| File name: | sample.zip |
| Full analysis: | https://app.any.run/tasks/ceee711e-2d7d-4b9d-9832-abfd92cd1bcf |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | October 09, 2019, 18:57:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
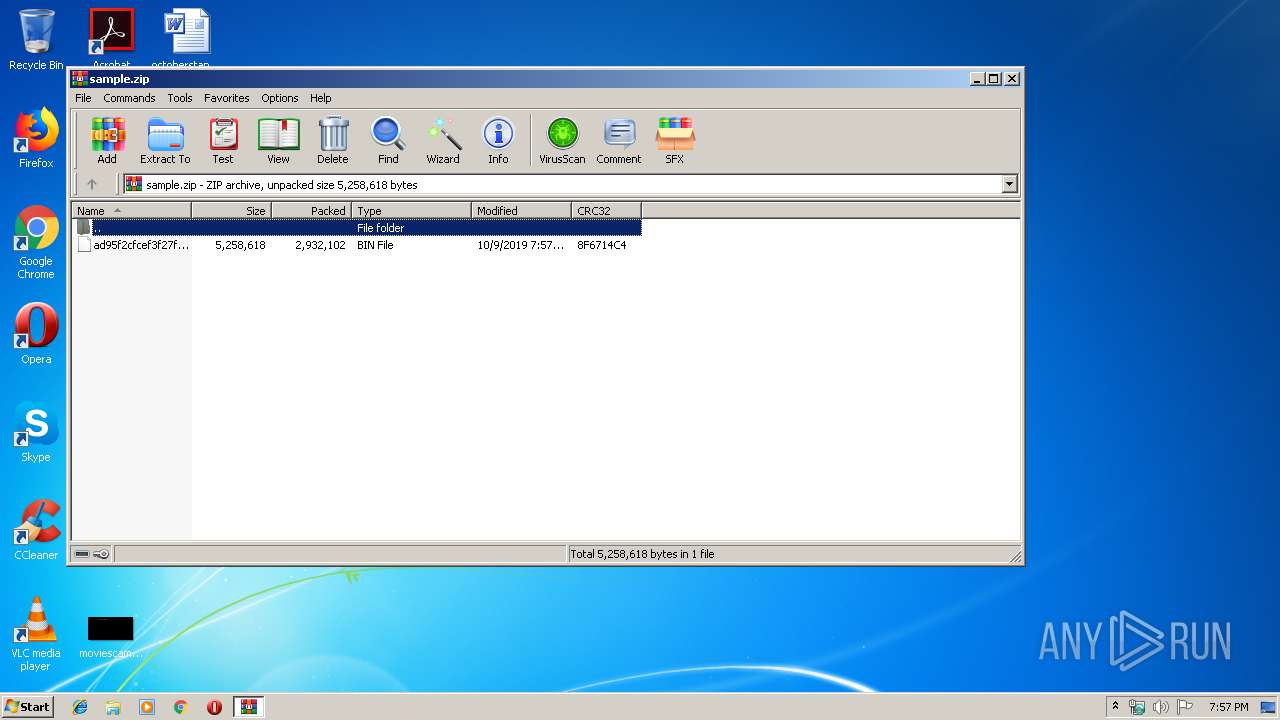
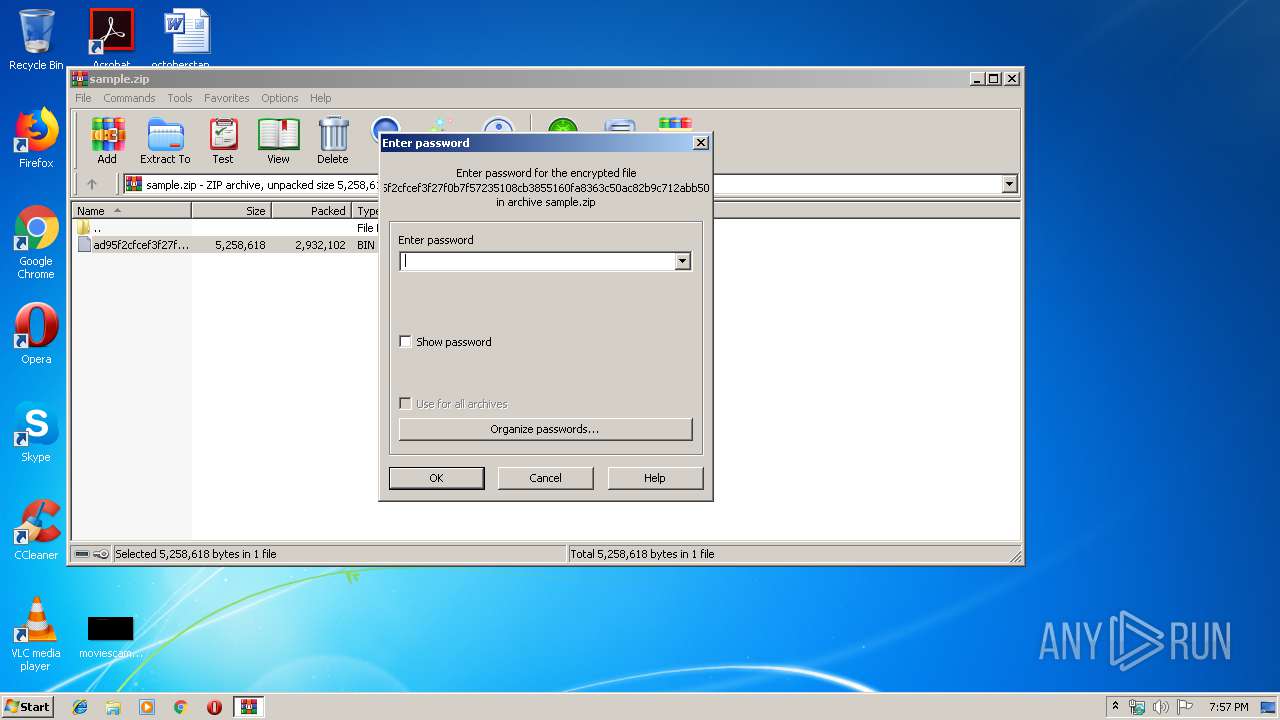
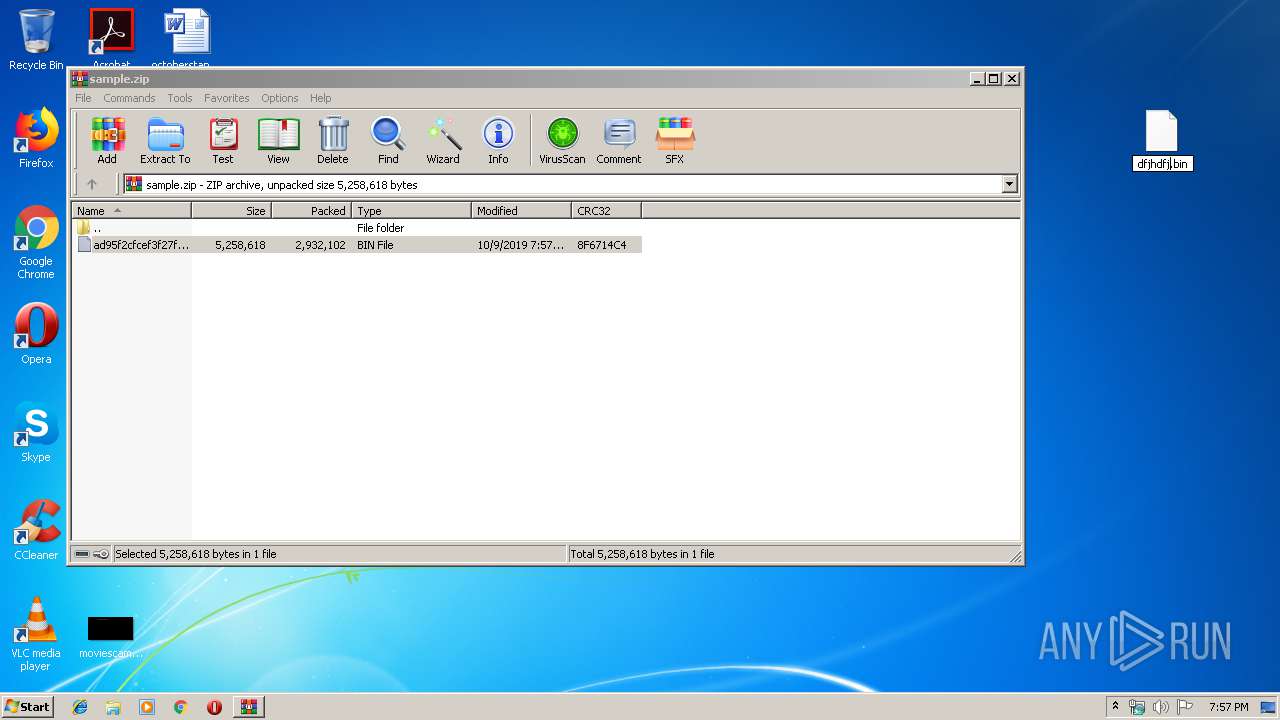
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A549CA865410281651EA193821C840B4 |
| SHA1: | A53298257234F4F03D4DECBDBB4F101AA45BF72F |
| SHA256: | 664B8B716AA93A382169ED1BF7D46D3F24C89693A7559E213386F09617D108C4 |
| SSDEEP: | 49152:abVC9A+ityAhirzBSqaggH+V6swknZEiN9Xxn1j1dYarDhUaCjpaZGpRi/D:SMAtQAM3s47sQZtZx1jZU6E/iL |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 1944)
Application was dropped or rewritten from another process
- APPS.exe (PID: 2944)
FORMBOOK was detected
- explorer.exe (PID: 236)
- nbtstat.exe (PID: 1408)
- Firefox.exe (PID: 2888)
Changes the autorun value in the registry
- nbtstat.exe (PID: 1408)
Connects to CnC server
- explorer.exe (PID: 236)
Actions looks like stealing of personal data
- nbtstat.exe (PID: 1408)
Stealing of credential data
- nbtstat.exe (PID: 1408)
SUSPICIOUS
Reads Internet Cache Settings
- explorer.exe (PID: 236)
Executed via COM
- EQNEDT32.EXE (PID: 1944)
Creates files in the user directory
- explorer.exe (PID: 236)
- nbtstat.exe (PID: 1408)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 1944)
Starts CMD.EXE for commands execution
- nbtstat.exe (PID: 1408)
Loads DLL from Mozilla Firefox
- nbtstat.exe (PID: 1408)
INFO
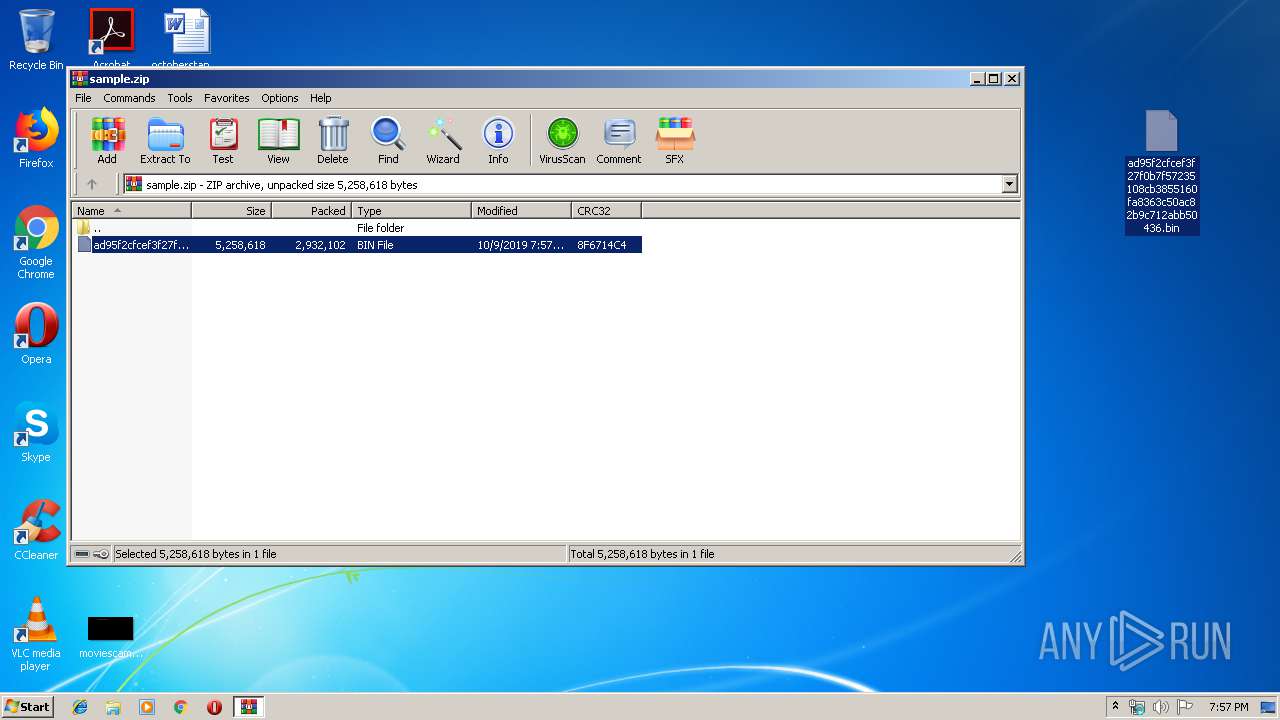
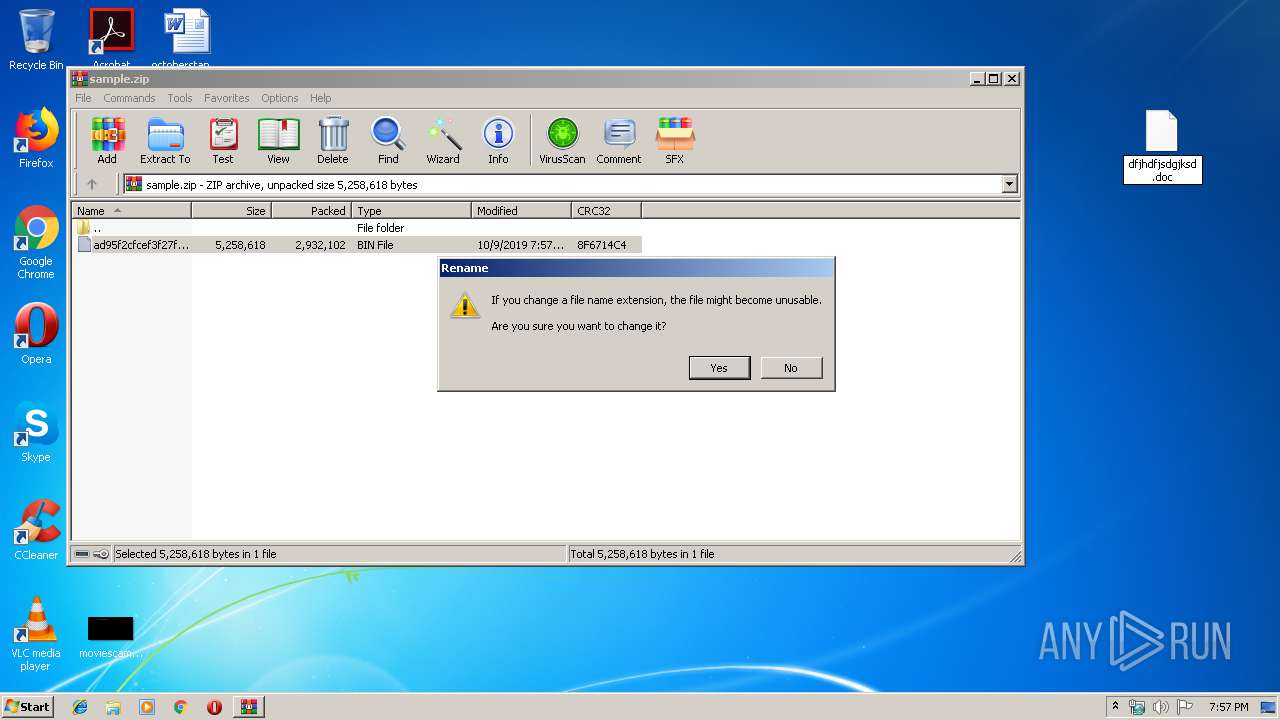
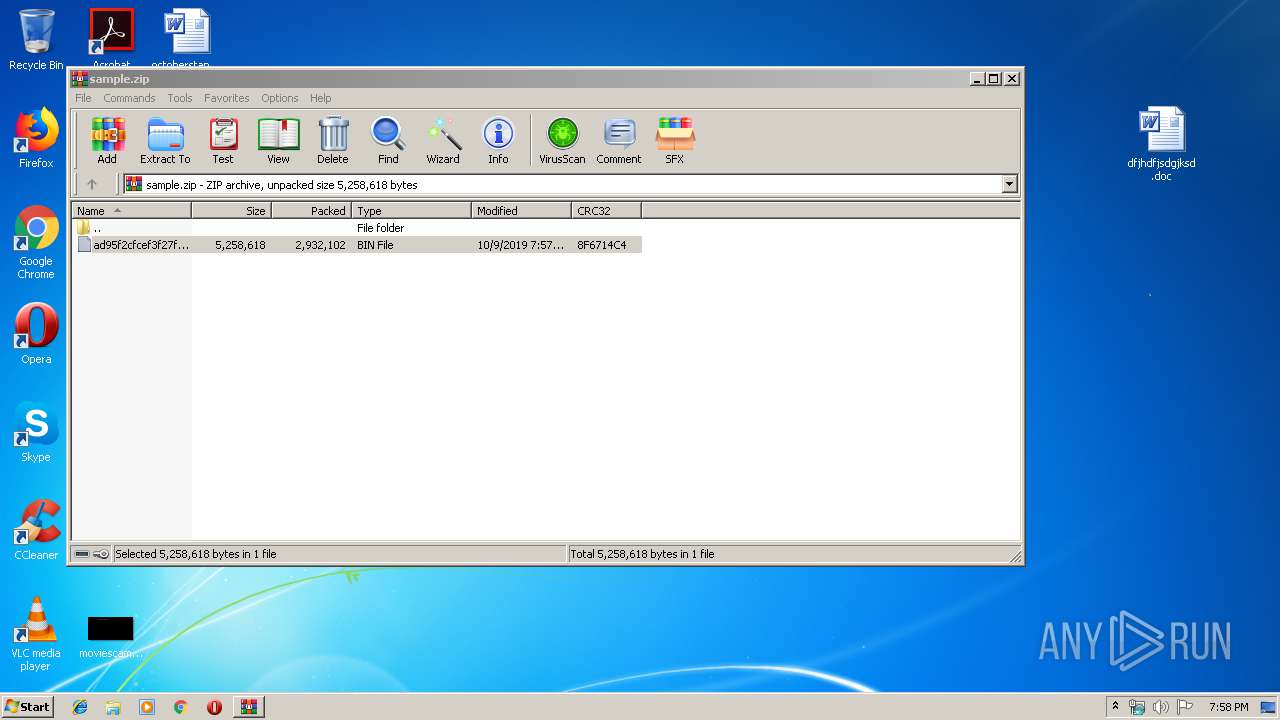
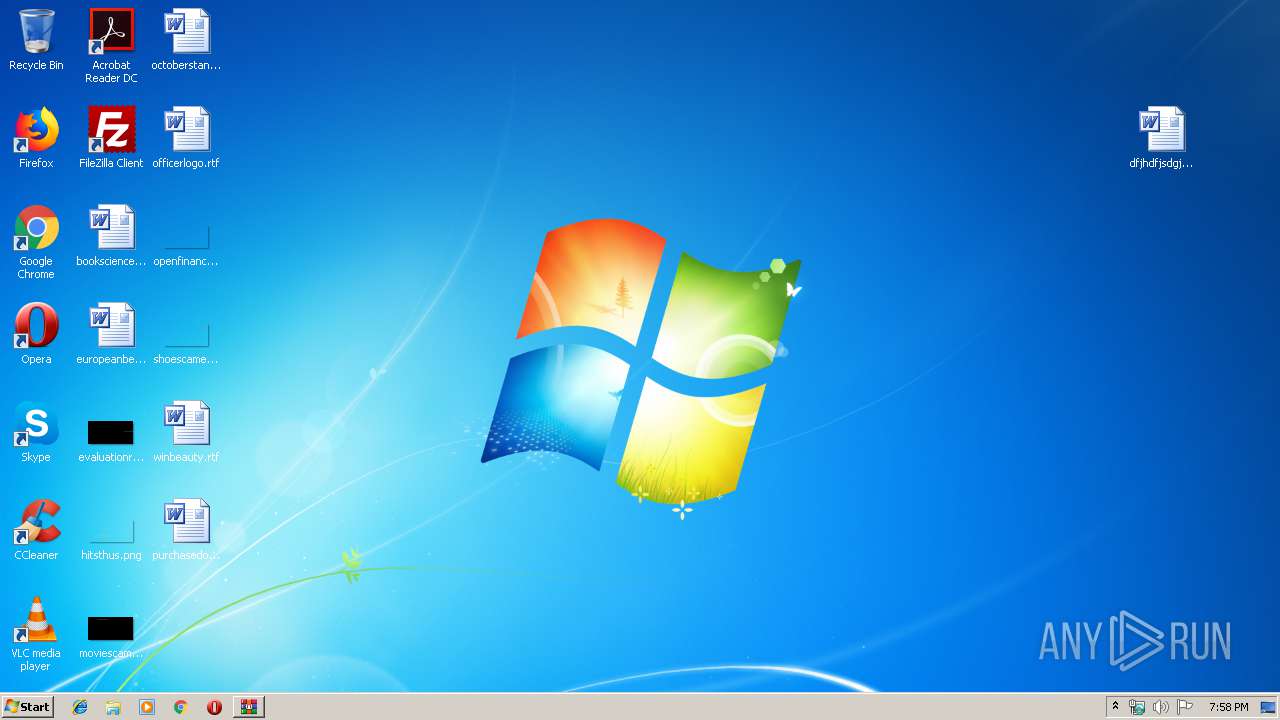
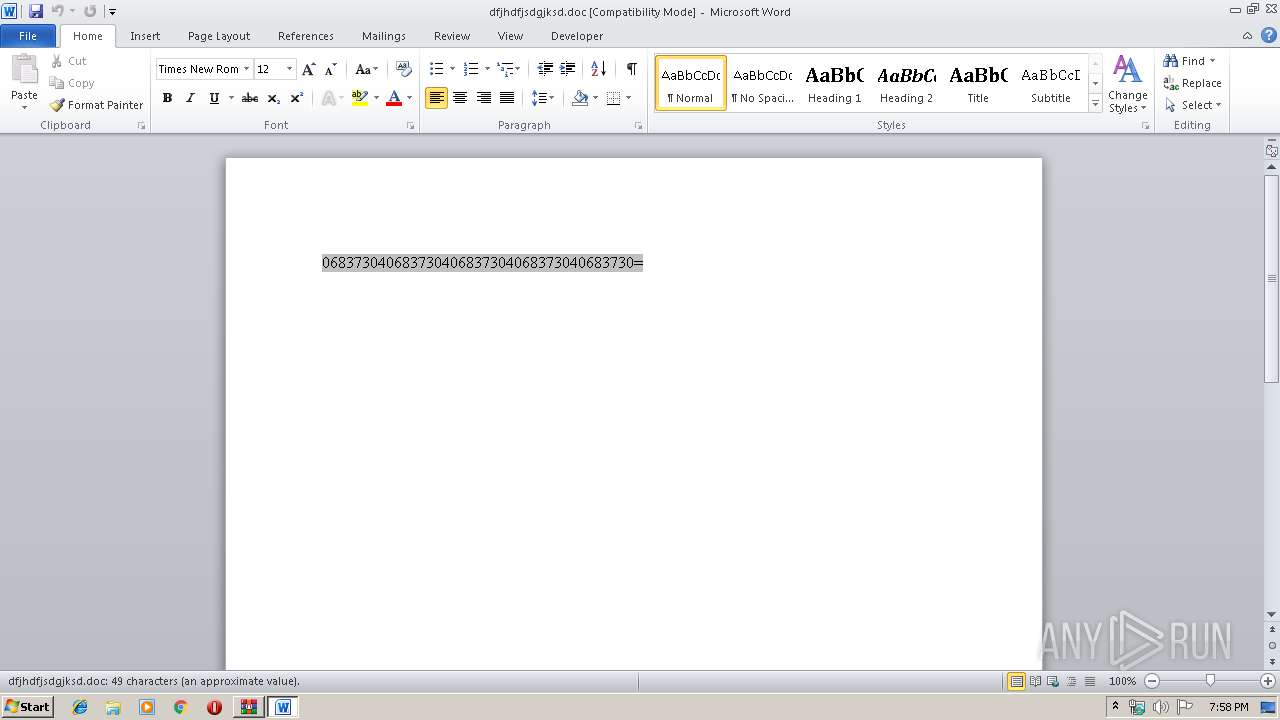
Manual execution by user
- WINWORD.EXE (PID: 2972)
- autochk.exe (PID: 2360)
- nbtstat.exe (PID: 1408)
Starts Microsoft Office Application
- explorer.exe (PID: 236)
Creates files in the user directory
- WINWORD.EXE (PID: 2972)
- Firefox.exe (PID: 2888)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2972)
Reads the hosts file
- nbtstat.exe (PID: 1408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:09 18:57:02 |
| ZipCRC: | 0x8f6714c4 |
| ZipCompressedSize: | 2932102 |
| ZipUncompressedSize: | 5258618 |
| ZipFileName: | ad95f2cfcef3f27f0b7f57235108cb3855160fa8363c50ac82b9c712abb50436.bin |
Total processes
46
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1408 | "C:\Windows\System32\nbtstat.exe" | C:\Windows\System32\nbtstat.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP NetBios Information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1708 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1812 | /c del "C:\Users\admin\AppData\Local\Temp\APPS.exe" | C:\Windows\System32\cmd.exe | — | nbtstat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2360 | "C:\Windows\System32\autochk.exe" | C:\Windows\System32\autochk.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto Check Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | nbtstat.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2944 | C:\Users\admin\AppData\Local\Temp\APPS.exe | C:\Users\admin\AppData\Local\Temp\APPS.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: LaKala Integrity Level: MEDIUM Description: Incmpatibilities Tester Summaryin Infogrames Exit code: 0 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\dfjhdfjsdgjksd.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 258
Read events
3 793
Write events
431
Delete events
34
Modification events
| (PID) Process: | (1708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1708) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample.zip | |||
| (PID) Process: | (1708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
2
Suspicious files
73
Text files
3
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1708.46712\ad95f2cfcef3f27f0b7f57235108cb3855160fa8363c50ac82b9c712abb50436.bin | — | |
MD5:— | SHA256:— | |||
| 236 | explorer.exe | C:\Users\admin\Desktop\ad95f2cfcef3f27f0b7f57235108cb3855160fa8363c50ac82b9c712abb50436.bin | — | |
MD5:— | SHA256:— | |||
| 236 | explorer.exe | C:\Users\admin\Desktop\dfjhdfjsdgjksd.doc | — | |
MD5:— | SHA256:— | |||
| 236 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019092020190921\index.dat | — | |
MD5:— | SHA256:— | |||
| 2972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8147.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 236 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\a7bd71699cd38d1c.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 236 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019100920191010\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1408 | nbtstat.exe | C:\Users\admin\AppData\Roaming\1L-3P7DE\1L-logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 2972 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 236 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
14
DNS requests
14
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
236 | explorer.exe | GET | — | 184.168.221.62:80 | http://www.monzastay.com/lv/?Wx=RImbpUNXckn0XbKrGmnySSVTo2Ci0DqcIwBttGzgOeJ4MFXVjjiYV30ItESdaPDlA9UzXw==&v2=lhnxV | US | — | — | malicious |
236 | explorer.exe | GET | — | 198.54.117.217:80 | http://www.hiddenhedonism.com/lv/?Wx=TtXFDlShZhOPCKZrOGb4ti1yAyDk3fOyZfqEPSWKu/3xfC7Edp9wXVAwRdoi58ux2I+0FA==&v2=lhnxV&sql=1 | US | — | — | malicious |
236 | explorer.exe | GET | — | 207.148.248.143:80 | http://www.allforensics.com/lv/?Wx=HrZypzIbaH+QzmXx54TvdqgZ/FptgsfRPoMCK4Y5sqn07lTyg2TE/HHuq+9rQkYYhqTFPQ==&v2=lhnxV&sql=1 | US | — | — | malicious |
236 | explorer.exe | POST | — | 198.54.117.217:80 | http://www.hiddenhedonism.com/lv/ | US | — | — | malicious |
236 | explorer.exe | POST | — | 198.54.117.217:80 | http://www.hiddenhedonism.com/lv/ | US | — | — | malicious |
236 | explorer.exe | GET | — | 104.233.144.35:80 | http://www.depdon.com/lv/?Wx=oYmyD1EPh9lisvu5gS6k02Qj9+nAkGXYa+DzKE6VIfuUOSZxawtEEcmQslLBQZaASA359Q==&v2=lhnxV&sql=1 | US | — | — | malicious |
236 | explorer.exe | POST | — | 207.148.248.143:80 | http://www.allforensics.com/lv/ | US | — | — | malicious |
236 | explorer.exe | POST | — | 104.233.144.35:80 | http://www.depdon.com/lv/ | US | — | — | malicious |
236 | explorer.exe | POST | — | 207.148.248.143:80 | http://www.allforensics.com/lv/ | US | — | — | malicious |
236 | explorer.exe | POST | — | 207.148.248.143:80 | http://www.allforensics.com/lv/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
236 | explorer.exe | 184.168.221.62:80 | www.monzastay.com | GoDaddy.com, LLC | US | malicious |
236 | explorer.exe | 198.54.117.217:80 | www.hiddenhedonism.com | Namecheap, Inc. | US | malicious |
236 | explorer.exe | 104.233.144.35:80 | www.depdon.com | PEG TECH INC | US | malicious |
— | — | 104.233.144.35:80 | www.depdon.com | PEG TECH INC | US | malicious |
236 | explorer.exe | 207.148.248.143:80 | www.allforensics.com | The Endurance International Group, Inc. | US | malicious |
— | — | 207.148.248.143:80 | www.allforensics.com | The Endurance International Group, Inc. | US | malicious |
1944 | EQNEDT32.EXE | 169.255.56.103:443 | alwetengroup.com | Web4Africa | ZA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
alwetengroup.com |
| malicious |
www.monzastay.com |
| malicious |
www.elementares-experten.com |
| unknown |
www.hiddenhedonism.com |
| malicious |
www.tv16543.info |
| unknown |
www.vbvhjx.com |
| unknown |
www.wardenmon.com |
| unknown |
www.depdon.com |
| malicious |
www.catechesisacco.com |
| unknown |
www.tushenli.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
236 | explorer.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
9 ETPRO signatures available at the full report