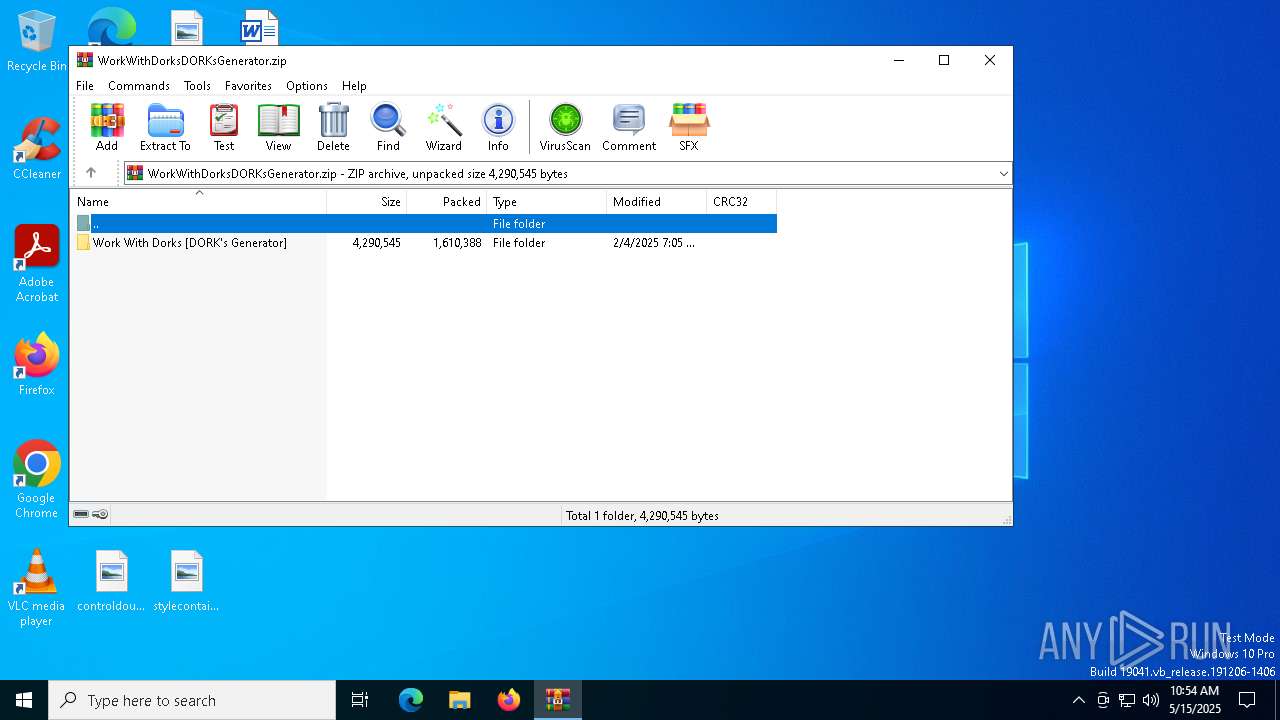
| File name: | WorkWithDorksDORKsGenerator.zip |
| Full analysis: | https://app.any.run/tasks/9758b12c-fb8f-40ca-b85f-a2a42c68a4f6 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 15, 2025, 10:54:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 8116F53344E6BE2A0FC592DC40898A03 |
| SHA1: | 364FB9CEDC4E4EC0DB45E3E7C7886874EB3AAD48 |
| SHA256: | 66CD9E93515C5B36FD6BE40B7958F643319EDE23DB768C44DF2FF0CA6CF535E8 |
| SSDEEP: | 49152:TpgbPKNN4PGqt5Rt0epYvQwAumi/YDjOB0+FX4RLNiegxkw5xNQ5/PG9WQ9c/Sub:COXOGqt5Rt0tHmVqB0+FXyigwa529Wws |
MALICIOUS
Create files in the Startup directory
- Service.exe (PID: 8180)
Changes the autorun value in the registry
- GreenField.exe (PID: 5048)
- GreenField.exe (PID: 7336)
ASYNCRAT has been detected (MUTEX)
- zxc.exe (PID: 856)
- zxc.exe (PID: 4304)
RAT has been found (auto)
- GreenField.exe (PID: 5048)
SUSPICIOUS
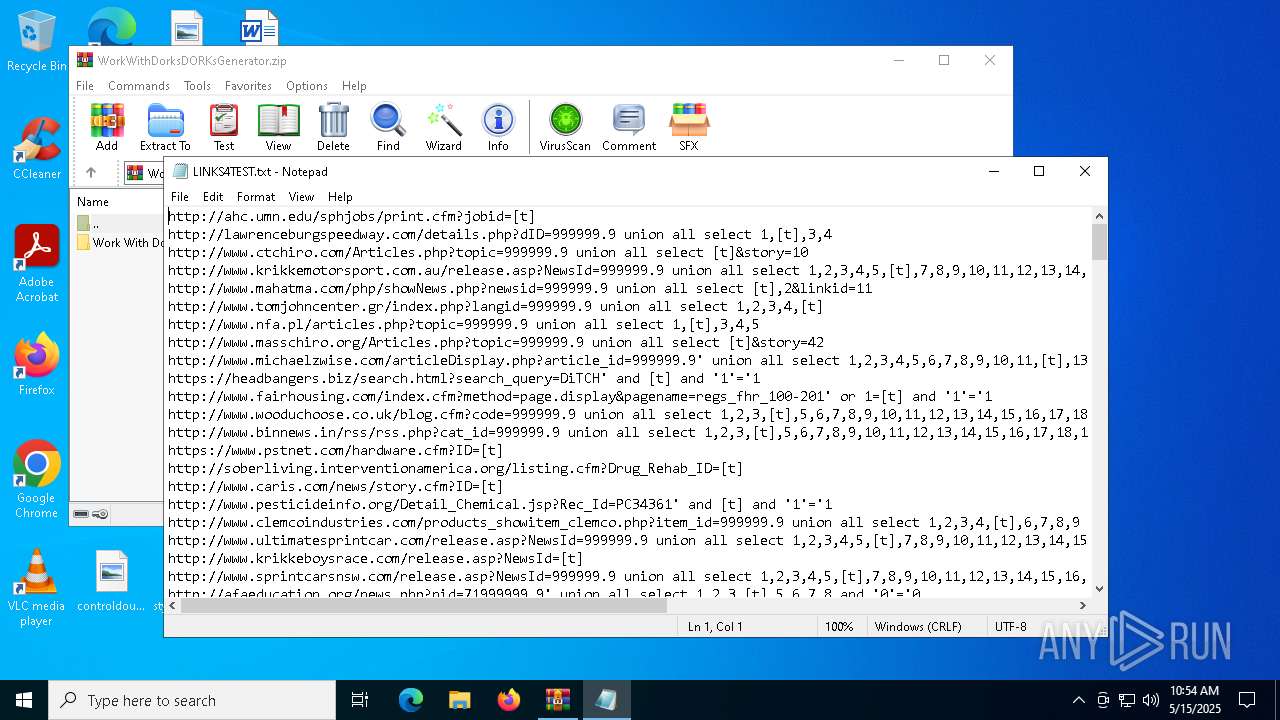
Executable content was dropped or overwritten
- Work With Dork_v_2_1.exe (PID: 8000)
- Service.exe (PID: 8180)
- GreenField.exe (PID: 5048)
Executes application which crashes
- bb2.exe (PID: 7960)
- bb2.exe (PID: 7952)
Reads security settings of Internet Explorer
- Work With Dork_v_2_1.exe (PID: 8000)
- Service.exe (PID: 8180)
- GreenField.exe (PID: 5048)
- GreenField.exe (PID: 7336)
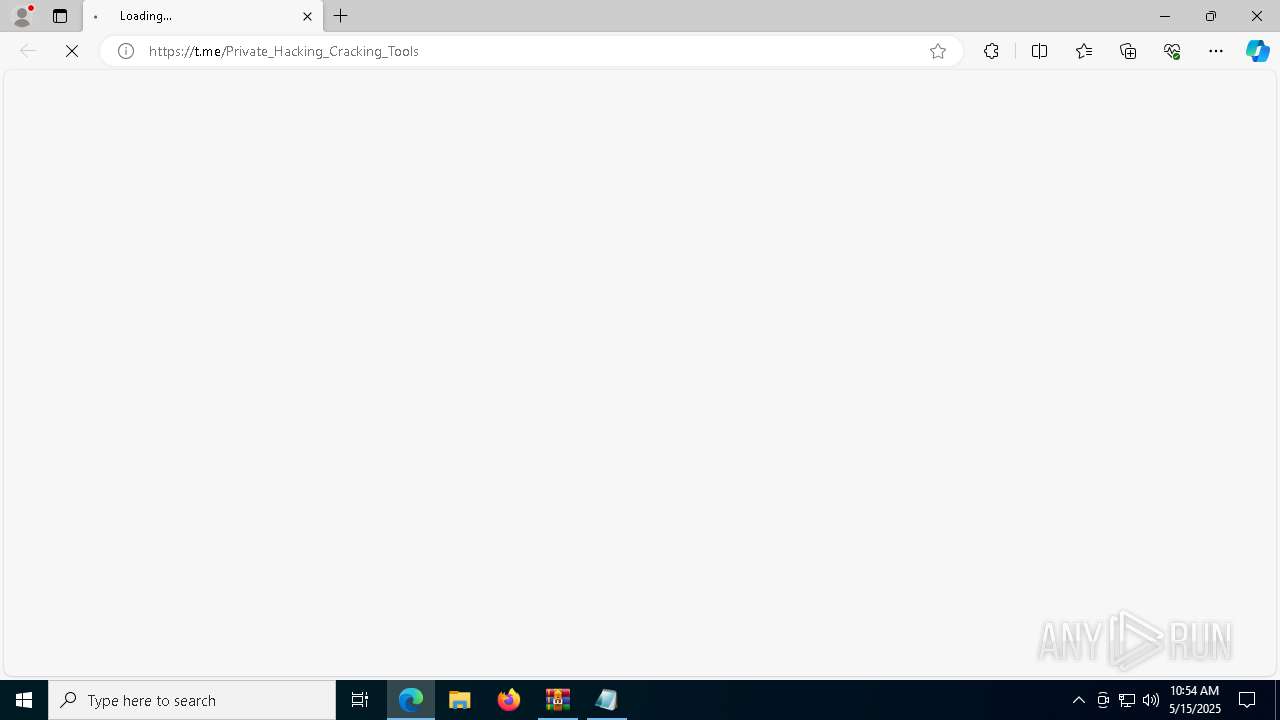
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Work With Dork_v_2_1.exe (PID: 8000)
Application launched itself
- zxc.exe (PID: 3008)
- zxc.exe (PID: 6744)
- zxc.exe (PID: 4728)
Connects to unusual port
- zxc.exe (PID: 856)
INFO
Checks supported languages
- bb2.exe (PID: 7960)
- Work With Dork_v_2_1.exe (PID: 8000)
- Service.exe (PID: 8180)
- zxc.exe (PID: 856)
- GreenField.exe (PID: 5048)
- bb2.exe (PID: 7952)
- identity_helper.exe (PID: 5728)
- PhotoBox.exe (PID: 4428)
- GreenField.exe (PID: 7336)
- PhotoBox.exe (PID: 4776)
- zxc.exe (PID: 4728)
- zxc.exe (PID: 6744)
- zxc.exe (PID: 7948)
- zxc.exe (PID: 3008)
- zxc.exe (PID: 4304)
Reads the computer name
- bb2.exe (PID: 7960)
- Work With Dork_v_2_1.exe (PID: 8000)
- Service.exe (PID: 8180)
- zxc.exe (PID: 856)
- GreenField.exe (PID: 5048)
- bb2.exe (PID: 7952)
- identity_helper.exe (PID: 5728)
- PhotoBox.exe (PID: 4428)
- GreenField.exe (PID: 7336)
- PhotoBox.exe (PID: 4776)
- zxc.exe (PID: 3008)
- zxc.exe (PID: 4304)
- zxc.exe (PID: 6744)
- zxc.exe (PID: 7948)
- zxc.exe (PID: 4728)
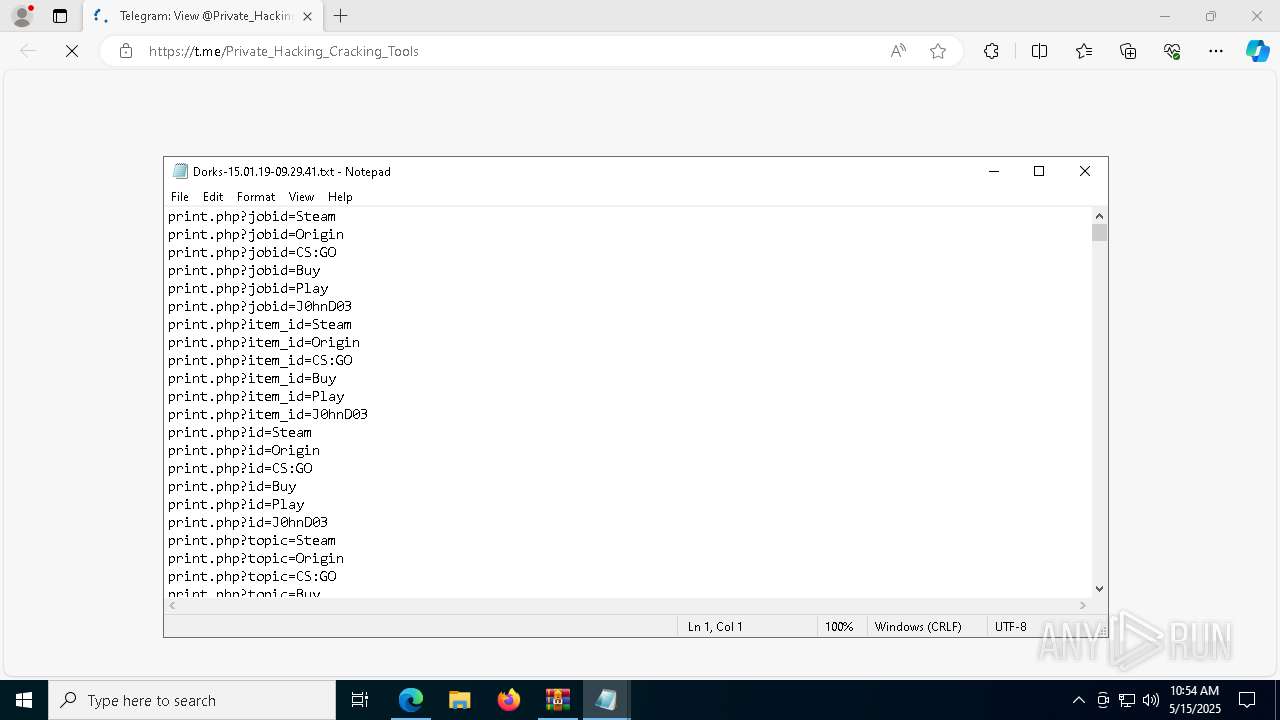
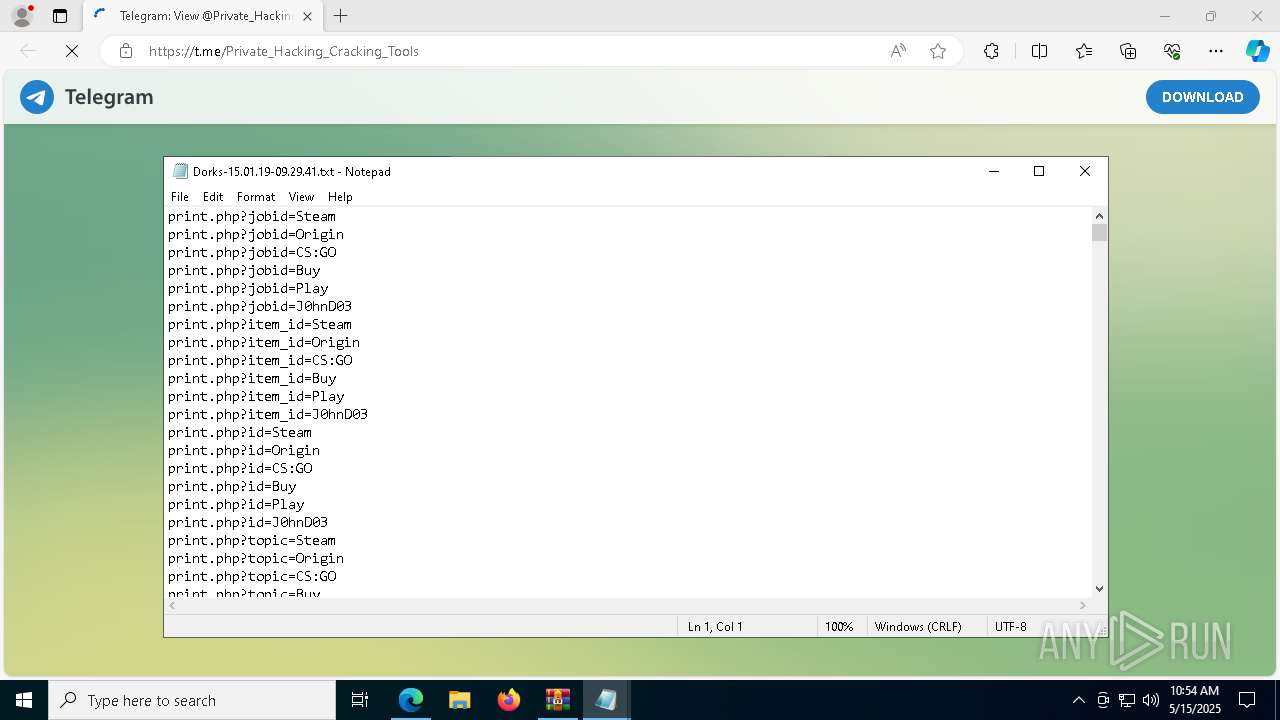
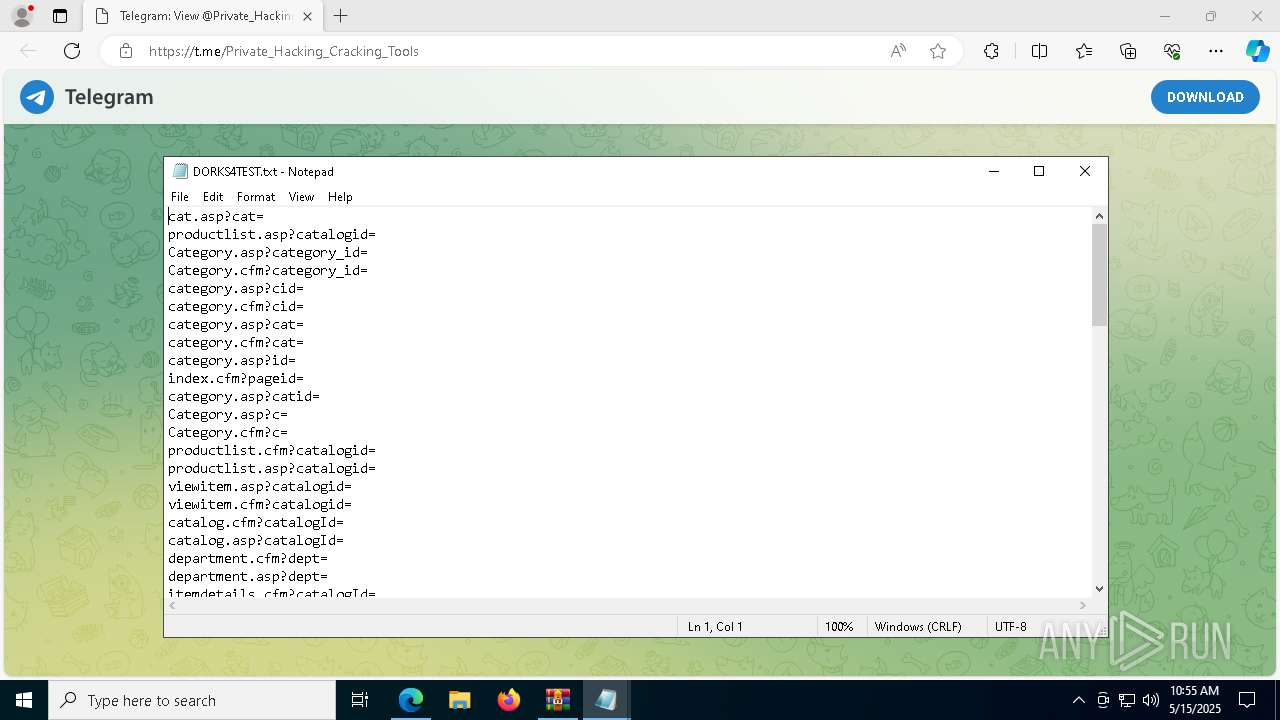
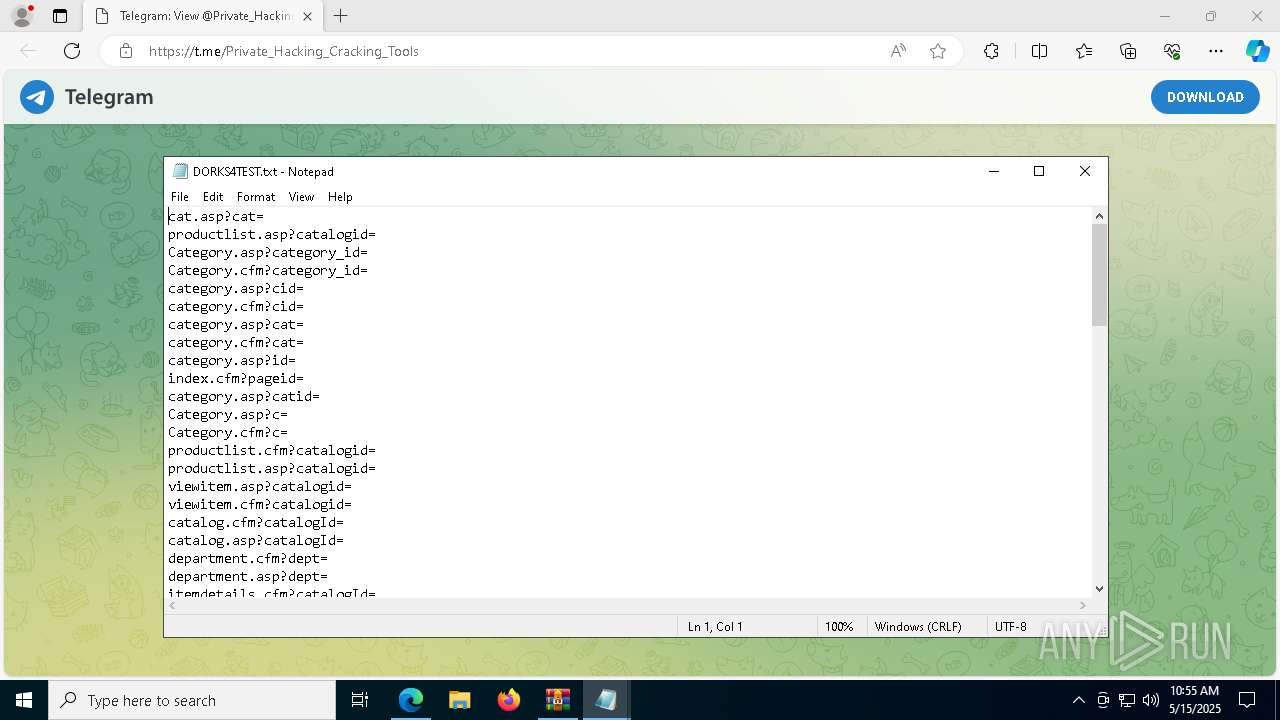
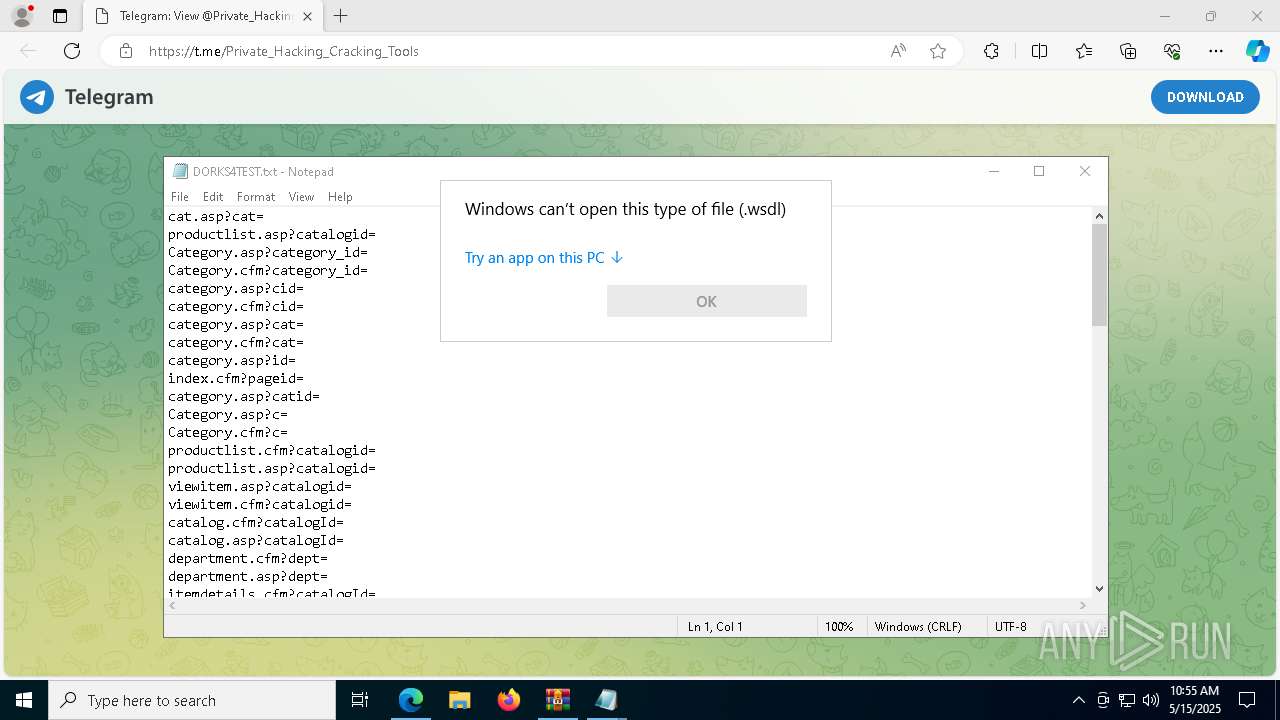
Manual execution by a user
- bb2.exe (PID: 7960)
- notepad.exe (PID: 8060)
- Work With Dork_v_2_1.exe (PID: 8000)
- notepad.exe (PID: 1012)
- notepad.exe (PID: 6036)
- OpenWith.exe (PID: 5964)
- GreenField.exe (PID: 7336)
- msedge.exe (PID: 3024)
- OpenWith.exe (PID: 6828)
- OpenWith.exe (PID: 8020)
Creates files or folders in the user directory
- Work With Dork_v_2_1.exe (PID: 8000)
- Service.exe (PID: 8180)
- WerFault.exe (PID: 1116)
- WerFault.exe (PID: 1764)
- GreenField.exe (PID: 5048)
- GreenField.exe (PID: 7336)
Checks proxy server information
- Work With Dork_v_2_1.exe (PID: 8000)
- GreenField.exe (PID: 5048)
- GreenField.exe (PID: 7336)
- slui.exe (PID: 3396)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8060)
- notepad.exe (PID: 1012)
- notepad.exe (PID: 6036)
Reads the machine GUID from the registry
- bb2.exe (PID: 7960)
- Service.exe (PID: 8180)
- Work With Dork_v_2_1.exe (PID: 8000)
- zxc.exe (PID: 856)
- GreenField.exe (PID: 5048)
- bb2.exe (PID: 7952)
- PhotoBox.exe (PID: 4428)
- GreenField.exe (PID: 7336)
- PhotoBox.exe (PID: 4776)
- zxc.exe (PID: 4304)
Disables trace logs
- Work With Dork_v_2_1.exe (PID: 8000)
- GreenField.exe (PID: 5048)
- GreenField.exe (PID: 7336)
Reads the software policy settings
- Work With Dork_v_2_1.exe (PID: 8000)
- GreenField.exe (PID: 5048)
- GreenField.exe (PID: 7336)
- slui.exe (PID: 3396)
Process checks computer location settings
- Service.exe (PID: 8180)
- GreenField.exe (PID: 5048)
- GreenField.exe (PID: 7336)
Auto-launch of the file from Registry key
- GreenField.exe (PID: 5048)
- GreenField.exe (PID: 7336)
Reads Environment values
- identity_helper.exe (PID: 5728)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5964)
- OpenWith.exe (PID: 6828)
- OpenWith.exe (PID: 8020)
Auto-launch of the file from Startup directory
- Service.exe (PID: 8180)
Application launched itself
- msedge.exe (PID: 8172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:02:04 08:05:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Work With Dorks [DORK's Generator]/ |
Total processes
194
Monitored processes
67
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5664 --field-trial-handle=2512,i,17455470005632521,6578284267973453451,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3752 --field-trial-handle=2512,i,17455470005632521,6578284267973453451,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | C:\Users\admin\AppData\Roaming\zxc.exe | C:\Users\admin\AppData\Roaming\zxc.exe | zxc.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: ConsoleApplication2 Version: 1.0.0.0 Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6824 --field-trial-handle=2512,i,17455470005632521,6578284267973453451,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3624 --field-trial-handle=2512,i,17455470005632521,6578284267973453451,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Dorks-15.01.19-09.29.41.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3716 --field-trial-handle=2512,i,17455470005632521,6578284267973453451,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7960 -s 1072 | C:\Windows\SysWOW64\WerFault.exe | — | bb2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6308 --field-trial-handle=2512,i,17455470005632521,6578284267973453451,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1764 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7952 -s 1076 | C:\Windows\SysWOW64\WerFault.exe | — | bb2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 682
Read events
28 623
Write events
59
Delete events
0
Modification events
| (PID) Process: | (7616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\WorkWithDorksDORKsGenerator.zip | |||
| (PID) Process: | (7616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8000) Work With Dork_v_2_1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (8000) Work With Dork_v_2_1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
12
Suspicious files
270
Text files
59
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF113f58.TMP | — | |
MD5:— | SHA256:— | |||
| 8172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF113f58.TMP | — | |
MD5:— | SHA256:— | |||
| 8172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF113f58.TMP | — | |
MD5:— | SHA256:— | |||
| 8172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF113f67.TMP | — | |
MD5:— | SHA256:— | |||
| 8172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF113f96.TMP | — | |
MD5:— | SHA256:— | |||
| 8172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
97
DNS requests
66
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6228 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705108&P2=404&P3=2&P4=Kq3DCiSt1%2fGSipn2c77MWVESrfJjM5BL2rMBMiFTAmFSACnR8KrMtQqH8GLGj1HYy12MuHmrWoUbWpVQsi5AJg%3d%3d | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6228 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747705108&P2=404&P3=2&P4=NNeicD8uf%2bnFfxMs9OVhPLiXQ%2fOmTwXmJdVoejw9eyidqBLqqueI%2bCYGDU1ALtzebgIaODBUEoqdXm6xRqe68g%3d%3d | unknown | — | — | whitelisted |
6228 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747705108&P2=404&P3=2&P4=NNeicD8uf%2bnFfxMs9OVhPLiXQ%2fOmTwXmJdVoejw9eyidqBLqqueI%2bCYGDU1ALtzebgIaODBUEoqdXm6xRqe68g%3d%3d | unknown | — | — | whitelisted |
6228 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747705108&P2=404&P3=2&P4=NNeicD8uf%2bnFfxMs9OVhPLiXQ%2fOmTwXmJdVoejw9eyidqBLqqueI%2bCYGDU1ALtzebgIaODBUEoqdXm6xRqe68g%3d%3d | unknown | — | — | whitelisted |
6228 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705108&P2=404&P3=2&P4=Kq3DCiSt1%2fGSipn2c77MWVESrfJjM5BL2rMBMiFTAmFSACnR8KrMtQqH8GLGj1HYy12MuHmrWoUbWpVQsi5AJg%3d%3d | unknown | — | — | whitelisted |
6228 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705108&P2=404&P3=2&P4=Kq3DCiSt1%2fGSipn2c77MWVESrfJjM5BL2rMBMiFTAmFSACnR8KrMtQqH8GLGj1HYy12MuHmrWoUbWpVQsi5AJg%3d%3d | unknown | — | — | whitelisted |
6228 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705108&P2=404&P3=2&P4=Kq3DCiSt1%2fGSipn2c77MWVESrfJjM5BL2rMBMiFTAmFSACnR8KrMtQqH8GLGj1HYy12MuHmrWoUbWpVQsi5AJg%3d%3d | unknown | — | — | whitelisted |
6228 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747705108&P2=404&P3=2&P4=Kq3DCiSt1%2fGSipn2c77MWVESrfJjM5BL2rMBMiFTAmFSACnR8KrMtQqH8GLGj1HYy12MuHmrWoUbWpVQsi5AJg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
8000 | Work With Dork_v_2_1.exe | 149.154.167.99:443 | t.me | Telegram Messenger Inc | GB | whitelisted |
8172 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7280 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
t.me |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
github.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8000 | Work With Dork_v_2_1.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
7280 | msedge.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
— | — | Misc activity | ET HUNTING EXE Downloaded from Github |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.strangled .net Domain |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |