| File name: | C:\Users\admin\AppData\Local\Temp\Rar$EXa1780.25675\NEW CONTRACT.exe |
| Full analysis: | https://app.any.run/tasks/b5156d61-4988-4311-a12e-e363fceb8613 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
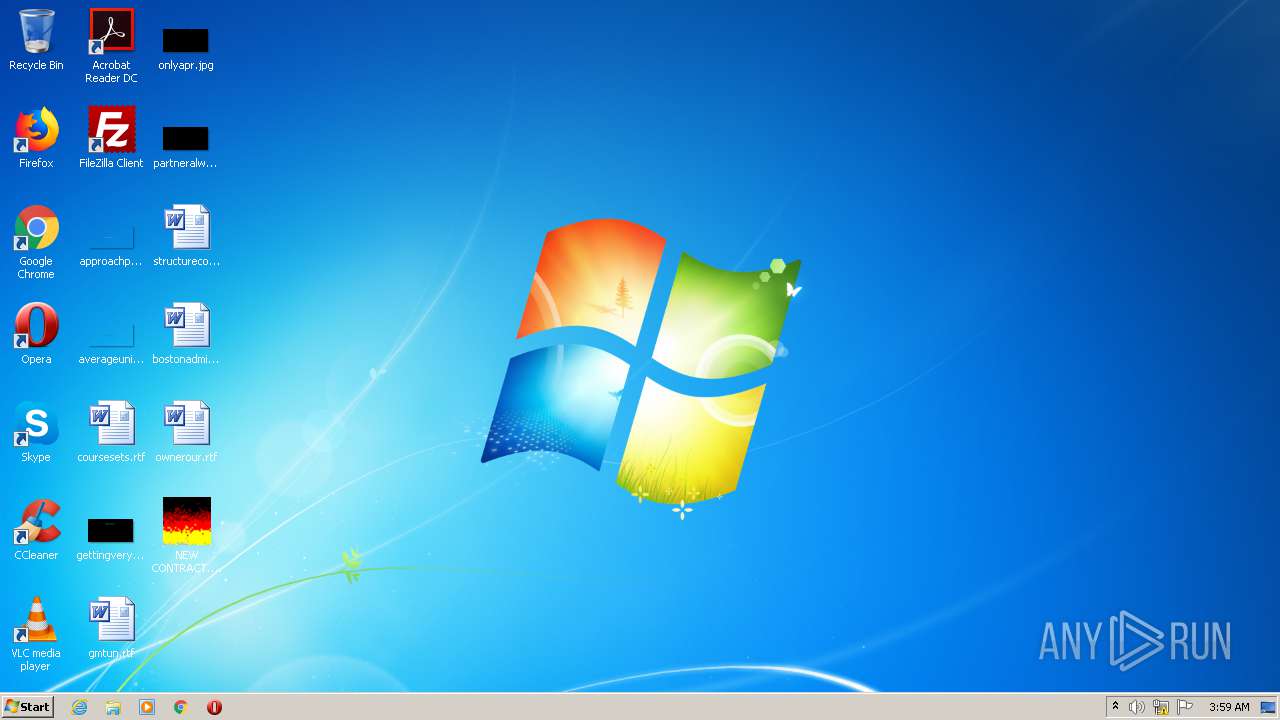
| Analysis date: | July 16, 2020, 02:59:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | FCF4EDF16E4C173CF5290005298AF685 |
| SHA1: | 13C03C0B40E362FE9ACBB62A695790EA436DFEE3 |
| SHA256: | 675D56191139C3B24869C61F555619A98F807FB847184448DFF6E6E796037382 |
| SSDEEP: | 12288:WpF3cmNfGqDJPDNlOW5wpiiEuuNyhWz/64LkHxSR6mSAx8DHxCR7c0XsuVajew:6FsoFwfWbFkS8hAxYAdyJ |
MALICIOUS
Runs app for hidden code execution
- NEW CONTRACT.exe (PID: 2772)
- WARZONE.exe (PID: 2712)
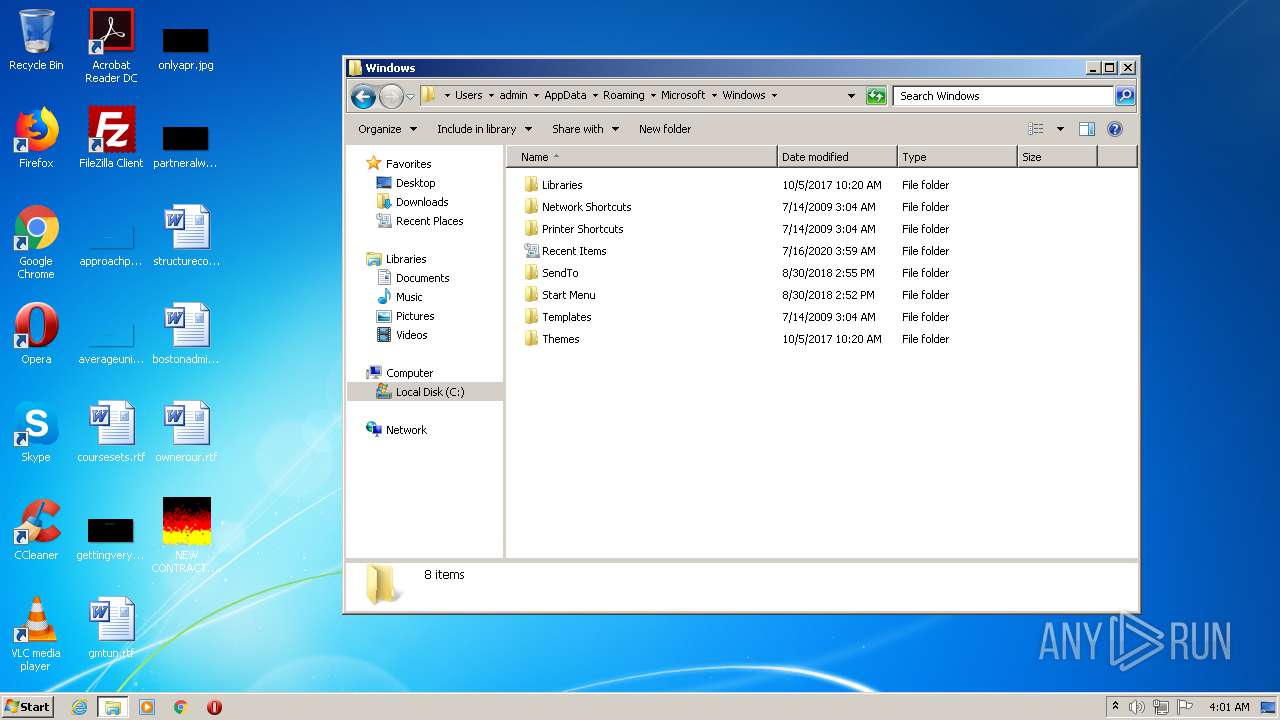
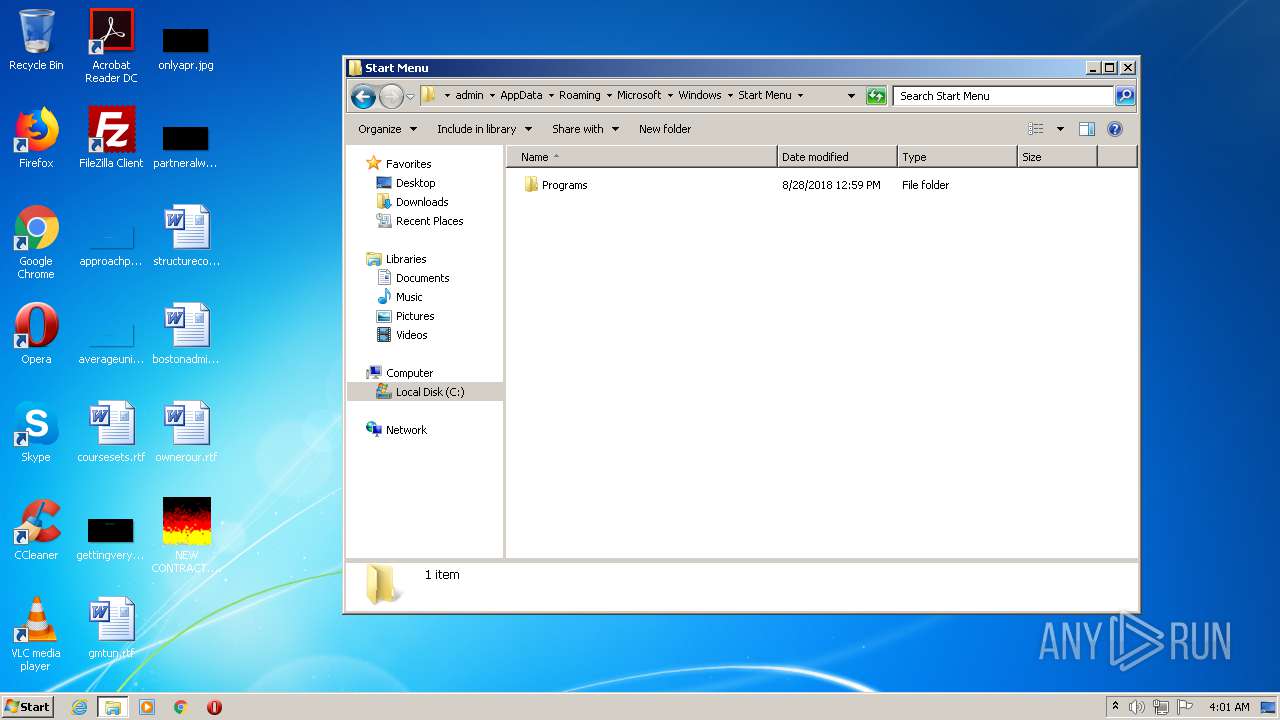
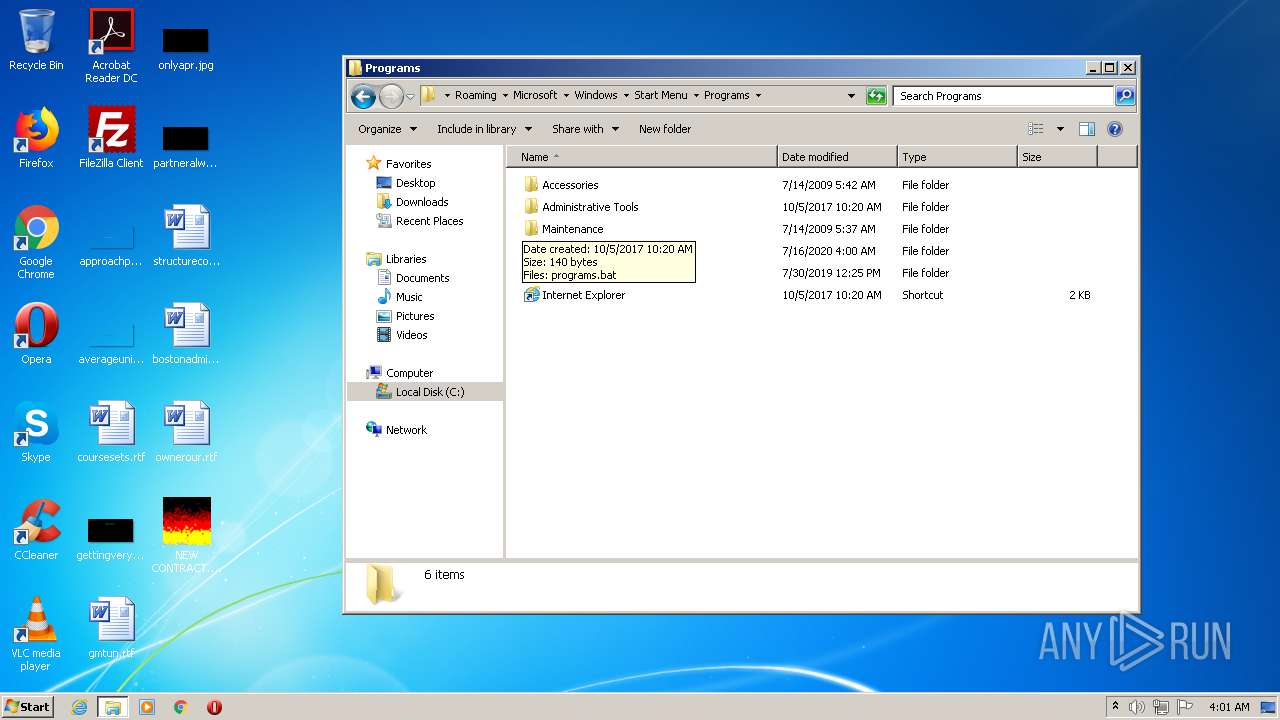
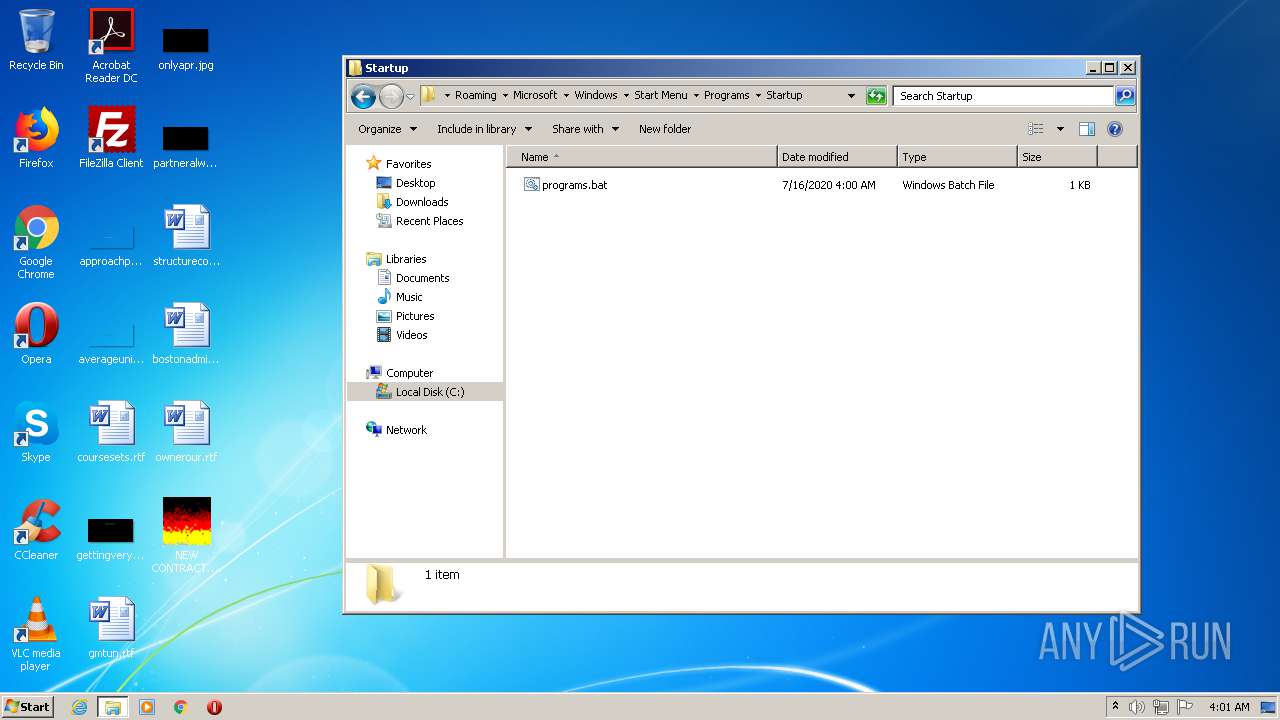
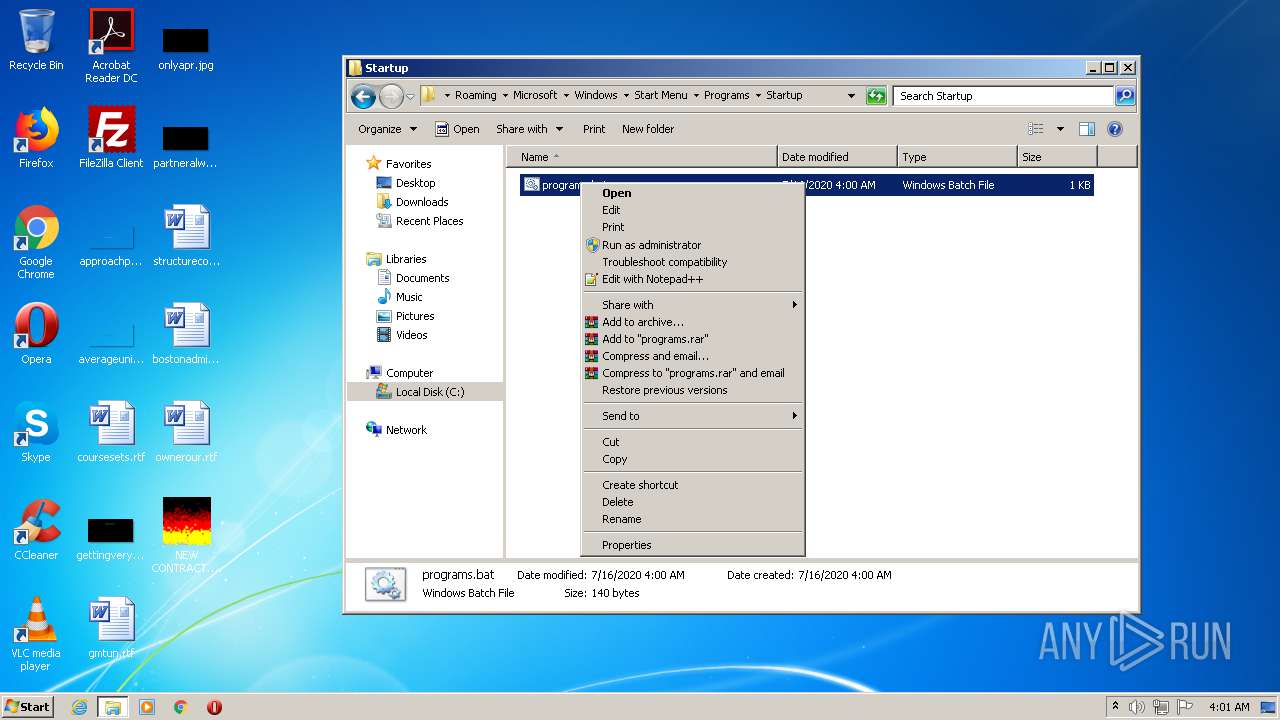
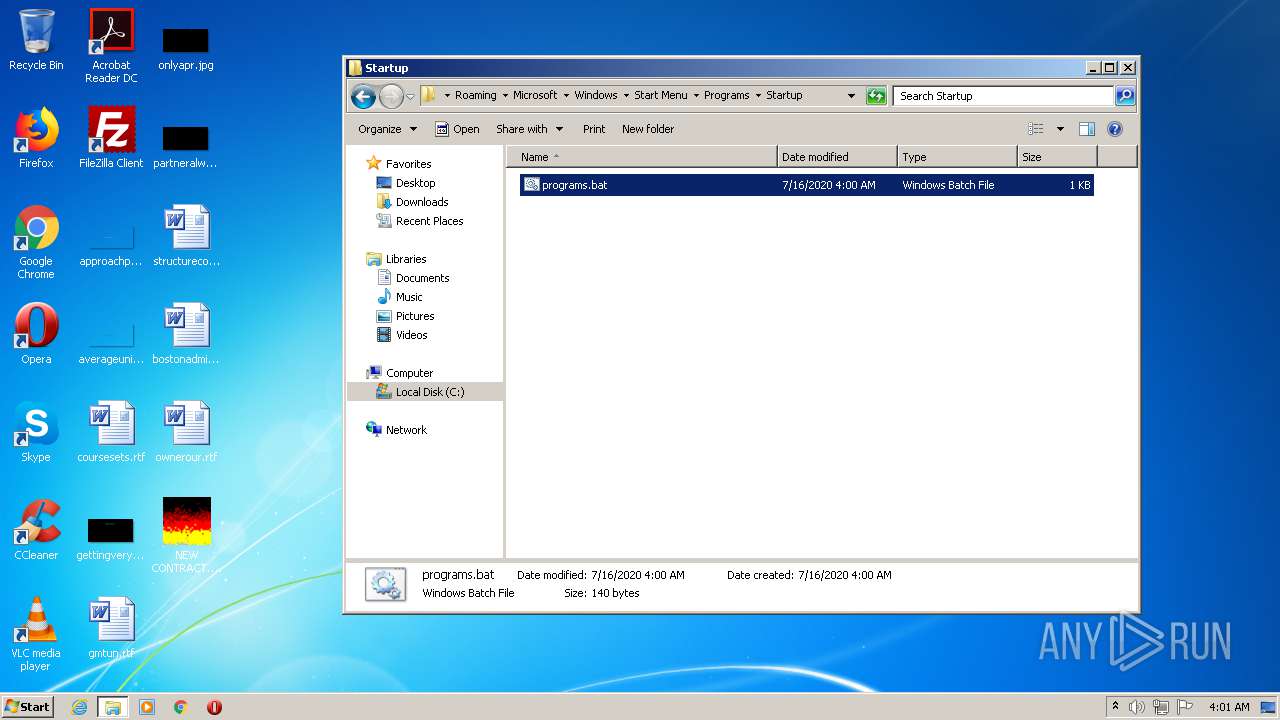
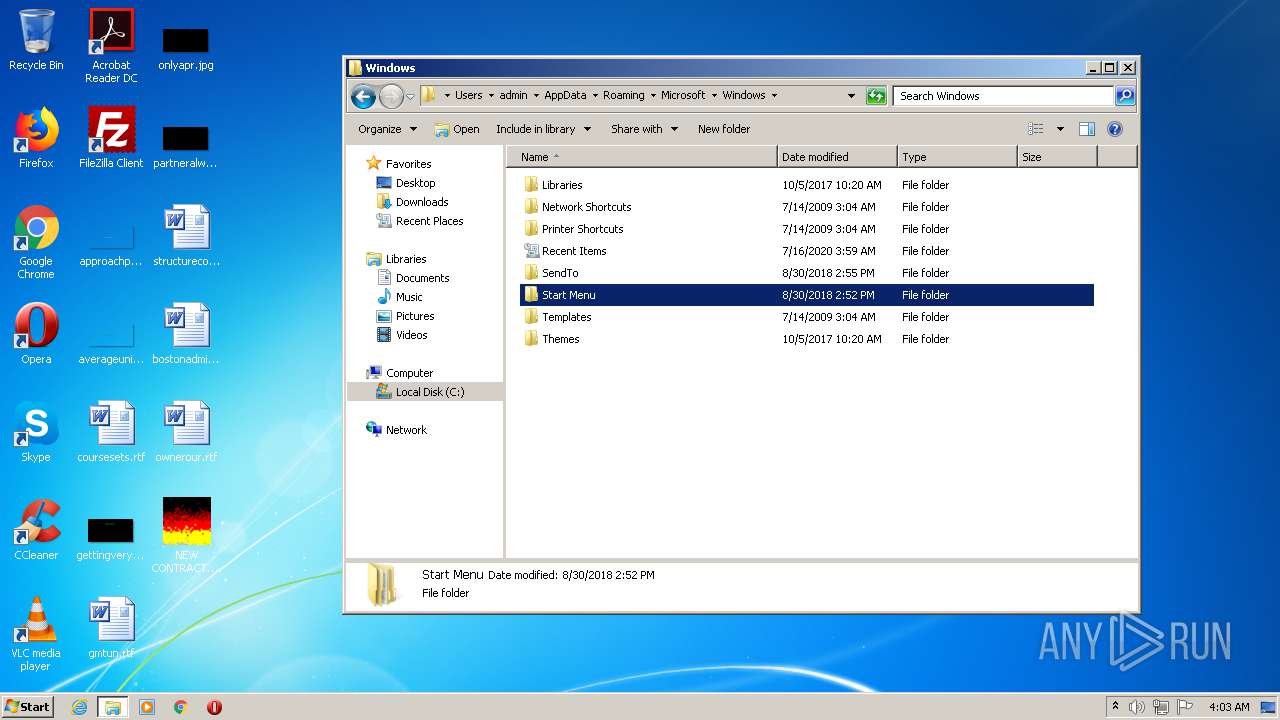
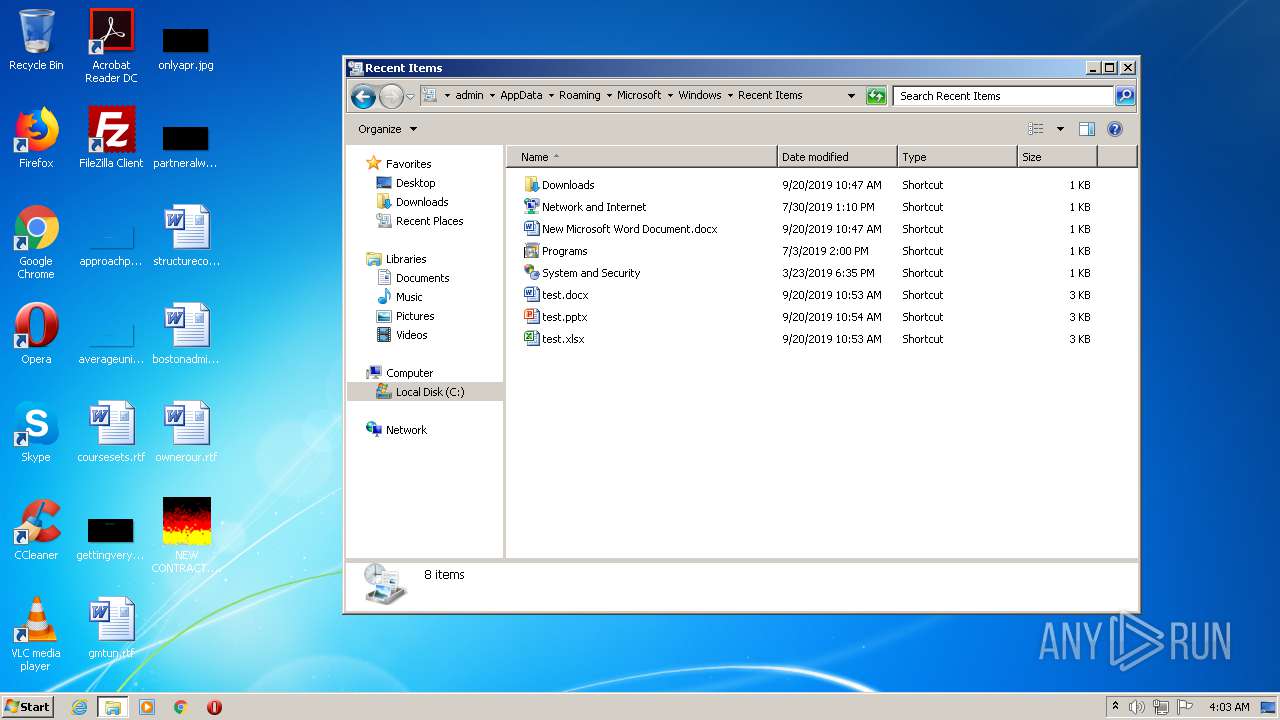
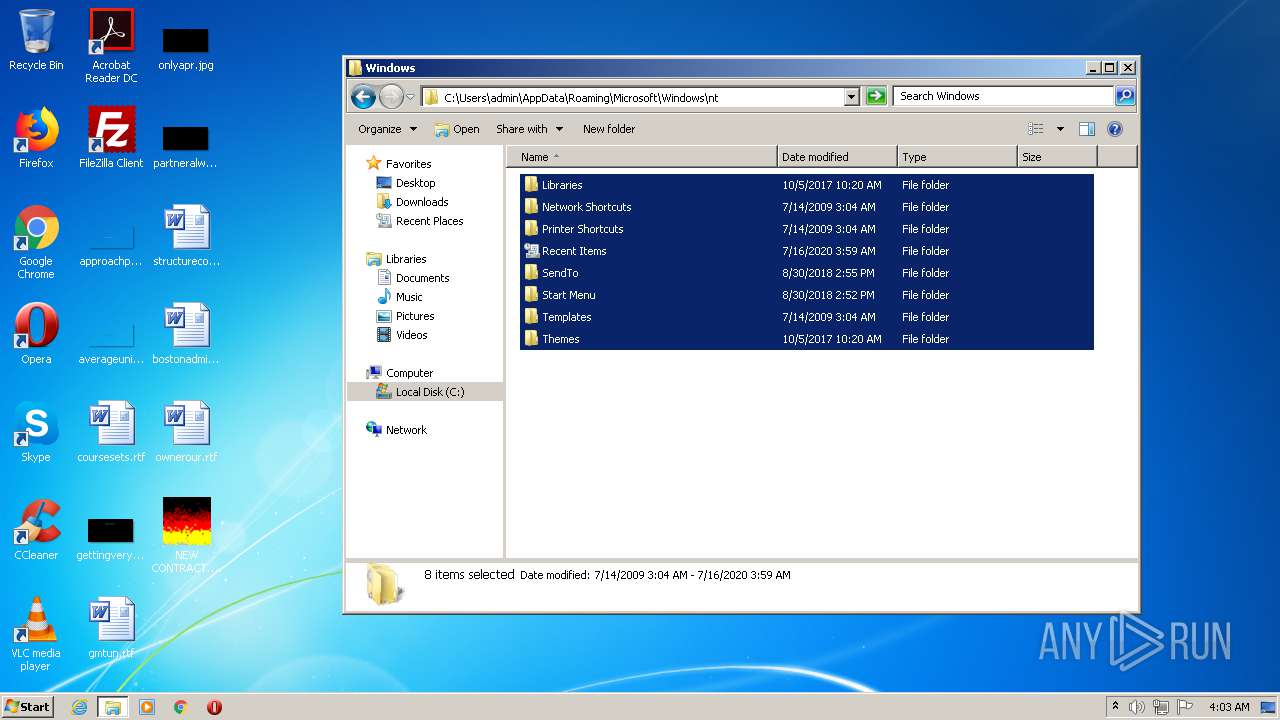
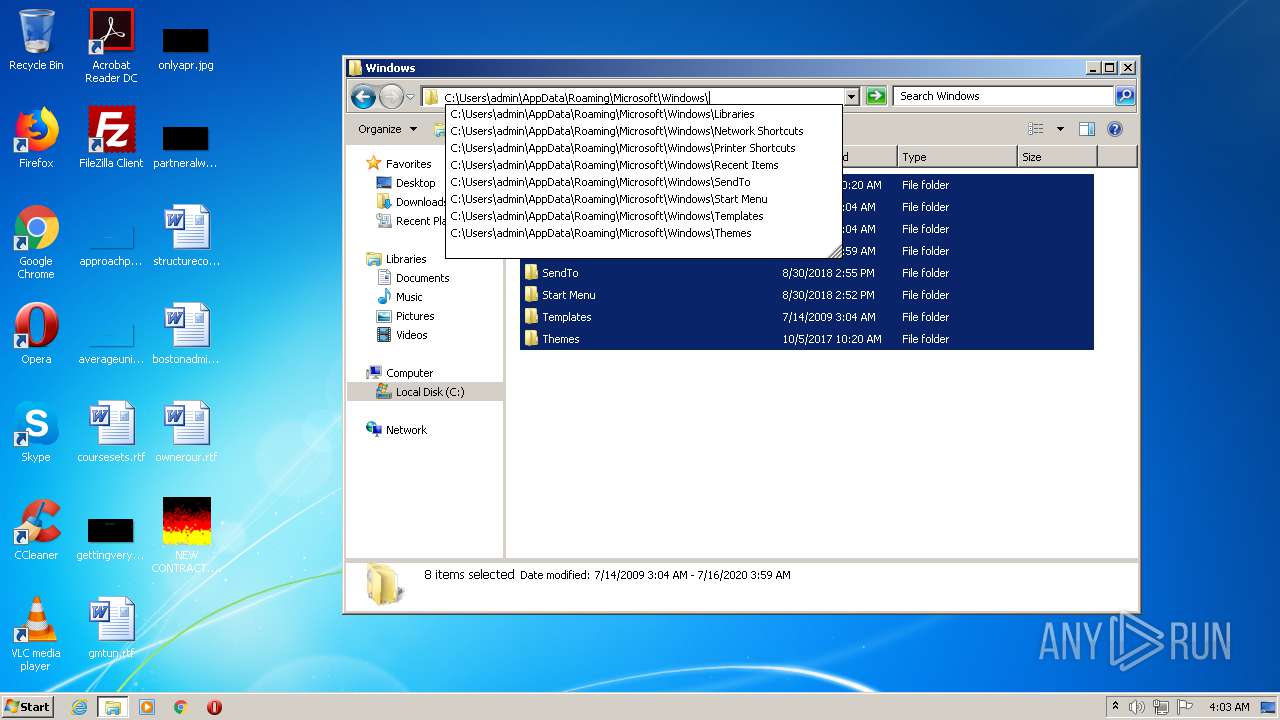
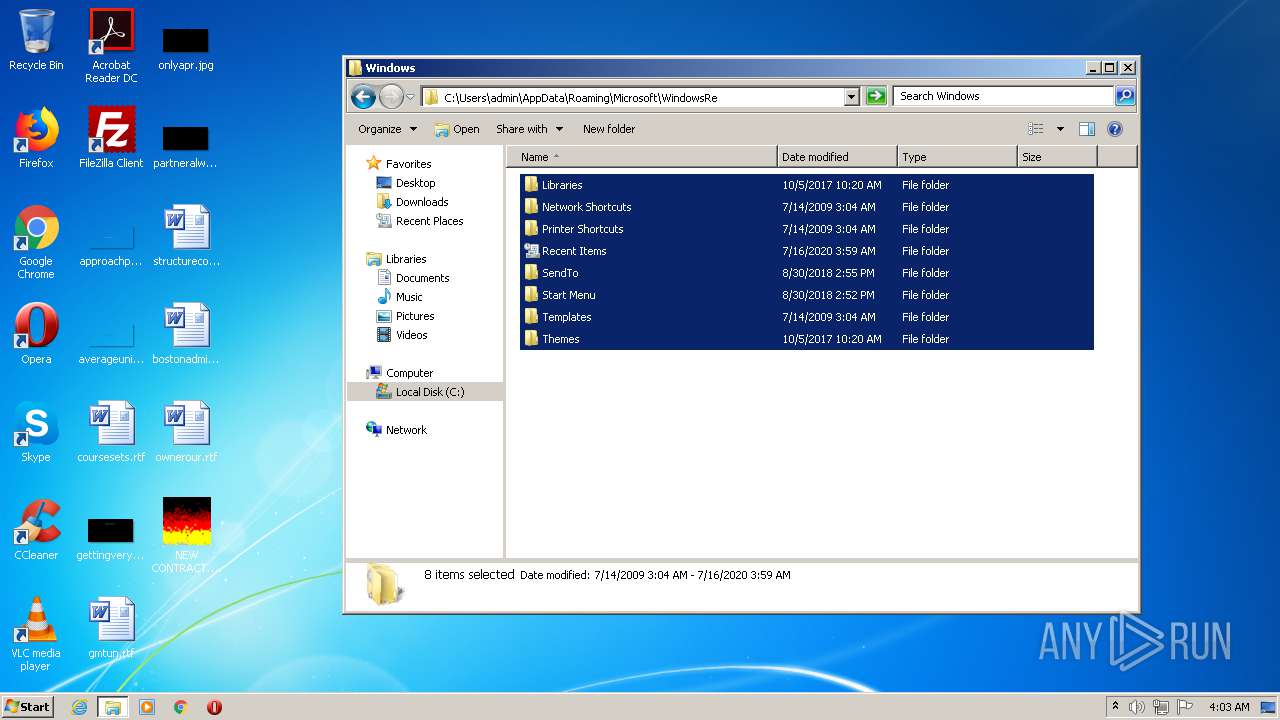
Writes to a start menu file
- NEW CONTRACT.exe (PID: 2772)
AVEMARIA was detected
- NEW CONTRACT.exe (PID: 2772)
- WARZONE.exe (PID: 2712)
Changes the autorun value in the registry
- NEW CONTRACT.exe (PID: 2772)
Loads dropped or rewritten executable
- dism.exe (PID: 608)
- dism.exe (PID: 3840)
Runs injected code in another process
- WARZONE.exe (PID: 2712)
Application was injected by another process
- explorer.exe (PID: 392)
SUSPICIOUS
Starts CMD.EXE for commands execution
- NEW CONTRACT.exe (PID: 2772)
- WARZONE.exe (PID: 2712)
- explorer.exe (PID: 392)
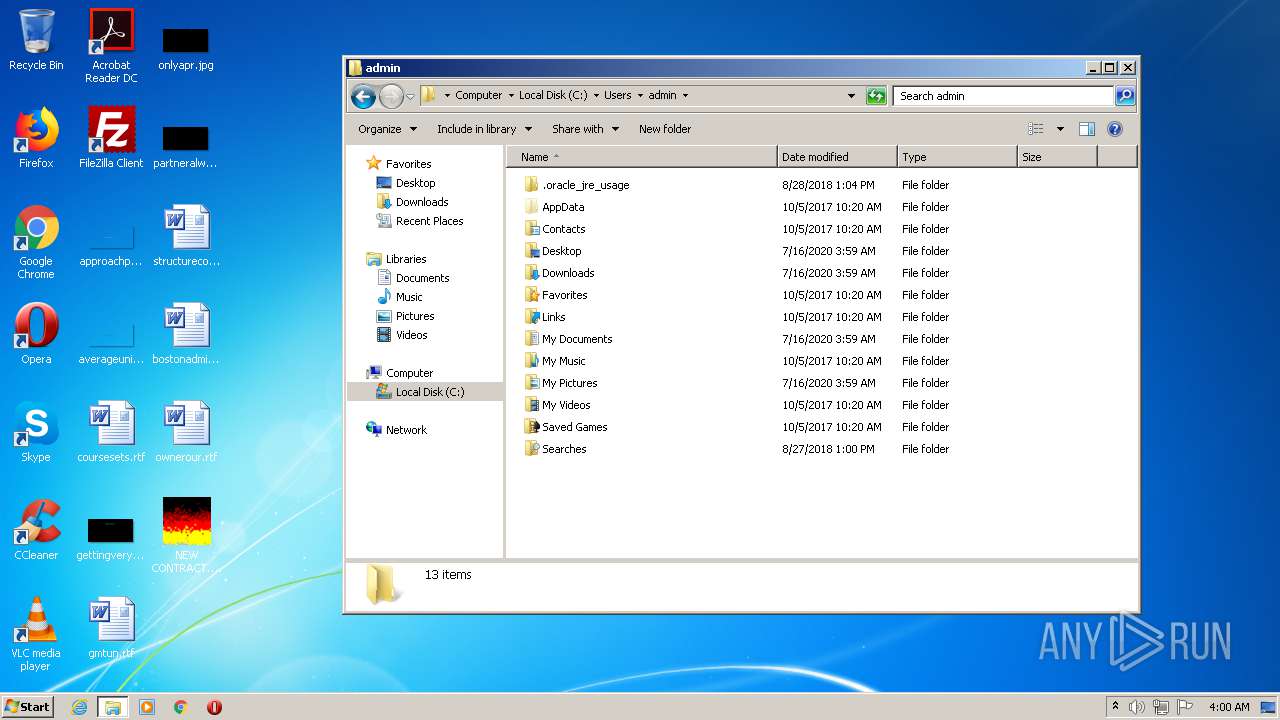
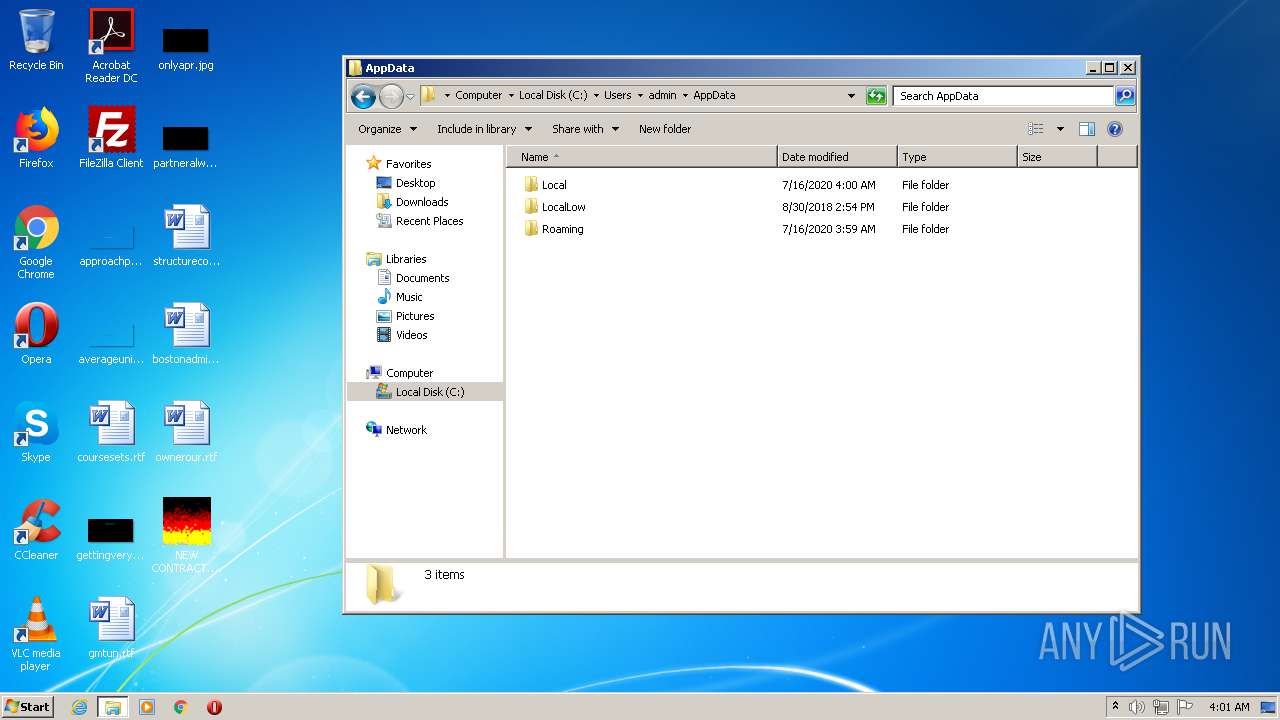
Creates files in the user directory
- NEW CONTRACT.exe (PID: 2772)
- powershell.exe (PID: 1744)
Executable content was dropped or overwritten
- NEW CONTRACT.exe (PID: 2772)
- cmd.exe (PID: 1316)
- DllHost.exe (PID: 2640)
- cmd.exe (PID: 1012)
- DllHost.exe (PID: 3220)
Starts itself from another location
- NEW CONTRACT.exe (PID: 2772)
Executed via COM
- DllHost.exe (PID: 2640)
- DllHost.exe (PID: 3220)
Executes PowerShell scripts
- NEW CONTRACT.exe (PID: 2604)
Uses WMIC.EXE to create a new process
- cmd.exe (PID: 3580)
Executed via WMI
- Roaming:ApplicationData (PID: 3284)
INFO
Manual execution by user
- explorer.exe (PID: 2916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:12 15:51:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 801280 |
| InitializedDataSize: | 749056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5191 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | ATLFire Module |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | ATLFIRE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | ATLFIRE.DLL |
| ProductName: | ATLFire Module |
| ProductVersion: | 1, 0, 0, 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 12-Jul-2020 13:51:49 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | ATLFire Module |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | ATLFIRE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | ATLFIRE.DLL |
| ProductName: | ATLFire Module |
| ProductVersion: | 1, 0, 0, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 12-Jul-2020 13:51:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000C3815 | 0x000C3A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.41056 |
.rdata | 0x000C5000 | 0x0003AD8C | 0x0003AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.6977 |
.data | 0x00100000 | 0x0006EEC4 | 0x0006B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.11235 |
.idata | 0x0016F000 | 0x00002249 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75734 |
.tls | 0x00172000 | 0x00000309 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0111738 |
.00cfg | 0x00173000 | 0x00000104 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0611629 |
.rsrc | 0x00174000 | 0x000024D6 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.4684 |
.reloc | 0x00177000 | 0x00007E7C | 0x00008000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.11209 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
7 | 1.18832 | 46 | UNKNOWN | English - United States | RT_STRING |
101 | 5.17943 | 418 | UNKNOWN | English - United States | REGISTRY |
102 | 2.14614 | 54 | UNKNOWN | English - United States | RT_DIALOG |
103 | 3.06987 | 396 | UNKNOWN | English - United States | RT_DIALOG |
201 | 2.51627 | 42 | UNKNOWN | English - United States | RT_MENU |
202 | 3.29534 | 566 | UNKNOWN | English - United States | RT_DIALOG |
203 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
86
Monitored processes
22
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 608 | "C:\Windows\system32\dism.exe" /online /norestart /apply-unattend:"C:\Users\admin\AppData\Local\Temp\ellocnak.xml" | C:\Windows\system32\dism.exe | — | pkgmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | WARZONE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1316 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | NEW CONTRACT.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1596 | "C:\Users\admin\Desktop\NEW CONTRACT.exe" | C:\Users\admin\Desktop\NEW CONTRACT.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ATLFire Module Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1744 | powershell Add-MpPreference -ExclusionPath C:\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | NEW CONTRACT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2368 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\AppData\Roaming\WARZONE.exe" | C:\Users\admin\AppData\Roaming\WARZONE.exe | — | dism.exe | |||||||||||
User: admin Integrity Level: HIGH Description: ATLFire Module Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2604 | "C:\Users\admin\Desktop\NEW CONTRACT.exe" | C:\Users\admin\Desktop\NEW CONTRACT.exe | dism.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: ATLFire Module Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
5 474
Read events
4 757
Write events
717
Delete events
0
Modification events
| (PID) Process: | (2772) NEW CONTRACT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (2772) NEW CONTRACT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (2772) NEW CONTRACT.exe | Key: | HKEY_CURRENT_USER\Software\_rptls |
| Operation: | write | Name: | Install |
Value: C:\Users\admin\Desktop\NEW CONTRACT.exe | |||
| (PID) Process: | (2772) NEW CONTRACT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\AHWQ3GFZFY |
| Operation: | write | Name: | inst |
Value: ED913ED4939B011A9410852034533CB9B2244C066E9CE104B168901D8B58881C68340919CF4C503FC1339D13CF9E48F1FA60F58FEEA317CE68CD4EF4B0530A148080D067B867718B820C3CFC90476EC0E9EA2E86AE1E | |||
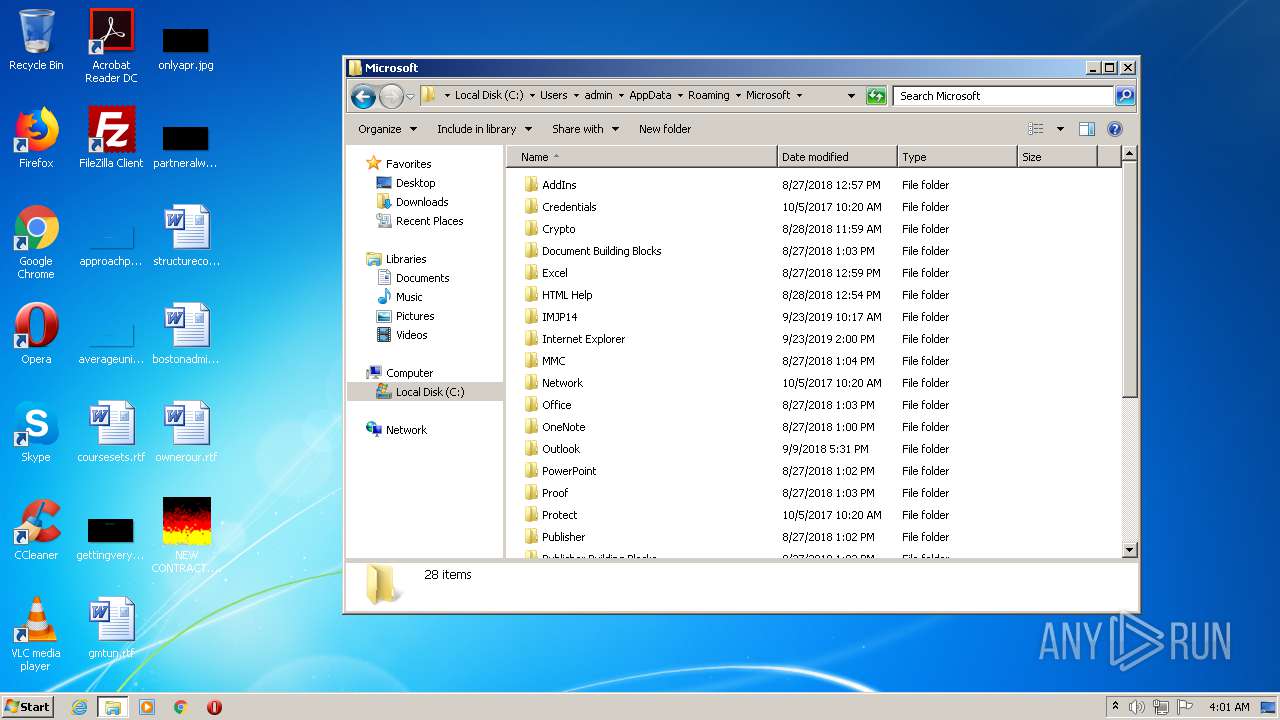
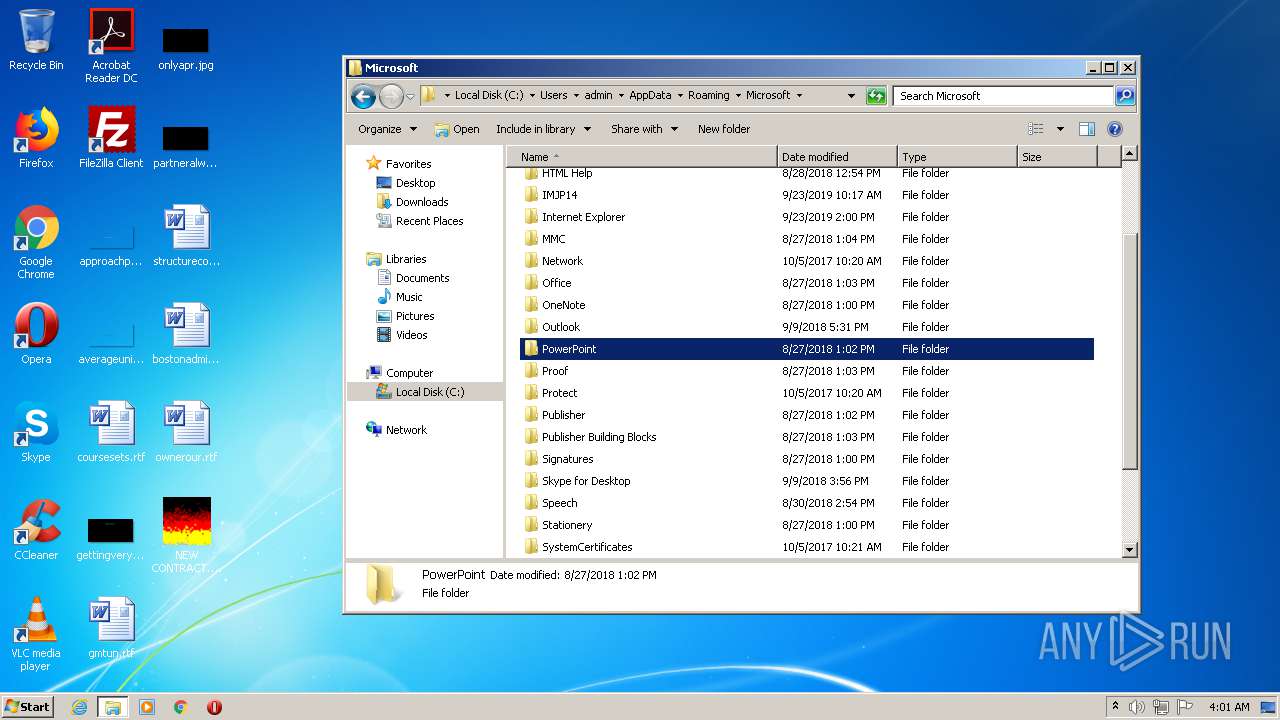
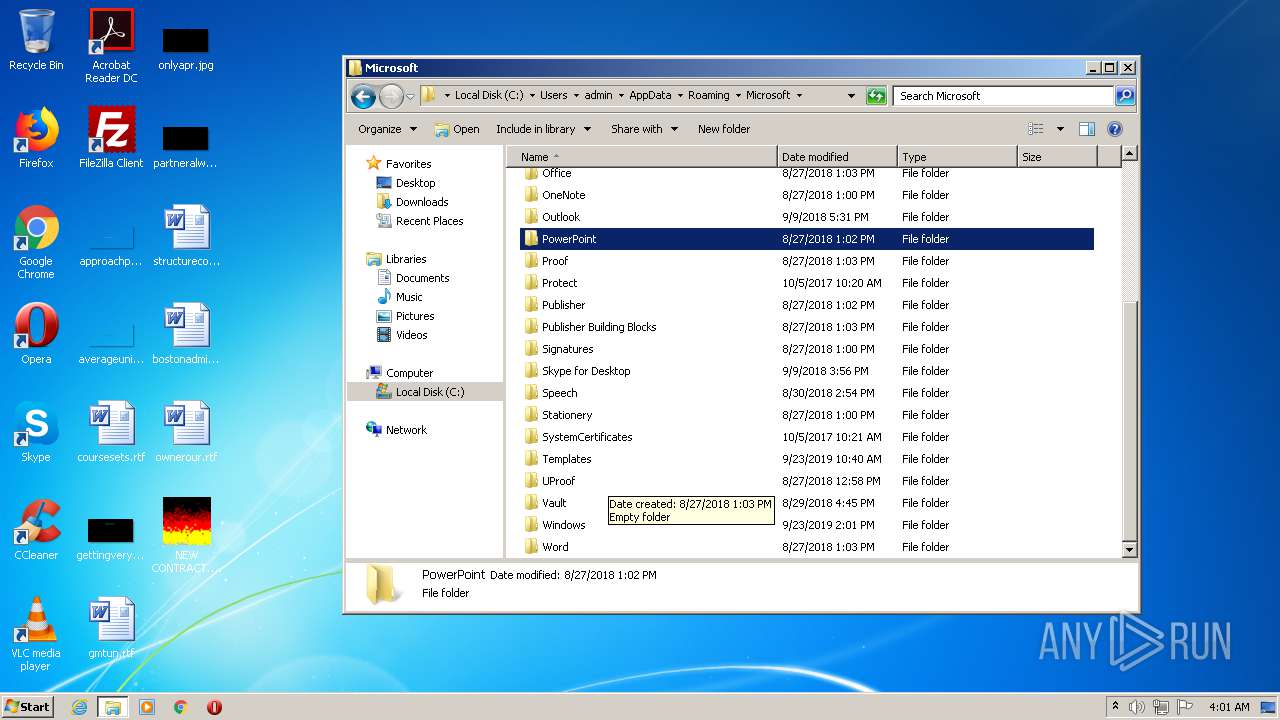
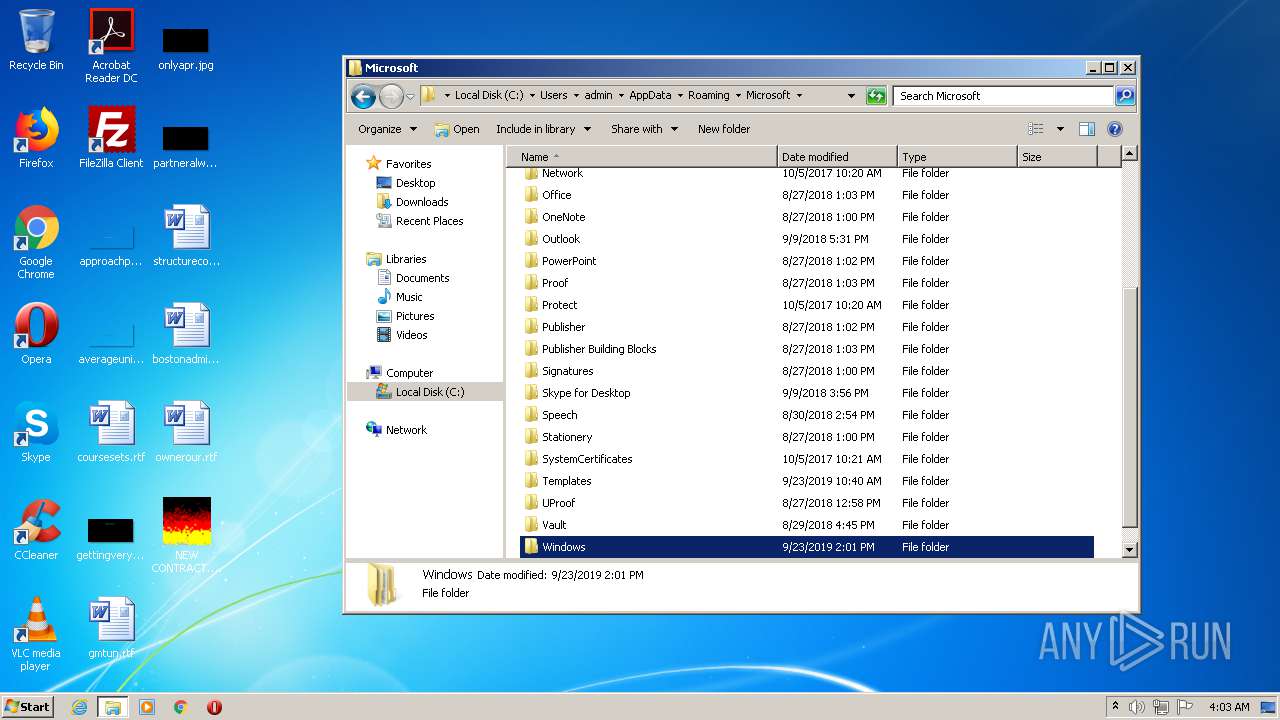
| (PID) Process: | (2772) NEW CONTRACT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | File |
Value: C:\Users\admin\AppData\Roaming\WARZONE.exe | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ebnzvat\JNEMBAR.rkr |
Value: 00000000000000000000000020000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000490000006F000000772C30000C000000250000006D9313007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000030E9C9010000000000000000C0DB2C02050000002000000000000000000000000100000064666C7464666C7400000000400000000459FF754803016300000000000000000100000000000000000000000000000000000000E803000000000000FFFFFFFF000000000000000008B72C02CCE8C90105000000FFFFFFFFAC54FF75000000000000000000000000C054FF754803016308B72C0200000000622902764803016308B72C0205000000D80B2C020000000040EBC90148EBC901C0DB2C02940A2C0220000000000000000000000000000000000000000500000000000000010000006C61746E64666C740000000011000000483D2B00403D2B0000EAC9012261FF754803016320EA0000F71FA3B6D4E9C9018291307620EAC90134A300009B1FA3B6E8E9C901B69C307638A31F024C06000000EAC901A89E1F020CEAC90111000000483D2B00403D2B0000EAC901C89E1F0270EA0000431CA3B620EAC9018291307670EAC90124EAC901279530760000000034A31F024CEAC901CD94307634A31F02F8EAC901A89E1F02E194307600000000A89E1F02F8EAC90154EAC9010C000000250000006D9313007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000030E9C9010000000000000000C0DB2C02050000002000000000000000000000000100000064666C7464666C7400000000400000000459FF754803016300000000000000000100000000000000000000000000000000000000E803000000000000FFFFFFFF000000000000000008B72C02CCE8C90105000000FFFFFFFFAC54FF75000000000000000000000000C054FF754803016308B72C0200000000622902764803016308B72C0205000000D80B2C020000000040EBC90148EBC901C0DB2C02940A2C0220000000000000000000000000000000000000000500000000000000010000006C61746E64666C740000000011000000483D2B00403D2B0000EAC9012261FF754803016320EA0000F71FA3B6D4E9C9018291307620EAC90134A300009B1FA3B6E8E9C901B69C307638A31F024C06000000EAC901A89E1F020CEAC90111000000483D2B00403D2B0000EAC901C89E1F0270EA0000431CA3B620EAC9018291307670EAC90124EAC901279530760000000034A31F024CEAC901CD94307634A31F02F8EAC901A89E1F02E194307600000000A89E1F02F8EAC90154EAC9010C000000250000006D9313007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000030E9C9010000000000000000C0DB2C02050000002000000000000000000000000100000064666C7464666C7400000000400000000459FF754803016300000000000000000100000000000000000000000000000000000000E803000000000000FFFFFFFF000000000000000008B72C02CCE8C90105000000FFFFFFFFAC54FF75000000000000000000000000C054FF754803016308B72C0200000000622902764803016308B72C0205000000D80B2C020000000040EBC90148EBC901C0DB2C02940A2C0220000000000000000000000000000000000000000500000000000000010000006C61746E64666C740000000011000000483D2B00403D2B0000EAC9012261FF754803016320EA0000F71FA3B6D4E9C9018291307620EAC90134A300009B1FA3B6E8E9C901B69C307638A31F024C06000000EAC901A89E1F020CEAC90111000000483D2B00403D2B0000EAC901C89E1F0270EA0000431CA3B620EAC9018291307670EAC90124EAC901279530760000000034A31F024CEAC901CD94307634A31F02F8EAC901A89E1F02E194307600000000A89E1F02F8EAC90154EAC901 | |||
| (PID) Process: | (1316) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1316) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\ARJ PBAGENPG.rkr |
Value: 00000000000000000000000020000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
Executable files
6
Suspicious files
3
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
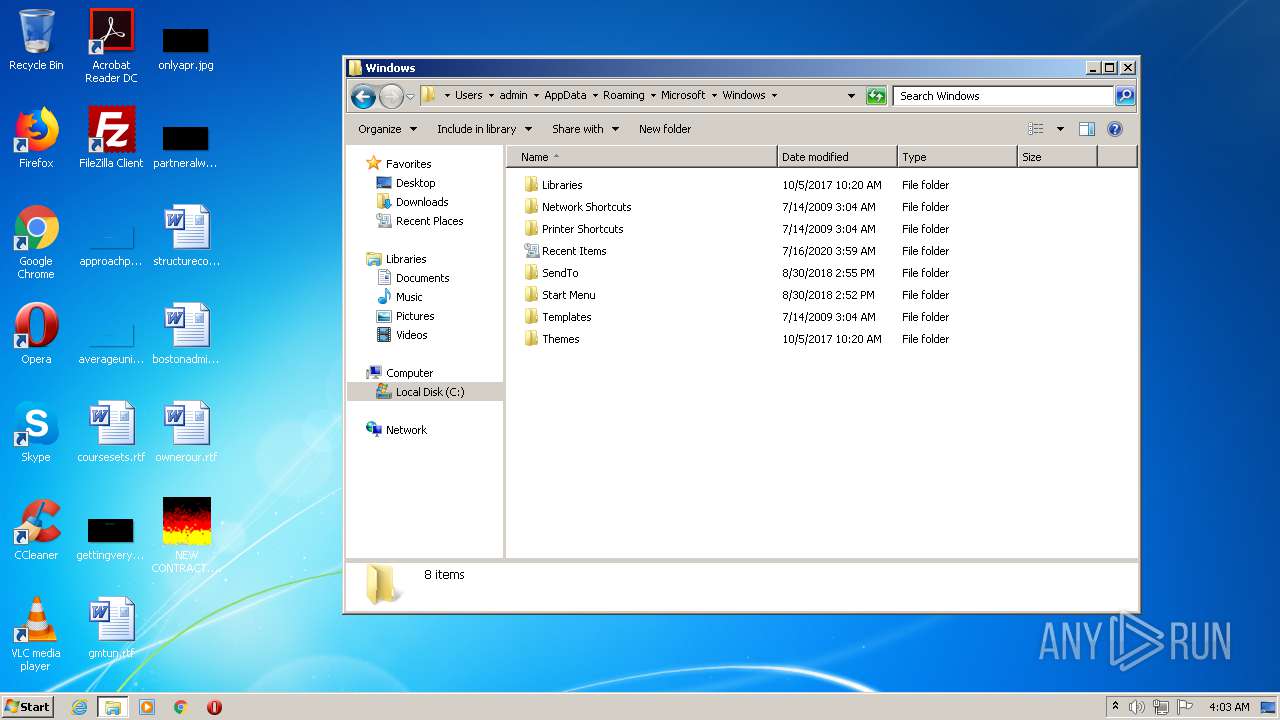
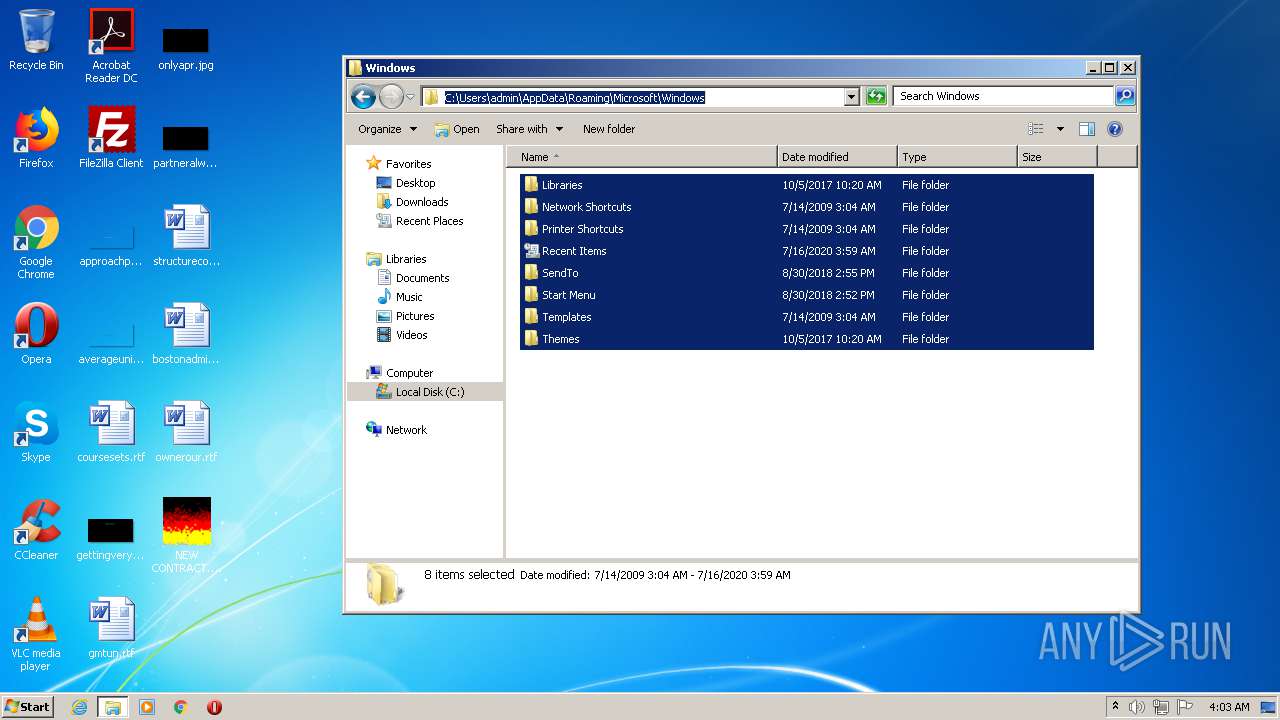
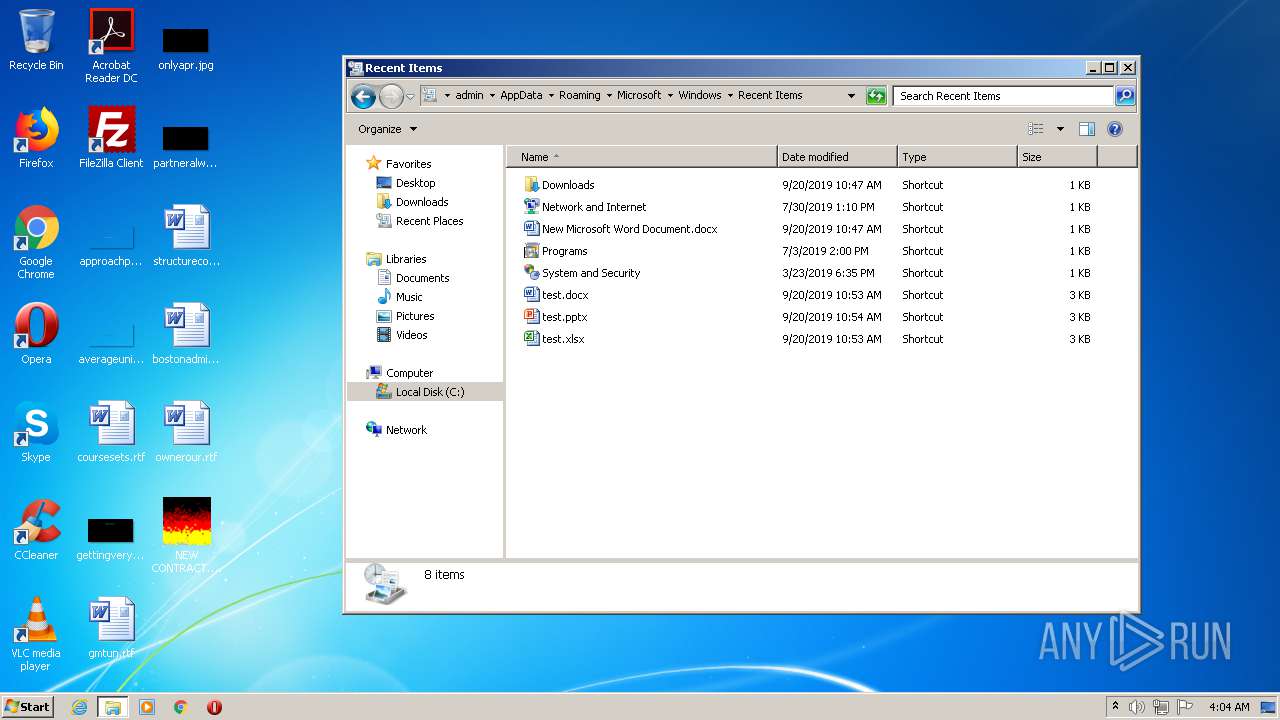
| 1744 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1YVT1L7B742TTHVC4RCY.temp | — | |
MD5:— | SHA256:— | |||
| 2772 | NEW CONTRACT.exe | C:\Users\admin\AppData\Roaming:ApplicationData | executable | |
MD5:— | SHA256:— | |||
| 2068 | pkgmgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
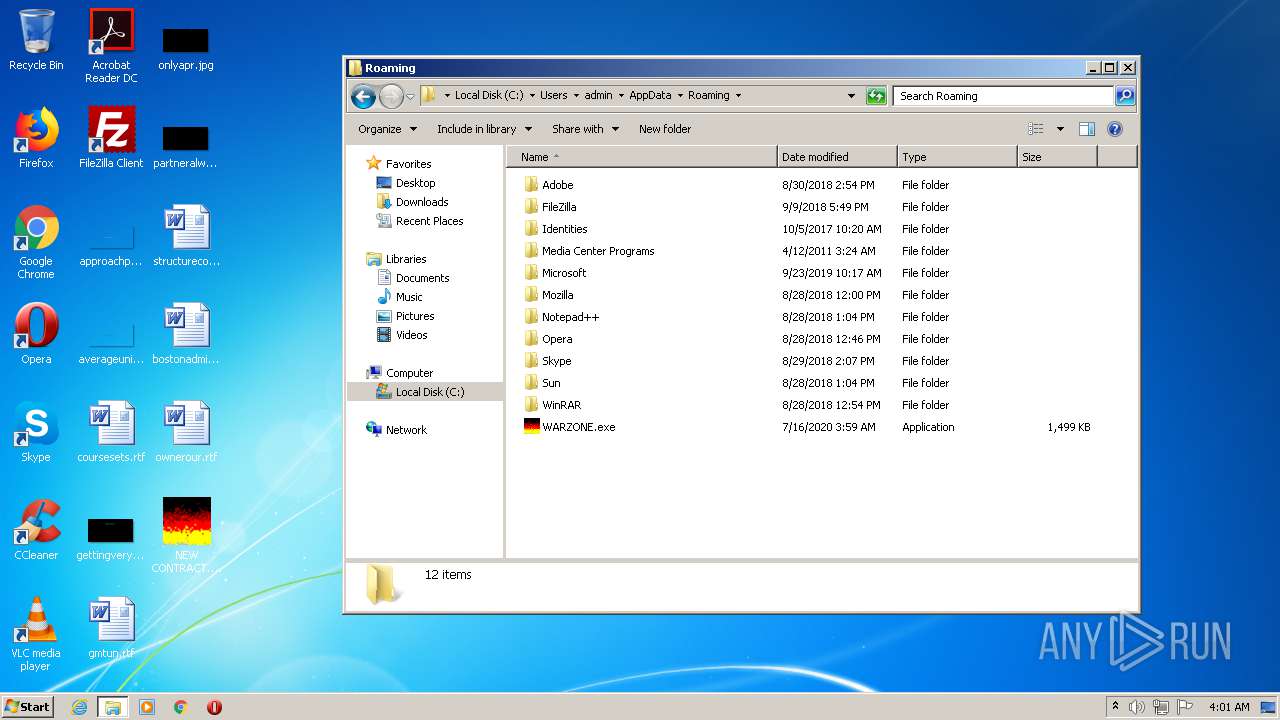
| 2772 | NEW CONTRACT.exe | C:\Users\admin\AppData\Roaming\WARZONE.exe | executable | |
MD5:— | SHA256:— | |||
| 2772 | NEW CONTRACT.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\programs.bat:start | text | |
MD5:6E62E15E16D6F574006D84199029E283 | SHA256:639A177E5FEE4E4805059B2E16A0DA3691CE88B9B0FC83FDA9ECD17AC761F86E | |||
| 1316 | cmd.exe | C:\Users\admin\AppData\Local\Temp\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 1744 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1744 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF24d35e.TMP | binary | |
MD5:— | SHA256:— | |||
| 3200 | pkgmgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
| 1316 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ellocnak.xml | xml | |
MD5:427EB7374887305B72F5C552837C9036 | SHA256:B3F421780A49CBE680A317259D4DF9CE1D0CDACA3020B4DF0DC18CC01D68CCBB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
41
DNS requests
5
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2712 | WARZONE.exe | 185.140.53.13:6389 | agu22.3utilities.com | myLoc managed IT AG | DE | malicious |
2604 | NEW CONTRACT.exe | 185.140.53.13:6389 | agu22.3utilities.com | myLoc managed IT AG | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
agu22.3utilities.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.3utilities .com |
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.3utilities .com |
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.3utilities .com |
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.3utilities .com |
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.3utilities .com |