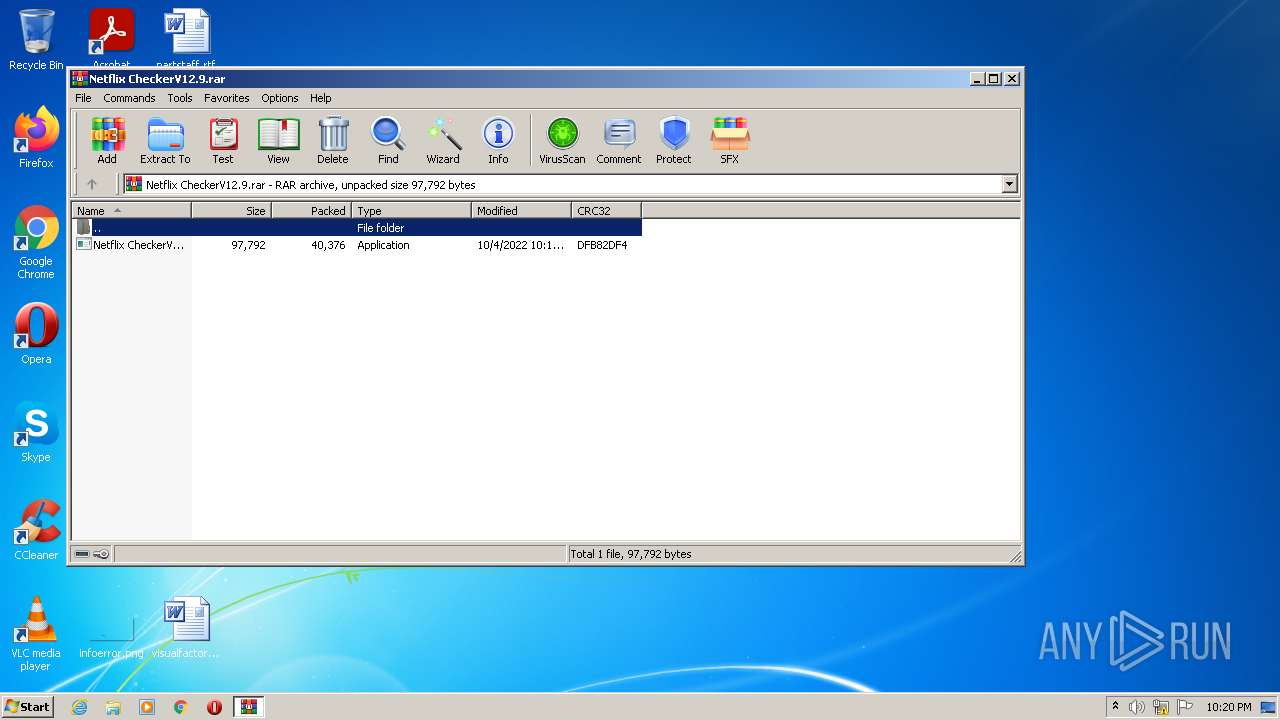
| File name: | Netflix CheckerV12.9.rar |
| Full analysis: | https://app.any.run/tasks/bc34ecc3-9f76-438d-956f-a07ed0f42d8a |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | October 04, 2022, 21:20:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A3E1B61309FABB87EDE7C168C49F8DE5 |
| SHA1: | 47E73FD4F69880C905499F1620111FFD6FC3051D |
| SHA256: | 66893148B0D748534DC339B1D78BA769DA59C03F825E731C996D5D410CE41247 |
| SSDEEP: | 768:tsfGR6aicvrOuLo0Q+DAFZhvTHLqd2fPf0Sx+2bs2QZ/vFsJnJuy3q+xEmvXK7:tNF6m7JDErpfPMvyQZXFs113q+xr+ |
MALICIOUS
Application was dropped or rewritten from another process
- Netflix CheckerV12.9.exe (PID: 2516)
Drops executable file immediately after starts
- WinRAR.exe (PID: 1752)
REDLINE detected by memory dumps
- Netflix CheckerV12.9.exe (PID: 2516)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 1752)
- Netflix CheckerV12.9.exe (PID: 2516)
Reads the computer name
- WinRAR.exe (PID: 1752)
- Netflix CheckerV12.9.exe (PID: 2516)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1752)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1752)
Reads Environment values
- Netflix CheckerV12.9.exe (PID: 2516)
INFO
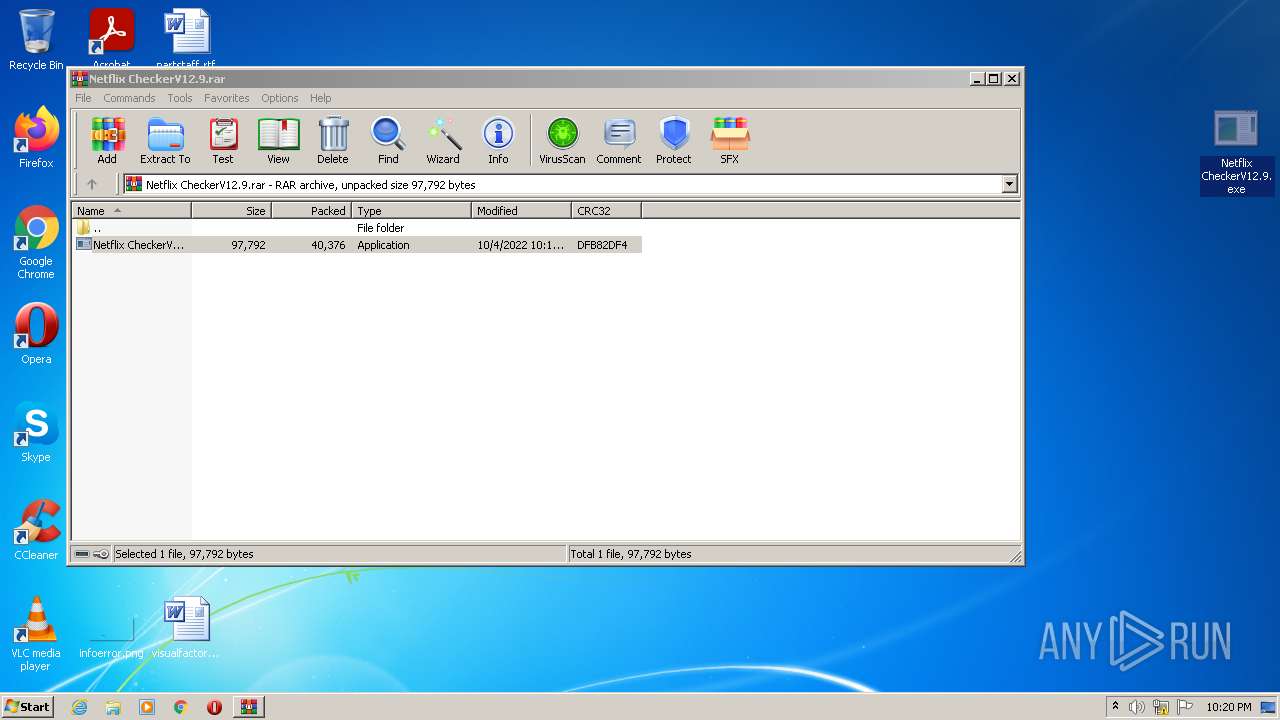
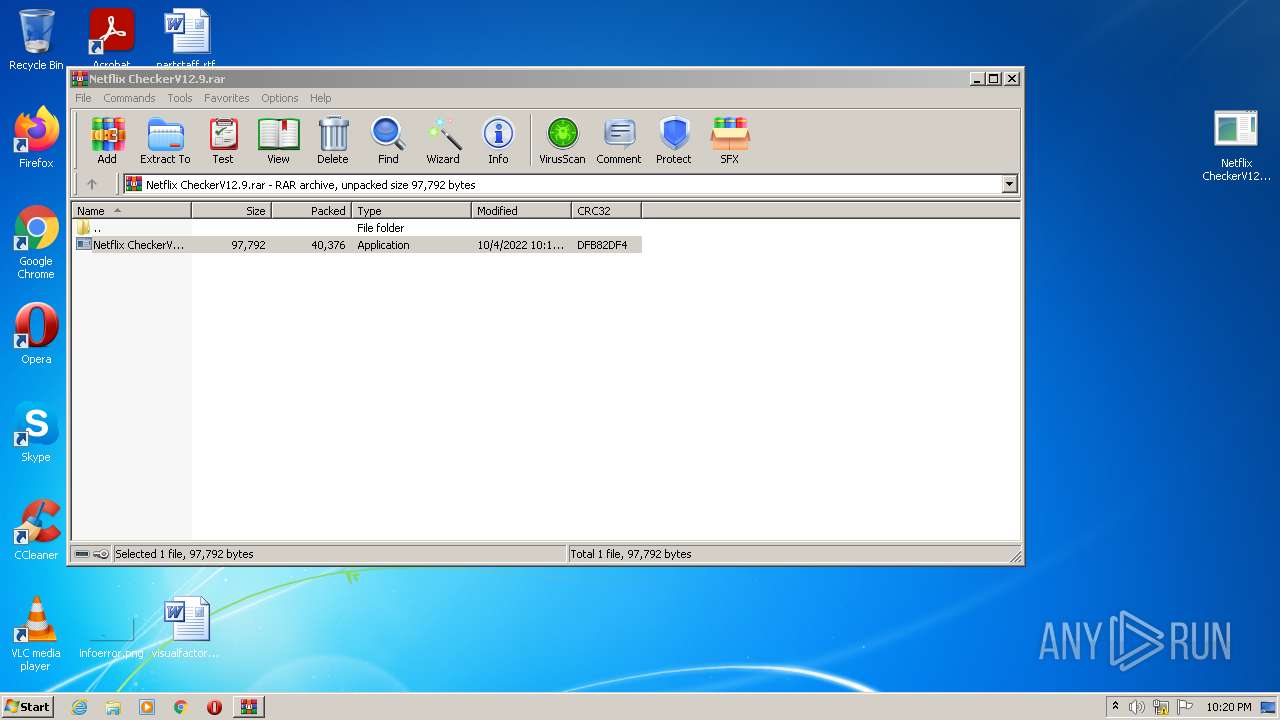
Manual execution by user
- Netflix CheckerV12.9.exe (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(2516) Netflix CheckerV12.9.exe
C2 (1)2.tcp.eu.ngrok.io:10642
Botnetcheat
US (151)
Environment
UNKNOWN
.
1
cmyredmyit_cmyardmys
my
as21
\
Local State
LocalPrefs.json
Host
Port
:
User
Pass
MANGO
%USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal
WanaLife
Def
Win
String.Replace
String.Remove
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
BCrypt.BCryptImportKey() failed with status code:{0}
BCrypt.BCryptGetProperty() (get size) failed with status code:{0}
BCrypt.BCryptGetProperty() failed with status code:{0}
-
http://
/
|
Yandex\YaAddon
2.tcp.eu.ngrok.io:10642
cheat
,
asf
*wallet*
Armory
\Armory
*.wallet
Atomic
\atomic
*
ibnejdfjmmkpcnlpebklmnkoeoihofec
Tronlink
jbdaocneiiinmjbjlgalhcelgbejmnid
NiftyWallet
nkbihfbeogaeaoehlefnkodbefgpgknn
Metamask
afbcbjpbpfadlkmhmclhkeeodmamcflc
MathWallet
hnfanknocfeofbddgcijnmhnfnkdnaad
Coinbase
fhbohimaelbohpjbbldcngcnapndodjp
BinanceChain
odbfpeeihdkbihmopkbjmoonfanlbfcl
BraveWallet
hpglfhgfnhbgpjdenjgmdgoeiappafln
GuardaWallet
blnieiiffboillknjnepogjhkgnoapac
EqualWallet
cjelfplplebdjjenllpjcblmjkfcffne
JaxxxLiberty
fihkakfobkmkjojpchpfgcmhfjnmnfpi
BitAppWallet
kncchdigobghenbbaddojjnnaogfppfj
iWallet
amkmjjmmflddogmhpjloimipbofnfjih
Wombat
UnknownExtension
_
Local Extension Settings
Coinomi
\Coinomi
Profile_
Tel
egram.exe
\Telegram Desktop\tdata
-*.lo--g
1*.1l1d1b
String
Replace
System.UI
File.IO
*.json
string.Replace
Guarda
\Guarda
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPstring.ReplaceROFILE%\Apstring.ReplacepData\Locastring.Replacel
ToString
(
UNIQUE
"
Width
Height
CopyFromScreen
kernel32
user32.dll
GetConsoleWindow
ShowWindow
SELECT * FROM Win32_Processor
Name
NumberOfCores
root\CIMV2
SELECT * FROM Win32_VideoController
AdapterRAM
ROWindowsServiceOT\SecurityCenteWindowsServicer2
ROWindowsServiceOT\SecurWindowsServiceityCenter
AntqueiresivirusProdqueiresuct
AntqueiresiSpyqueiresWareProdqueiresuct
FiqueiresrewallProqueiresduct
WindowsService
SELECT * FROM
queires
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELECT * FROM Win32_DiskDrive
SerialNumber
'
ExecutablePath
[
]
0 Mb or 0
SELECT * FROM Win32_OperatingSystem
TotalVisibleMemorySize
{0} MB or {1}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1752 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Netflix CheckerV12.9.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\Desktop\Netflix CheckerV12.9.exe" | C:\Users\admin\Desktop\Netflix CheckerV12.9.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
RedLine(PID) Process(2516) Netflix CheckerV12.9.exe C2 (1)2.tcp.eu.ngrok.io:10642 Botnetcheat US (151) Environment UNKNOWN . 1 cmyredmyit_cmyardmys my as21 \ Local State LocalPrefs.json Host Port : User Pass MANGO %USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal WanaLife Def Win String.Replace String.Remove windows-1251 AES Microsoft Primitive Provider ChainingModeGCM AuthTagLength ChainingMode ObjectLength KeyDataBlob BCrypt.BCryptImportKey() failed with status code:{0} BCrypt.BCryptGetProperty() (get size) failed with status code:{0} BCrypt.BCryptGetProperty() failed with status code:{0} - http:// / | Yandex\YaAddon 2.tcp.eu.ngrok.io:10642 cheat , asf *wallet* Armory \Armory *.wallet Atomic \atomic * ibnejdfjmmkpcnlpebklmnkoeoihofec Tronlink jbdaocneiiinmjbjlgalhcelgbejmnid NiftyWallet nkbihfbeogaeaoehlefnkodbefgpgknn Metamask afbcbjpbpfadlkmhmclhkeeodmamcflc MathWallet hnfanknocfeofbddgcijnmhnfnkdnaad Coinbase fhbohimaelbohpjbbldcngcnapndodjp BinanceChain odbfpeeihdkbihmopkbjmoonfanlbfcl BraveWallet hpglfhgfnhbgpjdenjgmdgoeiappafln GuardaWallet blnieiiffboillknjnepogjhkgnoapac EqualWallet cjelfplplebdjjenllpjcblmjkfcffne JaxxxLiberty fihkakfobkmkjojpchpfgcmhfjnmnfpi BitAppWallet kncchdigobghenbbaddojjnnaogfppfj iWallet amkmjjmmflddogmhpjloimipbofnfjih Wombat UnknownExtension _ Local Extension Settings Coinomi \Coinomi Profile_ Tel egram.exe \Telegram Desktop\tdata -*.lo--g 1*.1l1d1b String Replace System.UI File.IO *.json string.Replace Guarda \Guarda %USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng File.Write Handler npvo* %USERPstring.ReplaceROFILE%\Apstring.ReplacepData\Locastring.Replacel ToString ( UNIQUE " Width Height CopyFromScreen kernel32 user32.dll GetConsoleWindow ShowWindow SELECT * FROM Win32_Processor Name NumberOfCores root\CIMV2 SELECT * FROM Win32_VideoController AdapterRAM ROWindowsServiceOT\SecurityCenteWindowsServicer2 ROWindowsServiceOT\SecurWindowsServiceityCenter AntqueiresivirusProdqueiresuct AntqueiresiSpyqueiresWareProdqueiresuct FiqueiresrewallProqueiresduct WindowsService SELECT * FROM queires SOFTWARE\WOW6432Node\Clients\StartMenuInternet SOFTWARE\Clients\StartMenuInternet shell\open\command Unknown Version SELECT * FROM Win32_DiskDrive SerialNumber ' ExecutablePath [ ] 0 Mb or 0 SELECT * FROM Win32_OperatingSystem TotalVisibleMemorySize {0} MB or {1} x32 x64 x86 SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName CSDVersion Unknown _[ | |||||||||||||||
Total events
1 426
Read events
1 404
Write events
22
Delete events
0
Modification events
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Netflix CheckerV12.9.rar | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1752.7820\Netflix CheckerV12.9.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
13
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2516 | Netflix CheckerV12.9.exe | 18.197.239.5:10642 | 2.tcp.eu.ngrok.io | AMAZON-02 | DE | malicious |
— | — | 18.197.239.5:10642 | 2.tcp.eu.ngrok.io | AMAZON-02 | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
2.tcp.eu.ngrok.io |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |