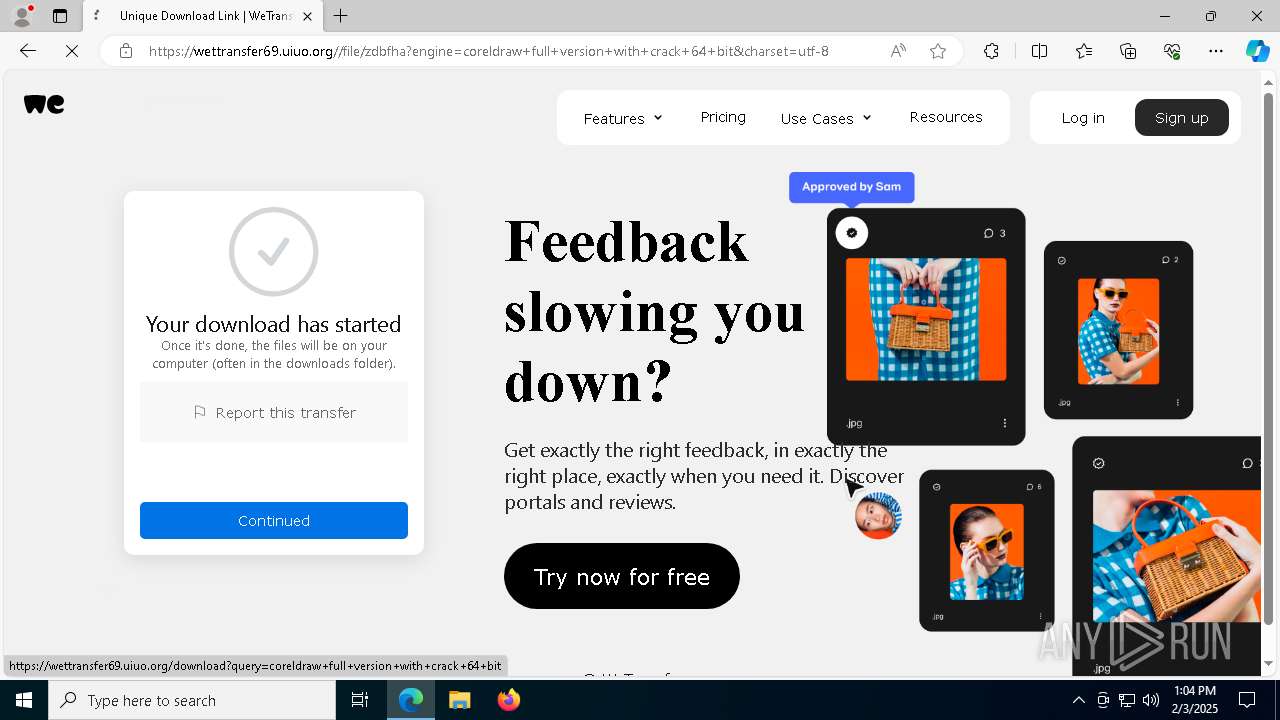
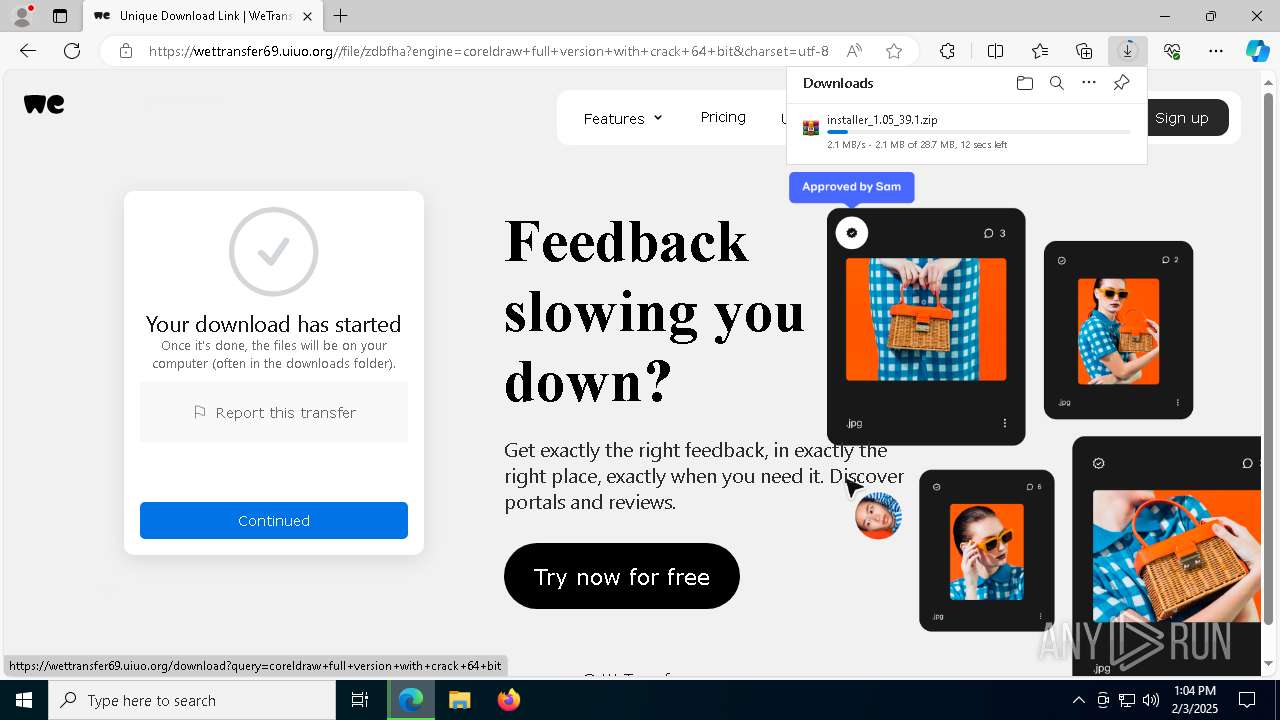
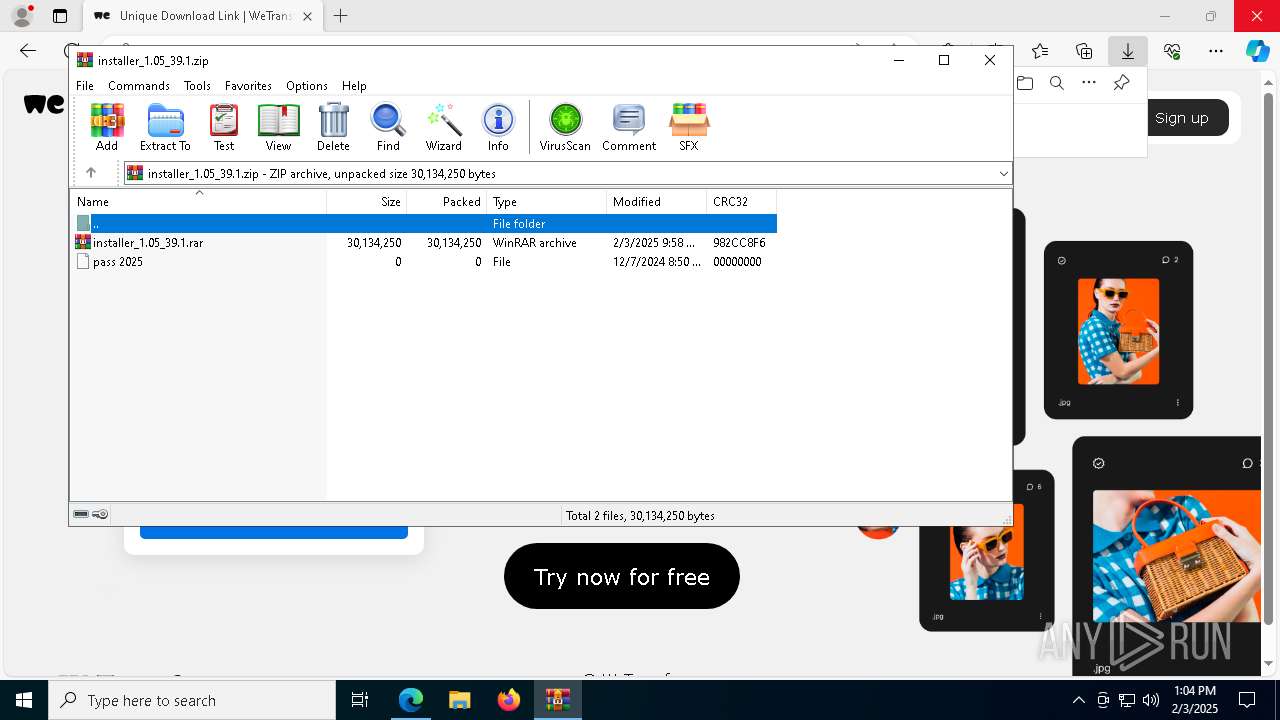
| URL: | https://h94af8b5.saferedirect.top/tmp/googlecollab/coreldraw+full+version+with+crack+64+bit |
| Full analysis: | https://app.any.run/tasks/bfaa6ccb-e7f2-47a0-87b0-43d3f40bd6aa |
| Verdict: | Malicious activity |
| Threats: | HijackLoader is a modular malware acting as a vehicle for distributing different types of malicious software on compromised systems. It gained prominence during the summer of 2023 and has since been used in multiple attacks against organizations from various sectors, including hospitality businesses. |
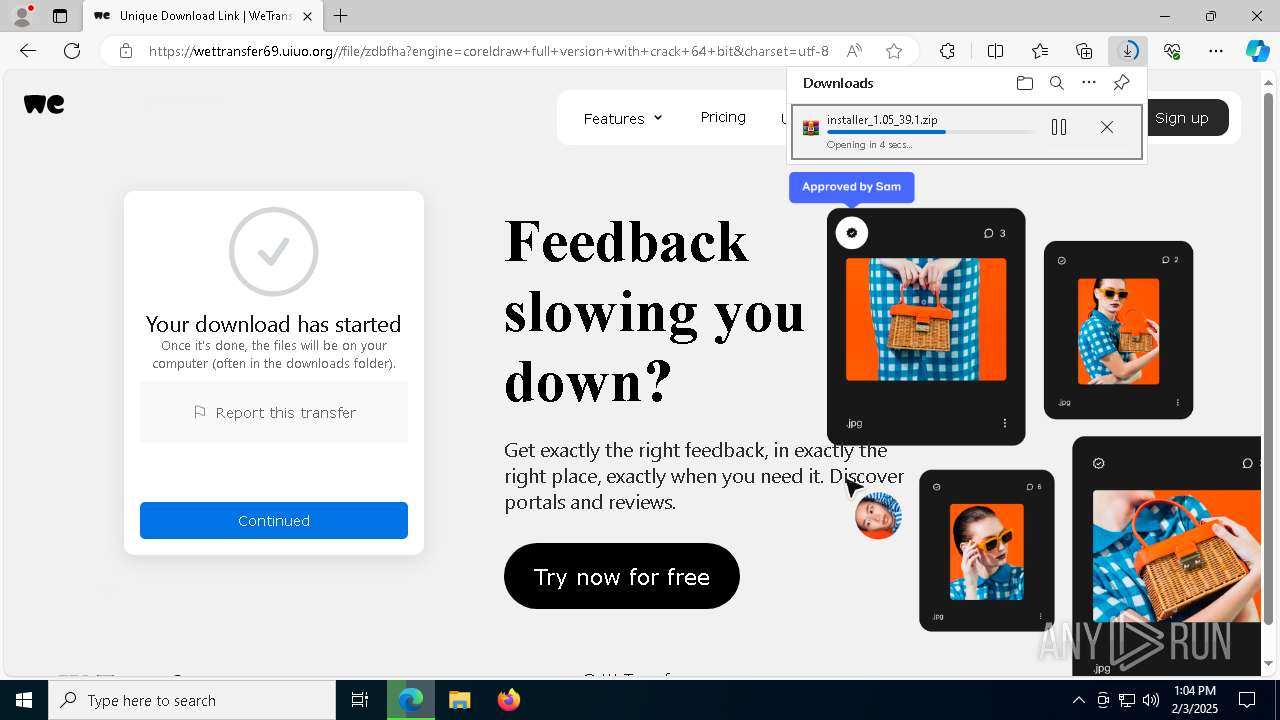
| Analysis date: | February 03, 2025, 13:04:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E6CCD0EEC5E56D003B973AE89FE72A4F |
| SHA1: | FCD093FE5995AAD6E845AD7B75A74DBC1BB751A3 |
| SHA256: | 68CD8A181B512772937120804161A60BCD27762EA4351F33854D3EB5D7E54674 |
| SSDEEP: | 3:N8gixJEcVfO7KZJjKOKG/BUWOMXWL6Z3fr3:2g+EcVfnJ2c/BUWOR23fD |
MALICIOUS
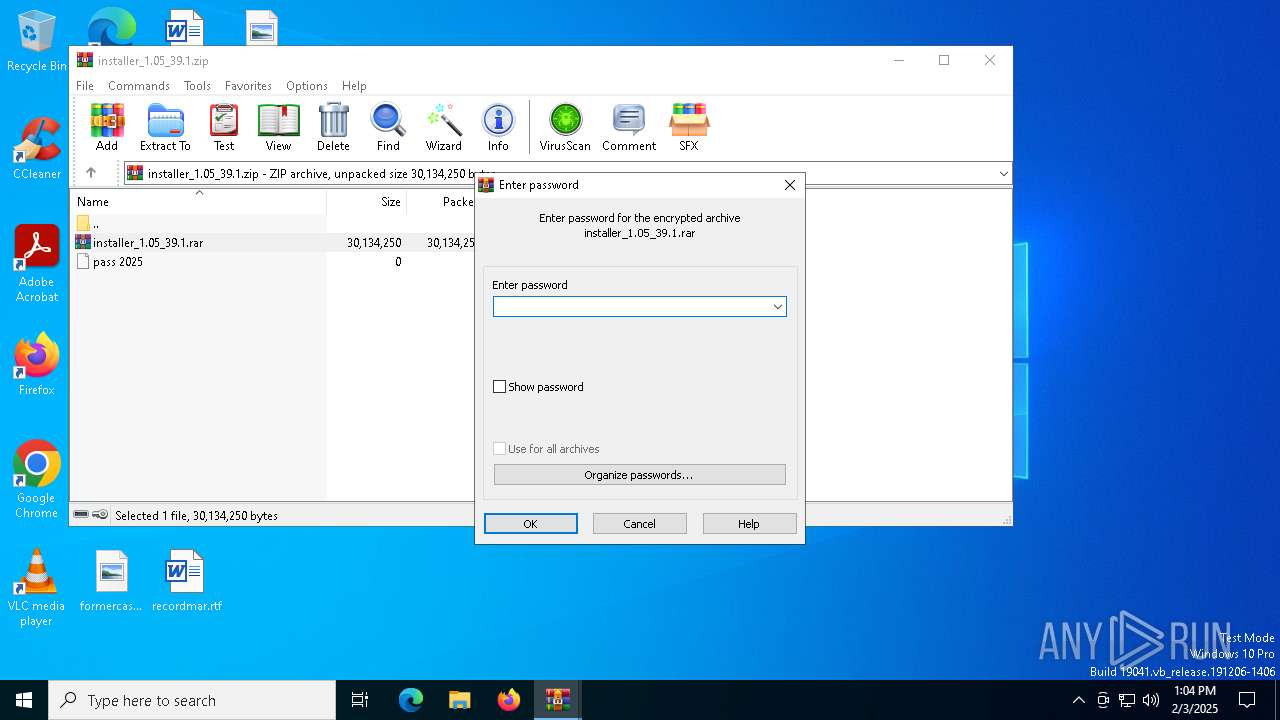
AutoIt loader has been detected (YARA)
- Thou.com (PID: 1512)
Steals credentials from Web Browsers
- Thou.com (PID: 1512)
Actions looks like stealing of personal data
- Thou.com (PID: 1512)
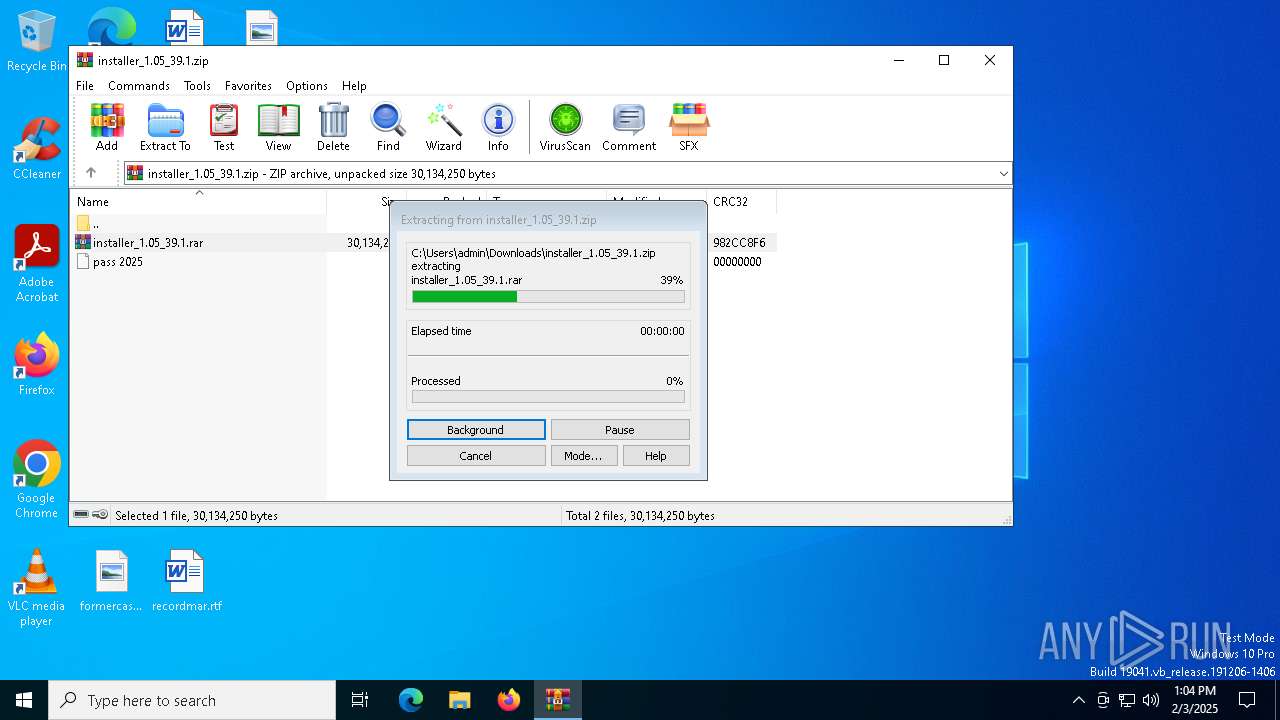
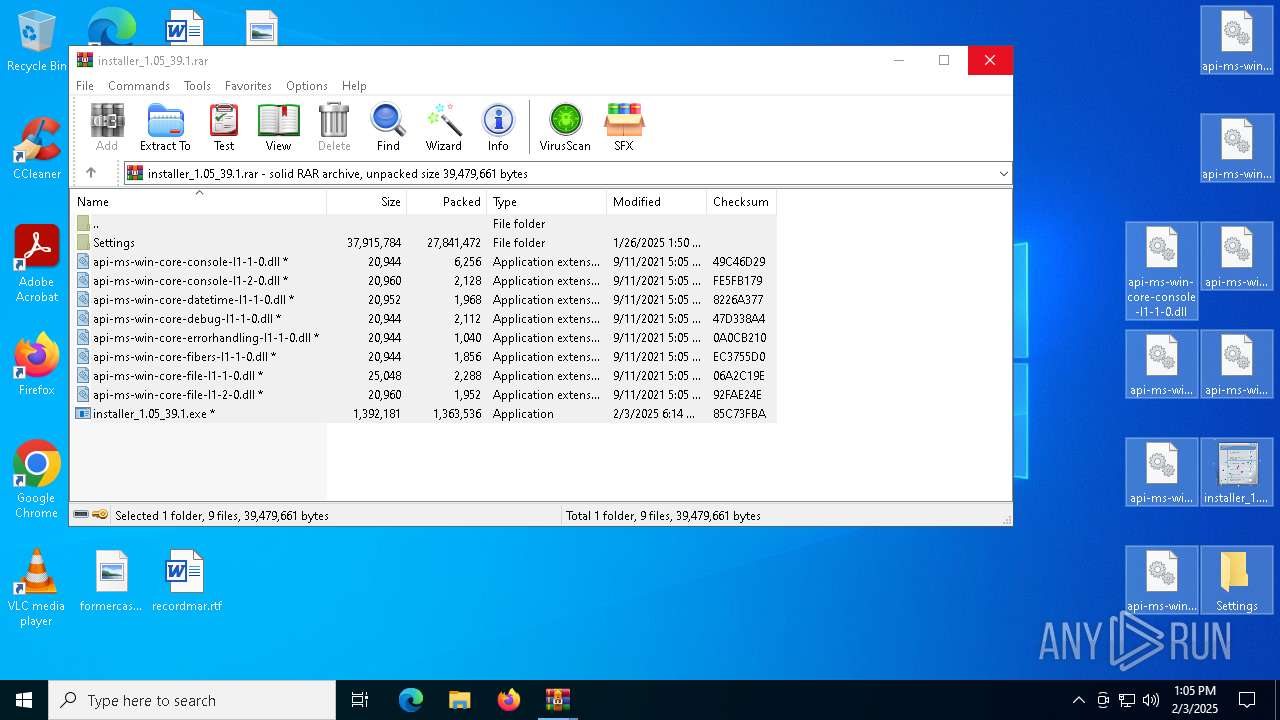
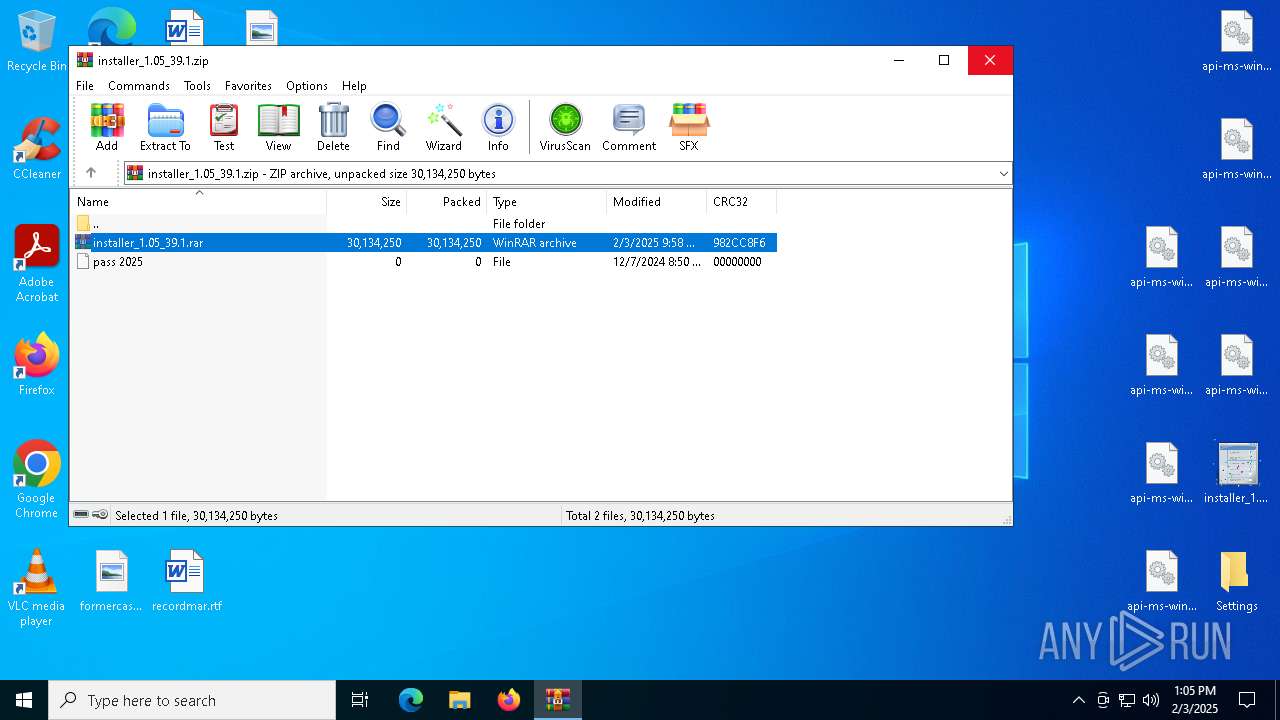
Executing a file with an untrusted certificate
- installer_1.05_39.1.exe (PID: 7064)
HIJACKLOADER has been detected (YARA)
- iTunesHelper.exe (PID: 640)
- iTunesHelper.exe (PID: 8040)
- iTunesHelper.exe (PID: 6712)
Known privilege escalation attack
- dllhost.exe (PID: 1356)
SUSPICIOUS
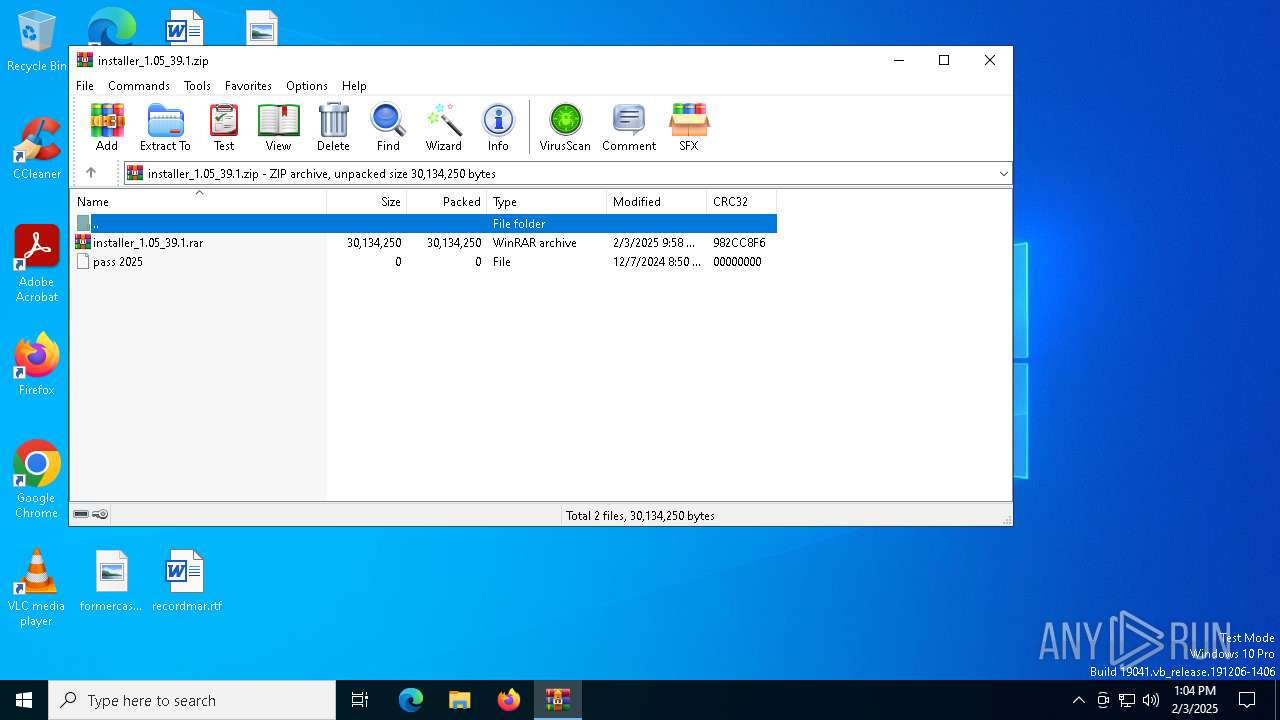
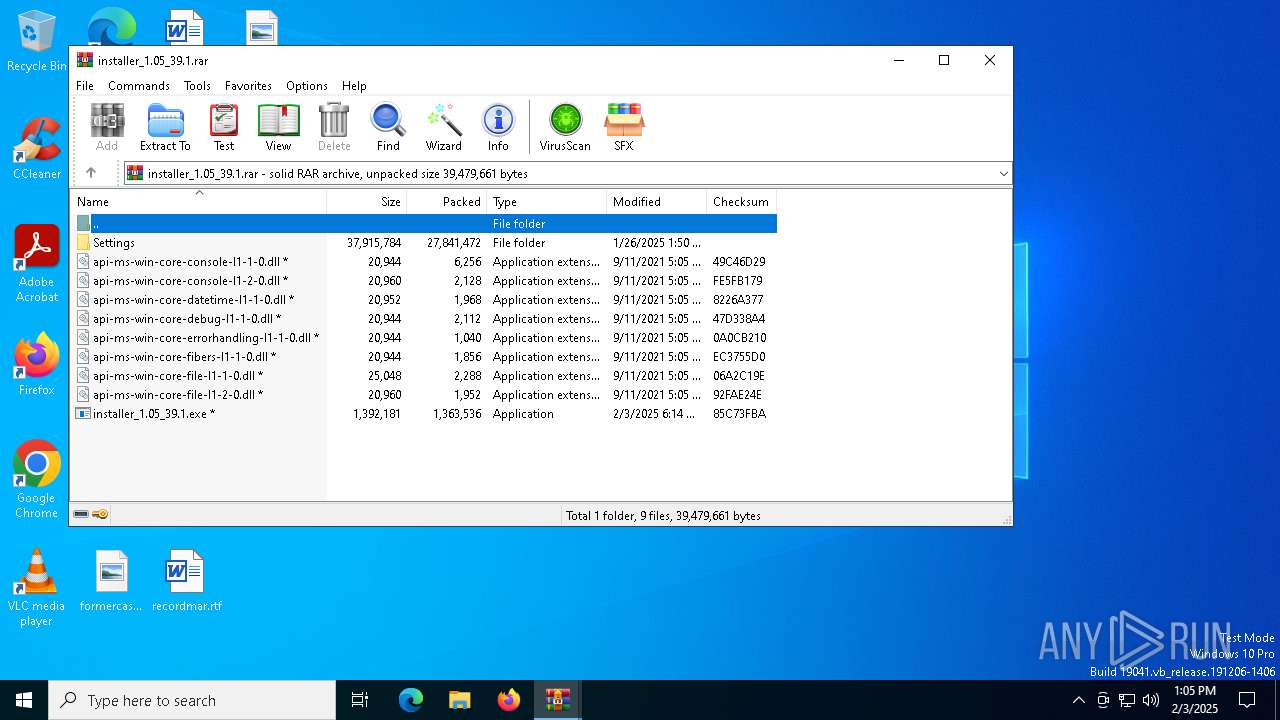
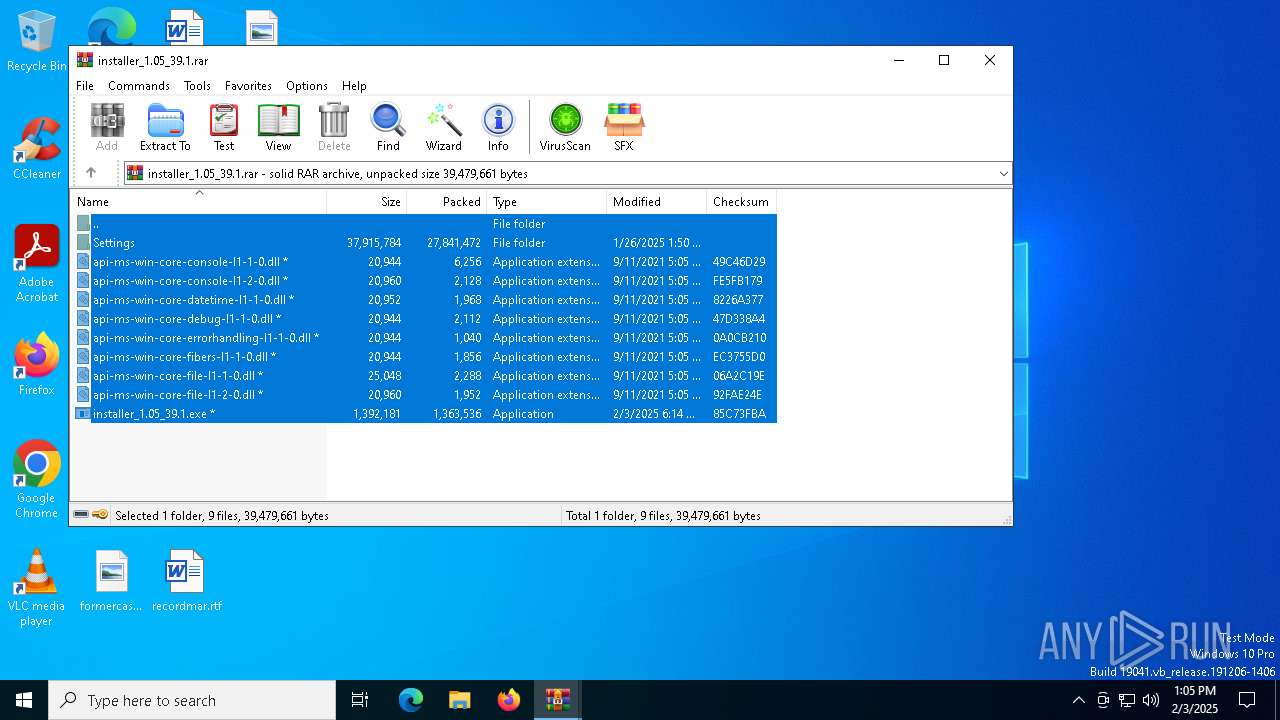
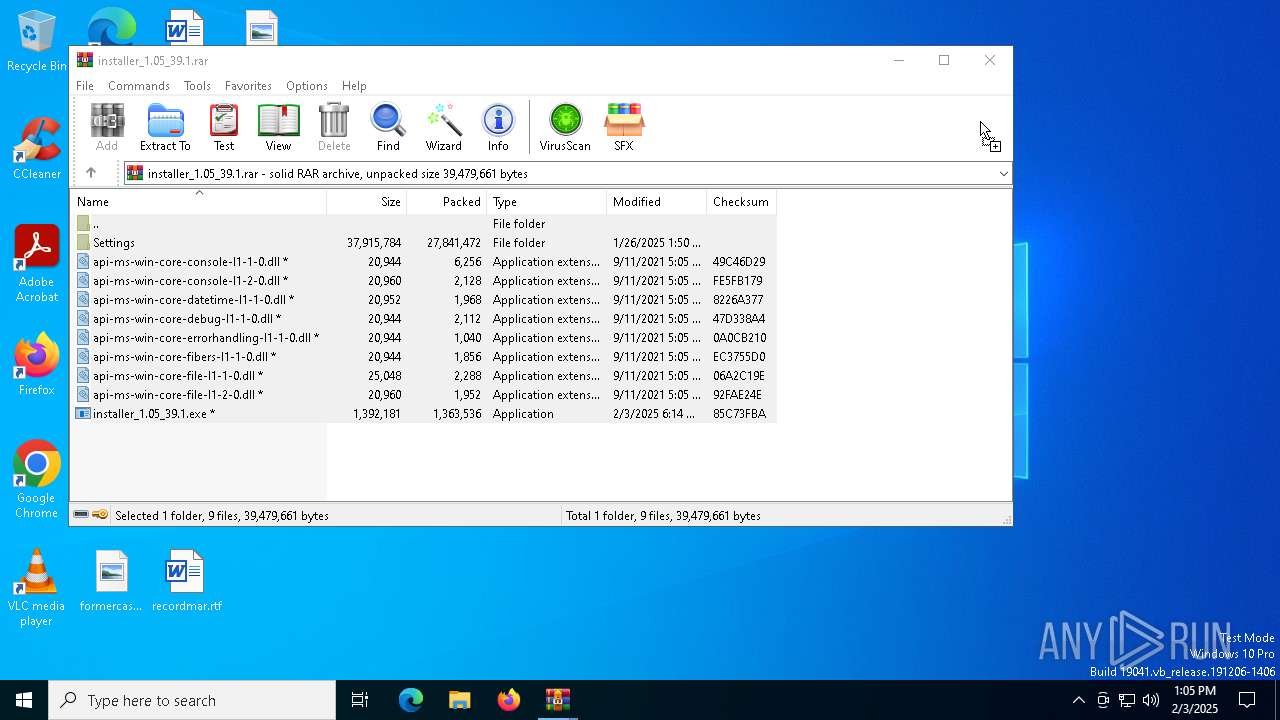
Application launched itself
- WinRAR.exe (PID: 6352)
- cmd.exe (PID: 1020)
Process drops legitimate windows executable
- WinRAR.exe (PID: 4264)
- Thou.com (PID: 1512)
- iTunesHelper.exe (PID: 640)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6352)
- installer_1.05_39.1.exe (PID: 7064)
- Thou.com (PID: 1512)
Starts CMD.EXE for commands execution
- installer_1.05_39.1.exe (PID: 7064)
- cmd.exe (PID: 1020)
Get information on the list of running processes
- cmd.exe (PID: 1020)
The executable file from the user directory is run by the CMD process
- Thou.com (PID: 1512)
Starts the AutoIt3 executable file
- cmd.exe (PID: 1020)
Starts application with an unusual extension
- cmd.exe (PID: 1020)
- iTunesHelper.exe (PID: 8040)
- iTunesHelper.exe (PID: 6712)
There is functionality for taking screenshot (YARA)
- Thou.com (PID: 1512)
- updater.exe (PID: 5964)
Checks Windows Trust Settings
- Thou.com (PID: 1512)
MS Edge headless start
- msedge.exe (PID: 5008)
- msedge.exe (PID: 7368)
The process checks if it is being run in the virtual environment
- Thou.com (PID: 1512)
The process drops C-runtime libraries
- Thou.com (PID: 1512)
- iTunesHelper.exe (PID: 640)
Executing commands from ".cmd" file
- installer_1.05_39.1.exe (PID: 7064)
Executable content was dropped or overwritten
- Thou.com (PID: 1512)
- iTunesHelper.exe (PID: 640)
- more.com (PID: 6828)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1020)
Connects to unusual port
- updater.exe (PID: 5964)
Starts itself from another location
- iTunesHelper.exe (PID: 640)
INFO
Reads Environment values
- identity_helper.exe (PID: 8056)
- identity_helper.exe (PID: 848)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6460)
Application launched itself
- msedge.exe (PID: 6460)
- msedge.exe (PID: 7560)
- chrome.exe (PID: 6612)
- msedge.exe (PID: 7368)
Reads the computer name
- identity_helper.exe (PID: 848)
- identity_helper.exe (PID: 8056)
- installer_1.05_39.1.exe (PID: 7064)
- extrac32.exe (PID: 7288)
- Thou.com (PID: 1512)
- iTunesHelper.exe (PID: 640)
- iTunesHelper.exe (PID: 8040)
- more.com (PID: 5980)
- iTunesHelper.exe (PID: 6712)
- updater.exe (PID: 5964)
- more.com (PID: 6828)
The sample compiled with english language support
- WinRAR.exe (PID: 4264)
- Thou.com (PID: 1512)
- iTunesHelper.exe (PID: 640)
- more.com (PID: 6828)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4264)
Process checks computer location settings
- installer_1.05_39.1.exe (PID: 7064)
- Thou.com (PID: 1512)
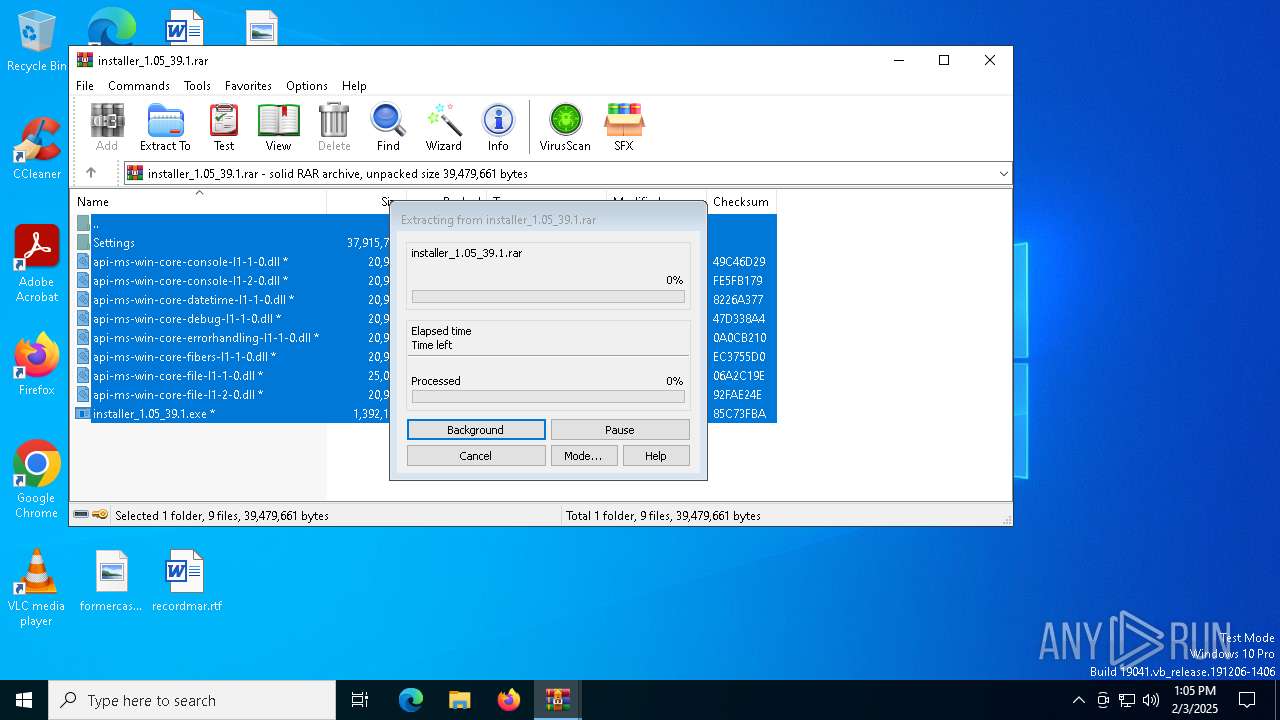
Manual execution by a user
- installer_1.05_39.1.exe (PID: 7064)
Checks supported languages
- identity_helper.exe (PID: 8056)
- extrac32.exe (PID: 7288)
- installer_1.05_39.1.exe (PID: 7064)
- identity_helper.exe (PID: 848)
- Thou.com (PID: 1512)
- iTunesHelper.exe (PID: 640)
- iTunesHelper.exe (PID: 8040)
- more.com (PID: 5980)
- iTunesHelper.exe (PID: 6712)
- more.com (PID: 6828)
- updater.exe (PID: 5964)
Creates a new folder
- cmd.exe (PID: 7200)
Create files in a temporary directory
- extrac32.exe (PID: 7288)
- installer_1.05_39.1.exe (PID: 7064)
- iTunesHelper.exe (PID: 8040)
- iTunesHelper.exe (PID: 6712)
- more.com (PID: 6828)
Reads mouse settings
- Thou.com (PID: 1512)
Reads the software policy settings
- Thou.com (PID: 1512)
- updater.exe (PID: 5964)
Creates files or folders in the user directory
- Thou.com (PID: 1512)
Checks proxy server information
- Thou.com (PID: 1512)
Creates files in the program directory
- iTunesHelper.exe (PID: 640)
Reads the machine GUID from the registry
- more.com (PID: 5980)
- Thou.com (PID: 1512)
- updater.exe (PID: 5964)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 1356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
228
Monitored processes
93
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Users\admin\GPtHd.exe\iTunesHelper.exe" | C:\Users\admin\GPtHd.exe\iTunesHelper.exe | Thou.com | ||||||||||||
User: admin Company: Apple Inc. Integrity Level: MEDIUM Description: iTunesHelper Exit code: 0 Version: 12.12.9.4 Modules
| |||||||||||||||
| 848 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4812 --field-trial-handle=2336,i,16181061236975729198,5032168218324413819,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Windows\System32\cmd.exe" /c copy Organic.mui Organic.mui.cmd & Organic.mui.cmd | C:\Windows\SysWOW64\cmd.exe | — | installer_1.05_39.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | Thou.com T | C:\Users\admin\AppData\Local\Temp\738559\Thou.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 5 Modules
| |||||||||||||||
| 2120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --no-appcompat-clear --mojo-platform-channel-handle=4572 --field-trial-handle=2312,i,5720961193012485142,2892057751467999242,262144 --disable-features=PaintHolding --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2572 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5304 --field-trial-handle=2336,i,16181061236975729198,5032168218324413819,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 550
Read events
21 461
Write events
89
Delete events
0
Modification events
| (PID) Process: | (6148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (6148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (6148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
71
Suspicious files
233
Text files
135
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135c0e.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135c0e.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135c0e.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135c0e.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135c1d.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
124
DNS requests
139
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
244 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6336 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7228 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1512 | Thou.com | GET | 200 | 216.58.206.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
244 | svchost.exe | GET | 200 | 95.101.78.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7228 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1512 | Thou.com | GET | 200 | 142.250.185.67:80 | http://o.pki.goog/we2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEQCb8PdjQeQ8lhCk5l9eniFq | unknown | — | — | whitelisted |
1512 | Thou.com | GET | 200 | 216.58.206.67:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
244 | svchost.exe | 95.101.78.42:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
244 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6460 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6712 | msedge.exe | 188.114.97.3:443 | h94af8b5.saferedirect.top | — | — | malicious |
6712 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6712 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
h94af8b5.saferedirect.top |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
go.microsoft.com |
| whitelisted |
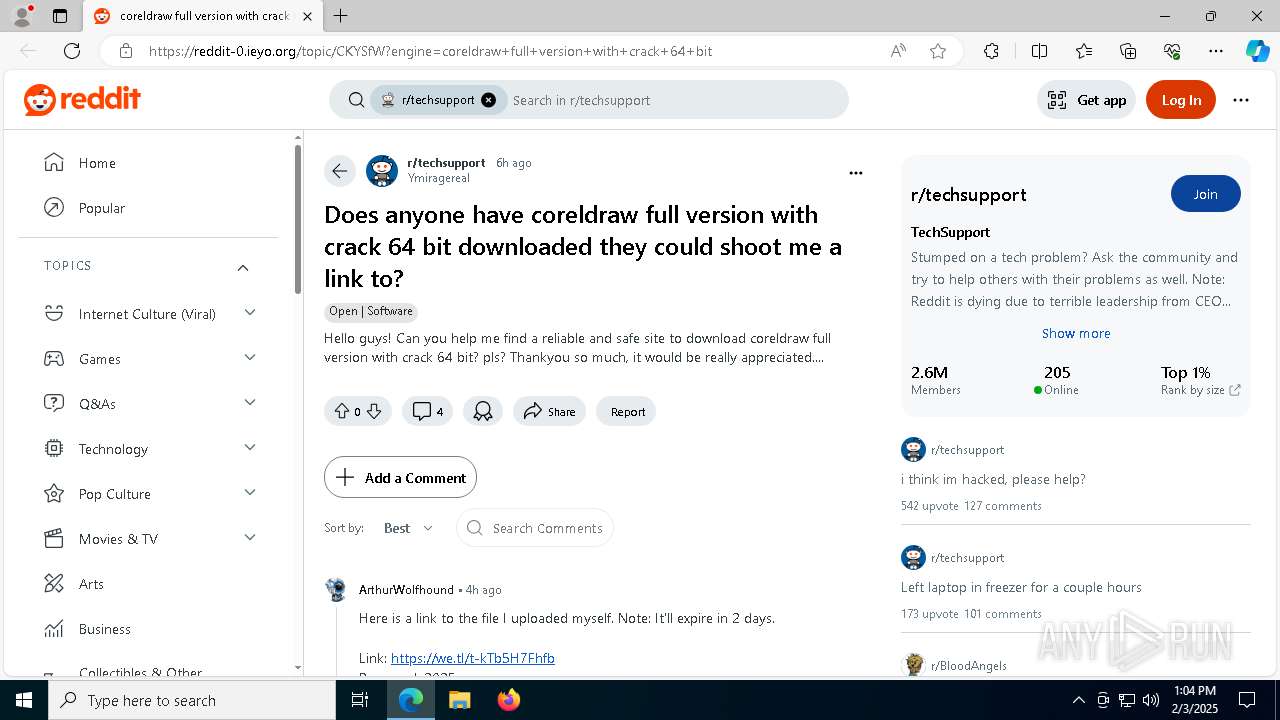
reddit-0.ieyo.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
6712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7372 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
7372 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
7372 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
7372 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
2192 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious domain by CrossDomain ( .servicelandingkaraoke .shop) |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Google\Chrome\User Data directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Microsoft\Edge\User Data directory exists )
|