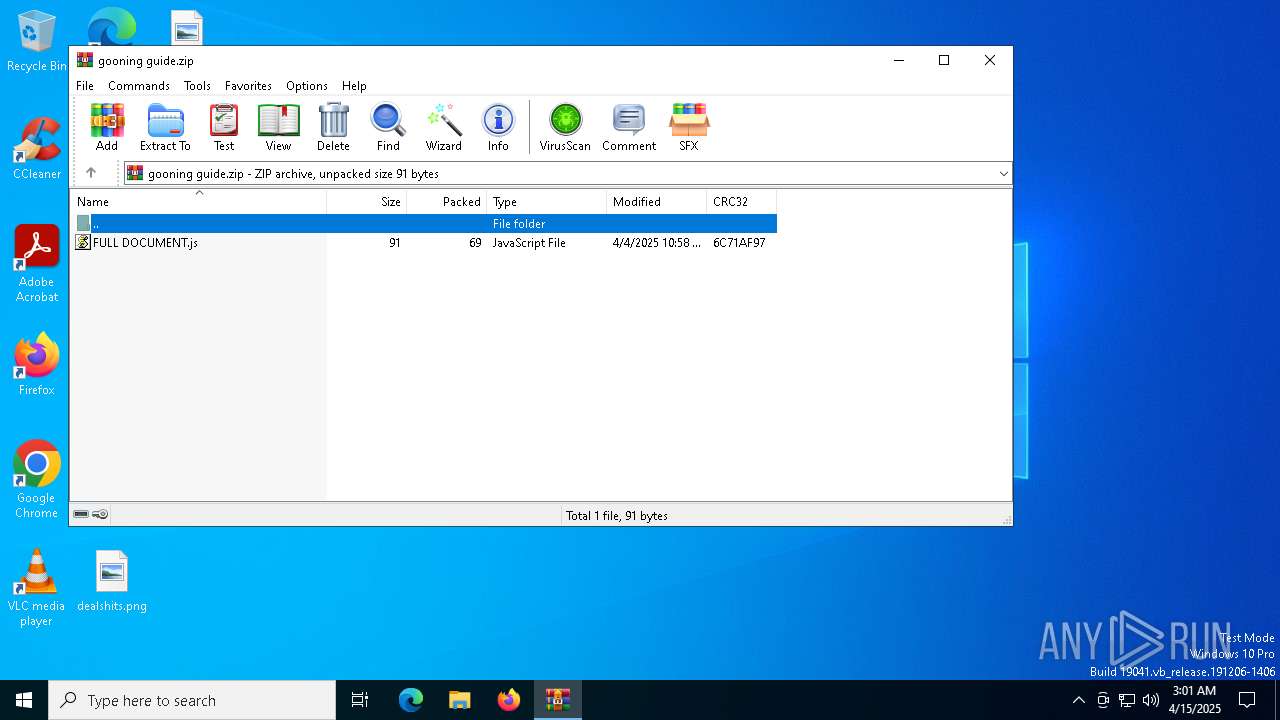
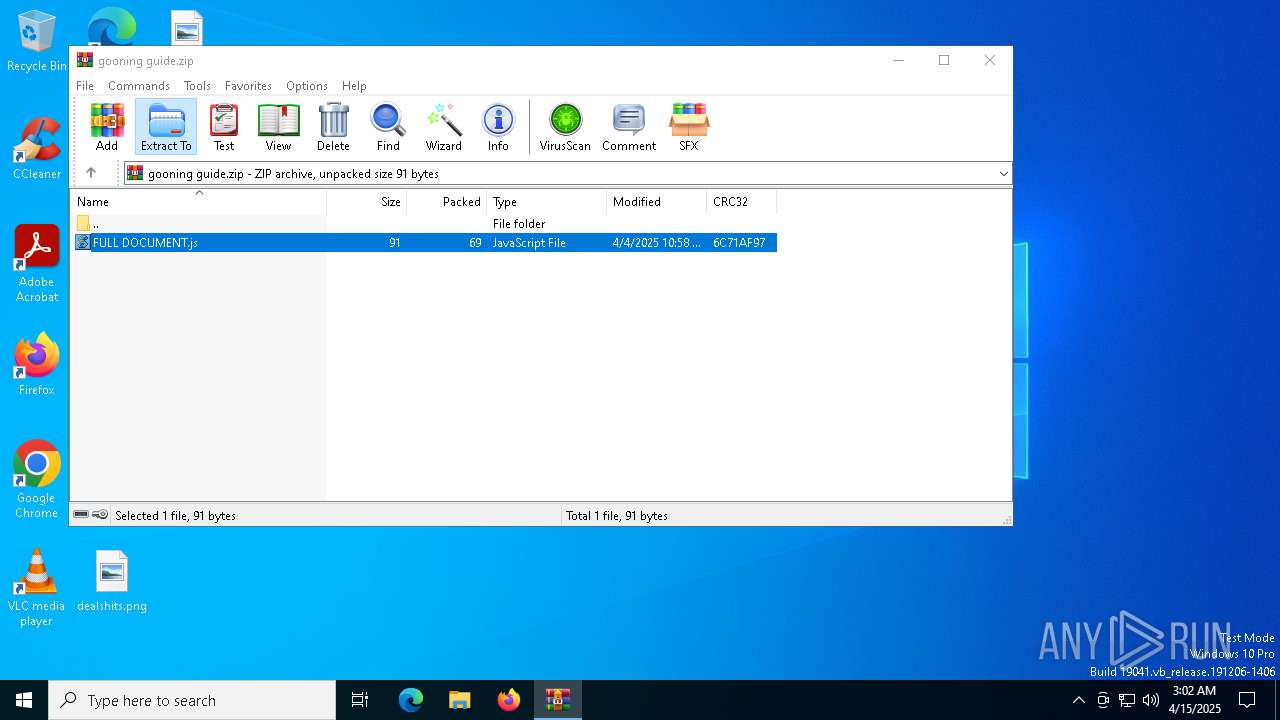
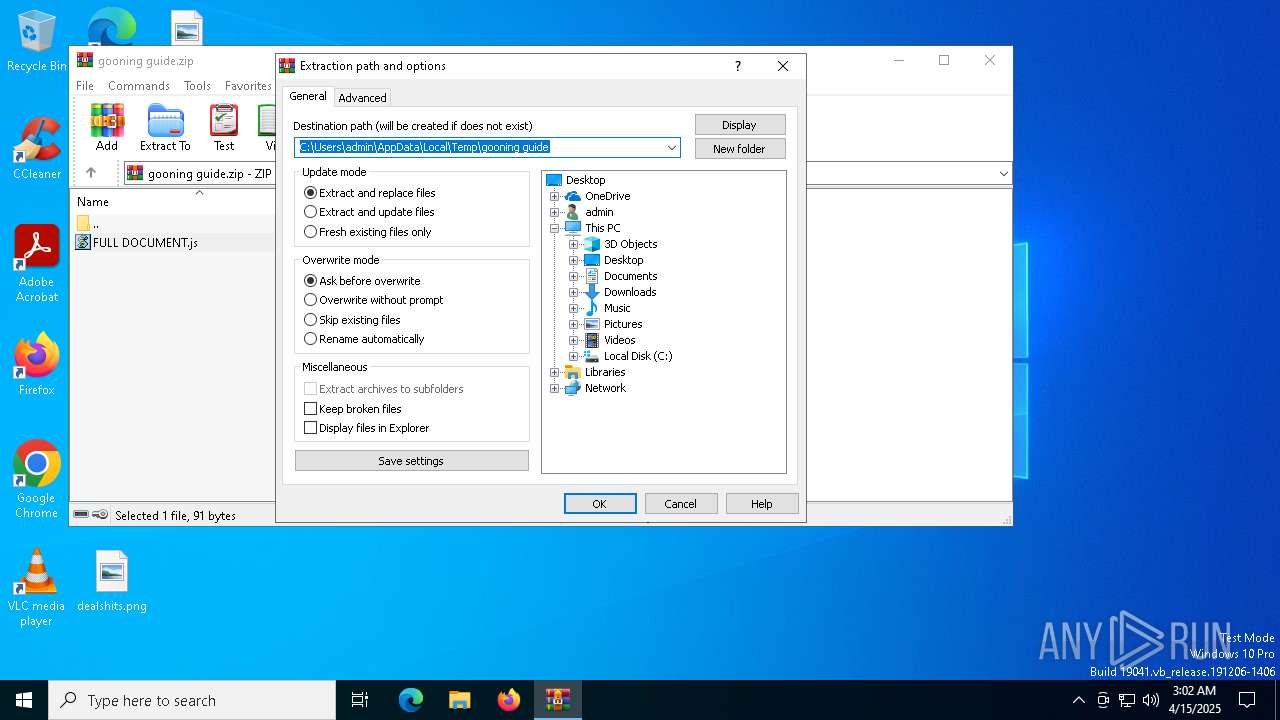
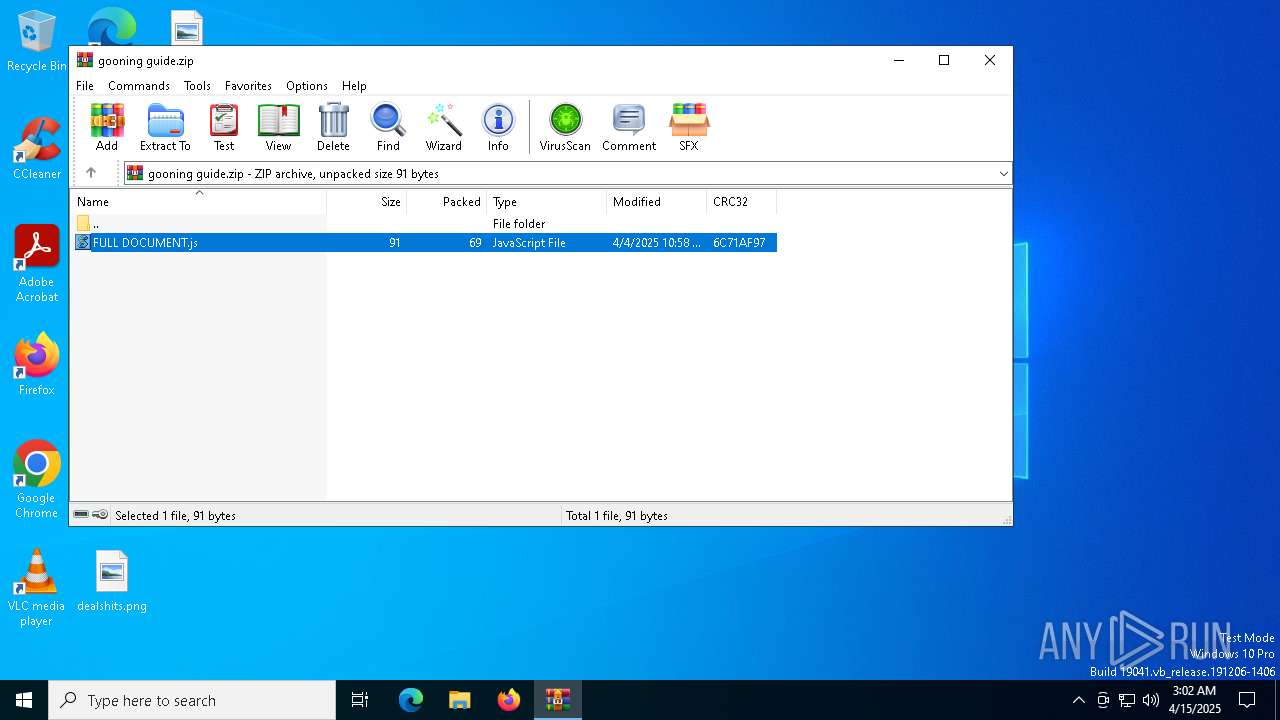
| File name: | gooning guide.zip |
| Full analysis: | https://app.any.run/tasks/ee6d3e48-b627-4d44-81e5-9bb489c75537 |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | April 15, 2025, 03:01:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 1559DB72A0A5BA6889CA7AA762F1751F |
| SHA1: | 383DD9C1EDA3C1172E7FA2C2A8656193D546A1F6 |
| SHA256: | 694A6F26BD8BCA64738C70752CB34B4517A83D9AD49562FA46DCE20D2C02FFD3 |
| SSDEEP: | 6:5jfSgXgllcgEmvMyx5saWG/ZSdxfSgXgllcysvB+l7n:5jKPllV7vMyx5sH+SGPllevBa7 |
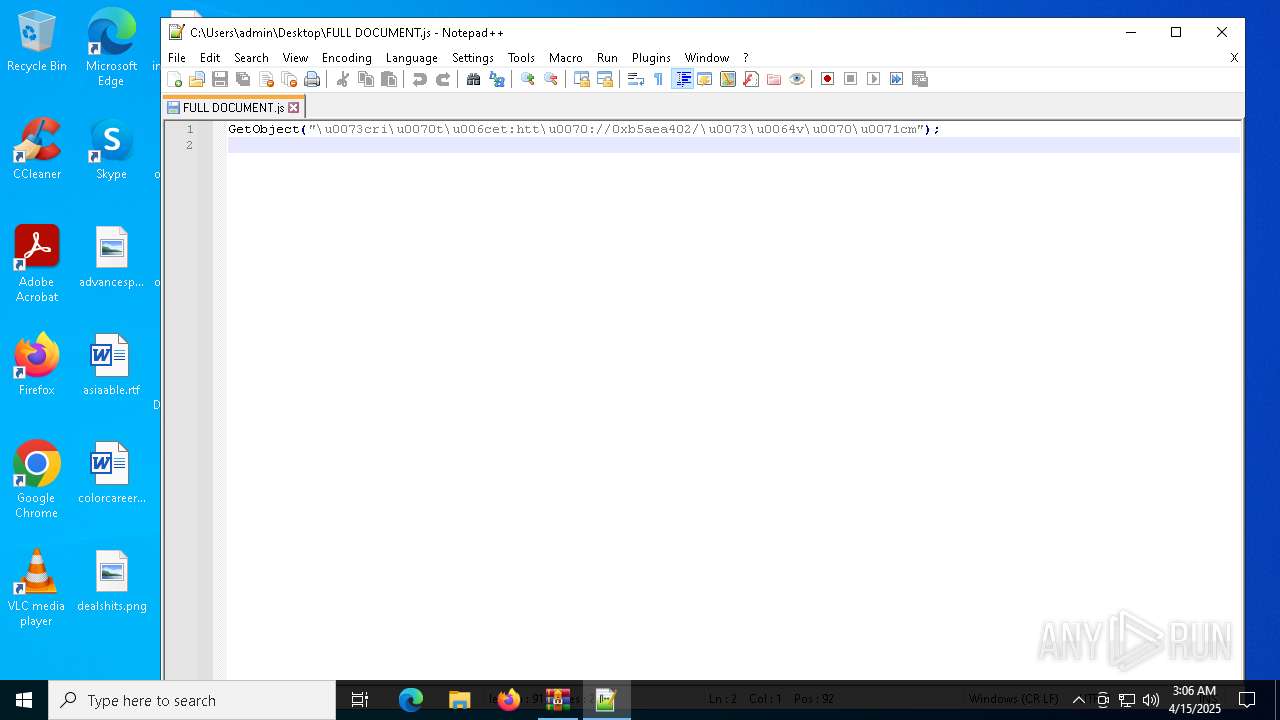
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 5588)
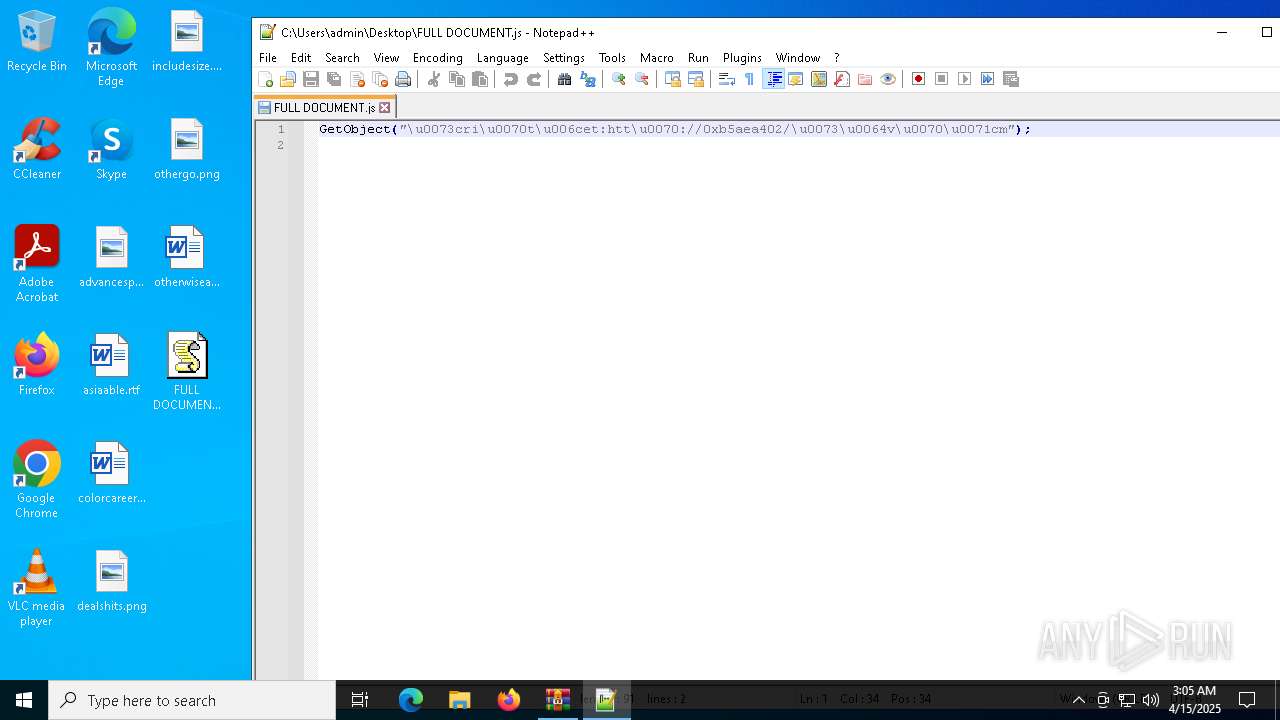
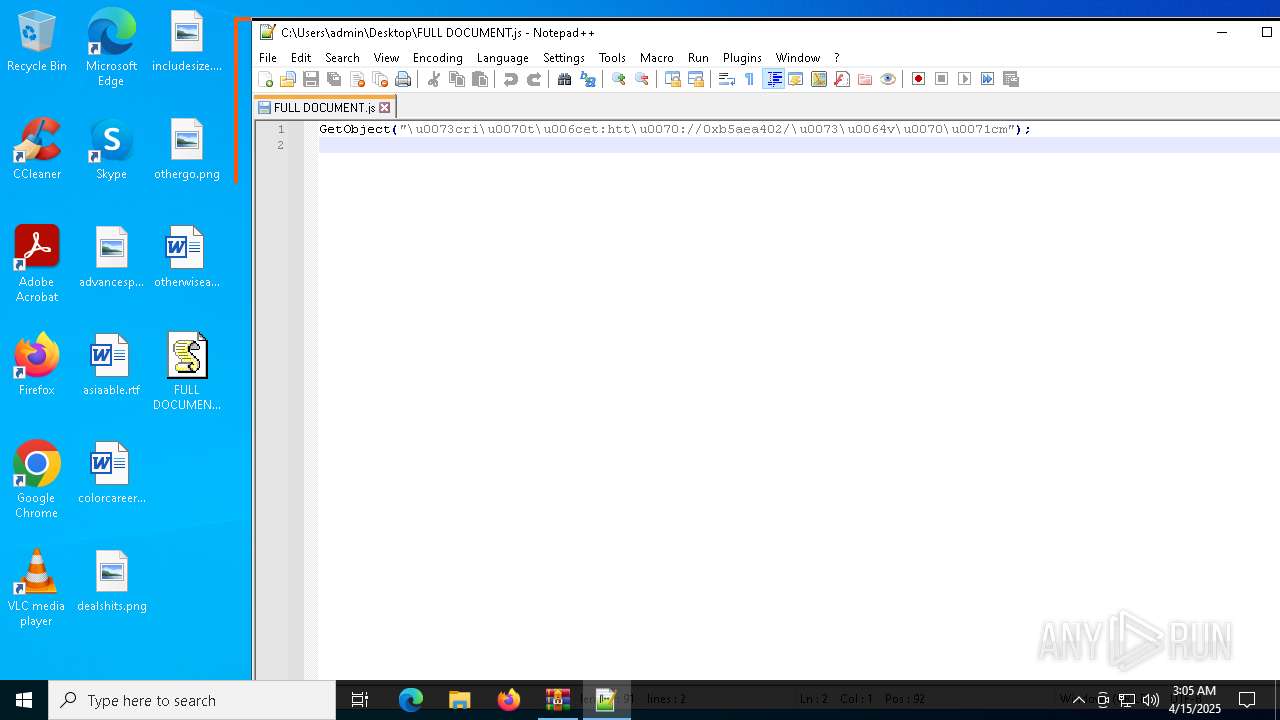
May hide the program window using WMI (SCRIPT)
- wscript.exe (PID: 4880)
Gets information about running processes via WMI (SCRIPT)
- wscript.exe (PID: 4880)
ANDROMEDA mutex has been found
- powershell.exe (PID: 5588)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 5588)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 4880)
Connects to the server without a host name
- wscript.exe (PID: 4880)
- powershell.exe (PID: 5588)
Executed via WMI
- powershell.exe (PID: 5588)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 4880)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 5588)
Reverses array data (POWERSHELL)
- powershell.exe (PID: 5588)
Creates an object to access WMI (SCRIPT)
- wscript.exe (PID: 4880)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 5588)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 5588)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 5588)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 5588)
Application launched itself
- powershell.exe (PID: 5588)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6824)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 5588)
Executable content was dropped or overwritten
- csc.exe (PID: 6824)
INFO
Creates files in the program directory
- wscript.exe (PID: 4880)
Checks proxy server information
- wscript.exe (PID: 4880)
- powershell.exe (PID: 5588)
- slui.exe (PID: 2244)
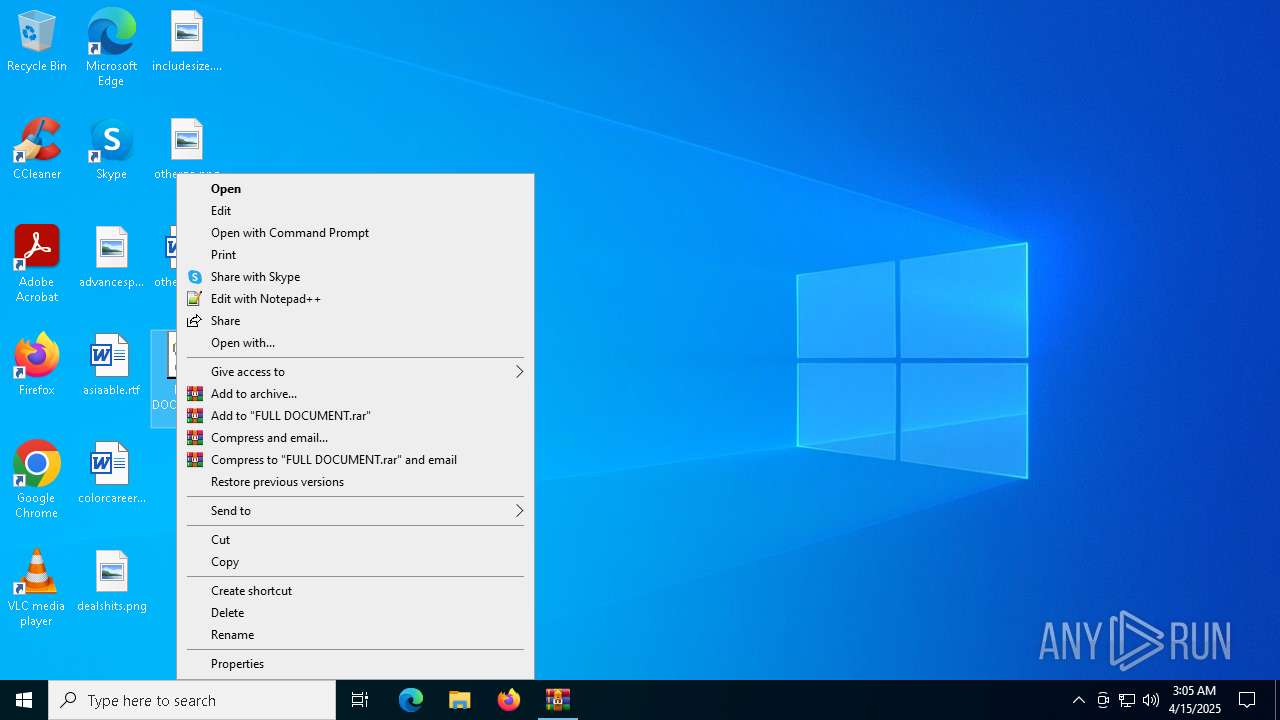
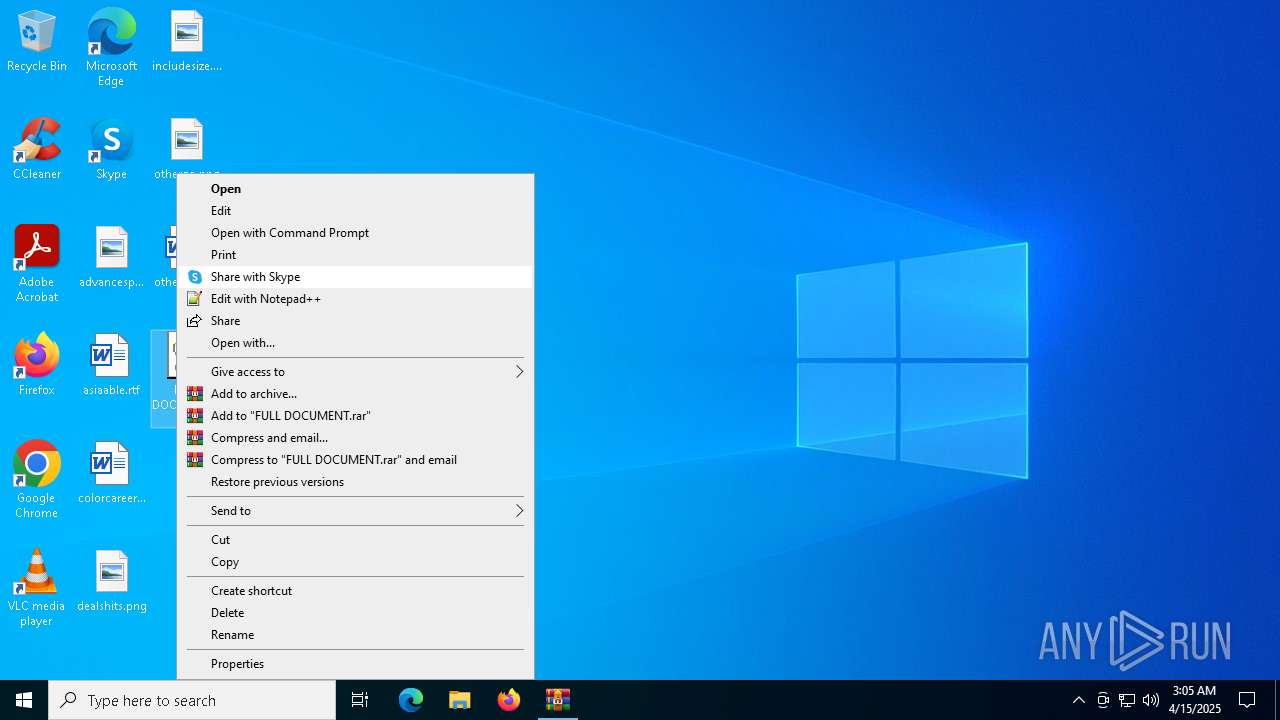
Manual execution by a user
- wscript.exe (PID: 4880)
- notepad++.exe (PID: 2320)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5588)
Disables trace logs
- powershell.exe (PID: 5588)
Checks supported languages
- csc.exe (PID: 6824)
- cvtres.exe (PID: 1280)
Create files in a temporary directory
- csc.exe (PID: 6824)
- cvtres.exe (PID: 1280)
Reads the machine GUID from the registry
- csc.exe (PID: 6824)
Reads the software policy settings
- slui.exe (PID: 6048)
- slui.exe (PID: 2244)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 5588)
- powershell.exe (PID: 5984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:04 10:58:54 |
| ZipCRC: | 0x6c71af97 |
| ZipCompressedSize: | 69 |
| ZipUncompressedSize: | 91 |
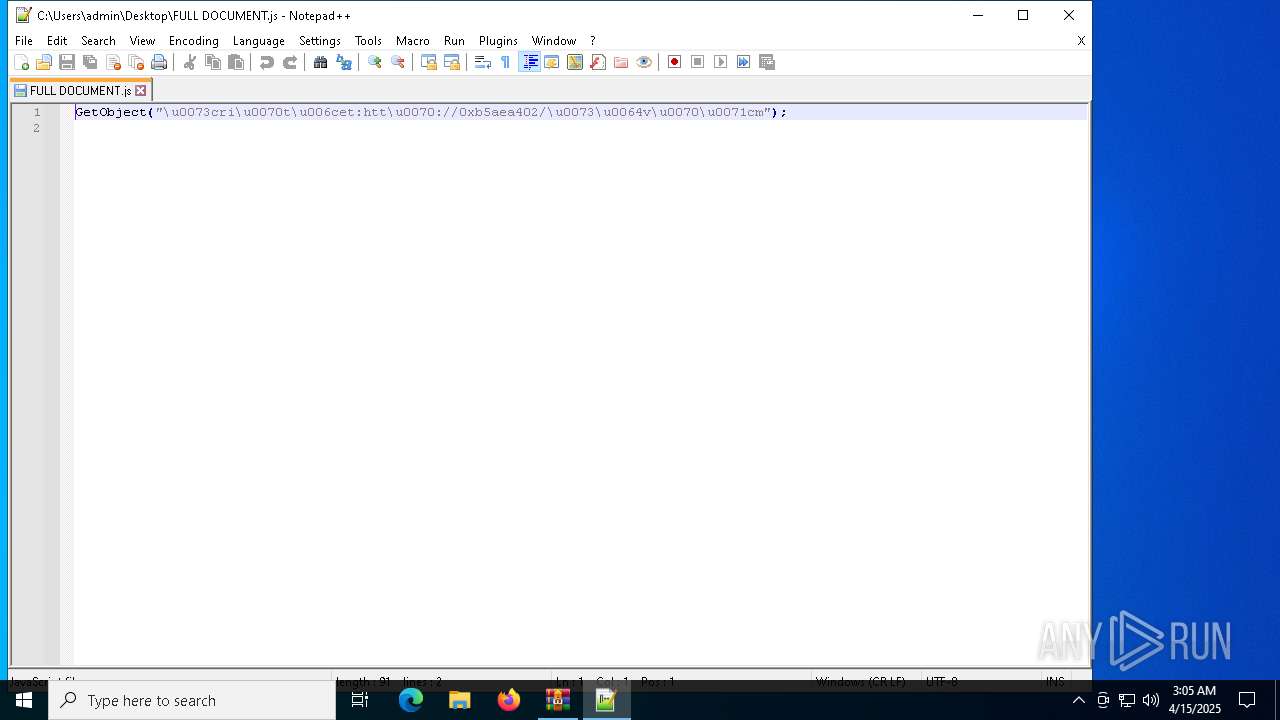
| ZipFileName: | FULL DOCUMENT.js |
Total processes
143
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES801A.tmp" "c:\Users\admin\AppData\Local\Temp\CSC90EE55B8F60E4781A6A1E4549068AC68.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2244 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\FULL DOCUMENT.js" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 3176 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4068 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\FULL DOCUMENT.js" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5588 | powershell.exe -ep bypass -file "C:\ProgramData\of.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5984 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Version 5.1 -s -NoLogo -NoProfile | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6048 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 133
Read events
14 105
Write events
15
Delete events
13
Modification events
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\gooning guide.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
1
Suspicious files
3
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4880 | wscript.exe | C:\ProgramData\of.ps1 | text | |
MD5:0732D0ECC974D89631B46A30F1742B97 | SHA256:09BE209C20934BAA279BD28CDB0A5BCDE776E68C43E1A37ABEA1301DBFD0172F | |||
| 5588 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_q5laqsuo.huk.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6824 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC90EE55B8F60E4781A6A1E4549068AC68.TMP | binary | |
MD5:ECCF70234056AE531CBE1BDAB700ACA7 | SHA256:6C1A1D2AD121A91A5F73DDA90D0FC33055562E70AC81FE9036E8937B7AF47613 | |||
| 4880 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\sdvpqcm[1].htm | html | |
MD5:35CDDFB167D6120E1D511724027402AA | SHA256:1BD2101021161F39987C08FDC508859AD05F3E8F63BB857057A09D4EC68B026E | |||
| 5588 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_edwpzeom.gdt.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5984 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wd3522j3.0.cs | text | |
MD5:6C161CFA88ACEE4E558632F3093AFEB2 | SHA256:D5ECDEA0F70D994AD880D4EF4E10B9452B19597BE697834D8BBE84ABE5C4AC61 | |||
| 5984 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wd3522j3.cmdline | text | |
MD5:91A81E2883343DDF47B86B70E4B6E6FE | SHA256:9C504197F3C8FEC2CA629C509E2CE244ABF0AED57C639F3154B5E5C44D0D5157 | |||
| 5984 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_azuiudmi.luh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2320 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:FE22EC5755BC98988F9656F73B2E6FB8 | SHA256:F972C425CE176E960F6347F1CA2F64A8CE2B95A375C33A03E57538052BA0624D | |||
| 6824 | csc.exe | C:\Users\admin\AppData\Local\Temp\wd3522j3.dll | executable | |
MD5:C1747BEE5AFCF85466DCF9B298E3CE70 | SHA256:DB9F513DBCD63C9182E7F002B6615DA9871AC1EED95149A3472C82084842A7FA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
24
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1168 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5588 | powershell.exe | GET | 404 | 181.174.164.2:80 | http://181.174.164.2/649566714 | unknown | — | — | unknown |
5588 | powershell.exe | GET | 404 | 181.174.164.2:80 | http://181.174.164.2/649566714 | unknown | — | — | unknown |
5588 | powershell.exe | GET | 404 | 181.174.164.2:80 | http://181.174.164.2/649566714 | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1168 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4880 | wscript.exe | GET | 200 | 181.174.164.2:80 | http://181.174.164.2/sdvpqcm | unknown | — | — | unknown |
5588 | powershell.exe | GET | 200 | 181.174.164.2:80 | http://181.174.164.2/649566714 | unknown | — | — | unknown |
5588 | powershell.exe | GET | 404 | 181.174.164.2:80 | http://181.174.164.2/649566714 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1168 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |