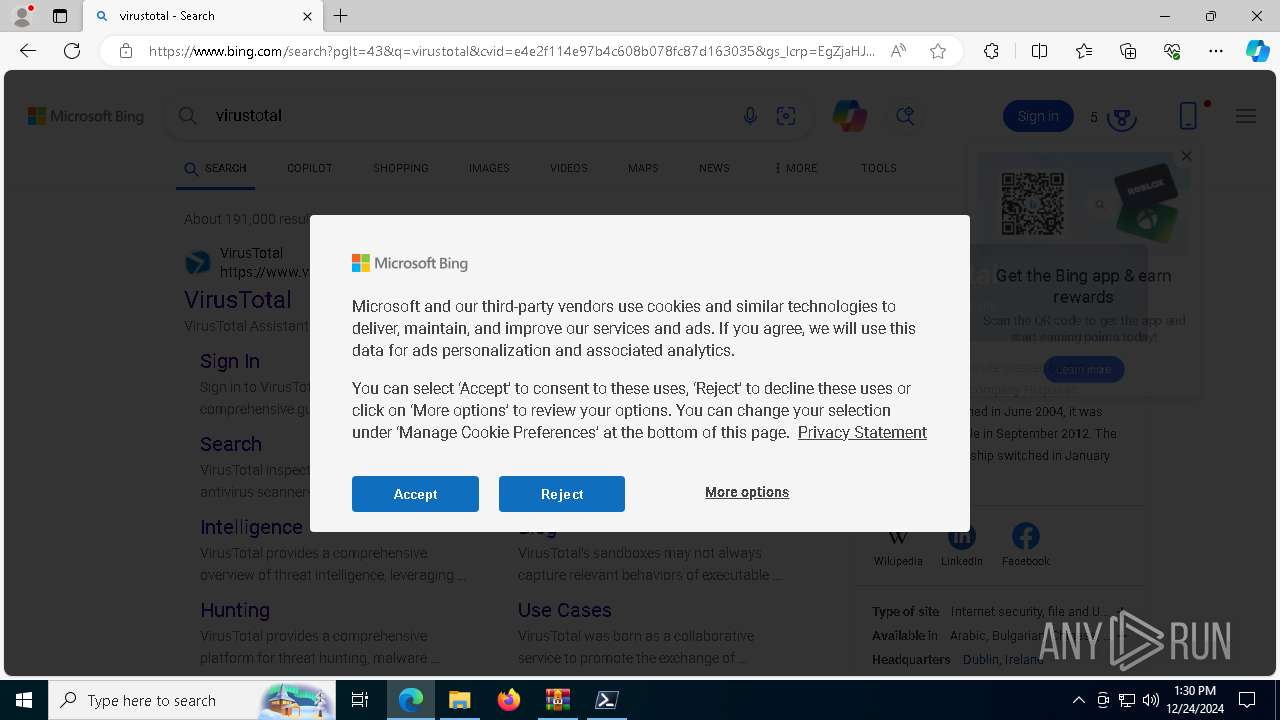
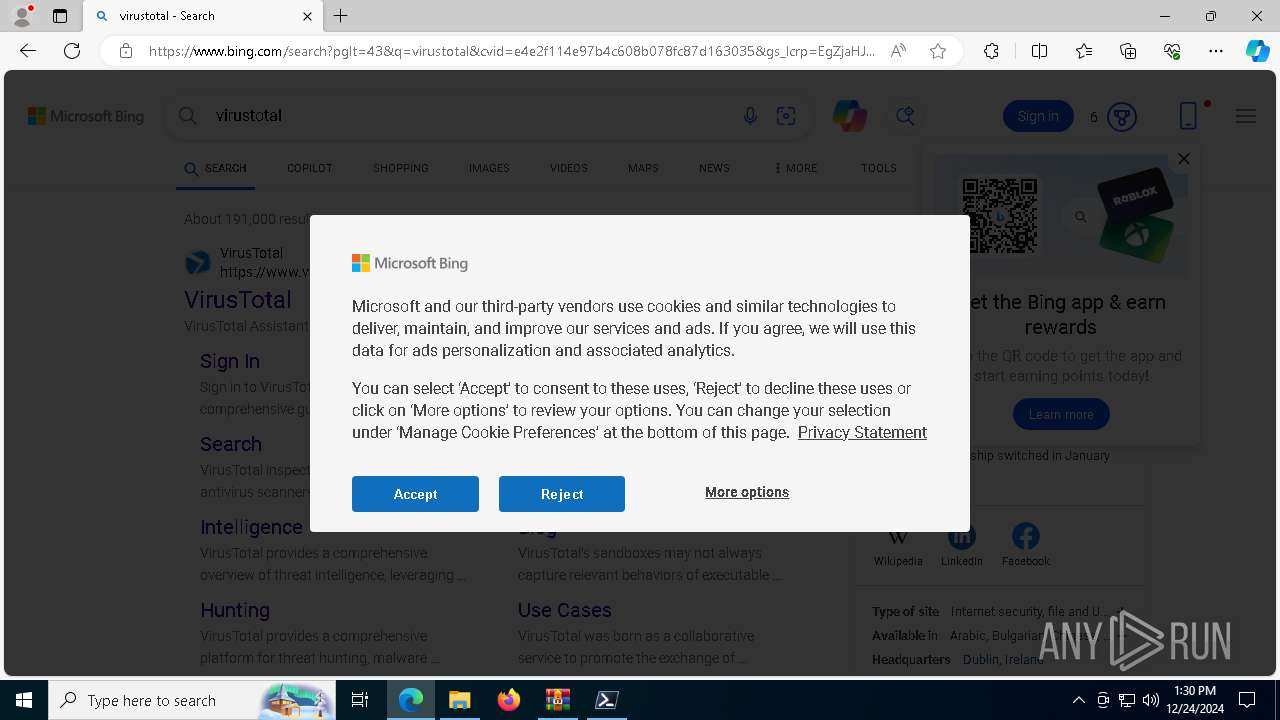
- msedge.exe (PID: 4540)
Application launched itself
- msedge.exe (PID: 4540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2024:12:23 15:54:41+00:00 |
| ArchivedFileName: | vce exam simulator 2.2.1 crackk.exe |
Total processes
201
Monitored processes
68
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5572 --field-trial-handle=2424,i,11591974410630056793,12940733159696080408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1320 --field-trial-handle=2424,i,11591974410630056793,12940733159696080408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 524 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6524 --field-trial-handle=2424,i,11591974410630056793,12940733159696080408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6864 --field-trial-handle=2424,i,11591974410630056793,12940733159696080408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=7484 --field-trial-handle=2424,i,11591974410630056793,12940733159696080408,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6676 --field-trial-handle=2424,i,11591974410630056793,12940733159696080408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3868 --field-trial-handle=2424,i,11591974410630056793,12940733159696080408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=6808 --field-trial-handle=2424,i,11591974410630056793,12940733159696080408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1576 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6400 --field-trial-handle=2424,i,11591974410630056793,12940733159696080408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
15 271
Read events
15 214
Write events
57
Delete events
0
Modification events
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\vce exam simulator 2.2.1 crackk.exe.7z | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
37
Suspicious files
818
Text files
117
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6244.26367\vce exam simulator 2.2.1 crackk.exe | — | |
MD5:— | SHA256:— | |||
| 7136 | vce exam simulator 2.2.1 crackk.exe | C:\Users\admin\AppData\Local\Temp\Earned | binary | |
MD5:23DC1CB4608CC0D9EE4C19EBC5AFBB18 | SHA256:AE5DABE69C7BC3014BC84F528D9D6F9E5180FB291AC67606BB6ADD1E9197877D | |||
| 7136 | vce exam simulator 2.2.1 crackk.exe | C:\Users\admin\AppData\Local\Temp\Malawi | binary | |
MD5:91A53CE5FA451D059806AE3E539CF38A | SHA256:962E2BC969CB5E5D1C6DEBE1DF1AA1B143A76235D66851EFF62FA60A2264EBE1 | |||
| 7136 | vce exam simulator 2.2.1 crackk.exe | C:\Users\admin\AppData\Local\Temp\Giant | binary | |
MD5:61986B5B8C0EE798BCBE01CF003EC160 | SHA256:7884B57063A2D3F4BBD7F0E257AA5D46620F6A0CBF19CCC55191CB59F50D4452 | |||
| 7136 | vce exam simulator 2.2.1 crackk.exe | C:\Users\admin\AppData\Local\Temp\Leading | binary | |
MD5:07BDD195A3DD4499ADBA76BD5099C1C4 | SHA256:58A7DD80A6ED5760D5854FBF872ED849DC8038C6830A976724909B2308F1003C | |||
| 7136 | vce exam simulator 2.2.1 crackk.exe | C:\Users\admin\AppData\Local\Temp\Vary | binary | |
MD5:FF200F0461B616F93558C59743F3D834 | SHA256:3F25CD216D16FB86F20A99ACBF7B44EDEC9A26DCEC2F93AEFD8FA92C776A2C0E | |||
| 7136 | vce exam simulator 2.2.1 crackk.exe | C:\Users\admin\AppData\Local\Temp\Reed | binary | |
MD5:C2D828DB4A1BC6A933A5DD08E9BD9860 | SHA256:C32BA28FB4D05B79A44C059B5DCE64B2C643C5413AC7B41B653B448C28701888 | |||
| 7136 | vce exam simulator 2.2.1 crackk.exe | C:\Users\admin\AppData\Local\Temp\Let | binary | |
MD5:5BA231E8355CCF5A593247DDAE88C07F | SHA256:170F47E746020D726CCDB482C209FAF3F1F23B514A2009DB2785C47CCFCD724E | |||
| 7136 | vce exam simulator 2.2.1 crackk.exe | C:\Users\admin\AppData\Local\Temp\No | binary | |
MD5:903EB3D3E9AD1FC11728B5FB60B91B4D | SHA256:CEA9531815CA1E3422C35341FDCD98FF9F2E5C0EF978CC4AA759C8AF801210DA | |||
| 7136 | vce exam simulator 2.2.1 crackk.exe | C:\Users\admin\AppData\Local\Temp\Performances | binary | |
MD5:5FA4E2D2588B2ABE9FFC10E27EDD400F | SHA256:3173C8678F4B6D46C9A0A7672643AE4C2F1CD200C6769E5959927E5048DBB4F1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
196
DNS requests
199
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5988 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5988 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2972 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6960 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6960 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6948 | pwsh.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6948 | pwsh.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2072 | msedge.exe | GET | 304 | 2.23.197.184:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5988 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5988 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6948 | pwsh.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
2072 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2072 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
2072 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
2072 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |