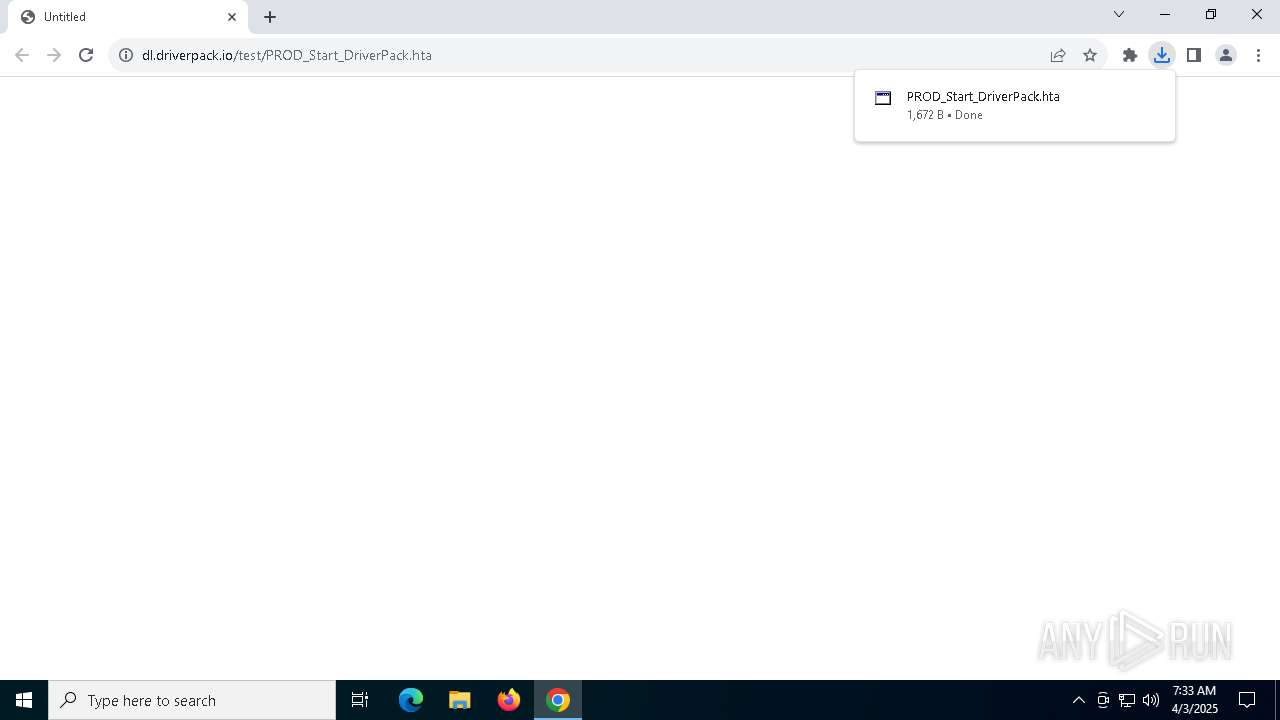
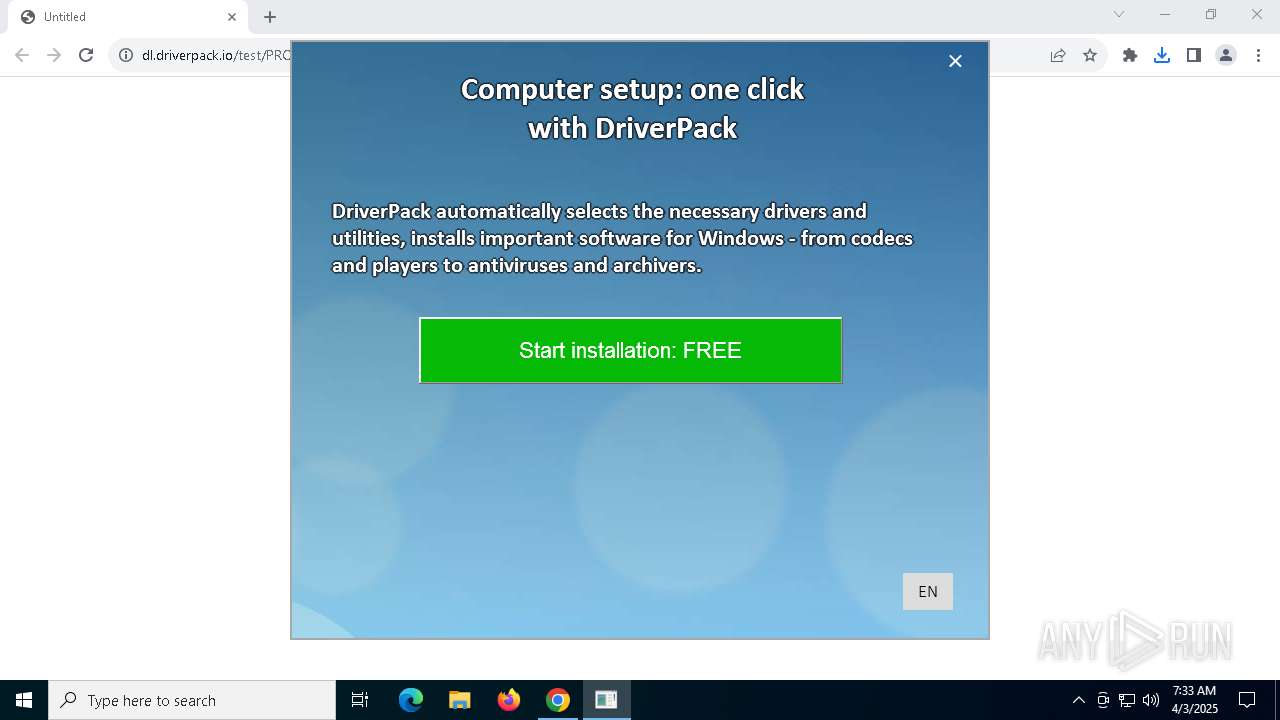
| URL: | https://dl.driverpack.io/test/PROD_Start_DriverPack.hta |
| Full analysis: | https://app.any.run/tasks/df8cea55-f232-48d9-ba05-d536c5bf89d5 |
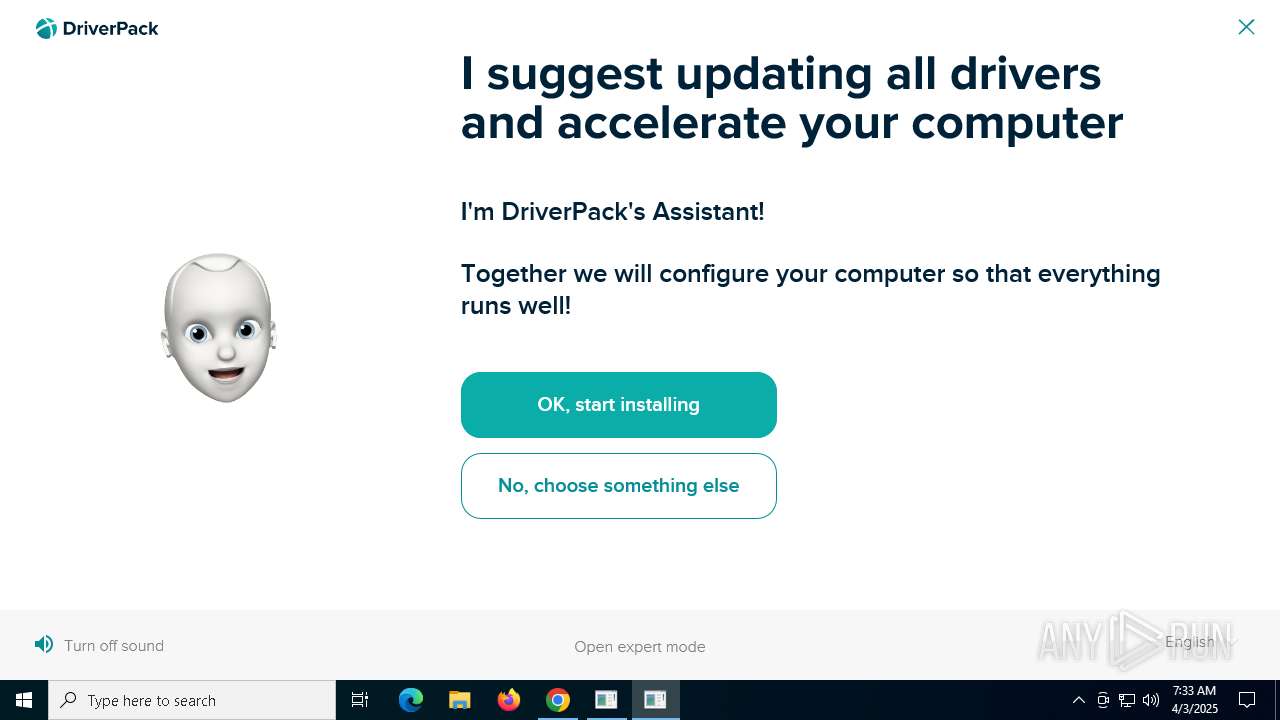
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | April 03, 2025, 07:32:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 55A01024808C6070D65C1907495AD846 |
| SHA1: | DCC21E792ABF600EFEABB70ED085D07A31826EC8 |
| SHA256: | 66E747E4F85A0FA8B1CFC19E3E79542CF89ECAC7C6B87376C706E582E884B687 |
| SSDEEP: | 3:N8RdSAXJOL+q10+ru:27SAQqqSGu |
MALICIOUS
Downloads files via BITSADMIN.EXE
- cmd.exe (PID: 5868)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7832)
Bypass execution policy to execute commands
- powershell.exe (PID: 7724)
Starts Visual C# compiler
- powershell.exe (PID: 7724)
ADWARE has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5868)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 856)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 4152)
Found strings related to reading or modifying Windows Defender settings
- mshta.exe (PID: 1164)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 1164)
- cmd.exe (PID: 8064)
- mshta.exe (PID: 5200)
The process verifies whether the antivirus software is installed
- mshta.exe (PID: 1164)
Query Microsoft Defender status
- mshta.exe (PID: 1164)
- cmd.exe (PID: 7868)
Cmdlet gets the status of antimalware software installed on the computer
- cmd.exe (PID: 7868)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7868)
- cmd.exe (PID: 7832)
Unpacks CAB file
- expand.exe (PID: 7708)
The executable file from the user directory is run by the CMD process
- 7za.exe (PID: 7404)
Executing commands from a ".bat" file
- mshta.exe (PID: 1164)
- cmd.exe (PID: 8064)
Application launched itself
- cmd.exe (PID: 8064)
- mshta.exe (PID: 1164)
Executing commands from ".cmd" file
- mshta.exe (PID: 5200)
The process hide an interactive prompt from the user
- cmd.exe (PID: 7832)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 7832)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7832)
Get information on the list of running processes
- cmd.exe (PID: 7832)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7832)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 7508)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6700)
Uses .NET C# to load dll
- powershell.exe (PID: 7724)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 5428)
Process requests binary or script from the Internet
- mshta.exe (PID: 1164)
Access to an unwanted program domain was detected
- svchost.exe (PID: 2196)
INFO
Application launched itself
- chrome.exe (PID: 4244)
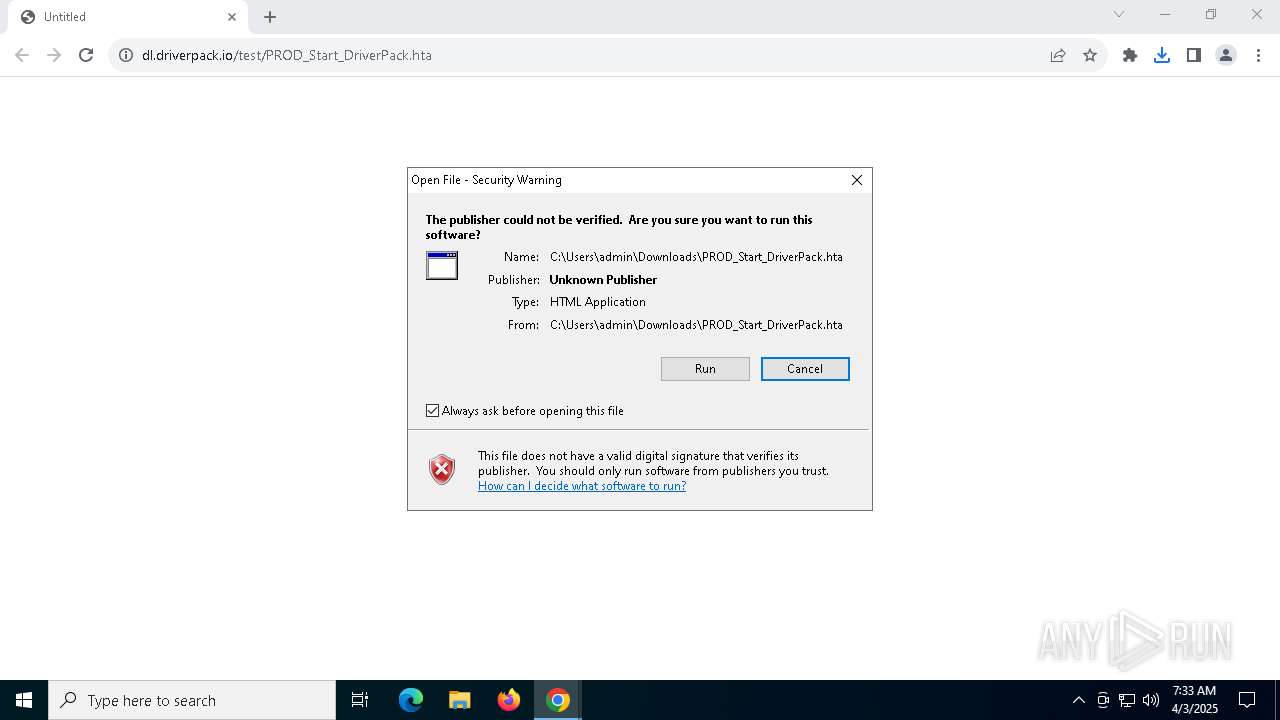
Autorun file from Downloads
- chrome.exe (PID: 4244)
- chrome.exe (PID: 7684)
Reads Microsoft Office registry keys
- chrome.exe (PID: 4244)
Reads Internet Explorer settings
- mshta.exe (PID: 1164)
- mshta.exe (PID: 5200)
- mshta.exe (PID: 872)
Checks proxy server information
- mshta.exe (PID: 1164)
- mshta.exe (PID: 5200)
- mshta.exe (PID: 872)
Uses BITSADMIN.EXE
- cmd.exe (PID: 7968)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 4152)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 856)
Reads the machine GUID from the registry
- expand.exe (PID: 7708)
- csc.exe (PID: 6700)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4428)
Create files in a temporary directory
- 7za.exe (PID: 7404)
- expand.exe (PID: 7708)
- cvtres.exe (PID: 7988)
Checks supported languages
- expand.exe (PID: 7708)
- 7za.exe (PID: 7404)
- csc.exe (PID: 6700)
Reads the computer name
- 7za.exe (PID: 7404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
247
Monitored processes
117
Malicious processes
3
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Windows\System32\cmd.exe" /c bitsadmin /info dwnl-task-50434 | findstr /V /C:"BITSADMIN version" /C:"BITS administration" /C:"(C) Copyright" /C:"BITSAdmin is deprecated" /C:"Administrative tools" | findstr /R /V "^f7f81a39-5f63-5b42-9efd-1f13b5431005quot; > "C:\Users\admin\AppData\Local\Temp\dwnl_50434\log_bits_info.txt" | C:\Windows\SysWOW64\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | C:\WINDOWS\system32\mshta.exe "http://dwrapper-prod.herokuapp.com/bin/watcher.html" | C:\Windows\SysWOW64\mshta.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | "tools\driverpack-wget.exe" --tries=3 --timeout 5 --retry-connrefused --wait=5 --timestamping --directory-prefix="C:\Users\admin\AppData\Local\Temp\beetle-cab\DriverPack\audio\en" "http://dl.driverpack.io/assistant/beetle/audio/en/TEAM-PROOF-3.mp3" -o "C:\Users\admin\AppData\Roaming\DRPSu\temp\wget_log_9907.log" | C:\Users\admin\AppData\Local\Temp\beetle-cab\DriverPack\Tools\driverpack-wget.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH | |||||||||||||||
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1164 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\Downloads\PROD_Start_DriverPack.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | findstr /V /C:"BITSADMIN version" /C:"BITS administration" /C:"(C) Copyright" /C:"BITSAdmin is deprecated" /C:"Administrative tools" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | "C:\Windows\System32\cmd.exe" /c ""tools\driverpack-wget.exe" --tries=3 --timeout 5 --retry-connrefused --wait=5 --timestamping --directory-prefix="C:\Users\admin\AppData\Local\Temp\beetle-cab\DriverPack\audio\en" "http://dl.driverpack.io/assistant/beetle/audio/en/CONTINUOUS-1.mp3" -o "C:\Users\admin\AppData\Roaming\DRPSu\temp\wget_log_12519.log" & echo DONE > "C:\Users\admin\AppData\Roaming\DRPSu\temp\wget_finished_12519.txt"" | C:\Windows\SysWOW64\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 1272 | bitsadmin /info dwnl-task-50434 | C:\Windows\SysWOW64\bitsadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BITS administration utility Exit code: 0 Version: 7.8.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | bitsadmin /info dwnl-task-50434 | C:\Windows\SysWOW64\bitsadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BITS administration utility Exit code: 0 Version: 7.8.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | bitsadmin /info dwnl-task-50434 | C:\Windows\SysWOW64\bitsadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BITS administration utility Exit code: 0 Version: 7.8.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 216
Read events
20 184
Write events
32
Delete events
0
Modification events
| (PID) Process: | (4244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4244) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7684) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000005400A7A06AA4DB01 | |||
| (PID) Process: | (4244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.hta\OpenWithProgids |
| Operation: | write | Name: | htafile |
Value: | |||
| (PID) Process: | (1164) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1164) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1164) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
45
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10dd42.TMP | — | |
MD5:— | SHA256:— | |||
| 4244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10dd42.TMP | — | |
MD5:— | SHA256:— | |||
| 4244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10dd42.TMP | — | |
MD5:— | SHA256:— | |||
| 4244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10dd42.TMP | — | |
MD5:— | SHA256:— | |||
| 4244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10dd42.TMP | — | |
MD5:— | SHA256:— | |||
| 4244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10dd52.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
78
TCP/UDP connections
43
DNS requests
32
Threats
53
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1164 | mshta.exe | GET | 200 | 54.73.53.134:80 | http://dwrapper-prod.herokuapp.com/bin/img/background.jpg | unknown | — | — | whitelisted |
1164 | mshta.exe | GET | 200 | 54.73.53.134:80 | http://dwrapper-prod.herokuapp.com/bin/src/missing-scripts-detector.js | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1164 | mshta.exe | GET | 404 | 18.195.235.189:80 | http://exampledd.matomo.cloud/matomo.php?idsite=1&rec=1&rand=97256501&apiv=1&cookie=1&bots=1&res=1280x720&h=7&m=33&s=23&uid=2162421366202543&action_name=Wrapper%20%2F%20SystemInfo%20%2F%20Data&e_c=Wrapper%20%2F%20SystemInfo%20%2F%20Data&e_a=Windows%2010%20x64%20IE9%20isNotFresh&e_n=&e_v=&ca=1&url=https%3A%2F%2Fmy-domain.com%2Fsystem_info.html%3Fwrapper_version%3D0.14%26windows_version%3DWindows%252010%26buildnumber%3D19045%26is64%3Dtrue%26Arc%3Dx64%26ievers%3D7%26ierealvers%3D9%26jsversion%3D11.0%26lang%3Den-us%26lang_short%3Den%26windows_is_fresh%3Dfalse | unknown | — | — | unknown |
1164 | mshta.exe | GET | 200 | 54.73.53.134:80 | http://dwrapper-prod.herokuapp.com/bin/src/variables/1.js | unknown | — | — | whitelisted |
1164 | mshta.exe | GET | 200 | 54.73.53.134:80 | http://dwrapper-prod.herokuapp.com/bin/src/variables/3.js | unknown | — | — | whitelisted |
1164 | mshta.exe | GET | 200 | 54.73.53.134:80 | http://dwrapper-prod.herokuapp.com/bin/src/variables/5.js | unknown | — | — | whitelisted |
1164 | mshta.exe | GET | 200 | 54.73.53.134:80 | http://dwrapper-prod.herokuapp.com/bin/src/statistics.js | unknown | — | — | whitelisted |
1164 | mshta.exe | GET | 200 | 54.73.53.134:80 | http://dwrapper-prod.herokuapp.com/bin/src/systeminfo.js | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 20.7.2.167:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7236 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
4244 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7236 | chrome.exe | 87.117.239.150:443 | dl.driverpack.io | Iomart Cloud Services Limited | GB | whitelisted |
7236 | chrome.exe | 172.217.16.142:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
7236 | chrome.exe | 172.217.16.196:443 | www.google.com | GOOGLE | US | whitelisted |
6544 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
dl.driverpack.io |
| whitelisted |
accounts.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud Application Platform (.herokuapp .com) |
1164 | mshta.exe | A Network Trojan was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud-Hosted Matomo Analytics (matomo .cloud) |
1164 | mshta.exe | A Network Trojan was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud Application Platform (.herokuapp .com) |
1164 | mshta.exe | Potentially Bad Traffic | ET HUNTING PowerShell DownloadFile Command Common In Powershell Stagers |
5200 | mshta.exe | Potentially Bad Traffic | ET INFO HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2196 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP DriverPack Domain in DNS Query |
5200 | mshta.exe | Potentially Bad Traffic | ET INFO HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2196 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP DriverPack Domain in DNS Query |