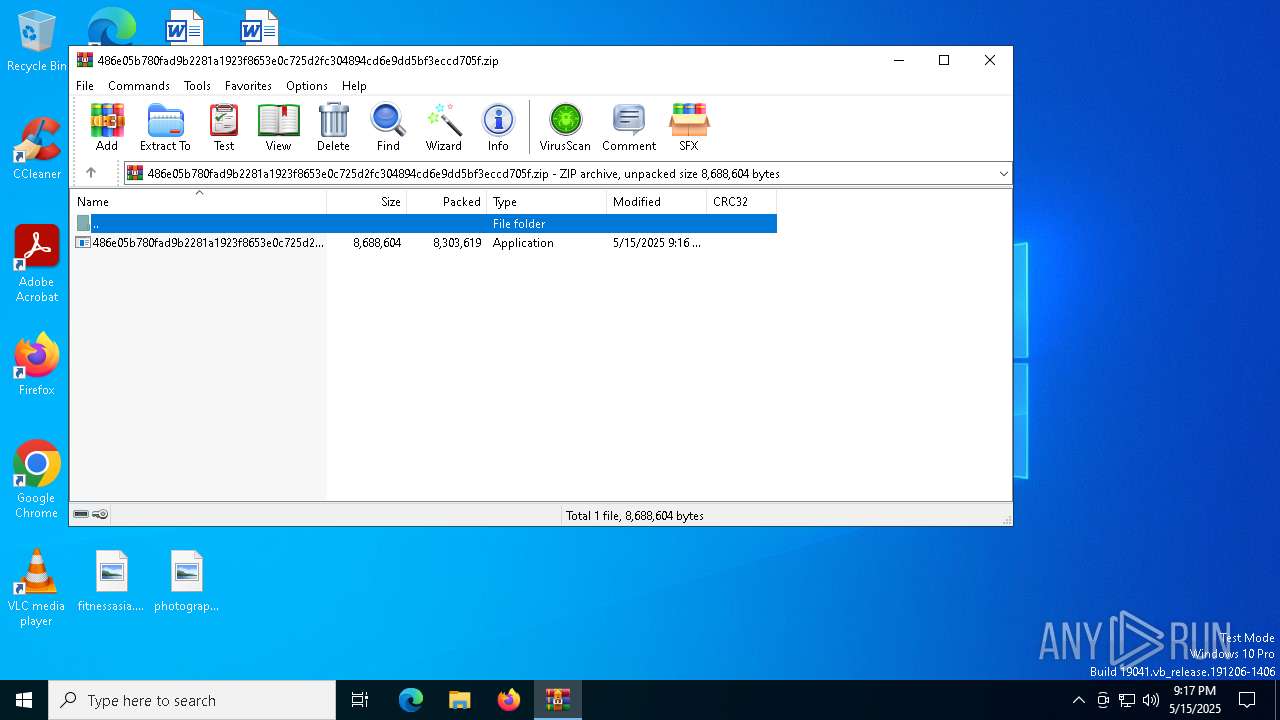
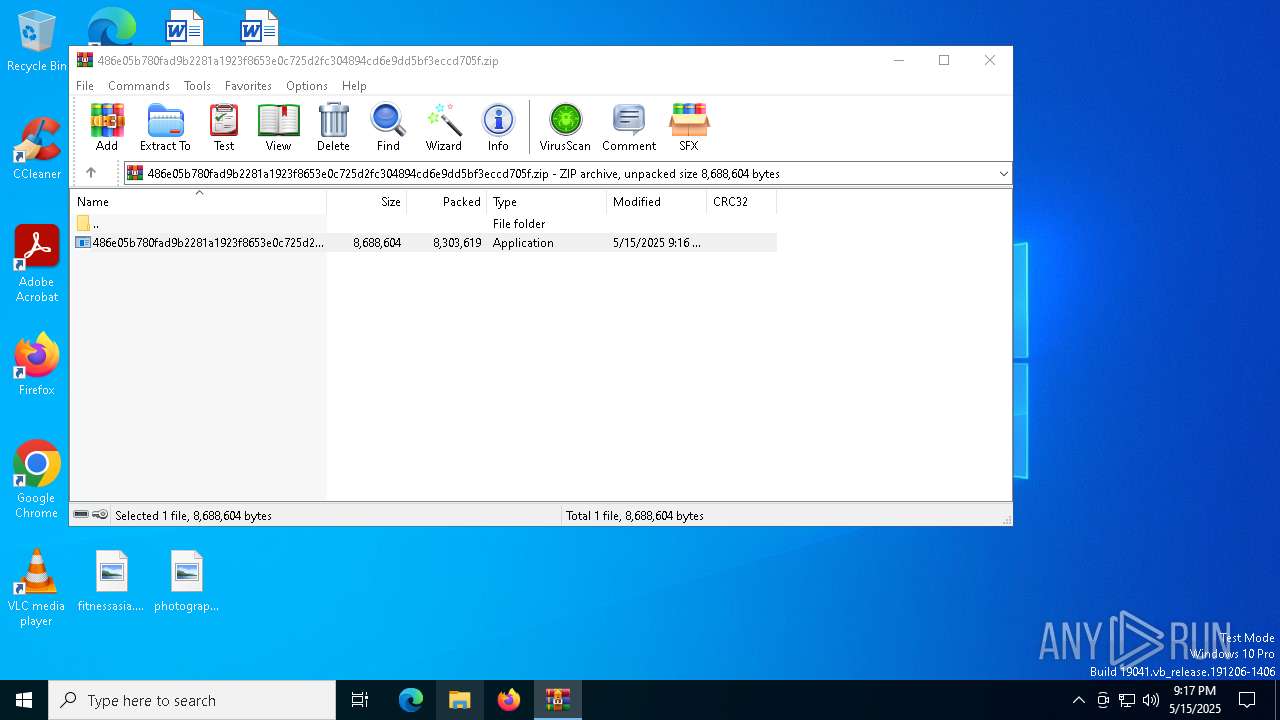
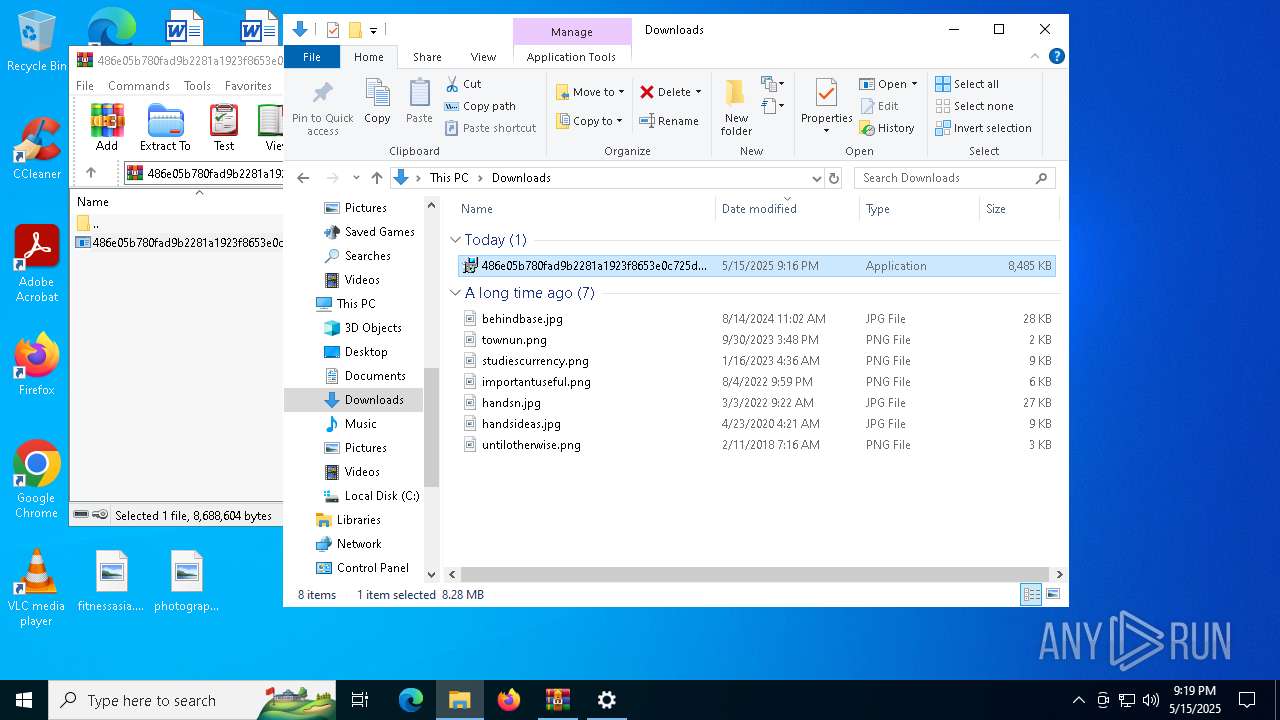
| File name: | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.zip |
| Full analysis: | https://app.any.run/tasks/7eafc382-59db-4f9b-a887-7d05b944c19e |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 15, 2025, 21:16:59 |
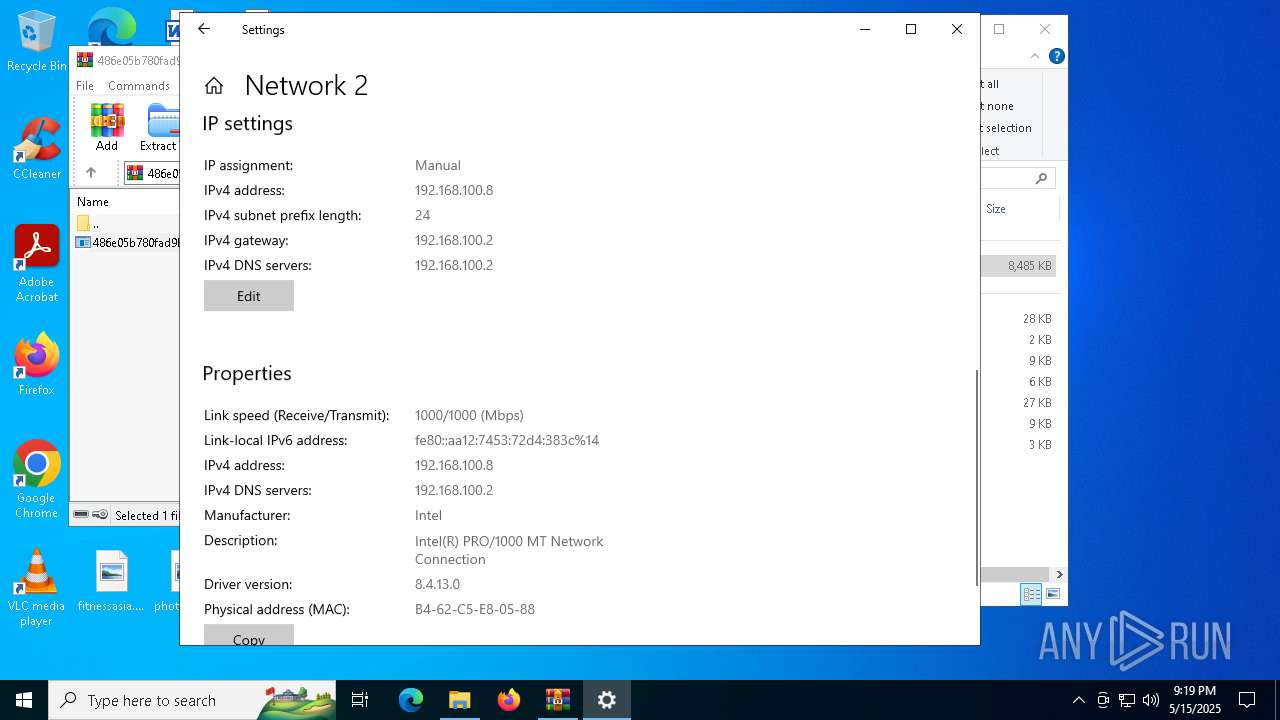
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
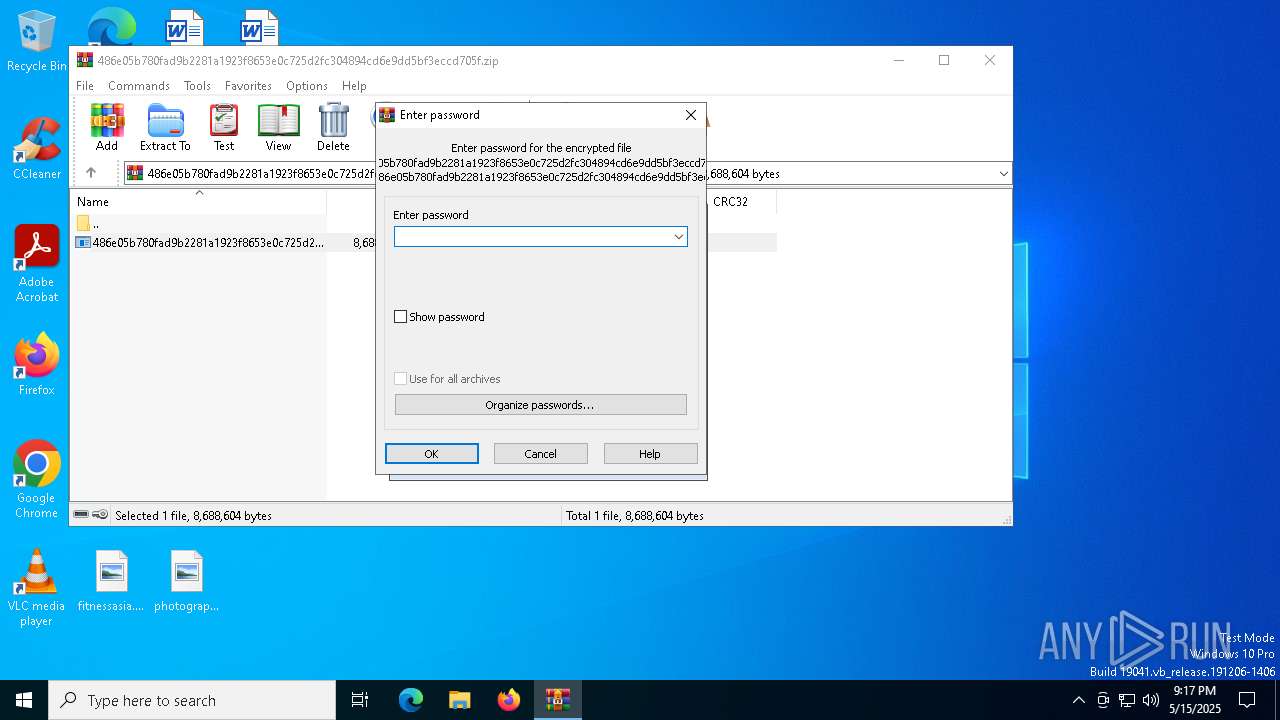
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 0488134831218E62FB111FAA78550640 |
| SHA1: | 6F022346D7A6C37A595EB1ED5820E886D8EB0092 |
| SHA256: | 684CEB05D00366EF34CFAD3A39E83AA6C72E273263FD8199933AB0621FEDD559 |
| SSDEEP: | 98304:CFeUoVcgznaS3SNx0FKHZCvGGDwAx90sE9vxgTbAmUZhGbm3lQRnzIlQzyg66Yys:A1yBw4p5lNZKiNZA |
MALICIOUS
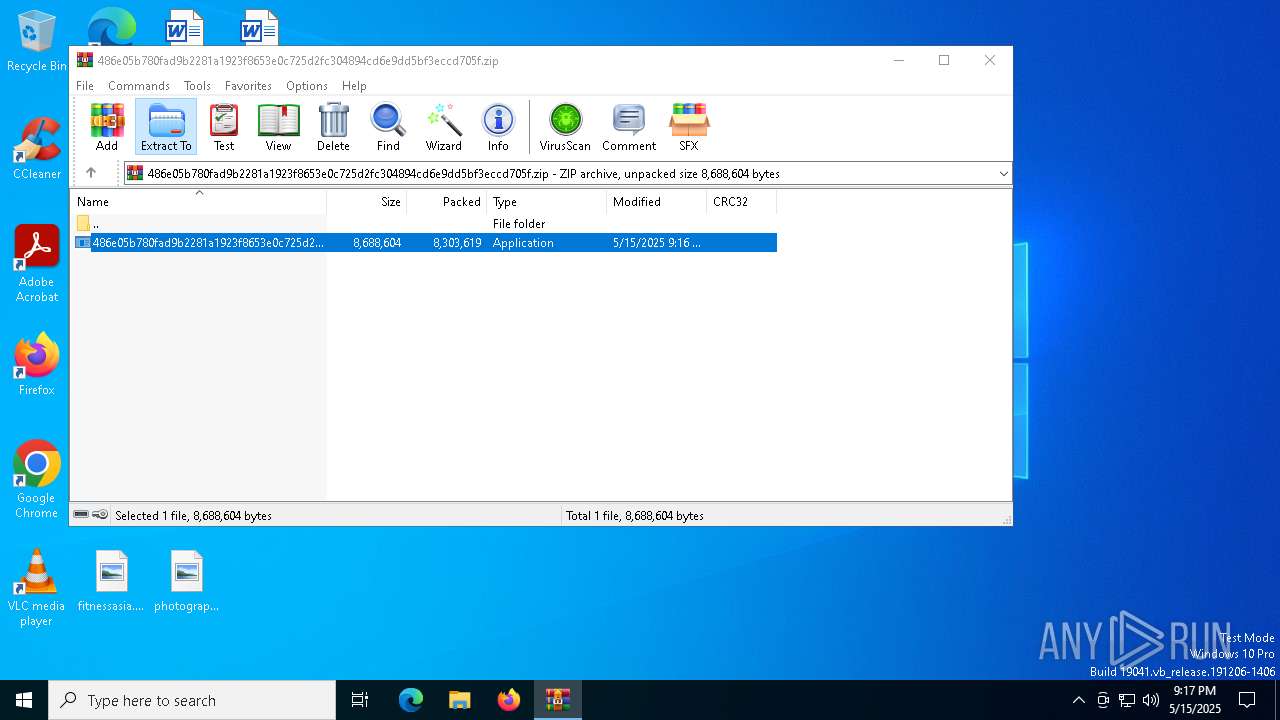
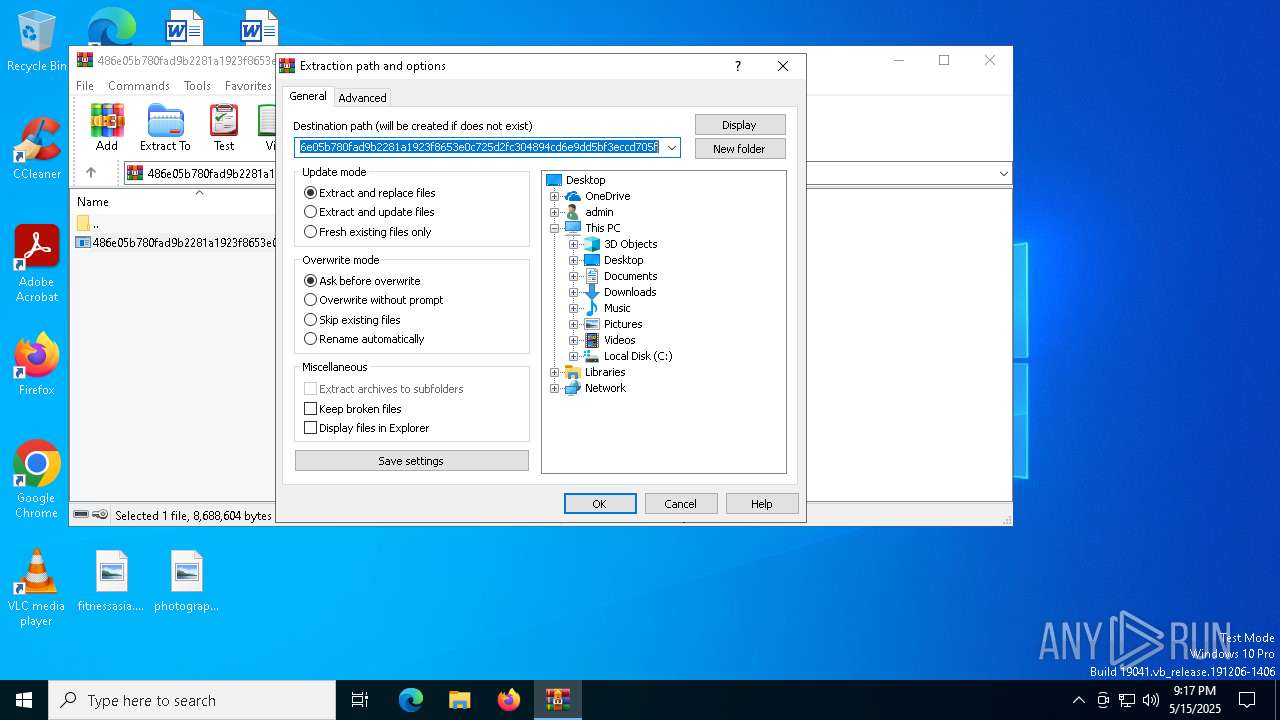
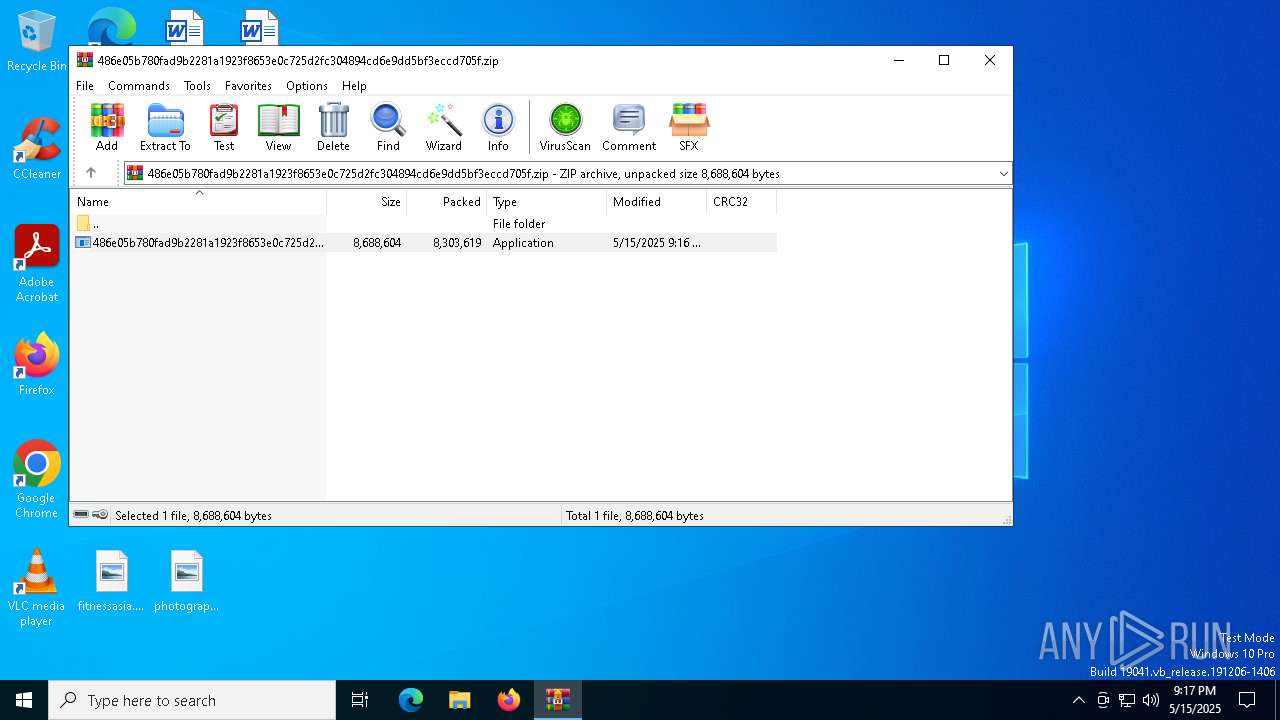
Generic archive extractor
- WinRAR.exe (PID: 780)
Executing a file with an untrusted certificate
- VectorMix32.exe (PID: 7892)
- XPFix.exe (PID: 7924)
HIJACKLOADER has been detected (YARA)
- LabFusion.exe (PID: 7676)
ASYNCRAT has been detected (SURICATA)
