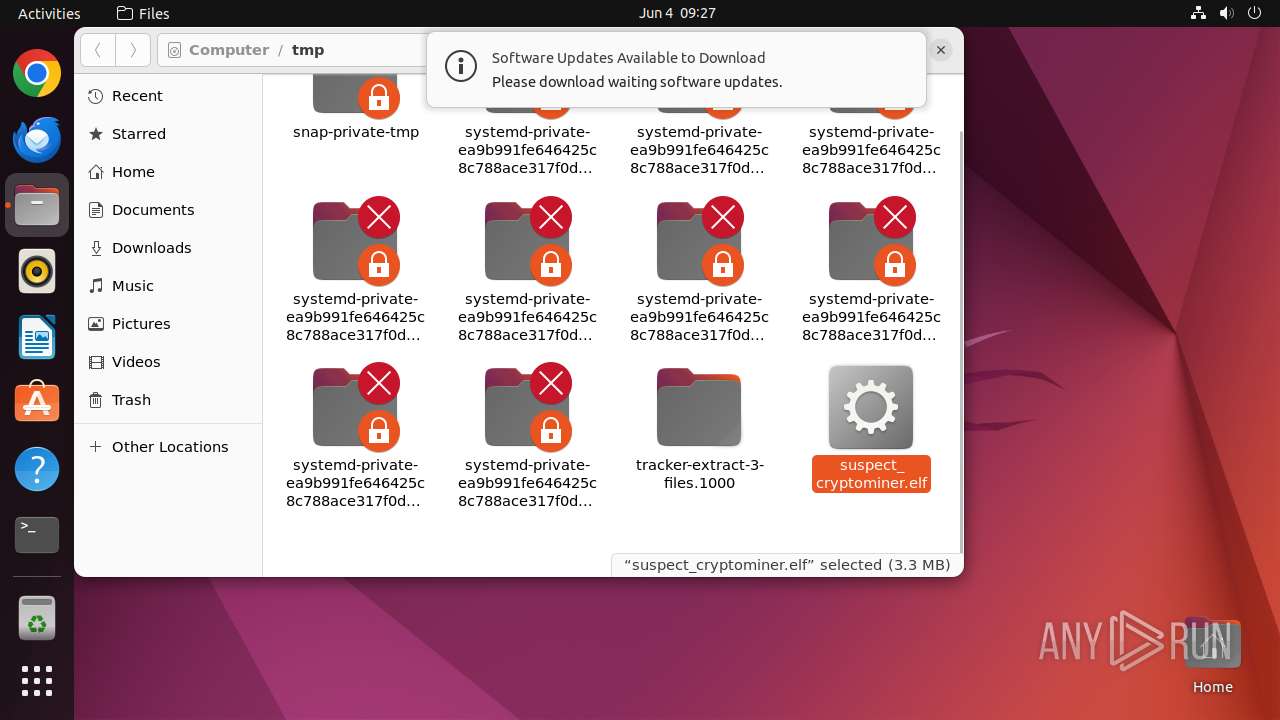
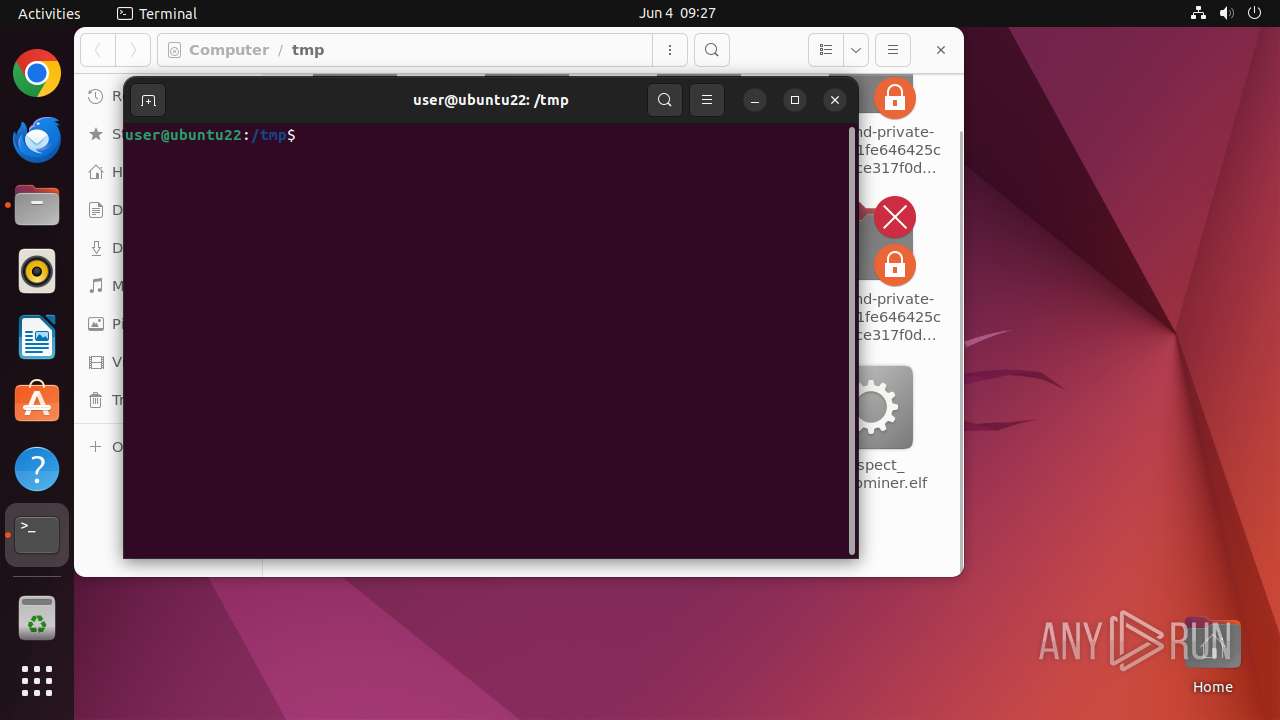
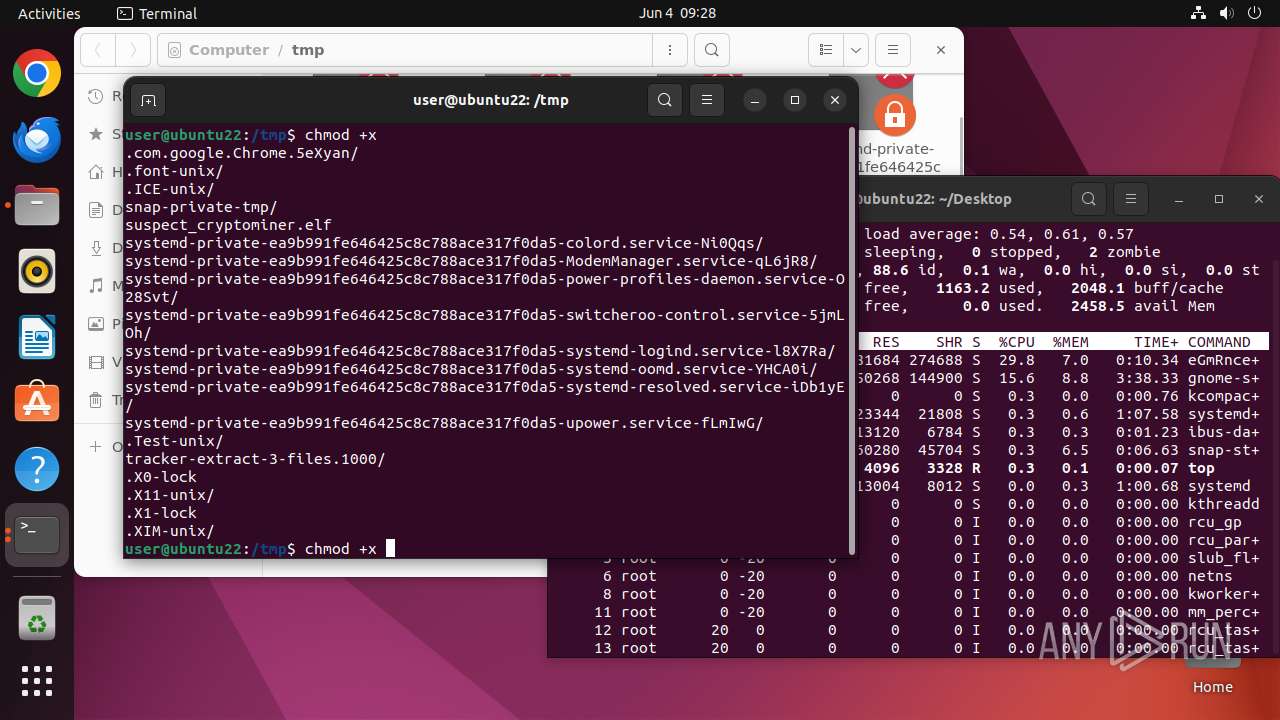
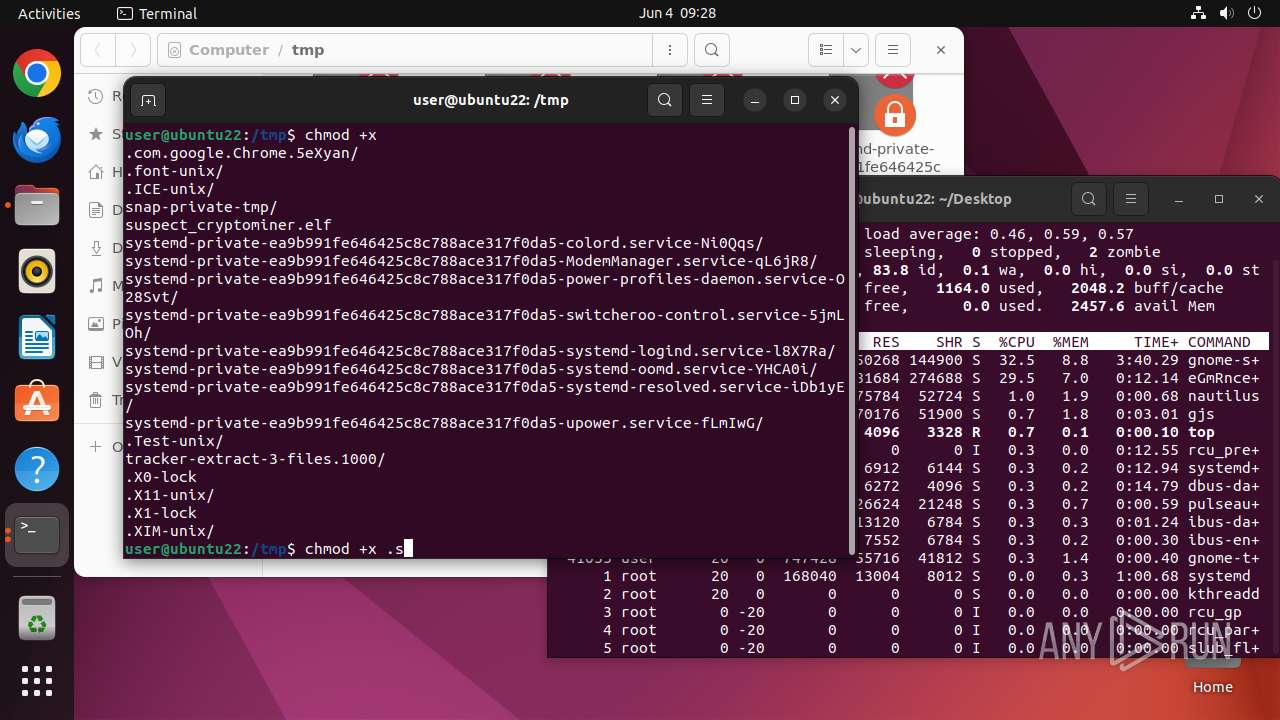
| File name: | suspect_cryptominer |
| Full analysis: | https://app.any.run/tasks/944ab5af-9274-4e3c-919b-797bf0ac5bb2 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | June 04, 2025, 08:27:36 |
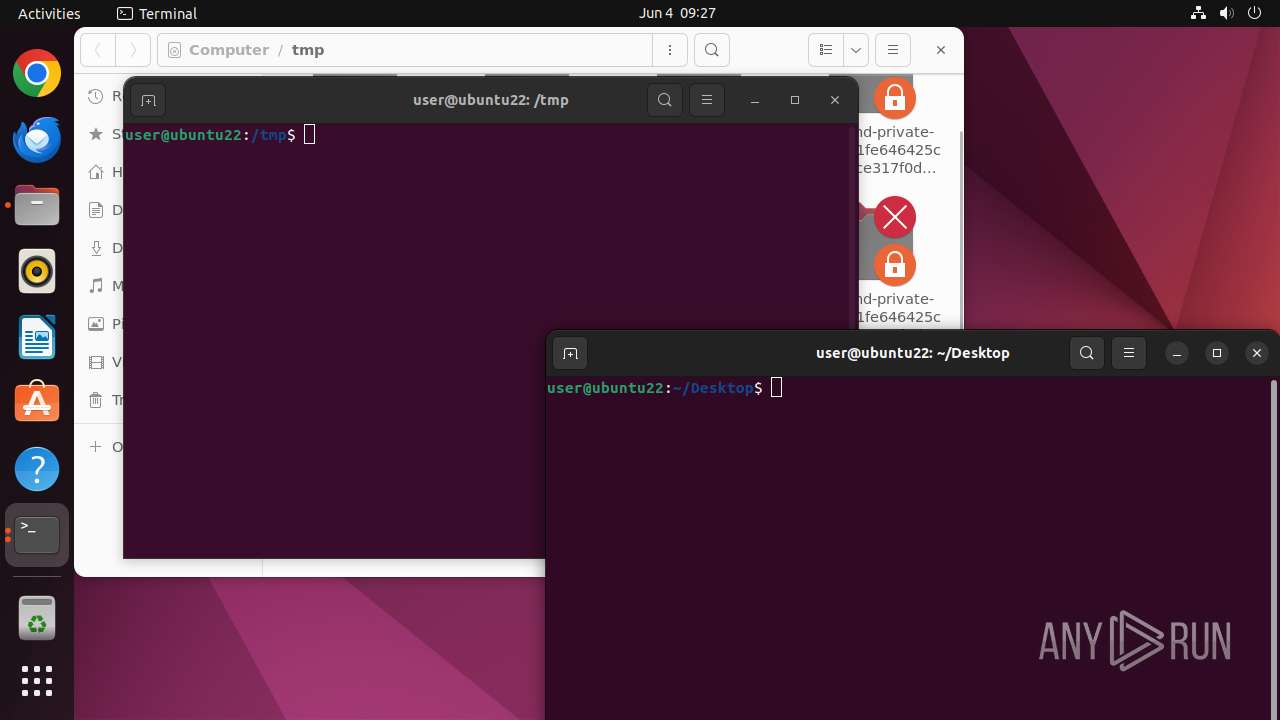
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MIME: | application/x-sharedlib |
| File info: | ELF 64-bit LSB shared object, x86-64, version 1 (SYSV), statically linked, no section header |
| MD5: | BEF192D23B72AAF9698967DACAF35C07 |
| SHA1: | 7B88CB40B60323984A5E8FB976C2A443CC26B244 |
| SHA256: | 68DE36F14A7C9E9514533A347D7C6BC830369C7528E07AF5C93E0BF7C1CD86DF |
| SSDEEP: | 98304:8zzJiH89vHtZjadzEkmCRdU4rJ2eLc1t9zjUkKa06N6QjUiJZ6tLsDUl2rH+Tmq6:AbeYTWgRUESC |
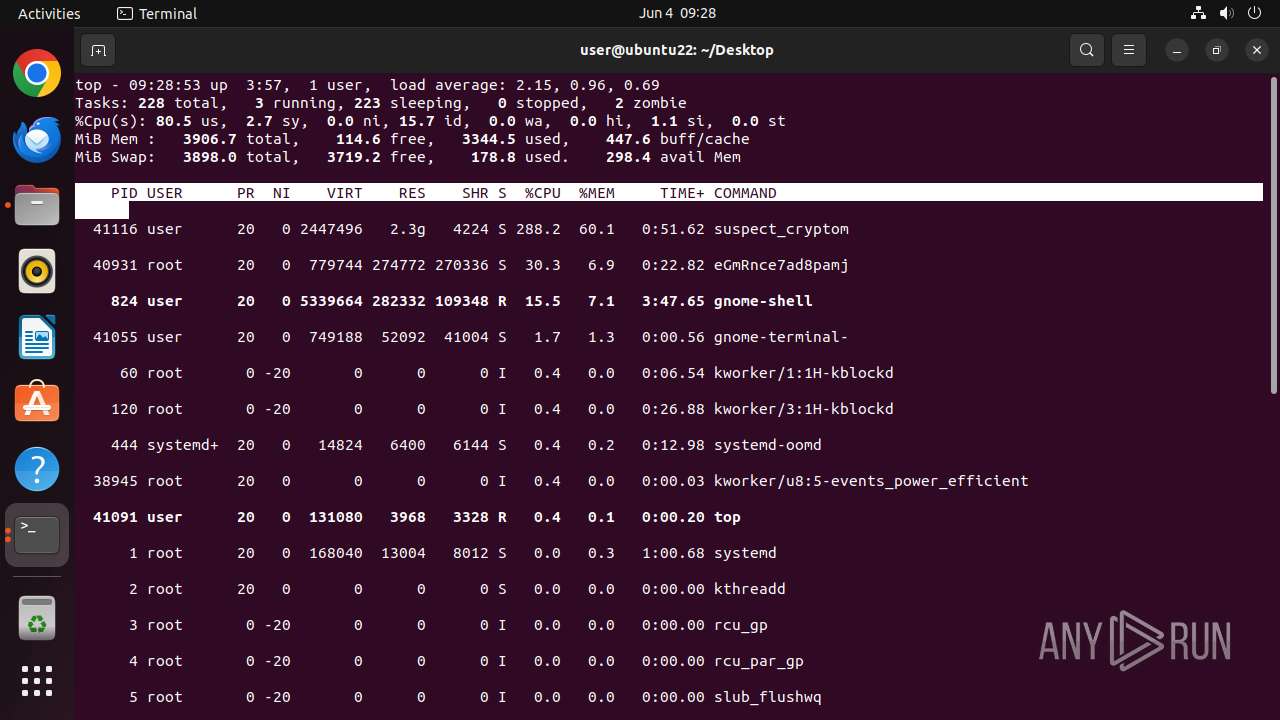
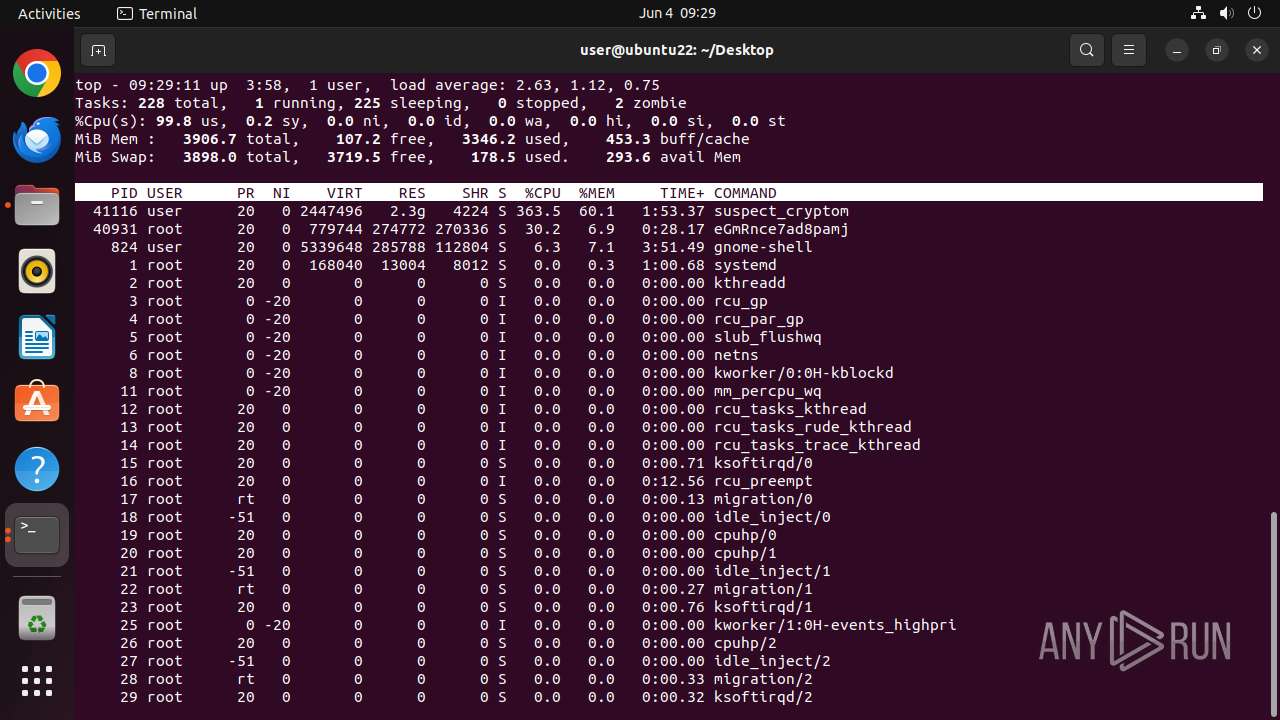
MALICIOUS
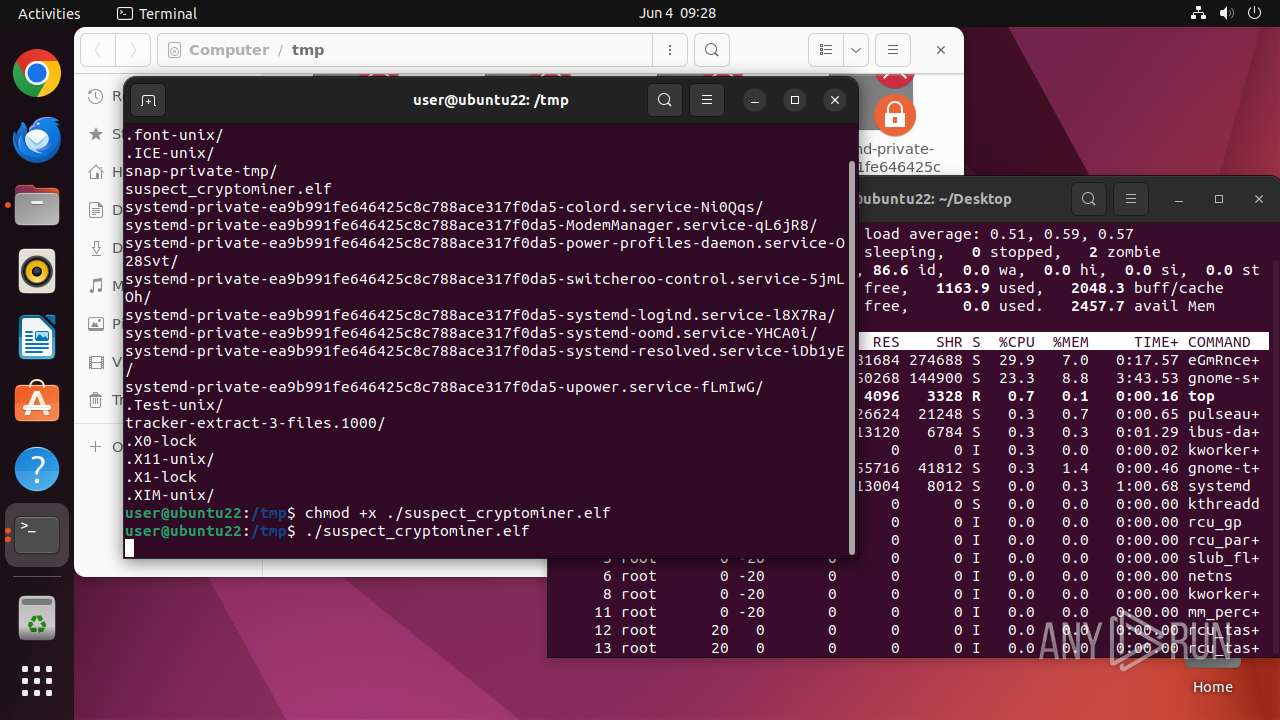
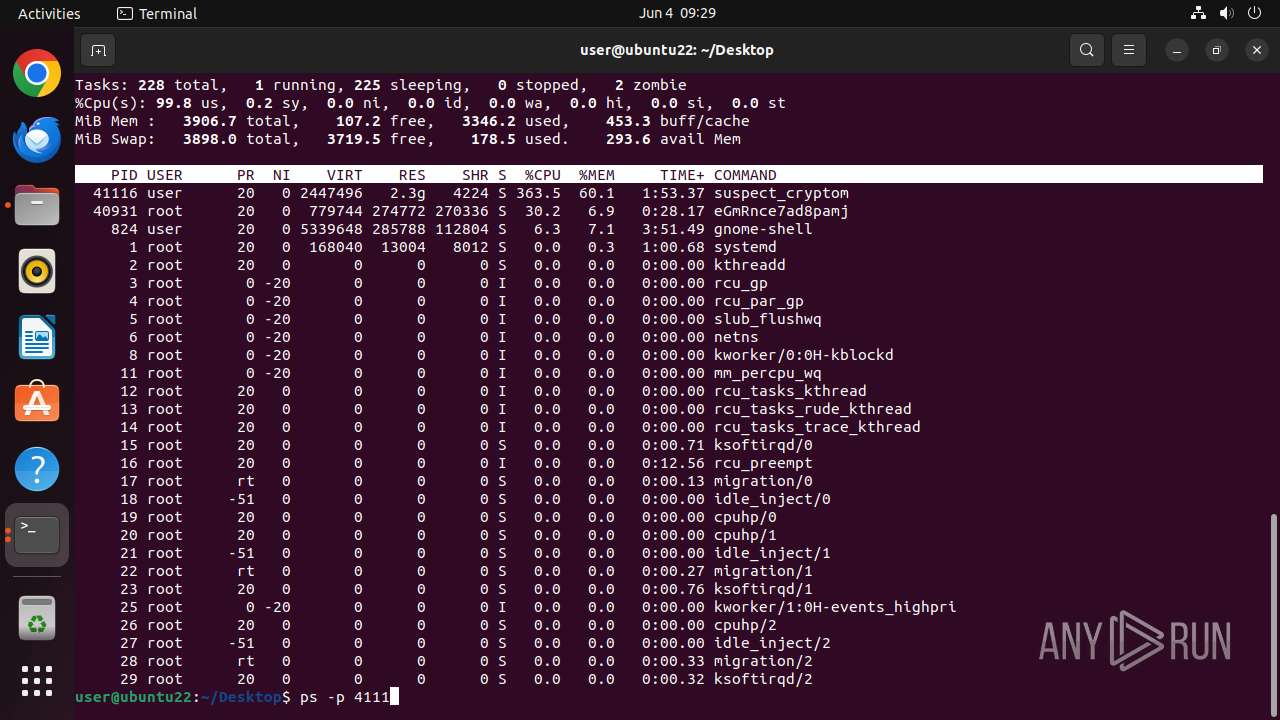
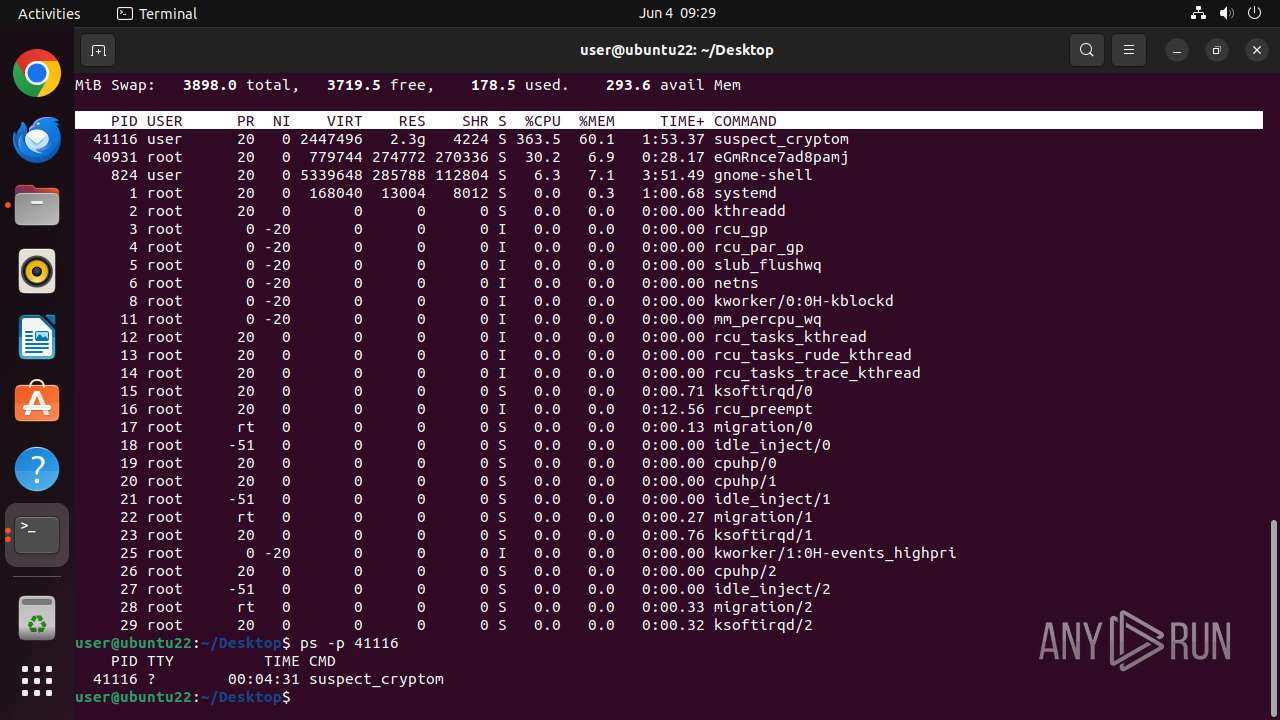
Connects to the CnC server
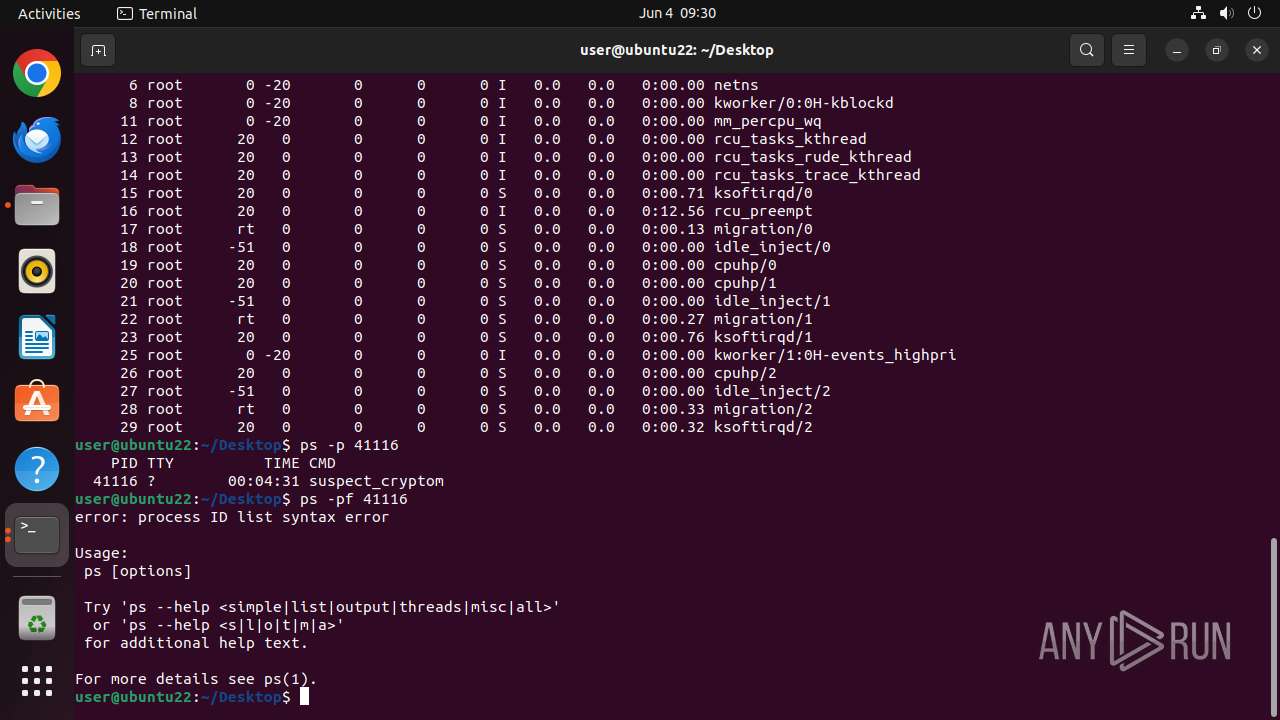
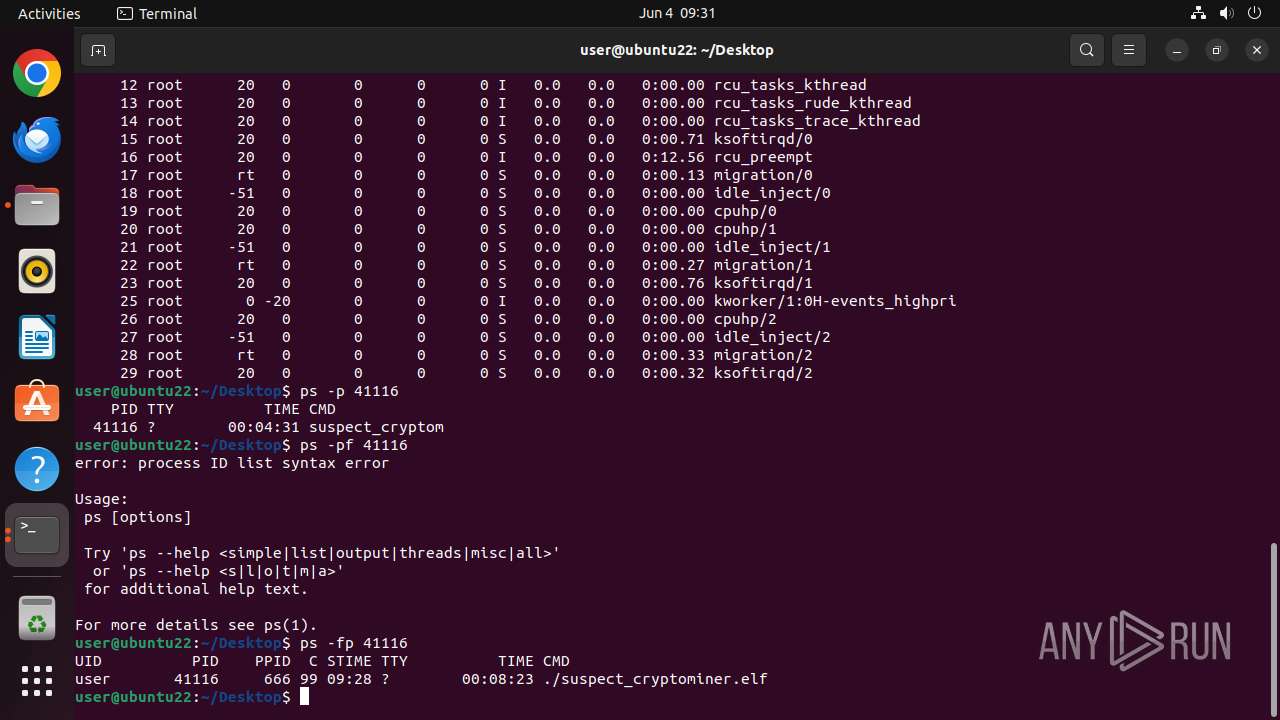
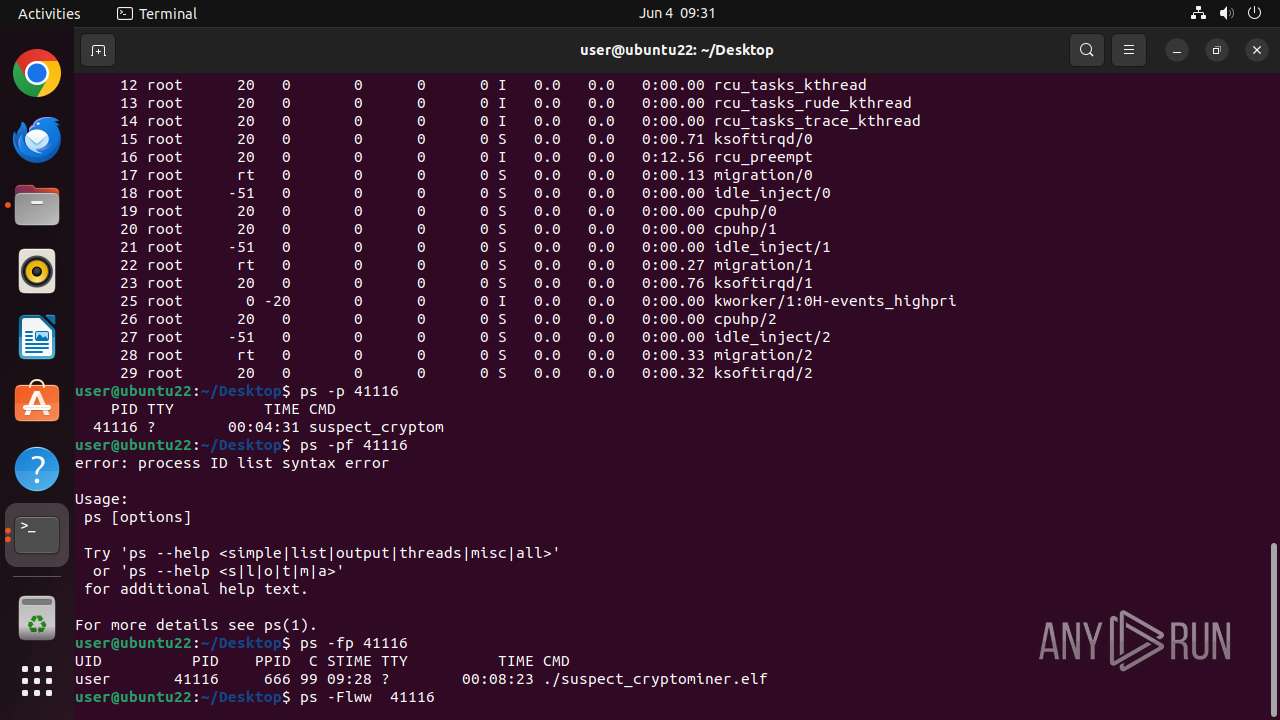
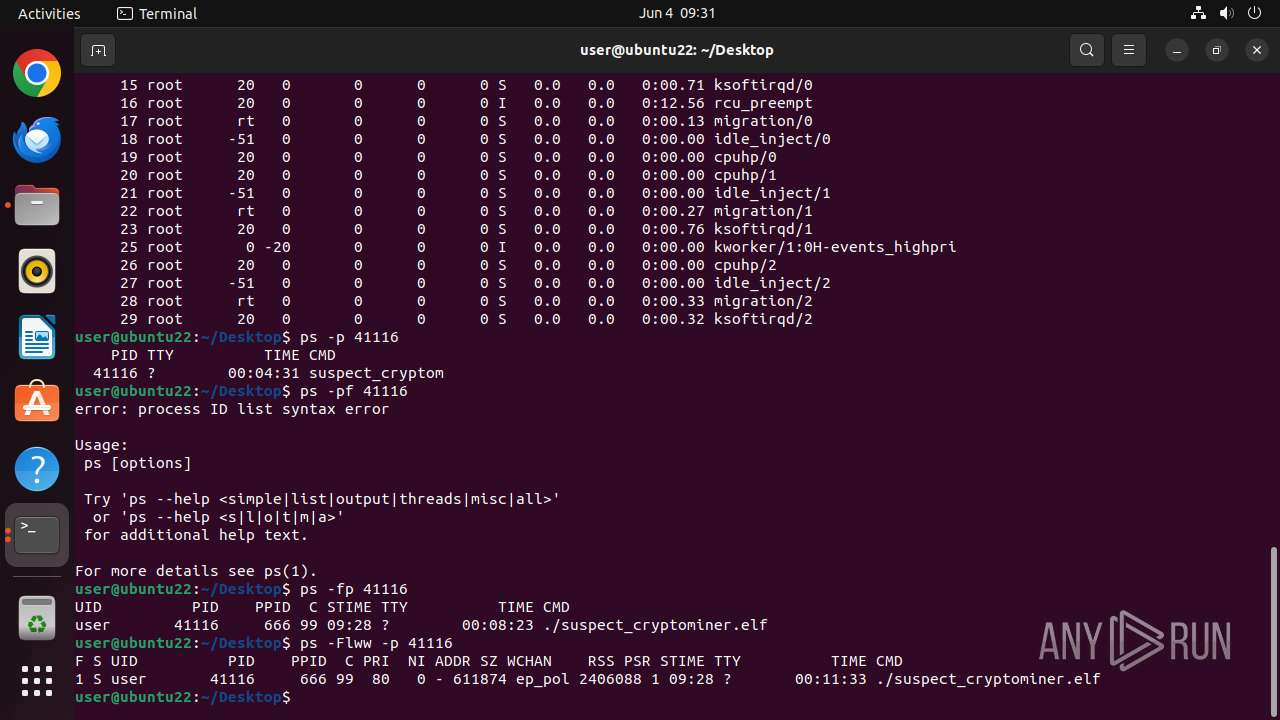
- suspect_cryptominer.elf (PID: 41116)
MINER has been detected (SURICATA)
- suspect_cryptominer.elf (PID: 41116)
SUSPICIOUS
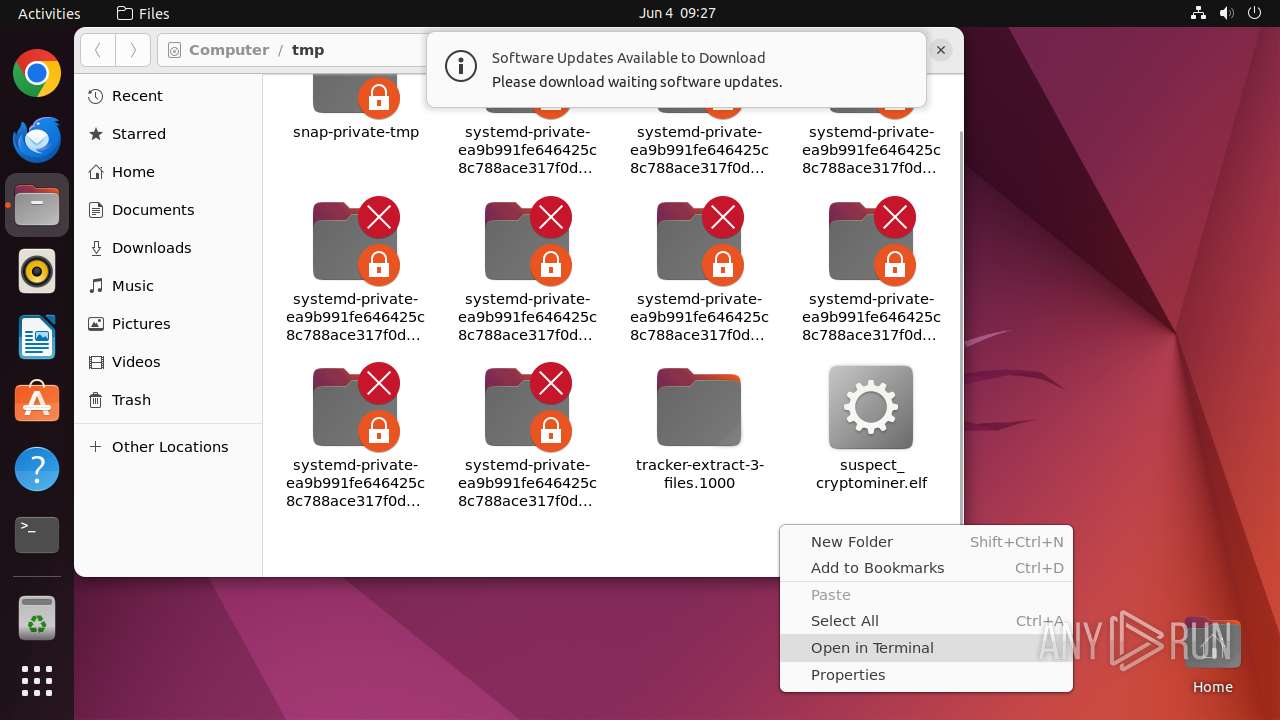
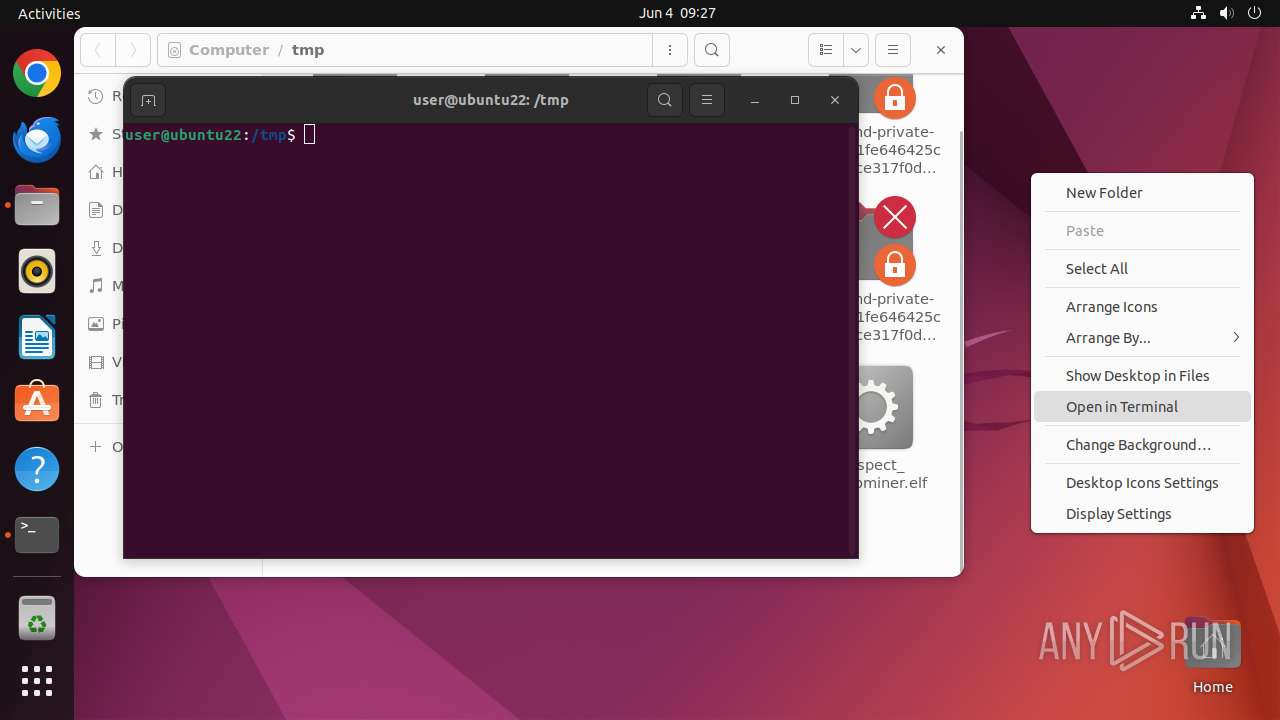
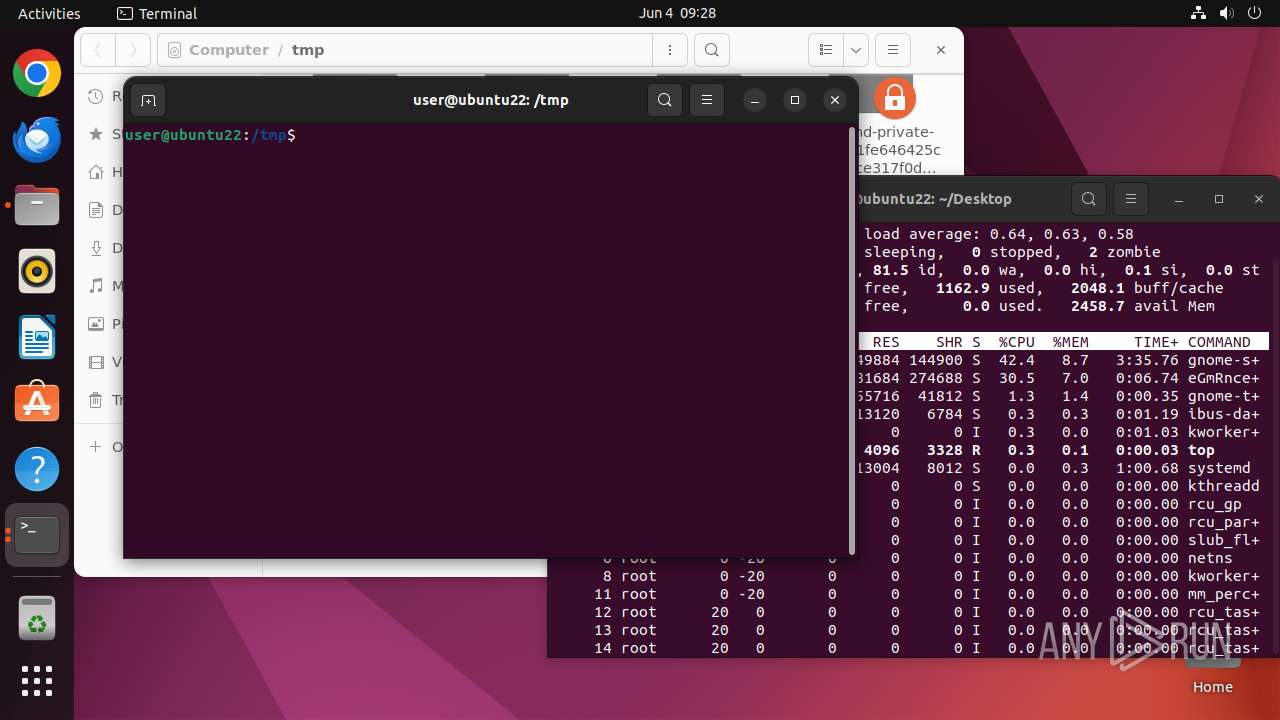
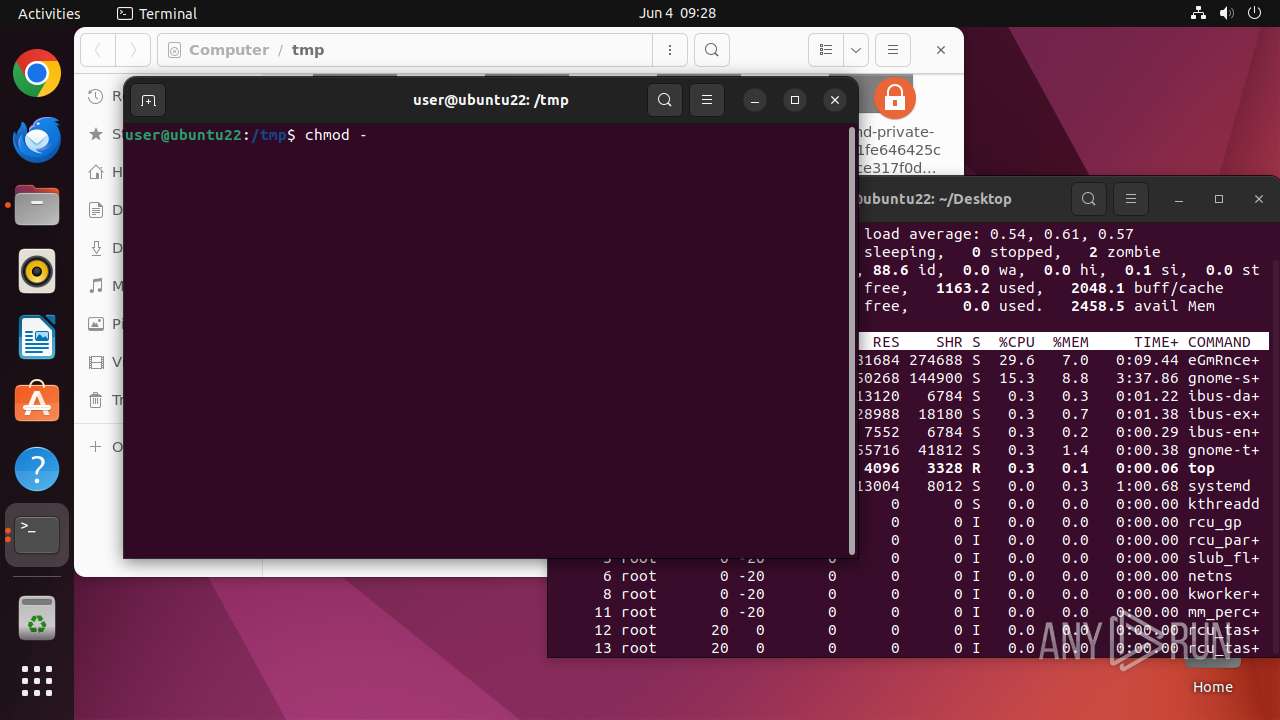
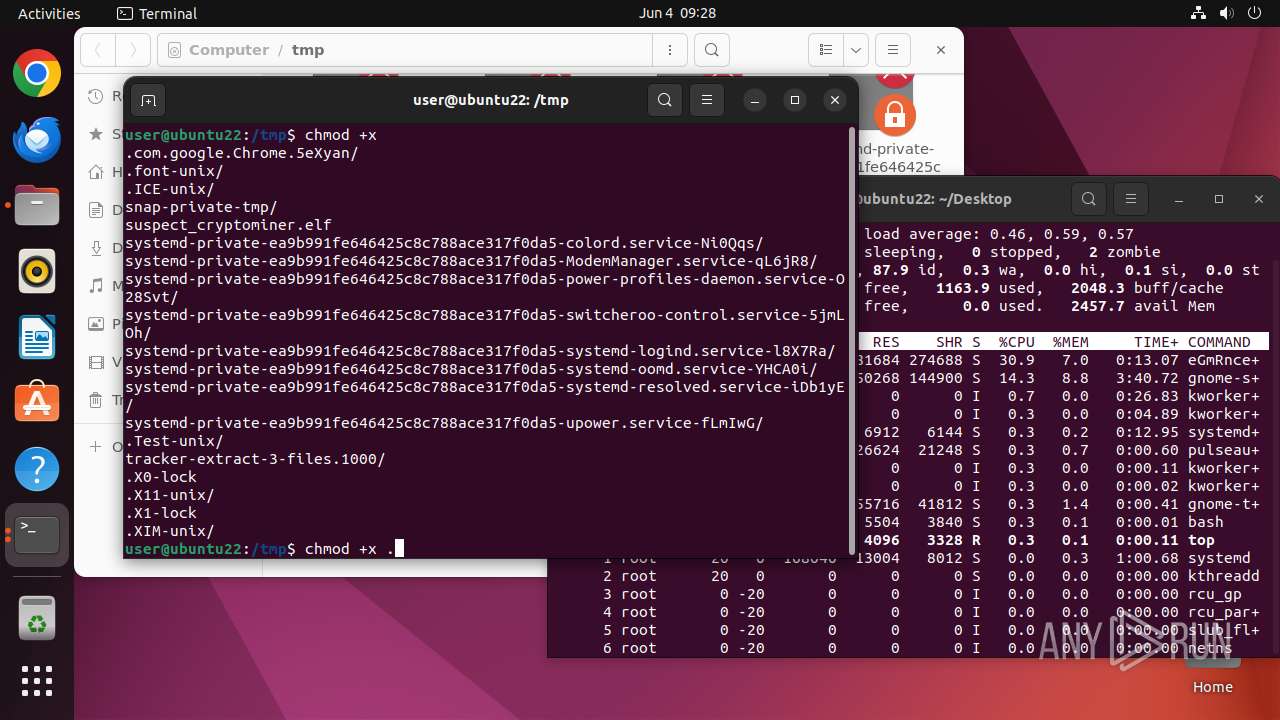
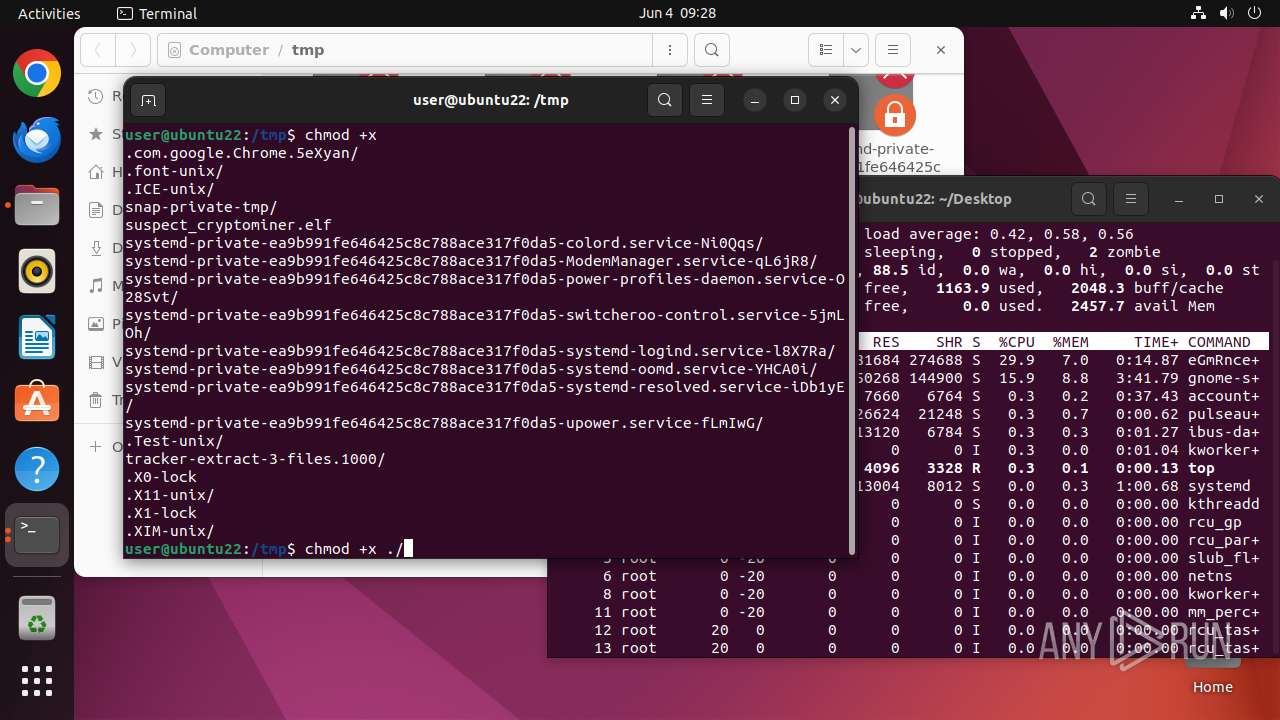
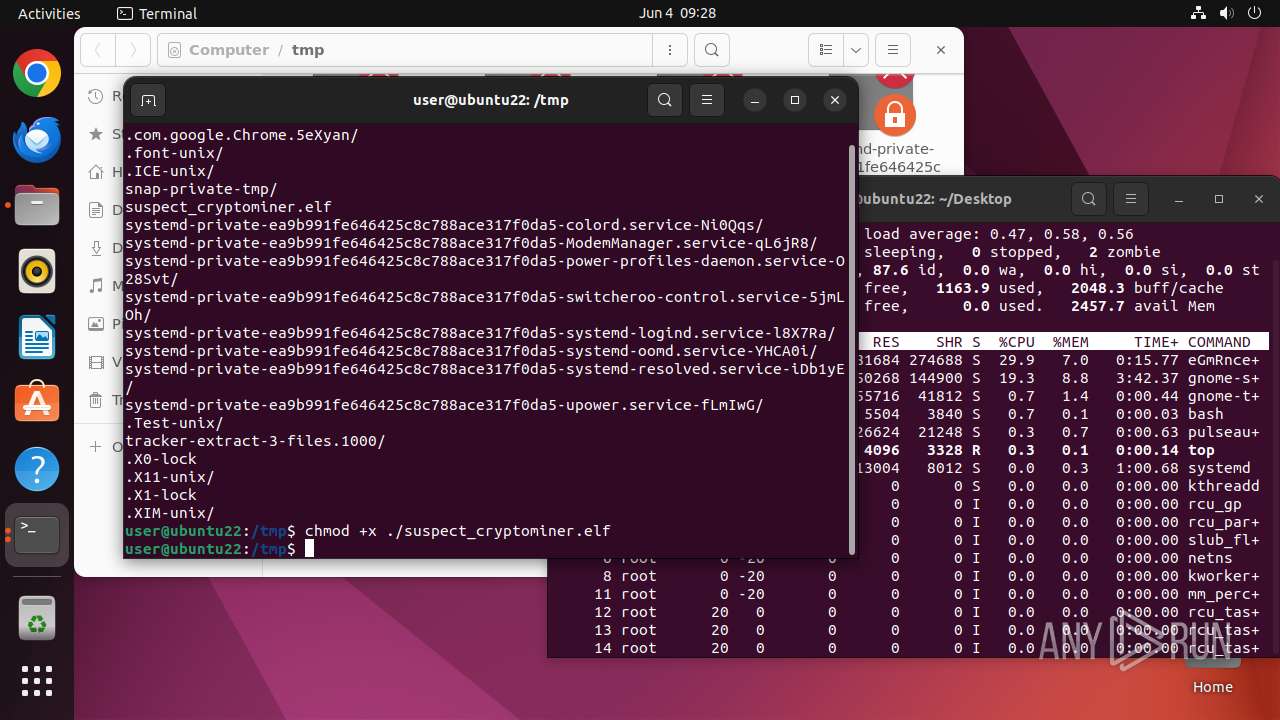
Executes commands using command-line interpreter
- sudo (PID: 41028)
- gnome-terminal-server (PID: 41055)
Checks DMI information (probably VM detection)
- suspect_cryptominer.elf (PID: 41115)
Connects to unusual port
- suspect_cryptominer.elf (PID: 41116)
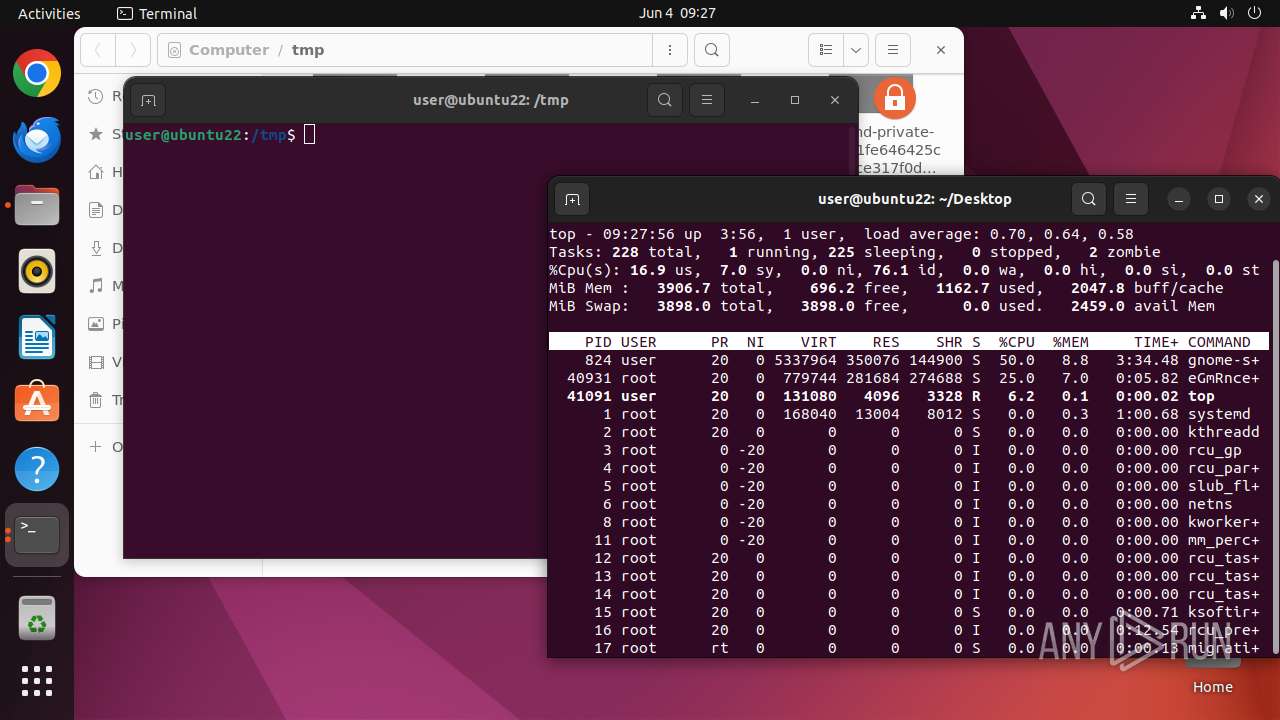
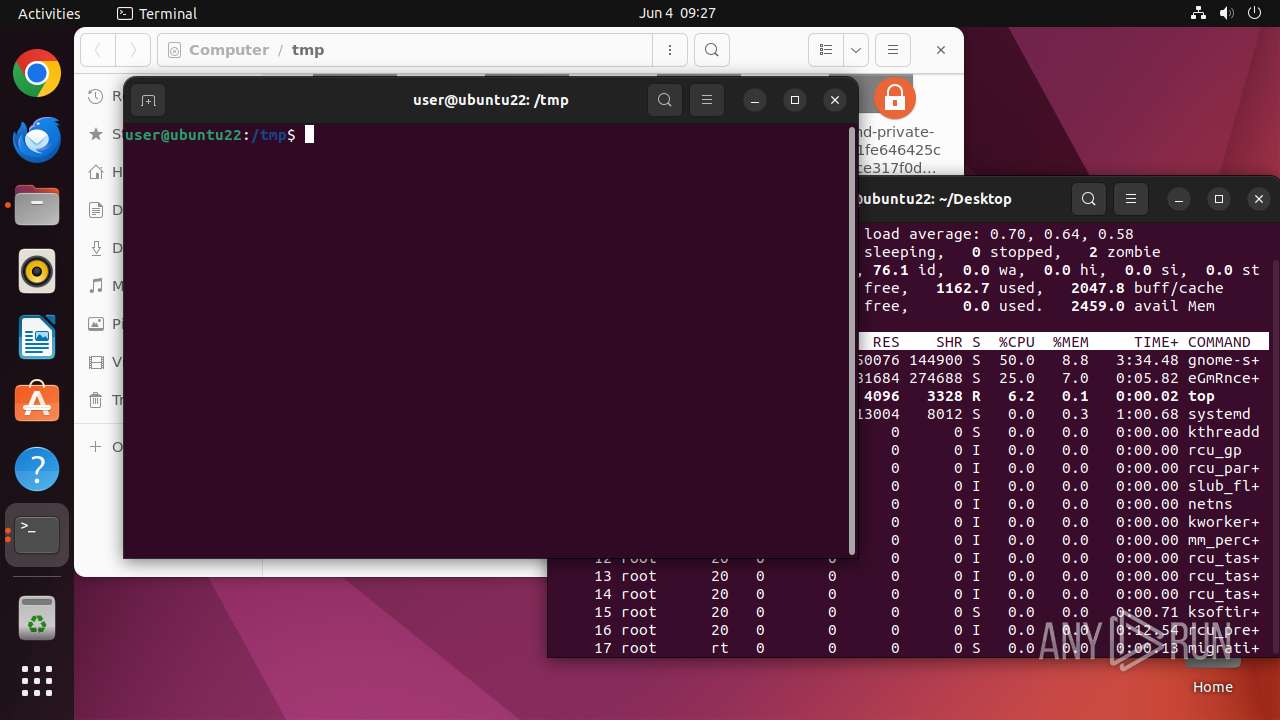
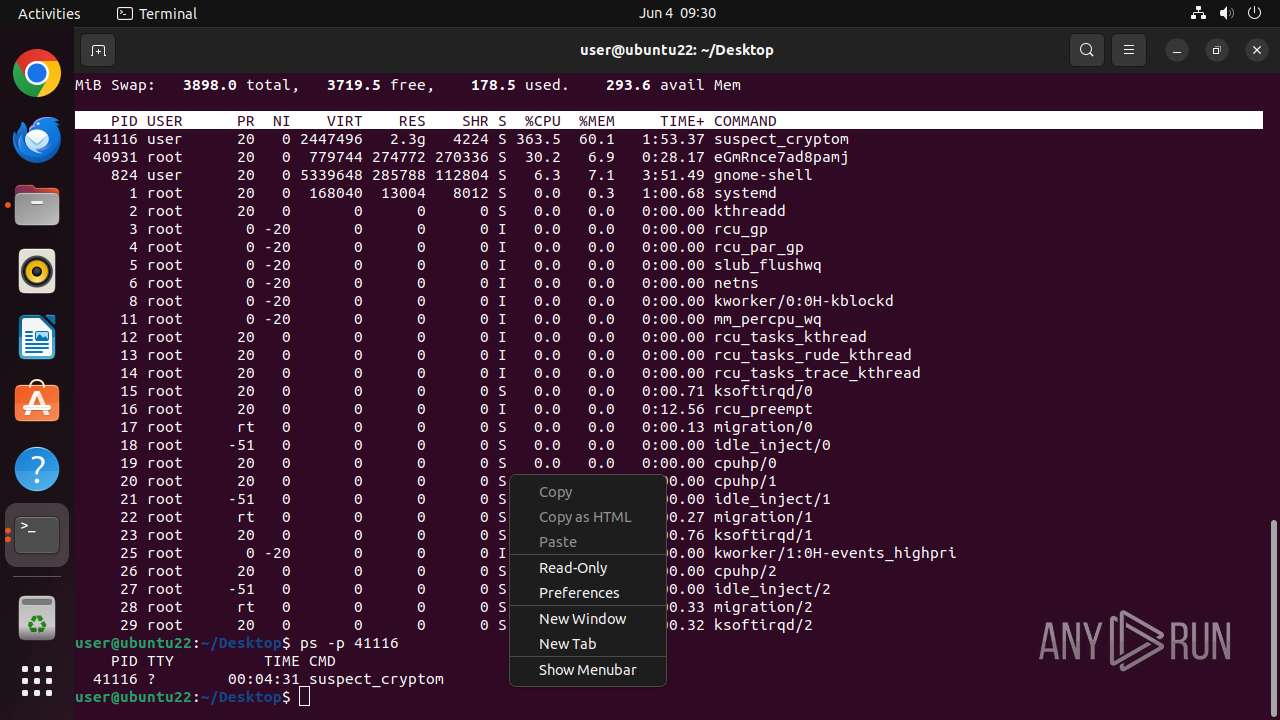
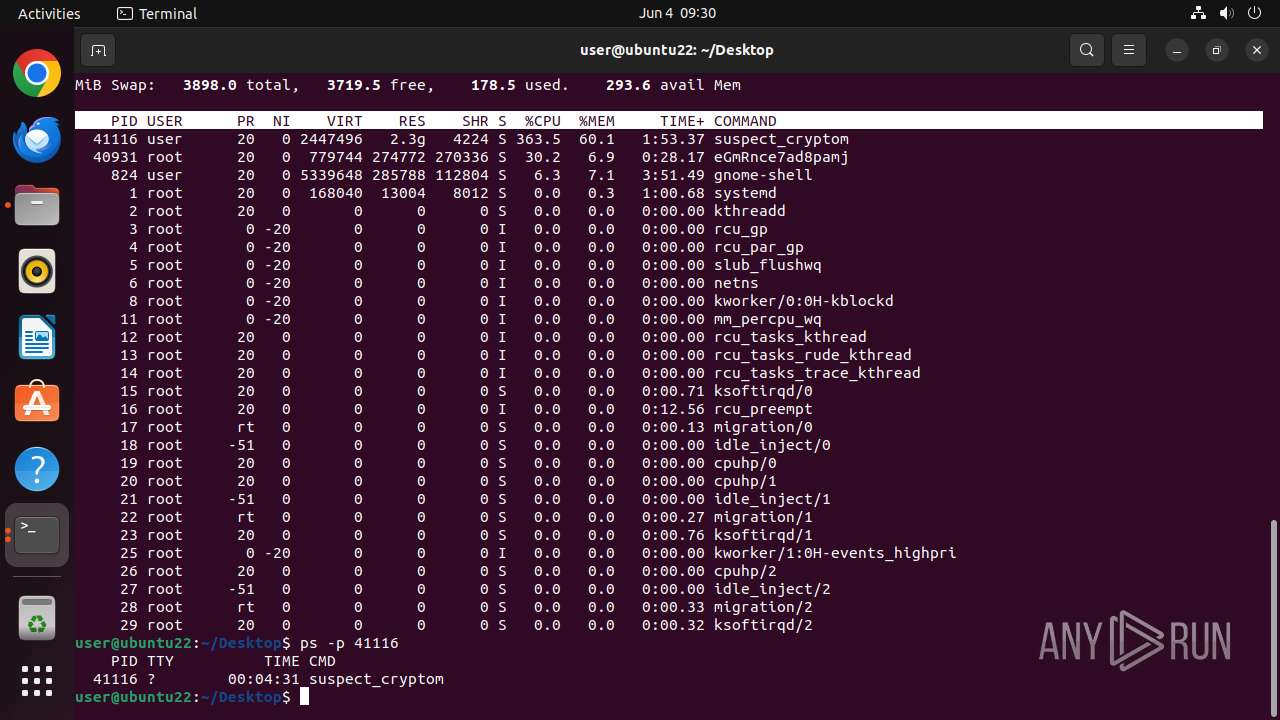
Gets information about currently running processes
- bash (PID: 41085)
Reads passwd file
- top (PID: 41091)
Potential Corporate Privacy Violation
- suspect_cryptominer.elf (PID: 41116)
INFO
Checks timezone
- python3.10 (PID: 41079)
- top (PID: 41091)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (49.8) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Shared object file |
| CPUType: | AMD x86-64 |
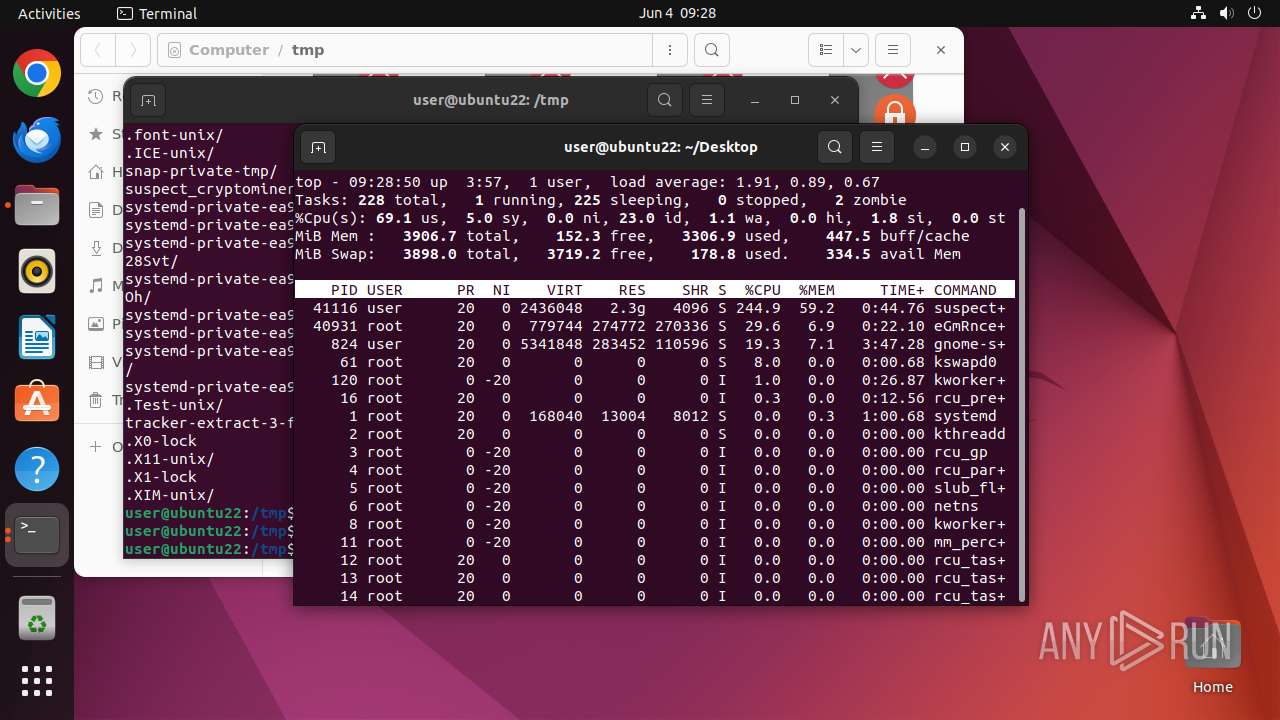
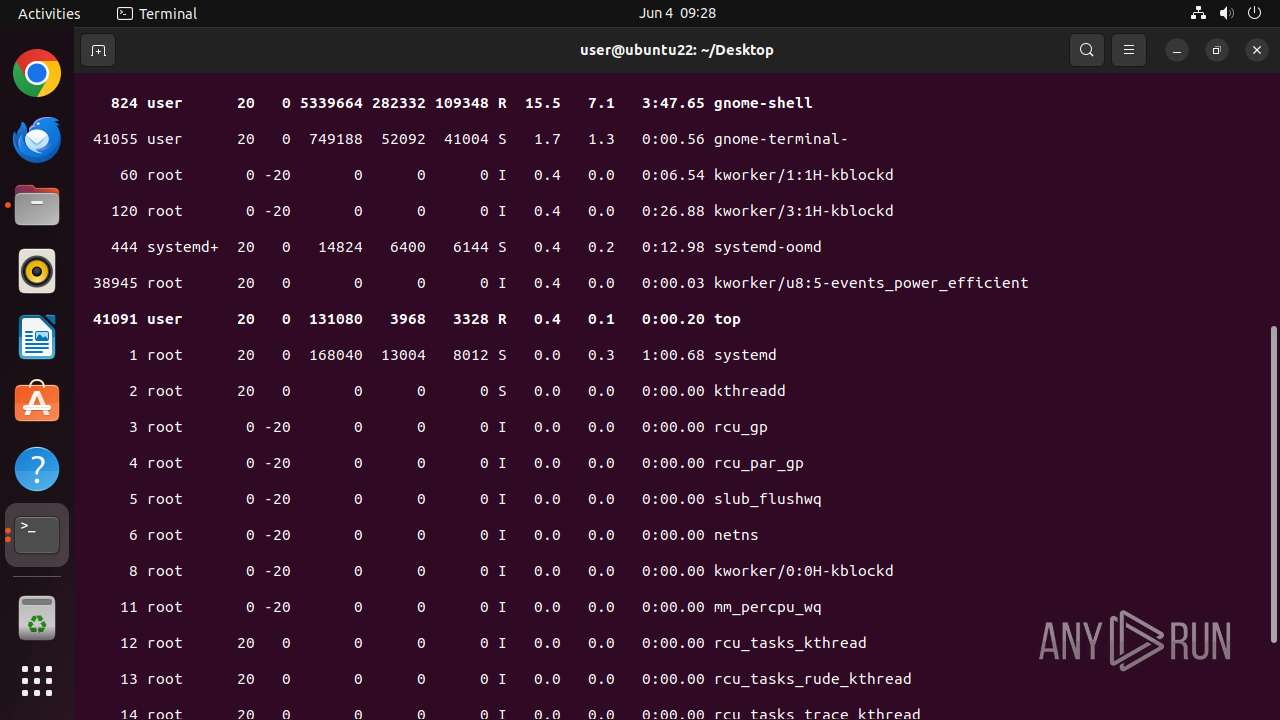
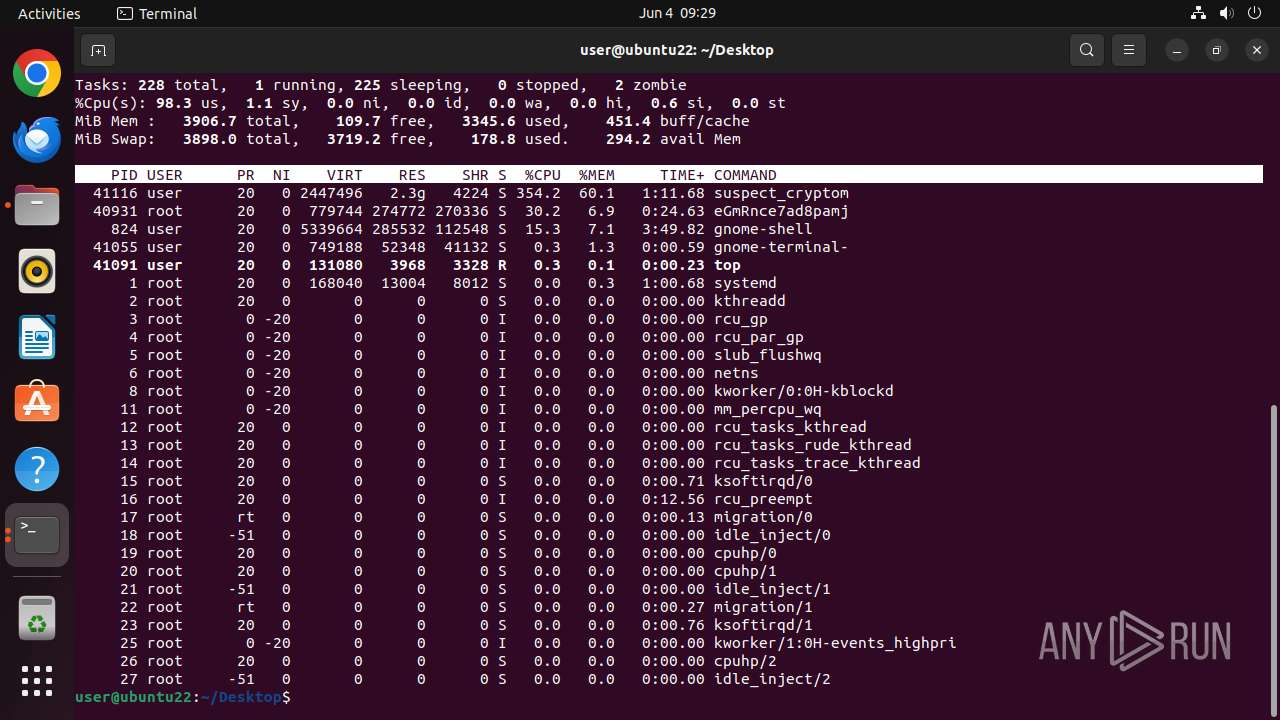
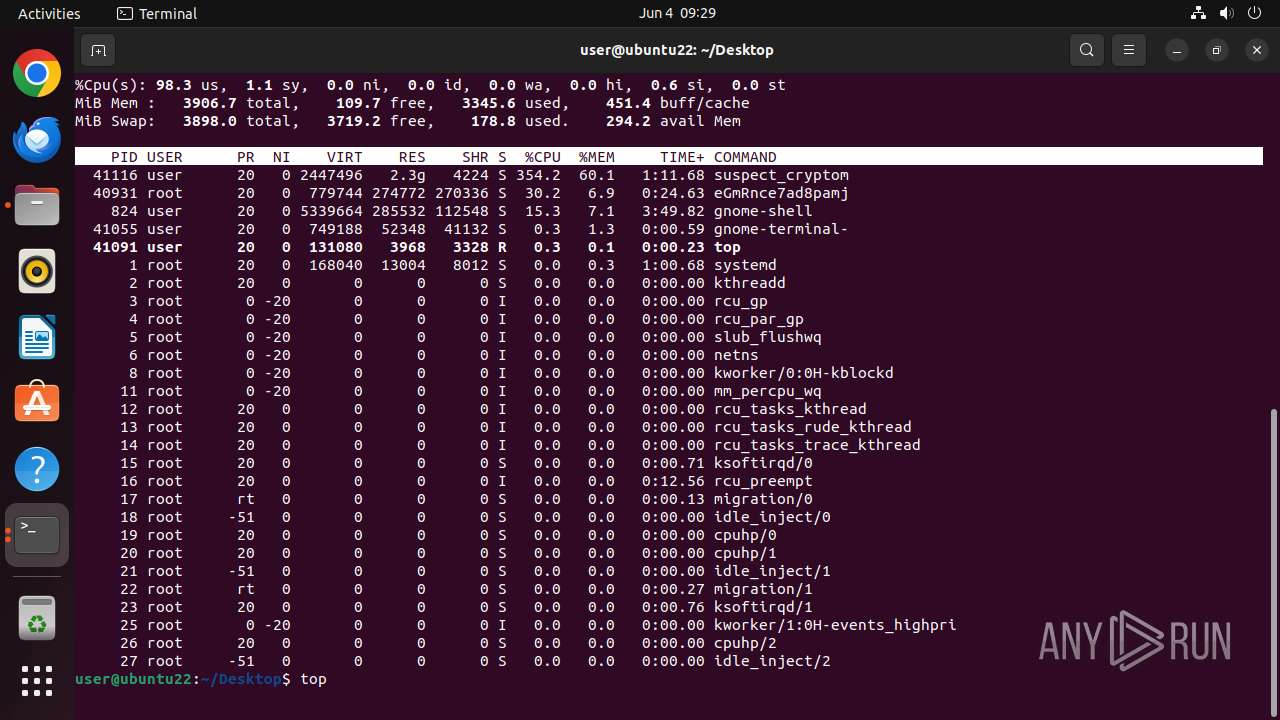
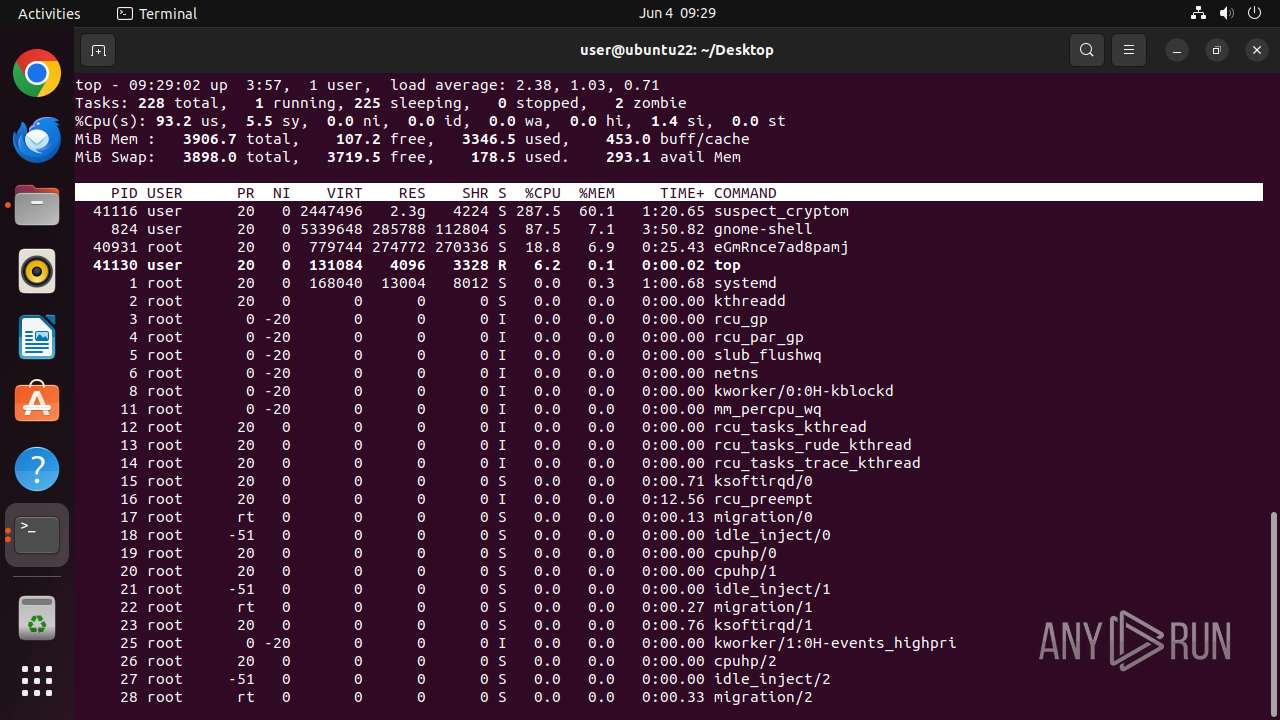
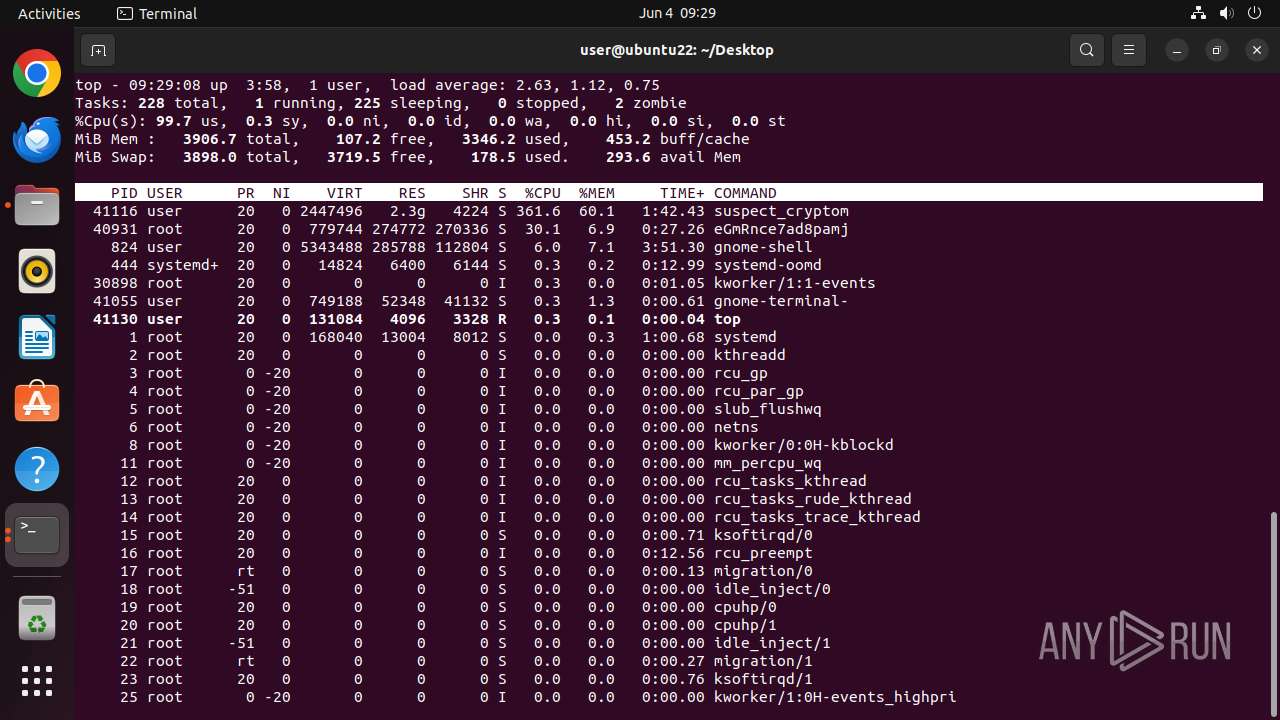
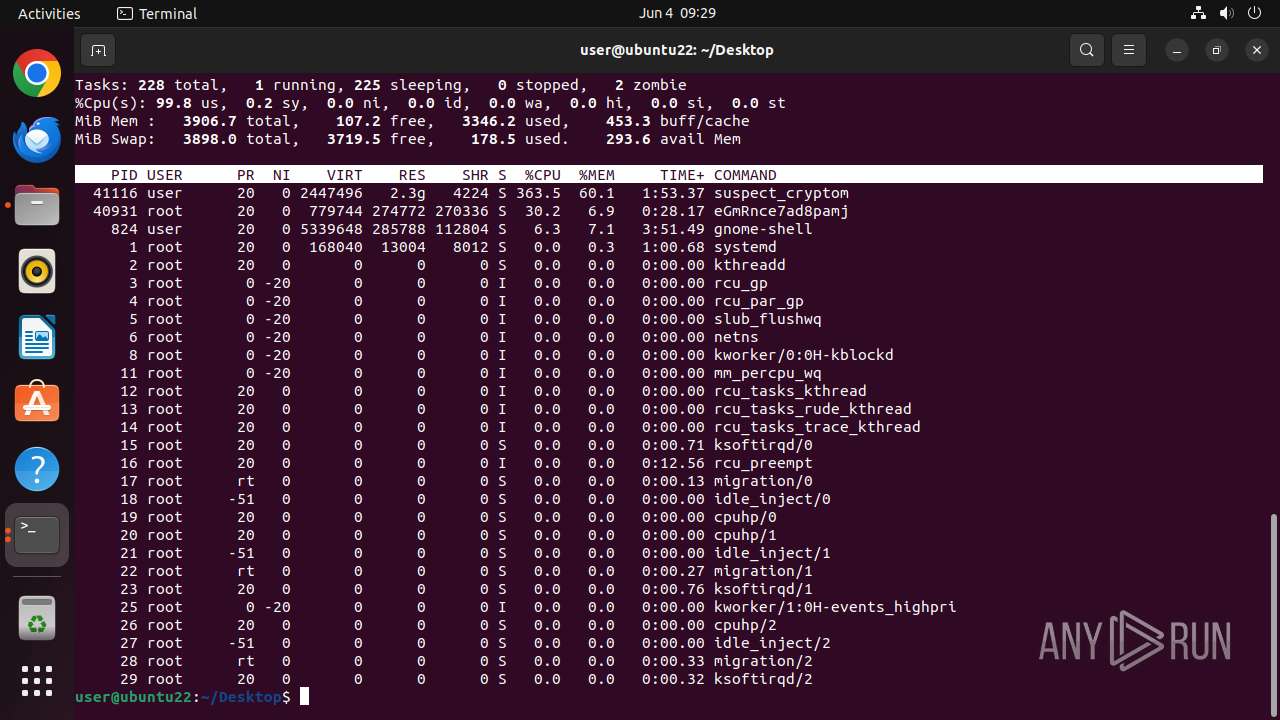
Total processes
175
Monitored processes
43
Malicious processes
2
Suspicious processes
2
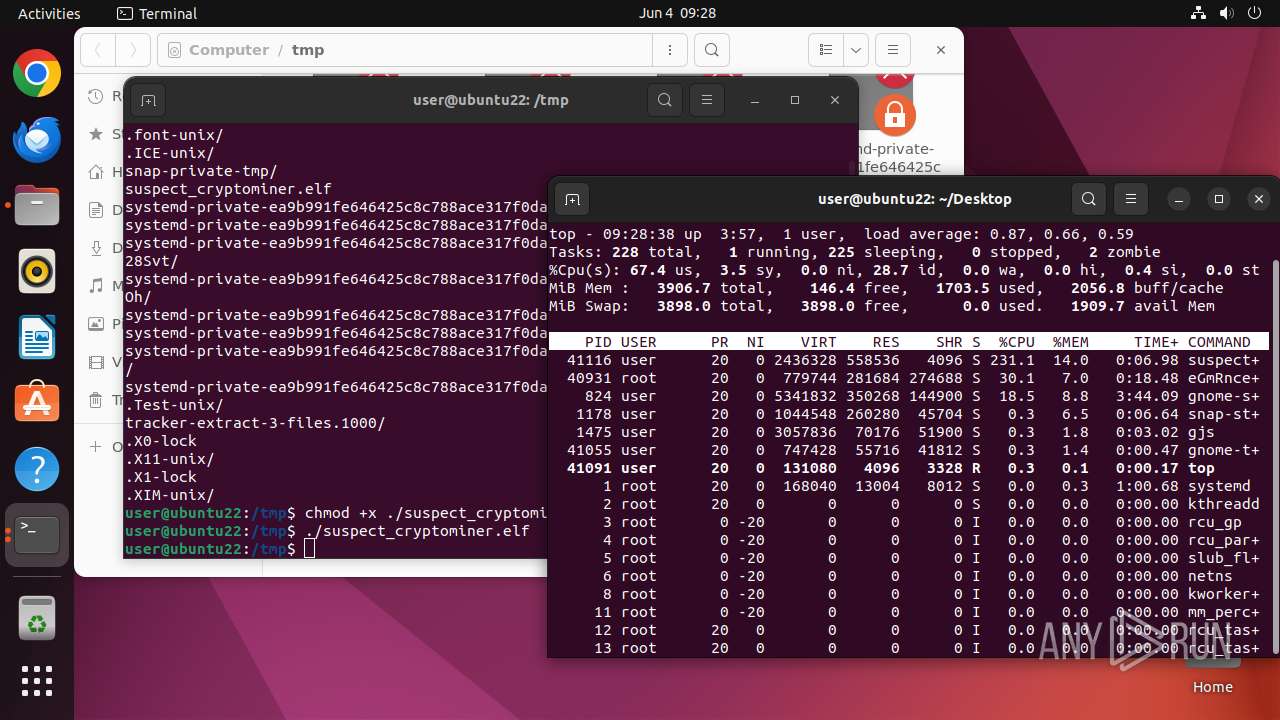
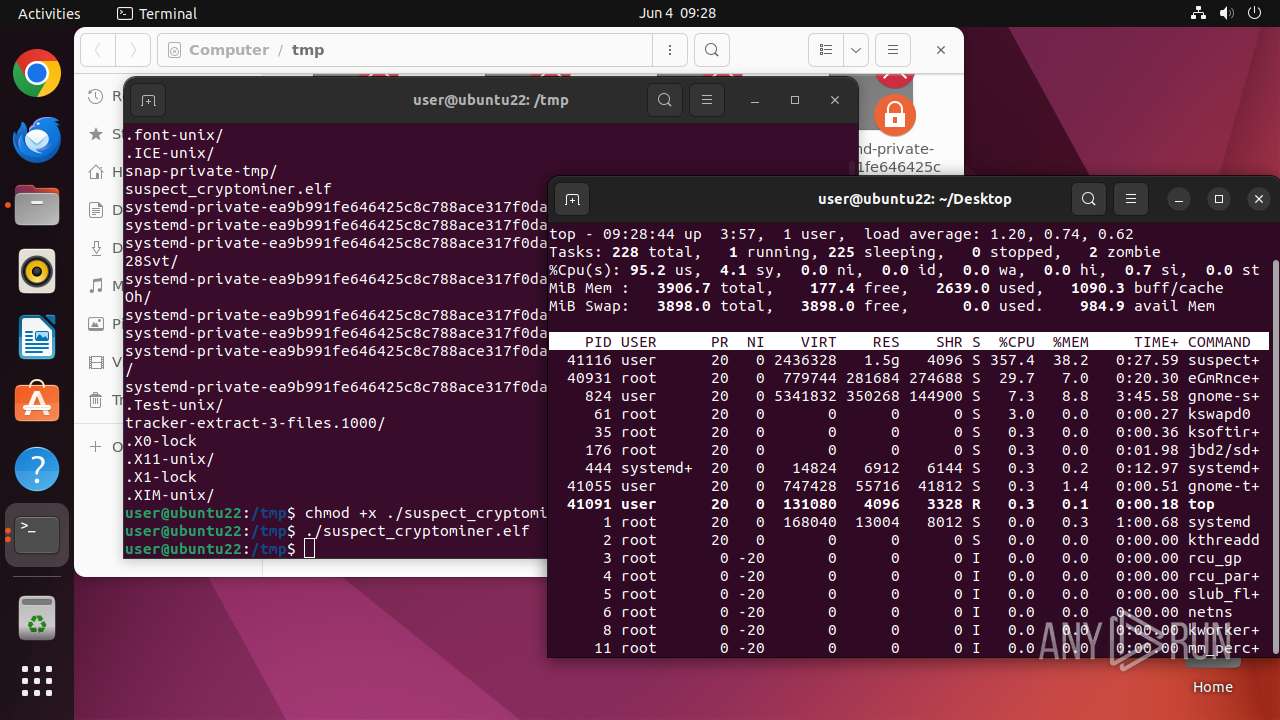
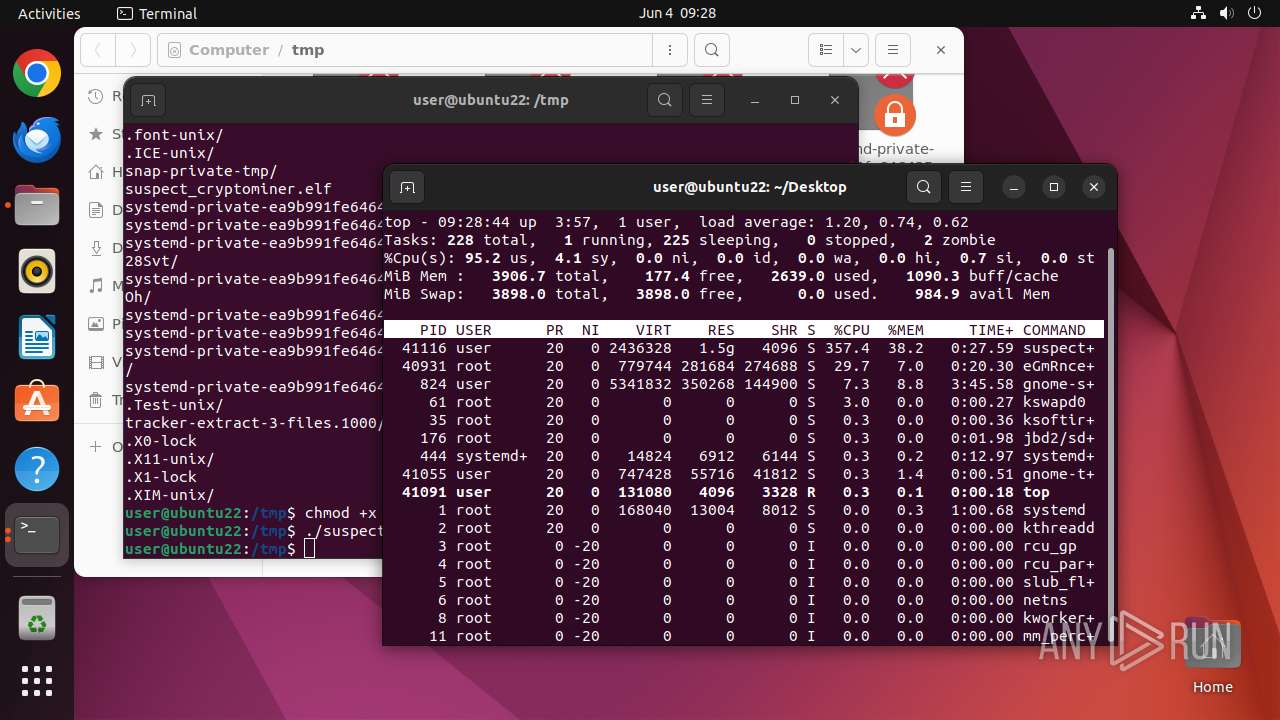
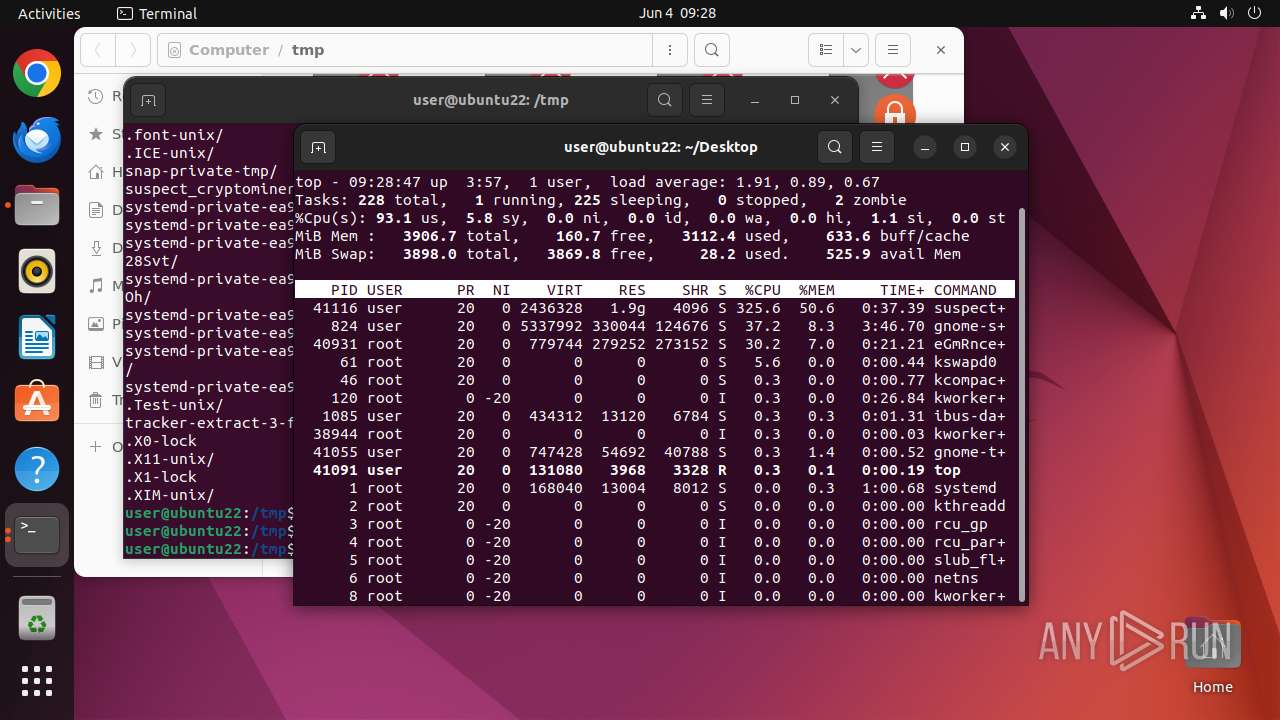
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
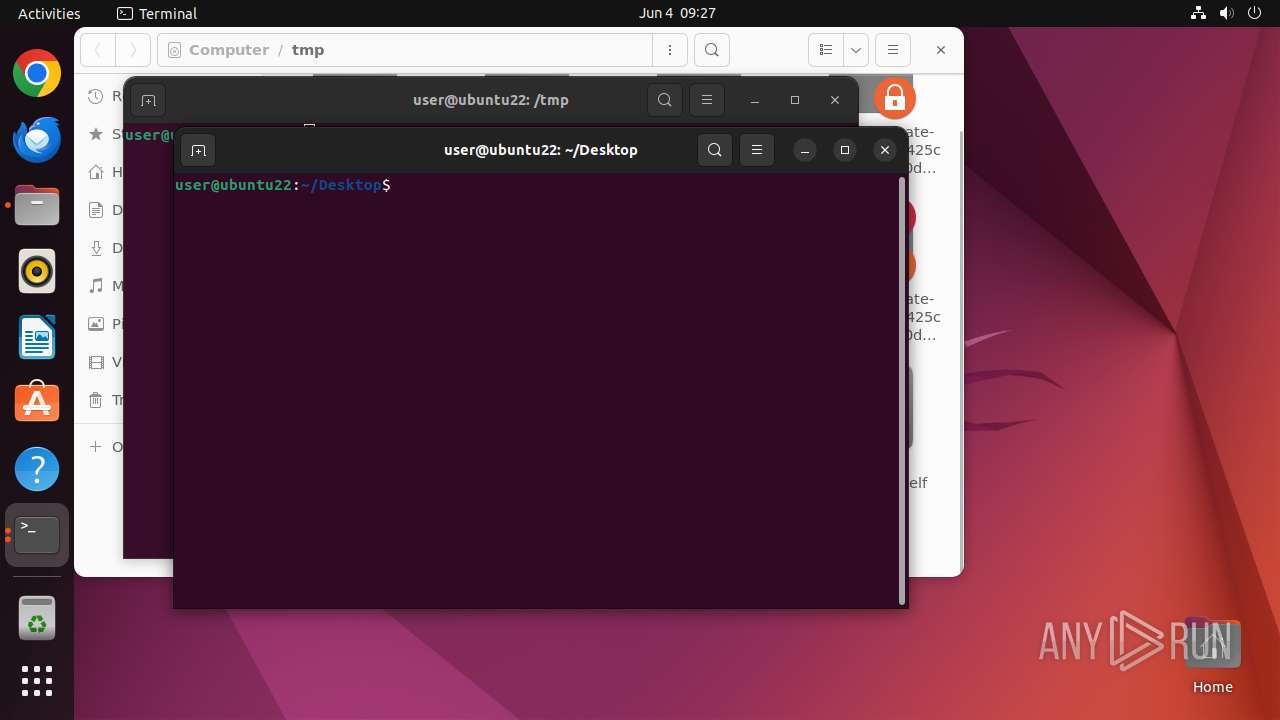
| 41027 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus /tmp/suspect_cryptominer\.elf " | /usr/bin/dash | — | IntiFjKCklFyPMJr | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41028 | sudo -iu user nautilus /tmp/suspect_cryptominer.elf | /usr/bin/sudo | — | dash | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41029 | nautilus /tmp/suspect_cryptominer.elf | /usr/bin/nautilus | — | sudo | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41030 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41048 | /lib/systemd/systemd-hostnamed | /usr/lib/systemd/systemd-hostnamed | — | systemd | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41055 | /usr/libexec/gnome-terminal-server | /usr/libexec/gnome-terminal-server | — | systemd | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41073 | bash | /usr/bin/bash | — | gnome-terminal-server | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41074 | /bin/sh /usr/bin/lesspipe | /usr/bin/dash | — | bash | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41075 | basename /usr/bin/lesspipe | /usr/bin/basename | — | dash | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41076 | /bin/sh /usr/bin/lesspipe | /usr/bin/dash | — | dash | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 | |||||||||||||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
13
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 204 | 91.189.91.97:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 195.181.175.41:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.57:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
41116 | suspect_cryptominer.elf | 85.239.243.201:19999 | auto.c3pool.org | CASABLANCA INT a.s. | CZ | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
4.100.168.192.in-addr.arpa |
| unknown |
connectivity-check.ubuntu.com |
| whitelisted |
auto.c3pool.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
41116 | suspect_cryptominer.elf | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
41116 | suspect_cryptominer.elf | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |