| File name: | 1.bat |
| Full analysis: | https://app.any.run/tasks/31aabf61-603c-473c-8509-5a0951fca331 |
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | July 28, 2024, 09:05:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | DA73712D7B9F73E772EEB4B4FD698AE0 |
| SHA1: | 0D725F090A7B75645A569ECBE9A034E027FBCD70 |
| SHA256: | 6779905A46C3B863336F0E76F813D4F0F14AFF38A979FF1CE1EE70307F9C4812 |
| SSDEEP: | 48:55sccKJzKLzBRzEJQRx7iGzdzKzCJ9s/j:5KccKJzYzvzES4GzdzKzC3sr |
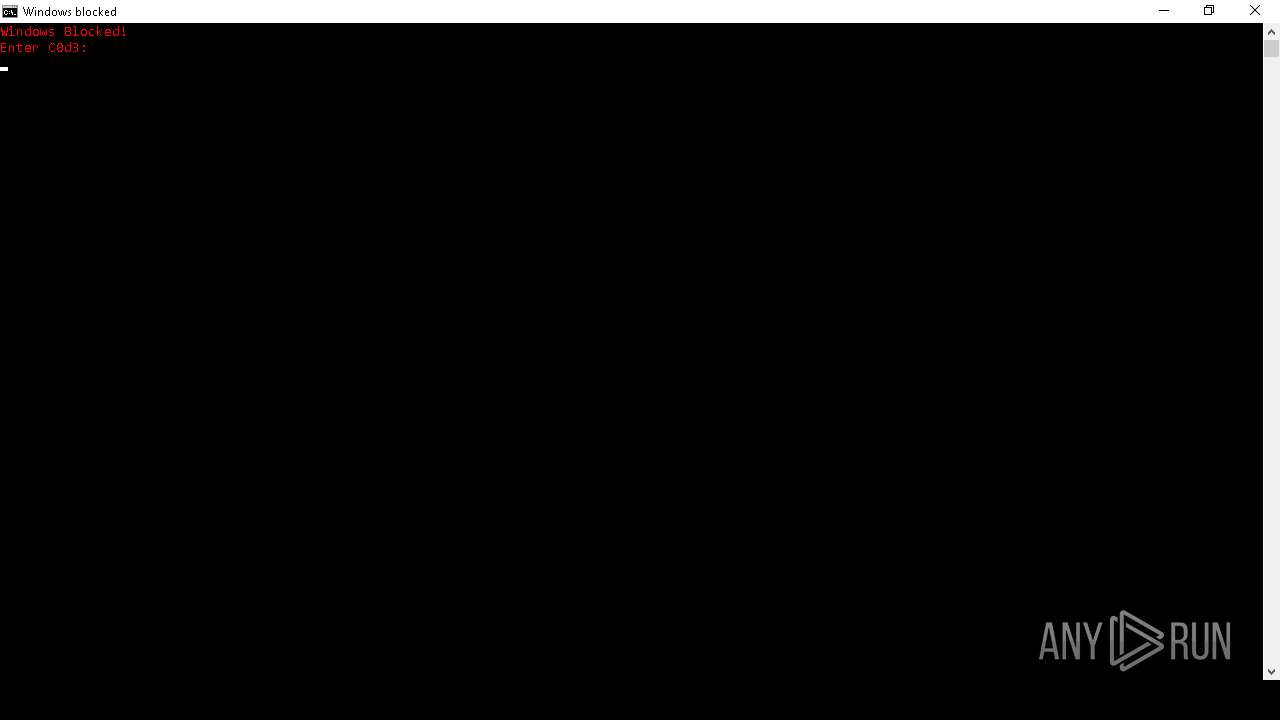
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 5496)
- exploreer.exe (PID: 7284)
NjRAT is detected
- Explorer.exe (PID: 8164)
- exploreer.exe (PID: 7284)
Drops the executable file immediately after the start
- Explorer.exe (PID: 8164)
- exploreer.exe (PID: 7284)
- tmpF448.tmp.exe (PID: 7972)
Create files in the Startup directory
- exploreer.exe (PID: 7284)
Connects to the CnC server
- exploreer.exe (PID: 7284)
NJRAT has been detected (SURICATA)
- exploreer.exe (PID: 7284)
NJRAT has been detected (YARA)
- exploreer.exe (PID: 7284)
Actions looks like stealing of personal data
- tmpF448.tmp.exe (PID: 7972)
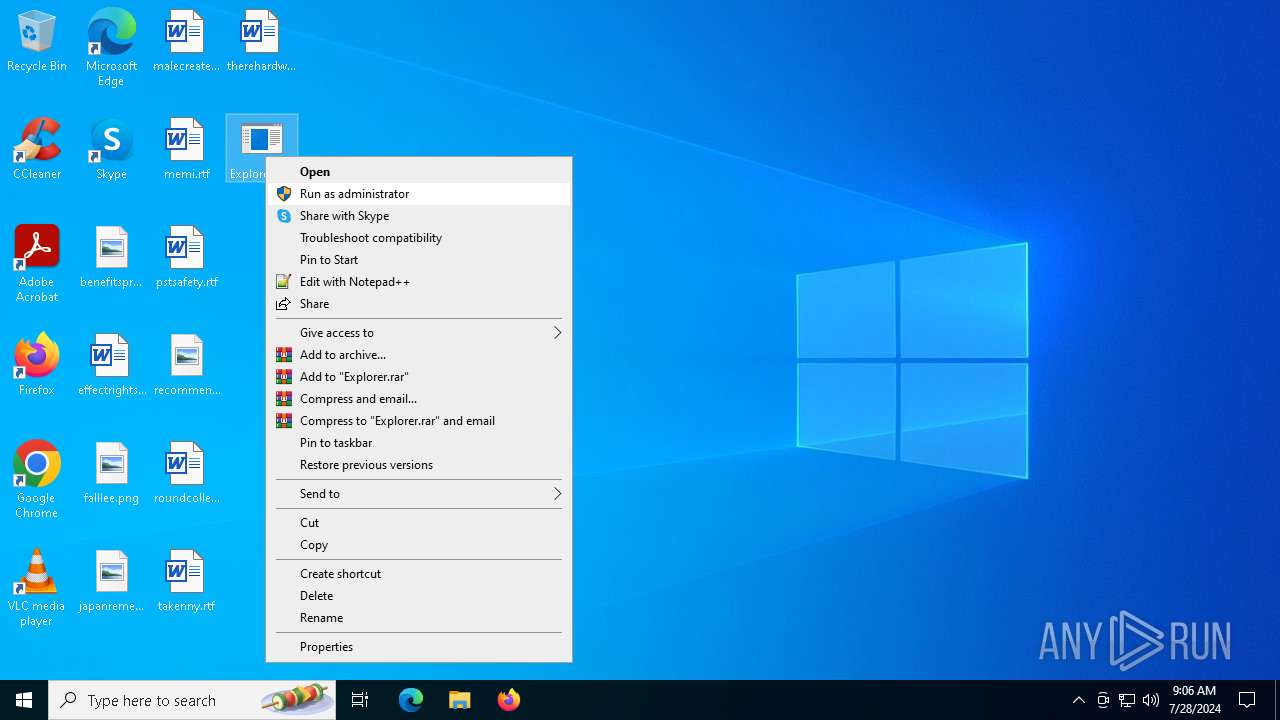
SUSPICIOUS
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6396)
Detected use of alternative data streams (AltDS)
- cmd.exe (PID: 6396)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6396)
Reads security settings of Internet Explorer
- StartMenuExperienceHost.exe (PID: 5332)
- Explorer.exe (PID: 8164)
- exploreer.exe (PID: 7284)
- tmp6D43.tmp.exe (PID: 1028)
- tmpF448.tmp.exe (PID: 7972)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 5332)
- SearchApp.exe (PID: 4180)
- Explorer.exe (PID: 8164)
- exploreer.exe (PID: 7284)
- tmp6D43.tmp.exe (PID: 1028)
- tmpF448.tmp.exe (PID: 7972)
Starts itself from another location
- Explorer.exe (PID: 8164)
Executable content was dropped or overwritten
- Explorer.exe (PID: 8164)
- exploreer.exe (PID: 7284)
- tmpF448.tmp.exe (PID: 7972)
Uses NETSH.EXE to add a firewall rule or allowed programs
- exploreer.exe (PID: 7284)
Contacting a server suspected of hosting an CnC
- exploreer.exe (PID: 7284)
Connects to unusual port
- exploreer.exe (PID: 7284)
Reads the BIOS version
- tmp6D43.tmp.exe (PID: 1028)
Connects to FTP
- tmp6D43.tmp.exe (PID: 1028)
Starts application with an unusual extension
- exploreer.exe (PID: 7284)
Starts CMD.EXE for commands execution
- tmp6D43.tmp.exe (PID: 1028)
Hides command output
- cmd.exe (PID: 2936)
Mutex name with non-standard characters
- tmpF448.tmp.exe (PID: 7972)
INFO
Checks proxy server information
- slui.exe (PID: 5196)
- SearchApp.exe (PID: 4180)
- explorer.exe (PID: 7088)
- slui.exe (PID: 7708)
- tmpABB5.tmp.scr (PID: 3568)
- tmp6D43.tmp.exe (PID: 1028)
Reads the software policy settings
- slui.exe (PID: 5196)
- SearchApp.exe (PID: 4180)
- slui.exe (PID: 7708)
Reads Microsoft Office registry keys
- explorer.exe (PID: 7088)
Reads security settings of Internet Explorer
- explorer.exe (PID: 7088)
Reads the computer name
- StartMenuExperienceHost.exe (PID: 5332)
- TextInputHost.exe (PID: 5420)
- SearchApp.exe (PID: 4180)
- Explorer.exe (PID: 8164)
- exploreer.exe (PID: 7284)
- tmp6D43.tmp.exe (PID: 1028)
- tmpABB5.tmp.scr (PID: 3568)
- tmpF448.tmp.exe (PID: 2248)
- tmpF448.tmp.exe (PID: 7972)
Checks supported languages
- StartMenuExperienceHost.exe (PID: 5332)
- TextInputHost.exe (PID: 5420)
- SearchApp.exe (PID: 4180)
- Explorer.exe (PID: 8164)
- exploreer.exe (PID: 7284)
- tmp6D43.tmp.exe (PID: 1028)
- tmpABB5.tmp.scr (PID: 3568)
- tmpF448.tmp.exe (PID: 7972)
- tmpF448.tmp.exe (PID: 2248)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 5332)
- SearchApp.exe (PID: 4180)
- Explorer.exe (PID: 8164)
- exploreer.exe (PID: 7284)
- tmp6D43.tmp.exe (PID: 1028)
- tmpF448.tmp.exe (PID: 7972)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 4180)
- exploreer.exe (PID: 7284)
- tmpABB5.tmp.scr (PID: 3568)
Creates files or folders in the user directory
- explorer.exe (PID: 7088)
- exploreer.exe (PID: 7284)
Reads Environment values
- SearchApp.exe (PID: 4180)
- exploreer.exe (PID: 7284)
- tmpABB5.tmp.scr (PID: 3568)
Process checks Internet Explorer phishing filters
- SearchApp.exe (PID: 4180)
Create files in a temporary directory
- exploreer.exe (PID: 7284)
- tmpF448.tmp.exe (PID: 7972)
Disables trace logs
- tmpABB5.tmp.scr (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
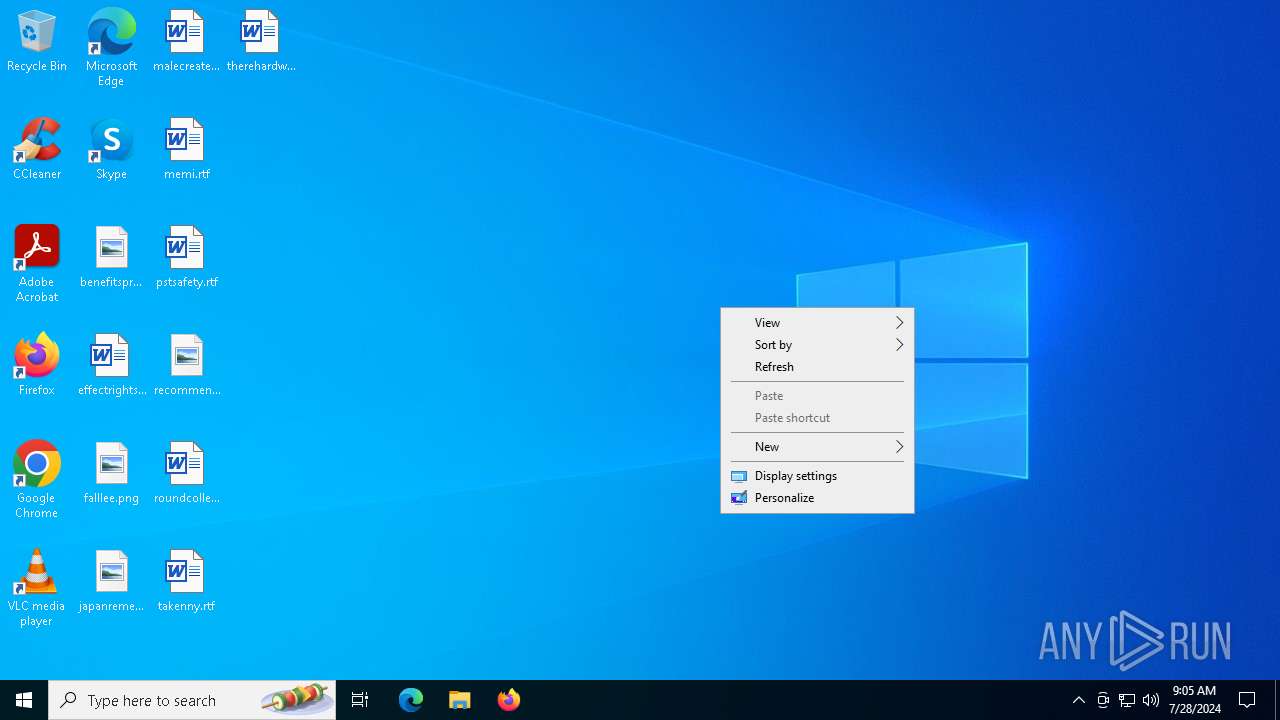
NjRat
(PID) Process(7284) exploreer.exe
C2uagbdfvuiashgfqyf.hopto.org
Ports1234
BotnetHacKed
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\3209c852f3690a05c1bf82e7f2b68178
Splitter|'|'|
Versionim523
Total processes
180
Monitored processes
35
Malicious processes
6
Suspicious processes
1
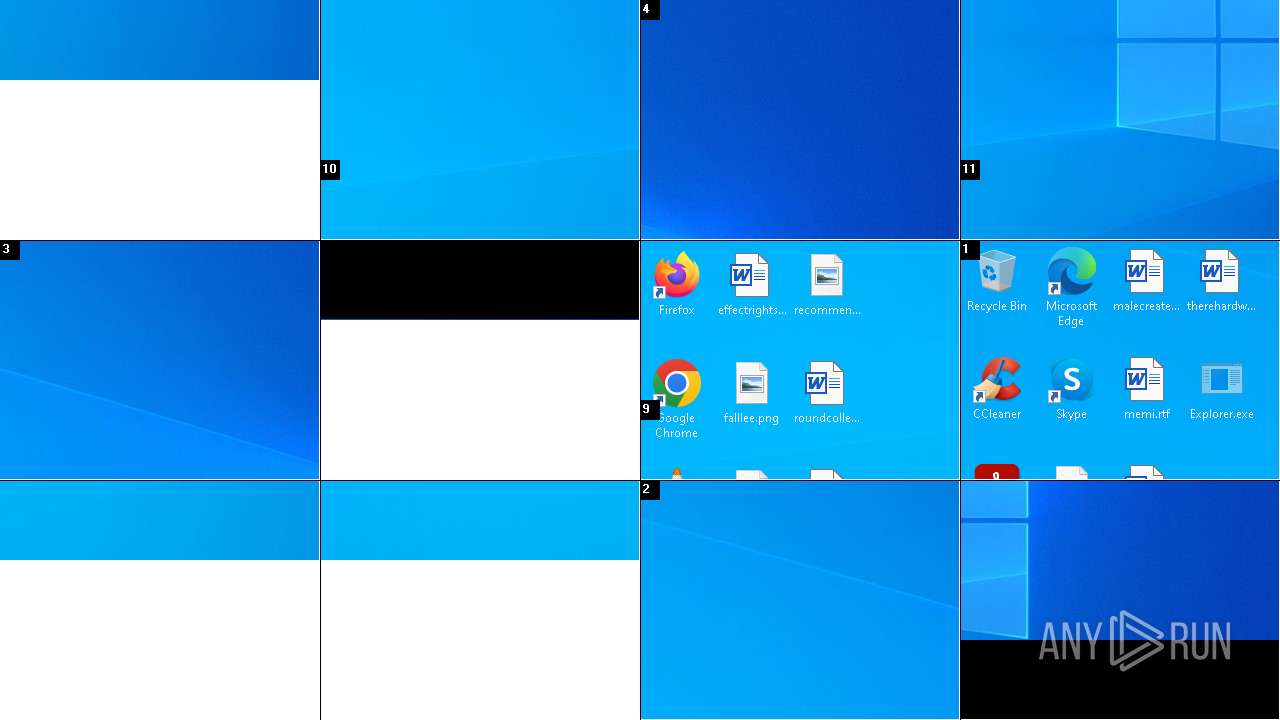
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer/v NoControlPanel /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1028 | "C:\Users\admin\AppData\Local\Temp\tmp6D43.tmp.exe" | C:\Users\admin\AppData\Local\Temp\tmp6D43.tmp.exe | exploreer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
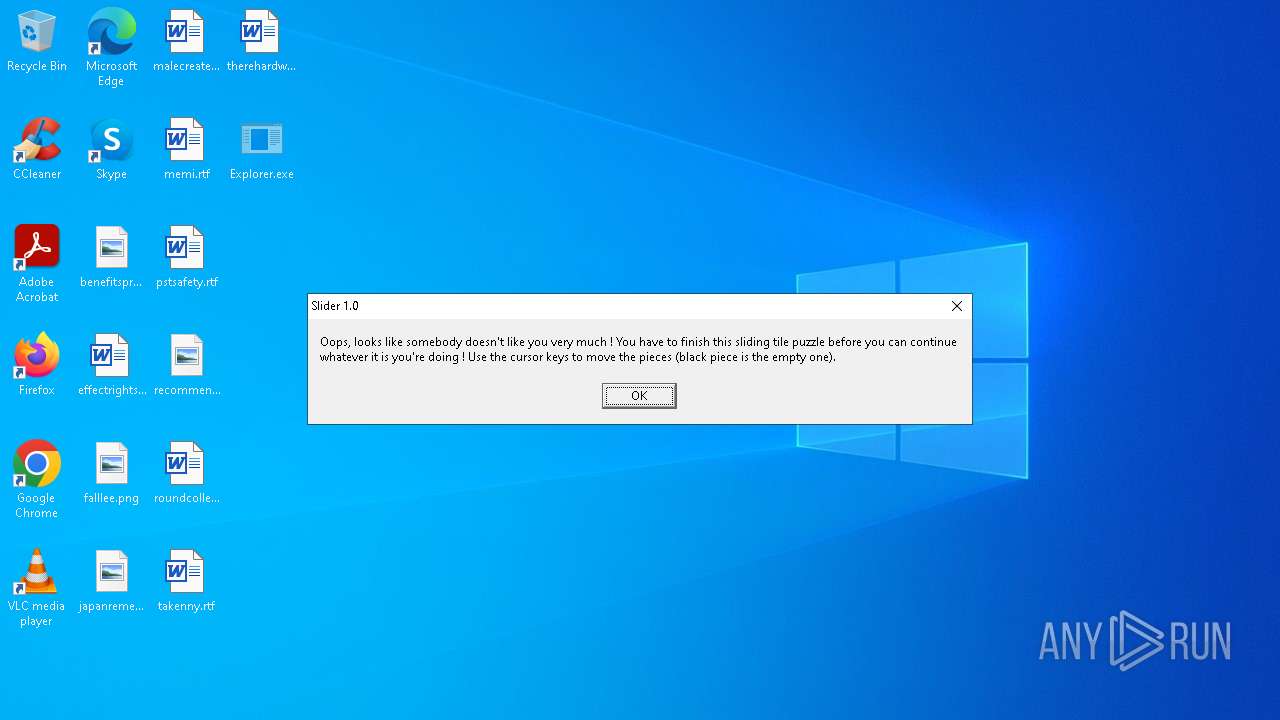
| 2248 | "C:\Users\admin\AppData\Local\Temp\3582-490\tmpF448.tmp.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\tmpF448.tmp.exe | — | tmpF448.tmp.exe | |||||||||||
User: admin Company: Andy Feys Integrity Level: HIGH Description: Slider Version: 1.0.0.0 Modules
| |||||||||||||||
| 2252 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableRegistryTools /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2936 | "C:\WINDOWS\system32\cmd.exe" /c del "C:\Users\admin\AppData\Local\Temp\tmp6D43.tmp.exe" >> NUL | C:\Windows\SysWOW64\cmd.exe | — | tmp6D43.tmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3280 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer /v NoDesktop /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3280 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
57 147
Read events
56 603
Write events
525
Delete events
19
Modification events
| (PID) Process: | (5496) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Win32 |
Value: C:\Windows\Win32.bat | |||
| (PID) Process: | (6640) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7088) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e72-85a9-11eb-90a8-9a9b76358421} |
| Operation: | write | Name: | Data |
Value: D60D00000DF0ADBA41000000080000000000008000000000000000300000000000000000FF06E703FF00000016000000FA99B7261F00000004400000030000000000000000000000000000000000000000005C005C003F005C00530054004F005200410047004500230056006F006C0075006D00650023007B00390030006300660033006400640036002D0030006100660037002D0031003100650063002D0062003400380030002D003800300036006500360066003600650036003900360033007D002300300030003000300030003000300030003100460035003000300030003000300023007B00350033006600350036003300300064002D0062003600620066002D0031003100640030002D0039003400660032002D003000300061003000630039003100650066006200380062007D000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005C005C003F005C0056006F006C0075006D0065007B00320066003500630035006500370032002D0038003500610039002D0031003100650062002D0039003000610038002D003900610039006200370036003300350038003400320031007D005C0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000004E005400460053000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000 | |||
| (PID) Process: | (7088) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e72-85a9-11eb-90a8-9a9b76358421} |
| Operation: | write | Name: | Generation |
Value: 2 | |||
| (PID) Process: | (7088) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e73-85a9-11eb-90a8-9a9b76358421} |
| Operation: | write | Name: | Data |
Value: D60D00000DF0ADBA01000000080000000000008000000000000000300000000000000000FF06E703FF00000016000000A6CD40161E00000004000000030000000000000000000000000000000000000000005C005C003F005C00530054004F005200410047004500230056006F006C0075006D00650023007B00390030006300660033006400640036002D0030006100660037002D0031003100650063002D0062003400380030002D003800300036006500360066003600650036003900360033007D002300300030003000300030003000330046004300420038003000300030003000300023007B00350033006600350036003300300064002D0062003600620066002D0031003100640030002D0039003400660032002D003000300061003000630039003100650066006200380062007D000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005C005C003F005C0056006F006C0075006D0065007B00320066003500630035006500370033002D0038003500610039002D0031003100650062002D0039003000610038002D003900610039006200370036003300350038003400320031007D005C0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000004E005400460053000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000 | |||
| (PID) Process: | (7088) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e73-85a9-11eb-90a8-9a9b76358421} |
| Operation: | write | Name: | Generation |
Value: 2 | |||
| (PID) Process: | (7088) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{eaf65672-68c3-4f99-8d5c-104b5f4d8fff} |
| Operation: | write | Name: | Data |
Value: D60D00000DF0ADBA01000000080000000000008000000000000000300000000000000000FF06E703FF000000160000009FF23EA01E00000004000000030000000000000000000000000000000000000000005C005C003F005C00530054004F005200410047004500230056006F006C0075006D00650023007B00390030006300660033006400640036002D0030006100660037002D0031003100650063002D0062003400380030002D003800300036006500360066003600650036003900360033007D002300300030003000300030003000330046004100410046003000300030003000300023007B00350033006600350036003300300064002D0062003600620066002D0031003100640030002D0039003400660032002D003000300061003000630039003100650066006200380062007D000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005C005C003F005C0056006F006C0075006D0065007B00650061006600360035003600370032002D0036003800630033002D0034006600390039002D0038006400350063002D003100300034006200350066003400640038006600660066007D005C0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000004E005400460053000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000 | |||
| (PID) Process: | (7088) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{eaf65672-68c3-4f99-8d5c-104b5f4d8fff} |
| Operation: | write | Name: | Generation |
Value: 2 | |||
| (PID) Process: | (7088) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e71-85a9-11eb-90a8-9a9b76358421} |
| Operation: | write | Name: | Data |
Value: D60D00000DF0ADBA0100000008000000000000800000000000000030000000000000000006020200FF000000100000000EE13DAC1E00000004000000030000000000000000000000000000000000000000005C005C003F005C00530054004F005200410047004500230056006F006C0075006D00650023007B00390030006300660033006400640036002D0030006100660037002D0031003100650063002D0062003400380030002D003800300036006500360066003600650036003900360033007D002300300030003000300030003000300030003000300031003000300030003000300023007B00350033006600350036003300300064002D0062003600620066002D0031003100640030002D0039003400660032002D003000300061003000630039003100650066006200380062007D000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005C005C003F005C0056006F006C0075006D0065007B00320066003500630035006500370031002D0038003500610039002D0031003100650062002D0039003000610038002D003900610039006200370036003300350038003400320031007D005C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000046004100540033003200000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000 | |||
| (PID) Process: | (7088) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e71-85a9-11eb-90a8-9a9b76358421} |
| Operation: | write | Name: | Generation |
Value: 2 | |||
Executable files
63
Suspicious files
34
Text files
172
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4180 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | der | |
MD5:66D9CFF6DF9E55C7F636B41FE33D6C69 | SHA256:B81E4869EC2C4F407FE3170A32BC5E29078B2C6B76CDA708C0838C5BE037B2DA | |||
| 4180 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ShellFeeds\TEMP-GLEAM-LIGHT.svg~RF1c1e9b.TMP | — | |
MD5:— | SHA256:— | |||
| 3280 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:8EDAB0DC454243595FDDC2EE625794DD | SHA256:C800CE50803585CA0CA95351435ADEB6408EA0C08FBCD953A71FD028D4C53DDF | |||
| 4180 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\INetCache\Q84V0JUH\-UAIppANYxiGpRWJy2NDph4qOEw.gz[2].js | s | |
MD5:9E527B91C2D8B31B0017B76049B5E4E3 | SHA256:38EDF0F961C1CCB287880B88F12F370775FC65B2E28227EEE215E849CDBE9BBC | |||
| 4180 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\Internet Explorer\DOMStore\ZWUI0EBX\www.bing[1].xml | text | |
MD5:85C395BAB8B304EB7AE56EC5F6A931CD | SHA256:E456078F5E8767368EFDB25309825B6380EAA81B01F2EE8374A16FB085137A44 | |||
| 6396 | cmd.exe | C:\Users\admin\AppData\Local\Temp:D | text | |
MD5:FAD6157B90665AF23A4AA05EAC7FE6E1 | SHA256:A770C63B1465581D54F36C5CBECBCFF21AC0E91805CD309452C29DE5EACA199D | |||
| 4180 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | der | |
MD5:ADC27DFFFBCDD0120F0324B5C99E200F | SHA256:45C85199FA440C86866ECFC5337B457A1DAB7380D0D59649ADE0CB99A61EF715 | |||
| 4180 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\INetCache\Q84V0JUH\th[6].svg | image | |
MD5:0246F65C9B9B7D9EE7BECCC8758C5D56 | SHA256:0391E85F3F3D3F789E211CD2E320788891F98EFA7CCA01547EE32DA9CDA11B1E | |||
| 4180 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:797764D7F8BFA26504C83505494257FE | SHA256:6684B8FE0C8B8BBB12ECF582F92F520D3E62B813159EFCDD407F2C614EEA6D1B | |||
| 4180 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\fbaf94e759052658216786bfbabcdced1b67a5c2.tbres | binary | |
MD5:702BCB58CCEDBE6708DE53C95B0510C4 | SHA256:5BCCC74776E88897DE957882AF5432966C701285DD2BDCB3FB0C73E359D2A61E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
51
DNS requests
29
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4180 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4180 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5824 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5368 | SearchApp.exe | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1180 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4236 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5368 | SearchApp.exe | 95.100.146.27:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
1028 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6564 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5196 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.hopto .org |
7284 | exploreer.exe | Malware Command and Control Activity Detected | ET MALWARE Generic njRAT/Bladabindi CnC Activity (ll) |
2284 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.hopto .org |
7284 | exploreer.exe | Malware Command and Control Activity Detected | ET MALWARE njrat ver 0.7d Malware CnC Callback (Remote Desktop) |
8 ETPRO signatures available at the full report