- VectorMix32.exe (PID: 7892)
SUSPICIOUS
Starts itself from another location
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7592)
- LabFusion.exe (PID: 7652)
Executable content was dropped or overwritten
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7592)
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7624)
- LabFusion.exe (PID: 7652)
- LabFusion.exe (PID: 7676)
Process drops legitimate windows executable
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7624)
- LabFusion.exe (PID: 7652)
The process drops C-runtime libraries
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7624)
- LabFusion.exe (PID: 7652)
There is functionality for taking screenshot (YARA)
- LabFusion.exe (PID: 7676)
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7624)
Contacting a server suspected of hosting an CnC
- VectorMix32.exe (PID: 7892)
Connects to unusual port
- VectorMix32.exe (PID: 7892)
Possibly patching Antimalware Scan Interface function (YARA)
- VectorMix32.exe (PID: 7892)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 780)
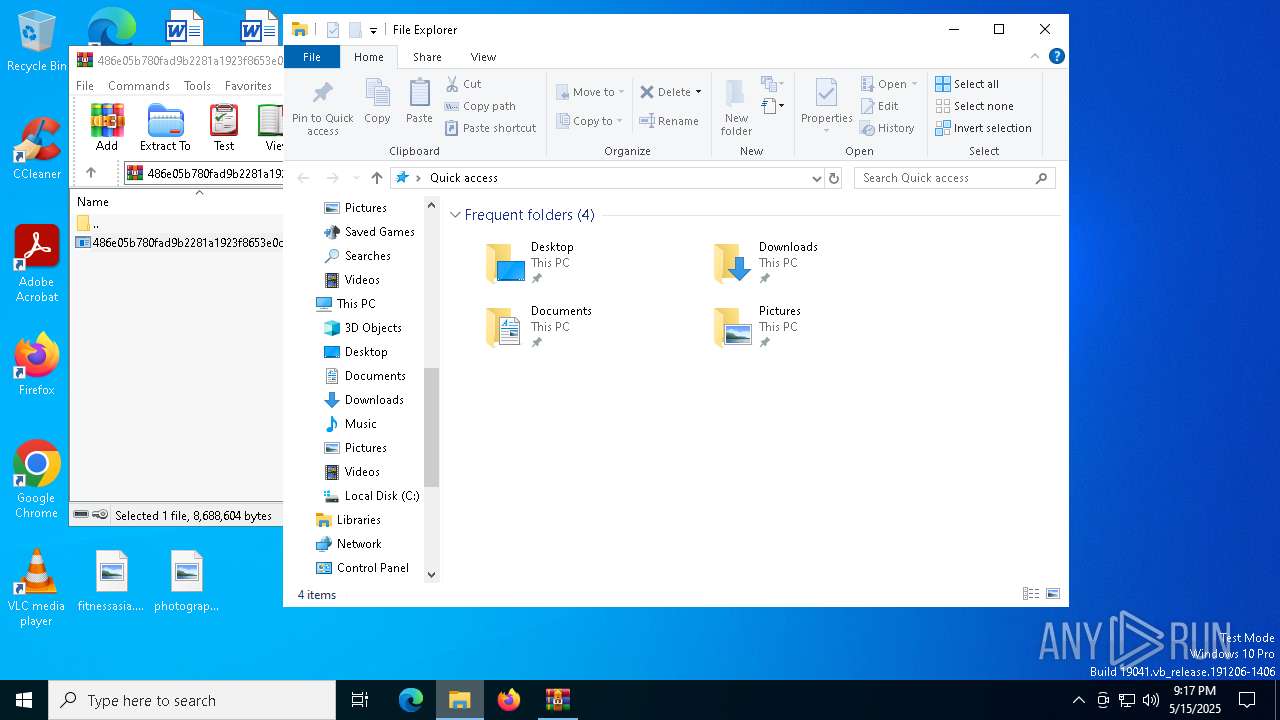
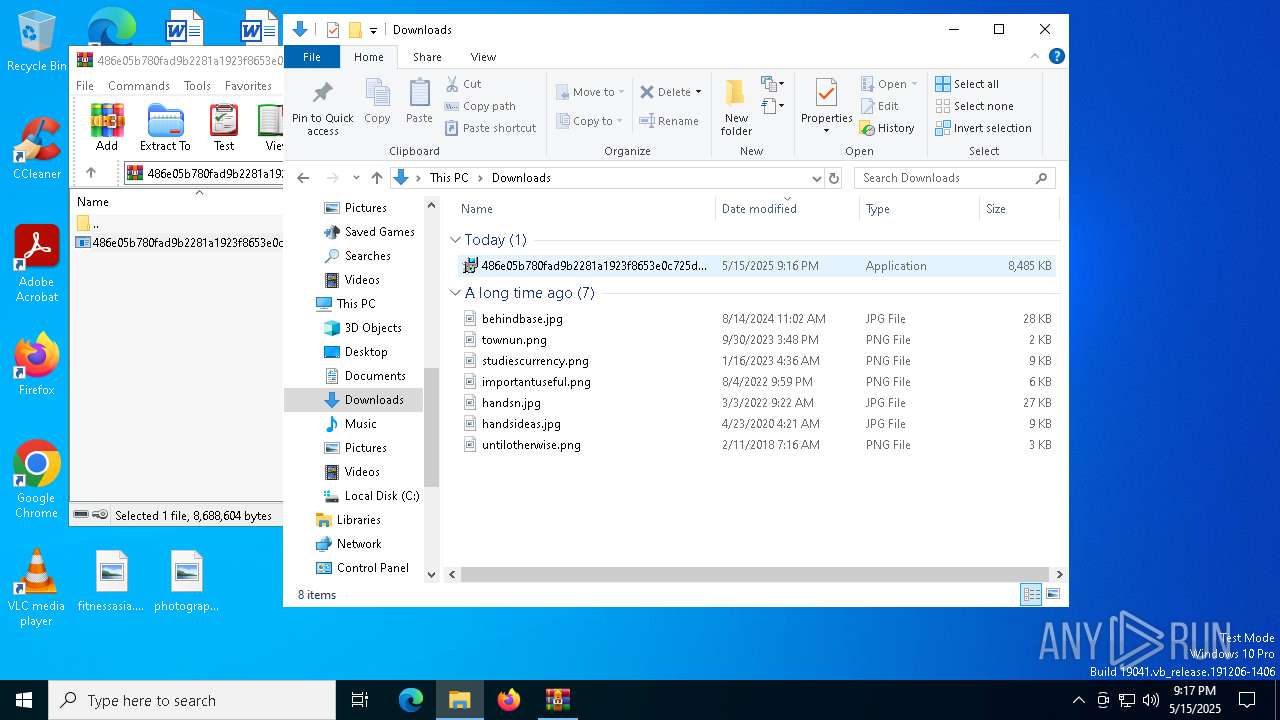
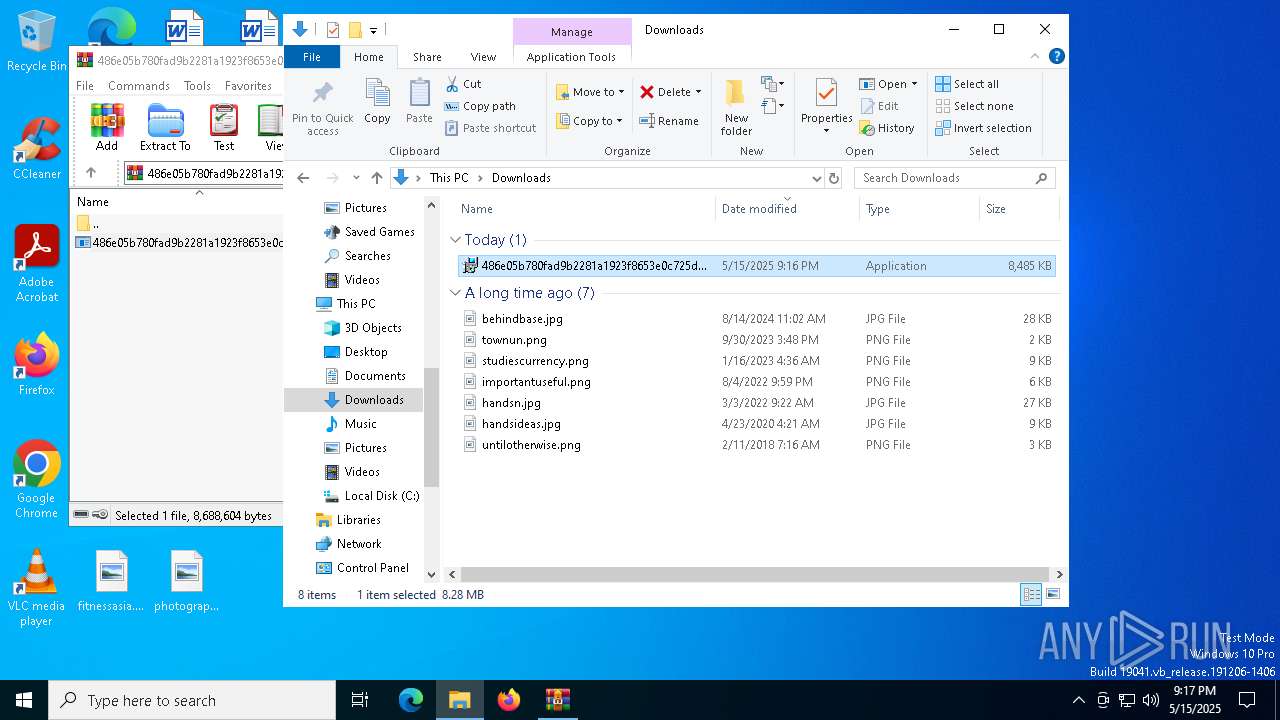
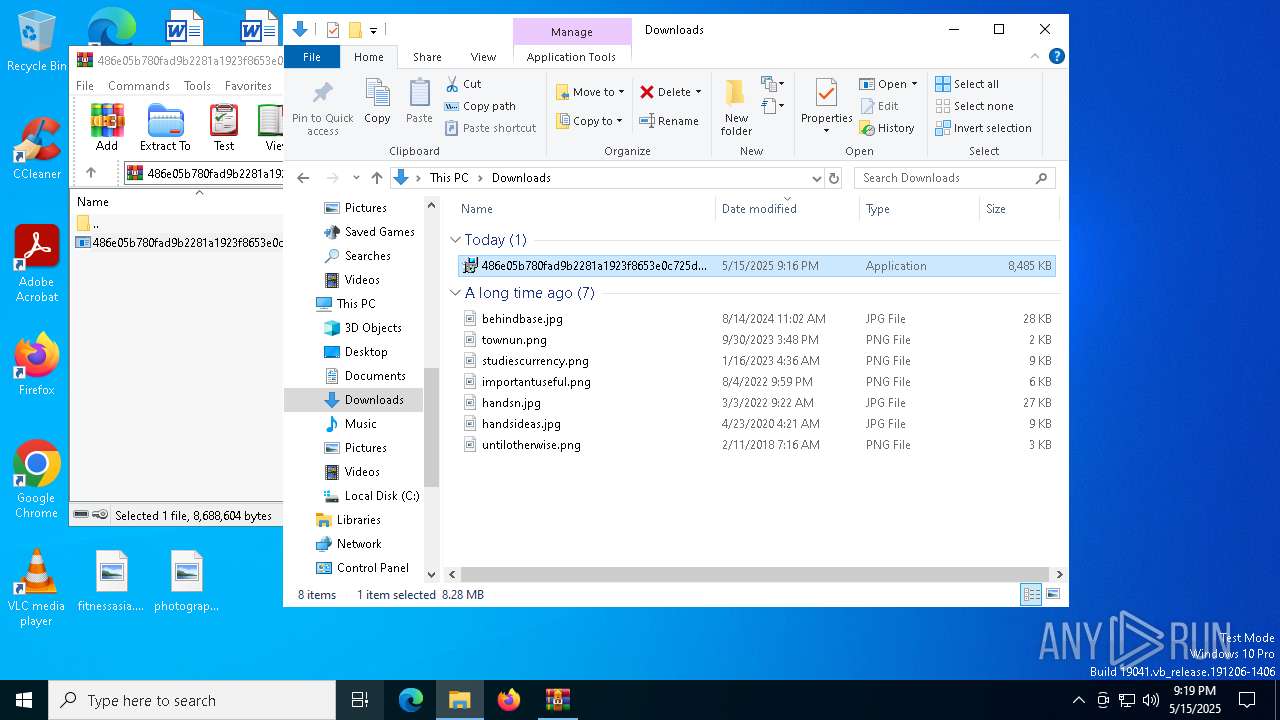
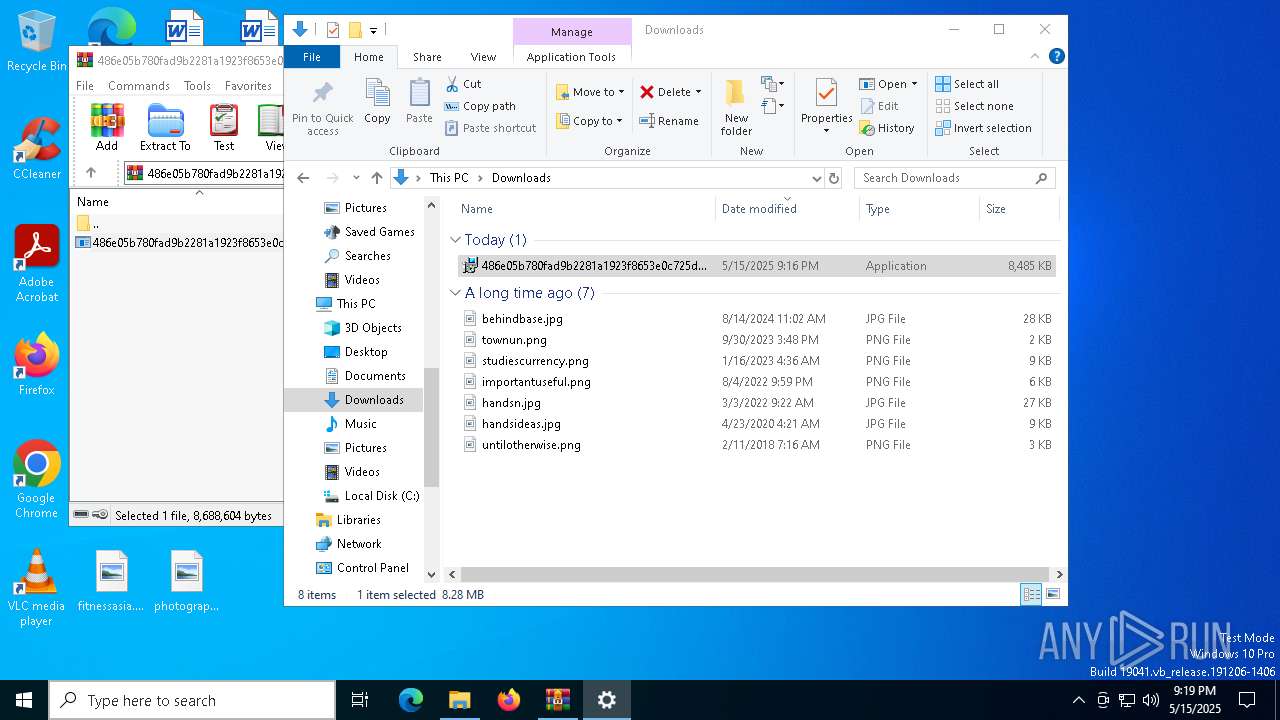
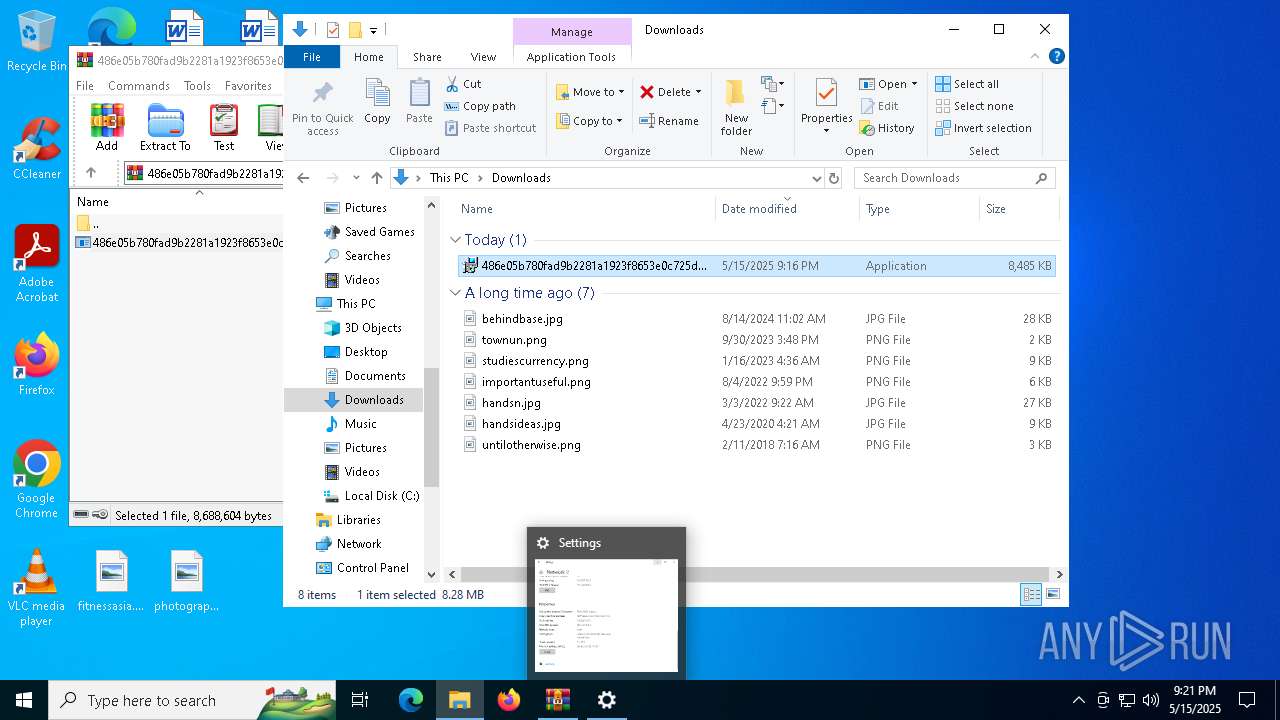
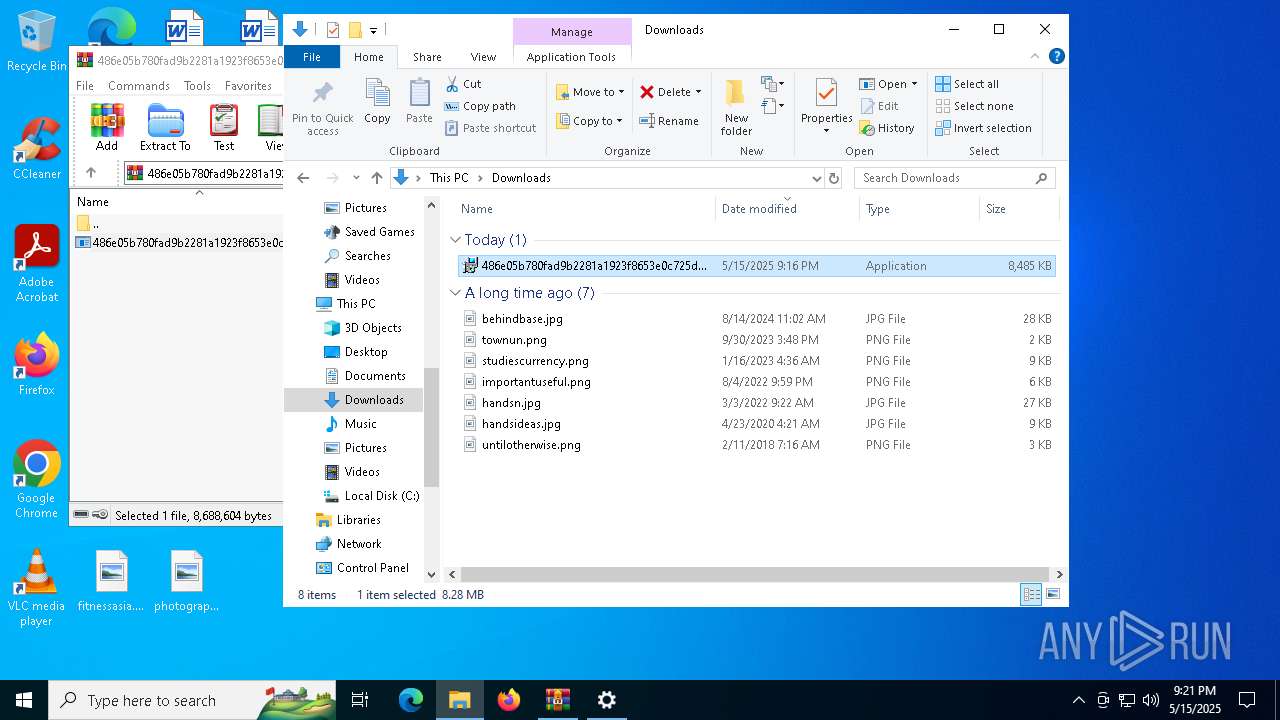
Manual execution by a user
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7592)
Checks supported languages
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7592)
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7624)
- LabFusion.exe (PID: 7652)
- LabFusion.exe (PID: 7676)
- VectorMix32.exe (PID: 7892)
- XPFix.exe (PID: 7924)
Create files in a temporary directory
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7592)
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7624)
- LabFusion.exe (PID: 7676)
- XPFix.exe (PID: 7924)
The sample compiled with english language support
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7592)
- WinRAR.exe (PID: 780)
- 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe (PID: 7624)
- LabFusion.exe (PID: 7652)
- LabFusion.exe (PID: 7676)
Reads the computer name
- LabFusion.exe (PID: 7652)
- LabFusion.exe (PID: 7676)
- VectorMix32.exe (PID: 7892)
- XPFix.exe (PID: 7924)
Creates files in the program directory
- LabFusion.exe (PID: 7652)
