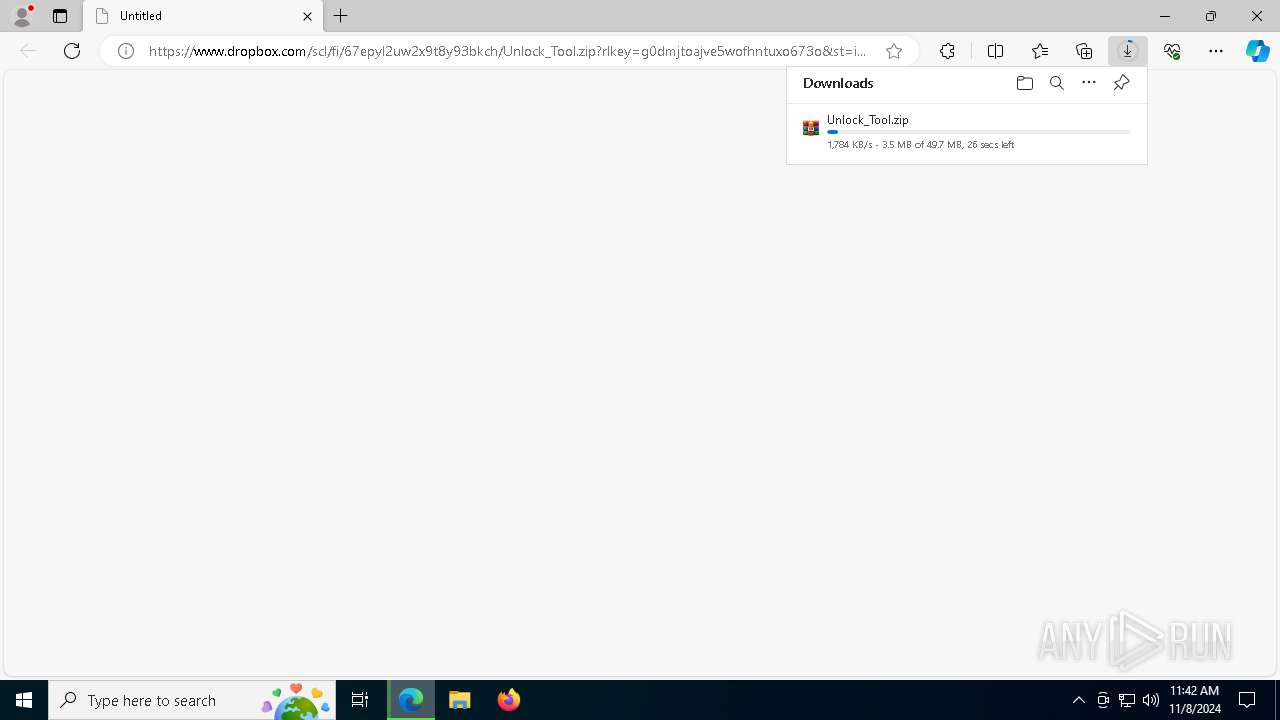
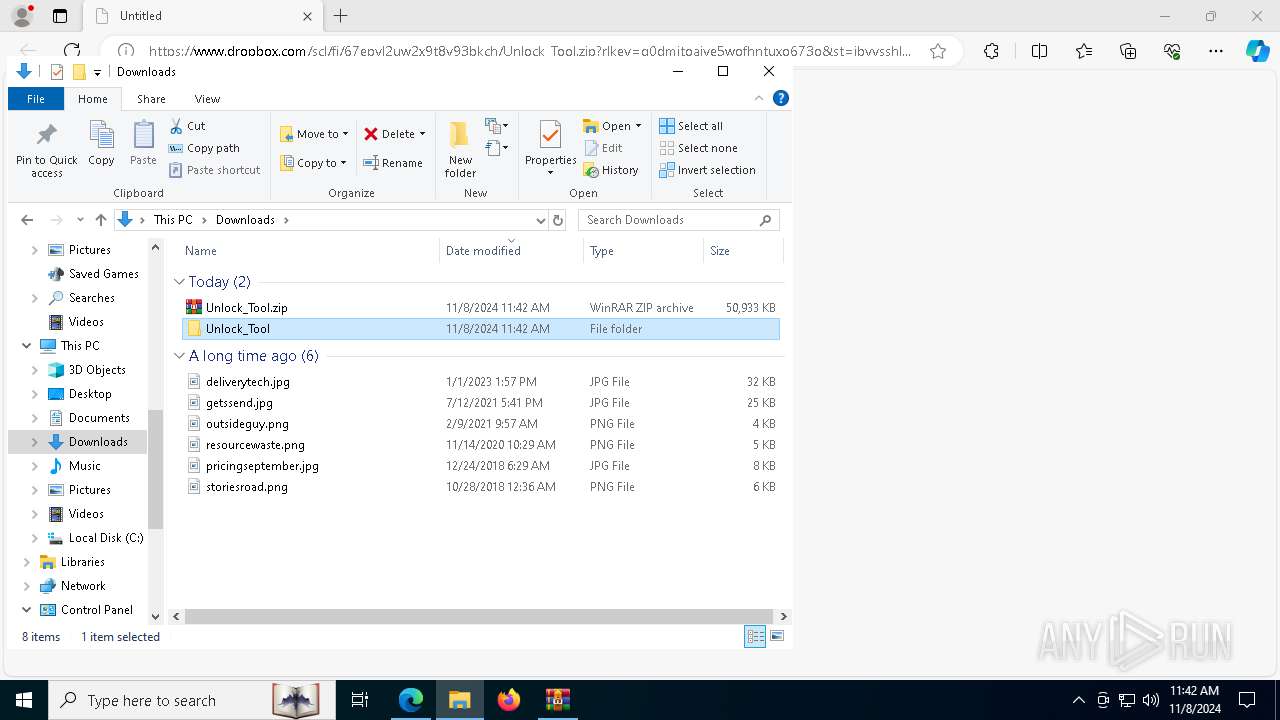
| URL: | https://www.dropbox.com/scl/fi/67epyl2uw2x9t8y93bkch/Unlock_Tool.zip?rlkey=g0dmjtoajve5wofhntuxo673o&st=ibvvsshl&dl=1 |
| Full analysis: | https://app.any.run/tasks/d36c7638-19b0-4b85-bf27-ebf8f5325b8c |
| Verdict: | Malicious activity |
| Threats: | Vidar is a dangerous malware that steals information and cryptocurrency from infected users. It derives its name from the ancient Scandinavian god of Vengeance. This stealer has been terrorizing the internet since 2018. |
| Analysis date: | November 08, 2024, 11:42:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CEB3F228F236AAEB62F31B4D68167DD4 |
| SHA1: | 1E9441B890B7D6A7F394B852606C8054F33D46D8 |
| SHA256: | 69031799D0085883215DA2677794AF75705288000595EC365C35FF4941B7AD38 |
| SSDEEP: | 3:N8DSLcVHGkG6TSw4ASOReHOafJKSLcaZOAcYnsmTAQdNl3TSNDGpNJDB:2OLHk9SAMw5Y5193e8pNJDB |
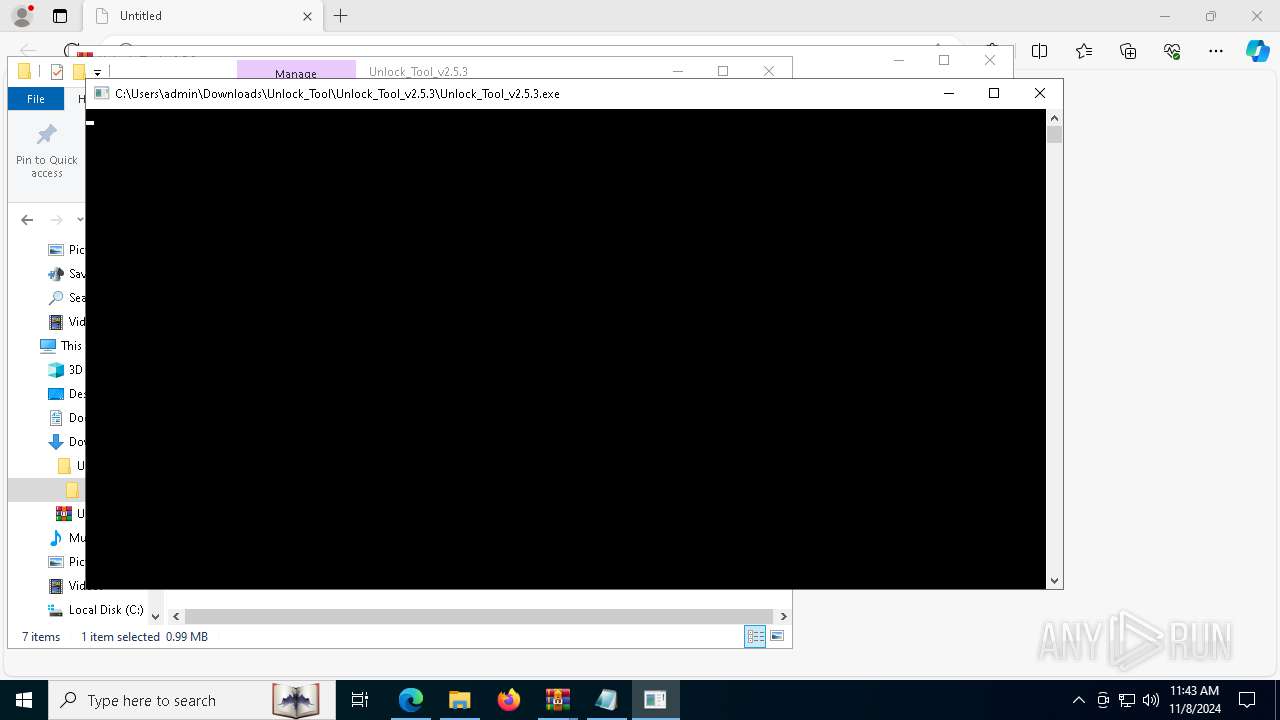
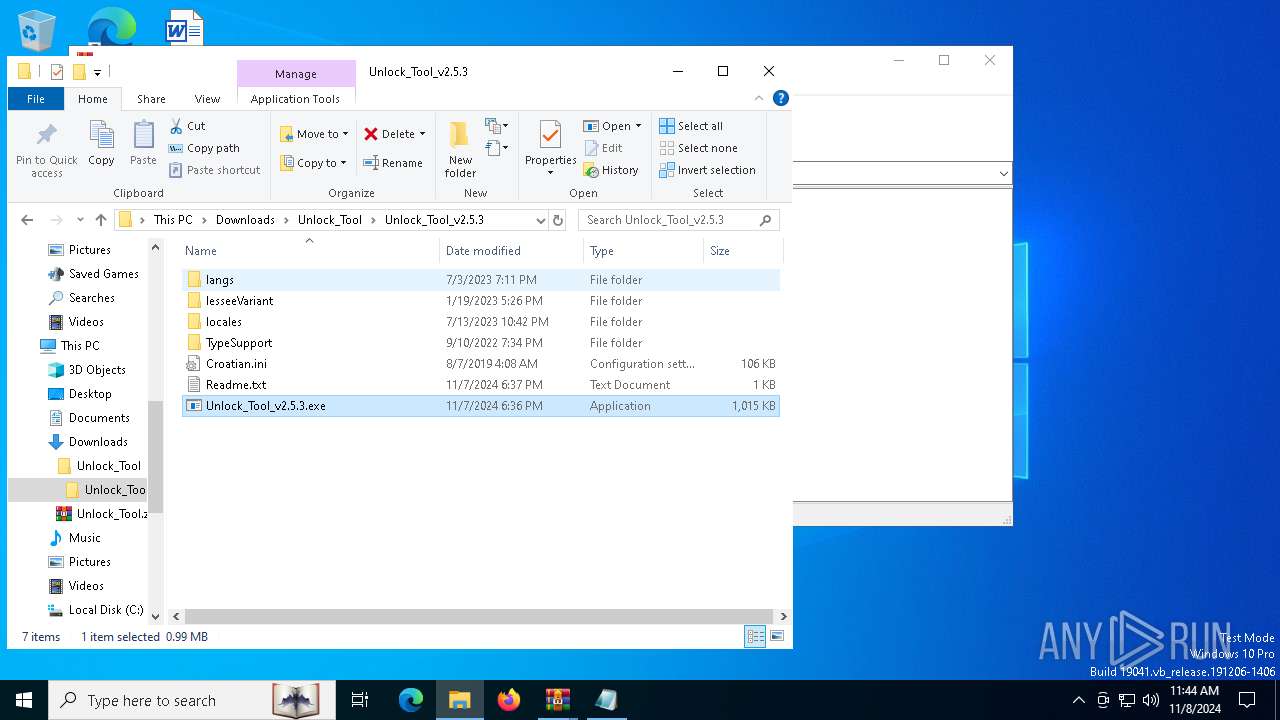
MALICIOUS
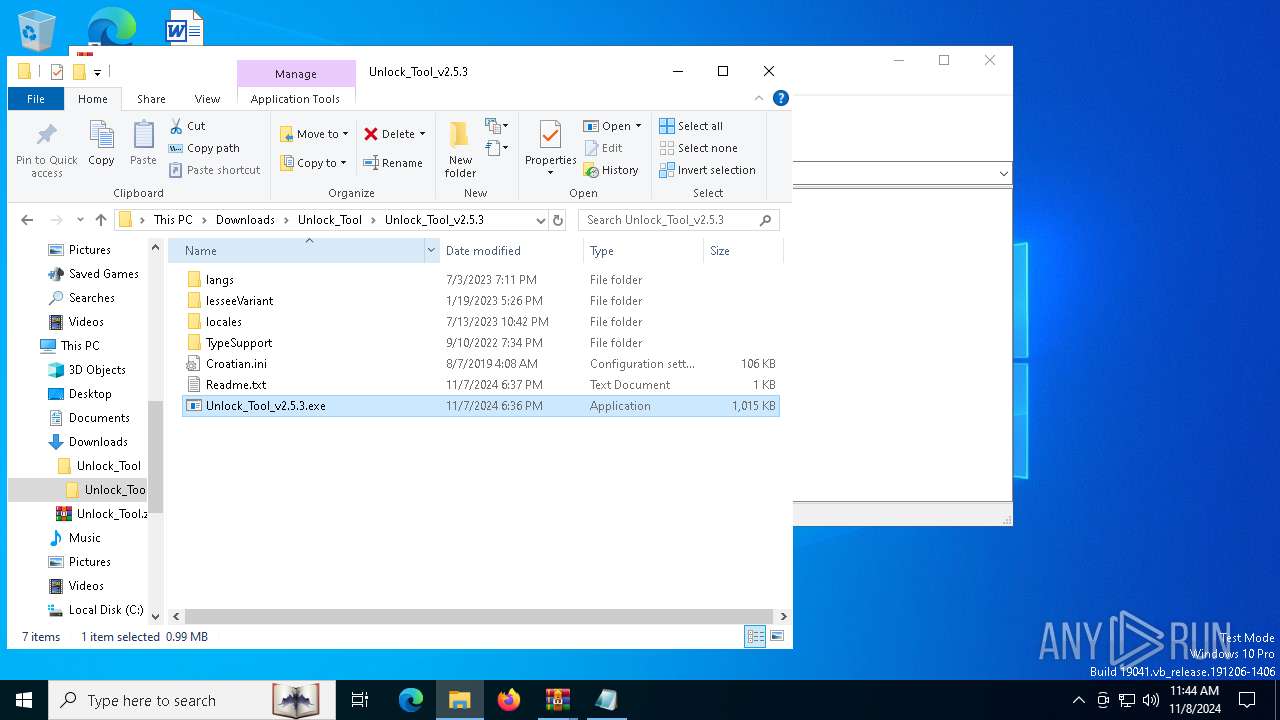
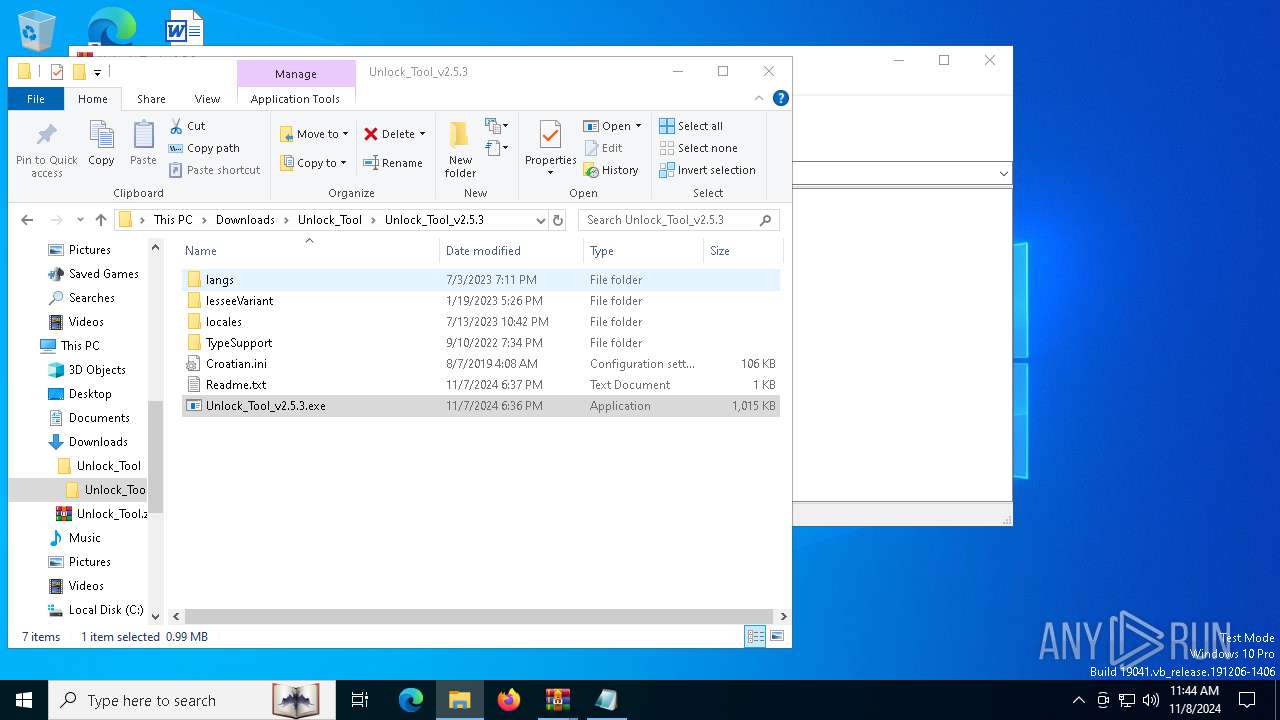
VIDAR has been detected (YARA)
- Unlock_Tool_v2.5.3.exe (PID: 7636)
- Unlock_Tool_v2.5.3.exe (PID: 1584)
SUSPICIOUS
Application launched itself
- Unlock_Tool_v2.5.3.exe (PID: 7204)
- Unlock_Tool_v2.5.3.exe (PID: 7980)
- Unlock_Tool_v2.5.3.exe (PID: 5892)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Unlock_Tool_v2.5.3.exe (PID: 1584)
- Unlock_Tool_v2.5.3.exe (PID: 7636)
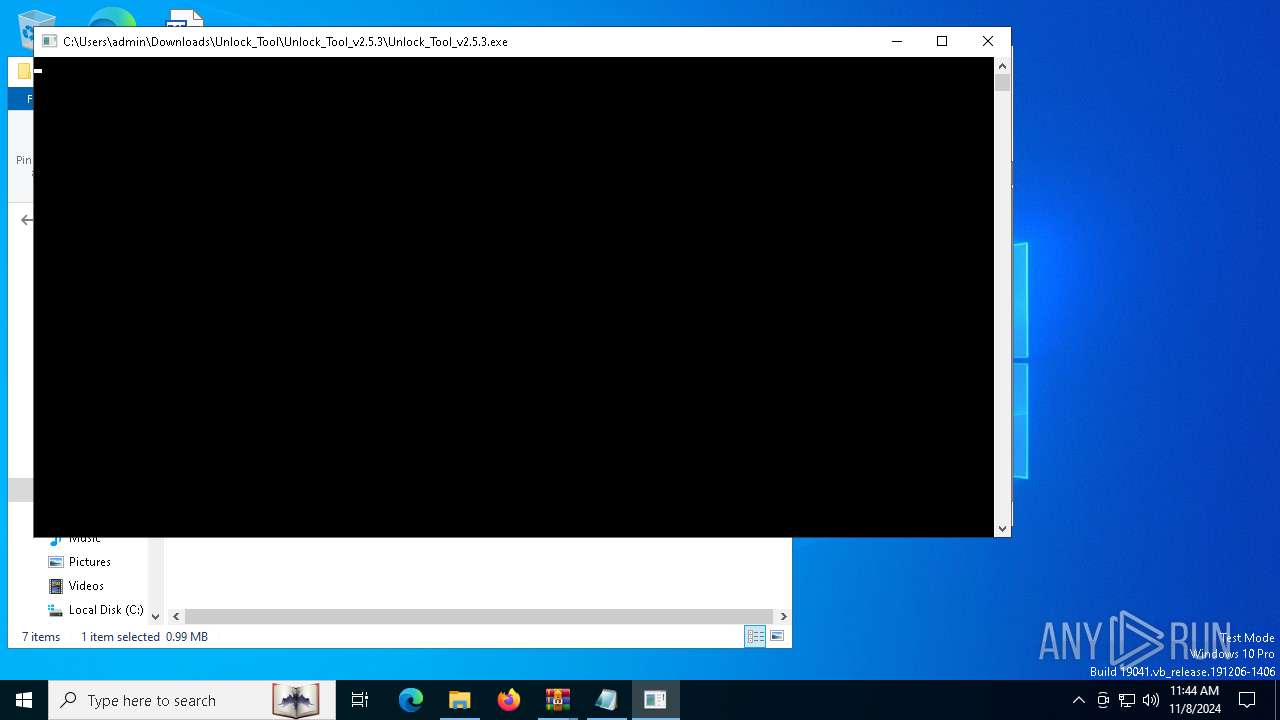
Executes application which crashes
- Unlock_Tool_v2.5.3.exe (PID: 7204)
- Unlock_Tool_v2.5.3.exe (PID: 7980)
- Unlock_Tool_v2.5.3.exe (PID: 5892)
Process drops legitimate windows executable
- Unlock_Tool_v2.5.3.exe (PID: 1584)
The process drops C-runtime libraries
- Unlock_Tool_v2.5.3.exe (PID: 1584)
Executable content was dropped or overwritten
- Unlock_Tool_v2.5.3.exe (PID: 1584)
The process drops Mozilla's DLL files
- Unlock_Tool_v2.5.3.exe (PID: 1584)
Starts CMD.EXE for commands execution
- Unlock_Tool_v2.5.3.exe (PID: 7636)
- Unlock_Tool_v2.5.3.exe (PID: 6880)
- Unlock_Tool_v2.5.3.exe (PID: 1584)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3836)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 7096)
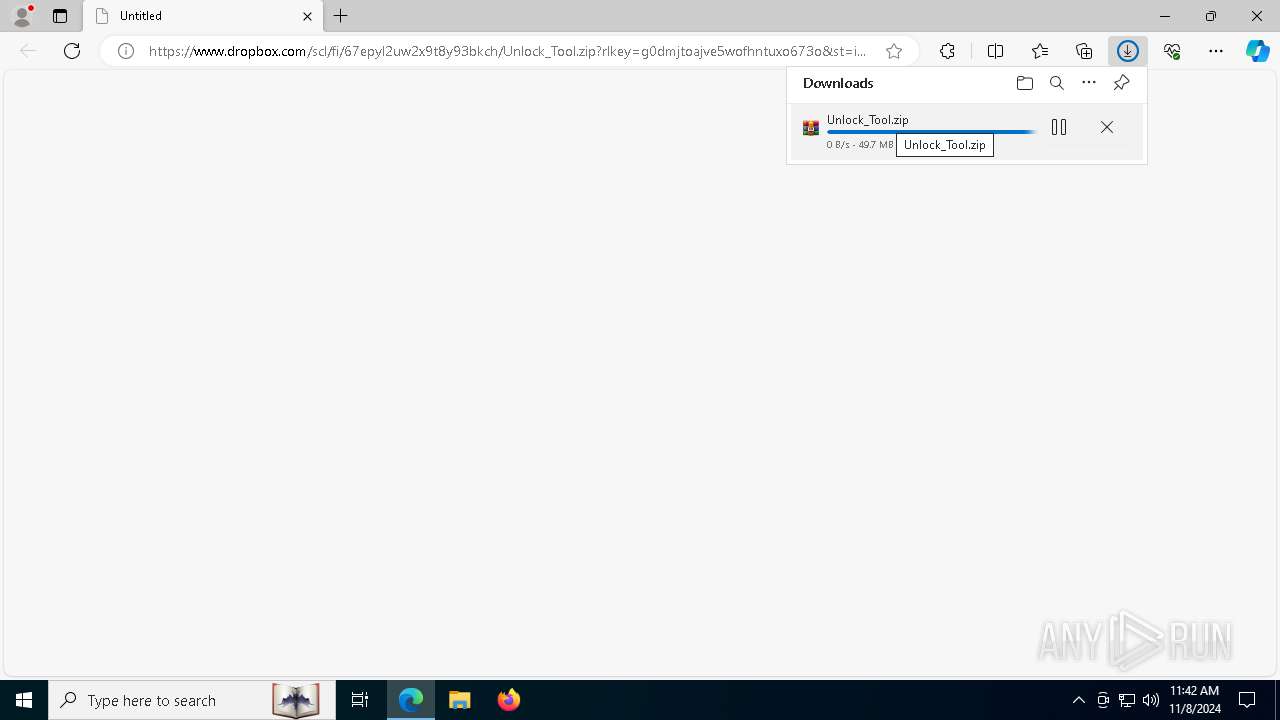
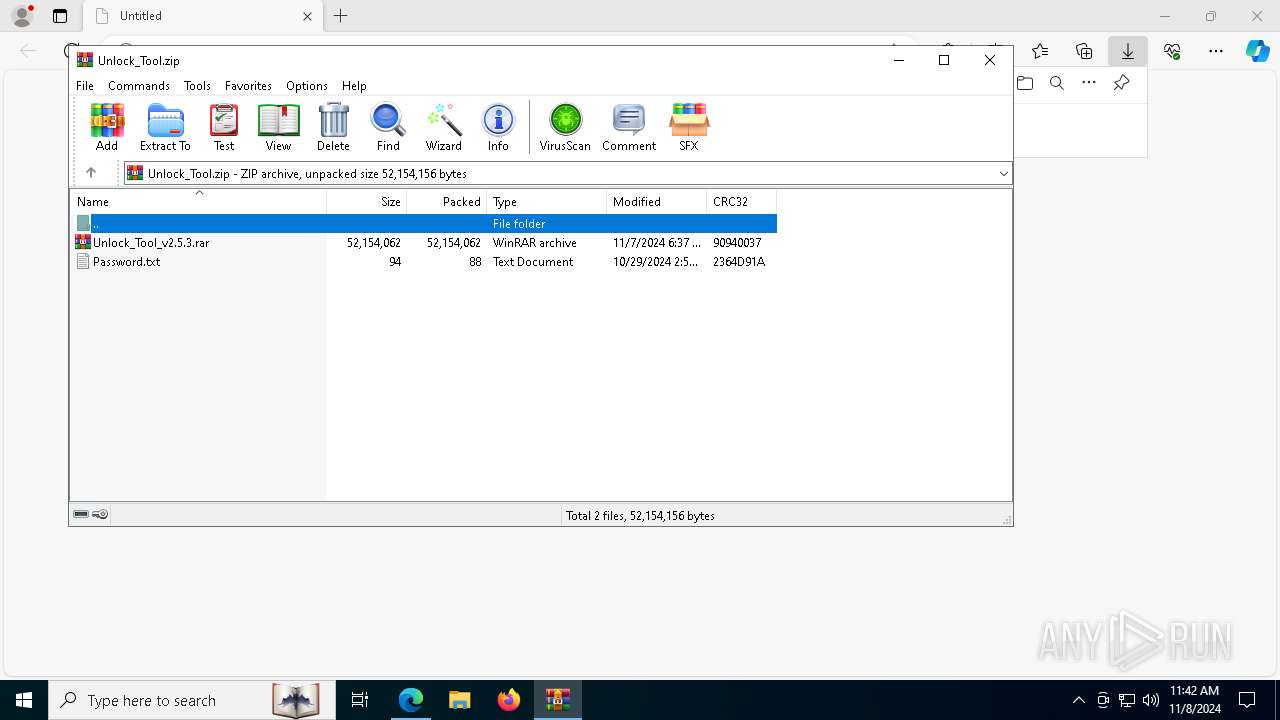
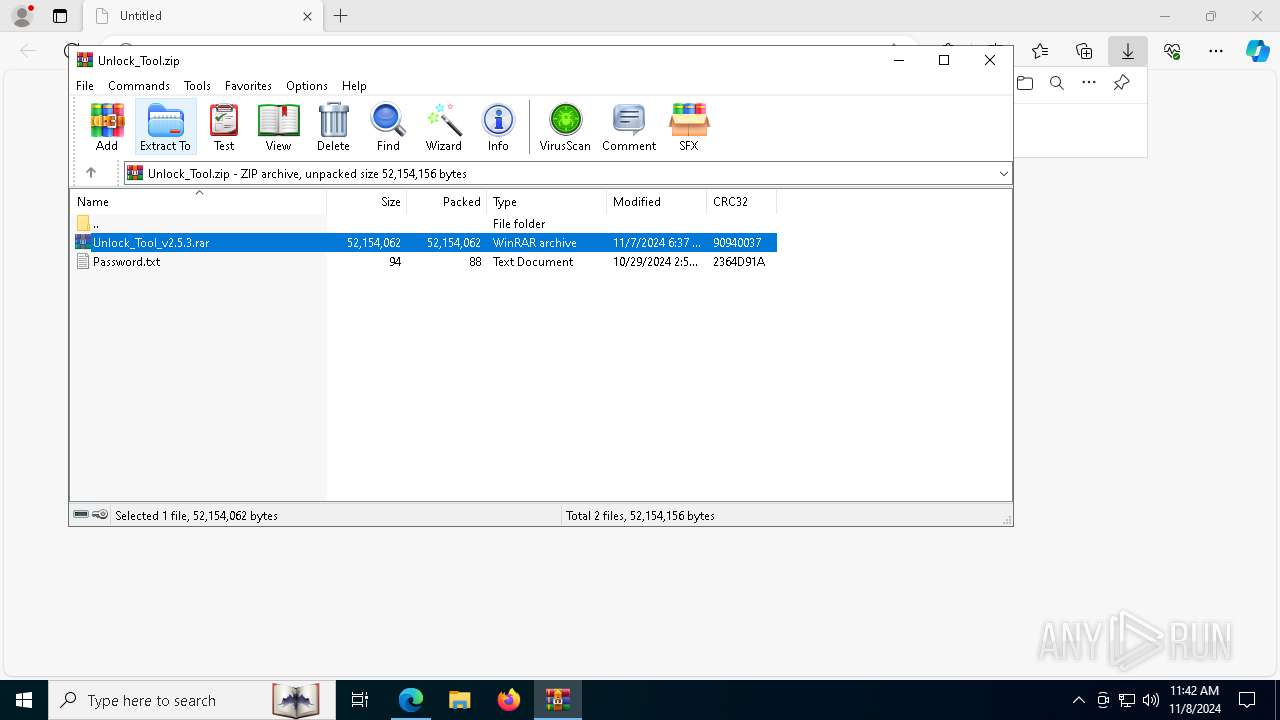
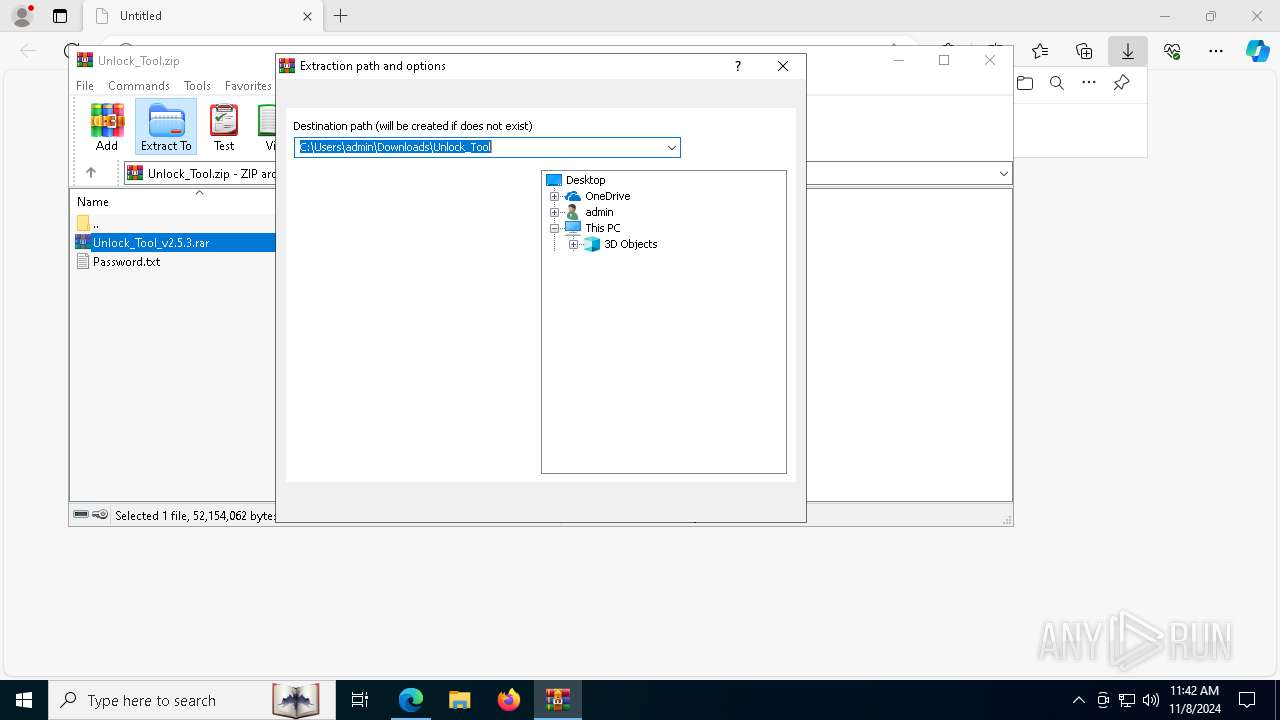
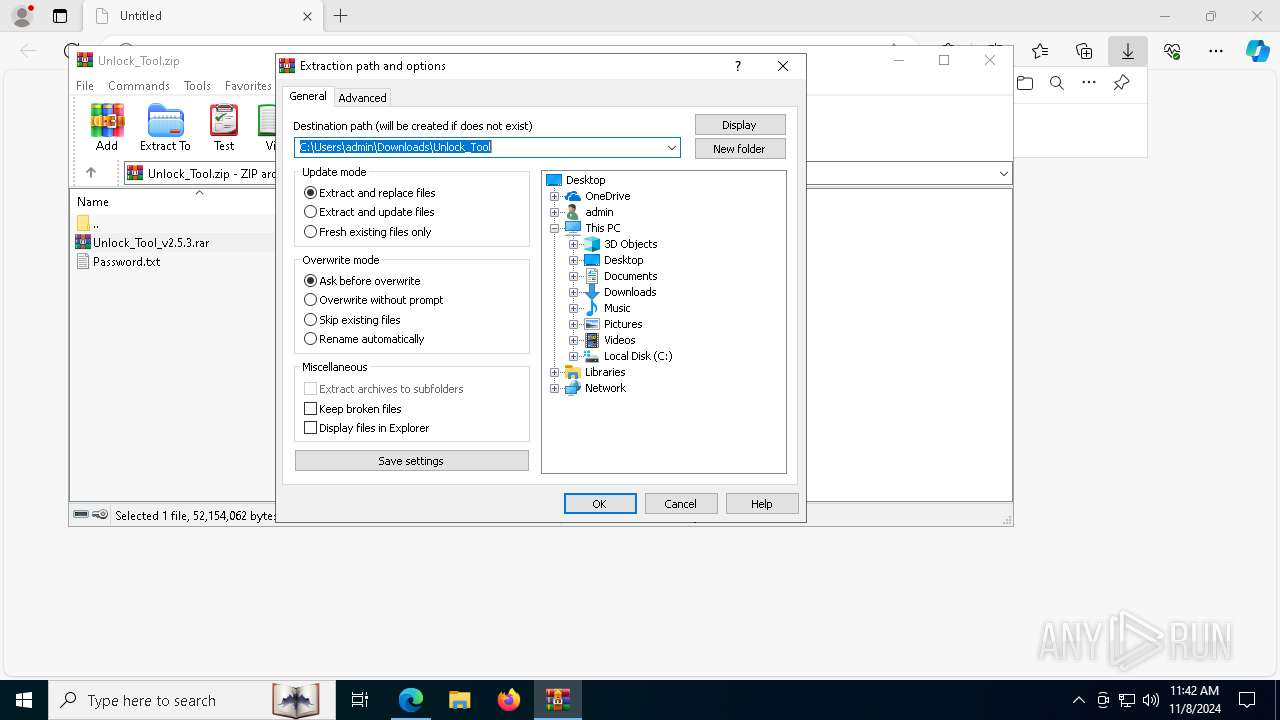
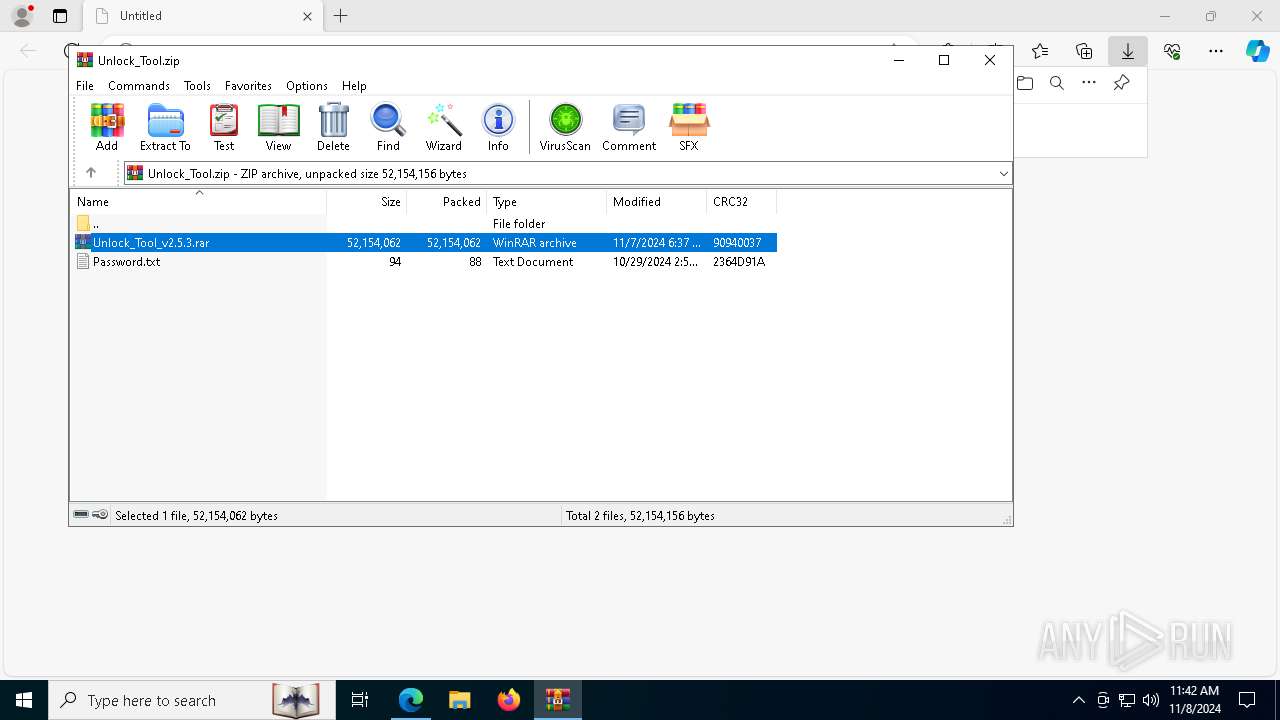
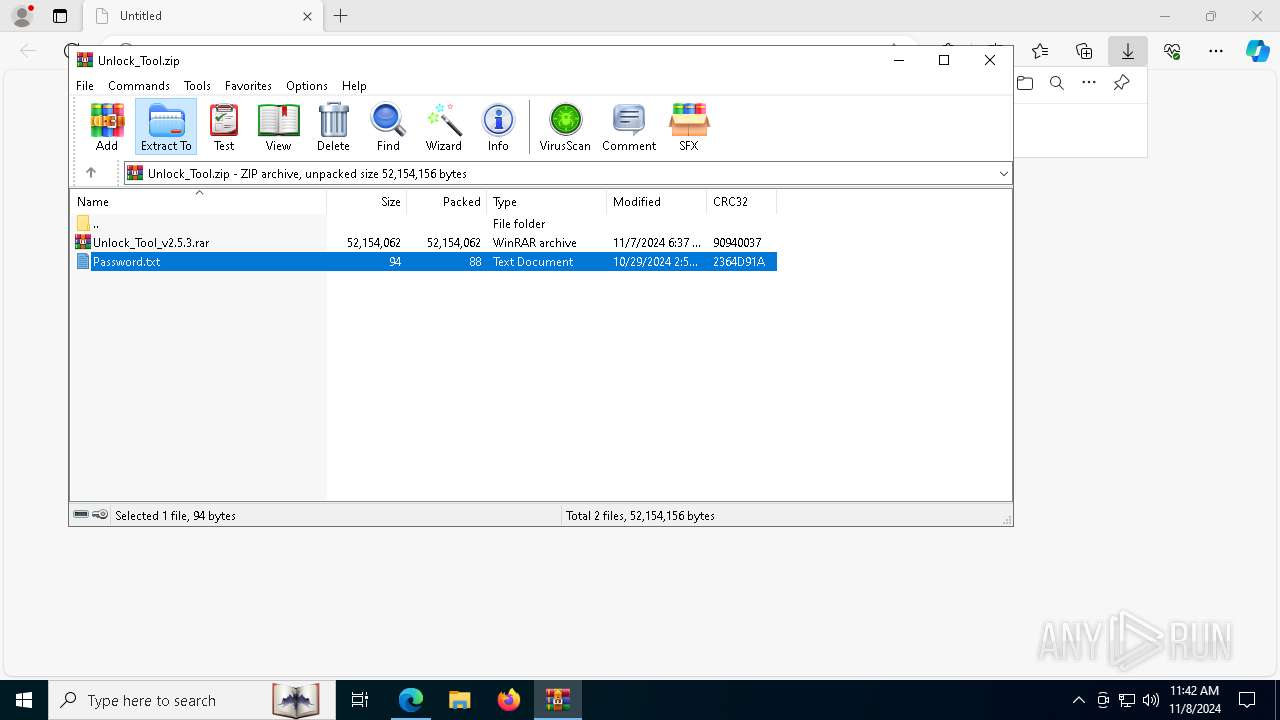
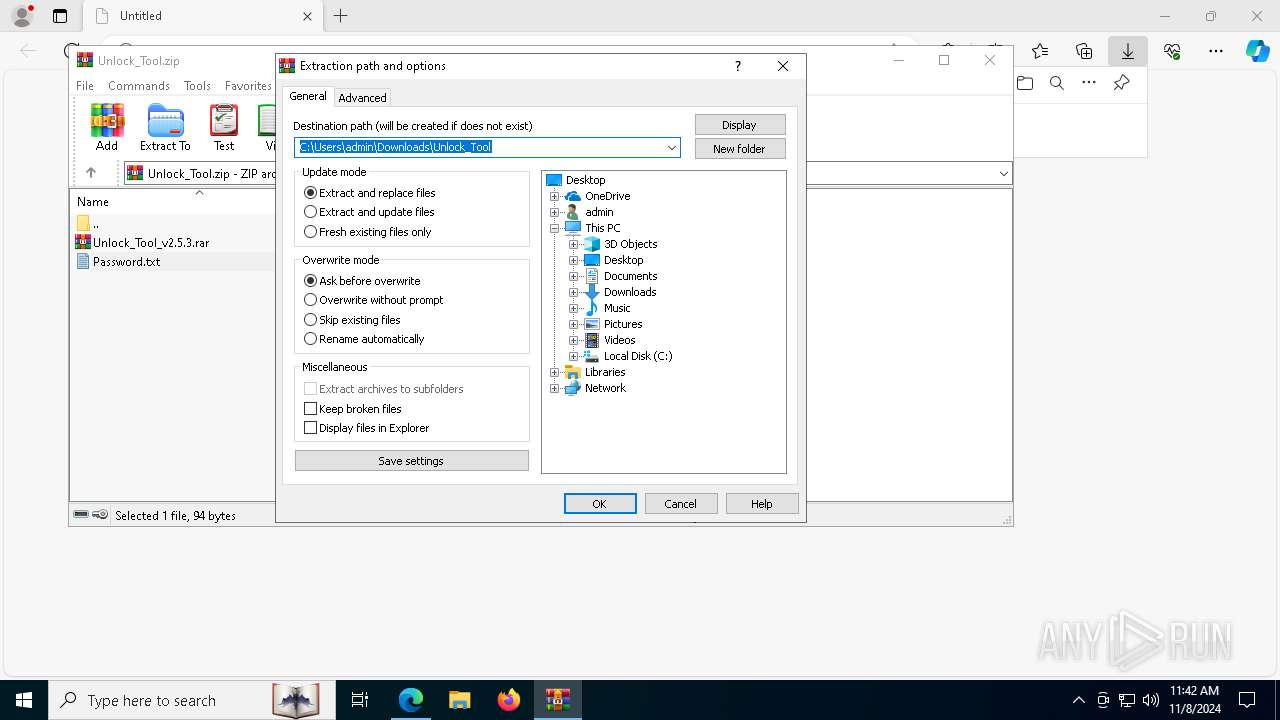
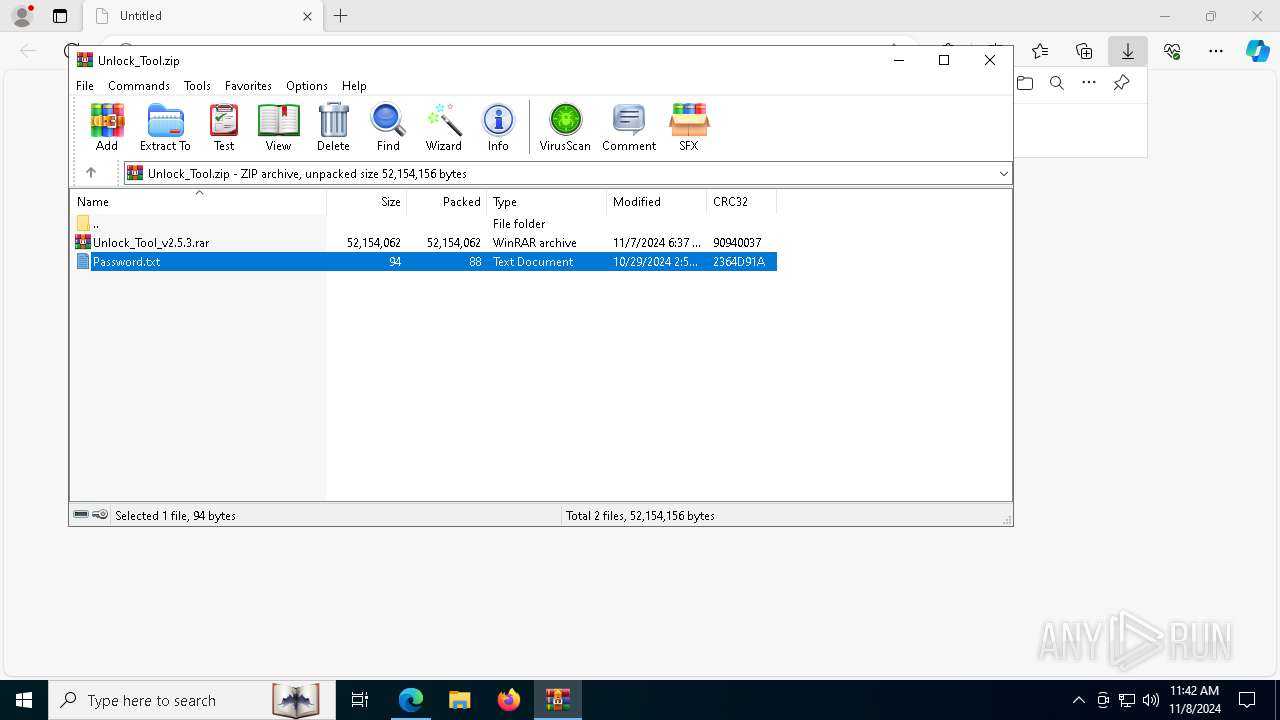
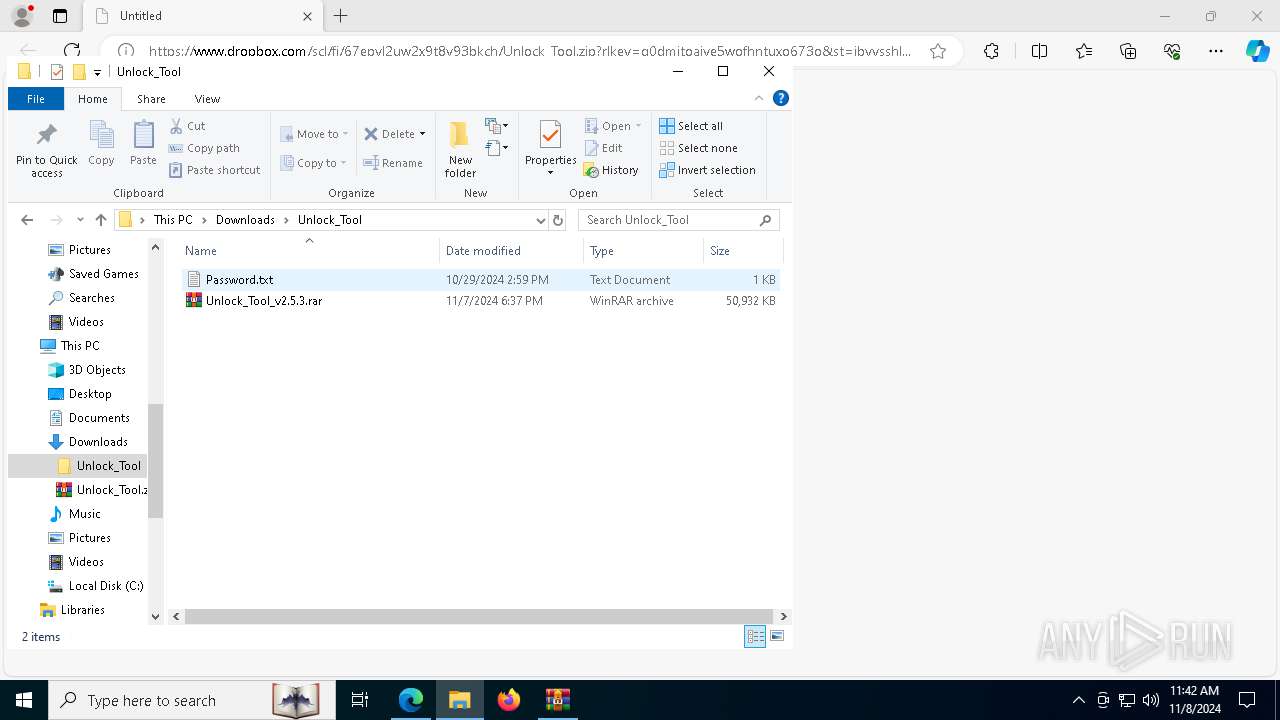
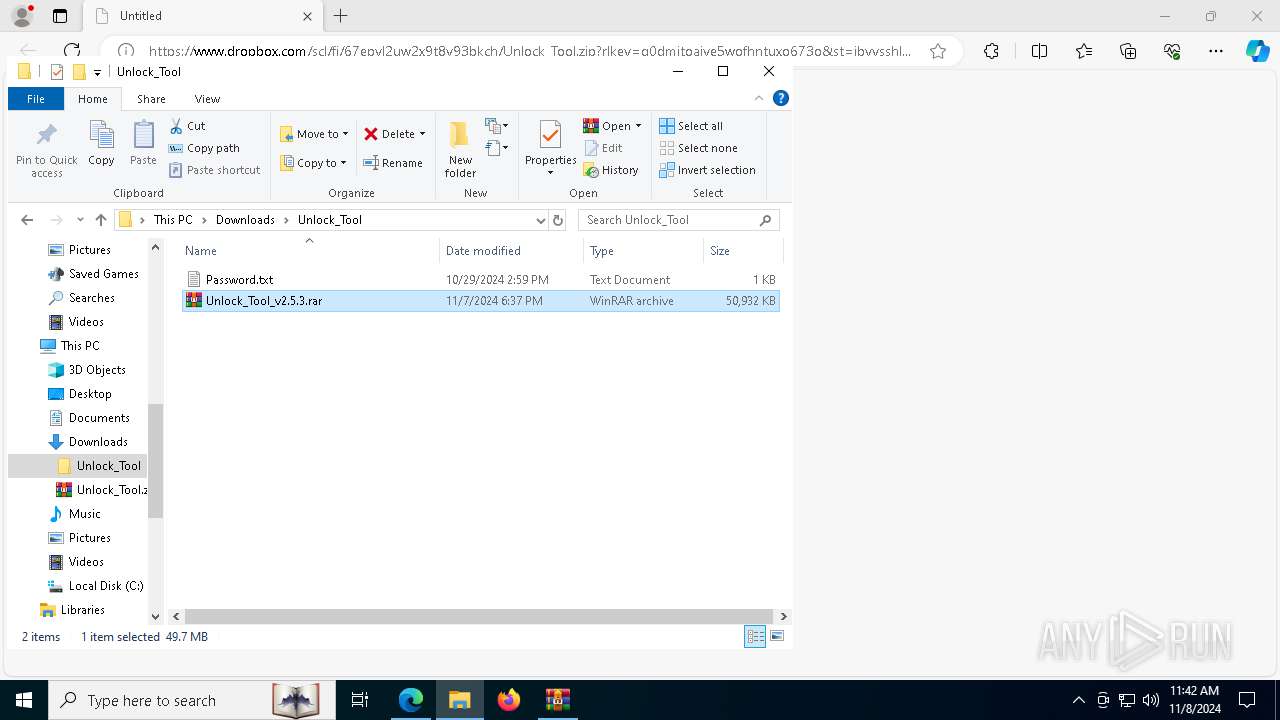
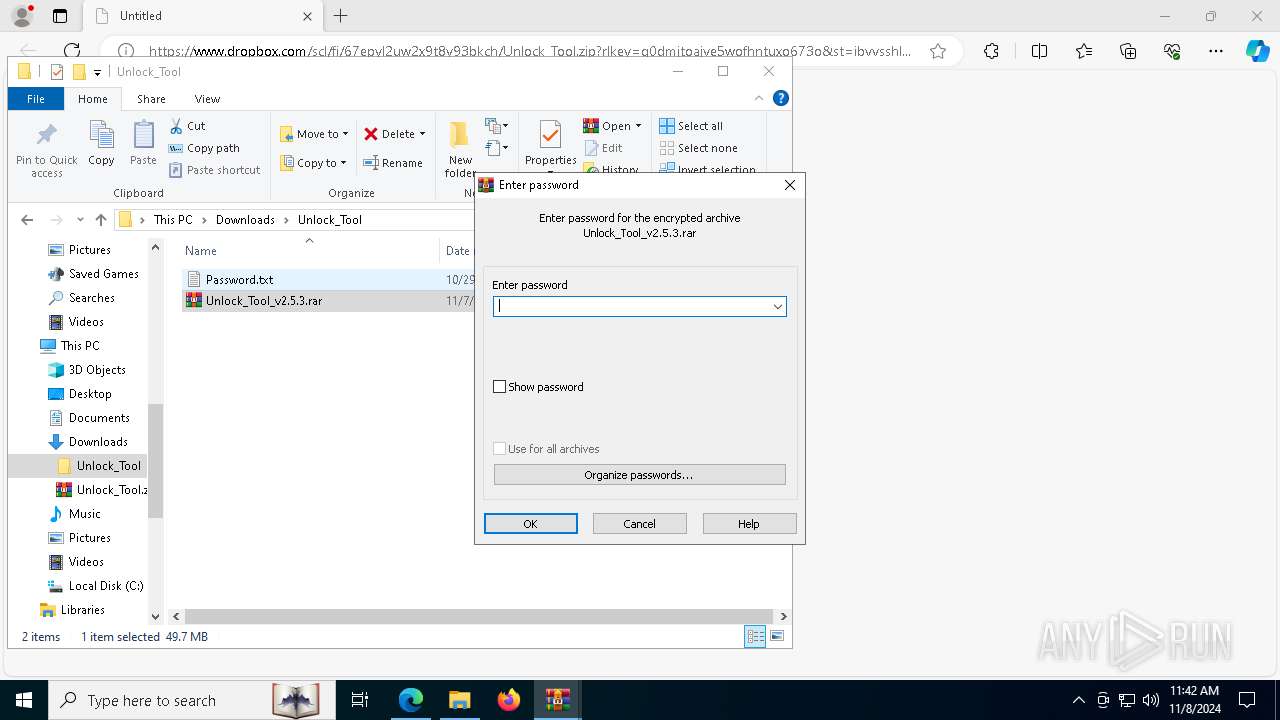
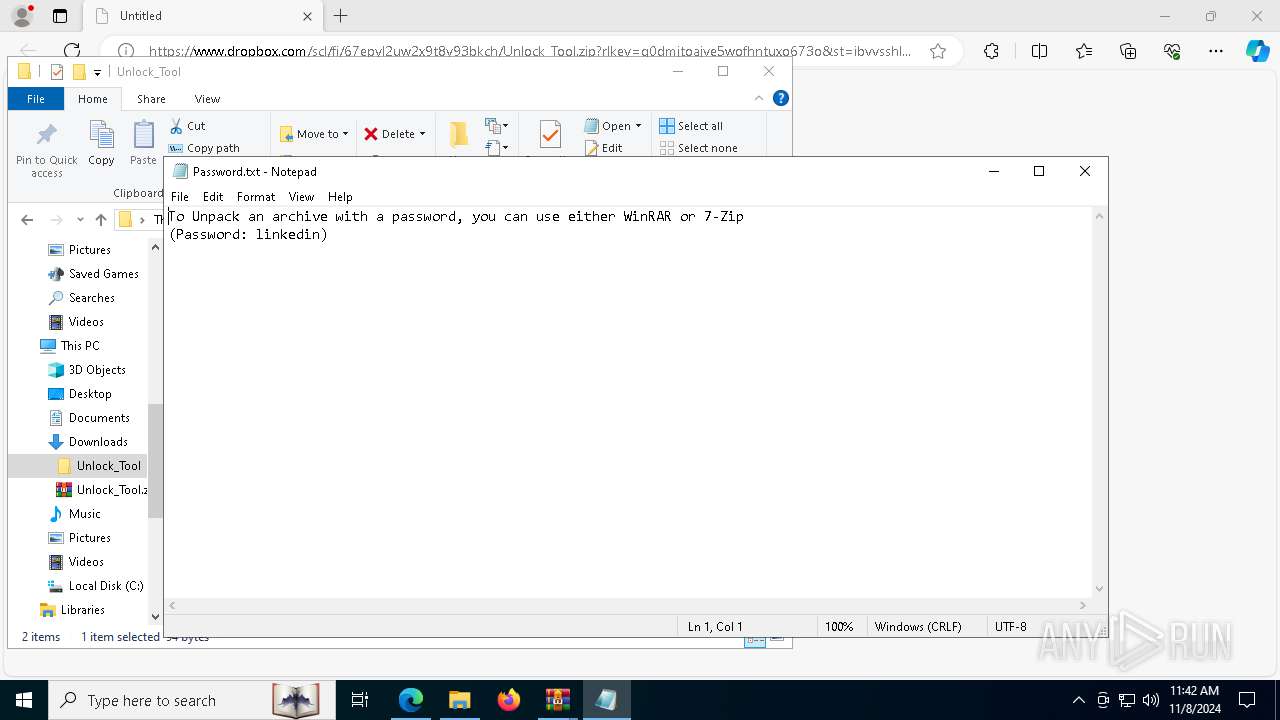
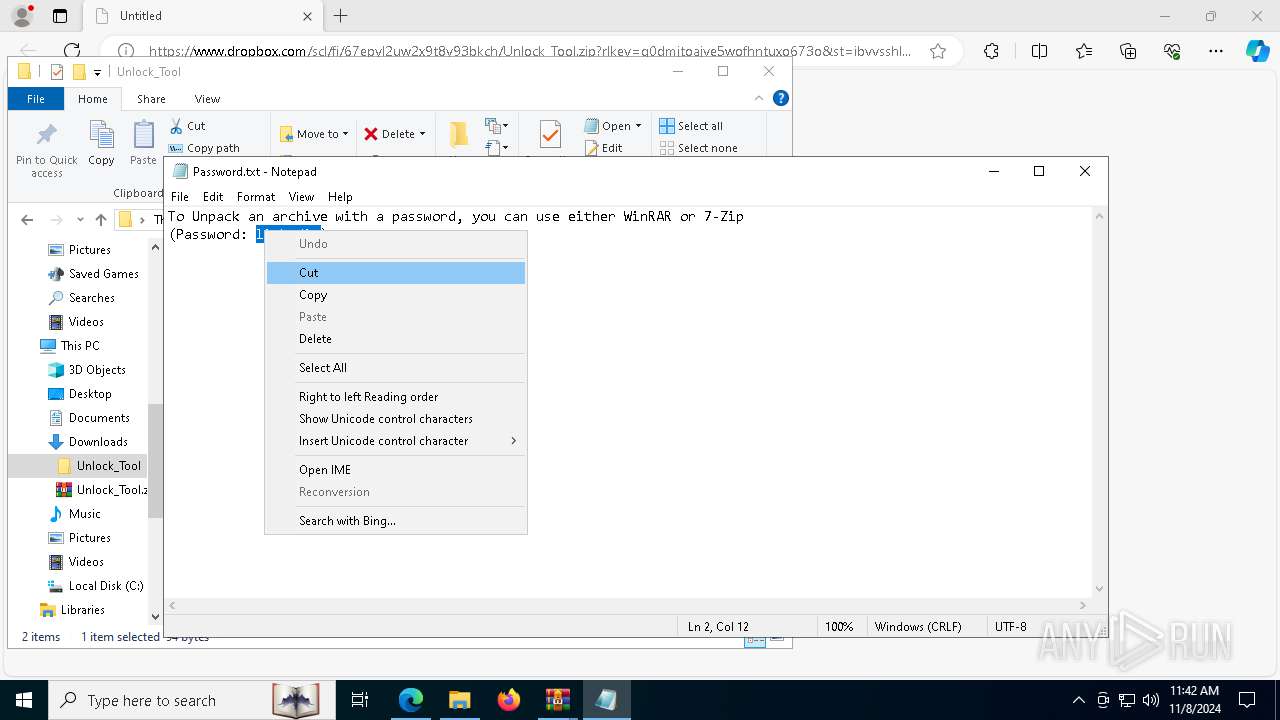
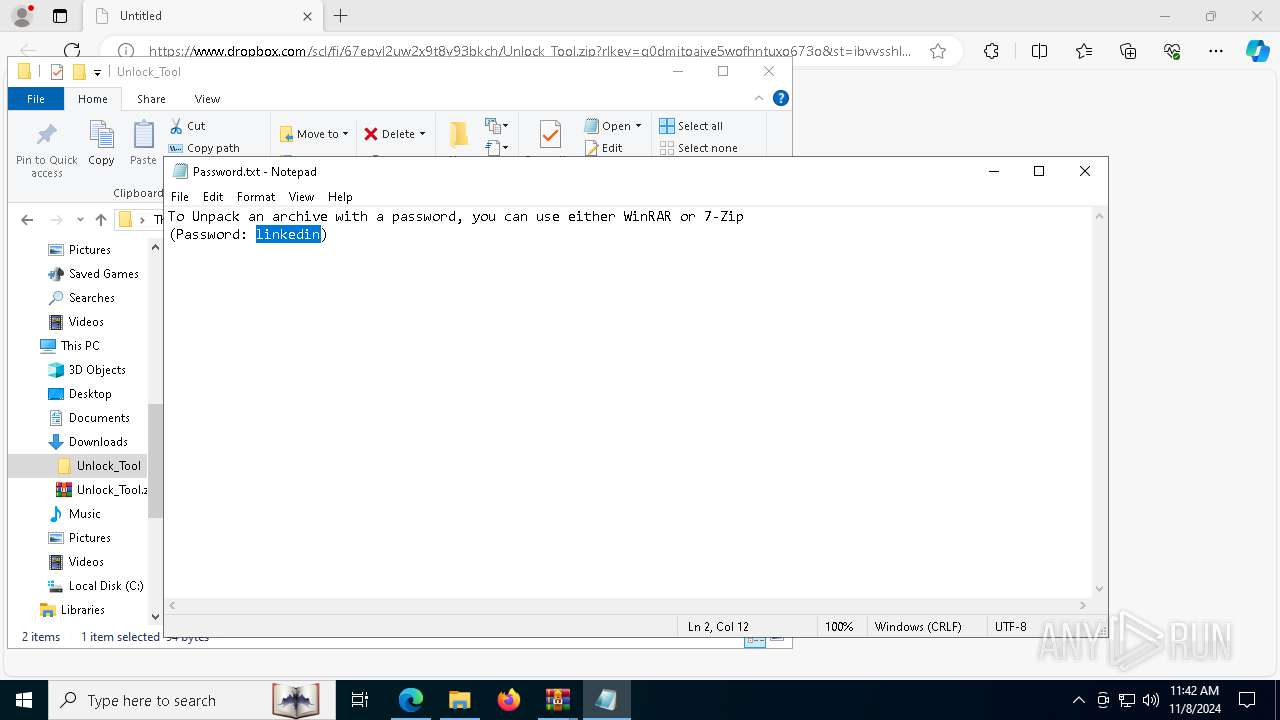
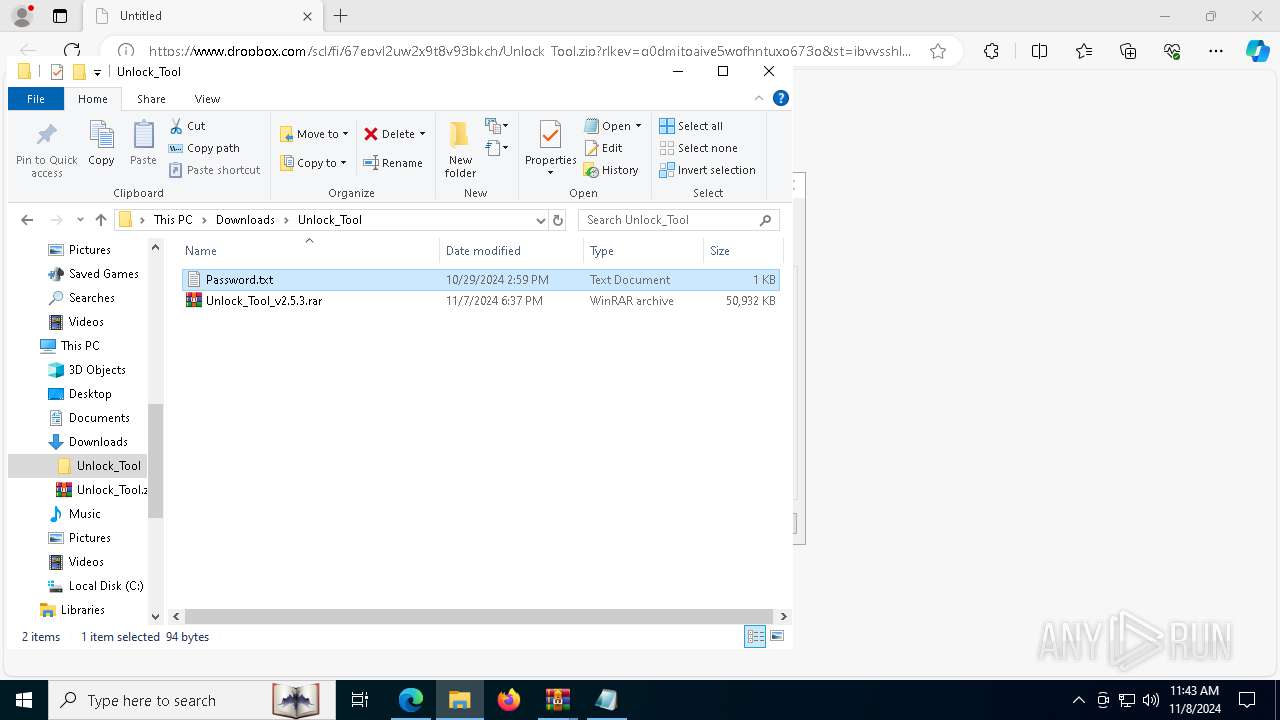
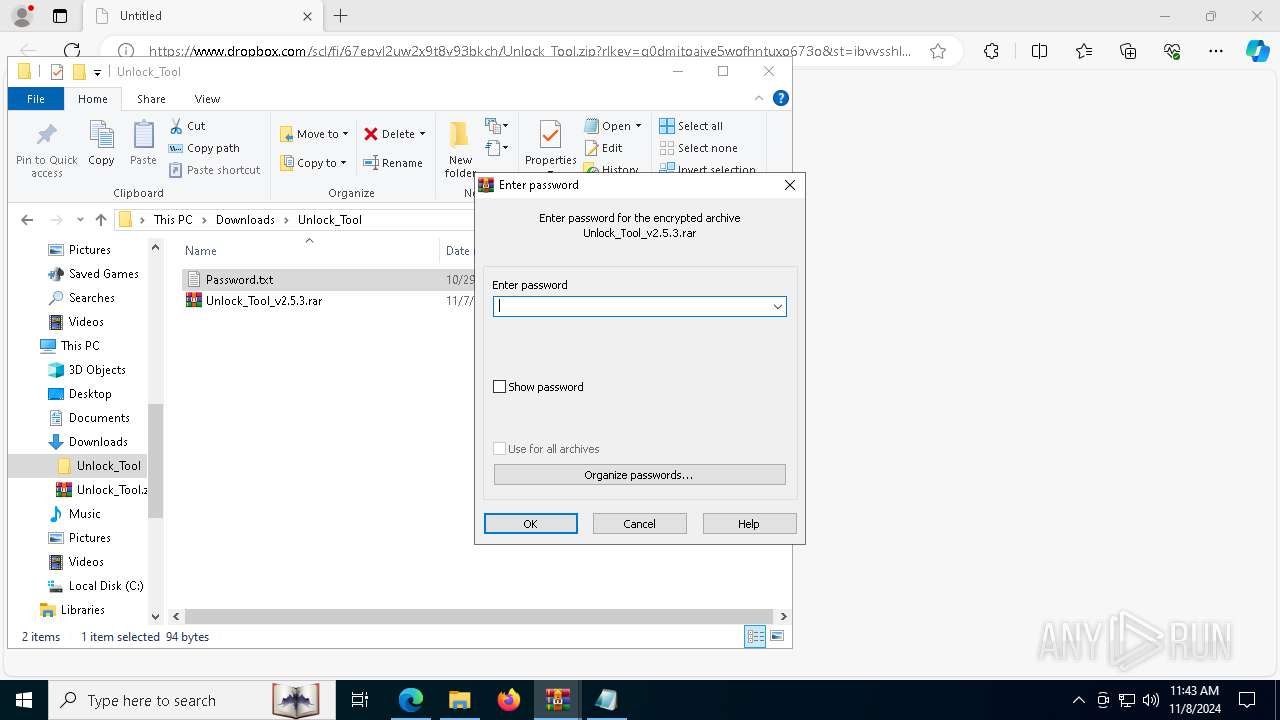
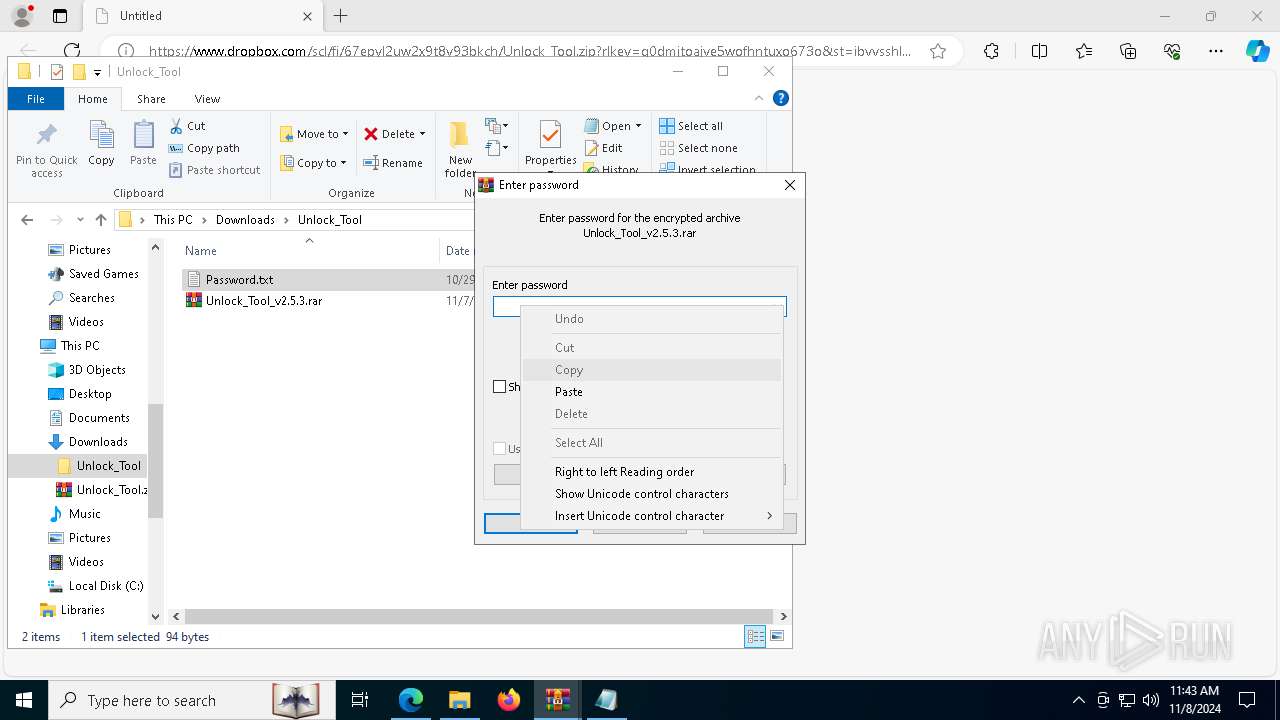
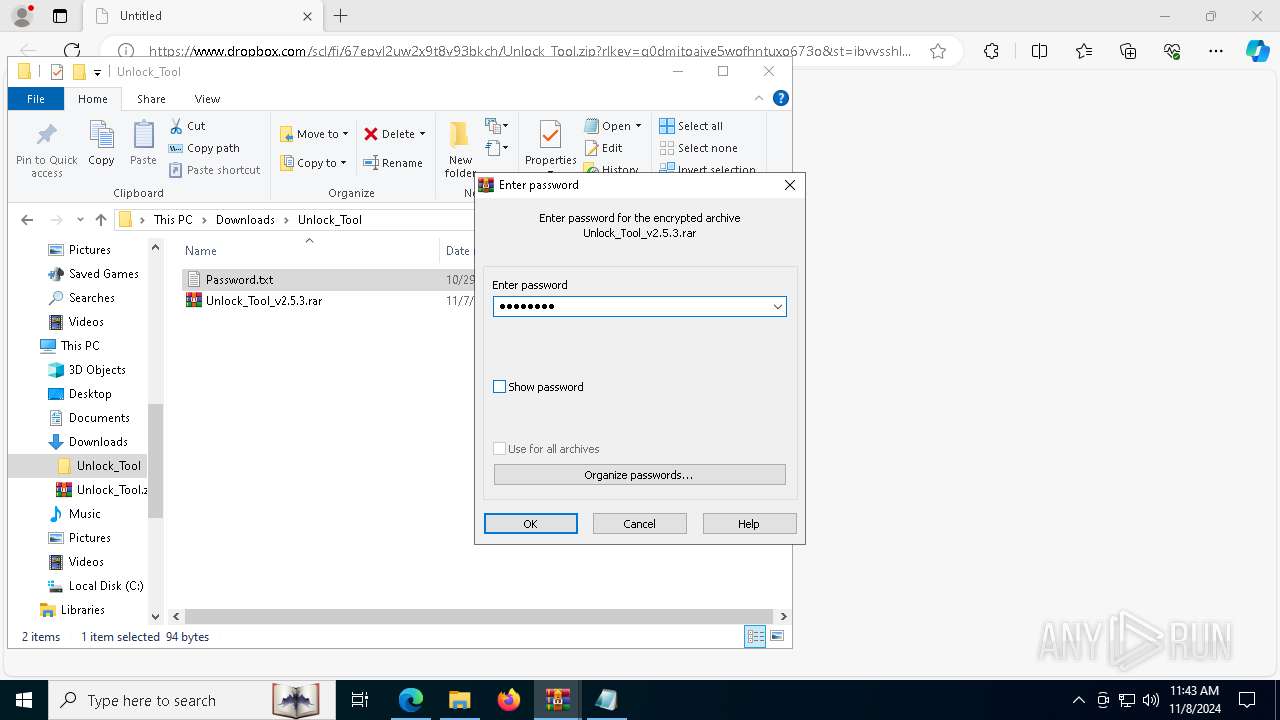
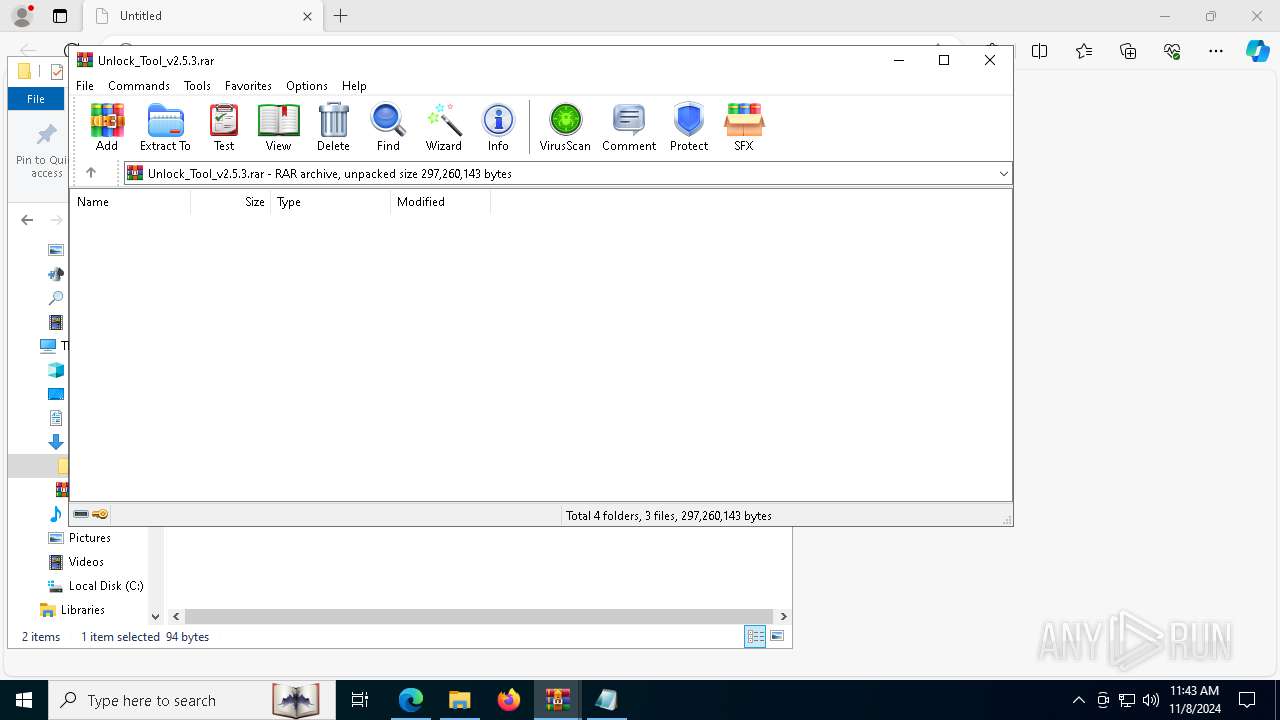
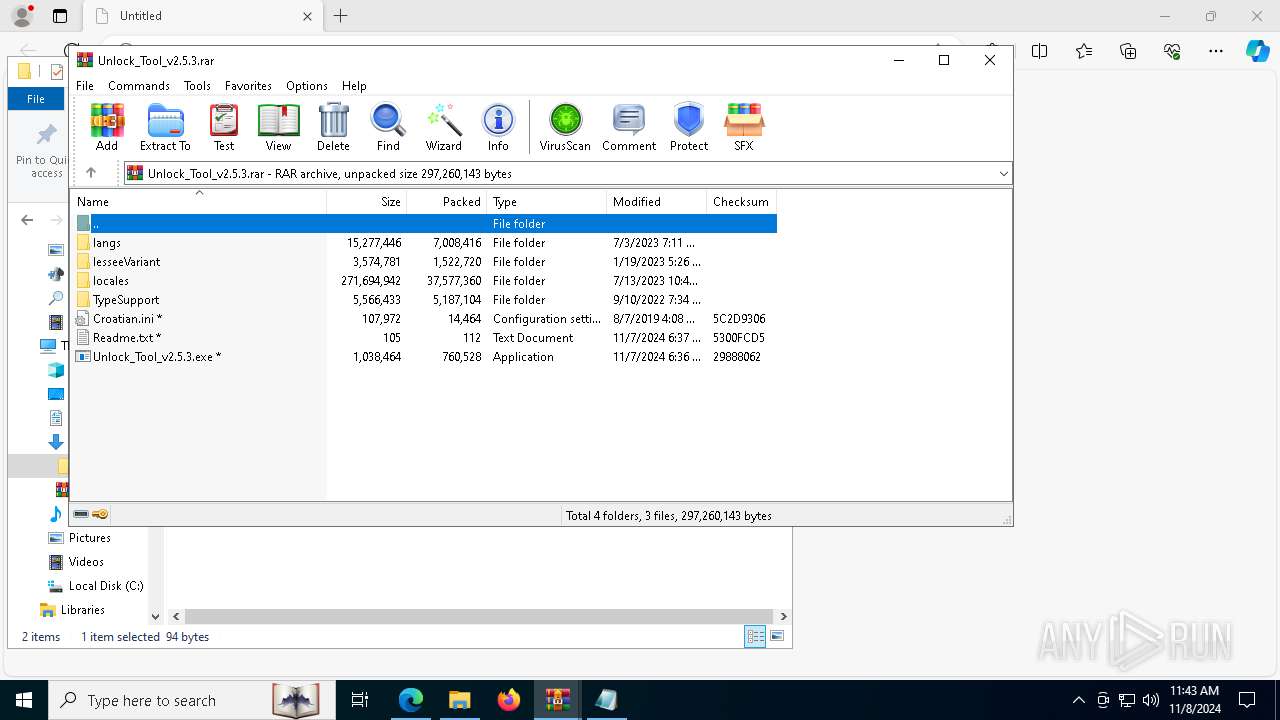
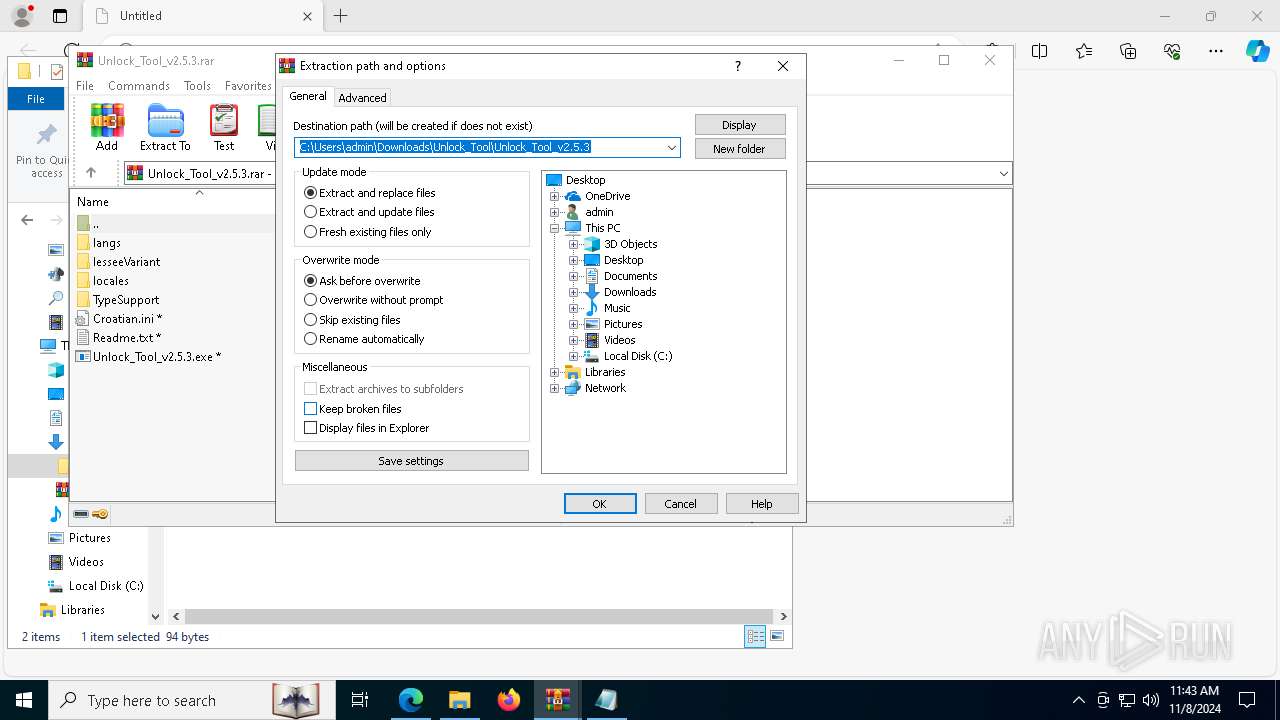
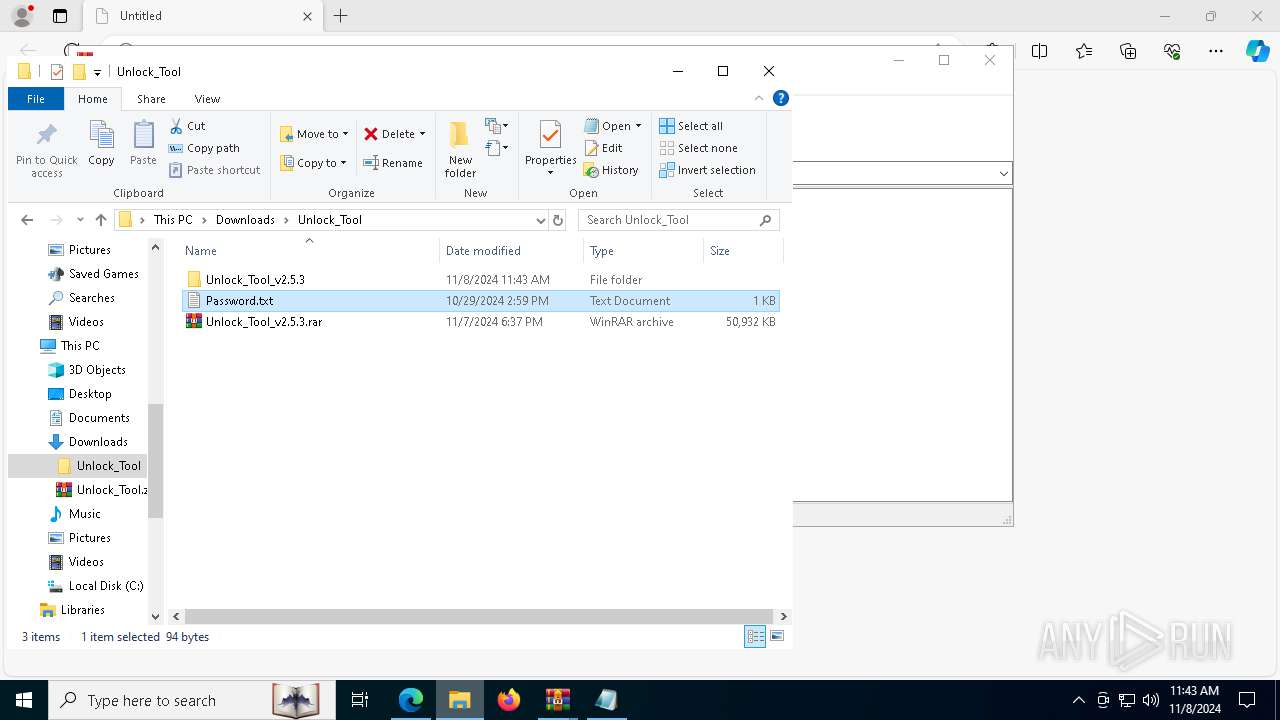
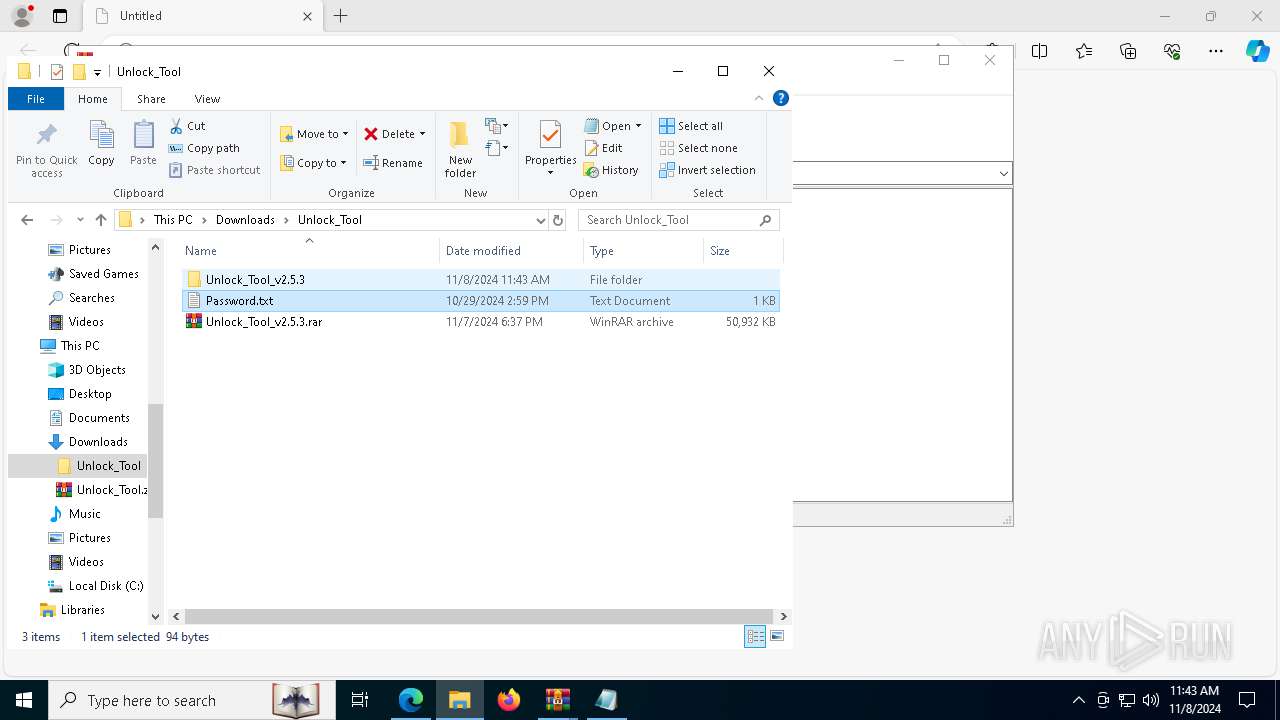
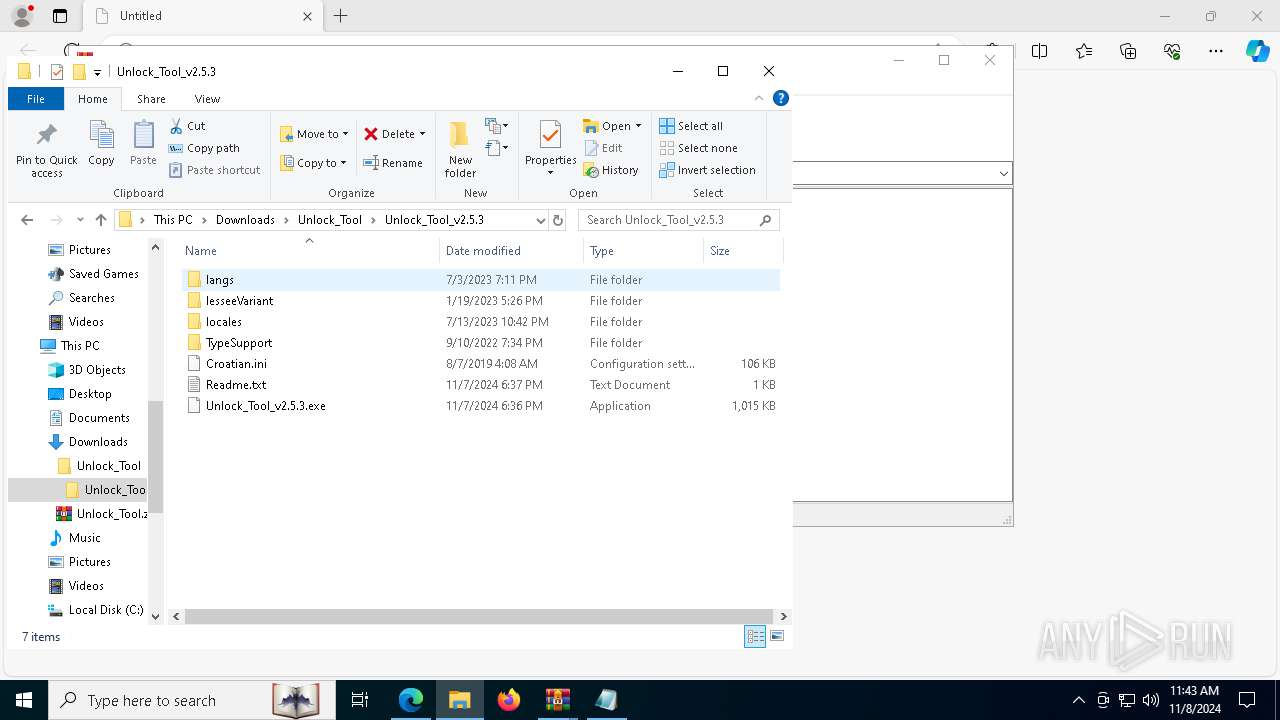
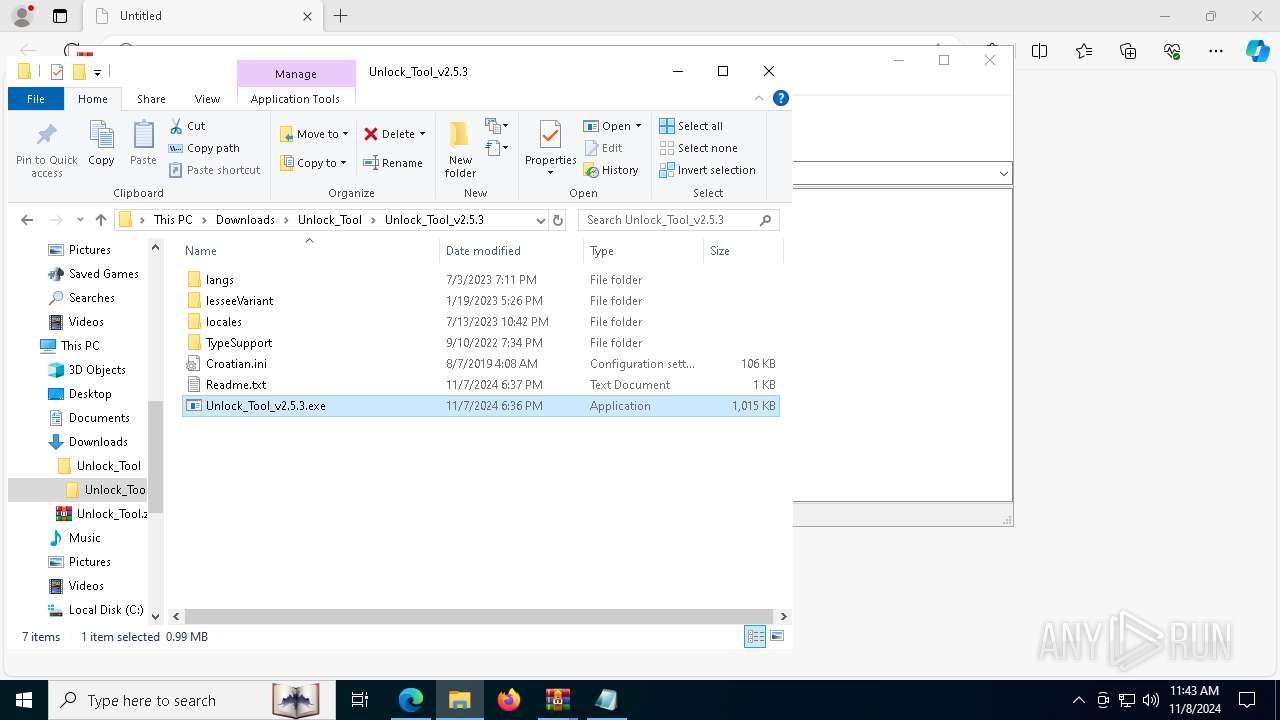
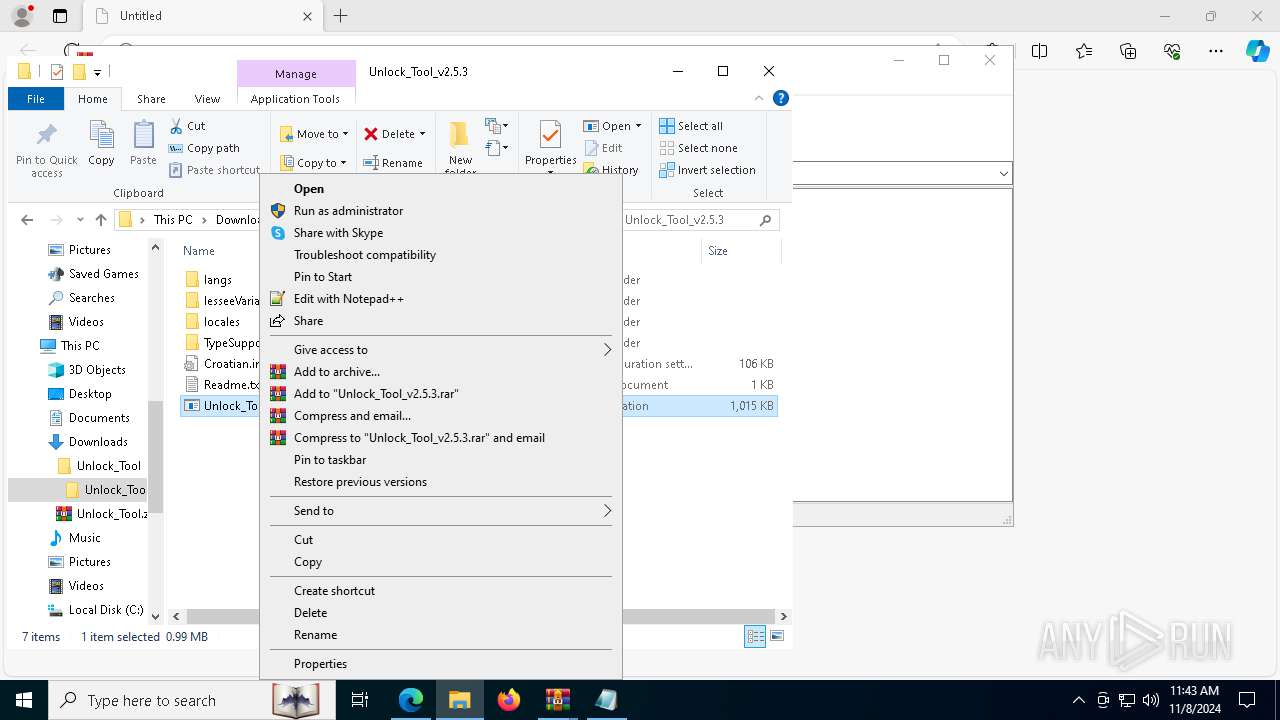
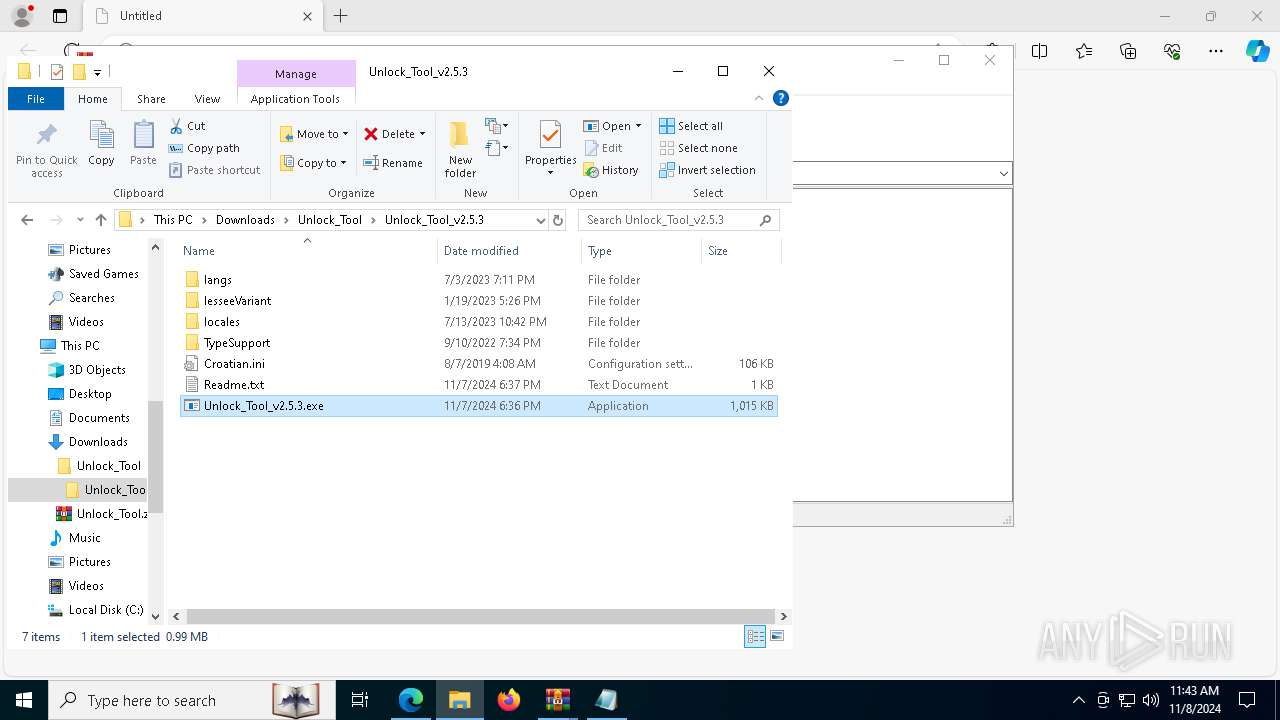
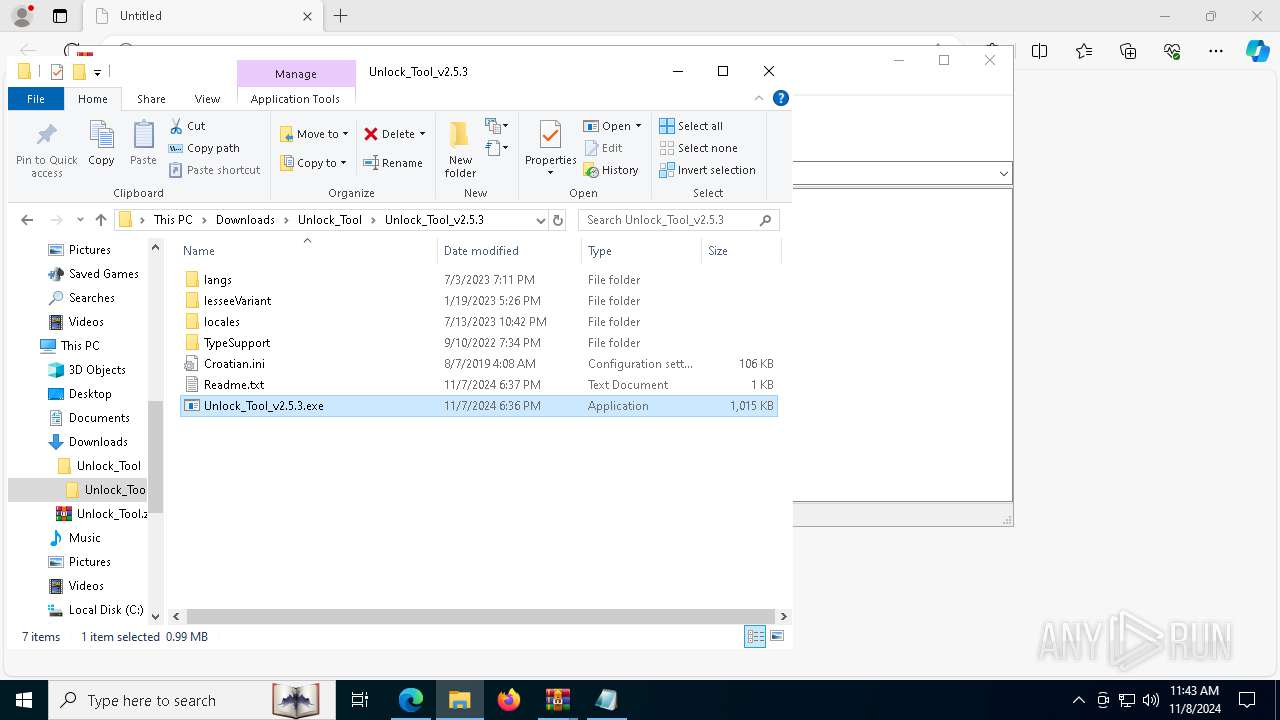
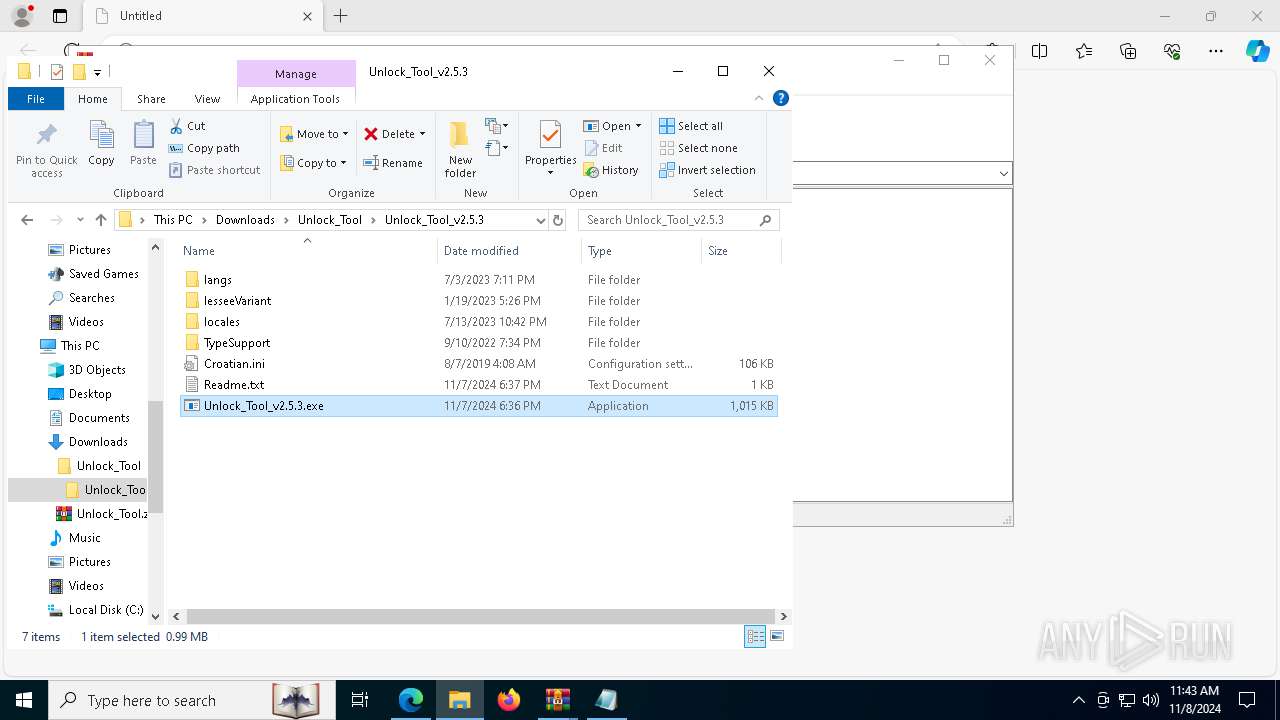
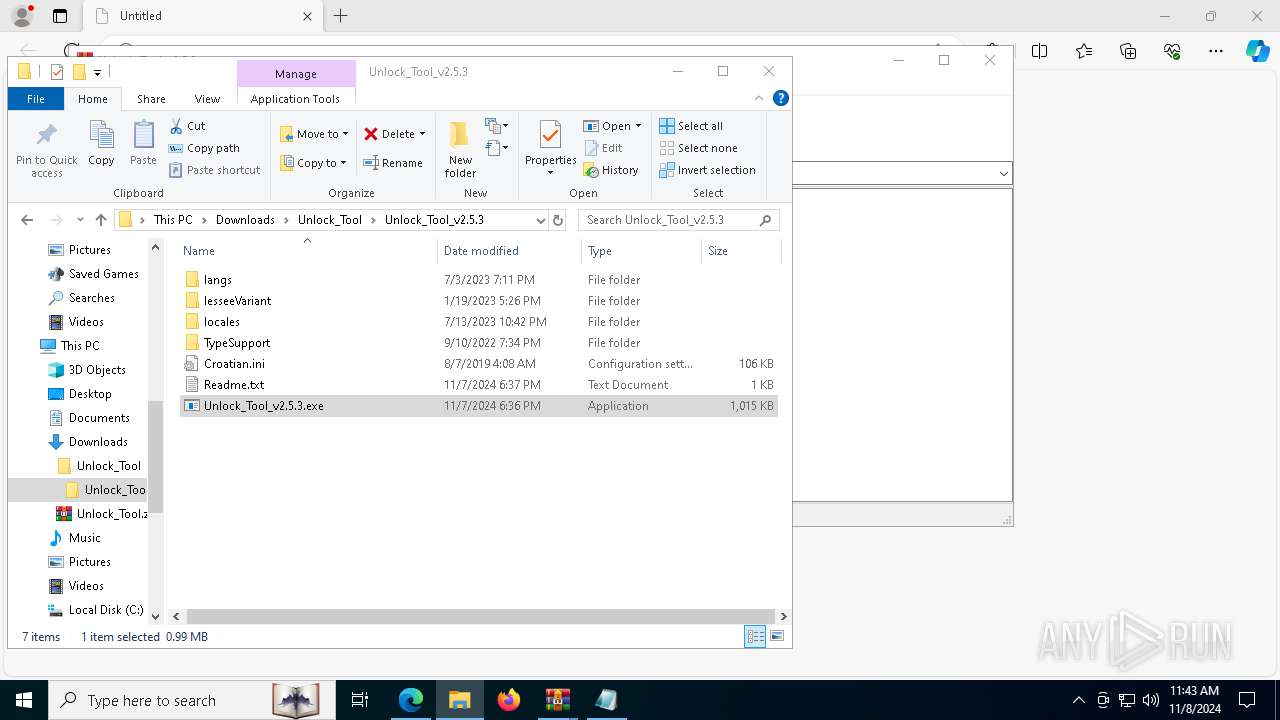
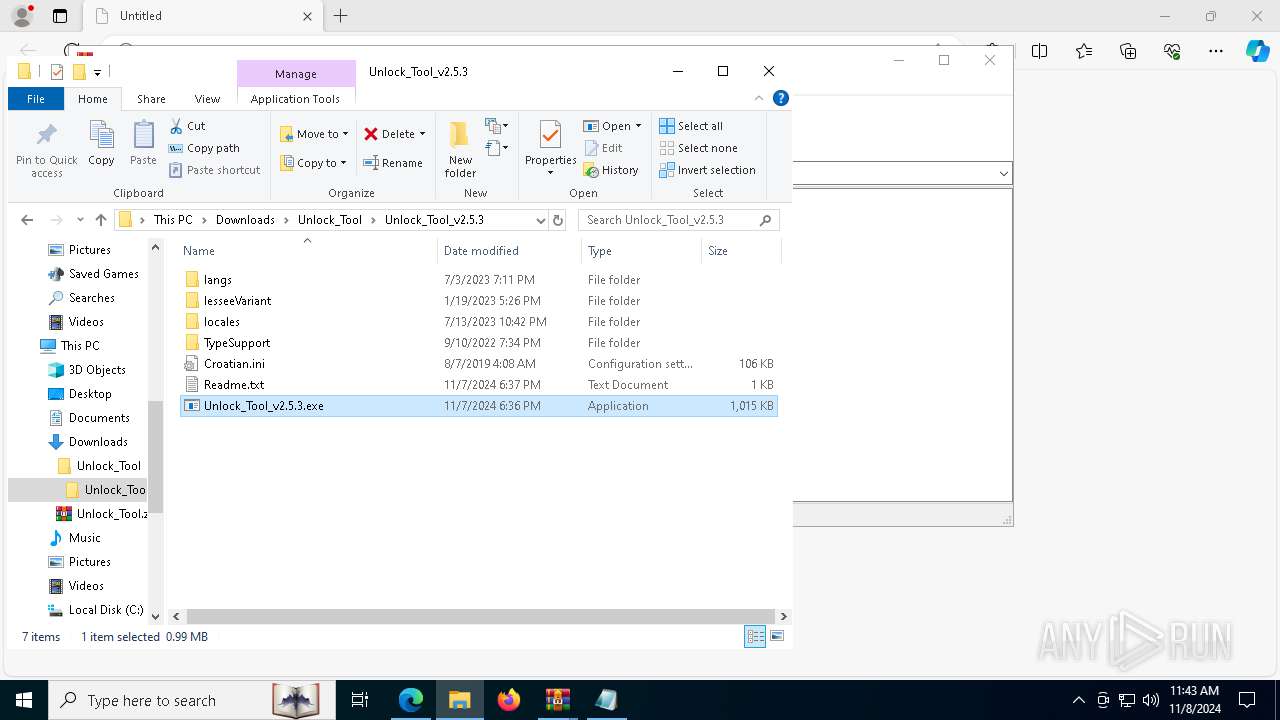
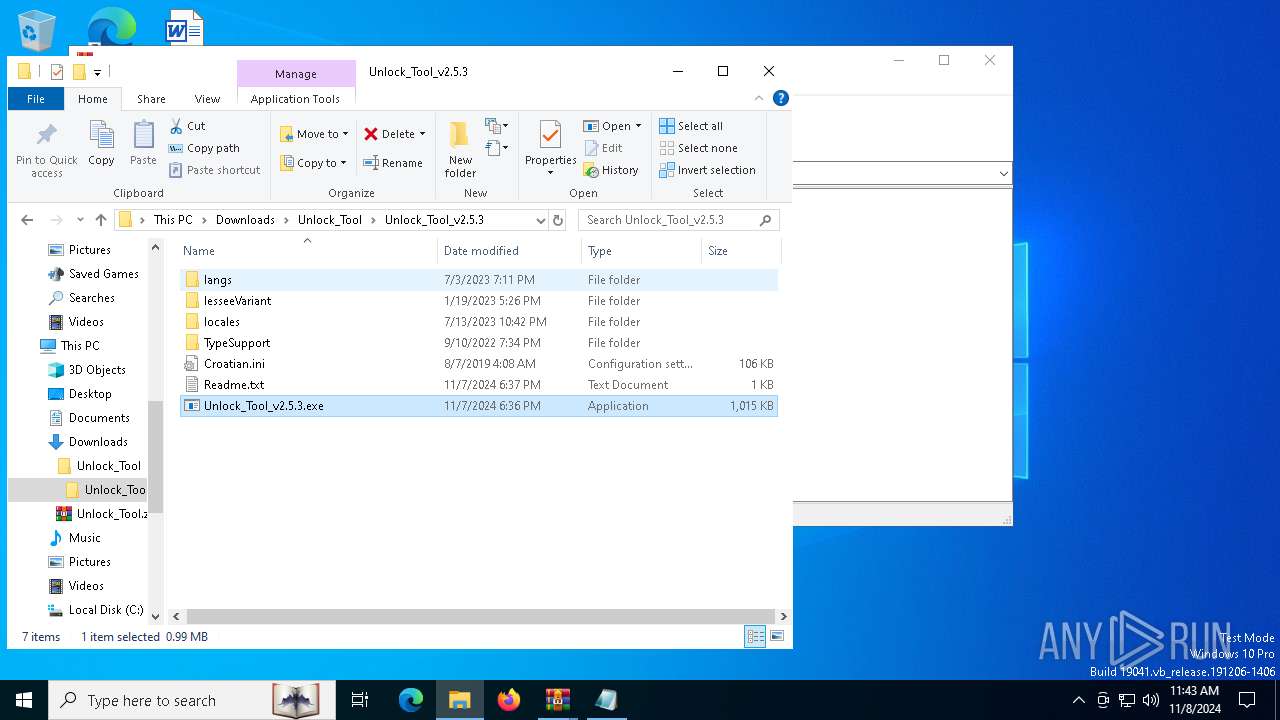
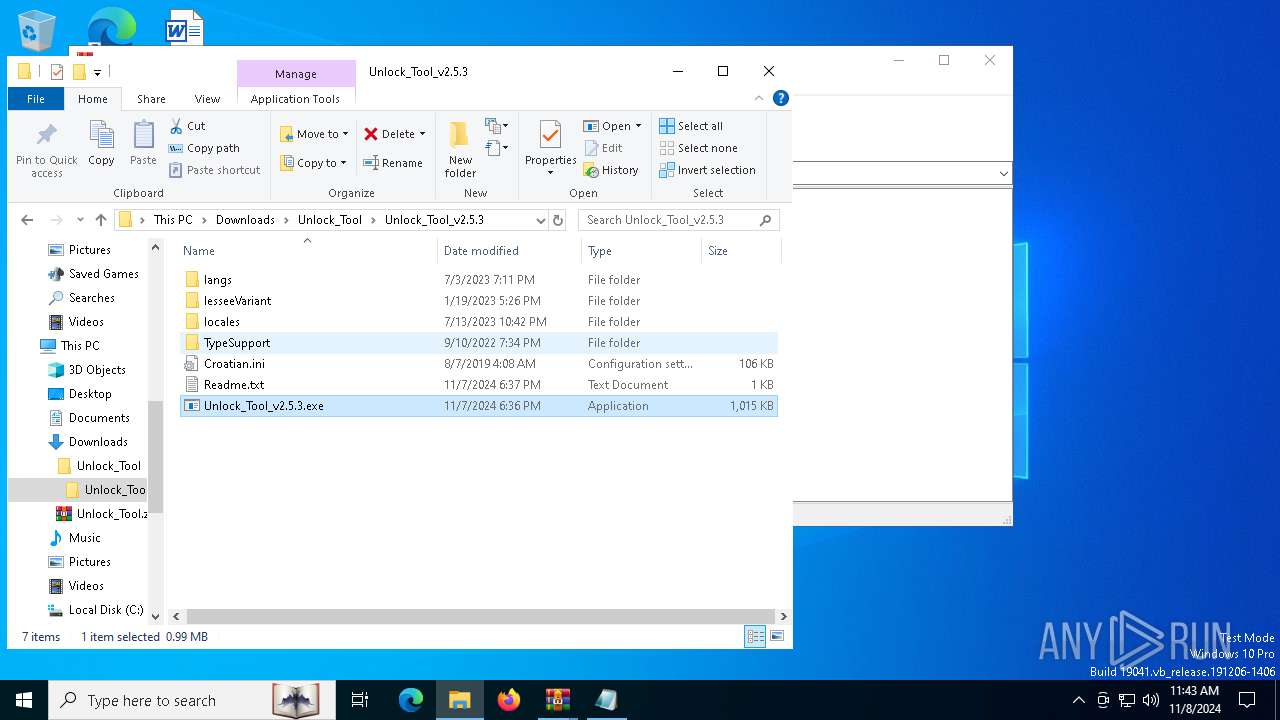
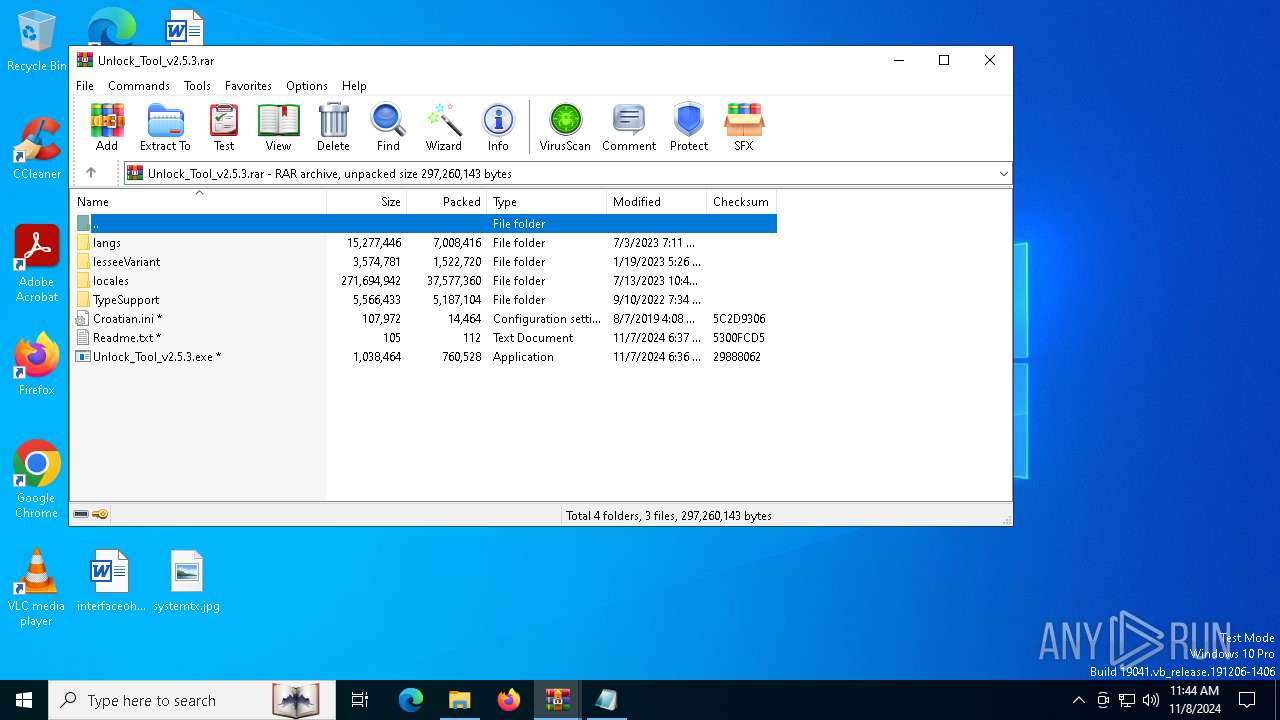
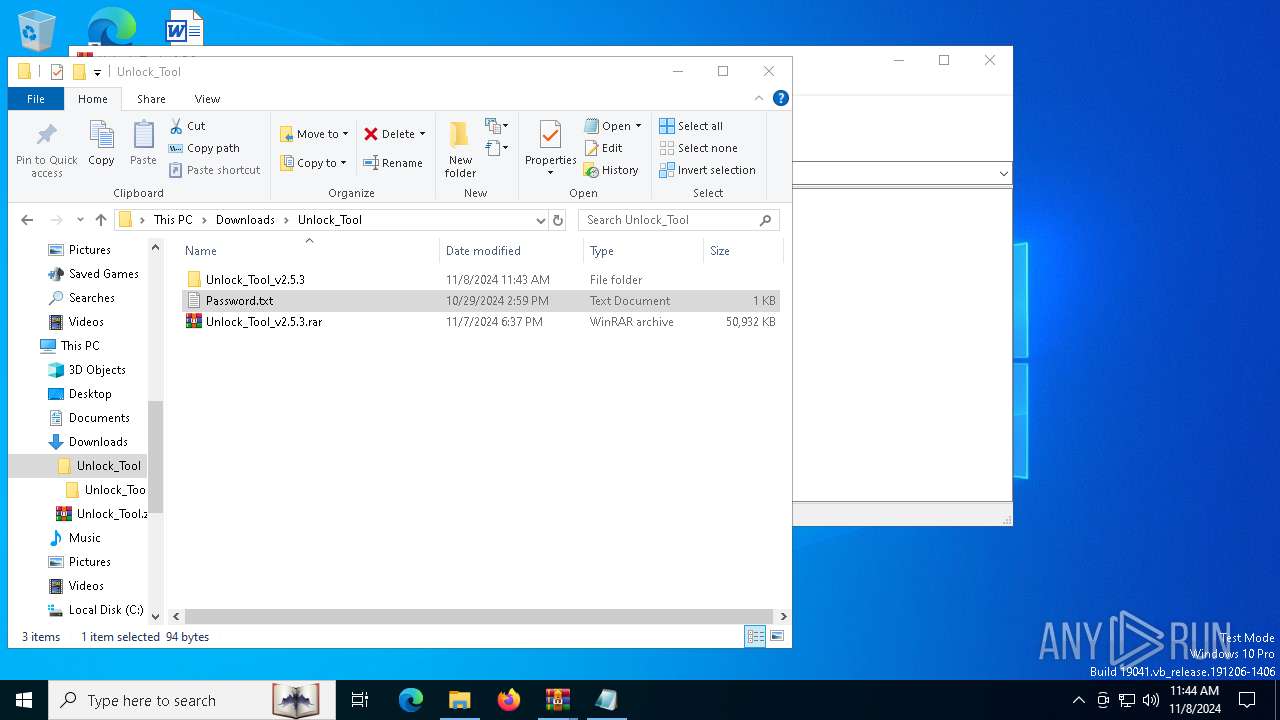
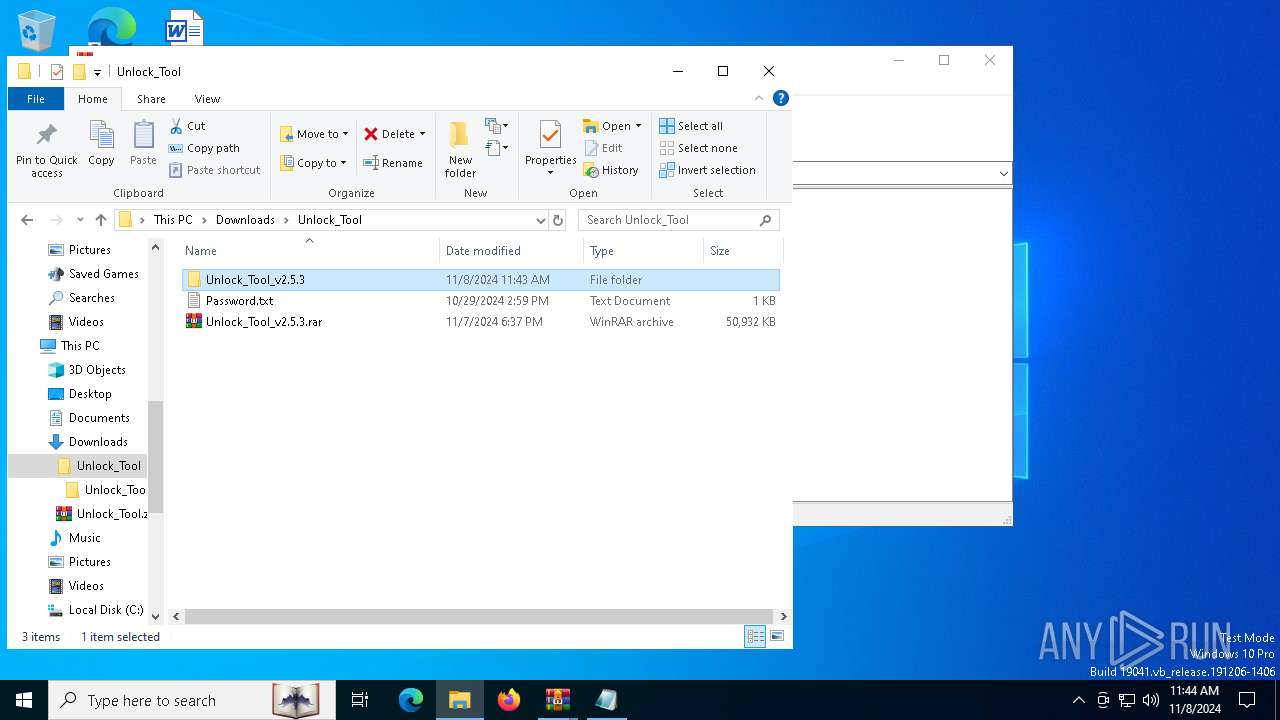
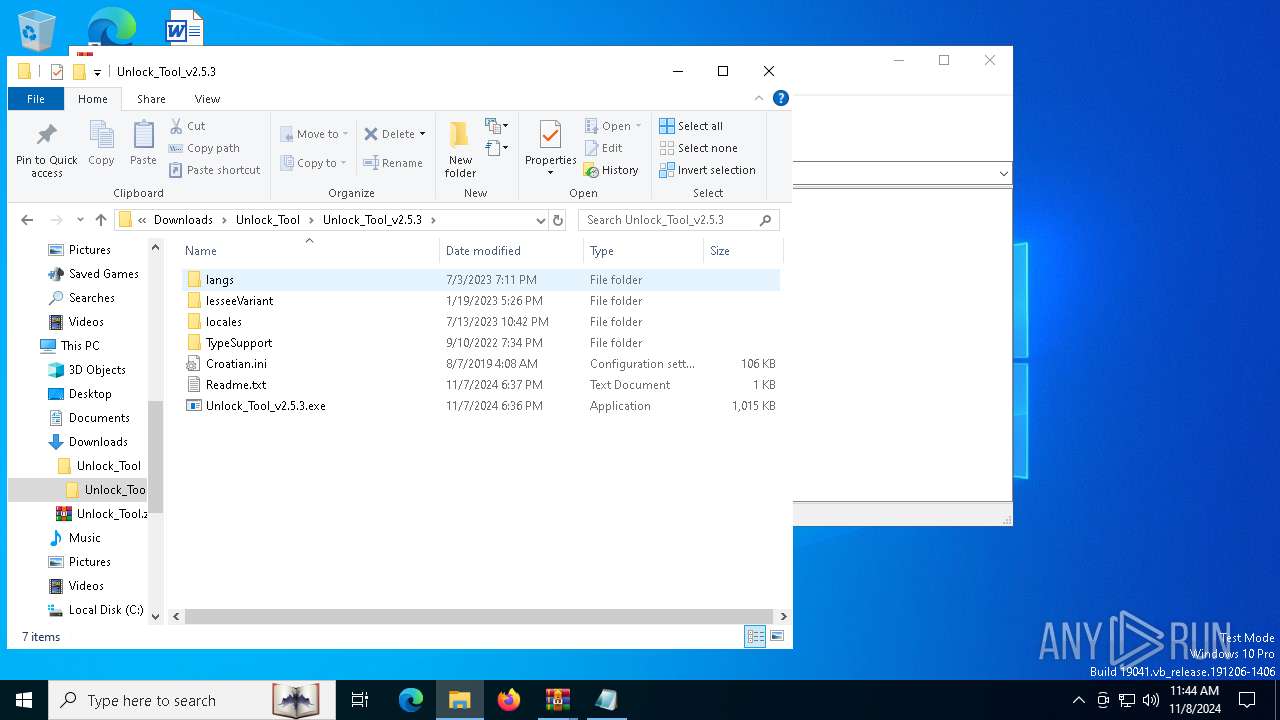
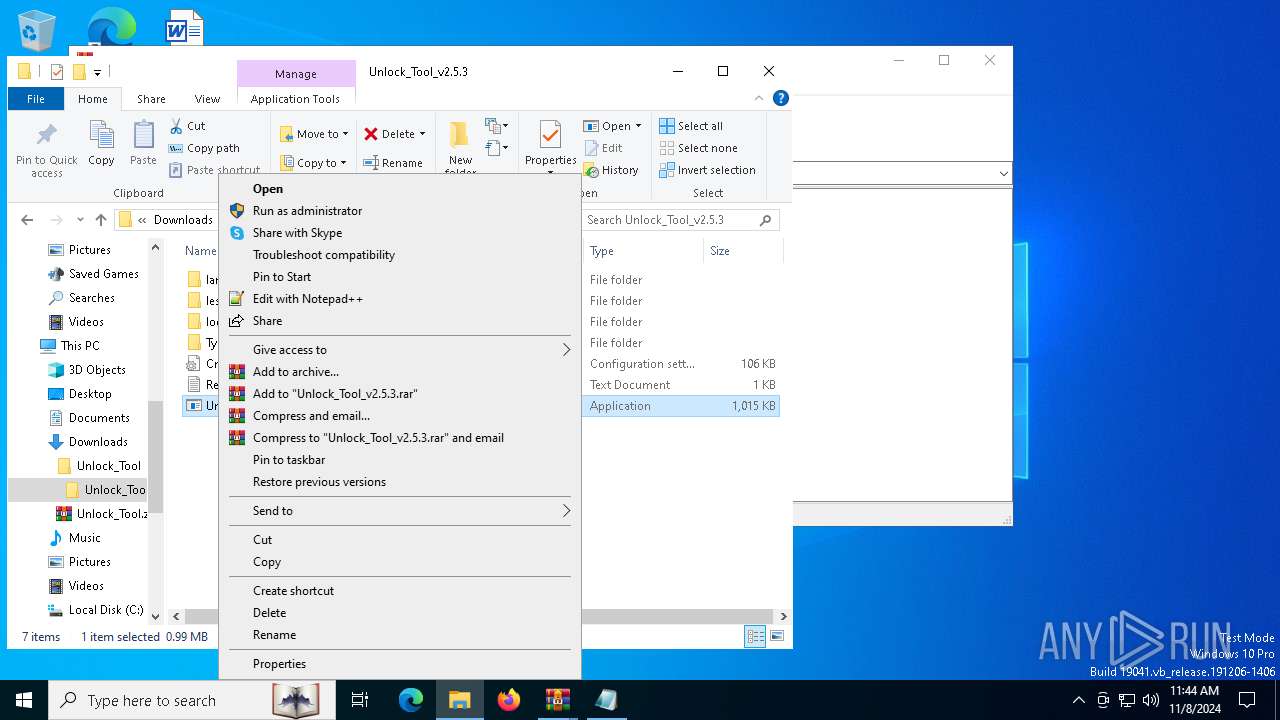
INFO
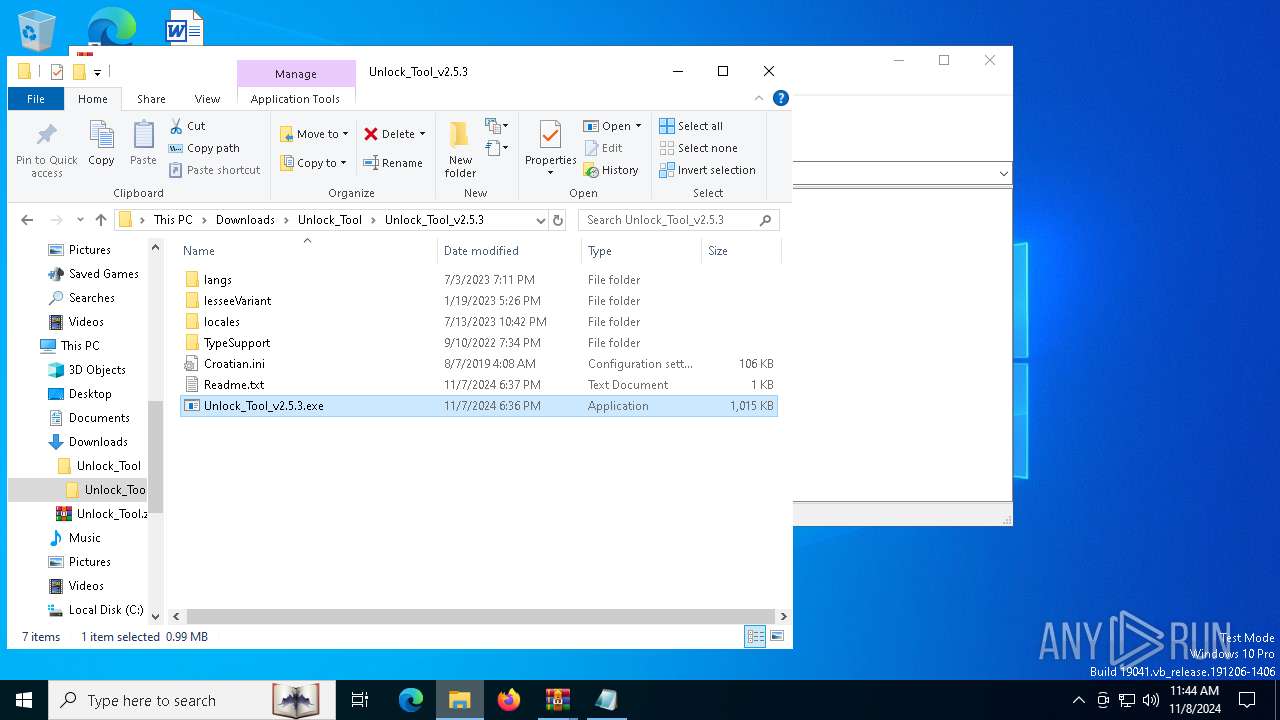
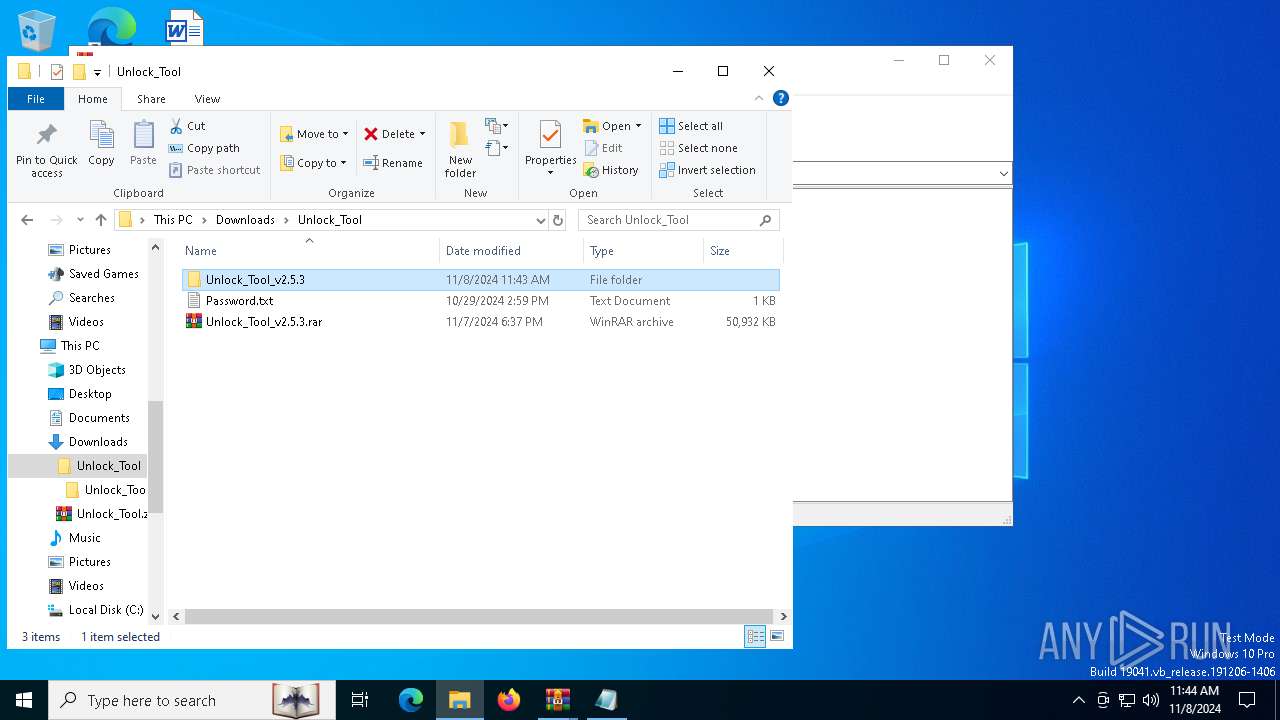
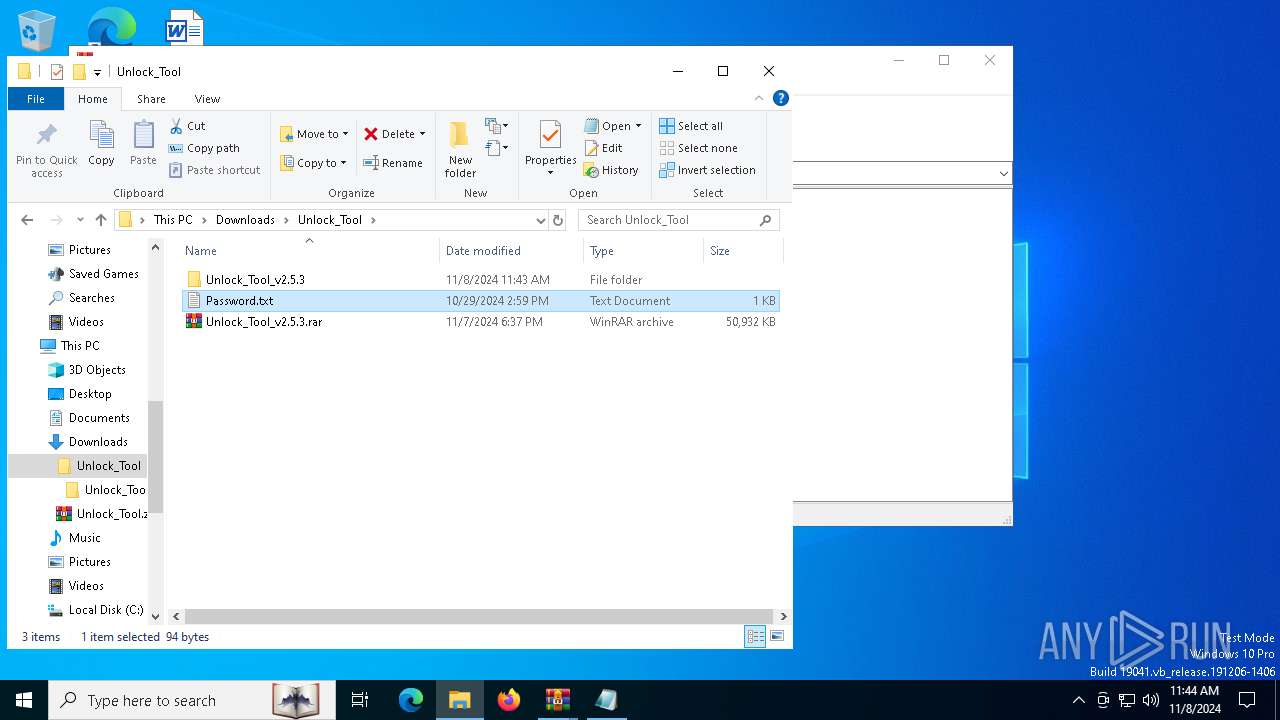
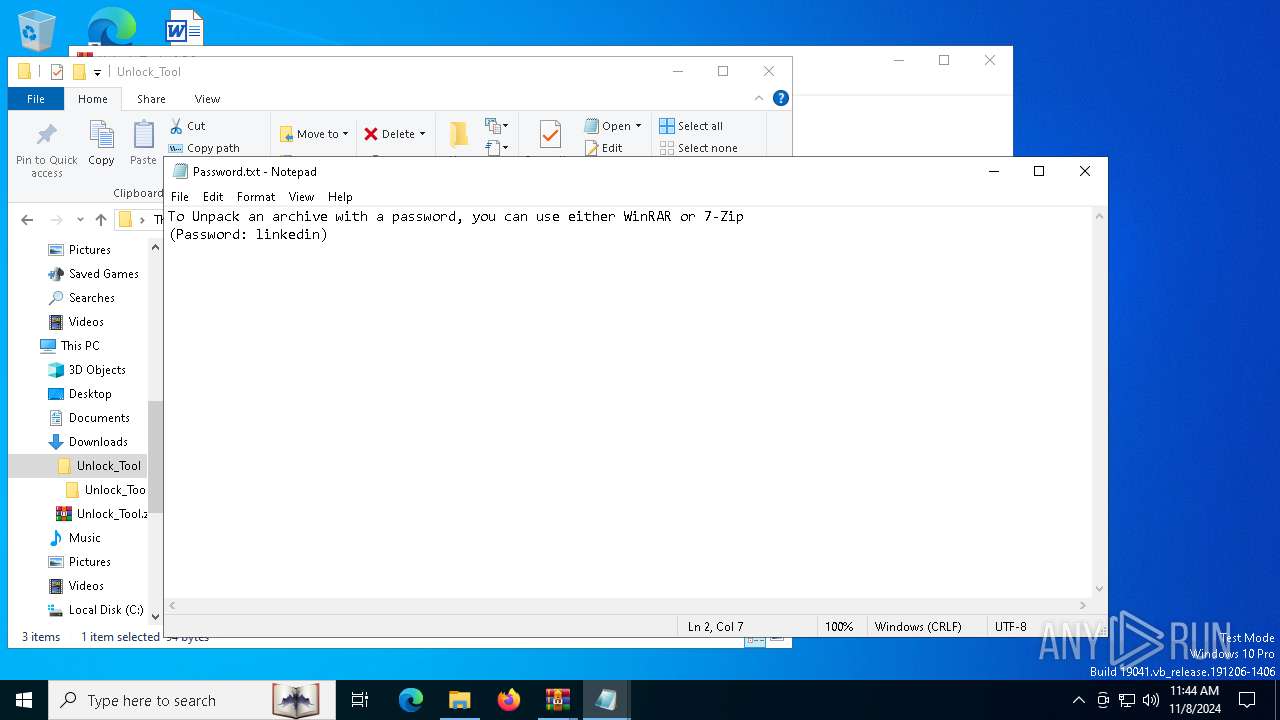
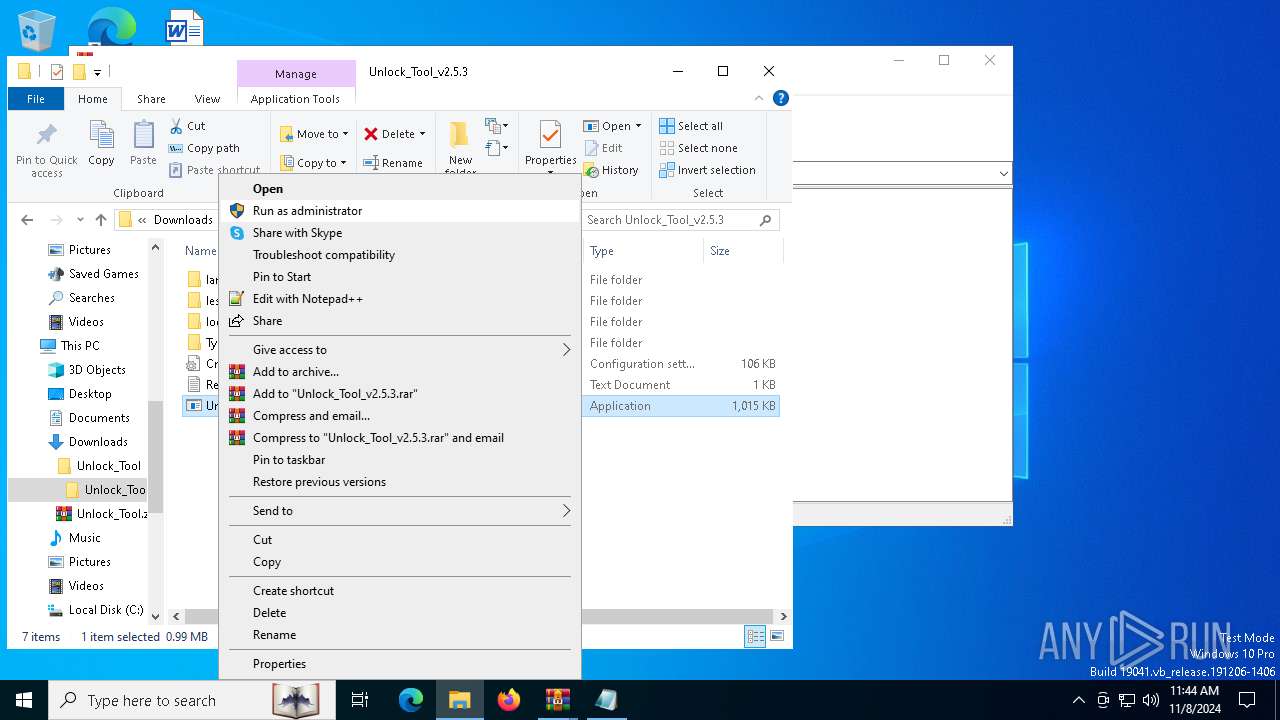
Manual execution by a user
- WinRAR.exe (PID: 8152)
- Unlock_Tool_v2.5.3.exe (PID: 7204)
- notepad.exe (PID: 7956)
- Unlock_Tool_v2.5.3.exe (PID: 7980)
- msedge.exe (PID: 8000)
- notepad.exe (PID: 1236)
- Unlock_Tool_v2.5.3.exe (PID: 5892)
- msedge.exe (PID: 7432)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8152)
- msedge.exe (PID: 2124)
Attempting to use instant messaging service
- Unlock_Tool_v2.5.3.exe (PID: 1584)
- Unlock_Tool_v2.5.3.exe (PID: 7636)
Application launched itself
- msedge.exe (PID: 1804)
- chrome.exe (PID: 2084)
- msedge.exe (PID: 6204)
- chrome.exe (PID: 6532)
- chrome.exe (PID: 7156)
- msedge.exe (PID: 3772)
- msedge.exe (PID: 7432)
- msedge.exe (PID: 1176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Vidar
(PID) Process(7636) Unlock_Tool_v2.5.3.exe
C2https://t.me/gos90t
URLhttps://steamcommunity.com/profiles/76561199800374635
RC40123456789ABCDEF
(PID) Process(1584) Unlock_Tool_v2.5.3.exe
C2https://t.me/gos90t
URLhttps://steamcommunity.com/profiles/76561199800374635
RC40123456789ABCDEF
Total processes
288
Monitored processes
136
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6836 --field-trial-handle=2436,i,8720624271494573249,15008314627604899304,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2a0,0x2a4,0x2a8,0x29c,0x2b0,0x7ffbc23f5fd8,0x7ffbc23f5fe4,0x7ffbc23f5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2300 --field-trial-handle=1920,i,10515431864514880017,18109450739081038680,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --remote-debugging-port=9223 --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=4504 --field-trial-handle=1920,i,10515431864514880017,18109450739081038680,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2472 --field-trial-handle=2252,i,13746141861566538243,15531167050266639491,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --instant-process --no-appcompat-clear --remote-debugging-port=9223 --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3744 --field-trial-handle=2252,i,13746141861566538243,15531167050266639491,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --remote-debugging-port=9223 --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4192 --field-trial-handle=2252,i,13746141861566538243,15531167050266639491,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1112 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2168 --field-trial-handle=2436,i,8720624271494573249,15008314627604899304,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1176 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://www.dropbox.com/scl/fi/67epyl2uw2x9t8y93bkch/Unlock_Tool.zip?rlkey=g0dmjtoajve5wofhntuxo673o&st=ibvvsshl&dl=1" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x210,0x214,0x218,0x1ec,0x21c,0x7ffbcca2dc40,0x7ffbcca2dc4c,0x7ffbcca2dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
21 097
Read events
21 007
Write events
62
Delete events
28
Modification events
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 74C43B86FB842F00 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 205A4486FB842F00 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590364 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7753C376-0511-45DC-89E1-7B0DB04DE47F} | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590364 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2A64A15E-A026-428A-AE05-C5A2962F6BBE} | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E44C6A86FB842F00 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
114
Suspicious files
844
Text files
678
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b678.TMP | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b687.TMP | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b687.TMP | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b678.TMP | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b6a6.TMP | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
265
DNS requests
225
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4700 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6604 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6356 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6604 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4516 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c1acadc6-5cc8-4bde-8b9e-fbecd9b3f963?P1=1731393399&P2=404&P3=2&P4=PWfZg9KZ9EBEp74gzcGGm8nKrdZe8QOkGnRRb%2fUHGXQFujPxn1Xo2PkGMMEmwsEQjRbmopOpG0UopPTT1pUgOA%3d%3d | unknown | — | — | whitelisted |
4516 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c1acadc6-5cc8-4bde-8b9e-fbecd9b3f963?P1=1731393399&P2=404&P3=2&P4=PWfZg9KZ9EBEp74gzcGGm8nKrdZe8QOkGnRRb%2fUHGXQFujPxn1Xo2PkGMMEmwsEQjRbmopOpG0UopPTT1pUgOA%3d%3d | unknown | — | — | whitelisted |
4516 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c1acadc6-5cc8-4bde-8b9e-fbecd9b3f963?P1=1731393399&P2=404&P3=2&P4=PWfZg9KZ9EBEp74gzcGGm8nKrdZe8QOkGnRRb%2fUHGXQFujPxn1Xo2PkGMMEmwsEQjRbmopOpG0UopPTT1pUgOA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1764 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.161:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
2620 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2620 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.dropbox.com |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1584 | Unlock_Tool_v2.5.3.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
1584 | Unlock_Tool_v2.5.3.exe | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
7636 | Unlock_Tool_v2.5.3.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
7636 | Unlock_Tool_v2.5.3.exe | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
— | — | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3 ETPRO signatures available at the full report