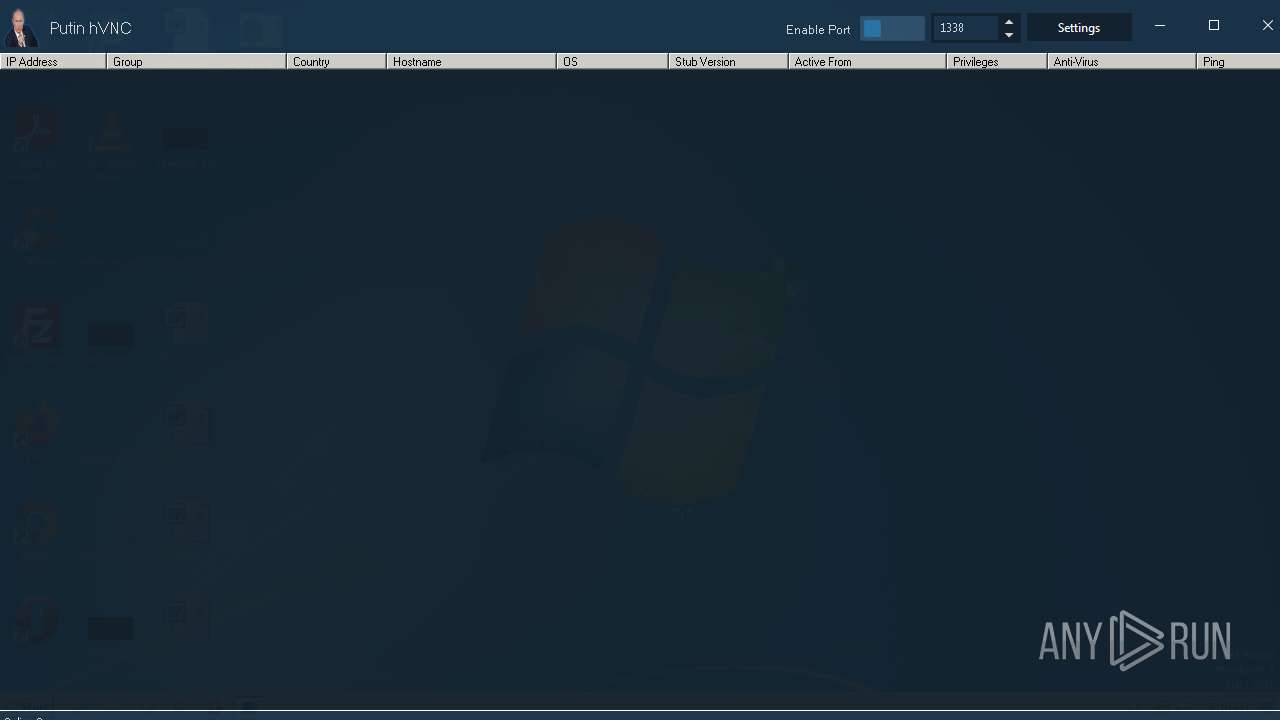
| File name: | Putin HVNC.exe |
| Full analysis: | https://app.any.run/tasks/d4760854-4e2a-4b59-ada5-5ecaaa903308 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | June 14, 2023, 16:10:03 |
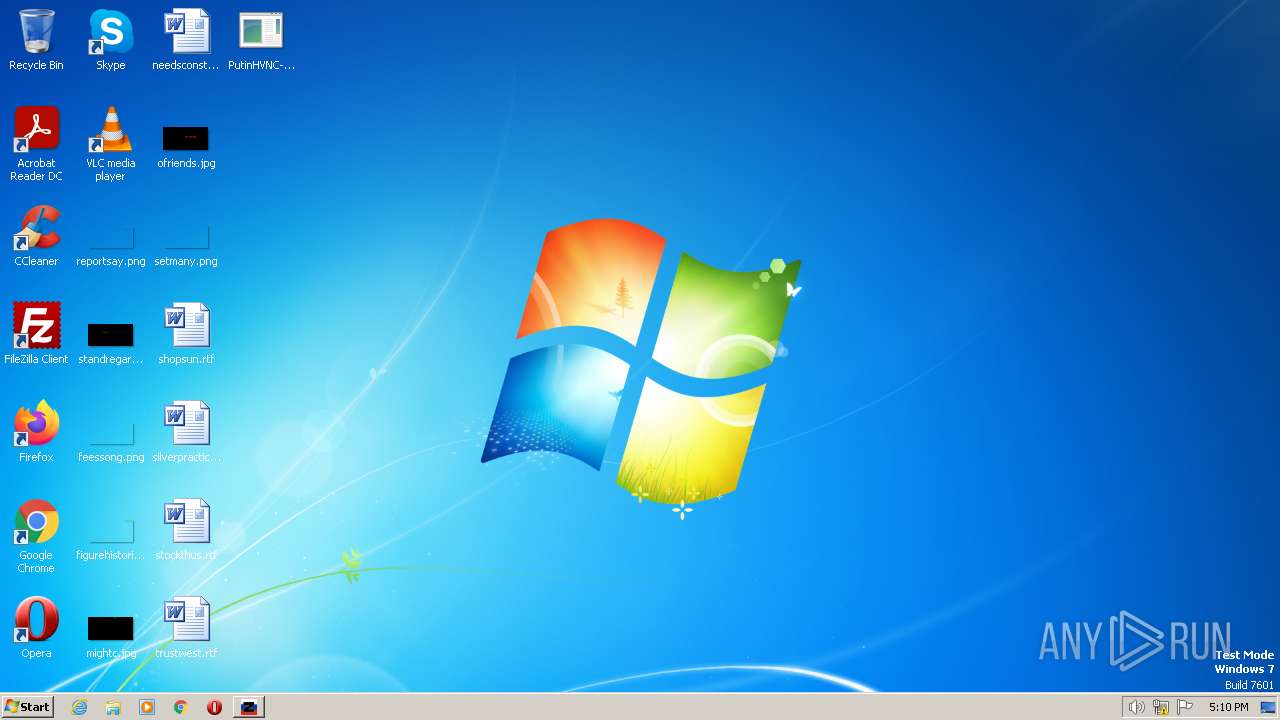
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D02B031B2304B254B88BD2B7BA91DBAF |
| SHA1: | B0F290256F24A2605B228DDD7D61CD5EA58EF00A |
| SHA256: | 6745E6D06F72DA9F03AA75A67E462A3DFB3D04B6DFDC41DD4B1D85E76686CE75 |
| SSDEEP: | 196608:sB+OhopE3jXIpi1DUbVwoDMp4IHkXBNB9B:UopE3TII5EVwSnLxVB |
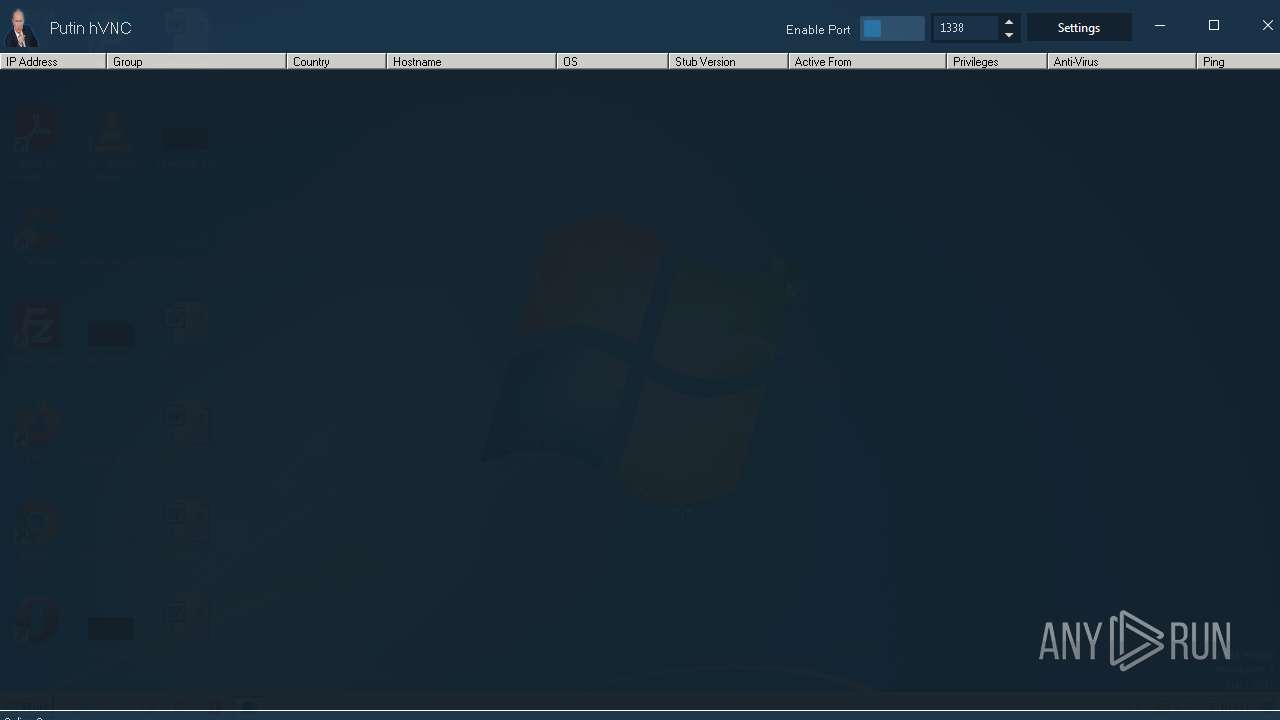
MALICIOUS
Loads dropped or rewritten executable
- PutinHVNC.exe (PID: 3252)
- Builder.exe (PID: 2840)
Application was dropped or rewritten from another process
- PutinHVNC.exe (PID: 3252)
- Test.exe (PID: 3288)
- Builder.exe (PID: 2840)
Uses Task Scheduler to autorun other applications
- Test.exe (PID: 3288)
QUASAR detected by memory dumps
- Test.exe (PID: 3288)
SUSPICIOUS
Reads the Internet Settings
- Putin HVNC.exe (PID: 3260)
- PutinHVNC.exe (PID: 3252)
Executable content was dropped or overwritten
- Putin HVNC.exe (PID: 3260)
- PutinHVNC.exe (PID: 3252)
- Test.exe (PID: 3288)
- Builder.exe (PID: 2840)
INFO
Checks supported languages
- Putin HVNC.exe (PID: 3260)
- PutinHVNC.exe (PID: 3252)
- Test.exe (PID: 3288)
- Builder.exe (PID: 2840)
The process checks LSA protection
- Putin HVNC.exe (PID: 3260)
- PutinHVNC.exe (PID: 3252)
- Test.exe (PID: 3288)
- Builder.exe (PID: 2840)
Reads the computer name
- Putin HVNC.exe (PID: 3260)
- PutinHVNC.exe (PID: 3252)
- Test.exe (PID: 3288)
- Builder.exe (PID: 2840)
Creates files in the program directory
- Putin HVNC.exe (PID: 3260)
Reads the machine GUID from the registry
- PutinHVNC.exe (PID: 3252)
- Builder.exe (PID: 2840)
- Test.exe (PID: 3288)
Reads Environment values
- Test.exe (PID: 3288)
Create files in a temporary directory
- PutinHVNC.exe (PID: 3252)
Creates files or folders in the user directory
- Test.exe (PID: 3288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(3288) Test.exe
Version1.4.1
C2 (2)78.140.241.23:4444
Sub_DirWindows System
Install_Namescupdate.exe
Mutexb6ff6b7f-6e01-4ada-8e62-225309051aaa
StartupWindows Update
TagOffice04
LogDirLogs
SignaturelRj1zocQe8KuE4xiEBXzVZkZ5nVaaVjsZpeq74tlscptz8/xlxblnLpnneuLIKdmqby0ADIeAeItDzXKm8w4tmlxzpVtjv25IcYn40T/vwV/XtnW7ySEVwEdt73TNN453InYy5eF6lLJ2kPKONC8SonN1UhrJ3/vVzeVSAlA2pBDnO+x95z5a4BvFdlK3DI92UFKg0Z9o3DaZxK4MSBj3YwoS162wFs+yjhIZxCQKgNfj8qZMdjBFZlUKCvWpbyV4A2NVl4199Beohf14xDjePqBeyzN0bSSyi7Hnp07OjPQ...
CertificateMIIE9DCCAtygAwIBAgIQALvCNfGYXuxsAlRr0xF2gTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMDMzMDE0NTM0OVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAmN/TSaECs52zv0k6WyzQnYkFxNpQLEoMy9KZdk1geERKdbotdqJzQiFSzRsefmCvaIAPBNr5...
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x15c00 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 187392 |
| CodeSize: | 162816 |
| LinkerVersion: | 14.33 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:01:30 08:18:05+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2023 08:18:05 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 30-Jan-2023 08:18:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00027B2C | 0x00027C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69476 |
.rdata | 0x00029000 | 0x0000A626 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22781 |
.data | 0x00034000 | 0x00035CA0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.15961 |
.didat | 0x0006A000 | 0x00000160 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.02447 |
.rsrc | 0x0006B000 | 0x0001F604 | 0x0001F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.50945 |
.reloc | 0x0008B000 | 0x0000292C | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.69098 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26192 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.13051 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 3.37168 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 3.51914 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 3.62938 | 4264 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 3.89267 | 1128 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.11236 | 440 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
OLEAUT32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
46
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1616 | "C:\Users\admin\AppData\Local\Temp\Putin HVNC.exe" | C:\Users\admin\AppData\Local\Temp\Putin HVNC.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2704 | "schtasks" /create /tn "Windows Update" /sc ONLOGON /tr "C:\Users\admin\AppData\Roaming\Windows System\scupdate.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | Test.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
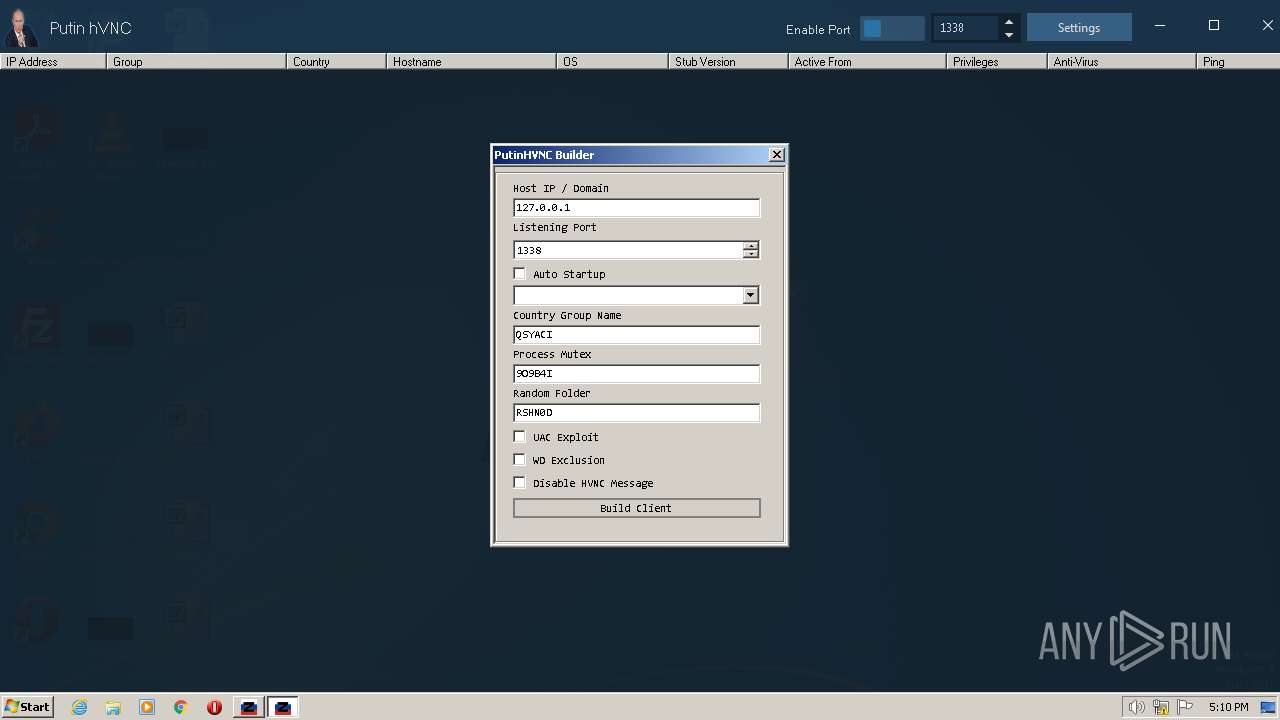
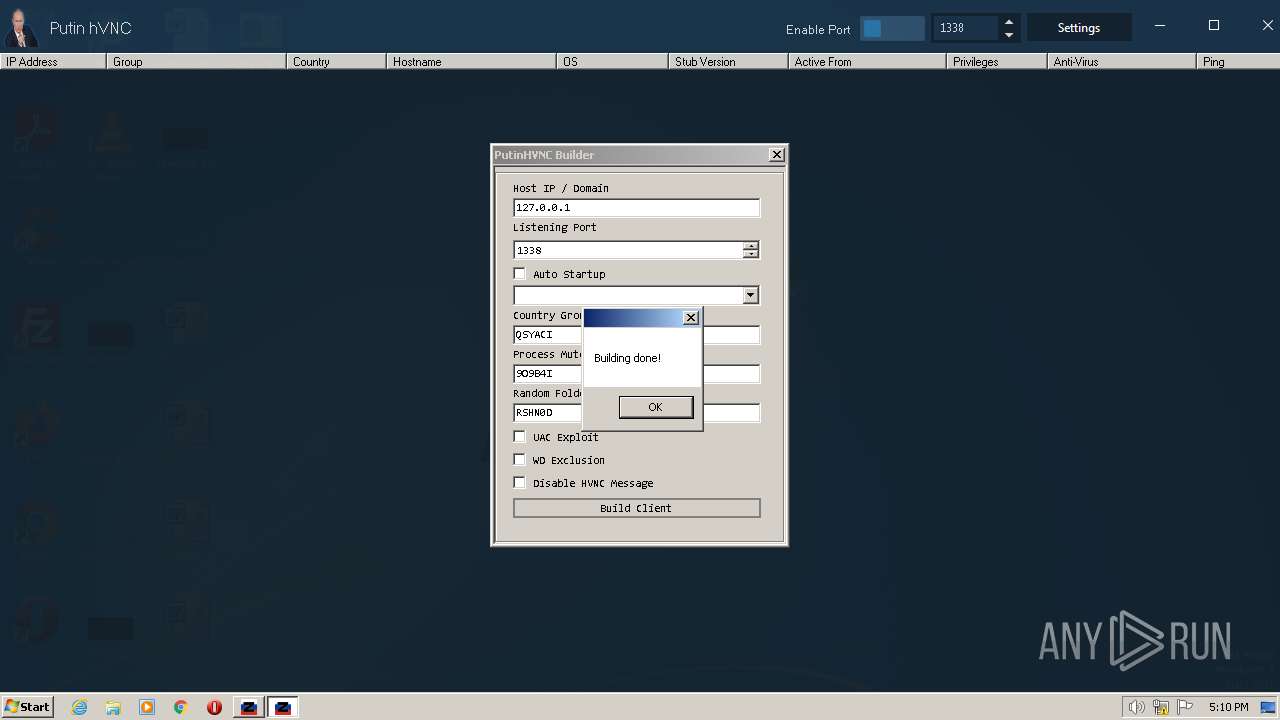
| 2840 | "C:\Program Files\PutinHVNC\Builder.exe" | C:\Program Files\PutinHVNC\Builder.exe | PutinHVNC.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: ClientBuilder Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3252 | "C:\Program Files\PutinHVNC\PutinHVNC.exe" | C:\Program Files\PutinHVNC\PutinHVNC.exe | Putin HVNC.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Putin HVNC Exit code: 0 Version: 1.0.1 Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\Putin HVNC.exe" | C:\Users\admin\AppData\Local\Temp\Putin HVNC.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3288 | "C:\Program Files\PutinHVNC\Test.exe" | C:\Program Files\PutinHVNC\Test.exe | Putin HVNC.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Windows Update Exit code: 0 Version: 1.4.1 Modules
Quasar(PID) Process(3288) Test.exe Version1.4.1 C2 (2)78.140.241.23:4444 Sub_DirWindows System Install_Namescupdate.exe Mutexb6ff6b7f-6e01-4ada-8e62-225309051aaa StartupWindows Update TagOffice04 LogDirLogs SignaturelRj1zocQe8KuE4xiEBXzVZkZ5nVaaVjsZpeq74tlscptz8/xlxblnLpnneuLIKdmqby0ADIeAeItDzXKm8w4tmlxzpVtjv25IcYn40T/vwV/XtnW7ySEVwEdt73TNN453InYy5eF6lLJ2kPKONC8SonN1UhrJ3/vVzeVSAlA2pBDnO+x95z5a4BvFdlK3DI92UFKg0Z9o3DaZxK4MSBj3YwoS162wFs+yjhIZxCQKgNfj8qZMdjBFZlUKCvWpbyV4A2NVl4199Beohf14xDjePqBeyzN0bSSyi7Hnp07OjPQ... CertificateMIIE9DCCAtygAwIBAgIQALvCNfGYXuxsAlRr0xF2gTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMDMzMDE0NTM0OVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAmN/TSaECs52zv0k6WyzQnYkFxNpQLEoMy9KZdk1geERKdbotdqJzQiFSzRsefmCvaIAPBNr5... | |||||||||||||||
Total events
611
Read events
581
Write events
30
Delete events
0
Modification events
| (PID) Process: | (3260) Putin HVNC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3260) Putin HVNC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3260) Putin HVNC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3260) Putin HVNC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3288) Test.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3252) PutinHVNC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3252) PutinHVNC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3252) PutinHVNC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3252) PutinHVNC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
9
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3260 | Putin HVNC.exe | C:\Program Files\PutinHVNC\dnlib.dll | executable | |
MD5:E517EAEABD955F1E0F83ED04A0E6DD86 | SHA256:D04369E2FAFABB36FDC31FC63B9A4BFD2BBA577A203EE8180F9B084D9B344676 | |||
| 3260 | Putin HVNC.exe | C:\Program Files\PutinHVNC\Guna.UI2.dll | executable | |
MD5:D65FD6DBBD3C9AC74139AEAEDC4A5816 | SHA256:84199A22C8669A39800272C3DA0D969EC4E8D77D67B9D324CA049953A5042C71 | |||
| 3260 | Putin HVNC.exe | C:\Program Files\PutinHVNC\client.bin | executable | |
MD5:60B39085C266F364C6B1269AB8FE79F5 | SHA256:AD45703EBDFD43596469416BC9E24374D77A6F361057A31B6CC659789522DA75 | |||
| 3260 | Putin HVNC.exe | C:\Program Files\PutinHVNC\Builder.exe | executable | |
MD5:11B490224802ACE8325DA73A76ED5B13 | SHA256:B13A6113422BB032F9EF8B8E4979F3AE7CC394A4EBB901467FDA8F96843E3FE2 | |||
| 3260 | Putin HVNC.exe | C:\Program Files\PutinHVNC\PutinHVNC.exe | executable | |
MD5:EA62C745965DD9937B6D48BA9C7580A8 | SHA256:6A82AA281E80EAA7FE8694C79C7741706A5DB8A7D626F5AB230AF0A91484205B | |||
| 3252 | PutinHVNC.exe | C:\Users\admin\AppData\Local\Temp\1a5fdae6-8f46-4b8b-a738-d6572f690d43\AgileDotNetRT.dll | executable | |
MD5:14FF402962AD21B78AE0B4C43CD1F194 | SHA256:FB9646CB956945BDC503E69645F6B5316D3826B780D3C36738D6B944E884D15B | |||
| 3288 | Test.exe | C:\Users\admin\AppData\Roaming\Windows System\scupdate.exe | executable | |
MD5:D9889F7FC1978C5BBF52EA0296172558 | SHA256:AAA7D0657CA026FE8EDCCEB83E69B5135D6CF7203CE398B0FC2975A8D3E2D0D8 | |||
| 3260 | Putin HVNC.exe | C:\Program Files\PutinHVNC\Test.exe | executable | |
MD5:D9889F7FC1978C5BBF52EA0296172558 | SHA256:AAA7D0657CA026FE8EDCCEB83E69B5135D6CF7203CE398B0FC2975A8D3E2D0D8 | |||
| 2840 | Builder.exe | C:\Users\admin\Desktop\PutinHVNC-Built.exe | executable | |
MD5:ABE5A99A1F996967EC409675BF106389 | SHA256:2075B8FC230AA3D0493700DE838BAE7646DC41EABDD857D9E148503CC30B3755 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4052 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |