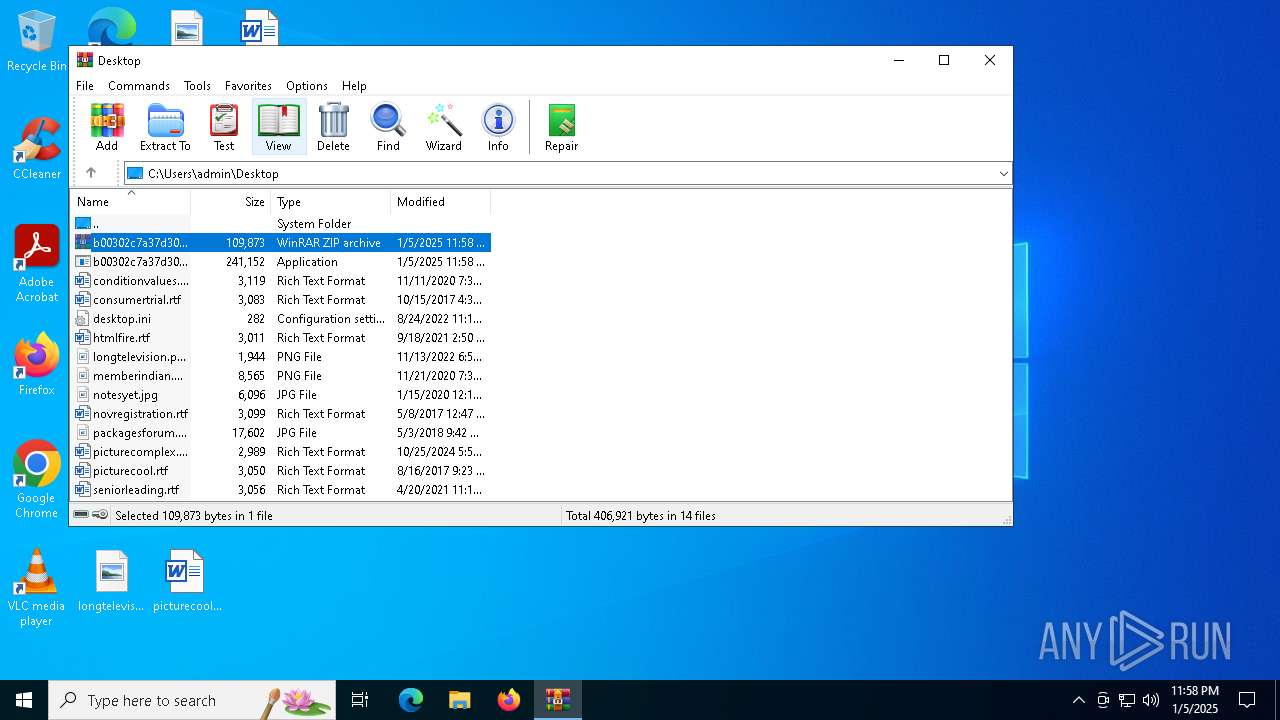
| File name: | b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.zip |
| Full analysis: | https://app.any.run/tasks/8a904d79-a6dd-4904-8653-43d28183138c |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | January 05, 2025, 23:58:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 375AB9C413EA247728523DC469D1C149 |
| SHA1: | 19629C06EB894D2B67474E87FD037704D6772092 |
| SHA256: | 692D1ADAC4CD53D5FD9FBE68BBF150F6F55EEA9D45018EA936D6245349C58CE4 |
| SSDEEP: | 3072:6m+igcuOftMx4P5rSgK6CWmYJ7kH6fmb35uDvZjaNJ3LenH:6m+2Mx44gfCZYJ7c6+L5g8ziH |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6592)
Changes the autorun value in the registry
- nbveek.exe (PID: 6804)
Uses Task Scheduler to run other applications
- nbveek.exe (PID: 6804)
AMADEY has been detected (YARA)
- nbveek.exe (PID: 6804)
AMADEY has been detected (SURICATA)
- nbveek.exe (PID: 6804)
Connects to the CnC server
- nbveek.exe (PID: 6804)
SUSPICIOUS
Reads security settings of Internet Explorer
- b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe (PID: 6760)
- WinRAR.exe (PID: 6592)
- nbveek.exe (PID: 6804)
Executable content was dropped or overwritten
- b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe (PID: 6760)
Starts itself from another location
- b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe (PID: 6760)
Starts CMD.EXE for commands execution
- nbveek.exe (PID: 6804)
- cmd.exe (PID: 6904)
Application launched itself
- cmd.exe (PID: 6904)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 6904)
Process requests binary or script from the Internet
- nbveek.exe (PID: 6804)
The process executes via Task Scheduler
- nbveek.exe (PID: 1596)
- nbveek.exe (PID: 6504)
- nbveek.exe (PID: 2600)
Contacting a server suspected of hosting an CnC
- nbveek.exe (PID: 6804)
Connects to the server without a host name
- nbveek.exe (PID: 6804)
INFO
Manual execution by a user
- b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe (PID: 6760)
Create files in a temporary directory
- b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe (PID: 6760)
Checks supported languages
- b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe (PID: 6760)
- nbveek.exe (PID: 6804)
- nbveek.exe (PID: 1596)
- nbveek.exe (PID: 6504)
- nbveek.exe (PID: 2600)
Process checks computer location settings
- b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe (PID: 6760)
- nbveek.exe (PID: 6804)
Reads the computer name
- b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe (PID: 6760)
- nbveek.exe (PID: 6804)
The process uses the downloaded file
- b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe (PID: 6760)
- nbveek.exe (PID: 6804)
Checks proxy server information
- nbveek.exe (PID: 6804)
Creates files or folders in the user directory
- nbveek.exe (PID: 6804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:01:05 22:00:10 |
| ZipCRC: | 0xa4692c09 |
| ZipCompressedSize: | 109617 |
| ZipUncompressedSize: | 241152 |
| ZipFileName: | b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe |
Total processes
133
Monitored processes
16
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1596 | "C:\Users\admin\AppData\Local\Temp\4b9a106e76\nbveek.exe" | C:\Users\admin\AppData\Local\Temp\4b9a106e76\nbveek.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2600 | "C:\Users\admin\AppData\Local\Temp\4b9a106e76\nbveek.exe" | C:\Users\admin\AppData\Local\Temp\4b9a106e76\nbveek.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6504 | "C:\Users\admin\AppData\Local\Temp\4b9a106e76\nbveek.exe" | C:\Users\admin\AppData\Local\Temp\4b9a106e76\nbveek.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6592 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6760 | "C:\Users\admin\Desktop\b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe" | C:\Users\admin\Desktop\b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6804 | "C:\Users\admin\AppData\Local\Temp\4b9a106e76\nbveek.exe" | C:\Users\admin\AppData\Local\Temp\4b9a106e76\nbveek.exe | b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6860 | "C:\Windows\System32\schtasks.exe" /Create /SC MINUTE /MO 1 /TN nbveek.exe /TR "C:\Users\admin\AppData\Local\Temp\4b9a106e76\nbveek.exe" /F | C:\Windows\SysWOW64\schtasks.exe | — | nbveek.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6876 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6904 | "C:\Windows\System32\cmd.exe" /k echo Y|CACLS "nbveek.exe" /P "admin:N"&&CACLS "nbveek.exe" /P "admin:R" /E&&echo Y|CACLS "..\4b9a106e76" /P "admin:N"&&CACLS "..\4b9a106e76" /P "admin:R" /E&&Exit | C:\Windows\SysWOW64\cmd.exe | — | nbveek.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6924 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 589
Read events
2 569
Write events
20
Delete events
0
Modification events
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.zip | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6804) nbveek.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders |
| Operation: | write | Name: | Startup |
Value: C:\Users\admin\AppData\Local\Temp\4b9a106e76\ | |||
| (PID) Process: | (6804) nbveek.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6760 | b00302c7a37d30e1d649945bce637c2be5ef5a1055e572df9866ef8281964b65.exe | C:\Users\admin\AppData\Local\Temp\4b9a106e76\nbveek.exe | executable | |
MD5:6779CD6F17FA7536C4490CC6D72A00A0 | SHA256:B00302C7A37D30E1D649945BCE637C2BE5EF5A1055E572DF9866EF8281964B65 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
24
DNS requests
7
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.21.20.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | svchost.exe | GET | 200 | 2.21.20.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6804 | nbveek.exe | GET | — | 62.204.41.242:80 | http://62.204.41.242/9vZbns/Plugins/cred64.dll | unknown | — | — | malicious |
6804 | nbveek.exe | GET | — | 62.204.41.242:80 | http://62.204.41.242/9vZbns/Plugins/cred64.dll | unknown | — | — | malicious |
6804 | nbveek.exe | GET | — | 62.204.41.242:80 | http://62.204.41.242/9vZbns/Plugins/cred64.dll | unknown | — | — | malicious |
5496 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6804 | nbveek.exe | POST | — | 62.204.41.242:80 | http://62.204.41.242/9vZbns/index.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | svchost.exe | 2.21.20.137:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.21.20.137:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6804 | nbveek.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 6 |
6804 | nbveek.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Check-In |
6804 | nbveek.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Bot Activity (POST) M2 |
6804 | nbveek.exe | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |
6804 | nbveek.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host DLL Request |
6804 | nbveek.exe | A Network Trojan was detected | BOTNET [ANY.RUN] Amadey Stealer plugin download request |
6804 | nbveek.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host DLL Request |
6804 | nbveek.exe | A Network Trojan was detected | BOTNET [ANY.RUN] Amadey Stealer plugin download request |
6804 | nbveek.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host DLL Request |
6804 | nbveek.exe | A Network Trojan was detected | BOTNET [ANY.RUN] Amadey Stealer plugin download request |