| File name: | Cdqpbck.exe |
| Full analysis: | https://app.any.run/tasks/0d1d7c02-b567-4c2f-bf13-55bdd3798860 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 17, 2025, 22:58:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 4252188DA5A4C0E6A3E6CEA13885AC9F |
| SHA1: | E110B95728B1940EB6364D3AB911DC32BF7A272F |
| SHA256: | 674A755E4F7BD797D0D0F22C530CED65C4A774D2F522129897CD91C501C64C8A |
| SSDEEP: | 49152:v3oeroqmVzvsDB6vjEfoZQV54RSBKjwb3mOYzBqVSkiWd5FEwpZhoRTekmd4DfPI:vxDyzUaj+kQESIjwazuxrmRTPJQPezPq |
MALICIOUS
Executing a file with an untrusted certificate
- Cdqpbck.exe (PID: 7320)
- Cdqpbck.exe (PID: 7436)
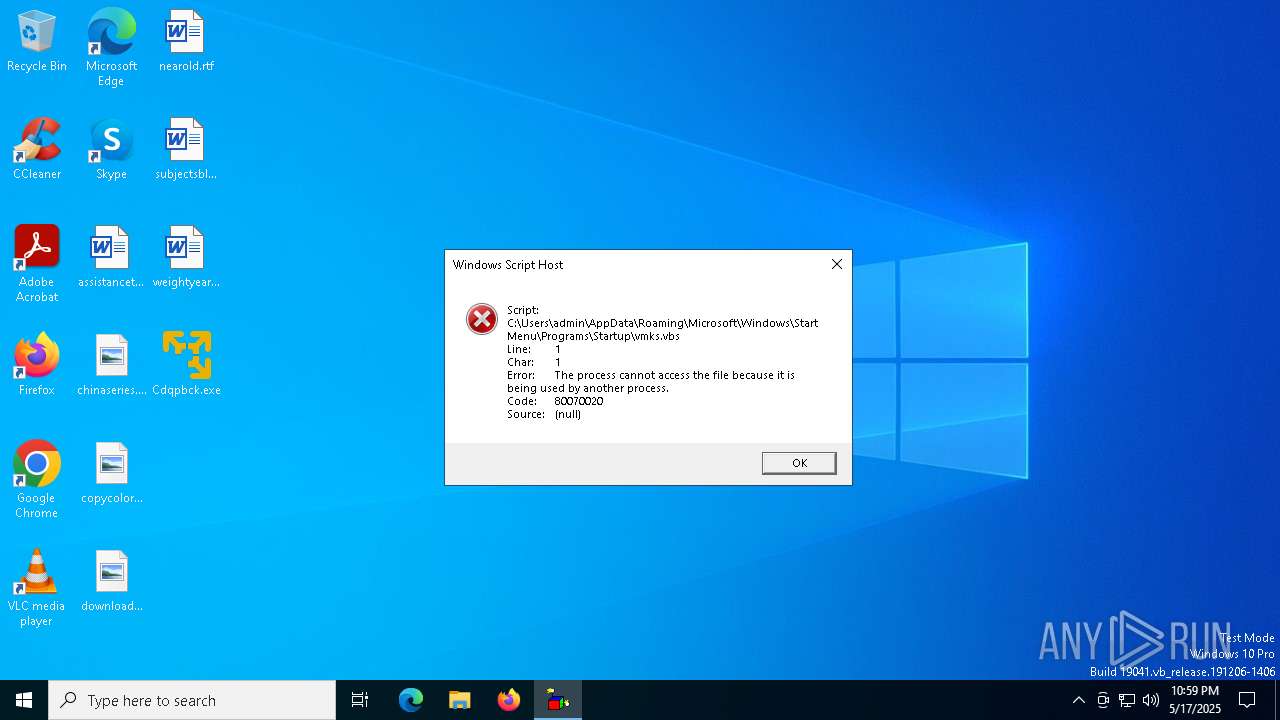
Create files in the Startup directory
- Cdqpbck.exe (PID: 7320)
ASYNCRAT has been detected (MUTEX)
- Cdqpbck.exe (PID: 7436)
ASYNCRAT has been detected (YARA)
- Cdqpbck.exe (PID: 7436)
SUSPICIOUS
Executable content was dropped or overwritten
- wscript.exe (PID: 7360)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7360)
Connects to unusual port
- Cdqpbck.exe (PID: 7436)
INFO
Reads the computer name
- Cdqpbck.exe (PID: 7320)
- Cdqpbck.exe (PID: 7436)
Reads the machine GUID from the registry
- Cdqpbck.exe (PID: 7320)
- Cdqpbck.exe (PID: 7436)
Auto-launch of the file from Startup directory
- Cdqpbck.exe (PID: 7320)
Checks supported languages
- Cdqpbck.exe (PID: 7320)
- Cdqpbck.exe (PID: 7436)
Creates files or folders in the user directory
- Cdqpbck.exe (PID: 7320)
Manual execution by a user
- wscript.exe (PID: 7360)
- Cdqpbck.exe (PID: 7436)
Reads the software policy settings
- slui.exe (PID: 7828)
Checks proxy server information
- slui.exe (PID: 7828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(7436) Cdqpbck.exe
C2 (1)gameto.ath.cx
Ports (1)8888
Version| Edit 3LOSH RAT
Options
AutoRunfalse
MutexAsyncMutex_7SI8OkPnX
InstallFolder%AppData%
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAPeWQ4YJ3MvReCGwLzn7rTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwNDI1MDA0MTA5WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKT9nYYTjYTZhY+g1tekZ8/F29gsEIDgf/8odvCbCmYKGGZZi2yND9NjtBXEMANM9PAXCyMapGva...
Server_SignatureCYVjei9FKzV0hV7yKXGBeIKTDKZ8SWzo86haqOrz5uI3njGTgpAzfEYQ8OZZYo0Q/m+43ZAYKAdbl6nJhJd8hvRUgJhMZhLY2ug7laA48YKm2tbTjiWS5+EnkNXpMnCPw7EHiKb3aL5elHyakJvSvs56mdxTHKCcPnLQXi7klHgU77cz8BbfdfN0GAQX62+ykHcLljsfBKK7LBYvnKmx0gmxOh8MM006p3VlAXe/QBTzeCcFQn74O14zFtdxE+mZ3Sc3tiySRV1zfmqeoppWkwCxqLDc0gteJ+VEsNJRrgJo...
Keys
AESf7bb23ceff624d8de52671ade86248382ddef9b0c4c766bc1085a63be5a72d45
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:12 20:15:33+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 879104 |
| InitializedDataSize: | 163328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd894e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.2.3.21887 |
| ProductVersionNumber: | 16.2.3.21887 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | VMware Workstation |
| CompanyName: | VMware, Inc. |
| FileDescription: | VMware Workstation |
| FileVersion: | 16.2.3.21887 |
| InternalName: | Cdqpbck.exe |
| LegalCopyright: | Copyright © 1998-2022 VMware, Inc. |
| LegalTrademarks: | - |
| OriginalFileName: | Cdqpbck.exe |
| ProductName: | VMware Workstation |
| ProductVersion: | 16.2.3.21887 |
| AssemblyVersion: | 16.2.3.21887 |
Total processes
124
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7320 | "C:\Users\admin\Desktop\Cdqpbck.exe" | C:\Users\admin\Desktop\Cdqpbck.exe | explorer.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Workstation Exit code: 4294967295 Version: 16.2.3.21887 Modules
| |||||||||||||||
| 7360 | wscript "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\vmks.vbs" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7436 | "C:\Users\admin\Desktop\Cdqpbck.exe" | C:\Users\admin\Desktop\Cdqpbck.exe | explorer.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Workstation Version: 16.2.3.21887 Modules
AsyncRat(PID) Process(7436) Cdqpbck.exe C2 (1)gameto.ath.cx Ports (1)8888 Version| Edit 3LOSH RAT Options AutoRunfalse MutexAsyncMutex_7SI8OkPnX InstallFolder%AppData% Certificates Cert1MIIE8jCCAtqgAwIBAgIQAPeWQ4YJ3MvReCGwLzn7rTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwNDI1MDA0MTA5WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKT9nYYTjYTZhY+g1tekZ8/F29gsEIDgf/8odvCbCmYKGGZZi2yND9NjtBXEMANM9PAXCyMapGva... Server_SignatureCYVjei9FKzV0hV7yKXGBeIKTDKZ8SWzo86haqOrz5uI3njGTgpAzfEYQ8OZZYo0Q/m+43ZAYKAdbl6nJhJd8hvRUgJhMZhLY2ug7laA48YKm2tbTjiWS5+EnkNXpMnCPw7EHiKb3aL5elHyakJvSvs56mdxTHKCcPnLQXi7klHgU77cz8BbfdfN0GAQX62+ykHcLljsfBKK7LBYvnKmx0gmxOh8MM006p3VlAXe/QBTzeCcFQn74O14zFtdxE+mZ3Sc3tiySRV1zfmqeoppWkwCxqLDc0gteJ+VEsNJRrgJo... Keys AESf7bb23ceff624d8de52671ade86248382ddef9b0c4c766bc1085a63be5a72d45 Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 7828 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 417
Read events
4 417
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7360 | wscript.exe | C:\Users\admin\AppData\Roaming\vmks.exe | executable | |
MD5:4252188DA5A4C0E6A3E6CEA13885AC9F | SHA256:674A755E4F7BD797D0D0F22C530CED65C4A774D2F522129897CD91C501C64C8A | |||
| 7320 | Cdqpbck.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\vmks.vbs | text | |
MD5:8834736F11C895DA516EF4B2CF840E57 | SHA256:698386DEE0B61B75ACC881B994CD74F9DAB75D4AB5DB3C678E830B55235A1937 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
45
DNS requests
15
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7636 | SIHClient.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7436 | Cdqpbck.exe | 213.209.143.51:8888 | gameto.ath.cx | Moon Dc | DE | malicious |
7636 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7636 | SIHClient.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7636 | SIHClient.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7636 | SIHClient.exe | 13.95.31.18:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
gameto.ath.cx |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to ath .cx Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to ath .cx Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to ath .cx Domain |