| File name: | AridekVM.exe |
| Full analysis: | https://app.any.run/tasks/eeba7d40-3d20-4683-bb09-f9819bf5ce22 |
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | December 05, 2019, 17:21:34 |
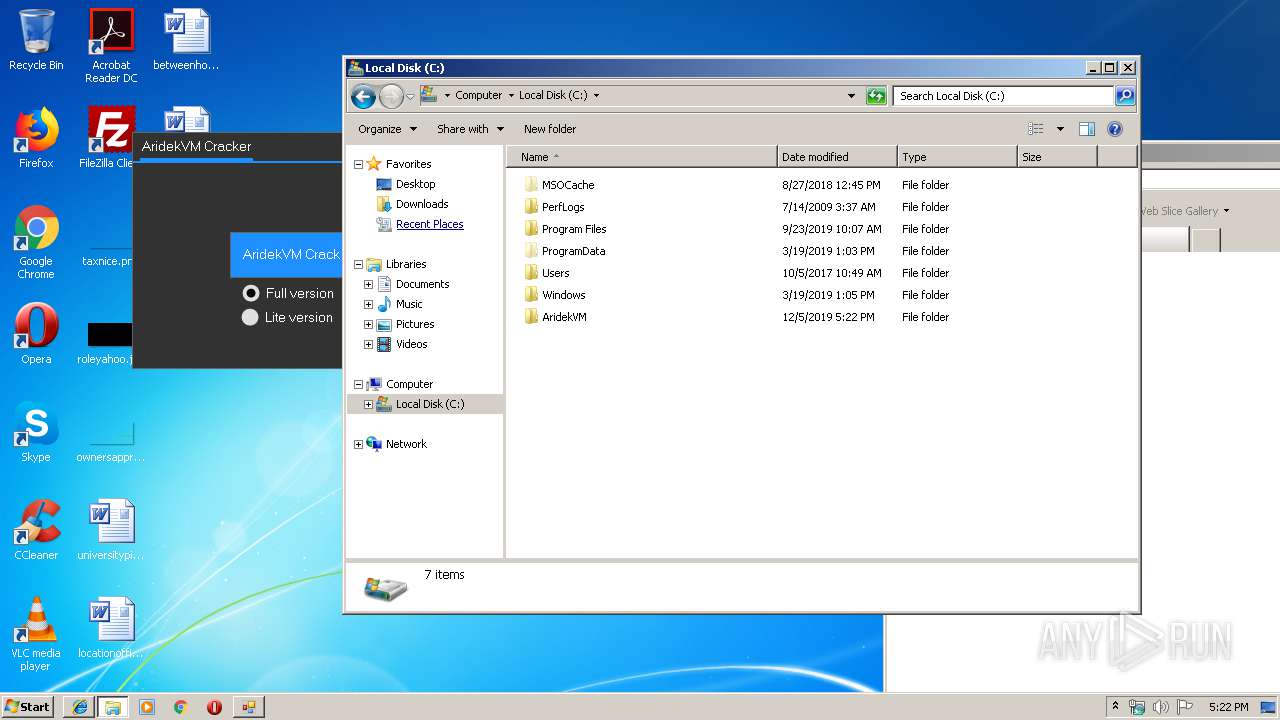
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E241C71A79271BC3EB9DA240F4E6FE0C |
| SHA1: | A2DA3AD3E5C4A81ADF9E9064D8212D78E27E1BCD |
| SHA256: | 65A71B7B0136EE94D2A8C9D83460F7936A669C52B9D5EAF86BE3882955437286 |
| SSDEEP: | 6144:/IIcrXQ4S33w614mazUBHfSdocWYD24N69AneYF/zRr0KVUdpbCz:ZcrNS33L10QdrXIqAneu7wdxCz |
MALICIOUS
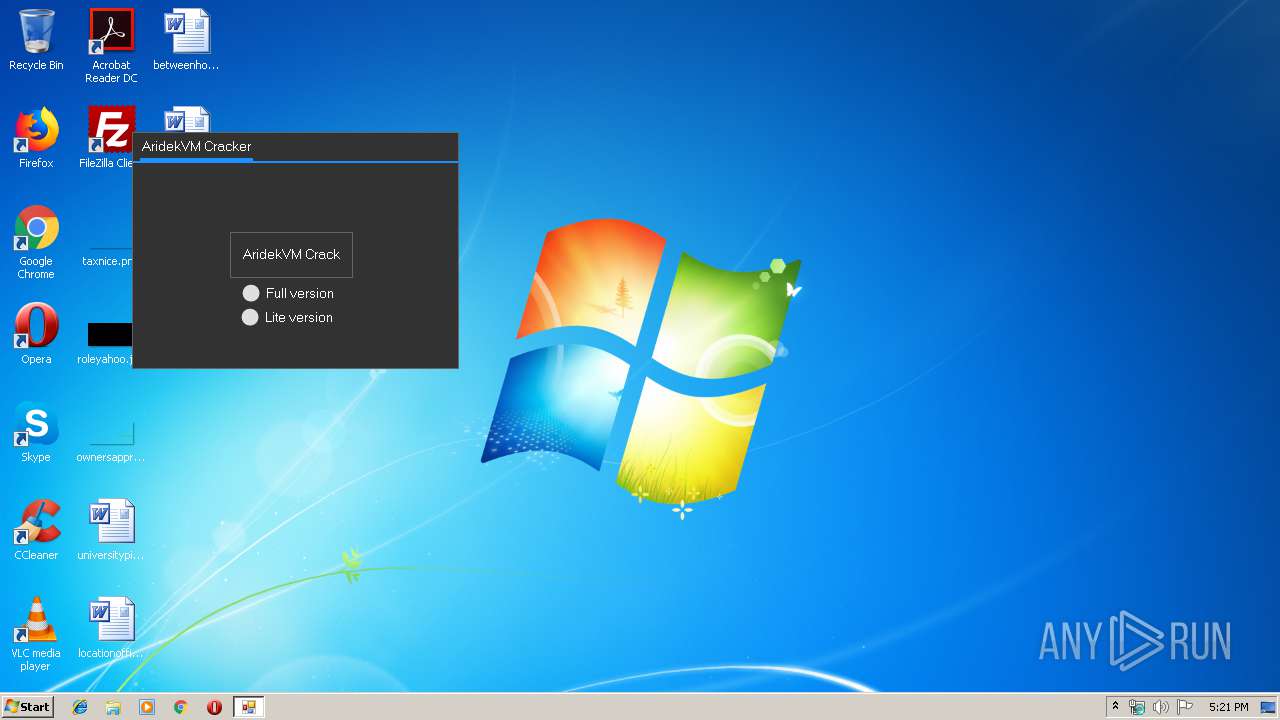
Application was dropped or rewritten from another process
- NVIDIAWeb.exe (PID: 1552)
- AridekVM Crack.exe (PID: 1296)
- NVIDIA Web Helper.exe (PID: 2548)
Writes to a start menu file
- NVIDIA Web Helper.exe (PID: 2548)
NJRAT was detected
- NVIDIA Web Helper.exe (PID: 2548)
Changes the autorun value in the registry
- NVIDIA Web Helper.exe (PID: 2548)
SUSPICIOUS
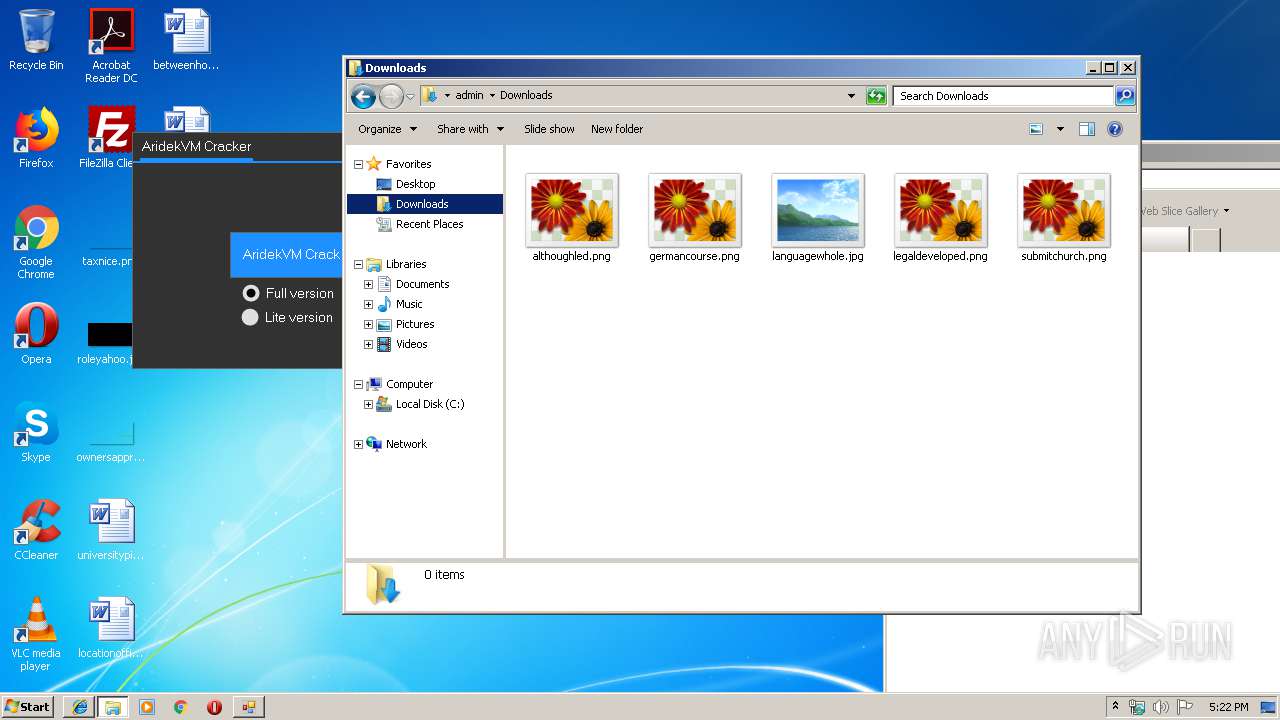
Creates files in the user directory
- AridekVM.exe (PID: 592)
- NVIDIAWeb.exe (PID: 1552)
- NVIDIA Web Helper.exe (PID: 2548)
Executable content was dropped or overwritten
- AridekVM.exe (PID: 592)
- NVIDIAWeb.exe (PID: 1552)
- NVIDIA Web Helper.exe (PID: 2548)
Starts itself from another location
- NVIDIAWeb.exe (PID: 1552)
Uses NETSH.EXE for network configuration
- NVIDIA Web Helper.exe (PID: 2548)
Connects to unusual port
- NVIDIA Web Helper.exe (PID: 2548)
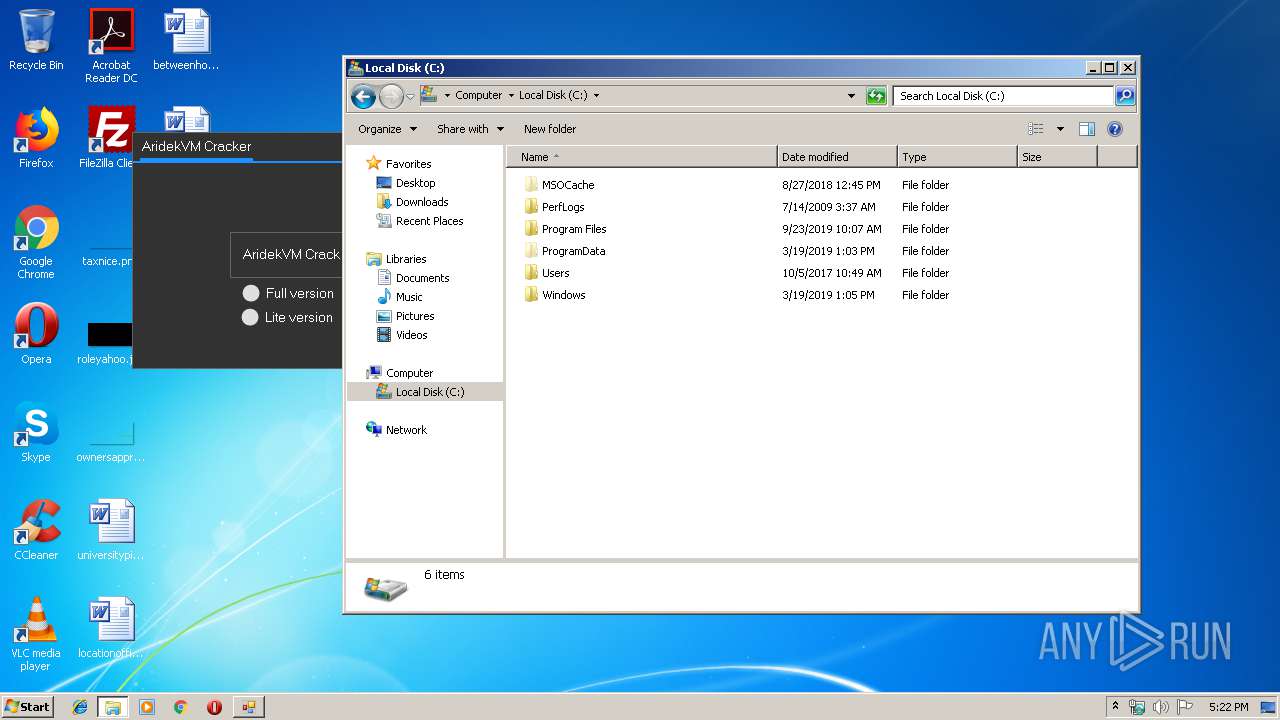
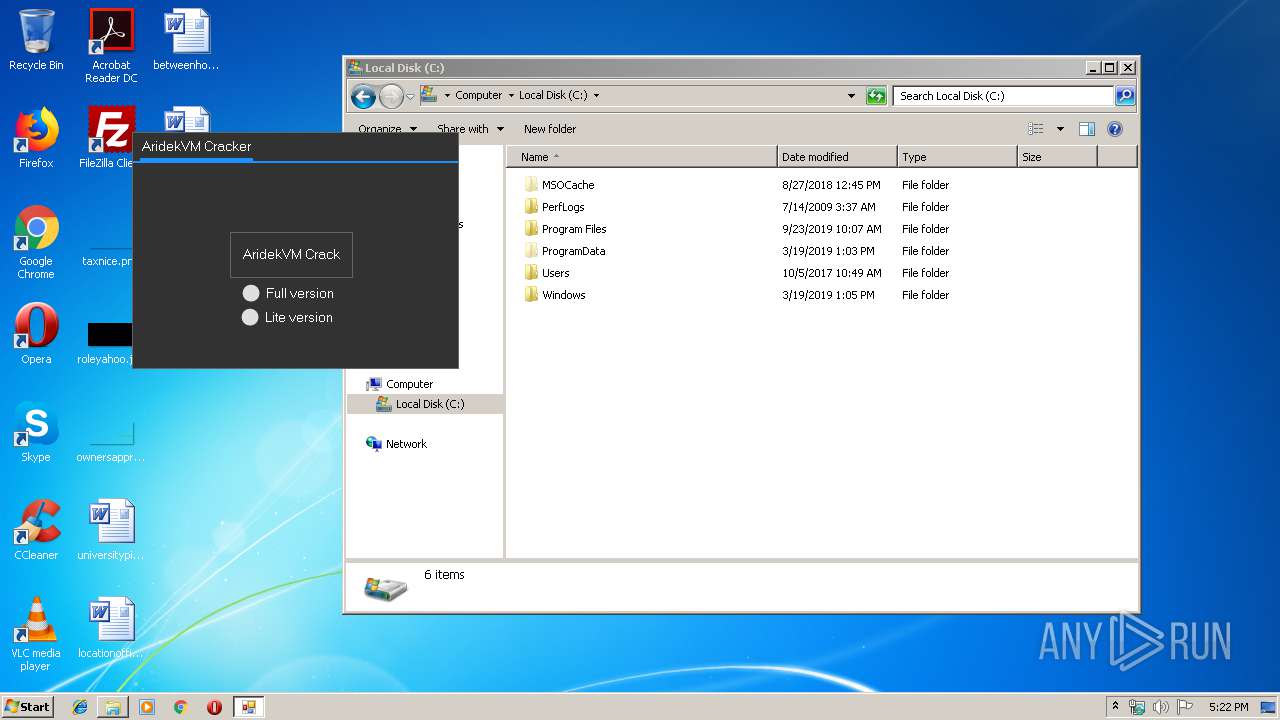
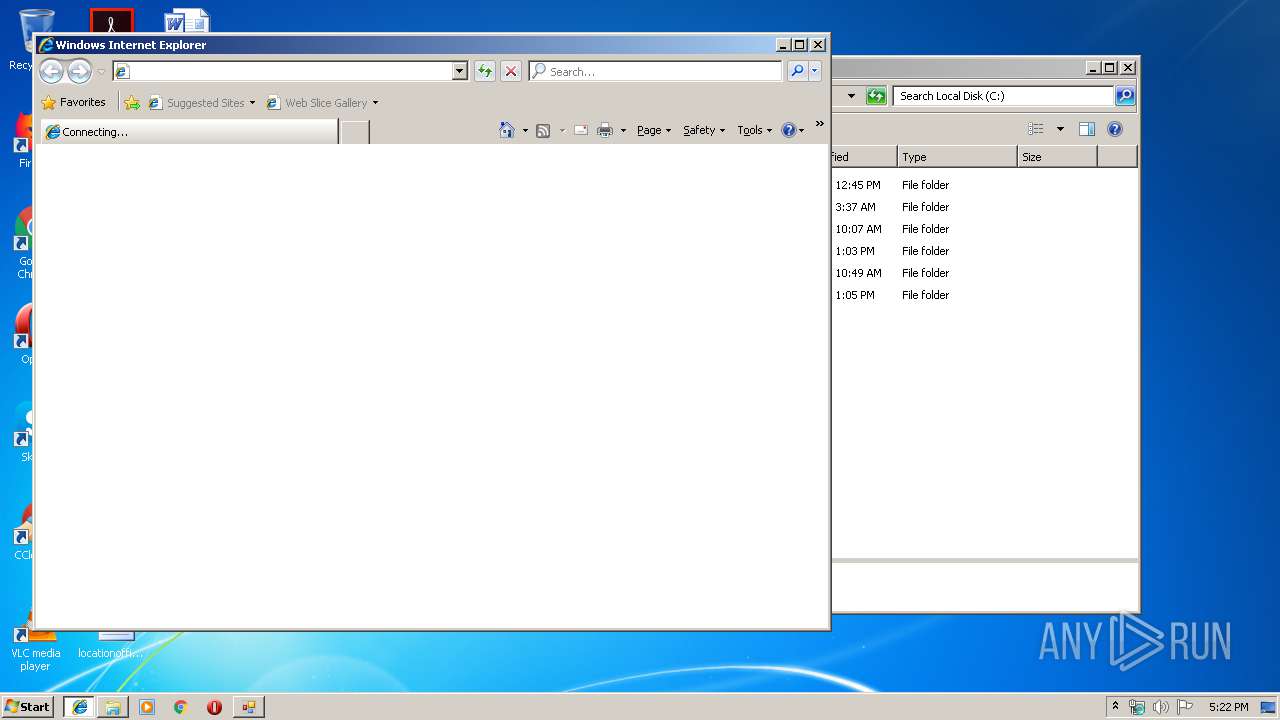
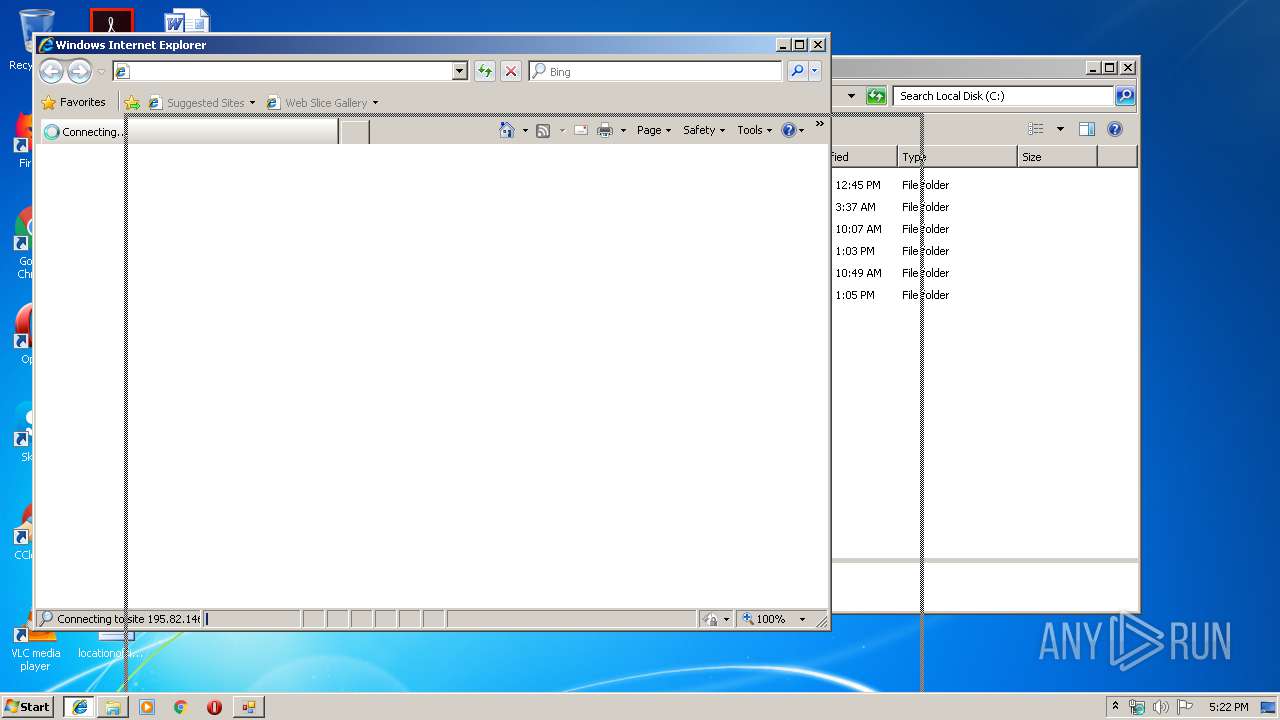
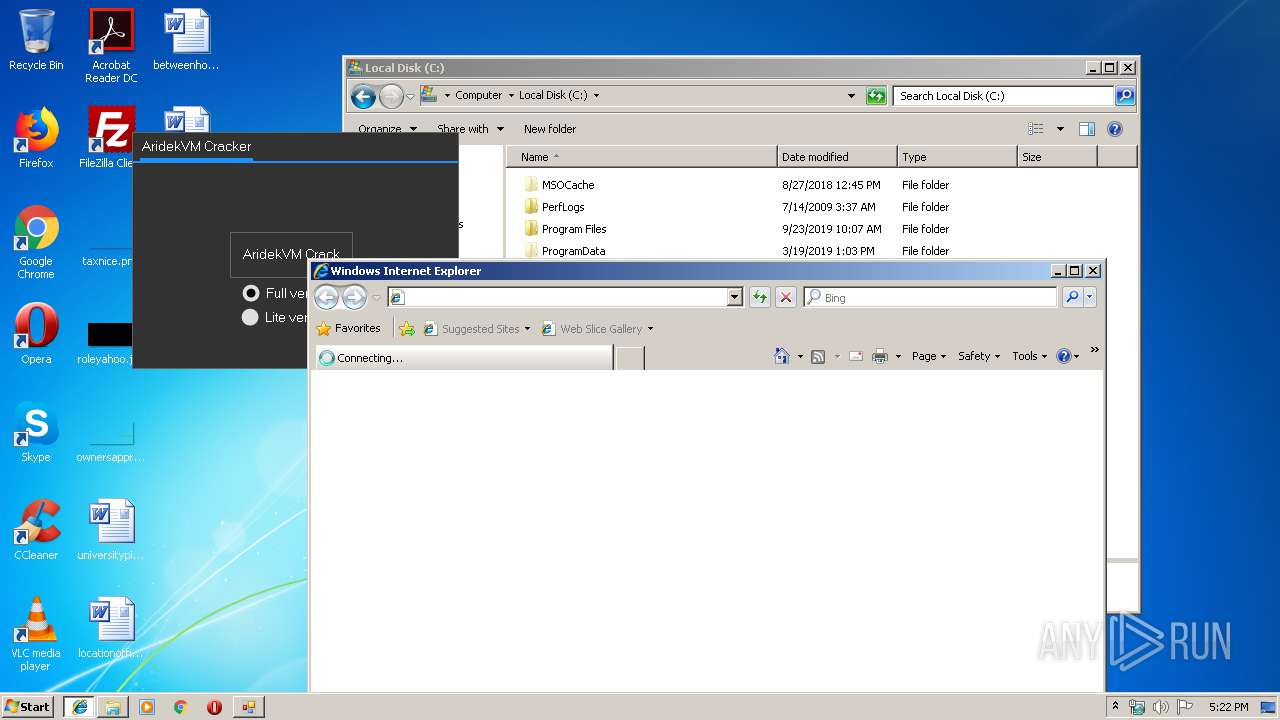
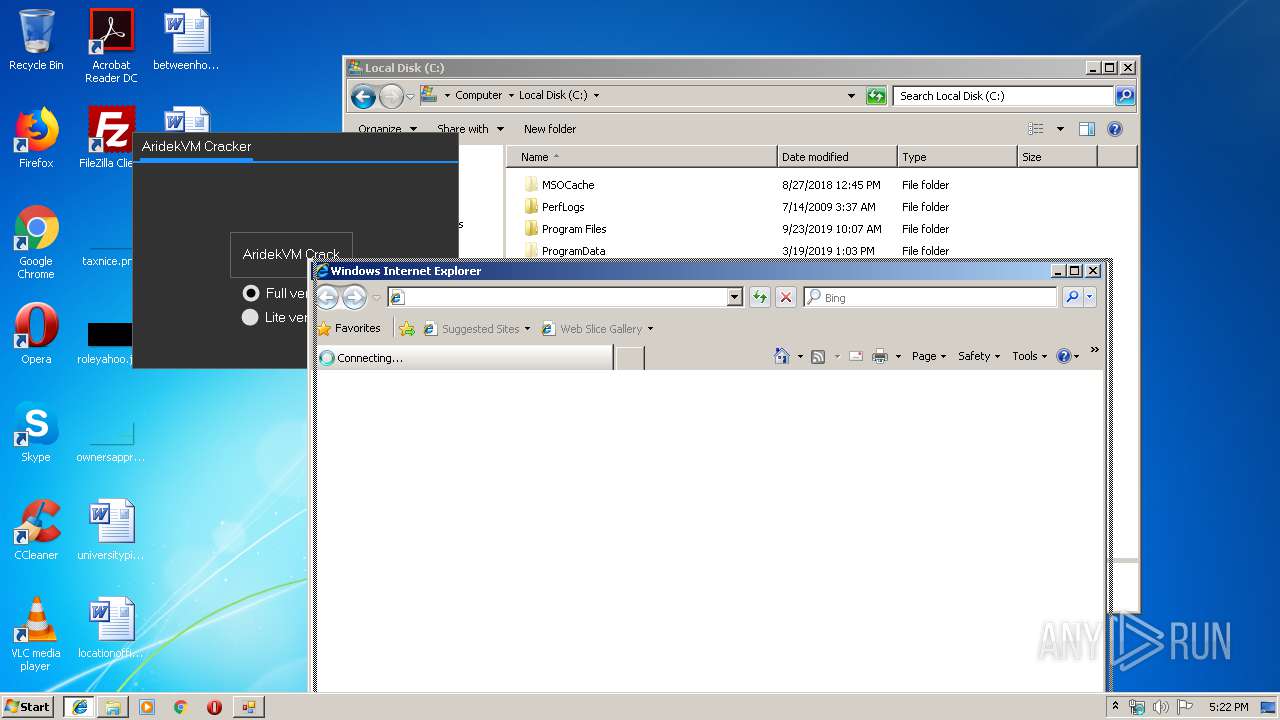
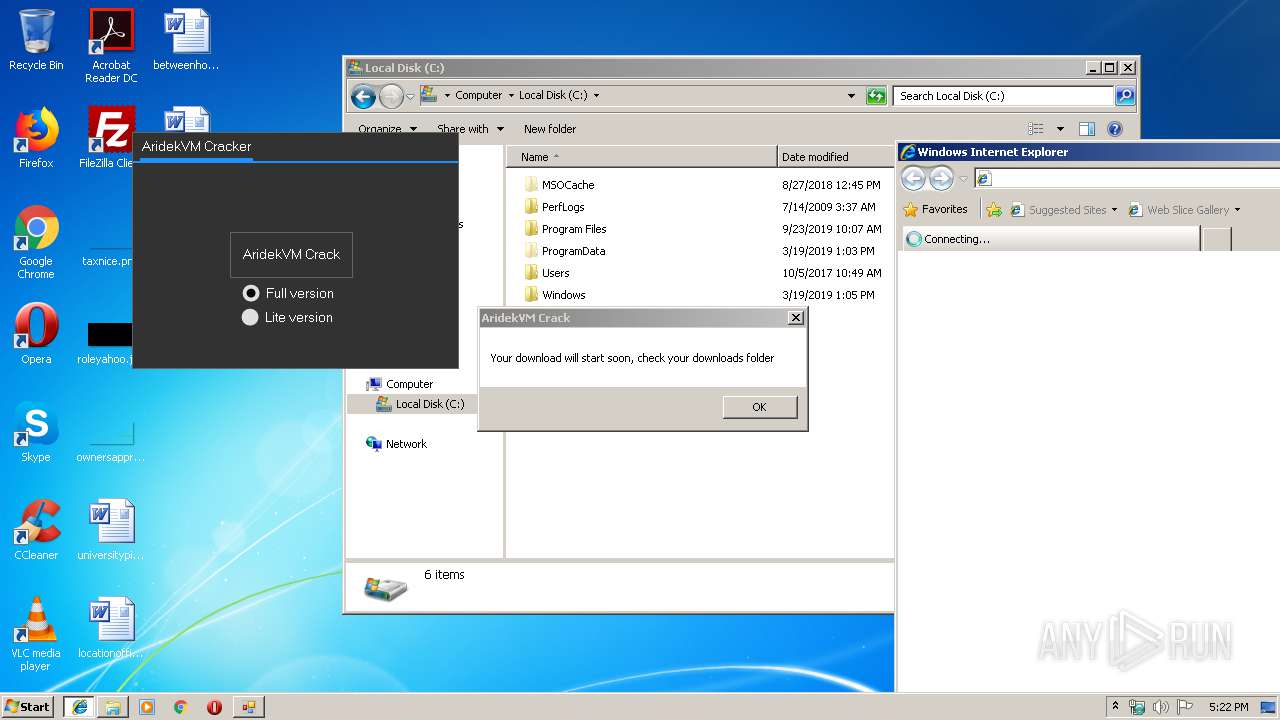
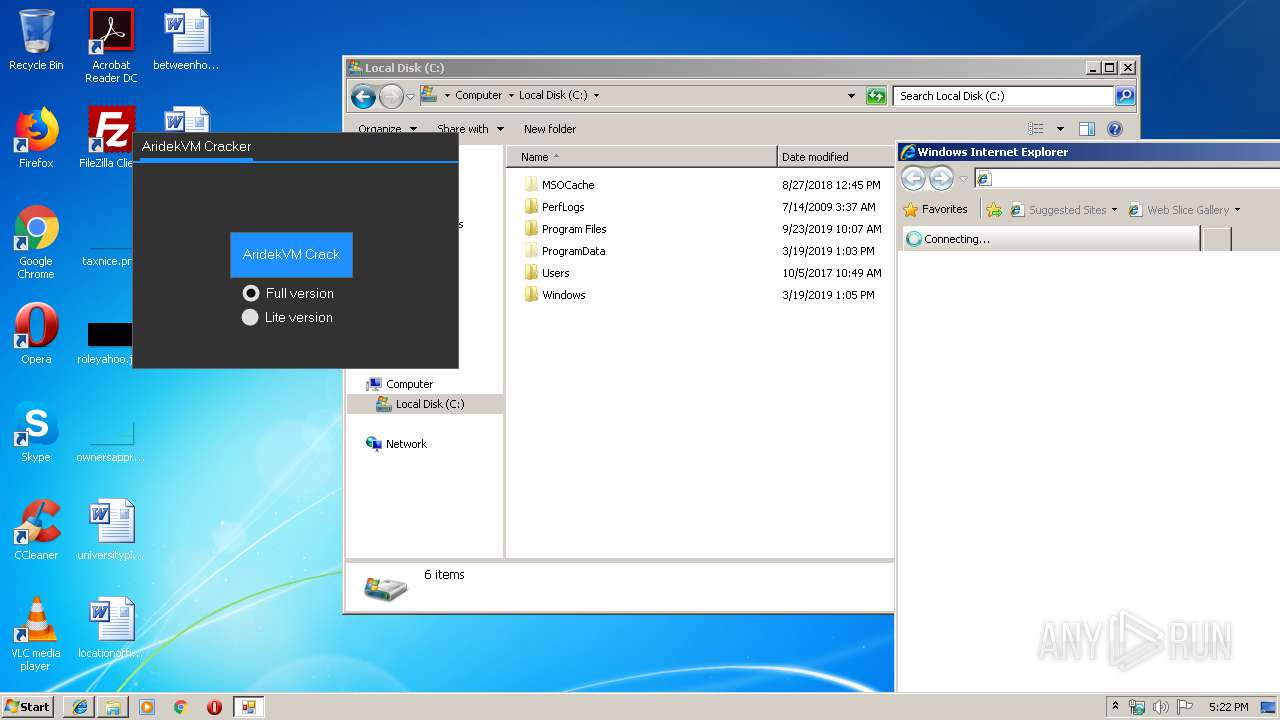
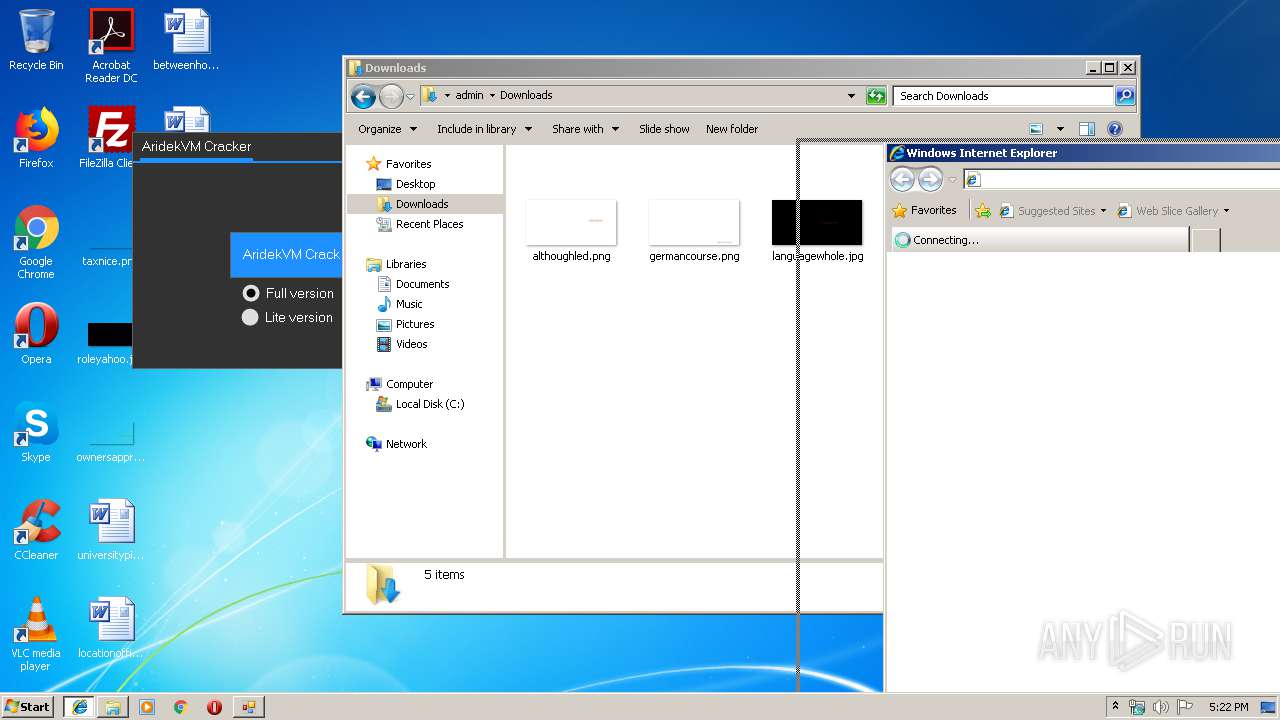
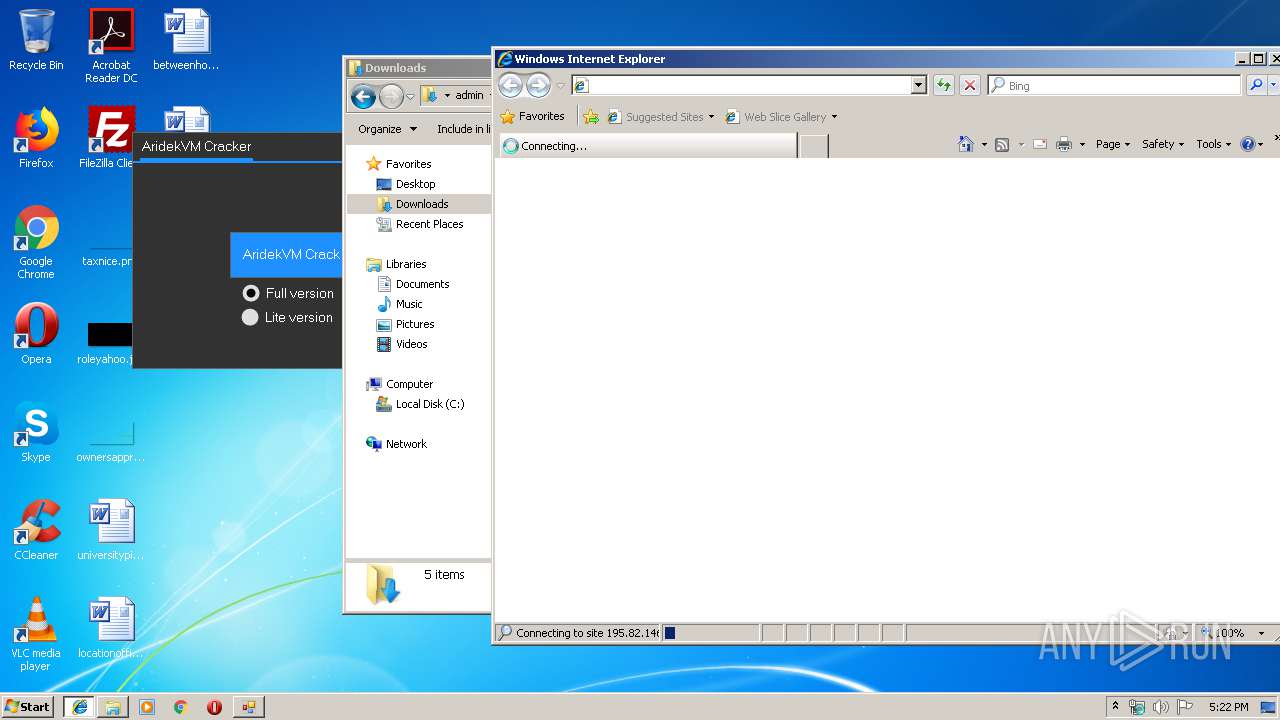
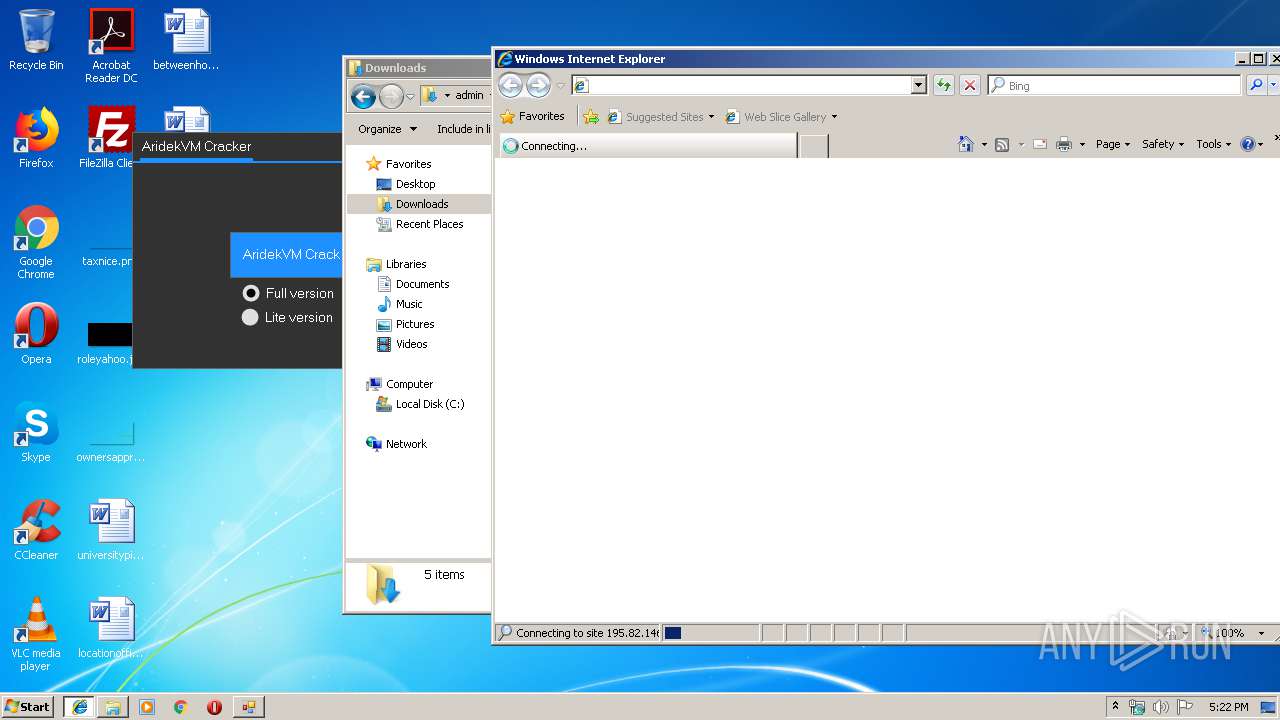
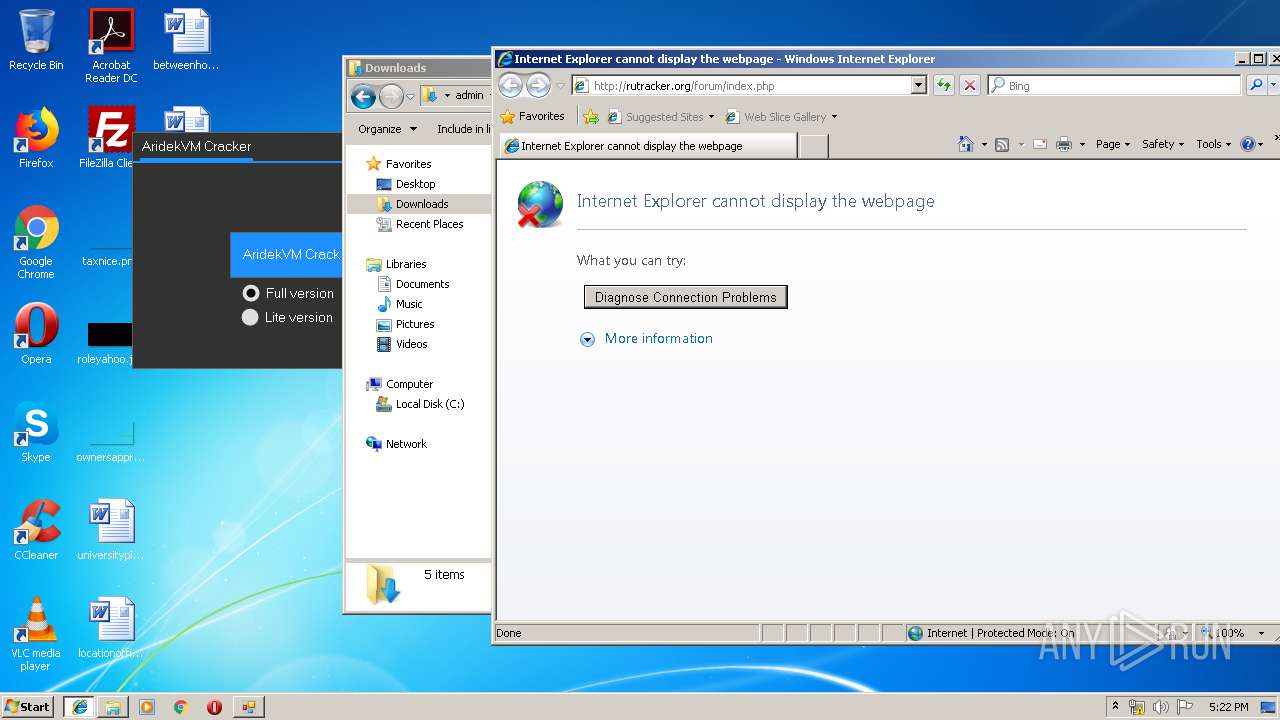
Starts Internet Explorer
- AridekVM Crack.exe (PID: 1296)
INFO
Manual execution by user
- explorer.exe (PID: 2128)
Changes internet zones settings
- iexplore.exe (PID: 1504)
Reads Internet Cache Settings
- iexplore.exe (PID: 2248)
Reads settings of System Certificates
- AridekVM Crack.exe (PID: 1296)
Reads internet explorer settings
- iexplore.exe (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:27 22:03:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 240640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d759 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2019 20:03:27 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 27-Apr-2019 20:03:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E854 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69231 |
.rdata | 0x00030000 | 0x00009A9C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13286 |
.data | 0x0003A000 | 0x000213D0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.25381 |
.gfids | 0x0005C000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.11154 |
.rsrc | 0x0005D000 | 0x0002E020 | 0x0002E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.94802 |
.reloc | 0x0008C000 | 0x00001FCC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64554 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.45536 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 3.13064 | 38056 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 3.01562 | 21640 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 2.71037 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 3.3296 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.15447 | 494 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
43
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Users\admin\AppData\Local\Temp\AridekVM.exe" | C:\Users\admin\AppData\Local\Temp\AridekVM.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1296 | "C:\Users\admin\AppData\Roaming\AridekVM Crack.exe" | C:\Users\admin\AppData\Roaming\AridekVM Crack.exe | AridekVM.exe | ||||||||||||
User: admin Company: 27805 Integrity Level: MEDIUM Description: AridekVM Crack Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | AridekVM Crack.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1552 | "C:\Users\admin\AppData\Roaming\NVIDIAWeb.exe" | C:\Users\admin\AppData\Roaming\NVIDIAWeb.exe | AridekVM.exe | ||||||||||||
User: admin Company: NVIDIA Corporation Integrity Level: MEDIUM Description: NVIDIA Web Helper Exit code: 0 Version: 1.841.2.74 Modules
| |||||||||||||||
| 2128 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2232 | netsh firewall add allowedprogram "C:\Users\admin\AppData\Roaming\NVIDIA Web Helper.exe" "NVIDIA Web Helper.exe" ENABLE | C:\Windows\system32\netsh.exe | — | NVIDIA Web Helper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1504 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | "C:\Users\admin\AppData\Roaming\NVIDIA Web Helper.exe" | C:\Users\admin\AppData\Roaming\NVIDIA Web Helper.exe | NVIDIAWeb.exe | ||||||||||||
User: admin Company: NVIDIA Corporation Integrity Level: MEDIUM Description: NVIDIA Web Helper Exit code: 0 Version: 1.841.2.74 Modules
| |||||||||||||||
Total events
1 265
Read events
1 078
Write events
187
Delete events
0
Modification events
| (PID) Process: | (592) AridekVM.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (592) AridekVM.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1552) NVIDIAWeb.exe | Key: | HKEY_CURRENT_USER |
| Operation: | write | Name: | di |
Value: ! | |||
| (PID) Process: | (1552) NVIDIAWeb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1552) NVIDIAWeb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2548) NVIDIA Web Helper.exe | Key: | HKEY_CURRENT_USER |
| Operation: | write | Name: | di |
Value: ! | |||
| (PID) Process: | (2548) NVIDIA Web Helper.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | SEE_MASK_NOZONECHECKS |
Value: 1 | |||
| (PID) Process: | (2232) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2232) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2232) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
Executable files
4
Suspicious files
0
Text files
15
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 592 | AridekVM.exe | C:\Users\admin\AppData\Roaming\NVIDIAWeb.exe | executable | |
MD5:9A43242ADF33A285138FDD85FC4BB9EB | SHA256:46174E61E18145897E93135E42767F0BB35E7536684D08CEABDEEA9D885D5740 | |||
| 592 | AridekVM.exe | C:\Users\admin\AppData\Roaming\AridekVM Crack.exe | executable | |
MD5:A1F34AD1259D61129B5F40AEAF50F6AE | SHA256:2EE1306925BB41A5B53E7916B54B67C7828DE51C90667668328603461121F0D5 | |||
| 1552 | NVIDIAWeb.exe | C:\Users\admin\AppData\Roaming\NVIDIA Web Helper.exe | executable | |
MD5:9A43242ADF33A285138FDD85FC4BB9EB | SHA256:46174E61E18145897E93135E42767F0BB35E7536684D08CEABDEEA9D885D5740 | |||
| 2248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:3B0DE898A391663C7E4FEA9288A82D30 | SHA256:5827B5FD9FD43B2475E878C031587AA4F8F7BDD1C8A4D55F4B03163E1008CE68 | |||
| 2548 | NVIDIA Web Helper.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\cf21d9e2774174a79b8b0c536b471eed.exe | executable | |
MD5:9A43242ADF33A285138FDD85FC4BB9EB | SHA256:46174E61E18145897E93135E42767F0BB35E7536684D08CEABDEEA9D885D5740 | |||
| 2248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\96TGJYWF\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\E37B3GBL\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OU75HTX8\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1504 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2548 | NVIDIA Web Helper.exe | 141.255.151.10:1177 | fodasse.duckdns.org | Lost Oasis SARL | FR | malicious |
1504 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2248 | iexplore.exe | 195.82.146.214:80 | rutracker.org | Dreamtorrent Corp | RU | unknown |
1296 | AridekVM Crack.exe | 109.238.11.157:443 | srv-file5.gofile.io | Ikoula Net SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fodasse.duckdns.org |
| malicious |
www.bing.com |
| whitelisted |
rutracker.org |
| whitelisted |
srv-file5.gofile.io |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |