| File name: | clipsexsub.exe |
| Full analysis: | https://app.any.run/tasks/d9fdfcac-41d9-434b-baf6-8e11ba0c8a0f |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | February 07, 2026, 11:20:53 |
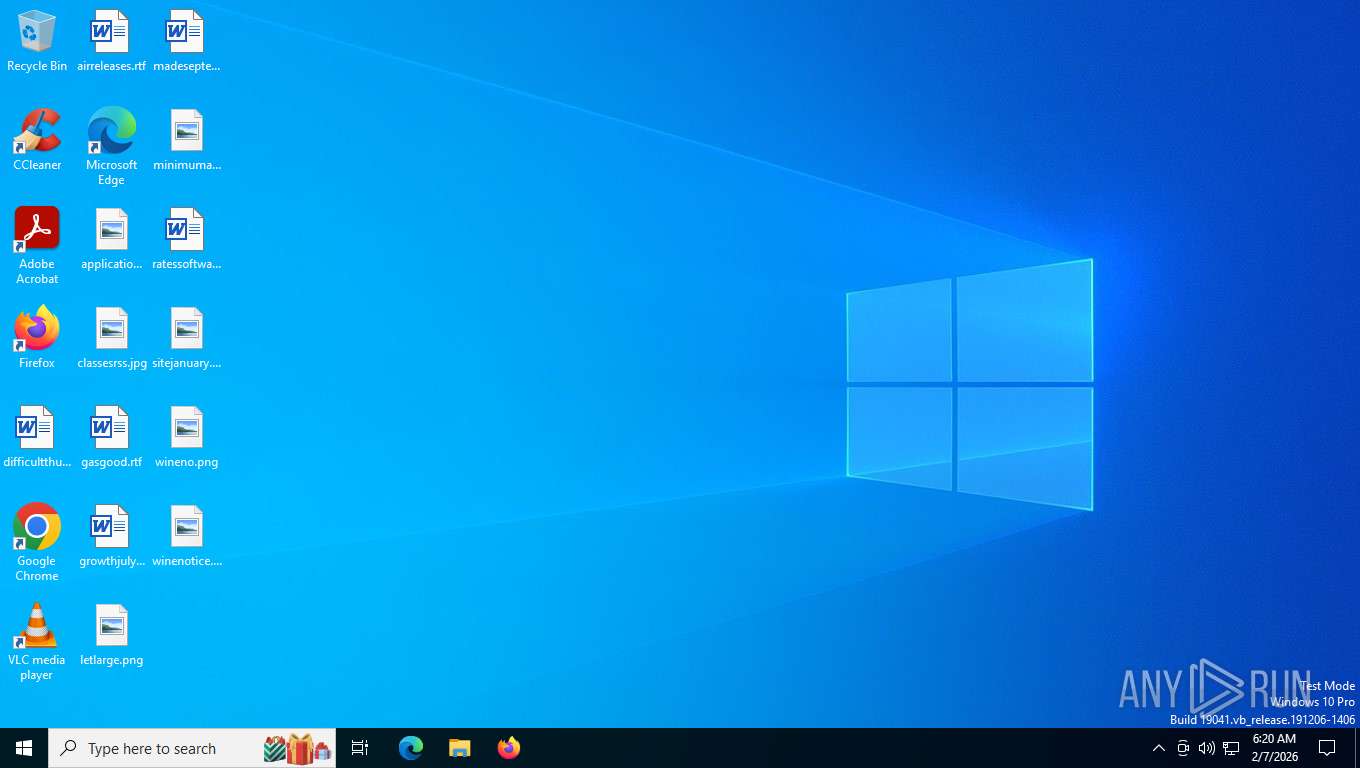
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 303FCF9046BCAE7C658EE462AA1CD697 |
| SHA1: | E642405743974F43B6FA74B9590C1D76EAC64EBA |
| SHA256: | 68F70C0A765A6AE81922C3BDA2B4F70D28CF62FC7CEA47AE41E13685695B7E25 |
| SSDEEP: | 1536:DSSjOS/DY3ClrB3TWR12bbAwcSCWnta6g5UVclN:DSSjOF3ClrB6R12bbAdota6g5GY |
MALICIOUS
ASYNCRAT has been detected (YARA)
- clipsexsub.exe (PID: 1732)
SUSPICIOUS
No suspicious indicators.INFO
Reads the computer name
- clipsexsub.exe (PID: 1732)
Checks supported languages
- clipsexsub.exe (PID: 1732)
Reads the machine GUID from the registry
- clipsexsub.exe (PID: 1732)
Checks proxy server information
- slui.exe (PID: 7272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(1732) clipsexsub.exe
C2 (7)clipsexsub3x.net
104.26.13.217
104.26.12.217
172.67.71.10
2606:4700:20::681a:cd9
2606:4700:20::681a:dd9
2606:4700:20::ac43:470a
Ports (5)4782
1604
443
8080
8848
Version1.0.7
Options
AutoRuntrue
MutexElydraIdentity_TrustMutex_v2034
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVALV2hi3nDM88rPB/M+k+VIWkqiwpMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI1MDQxMDE0MzgxNFoXDTM2MDExODE0MzgxNFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignaturecK2Lxpo8yHg3hd7hi1zOaoi4nRCt8zwWWIqt47kvbQG/LitfftJRNuaH/BqlTkVeqO9INgx0WxNrdZbX2GEcaAJ9bp8gRPZoGLaztfXRN0KPrspdEh8jiGHi3q7KJtOkaMhzF39ahI8+KhXHrYa/hjg4MXp8h3keIRrNM9HH80U=
Keys
AESebbc6caaf8a8578e4f691122b434b6ebffa45ce03f10a4509bd0859d64489262
SaltDcRatByqwqdanchun
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:01:12 03:47:42+00:00 |
| ImageFileCharacteristics: | Executable |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 60416 |
| InitializedDataSize: | 15360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x10ace |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 144.0.7547.0 |
| ProductVersionNumber: | 144.0.7547.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Google LLC |
| FileDescription: | Google Installer (x86) |
| FileVersion: | 144.0.7547.0 |
| InternalName: | clipsexsub3x.net |
| LegalCopyright: | Copyright 2025 Google LLC. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | clipsexsub3x.net |
| ProductName: | Google Installer (x86) |
| ProductVersion: | 144.0.7547.0 |
| AssemblyVersion: | 144.0.7547.0 |
Total processes
141
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1732 | "C:\Users\admin\Desktop\clipsexsub.exe" | C:\Users\admin\Desktop\clipsexsub.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Installer (x86) Version: 144.0.7547.0 Modules
AsyncRat(PID) Process(1732) clipsexsub.exe C2 (7)clipsexsub3x.net 104.26.13.217 104.26.12.217 172.67.71.10 2606:4700:20::681a:cd9 2606:4700:20::681a:dd9 2606:4700:20::ac43:470a Ports (5)4782 1604 443 8080 8848 Version1.0.7 Options AutoRuntrue MutexElydraIdentity_TrustMutex_v2034 InstallFolder%AppData% Certificates Cert1MIICMDCCAZmgAwIBAgIVALV2hi3nDM88rPB/M+k+VIWkqiwpMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI1MDQxMDE0MzgxNFoXDTM2MDExODE0MzgxNFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A... Server_SignaturecK2Lxpo8yHg3hd7hi1zOaoi4nRCt8zwWWIqt47kvbQG/LitfftJRNuaH/BqlTkVeqO9INgx0WxNrdZbX2GEcaAJ9bp8gRPZoGLaztfXRN0KPrspdEh8jiGHi3q7KJtOkaMhzF39ahI8+KhXHrYa/hjg4MXp8h3keIRrNM9HH80U= Keys AESebbc6caaf8a8578e4f691122b434b6ebffa45ce03f10a4509bd0859d64489262 SaltDcRatByqwqdanchun | |||||||||||||||
| 7272 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 944
Read events
3 944
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
29
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2036 | RUXIMICS.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/RUXIM?os=Windows&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3623&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&FlightRing=Retail&AttrDataVer=186&App=RUXIM&AppVer=&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
2036 | RUXIMICS.exe | GET | 200 | 95.101.54.128:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 95.101.54.128:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
3004 | svchost.exe | GET | 200 | 95.101.54.128:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
3004 | svchost.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaasMedic?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&appVer=10.0.19041.3758&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4 | US | text | 3.41 Kb | whitelisted |
— | — | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | unknown |
3548 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
3292 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
3292 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | US | binary | 400 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3004 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2036 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.155:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
2036 | RUXIMICS.exe | 95.101.54.128:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 95.101.54.128:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
3004 | svchost.exe | 95.101.54.128:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6712 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
clipsexsub3x.net |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2036 | RUXIMICS.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |