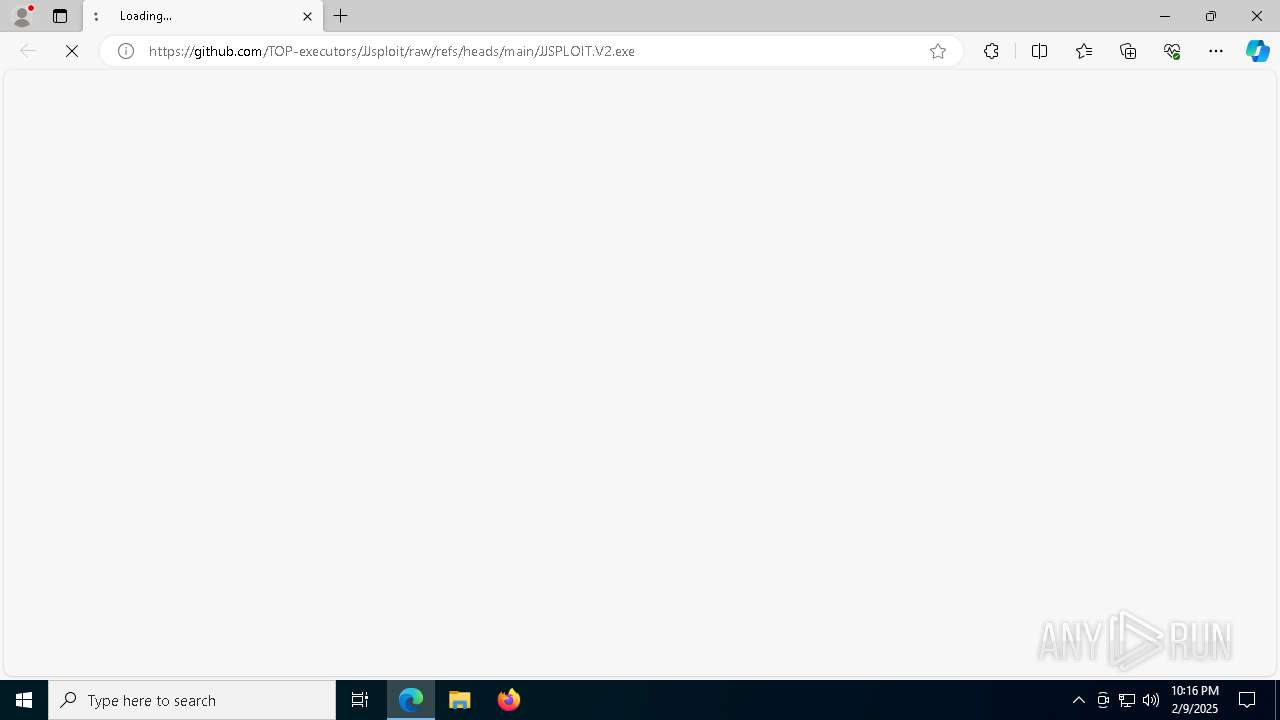
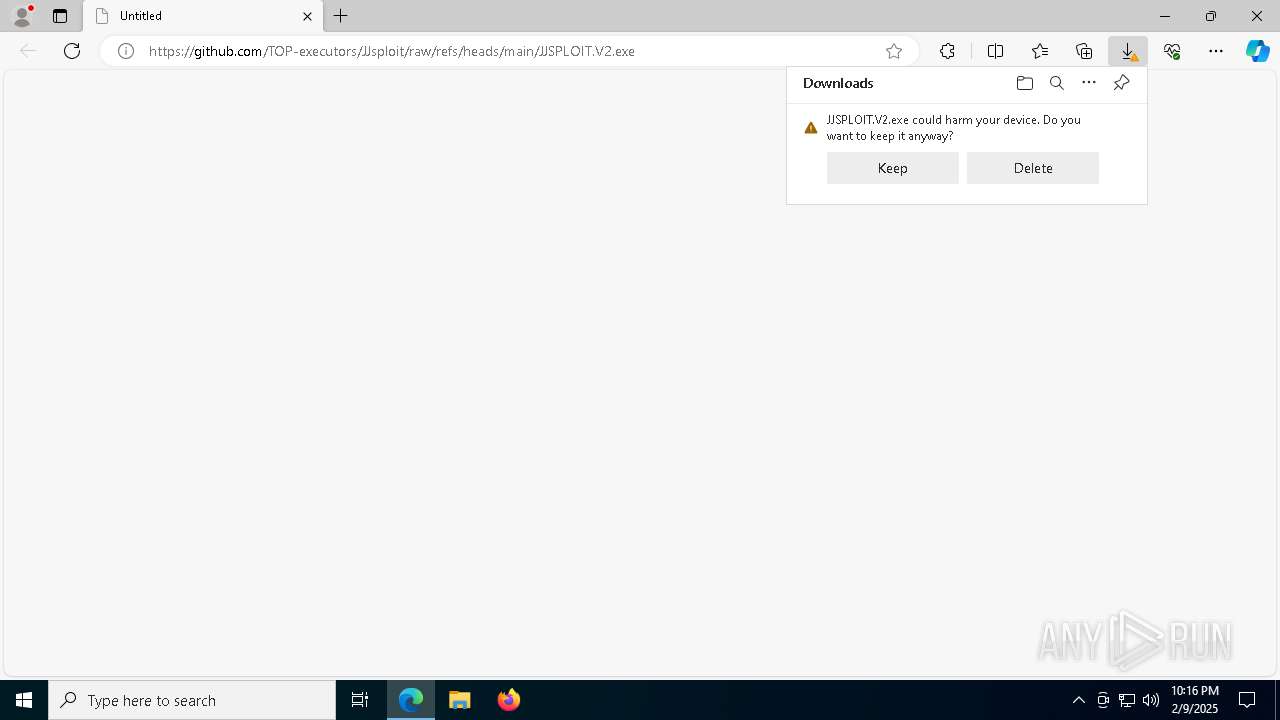
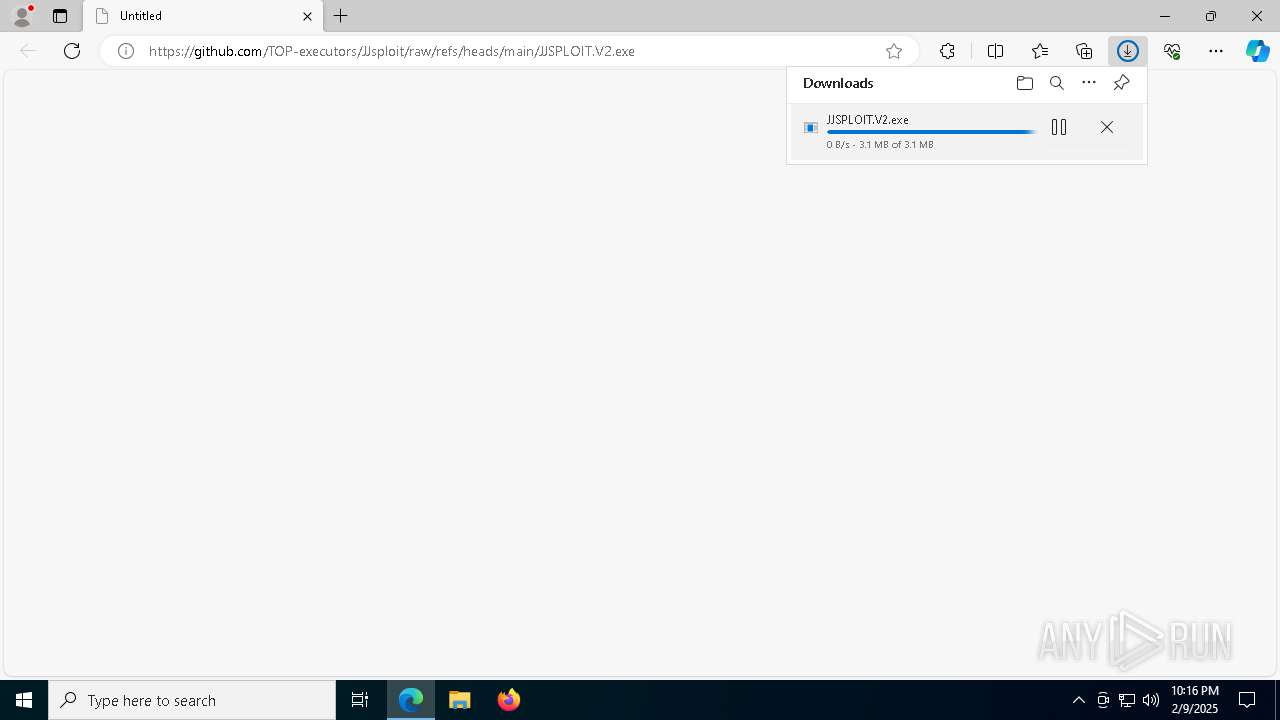
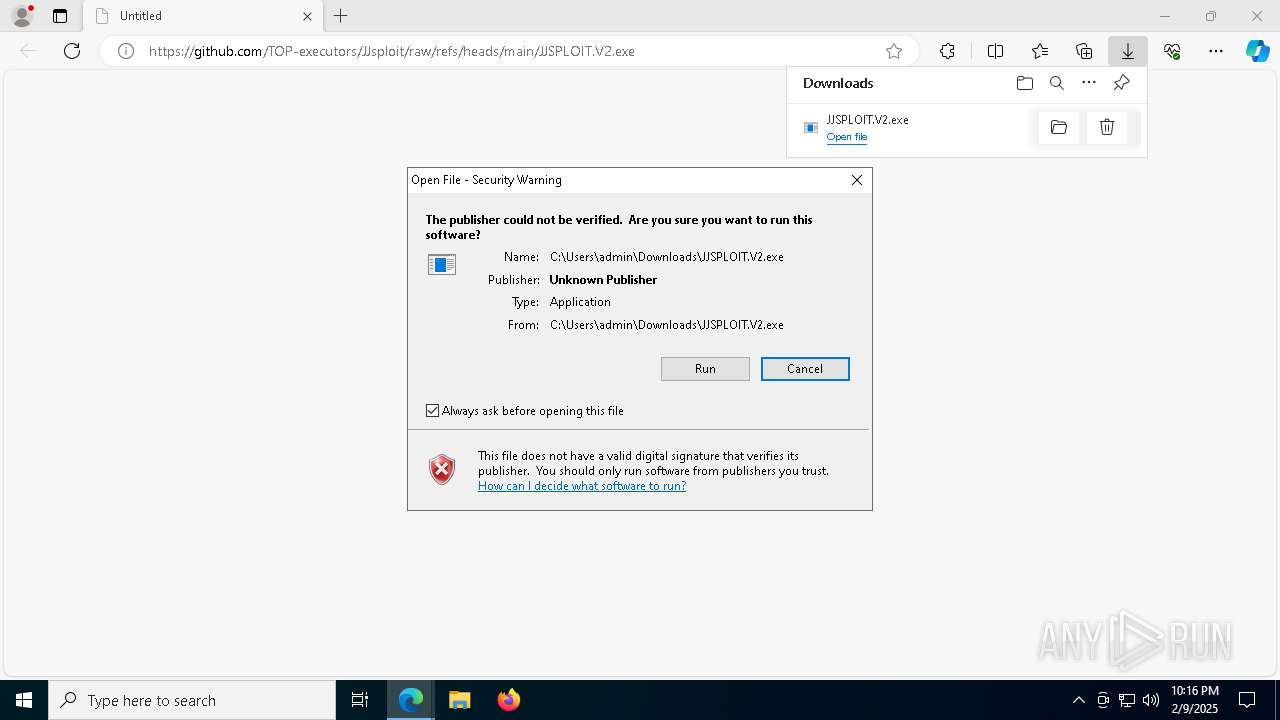
| URL: | https://github.com/TOP-executors/JJsploit/raw/refs/heads/main/JJSPLOIT.V2.exe |
| Full analysis: | https://app.any.run/tasks/3ca06fbd-f689-46eb-8a27-8f917fae0abb |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | February 09, 2025, 22:16:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A0F16BBB3AE4199E81BCC494F007F125 |
| SHA1: | 0A3119D461FBB604FBC8037279C2B788026F0AF6 |
| SHA256: | 683200153A76C28515E4E93B7A99187E87D6D612CC1F1C168938BB749E1DEB39 |
| SSDEEP: | 3:N8tEdDRmaKKLNKiF+A:2uZRJLNKiYA |
MALICIOUS
Changes the autorun value in the registry
- JJSPLOIT.V2.exe (PID: 7788)
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
- windows 3543.exe (PID: 3560)
QUASAR has been detected (YARA)
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
- windows 3543.exe (PID: 3560)
SUSPICIOUS
Cleans NTFS data stream (Zone Identifier)
- JJSPLOIT.V2.exe (PID: 7788)
Probably fake Windows Update file has been dropped
- JJSPLOIT.V2.exe (PID: 7788)
Executable content was dropped or overwritten
- JJSPLOIT.V2.exe (PID: 7788)
Starts itself from another location
- JJSPLOIT.V2.exe (PID: 7788)
Probably fake Windows Update
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
- windows 3543.exe (PID: 3560)
There is functionality for taking screenshot (YARA)
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
- windows 3543.exe (PID: 3560)
Reads the date of Windows installation
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
Connects to unusual port
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
- windows 3543.exe (PID: 3560)
Reads security settings of Internet Explorer
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
Executing commands from a ".bat" file
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
Starts CMD.EXE for commands execution
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
Starts application with an unusual extension
- cmd.exe (PID: 7976)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 3688)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7976)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 3688)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2192)
The executable file from the user directory is run by the CMD process
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
- windows 3543.exe (PID: 3560)
INFO
Application launched itself
- msedge.exe (PID: 6340)
Reads Environment values
- identity_helper.exe (PID: 7792)
- JJSPLOIT.V2.exe (PID: 7788)
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
- windows 3543.exe (PID: 3560)
Checks supported languages
- JJSPLOIT.V2.exe (PID: 7788)
- identity_helper.exe (PID: 7792)
- windows 3543.exe (PID: 5244)
- chcp.com (PID: 1460)
- windows 3543.exe (PID: 5256)
- chcp.com (PID: 7556)
- windows 3543.exe (PID: 7372)
- chcp.com (PID: 6312)
- windows 3543.exe (PID: 3188)
- chcp.com (PID: 4392)
- windows 3543.exe (PID: 3560)
Reads the computer name
- identity_helper.exe (PID: 7792)
- JJSPLOIT.V2.exe (PID: 7788)
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
- windows 3543.exe (PID: 3560)
Executable content was dropped or overwritten
- msedge.exe (PID: 6340)
- msedge.exe (PID: 6672)
- msedge.exe (PID: 7476)
Reads the machine GUID from the registry
- JJSPLOIT.V2.exe (PID: 7788)
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
- windows 3543.exe (PID: 3560)
Creates files or folders in the user directory
- JJSPLOIT.V2.exe (PID: 7788)
Process checks computer location settings
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
Create files in a temporary directory
- windows 3543.exe (PID: 5244)
- windows 3543.exe (PID: 5256)
- windows 3543.exe (PID: 7372)
- windows 3543.exe (PID: 3188)
Changes the display of characters in the console
- cmd.exe (PID: 7976)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 3688)
The sample compiled with english language support
- msedge.exe (PID: 7476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(5244) windows 3543.exe
Version1.4.1
C2 (6)192.168.50.1:4782
10.0.0.113:4782
LETSQOOO-62766.portmap.host:62766
89.10.178.51:4782
LETSQOOO-62766.portmap.host:62766
Sub_Dirwindows updater
Install_Namewindows 3543.exe
Mutex90faf922-159d-4166-b661-4ba16af8650e
Startupwindows background updater
TagROBLOX EXECUTOR
LogDirroblox executor
SignatureDowhTcCNRmPne/jP3WQ8VLNtjW2b7COPJ9f99kZ79UFTzRFEvY6/5+otwvW1Bwmg9g0QfHHt35ZhSkuKX/JTqAAzWBJF4jgN5VBXj8eypchVIP3+JtYmO932+ak0qLmQH0HXpIdH0VUJZJaxFcaI3G20cO9f5EBgxHsey09u6g7O39z3AMmFvru9wuI2/bQkFreKMve5G63LPGchmgImAWCO+i3qtDNkH/D47EjSUKhBQjEwRNXoIahVTqBJr+eIfI/o/mQV8pWk2FKc5M20xfErtWCuSzMJ0rIULHdKHXDZ...
CertificateMIIE9DCCAtygAwIBAgIQAKXago0cfl52srIGgNzsZzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDgyNTE2NDk0M1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAhErQjQ8fpDYpYN1iZUcL3evTfxYkIWCVDolaEBfQA2elEwvnikLo+0s8mPHF86S0Qr9u+daX...
(PID) Process(5256) windows 3543.exe
Version1.4.1
C2 (6)192.168.50.1:4782
10.0.0.113:4782
LETSQOOO-62766.portmap.host:62766
89.10.178.51:4782
LETSQOOO-62766.portmap.host:62766
Sub_Dirwindows updater
Install_Namewindows 3543.exe
Mutex90faf922-159d-4166-b661-4ba16af8650e
Startupwindows background updater
TagROBLOX EXECUTOR
LogDirroblox executor
SignatureDowhTcCNRmPne/jP3WQ8VLNtjW2b7COPJ9f99kZ79UFTzRFEvY6/5+otwvW1Bwmg9g0QfHHt35ZhSkuKX/JTqAAzWBJF4jgN5VBXj8eypchVIP3+JtYmO932+ak0qLmQH0HXpIdH0VUJZJaxFcaI3G20cO9f5EBgxHsey09u6g7O39z3AMmFvru9wuI2/bQkFreKMve5G63LPGchmgImAWCO+i3qtDNkH/D47EjSUKhBQjEwRNXoIahVTqBJr+eIfI/o/mQV8pWk2FKc5M20xfErtWCuSzMJ0rIULHdKHXDZ...
CertificateMIIE9DCCAtygAwIBAgIQAKXago0cfl52srIGgNzsZzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDgyNTE2NDk0M1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAhErQjQ8fpDYpYN1iZUcL3evTfxYkIWCVDolaEBfQA2elEwvnikLo+0s8mPHF86S0Qr9u+daX...
(PID) Process(7372) windows 3543.exe
Version1.4.1
C2 (6)192.168.50.1:4782
10.0.0.113:4782
LETSQOOO-62766.portmap.host:62766
89.10.178.51:4782
LETSQOOO-62766.portmap.host:62766
Sub_Dirwindows updater
Install_Namewindows 3543.exe
Mutex90faf922-159d-4166-b661-4ba16af8650e
Startupwindows background updater
TagROBLOX EXECUTOR
LogDirroblox executor
SignatureDowhTcCNRmPne/jP3WQ8VLNtjW2b7COPJ9f99kZ79UFTzRFEvY6/5+otwvW1Bwmg9g0QfHHt35ZhSkuKX/JTqAAzWBJF4jgN5VBXj8eypchVIP3+JtYmO932+ak0qLmQH0HXpIdH0VUJZJaxFcaI3G20cO9f5EBgxHsey09u6g7O39z3AMmFvru9wuI2/bQkFreKMve5G63LPGchmgImAWCO+i3qtDNkH/D47EjSUKhBQjEwRNXoIahVTqBJr+eIfI/o/mQV8pWk2FKc5M20xfErtWCuSzMJ0rIULHdKHXDZ...
CertificateMIIE9DCCAtygAwIBAgIQAKXago0cfl52srIGgNzsZzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDgyNTE2NDk0M1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAhErQjQ8fpDYpYN1iZUcL3evTfxYkIWCVDolaEBfQA2elEwvnikLo+0s8mPHF86S0Qr9u+daX...
(PID) Process(3188) windows 3543.exe
Version1.4.1
C2 (6)192.168.50.1:4782
10.0.0.113:4782
LETSQOOO-62766.portmap.host:62766
89.10.178.51:4782
LETSQOOO-62766.portmap.host:62766
Sub_Dirwindows updater
Install_Namewindows 3543.exe
Mutex90faf922-159d-4166-b661-4ba16af8650e
Startupwindows background updater
TagROBLOX EXECUTOR
LogDirroblox executor
SignatureDowhTcCNRmPne/jP3WQ8VLNtjW2b7COPJ9f99kZ79UFTzRFEvY6/5+otwvW1Bwmg9g0QfHHt35ZhSkuKX/JTqAAzWBJF4jgN5VBXj8eypchVIP3+JtYmO932+ak0qLmQH0HXpIdH0VUJZJaxFcaI3G20cO9f5EBgxHsey09u6g7O39z3AMmFvru9wuI2/bQkFreKMve5G63LPGchmgImAWCO+i3qtDNkH/D47EjSUKhBQjEwRNXoIahVTqBJr+eIfI/o/mQV8pWk2FKc5M20xfErtWCuSzMJ0rIULHdKHXDZ...
CertificateMIIE9DCCAtygAwIBAgIQAKXago0cfl52srIGgNzsZzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDgyNTE2NDk0M1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAhErQjQ8fpDYpYN1iZUcL3evTfxYkIWCVDolaEBfQA2elEwvnikLo+0s8mPHF86S0Qr9u+daX...
(PID) Process(3560) windows 3543.exe
Version1.4.1
C2 (6)192.168.50.1:4782
10.0.0.113:4782
LETSQOOO-62766.portmap.host:62766
89.10.178.51:4782
LETSQOOO-62766.portmap.host:62766
Sub_Dirwindows updater
Install_Namewindows 3543.exe
Mutex90faf922-159d-4166-b661-4ba16af8650e
Startupwindows background updater
TagROBLOX EXECUTOR
LogDirroblox executor
SignatureDowhTcCNRmPne/jP3WQ8VLNtjW2b7COPJ9f99kZ79UFTzRFEvY6/5+otwvW1Bwmg9g0QfHHt35ZhSkuKX/JTqAAzWBJF4jgN5VBXj8eypchVIP3+JtYmO932+ak0qLmQH0HXpIdH0VUJZJaxFcaI3G20cO9f5EBgxHsey09u6g7O39z3AMmFvru9wuI2/bQkFreKMve5G63LPGchmgImAWCO+i3qtDNkH/D47EjSUKhBQjEwRNXoIahVTqBJr+eIfI/o/mQV8pWk2FKc5M20xfErtWCuSzMJ0rIULHdKHXDZ...
CertificateMIIE9DCCAtygAwIBAgIQAKXago0cfl52srIGgNzsZzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDgyNTE2NDk0M1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAhErQjQ8fpDYpYN1iZUcL3evTfxYkIWCVDolaEBfQA2elEwvnikLo+0s8mPHF86S0Qr9u+daX...
Total processes
205
Monitored processes
74
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7872 --field-trial-handle=2360,i,8374248031151363311,373127812902750100,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1192 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=912 --field-trial-handle=2360,i,8374248031151363311,373127812902750100,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1460 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1808 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1876 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=5512 --field-trial-handle=2360,i,8374248031151363311,373127812902750100,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5232 --field-trial-handle=2360,i,8374248031151363311,373127812902750100,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5812 --field-trial-handle=2360,i,8374248031151363311,373127812902750100,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
10 895
Read events
10 875
Write events
20
Delete events
0
Modification events
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 48A19239538C2F00 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4917942A-B31E-4049-8F9B-19D7B0A1B300} | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C50E7339538C2F00 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E26D04AA-A75E-45C7-AFEE-A9214FE470AA} | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 80C0AE39538C2F00 | |||
| (PID) Process: | (6340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
20
Suspicious files
519
Text files
95
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135bcf.TMP | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135bdf.TMP | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135bdf.TMP | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135bdf.TMP | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135bcf.TMP | — | |
MD5:— | SHA256:— | |||
| 6340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
66
DNS requests
68
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7992 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739209074&P2=404&P3=2&P4=h3WlcNufhsXQHQTESDuvkRz9TIaalyY2TU4pSu0yYuiGC95p6PHwjzCpnJoaRwbrByZyxNLhReYEVG5OfnT7bw%3d%3d | unknown | — | — | whitelisted |
7992 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739209074&P2=404&P3=2&P4=h3WlcNufhsXQHQTESDuvkRz9TIaalyY2TU4pSu0yYuiGC95p6PHwjzCpnJoaRwbrByZyxNLhReYEVG5OfnT7bw%3d%3d | unknown | — | — | whitelisted |
7992 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739209074&P2=404&P3=2&P4=CS2v4mfxAMXe2NcYPKAEiI2i2uPTGm%2bXm31MAi5TEeEPFWOSRDrLGUBuyp%2bfRNly5xnGQT1JcLC9wCQV15cWaQ%3d%3d | unknown | — | — | whitelisted |
7992 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739209074&P2=404&P3=2&P4=h3WlcNufhsXQHQTESDuvkRz9TIaalyY2TU4pSu0yYuiGC95p6PHwjzCpnJoaRwbrByZyxNLhReYEVG5OfnT7bw%3d%3d | unknown | — | — | whitelisted |
7992 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/de2c6004-9bb9-4e49-b0e2-d9188dc643bb?P1=1739209075&P2=404&P3=2&P4=LXraNsGlDcpjR1djFczJiUctnegYUjsvJlDEAsOaoD5teEfpPzHw6vrUub3o4FT6gYpwA396g%2b5Uzpw5%2fEyC1A%3d%3d | unknown | — | — | whitelisted |
7992 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739209074&P2=404&P3=2&P4=CS2v4mfxAMXe2NcYPKAEiI2i2uPTGm%2bXm31MAi5TEeEPFWOSRDrLGUBuyp%2bfRNly5xnGQT1JcLC9wCQV15cWaQ%3d%3d | unknown | — | — | whitelisted |
7992 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739209074&P2=404&P3=2&P4=CS2v4mfxAMXe2NcYPKAEiI2i2uPTGm%2bXm31MAi5TEeEPFWOSRDrLGUBuyp%2bfRNly5xnGQT1JcLC9wCQV15cWaQ%3d%3d | unknown | — | — | whitelisted |
7992 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739209074&P2=404&P3=2&P4=CS2v4mfxAMXe2NcYPKAEiI2i2uPTGm%2bXm31MAi5TEeEPFWOSRDrLGUBuyp%2bfRNly5xnGQT1JcLC9wCQV15cWaQ%3d%3d | unknown | — | — | whitelisted |
7992 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739209074&P2=404&P3=2&P4=CS2v4mfxAMXe2NcYPKAEiI2i2uPTGm%2bXm31MAi5TEeEPFWOSRDrLGUBuyp%2bfRNly5xnGQT1JcLC9wCQV15cWaQ%3d%3d | unknown | — | — | whitelisted |
7992 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/de2c6004-9bb9-4e49-b0e2-d9188dc643bb?P1=1739209075&P2=404&P3=2&P4=LXraNsGlDcpjR1djFczJiUctnegYUjsvJlDEAsOaoD5teEfpPzHw6vrUub3o4FT6gYpwA396g%2b5Uzpw5%2fEyC1A%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6340 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6672 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6672 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6672 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6672 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
6672 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
github.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
go.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6672 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6672 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2192 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2192 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .host) |
2192 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2192 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .host) |
2192 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2192 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .host) |
2192 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2192 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .host) |