Creates files or folders in the user directory
- LabFusion.exe (PID: 7676)
The sample compiled with chinese language support
- LabFusion.exe (PID: 7676)
Reads the machine GUID from the registry
- VectorMix32.exe (PID: 7892)
Reads the software policy settings
- slui.exe (PID: 7308)
- VectorMix32.exe (PID: 7892)
- slui.exe (PID: 896)
Checks proxy server information
- slui.exe (PID: 896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:15 21:16:38 |
| ZipCRC: | 0xe730c389 |
| ZipCompressedSize: | 8303619 |
| ZipUncompressedSize: | 8688604 |
| ZipFileName: | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe |
Total processes
148
Monitored processes
12
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 896 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7272 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7308 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7548 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7592 | "C:\Users\admin\Downloads\486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe" | C:\Users\admin\Downloads\486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | explorer.exe | ||||||||||||
User: admin Company: Reclaim Integrity Level: MEDIUM Description: Flagship Exit code: 0 Version: 3.6.1.0 Modules
| |||||||||||||||
| 7624 | "C:\Users\admin\AppData\Local\Temp\{F2B180AA-CD77-4A5B-B5AC-12E1F7631E91}\.cr\486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe" -burn.clean.room="C:\Users\admin\Downloads\486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe" -burn.filehandle.attached=676 -burn.filehandle.self=672 | C:\Users\admin\AppData\Local\Temp\{F2B180AA-CD77-4A5B-B5AC-12E1F7631E91}\.cr\486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | ||||||||||||
User: admin Company: Reclaim Integrity Level: MEDIUM Description: Flagship Exit code: 0 Version: 3.6.1.0 Modules
| |||||||||||||||
| 7652 | C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.ba\LabFusion.exe | C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.ba\LabFusion.exe | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | ||||||||||||
User: admin Company: AnyMP4 Integrity Level: MEDIUM Description: AnyMP4 Blu-ray Player Exit code: 0 Version: 6.5.68.144795 Modules
| |||||||||||||||
| 7676 | C:\ProgramData\writerdebug\LabFusion.exe | C:\ProgramData\writerdebug\LabFusion.exe | LabFusion.exe | ||||||||||||
User: admin Company: AnyMP4 Integrity Level: MEDIUM Description: AnyMP4 Blu-ray Player Exit code: 0 Version: 6.5.68.144795 Modules
| |||||||||||||||
Total events
7 592
Read events
7 566
Write events
13
Delete events
13
Modification events
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.zip | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
17
Suspicious files
8
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 780 | WinRAR.exe | C:\Users\admin\Downloads\486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | executable | |
MD5:DCC9A4B03E126F3205E8596D4F93B4F3 | SHA256:486E05B780FAD9B2281A1923F8653E0C725D2FC304894CD6E9DD5BF3ECCD705F | |||
| 7592 | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | C:\Users\admin\AppData\Local\Temp\{F2B180AA-CD77-4A5B-B5AC-12E1F7631E91}\.cr\486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | executable | |
MD5:2F545CC6BB61542C1A25608A5B7E53A6 | SHA256:BFF7030495139A59018E88811DE6EF81582A4D6475C0997F21F13BAFCBCC8A29 | |||
| 7652 | LabFusion.exe | C:\ProgramData\writerdebug\LabFusion.exe | executable | |
MD5:EF65CFADFC4B4914A11ACDD61714C6EB | SHA256:8470C56B9B9417E722AD3F0A587CB0317CE79A03180DF6FCED8207C2F69D9201 | |||
| 7624 | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.ba\msvcr120.dll | executable | |
MD5:AEB29CCC27E16C4FD223A00189B44524 | SHA256:D28C7AB34842B6149609BD4E6B566DDAB8B891F0D5062480A253EF20A6A2CAAA | |||
| 7624 | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.ba\msvcp120.dll | executable | |
MD5:EDEF53778EAAFE476EE523BE5C2AB67F | SHA256:92FAEDD18A29E1BD2DD27A1D805EA5AA3E73B954A625AF45A74F49D49506D20F | |||
| 7624 | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.ba\LabFusion.exe | executable | |
MD5:EF65CFADFC4B4914A11ACDD61714C6EB | SHA256:8470C56B9B9417E722AD3F0A587CB0317CE79A03180DF6FCED8207C2F69D9201 | |||
| 7676 | LabFusion.exe | C:\Users\admin\AppData\Local\Temp\F0621AF.tmp | — | |
MD5:— | SHA256:— | |||
| 7624 | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.ba\BootstrapperApplicationData.xml | xml | |
MD5:311BCFCF57783A6300AA958D678FA505 | SHA256:F2B2BEA866DAB4430E55C2884217DD2EA1926575B454F79EDB7DA228B3D8D381 | |||
| 7624 | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.ba\Qt5Gui.dll | executable | |
MD5:72AC63E9E9F015D6471DDE58297A4FC6 | SHA256:6B8A49B6B37D69213762C8F2C8A9970014364F4055F08A850D27C0343FBE00DE | |||
| 7624 | 486e05b780fad9b2281a1923f8653e0c725d2fc304894cd6e9dd5bf3eccd705f.exe | C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.ba\Qt5Core.dll | executable | |
MD5:B03D12CDE3CECC10FA32D74E5B487F5C | SHA256:58222718A1B04AF9F3578713C190EBA513DA81C37FFF9615E2C43228427206E2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
41
DNS requests
22
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7756 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7756 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4156 | SystemSettings.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4156 | SystemSettings.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
2104 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4932 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
delamanodedios7.dynuddns.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.dynuddns .com Domain |
7892 | VectorMix32.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
7892 | VectorMix32.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
7892 | VectorMix32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
7892 | VectorMix32.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |